| File name: | LaunchMacrobond.exe |
| Full analysis: | https://app.any.run/tasks/934ce2ed-ef7a-4a20-8d1d-cbb2fd67e853 |
| Verdict: | Malicious activity |
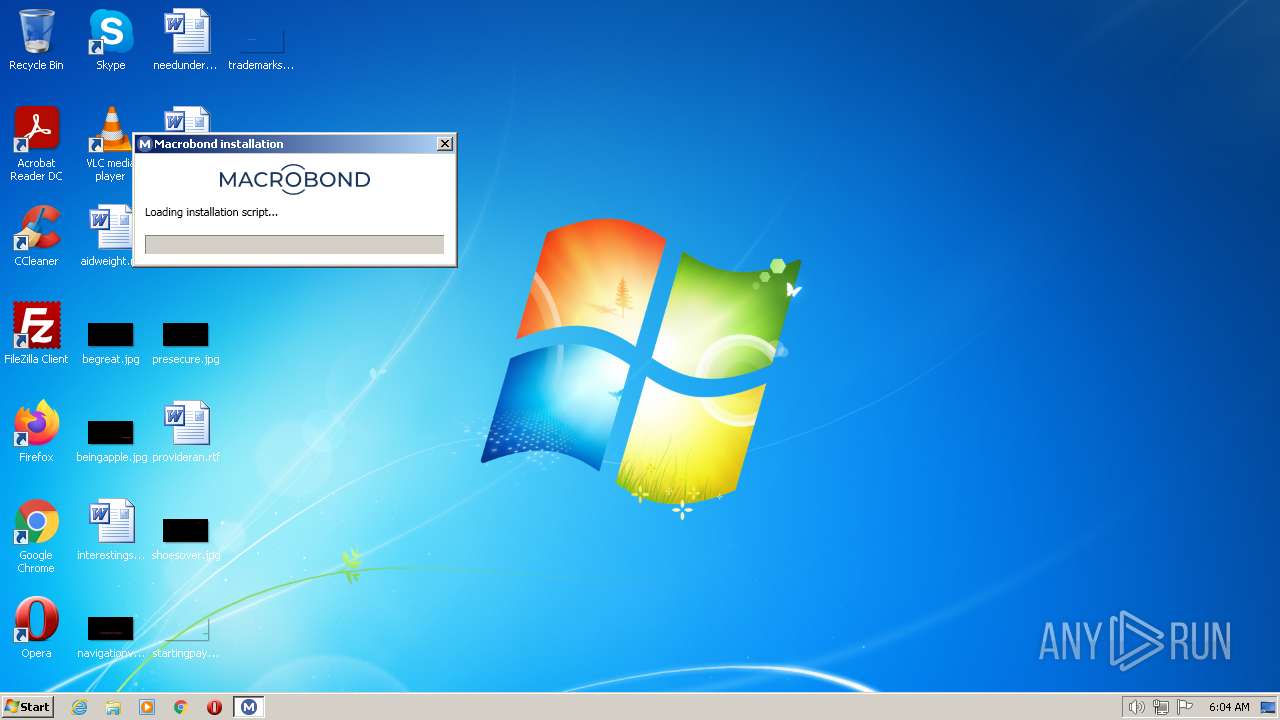
| Analysis date: | December 06, 2022, 06:04:51 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 71D0744EEEA6ED3932BE8AD980E54DBD |
| SHA1: | 8120D498527A397A1EE8DAC56BF9A0C3F502247A |
| SHA256: | 043D3D03D72427042C38ECB64433CD812084E19CDF90969C6860E62D7C05391B |
| SSDEEP: | 3072:eNQ2/osDXEEeDCWu6irWrJCputUrsrUjUKyDC:6CCmCvUVC |
MALICIOUS
No malicious indicators.SUSPICIOUS
Adds/modifies Windows certificates
- LaunchMacrobond.exe (PID: 2056)
Reads settings of System Certificates
- LaunchMacrobond.exe (PID: 2056)
- msiexec.exe (PID: 292)
Reads the Internet Settings
- LaunchMacrobond.exe (PID: 2056)
INFO
Checks supported languages
- LaunchMacrobond.exe (PID: 2056)
Reads Environment values
- LaunchMacrobond.exe (PID: 2056)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 292)
Reads the computer name
- LaunchMacrobond.exe (PID: 2056)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 2048-Dec-01 16:37:19 |
| Debug artifacts: |
|
| Comments: | Macrobond Bootstrapper |
| CompanyName: | Macrobond Financial |
| FileDescription: | Macrobond Bootstrapper |
| FileVersion: | 1.0.28.12390 |
| InternalName: | LaunchMacrobond.exe |
| LegalCopyright: | Copyright © 2009-2021 Macrobond Financial |
| OriginalFilename: | LaunchMacrobond.exe |
| ProductName: | MacrobondBootstrapper |
| ProductVersion: | 1.0.28.12390 |
| Assembly Version: | 1.0.28.12390 |
DOS Header
| e_magic: | MZ |
|---|---|
| e_cblp: | 144 |
| e_cp: | 3 |
| e_crlc: | - |
| e_cparhdr: | 4 |
| e_minalloc: | - |
| e_maxalloc: | 65535 |
| e_ss: | - |
| e_sp: | 184 |
| e_csum: | - |
| e_ip: | - |
| e_cs: | - |
| e_ovno: | - |
| e_oemid: | - |
| e_oeminfo: | - |
| e_lfanew: | 128 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| NumberofSections: | 3 |
| TimeDateStamp: | 2048-Dec-01 16:37:19 |
| PointerToSymbolTable: | - |
| NumberOfSymbols: | - |
| SizeOfOptionalHeader: | 224 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 8192 | 156376 | 156672 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 4.42982 |
.rsrc | 172032 | 131604 | 132096 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.71691 |
.reloc | 311296 | 12 | 512 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.10191 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 7.64306 | 3810 | UNKNOWN | UNKNOWN | RT_ICON |
2 | 1.97961 | 19496 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 2.65787 | 5672 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 3.69907 | 2216 | UNKNOWN | UNKNOWN | RT_ICON |
5 | 4.23758 | 1384 | UNKNOWN | UNKNOWN | RT_ICON |
6 | 7.74132 | 5626 | UNKNOWN | UNKNOWN | RT_ICON |
7 | 2.44042 | 67624 | UNKNOWN | UNKNOWN | RT_ICON |
8 | 2.5786 | 16936 | UNKNOWN | UNKNOWN | RT_ICON |
9 | 2.78255 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
10 | 3.0498 | 1128 | UNKNOWN | UNKNOWN | RT_ICON |
Imports
mscoree.dll |
Total processes
39
Monitored processes
5
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
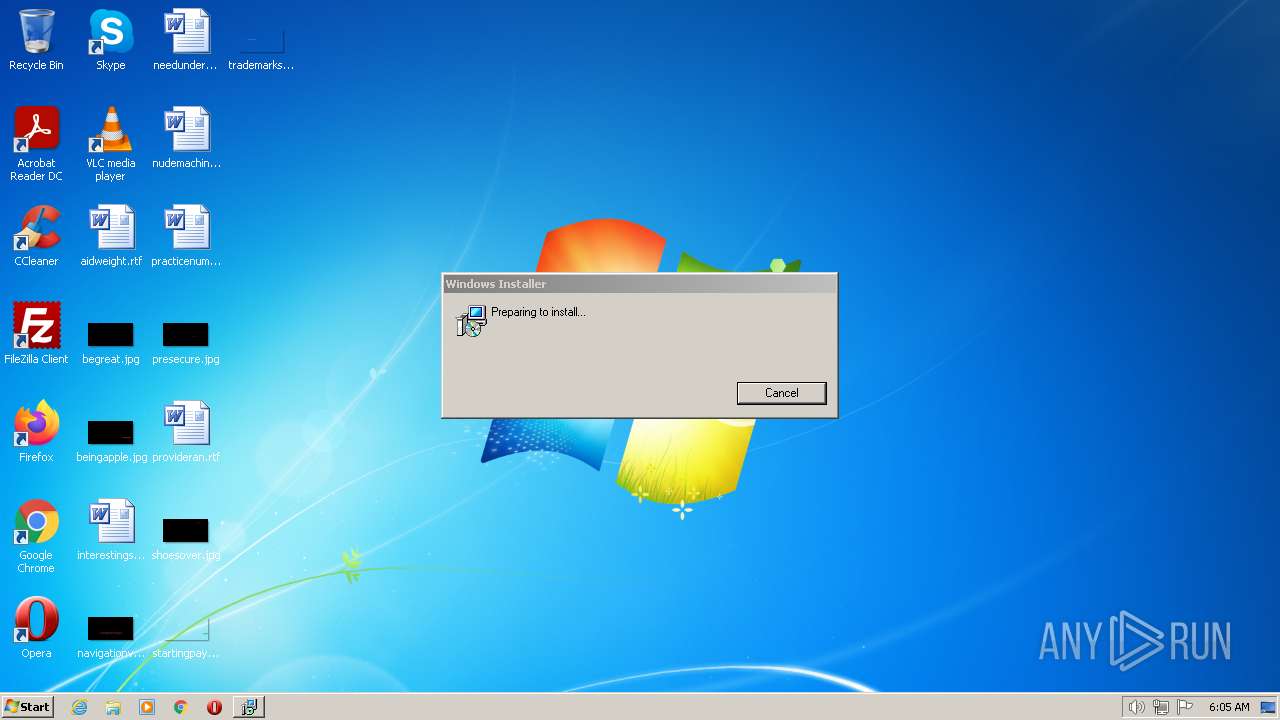
| 292 | "C:\Windows\System32\msiexec.exe" /i "C:\Users\admin\AppData\Local\Temp\Macrobond\422e823b0ed345299119e7c9be14dea8\Macrobond.msi" PATCH="https://download.macrobond.com/installation/mainapp/1.23.0.3853-release/Patch-1.25.105.21508-release.msp" MBSOURCEURL="https://download.macrobond.com/installation/mainapp/1.23.0.3853-release" | C:\Windows\System32\msiexec.exe | LaunchMacrobond.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1996 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2056 | "C:\Users\admin\AppData\Local\Temp\LaunchMacrobond.exe" | C:\Users\admin\AppData\Local\Temp\LaunchMacrobond.exe | Explorer.EXE | ||||||||||||
User: admin Company: Macrobond Financial Integrity Level: MEDIUM Description: Macrobond Bootstrapper Exit code: 0 Version: 1.0.28.12390 Modules
| |||||||||||||||
| 2948 | "C:\Windows\SYSTEM32\WISPTIS.EXE" /ManualLaunch; | C:\Windows\SYSTEM32\WISPTIS.EXE | — | LaunchMacrobond.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Pen and Touch Input Component Exit code: 3221226540 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2996 | "C:\Windows\SYSTEM32\WISPTIS.EXE" /ManualLaunch; | C:\Windows\SYSTEM32\WISPTIS.EXE | LaunchMacrobond.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Pen and Touch Input Component Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
7 219
Read events
7 112
Write events
101
Delete events
6
Modification events
| (PID) Process: | (2056) LaunchMacrobond.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: LaunchMacrobond.exe | |||
| (PID) Process: | (2056) LaunchMacrobond.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\LaunchMacrobond_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2056) LaunchMacrobond.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\LaunchMacrobond_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2056) LaunchMacrobond.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\LaunchMacrobond_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (2056) LaunchMacrobond.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\LaunchMacrobond_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (2056) LaunchMacrobond.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\LaunchMacrobond_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (2056) LaunchMacrobond.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\LaunchMacrobond_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (2056) LaunchMacrobond.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\LaunchMacrobond_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2056) LaunchMacrobond.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\LaunchMacrobond_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2056) LaunchMacrobond.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\LaunchMacrobond_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
Executable files
0
Suspicious files
2
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2056 | LaunchMacrobond.exe | C:\Users\admin\AppData\Local\Temp\Macrobond\422e823b0ed345299119e7c9be14dea8\Macrobond.msi | — | |
MD5:— | SHA256:— | |||
| 2056 | LaunchMacrobond.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\77EC63BDA74BD0D0E0426DC8F8008506 | binary | |
MD5:— | SHA256:— | |||
| 2056 | LaunchMacrobond.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\77EC63BDA74BD0D0E0426DC8F8008506 | compressed | |
MD5:FC4666CBCA561E864E7FDF883A9E6661 | SHA256:10F3DEB6C452D749A7451B5D065F4C0449737E5EE8A44F4D15844B503141E65B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
7
DNS requests
3
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2056 | LaunchMacrobond.exe | GET | 200 | 8.248.141.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?c31f2d6cb58f7fcf | US | compressed | 61.4 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2056 | LaunchMacrobond.exe | 8.248.141.254:80 | ctldl.windowsupdate.com | LEVEL3 | US | suspicious |
2056 | LaunchMacrobond.exe | 79.136.101.43:443 | download.macrobond.com | Bahnhof AB | SE | suspicious |
2056 | LaunchMacrobond.exe | 79.136.101.36:443 | app1.macrobondfinancial.com | Bahnhof AB | SE | unknown |
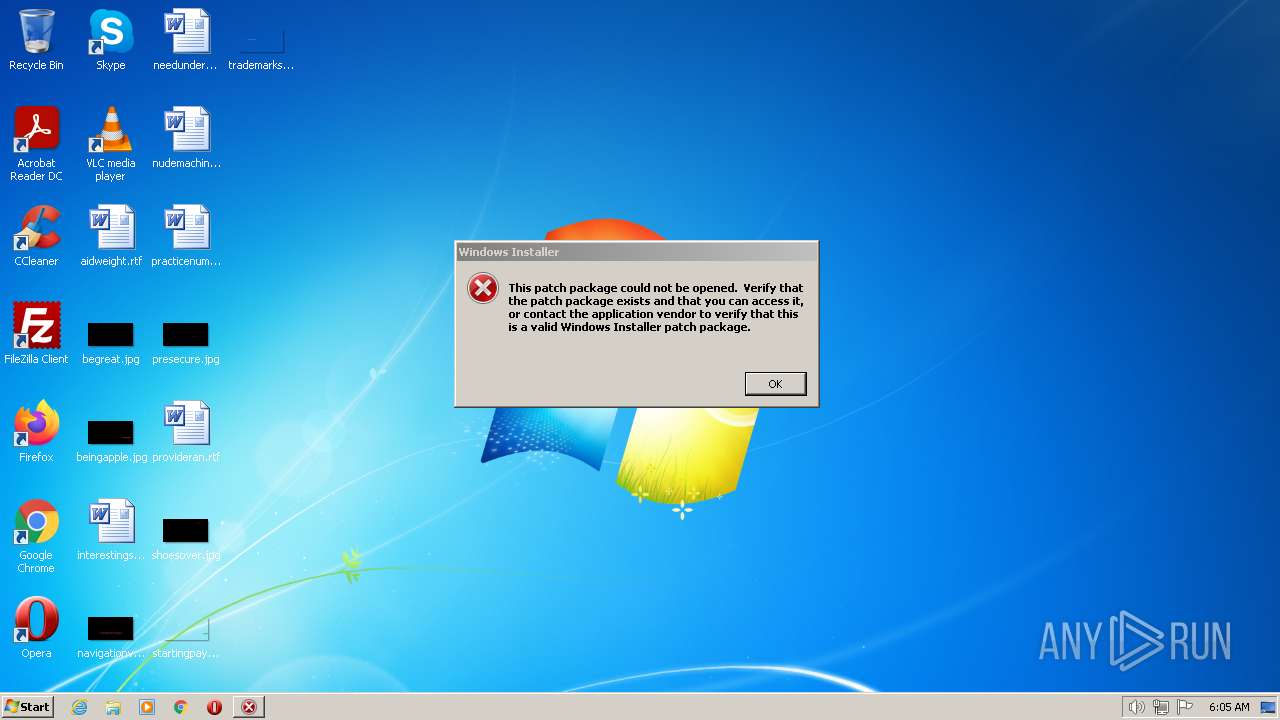
292 | msiexec.exe | 79.136.101.43:443 | download.macrobond.com | Bahnhof AB | SE | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
app1.macrobondfinancial.com |
| unknown |
download.macrobond.com |
| suspicious |
ctldl.windowsupdate.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
292 | msiexec.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |