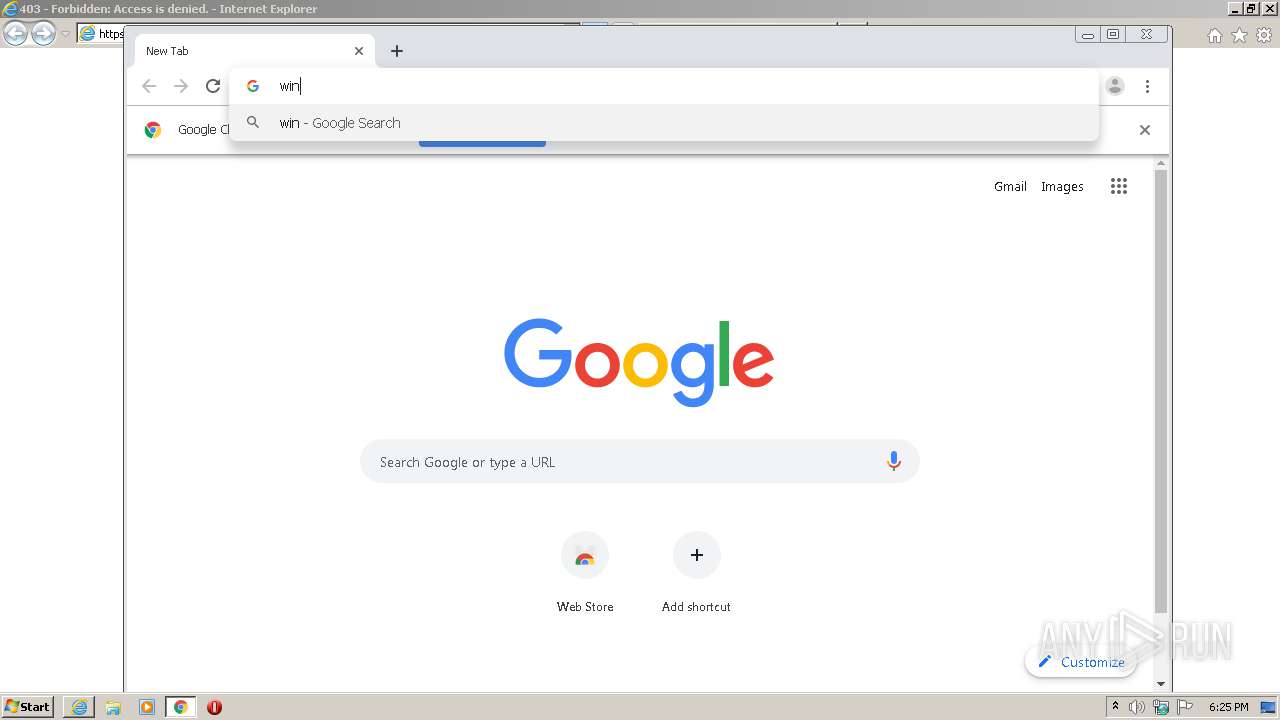
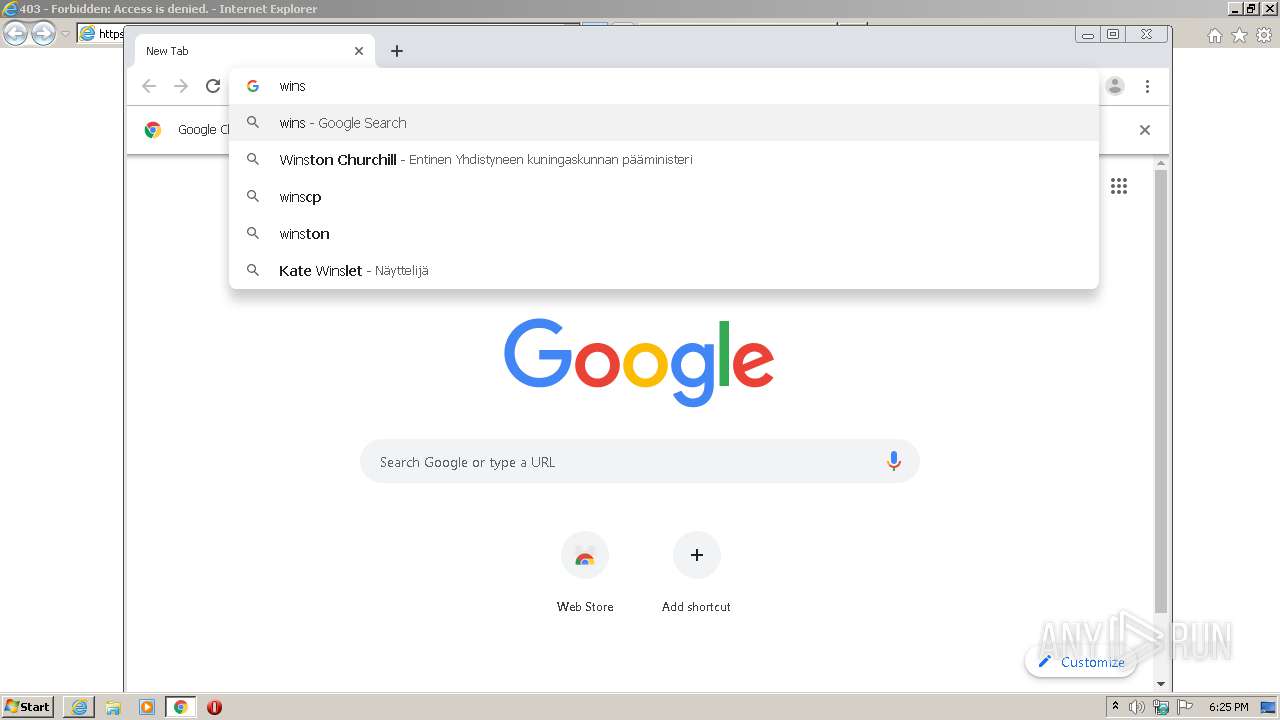
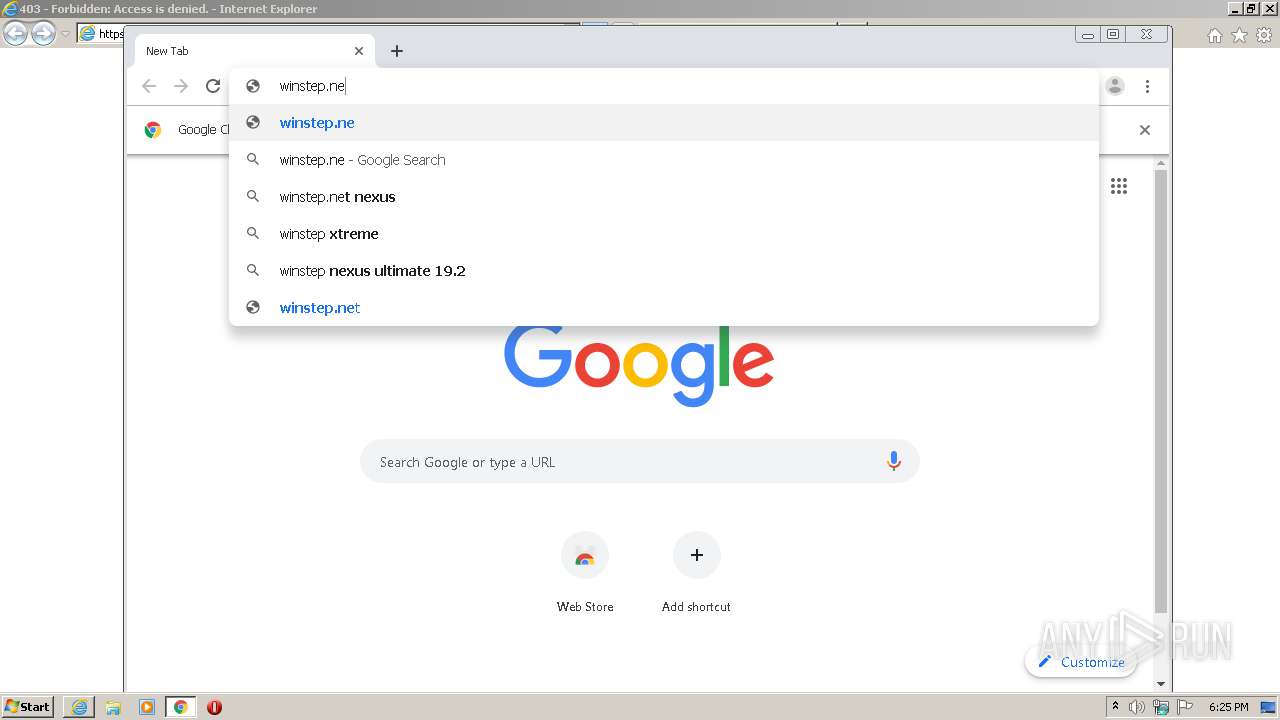
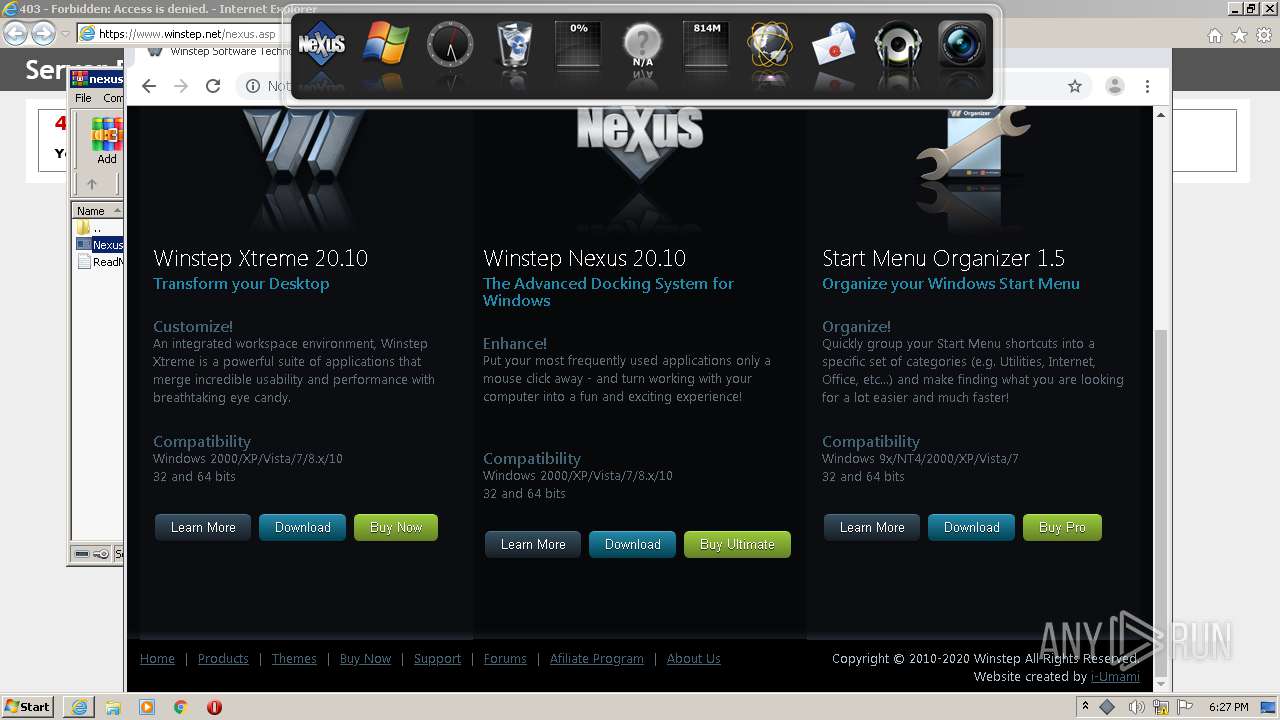
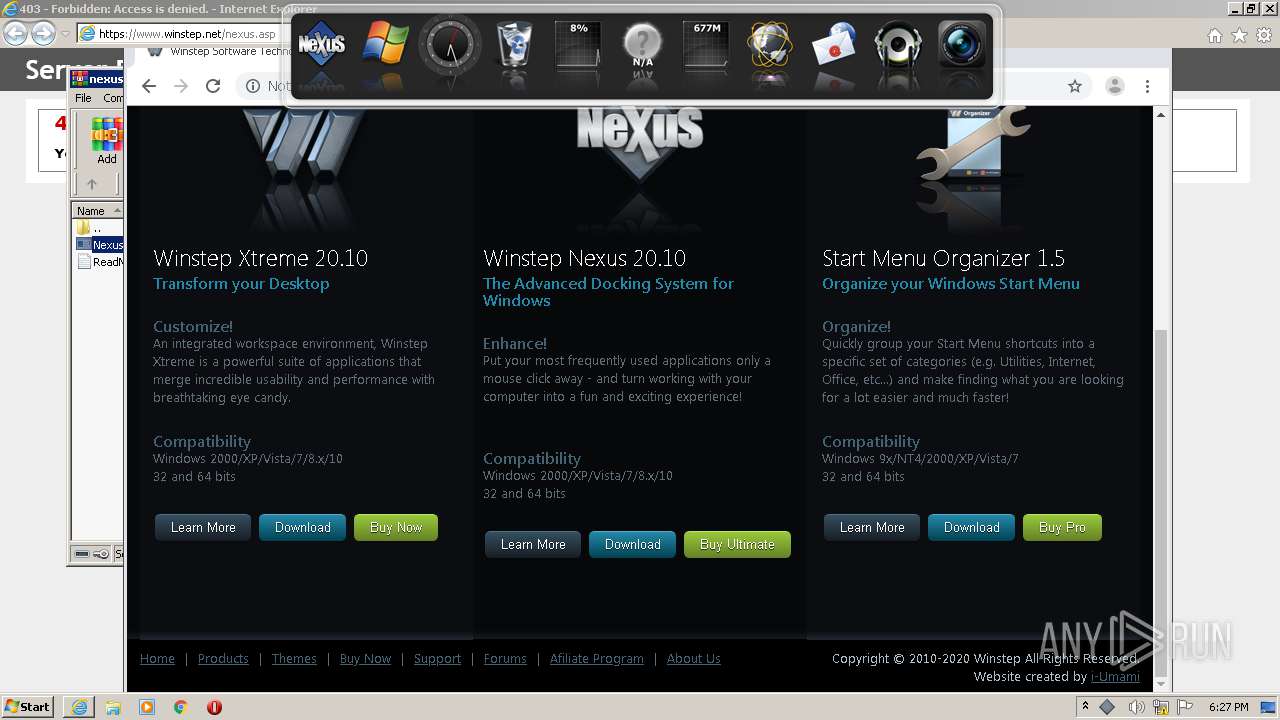
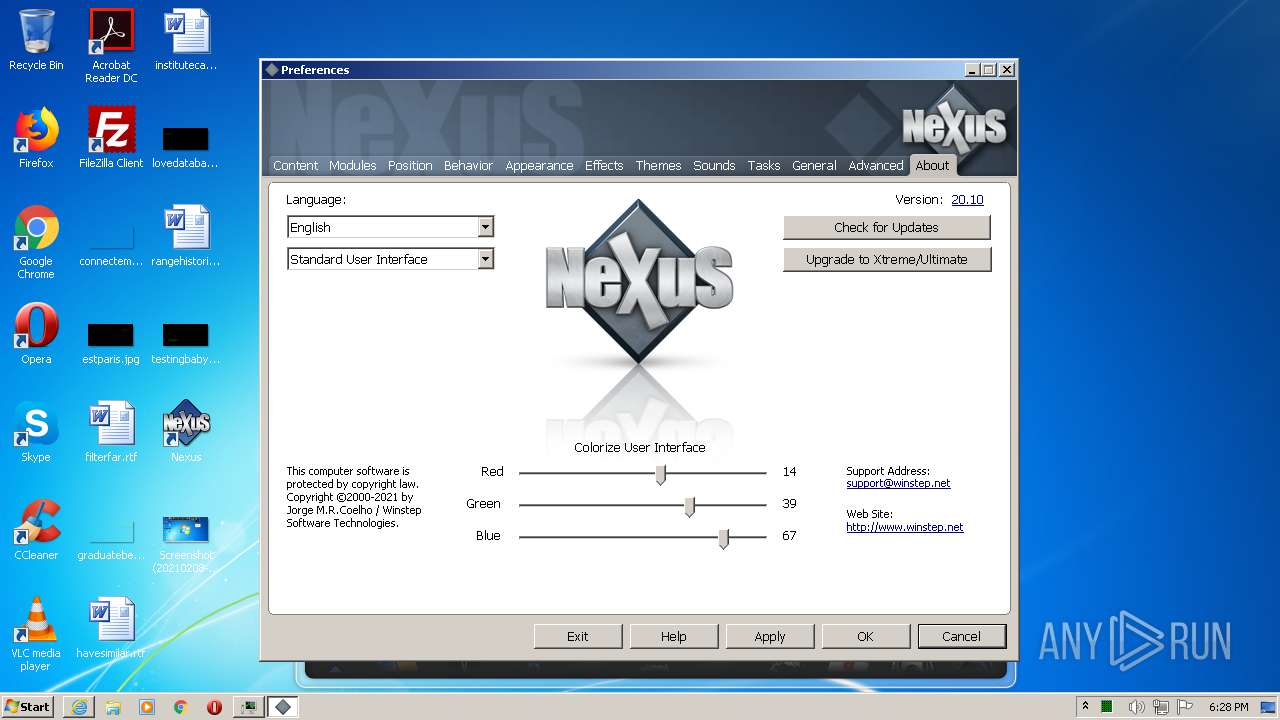
| URL: | https://www.winstep.net/nexus.asp |
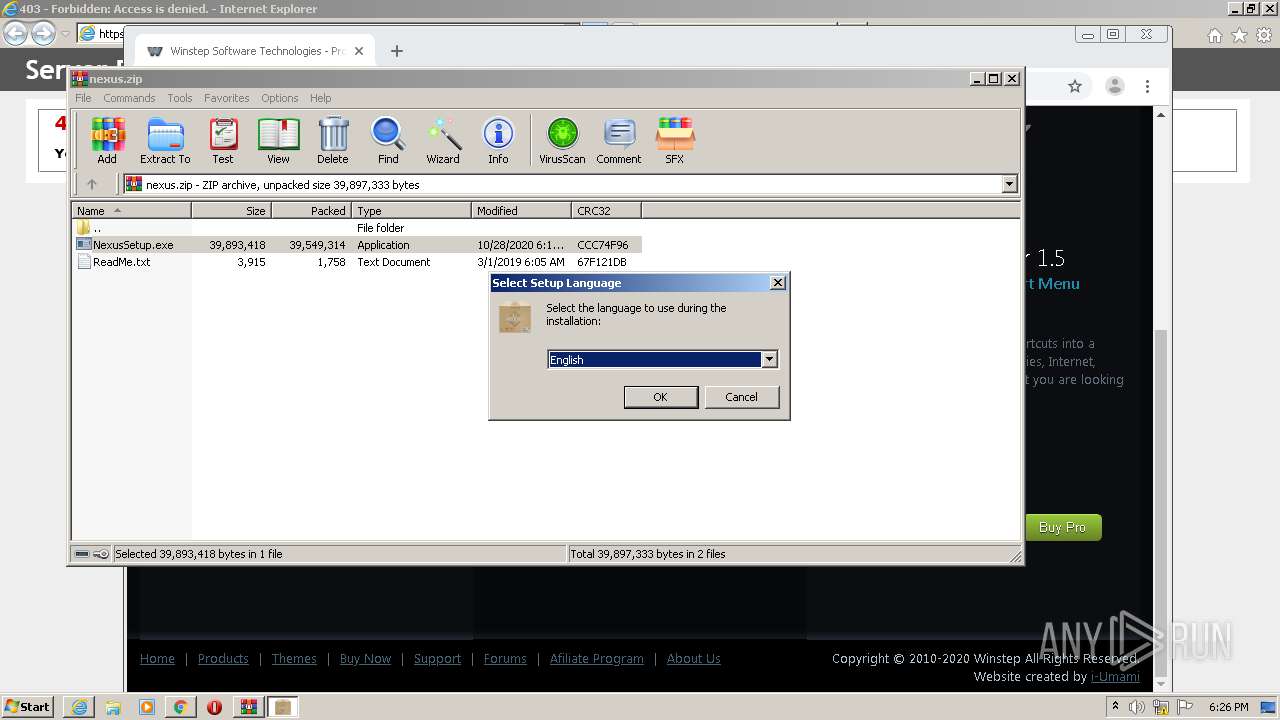
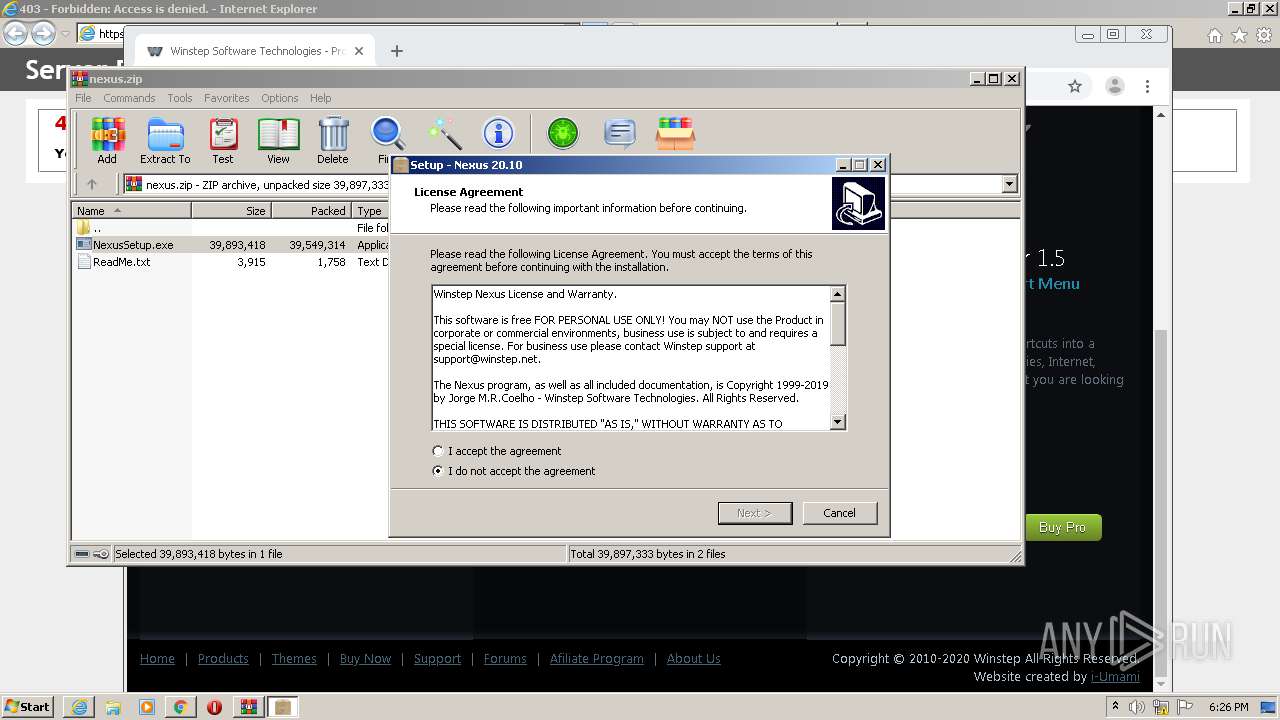
| Full analysis: | https://app.any.run/tasks/be8c7e3b-135f-40d2-8f66-3f7908ed1507 |
| Verdict: | Malicious activity |
| Analysis date: | February 08, 2021, 18:24:27 |
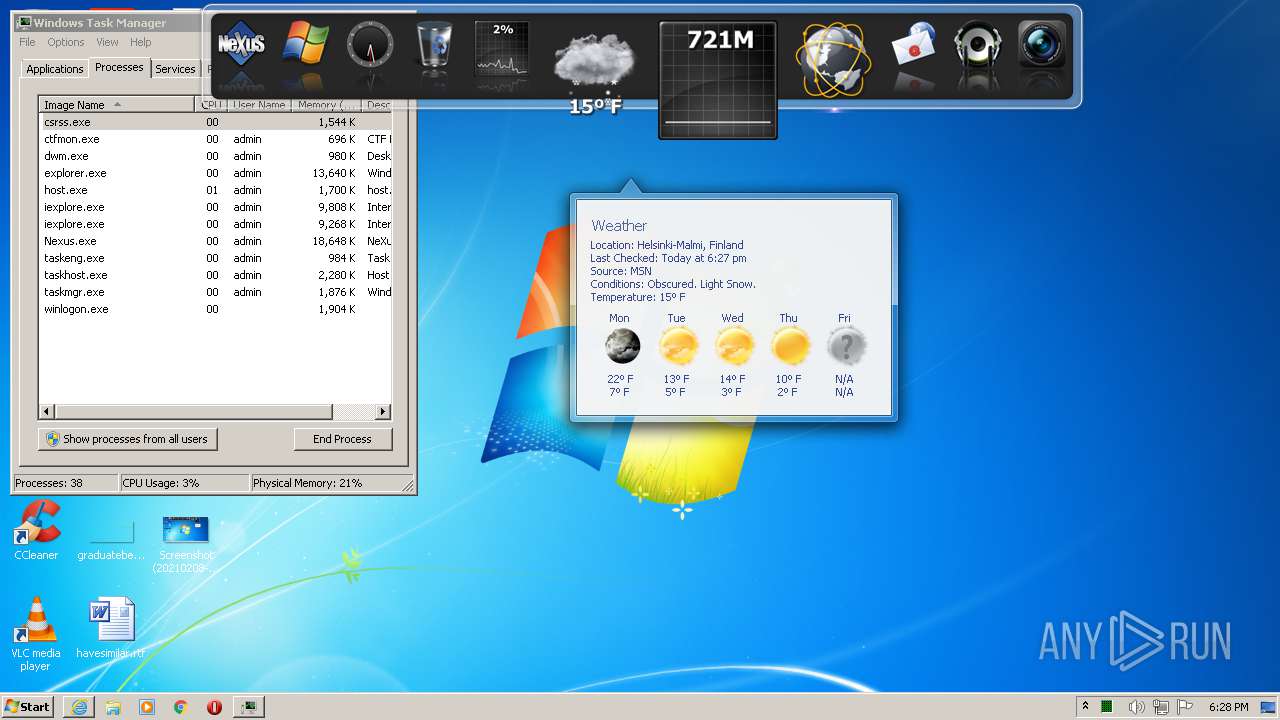
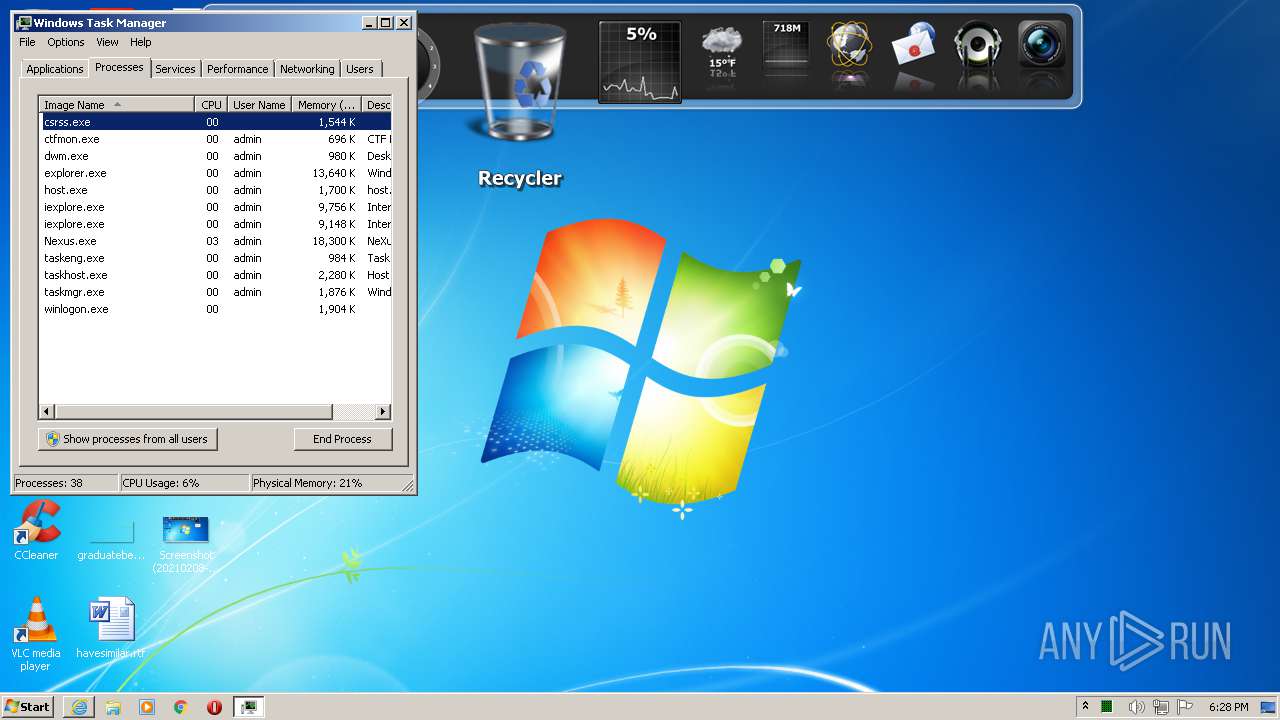
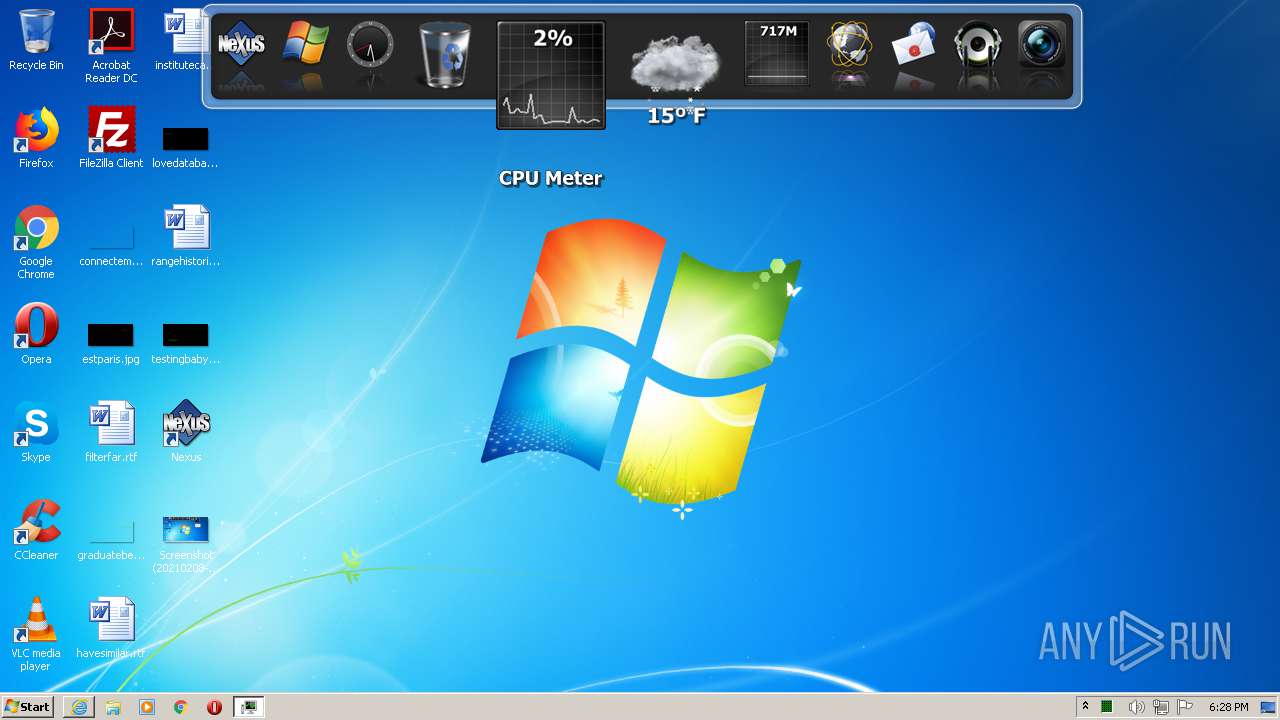
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
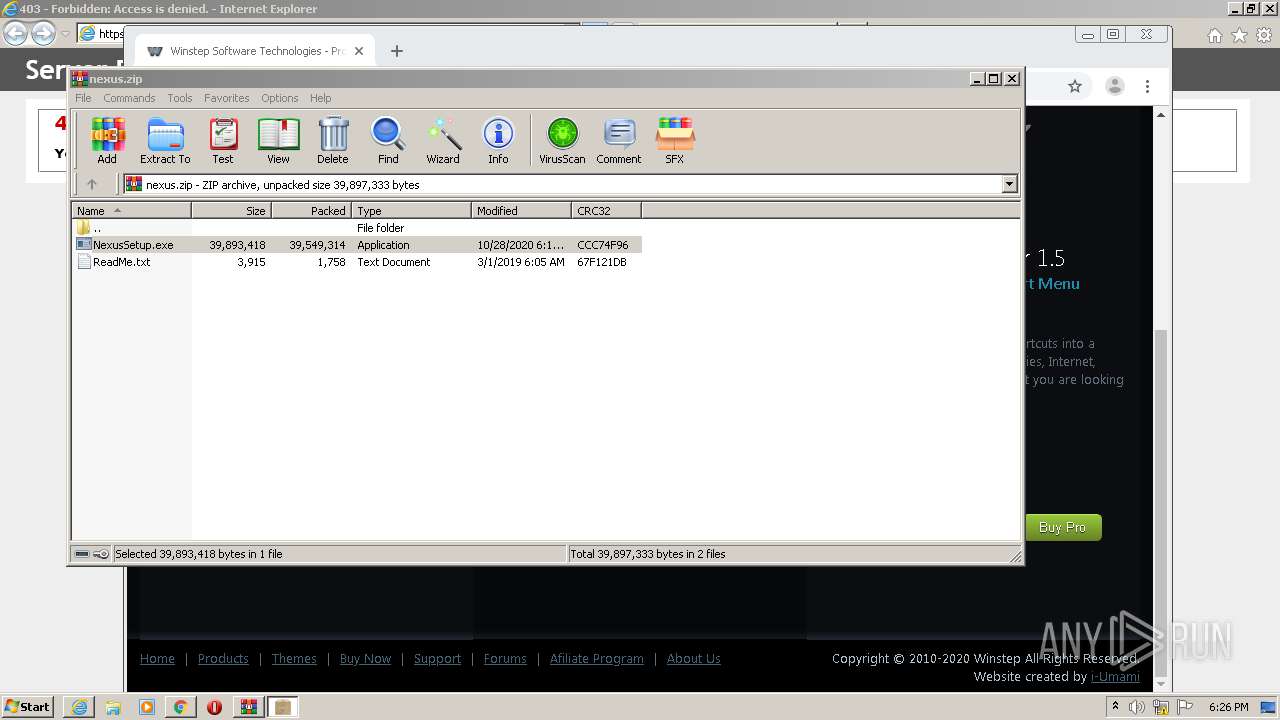
| MD5: | 97BB3F295CB658381FA256963C24AF9E |
| SHA1: | B0E1DD4250DED49AC6FE3C3BAA01CAE00790E90A |
| SHA256: | 043CCFB0D856CBB673EF0D6014C268CDBE0A303BF037228F69A59DB607D9827B |
| SSDEEP: | 3:N8DSLxLL0Q4QWLd:2OLxAQMd |
MALICIOUS
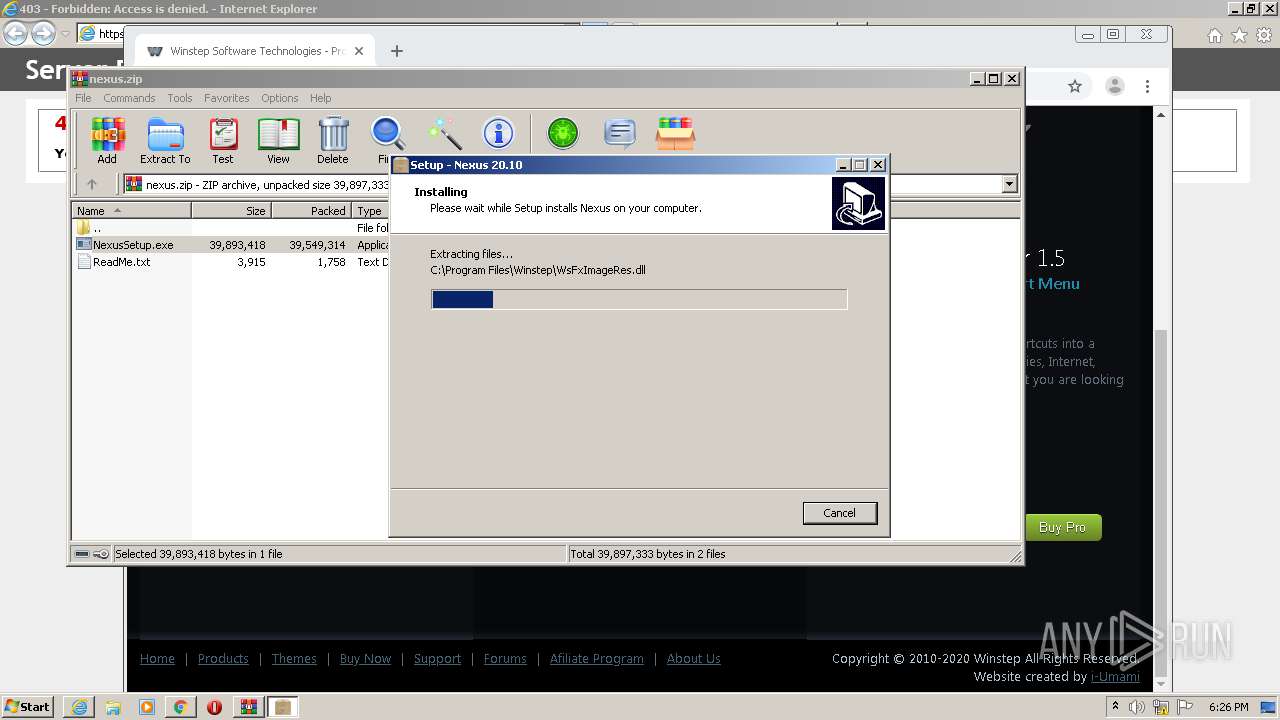
Drops executable file immediately after starts
- NexusSetup.exe (PID: 2264)
- NexusSetup.exe (PID: 2900)
Registers / Runs the DLL via REGSVR32.EXE
- NexusSetup.tmp (PID: 2484)
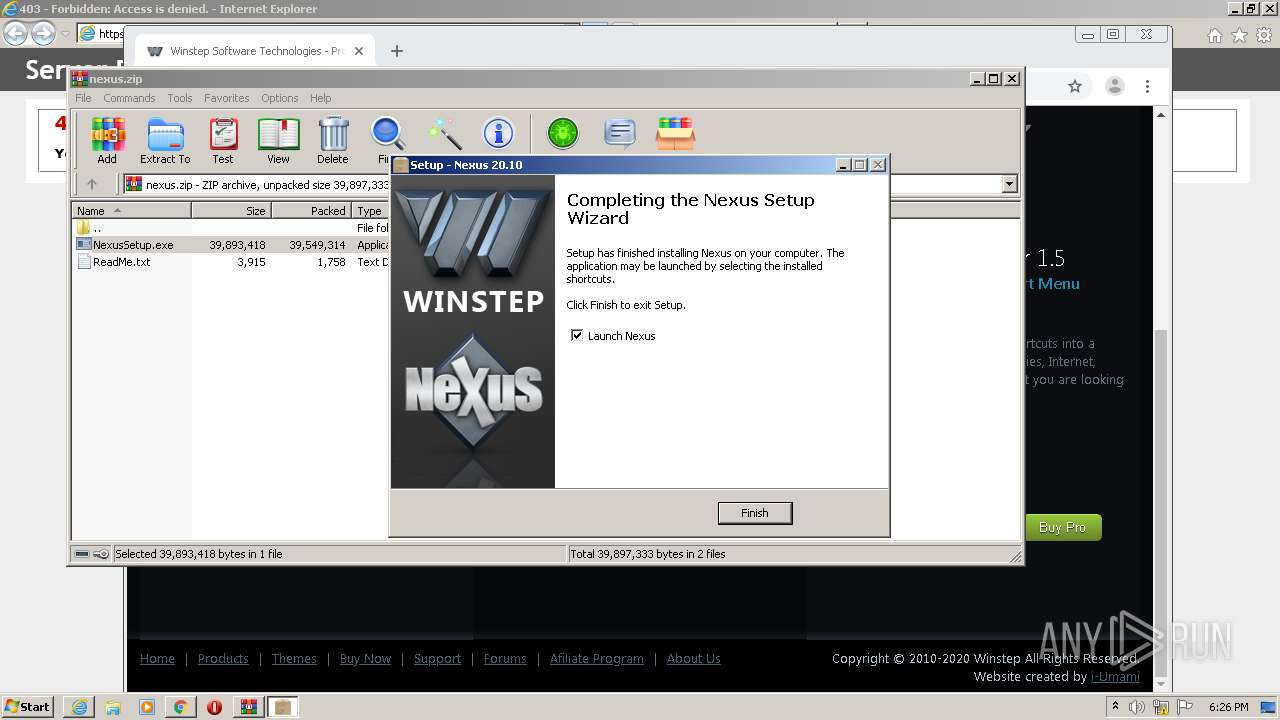
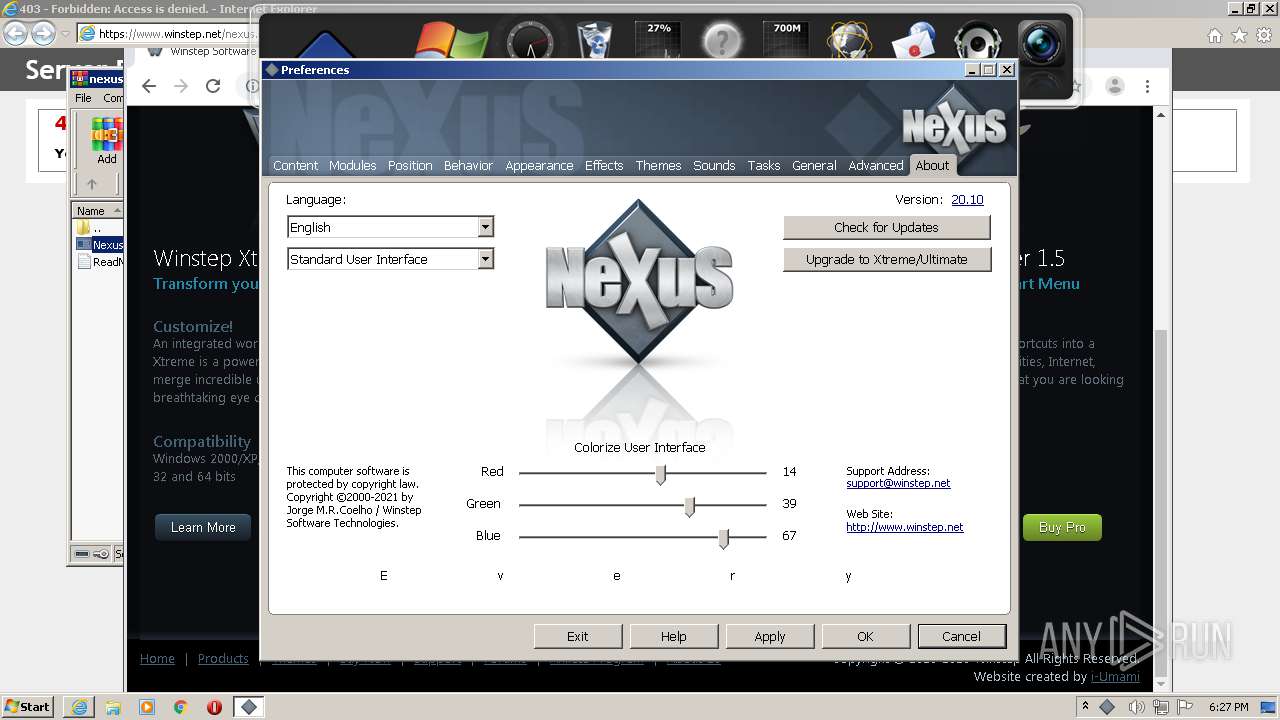
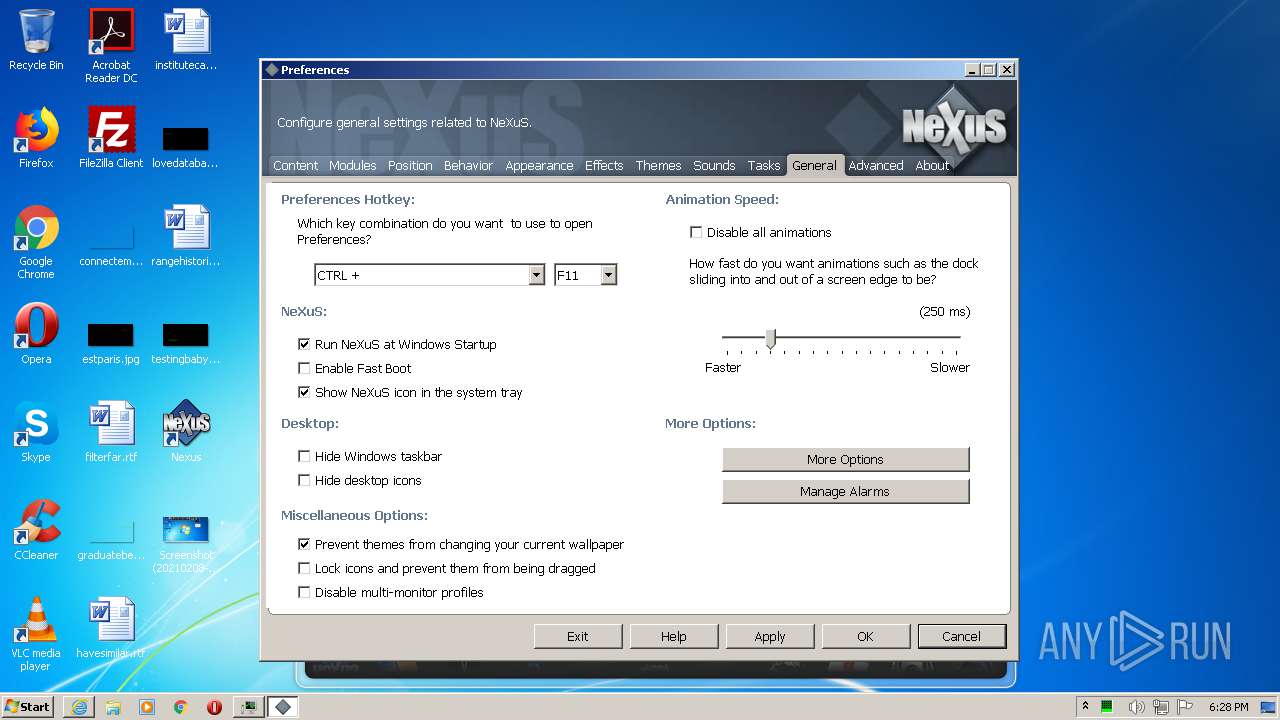
Changes the autorun value in the registry
- NexusSetup.tmp (PID: 2484)
- Nexus.exe (PID: 3984)
Loads dropped or rewritten executable
- regsvr32.exe (PID: 2544)
- regsvr32.exe (PID: 3876)
- regsvr32.exe (PID: 3992)
- regsvr32.exe (PID: 1768)
- WsxService.exe (PID: 4036)
- Nexus.exe (PID: 3984)
- WsxService.exe (PID: 792)
- winstep.exe (PID: 3428)
- wsupdate.exe (PID: 2452)
- winstep.exe (PID: 2960)
Application was dropped or rewritten from another process
- WsxService.exe (PID: 4036)
- WsxService.exe (PID: 792)
- Nexus.exe (PID: 3984)
- winstep.exe (PID: 2960)
- winstep.exe (PID: 3428)
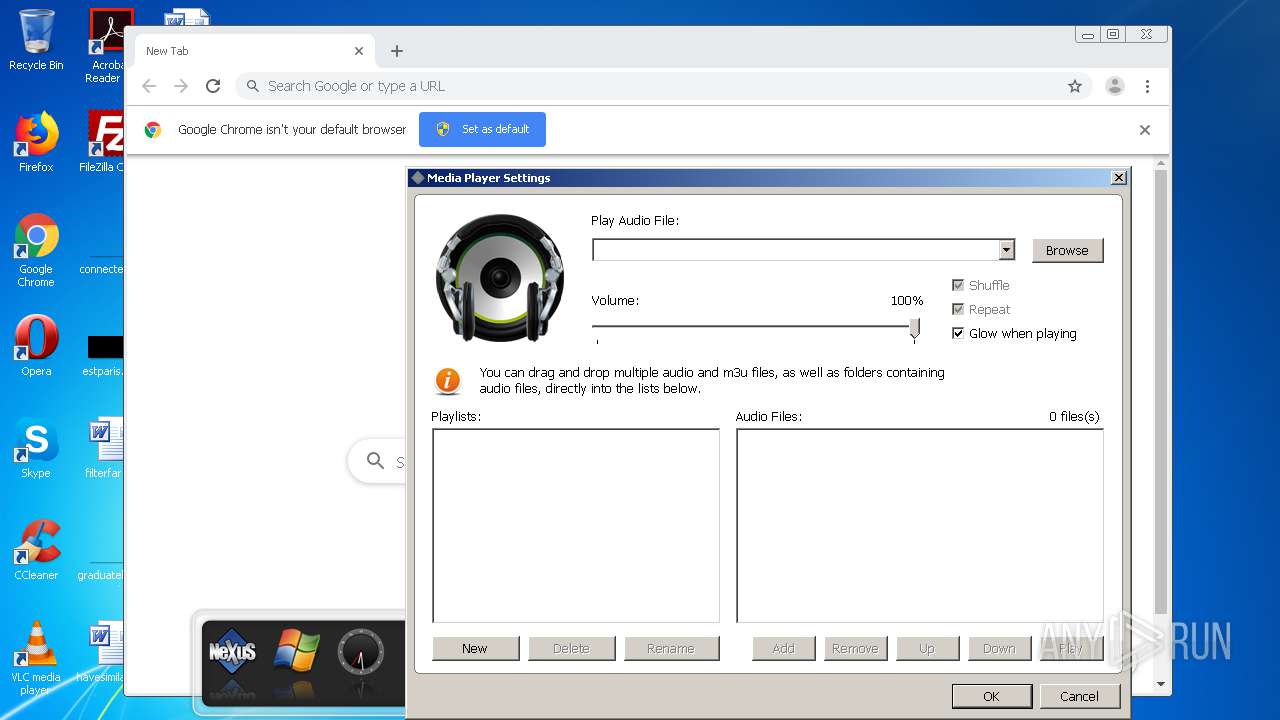
- WsMMPlay.exe (PID: 3032)
- wsupdate.exe (PID: 2452)
SUSPICIOUS
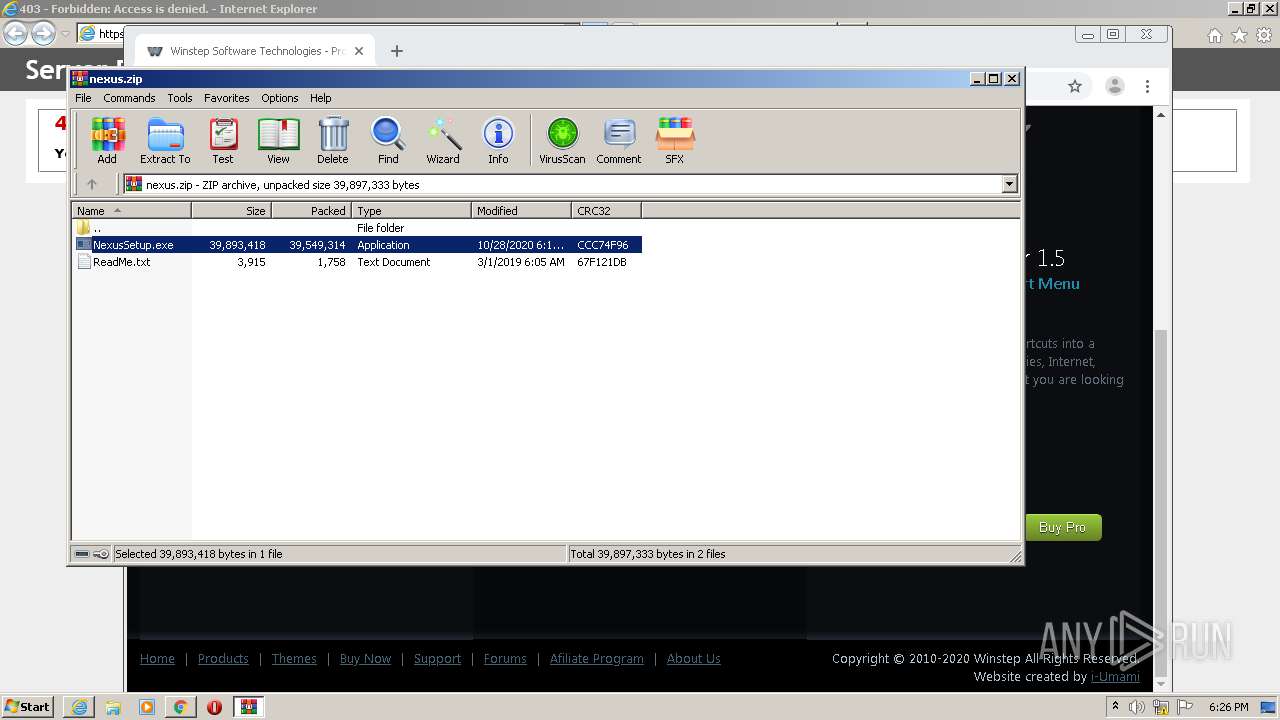
Executable content was dropped or overwritten
- NexusSetup.exe (PID: 2900)
- NexusSetup.exe (PID: 2264)
- NexusSetup.tmp (PID: 2484)
Modifies files in Chrome extension folder
- chrome.exe (PID: 3920)
Drops a file with too old compile date
- NexusSetup.exe (PID: 2264)
- NexusSetup.exe (PID: 2900)
- NexusSetup.tmp (PID: 2484)
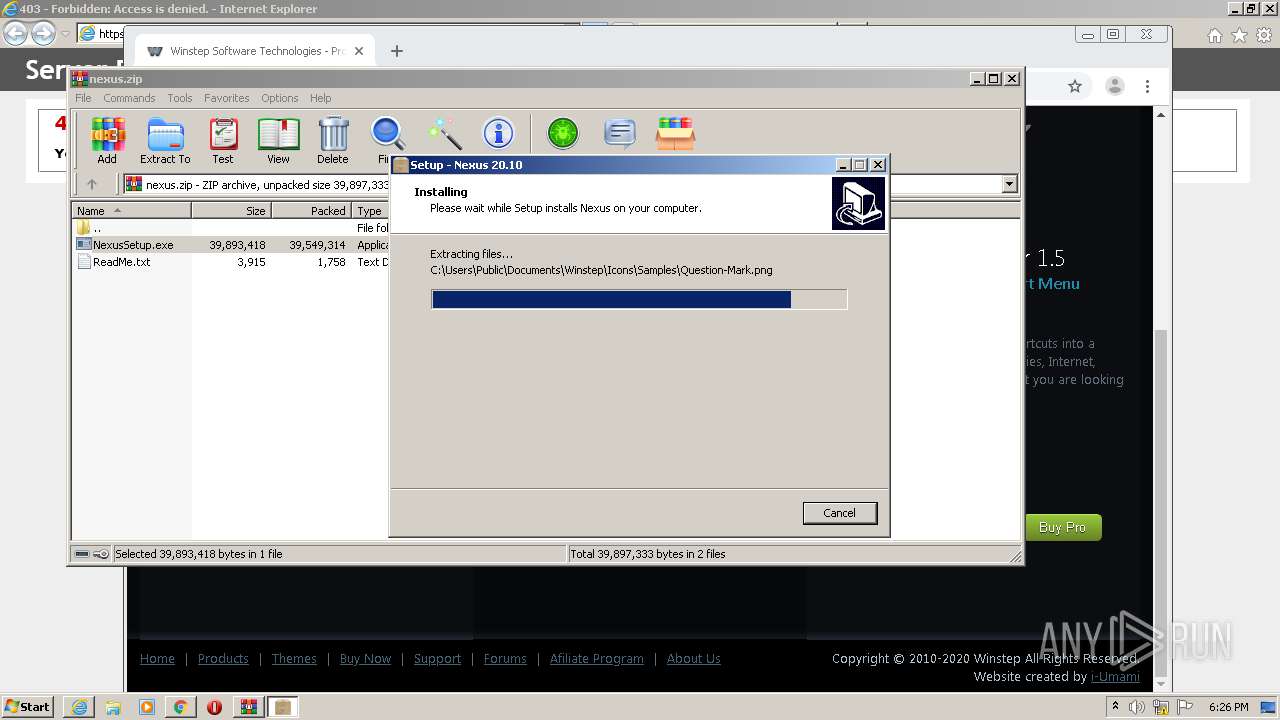
Creates files in the Windows directory
- NexusSetup.tmp (PID: 2484)
- WsxService.exe (PID: 792)
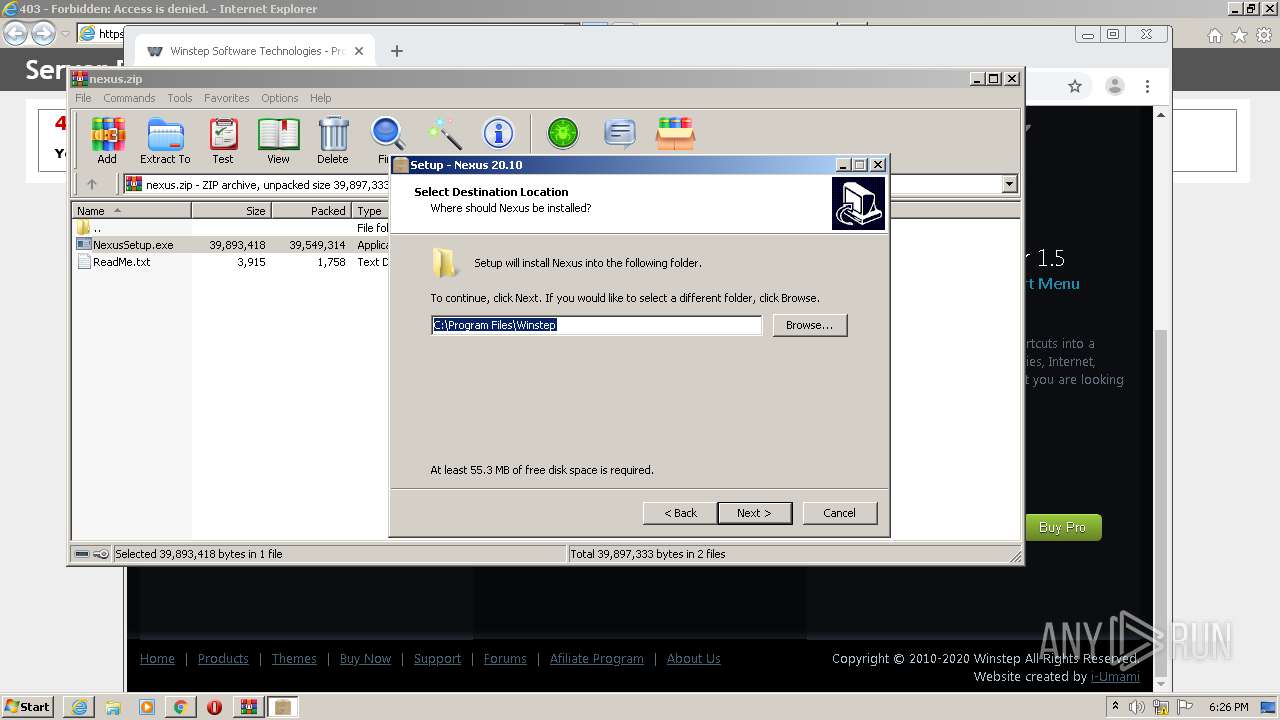
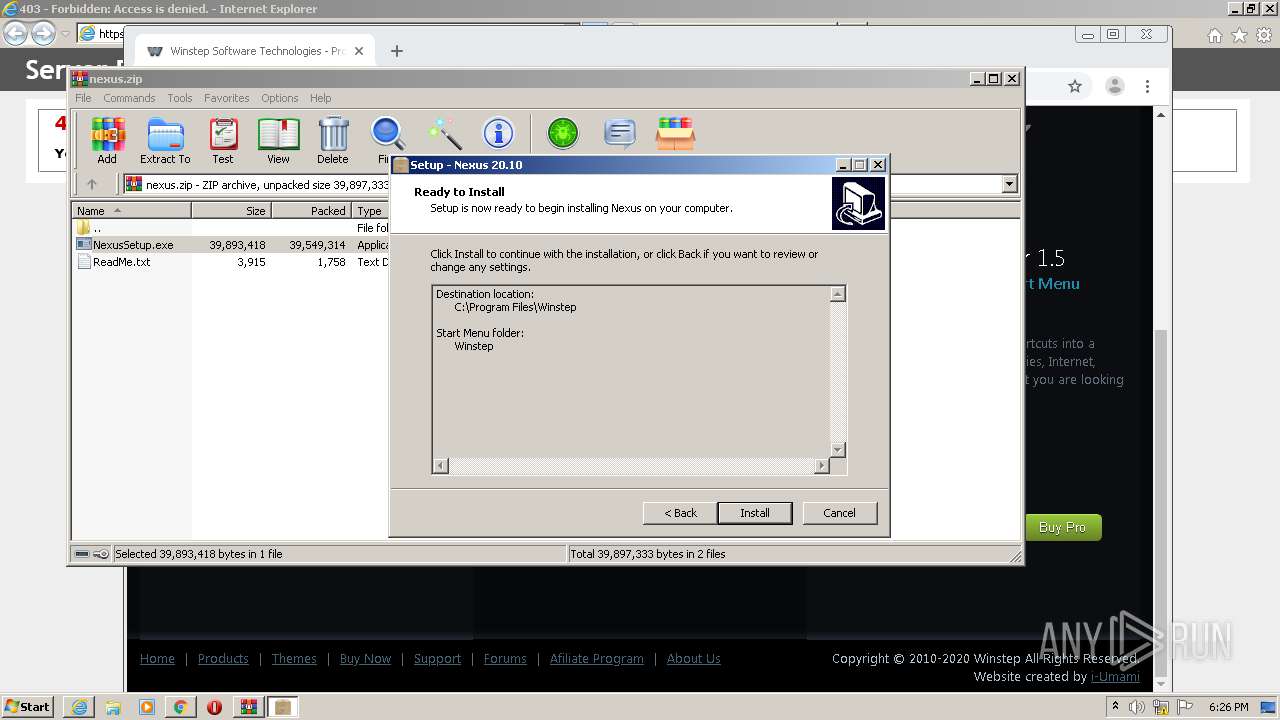
Creates a directory in Program Files
- NexusSetup.tmp (PID: 2484)
Drops a file that was compiled in debug mode
- NexusSetup.tmp (PID: 2484)
Changes default file association
- NexusSetup.tmp (PID: 2484)
Creates/Modifies COM task schedule object
- regsvr32.exe (PID: 3876)
- regsvr32.exe (PID: 2544)
Creates or modifies windows services
- WsxService.exe (PID: 4036)
Writes to a desktop.ini file (may be used to cloak folders)
- Nexus.exe (PID: 3984)
Executed as Windows Service
- WsxService.exe (PID: 792)
INFO
Reads internet explorer settings
- iexplore.exe (PID: 2212)
Reads the hosts file
- chrome.exe (PID: 3920)
- chrome.exe (PID: 768)
- chrome.exe (PID: 1524)
- chrome.exe (PID: 852)
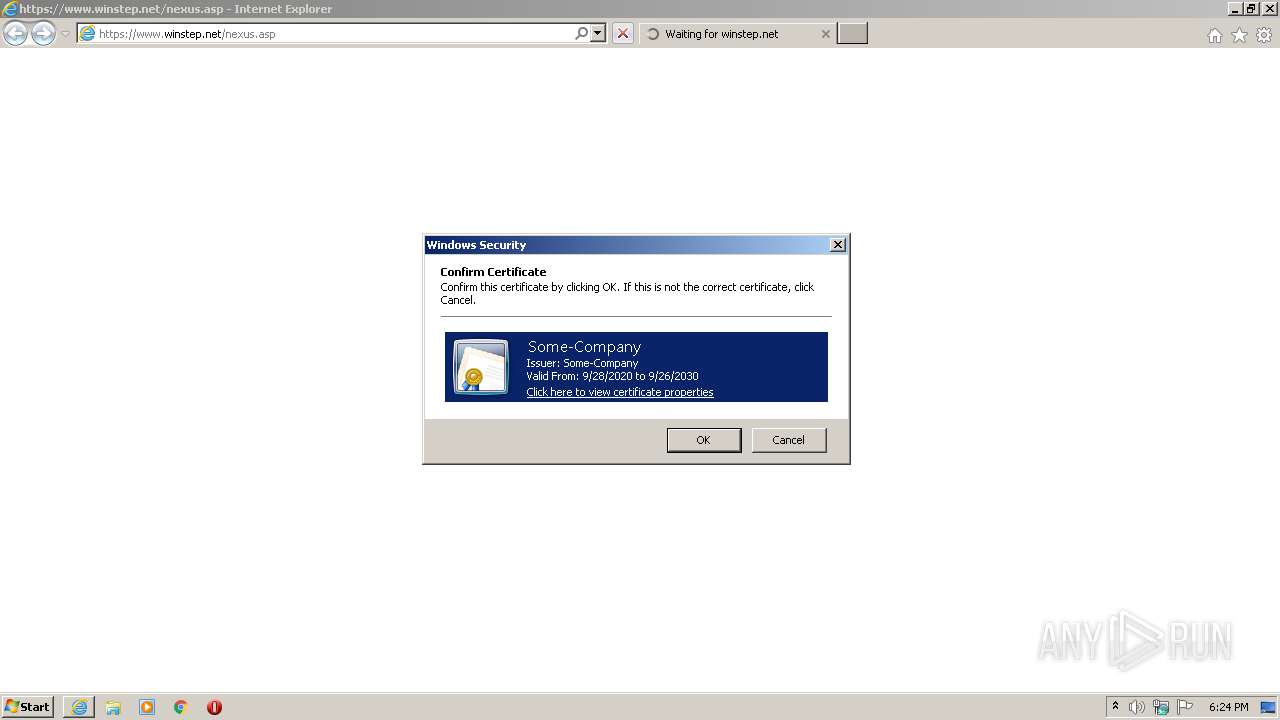
Reads settings of System Certificates
- chrome.exe (PID: 768)
- iexplore.exe (PID: 1036)
Changes settings of System certificates
- iexplore.exe (PID: 1036)
Application launched itself
- iexplore.exe (PID: 1036)
- chrome.exe (PID: 3920)
- chrome.exe (PID: 1524)
Changes internet zones settings
- iexplore.exe (PID: 1036)
Manual execution by user
- chrome.exe (PID: 3920)
- chrome.exe (PID: 1524)
Application was dropped or rewritten from another process
- NexusSetup.tmp (PID: 3072)
- NexusSetup.tmp (PID: 2484)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1036)
Creates files in the user directory
- iexplore.exe (PID: 1036)
Creates files in the program directory
- NexusSetup.tmp (PID: 2484)
Creates a software uninstall entry
- NexusSetup.tmp (PID: 2484)
Dropped object may contain Bitcoin addresses
- Nexus.exe (PID: 3984)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
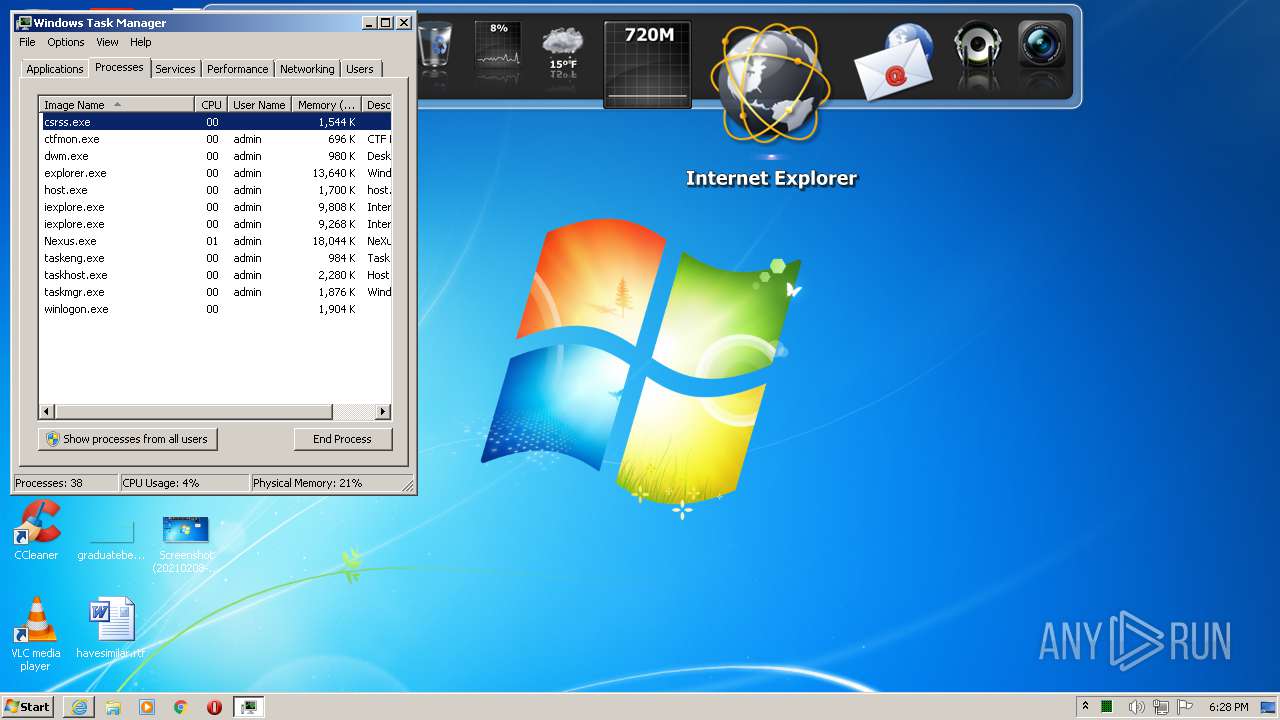
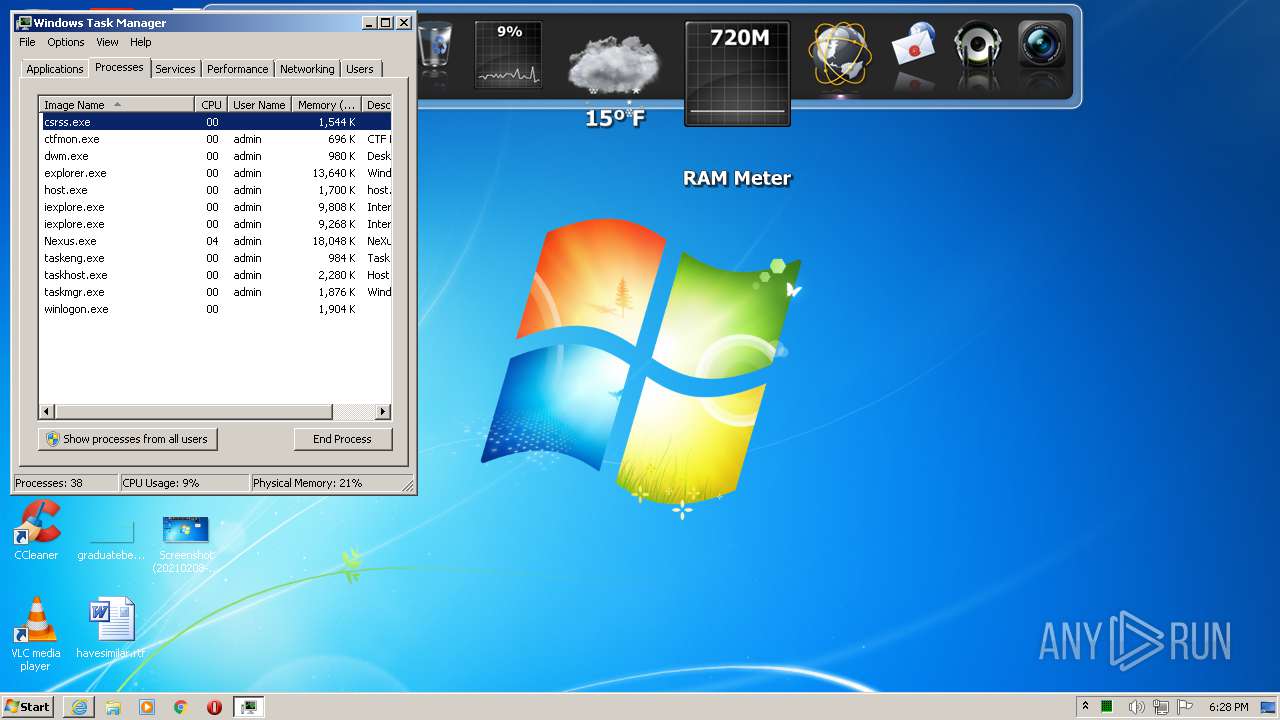
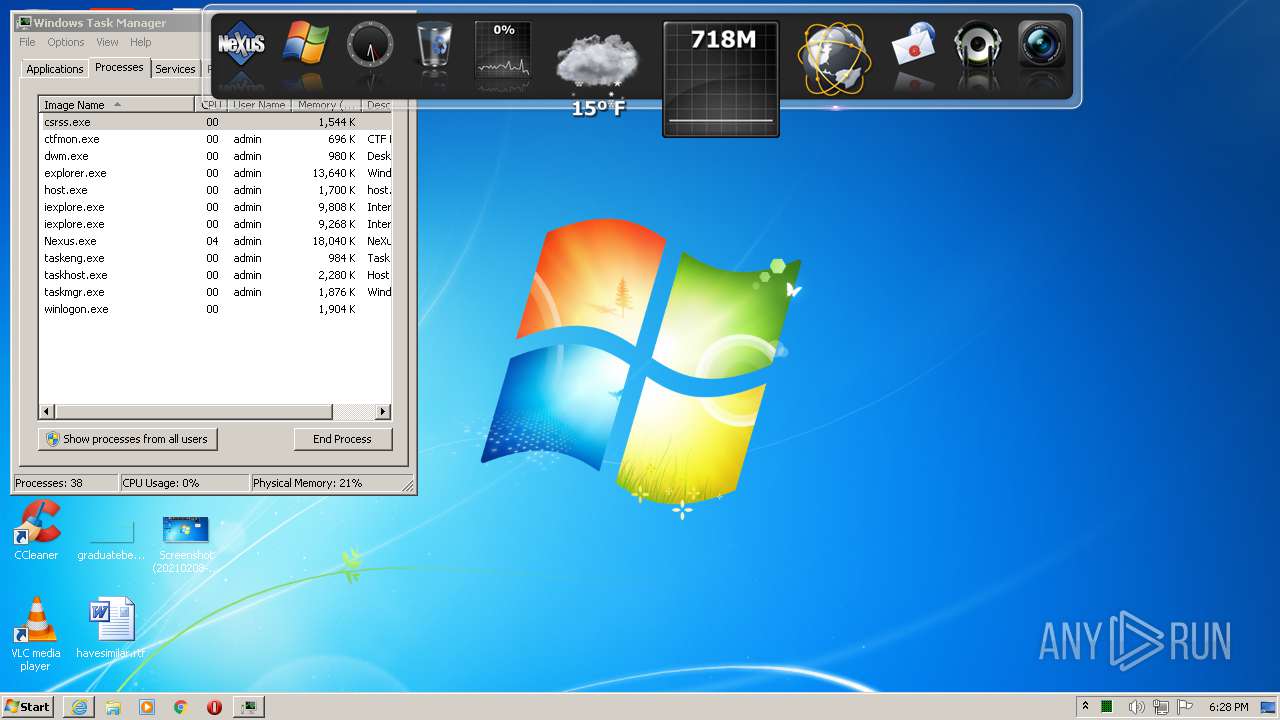
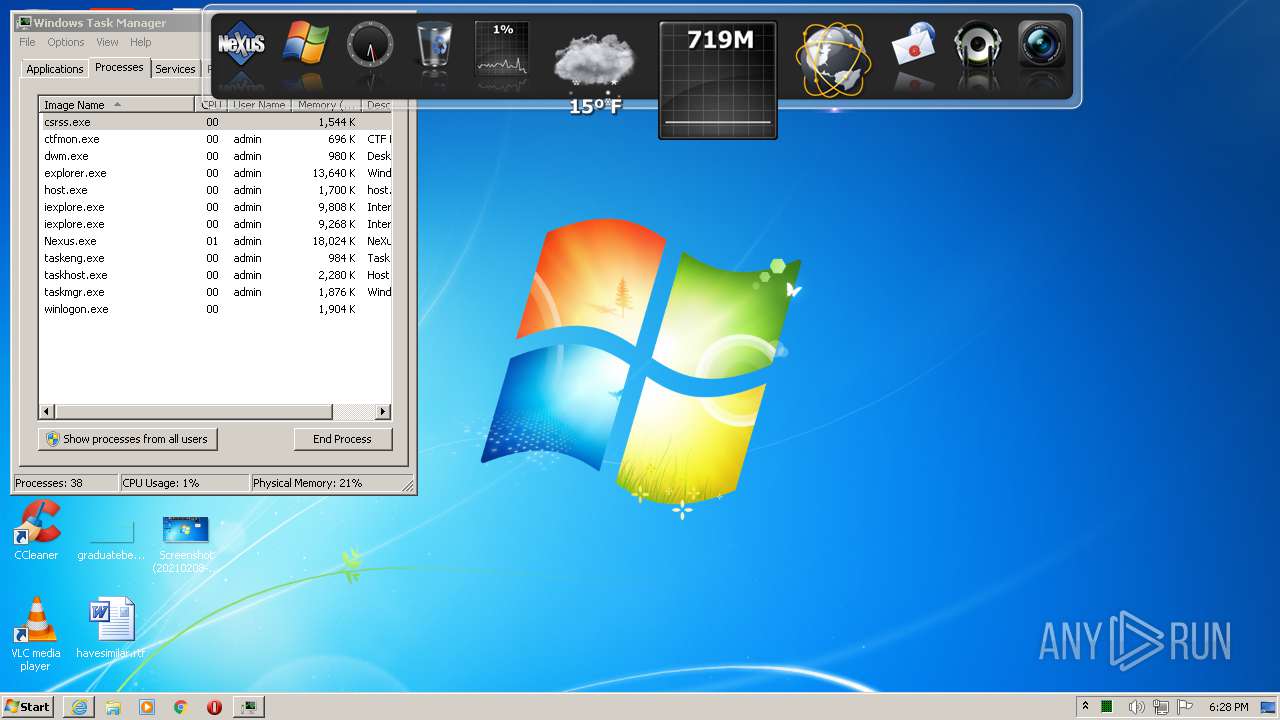
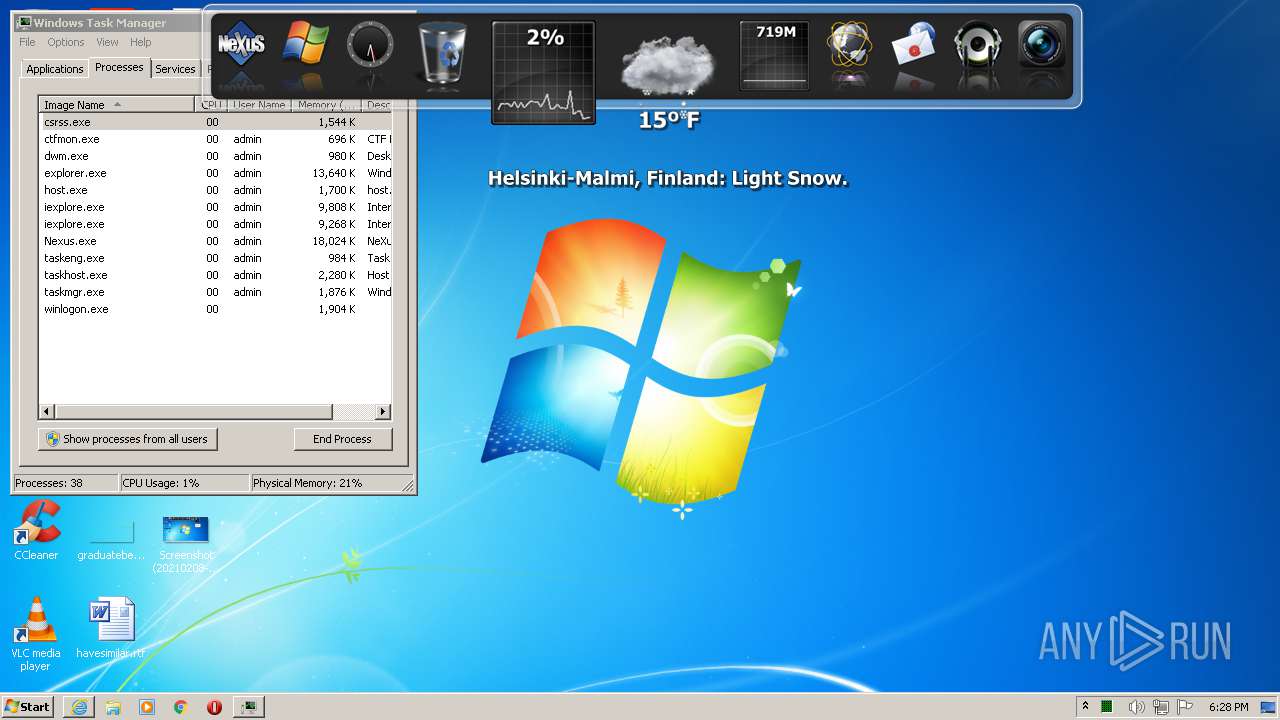
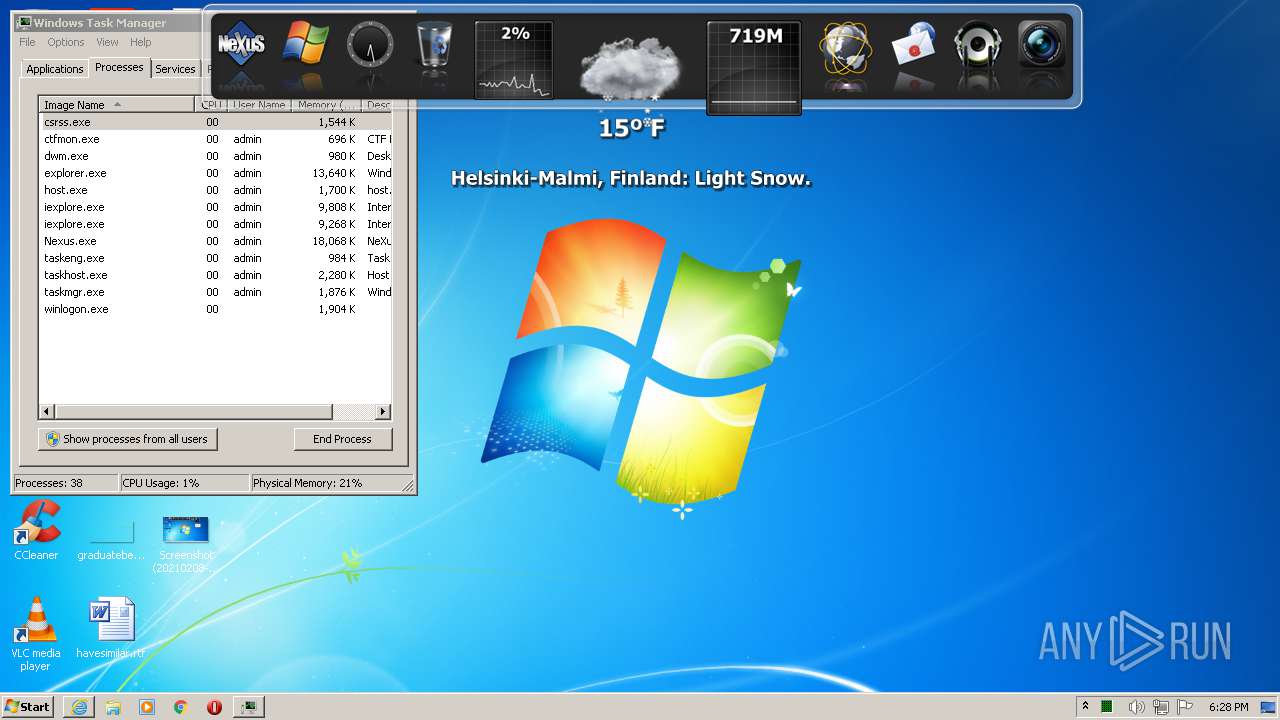
Total processes
112
Monitored processes
69
Malicious processes
10
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 120 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,5956008336181914141,13146652359866252470,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11867321600015164706 --mojo-platform-channel-handle=3504 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 768 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,5956008336181914141,13146652359866252470,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=1919198238060879231 --mojo-platform-channel-handle=1624 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 792 | "C:\Program Files\Winstep\WsxService" | C:\Program Files\Winstep\WsxService.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Winstep Software Technologies Integrity Level: SYSTEM Description: Winstep Helper Service Exit code: 0 Version: 19.10.0104 Modules
| |||||||||||||||
| 852 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,13240943056815033269,1942157958677835946,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=18373834761669760499 --mojo-platform-channel-handle=1632 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1036 | "C:\Program Files\Internet Explorer\iexplore.exe" https://www.winstep.net/nexus.asp | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1356 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,5956008336181914141,13146652359866252470,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4474042238797599062 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2500 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1408 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,13240943056815033269,1942157958677835946,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=2341696809553351306 --mojo-platform-channel-handle=3600 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
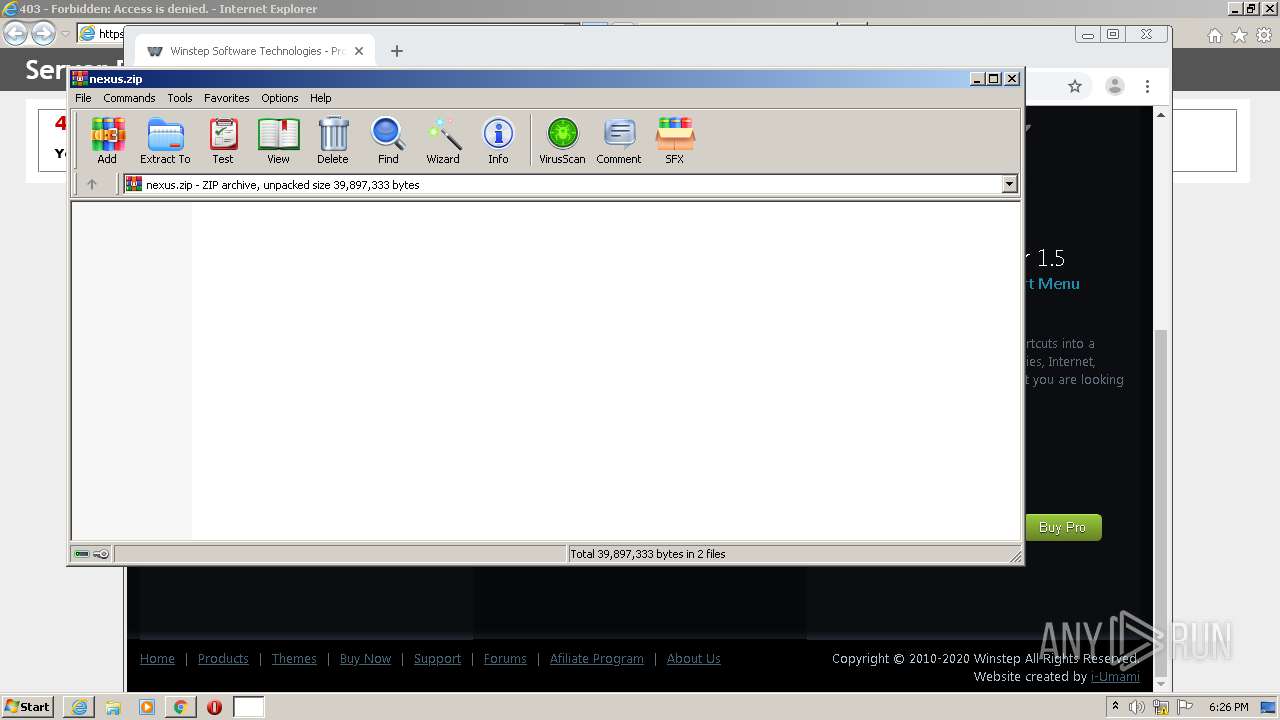
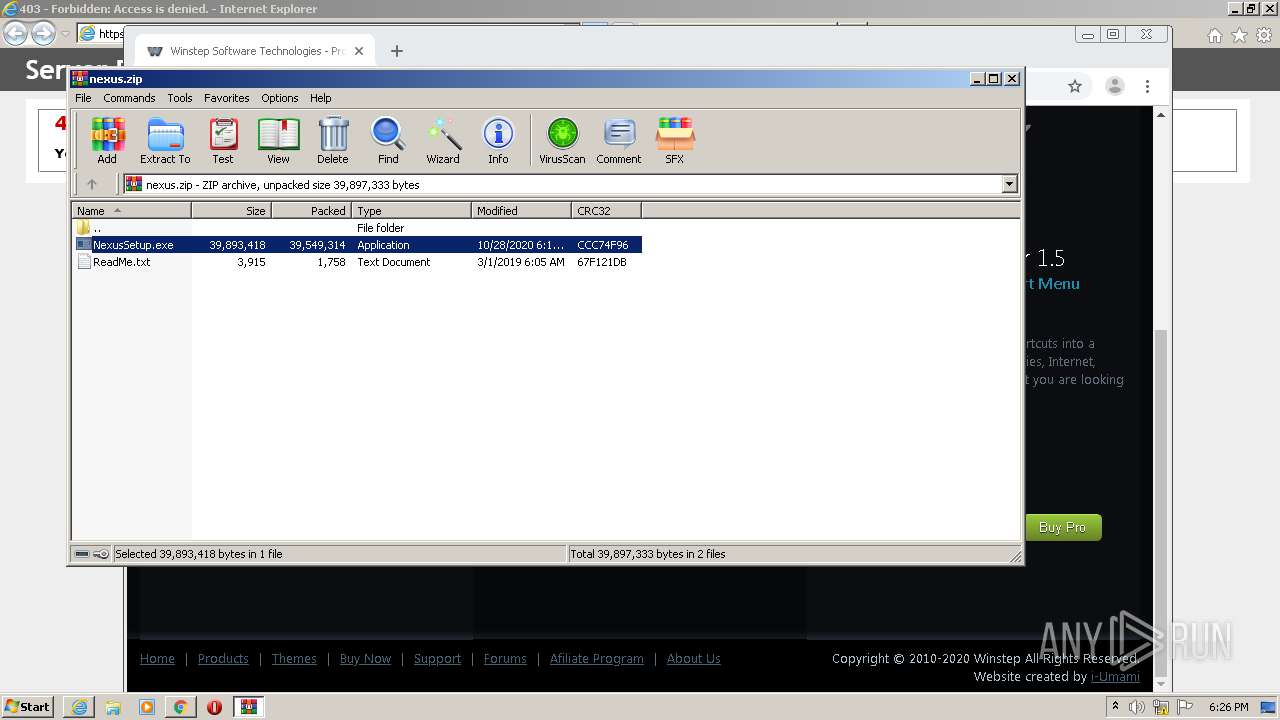
| 1500 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\nexus.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | chrome.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 1524 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1648 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,5956008336181914141,13146652359866252470,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10659269373472967284 --mojo-platform-channel-handle=3688 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
8 320
Read events
4 344
Write events
3 932
Delete events
44
Modification events
| (PID) Process: | (1036) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 3185798560 | |||
| (PID) Process: | (1036) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30867015 | |||
| (PID) Process: | (1036) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1036) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1036) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1036) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1036) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (1036) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A5000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1036) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1036) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
21
Suspicious files
84
Text files
939
Unknown types
179
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2212 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabB43D.tmp | — | |
MD5:— | SHA256:— | |||
| 2212 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarB43E.tmp | — | |
MD5:— | SHA256:— | |||
| 1036 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3920 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-602181FE-F50.pma | — | |
MD5:— | SHA256:— | |||
| 3920 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\dce88e63-3430-4c0d-a1be-c368bc2fce3e.tmp | — | |
MD5:— | SHA256:— | |||
| 3920 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2212 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\07CEF2F654E3ED6050FFC9B6EB844250_3431D4C539FB2CFCB781821E9902850D | binary | |
MD5:CA475668511E5C3B3CA630717F2A8069 | SHA256:77430BEB972FBDADD368BBAD169AD25C10121F8546C9166F6CDCA416EFD97C7C | |||
| 2212 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\07CEF2F654E3ED6050FFC9B6EB844250_3431D4C539FB2CFCB781821E9902850D | der | |
MD5:3B3A05EA154BA668BD3371073407B77A | SHA256:1147645FD20725824B517D0CD72FCBE4546E4049A43081DEE0F6E15ABCAE700E | |||
| 3920 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:C2DDBA63E4A2BD2E39A8B6C2C6384AAE | SHA256:6D5C1C78341C6F84911055D970ADDB0EC3499F8BF7FADE062122A22209CE67D9 | |||
| 3920 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFdefee.TMP | text | |
MD5:D4322EEBAC92D1B8F7A6F5E39F6264B7 | SHA256:A3EEDF21B850DCC7CE5AE04395ECDD2D29DA4EA549C8A185DD9E8B552A87B8C2 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
59
TCP/UDP connections
71
DNS requests
61
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2212 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | US | der | 727 b | whitelisted |
768 | chrome.exe | GET | 200 | 142.250.34.2:80 | http://edgedl.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzI0QUFXNV9zT2RvdUwyMERESEZGVmJnQQ/1.0.0.6_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | crx | 242 Kb | whitelisted |
768 | chrome.exe | GET | 200 | 162.216.6.139:80 | http://winstep.net/main.css | US | text | 4.68 Kb | whitelisted |
768 | chrome.exe | GET | 200 | 162.216.6.139:80 | http://winstep.net/videobox.css | US | text | 1.21 Kb | whitelisted |
768 | chrome.exe | GET | 200 | 162.216.6.139:80 | http://winstep.net/ | US | html | 10.8 Kb | whitelisted |
768 | chrome.exe | GET | 200 | 162.216.6.139:80 | http://winstep.net/js/swfobject.js | US | text | 2.41 Kb | whitelisted |
768 | chrome.exe | GET | 200 | 162.216.6.139:80 | http://winstep.net/js/jquery-1.3.2.min.js | US | text | 55.9 Kb | whitelisted |
768 | chrome.exe | GET | 200 | 162.216.6.139:80 | http://winstep.net/js/jquery-galleryview-1.1/jquery.galleryview-1.1.js | US | text | 18.3 Kb | whitelisted |
768 | chrome.exe | GET | 200 | 162.216.6.139:80 | http://winstep.net/images/headlight_screenshot0.jpg | US | image | 166 Kb | whitelisted |
768 | chrome.exe | GET | 200 | 162.216.6.139:80 | http://winstep.net/js/jquery-galleryview-1.1/jquery.timers-1.1.2.js | US | text | 3.45 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
768 | chrome.exe | 142.250.34.2:80 | edgedl.gvt1.com | Google Inc. | US | whitelisted |
2212 | iexplore.exe | 162.216.6.139:443 | www.winstep.net | HIVELOCITY VENTURES CORP | US | unknown |
2212 | iexplore.exe | 151.139.128.14:80 | ocsp.usertrust.com | Highwinds Network Group, Inc. | US | suspicious |
1036 | iexplore.exe | 13.107.21.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
768 | chrome.exe | 142.250.73.227:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
768 | chrome.exe | 172.217.18.99:443 | www.google.com.ua | Google Inc. | US | whitelisted |
768 | chrome.exe | 142.250.73.202:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
768 | chrome.exe | 142.250.185.131:443 | www.gstatic.com | Google Inc. | US | whitelisted |
768 | chrome.exe | 172.217.8.13:443 | accounts.google.com | Google Inc. | US | unknown |
768 | chrome.exe | 142.250.186.46:443 | apis.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.winstep.net |
| unknown |
ocsp.usertrust.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |