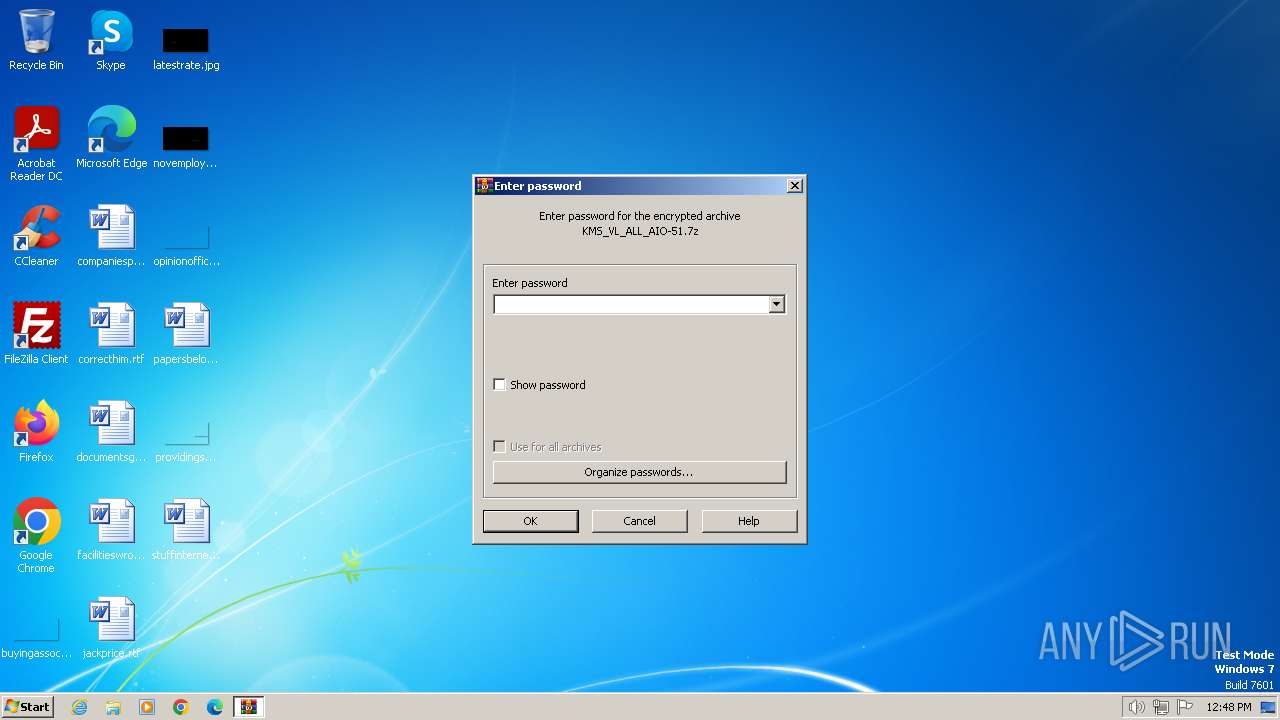
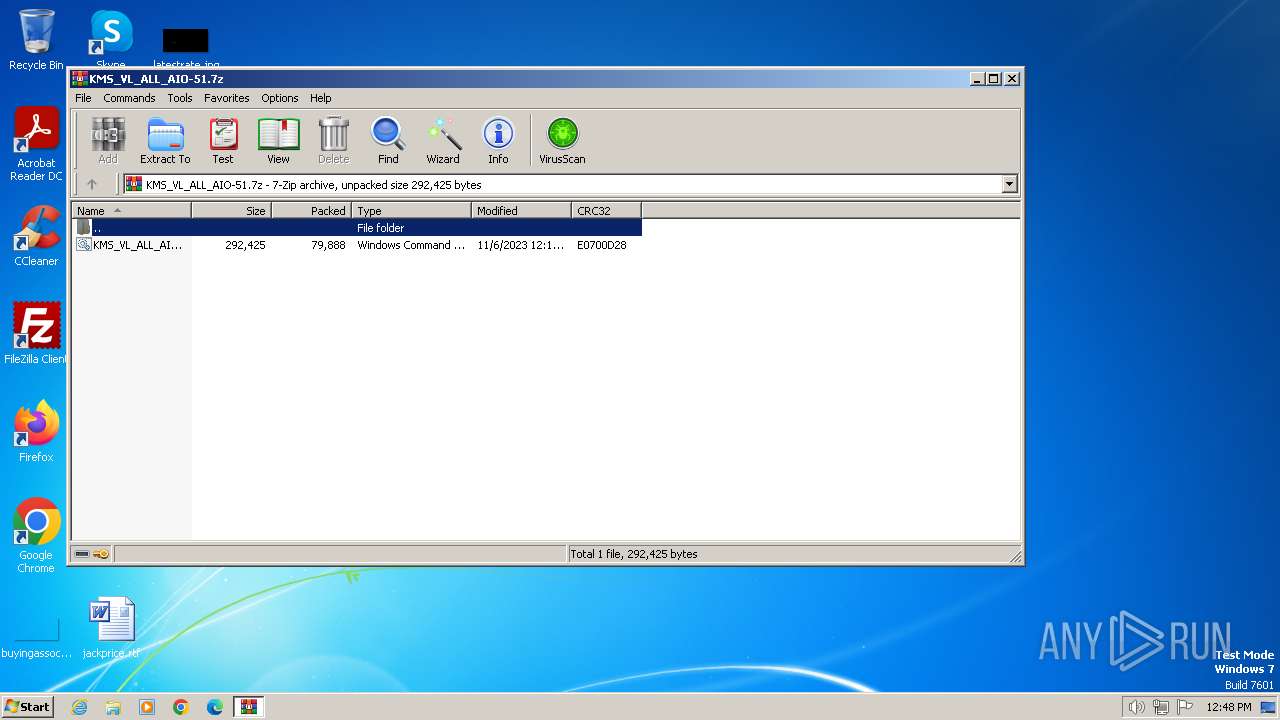
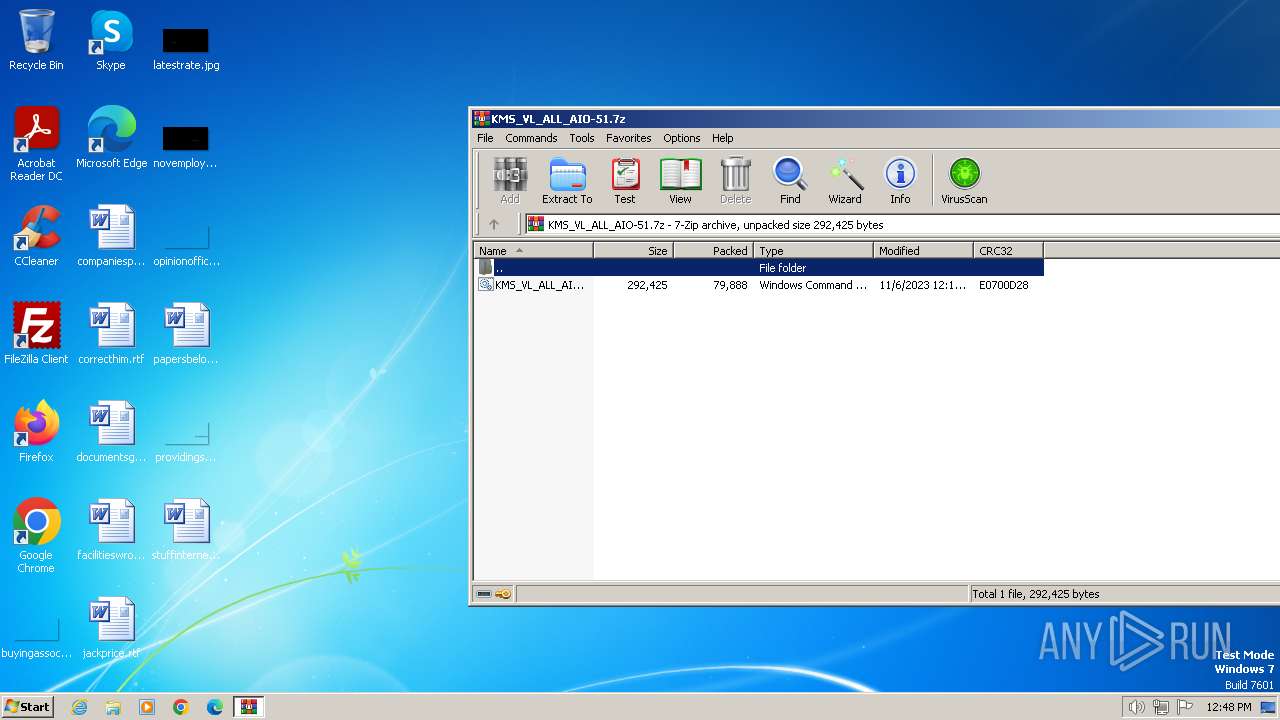
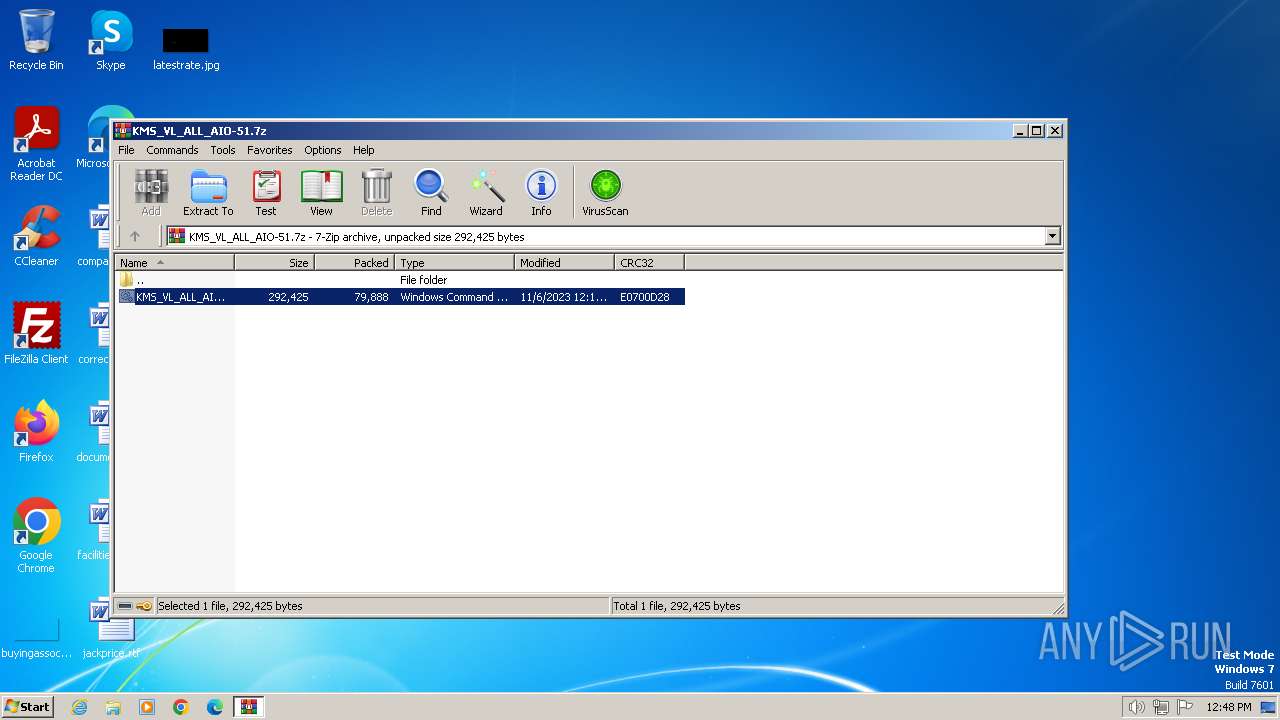
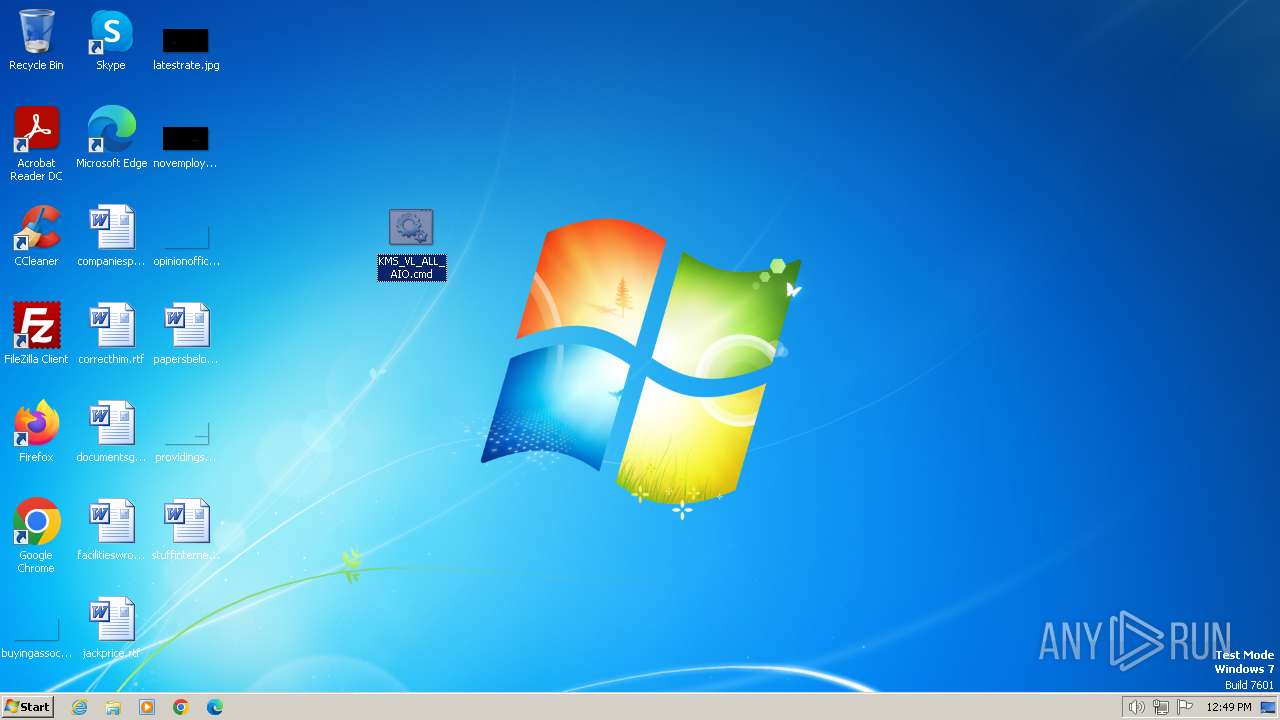
| File name: | KMS_VL_ALL_AIO-51.7z |
| Full analysis: | https://app.any.run/tasks/febf9342-bb52-42ab-8861-3708c08edd42 |
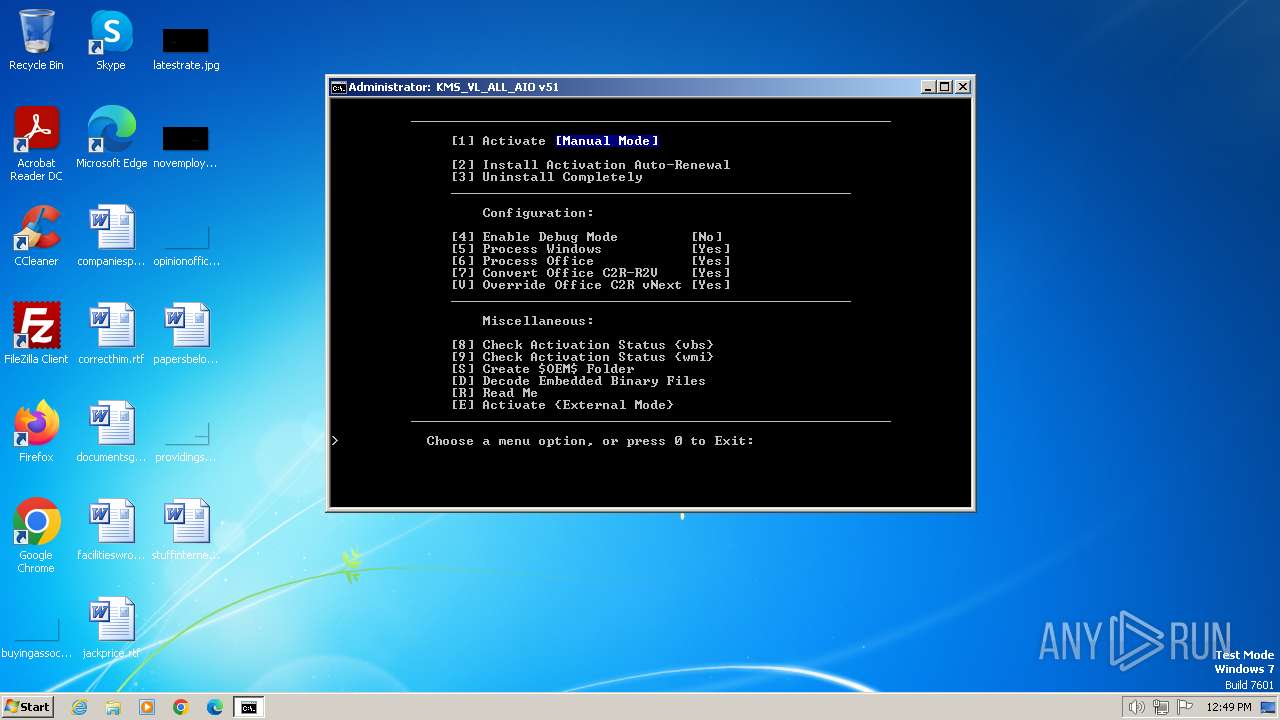
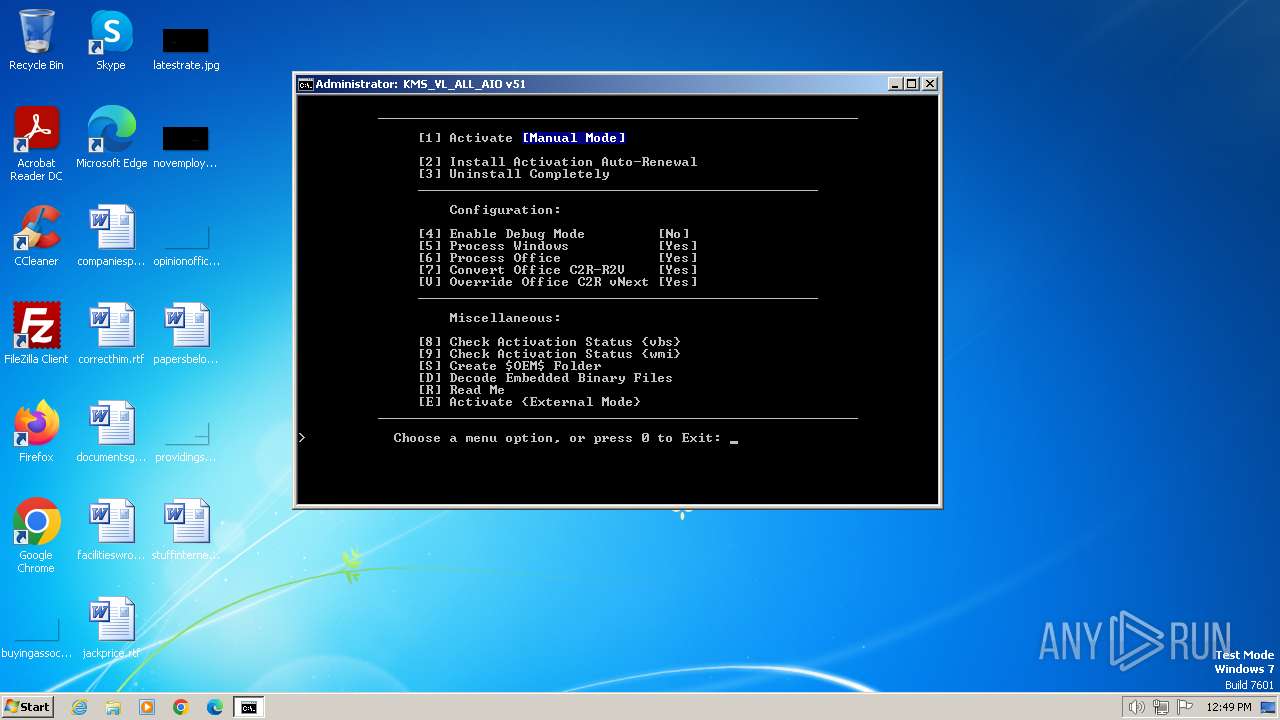
| Verdict: | Malicious activity |
| Analysis date: | March 15, 2024, 12:48:21 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-7z-compressed |
| File info: | 7-zip archive data, version 0.4 |
| MD5: | E47E9CDBAD339AFDF97B99D9CF9E8E3C |
| SHA1: | 823462EC4B71E1BA55C80C4A993618AF9EA55797 |
| SHA256: | 04356AD86C9D67AACB7ABA15991C074F9EE943EBBB53188A5B8A0F5BD6A8DDF9 |
| SSDEEP: | 1536:8sfQqrext+fR62gy54TFJ4rVOeR6E2S6AZNUYpYBSuvQftfJqFbJKt157UDC4:8pqaxtqR7FRGmd7tBSbJKt1lYd |
MALICIOUS
Starts Visual C# compiler
- powershell.exe (PID: 3588)
Drops the executable file immediately after the start
- powershell.exe (PID: 3588)
- csc.exe (PID: 4016)
Creates a writable file in the system directory
- powershell.exe (PID: 3588)
Starts NET.EXE for service management
- cmd.exe (PID: 2576)
- net.exe (PID: 920)
- net.exe (PID: 3244)
- net.exe (PID: 3052)
SUSPICIOUS
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 2420)
- cmd.exe (PID: 2576)
Reads the Internet Settings
- cscript.exe (PID: 1768)
- WMIC.exe (PID: 1824)
- WMIC.exe (PID: 712)
- WMIC.exe (PID: 2184)
- WMIC.exe (PID: 2908)
- WMIC.exe (PID: 3088)
- WMIC.exe (PID: 1784)
- WMIC.exe (PID: 3496)
- WMIC.exe (PID: 3260)
- WMIC.exe (PID: 1956)
- WMIC.exe (PID: 696)
- WMIC.exe (PID: 2728)
- WMIC.exe (PID: 2744)
- WMIC.exe (PID: 3468)
Uses WMIC.EXE to obtain computer system information
- cmd.exe (PID: 2420)
- cmd.exe (PID: 2576)
Runs shell command (SCRIPT)
- cscript.exe (PID: 1768)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 2420)
- cmd.exe (PID: 2576)
Uses RUNDLL32.EXE to load library
- cscript.exe (PID: 1768)
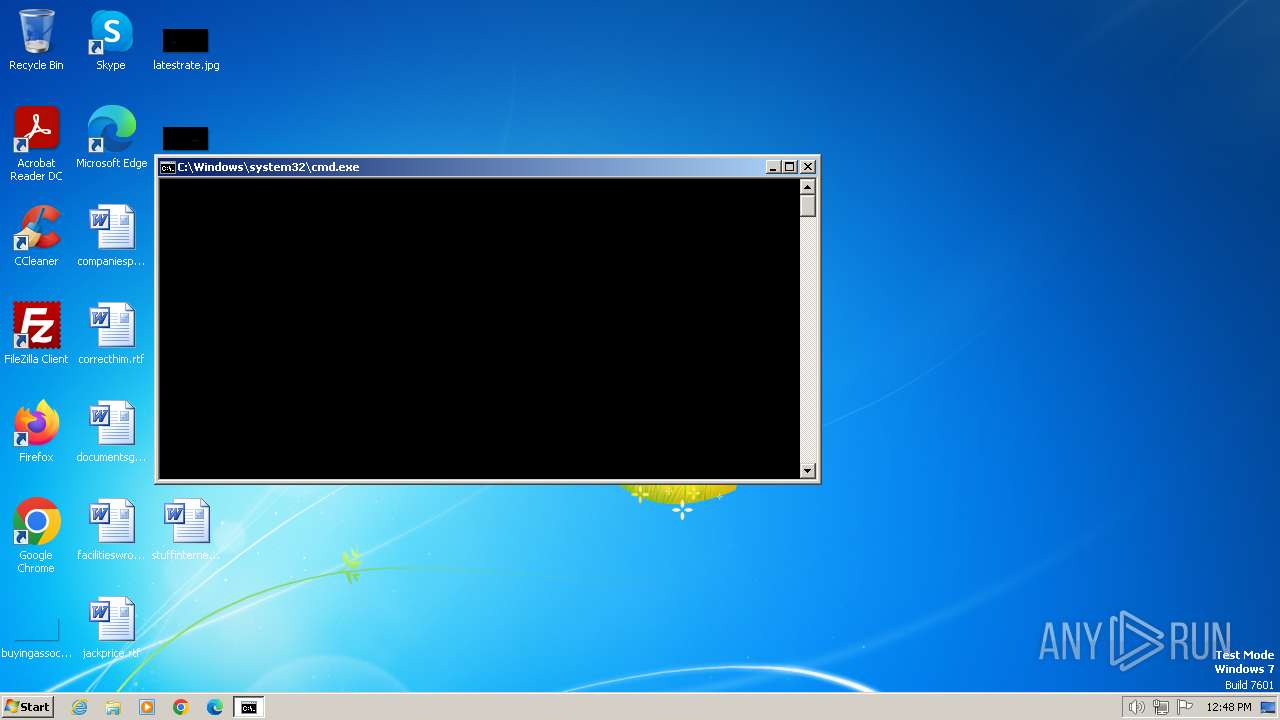
Starts CMD.EXE for commands execution
- cscript.exe (PID: 1768)
- cmd.exe (PID: 2576)
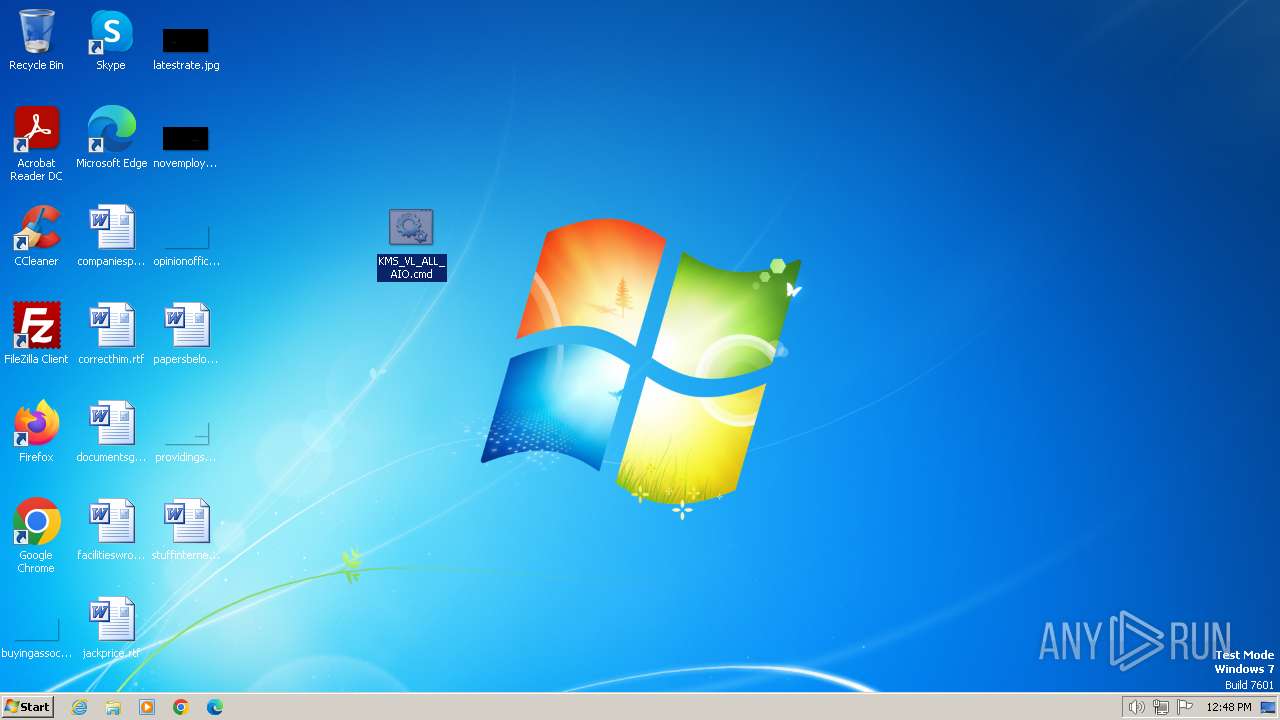
Executing commands from ".cmd" file
- cscript.exe (PID: 1768)
Starts SC.EXE for service management
- cmd.exe (PID: 2576)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 2576)
Possibly malicious use of IEX has been detected
- cmd.exe (PID: 2576)
Probably obfuscated PowerShell command line is found
- cmd.exe (PID: 2576)
Executable content was dropped or overwritten
- csc.exe (PID: 4016)
- powershell.exe (PID: 3588)
Uses .NET C# to load dll
- powershell.exe (PID: 3588)
Hides command output
- cmd.exe (PID: 2340)
- cmd.exe (PID: 2360)
- cmd.exe (PID: 2864)
- cmd.exe (PID: 2572)
- cmd.exe (PID: 2296)
- cmd.exe (PID: 2292)
- cmd.exe (PID: 3180)
- cmd.exe (PID: 3620)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 2576)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 2576)
- cmd.exe (PID: 568)
- cmd.exe (PID: 3444)
Uses WMIC.EXE to obtain service application data
- cmd.exe (PID: 2156)
Application launched itself
- cmd.exe (PID: 2576)
INFO
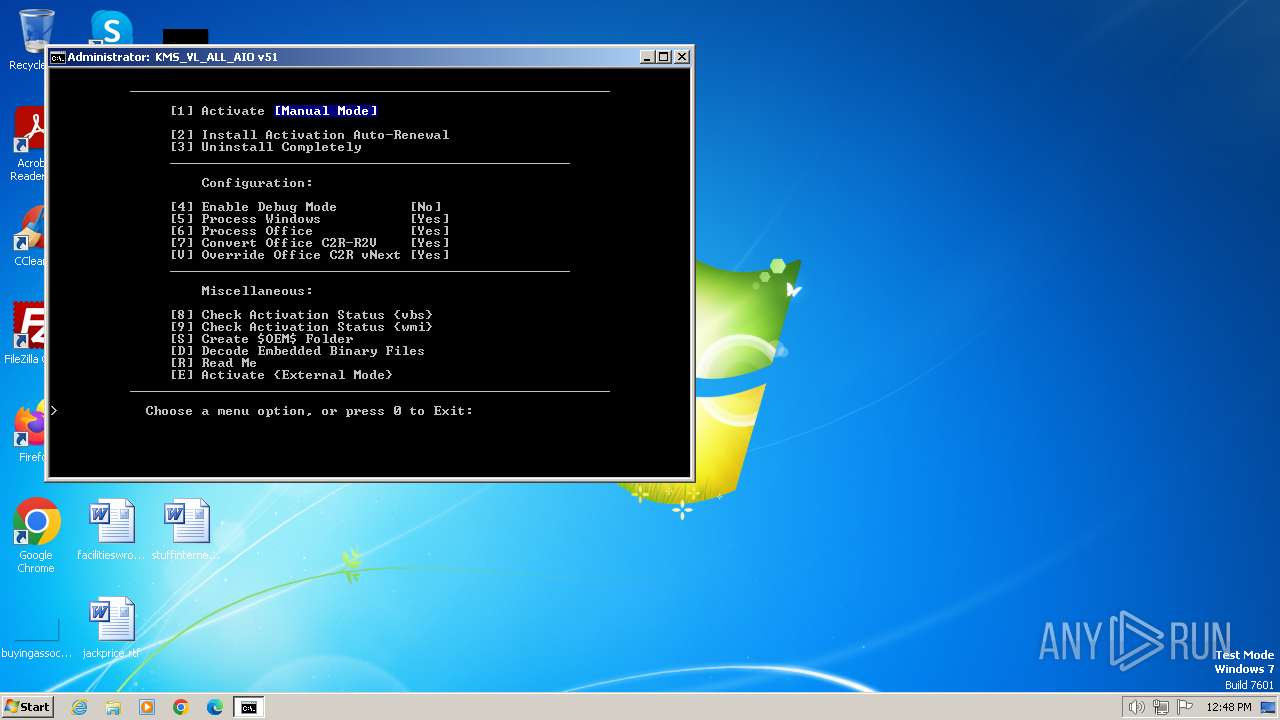
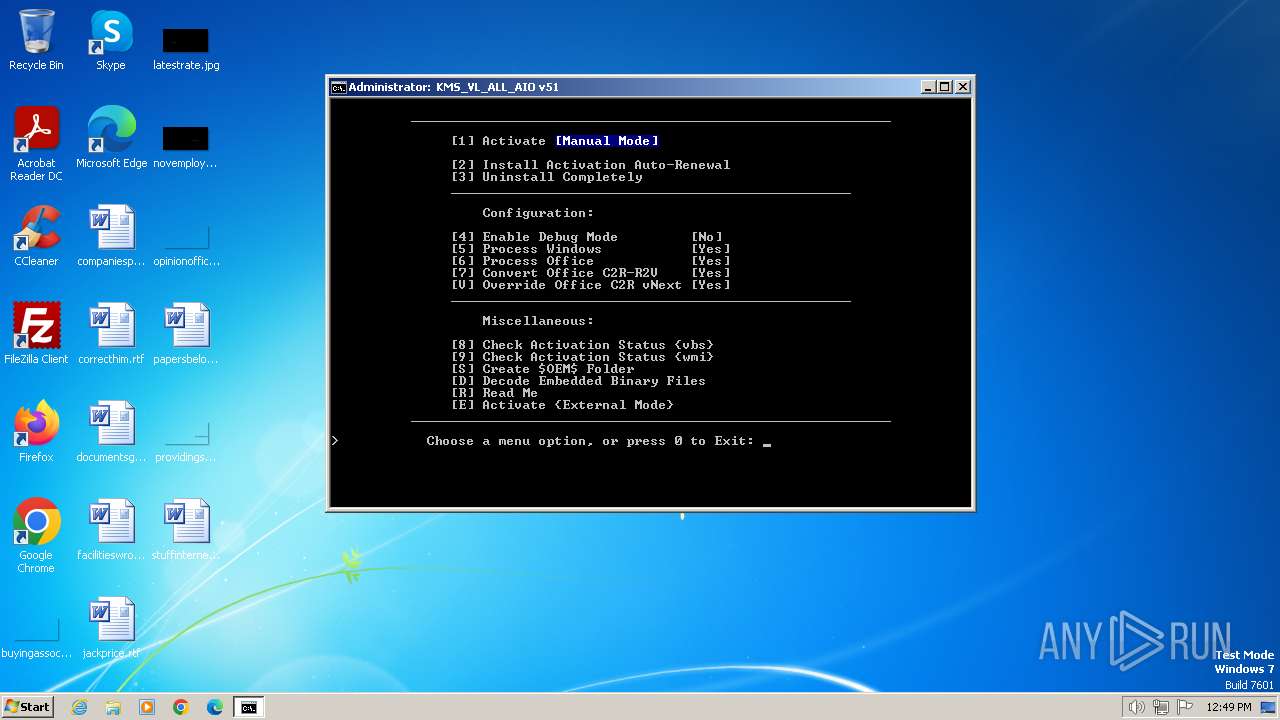
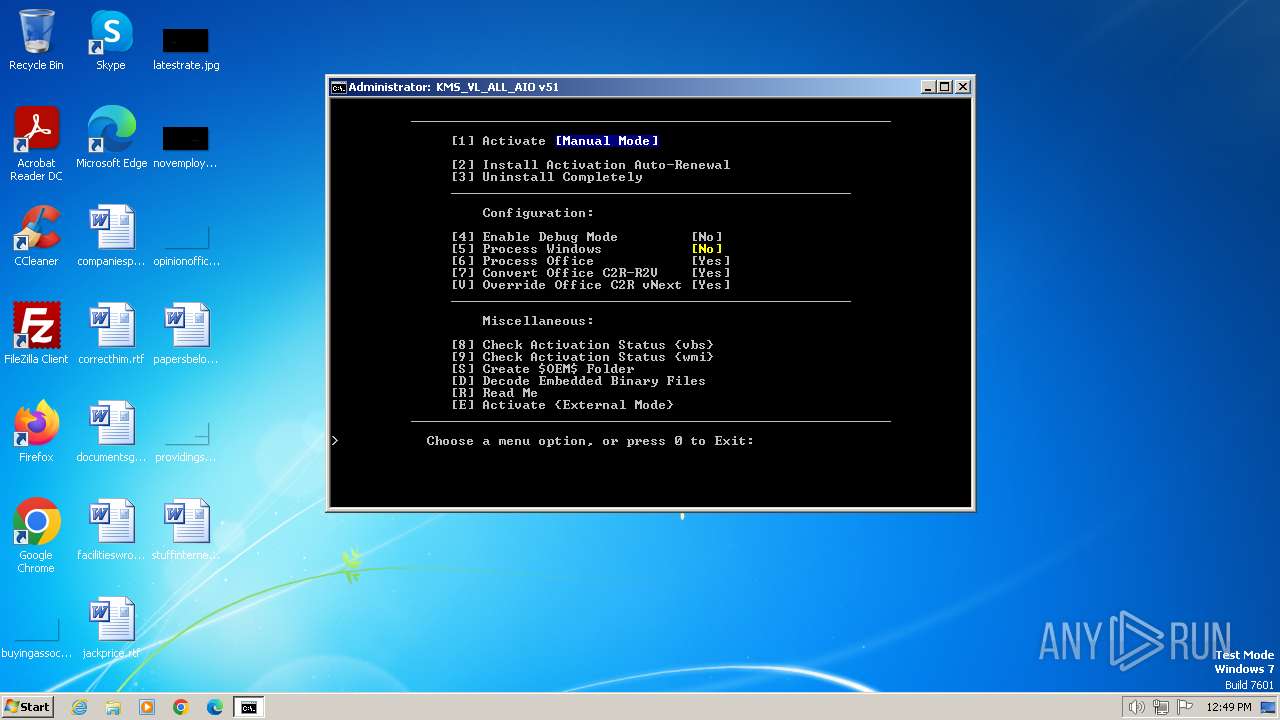
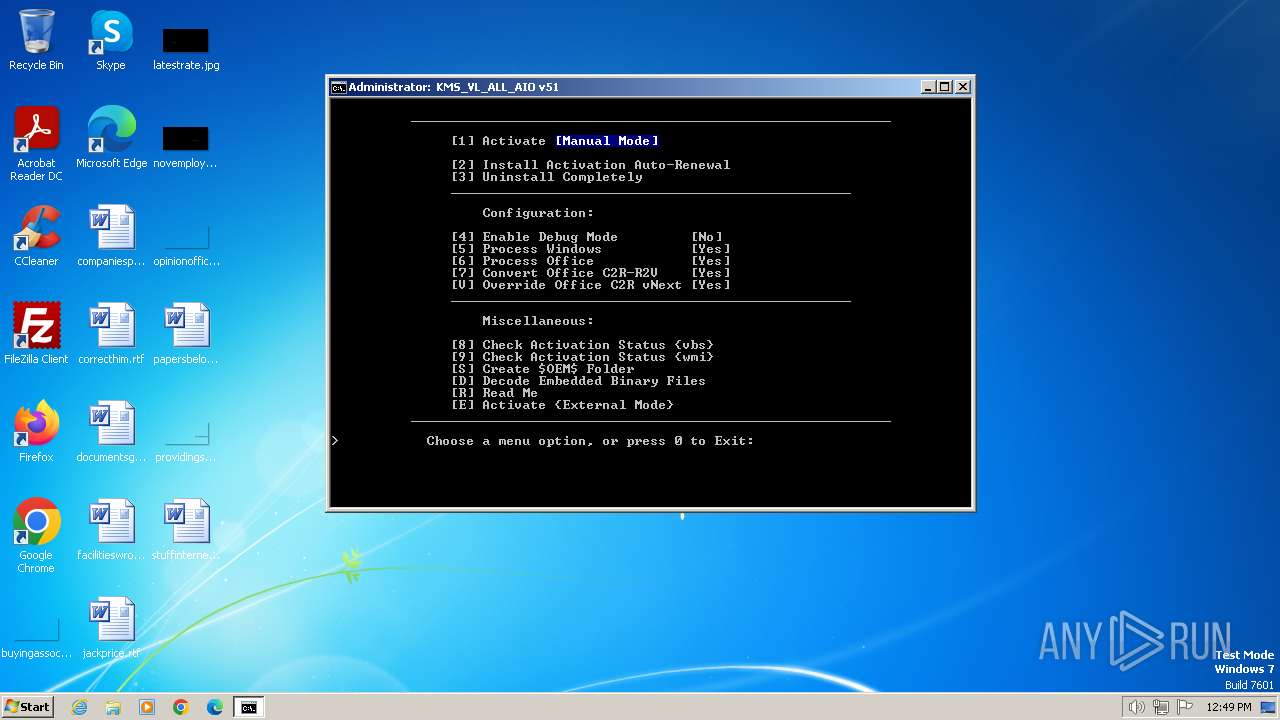
Manual execution by a user
- cmd.exe (PID: 2420)
- wmpnscfg.exe (PID: 4064)
Reads security settings of Internet Explorer
- cscript.exe (PID: 1768)
Reads the computer name
- wmpnscfg.exe (PID: 4064)
Checks supported languages
- mode.com (PID: 1172)
- mode.com (PID: 2656)
- wmpnscfg.exe (PID: 4064)
- csc.exe (PID: 4016)
- cvtres.exe (PID: 4056)
- mode.com (PID: 2308)
- mode.com (PID: 2912)
Reads the machine GUID from the registry
- csc.exe (PID: 4016)
- cvtres.exe (PID: 4056)
Reads Microsoft Office registry keys
- reg.exe (PID: 3200)
- reg.exe (PID: 2404)
- reg.exe (PID: 2512)
- reg.exe (PID: 3664)
Checks operating system version
- cmd.exe (PID: 2576)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .7z | | | 7-Zip compressed archive (v0.4) (57.1) |
|---|---|---|
| .7z | | | 7-Zip compressed archive (gen) (42.8) |
EXIF
MPEG
| MPEGAudioVersion: | 2.5 |
|---|---|
| AudioLayer: | 3 |
| AudioBitrate: | 128 kbps |
| SampleRate: | 11025 |
| ChannelMode: | Dual Channel |
| MSStereo: | Off |
| IntensityStereo: | On |
| CopyrightFlag: | - |
| OriginalMedia: | - |
| Emphasis: | None |
Composite
| Duration: | 5.01 s (approx) |
|---|
Total processes
244
Monitored processes
198
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 128 | reg query "HKCU\Software\Microsoft\Windows\CurrentVersion\Explorer\User Shell Folders" /v Desktop | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 292 | reg delete "HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\osppsvc.exe" /f /v Debugger | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 324 | find /i "STOPPED" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 548 | reg query HKCU\SOFTWARE\Microsoft\Office\16.0\Common\Licensing\LicensingNext /v MigrationToV5Done | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 552 | reg query "HKLM\SOFTWARE\Microsoft\Windows Script Host\Settings" /v Enabled | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 568 | C:\Windows\system32\cmd.exe /c wmic path SoftwareLicensingProduct where "ApplicationID='55c92734-d682-4d71-983e-d6ec3f16059f' and Description like '%KMSCLIENT%' " get ID /value | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 668 | powershell -nop -c "&{$W=$Host.UI.RawUI.WindowSize;$B=$Host.UI.RawUI.BufferSize;$W.Height=31;$B.Height=300;$Host.UI.RawUI.WindowSize=$W;$Host.UI.RawUI.BufferSize=$B;}" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 696 | wmic path SoftwareLicensingProduct where "Description like '%KMSCLIENT%'" get Name /value | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 712 | wmic path Win32_ComputerSystem get CreationClassName /value | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 748 | find /i "Full" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (grep) Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
18 733
Read events
18 662
Write events
53
Delete events
18
Modification events
| (PID) Process: | (3956) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3956) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3956) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3956) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (3956) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (3956) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (3956) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\curl-8.5.0_1-win32-mingw.zip | |||
| (PID) Process: | (3956) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\KMS_VL_ALL_AIO-51.7z | |||
| (PID) Process: | (3956) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3956) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
Executable files
2
Suspicious files
10
Text files
5
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2324 | powershell.exe | C:\Users\admin\AppData\Local\Temp\kgkk1zmc.lnq.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 3956 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb3956.40359\KMS_VL_ALL_AIO.cmd | text | |
MD5:90D94AB45D1C4ACD9377E73E46C4BCA8 | SHA256:B80707DE08A518394CD343AFBD506FFEEE25DB34B4068F7970F4D2EEA3DFDBDC | |||
| 2184 | powershell.exe | C:\Users\admin\AppData\Local\Temp\eswbod1e.dar.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 2576 | cmd.exe | C:\Windows\Temp\`.txt | text | |
MD5:FFE40BE0916C7302AE237FEEBE53CF4B | SHA256:6EF78A8EF8E0752565DCC75E10DB254A573A51EAA183F0BFF99494E62F0B57C6 | |||
| 2324 | powershell.exe | C:\Users\admin\AppData\Local\Temp\w2nsmil2.pjo.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 2184 | powershell.exe | C:\Users\admin\AppData\Local\Temp\mdaquvif.pqb.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 2184 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:446DD1CF97EABA21CF14D03AEBC79F27 | SHA256:A7DE5177C68A64BD48B36D49E2853799F4EBCFA8E4761F7CC472F333DC5F65CF | |||
| 3588 | powershell.exe | C:\Windows\Temp\a0rugxy2\a0rugxy2.0.cs | text | |
MD5:EAFBB318108FC62A15B458EBBA405940 | SHA256:45EE3DD57AA47FCF92C09A44276DE5EF1688BB0563E09206D8E882528E6DE9D2 | |||
| 668 | powershell.exe | C:\Users\admin\AppData\Local\Temp\kugjni1l.jnf.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 3588 | powershell.exe | C:\Windows\Temp\a0rugxy2\a0rugxy2.cmdline | text | |
MD5:580D2D8320C72FE74937D6A790D28AAC | SHA256:F232A7F51257FDB30E9F7B0B275053C9BC88946B780571A6218DAE06BDCE8309 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |