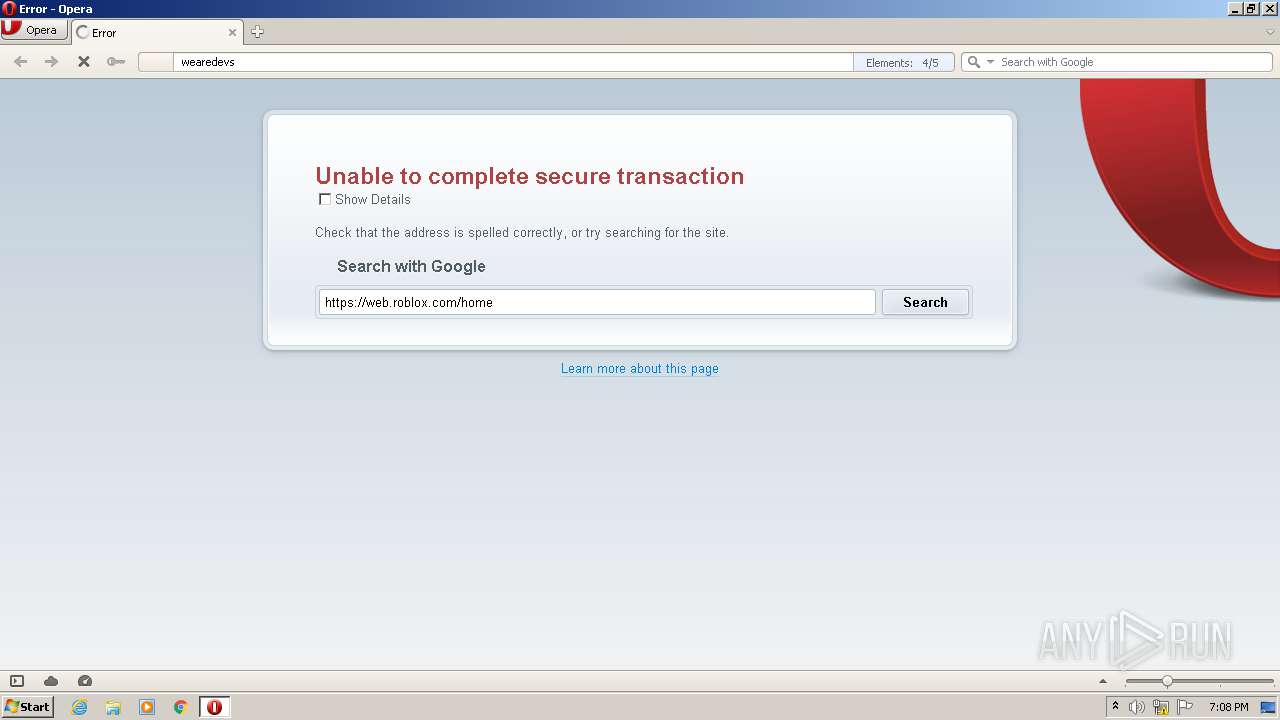
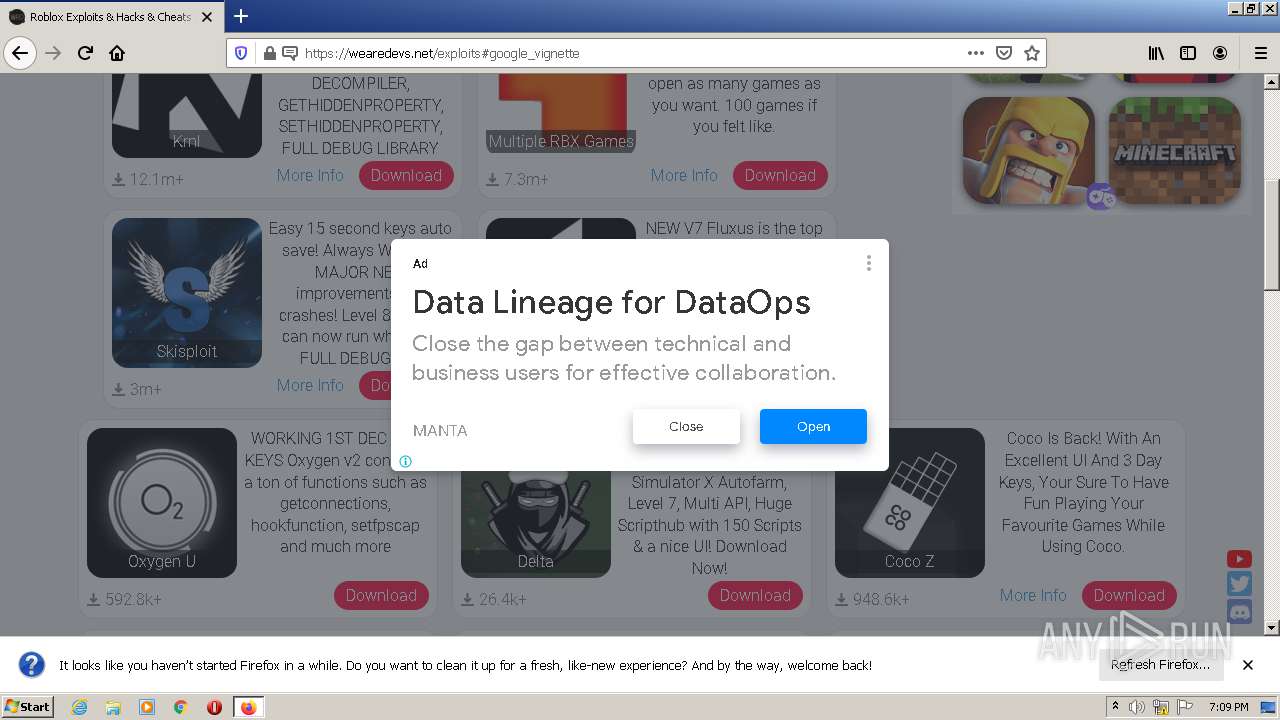
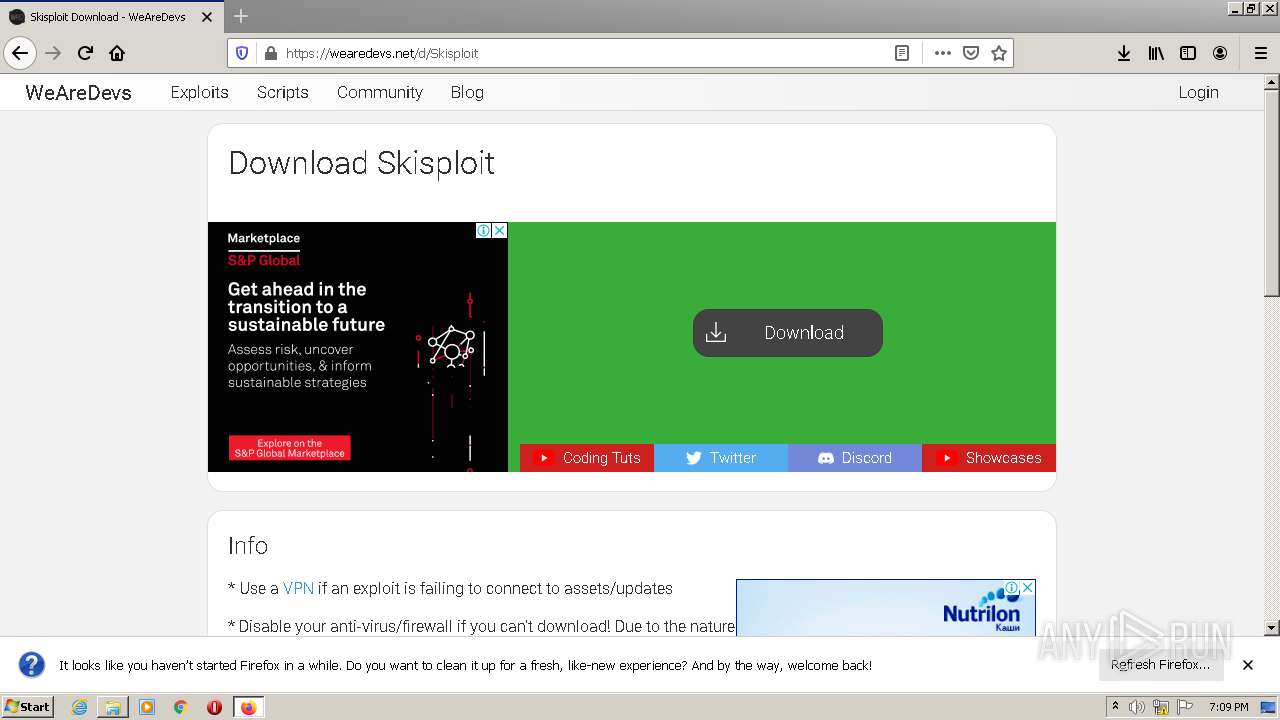
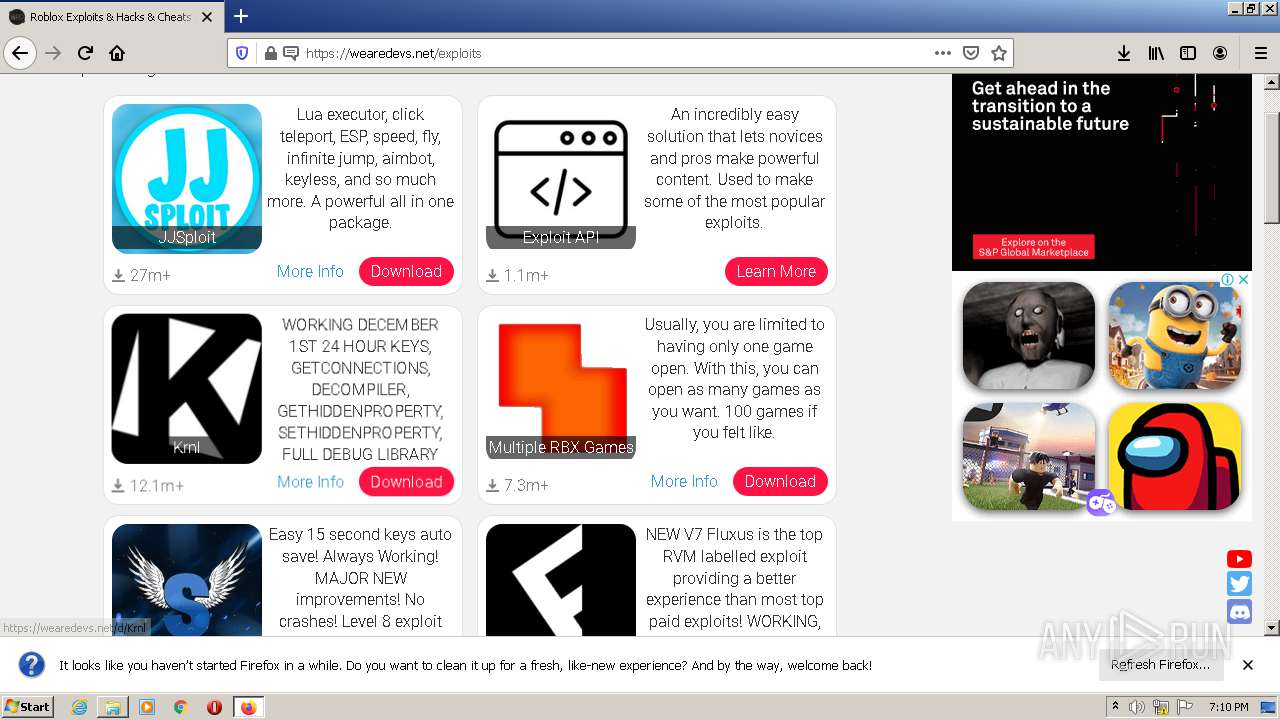
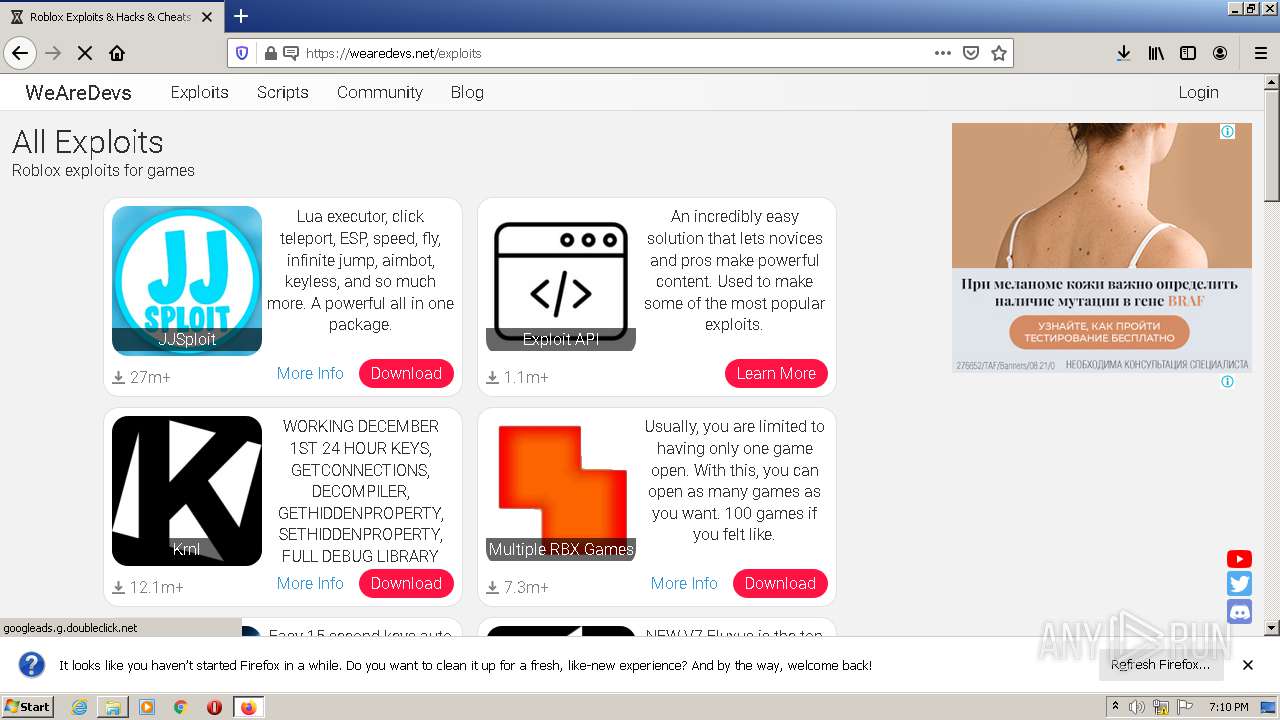
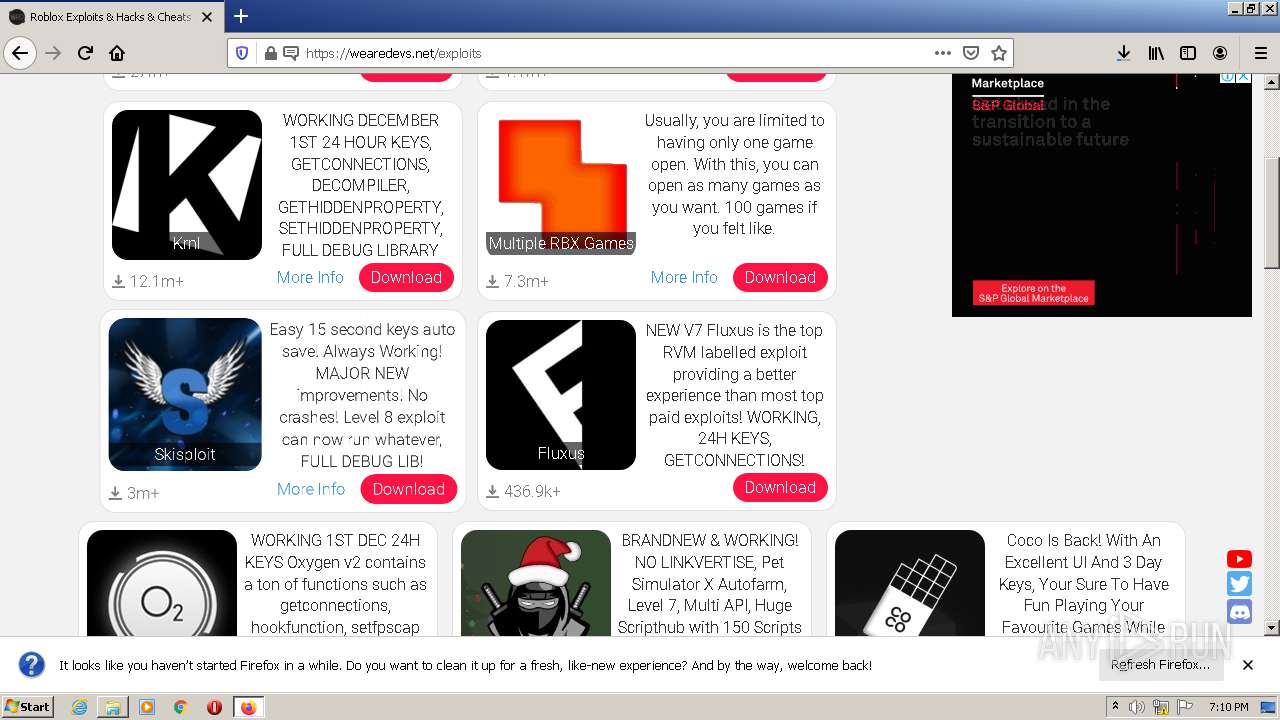
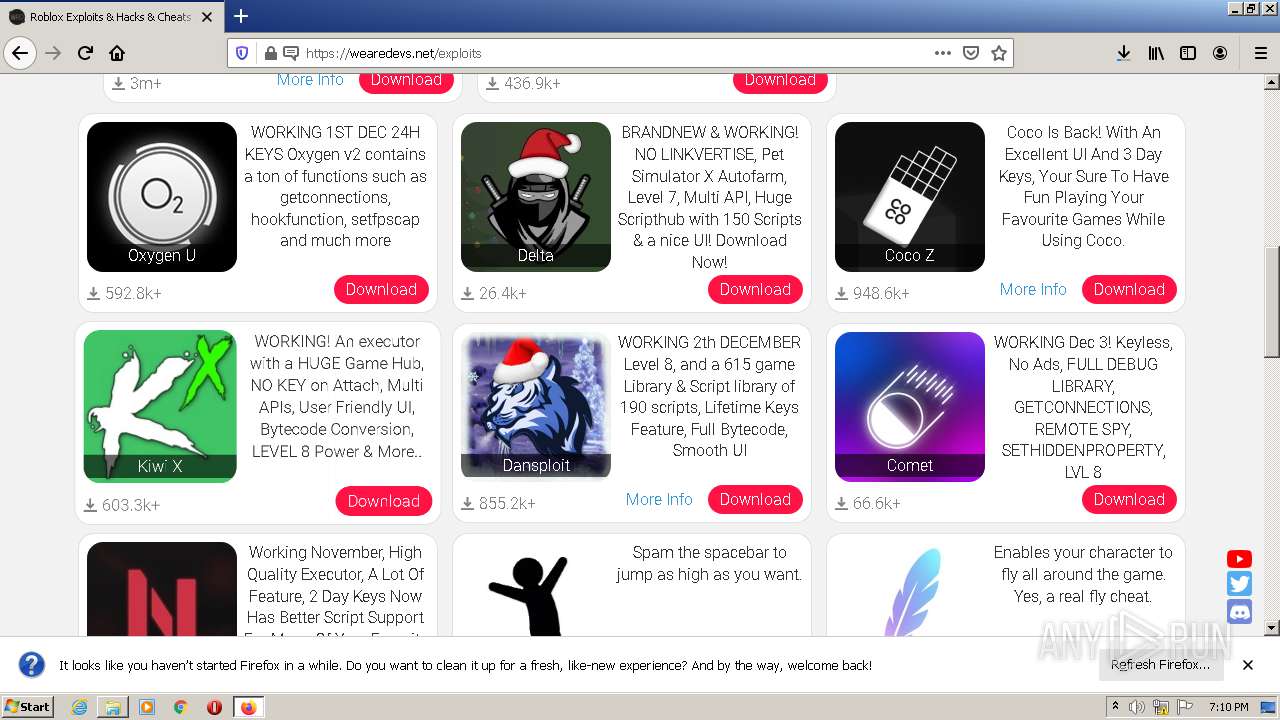
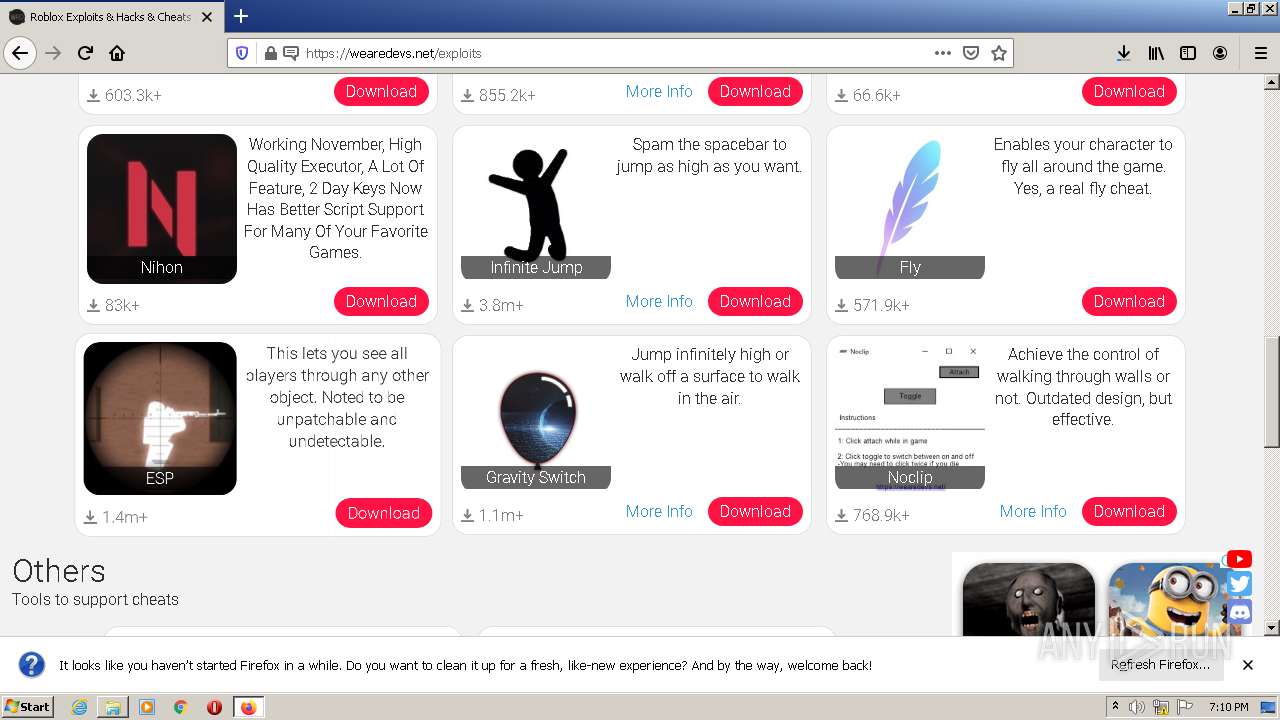
| URL: | https://web.roblox.com/home |
| Full analysis: | https://app.any.run/tasks/b2d38dc8-0811-4c02-8320-1f14feb407c5 |
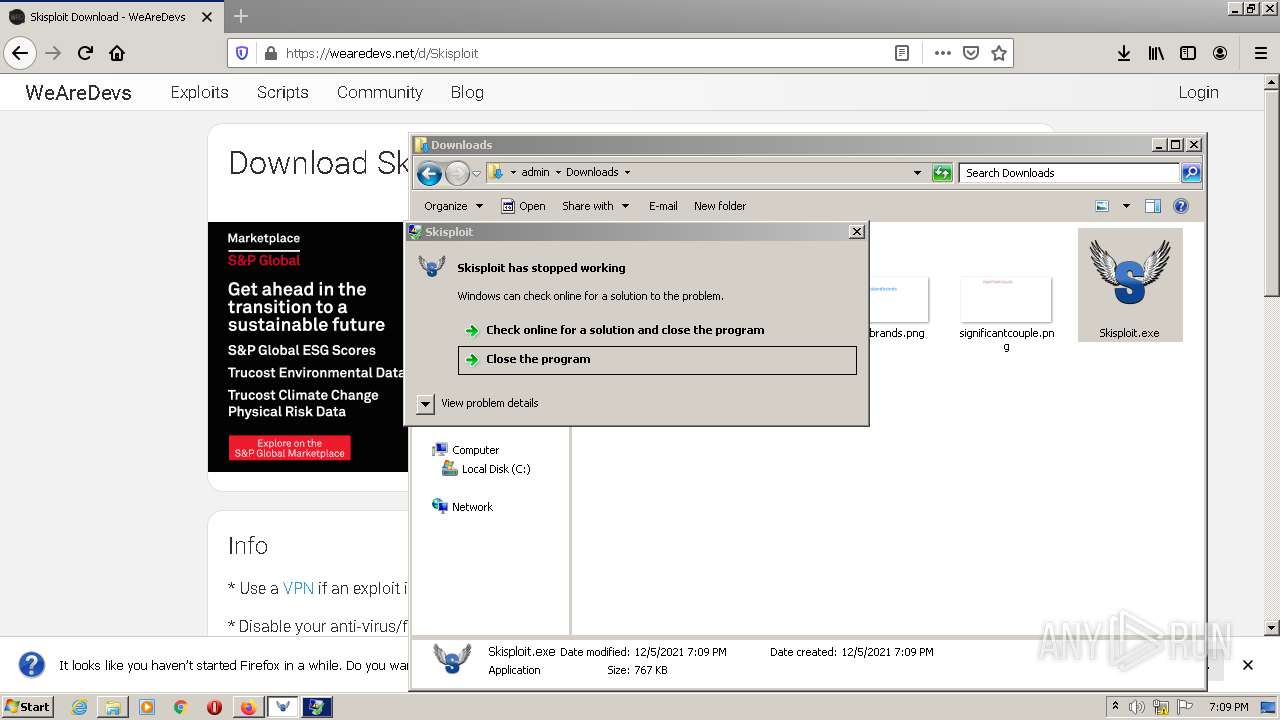
| Verdict: | Malicious activity |
| Analysis date: | December 05, 2021, 19:07:31 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 5147A3EEAA6520414838932FF4D472FB |
| SHA1: | A547F344772B2ECCEDE55C1F3670361834ED51A1 |
| SHA256: | 0435033D7681142FAF64D2DD35211EF90112506FBD70AECD450405B7B5CC1D72 |
| SSDEEP: | 3:N8RDXIWK9:2CN9 |
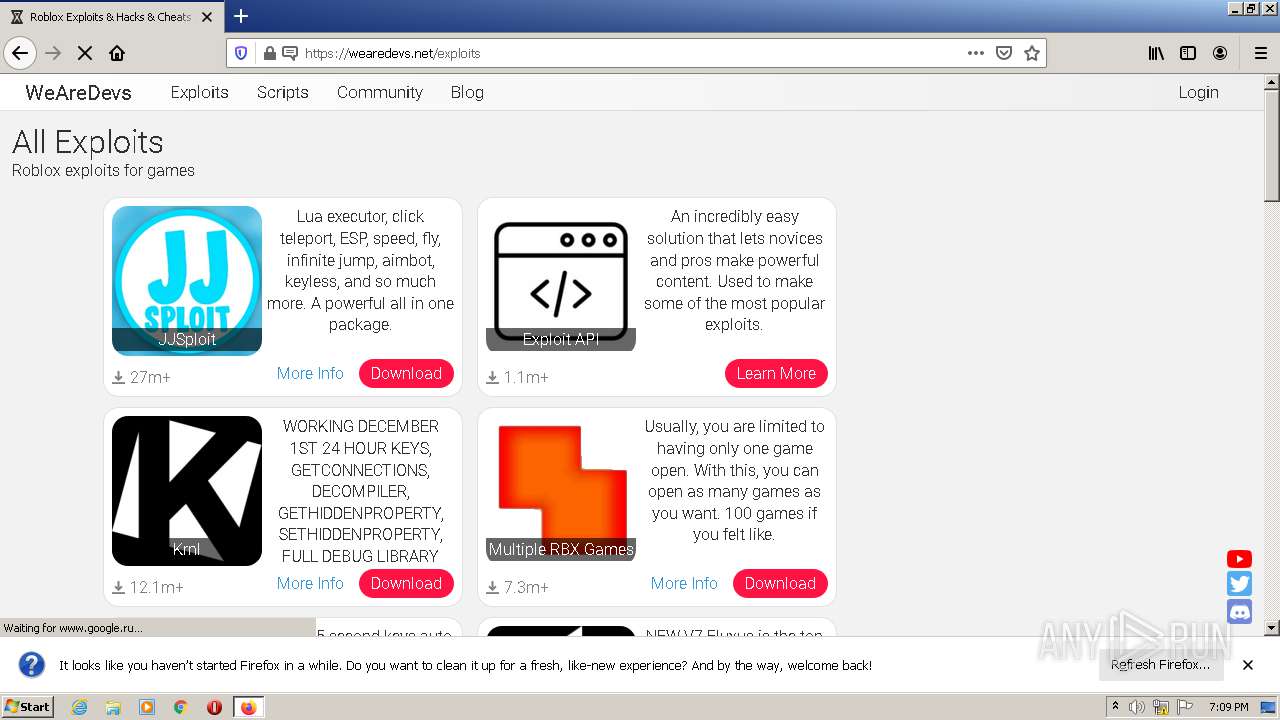
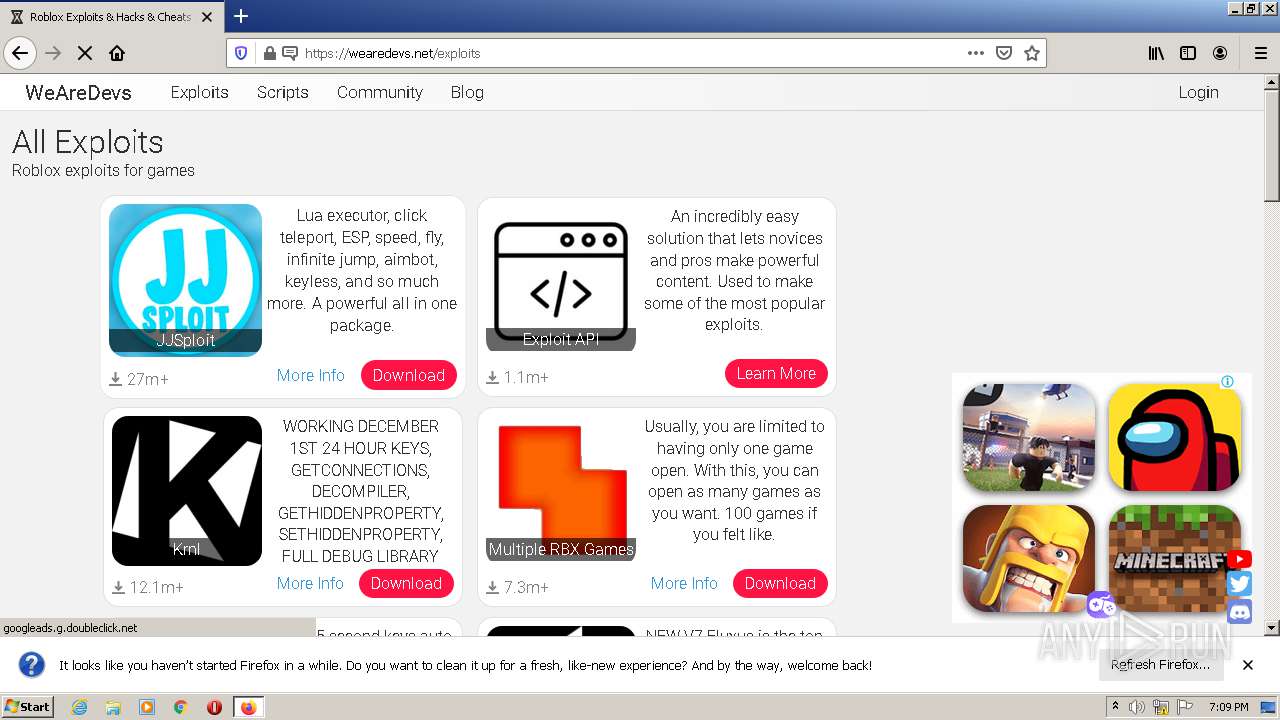
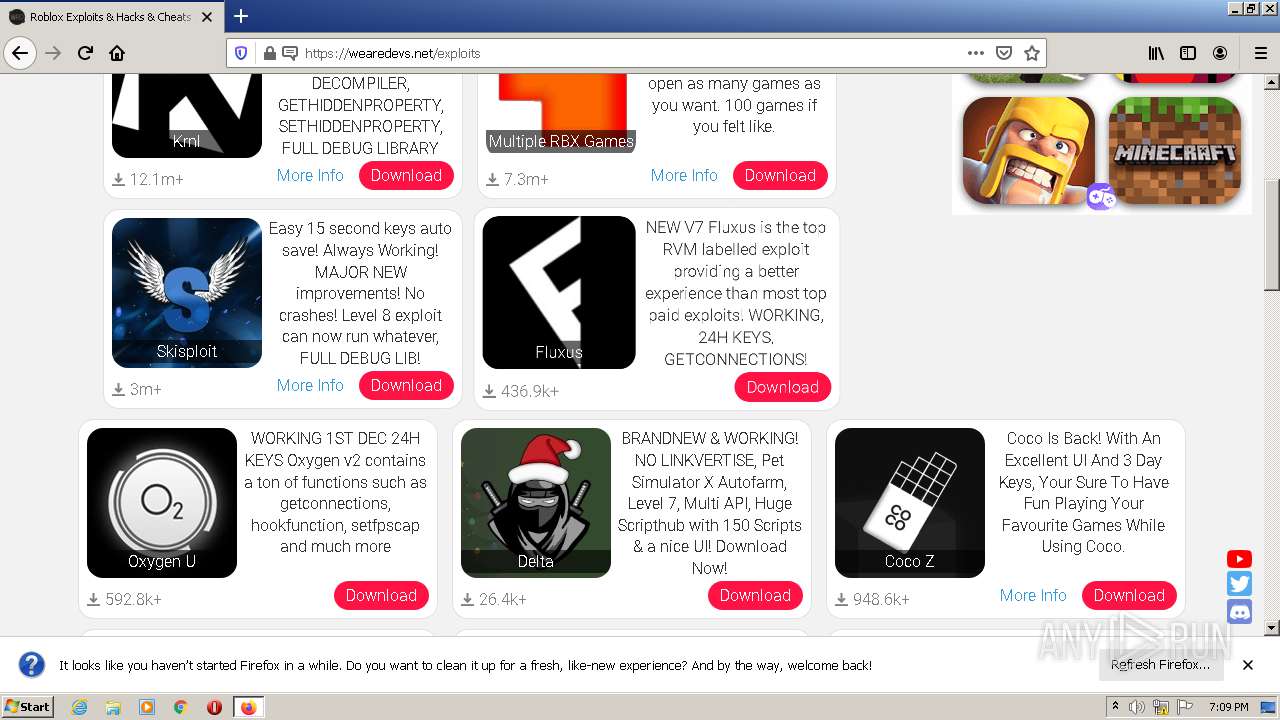
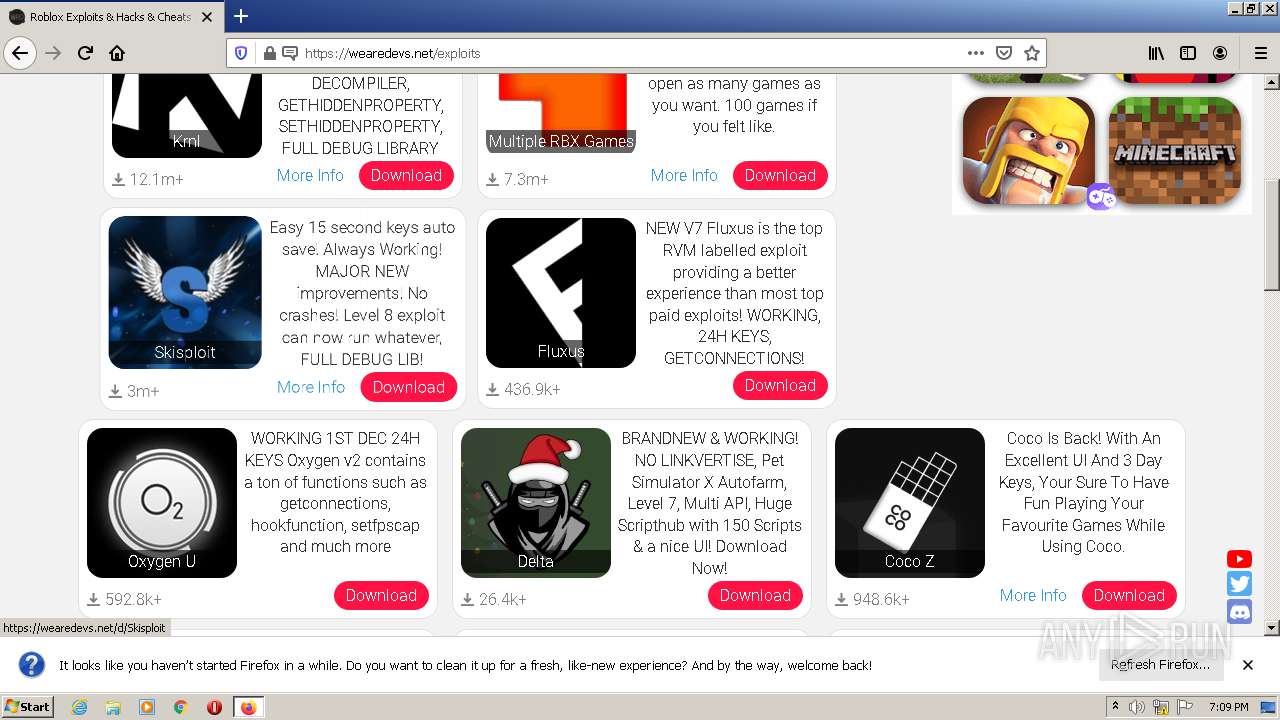
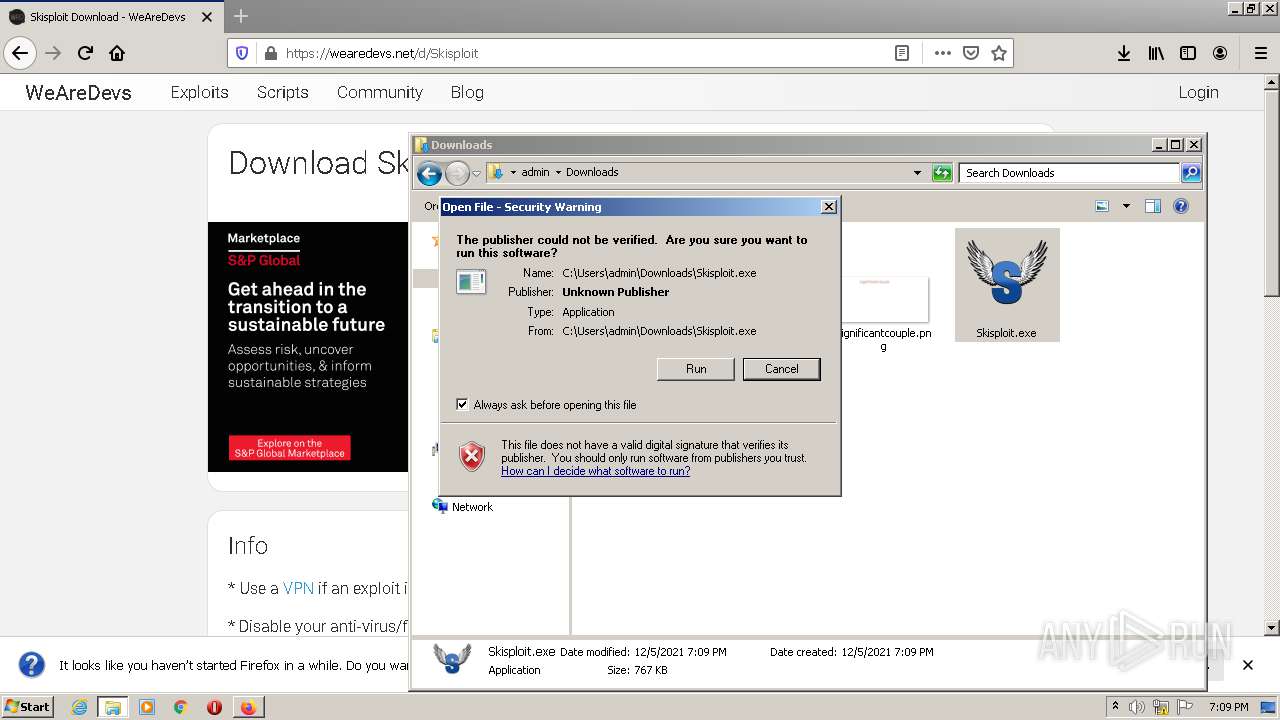
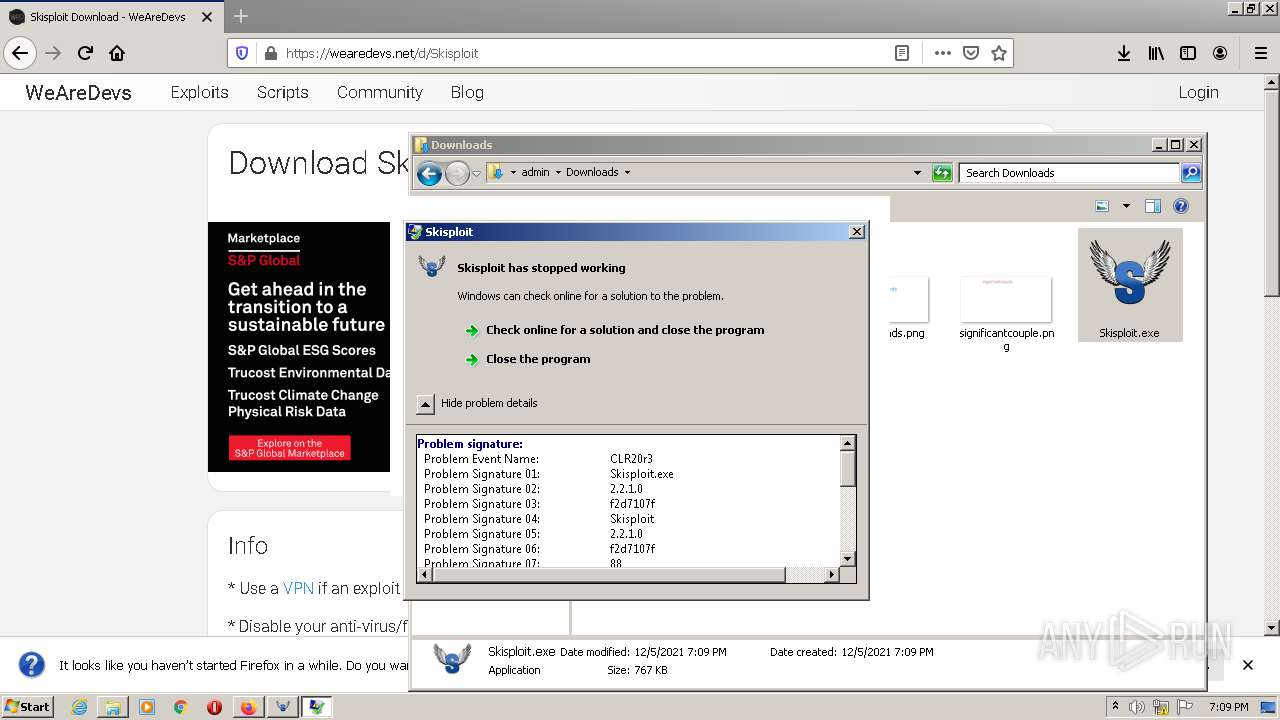
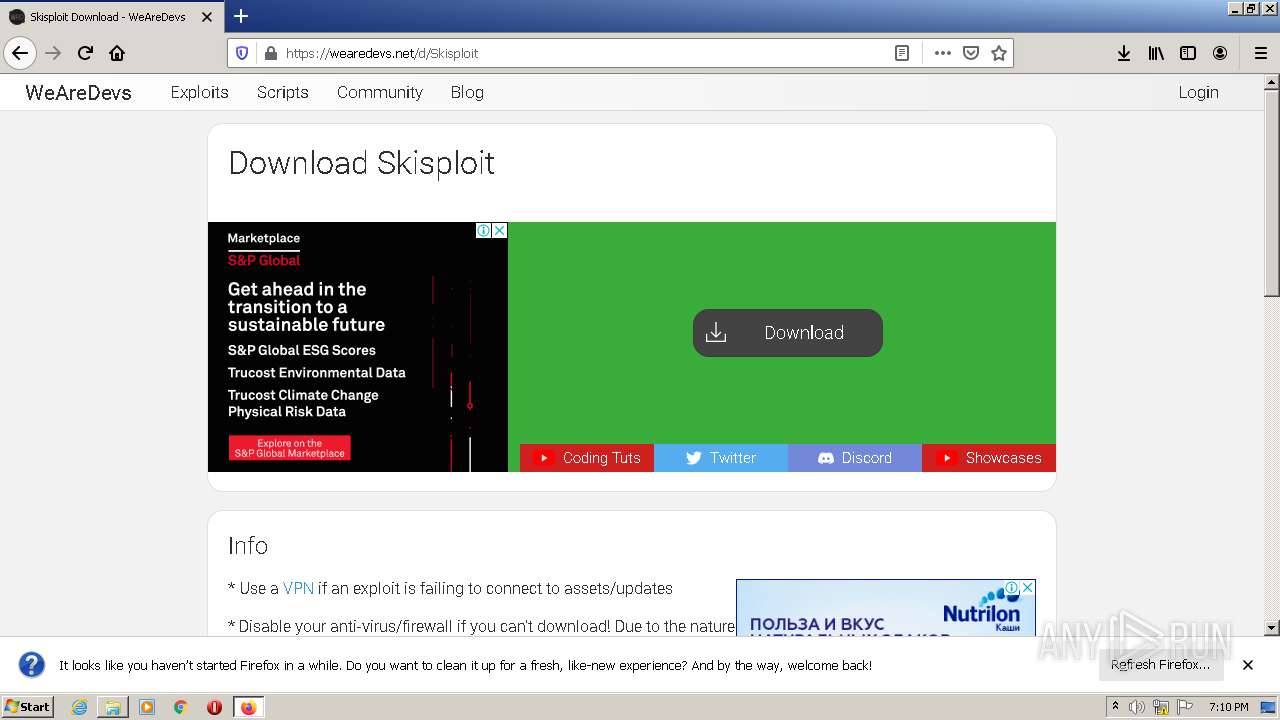
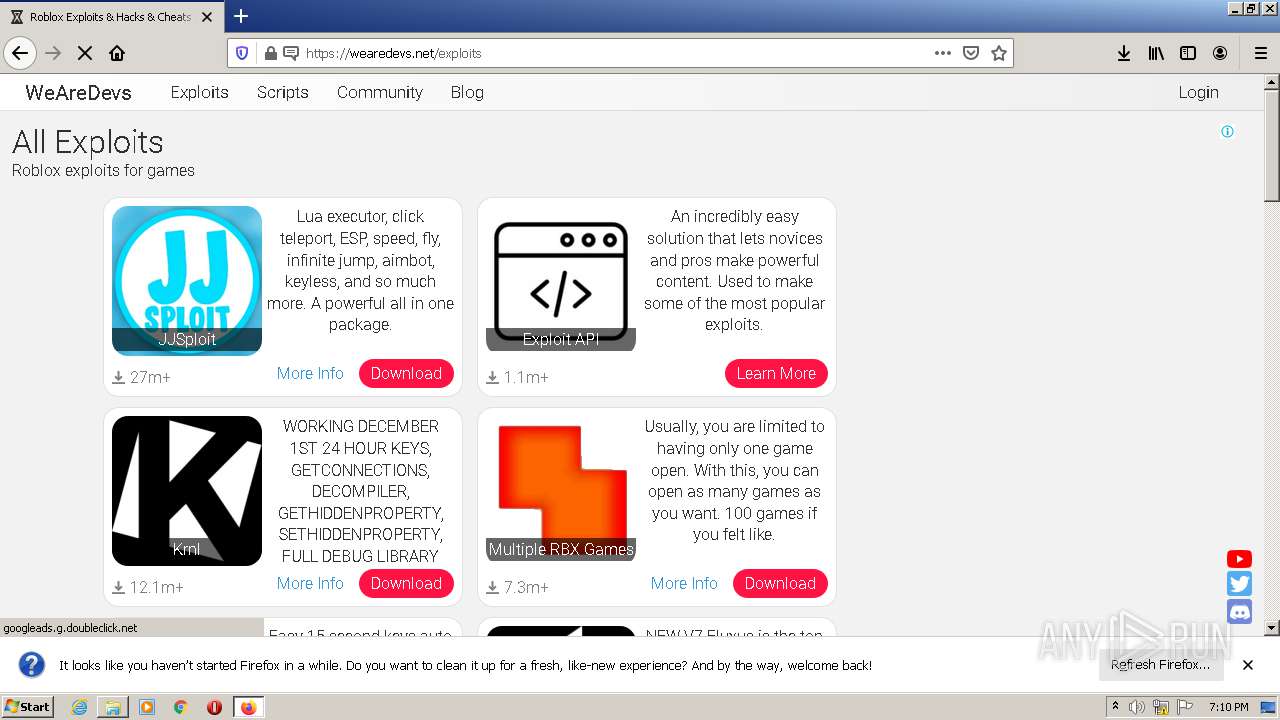
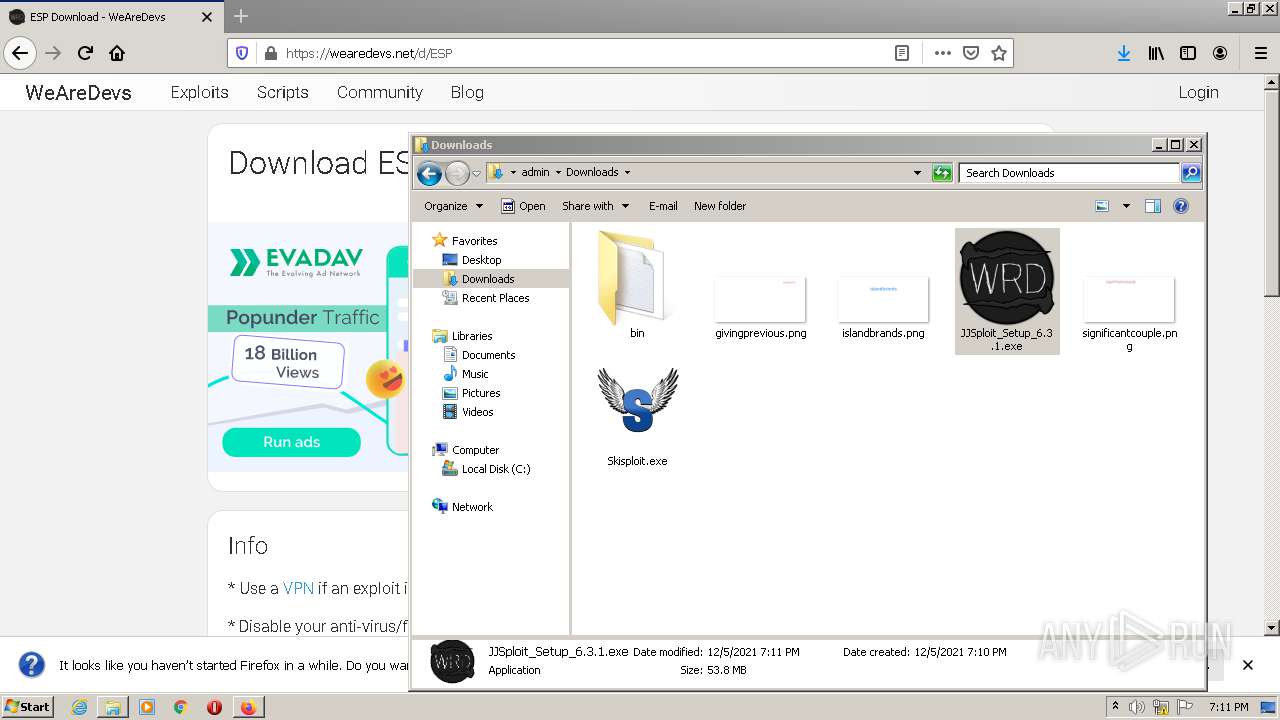
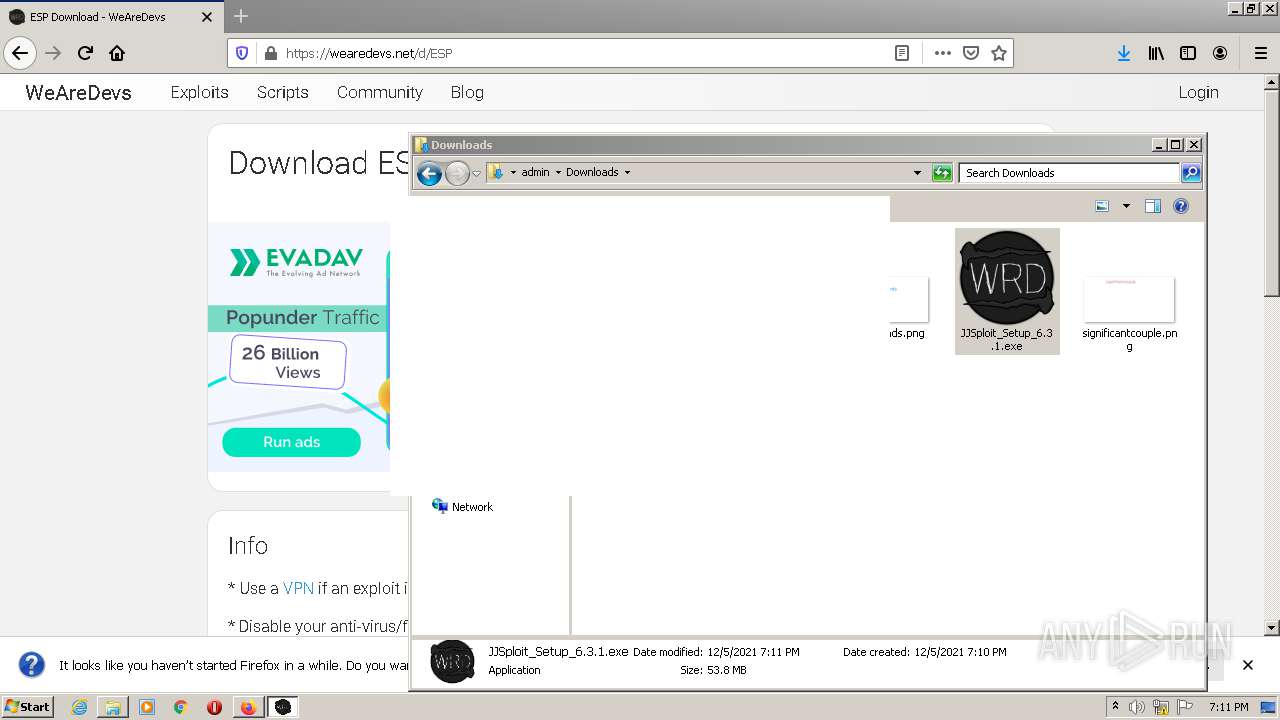
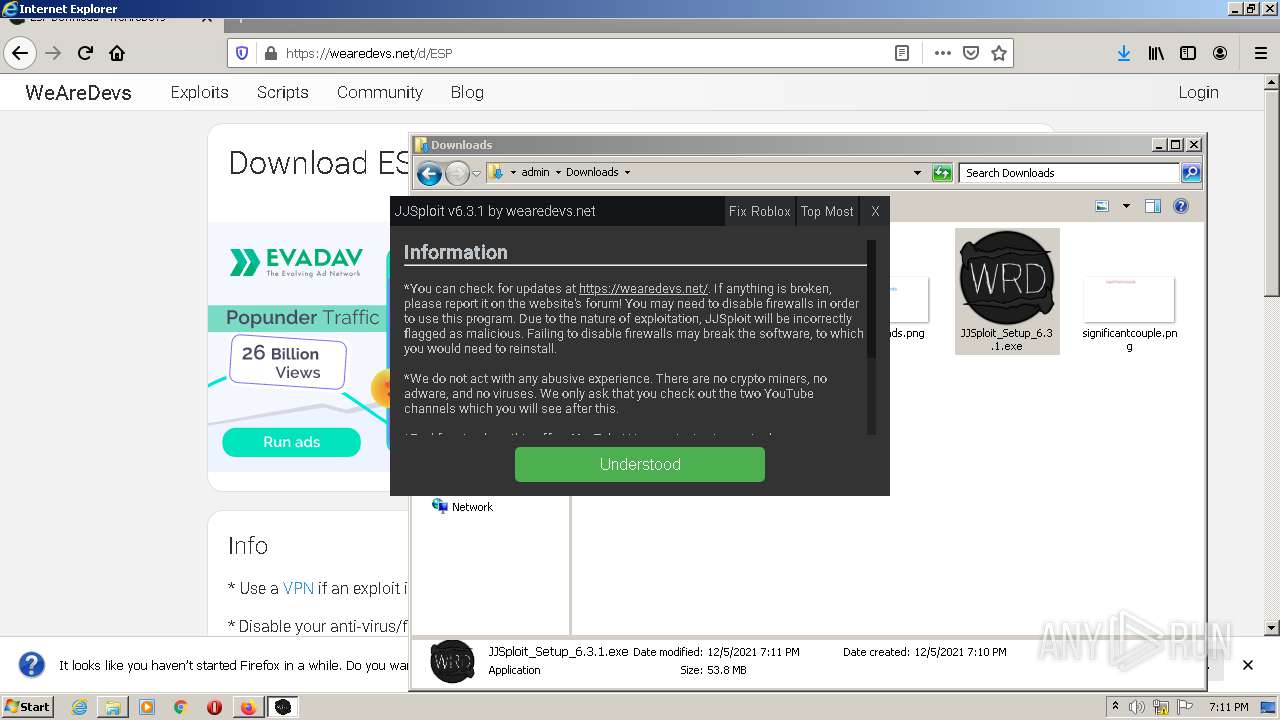
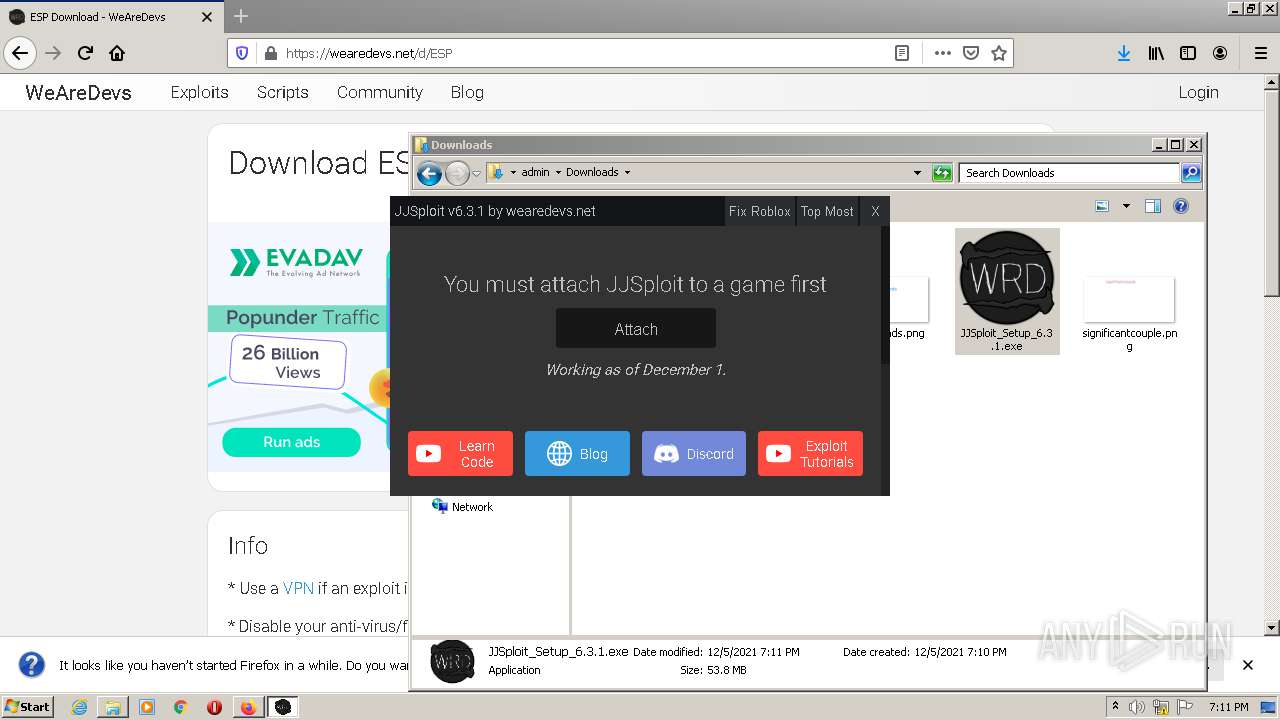
MALICIOUS
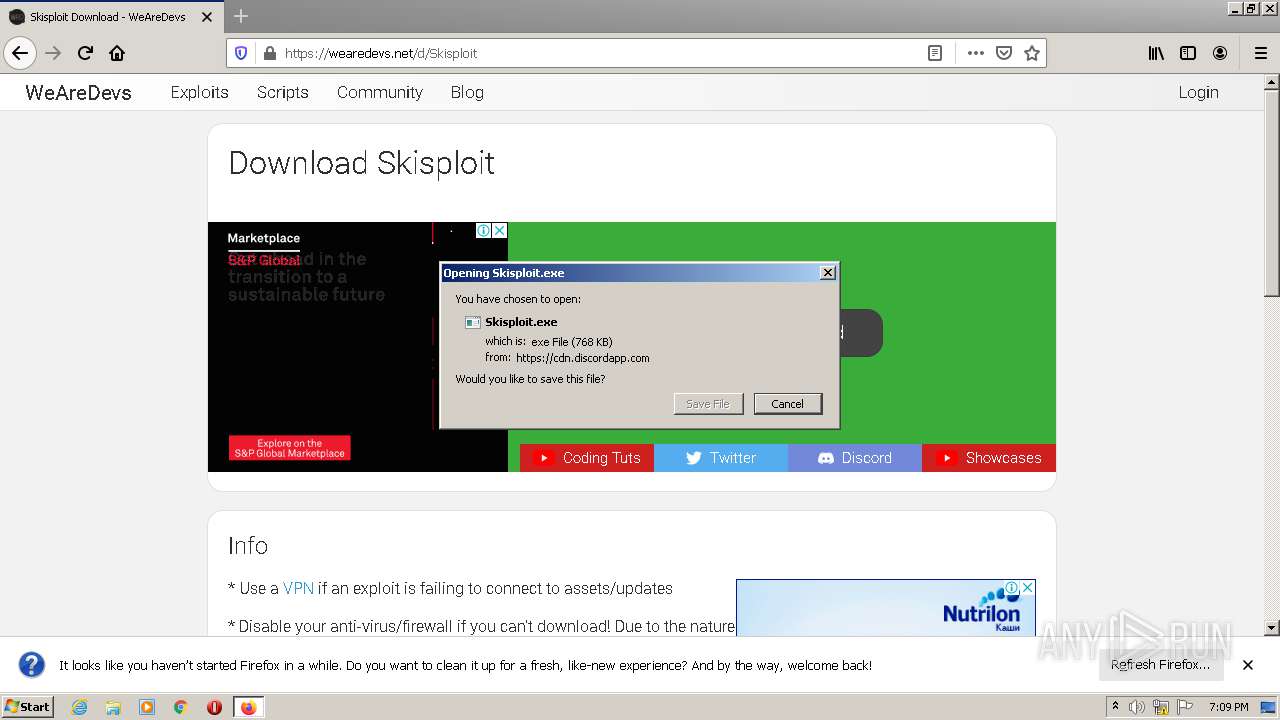
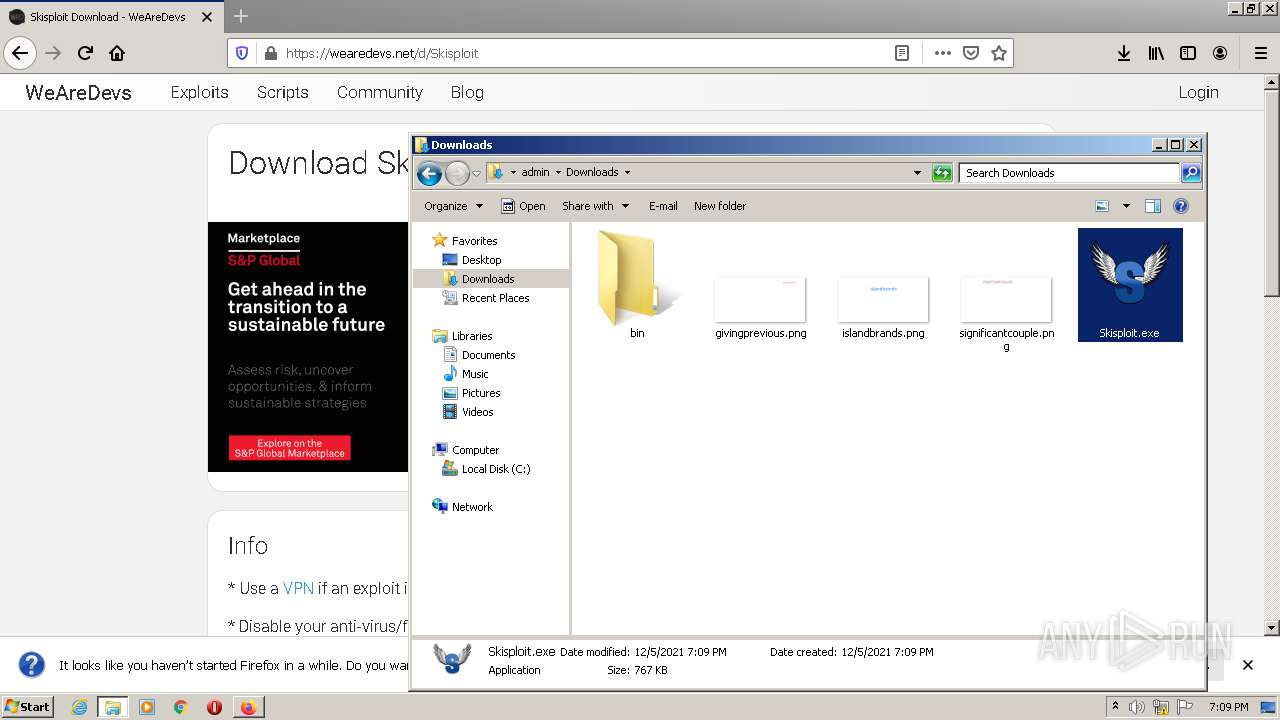
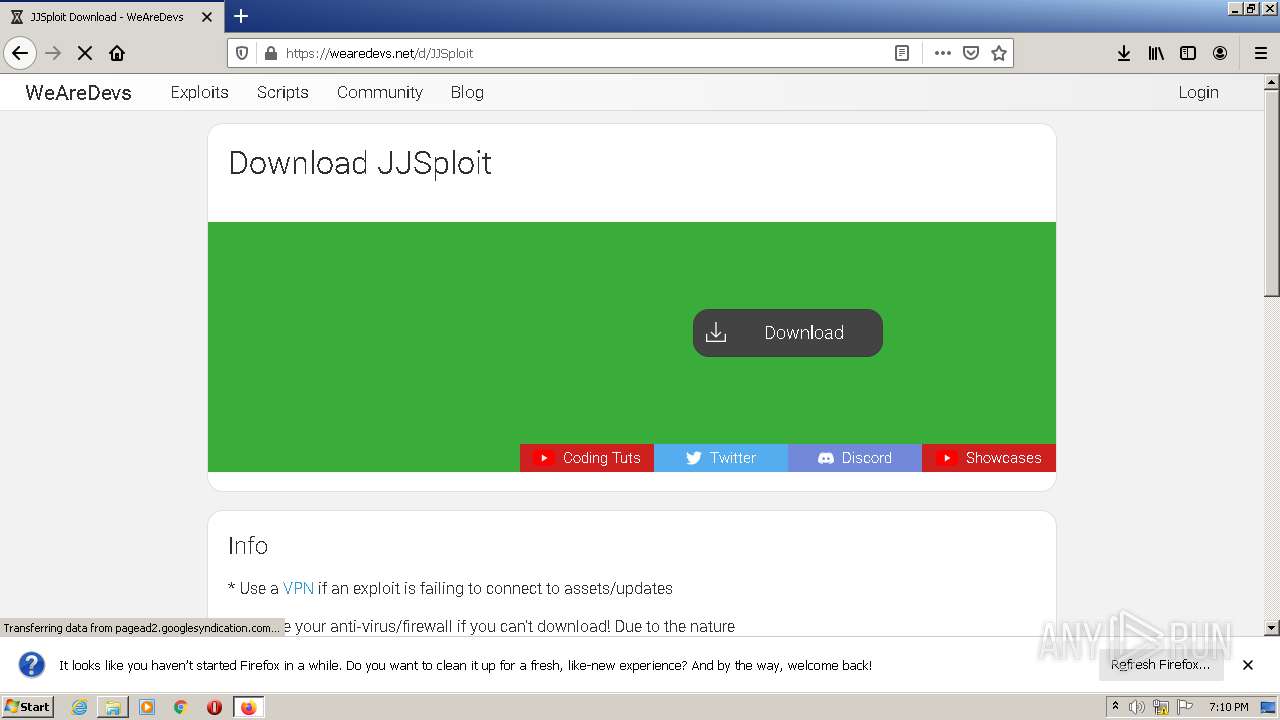
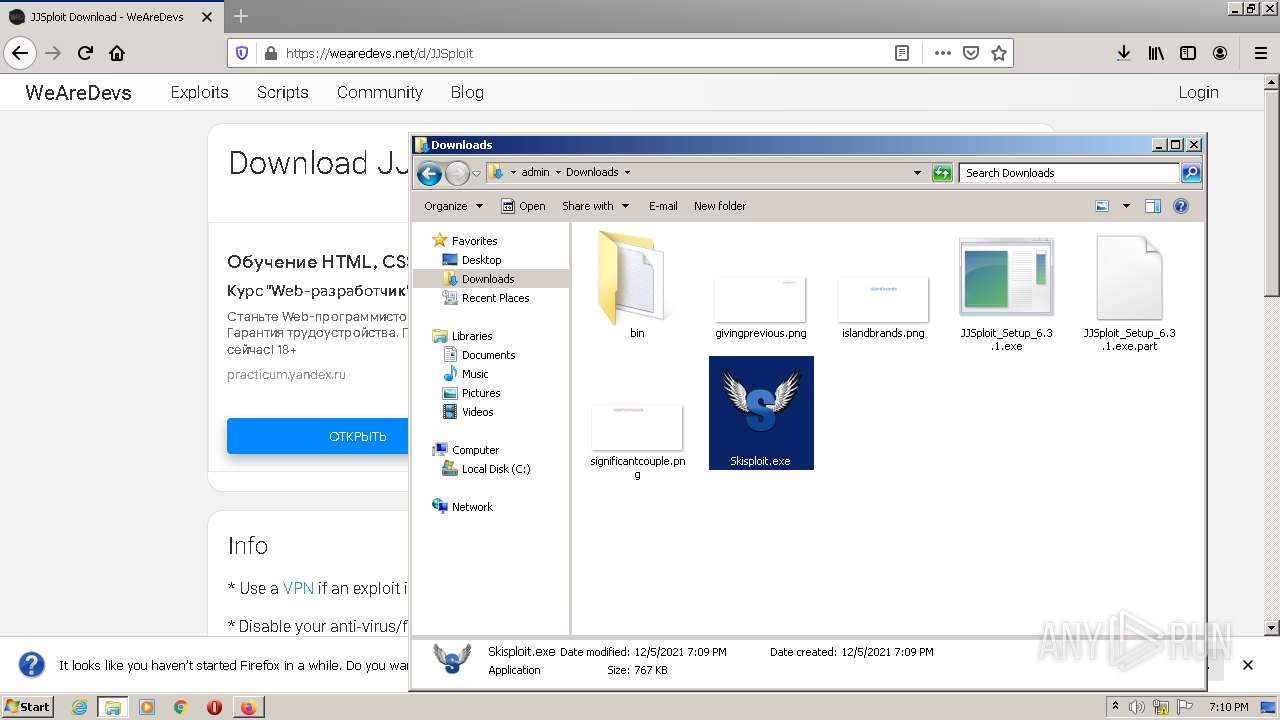
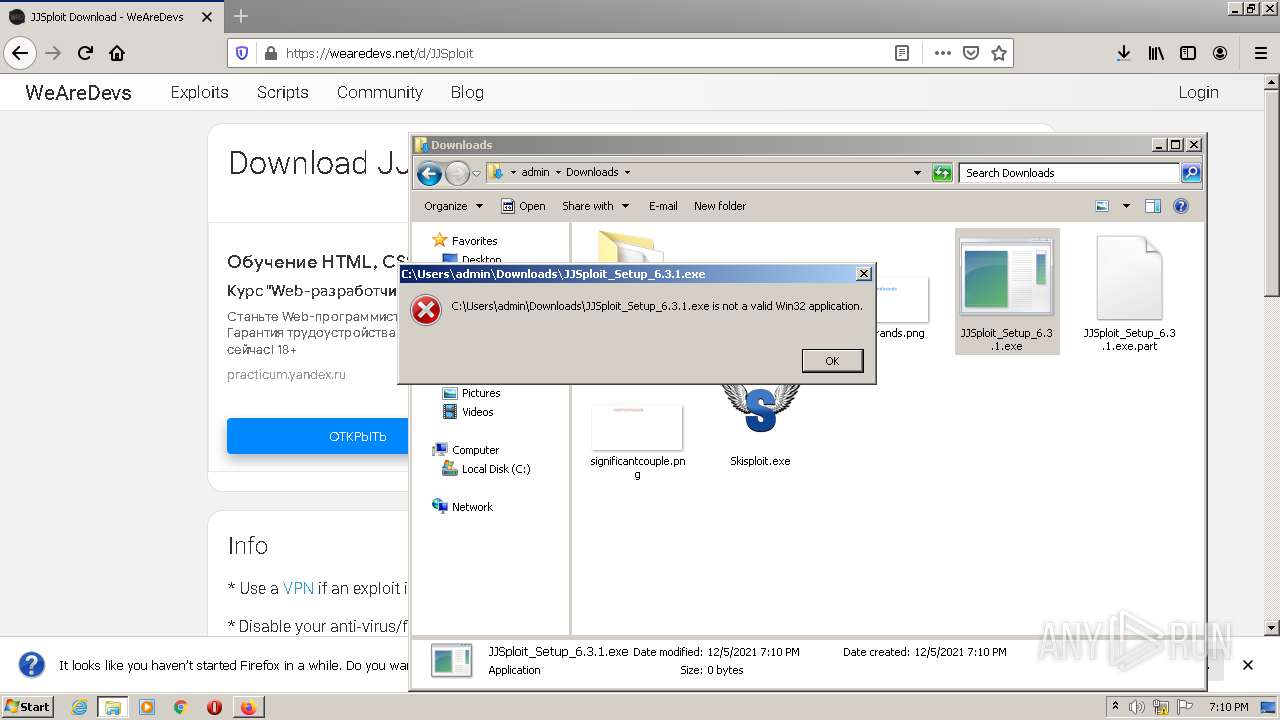
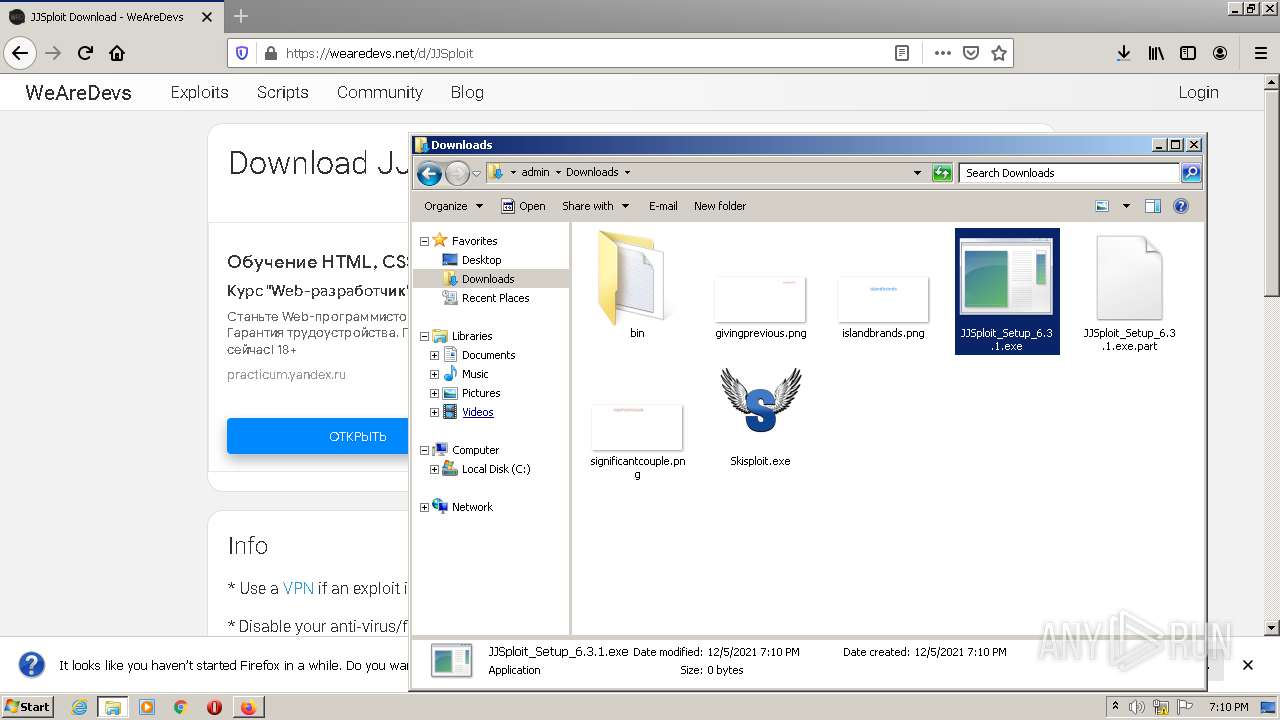
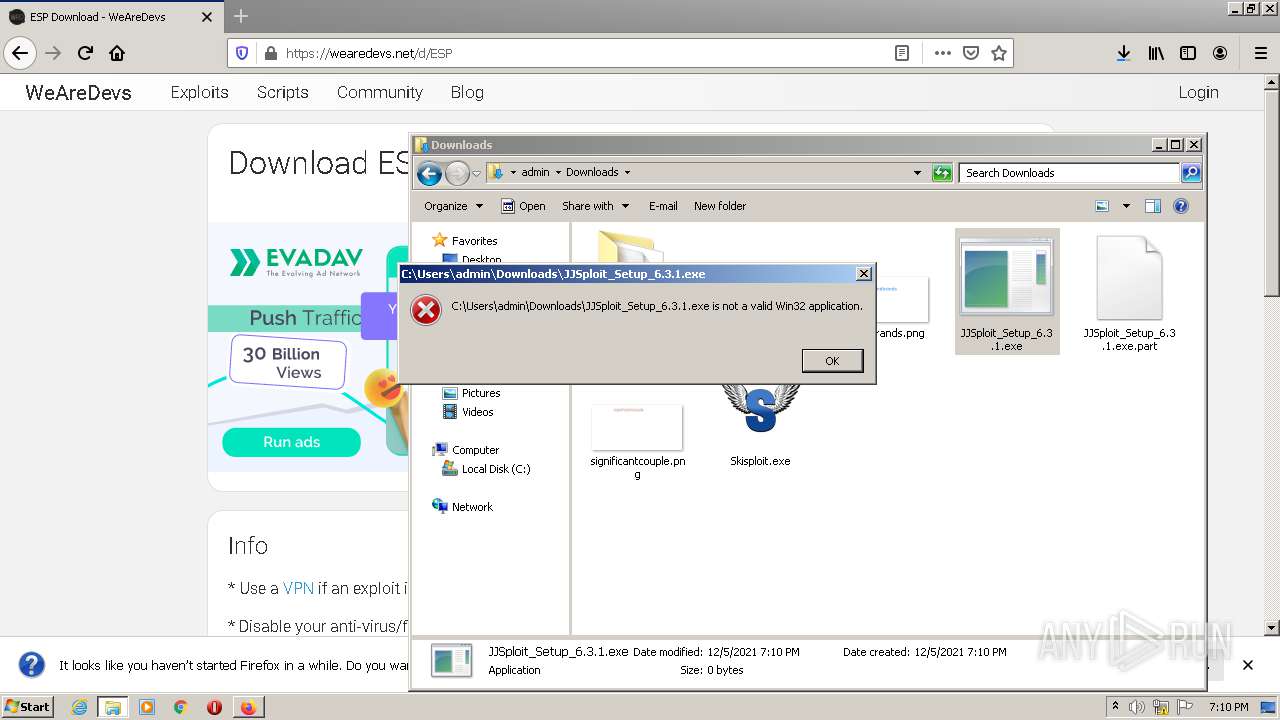
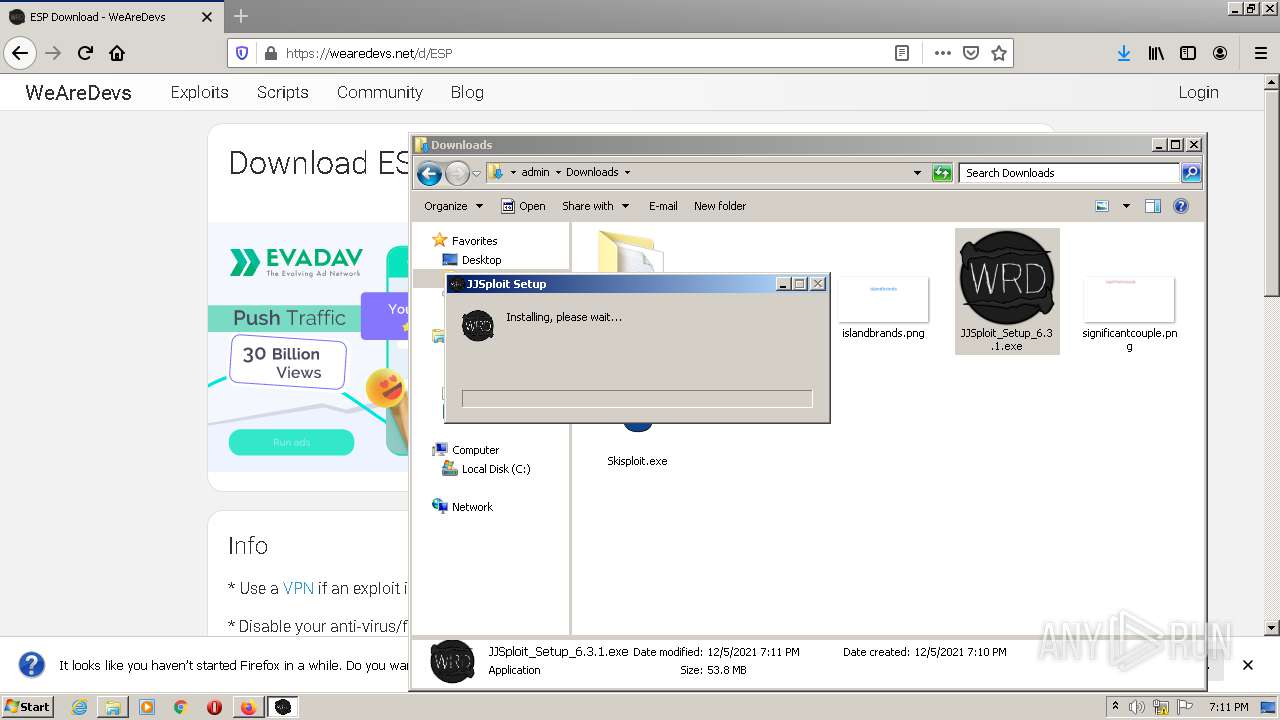
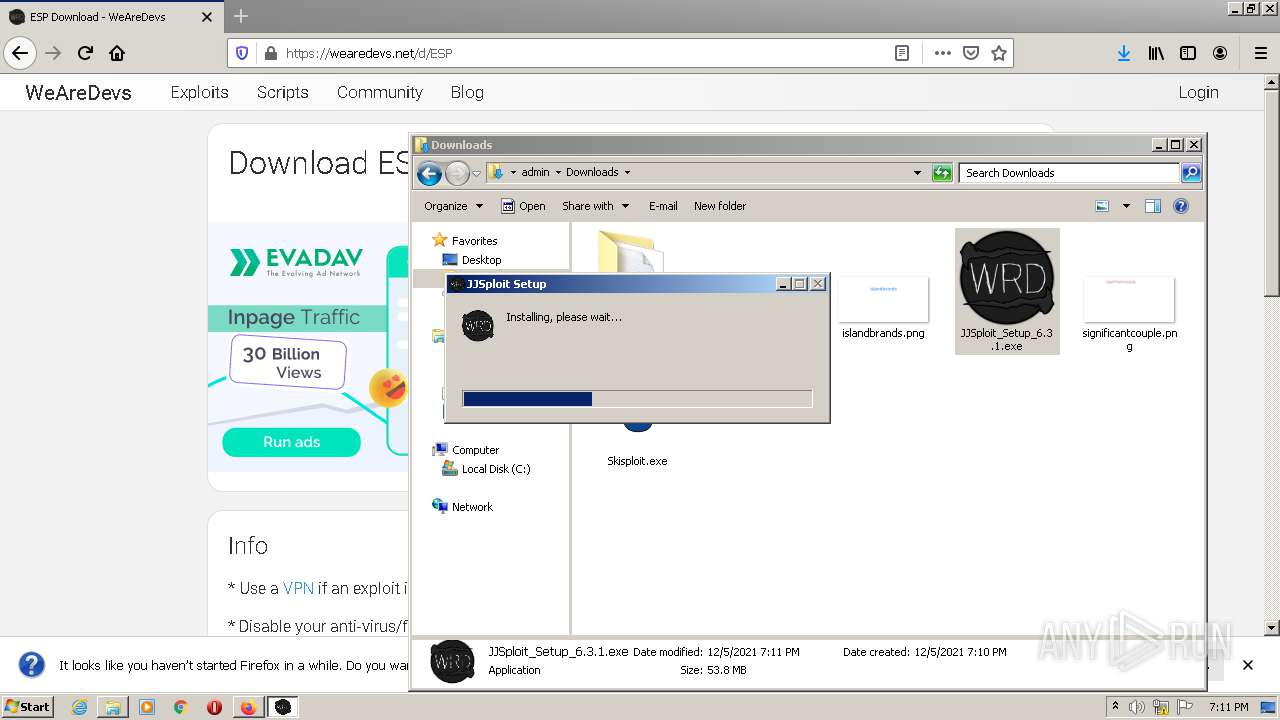
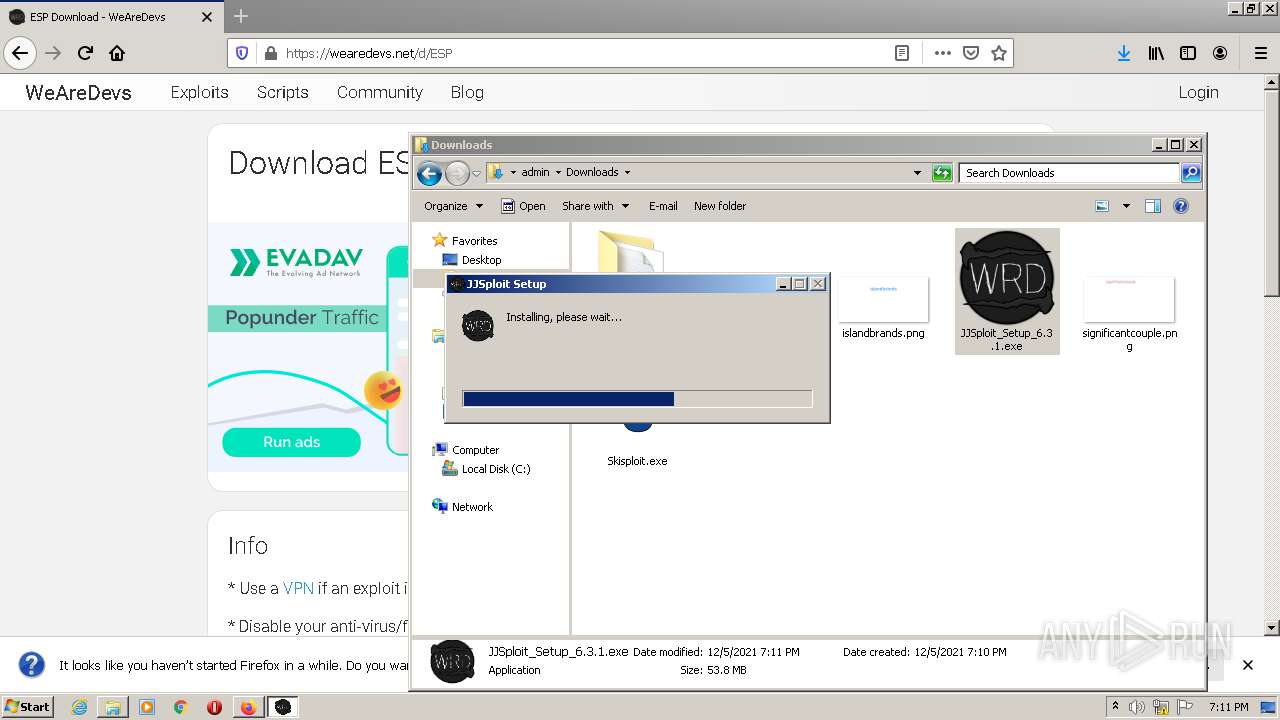
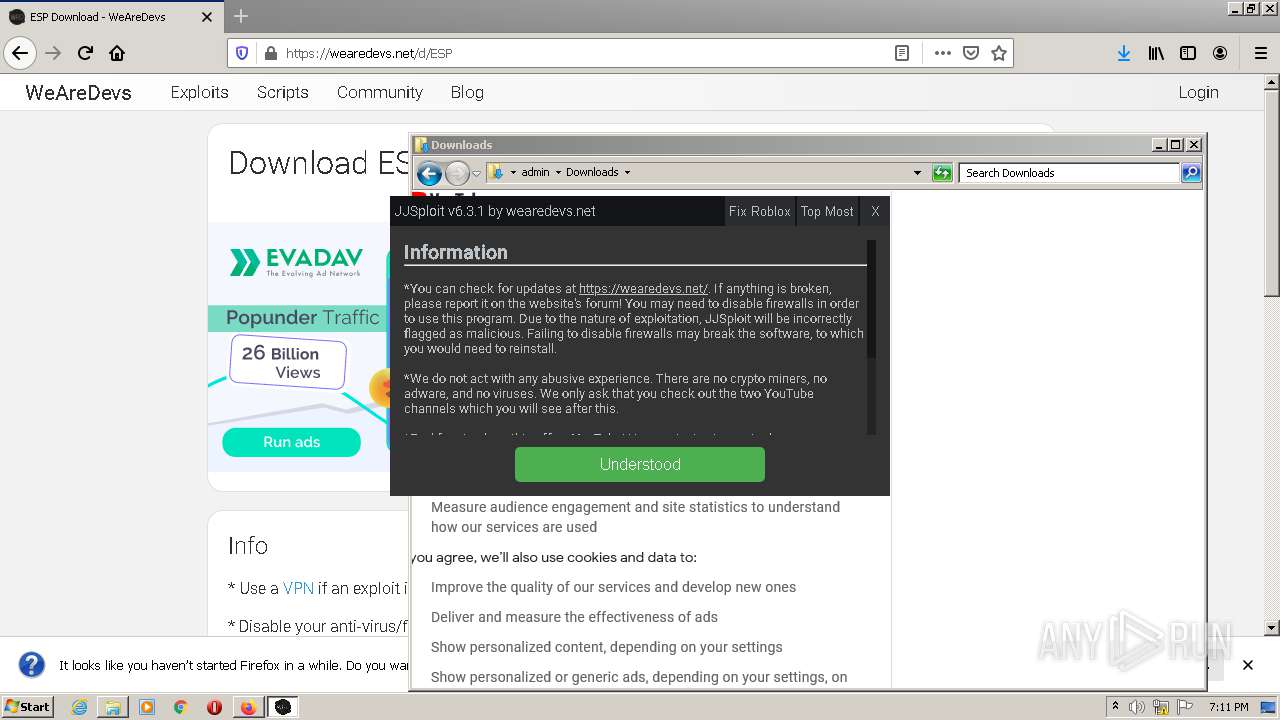
Application was dropped or rewritten from another process
- Skisploit.exe (PID: 2984)
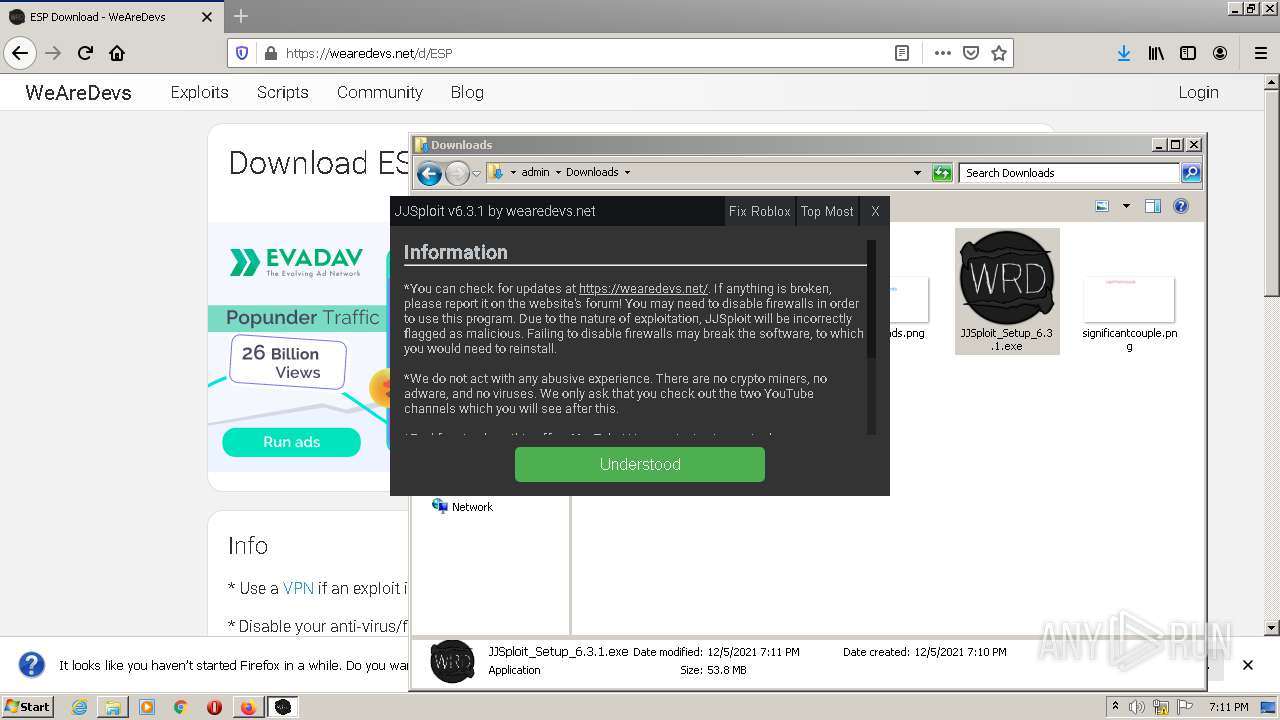
- JJSploit_Setup_6.3.1.exe (PID: 2344)
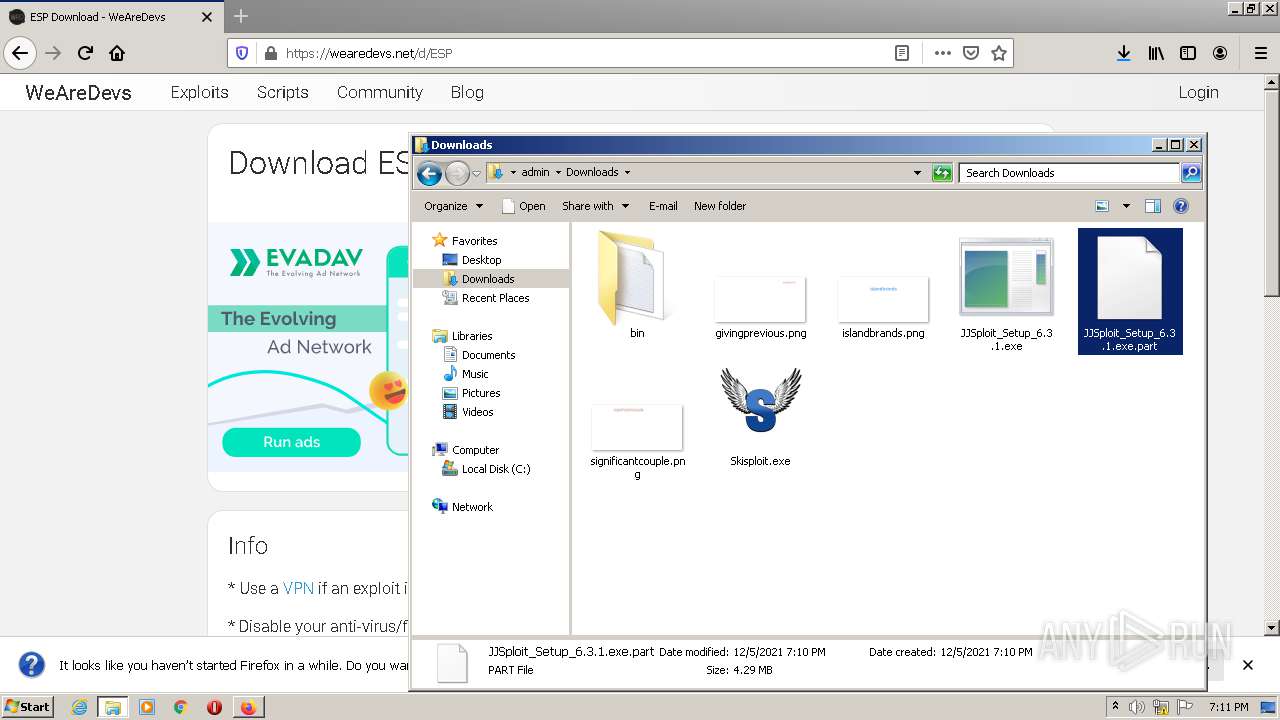
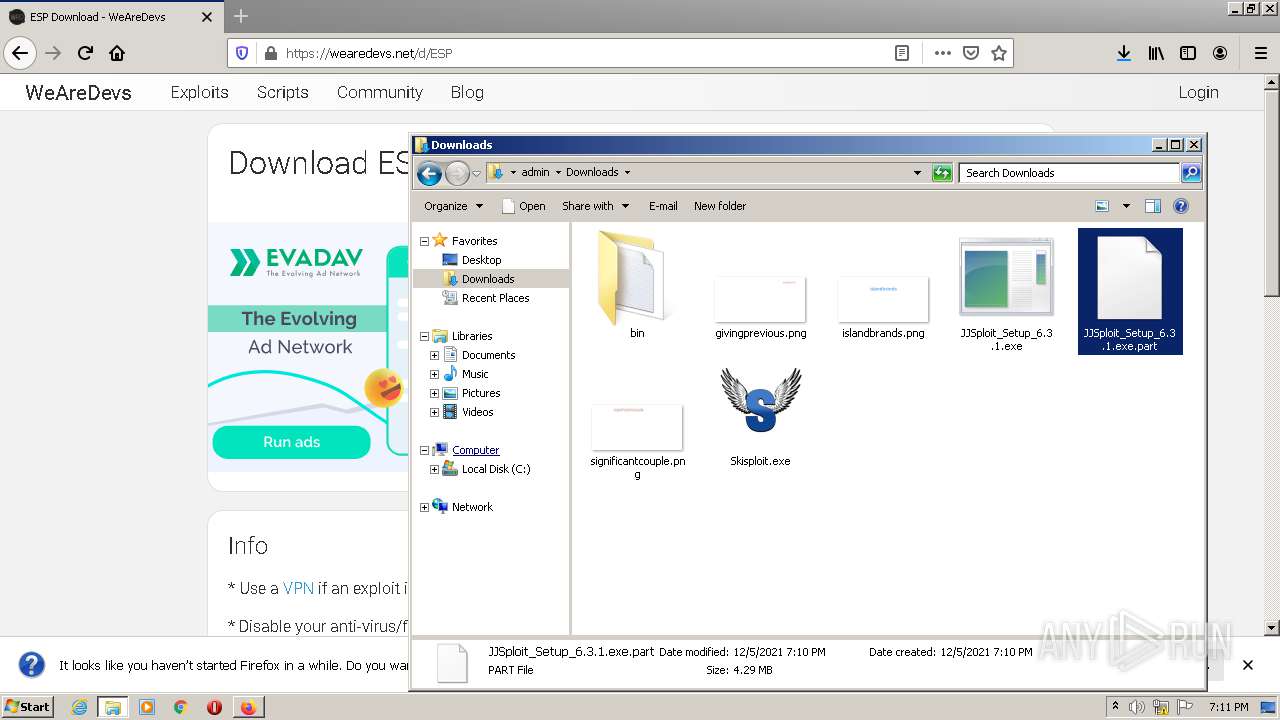
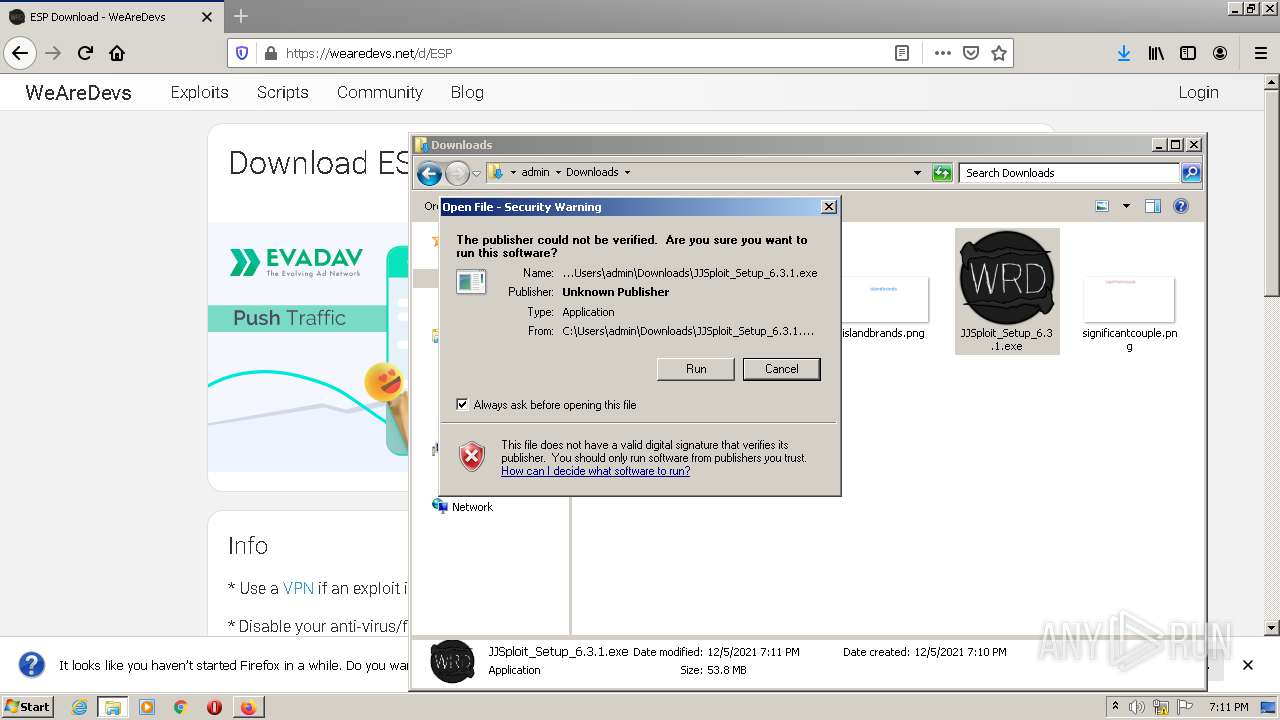
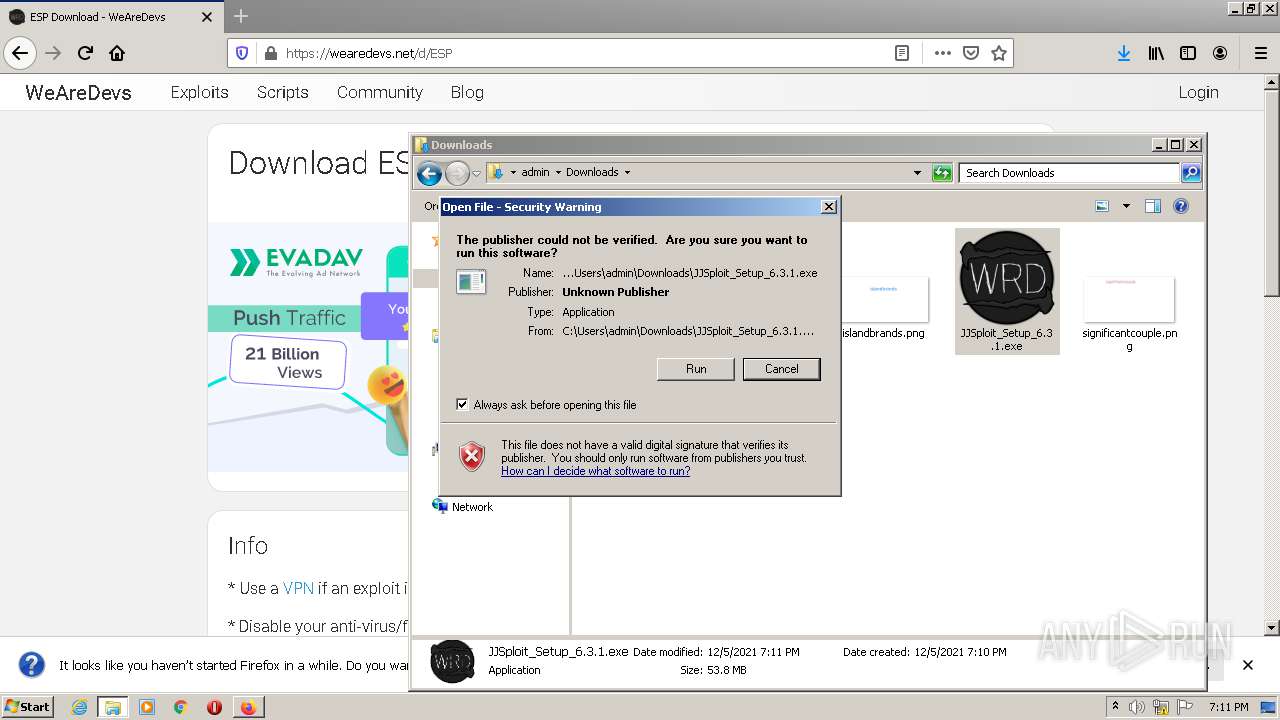
Drops executable file immediately after starts
- JJSploit_Setup_6.3.1.exe (PID: 2344)
- JJSploit.exe (PID: 2004)
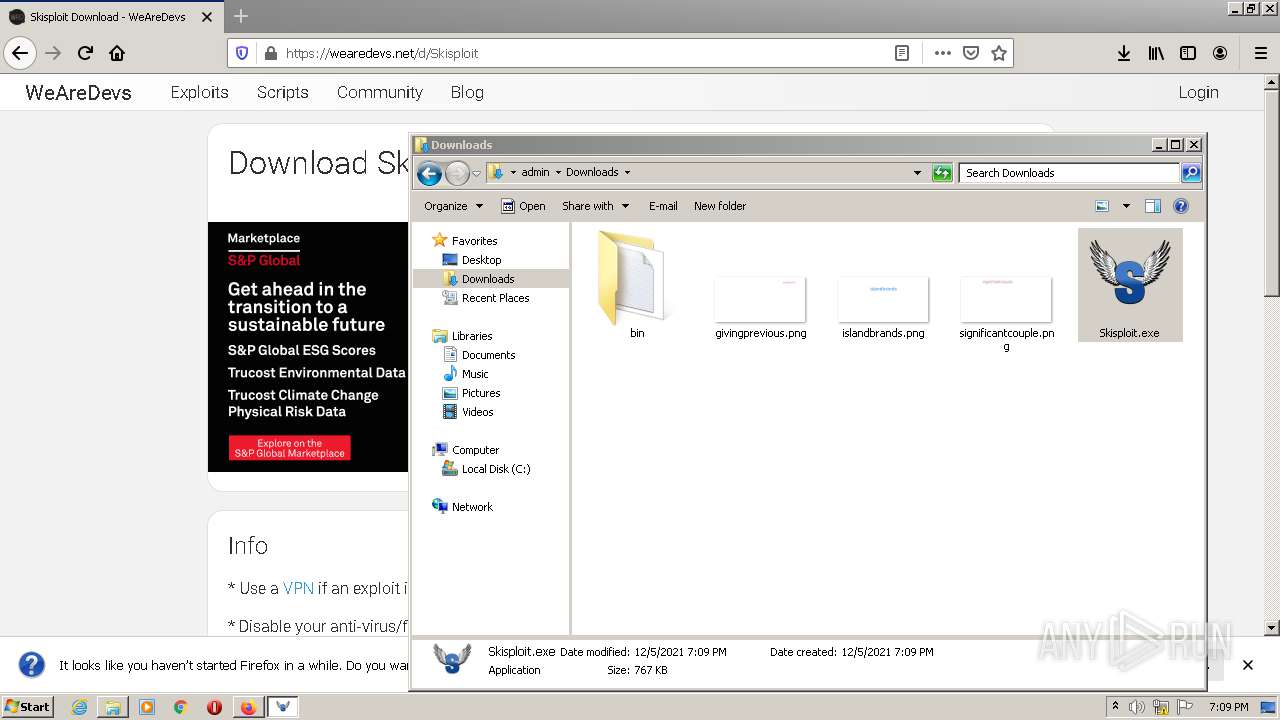
Loads dropped or rewritten executable
- JJSploit.exe (PID: 2004)
- JJSploit_Setup_6.3.1.exe (PID: 2344)
- JJSploit.exe (PID: 1052)
- JJSploit.exe (PID: 2928)
- JJSploit.exe (PID: 1696)
SUSPICIOUS
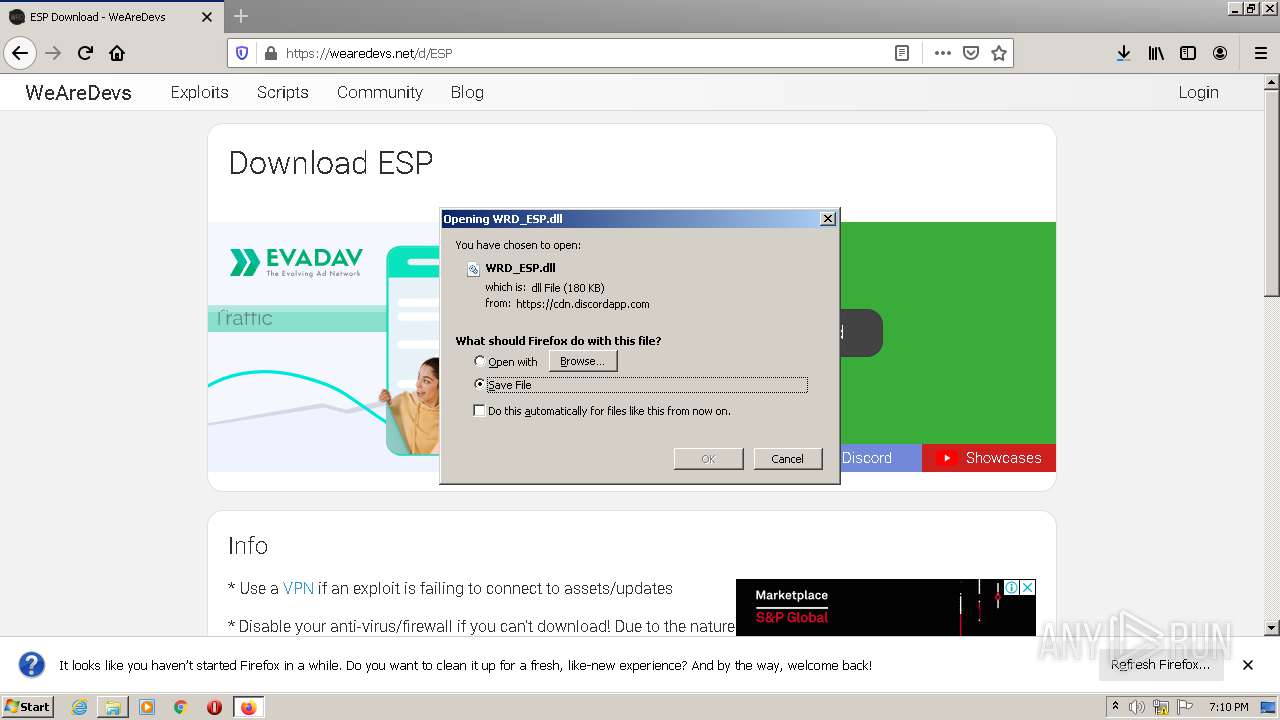
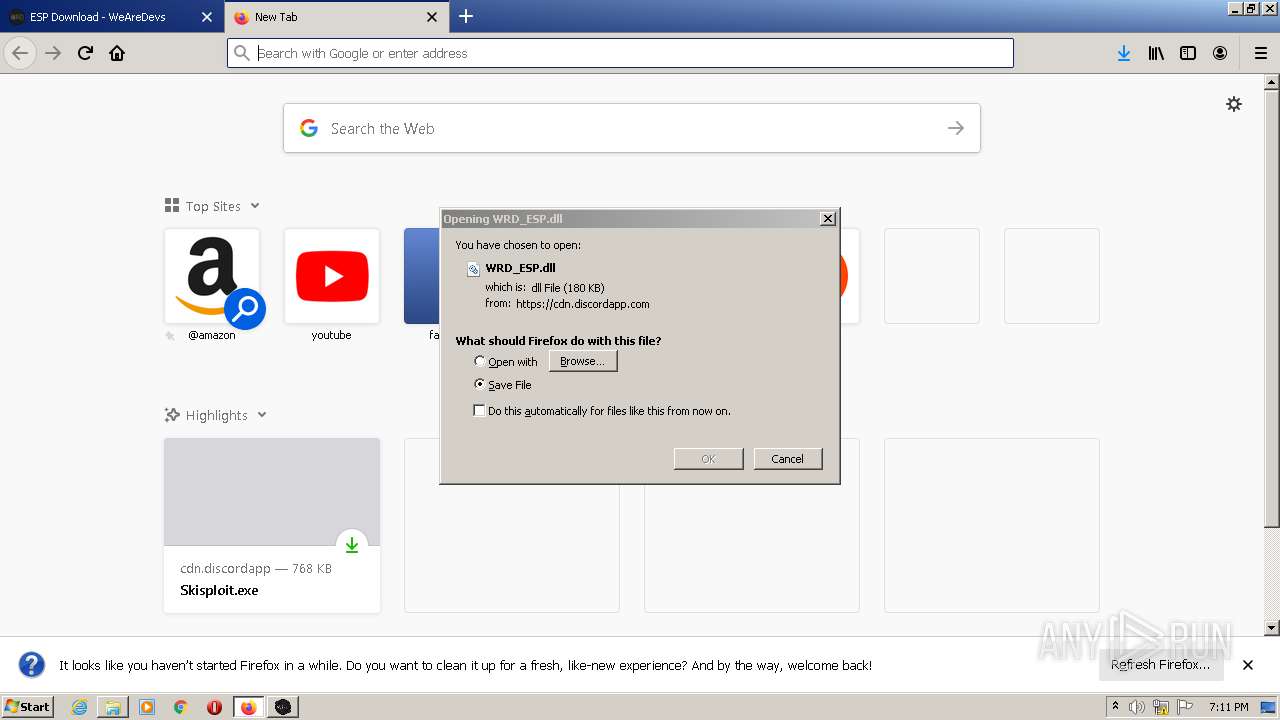
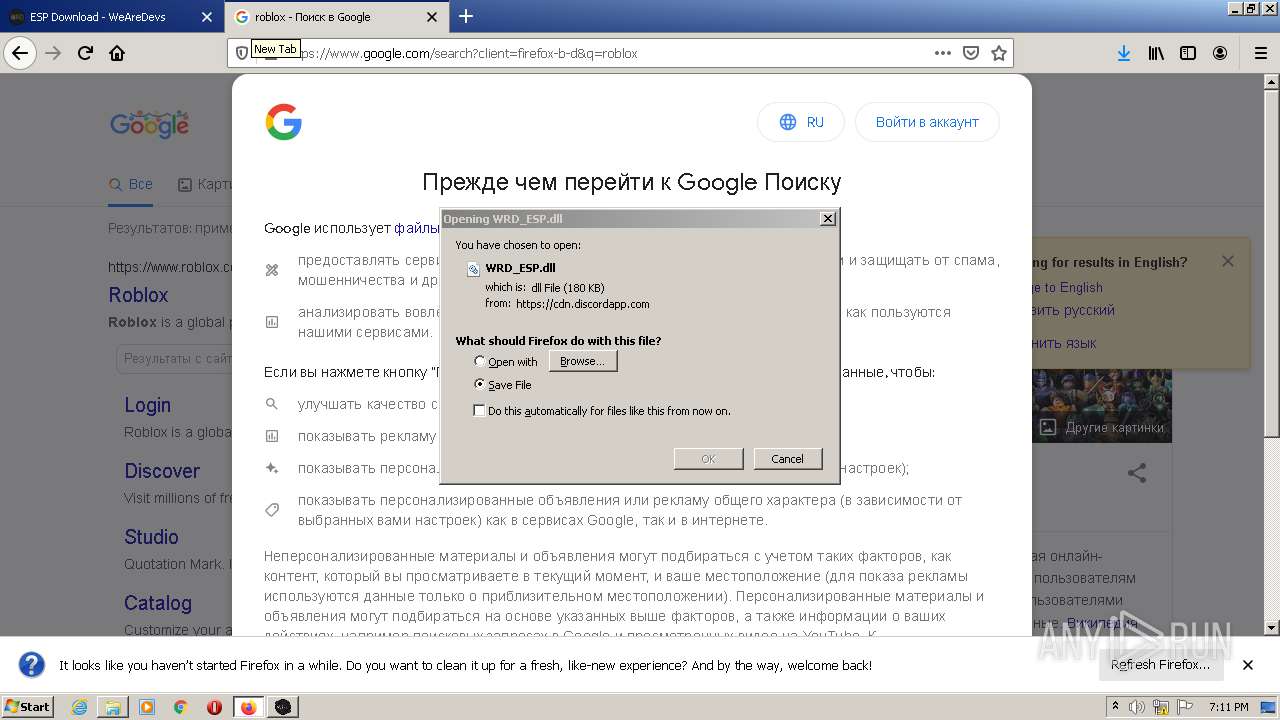
Executable content was dropped or overwritten
- firefox.exe (PID: 336)
- JJSploit_Setup_6.3.1.exe (PID: 2344)
- JJSploit.exe (PID: 2004)
Drops a file with a compile date too recent
- firefox.exe (PID: 336)
- JJSploit_Setup_6.3.1.exe (PID: 2344)
- JJSploit.exe (PID: 2004)
Checks supported languages
- Skisploit.exe (PID: 2984)
- JJSploit_Setup_6.3.1.exe (PID: 2344)
- JJSploit.exe (PID: 2004)
- JJSploit.exe (PID: 2928)
- JJSploit.exe (PID: 1052)
- JJSploit.exe (PID: 1696)
Reads the computer name
- Skisploit.exe (PID: 2984)
- JJSploit_Setup_6.3.1.exe (PID: 2344)
- JJSploit.exe (PID: 2004)
- JJSploit.exe (PID: 2928)
Drops a file that was compiled in debug mode
- firefox.exe (PID: 336)
- JJSploit_Setup_6.3.1.exe (PID: 2344)
- JJSploit.exe (PID: 2004)
Reads Environment values
- Skisploit.exe (PID: 2984)
Starts Internet Explorer
- rundll32.exe (PID: 3648)
- JJSploit.exe (PID: 2004)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 2788)
- iexplore.exe (PID: 2244)
- iexplore.exe (PID: 872)
Creates a software uninstall entry
- JJSploit_Setup_6.3.1.exe (PID: 2344)
Drops a file with too old compile date
- JJSploit_Setup_6.3.1.exe (PID: 2344)
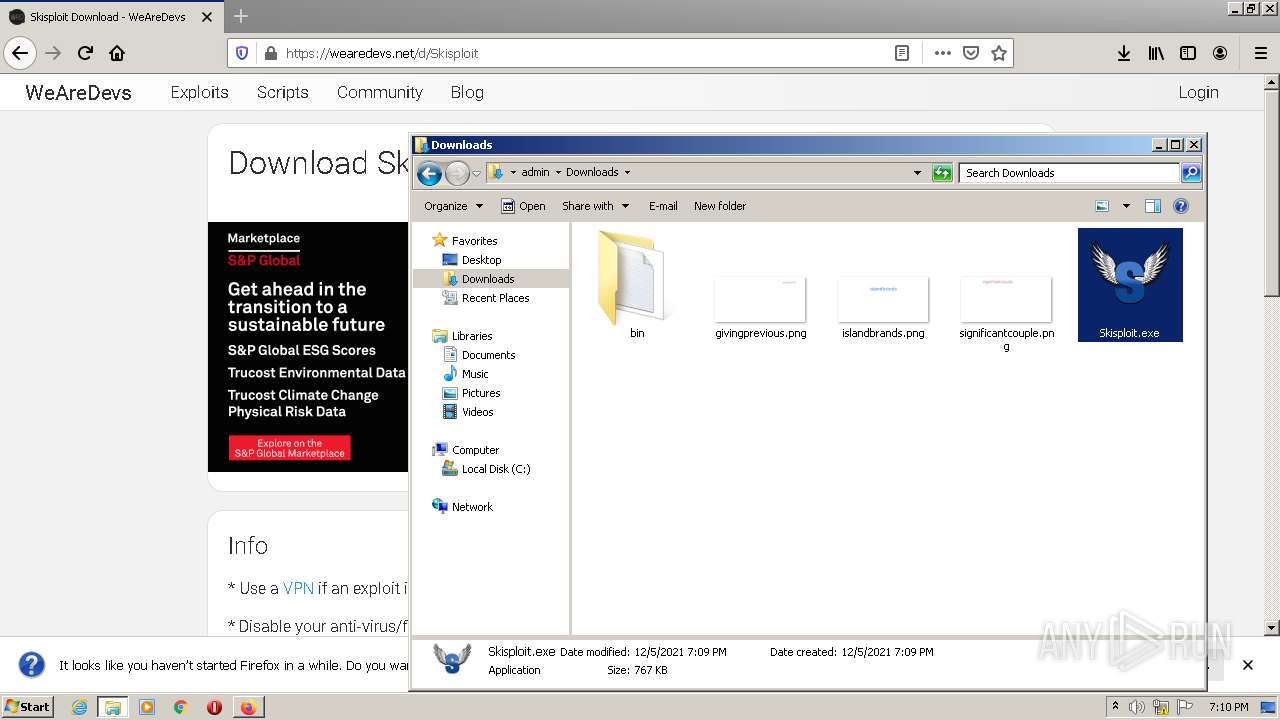
Creates files in the user directory
- JJSploit_Setup_6.3.1.exe (PID: 2344)
- JJSploit.exe (PID: 2004)
Application launched itself
- JJSploit.exe (PID: 2004)
INFO
Check for Java to be installed
- opera.exe (PID: 3408)
Checks supported languages
- opera.exe (PID: 3408)
- firefox.exe (PID: 336)
- firefox.exe (PID: 1928)
- firefox.exe (PID: 3976)
- firefox.exe (PID: 2424)
- firefox.exe (PID: 3324)
- firefox.exe (PID: 2504)
- firefox.exe (PID: 2216)
- firefox.exe (PID: 1112)
- explorer.exe (PID: 888)
- WISPTIS.EXE (PID: 1792)
- iexplore.exe (PID: 2976)
- rundll32.exe (PID: 3648)
- iexplore.exe (PID: 2788)
- iexplore.exe (PID: 3220)
- iexplore.exe (PID: 828)
- iexplore.exe (PID: 2244)
- iexplore.exe (PID: 872)
- firefox.exe (PID: 3680)
Reads the computer name
- firefox.exe (PID: 336)
- opera.exe (PID: 3408)
- firefox.exe (PID: 3976)
- firefox.exe (PID: 2424)
- firefox.exe (PID: 3324)
- firefox.exe (PID: 2216)
- firefox.exe (PID: 2504)
- explorer.exe (PID: 888)
- firefox.exe (PID: 1112)
- rundll32.exe (PID: 3648)
- WISPTIS.EXE (PID: 1792)
- iexplore.exe (PID: 2788)
- iexplore.exe (PID: 2976)
- iexplore.exe (PID: 3220)
- iexplore.exe (PID: 828)
- iexplore.exe (PID: 872)
- iexplore.exe (PID: 2244)
- firefox.exe (PID: 3680)
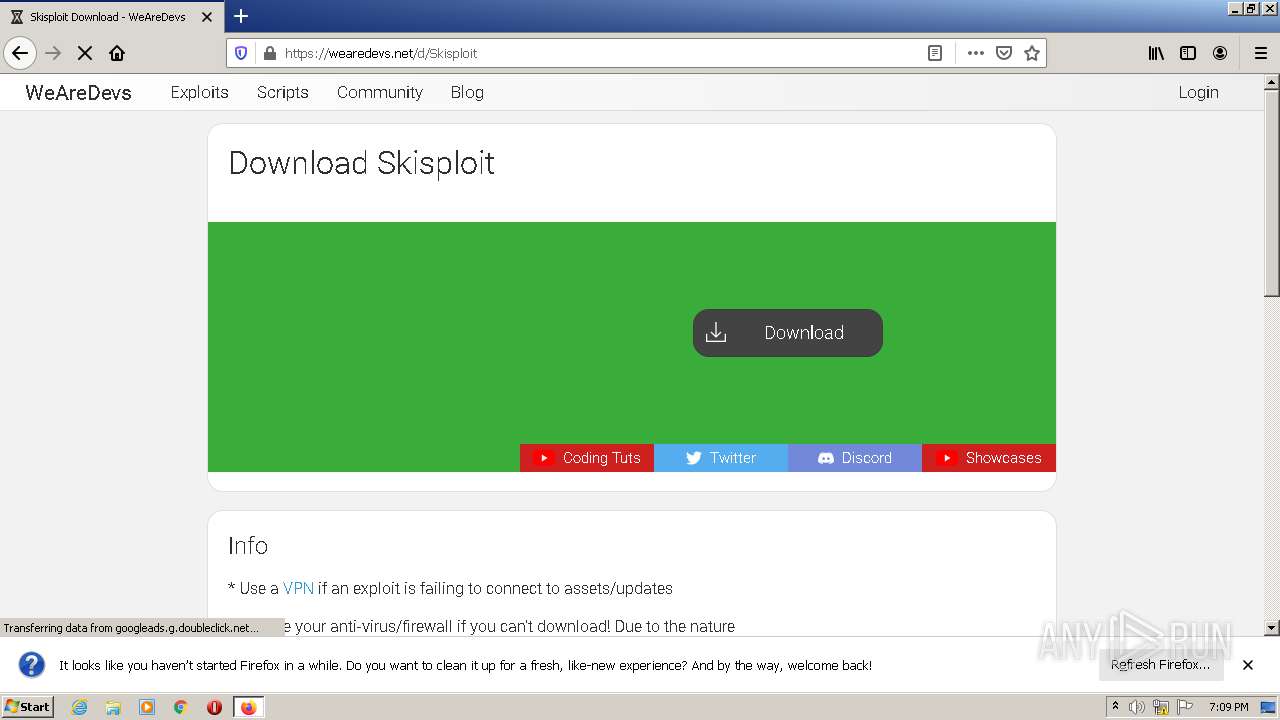
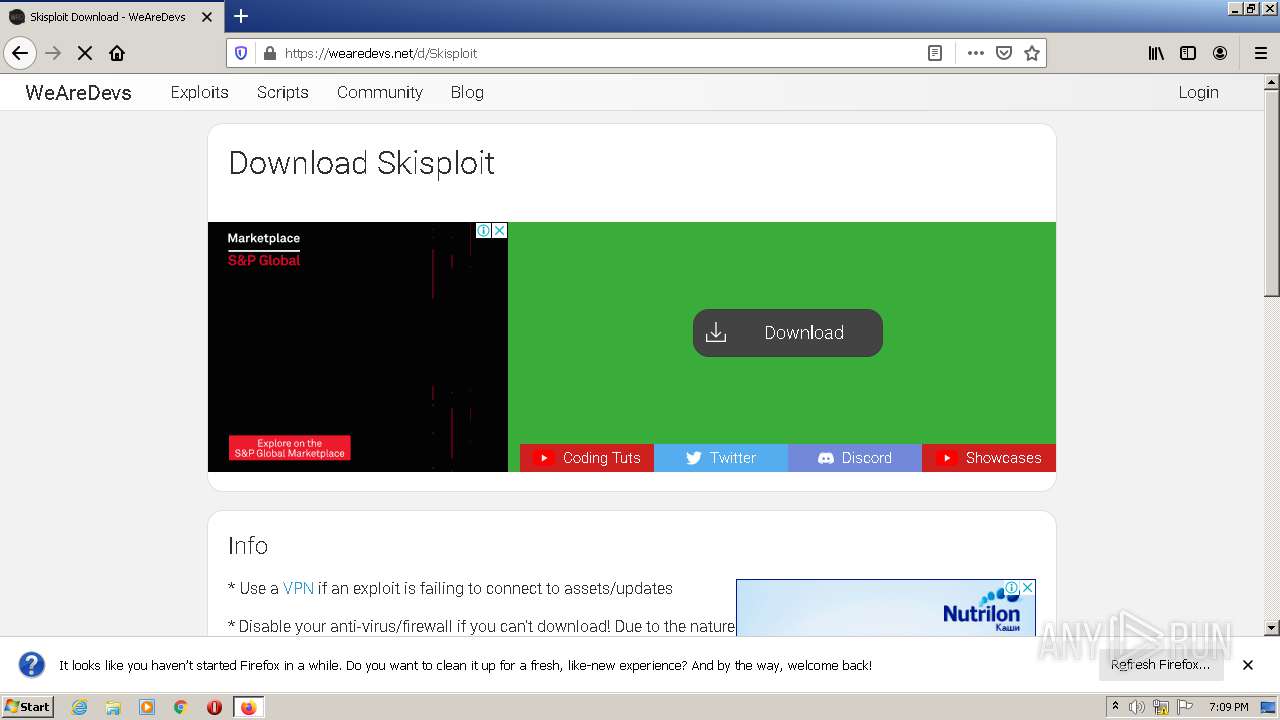
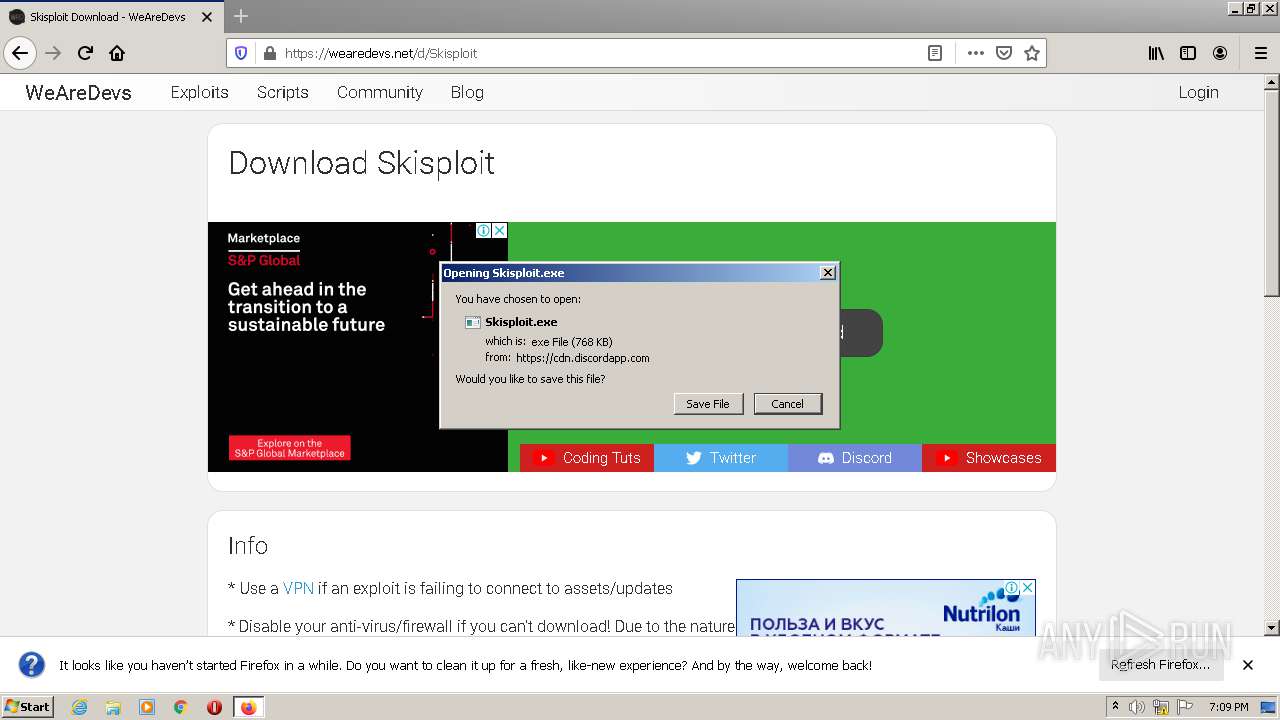
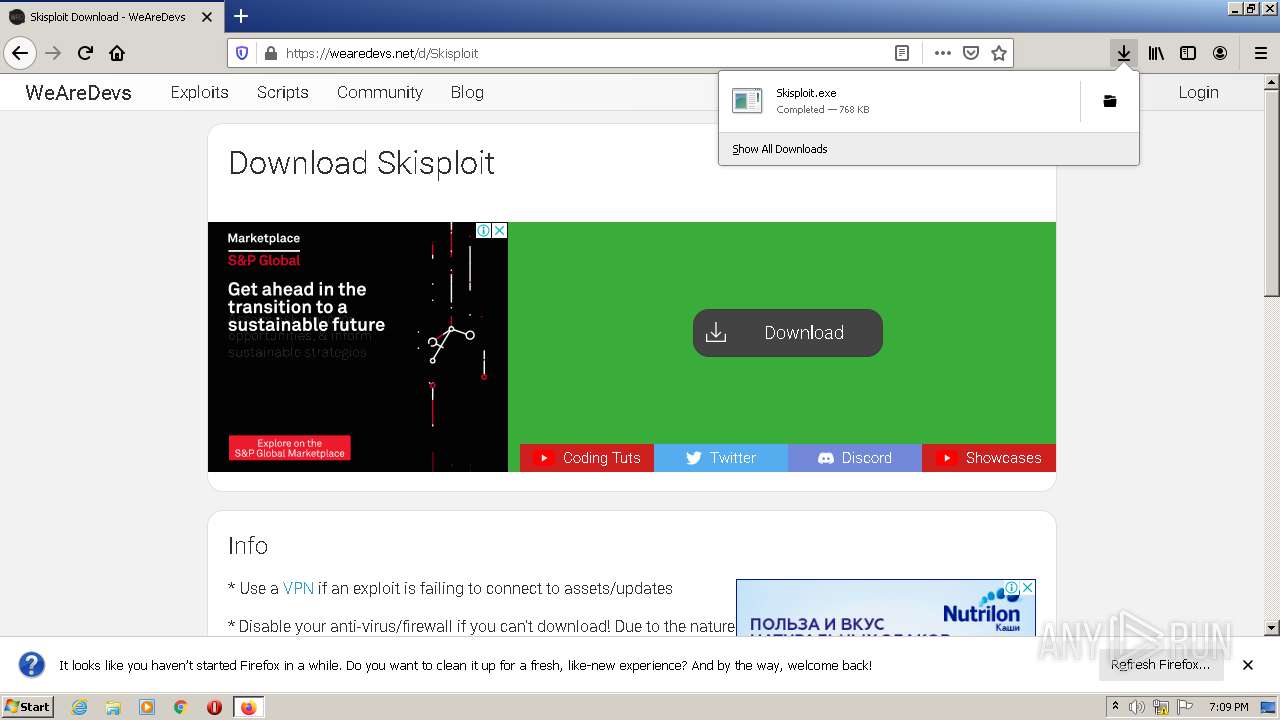
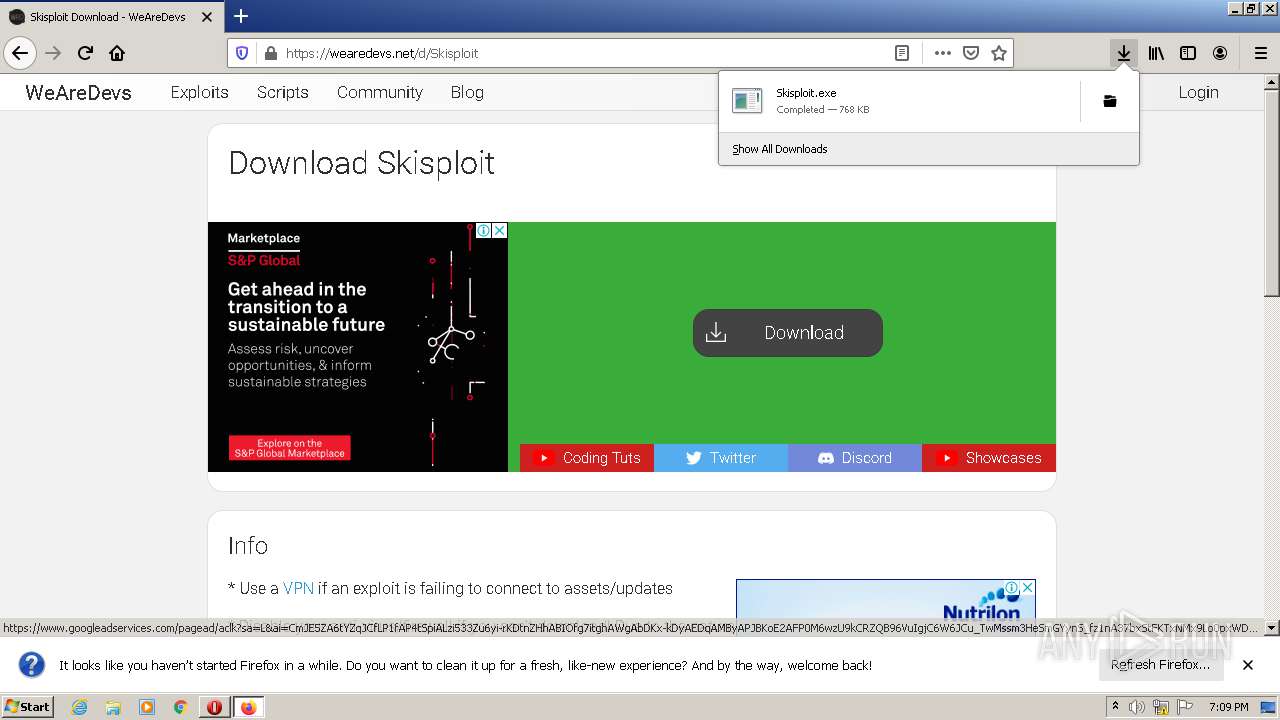
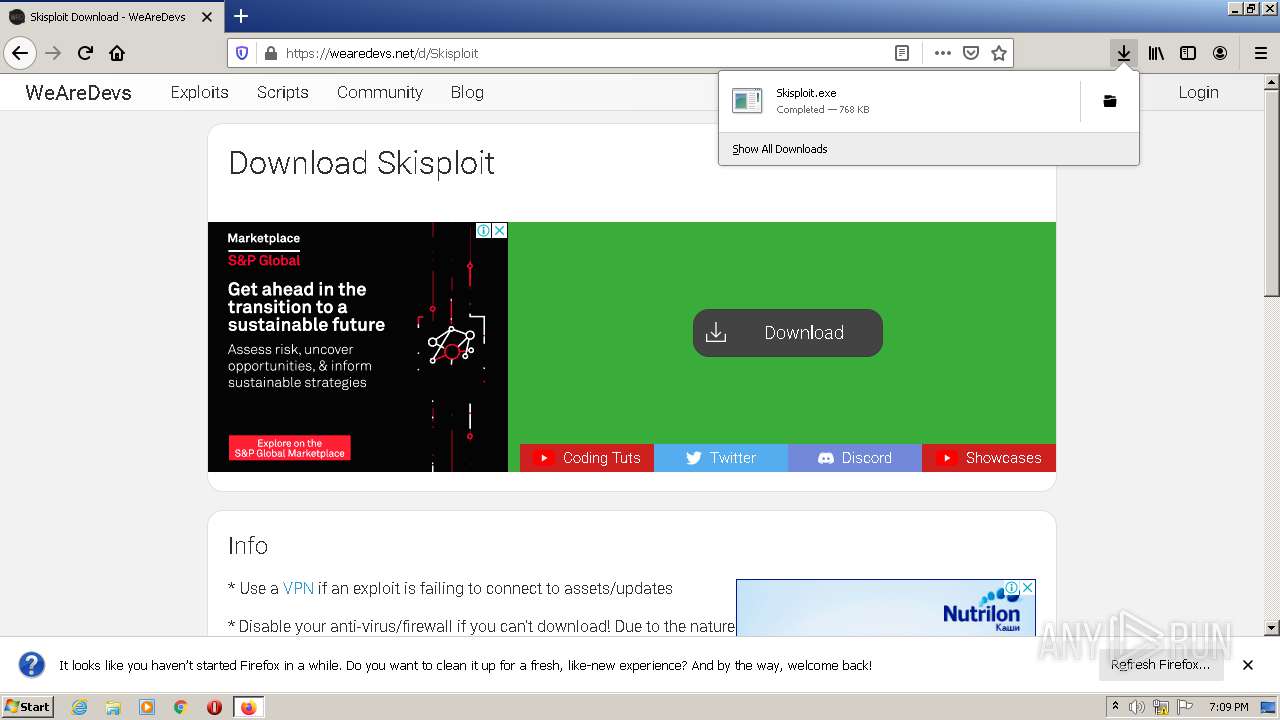
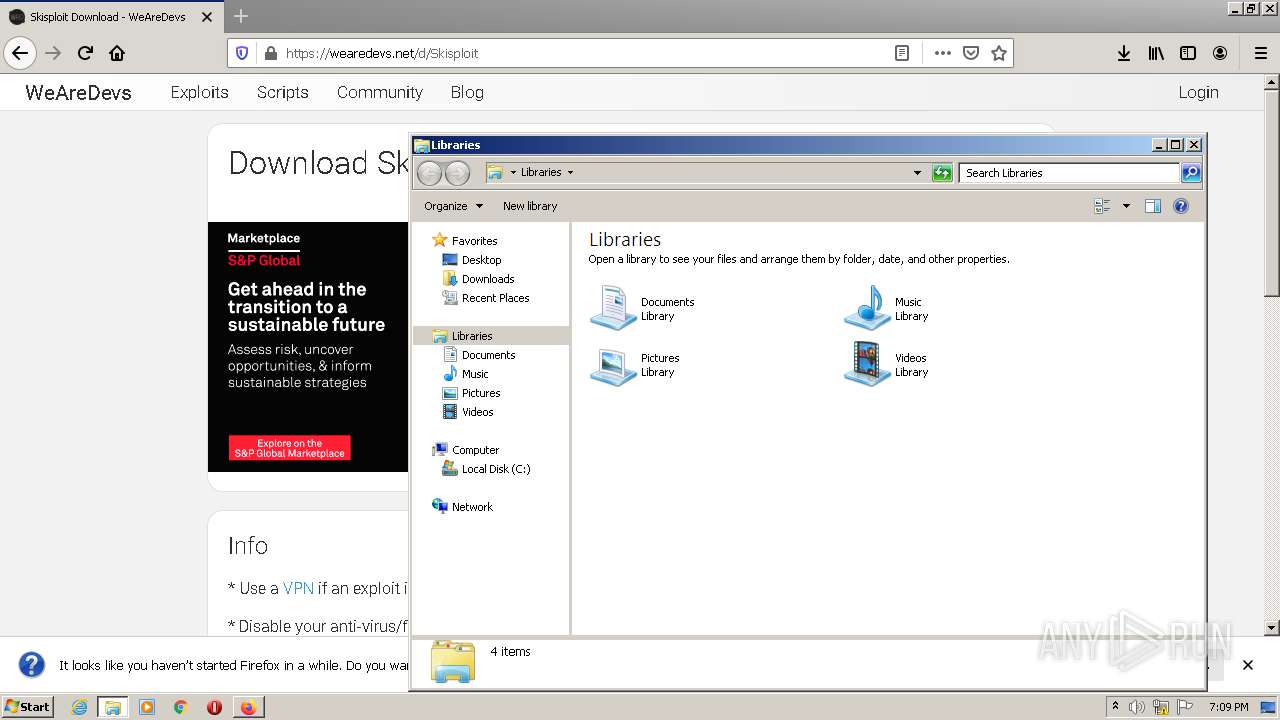
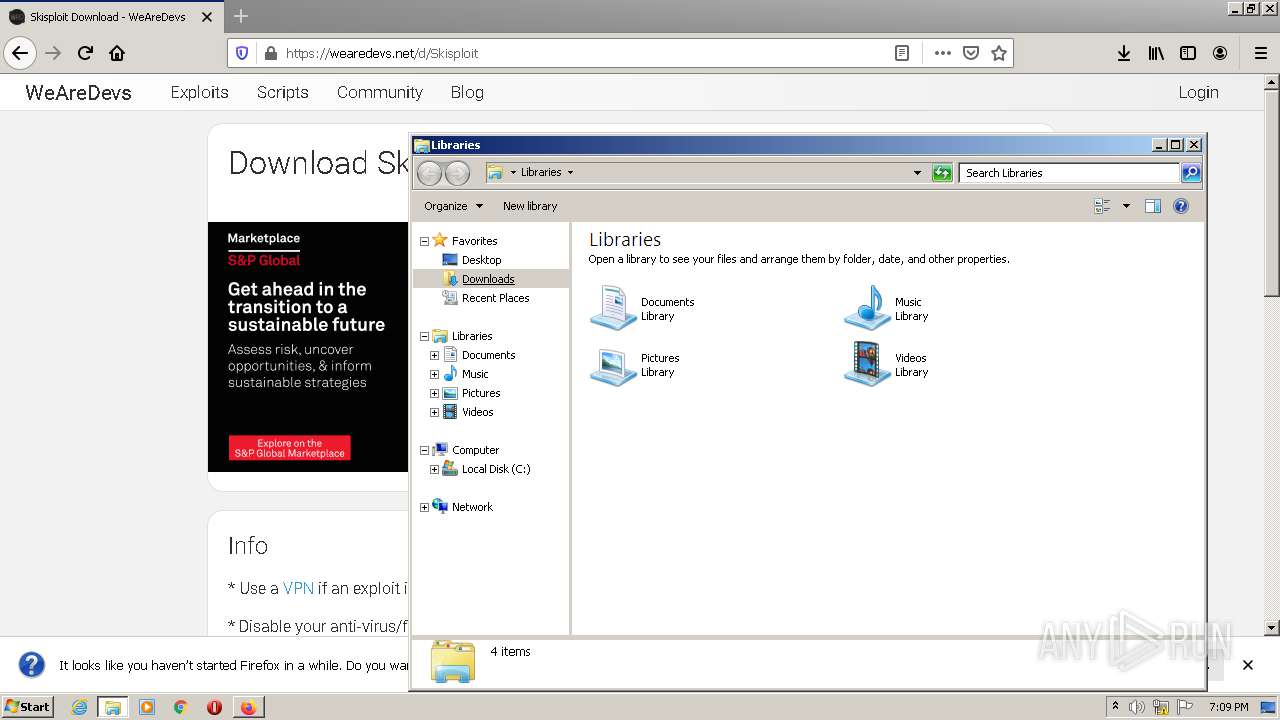
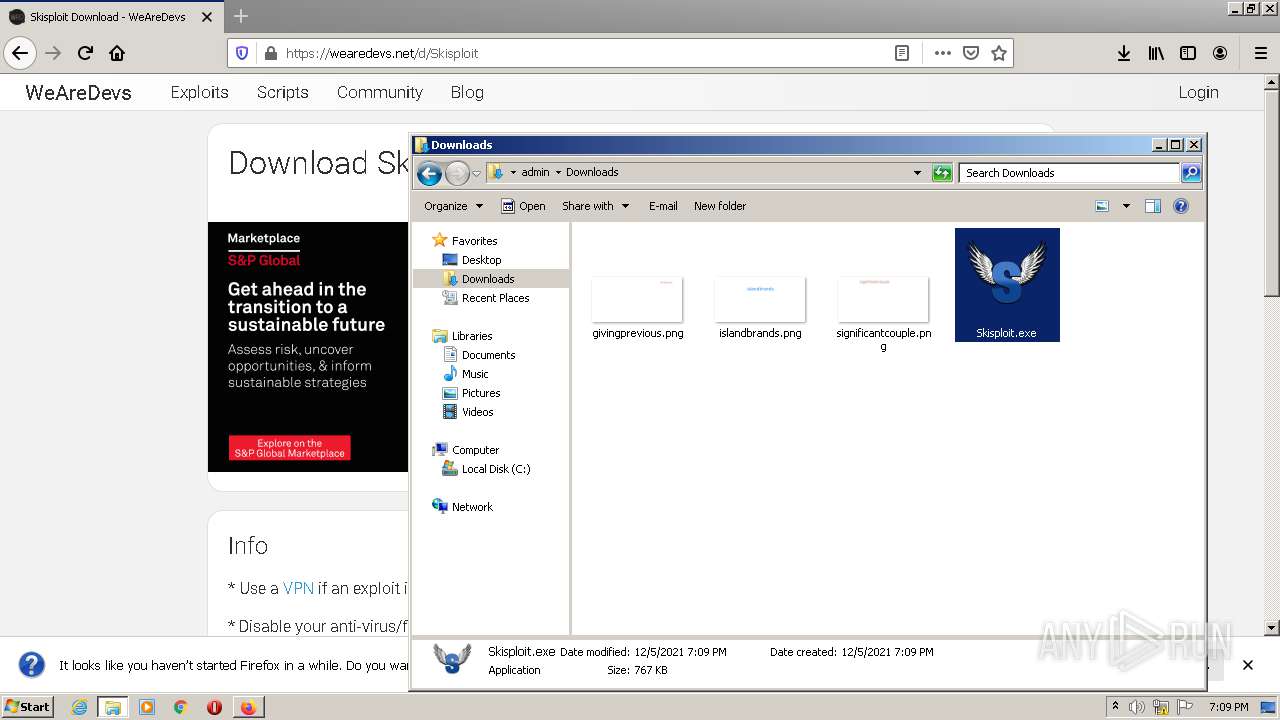
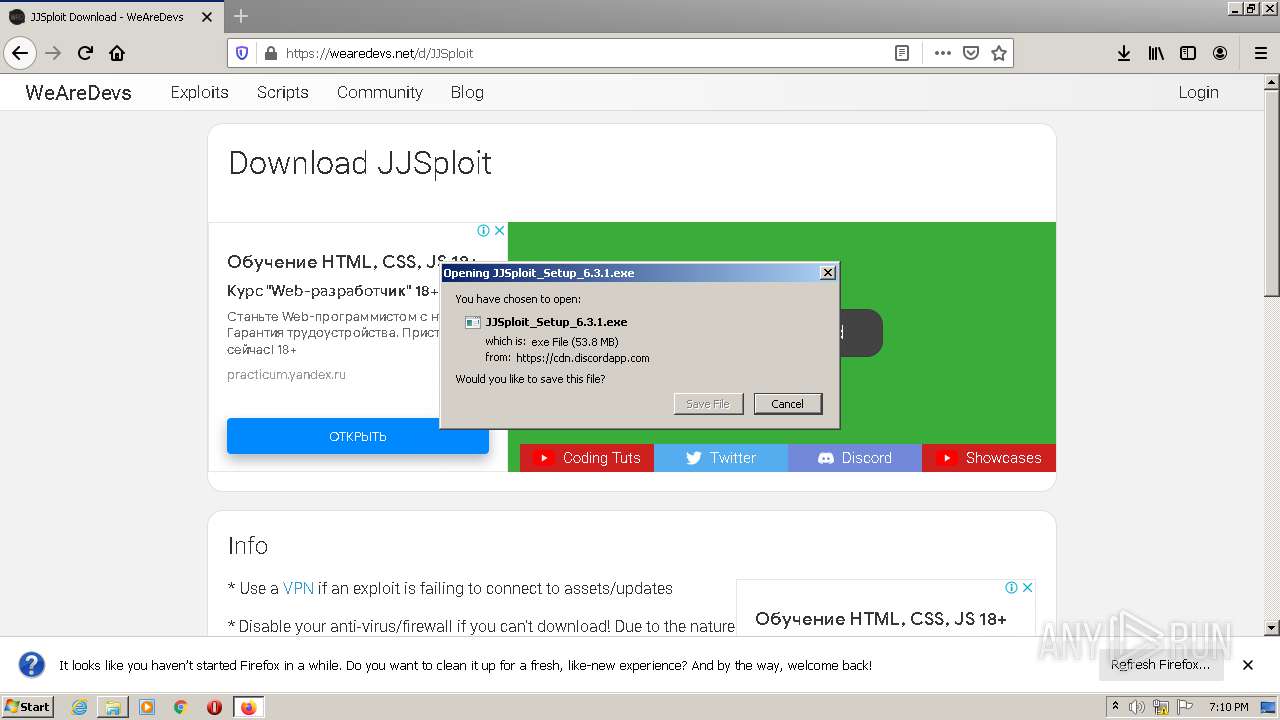
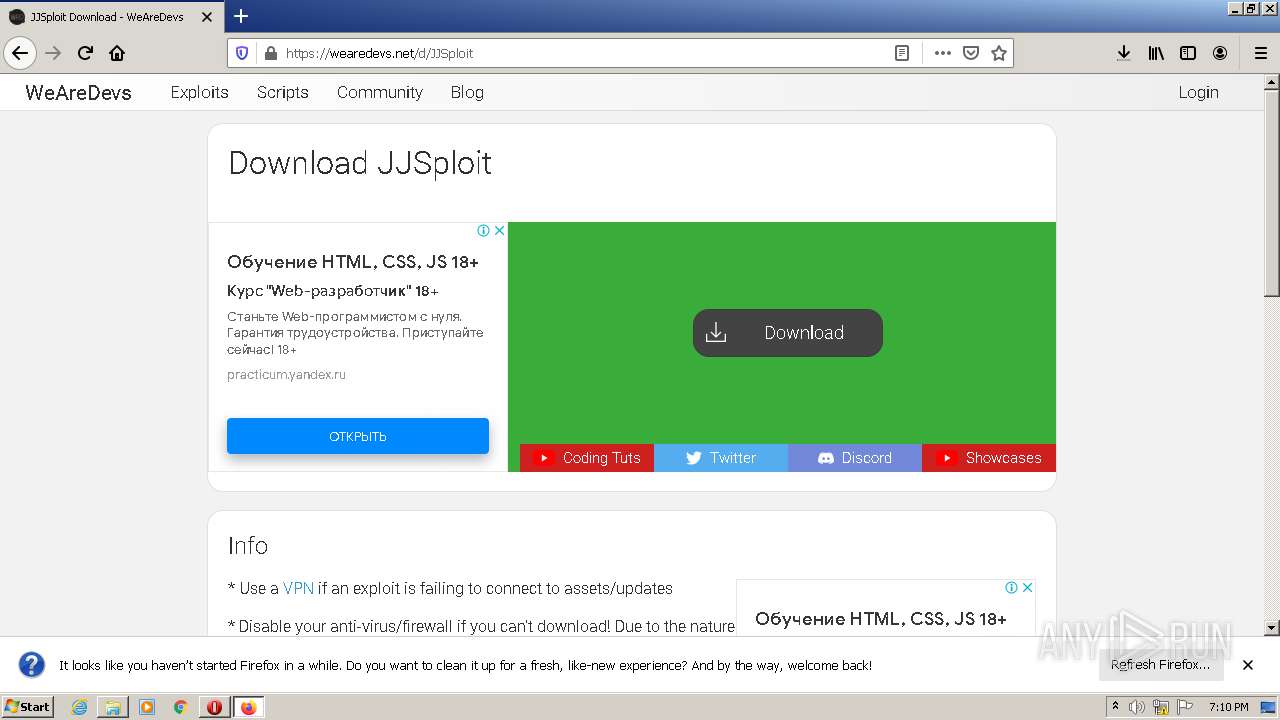
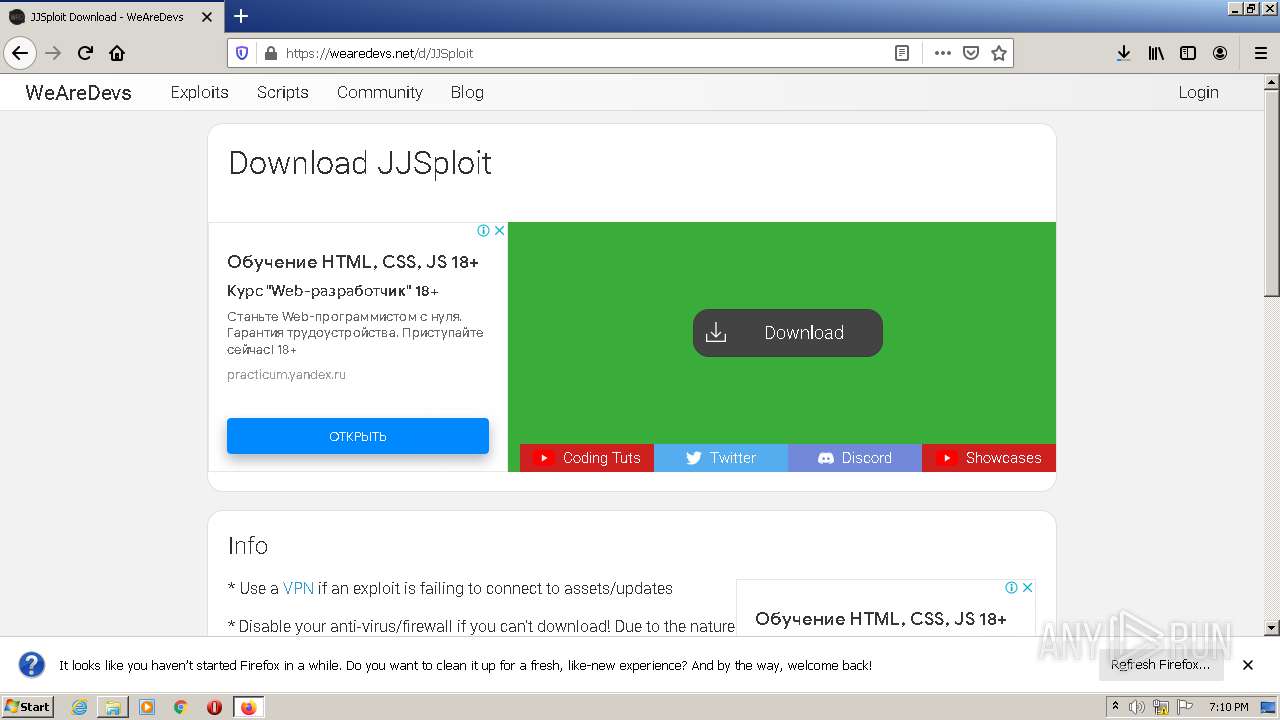
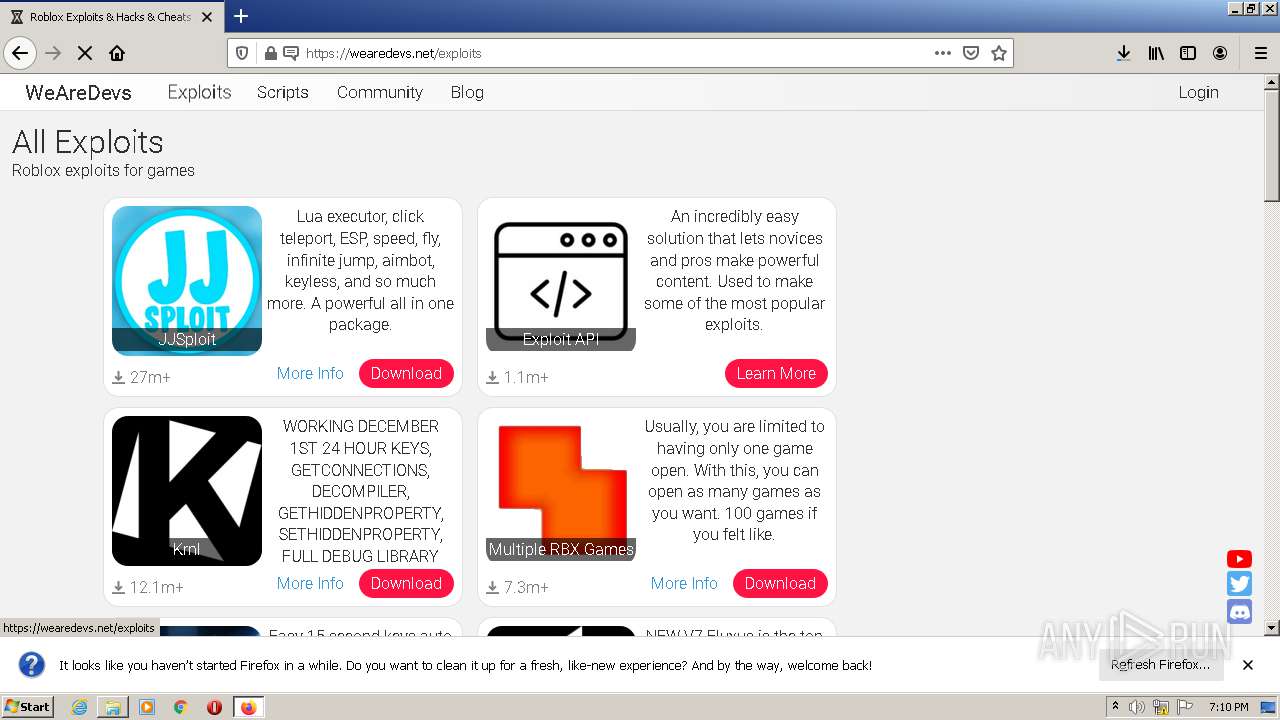
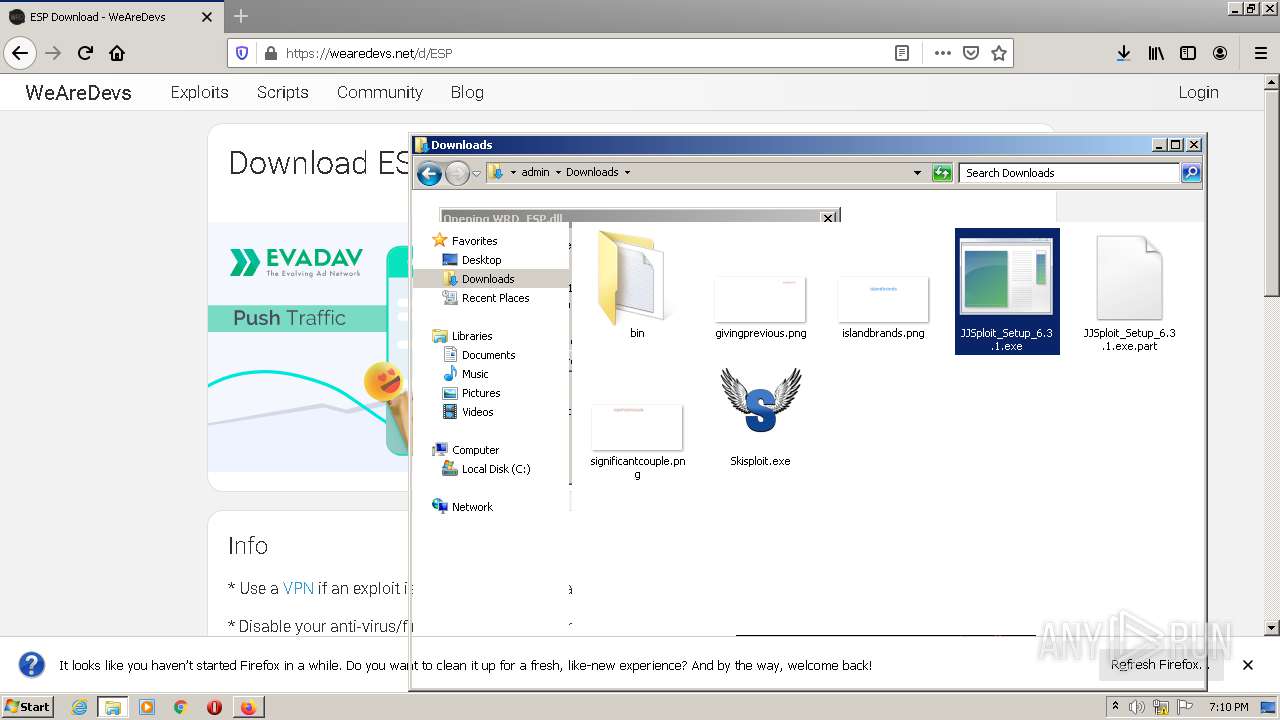
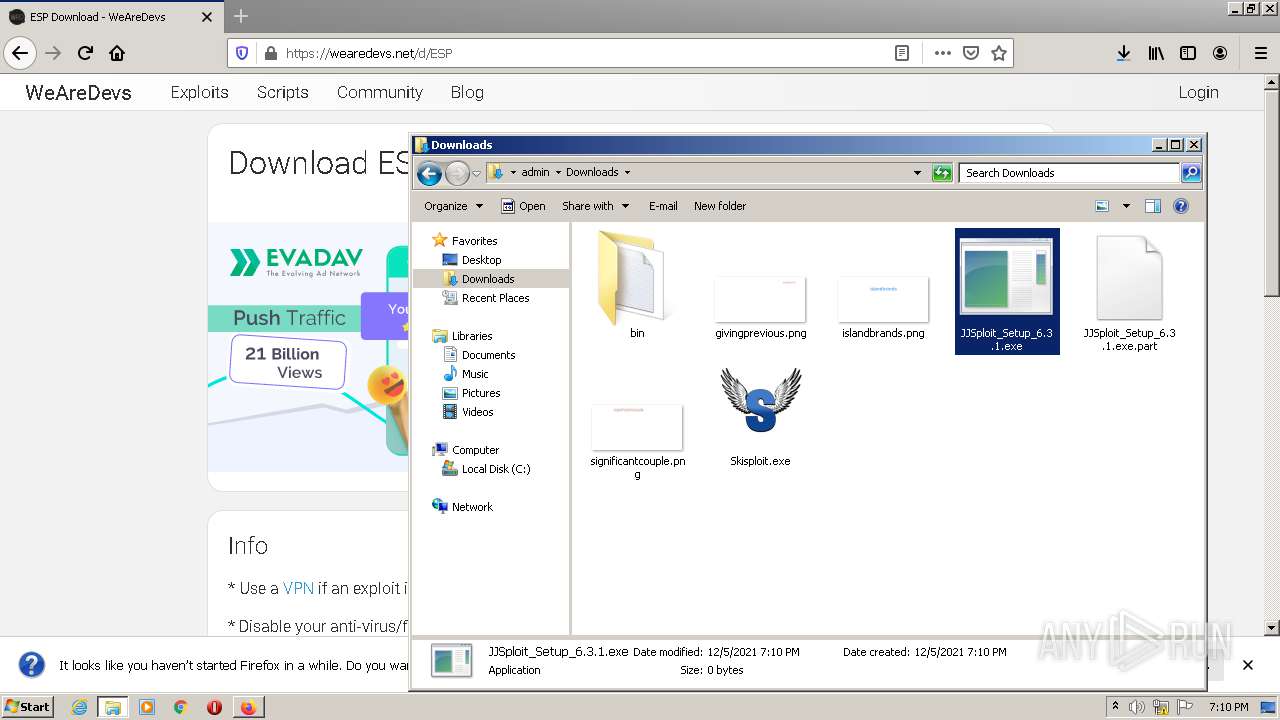
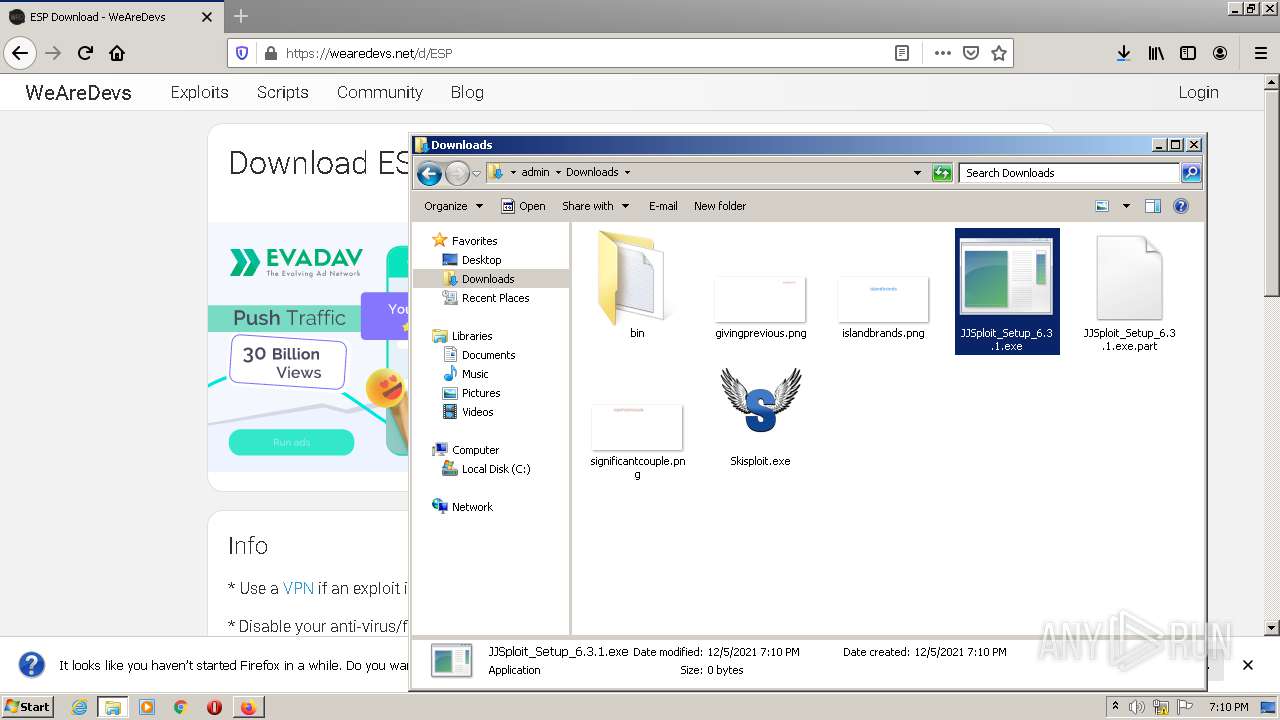
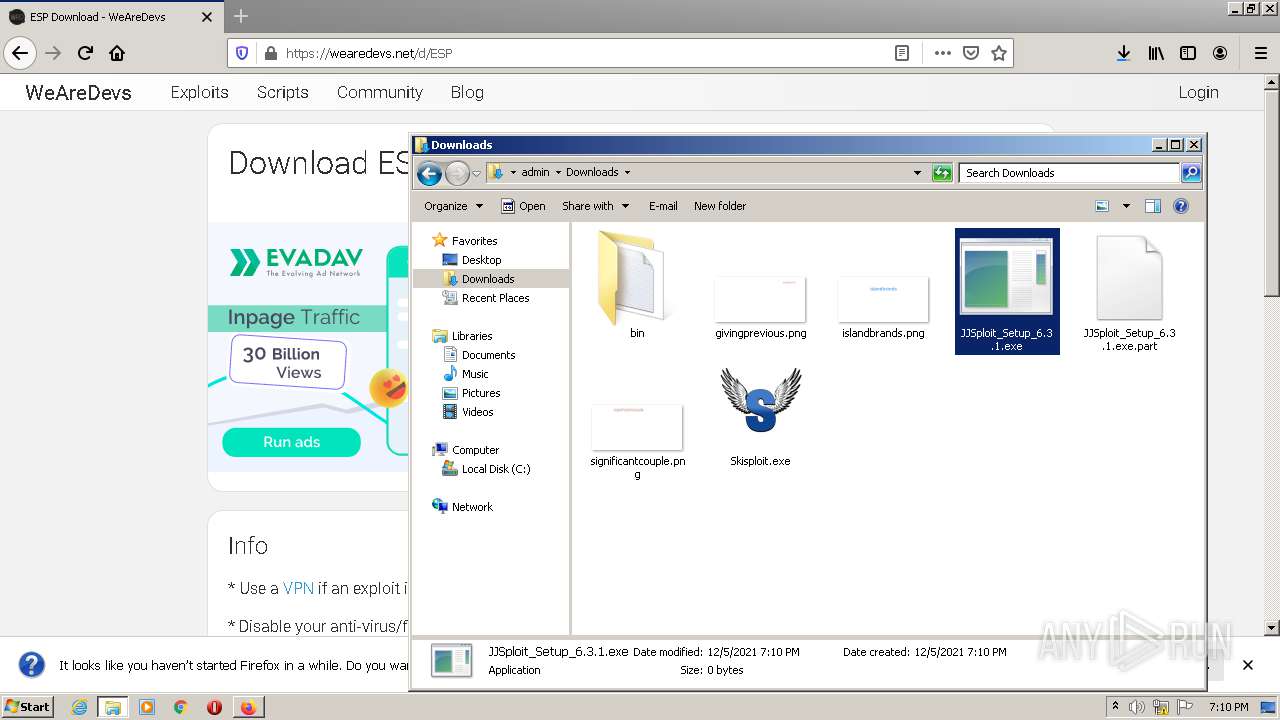
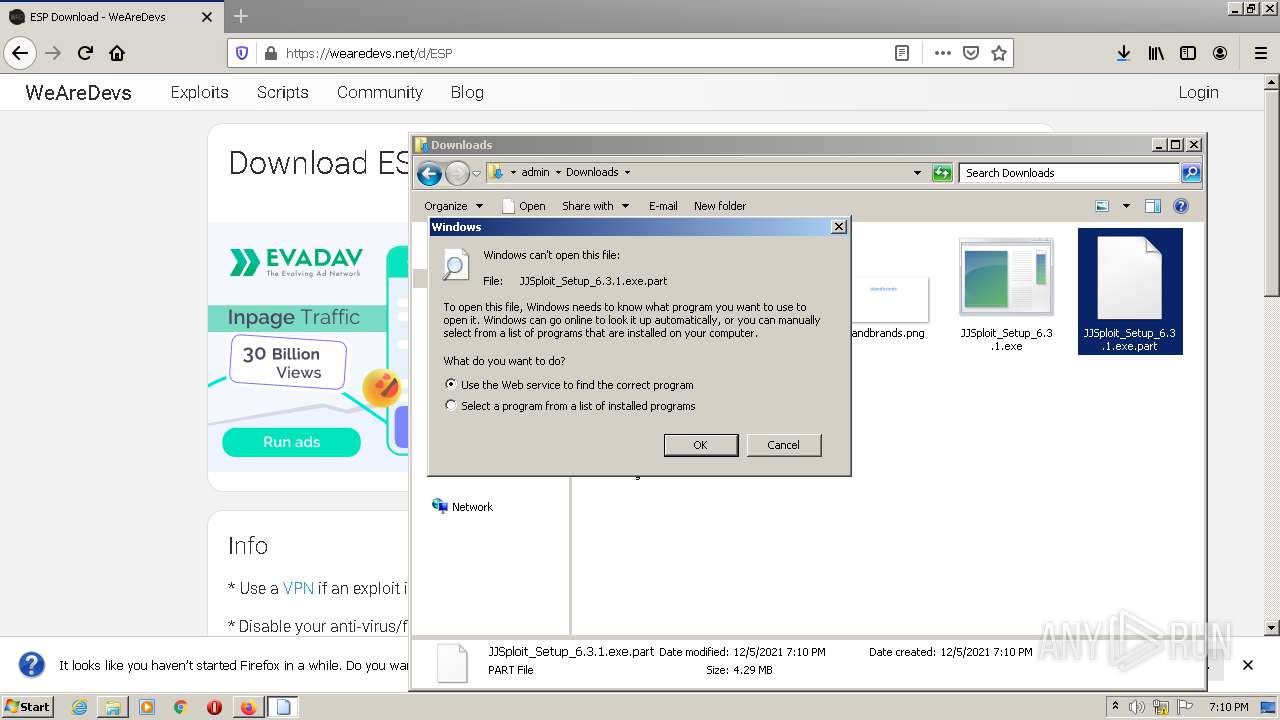
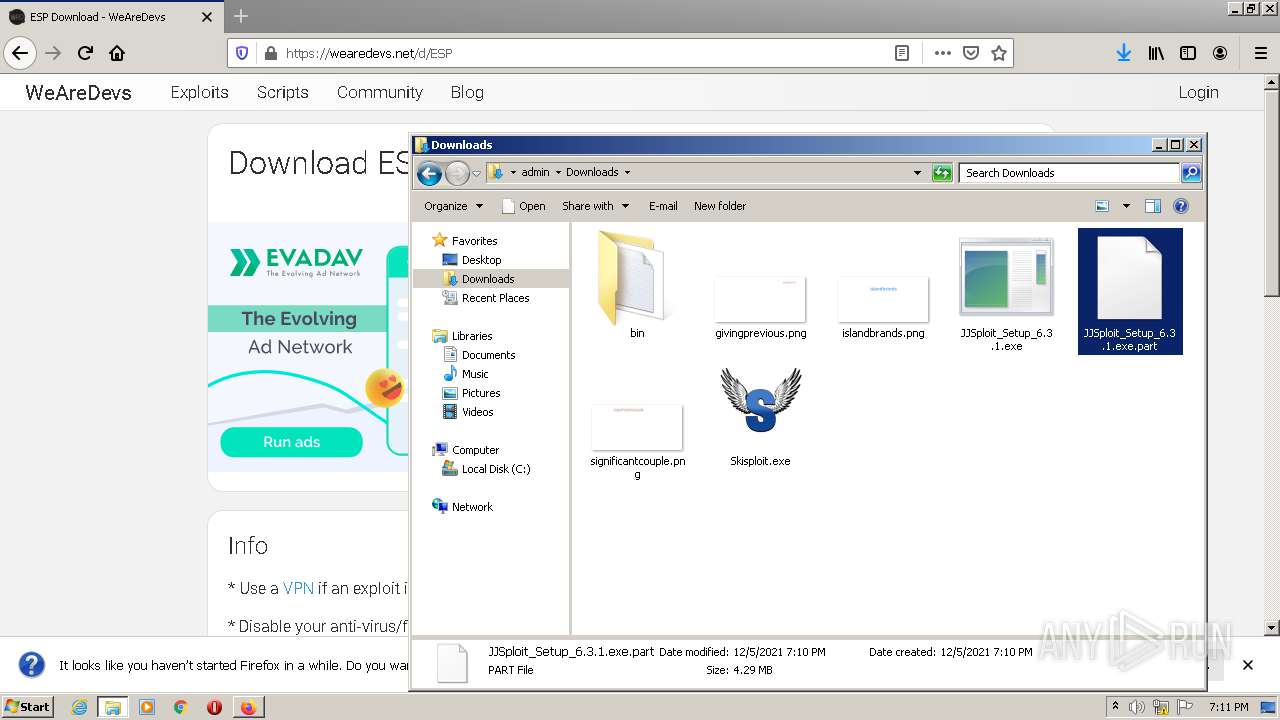
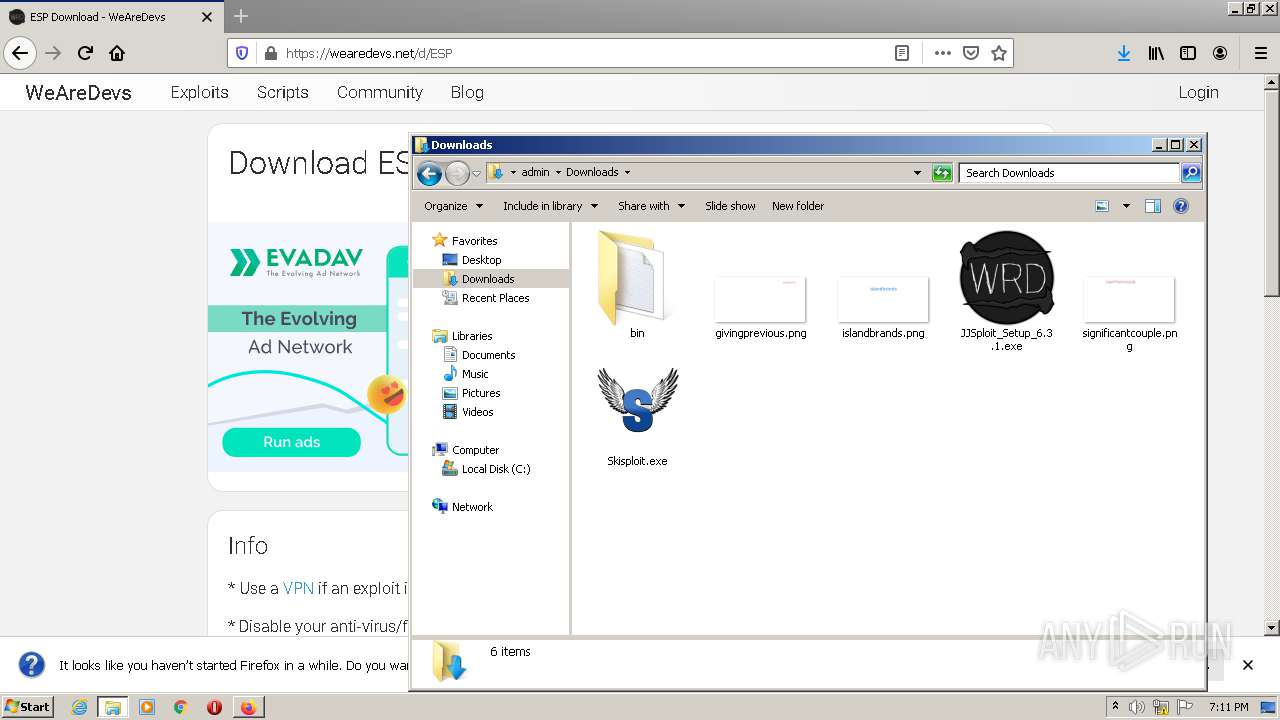
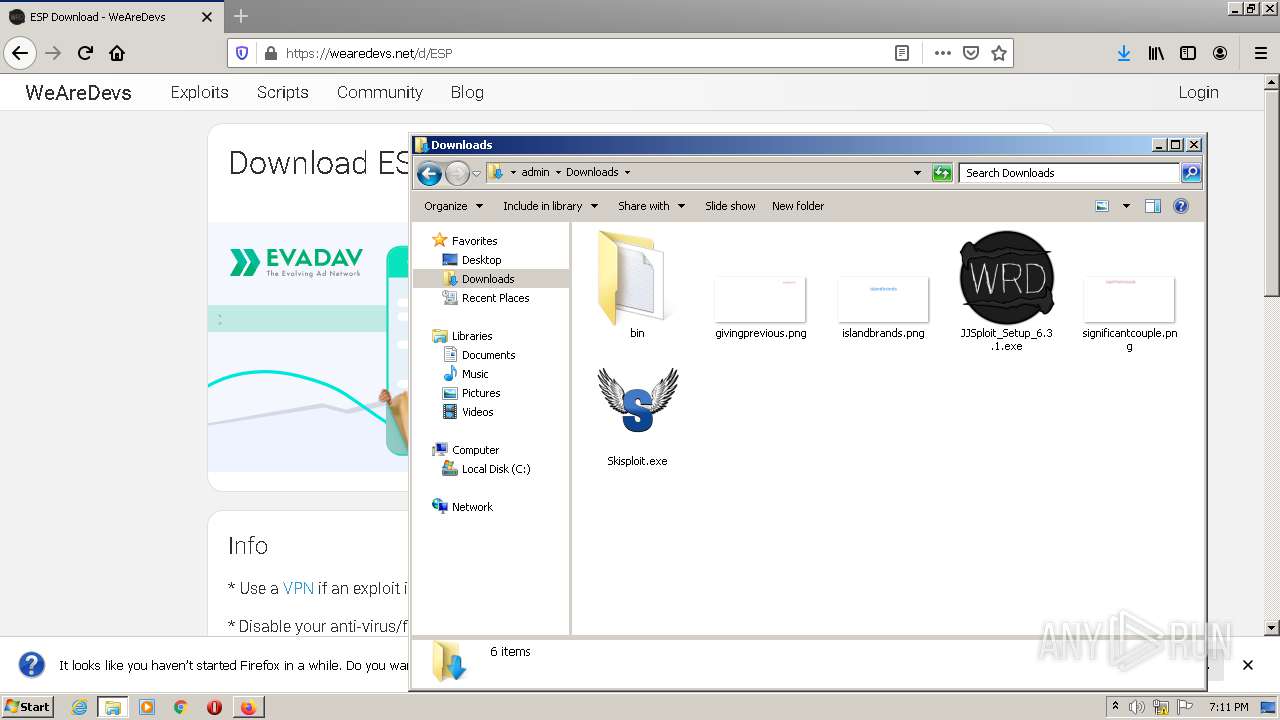
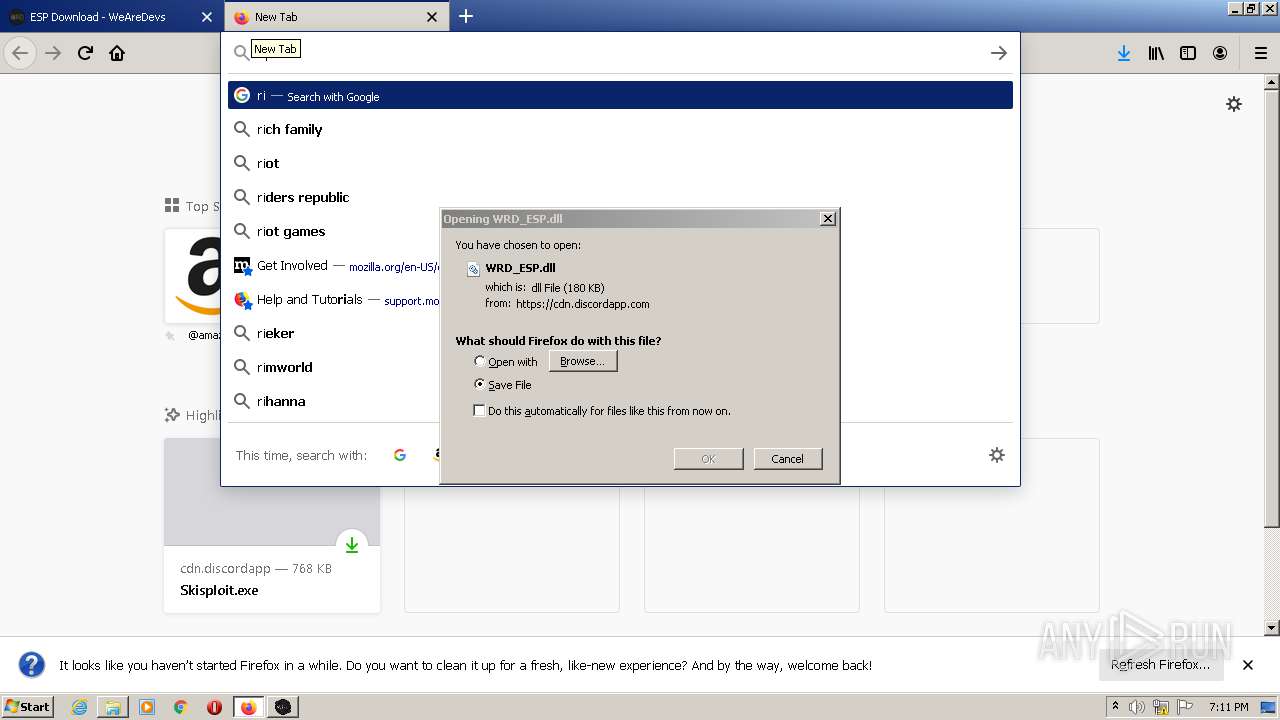
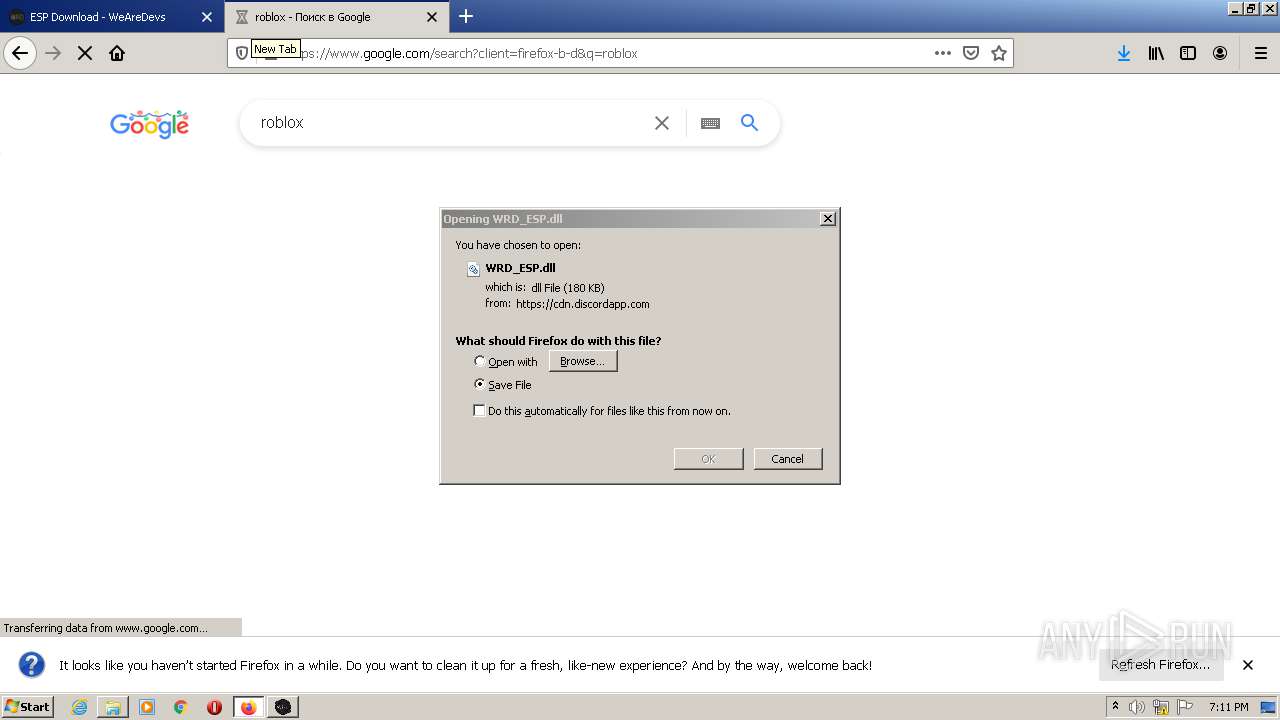
Manual execution by user
- firefox.exe (PID: 1928)
- Skisploit.exe (PID: 2984)
- explorer.exe (PID: 888)
- rundll32.exe (PID: 3648)
- JJSploit_Setup_6.3.1.exe (PID: 2344)
- JJSploit.exe (PID: 2004)
Reads the date of Windows installation
- opera.exe (PID: 3408)
- firefox.exe (PID: 336)
- iexplore.exe (PID: 2976)
- iexplore.exe (PID: 828)
- iexplore.exe (PID: 3220)
Reads CPU info
- firefox.exe (PID: 336)
Dropped object may contain Bitcoin addresses
- opera.exe (PID: 3408)
- firefox.exe (PID: 336)
Application launched itself
- firefox.exe (PID: 1928)
- firefox.exe (PID: 336)
- iexplore.exe (PID: 2976)
- iexplore.exe (PID: 3220)
- iexplore.exe (PID: 828)
Creates files in the user directory
- opera.exe (PID: 3408)
- firefox.exe (PID: 336)
- iexplore.exe (PID: 2788)
- iexplore.exe (PID: 2244)
- iexplore.exe (PID: 872)
Creates files in the program directory
- firefox.exe (PID: 336)
Checks Windows Trust Settings
- firefox.exe (PID: 336)
- iexplore.exe (PID: 2788)
- iexplore.exe (PID: 2976)
- iexplore.exe (PID: 872)
- iexplore.exe (PID: 2244)
- iexplore.exe (PID: 828)
- iexplore.exe (PID: 3220)
Reads settings of System Certificates
- Skisploit.exe (PID: 2984)
- iexplore.exe (PID: 2788)
- iexplore.exe (PID: 2976)
- JJSploit.exe (PID: 2004)
- iexplore.exe (PID: 2244)
- iexplore.exe (PID: 872)
- iexplore.exe (PID: 3220)
- iexplore.exe (PID: 828)
Reads internet explorer settings
- iexplore.exe (PID: 2788)
- iexplore.exe (PID: 872)
- iexplore.exe (PID: 2244)
Changes internet zones settings
- iexplore.exe (PID: 2976)
- iexplore.exe (PID: 828)
- iexplore.exe (PID: 3220)
Reads the hosts file
- JJSploit.exe (PID: 2004)
Changes settings of System certificates
- iexplore.exe (PID: 828)
- iexplore.exe (PID: 3220)
Adds / modifies Windows certificates
- iexplore.exe (PID: 828)
- iexplore.exe (PID: 3220)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
75
Monitored processes
26
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 336 | "C:\Program Files\Mozilla Firefox\firefox.exe" | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 83.0 Modules
| |||||||||||||||
| 828 | "C:\Program Files\Internet Explorer\iexplore.exe" https://www.youtube.com/channel/UC3YNONzSHPW12m3AT48fMHw?view_as=subscriber | C:\Program Files\Internet Explorer\iexplore.exe | JJSploit.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 872 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3220 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 888 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1052 | "C:\Users\admin\AppData\Local\Programs\jjsploit\JJSploit.exe" --type=renderer --field-trial-handle=1180,12085032284030255845,6996483215824204932,131072 --disable-features=LayoutNG,SpareRendererForSitePerProcess --lang=en-US --app-path="C:\Users\admin\AppData\Local\Programs\jjsploit\resources\app.asar" --no-sandbox --no-zygote --preload="C:\Users\admin\AppData\Local\Programs\jjsploit\resources\app.asar\build\preload.js" --background-color=#fff --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2931602694947216388 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1588 /prefetch:1 | C:\Users\admin\AppData\Local\Programs\jjsploit\JJSploit.exe | — | JJSploit.exe | |||||||||||
User: admin Company: GitHub, Inc. Integrity Level: MEDIUM Description: JJSploit Exit code: 0 Version: 6.3.1 Modules
| |||||||||||||||
| 1112 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="336.34.1928517636\99265373" -childID 5 -isForBrowser -prefsHandle 2448 -prefMapHandle 3596 -prefsLen 9187 -prefMapSize 238726 -parentBuildID 20201112153044 -appdir "C:\Program Files\Mozilla Firefox\browser" - 336 "\\.\pipe\gecko-crash-server-pipe.336" 4020 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 83.0 Modules
| |||||||||||||||
| 1528 | "C:\Windows\SYSTEM32\WISPTIS.EXE" /ManualLaunch; | C:\Windows\SYSTEM32\WISPTIS.EXE | — | Skisploit.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Pen and Touch Input Component Exit code: 3221226540 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1696 | "C:\Users\admin\AppData\Local\Programs\jjsploit\JJSploit.exe" --type=gpu-process --field-trial-handle=1180,12085032284030255845,6996483215824204932,131072 --disable-features=LayoutNG,SpareRendererForSitePerProcess --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=IAAAAAAAAADgAAAgAAAAAAAAYAAAAAAACAAAAAAAAAAoAAAABAAAACAAAAAAAAAAKAAAAAAAAAAwAAAAAAAAADgAAAAAAAAAEAAAAAAAAAAAAAAABQAAABAAAAAAAAAAAAAAAAYAAAAQAAAAAAAAAAEAAAAFAAAAEAAAAAAAAAABAAAABgAAAA== --service-request-channel-token=9877068866172700683 --mojo-platform-channel-handle=2624 /prefetch:2 | C:\Users\admin\AppData\Local\Programs\jjsploit\JJSploit.exe | — | JJSploit.exe | |||||||||||
User: admin Company: GitHub, Inc. Integrity Level: MEDIUM Description: JJSploit Exit code: 0 Version: 6.3.1 Modules
| |||||||||||||||
| 1792 | "C:\Windows\SYSTEM32\WISPTIS.EXE" /ManualLaunch; | C:\Windows\SYSTEM32\WISPTIS.EXE | Skisploit.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Pen and Touch Input Component Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1928 | "C:\Program Files\Mozilla Firefox\firefox.exe" | C:\Program Files\Mozilla Firefox\firefox.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 83.0 Modules
| |||||||||||||||
Total events
69 703
Read events
68 998
Write events
685
Delete events
20
Modification events
| (PID) Process: | (3408) opera.exe | Key: | HKEY_CURRENT_USER\Software\Opera Software |
| Operation: | write | Name: | Last CommandLine v2 |
Value: C:\Program Files\Opera\opera.exe "https://web.roblox.com/home" | |||
| (PID) Process: | (3408) opera.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1928) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Launcher |
Value: 804318C629000000 | |||
| (PID) Process: | (336) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Browser |
Value: 774A18C629000000 | |||
| (PID) Process: | (336) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Telemetry |
Value: 0 | |||
| (PID) Process: | (336) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\DllPrefetchExperiment |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe |
Value: 0 | |||
| (PID) Process: | (336) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Default Browser Agent |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox|DisableTelemetry |
Value: 1 | |||
| (PID) Process: | (336) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Default Browser Agent |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox|DisableDefaultBrowserAgent |
Value: 0 | |||
| (PID) Process: | (336) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Default Browser Agent |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox|ServicesSettingsServer |
Value: https://firefox.settings.services.mozilla.com/v1 | |||
| (PID) Process: | (336) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Default Browser Agent |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox|SecurityContentSignatureRootHash |
Value: 97:E8:BA:9C:F1:2F:B3:DE:53:CC:42:A4:E6:57:7E:D6:4D:F4:93:C2:47:B4:14:FE:A0:36:81:8D:38:23:56:0E | |||
Executable files
27
Suspicious files
220
Text files
224
Unknown types
147
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3408 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\opr567B.tmp | text | |
MD5:— | SHA256:— | |||
| 3408 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\operaprefs.ini | text | |
MD5:— | SHA256:— | |||
| 3408 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\tasks.xml | xml | |
MD5:— | SHA256:— | |||
| 3408 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\opssl6.dat | binary | |
MD5:— | SHA256:— | |||
| 3408 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\sessions\autosave.win.bak | text | |
MD5:46A734B275C8C258D9D6F508E73B36AD | SHA256:B80192EDC377DD212C9E488E1983FBCD68CF83330576EFD7579B7AB30FA3672B | |||
| 3408 | opera.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\16ec093b8f51508f.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 3408 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\global_history.dat | text | |
MD5:— | SHA256:— | |||
| 3408 | opera.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\6YX7CZPY4575WSBPWW4M.temp | binary | |
MD5:— | SHA256:— | |||
| 3408 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\sessions\oprA98E.tmp | text | |
MD5:— | SHA256:— | |||
| 3408 | opera.exe | C:\Users\admin\AppData\Local\Opera\Opera\cache\sesn\opr00003.tmp | xml | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
73
TCP/UDP connections
181
DNS requests
242
Threats
19
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3408 | opera.exe | GET | — | 185.26.182.109:80 | http://redir.opera.com/speeddials/booking | unknown | — | — | whitelisted |
3408 | opera.exe | GET | — | 185.26.182.109:80 | http://redir.opera.com/speeddials/amazon/ | unknown | — | — | whitelisted |
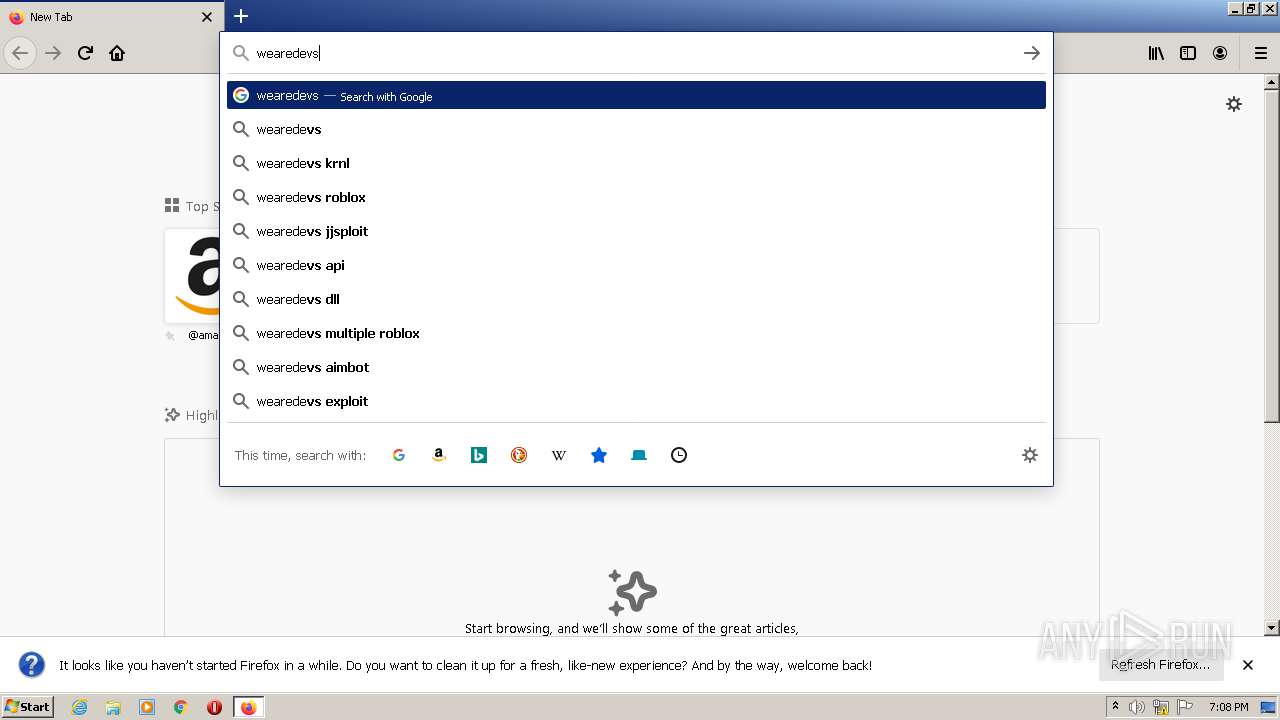
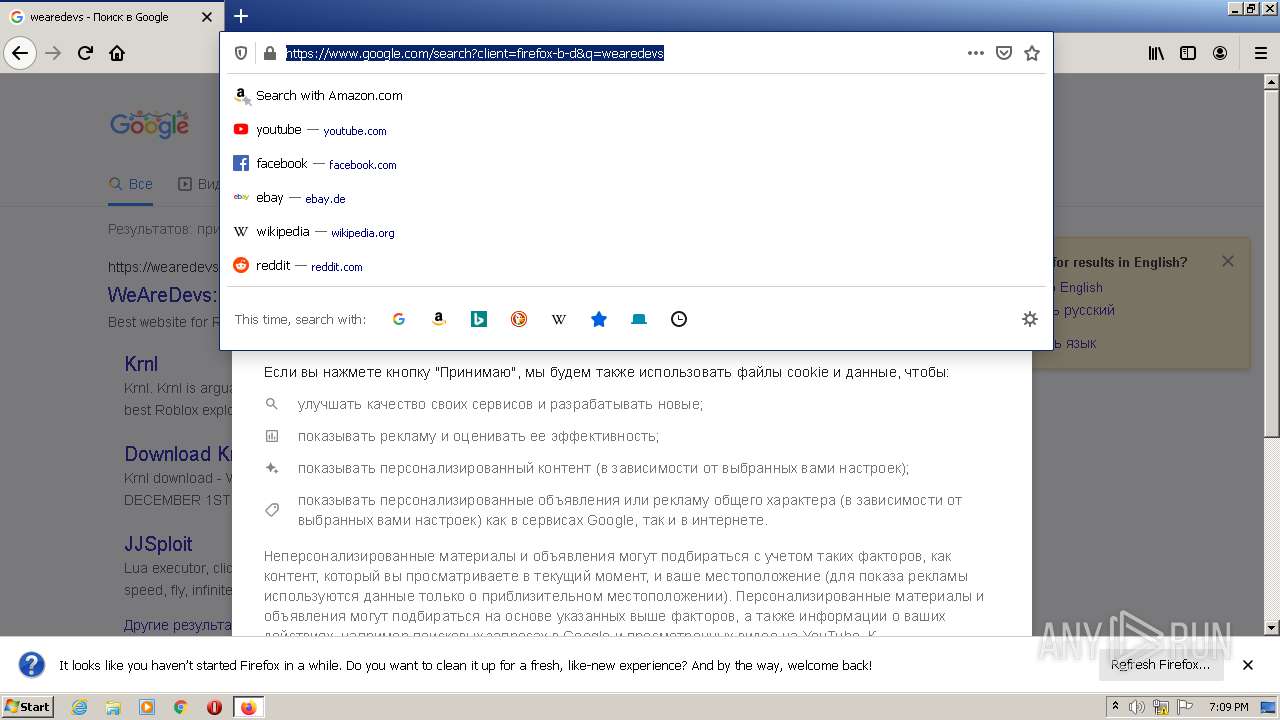
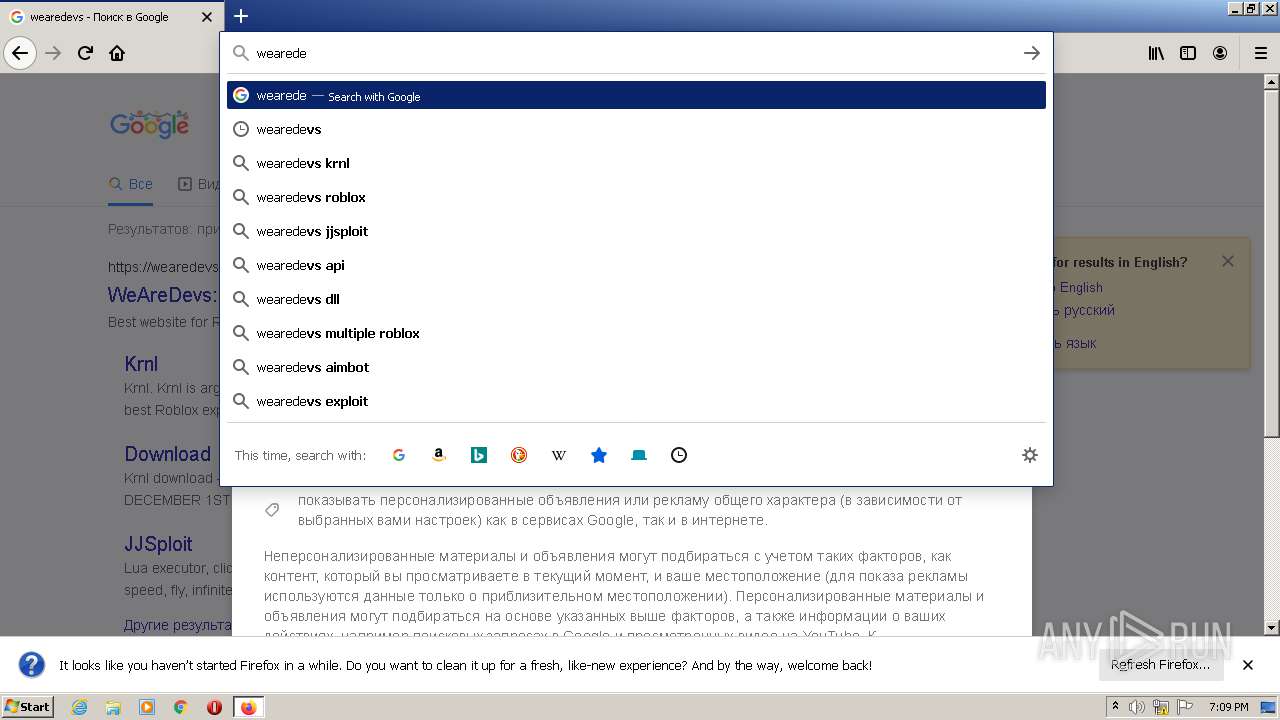
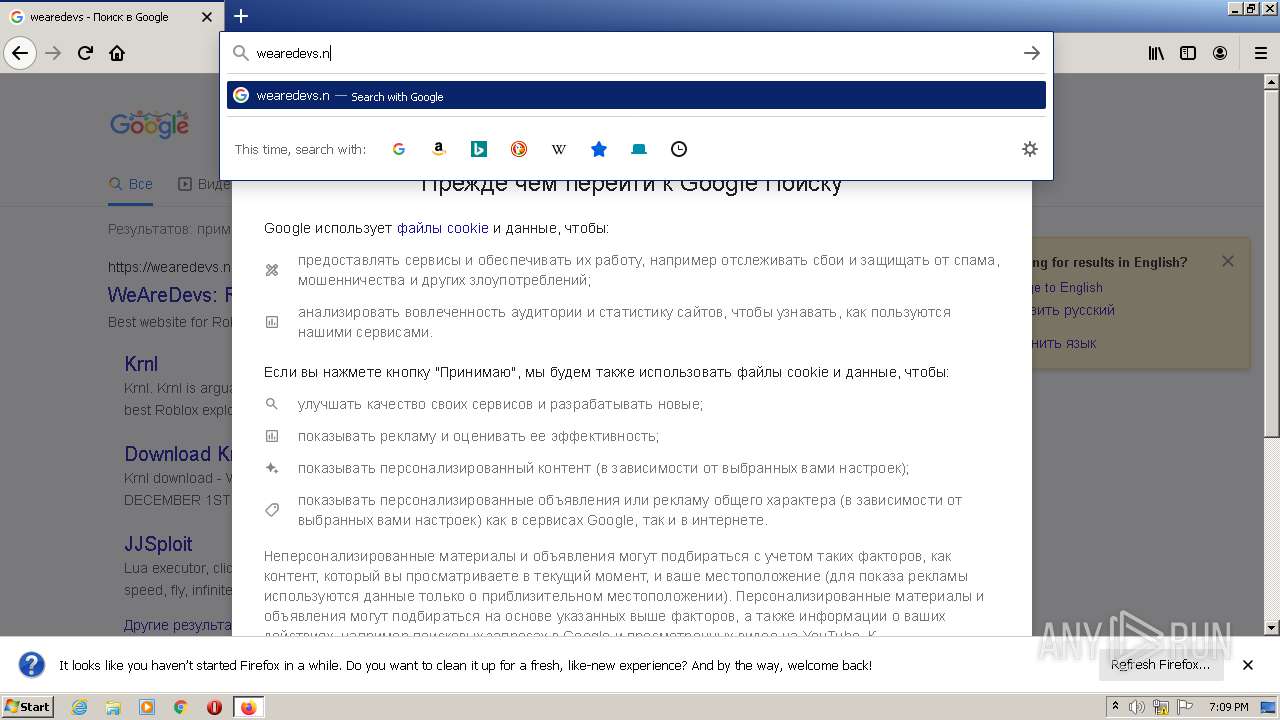
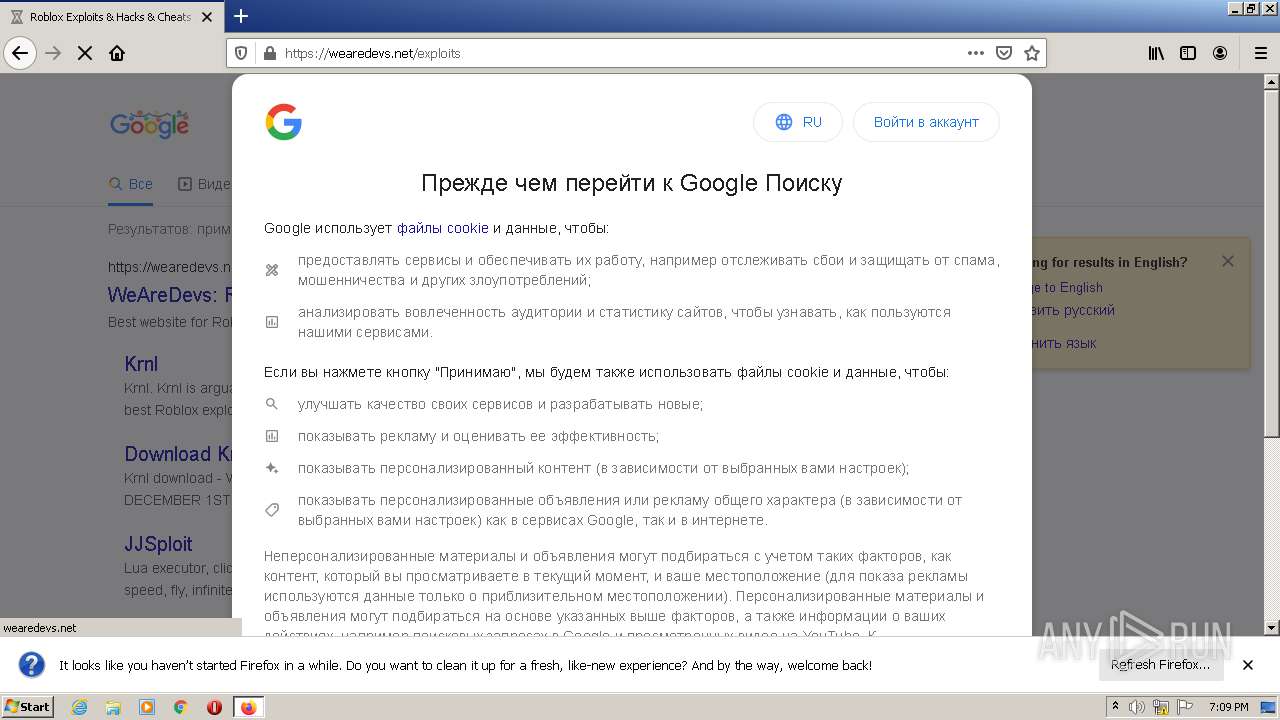
3408 | opera.exe | GET | 302 | 172.217.16.131:80 | http://www.google.com.ua/search?client=opera&q=wearedevs&sourceid=opera&ie=utf-8&oe=utf-8&channel=suggest | US | html | 338 b | whitelisted |
3408 | opera.exe | GET | 302 | 172.217.16.131:80 | http://www.google.com.ua/search?q=wearedevs&sourceid=opera&ie=utf-8&oe=utf-8&channel=suggest | US | html | 322 b | whitelisted |
3408 | opera.exe | GET | 200 | 142.250.186.46:80 | http://clients1.google.com/complete/search?q=weare&client=opera-suggest-omnibox&hl=de | US | text | 139 b | whitelisted |
3408 | opera.exe | GET | 200 | 142.250.185.227:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQCu6LHDc9xznwoAAAABGVhU | US | der | 472 b | whitelisted |
3408 | opera.exe | GET | 200 | 142.250.185.227:80 | http://crl.pki.goog/gtsr1/gtsr1.crl | US | der | 760 b | whitelisted |
3408 | opera.exe | GET | 200 | 93.184.220.29:80 | http://crl3.digicert.com/DigiCertHighAssuranceEVRootCA.crl | US | der | 592 b | whitelisted |
3408 | opera.exe | GET | 302 | 185.26.182.109:80 | http://redir.opera.com/speeddials/booking.com | unknown | html | 221 b | whitelisted |
3408 | opera.exe | GET | 302 | 185.26.182.109:80 | http://redir.opera.com/speeddials/previews/shopping/de | unknown | html | 315 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
336 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | — | US | whitelisted |
336 | firefox.exe | 143.204.98.23:443 | firefox.settings.services.mozilla.com | — | US | malicious |
336 | firefox.exe | 143.204.98.30:443 | content-signature-2.cdn.mozilla.net | — | US | suspicious |
— | — | 128.116.123.3:443 | web.roblox.com | University Corporation for Atmospheric Research | US | suspicious |
3408 | opera.exe | 185.26.182.118:443 | sitecheck2.opera.com | Opera Software AS | — | suspicious |
3408 | opera.exe | 185.26.182.94:443 | sitecheck2.opera.com | Opera Software AS | — | whitelisted |
3408 | opera.exe | 185.26.182.93:443 | sitecheck2.opera.com | Opera Software AS | — | whitelisted |
3408 | opera.exe | 185.26.182.112:443 | sitecheck2.opera.com | Opera Software AS | — | malicious |
3408 | opera.exe | 93.184.220.29:80 | crl3.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3408 | opera.exe | 128.116.123.3:443 | web.roblox.com | University Corporation for Atmospheric Research | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
web.roblox.com |
| malicious |
sitecheck2.opera.com |
| whitelisted |
certs.opera.com |
| whitelisted |
crl3.digicert.com |
| whitelisted |
crl4.digicert.com |
| whitelisted |
redir.opera.com |
| whitelisted |
clients1.google.com |
| whitelisted |
www.google.com.ua |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
crl.pki.goog |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3408 | opera.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
3408 | opera.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
3408 | opera.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
3408 | opera.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
3408 | opera.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
3408 | opera.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
3408 | opera.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
3408 | opera.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
3408 | opera.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
3408 | opera.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
1 ETPRO signatures available at the full report