| URL: | http://elizabethejgx.dns04.com/manual-greenbrier-universal-remote.html |
| Full analysis: | https://app.any.run/tasks/d13aaded-dd4a-4a2e-b944-c1b4d98a0370 |
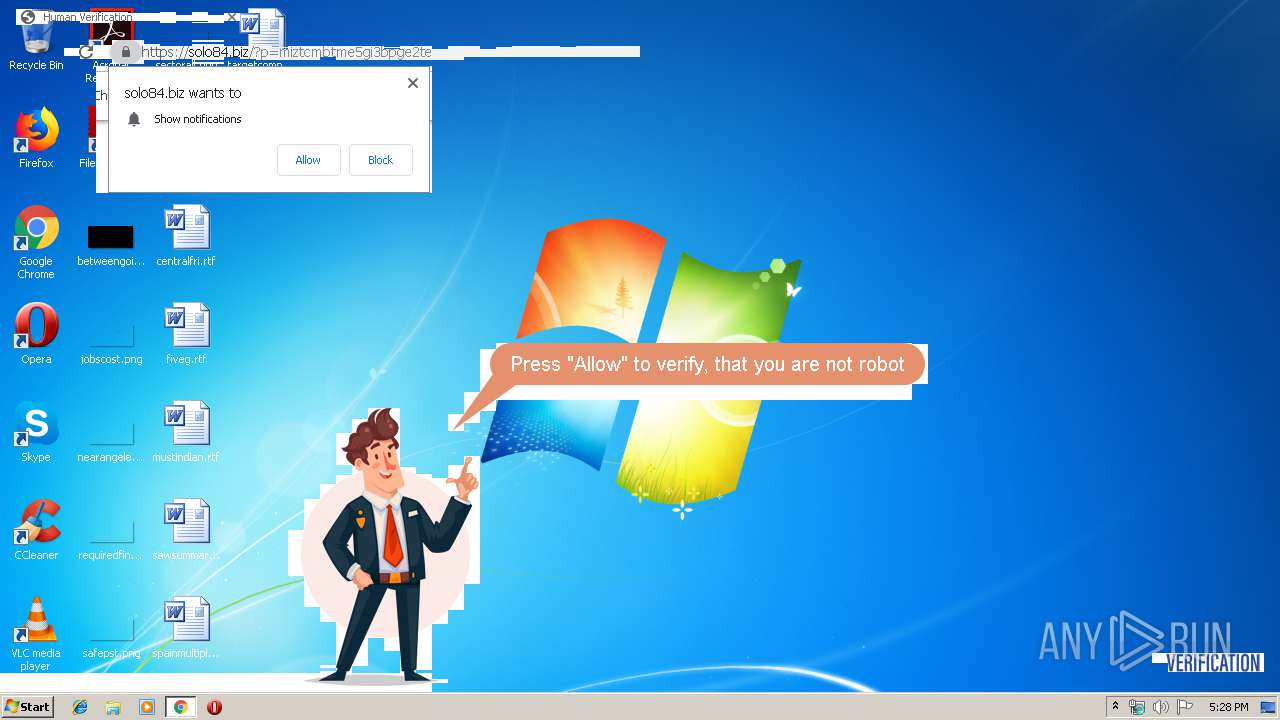
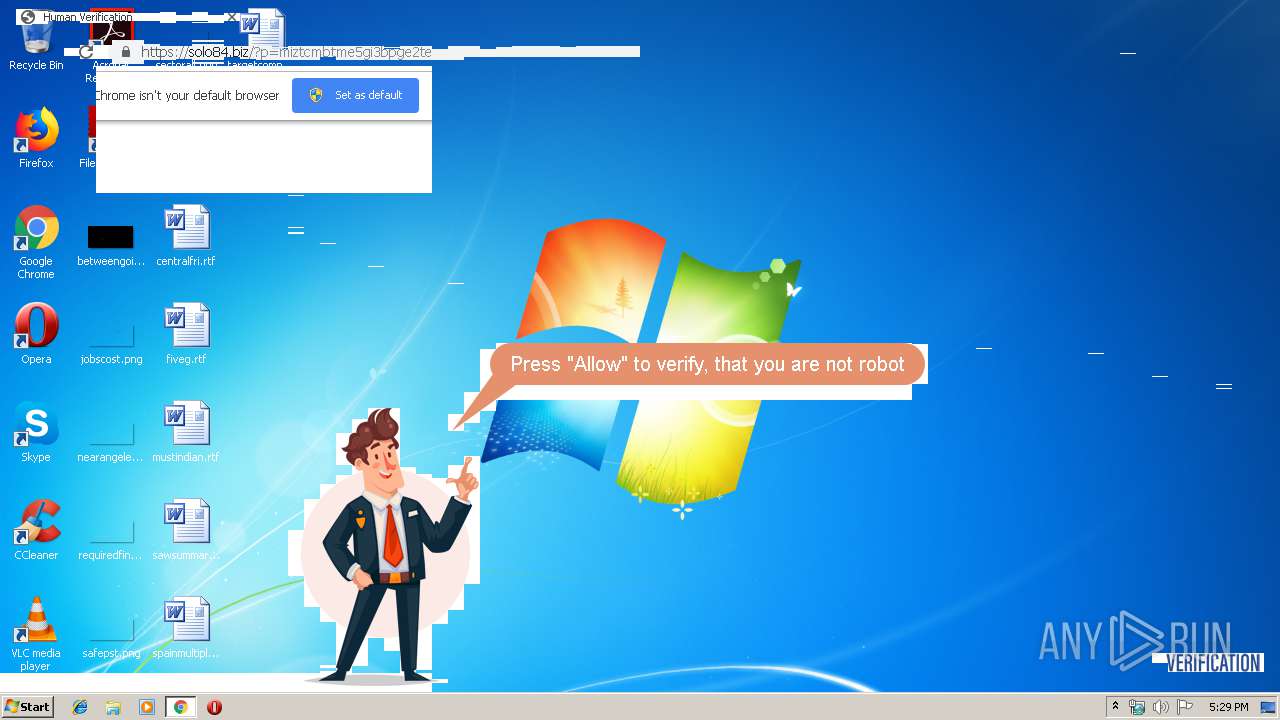
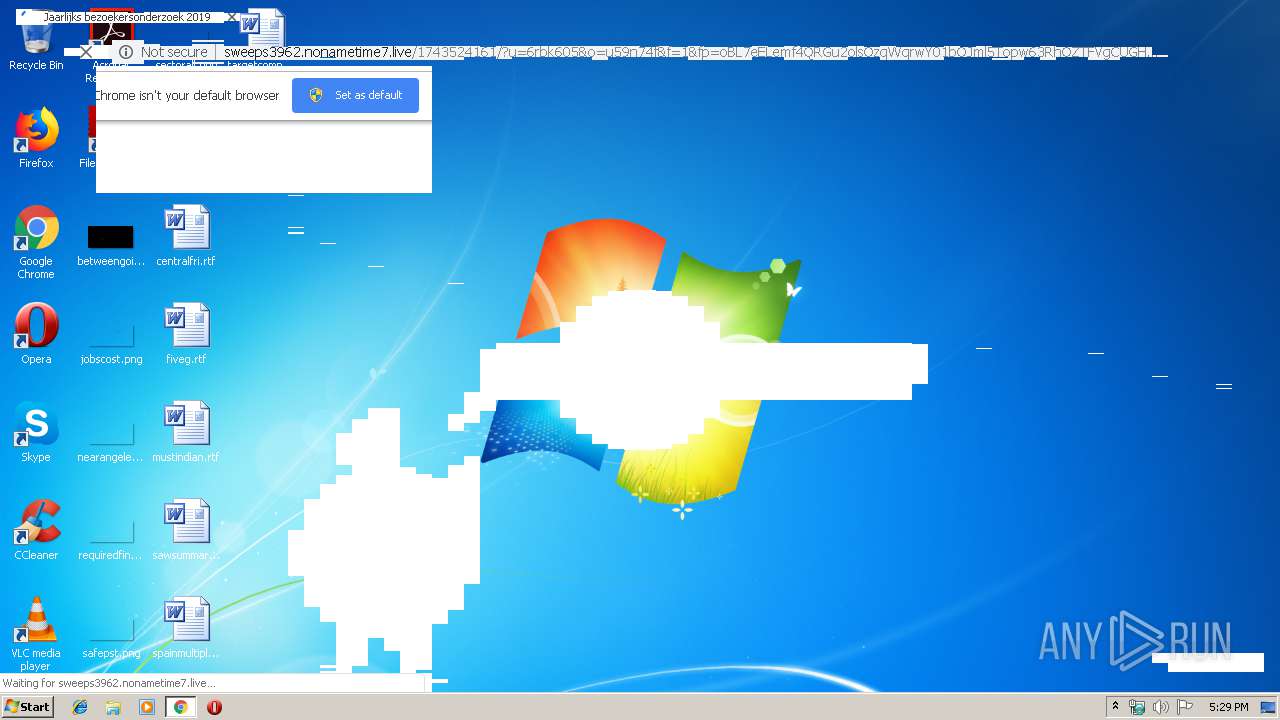
| Verdict: | Malicious activity |
| Analysis date: | December 06, 2019, 17:28:31 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 4B48F06E67BF8CC2015DA5F276F47303 |
| SHA1: | E45FFB33D35242C185DF9FF75C0DE03C35BC7592 |
| SHA256: | 042D026341CF6D8F84FB33FC18DDFA459290C5285FBE5CA9D2A46A4EF4D2F2C6 |
| SSDEEP: | 3:N1KbCfp8moR6EJfhXMbe7WEJIXA3mLQn:Cgp8ZR623WgIdQ |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 1608)
INFO
Reads the hosts file
- chrome.exe (PID: 1608)
- chrome.exe (PID: 3944)
Application launched itself
- chrome.exe (PID: 1608)
Connects to unusual port
- chrome.exe (PID: 3944)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
64
Monitored processes
28
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 184 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,314740921139912077,6852643483249543325,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15760555620188364640 --mojo-platform-channel-handle=4396 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 392 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,314740921139912077,6852643483249543325,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1117688003370905444 --renderer-client-id=9 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2784 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 788 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,314740921139912077,6852643483249543325,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15344777472833395924 --mojo-platform-channel-handle=3372 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 964 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,314740921139912077,6852643483249543325,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11815027290319040413 --mojo-platform-channel-handle=1948 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1292 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,314740921139912077,6852643483249543325,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10119957698642762235 --mojo-platform-channel-handle=3104 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1412 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,314740921139912077,6852643483249543325,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12581779829631761271 --mojo-platform-channel-handle=4324 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1608 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "http://elizabethejgx.dns04.com/manual-greenbrier-universal-remote.html" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1636 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,314740921139912077,6852643483249543325,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16187847016525719430 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2244 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1756 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,314740921139912077,6852643483249543325,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5601817155916008954 --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3456 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1796 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,314740921139912077,6852643483249543325,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1597858314573427827 --mojo-platform-channel-handle=3816 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
237
Read events
150
Write events
82
Delete events
5
Modification events
| (PID) Process: | (1880) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 1608-13220126932790500 |
Value: 259 | |||
| (PID) Process: | (1608) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1608) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1608) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1608) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1608) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1608) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1608) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1608) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (1608) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
Executable files
0
Suspicious files
38
Text files
255
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1608 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1608 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\d8bc34f3-6dea-4c27-8da1-a6a0c158ac42.tmp | — | |
MD5:— | SHA256:— | |||
| 1608 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1608 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1608 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1608 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF39b485.TMP | text | |
MD5:— | SHA256:— | |||
| 1608 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF39b502.TMP | text | |
MD5:— | SHA256:— | |||
| 1608 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 1608 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1608 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF39b485.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
47
TCP/UDP connections
42
DNS requests
30
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3944 | chrome.exe | GET | 200 | 85.209.89.163:80 | http://elizabethejgx.dns04.com/manual-greenbrier-universal-remote.html | unknown | html | 9.97 Kb | suspicious |
3944 | chrome.exe | GET | 200 | 185.244.216.110:80 | http://vm508823.had.su/serv163 | unknown | text | 66 b | suspicious |
3944 | chrome.exe | GET | 200 | 172.217.16.193:80 | http://3.bp.blogspot.com/-QaVq1selb0I/TitF3T6NyjI/AAAAAAAAACY/swbfC8WSBYk/s1600/Greenbrier+Inc+Universal+Remote+FOUR.jpg | US | image | 291 Kb | whitelisted |
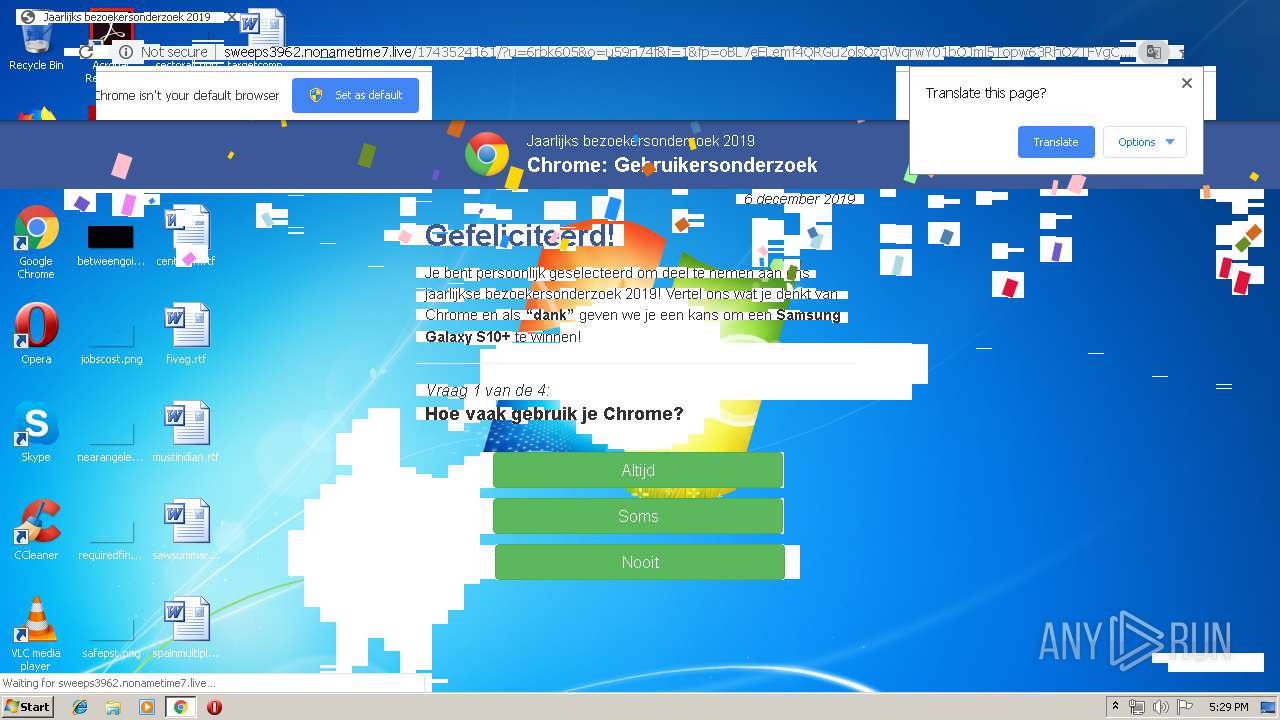
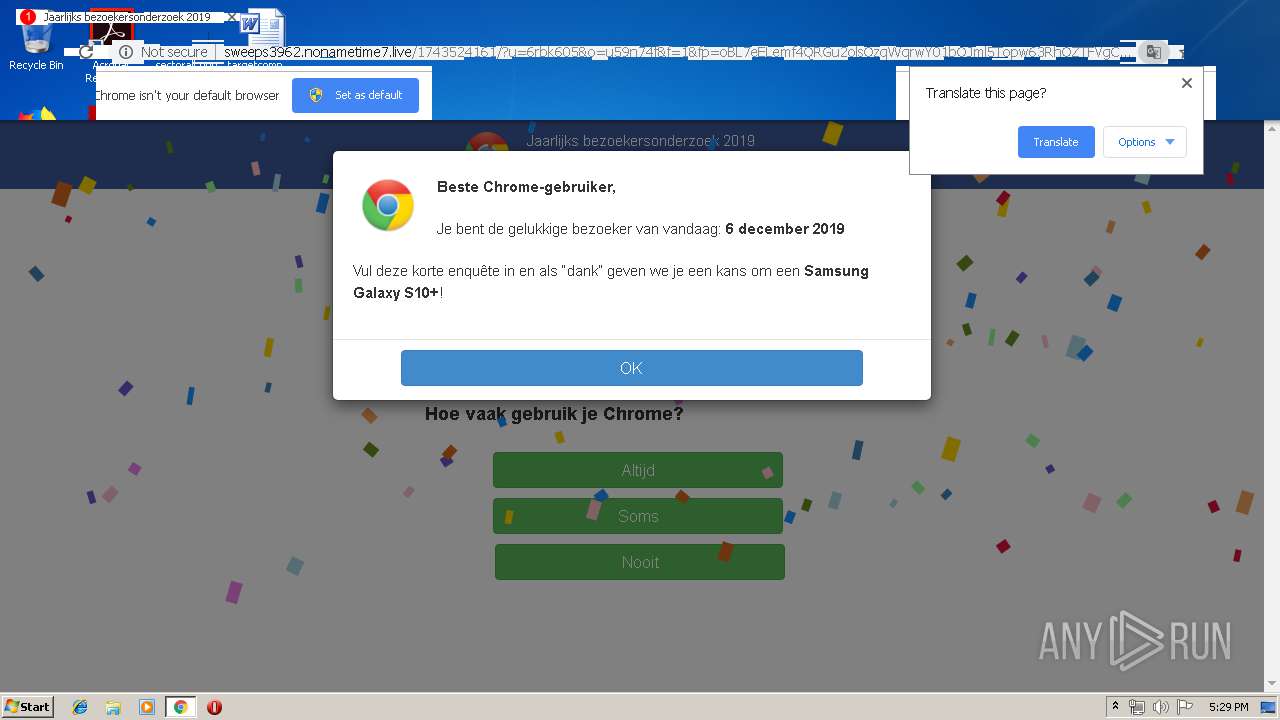
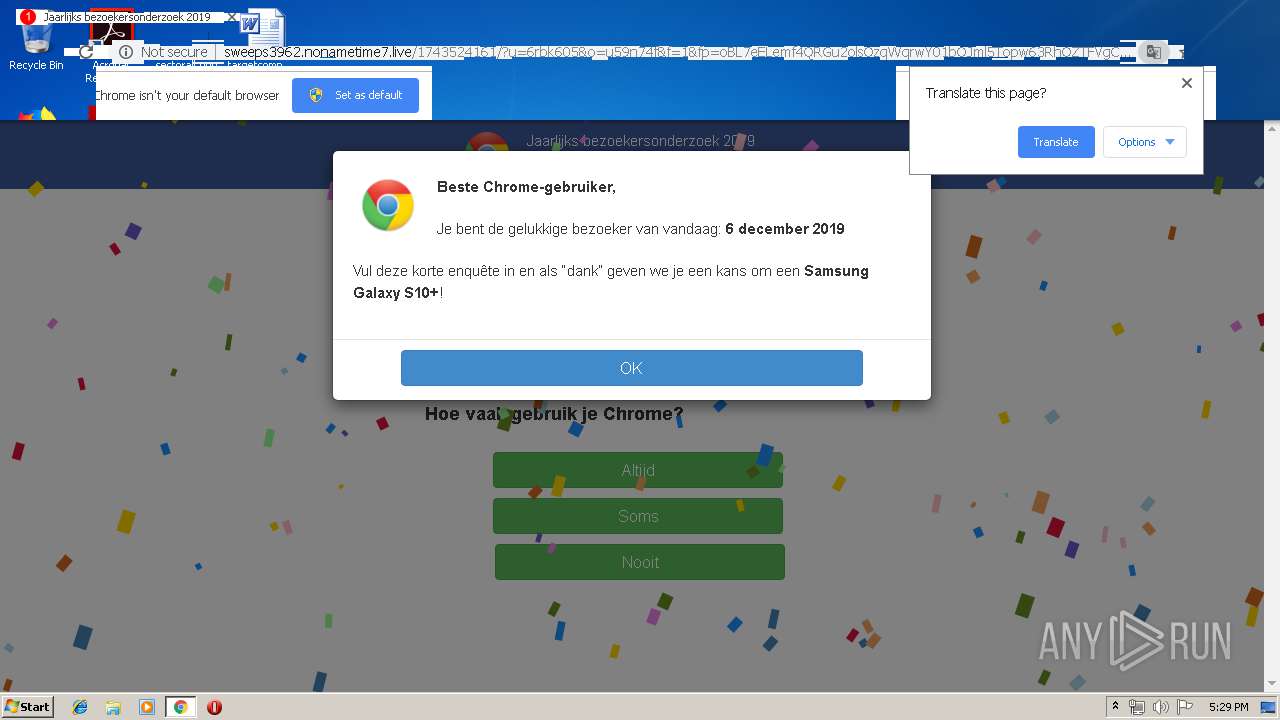
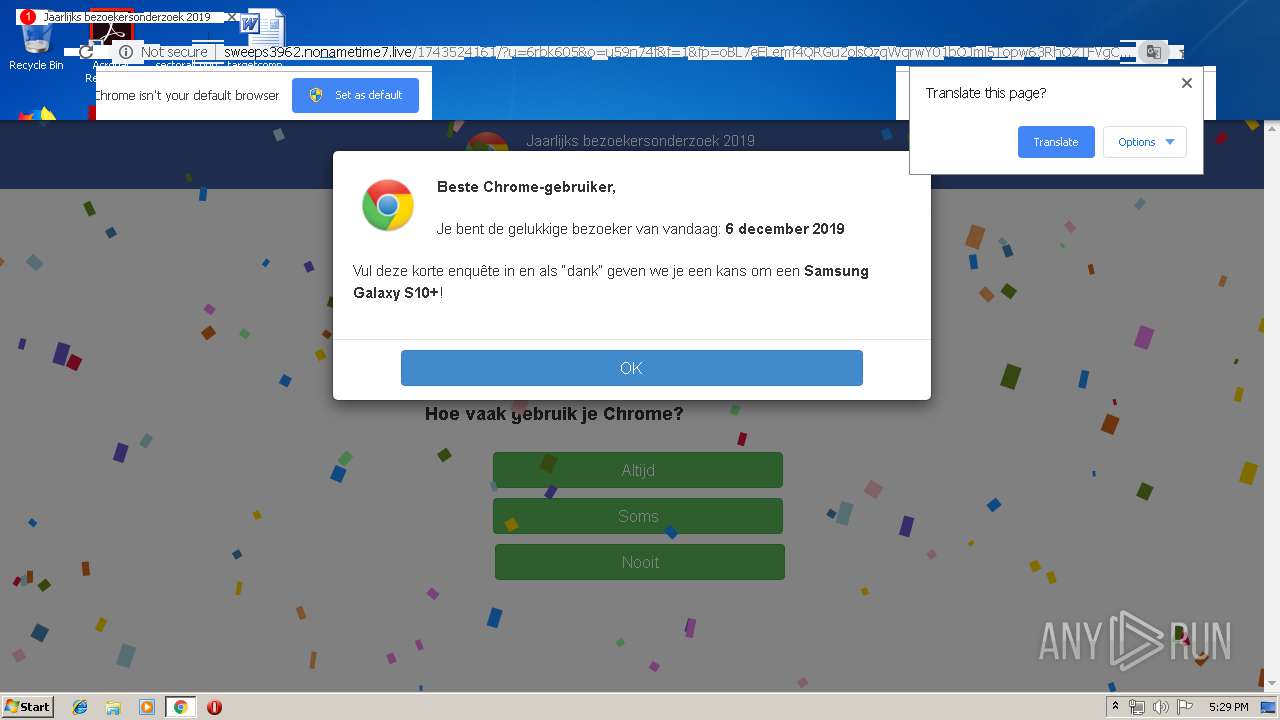
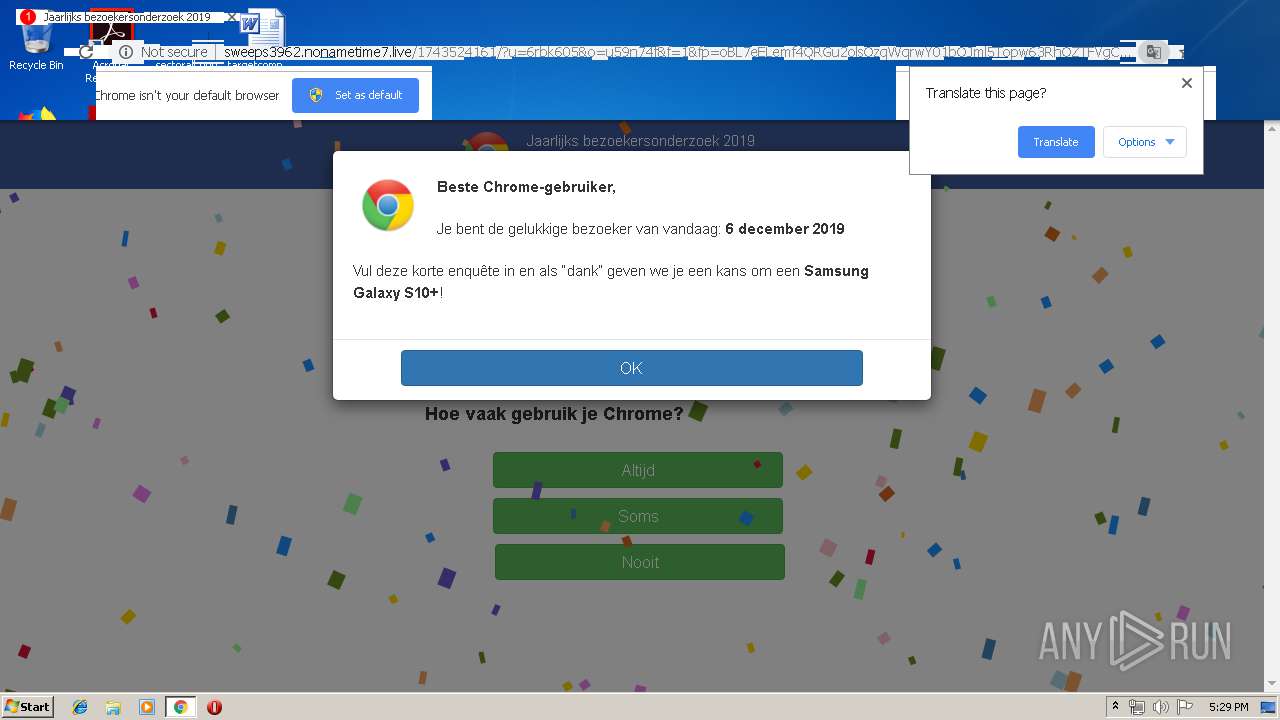
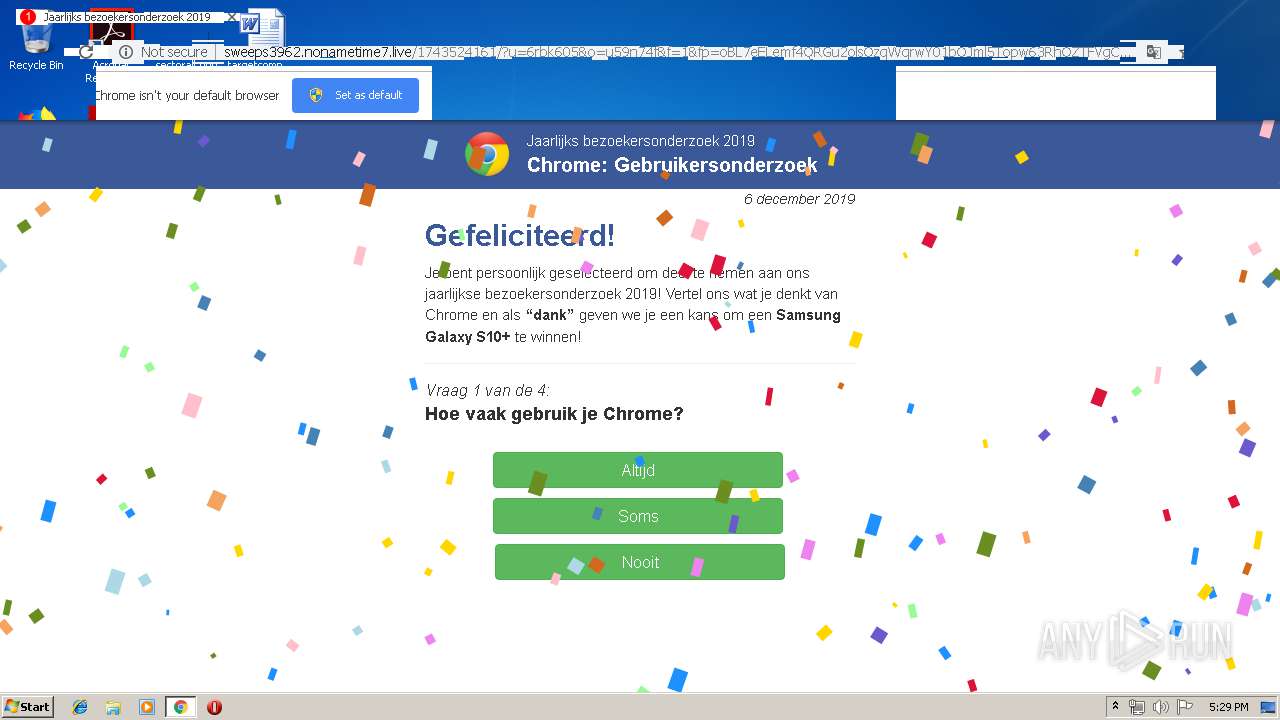
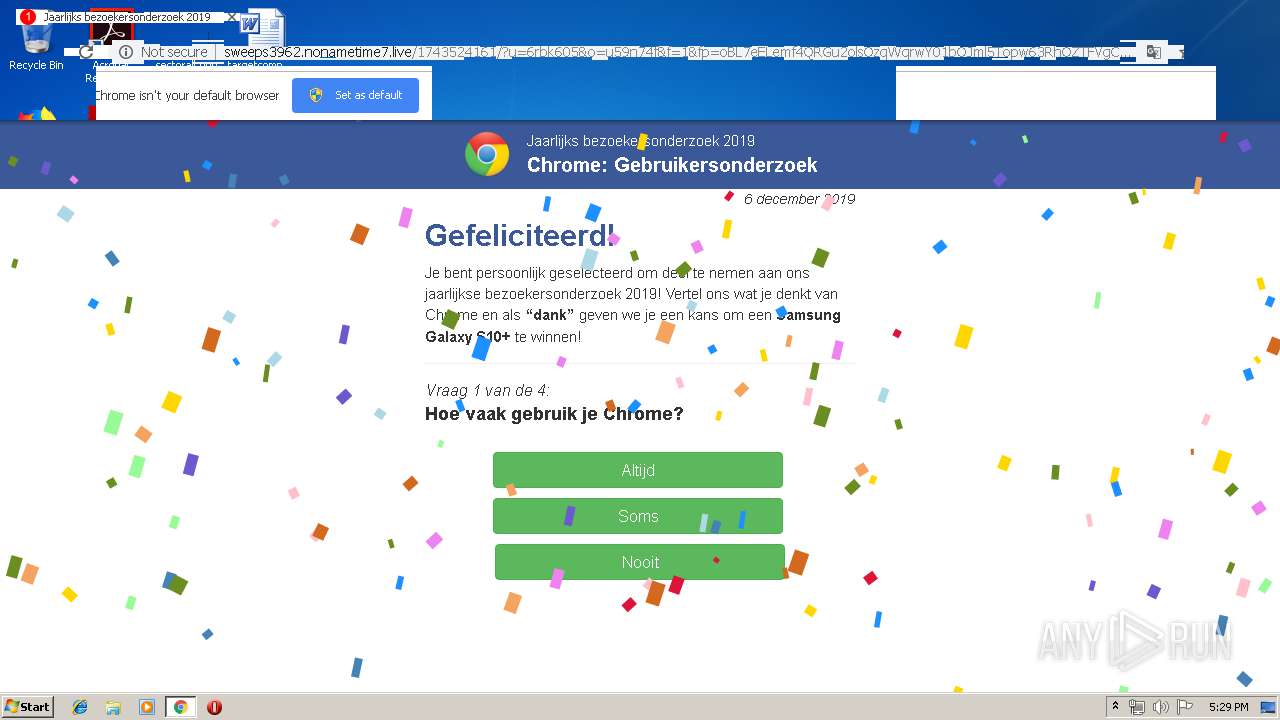
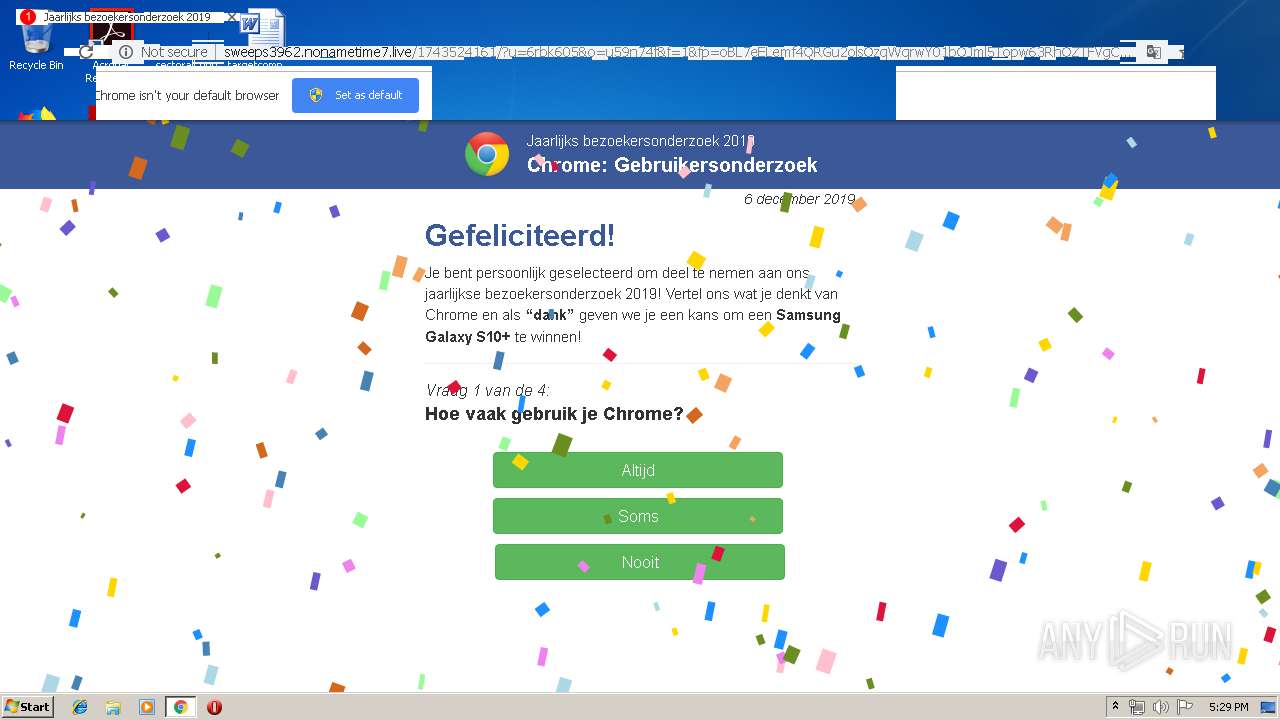
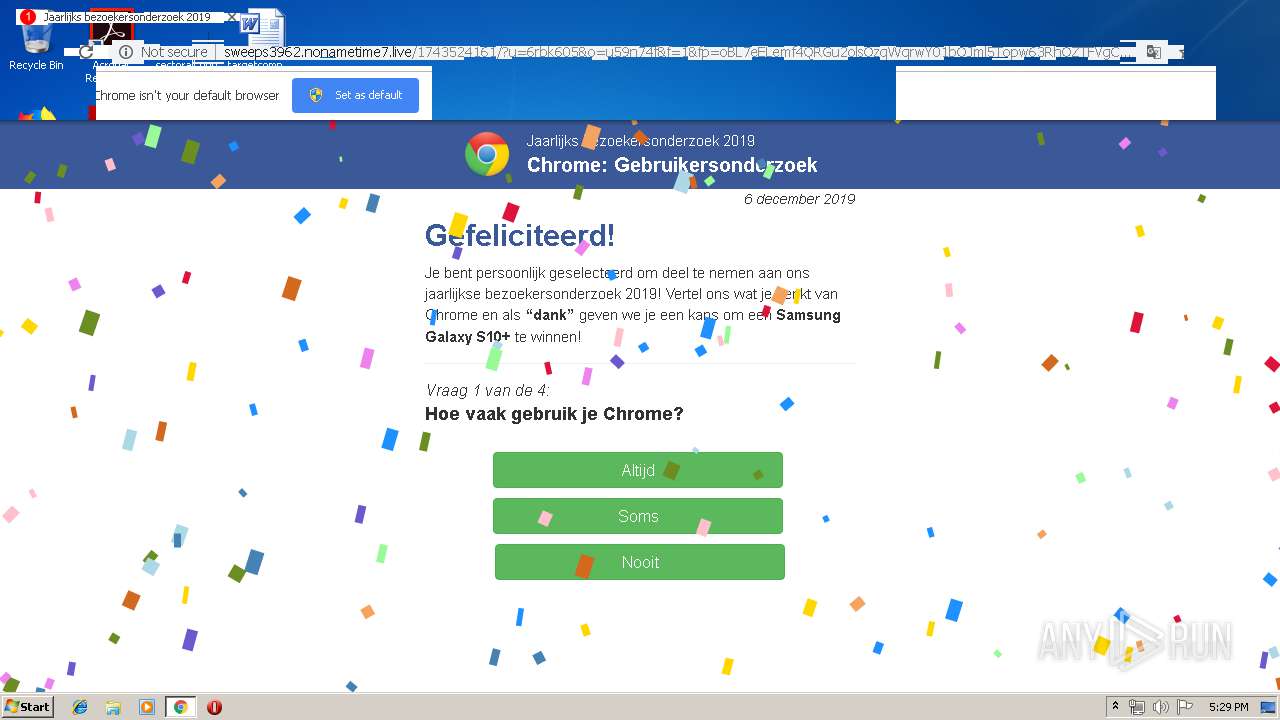
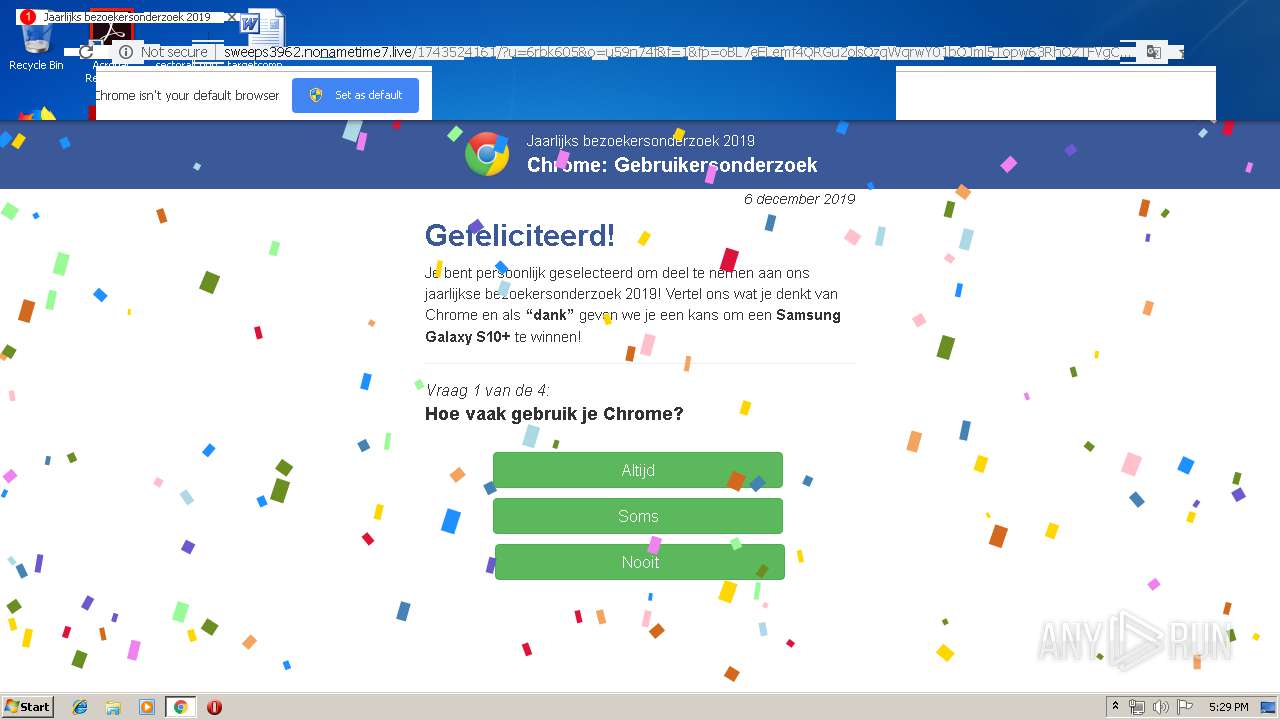
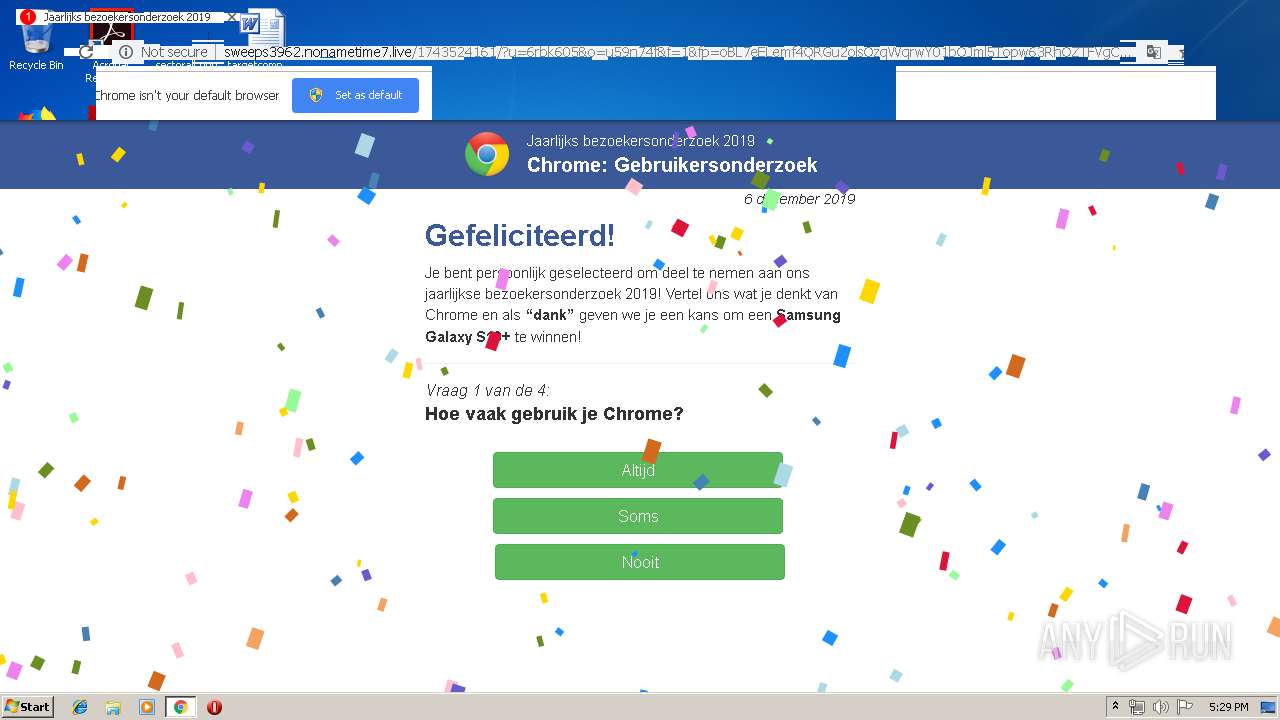
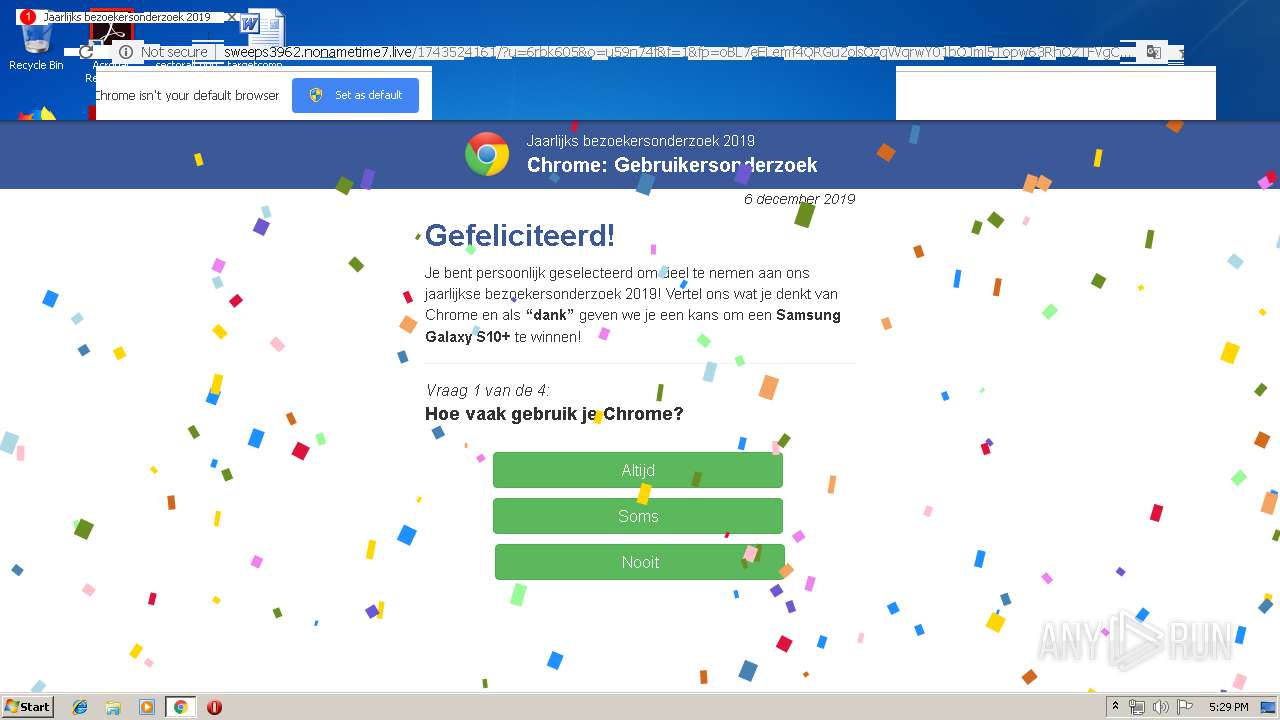
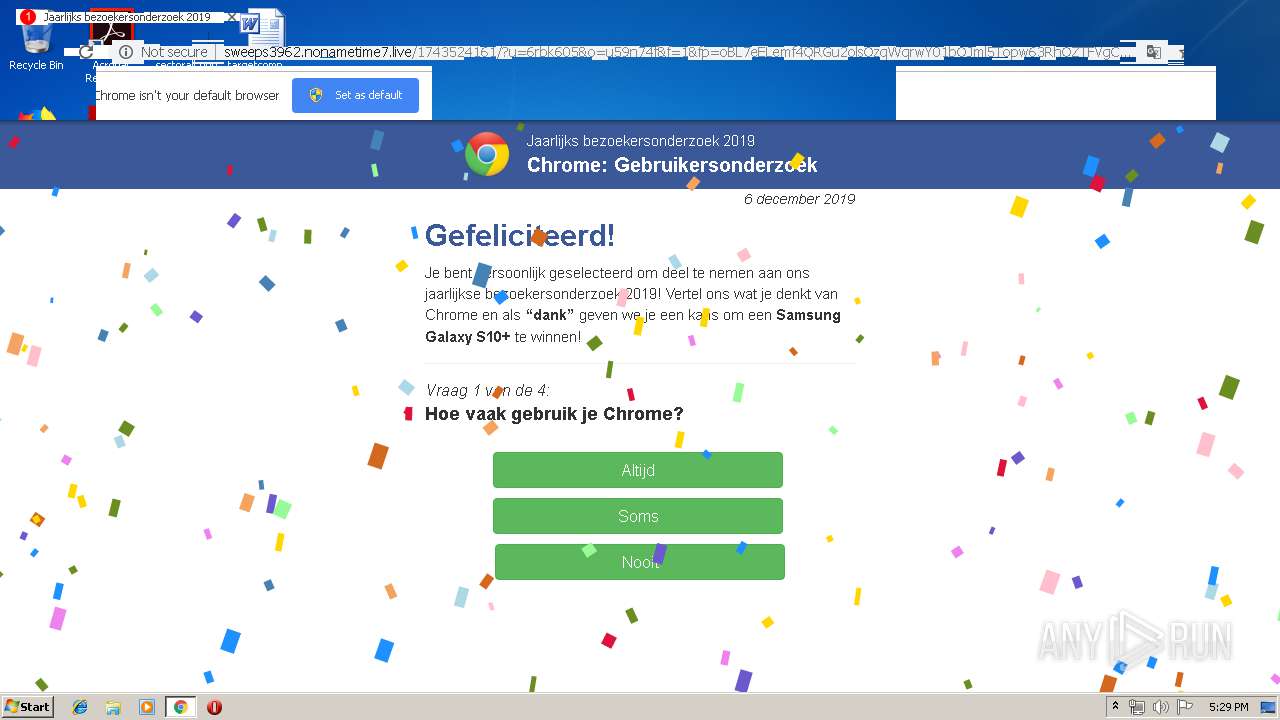
3944 | chrome.exe | GET | 200 | 185.89.102.137:80 | http://sweeps3962.nonametime7.live/1743524161/?u=6rbk605&o=u59n74f&f=1&fp=oBL7eELemf4QRGu2olsOzqWqrwY01bOJml5Topw63RhOZTFVgCUGHpiXDzYyYKWUJNoSw%2BNDzscMXnJOKasj%2BuFgOGlSpPPj8hwQBPjmgc25xDQTTJDUNG6iQlI18Rc6X44Hq60%2B0Rk9mo3gqbRmp7VyQwkNMJESXlXMX78pHiQ%2BgVByPs8XHjO5vXQjGoCdtfKp6b56NVB92MlsdGJEL6V9unn6mflNelSQ22Fu7b9%2FHad8KUefOVs2FFAn6yF80G8QpmoeVlqzXyI0IB3exIcmFfyfPF4POXy9d0ZiB0QTjNcwPBMZXsWgq5o%2B6onjdz2%2B0yNdaheCf8YVKCfPt7RHUcRmKQH6euuzav9h3J0CExCMj7d1DIZBG8938dz%2Bz3EfWHKhzct13f7bk2Mg0WQrN66cUrilSjeR095PAFcetIkJTC%2FQWJNZzyDKmtbq1RiD5s13Fl1P%2FUW3M5PFYCx9TAFUFDOruLBmUr6aqDa3Lqwh%2FIDFULgTVC7FUIZAt18jlfVQxU8%2B0Eee20pDjk1jz%2BHAkaTcrsXO3syYjAMJcO8eMzWv3j7PRlAr7ak3hRe9YMtT04IFeRiI6Yt%2FGhU9ScTPJhs3CbxYtcujAU0zJOGxts7J3DL5U5J8FKHdD2d3fJ%2FaG%2FhTjvWvBtyvJQ%3D%3D | UA | html | 16.7 Kb | suspicious |
3944 | chrome.exe | GET | 200 | 185.89.102.137:80 | http://sweeps3962.nonametime7.live/media/mainstream/us/wap/mobsurvey/logo1.js | UA | text | 12.7 Kb | suspicious |
3944 | chrome.exe | GET | 200 | 185.89.102.137:80 | http://sweeps3962.nonametime7.live/media/mainstream/nl/wap/mobsurvey/modernizr-2.6.2-respond-1.1.0.min.js | UA | html | 17.8 Kb | suspicious |
3944 | chrome.exe | GET | 200 | 185.89.102.137:80 | http://sweeps3962.nonametime7.live/media/mainstream/nl/wap/mobsurvey/nl-en.js | UA | text | 5.03 Kb | suspicious |
3944 | chrome.exe | GET | 200 | 172.217.16.193:80 | http://3.bp.blogspot.com/-6j2QV0Jnx_s/Tis78aqsEWI/AAAAAAAAAB0/_-qFoUtnq9I/w1200-h630-p-nu/Greenbrier%2BInternational%2BInc%2BUniversal%2BRemote%2BInstructions%2BMAIN.jpeg | US | image | 214 Kb | whitelisted |
3944 | chrome.exe | GET | 200 | 172.217.16.193:80 | http://2.bp.blogspot.com/-aJc2ixOqISc/Tis8RE9Ma4I/AAAAAAAAAB8/itBLp2wWbOY/s1600/Greenbrier%2BInternational%2BInc%2BUniversal%2BRemote%2Bmodel%2B110064.jpeg | US | image | 57.6 Kb | whitelisted |
3944 | chrome.exe | GET | 200 | 185.89.102.137:80 | http://sweeps3962.nonametime7.live/media/mainstream/nl/wap/mobsurvey/bootstrap.min.css | UA | text | 97.6 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3944 | chrome.exe | 172.217.22.67:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3944 | chrome.exe | 85.209.89.163:80 | elizabethejgx.dns04.com | — | — | suspicious |
3944 | chrome.exe | 216.58.208.45:443 | accounts.google.com | Google Inc. | US | whitelisted |
3944 | chrome.exe | 185.244.216.110:80 | vm508823.had.su | — | — | suspicious |
3944 | chrome.exe | 172.217.16.193:80 | 2.bp.blogspot.com | Google Inc. | US | whitelisted |
3944 | chrome.exe | 172.217.16.193:443 | 2.bp.blogspot.com | Google Inc. | US | whitelisted |
3944 | chrome.exe | 172.217.22.22:443 | i.ytimg.com | Google Inc. | US | whitelisted |
3944 | chrome.exe | 151.101.13.208:80 | wvns.images.worldnow.com | Fastly | US | unknown |
— | — | 151.101.13.208:80 | wvns.images.worldnow.com | Fastly | US | unknown |
3944 | chrome.exe | 151.101.12.84:443 | s-media-cache-ak0.pinimg.com | Fastly | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
elizabethejgx.dns04.com |
| suspicious |
accounts.google.com |
| shared |
vm508823.had.su |
| suspicious |
2.bp.blogspot.com |
| whitelisted |
3.bp.blogspot.com |
| whitelisted |
1.bp.blogspot.com |
| whitelisted |
4.bp.blogspot.com |
| whitelisted |
wvns.images.worldnow.com |
| unknown |
i.ytimg.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .su TLD (Soviet Union) Often Malware Related |
1080 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |
3944 | chrome.exe | Potentially Bad Traffic | ET POLICY HTTP Request to .su TLD (Soviet Union) Often Malware Related |
1080 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |
1080 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .life TLD |
3944 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Request to Suspicious *.life Domain |
3 ETPRO signatures available at the full report