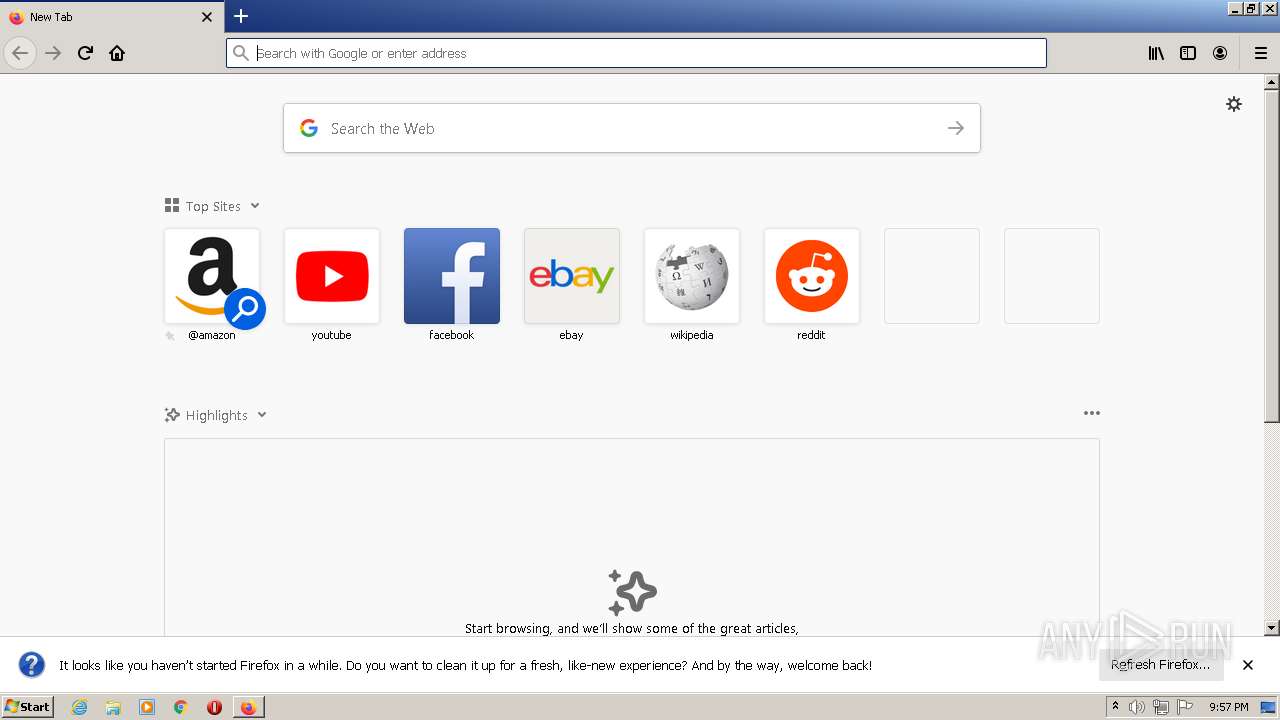
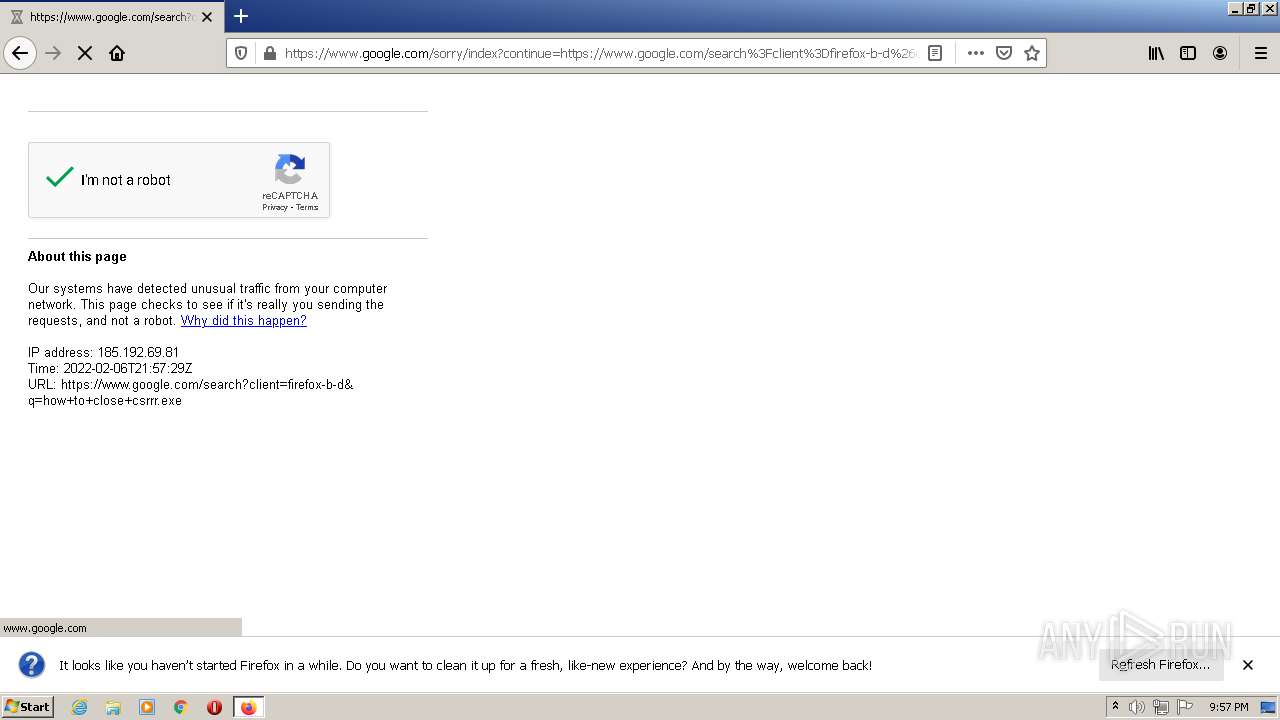
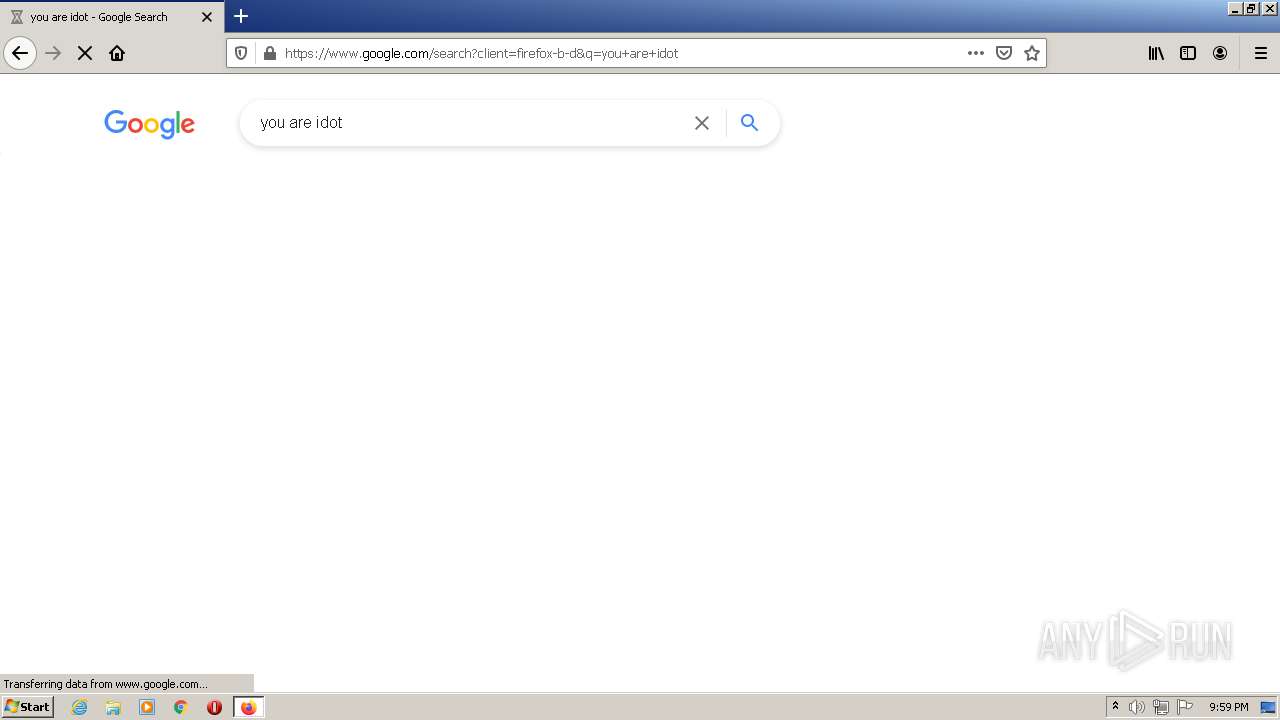
| URL: | https://www.youtube.com/watch?v=dQw4w9WgXcQ |
| Full analysis: | https://app.any.run/tasks/a6f8fcad-0fce-4263-9735-661c9d6b6951 |
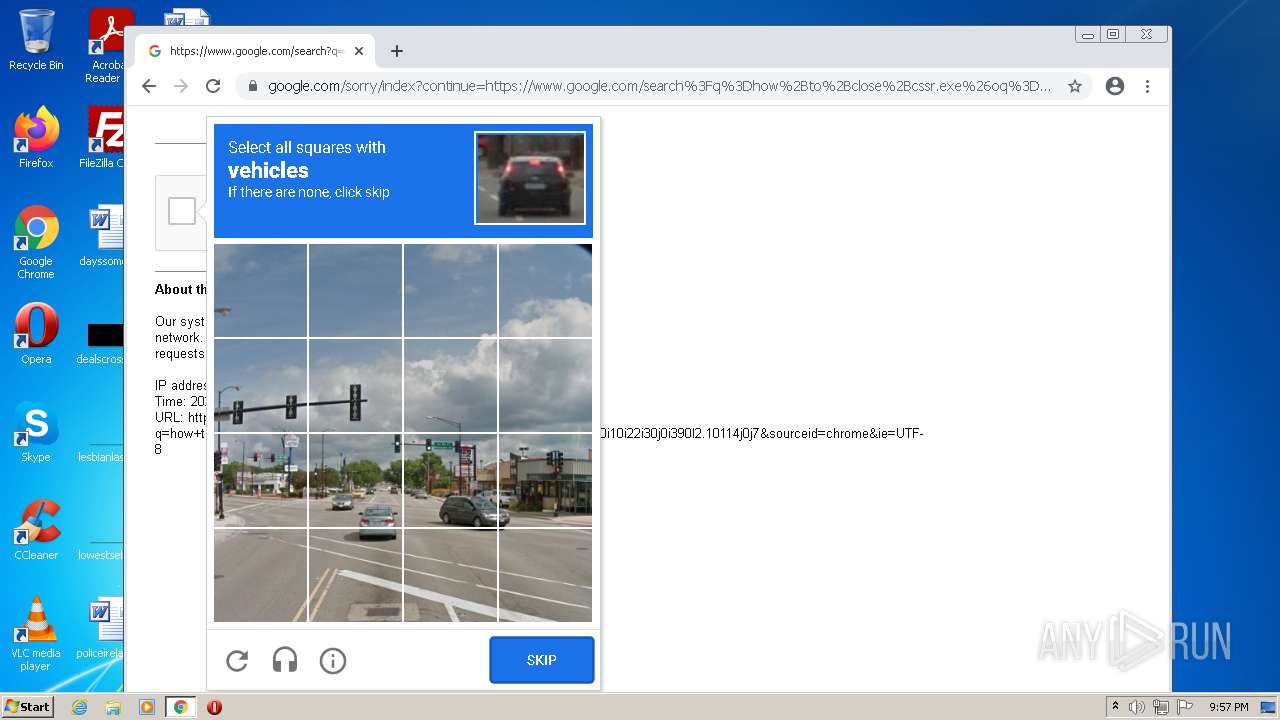
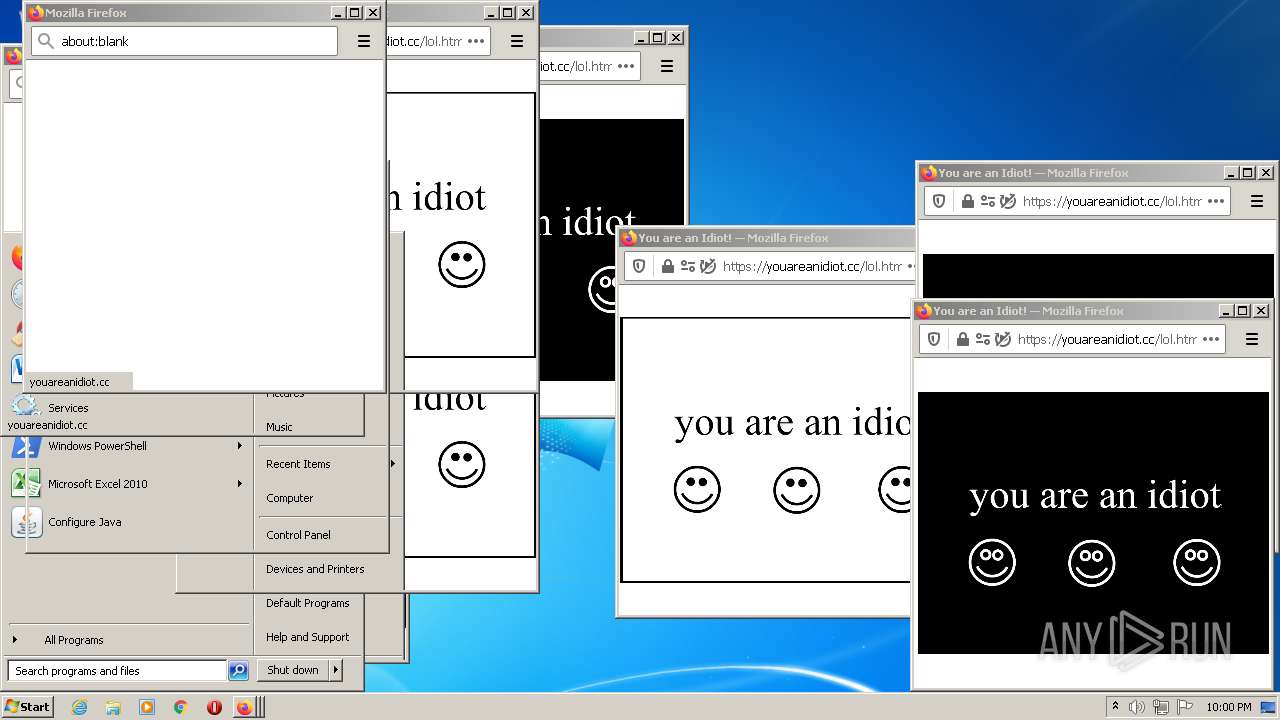
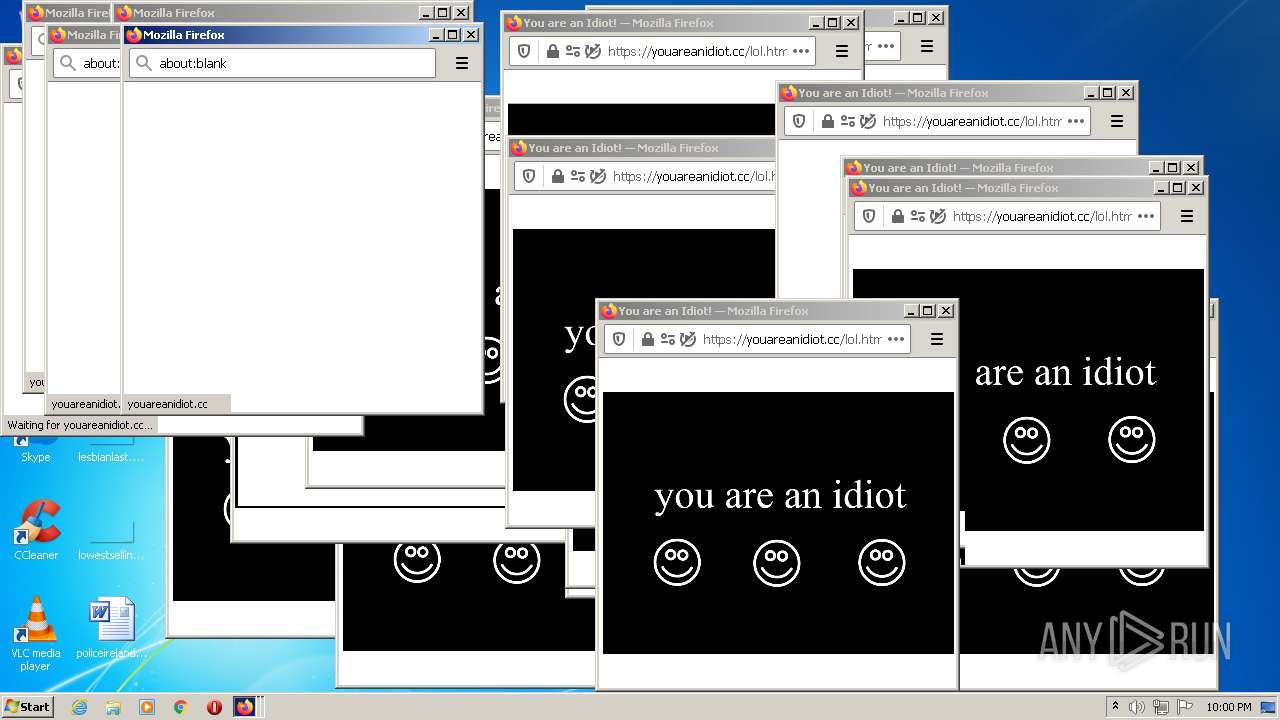
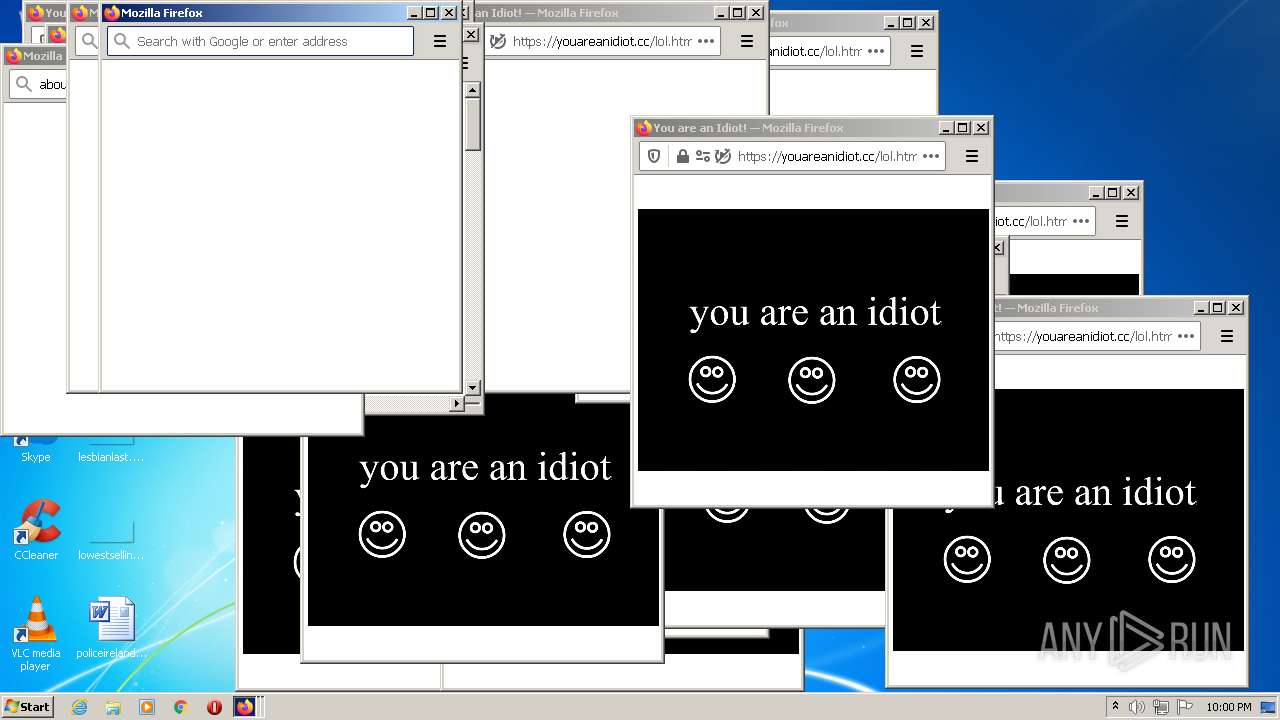
| Verdict: | Malicious activity |
| Analysis date: | February 06, 2022, 21:55:49 |
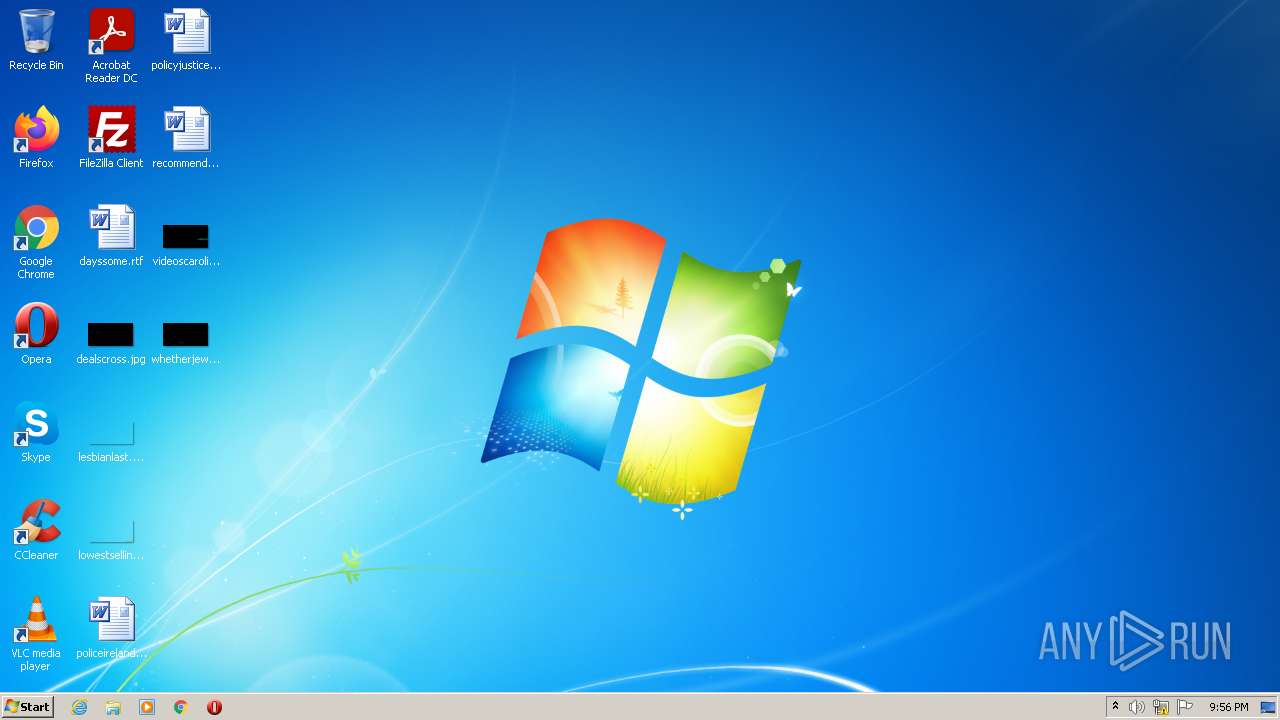
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 75170FC230CD88F32E475FF4087F81D9 |
| SHA1: | DF2C6F7AFC1A58783E15F2AE0118FF039D8A4755 |
| SHA256: | 0424974C68530290458C8D58674E2637F65ABC127057957D7B3ACBD24C208F93 |
| SSDEEP: | 3:N8DSLUxGTKSEIYsBRk0:2OLUxGF5YsBi0 |
MALICIOUS
No malicious indicators.SUSPICIOUS
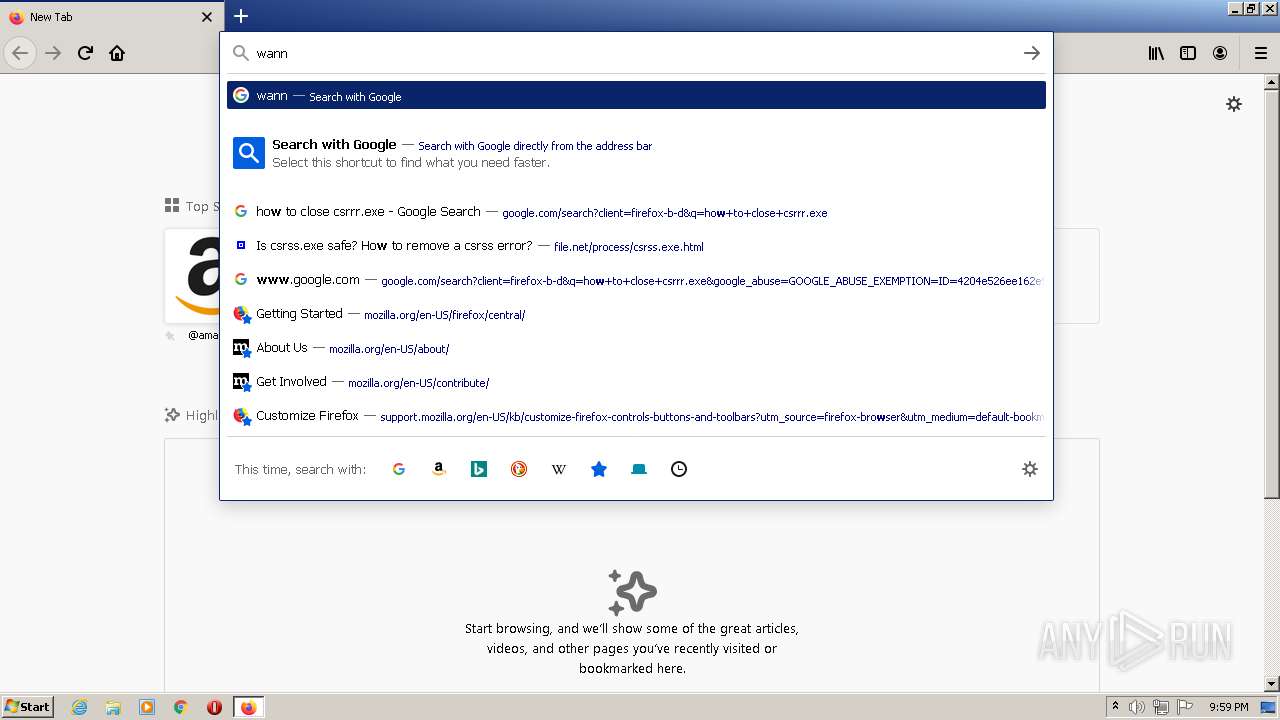
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3396)
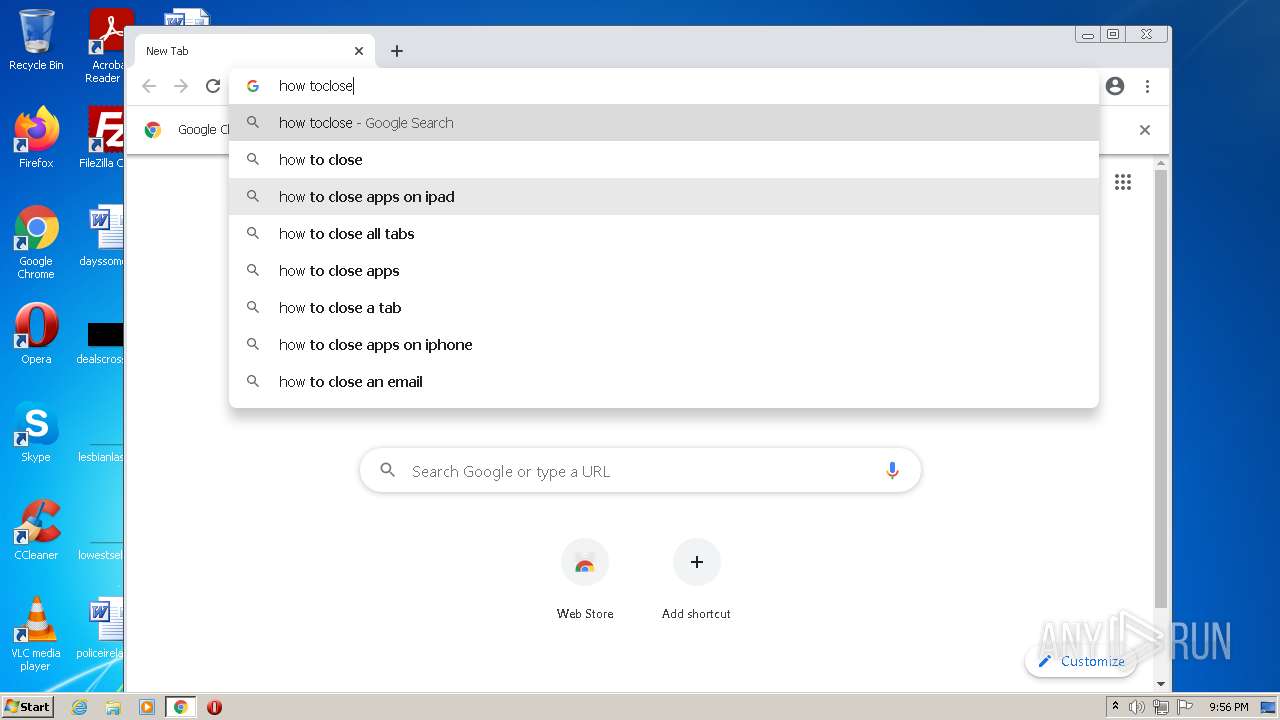
Modifies files in Chrome extension folder
- chrome.exe (PID: 3192)
INFO
Checks supported languages
- iexplore.exe (PID: 1248)
- iexplore.exe (PID: 3396)
- chrome.exe (PID: 3192)
- chrome.exe (PID: 2408)
- chrome.exe (PID: 4024)
- chrome.exe (PID: 2784)
- chrome.exe (PID: 2140)
- chrome.exe (PID: 3672)
- chrome.exe (PID: 2844)
- chrome.exe (PID: 2728)
- chrome.exe (PID: 4064)
- chrome.exe (PID: 1976)
- chrome.exe (PID: 1128)
- chrome.exe (PID: 1592)
- chrome.exe (PID: 3464)
- chrome.exe (PID: 3928)
- chrome.exe (PID: 3420)
- chrome.exe (PID: 3716)
- chrome.exe (PID: 3704)
- chrome.exe (PID: 2752)
- chrome.exe (PID: 2552)
- chrome.exe (PID: 3260)
- chrome.exe (PID: 1808)
- chrome.exe (PID: 596)
- chrome.exe (PID: 412)
- chrome.exe (PID: 2352)
- chrome.exe (PID: 2768)
- chrome.exe (PID: 2496)
- chrome.exe (PID: 3036)
- chrome.exe (PID: 4024)
- chrome.exe (PID: 1532)
- chrome.exe (PID: 2412)
- chrome.exe (PID: 372)
- chrome.exe (PID: 3228)
- chrome.exe (PID: 2972)
- firefox.exe (PID: 2072)
- firefox.exe (PID: 2976)
- firefox.exe (PID: 2548)
- firefox.exe (PID: 2600)
- firefox.exe (PID: 2600)
- firefox.exe (PID: 3384)
- firefox.exe (PID: 3024)
- taskmgr.exe (PID: 408)
- firefox.exe (PID: 2248)
- firefox.exe (PID: 2896)
- firefox.exe (PID: 3628)
- firefox.exe (PID: 3584)
- firefox.exe (PID: 2108)
- firefox.exe (PID: 2032)
- firefox.exe (PID: 3656)
- firefox.exe (PID: 3056)
Reads the computer name
- iexplore.exe (PID: 1248)
- iexplore.exe (PID: 3396)
- chrome.exe (PID: 3192)
- chrome.exe (PID: 3228)
- chrome.exe (PID: 4024)
- chrome.exe (PID: 1128)
- chrome.exe (PID: 2768)
- chrome.exe (PID: 4024)
- chrome.exe (PID: 2972)
- firefox.exe (PID: 2072)
- firefox.exe (PID: 2976)
- firefox.exe (PID: 2548)
- firefox.exe (PID: 3628)
- firefox.exe (PID: 3384)
- firefox.exe (PID: 2600)
- firefox.exe (PID: 3024)
- taskmgr.exe (PID: 408)
- firefox.exe (PID: 2896)
- firefox.exe (PID: 3584)
- firefox.exe (PID: 2108)
- firefox.exe (PID: 2032)
- firefox.exe (PID: 3656)
- firefox.exe (PID: 3056)
Changes internet zones settings
- iexplore.exe (PID: 1248)
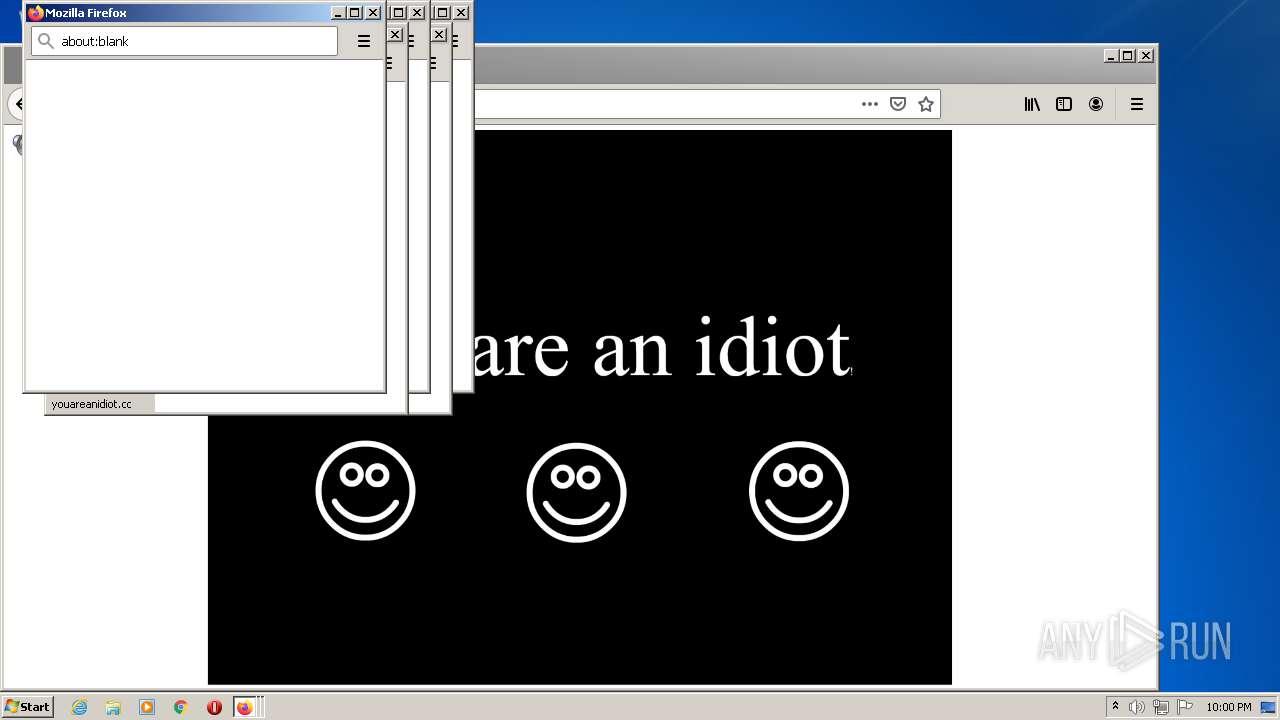
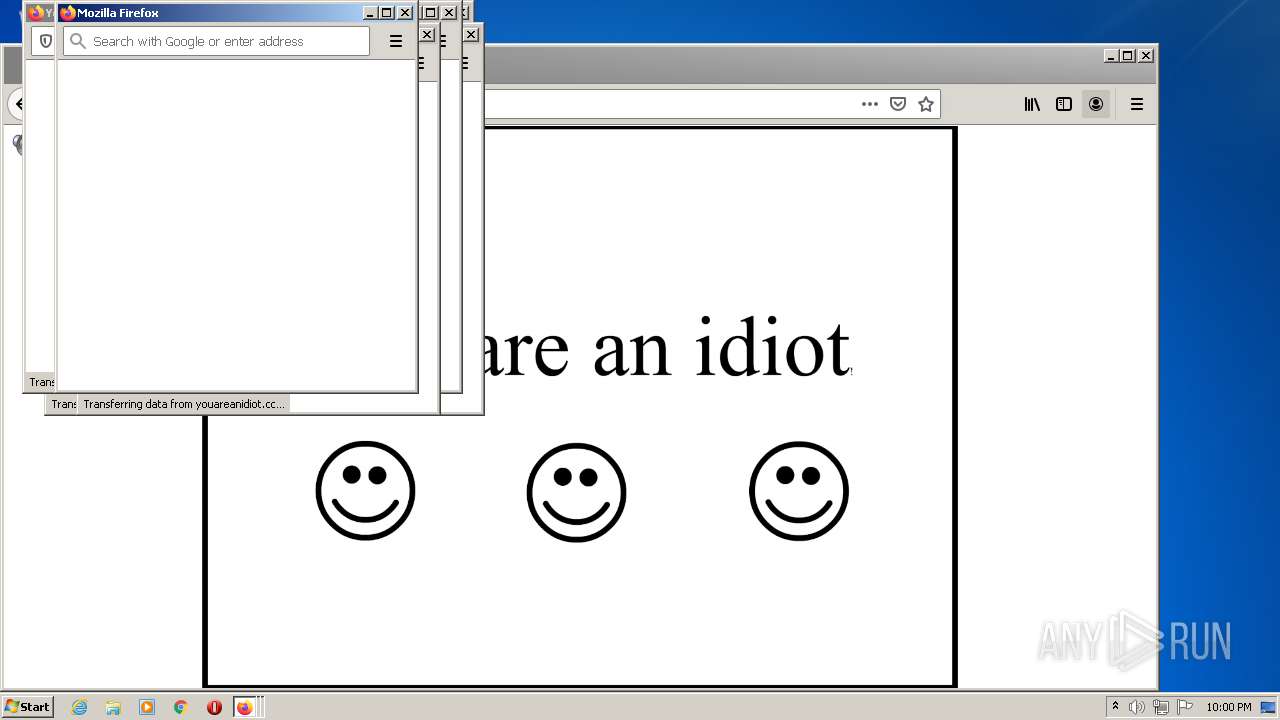
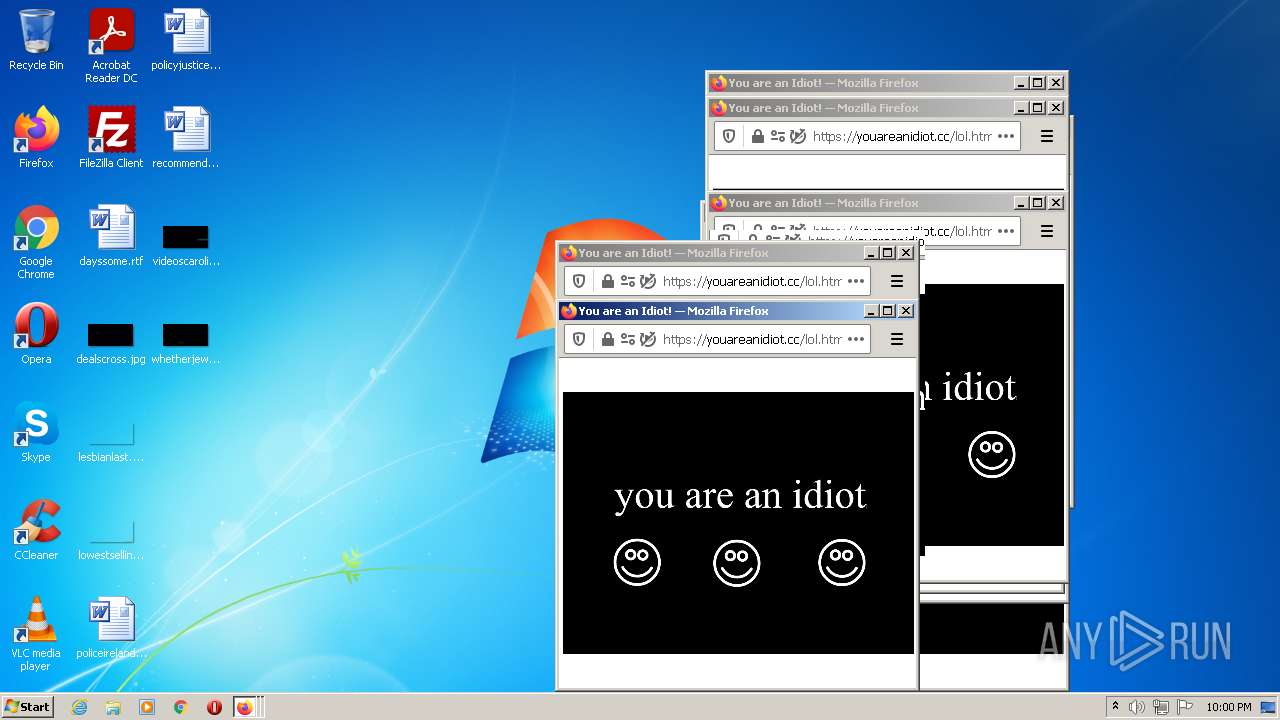
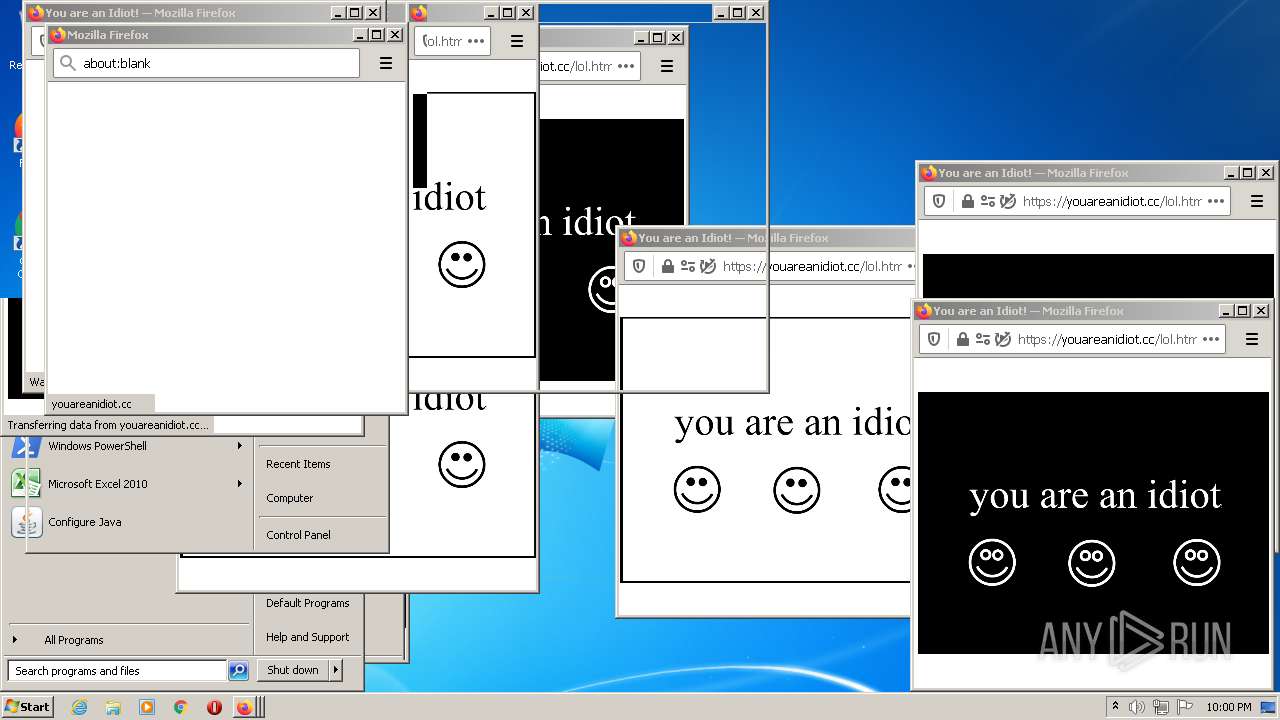
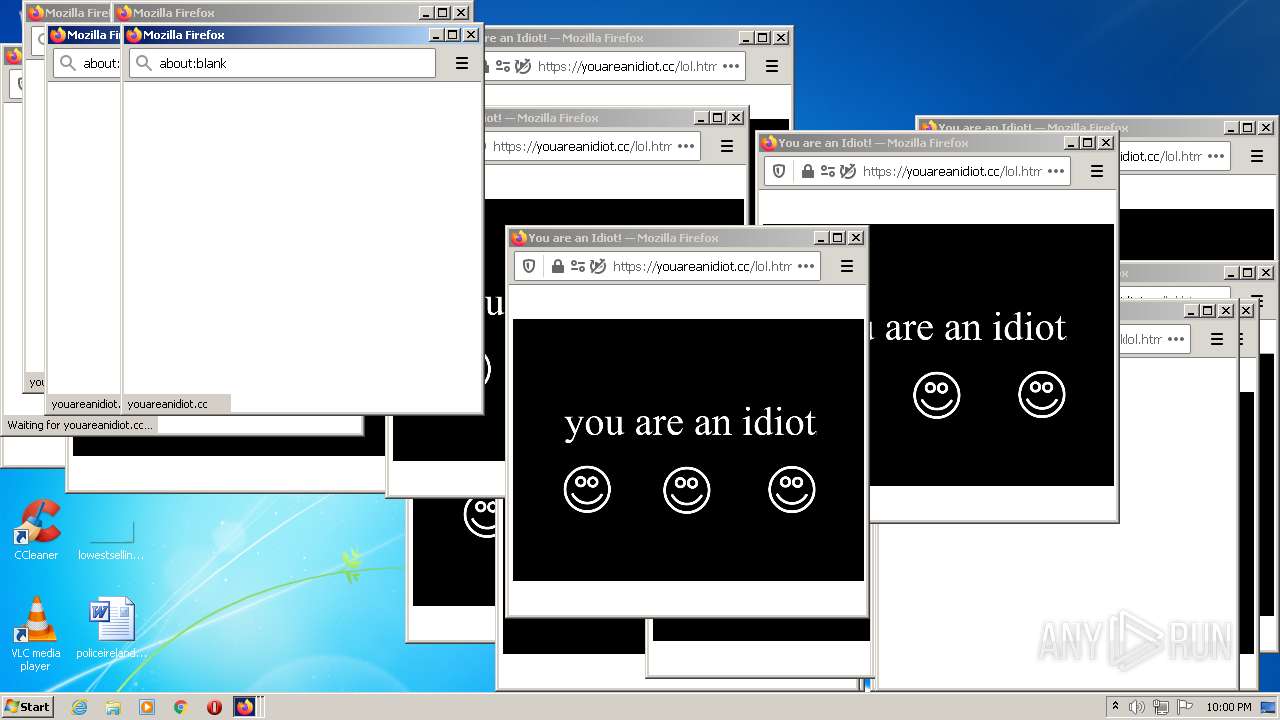
Application launched itself
- iexplore.exe (PID: 1248)
- chrome.exe (PID: 3192)
- firefox.exe (PID: 2600)
- firefox.exe (PID: 2976)
- firefox.exe (PID: 2248)
- firefox.exe (PID: 2896)
Checks Windows Trust Settings
- iexplore.exe (PID: 1248)
- iexplore.exe (PID: 3396)
Reads settings of System Certificates
- iexplore.exe (PID: 1248)
- iexplore.exe (PID: 3396)
- chrome.exe (PID: 3228)
Reads internet explorer settings
- iexplore.exe (PID: 3396)
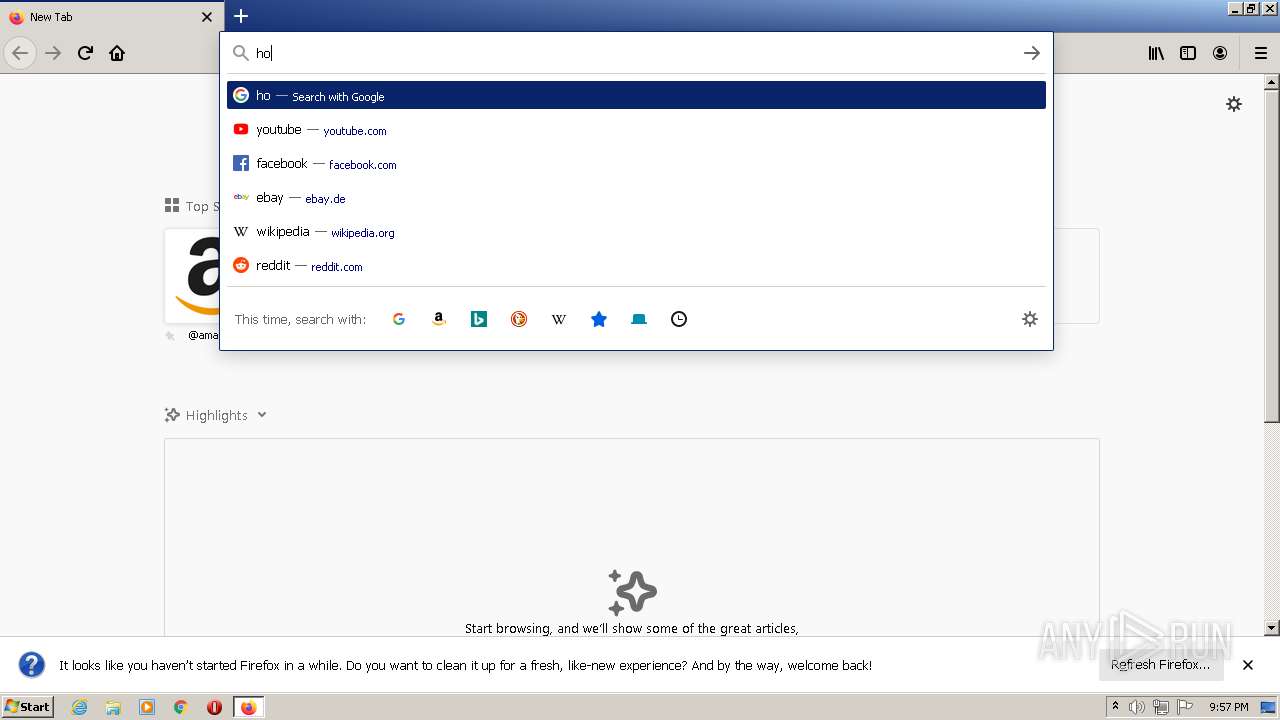
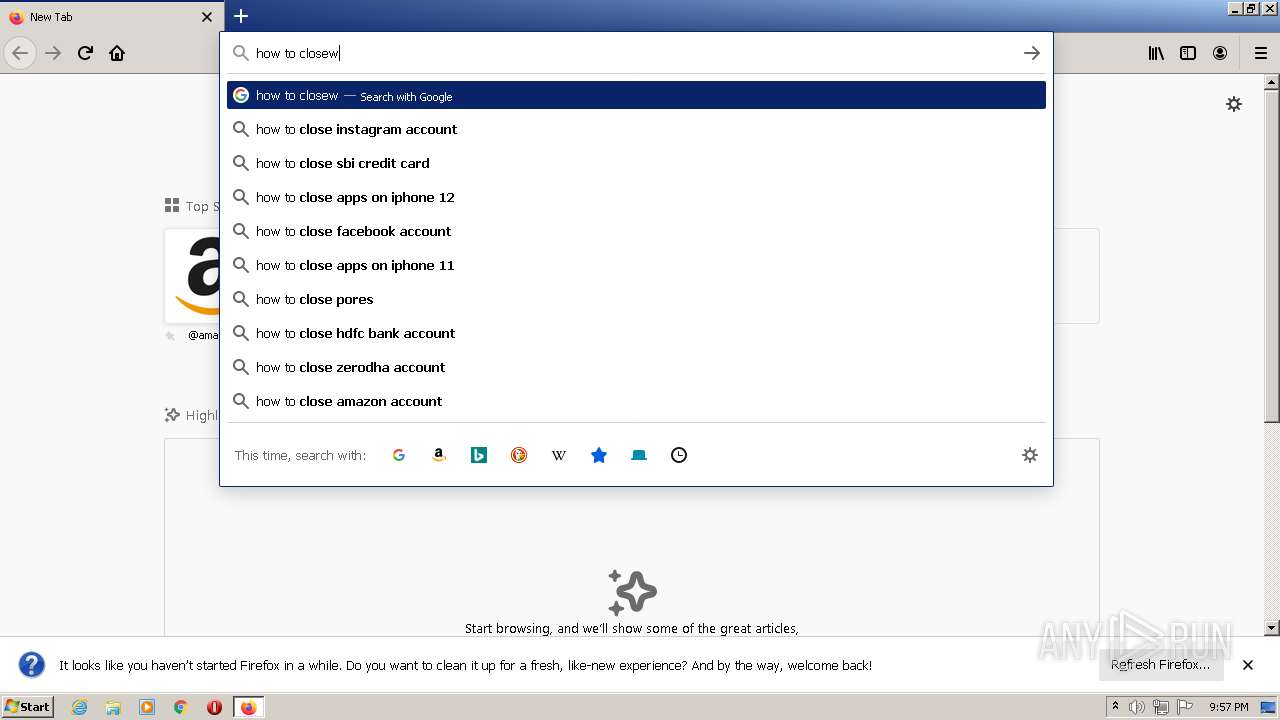
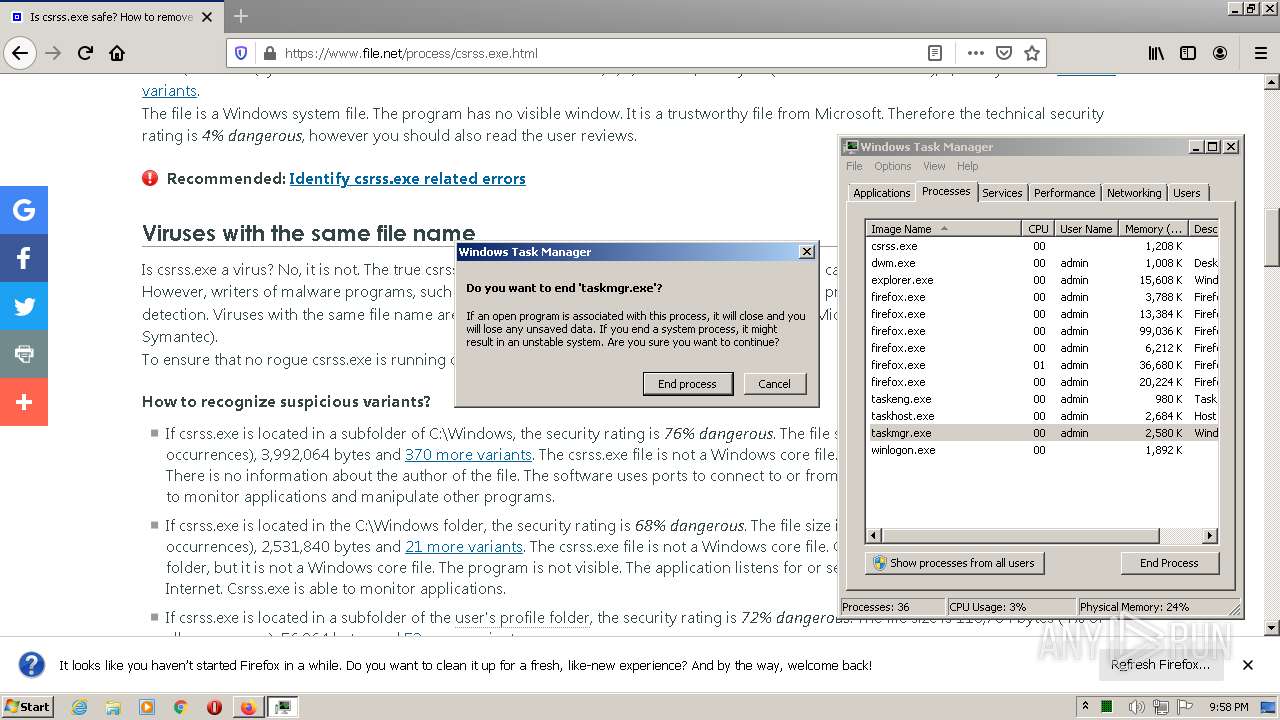
Manual execution by user
- chrome.exe (PID: 3192)
- firefox.exe (PID: 2600)
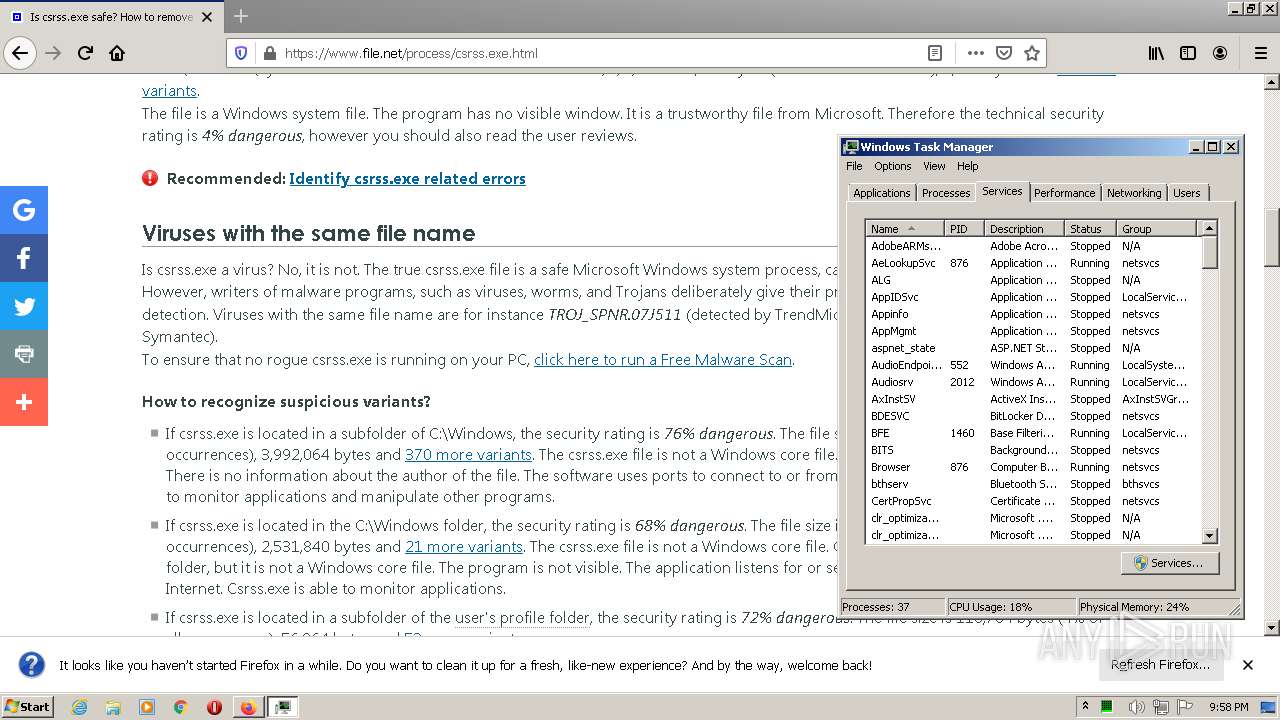
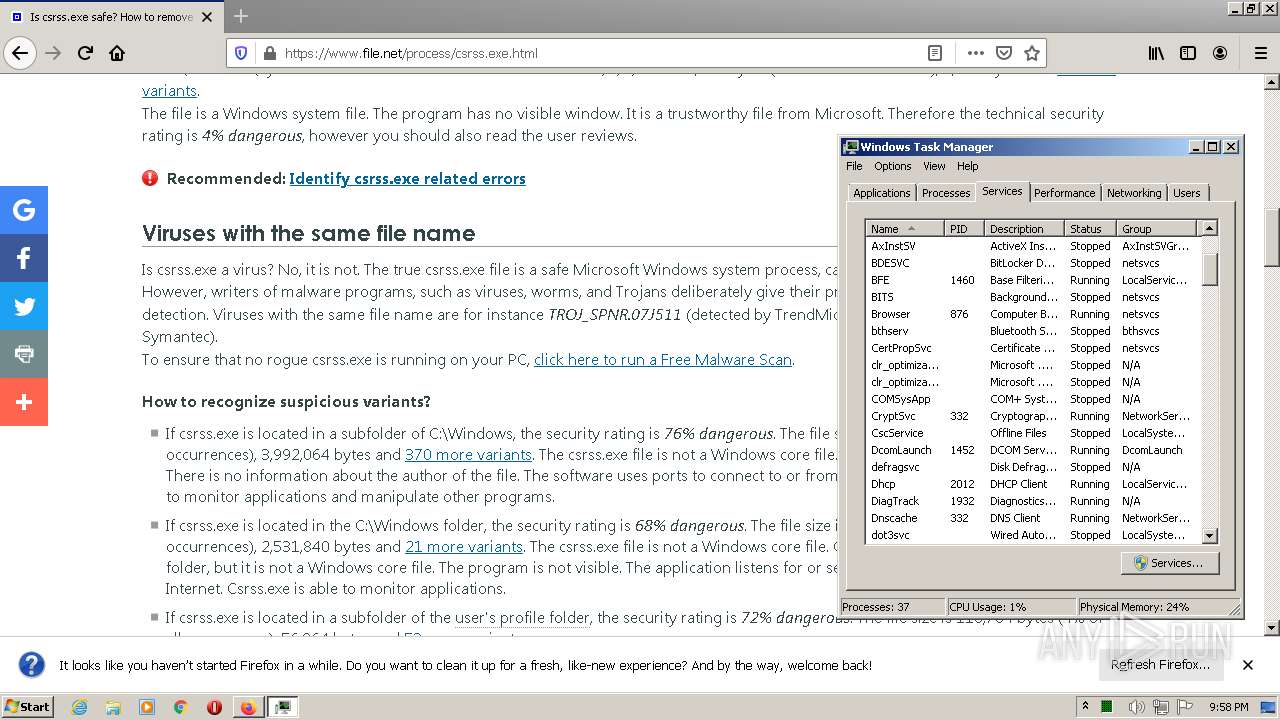
- taskmgr.exe (PID: 408)
- firefox.exe (PID: 2248)
Creates files in the user directory
- iexplore.exe (PID: 3396)
- firefox.exe (PID: 2896)
- firefox.exe (PID: 2976)
Reads the date of Windows installation
- iexplore.exe (PID: 1248)
- chrome.exe (PID: 2972)
- firefox.exe (PID: 2976)
- firefox.exe (PID: 2896)
Reads the hosts file
- chrome.exe (PID: 3192)
- chrome.exe (PID: 3228)
Reads CPU info
- firefox.exe (PID: 2976)
- firefox.exe (PID: 2896)
Creates files in the program directory
- firefox.exe (PID: 2976)
- firefox.exe (PID: 2896)
Dropped object may contain Bitcoin addresses
- firefox.exe (PID: 2976)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
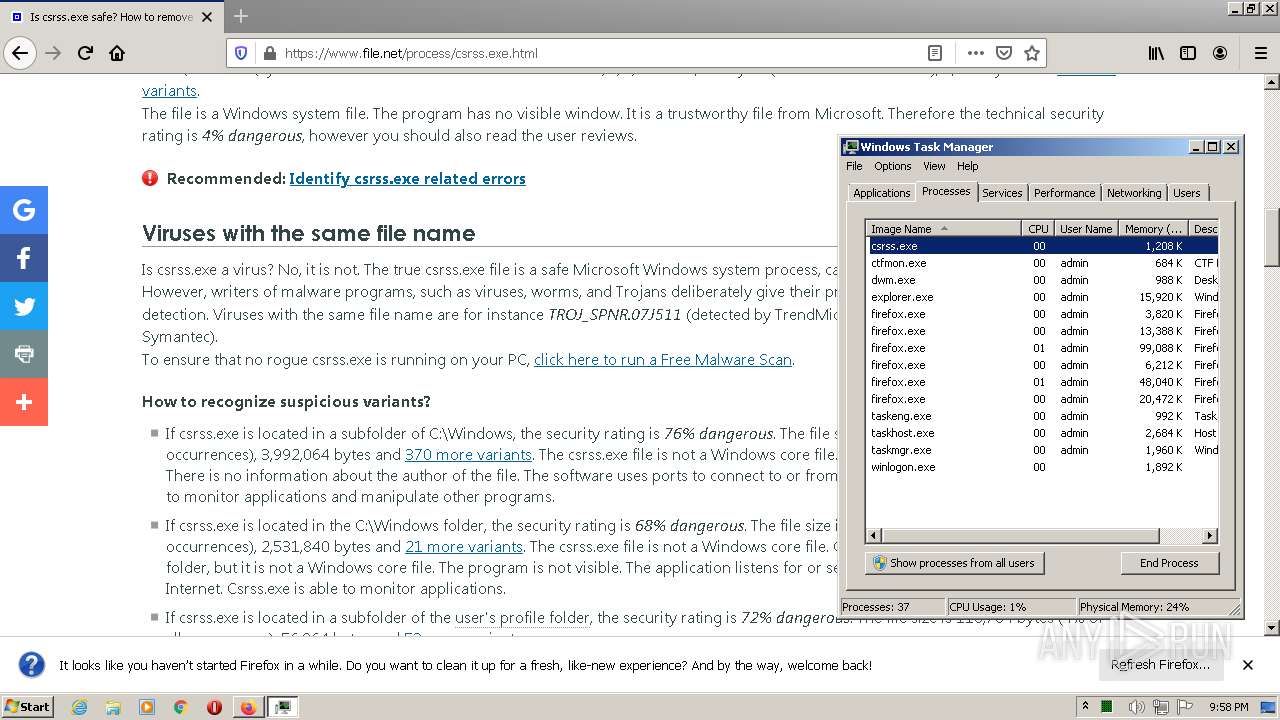
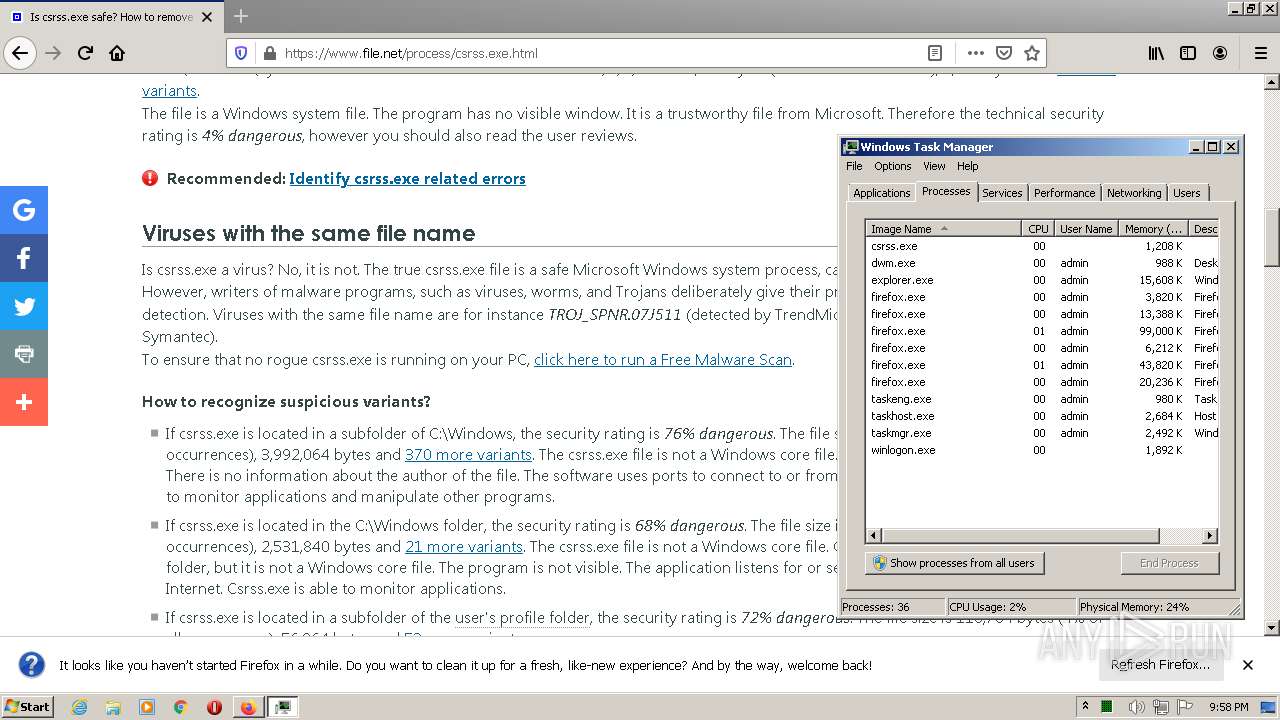
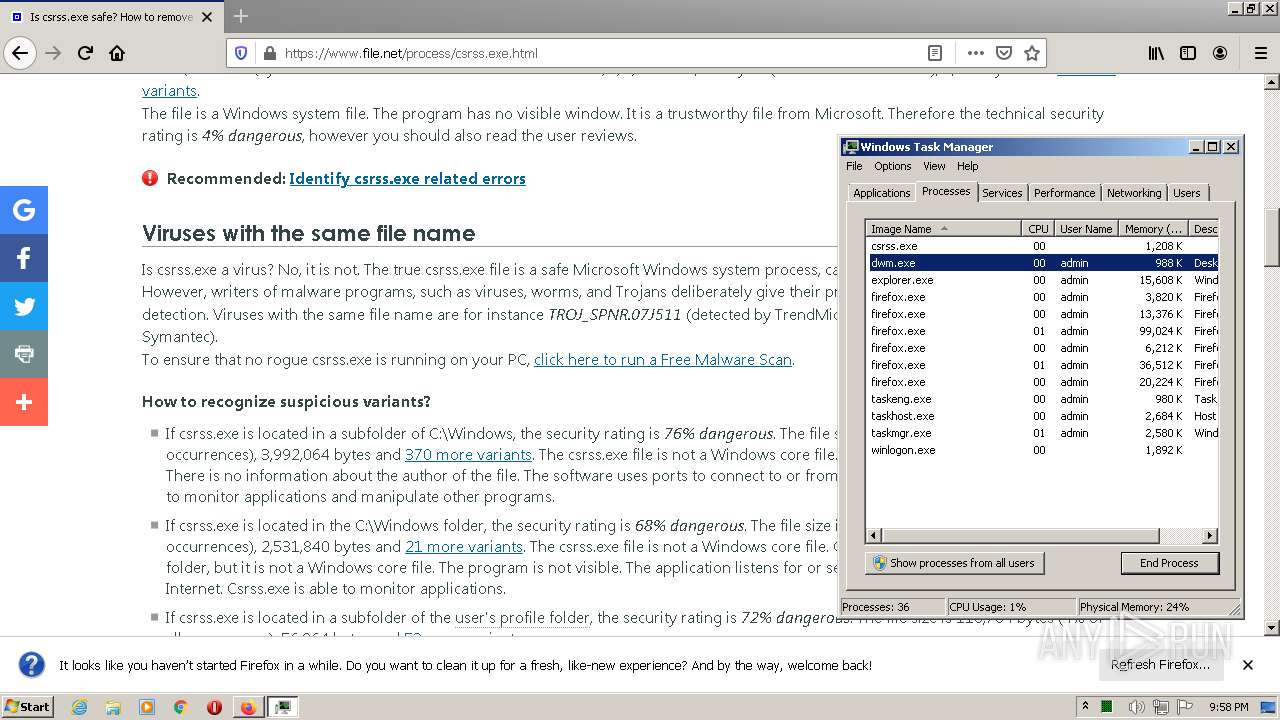
Total processes
89
Monitored processes
51
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 372 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1064,18093312501161254056,13256012979582460426,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=29 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3948 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
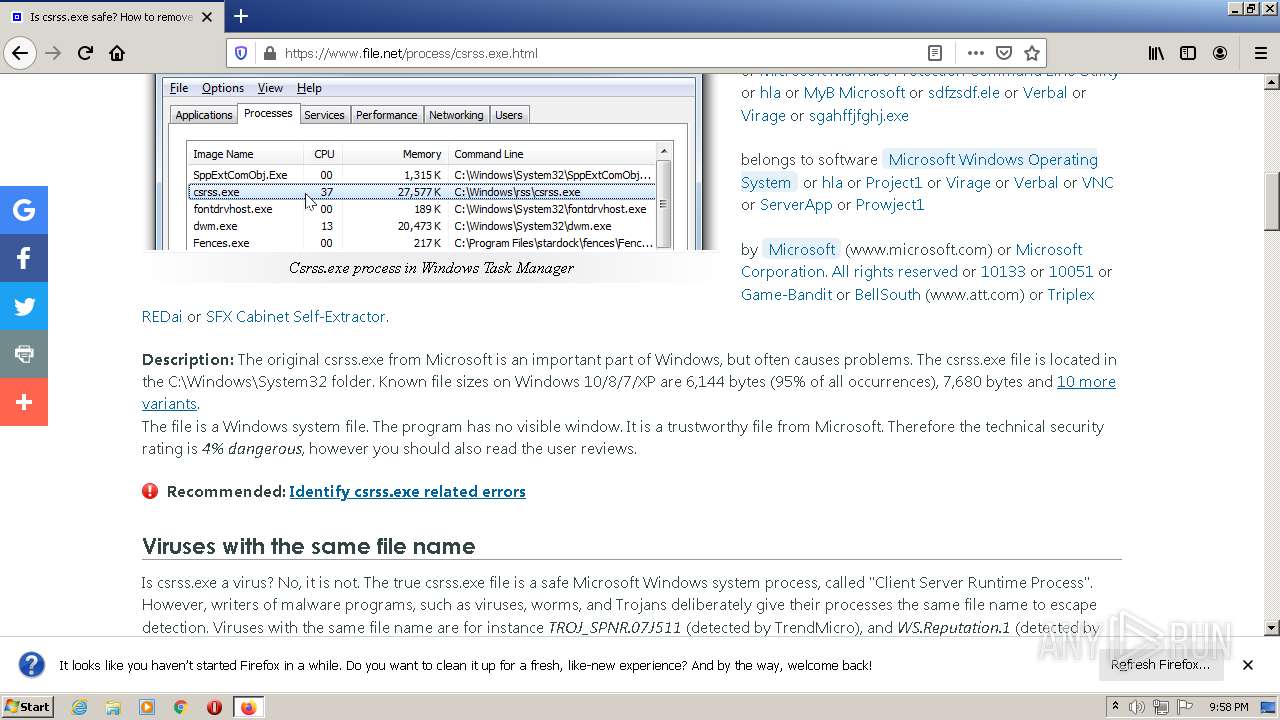
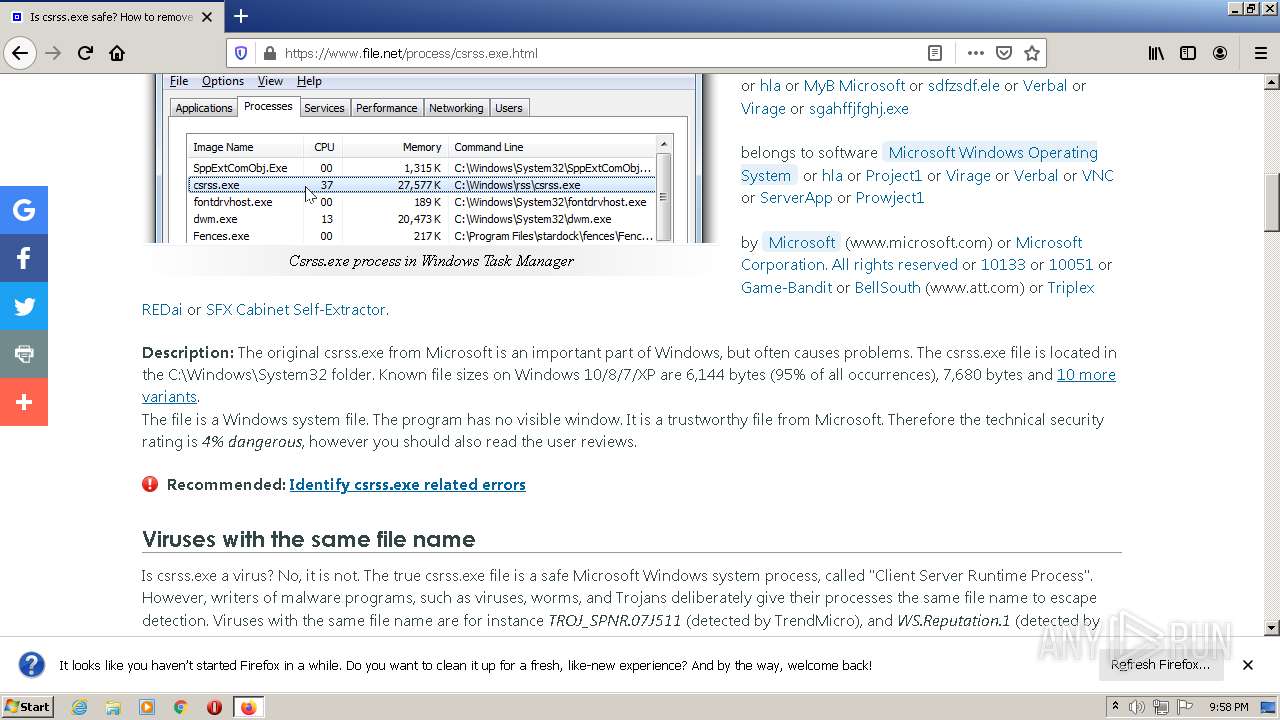
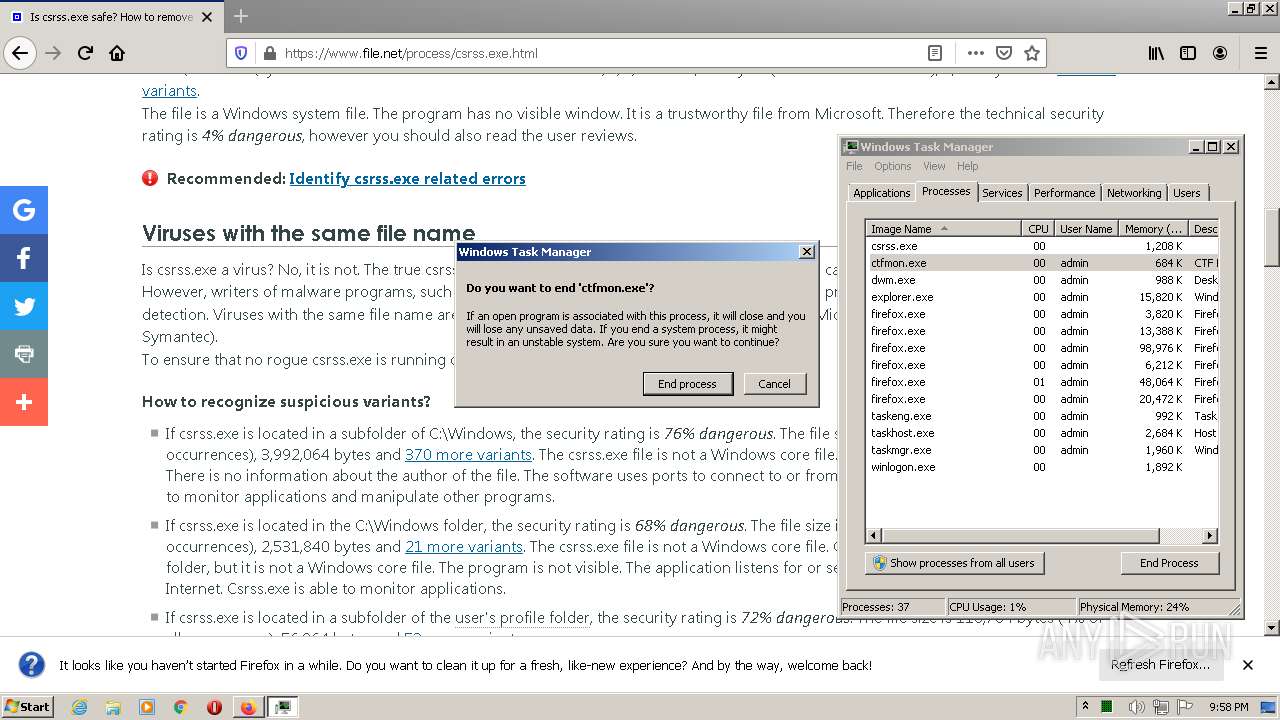
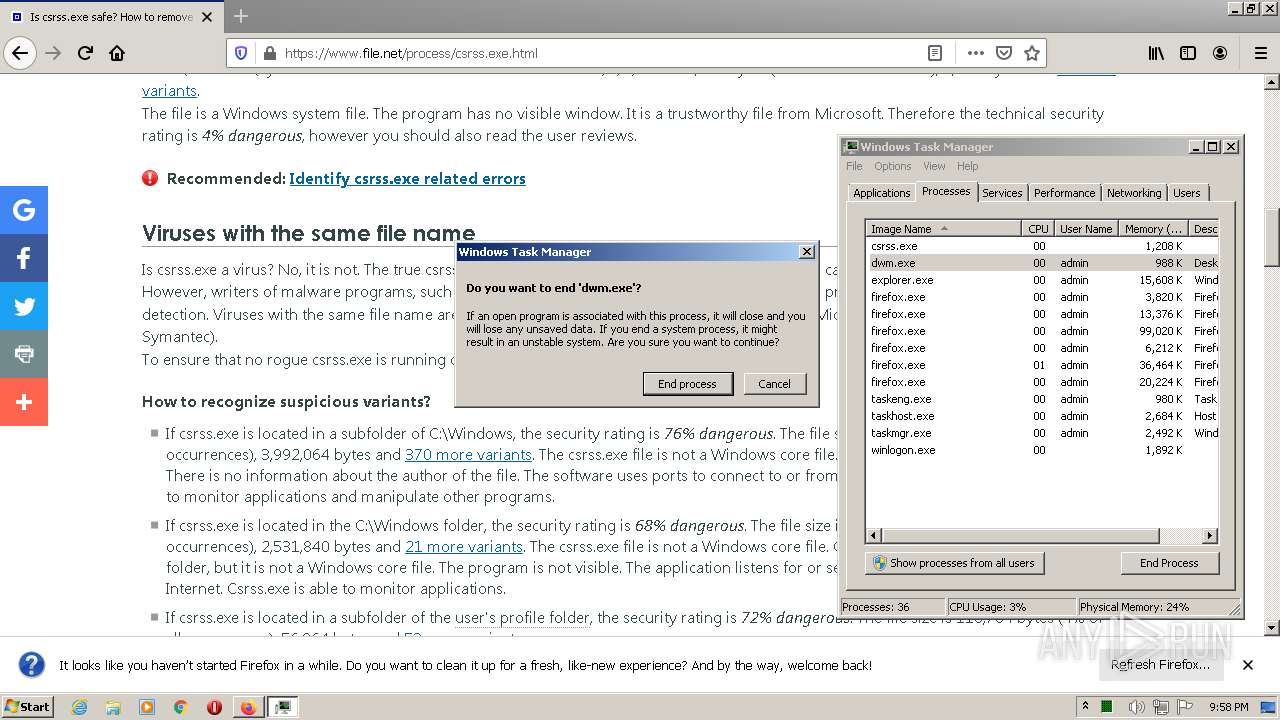
| 408 | "C:\Windows\system32\taskmgr.exe" /4 | C:\Windows\system32\taskmgr.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Task Manager Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 412 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1064,18093312501161254056,13256012979582460426,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2848 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 596 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1064,18093312501161254056,13256012979582460426,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3800 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1128 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1064,18093312501161254056,13256012979582460426,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgAAAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --use-gl=swiftshader-webgl --mojo-platform-channel-handle=1032 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1248 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://www.youtube.com/watch?v=dQw4w9WgXcQ" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1532 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1064,18093312501161254056,13256012979582460426,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3212 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1592 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1064,18093312501161254056,13256012979582460426,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3236 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1808 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1064,18093312501161254056,13256012979582460426,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=4156 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1976 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1064,18093312501161254056,13256012979582460426,131072 --enable-features=PasswordImport --lang=en-US --instant-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1928 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
45 945
Read events
45 668
Write events
274
Delete events
3
Modification events
| (PID) Process: | (1248) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (1248) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (1248) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30940068 | |||
| (PID) Process: | (1248) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (1248) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30940068 | |||
| (PID) Process: | (1248) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1248) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1248) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1248) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1248) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
355
Text files
205
Unknown types
110
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1248 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | der | |
MD5:— | SHA256:— | |||
| 3396 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:— | SHA256:— | |||
| 3396 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 3396 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\0158PGF4.txt | text | |
MD5:— | SHA256:— | |||
| 3396 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\F2DDCD2B5F37625B82E81F4976CEE400_2C7C232DD1DEC4CAEEDF282CDEC7D367 | binary | |
MD5:— | SHA256:— | |||
| 1248 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | binary | |
MD5:— | SHA256:— | |||
| 3396 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\CAF4703619713E3F18D8A9D5D88D6288_A7725538C46DE2D0088EE44974E2CEBA | binary | |
MD5:— | SHA256:— | |||
| 3396 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\A16C6C16D94F76E0808C087DFC657D99_72743A90D6191511AB3814E7FF957879 | binary | |
MD5:— | SHA256:— | |||
| 3396 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\F2DDCD2B5F37625B82E81F4976CEE400_2C7C232DD1DEC4CAEEDF282CDEC7D367 | der | |
MD5:— | SHA256:— | |||
| 3396 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\CAF4703619713E3F18D8A9D5D88D6288_A7725538C46DE2D0088EE44974E2CEBA | der | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
49
TCP/UDP connections
141
DNS requests
266
Threats
11
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1248 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
3396 | iexplore.exe | GET | 200 | 142.250.185.163:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQCv%2F46iPAj3HwoAAAABLgd6 | US | der | 472 b | whitelisted |
3396 | iexplore.exe | GET | 200 | 142.250.185.163:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | der | 724 b | whitelisted |
3396 | iexplore.exe | GET | 200 | 142.250.185.163:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQCUwk%2Bg6jTdGwoAAAABLgJT | US | der | 472 b | whitelisted |
3396 | iexplore.exe | GET | 200 | 142.250.185.163:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEBZHO7LF43PWCgAAAAEuB4I%3D | US | der | 471 b | whitelisted |
3396 | iexplore.exe | GET | 200 | 142.250.185.163:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQDIRy5Lqyj5dAoAAAABLgV%2F | US | der | 472 b | whitelisted |
3396 | iexplore.exe | GET | 200 | 142.250.185.163:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQDKa002niAMOQoAAAABLgV0 | US | der | 472 b | whitelisted |
3396 | iexplore.exe | GET | 200 | 142.250.185.163:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQDfzJPL1j6yvwoAAAABLgJc | US | der | 472 b | whitelisted |
3396 | iexplore.exe | GET | 200 | 142.250.185.163:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEG0ZFurn2tviCgAAAAExW20%3D | US | der | 471 b | whitelisted |
2976 | firefox.exe | POST | 200 | 142.250.185.163:80 | http://ocsp.pki.goog/gts1c3 | US | der | 472 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3396 | iexplore.exe | 142.250.185.174:443 | www.youtube.com | Google Inc. | US | whitelisted |
3396 | iexplore.exe | 178.79.242.128:80 | ctldl.windowsupdate.com | Limelight Networks, Inc. | DE | malicious |
1248 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
3396 | iexplore.exe | 142.250.185.163:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
1248 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3396 | iexplore.exe | 142.250.186.42:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3396 | iexplore.exe | 142.250.186.54:443 | i.ytimg.com | Google Inc. | US | suspicious |
3396 | iexplore.exe | 216.58.212.163:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3396 | iexplore.exe | 173.194.139.9:443 | r4---sn-aigzrn7k.googlevideo.com | Google Inc. | US | whitelisted |
3396 | iexplore.exe | 142.250.185.100:443 | www.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.youtube.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
i.ytimg.com |
| whitelisted |
r4---sn-aigzrn7k.googlevideo.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
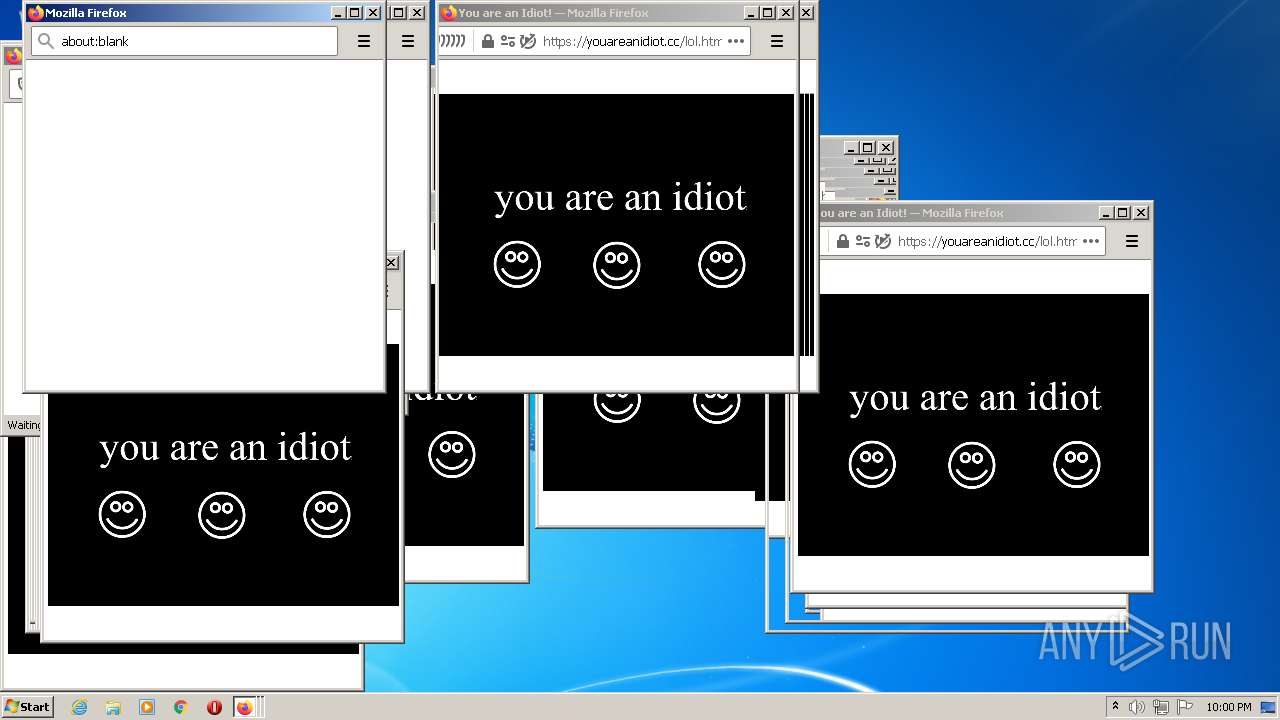
2976 | firefox.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
2976 | firefox.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
2976 | firefox.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
2976 | firefox.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
2896 | firefox.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
2896 | firefox.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
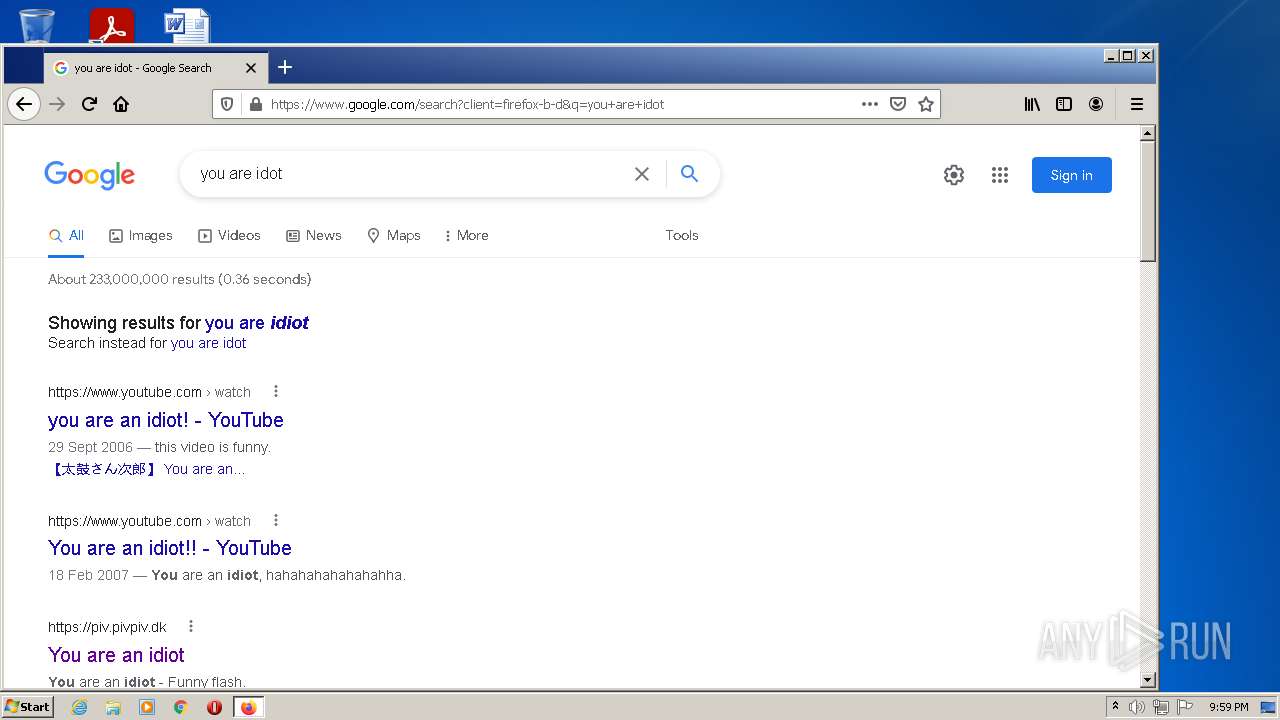
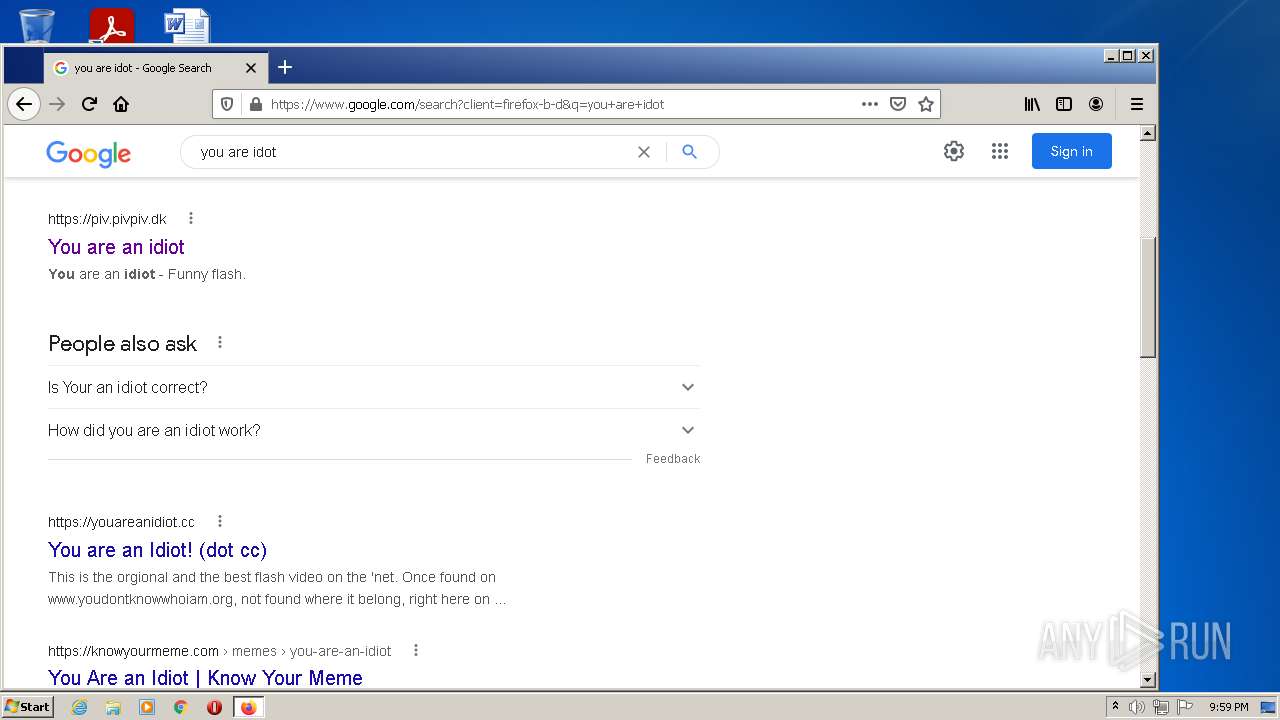
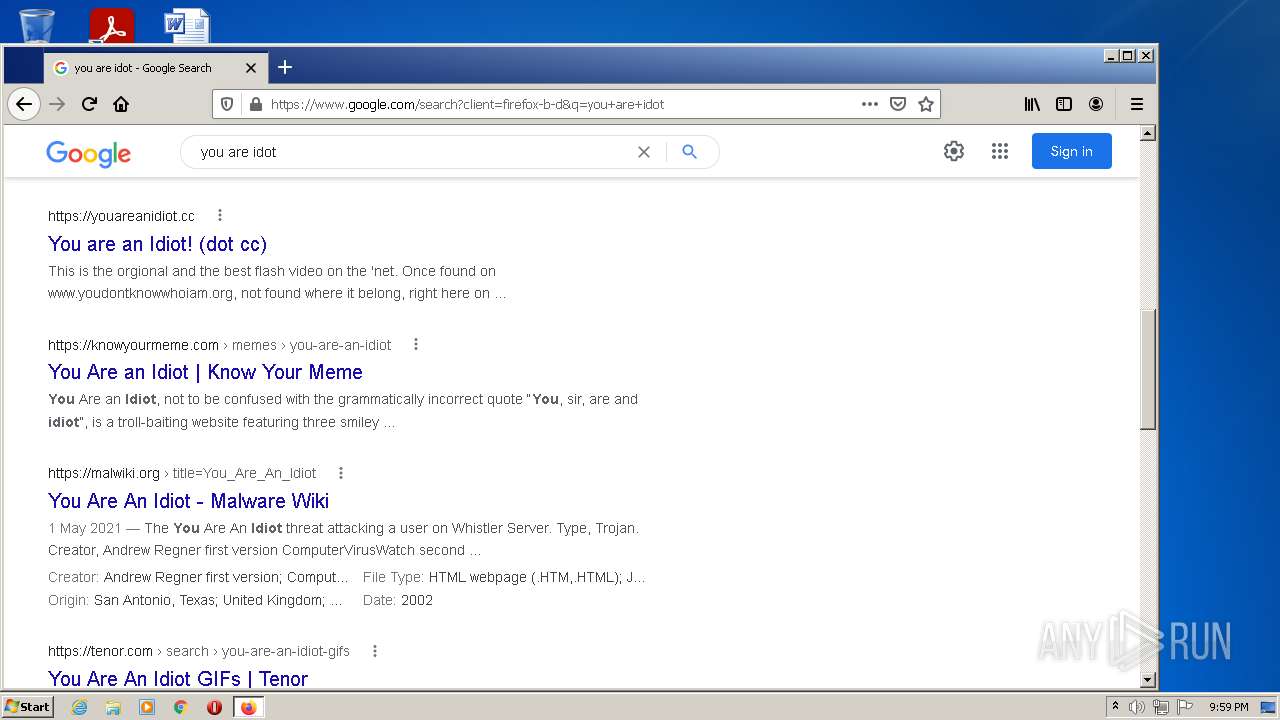
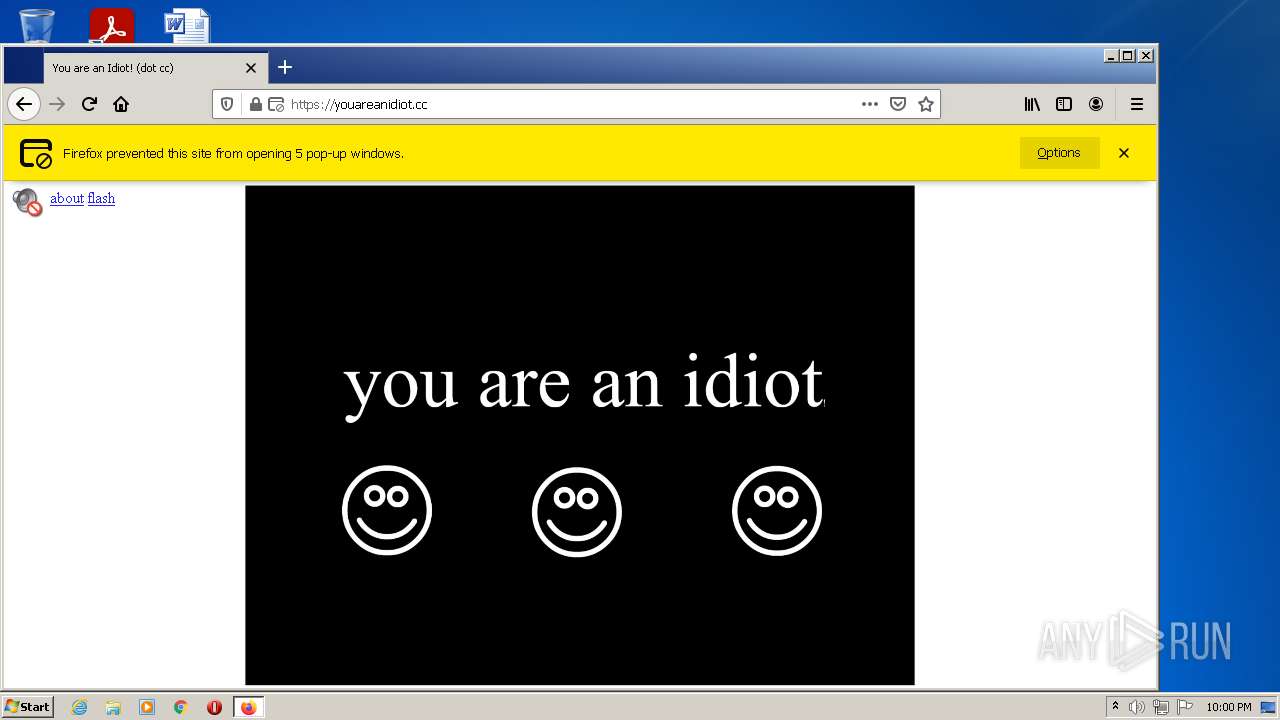
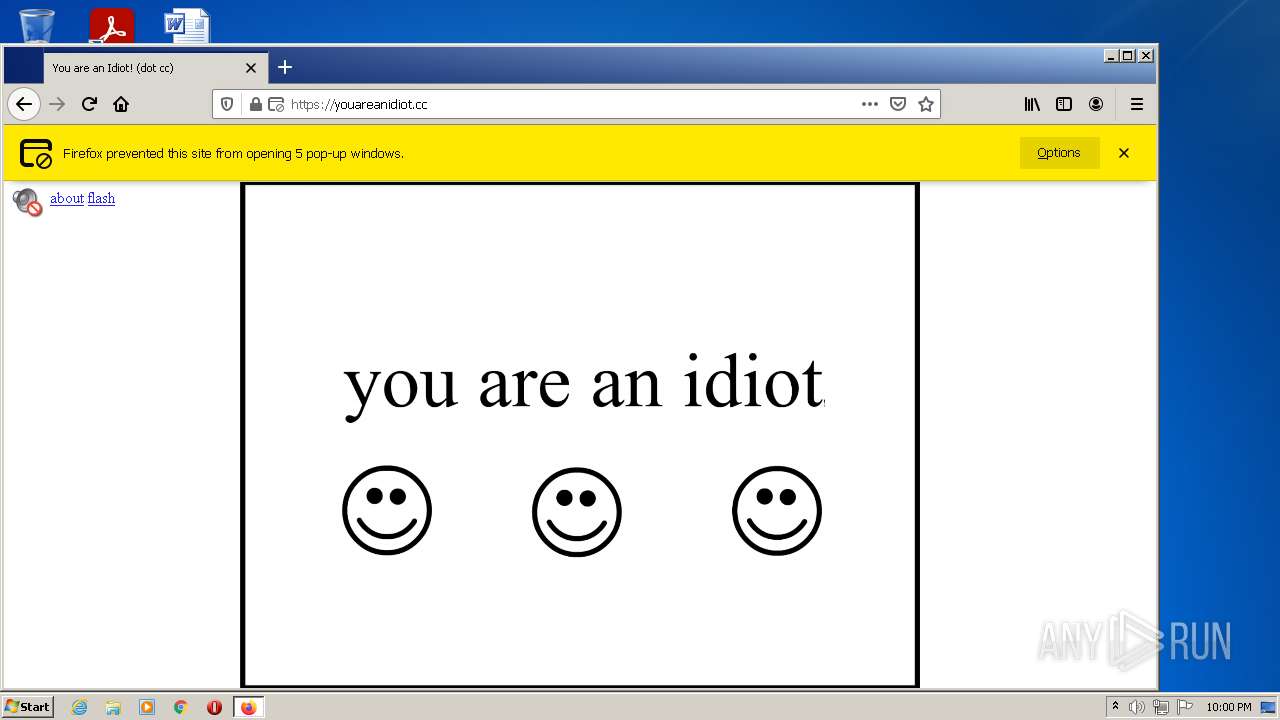
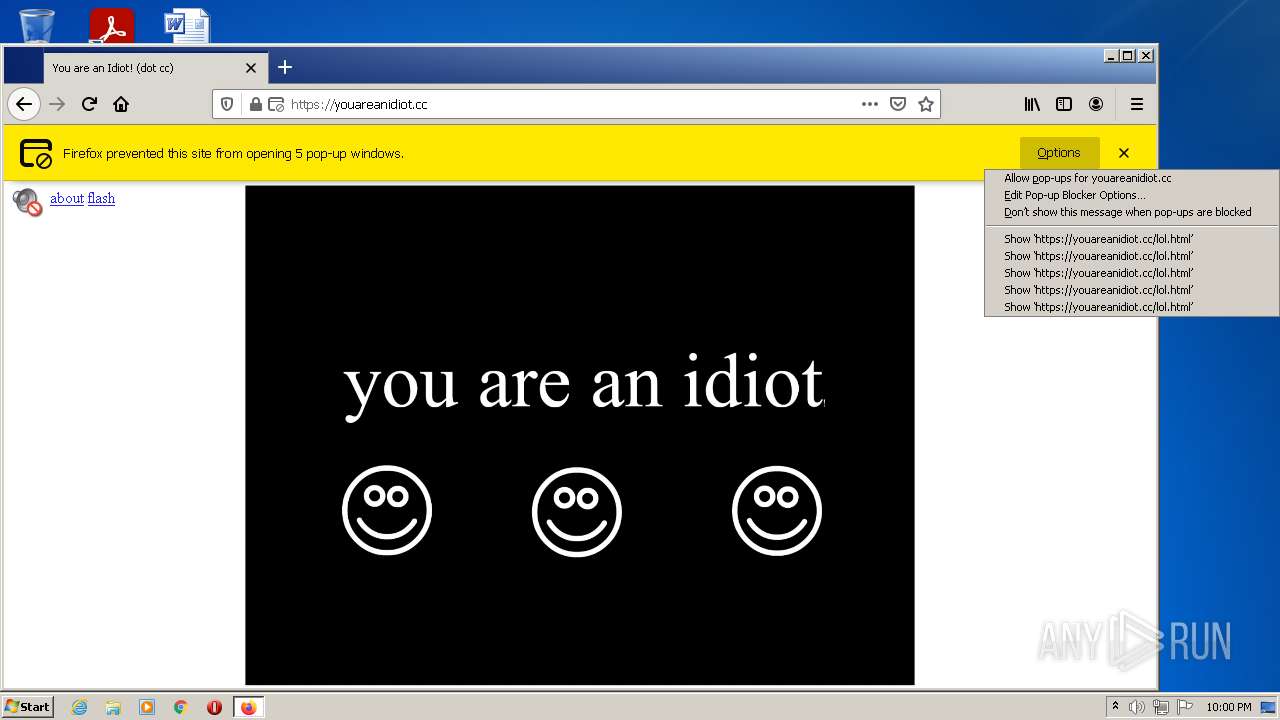
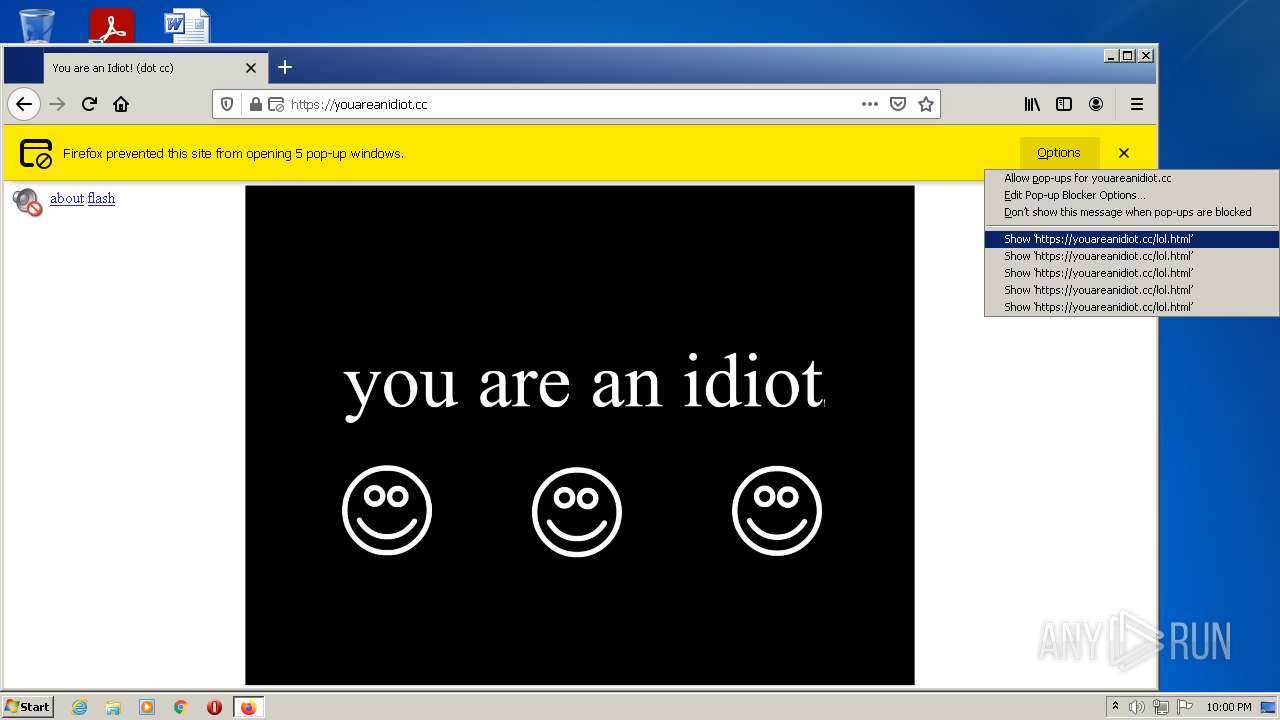
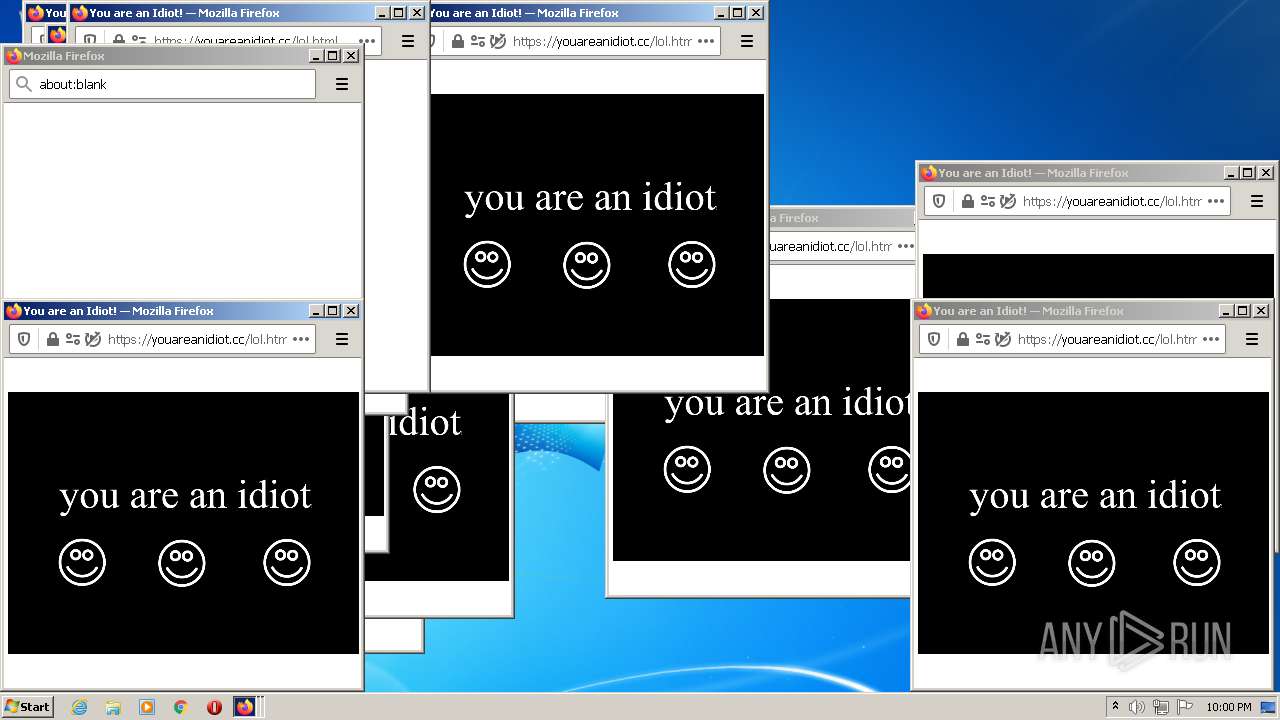
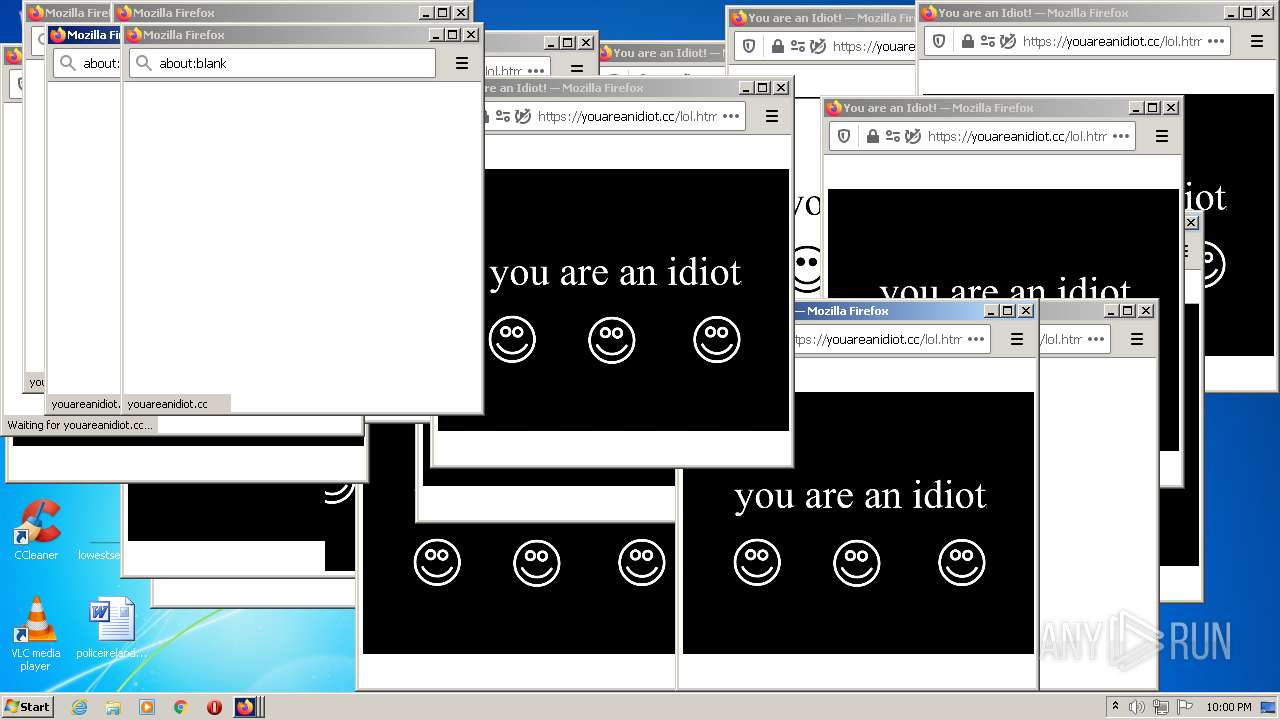
— | — | Potentially Bad Traffic | ET DNS Query for .cc TLD |
— | — | Potentially Bad Traffic | ET DNS Query for .cc TLD |
— | — | Potentially Bad Traffic | ET DNS Query for .cc TLD |
2896 | firefox.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |