| File name: | 0725b370325fc8144d5af7087cf6a97131e72f6b3dede2b42bb92290e9944a35.bin.gz |
| Full analysis: | https://app.any.run/tasks/d4c0339d-01ec-42e7-a66f-ea508018d216 |
| Verdict: | Malicious activity |
| Analysis date: | May 15, 2019, 14:56:44 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/gzip |
| File info: | gzip compressed data, max compression, from Unix |
| MD5: | 8E2B3DB0C9E3B725EFA45AF9AF20379F |
| SHA1: | 258B9FFE503B08DEA703D21AE600BDAF60BC480E |
| SHA256: | 0421B90D58D8D47B5FB3656449351BBEA58AA56FA7CB87B5933FF0E5AA295978 |
| SSDEEP: | 24576:acN7yi/XDAjx+voqrouFuJtP7y62JoRGZ5QsfMXo7VPHma0v9gwpbKpppn:a2OiroqrouFYtP7y6OoS5dWop/GVbUTn |
MALICIOUS
Application was dropped or rewritten from another process
- 0725b370325fc8144d5af7087cf6a97131e72f6b3dede2b42bb92290e9944a35.bin.exe (PID: 2520)
Changes the autorun value in the registry
- 0725b370325fc8144d5af7087cf6a97131e72f6b3dede2b42bb92290e9944a35.bin.exe (PID: 2520)
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 3572)
- 0725b370325fc8144d5af7087cf6a97131e72f6b3dede2b42bb92290e9944a35.bin.exe (PID: 2520)
Adds new firewall rule via NETSH.EXE
- 0725b370325fc8144d5af7087cf6a97131e72f6b3dede2b42bb92290e9944a35.bin.exe (PID: 2520)
SUSPICIOUS
Checks for external IP
- 0725b370325fc8144d5af7087cf6a97131e72f6b3dede2b42bb92290e9944a35.bin.exe (PID: 2520)
Reads Environment values
- 0725b370325fc8144d5af7087cf6a97131e72f6b3dede2b42bb92290e9944a35.bin.exe (PID: 2520)
Creates files in the program directory
- 0725b370325fc8144d5af7087cf6a97131e72f6b3dede2b42bb92290e9944a35.bin.exe (PID: 2520)
Changes tracing settings of the file or console
- 0725b370325fc8144d5af7087cf6a97131e72f6b3dede2b42bb92290e9944a35.bin.exe (PID: 2520)
Executable content was dropped or overwritten
- 0725b370325fc8144d5af7087cf6a97131e72f6b3dede2b42bb92290e9944a35.bin.exe (PID: 2520)
Uses NETSH.EXE for network configuration
- 0725b370325fc8144d5af7087cf6a97131e72f6b3dede2b42bb92290e9944a35.bin.exe (PID: 2520)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .z/gz/gzip | | | GZipped data (100) |
|---|
EXIF
ZIP
| Compression: | Deflated |
|---|---|
| Flags: | (none) |
| ModifyDate: | 0000:00:00 00:00:00 |
| ExtraFlags: | Maximum Compression |
| OperatingSystem: | Unix |
Total processes
39
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2520 | "C:\Users\admin\Desktop\0725b370325fc8144d5af7087cf6a97131e72f6b3dede2b42bb92290e9944a35.bin.exe" | C:\Users\admin\Desktop\0725b370325fc8144d5af7087cf6a97131e72f6b3dede2b42bb92290e9944a35.bin.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
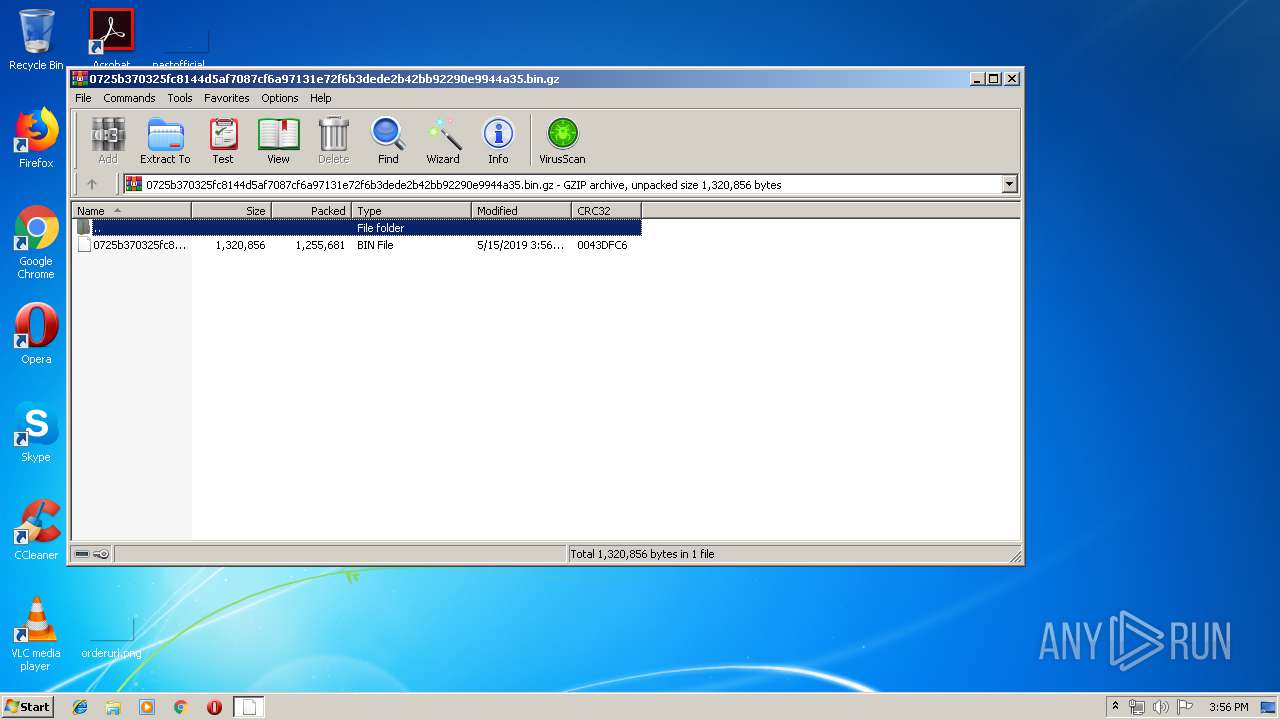
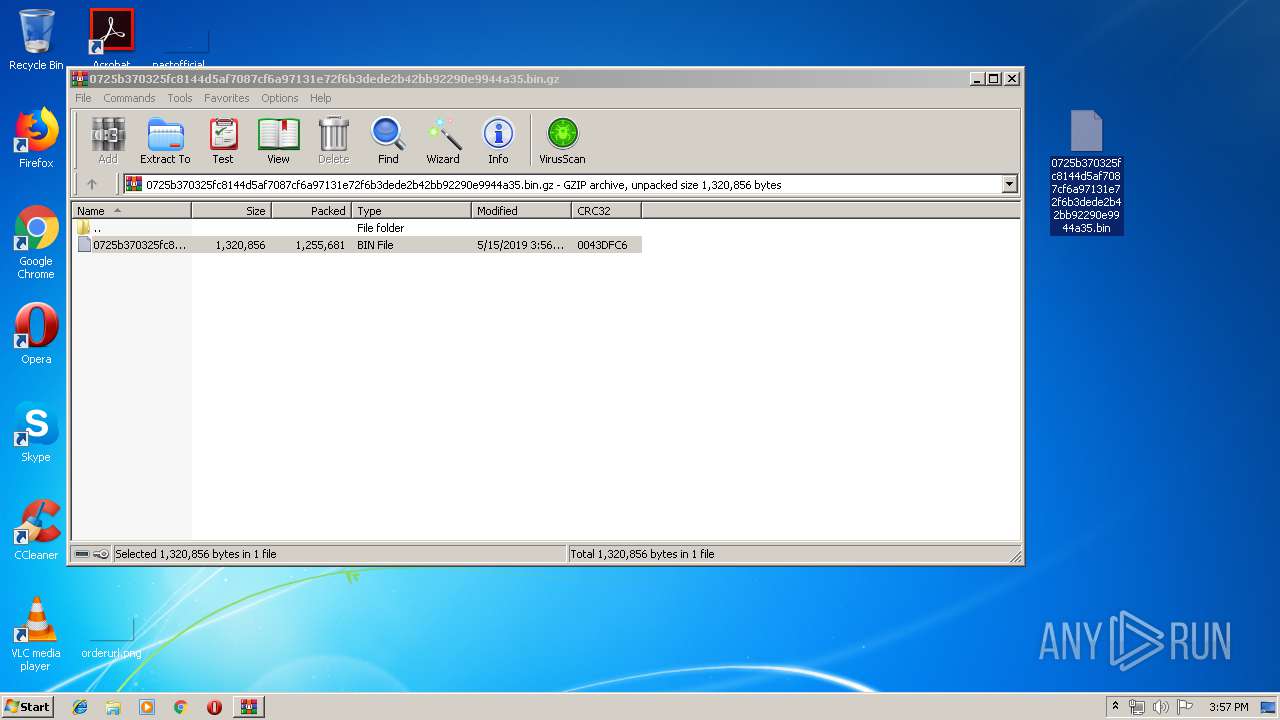
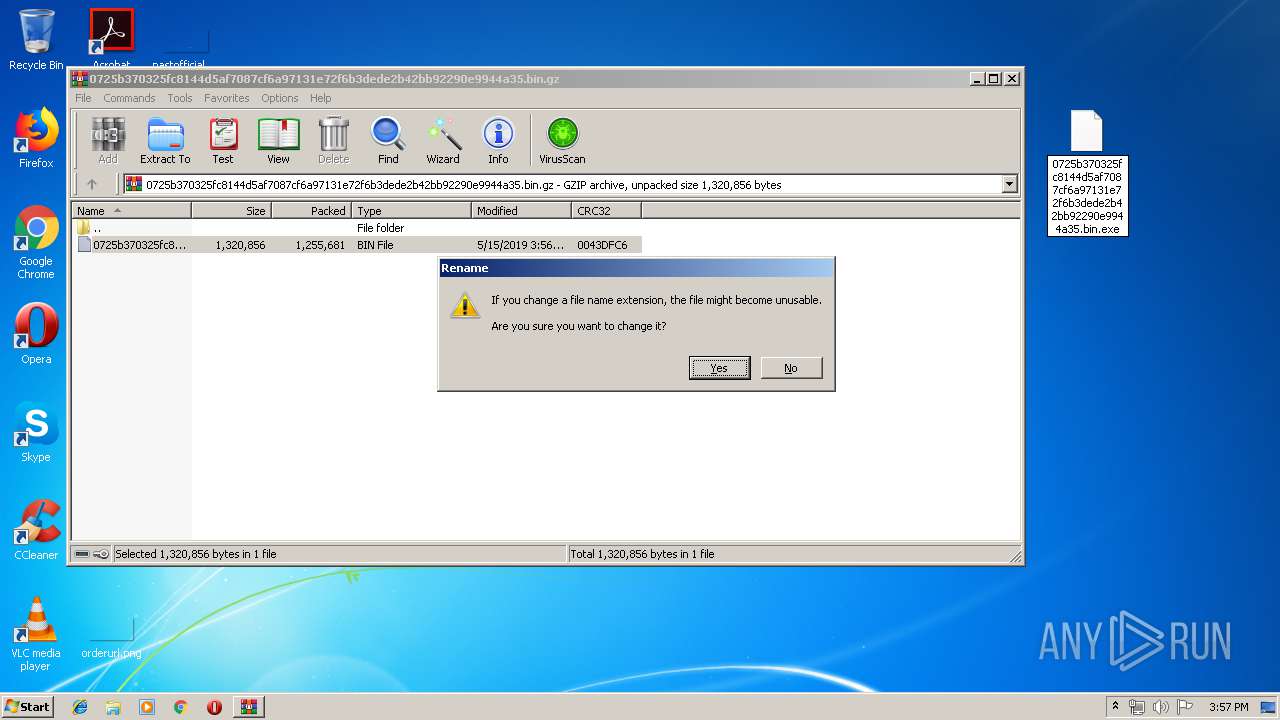
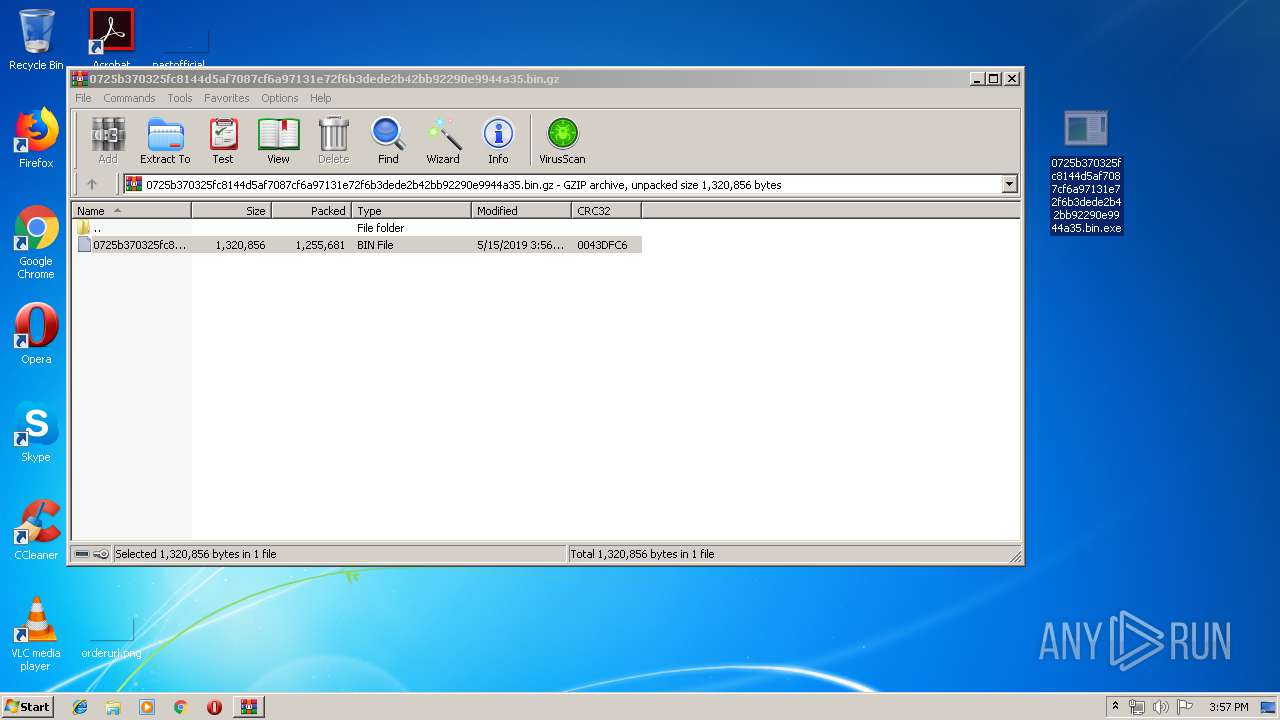
| 2964 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\0725b370325fc8144d5af7087cf6a97131e72f6b3dede2b42bb92290e9944a35.bin.gz" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3572 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe4_ Global\UsGthrCtrlFltPipeMssGthrPipe4 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3908 | "netsh.exe" advfirewall firewall add rule name="kraken.exe" profile=any enable=yes DIR=in program="C:\Users\admin\Desktop\0725b370325fc8144d5af7087cf6a97131e72f6b3dede2b42bb92290e9944a35.bin.exe" Action=Allow | C:\Windows\system32\netsh.exe | — | 0725b370325fc8144d5af7087cf6a97131e72f6b3dede2b42bb92290e9944a35.bin.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Network Command Shell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
531
Read events
449
Write events
82
Delete events
0
Modification events
| (PID) Process: | (2964) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2964) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2964) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2964) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\0725b370325fc8144d5af7087cf6a97131e72f6b3dede2b42bb92290e9944a35.bin.gz | |||
| (PID) Process: | (2964) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2964) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2964) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2964) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2520) 0725b370325fc8144d5af7087cf6a97131e72f6b3dede2b42bb92290e9944a35.bin.exe | Key: | HKEY_CLASSES_ROOT\CID\{D3558E25-821F3-72C3-8A52-54A482A54739}\36A92875 |
| Operation: | write | Name: | 2 |
Value: 159021122206117200165108097018043012143072010113 | |||
| (PID) Process: | (2520) 0725b370325fc8144d5af7087cf6a97131e72f6b3dede2b42bb92290e9944a35.bin.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
Executable files
1
Suspicious files
1
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2964 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2964.23095\0725b370325fc8144d5af7087cf6a97131e72f6b3dede2b42bb92290e9944a35.bin | — | |
MD5:— | SHA256:— | |||
| 2520 | 0725b370325fc8144d5af7087cf6a97131e72f6b3dede2b42bb92290e9944a35.bin.exe | C:\Users\admin\Desktop\loader.dll | executable | |
MD5:— | SHA256:— | |||
| 2520 | 0725b370325fc8144d5af7087cf6a97131e72f6b3dede2b42bb92290e9944a35.bin.exe | C:\ProgramData\Isolated Storage\36A92875\90424E7E | binary | |
MD5:BF565BDFC5DD1697D8D225BC9DBFFEC0 | SHA256:01D8EB441C0B654A122F7A631555D752427E487D2307139E91B1F1E4E77DE93F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
120
DNS requests
6
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2520 | 0725b370325fc8144d5af7087cf6a97131e72f6b3dede2b42bb92290e9944a35.bin.exe | GET | 200 | 104.20.16.242:80 | http://icanhazip.com/ | US | text | 12 b | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 212.92.115.107:24185 | — | NForce Entertainment B.V. | NL | unknown |
2520 | 0725b370325fc8144d5af7087cf6a97131e72f6b3dede2b42bb92290e9944a35.bin.exe | 104.20.16.242:80 | icanhazip.com | Cloudflare Inc | US | shared |
2520 | 0725b370325fc8144d5af7087cf6a97131e72f6b3dede2b42bb92290e9944a35.bin.exe | 185.64.89.42:33445 | mrflibble.c4.ee | Pulsant (Scotland) Ltd | GB | unknown |
— | — | 108.61.165.198:33445 | — | Choopa, LLC | NL | unknown |
2520 | 0725b370325fc8144d5af7087cf6a97131e72f6b3dede2b42bb92290e9944a35.bin.exe | 108.61.165.198:33445 | — | Choopa, LLC | NL | unknown |
— | — | 139.162.217.110:33445 | — | Linode, LLC | GB | unknown |
2520 | 0725b370325fc8144d5af7087cf6a97131e72f6b3dede2b42bb92290e9944a35.bin.exe | 139.162.217.110:33445 | — | Linode, LLC | GB | unknown |
— | — | 83.137.53.211:1813 | d4rk4.ru | SVS Communication | RU | unknown |
2520 | 0725b370325fc8144d5af7087cf6a97131e72f6b3dede2b42bb92290e9944a35.bin.exe | 83.137.53.211:1813 | d4rk4.ru | SVS Communication | RU | unknown |
— | — | 138.94.71.250:33445 | home.vikingmakt.com.br | Intervel Informatica Ltda | BR | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
icanhazip.com |
| shared |
mrflibble.c4.ee |
| unknown |
d4rk4.ru |
| malicious |
home.vikingmakt.com.br |
| unknown |
tox.deadteam.org |
| unknown |
biribiri.org |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2520 | 0725b370325fc8144d5af7087cf6a97131e72f6b3dede2b42bb92290e9944a35.bin.exe | Attempted Information Leak | ET POLICY IP Check Domain (icanhazip. com in HTTP Host) |
2520 | 0725b370325fc8144d5af7087cf6a97131e72f6b3dede2b42bb92290e9944a35.bin.exe | A Network Trojan was detected | MALWARE [PTsecurity] Kraken |