| download: | vrc.exe |
| Full analysis: | https://app.any.run/tasks/a37ddc75-a465-48b5-ac67-596f3cc0380f |
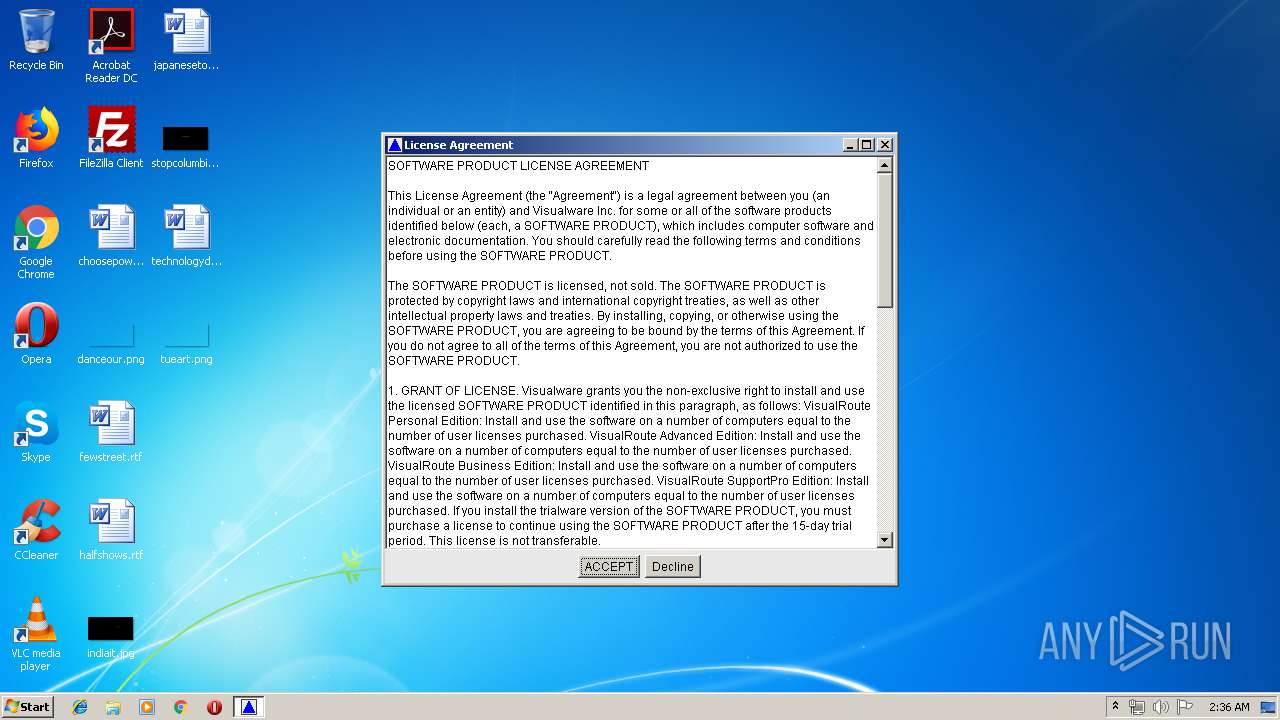
| Verdict: | Malicious activity |
| Analysis date: | April 15, 2019, 01:35:48 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 0FFADBD48D6749395ED9BCDBFF9BEC47 |
| SHA1: | C09D5D2404C6A72ED274295B2F15ABF839D1C22A |
| SHA256: | 04199478669337B98007BB228DBA25B56312A2509EBB18FB98D7C1A078A622B9 |
| SSDEEP: | 98304:ViIhwCMMkl/Tw7FOAplAvOy8S4XeBbdLoq0yBb7JXHlHugghr3YCOCiieQKE:8Ihw39l0JOApoLQeBbd82Bb7JFHAr3wa |
MALICIOUS
Loads dropped or rewritten executable
- java.exe (PID: 2540)
- java.exe (PID: 2624)
- java.exe (PID: 2332)
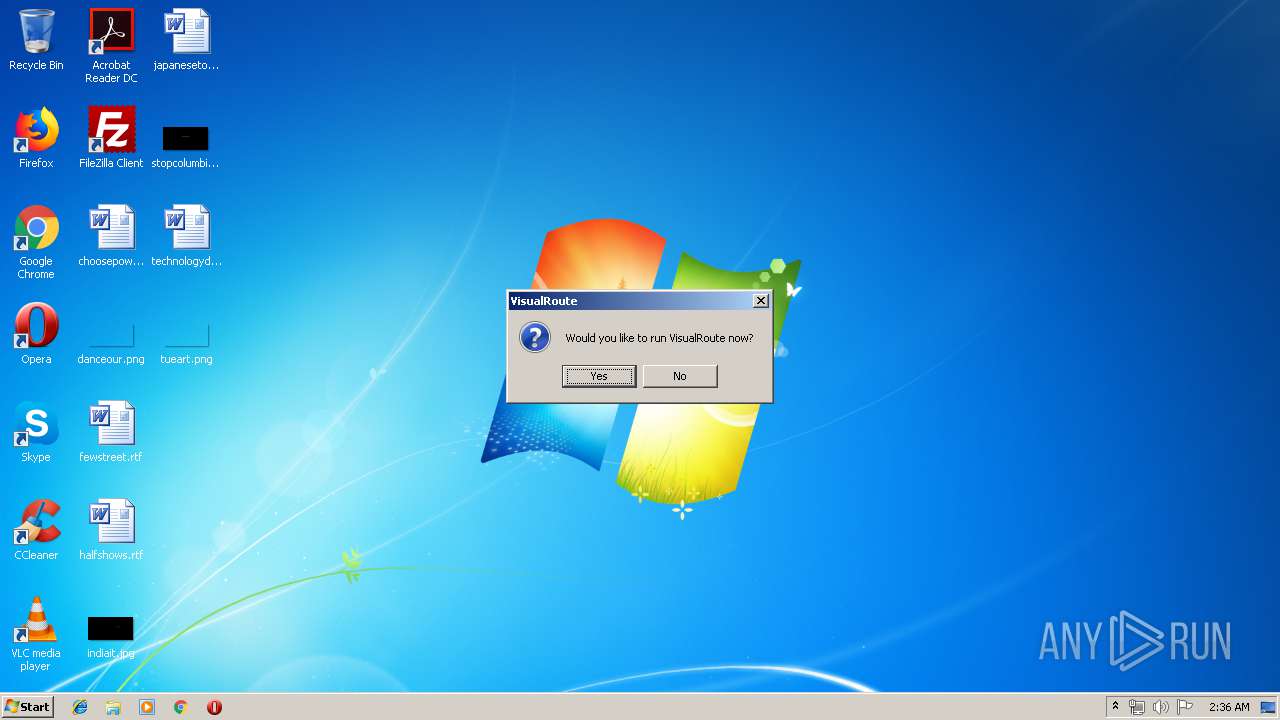
Application was dropped or rewritten from another process
- VisualRoute.exe (PID: 2436)
- MakeLink.exe (PID: 296)
- VisualRoute.exe (PID: 2312)
SUSPICIOUS
Executable content was dropped or overwritten
- java.exe (PID: 2540)
- java.exe (PID: 3820)
- java.exe (PID: 3304)
- java.exe (PID: 2624)
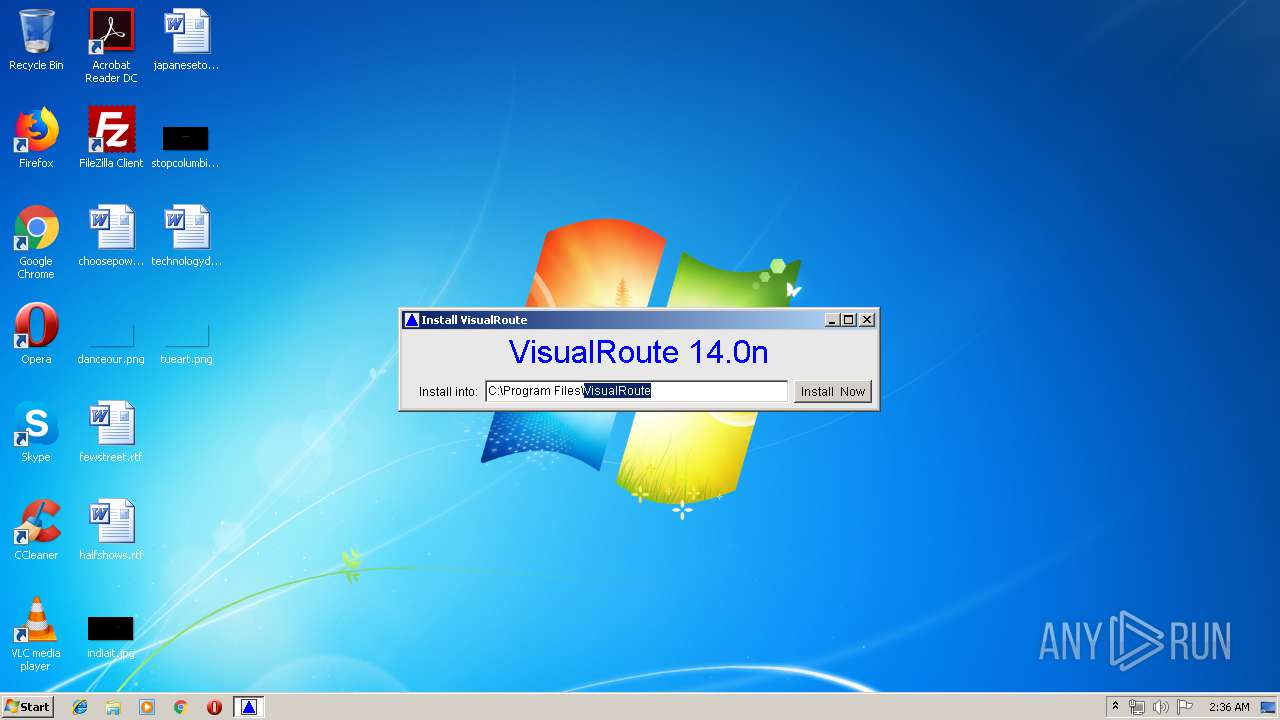
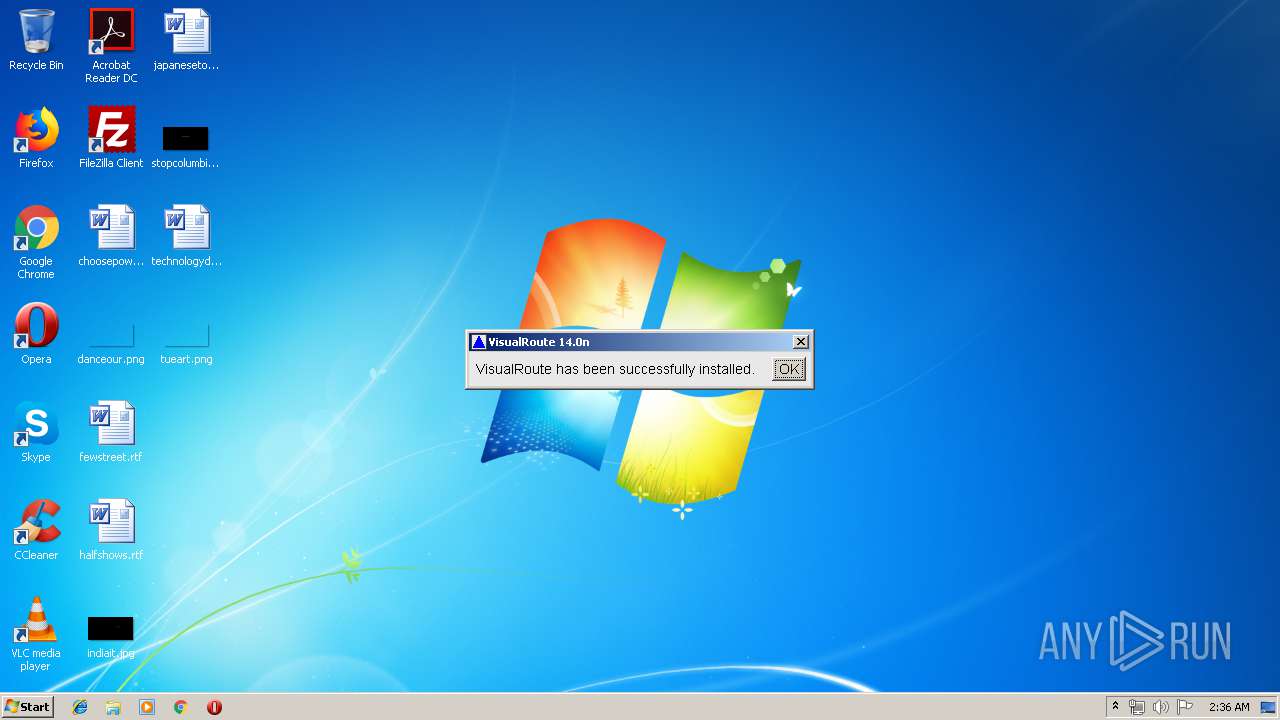
Creates a software uninstall entry
- java.exe (PID: 2540)
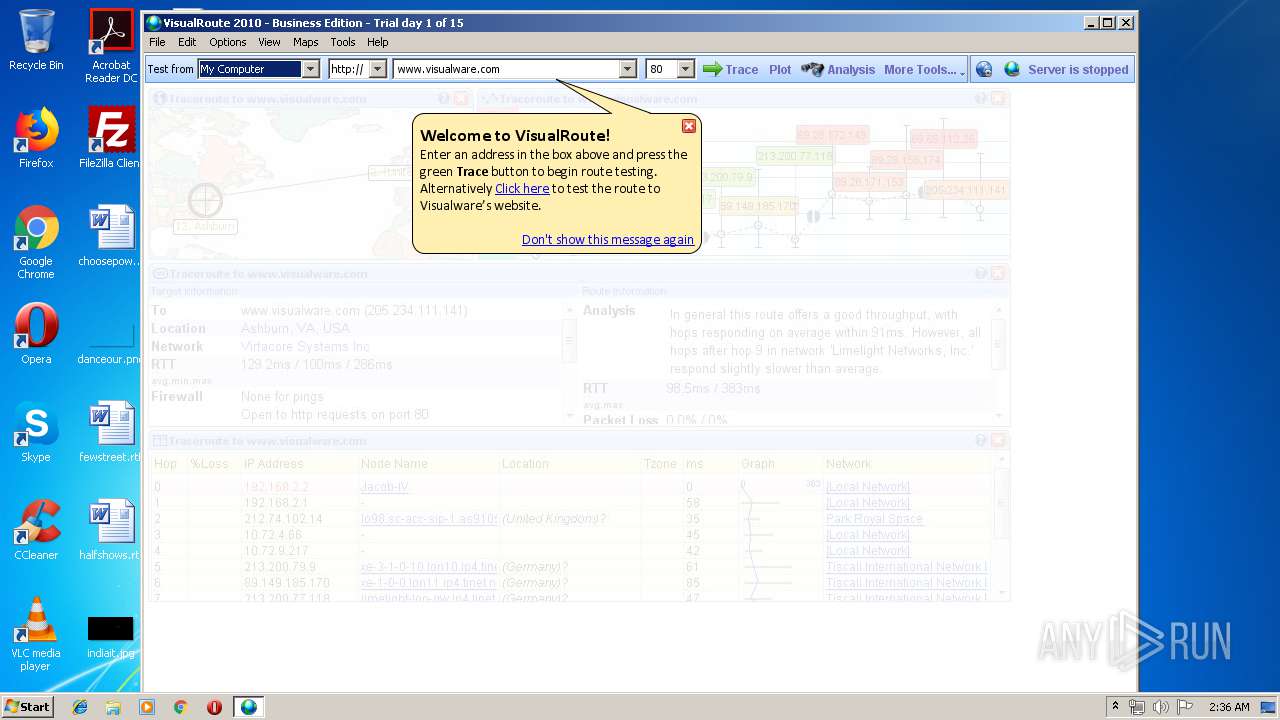
Uses IPCONFIG.EXE to discover IP address
- java.exe (PID: 2624)
Creates files in the program directory
- MakeLink.exe (PID: 296)
- java.exe (PID: 2540)
INFO
Dropped object may contain Bitcoin addresses
- java.exe (PID: 2540)
- java.exe (PID: 2624)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2005:12:19 19:55:35+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 6656 |
| InitializedDataSize: | 5120 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x26c8 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Dec-2005 18:55:35 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 19-Dec-2005 18:55:35 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000185C | 0x00001A00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.99769 |
.rdata | 0x00003000 | 0x0000062A | 0x00000800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.11709 |
.data | 0x00004000 | 0x000005A4 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.35117 |
.rsrc | 0x00005000 | 0x00000600 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.67749 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.81282 | 540 | Latin 1 / Western European | English - United States | RT_MANIFEST |
234 | 2.16096 | 20 | Latin 1 / Western European | English - United States | RT_GROUP_ICON |
Imports
ADVAPI32.dll |
KERNEL32.dll |
MSVCRT.dll |
SHELL32.dll |
USER32.dll |
Total processes
45
Monitored processes
11
Malicious processes
2
Suspicious processes
2
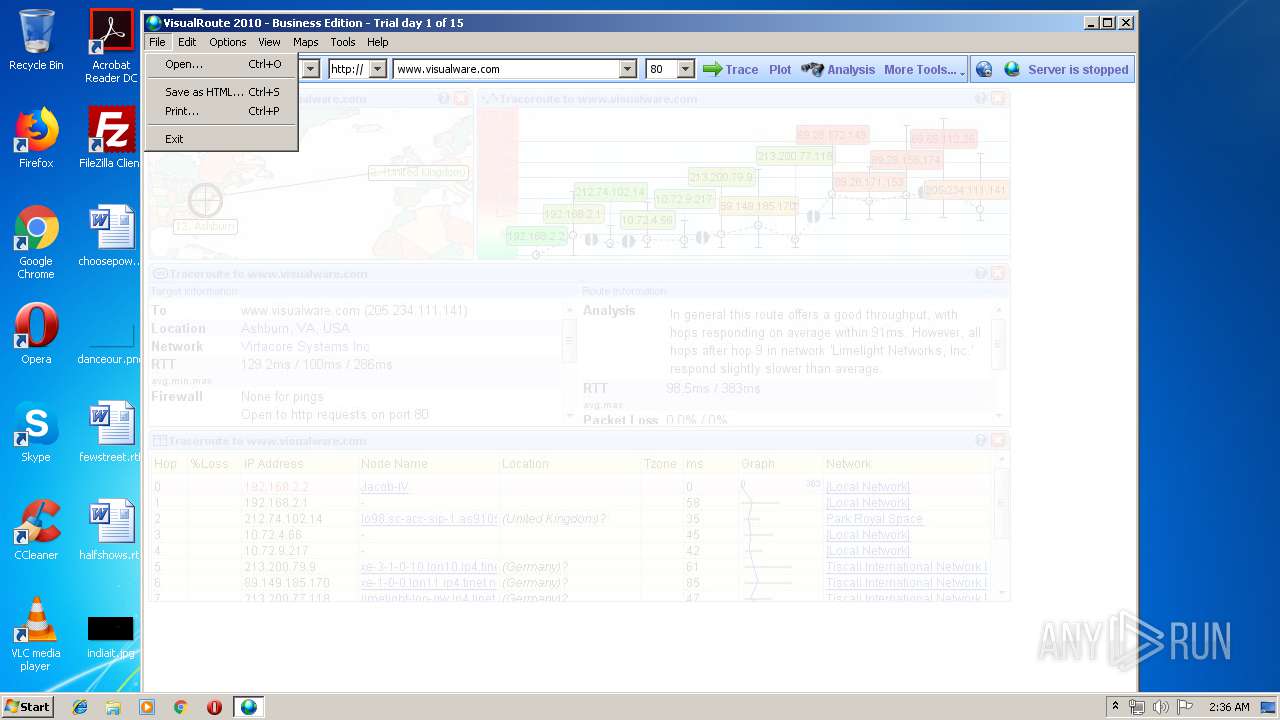
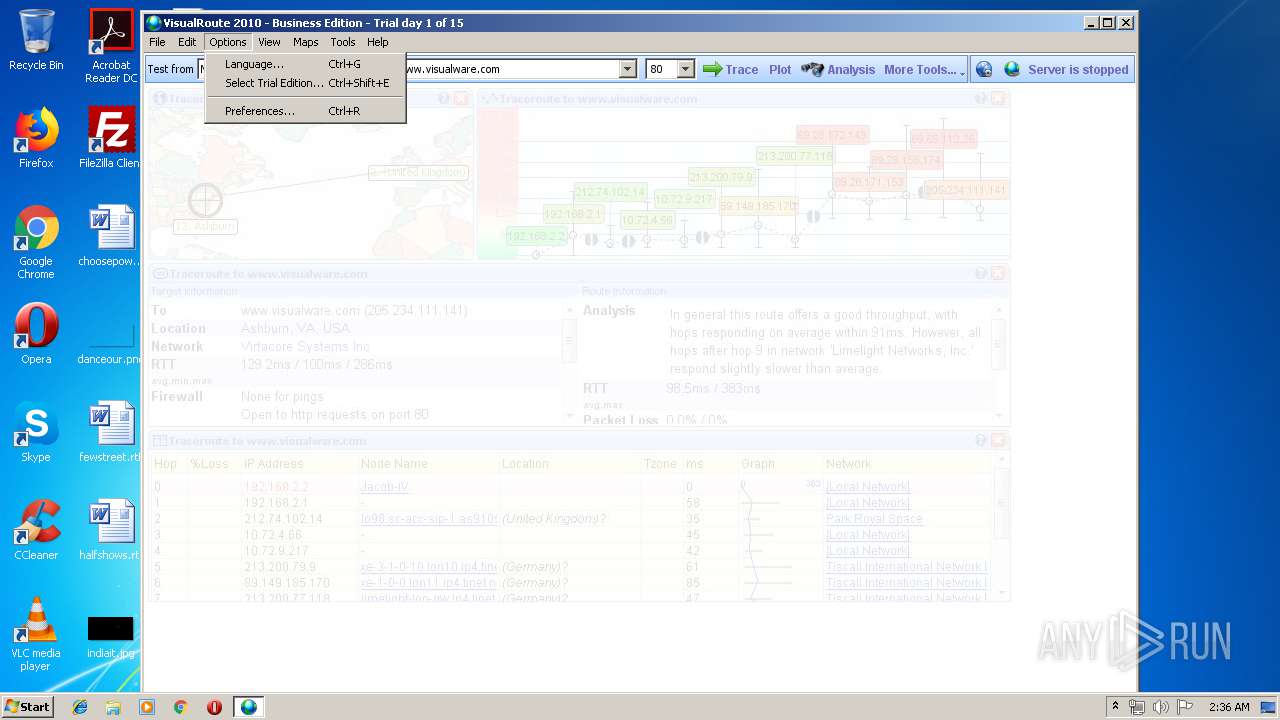
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 296 | "C:\Users\admin\AppData\Local\Temp\X435F04\MakeLink" C:\Users\admin\AppData\Local\Temp\X435F04\makelinks.txt | C:\Users\admin\AppData\Local\Temp\X435F04\MakeLink.exe | — | java.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
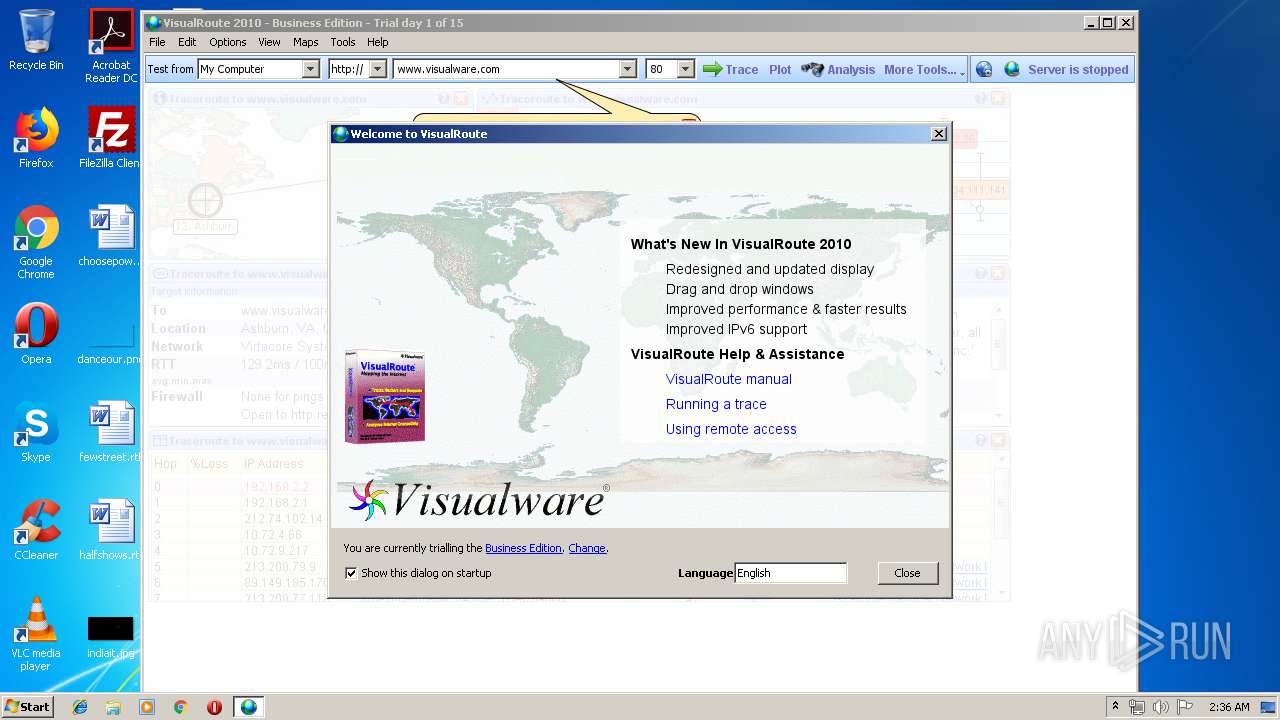
| 2312 | "C:\Program Files\VisualRoute\VisualRoute.exe" | C:\Program Files\VisualRoute\VisualRoute.exe | — | java.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2332 | java -mx256m jexepackboot R "C:\Program Files\VisualRoute\VisualRoute.exe" "C:\Users\admin\AppData\Local\Temp\X43C984" /install | C:\ProgramData\Oracle\Java\javapath\java.exe | — | VisualRoute.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: HIGH Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.920.14 Modules
| |||||||||||||||
| 2436 | "C:\Program Files\VisualRoute\VisualRoute.exe" -Q* /install | C:\Program Files\VisualRoute\VisualRoute.exe | — | java.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2540 | java -mx256m jexepackboot ER "C:\Users\admin\AppData\Local\Temp\vrc.exe" "C:\Users\admin\AppData\Local\Temp\X435F04" | C:\ProgramData\Oracle\Java\javapath\java.exe | vrc.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: HIGH Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.920.14 Modules
| |||||||||||||||
| 2624 | java -mx256m jexepackboot R "C:\Program Files\VisualRoute\VisualRoute.exe" "C:\Users\admin\AppData\Local\Temp\X43F908" | C:\ProgramData\Oracle\Java\javapath\java.exe | VisualRoute.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: HIGH Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.920.14 Modules
| |||||||||||||||
| 2640 | ipconfig.exe /all | C:\Windows\system32\ipconfig.exe | — | java.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: IP Configuration Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3232 | "C:\Users\admin\AppData\Local\Temp\vrc.exe" | C:\Users\admin\AppData\Local\Temp\vrc.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 3304 | java -mx256m jexepackboot E "C:\Program Files\VisualRoute\VisualRoute.exe" "C:\Users\admin\AppData\Local\Temp\X43F908" | C:\ProgramData\Oracle\Java\javapath\java.exe | VisualRoute.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: HIGH Description: Java(TM) Platform SE binary Exit code: 12345 Version: 8.0.920.14 Modules
| |||||||||||||||
| 3820 | java -mx256m jexepackboot E "C:\Program Files\VisualRoute\VisualRoute.exe" "C:\Users\admin\AppData\Local\Temp\X43C984" /install | C:\ProgramData\Oracle\Java\javapath\java.exe | VisualRoute.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: HIGH Description: Java(TM) Platform SE binary Exit code: 12345 Version: 8.0.920.14 Modules
| |||||||||||||||
Total events
220
Read events
209
Write events
11
Delete events
0
Modification events
| (PID) Process: | (2540) java.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: java.exe | |||
| (PID) Process: | (2540) java.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\App Paths\VisualRoute.exe |
| Operation: | write | Name: | |
Value: C:\Program Files\VisualRoute\VisualRoute.exe | |||
| (PID) Process: | (2540) java.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\App Paths\VisualRoute.exe |
| Operation: | write | Name: | Path |
Value: C:\Program Files\VisualRoute | |||
| (PID) Process: | (2540) java.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\VisualRoute |
| Operation: | write | Name: | DisplayName |
Value: VisualRoute | |||
| (PID) Process: | (2540) java.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\VisualRoute |
| Operation: | write | Name: | UninstallString |
Value: "C:\Program Files\VisualRoute\Uninstall.exe" "C:\Program Files\VisualRoute" | |||
| (PID) Process: | (2332) java.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: java.exe | |||
| (PID) Process: | (2332) java.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2332) java.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2624) java.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: java.exe | |||
Executable files
25
Suspicious files
36
Text files
413
Unknown types
13
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2540 | java.exe | C:\Users\admin\.oracle_jre_usage\90737d32e3abaa4.timestamp | text | |
MD5:— | SHA256:— | |||
| 3844 | vrc.exe | C:\Users\admin\AppData\Local\Temp\X435F04\jexepackboot.class | class | |
MD5:EEC36E37CEA2A02ED0AD4D29F4402293 | SHA256:5189CD87E4D46DAB11E7E204BDE8ADAF9226346C7428085FE182A380764A882E | |||
| 2540 | java.exe | C:\Users\admin\AppData\Local\Temp\X435F04\packlist.txt | text | |
MD5:— | SHA256:— | |||
| 2540 | java.exe | C:\Users\admin\AppData\Local\Temp\X435F04\install.ini | text | |
MD5:— | SHA256:— | |||
| 2540 | java.exe | C:\Users\admin\AppData\Local\Temp\X435F04\src\data\countrycodes.txt | text | |
MD5:— | SHA256:— | |||
| 2540 | java.exe | C:\Users\admin\AppData\Local\Temp\X435F04\src\data\geo.vdb | binary | |
MD5:— | SHA256:— | |||
| 2540 | java.exe | C:\Users\admin\AppData\Local\Temp\X435F04\src\data\cities.txt+ | binary | |
MD5:— | SHA256:— | |||
| 2540 | java.exe | C:\Users\admin\AppData\Local\Temp\X435F04\src\data\ip2cc.db | binary | |
MD5:— | SHA256:— | |||
| 2540 | java.exe | C:\Users\admin\AppData\Local\Temp\X435F04\src\data\domains.txt+ | binary | |
MD5:— | SHA256:— | |||
| 2540 | java.exe | C:\Users\admin\AppData\Local\Temp\X435F04\src\data\iptonet.txt+ | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
4
DNS requests
5
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2624 | java.exe | GET | 200 | 38.100.141.80:80 | http://www.visualroute.com/updates/updates.txt | US | text | 86 b | malicious |
2624 | java.exe | GET | 200 | 38.100.141.80:80 | http://www.visualroute.com/clientconfig/languagesv11.txt | US | text | 980 b | malicious |
2624 | java.exe | GET | 200 | 38.100.141.80:80 | http://www.visualroute.com/clientconfig/fixedagents14.bin | US | binary | 128 b | malicious |
2624 | java.exe | GET | 400 | 38.100.141.75:80 | http://secure.visualware.com./crm/LiveUpdate?q=pwiQVzV3NqsRKIo5sPZhArp28J2OjCRQvuDQaWtPpANGhA4z3CGoy7RWZKLl9jTemMN5C1C3fMSyNmssggYXa1wtiFAElMYfs8v8rcewIT0y1OpBehVMC9yl1qxiBLK4 | US | — | — | suspicious |
2624 | java.exe | GET | — | 38.100.141.110:80 | http://update.visualware.com/hotlinks/Hotlinks?p=VR&e=2&b=7521&v=140013&i=0&o=W&t=T&j=o-1.8.0_92 | US | — | — | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2624 | java.exe | 38.100.141.75:80 | secure.visualware.com | Cogent Communications | US | unknown |
2624 | java.exe | 38.100.141.76:80 | www.visualware.com | Cogent Communications | US | suspicious |
— | — | 38.100.141.110:80 | update.visualware.com | Cogent Communications | US | suspicious |
2624 | java.exe | 38.100.141.80:80 | www.visualroute.com | Cogent Communications | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.visualroute.com |
| malicious |
update.visualware.com |
| suspicious |
www.visualware.com |
| malicious |
secure.visualware.com |
| suspicious |
pwiQVzV3NqsRKIo5sPZhArp28J2OjCRQvuDQaWtPpA.NGhA4z3CGoy7RWZKLl9jTemMN5C1C3fMSyNmssggYXa.1wtiFAElMYfs8v8rcewIT0y1OpBehVMC9yl1qxiBLK4.LiveUpdate.crm.visualware.com |
| unknown |