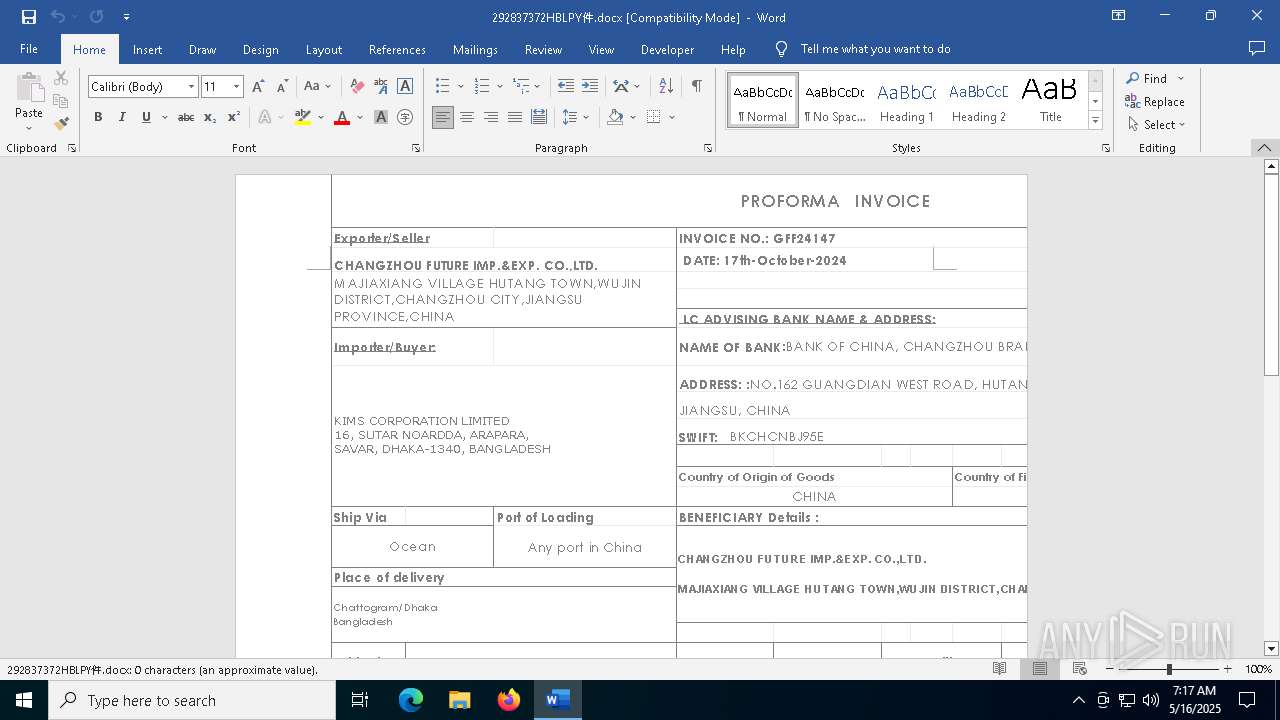
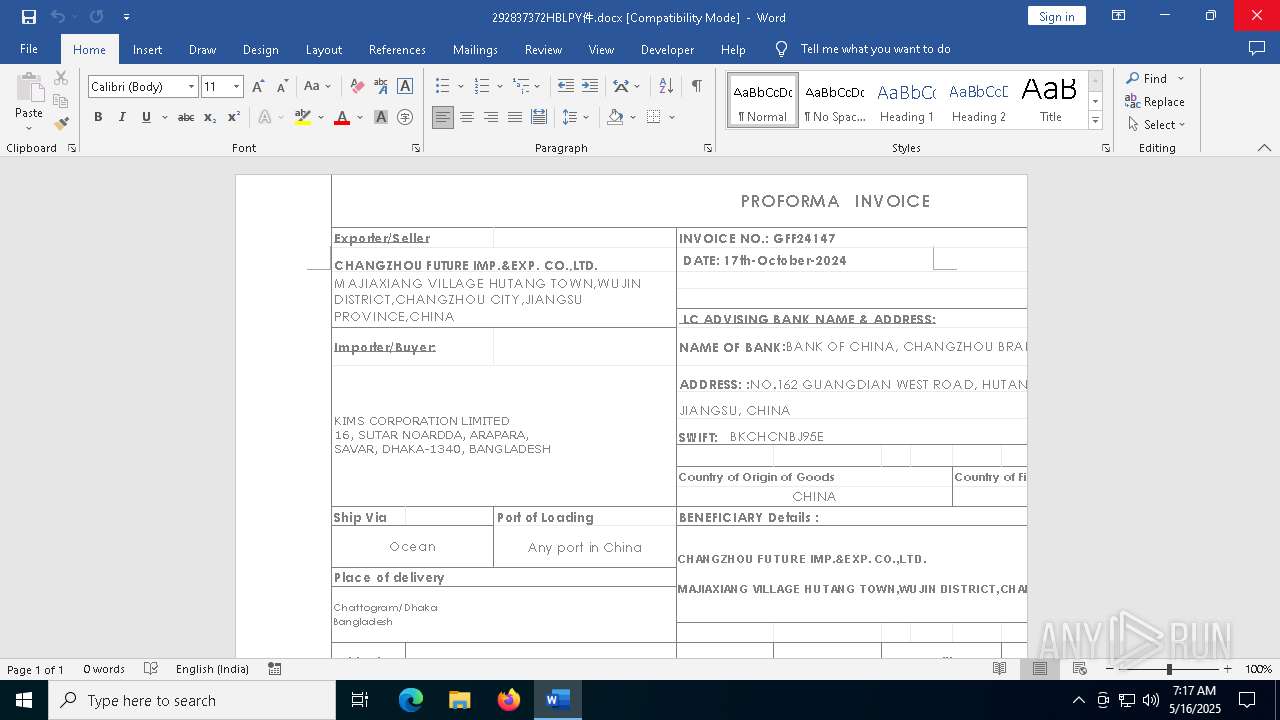
| File name: | 292837372HBLPY件.docx |
| Full analysis: | https://app.any.run/tasks/e0ffb79d-26cf-4fed-95e0-a30f470ea243 |
| Verdict: | Malicious activity |
| Analysis date: | May 16, 2025, 07:17:14 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.openxmlformats-officedocument.wordprocessingml.document |
| File info: | Microsoft Word 2007+ |
| MD5: | 52980129FBEA824165122BB21BBCAAA1 |
| SHA1: | 840DDA4E70C4752FBFBC52302F9866557F69ED5E |
| SHA256: | 03D798635969A616B7BCDD0058EF3DAC9901E3F869BADBBB045D39C02461DE55 |
| SSDEEP: | 6144:etVDSKFwU76pPjiH0qDQ2VseeiNCqTnl3mZT:et9SIH7OOM2O1iMklWZT |
MALICIOUS
EXPLOIT has been detected (SURICATA)
- WINWORD.EXE (PID: 2432)
SUSPICIOUS
Connects to the server without a host name
- WINWORD.EXE (PID: 2432)
INFO
Reads the software policy settings
- slui.exe (PID: 5892)
- slui.exe (PID: 6388)
Checks proxy server information
- slui.exe (PID: 6388)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .docx | | | Word Microsoft Office Open XML Format document (52.2) |
|---|---|---|
| .zip | | | Open Packaging Conventions container (38.8) |
| .zip | | | ZIP compressed archive (8.8) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0002 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2025:05:16 07:23:08 |
| ZipCRC: | 0xf5c0e2b4 |
| ZipCompressedSize: | 432 |
| ZipUncompressedSize: | 2503 |
| ZipFileName: | [Content_Types].xml |
XML
| Template: | Normal.dotm |
|---|---|
| TotalEditTime: | 1 minute |
| Pages: | 1 |
| Words: | - |
| Characters: | - |
| Application: | Microsoft Office Word |
| DocSecurity: | None |
| Lines: | 1 |
| Paragraphs: | 1 |
| ScaleCrop: | No |
| Company: | Grizli777 |
| LinksUpToDate: | No |
| CharactersWithSpaces: | - |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| AppVersion: | 12 |
| Keywords: | - |
| LastModifiedBy: | 91974 |
| RevisionNumber: | 2 |
| CreateDate: | 2025:05:15 05:27:00Z |
| ModifyDate: | 2025:05:15 05:28:00Z |
XMP
| Title: | - |
|---|---|
| Subject: | - |
| Creator: | 91974 |
| Description: | - |
Total processes
140
Monitored processes
5
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1228 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2432 | "C:\Program Files\Microsoft Office\Root\Office16\WINWORD.EXE" /n C:\Users\admin\AppData\Local\Temp\292837372HBLPY件.docx /o "" | C:\Program Files\Microsoft Office\root\Office16\WINWORD.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Version: 16.0.16026.20146 Modules
| |||||||||||||||
| 5892 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6388 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7336 | "C:\Program Files\Microsoft Office\root\VFS\ProgramFilesCommonX64\Microsoft Shared\OFFICE16\ai.exe" "2C951377-925D-4F48-8E07-528CE8A7B839" "B243F0FE-1B7C-45F2-A248-1A5CC87D7E98" "2432" | C:\Program Files\Microsoft Office\root\VFS\ProgramFilesCommonX64\Microsoft Shared\OFFICE16\ai.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Artificial Intelligence (AI) Host for the Microsoft® Windows® Operating System and Platform x64. Version: 0.12.2.0 Modules
| |||||||||||||||
Total events
16 233
Read events
15 855
Write events
352
Delete events
26
Modification events
| (PID) Process: | (2432) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\Common\ClientTelemetry\Sampling |
| Operation: | write | Name: | 0 |
Value: 017012000000001000B24E9A3E02000000000000000600000000000000 | |||
| (PID) Process: | (2432) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\Common\CrashPersistence\WINWORD\2432 |
| Operation: | write | Name: | 0 |
Value: 0B0E103C48617497CFD740B3655C4A33E80B8B230046F2A0C28EA9C6F1ED016A04102400449A7D64B29D01008500A907556E6B6E6F776EC906022222CA0DC2190000C91003783634C5118013D2120B770069006E0077006F00720064002E00650078006500C51620C517808004C91808323231322D44656300 | |||
| (PID) Process: | (2432) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | en-US |
Value: 2 | |||
| (PID) Process: | (2432) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | de-de |
Value: 2 | |||
| (PID) Process: | (2432) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | fr-fr |
Value: 2 | |||
| (PID) Process: | (2432) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | es-es |
Value: 2 | |||
| (PID) Process: | (2432) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | it-it |
Value: 2 | |||
| (PID) Process: | (2432) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | ja-jp |
Value: 2 | |||
| (PID) Process: | (2432) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | ko-kr |
Value: 2 | |||
| (PID) Process: | (2432) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | pt-br |
Value: 2 | |||
Executable files
33
Suspicious files
137
Text files
18
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2432 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | binary | |
MD5:765AE3C24FFE358BDB837D940604B5F7 | SHA256:53BCEB238D9C92DA3B56548AE424D3BBBD792E2435BD0B4DBF4389C6C7118854 | |||
| 2432 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\AddInClassifierCache\OfficeSharedEntities.bin | text | |
MD5:CC90D669144261B198DEAD45AA266572 | SHA256:89C701EEFF939A44F28921FD85365ECD87041935DCD0FE0BAF04957DA12C9899 | |||
| 2432 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$2837372HBLPY件.docx | binary | |
MD5:C33A7575A1688424E999B7554EB90723 | SHA256:4A1C8F8004053C4A1D9D45D10560C6DD9A216B1AEED351A1DD59E40E7FCD4C54 | |||
| 2432 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\TokenBroker\Cache\089d66ba04a8cec4bdc5267f42f39cf84278bb67.tbres | binary | |
MD5:3FD46302439C9887E3609988E48CC77F | SHA256:AE49AFC43D0E17AEE7BC6771D8B4A94F21033FE10177A88E67F299EDA399E614 | |||
| 2432 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\TokenBroker\Cache\56a61aeb75d8f5be186c26607f4bb213abe7c5ec.tbres | binary | |
MD5:2505F1593B9405494BB0F42EA30779A9 | SHA256:43289CAB3D84BEDF40369D0817794E19D8D825E740C92D95DFC2B30ACB5D1559 | |||
| 2432 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\WebServiceCache\AllUsers\officeclient.microsoft.com\81897A42-2E95-4E69-B5CC-F28A01CB6ED3 | xml | |
MD5:D65B72E829B43C1F2516209AA4A8D2C8 | SHA256:4109C8D3FD53C4C9C5305FD886C5A9D7E606E16CD6E8C8FE8824EDD2A443E025 | |||
| 2432 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\ResourceInfoCache\07fc2a8c43a1d1f16572d21e959a4847e306edae.temp | binary | |
MD5:F9EF2341E05D9F6942C915B7182C9C22 | SHA256:A84B7176058B11AC6921531A92C2AE201DD14C6F857924DF49E4FE3B59BED567 | |||
| 2432 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\AddInClassifierCache\OfficeSharedEntitiesUpdated.bin | text | |
MD5:2676BD90B2F6DEFE249CBA91F36F82F5 | SHA256:DBF51E947D58102811C51803044F28290F04D8AAFECC59B8C5FDC503B2A2420B | |||
| 2432 | WINWORD.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\8B2B9A00839EED1DFDCCC3BFC2F5DF12 | binary | |
MD5:083D16E57EF95CC5F908BE87698DF9BF | SHA256:A7ED5EE25CB109C2DB075B61A98B08CB435F43549DFDCCE4DA33855960C02C85 | |||
| 2432 | WINWORD.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\8B2B9A00839EED1DFDCCC3BFC2F5DF12 | binary | |
MD5:4A90329071AE30B759D279CCA342B0A6 | SHA256:4F544379EDA8E2653F71472AB968AEFD6B5D1F4B3CE28A5EDB14196184ED3B60 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
18
TCP/UDP connections
69
DNS requests
28
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.19.11.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2432 | WINWORD.EXE | GET | 200 | 142.250.186.99:80 | http://c.pki.goog/r/gsr1.crl | unknown | — | — | whitelisted |
2432 | WINWORD.EXE | GET | 200 | 142.250.186.99:80 | http://c.pki.goog/r/r4.crl | unknown | — | — | whitelisted |
2432 | WINWORD.EXE | HEAD | 200 | 107.175.246.45:80 | http://107.175.246.45/590/esb/verygreatpersonwhichperfectattitudiegoodfroinhisworkingskill_________verygreatpersonwhichperfectattitudiegoodfroinhisworkingskill_______verygreatpersonwhichperfectattitudiegoodfroinhisworkingskill.doc | unknown | — | — | unknown |
2432 | WINWORD.EXE | GET | 200 | 107.175.246.45:80 | http://107.175.246.45/590/esb/verygreatpersonwhichperfectattitudiegoodfroinhisworkingskill_________verygreatpersonwhichperfectattitudiegoodfroinhisworkingskill_______verygreatpersonwhichperfectattitudiegoodfroinhisworkingskill.doc | unknown | — | — | unknown |
2432 | WINWORD.EXE | HEAD | 200 | 107.175.246.45:80 | http://107.175.246.45/590/esb/verygreatpersonwhichperfectattitudiegoodfroinhisworkingskill_________verygreatpersonwhichperfectattitudiegoodfroinhisworkingskill_______verygreatpersonwhichperfectattitudiegoodfroinhisworkingskill.doc | unknown | — | — | unknown |
2432 | WINWORD.EXE | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | whitelisted |
2432 | WINWORD.EXE | GET | 200 | 2.19.11.120:80 | http://crl.microsoft.com/pki/crl/products/microsoftrootcert.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 2.19.11.120:80 | crl.microsoft.com | Elisa Oyj | NL | whitelisted |
— | — | 23.219.150.101:80 | www.microsoft.com | AKAMAI-AS | CL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2432 | WINWORD.EXE | 52.109.89.18:443 | officeclient.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2432 | WINWORD.EXE | 52.123.130.14:443 | ecs.office.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2432 | WINWORD.EXE | 2.16.168.119:443 | omex.cdn.office.net | Akamai International B.V. | RU | whitelisted |
2432 | WINWORD.EXE | 188.114.97.3:443 | smol.re | CLOUDFLARENET | NL | unknown |
2432 | WINWORD.EXE | 142.250.186.99:80 | c.pki.goog | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
officeclient.microsoft.com |
| whitelisted |
ecs.office.com |
| whitelisted |
omex.cdn.office.net |
| whitelisted |
smol.re |
| unknown |
c.pki.goog |
| whitelisted |
client.wns.windows.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2432 | WINWORD.EXE | Potentially Bad Traffic | ET HUNTING Microsoft Office User-Agent Requesting A Doc File |
2432 | WINWORD.EXE | Potentially Bad Traffic | ET INFO Dotted Quad Host DOC Request |
2432 | WINWORD.EXE | Potentially Bad Traffic | ET INFO Dotted Quad Host DOC Request |
2432 | WINWORD.EXE | Misc Attack | EXPLOIT [ANY.RUN] Obfuscated RTF document including the CLSID of the Equation Editor (CVE-2017-11882) |
2432 | WINWORD.EXE | Misc activity | ET USER_AGENTS Microsoft Office Existence Discovery User-Agent |
2432 | WINWORD.EXE | Potentially Bad Traffic | ET INFO Dotted Quad Host DOC Request |