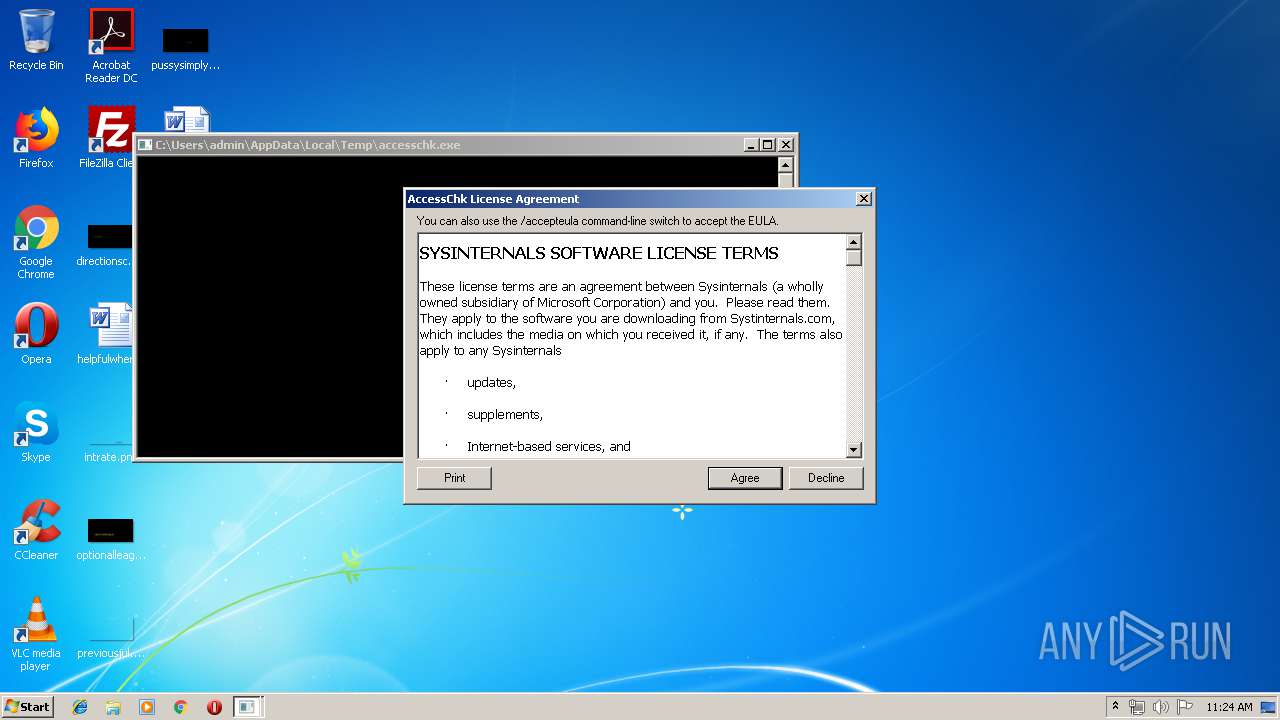
| File name: | accesschk.exe |
| Full analysis: | https://app.any.run/tasks/8bd72362-8c4f-4f70-892f-4115dcef838a |
| Verdict: | Malicious activity |
| Analysis date: | April 23, 2019, 10:23:50 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows |
| MD5: | 279EEBEA94B1909F84C02B427C67316C |
| SHA1: | 2E2E712E5B73FAB842E84D1451F9EAAC391F0419 |
| SHA256: | 03CBA9A8BB79772942DCB812C70F09DBAB34944E918B71450347FFAB2AAB9B0A |
| SSDEEP: | 3072:S3IDkQgXRse0Ooyw9VLm67ZiJiJELhgRqRHmd9p5TtnsCVb+tTSMi5I:pkQg/0n1LN7ZMhjRGrLWCVs5 |
MALICIOUS
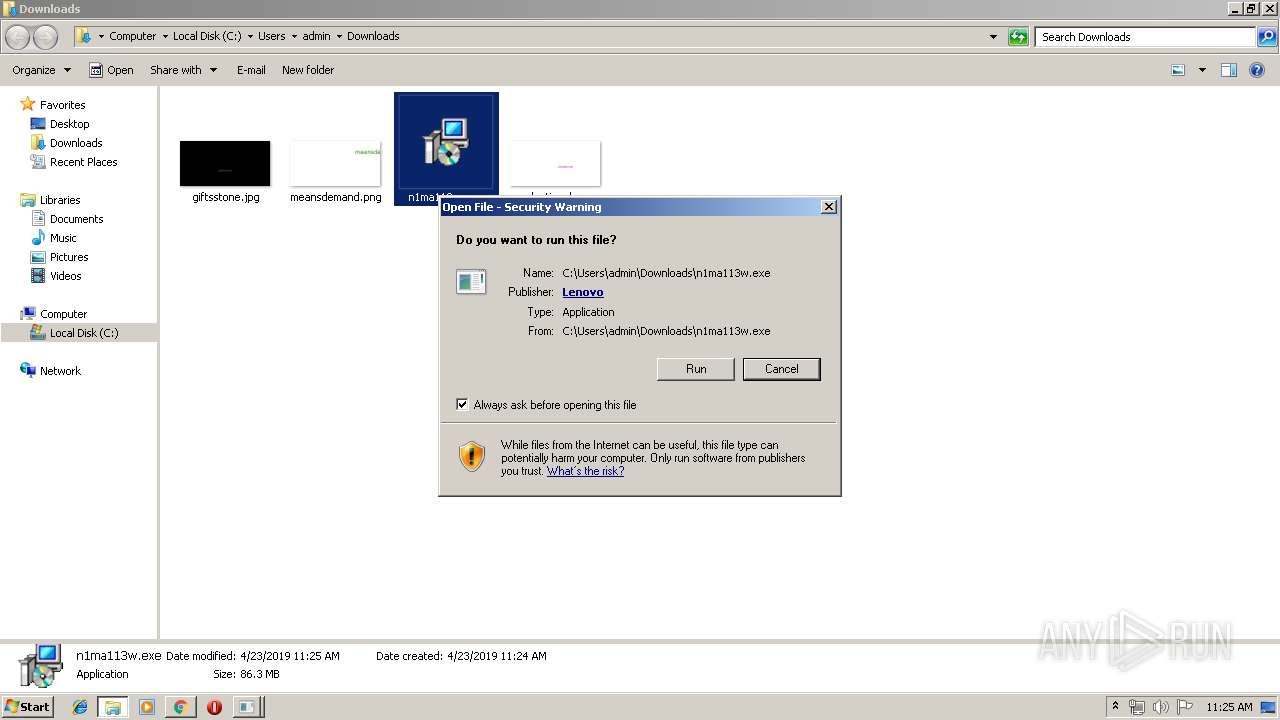
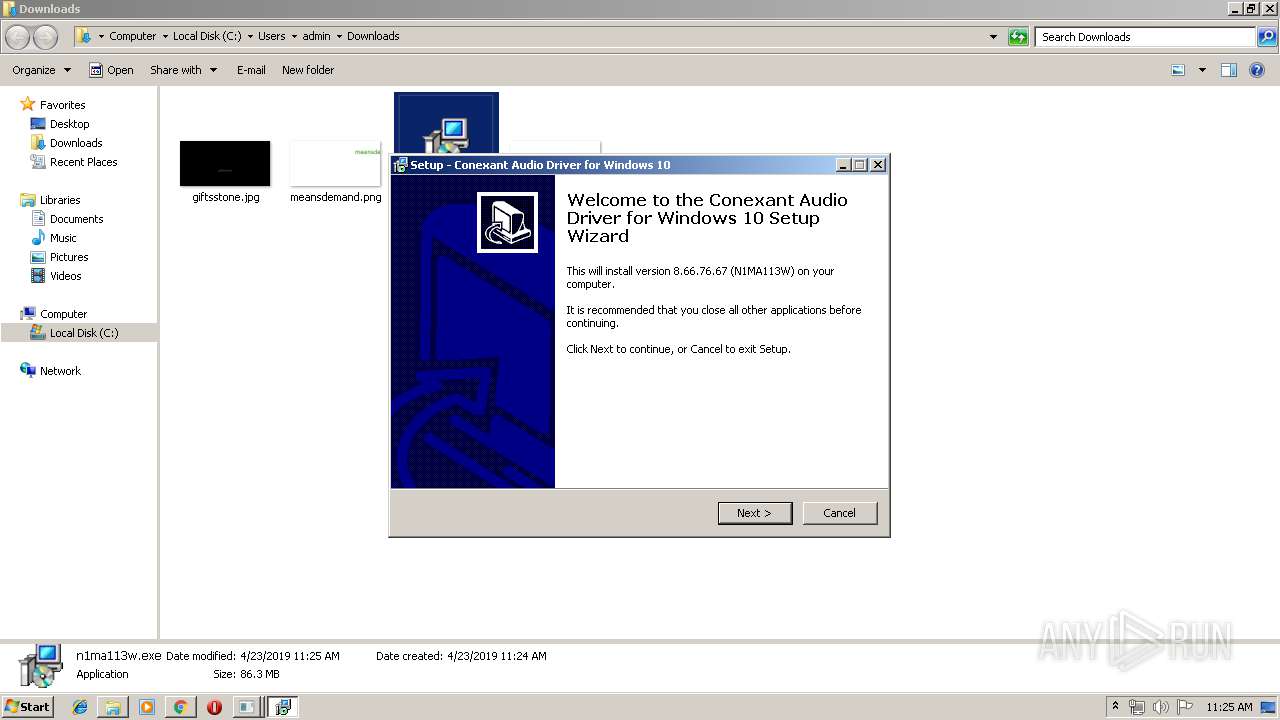
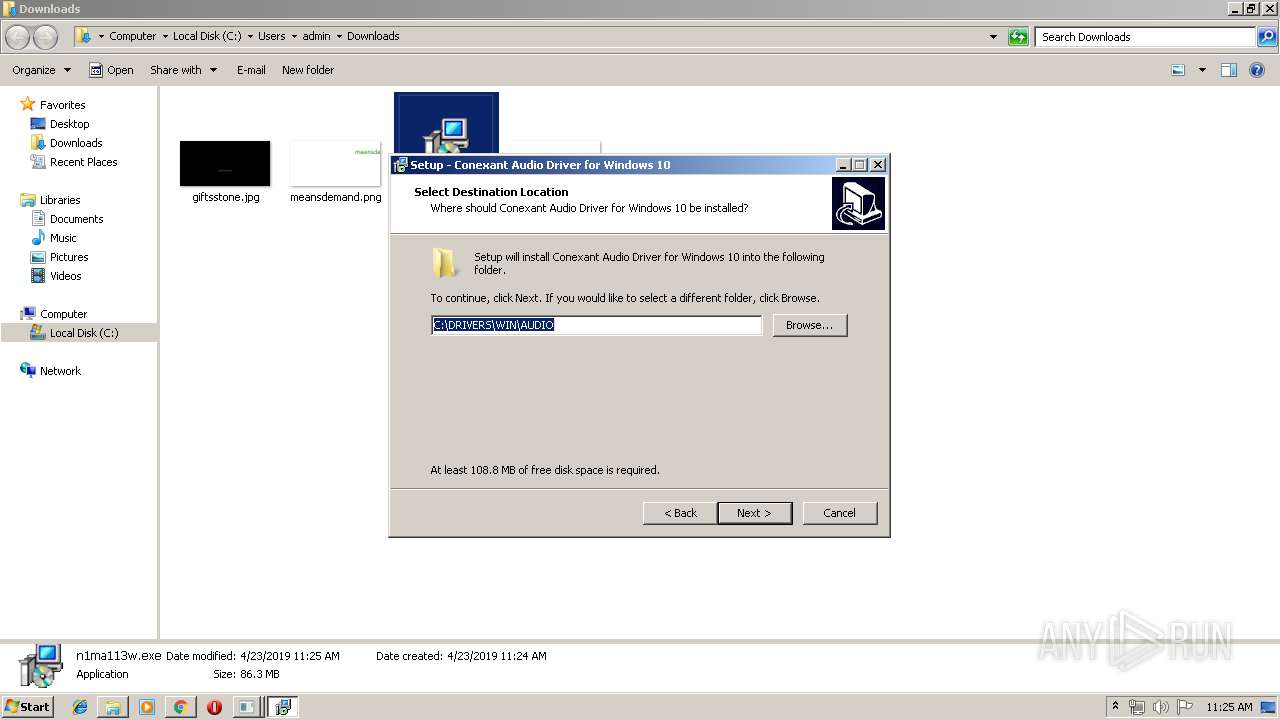
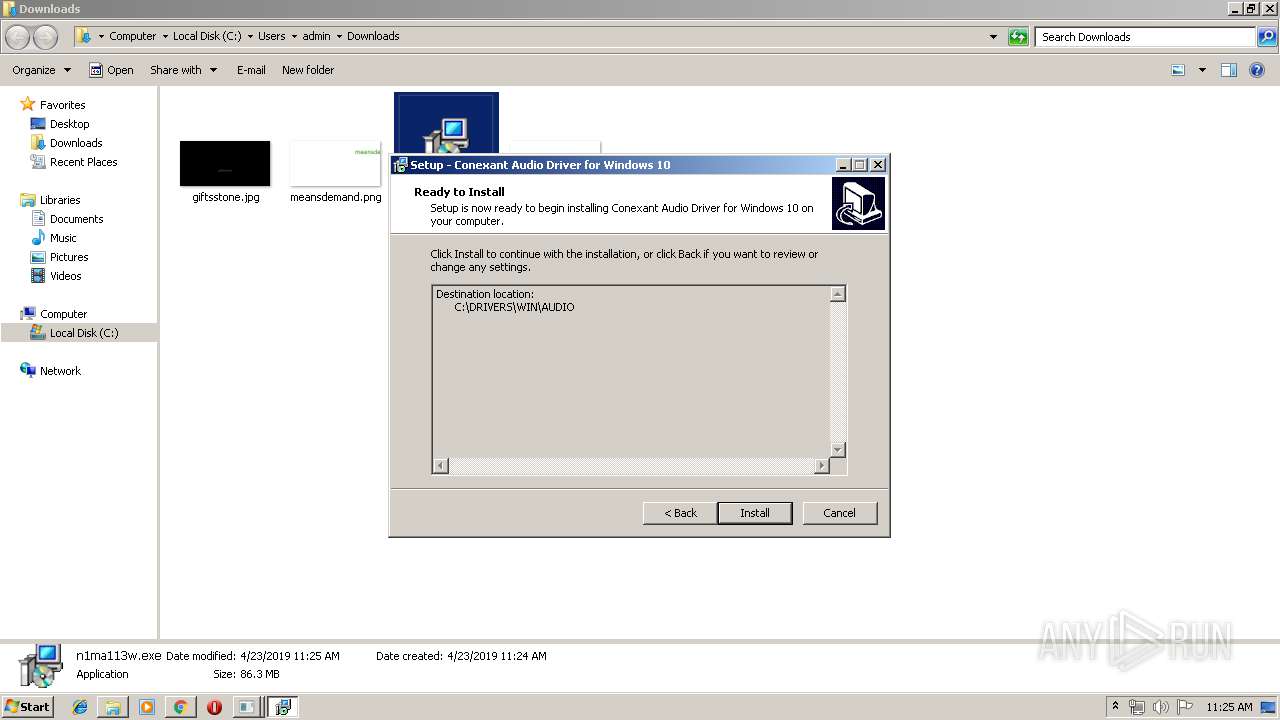
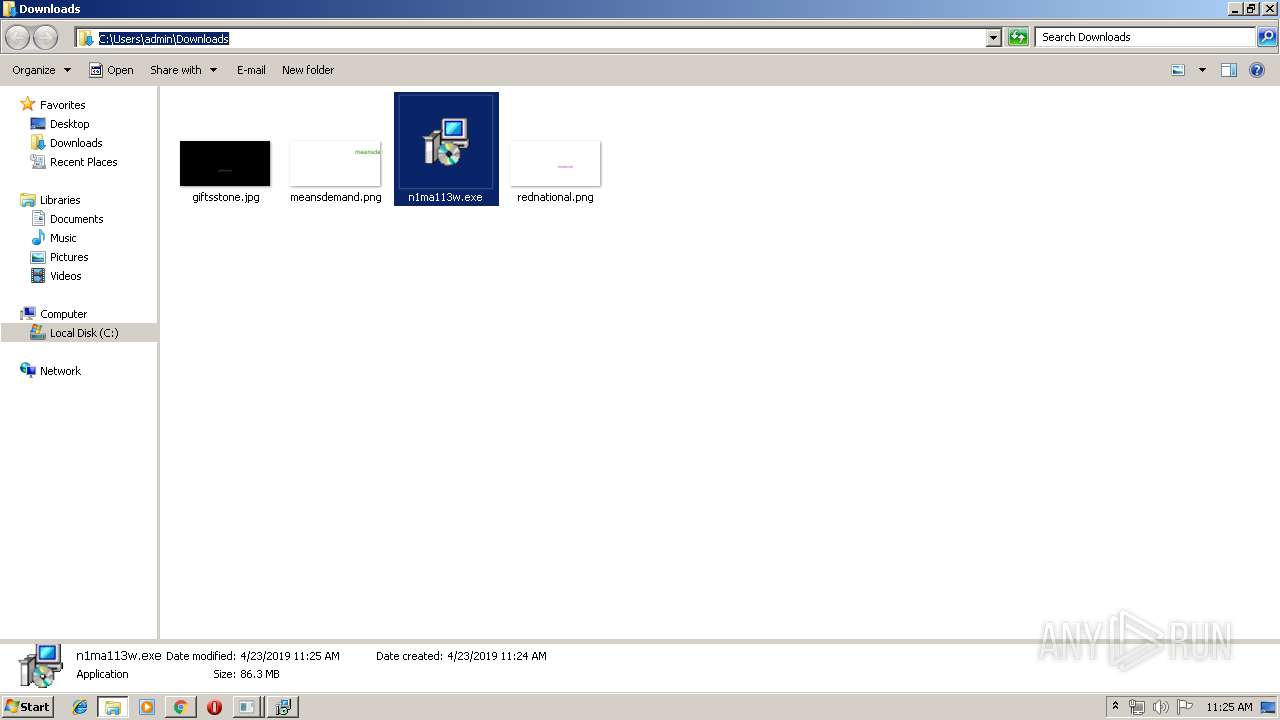
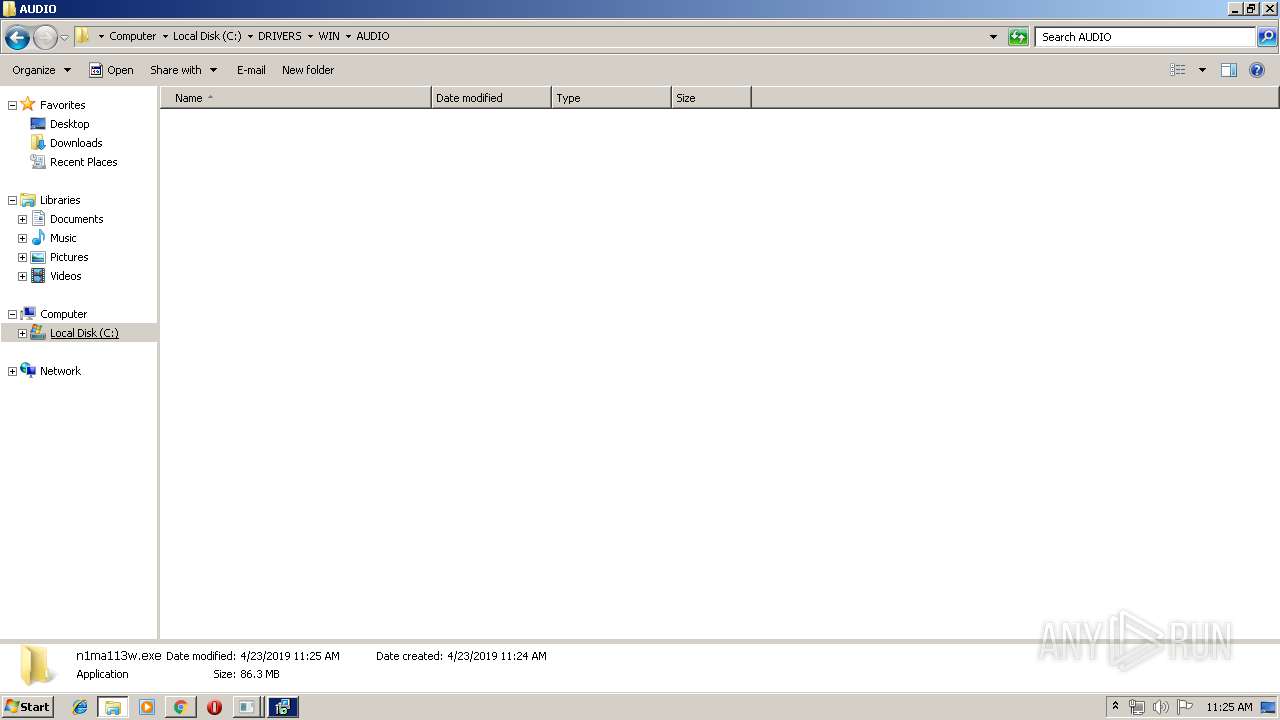
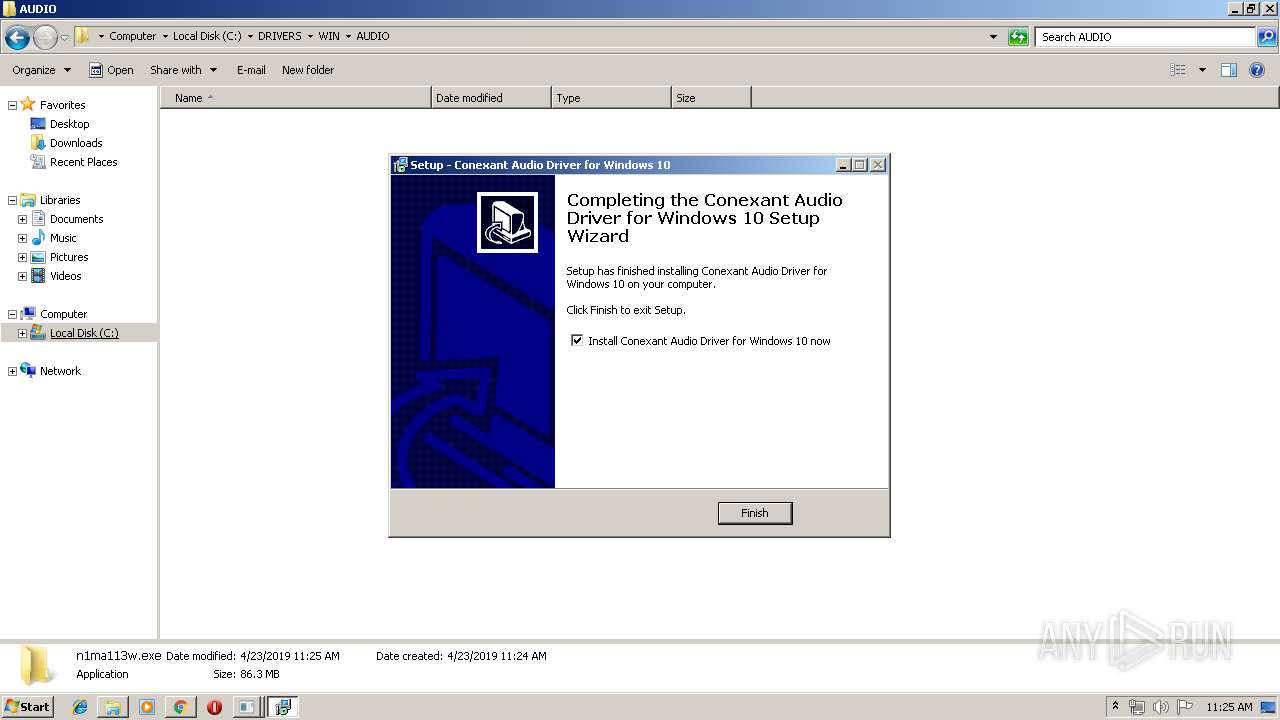
Application was dropped or rewritten from another process
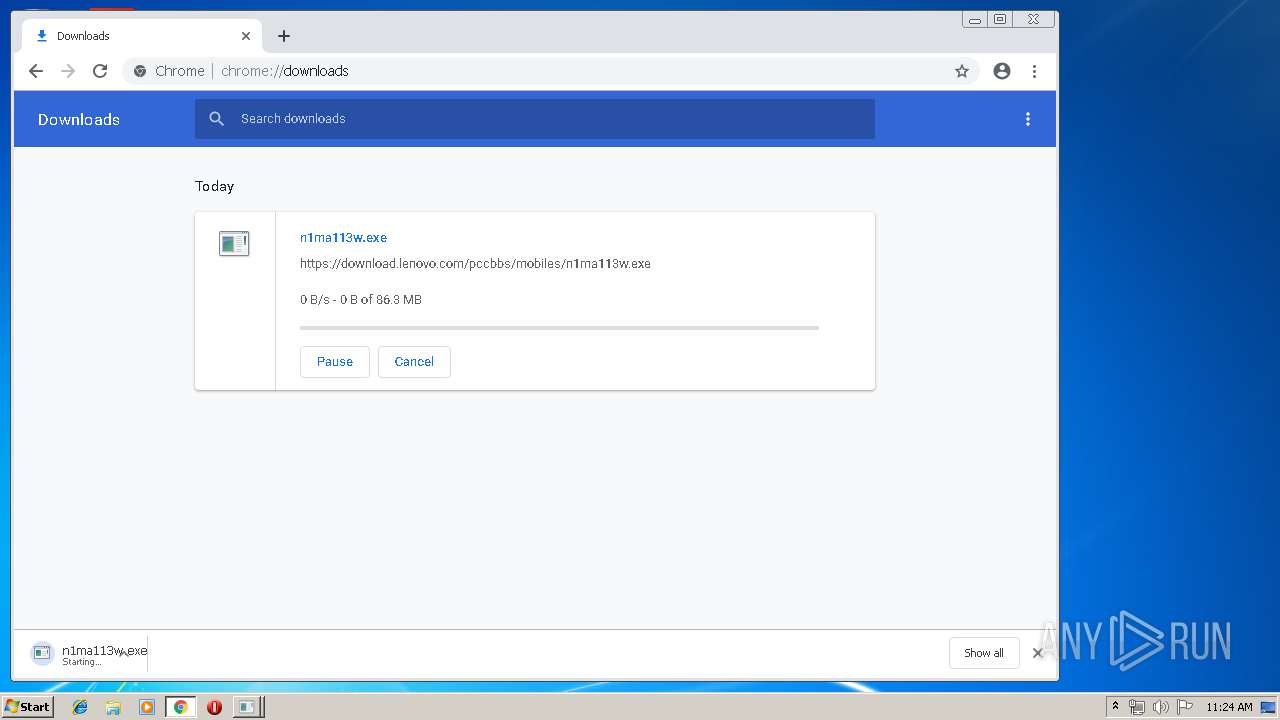
- n1ma113w.exe (PID: 868)
- n1ma113w.exe (PID: 1104)
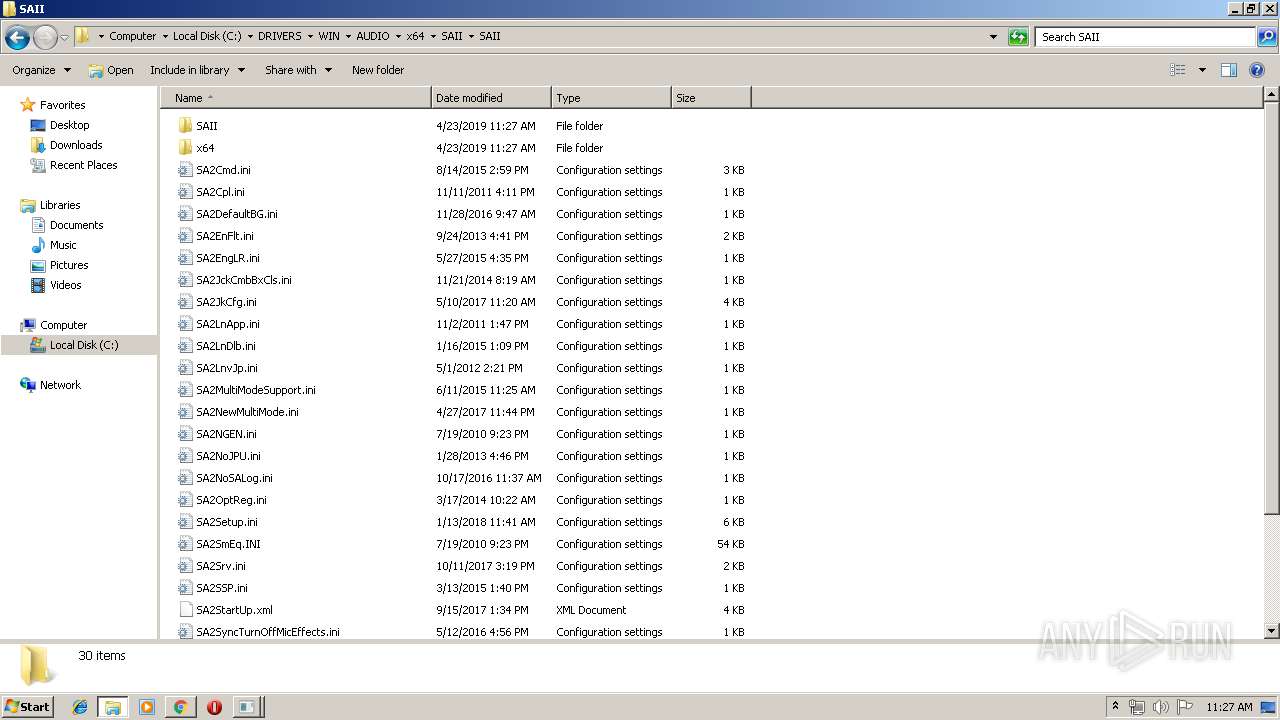
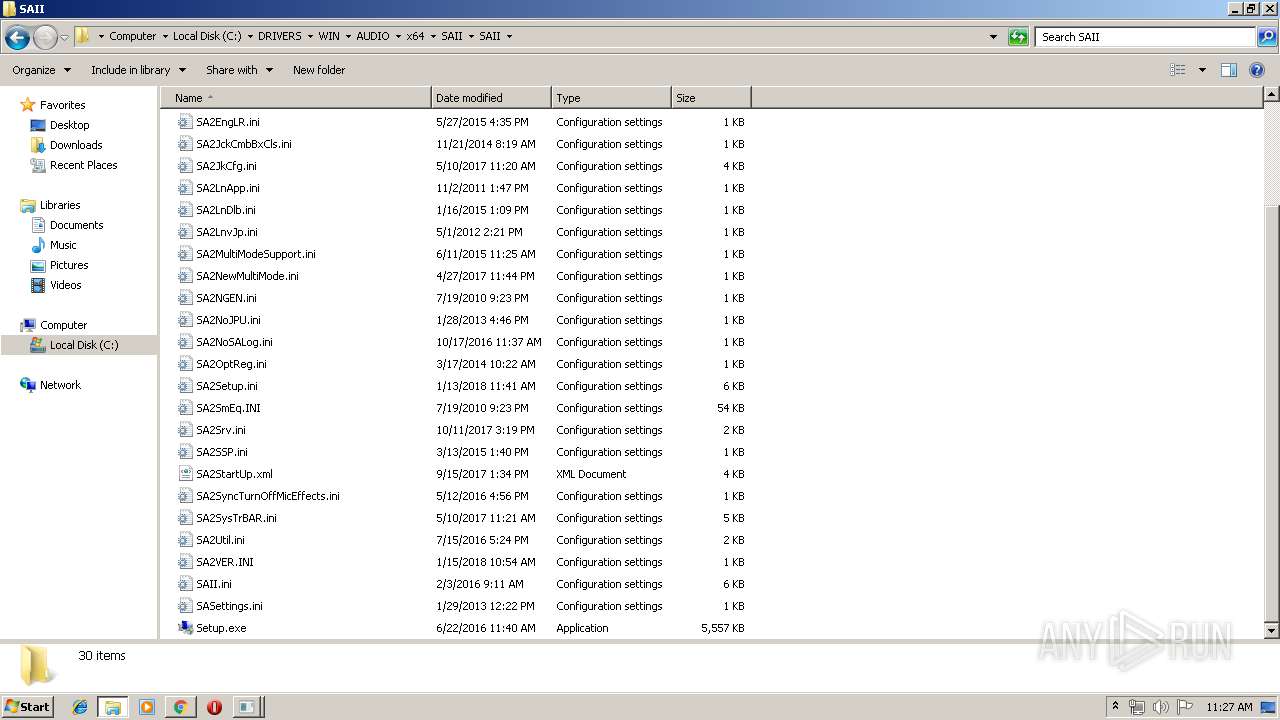
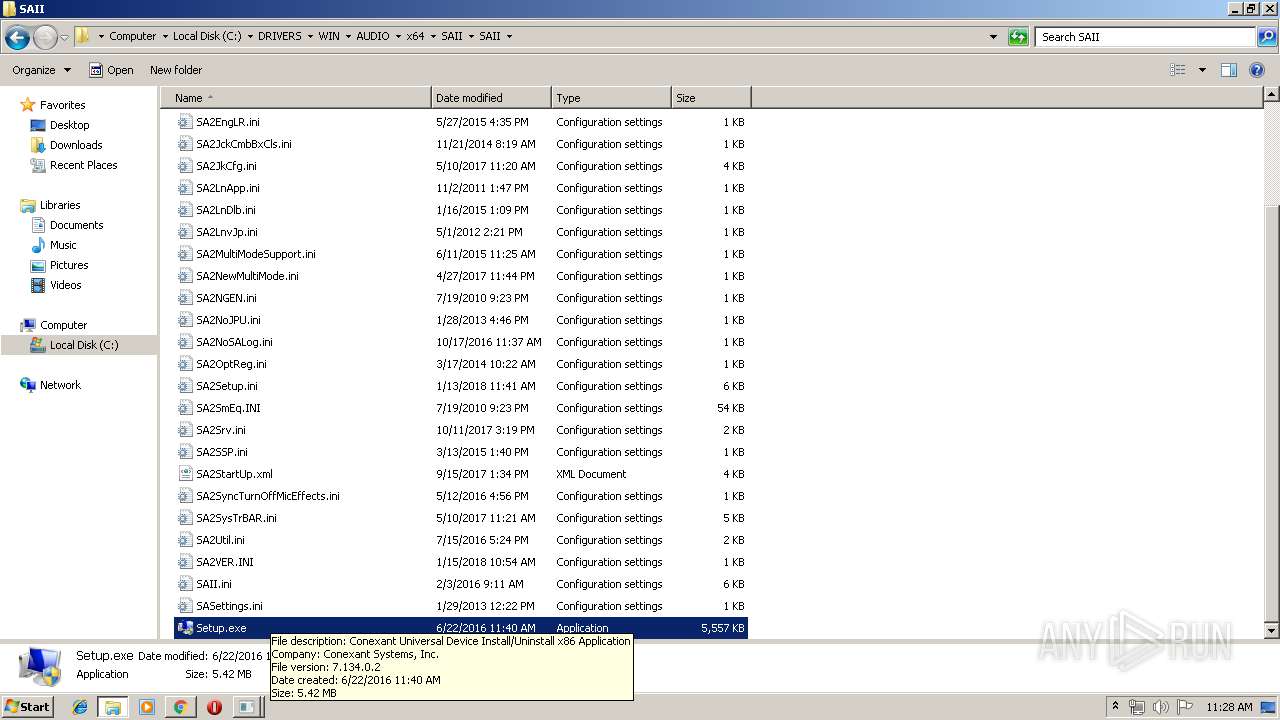
- Setup.exe (PID: 2172)
- Setup.exe (PID: 3604)
- CxUtilSvc.exe (PID: 3688)
- CxUtilSvc.exe (PID: 3472)
- SASrv.exe (PID: 2708)
- SAsrv.exe (PID: 3488)
- SACpl.exe (PID: 1300)
Starts NET.EXE for service management
- Setup.exe (PID: 2172)
Loads dropped or rewritten executable
- Setup.exe (PID: 2172)
- regsvr32.exe (PID: 2164)
- mscorsvw.exe (PID: 1472)
- mscorsvw.exe (PID: 2948)
- mscorsvw.exe (PID: 2416)
- mscorsvw.exe (PID: 980)
- mscorsvw.exe (PID: 3896)
Registers / Runs the DLL via REGSVR32.EXE
- Setup.exe (PID: 2172)
Uses Task Scheduler to run other applications
- Setup.exe (PID: 2172)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 1892)
- schtasks.exe (PID: 3452)
- schtasks.exe (PID: 1580)
- schtasks.exe (PID: 2056)
SUSPICIOUS
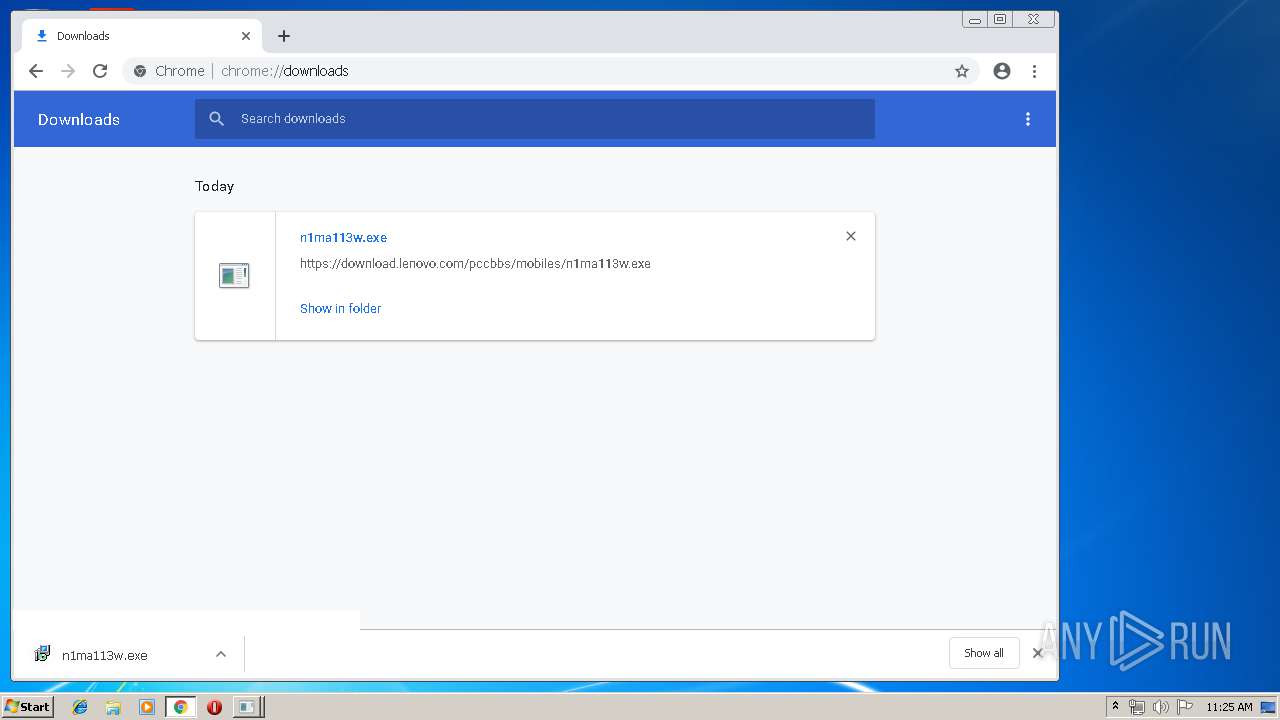
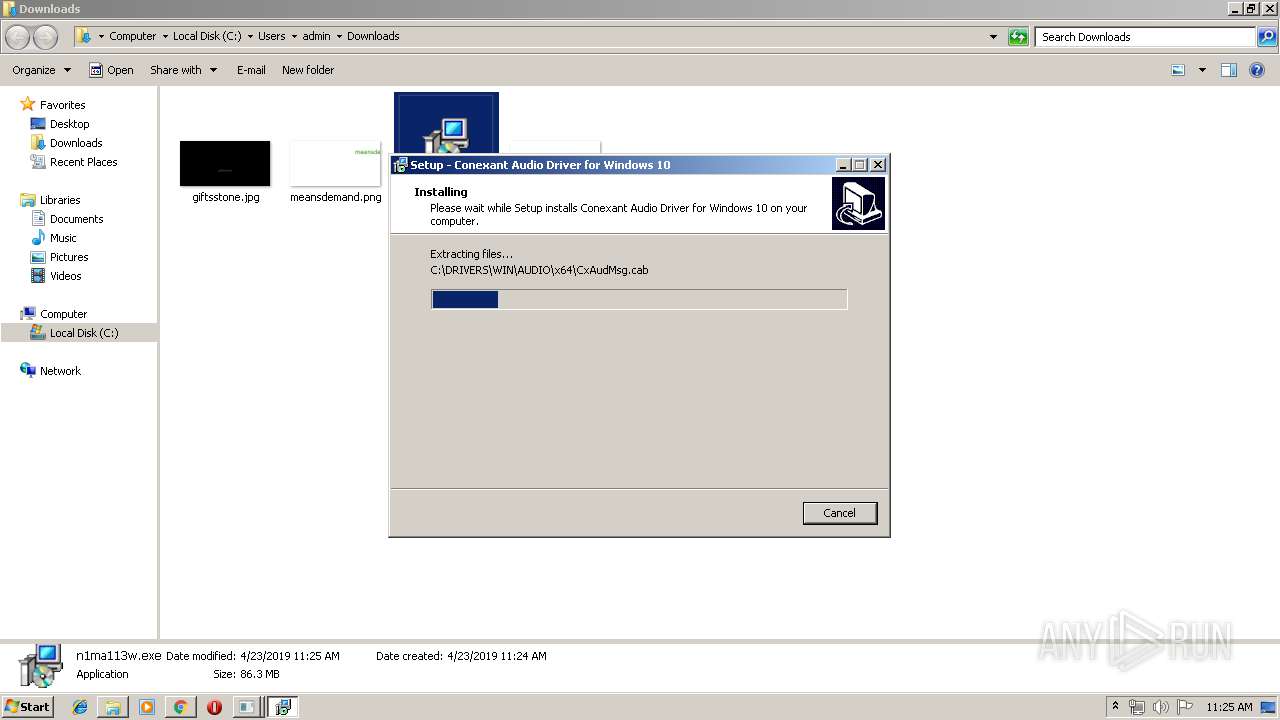
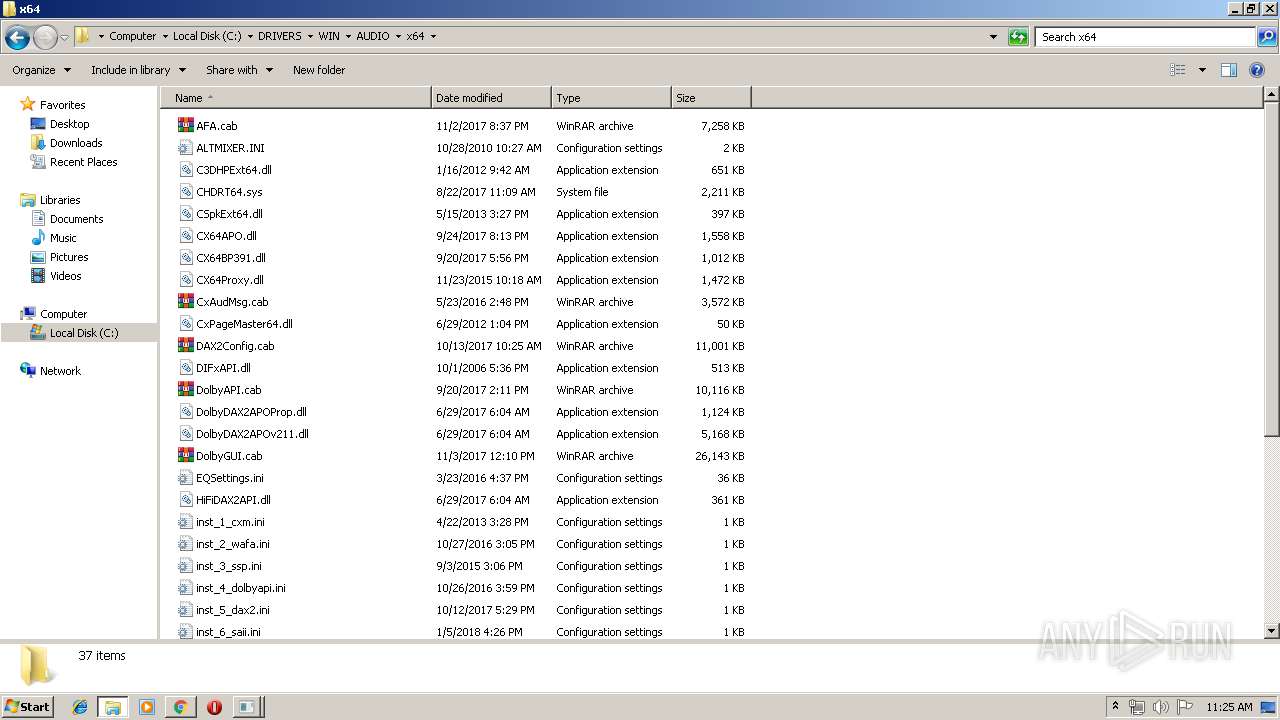
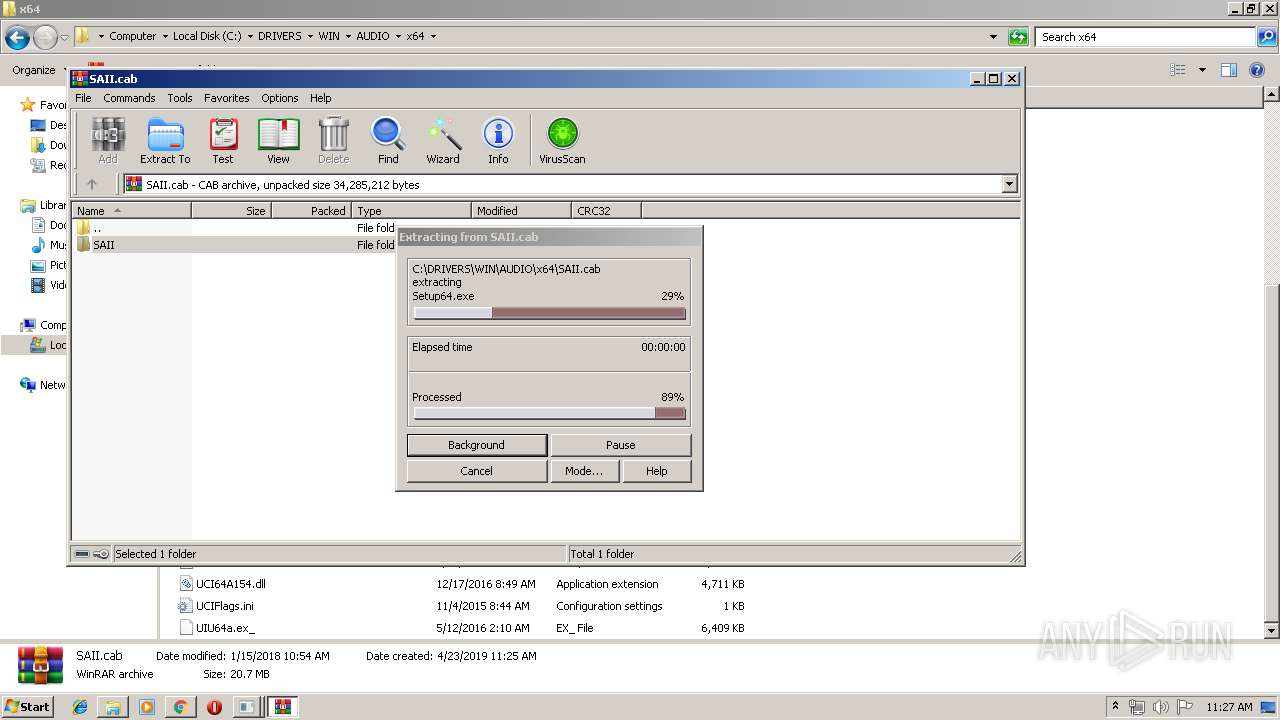
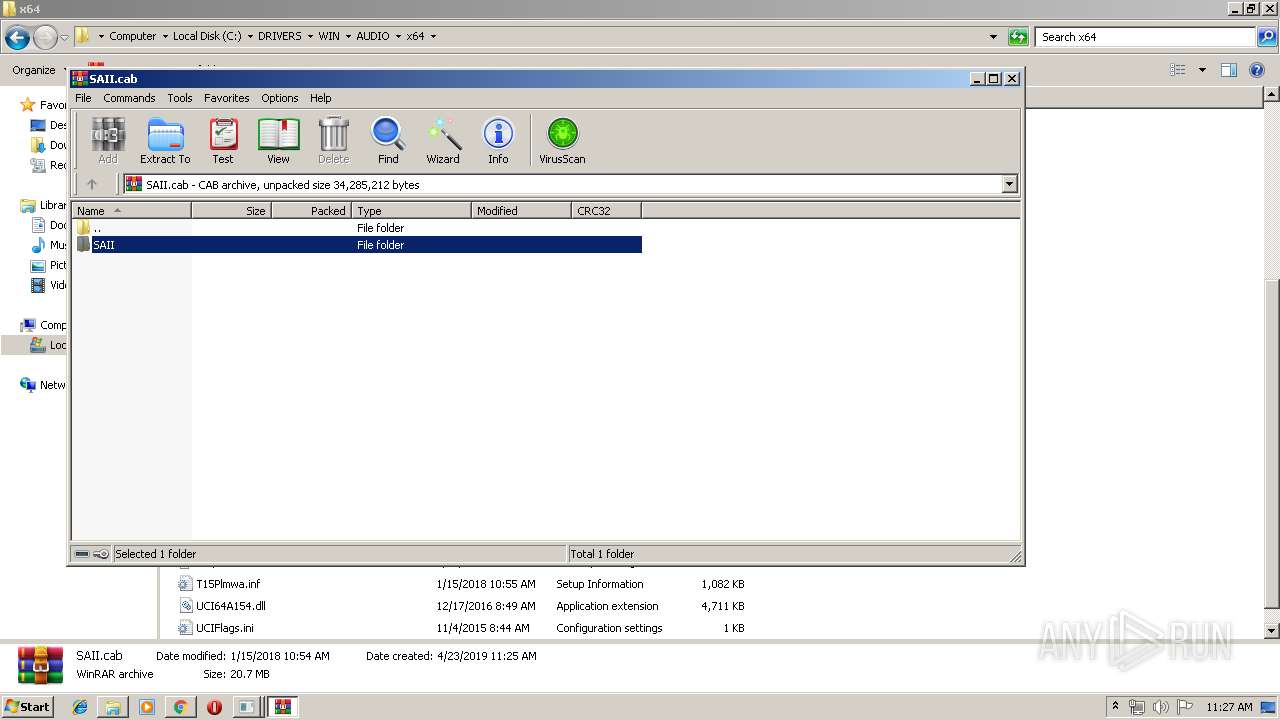
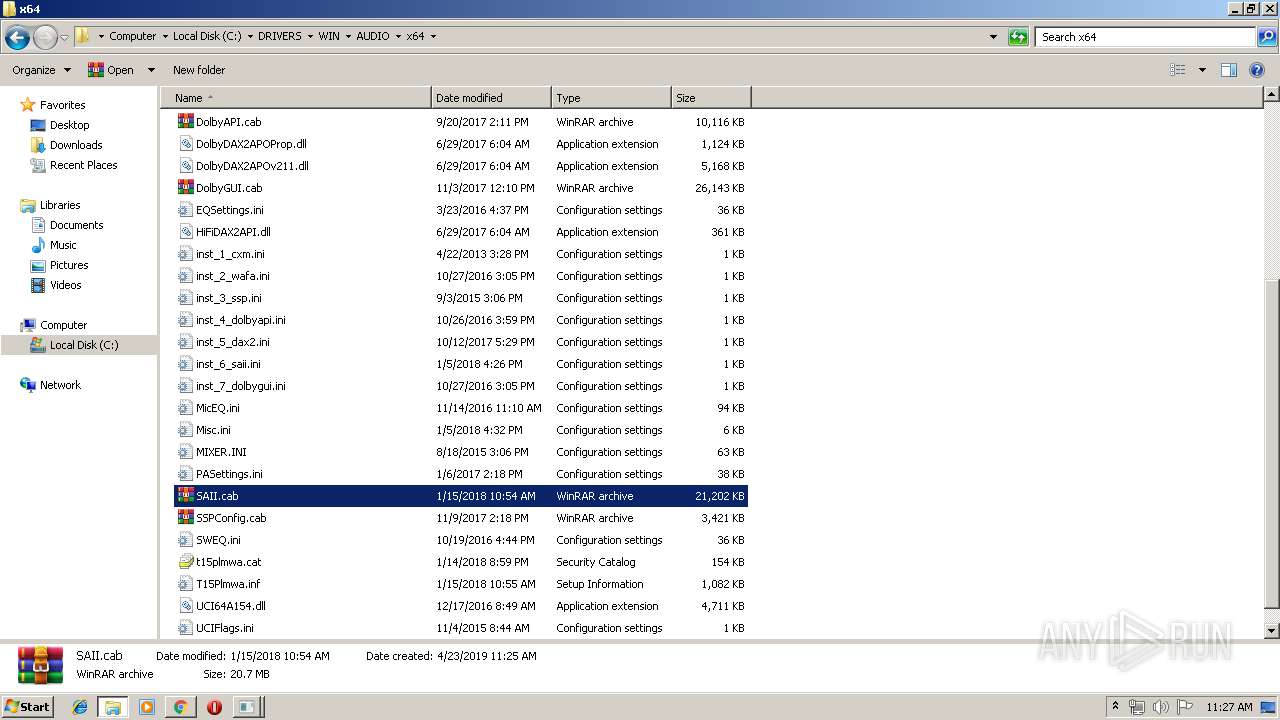
Executable content was dropped or overwritten
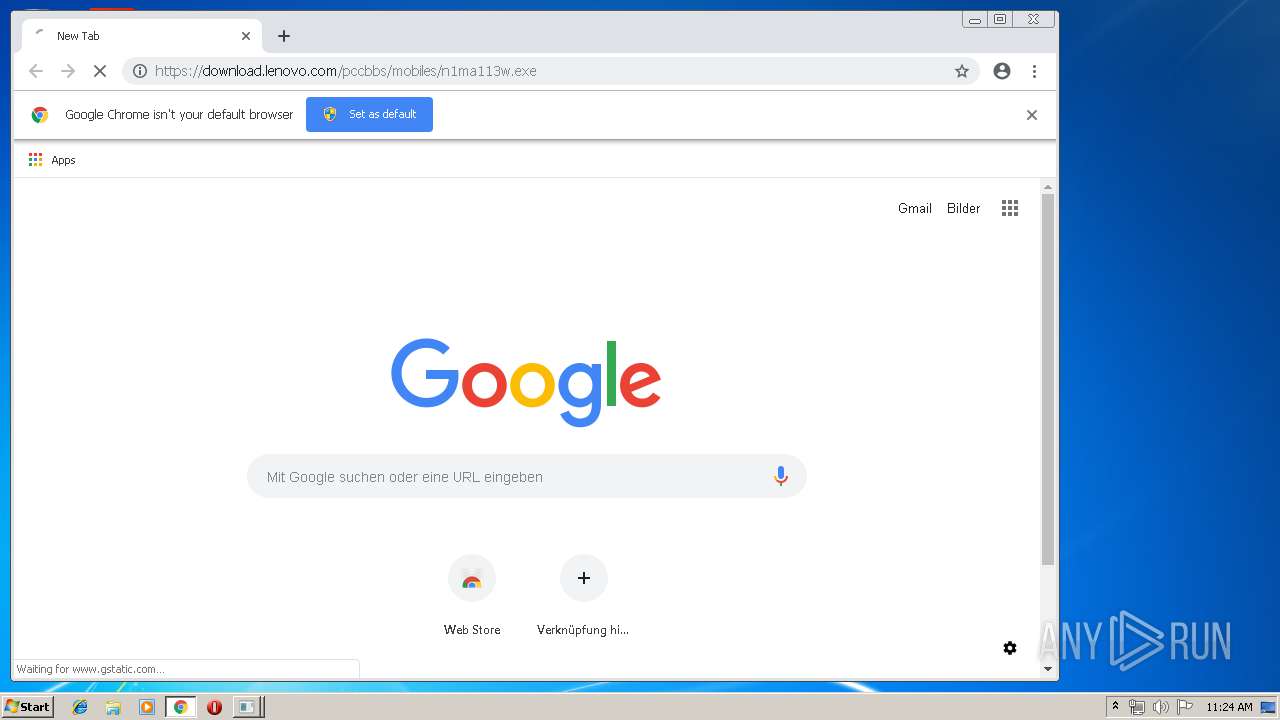
- chrome.exe (PID: 2512)
- WinRAR.exe (PID: 3716)
- n1ma113w.tmp (PID: 3568)
- n1ma113w.exe (PID: 1104)
- n1ma113w.exe (PID: 868)
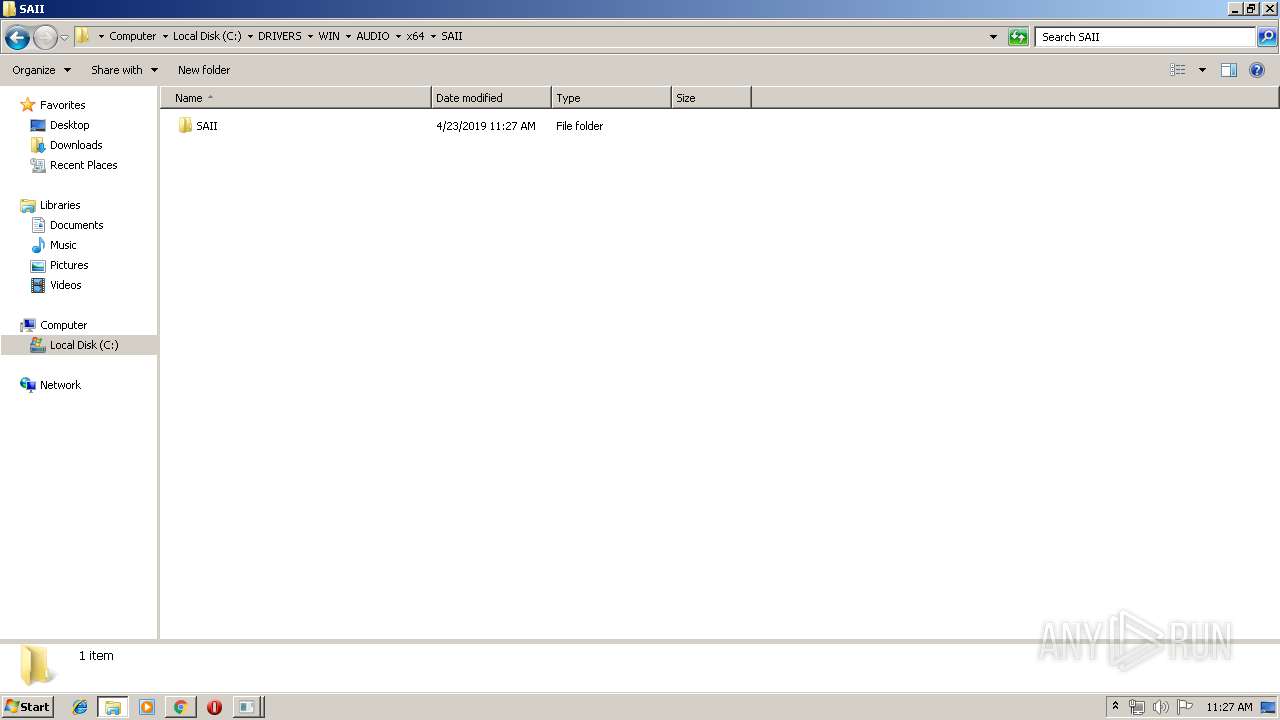
- Setup.exe (PID: 2172)
- mscorsvw.exe (PID: 2416)
- mscorsvw.exe (PID: 3896)
- mscorsvw.exe (PID: 980)
- mscorsvw.exe (PID: 2948)
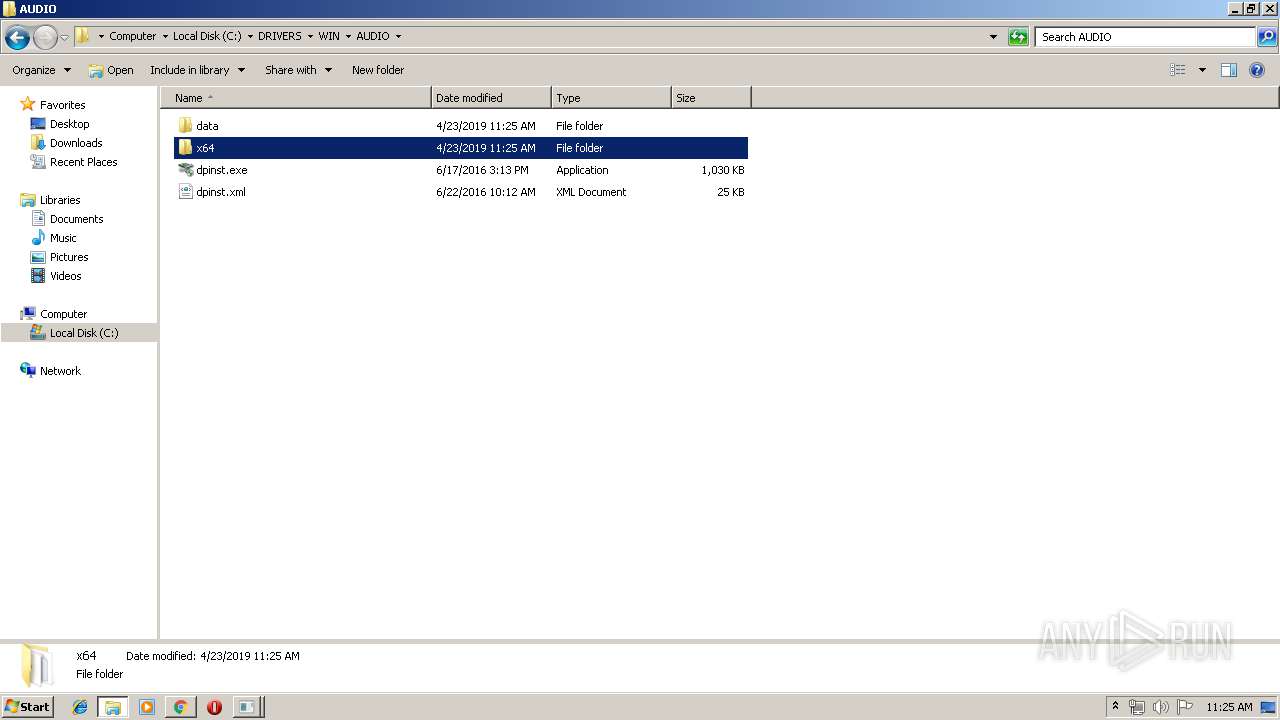
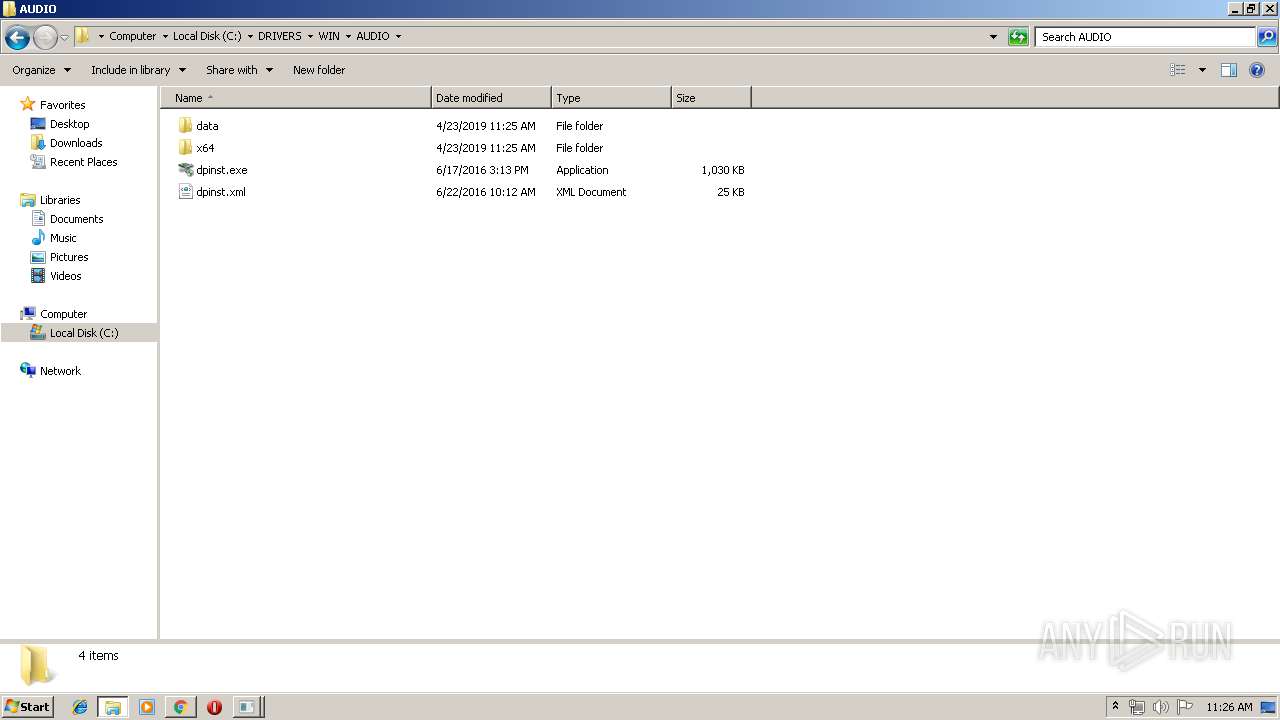
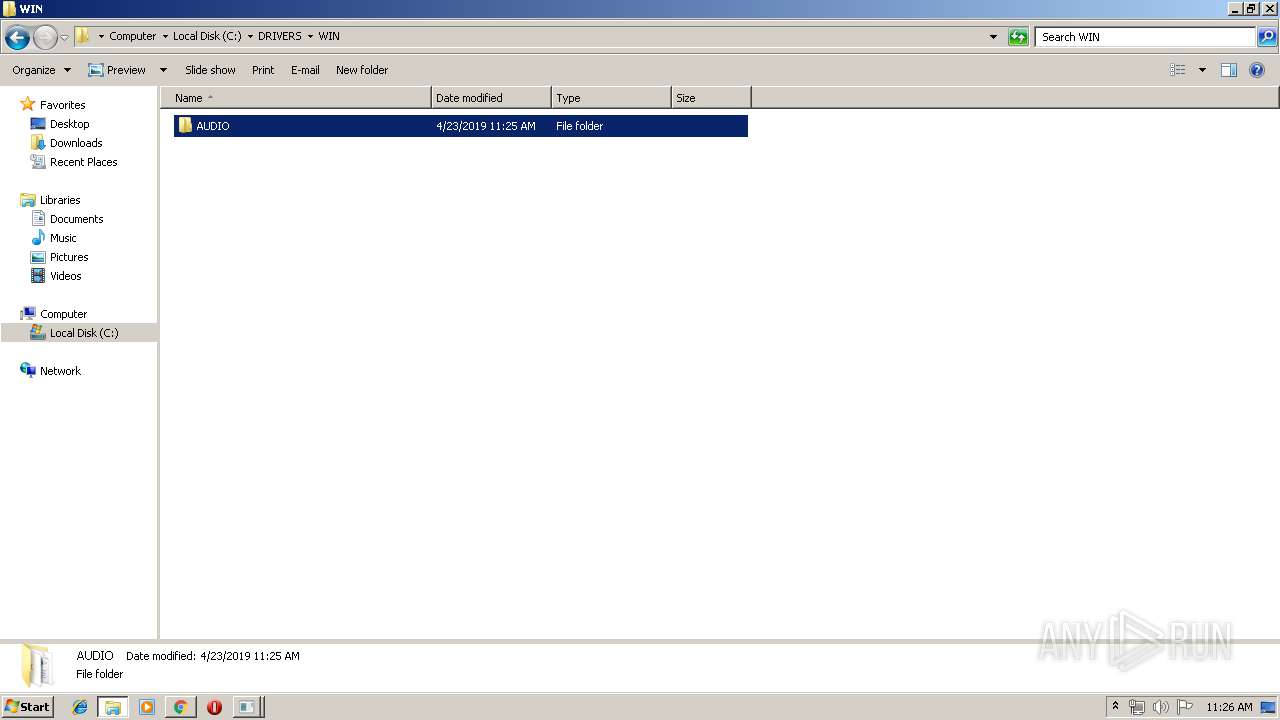
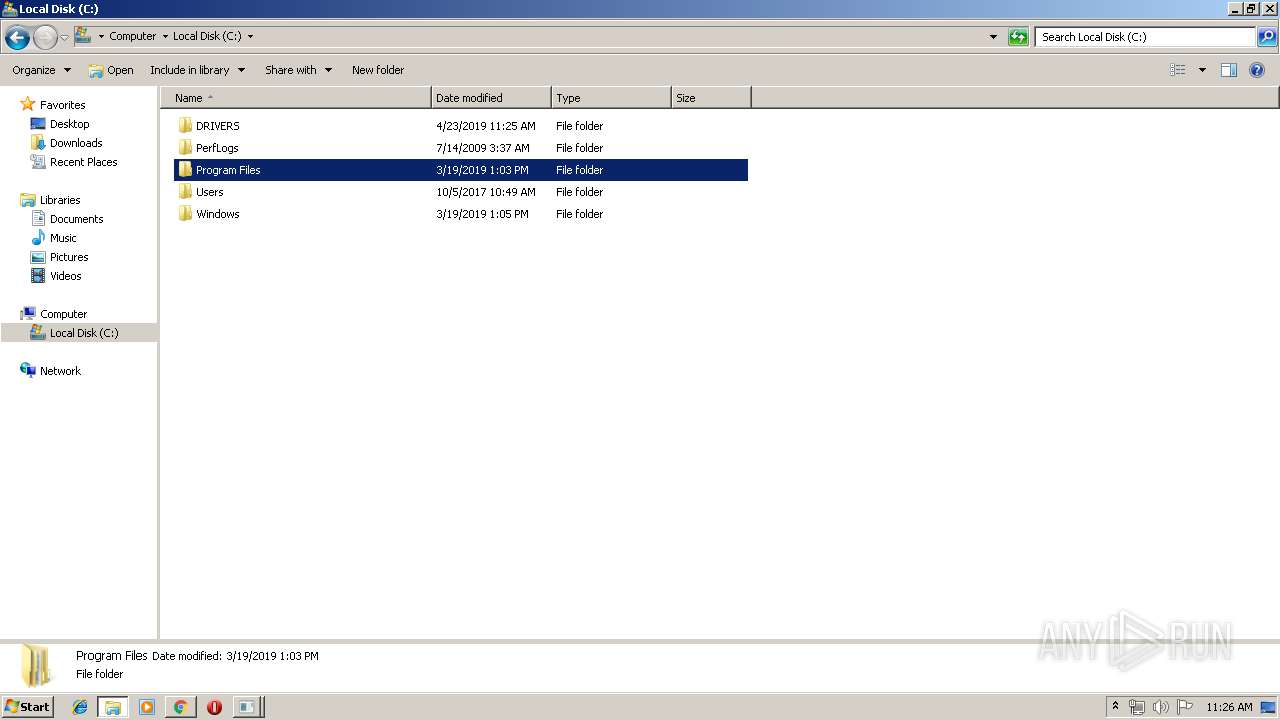
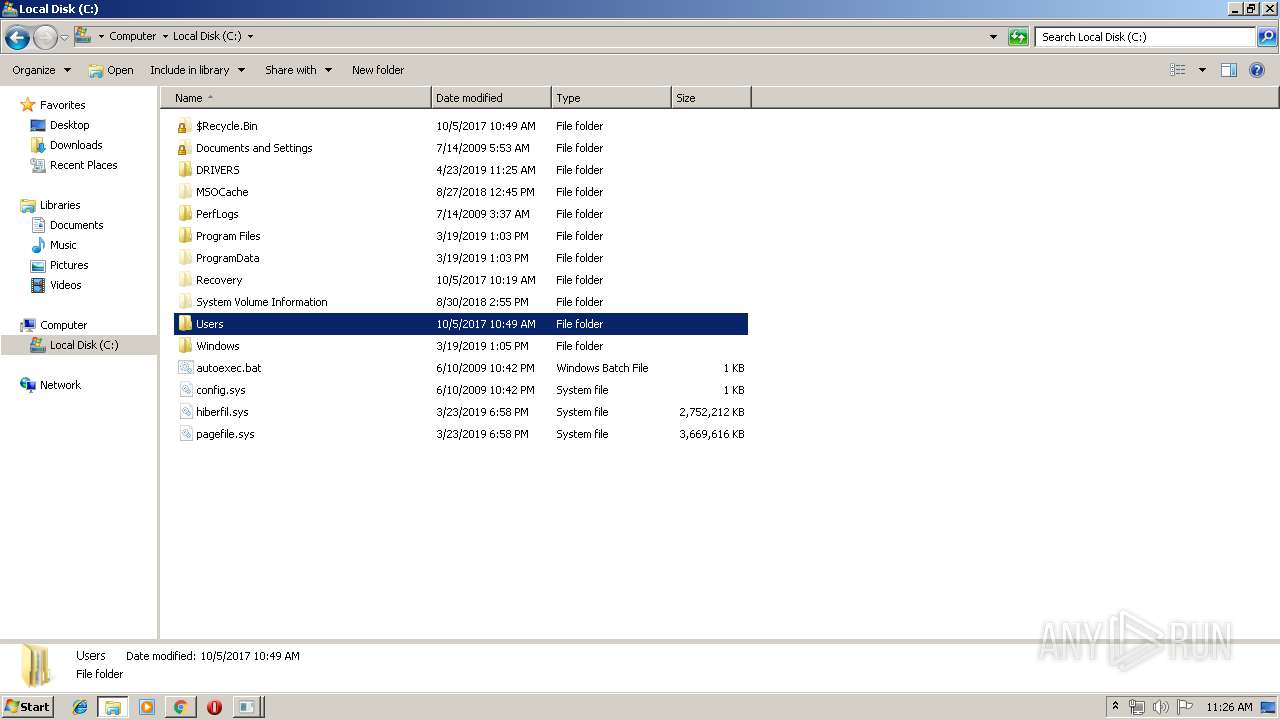
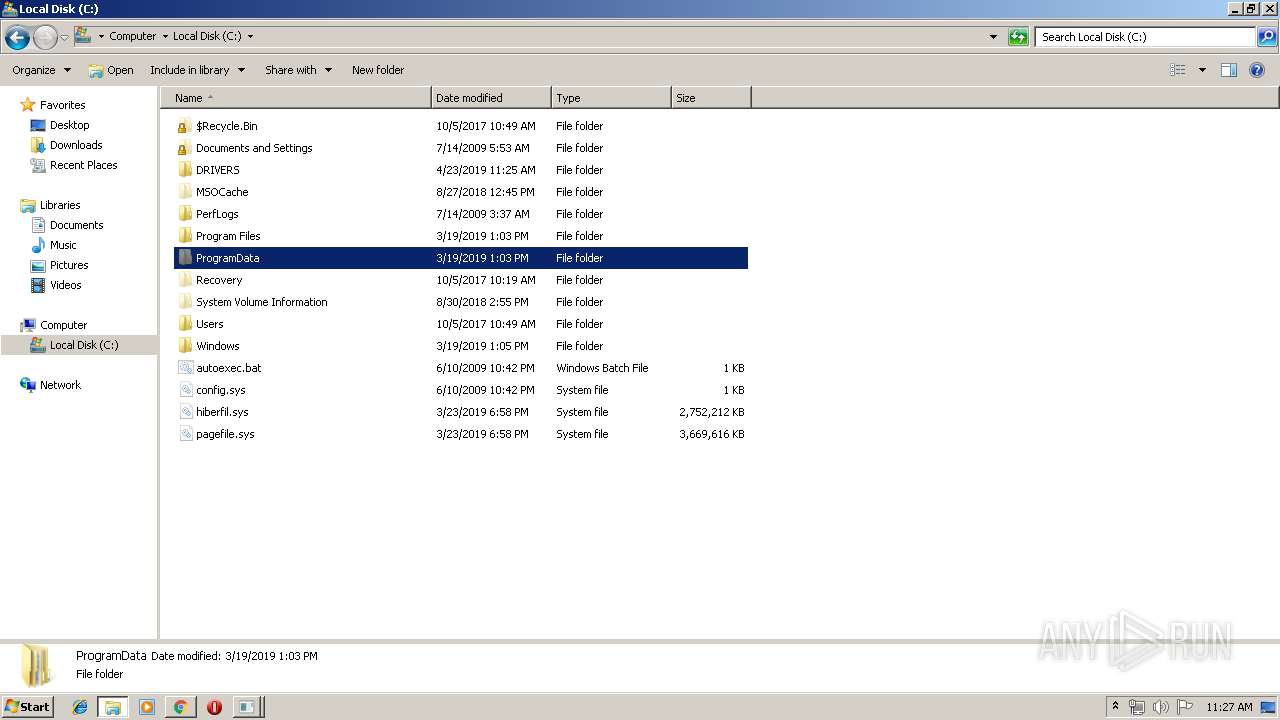
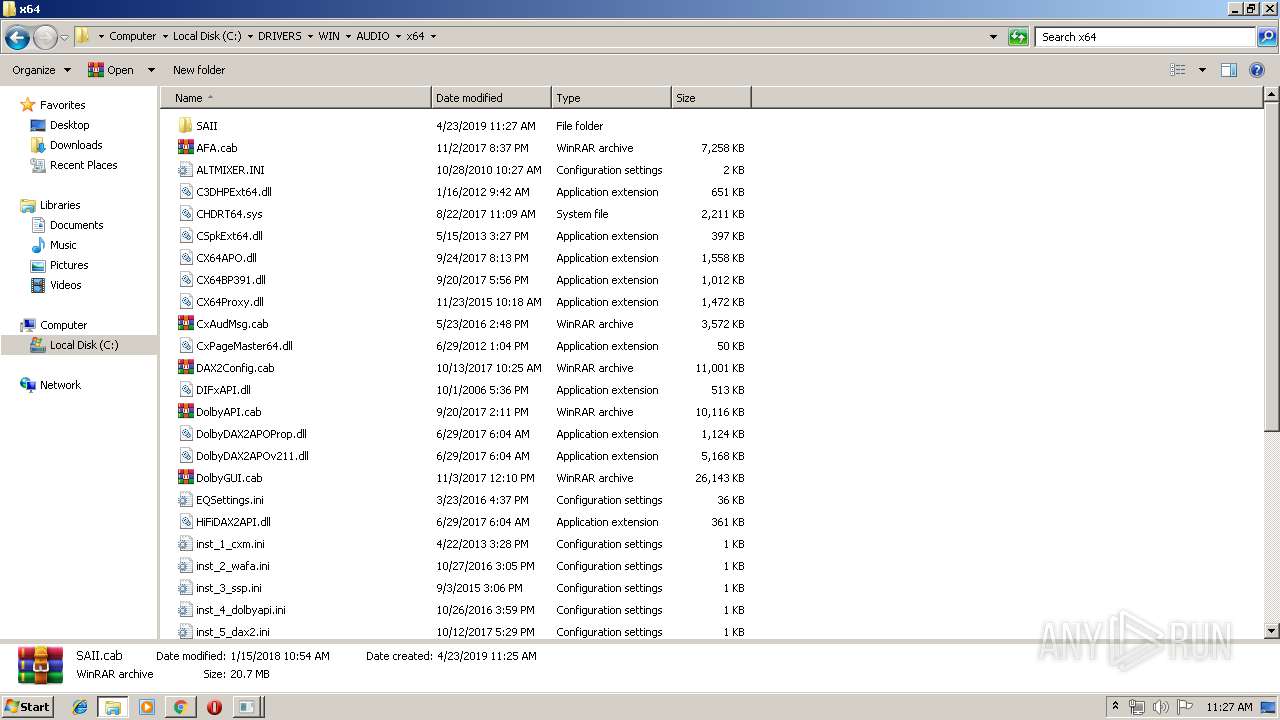
Creates files in the Windows directory
- Setup.exe (PID: 2172)
- ngen.exe (PID: 2556)
- ngen.exe (PID: 2812)
- mscorsvw.exe (PID: 2416)
- mscorsvw.exe (PID: 2948)
- mscorsvw.exe (PID: 3896)
- mscorsvw.exe (PID: 980)
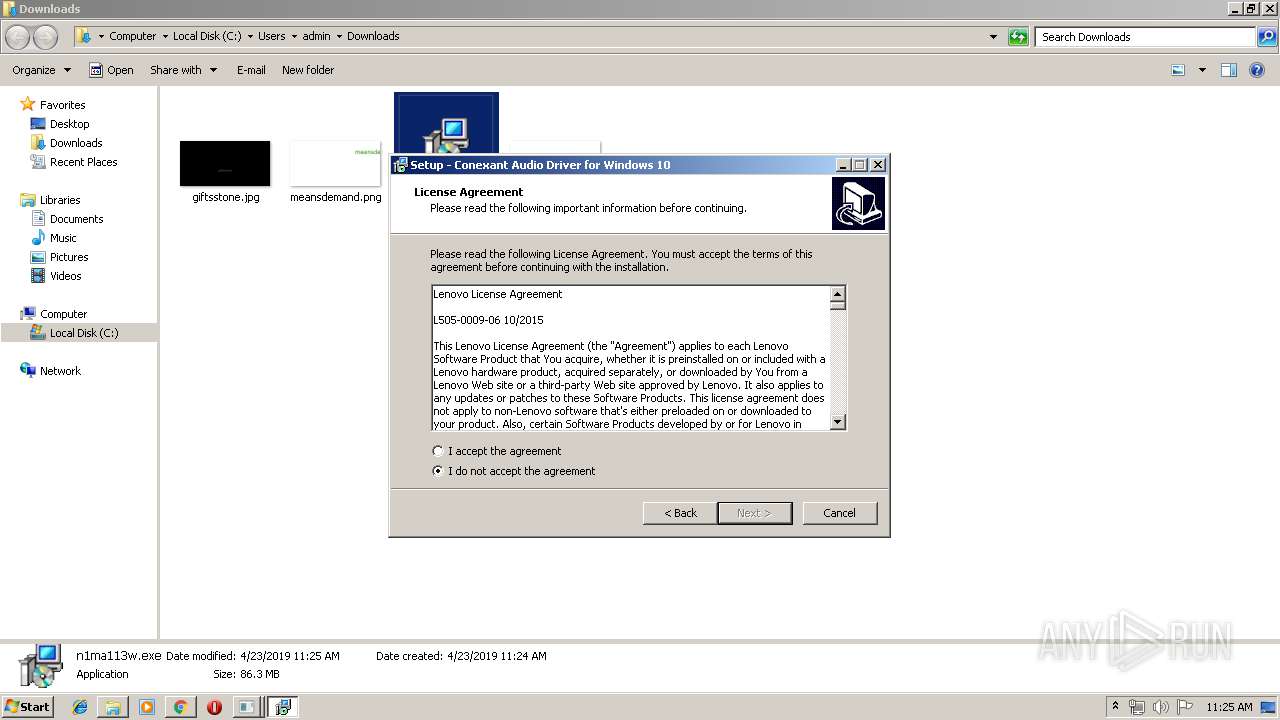
Creates or modifies windows services
- Setup.exe (PID: 2172)
- SASrv.exe (PID: 2708)
Modifies files in Chrome extension folder
- chrome.exe (PID: 2512)
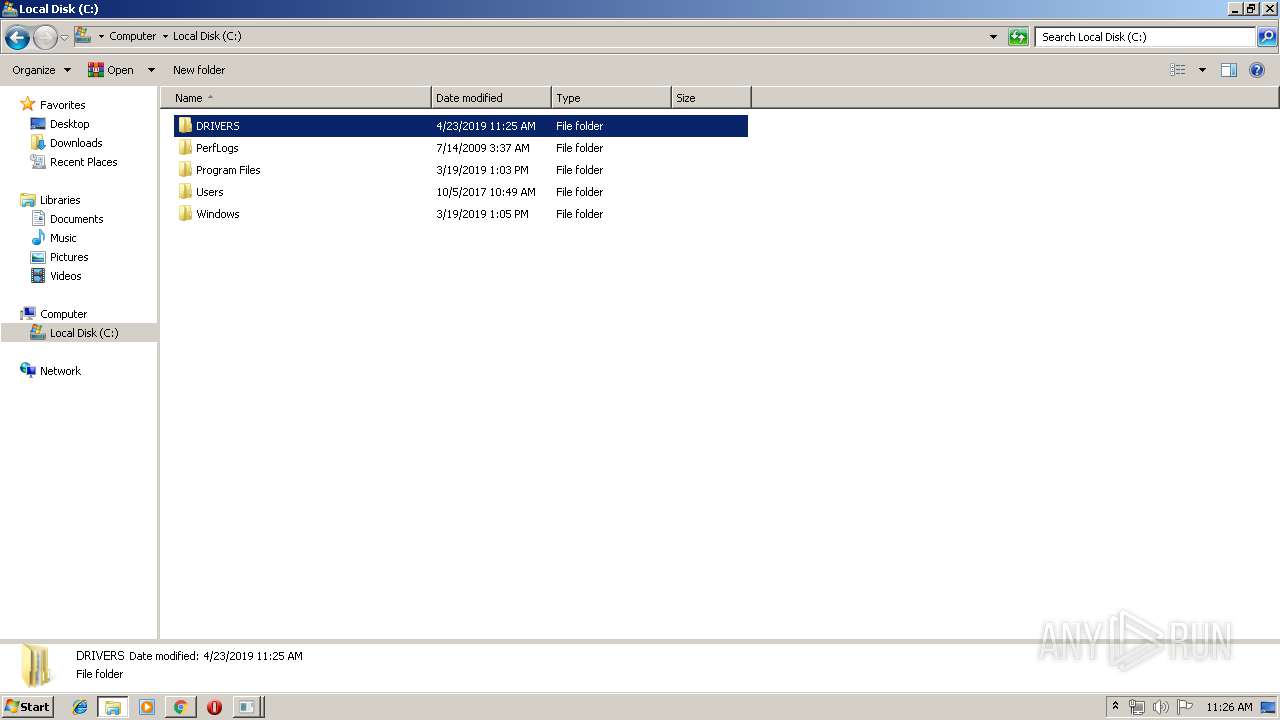
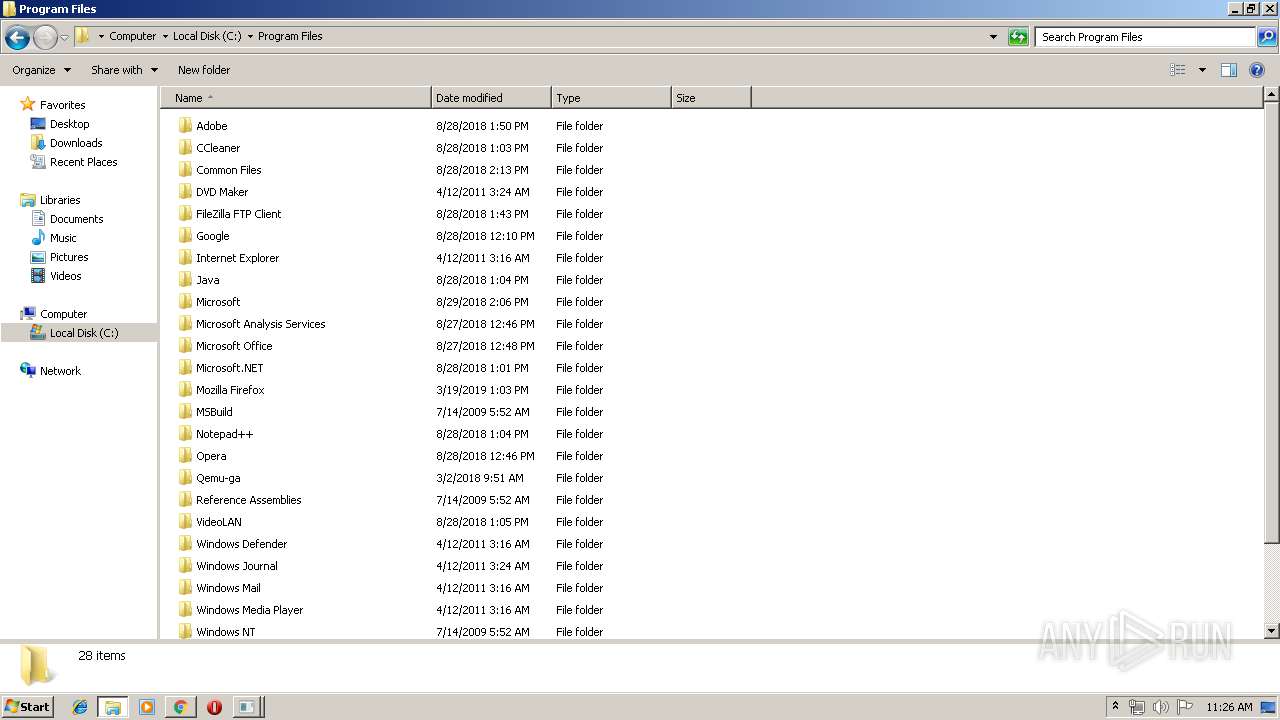
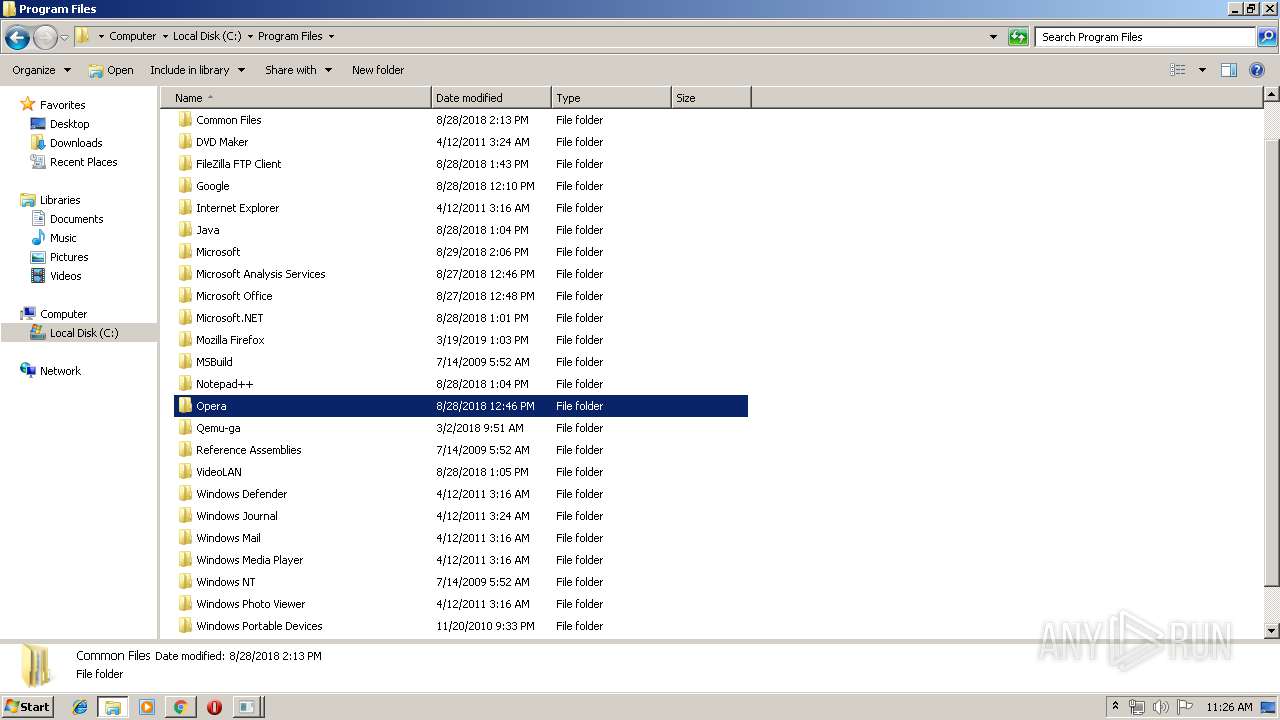
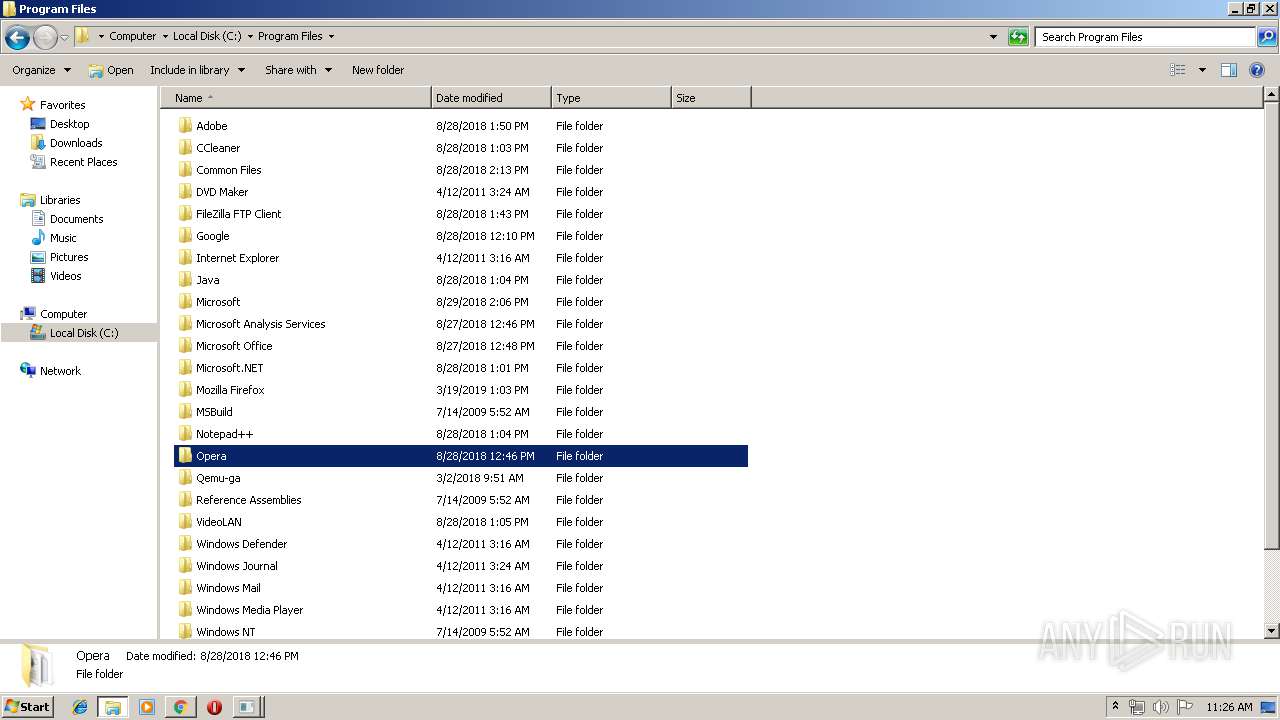
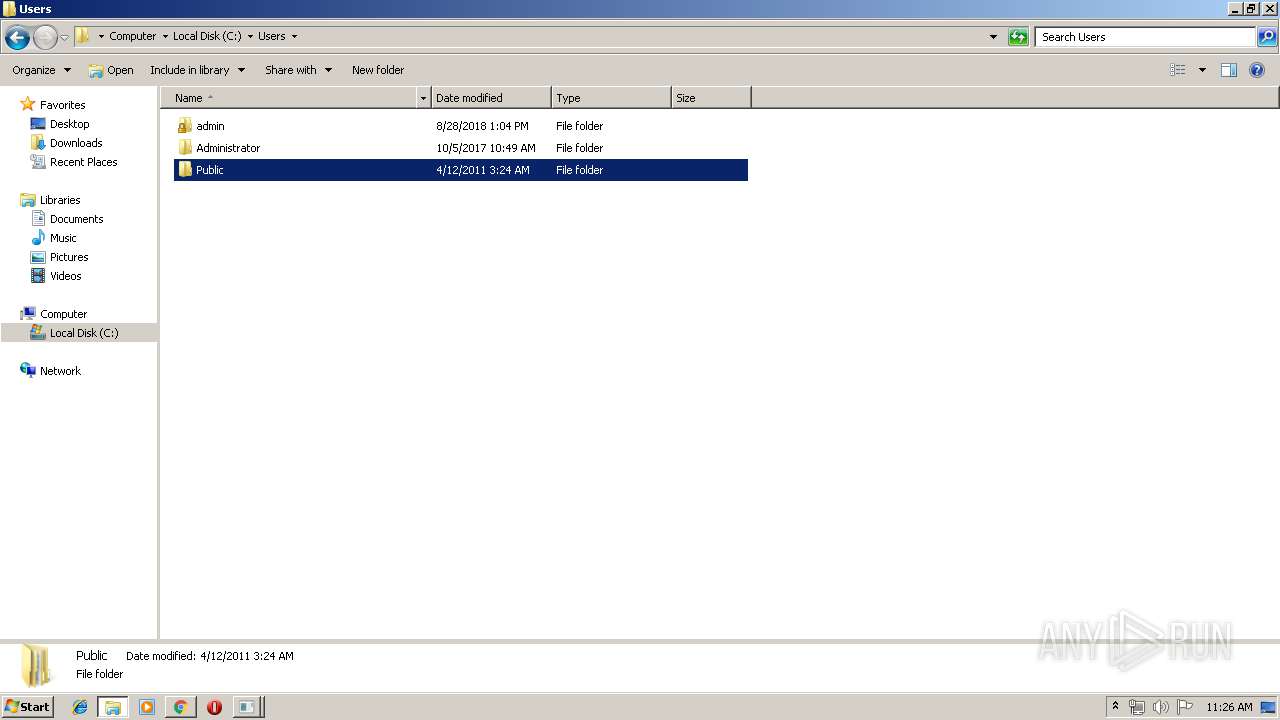
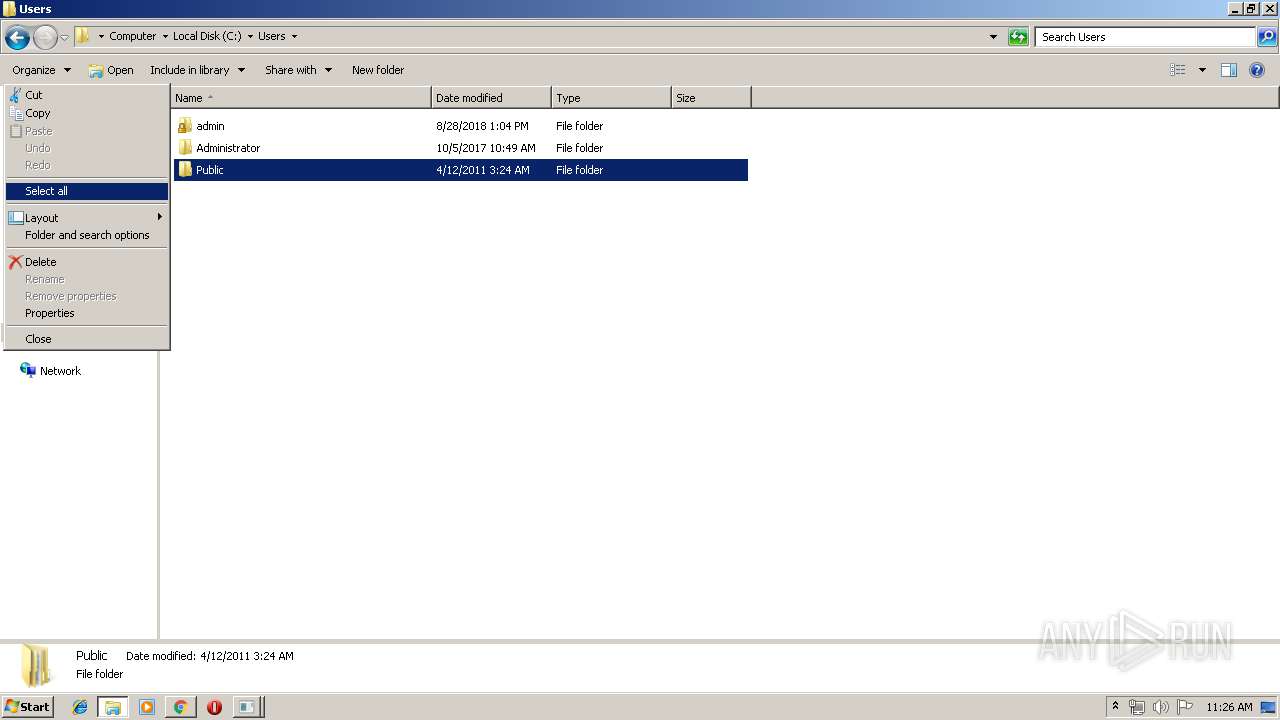
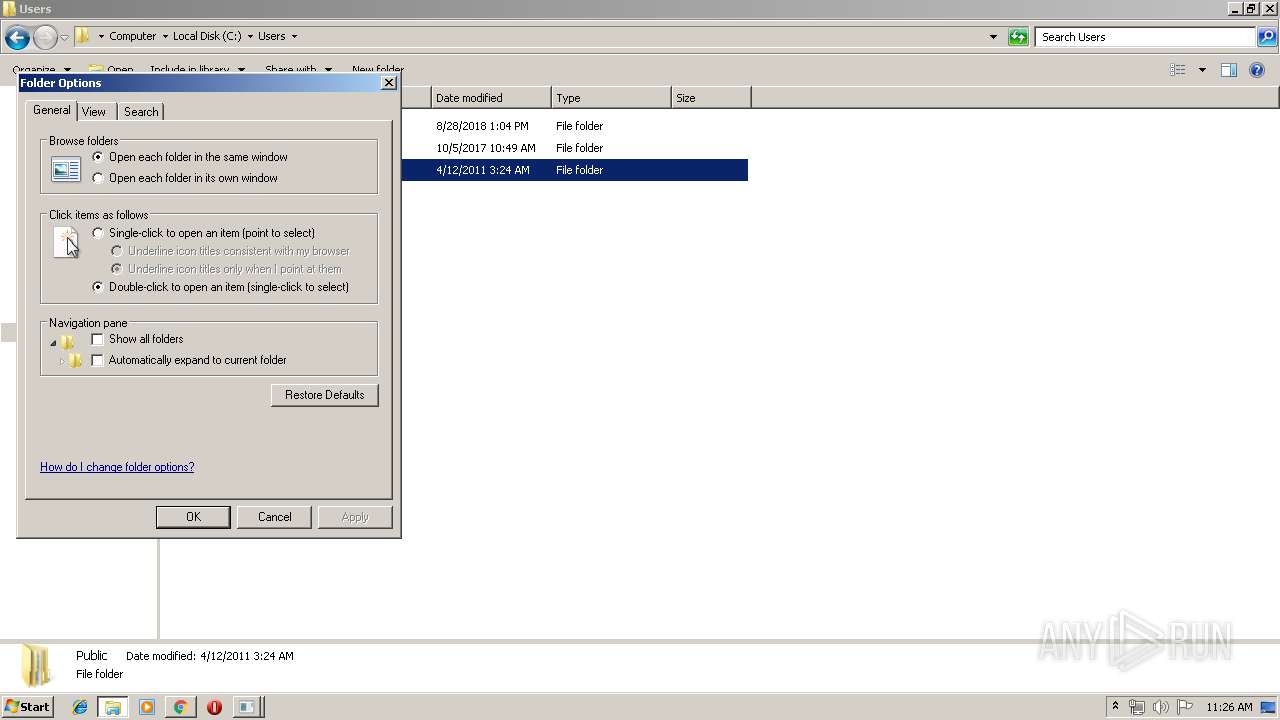
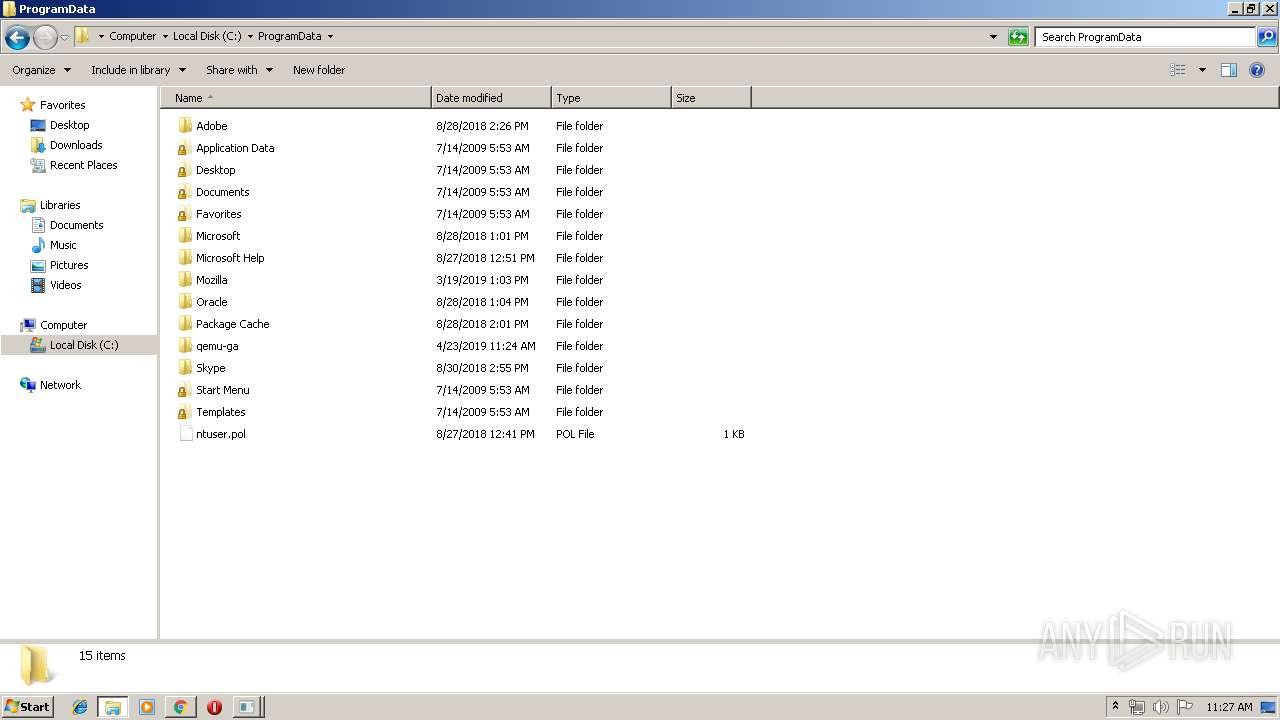
Searches for installed software
- Setup.exe (PID: 2172)
Creates files in the program directory
- Setup.exe (PID: 2172)
Creates COM task schedule object
- Setup.exe (PID: 2172)
- regsvr32.exe (PID: 2164)
Creates a software uninstall entry
- Setup.exe (PID: 2172)
Removes files from Windows directory
- mscorsvw.exe (PID: 2416)
- mscorsvw.exe (PID: 3896)
- Setup.exe (PID: 2172)
- mscorsvw.exe (PID: 2948)
- mscorsvw.exe (PID: 980)
Modifies the open verb of a shell class
- Setup.exe (PID: 2172)
INFO
Application launched itself
- chrome.exe (PID: 2512)
Application was dropped or rewritten from another process
- n1ma113w.tmp (PID: 3400)
- n1ma113w.tmp (PID: 3568)
Reads settings of System Certificates
- chrome.exe (PID: 2512)
Loads dropped or rewritten executable
- n1ma113w.tmp (PID: 3568)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2011:08:10 04:46:06+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 153088 |
| InitializedDataSize: | 172032 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x9b21 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 5.2.0.0 |
| ProductVersionNumber: | 5.2.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | Special build |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Sysinternals - www.sysinternals.com |
| FileDescription: | Reports effective permissions for securable objects |
| FileVersion: | 5.02 |
| InternalName: | Accesschk |
| LegalCopyright: | Copyright (C) 2006-2011 Mark Russinovich |
| OriginalFileName: | accesschk.exe |
| ProductName: | Sysinternals AccessChk |
| ProductVersion: | 5.02 |
| SpecialBuild: |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 10-Aug-2011 02:46:06 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Sysinternals - www.sysinternals.com |
| FileDescription: | Reports effective permissions for securable objects |
| FileVersion: | 5.02 |
| InternalName: | Accesschk |
| LegalCopyright: | Copyright (C) 2006-2011 Mark Russinovich |
| OriginalFilename: | accesschk.exe |
| ProductName: | Sysinternals AccessChk |
| ProductVersion: | 5.02 |
| SpecialBuild: | - |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 10-Aug-2011 02:46:06 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000255FC | 0x00025600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.58312 |
.rdata | 0x00027000 | 0x00008D52 | 0x00008E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.04144 |
.data | 0x00030000 | 0x0001FA48 | 0x0001DE00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.460068 |
.rsrc | 0x00050000 | 0x000014A8 | 0x00001600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.4421 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.89381 | 891 | UNKNOWN | English - United States | RT_MANIFEST |
101 | 4.45986 | 3216 | UNKNOWN | English - United States | BINRES |
Imports
ADVAPI32.dll |
COMDLG32.dll |
GDI32.dll |
KERNEL32.dll |
NETAPI32.dll |
USER32.dll |
VERSION.dll |
Total processes
117
Monitored processes
57
Malicious processes
8
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 300 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=960,12107015881543131917,17542509425726505650,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=2181600214301845056 --mojo-platform-channel-handle=928 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 772 | "C:\Windows\system32\net.exe" start CxUtilSvc | C:\Windows\system32\net.exe | — | Setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
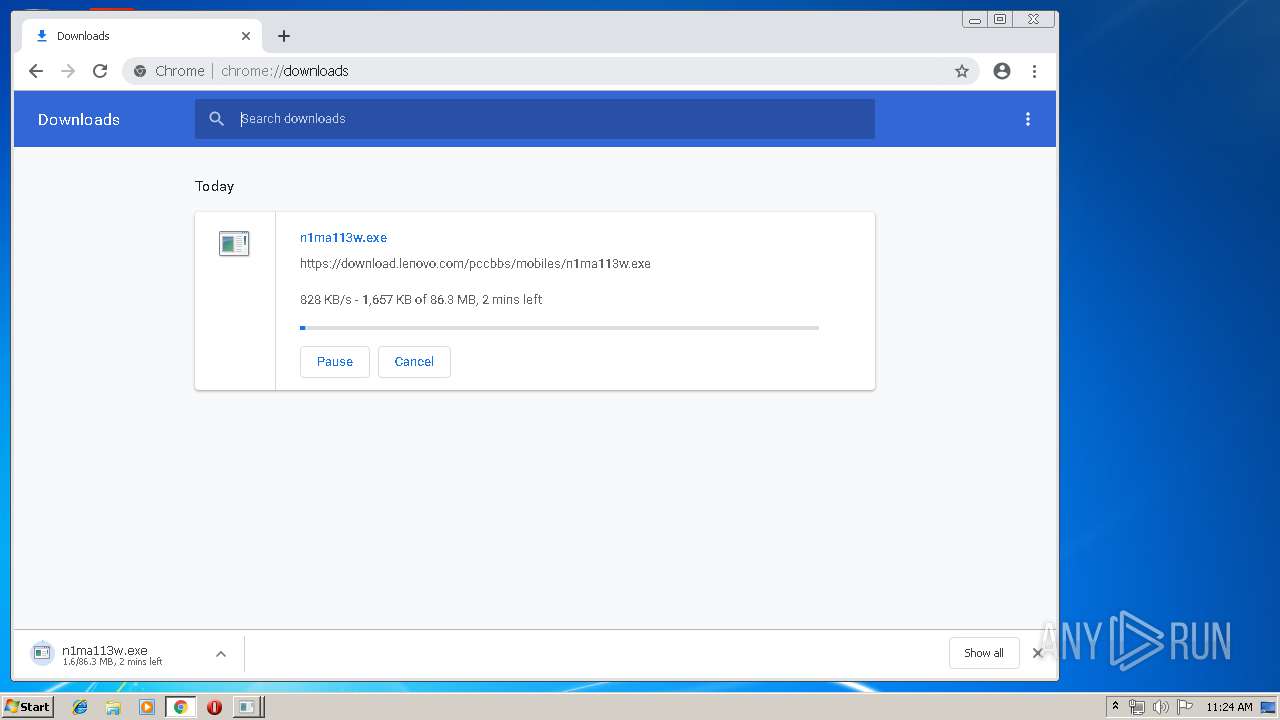
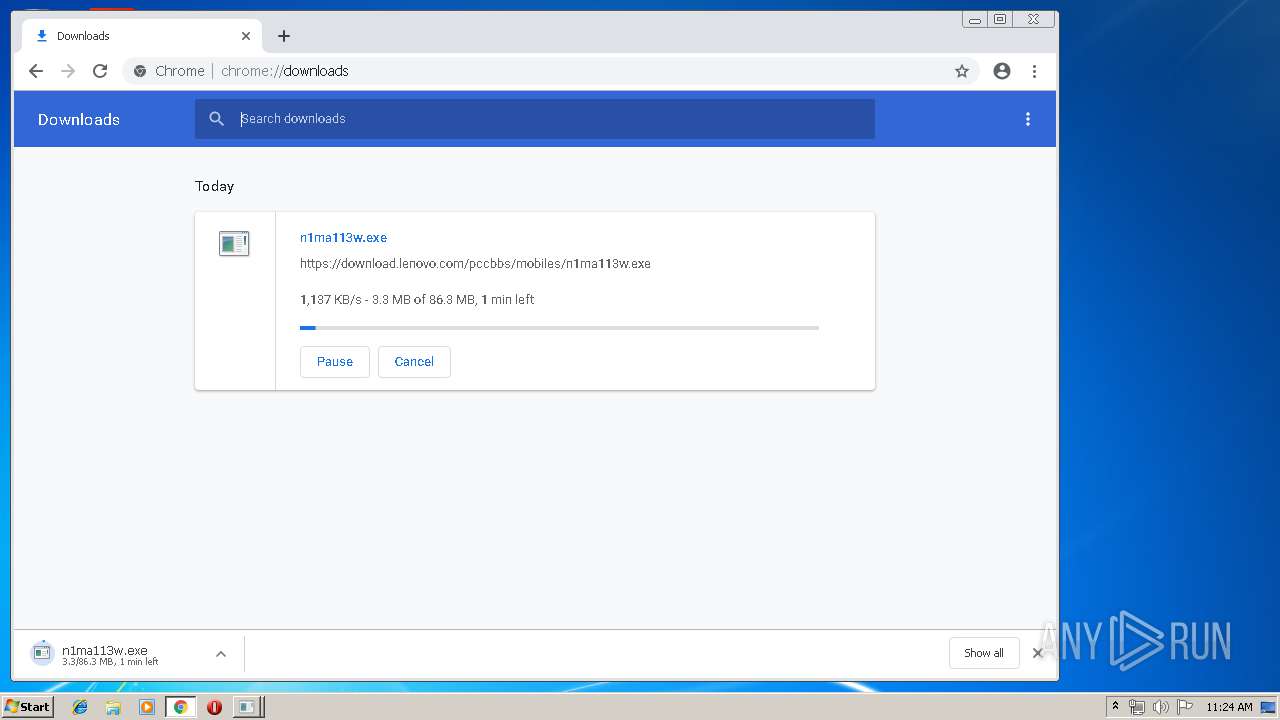
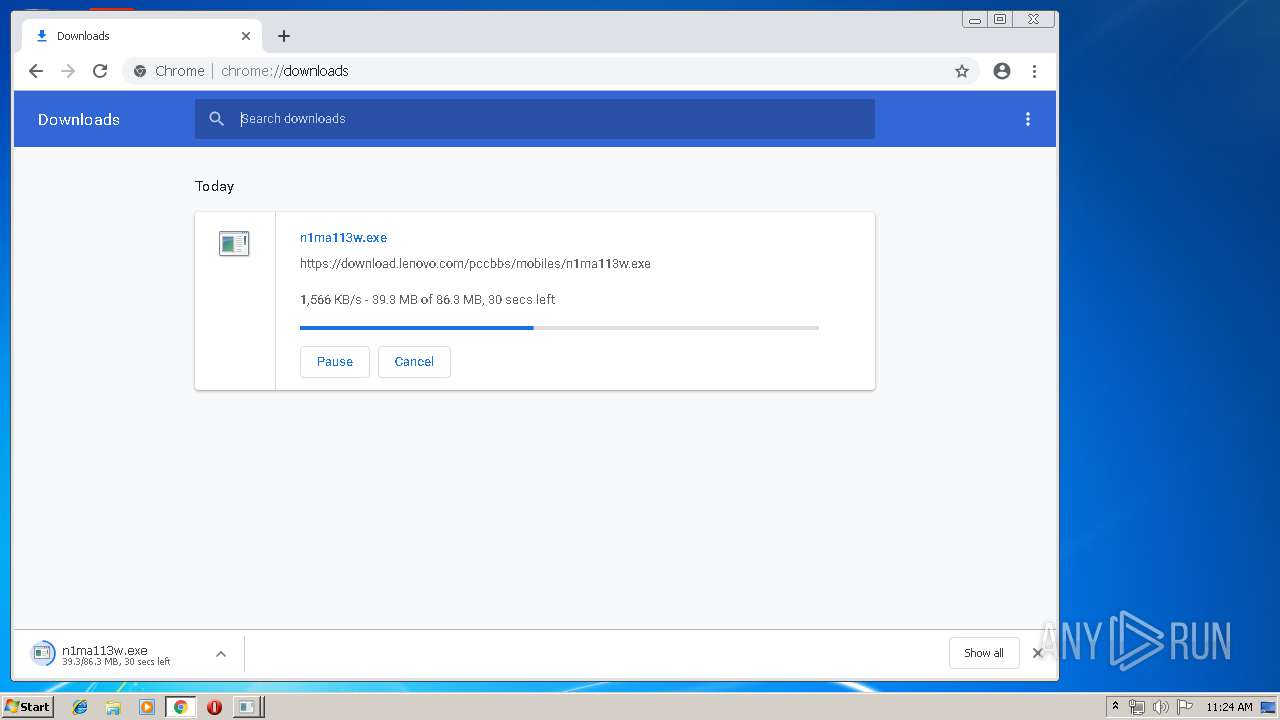
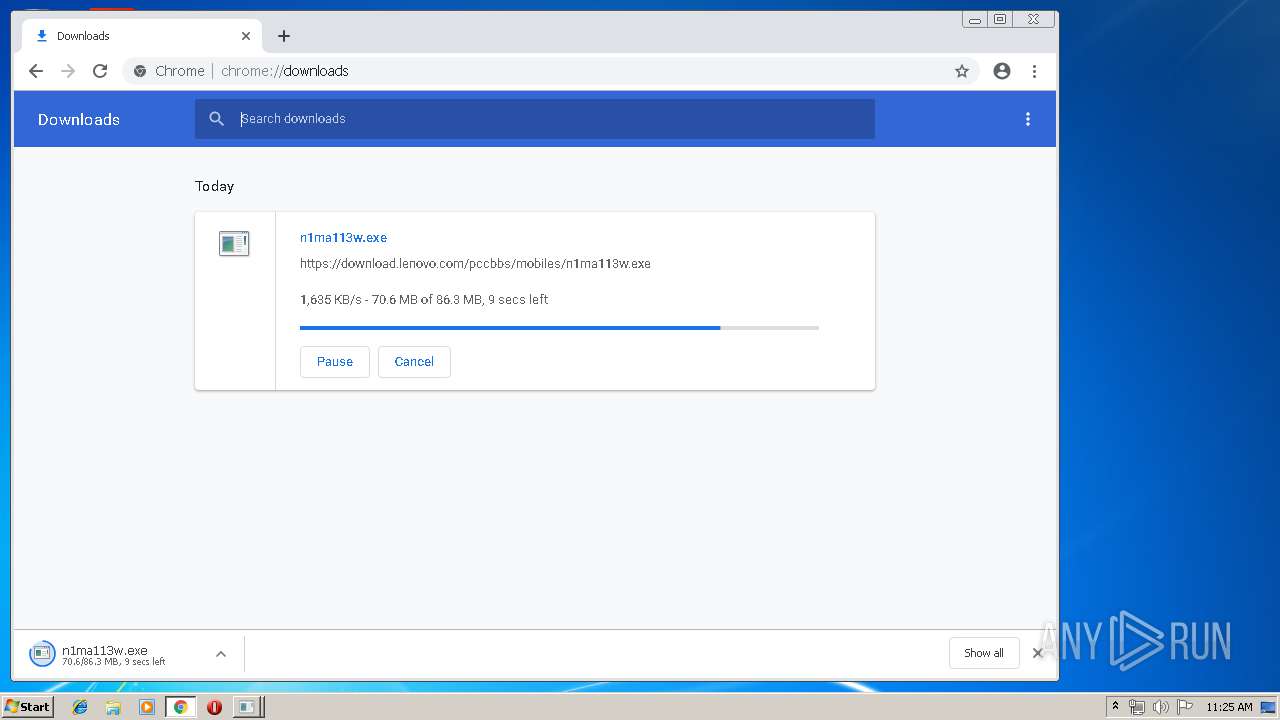
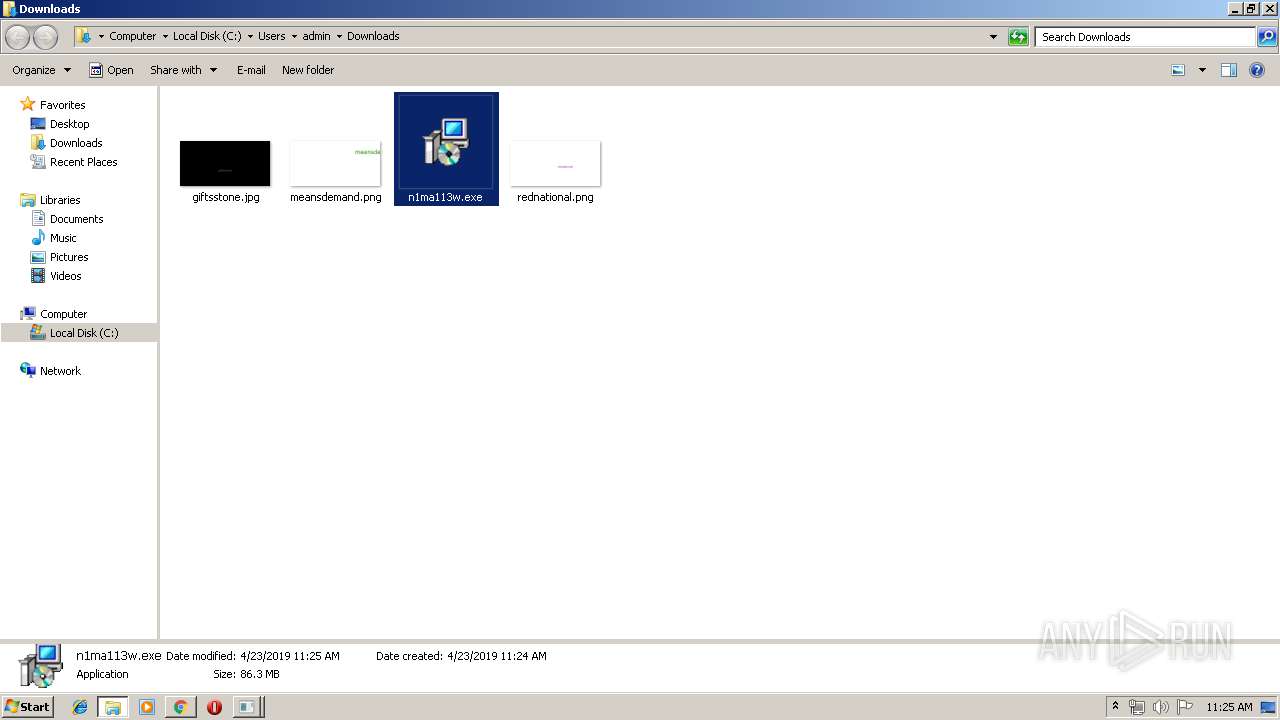
| 868 | "C:\Users\admin\Downloads\n1ma113w.exe" /SPAWNWND=$201F0 /NOTIFYWND=$301D2 | C:\Users\admin\Downloads\n1ma113w.exe | n1ma113w.tmp | ||||||||||||
User: admin Company: Lenovo Group Limited Integrity Level: HIGH Description: For Lenovo Updates Catalog Exit code: 4294967295 Version: 8.66.76.67 (N1MA113W Modules
| |||||||||||||||
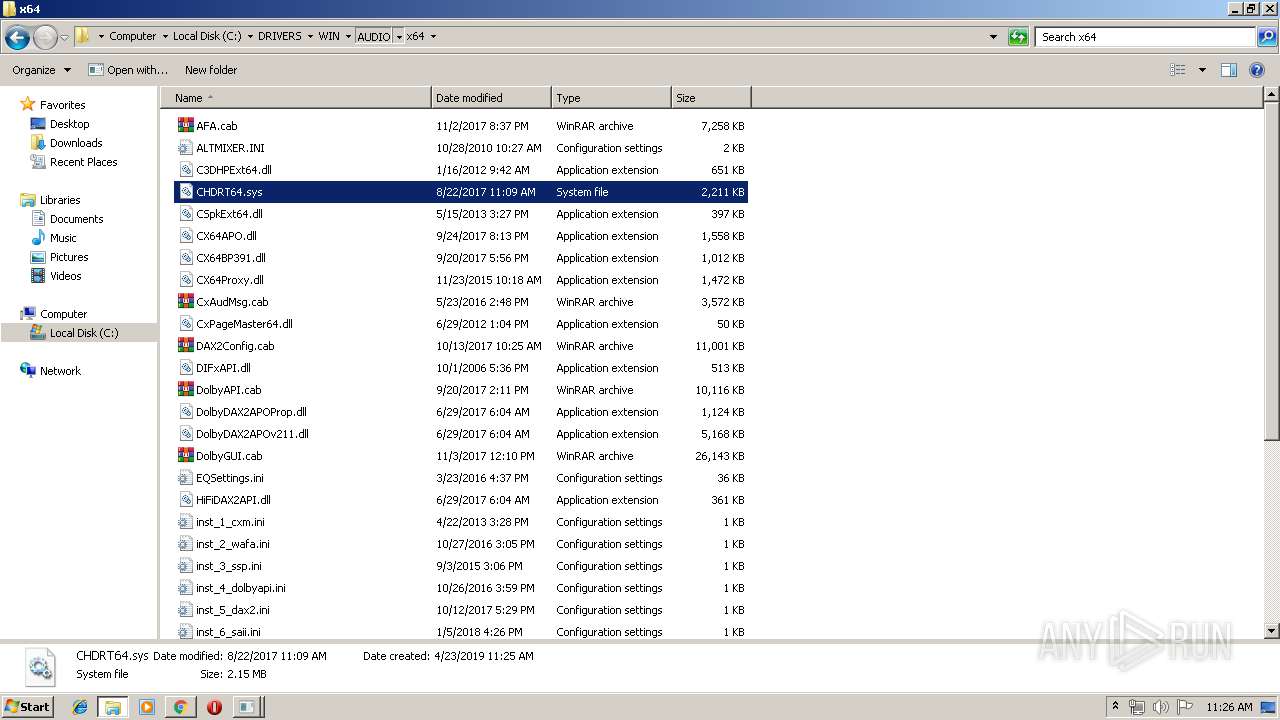
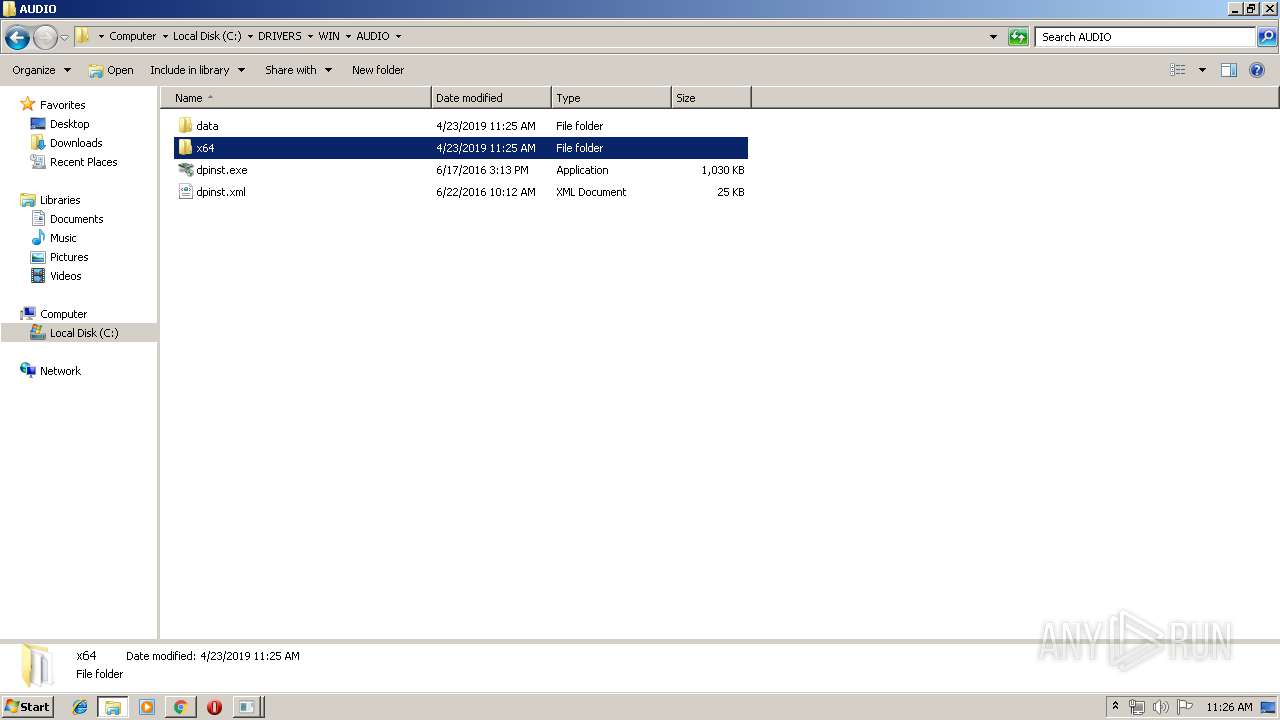
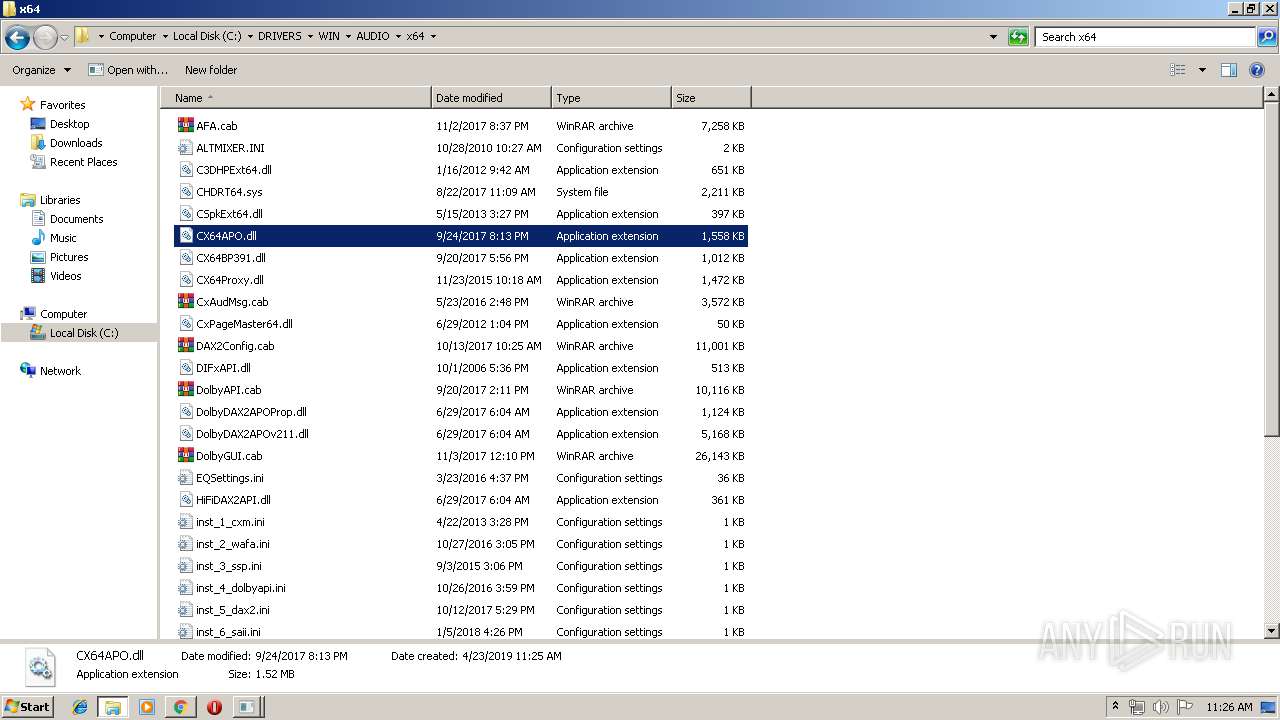
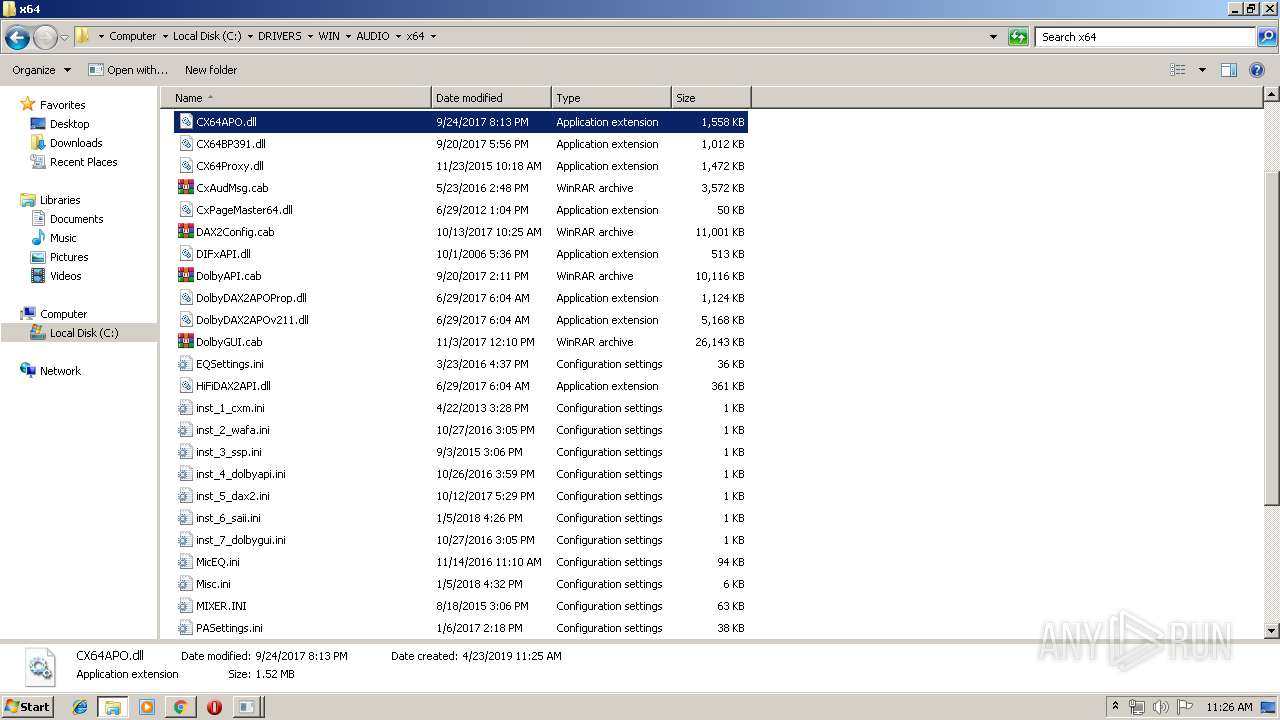
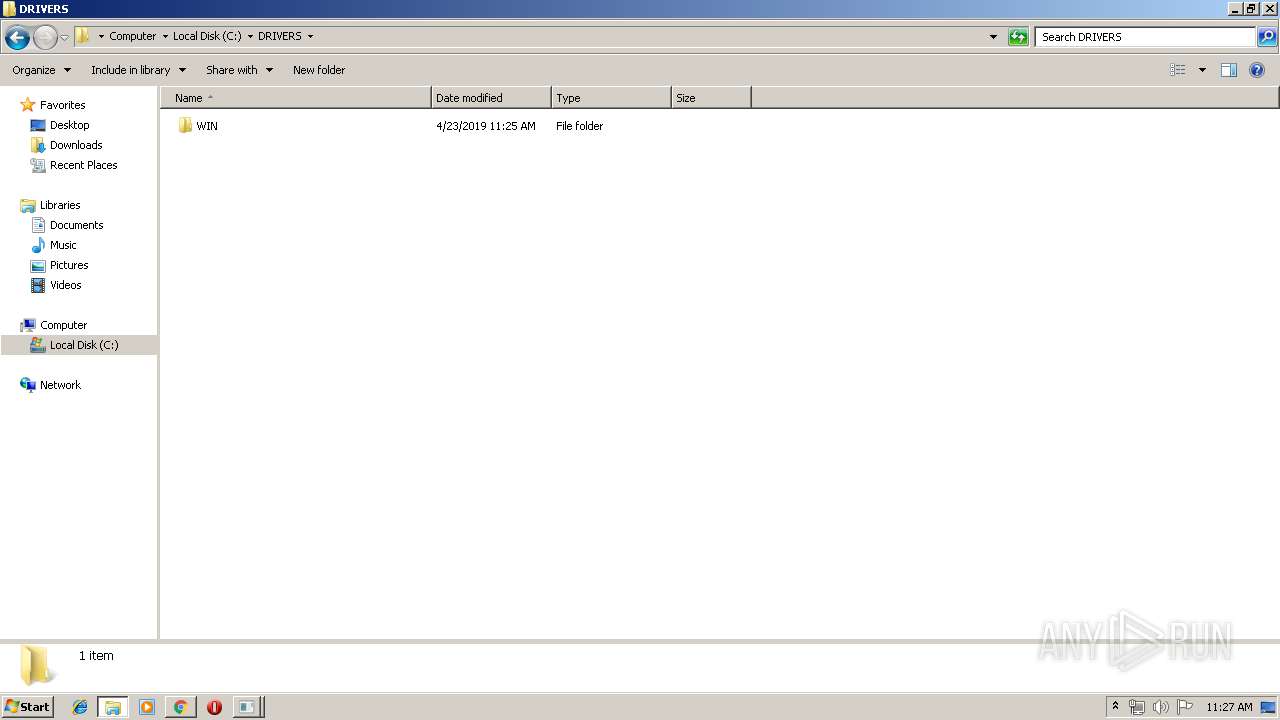
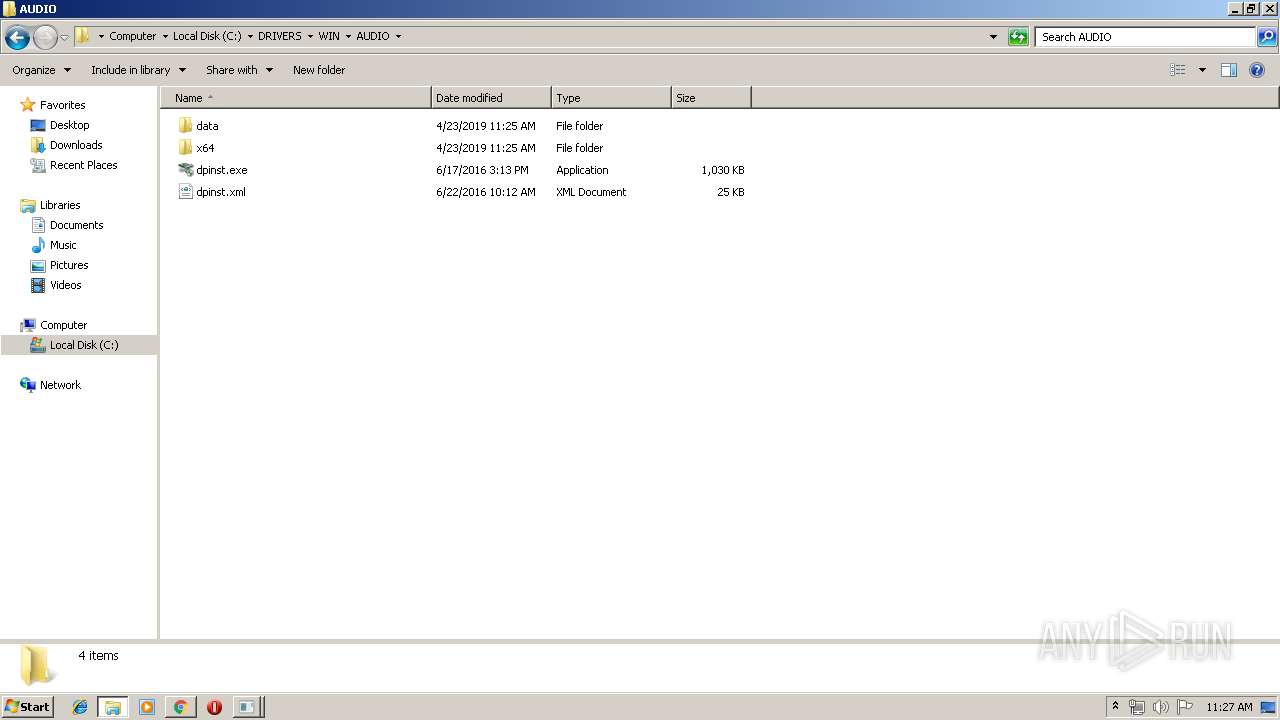
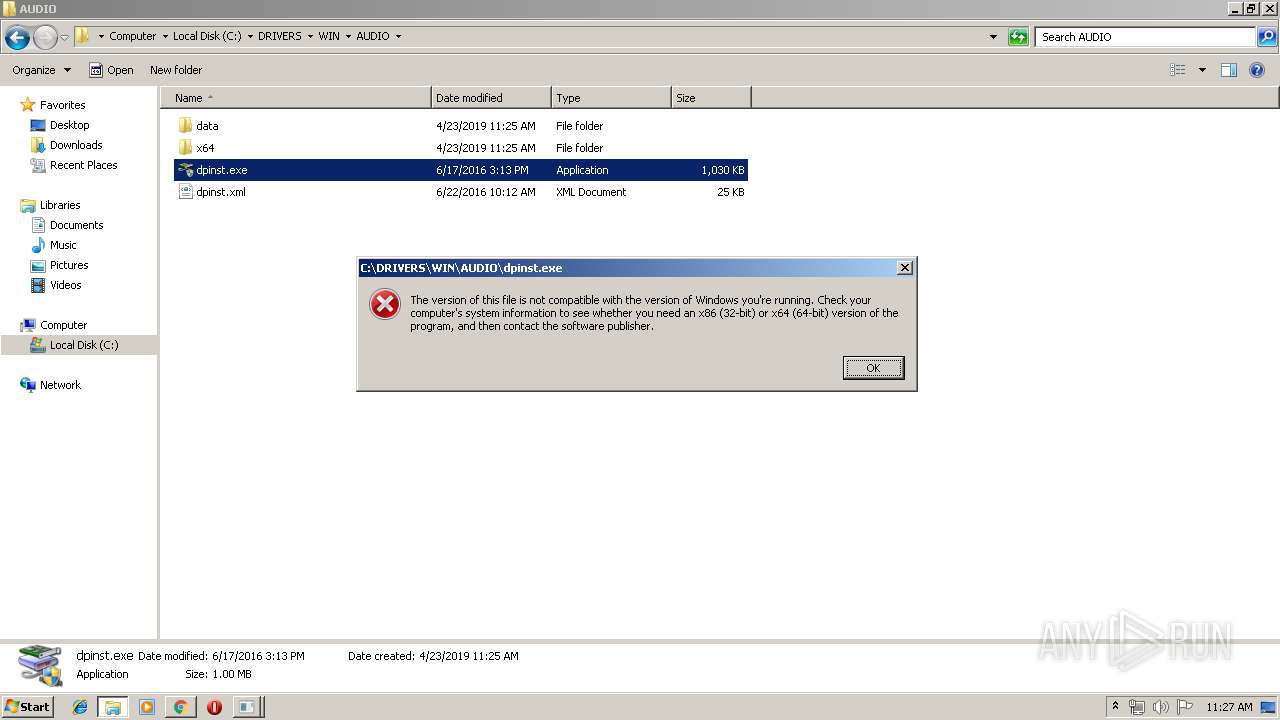
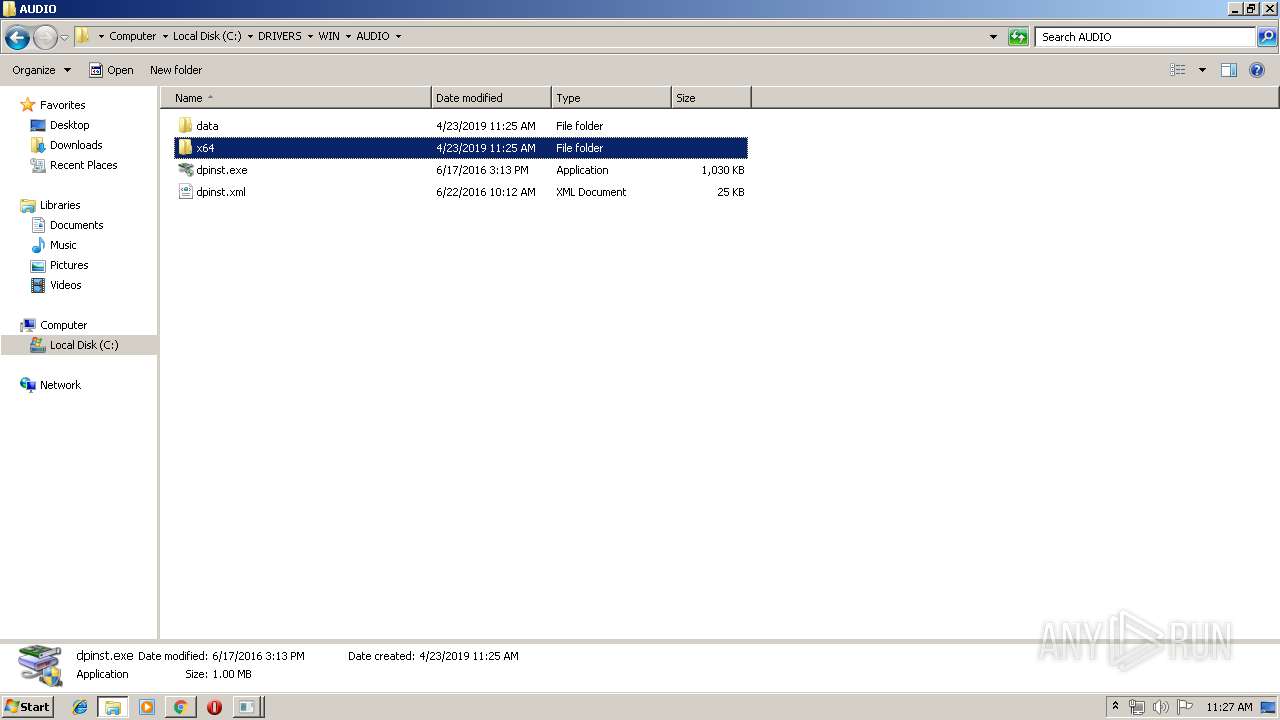
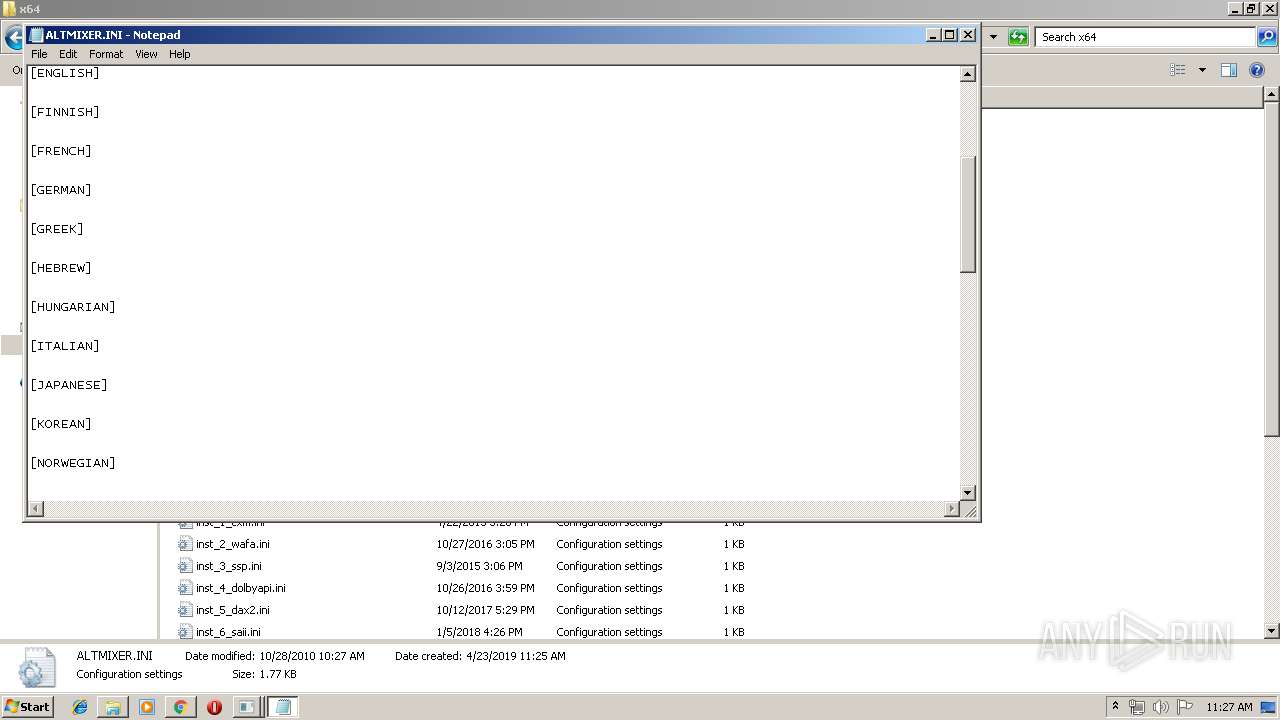
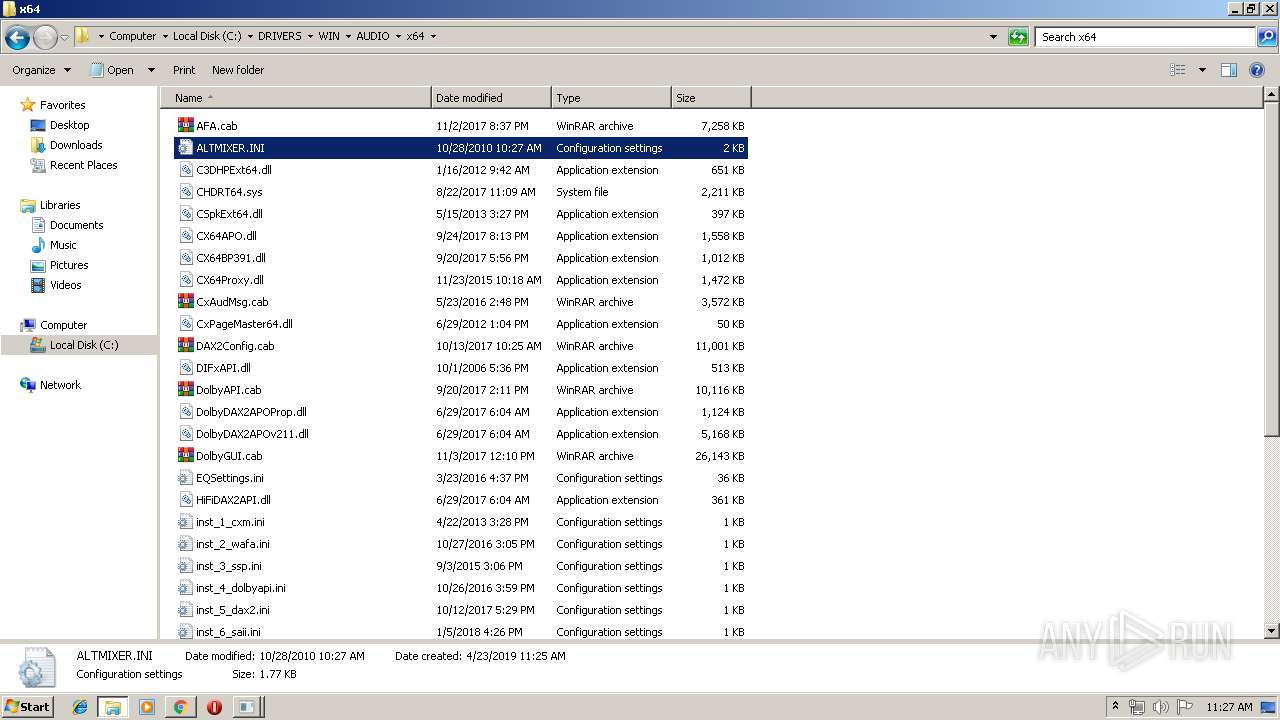
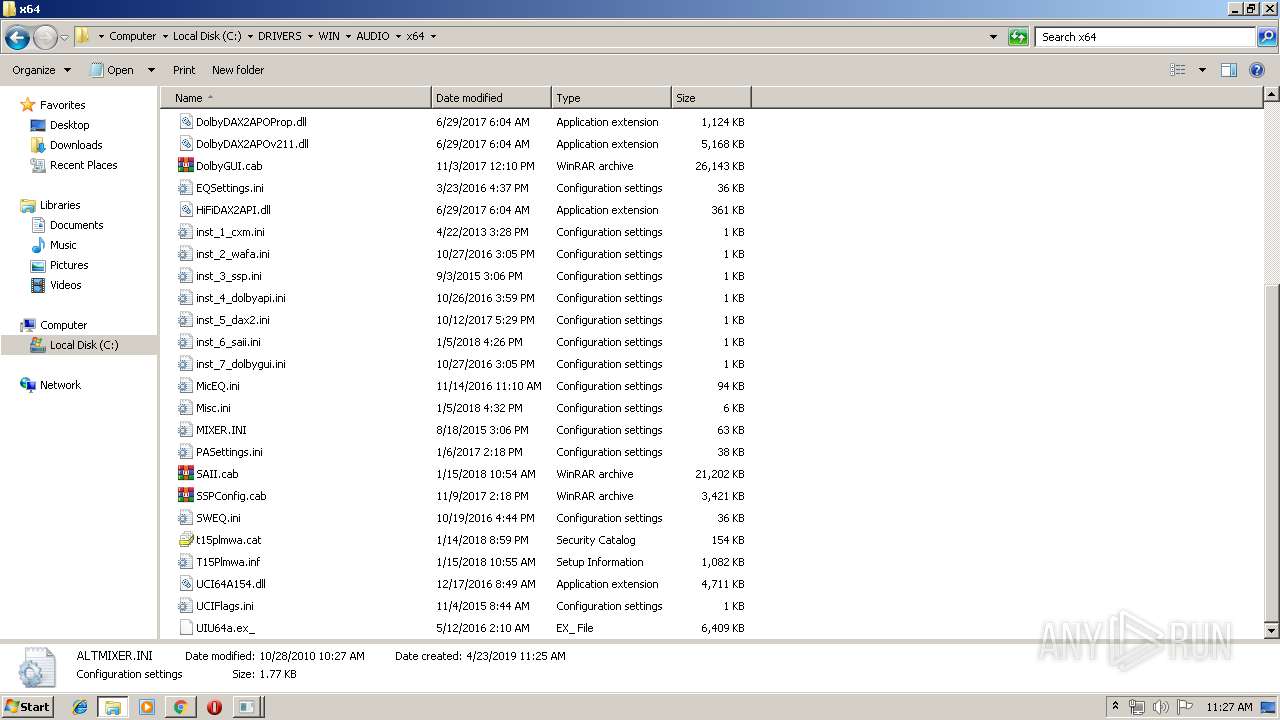
| 908 | "C:\Windows\system32\NOTEPAD.EXE" C:\DRIVERS\WIN\AUDIO\x64\ALTMIXER.INI | C:\Windows\system32\NOTEPAD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 980 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\mscorsvw.exe -StartupEvent 1b4 -InterruptEvent 0 -NGENProcess 18c -Pipe 1b0 -Comment "NGen Worker Process" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\mscorsvw.exe | ngen.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: .NET Runtime Optimization Service Exit code: 0 Version: 4.6.1055.0 built by: NETFXREL2 Modules
| |||||||||||||||
| 992 | "C:\Windows\system32\dllhost.exe" | C:\Windows\system32\dllhost.exe | — | n1ma113w.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1104 | "C:\Users\admin\Downloads\n1ma113w.exe" | C:\Users\admin\Downloads\n1ma113w.exe | explorer.exe | ||||||||||||
User: admin Company: Lenovo Group Limited Integrity Level: MEDIUM Description: For Lenovo Updates Catalog Exit code: 4294967295 Version: 8.66.76.67 (N1MA113W Modules
| |||||||||||||||
| 1184 | "C:\Windows\System32\net.exe" stop saservice | C:\Windows\System32\net.exe | — | Setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
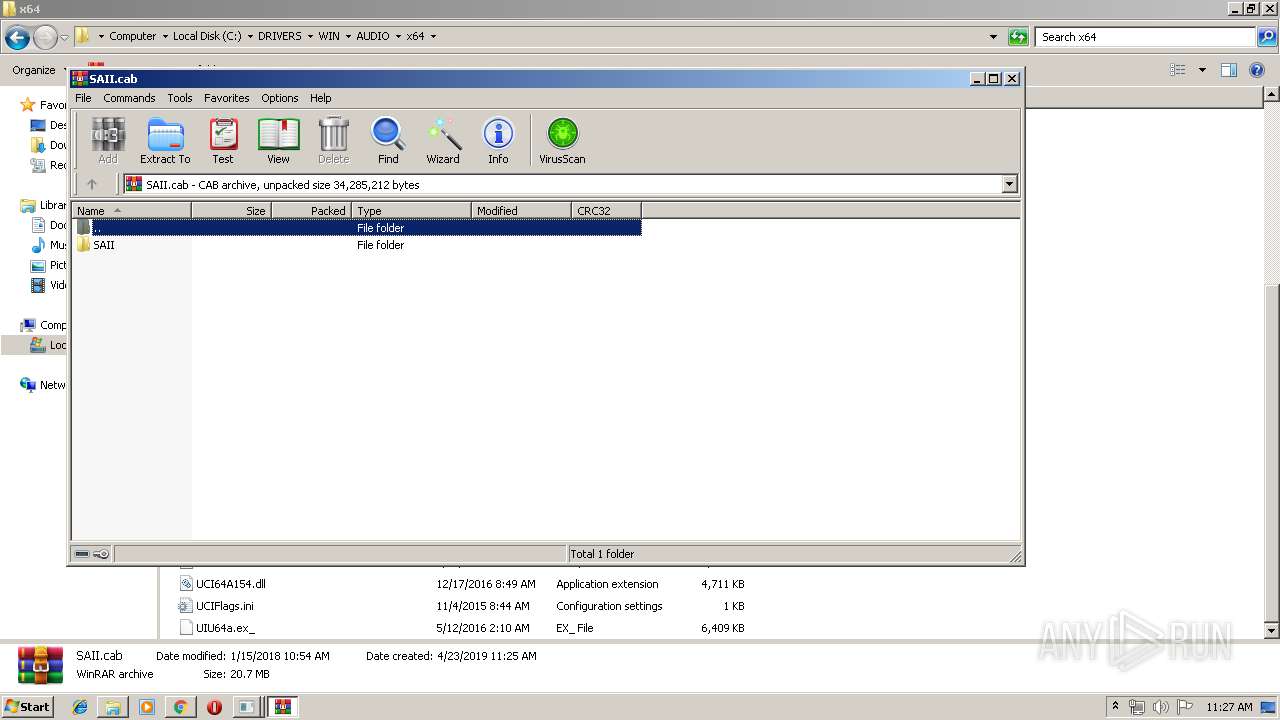
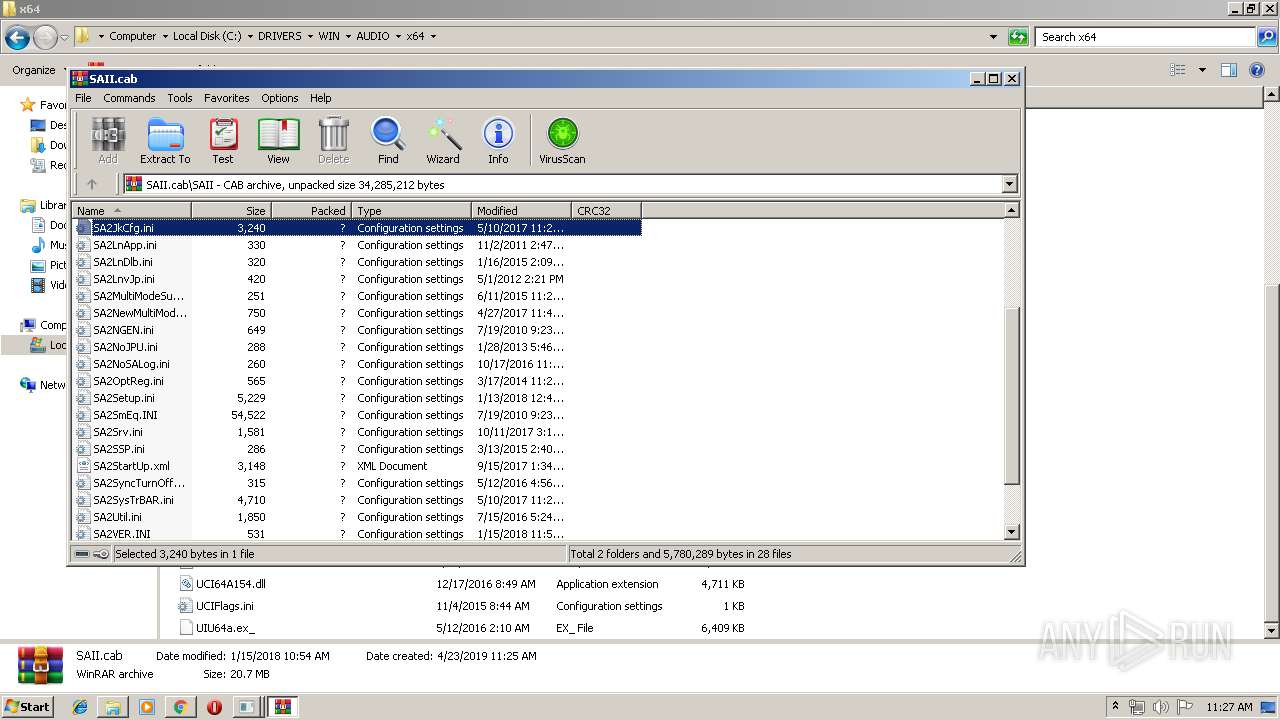
| 1300 | "C:\Program Files\CONEXANT\SAII\SACpl.exe" /c /delay:45 | C:\Program Files\CONEXANT\SAII\SACpl.exe | — | taskeng.exe | |||||||||||
User: admin Company: Conexant Systems, Inc. Integrity Level: MEDIUM Description: SmartAudio CPL (32bit) Exit code: 0 Version: 6.0.48.0 Modules
| |||||||||||||||
| 1364 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,12107015881543131917,17542509425726505650,131072 --enable-features=PasswordImport --service-pipe-token=17825549199629418944 --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17825549199629418944 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1984 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
4 138
Read events
2 127
Write events
1 998
Delete events
13
Modification events
| (PID) Process: | (3952) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2512-13200488653727750 |
Value: 259 | |||
| (PID) Process: | (2512) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2512) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2512) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2512) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2512) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2512) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2512) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2512) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
| (PID) Process: | (2512) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2512-13200488653727750 |
Value: 259 | |||
Executable files
108
Suspicious files
83
Text files
571
Unknown types
18
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2512 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2512 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2512 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2512 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 2512 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 2512 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\fd6cb9fa-4e68-4646-b943-24507a36e041.tmp | — | |
MD5:— | SHA256:— | |||
| 2512 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2512 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2512 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2512 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
25
DNS requests
16
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2512 | chrome.exe | GET | 200 | 173.194.139.6:80 | http://r1---sn-aigzrn7k.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=185.230.125.140&mm=28&mn=sn-aigzrn7k&ms=nvh&mt=1556015002&mv=m&pl=24&shardbypass=yes | US | crx | 842 Kb | whitelisted |
2512 | chrome.exe | GET | 302 | 172.217.18.14:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 506 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2512 | chrome.exe | 172.217.22.67:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
— | — | 172.217.23.174:80 | — | Google Inc. | US | whitelisted |
2512 | chrome.exe | 172.217.21.195:443 | www.google.com.ua | Google Inc. | US | whitelisted |
2512 | chrome.exe | 216.58.210.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
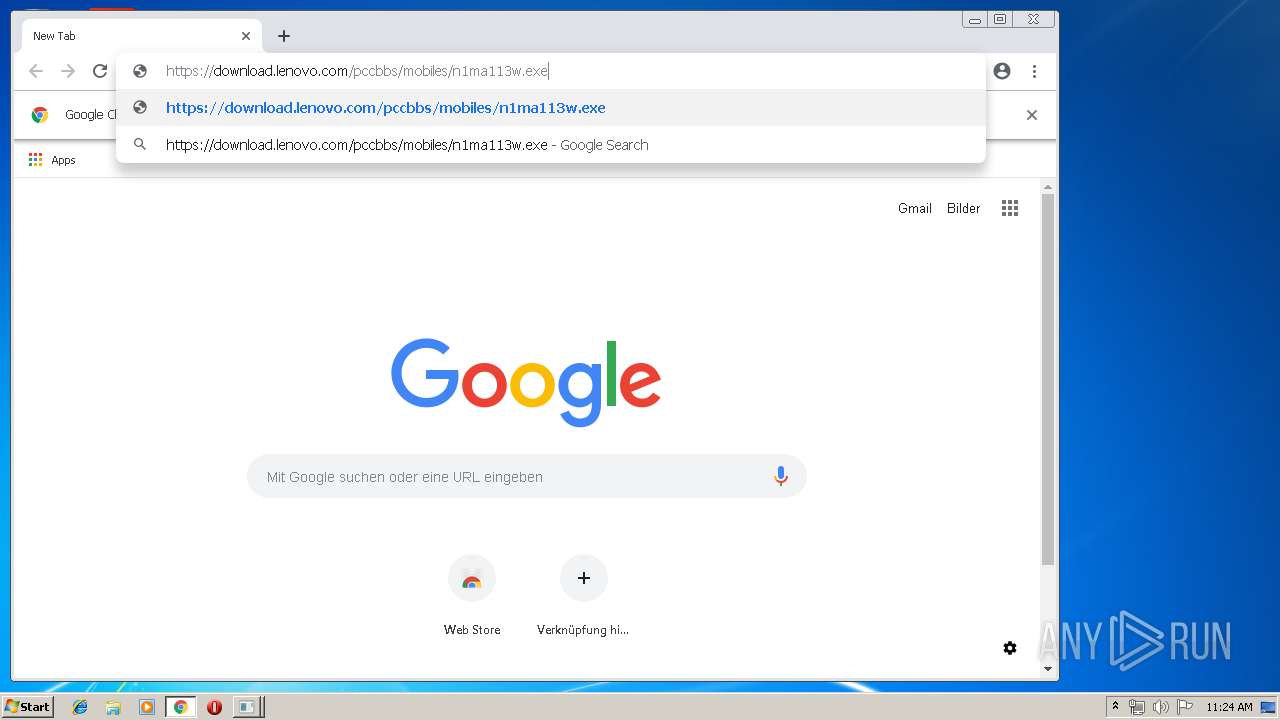
2512 | chrome.exe | 2.18.232.126:443 | download.lenovo.com | Akamai International B.V. | — | whitelisted |
2512 | chrome.exe | 172.217.16.142:443 | clients1.google.com | Google Inc. | US | whitelisted |
2512 | chrome.exe | 172.217.16.195:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2512 | chrome.exe | 172.217.18.99:443 | www.google.ch | Google Inc. | US | whitelisted |
2512 | chrome.exe | 216.58.207.78:443 | clients2.google.com | Google Inc. | US | whitelisted |
2512 | chrome.exe | 216.58.210.4:443 | www.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
www.google.com.ua |
| whitelisted |
accounts.google.com |
| shared |
clients1.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
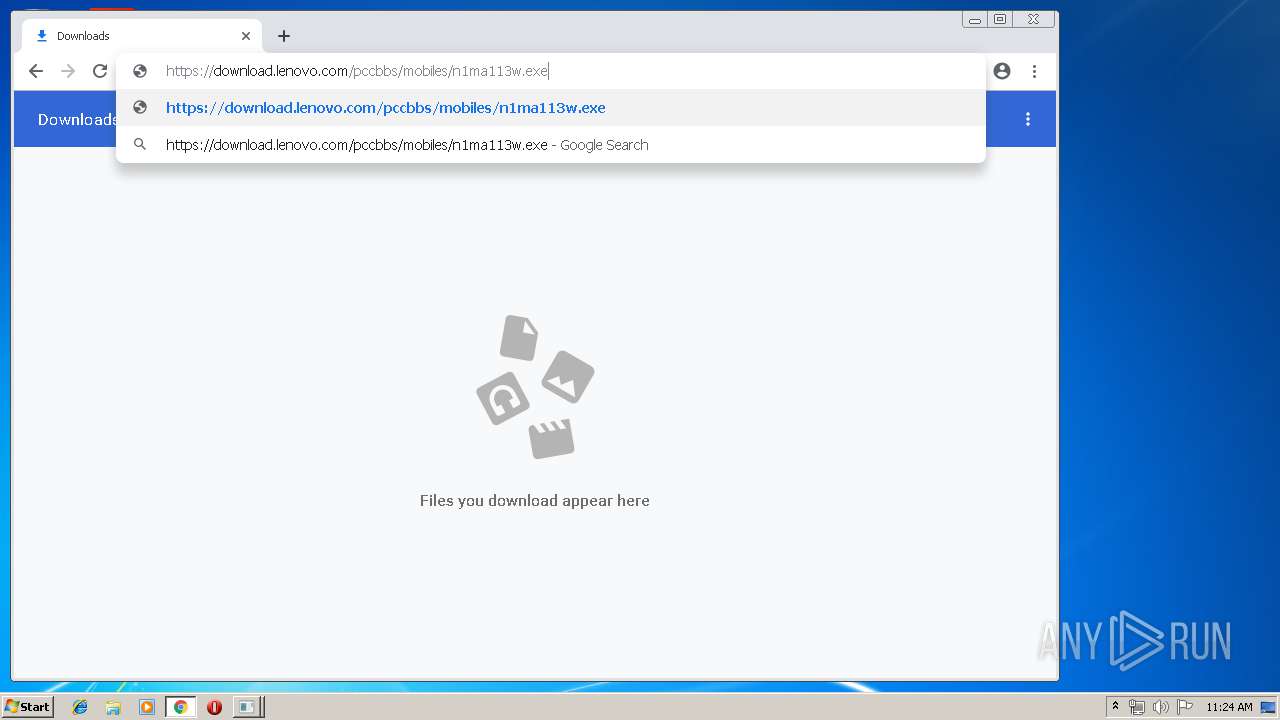
download.lenovo.com |
| suspicious |
www.google.com |
| malicious |
www.google.ch |
| whitelisted |
Threats
Process | Message |
|---|---|
SASrv.exe | SASrv.exe(tid 5a8) 0:[ J_CMDLINE] - Option - Install Service.
|
SASrv.exe | SASrv.exe(tid 5a8) 0:[ J_CMDLINE] - Option - Install Service.
|
SASrv.exe | SASrv.exe(tid 5a8) 31:[ J_STATE] - Conexant SmartAudio service installed.
|
SAsrv.exe | SAsrv.exe(tid 23c) 0:[ J_STATE] - _tWinMain
|
SAsrv.exe | SAsrv.exe(tid 804) 0:[ J_STATE] - service_main started
|
SAsrv.exe | SAsrv.exe(tid ea8) 15:[ J_WINDOWS] - Windows Version is WINDOWS VISTA or later
|