| File name: | Caff54e1.exe |
| Full analysis: | https://app.any.run/tasks/8a09a89a-6103-4885-8f03-6237a7d7fead |
| Verdict: | Malicious activity |
| Analysis date: | February 21, 2020, 21:50:33 |
| OS: | Windows 10 Professional (build: 16299, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows |
| MD5: | 64AABB8C0CA6245F28DC0D7936208706 |
| SHA1: | 5C3353BE0C746F65FF1BB04BD442A956FB3A2C00 |
| SHA256: | 03C962EBB541A709B92957E301EA03F1790B6A57D4D0605F618FB0BE392C8066 |
| SSDEEP: | 6144:vDwYweNHD22Pw2VcYDyw0pkBn88oXhp97:v9LH5YQcYDNakBmhp97 |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executed via COM
- DataExchangeHost.exe (PID: 5992)
- RuntimeBroker.exe (PID: 1668)
- RuntimeBroker.exe (PID: 2708)
Reads the machine GUID from the registry
- Caff54e1.exe (PID: 3700)
INFO
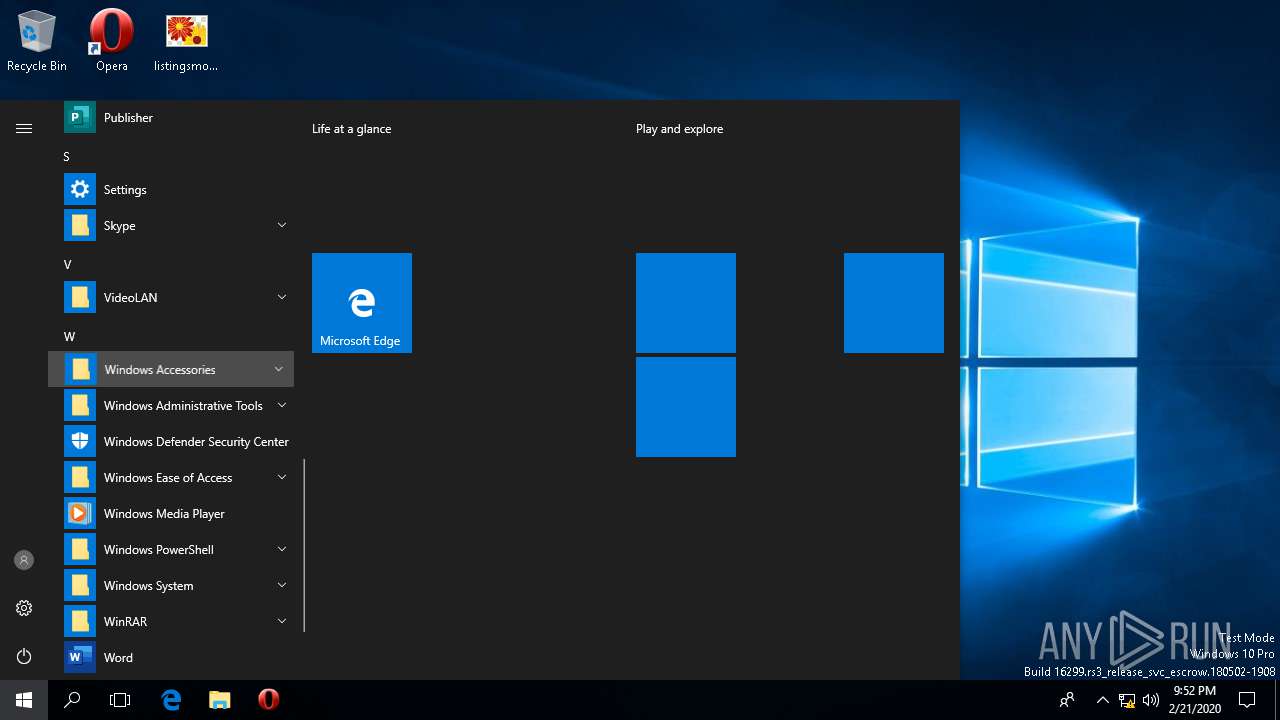
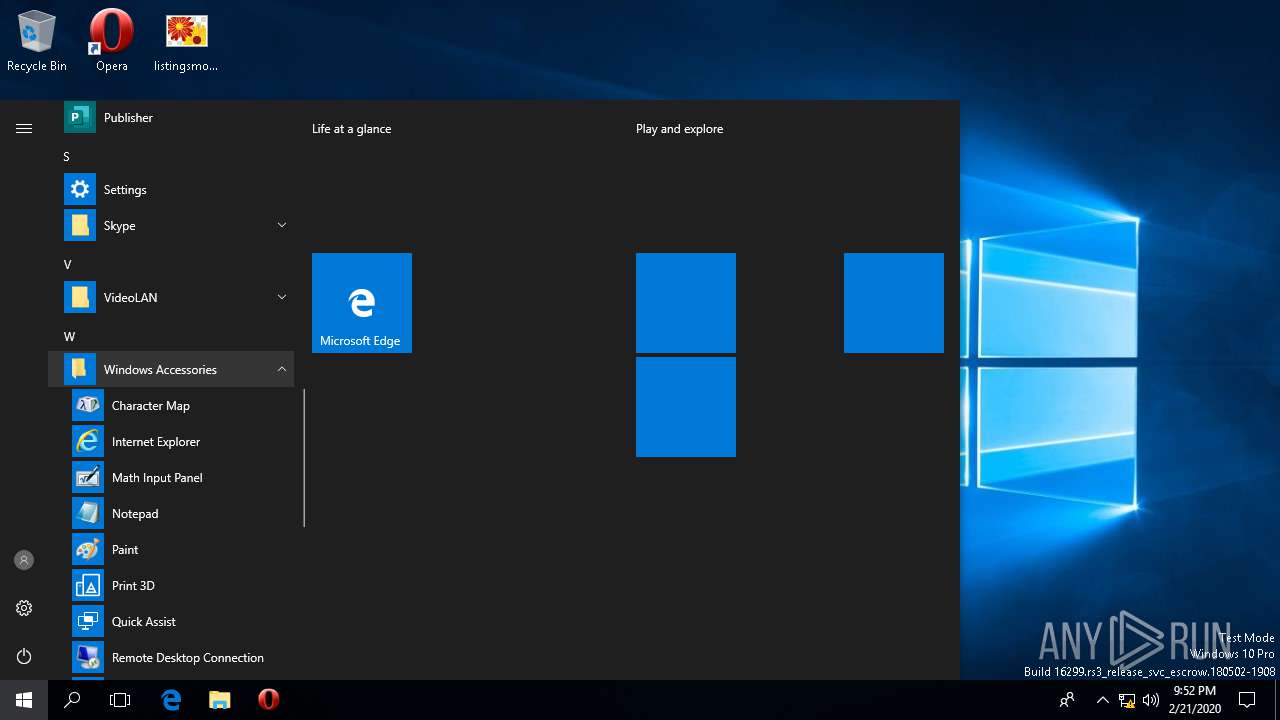
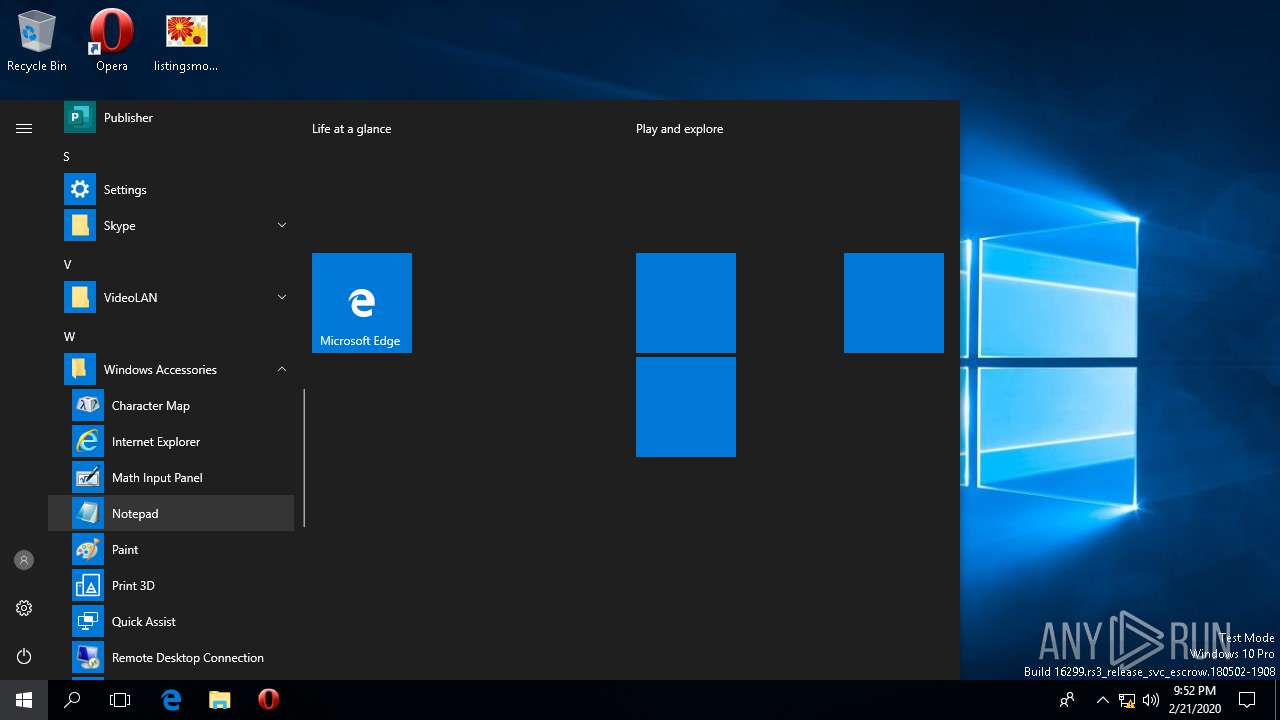
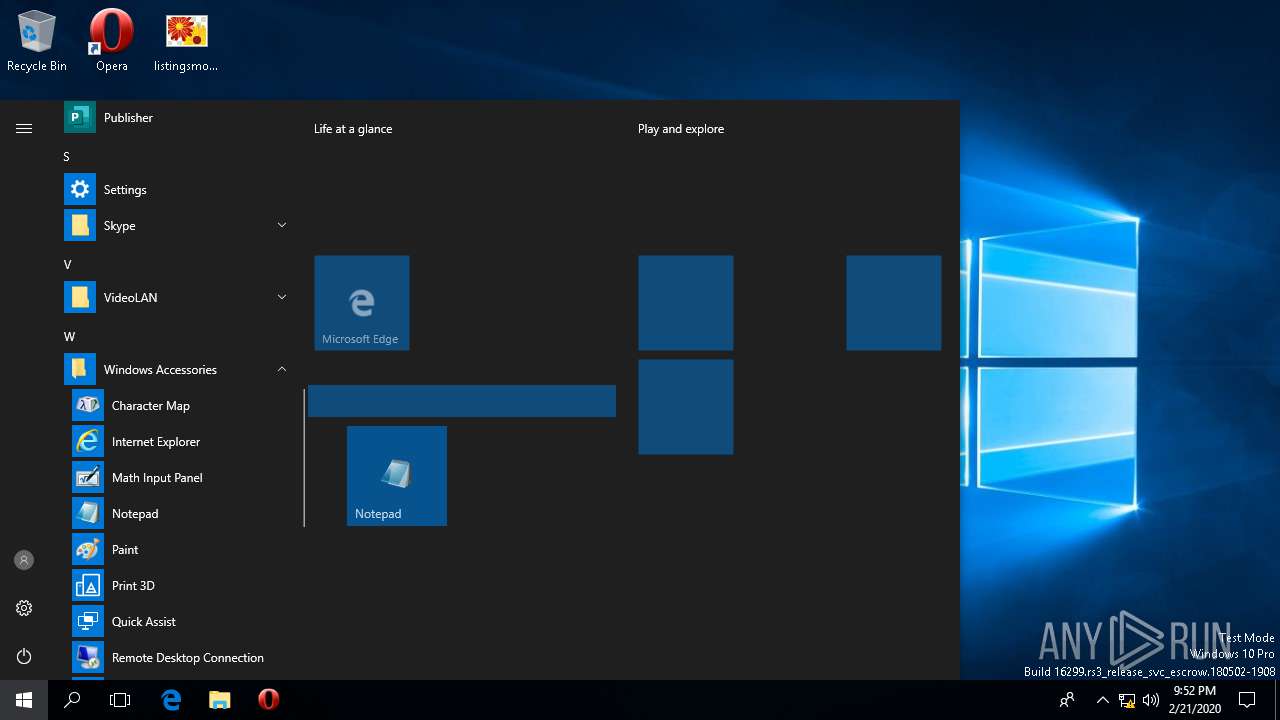
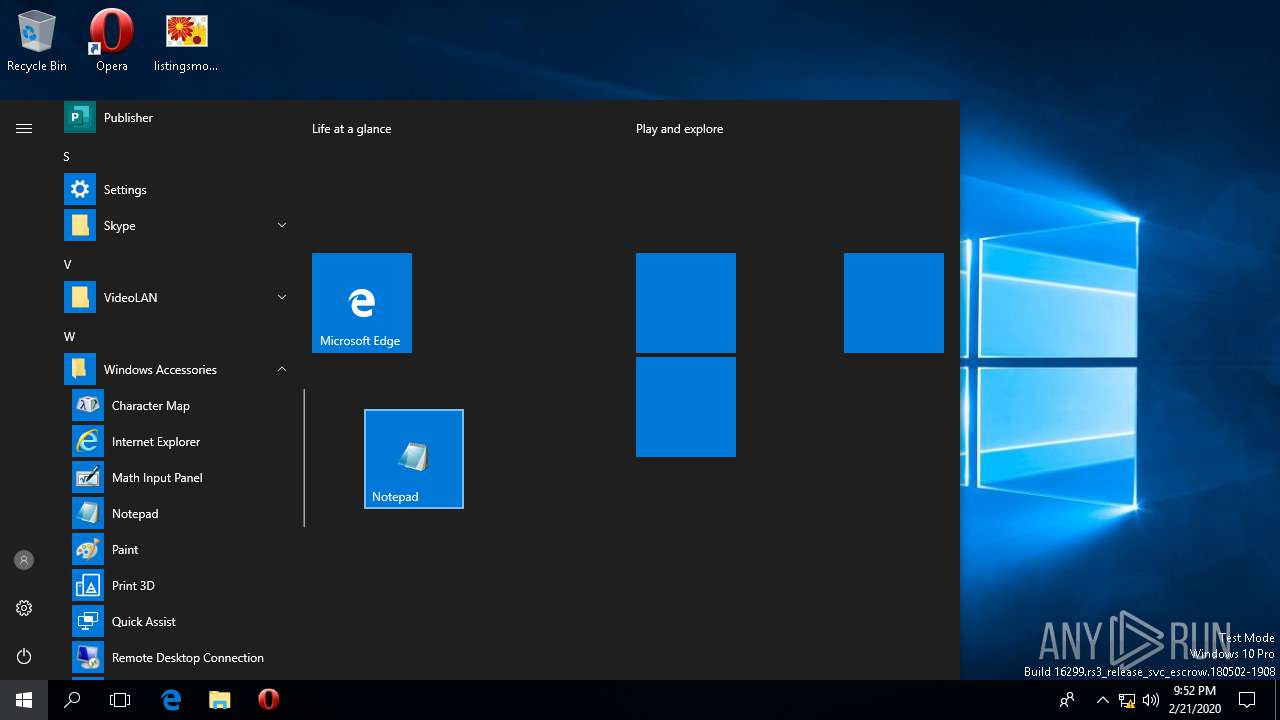
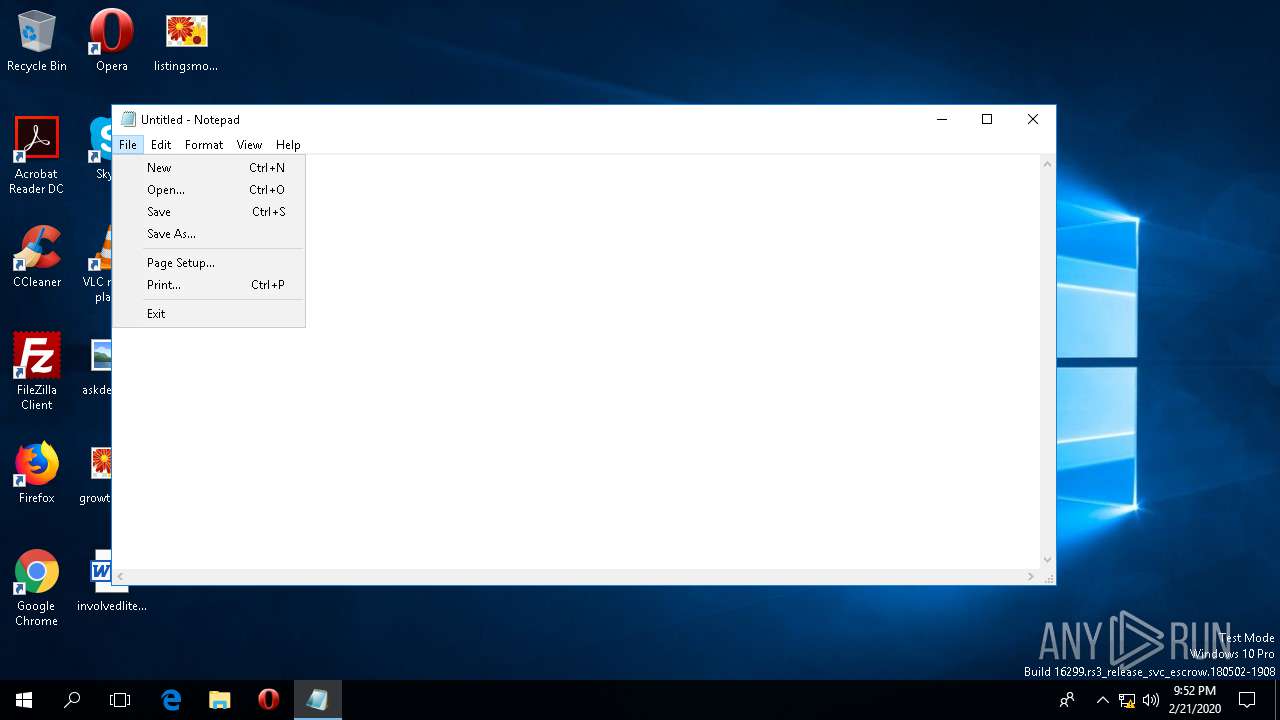
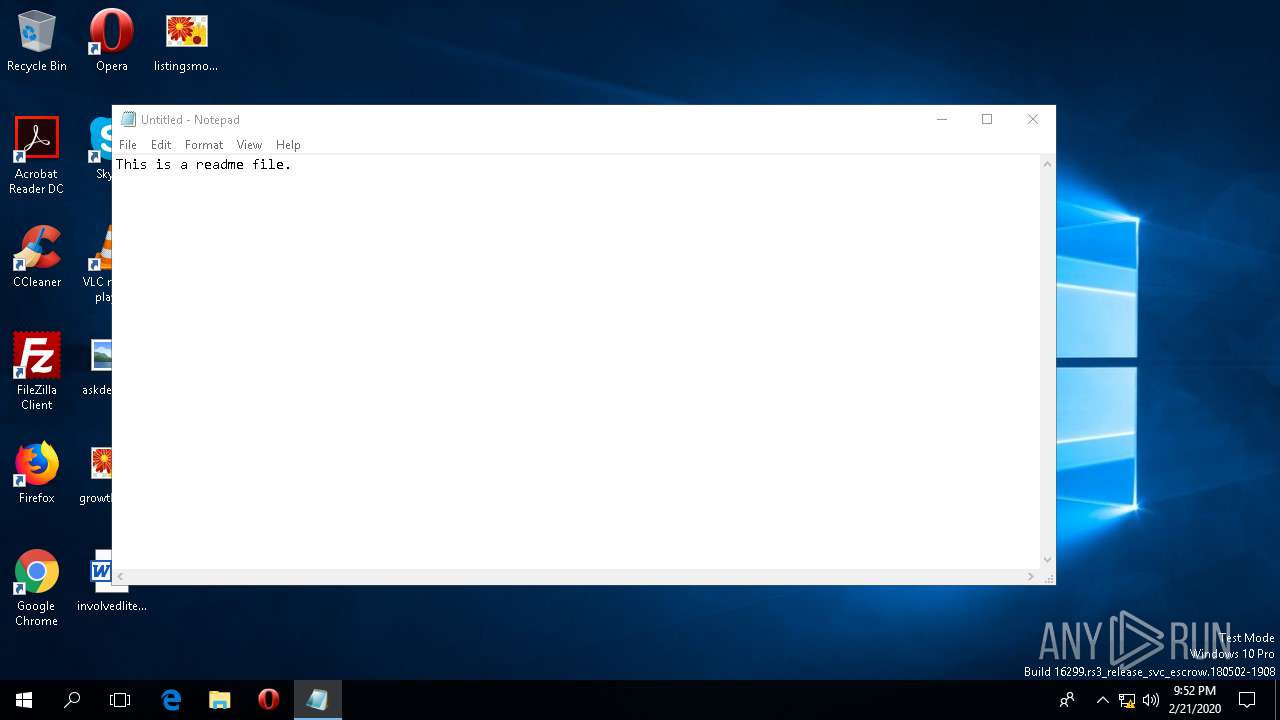
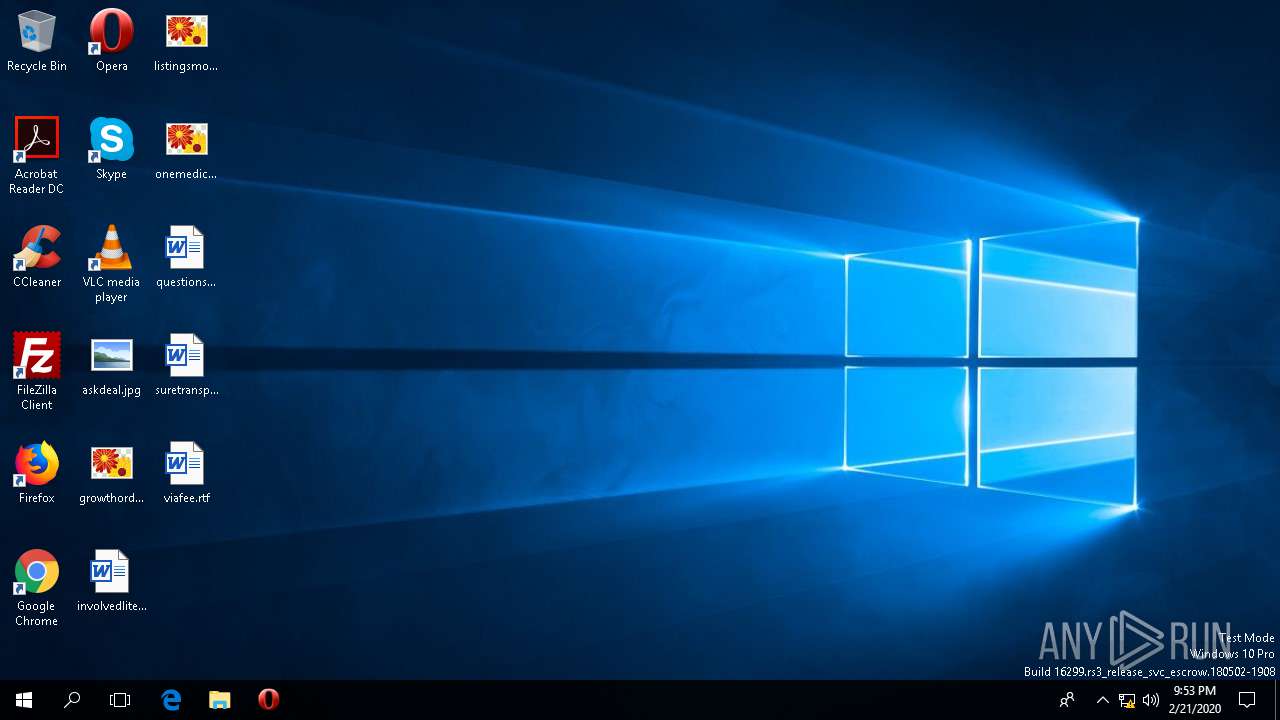
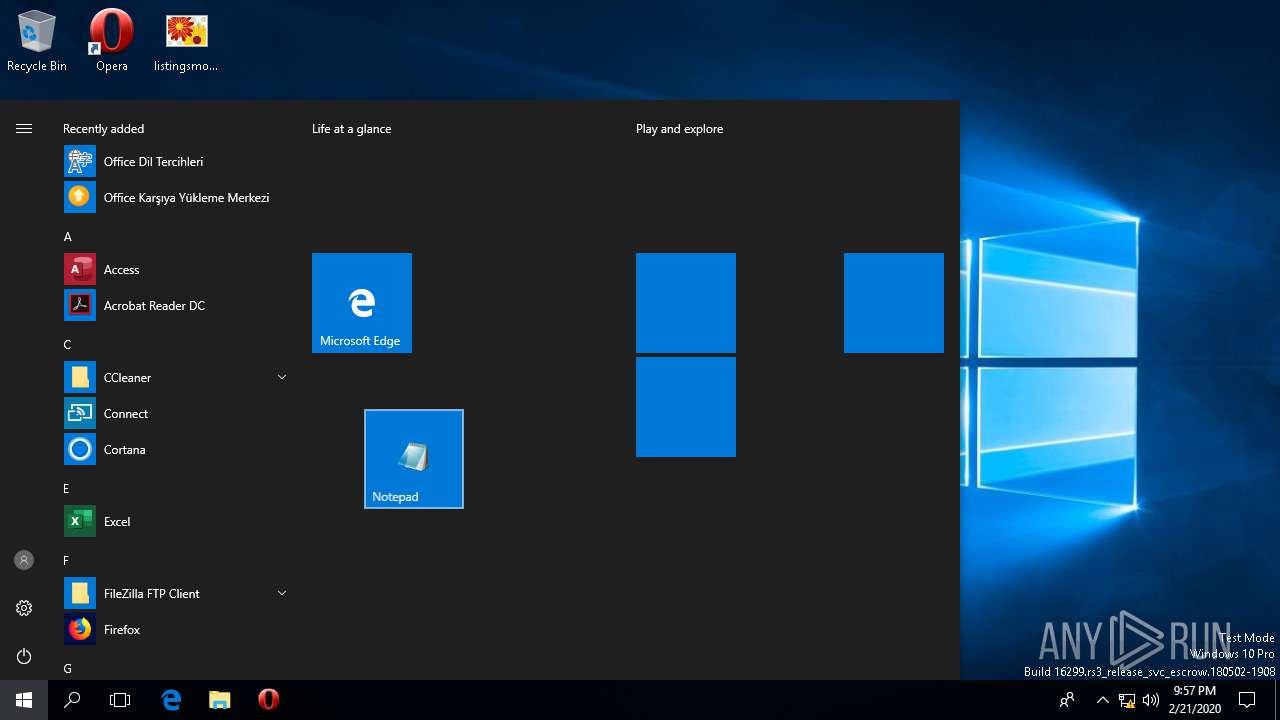
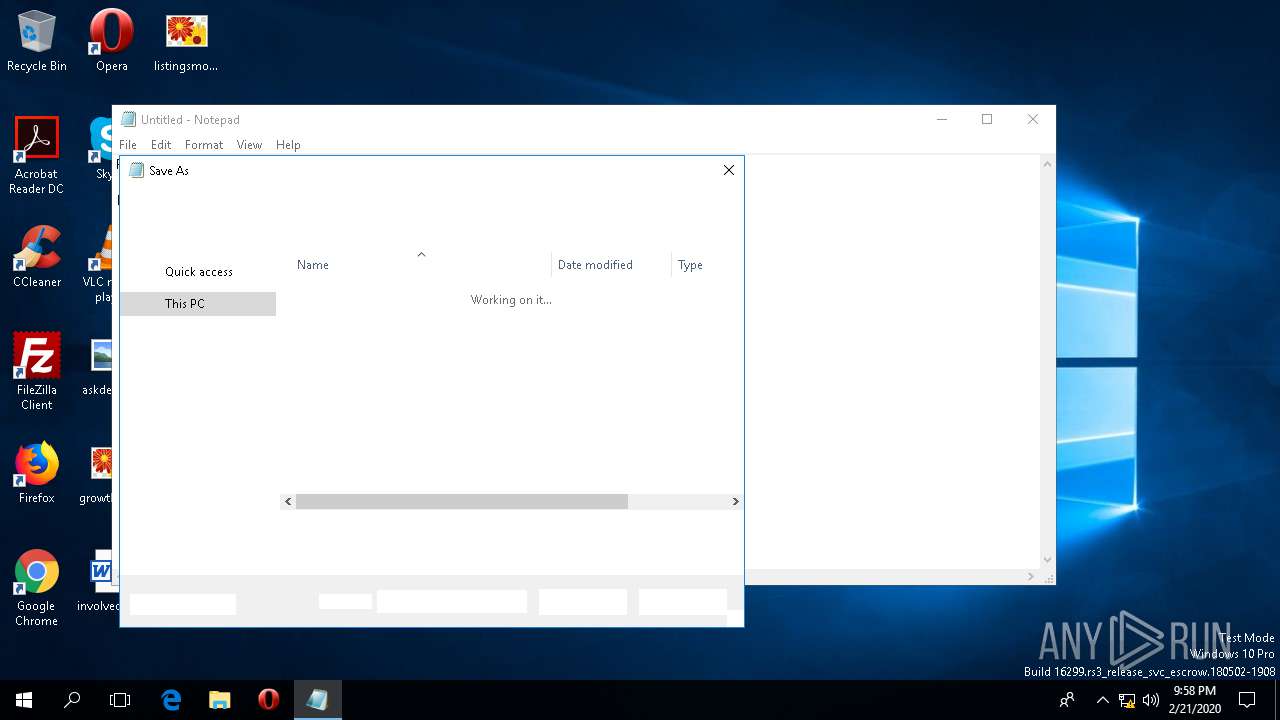
Manual execution by user
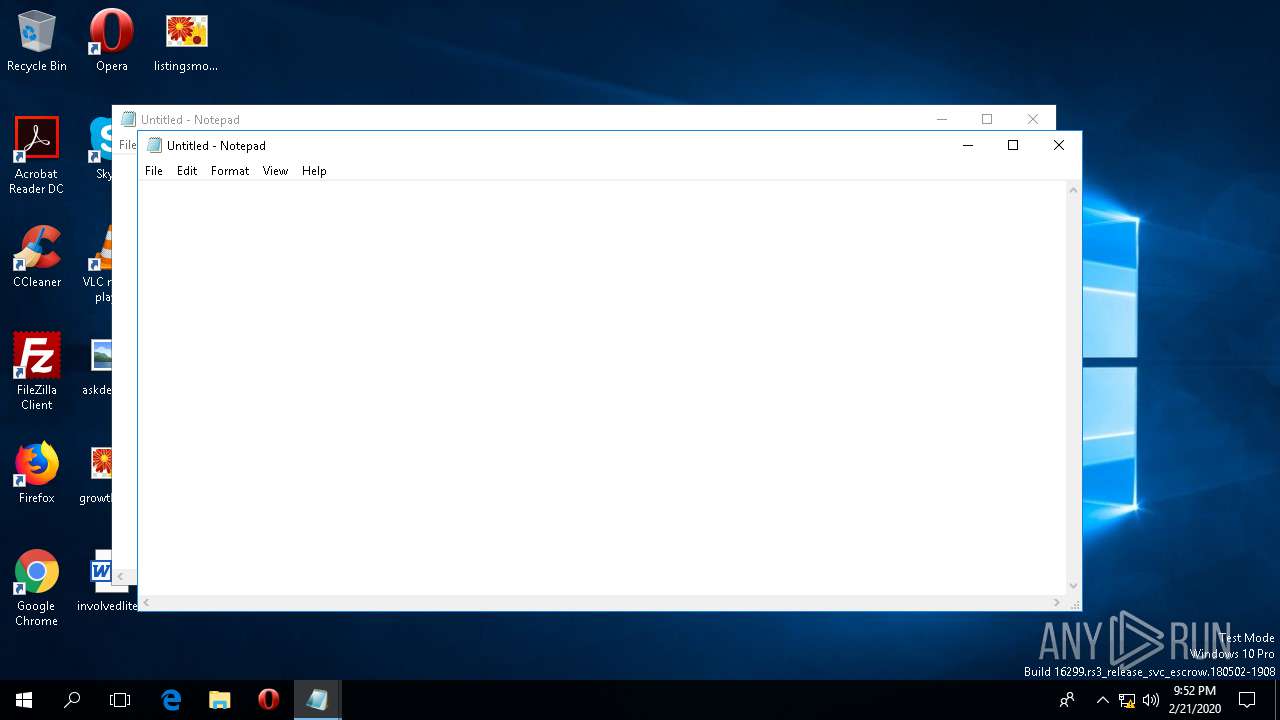
- notepad.exe (PID: 5532)
- notepad.exe (PID: 1164)
- notepad.exe (PID: 5396)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .dll | | | Win32 Dynamic Link Library (generic) (43.5) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (29.8) |
| .exe | | | Generic Win/DOS Executable (13.2) |
| .exe | | | DOS Executable Generic (13.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:02:20 02:41:23+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 12 |
| CodeSize: | 53248 |
| InitializedDataSize: | 151552 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x3740 |
| OSVersion: | 5 |
| ImageVersion: | 5 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 14.12.0.18020 |
| ProductVersionNumber: | 14.12.0.18020 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Dynamic link library |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Citrix Systems, Inc. |
| FileDescription: | Citrix Receiver VDIME Resource DLL (Win32) |
| FileVersion: | 14.12.0.18020 |
| InternalName: | VDIME |
| LegalCopyright: | Copyright (c) 1990-2018 Citrix Systems, Inc. |
| OriginalFileName: | VDIME.DLL |
| ProductName: | Citrix Receiver |
| ProductVersion: | 14.12.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 20-Feb-2020 01:41:23 |
| Detected languages: |
|
| CompanyName: | Citrix Systems, Inc. |
| FileDescription: | Citrix Receiver VDIME Resource DLL (Win32) |
| FileVersion: | 14.12.0.18020 |
| InternalName: | VDIME |
| LegalCopyright: | Copyright (c) 1990-2018 Citrix Systems, Inc. |
| OriginalFilename: | VDIME.DLL |
| ProductName: | Citrix Receiver |
| ProductVersion: | 14.12.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000108 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 7 |
| Time date stamp: | 20-Feb-2020 01:41:23 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00002830 | 0x00003000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.66108 |
.idata | 0x0001A000 | 0x00000448 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.88245 |
.data | 0x0000E000 | 0x0000B918 | 0x0000C000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.74853 |
.reloc | 0x00032000 | 0x000002C4 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 1.61073 |
.rsrc | 0x00031000 | 0x00000608 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.94768 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.53114 | 832 | UNKNOWN | German - Germany | RT_VERSION |
2 | 4.91161 | 381 | UNKNOWN | English - United States | RT_MANIFEST |
7 | 3.20794 | 88 | UNKNOWN | Chinese - PRC | RT_STRING |
Imports
ADVAPI32.dll |
GDI32.dll |
KERNEL32.dll |
OLEAUT32.dll |
SHLWAPI.dll |
USER32.dll |
Total processes
92
Monitored processes
8
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
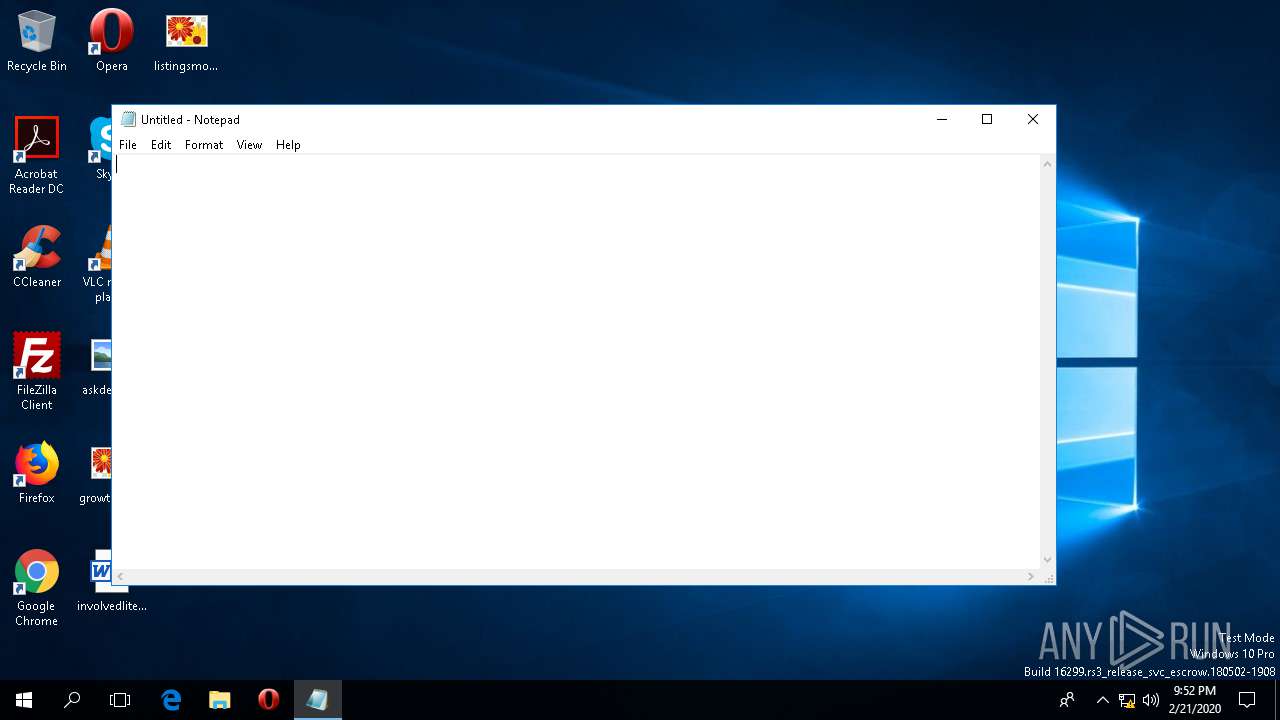
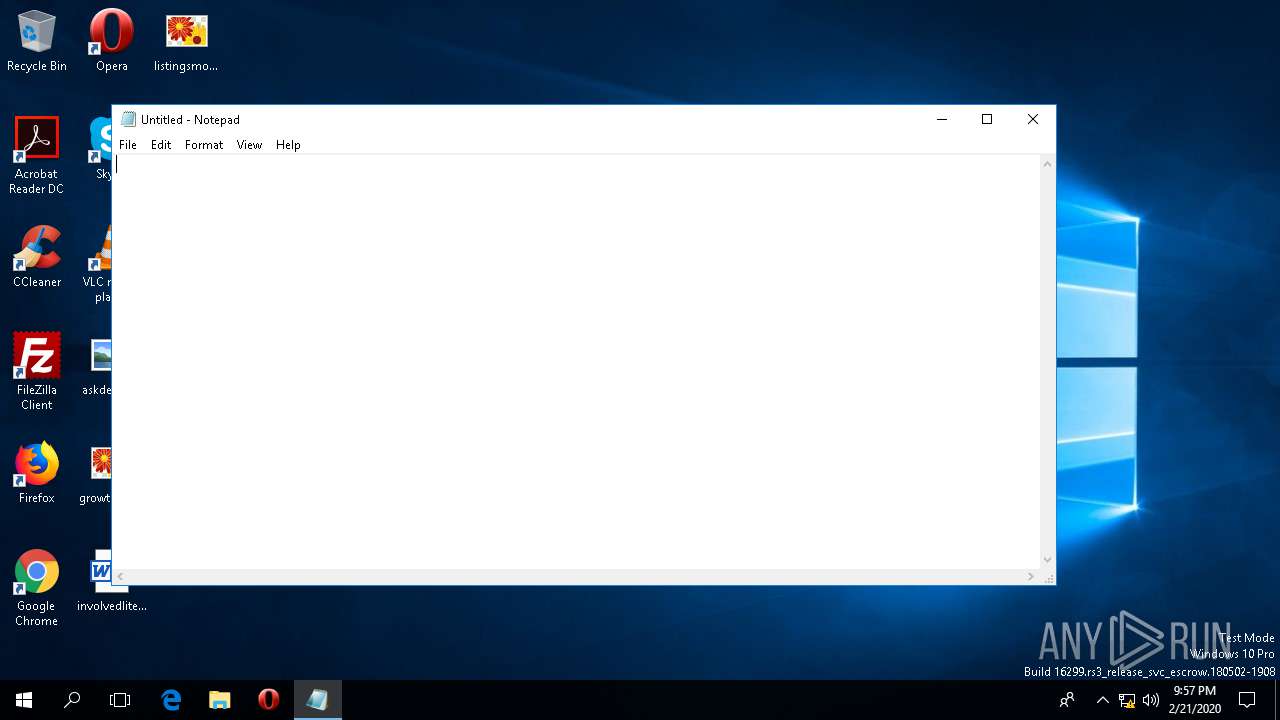
| 1164 | "C:\WINDOWS\system32\notepad.exe" | C:\WINDOWS\system32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1668 | C:\Windows\System32\RuntimeBroker.exe -Embedding | C:\Windows\System32\RuntimeBroker.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Runtime Broker Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2708 | C:\Windows\System32\RuntimeBroker.exe -Embedding | C:\Windows\System32\RuntimeBroker.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Runtime Broker Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3700 | "C:\Users\admin\AppData\Local\Temp\Caff54e1.exe" | C:\Users\admin\AppData\Local\Temp\Caff54e1.exe | explorer.exe | ||||||||||||
User: admin Company: Citrix Systems, Inc. Integrity Level: MEDIUM Description: Citrix Receiver VDIME Resource DLL (Win32) Exit code: 0 Version: 14.12.0.18020 Modules
| |||||||||||||||
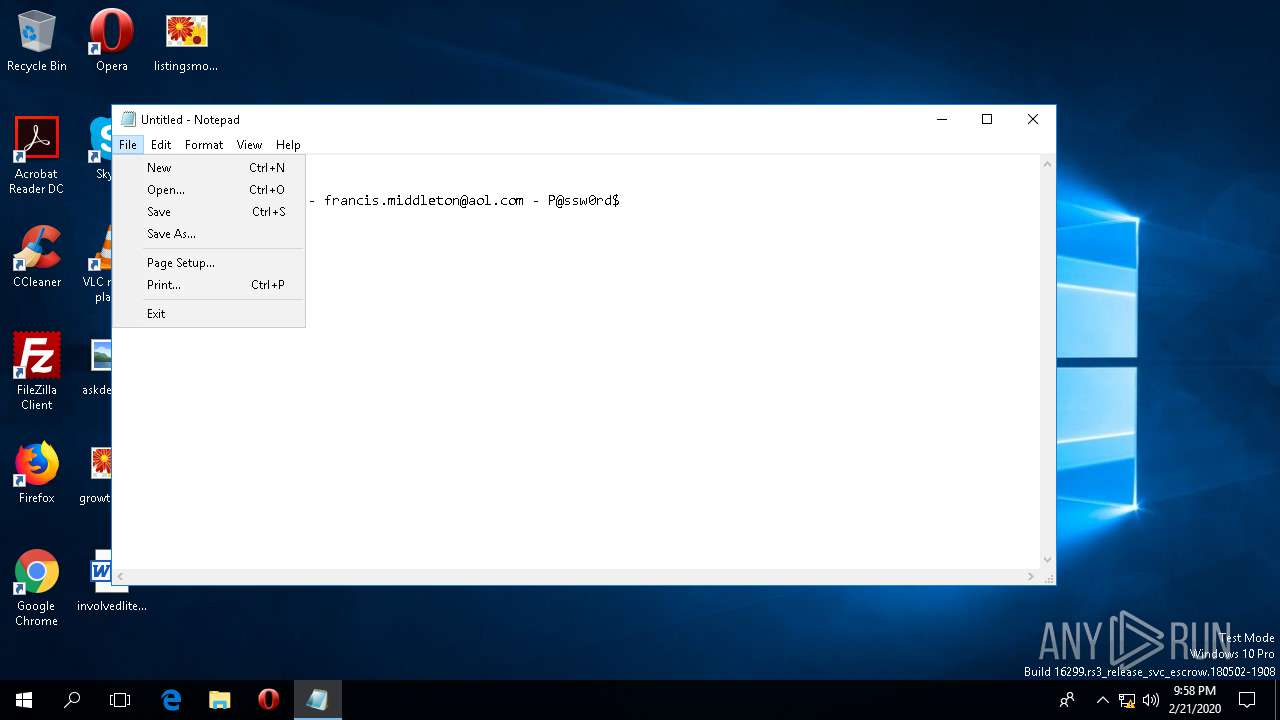
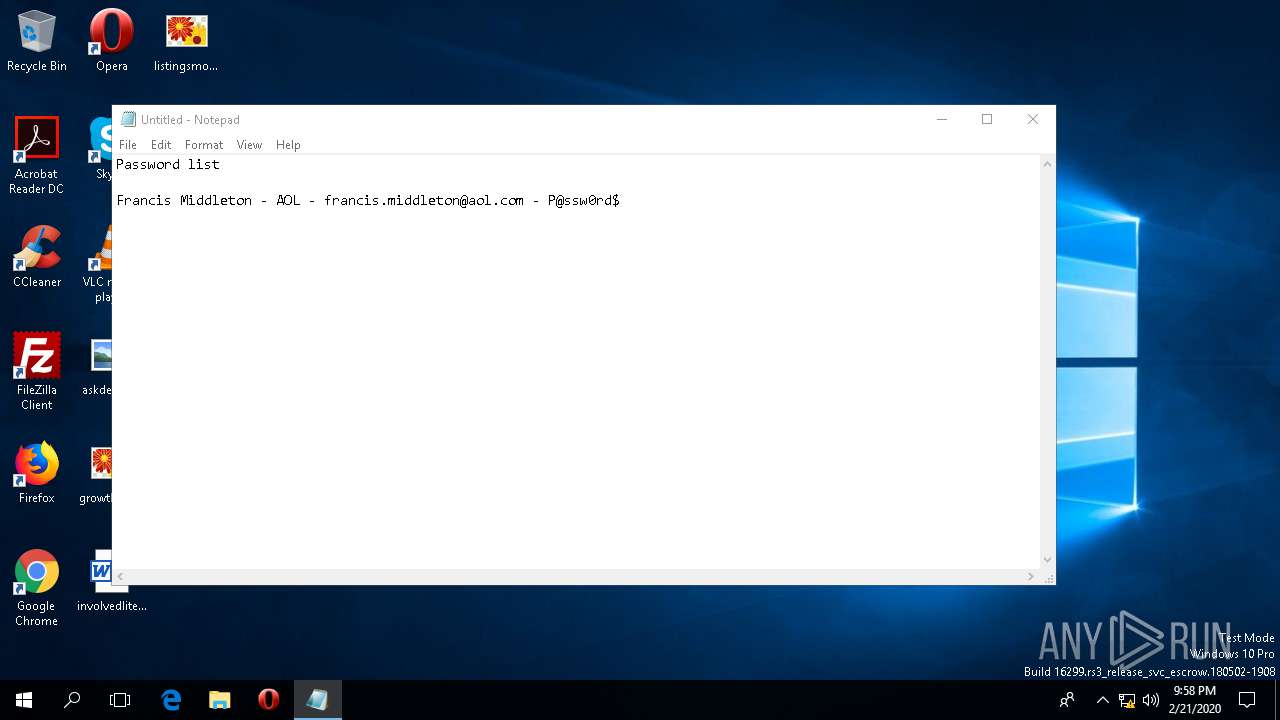
| 5396 | "C:\WINDOWS\system32\notepad.exe" | C:\WINDOWS\system32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5456 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\WINDOWS\system32\conhost.exe | Caff54e1.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5532 | "C:\WINDOWS\system32\notepad.exe" | C:\WINDOWS\system32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5992 | C:\Windows\System32\DataExchangeHost.exe -Embedding | C:\Windows\System32\DataExchangeHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Data Exchange Host Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
326 945
Read events
326 811
Write events
128
Delete events
6
Modification events
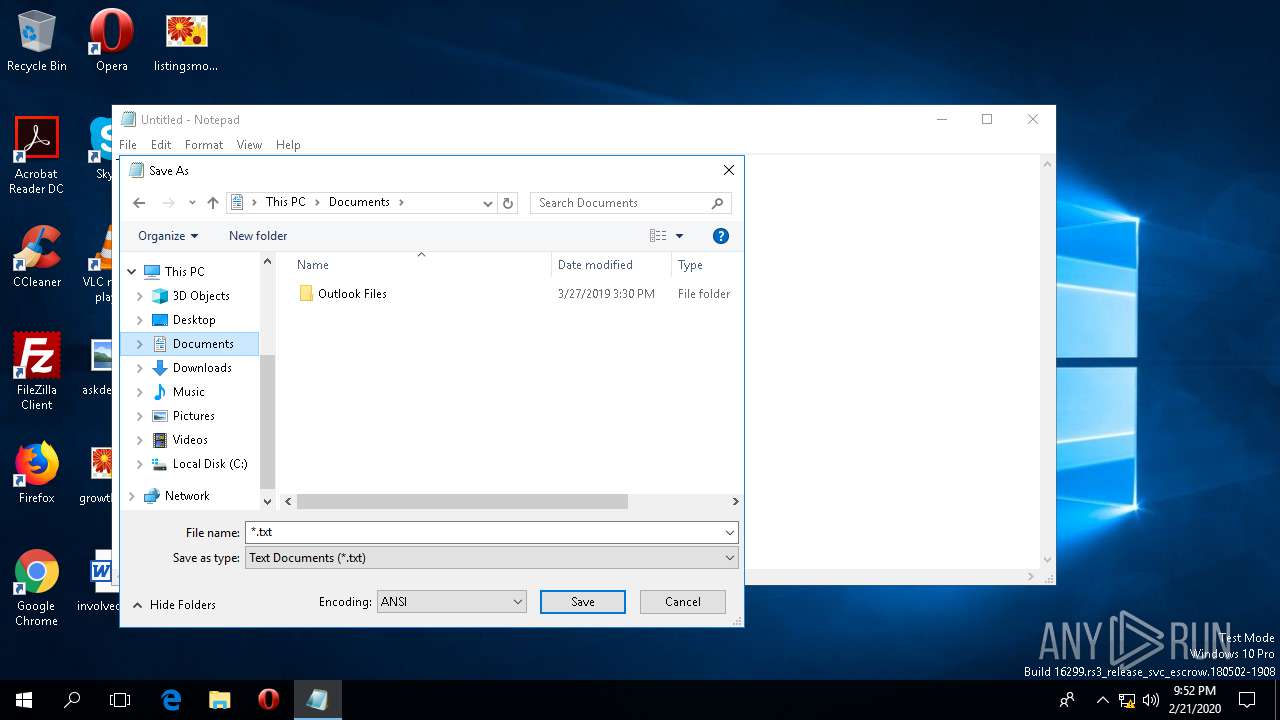
| (PID) Process: | (1164) notepad.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Notepad |
| Operation: | write | Name: | iWindowPosX |
Value: 130 | |||
| (PID) Process: | (1164) notepad.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Notepad |
| Operation: | write | Name: | iWindowPosY |
Value: 130 | |||
| (PID) Process: | (1164) notepad.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Notepad |
| Operation: | write | Name: | iWindowPosDX |
Value: 960 | |||
| (PID) Process: | (1164) notepad.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Notepad |
| Operation: | write | Name: | iWindowPosDY |
Value: 489 | |||
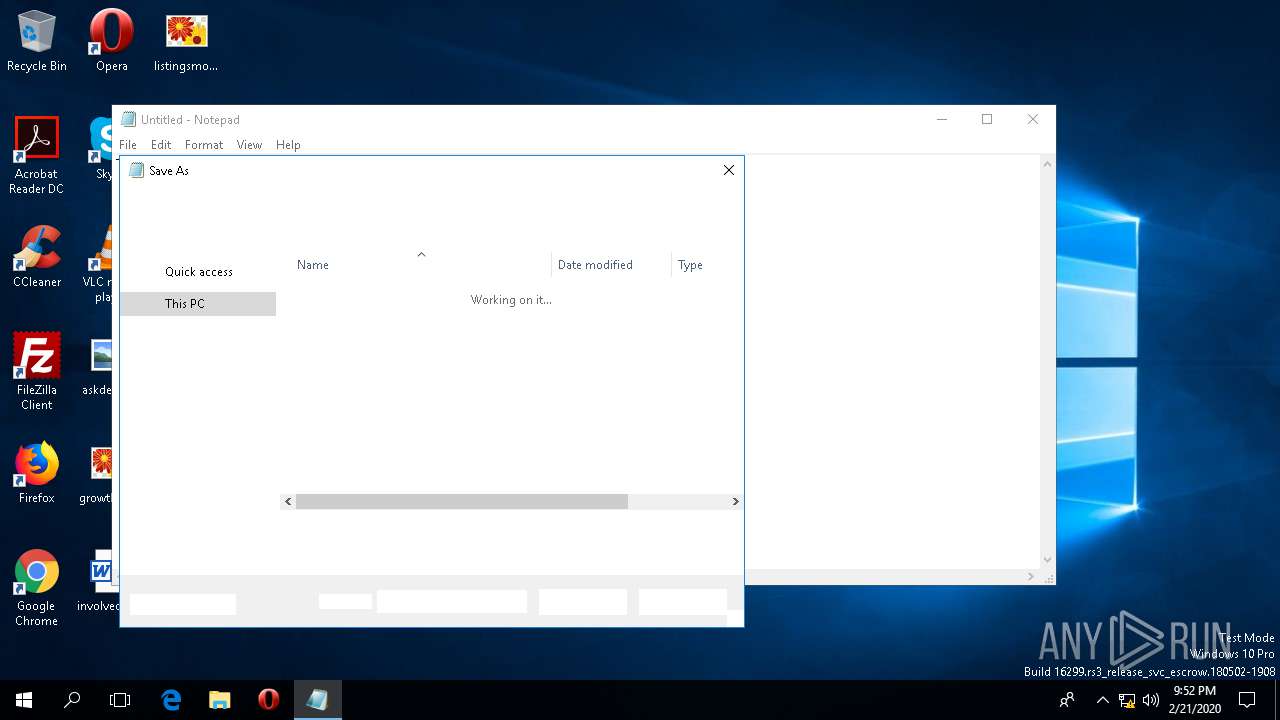
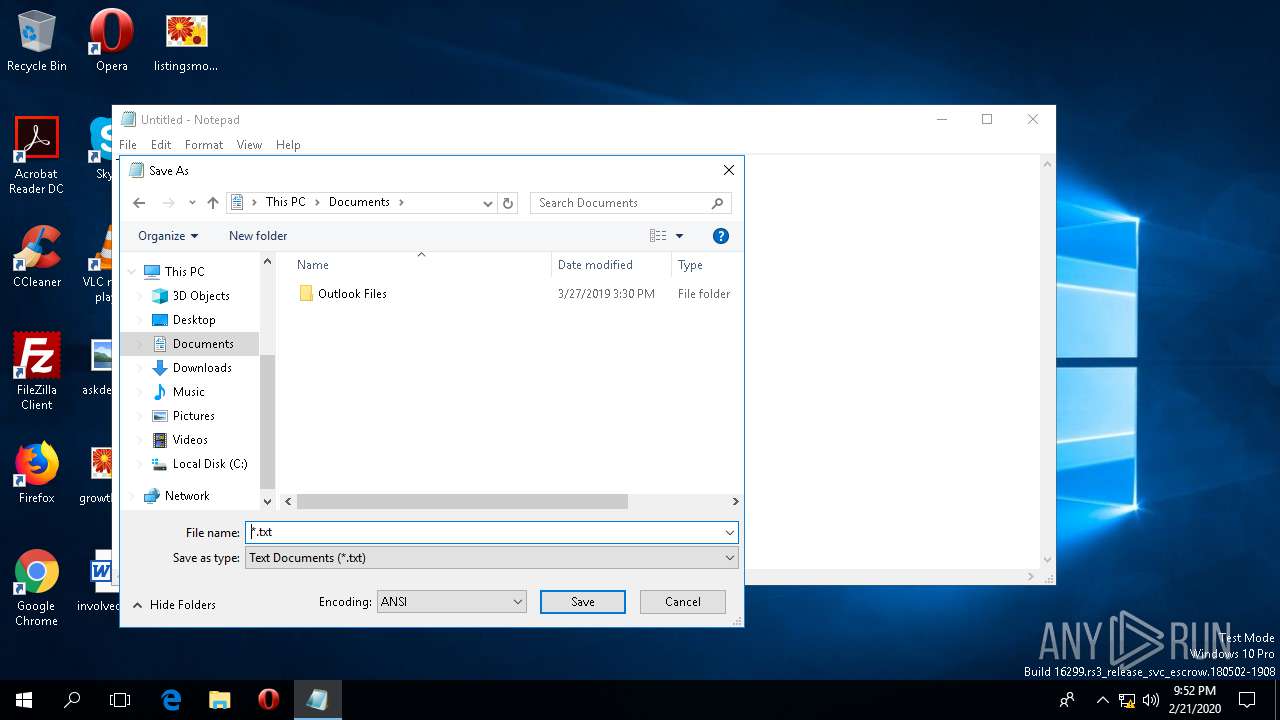
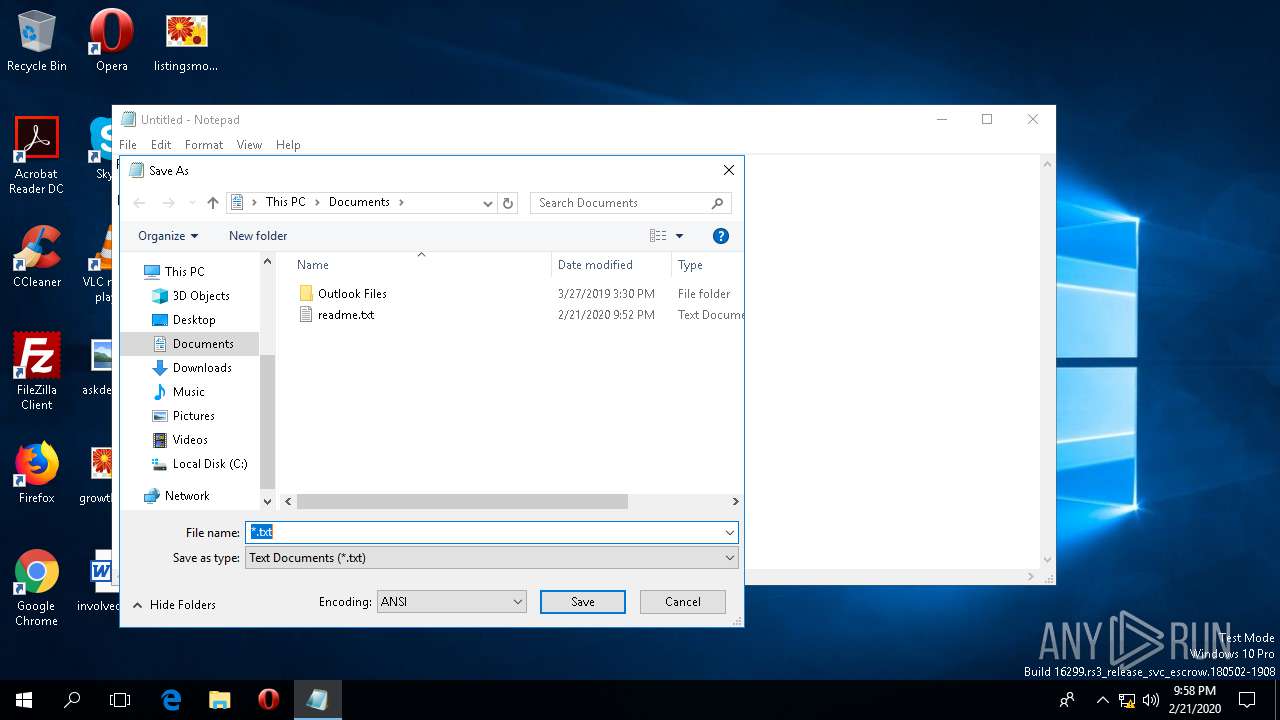
| (PID) Process: | (5532) notepad.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\LastVisitedPidlMRU |
| Operation: | write | Name: | MRUListEx |
Value: FFFFFFFF | |||
| (PID) Process: | (5532) notepad.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 0202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (5532) notepad.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 040000000300000000000000080000000100000007000000060000000500000002000000FFFFFFFF | |||
| (PID) Process: | (5532) notepad.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\4 |
| Operation: | write | Name: | MRUListEx |
Value: 050000000000000001000000040000000200000003000000FFFFFFFF | |||
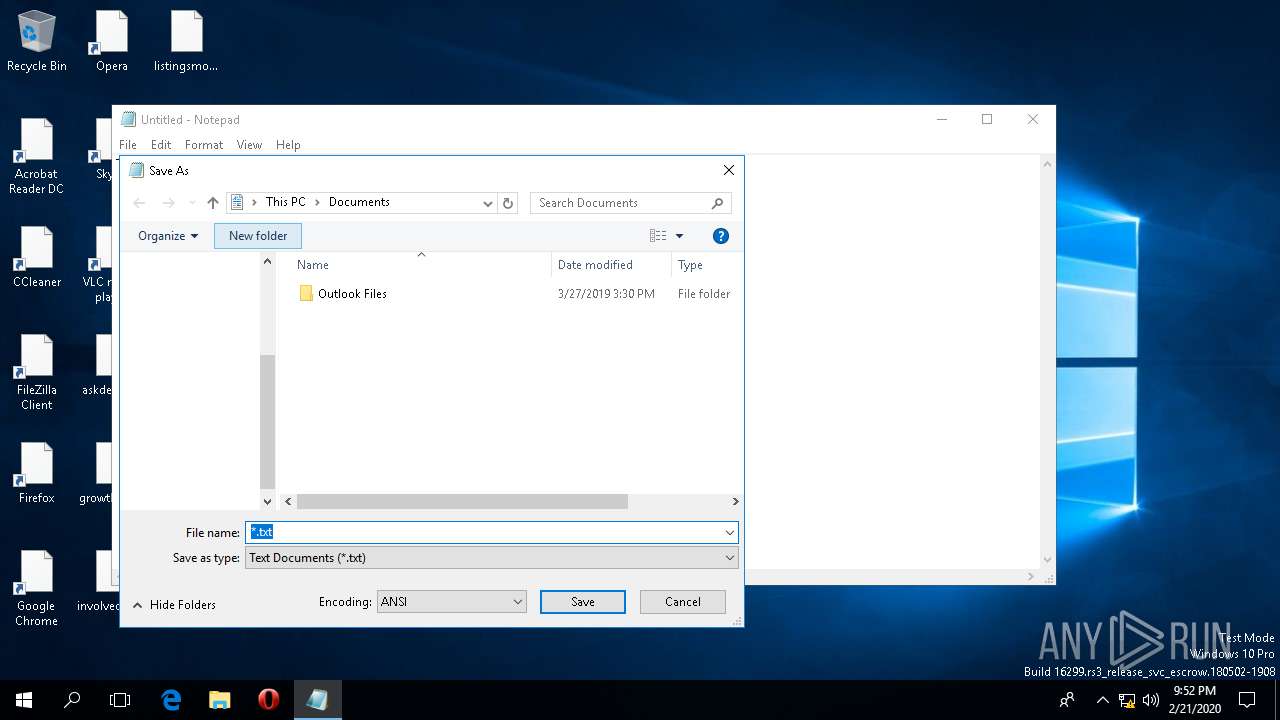
| (PID) Process: | (5532) notepad.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\95\Shell |
| Operation: | write | Name: | SniffedFolderType |
Value: Documents | |||
| (PID) Process: | (5532) notepad.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\192\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
0
Suspicious files
0
Text files
2
Unknown types
0
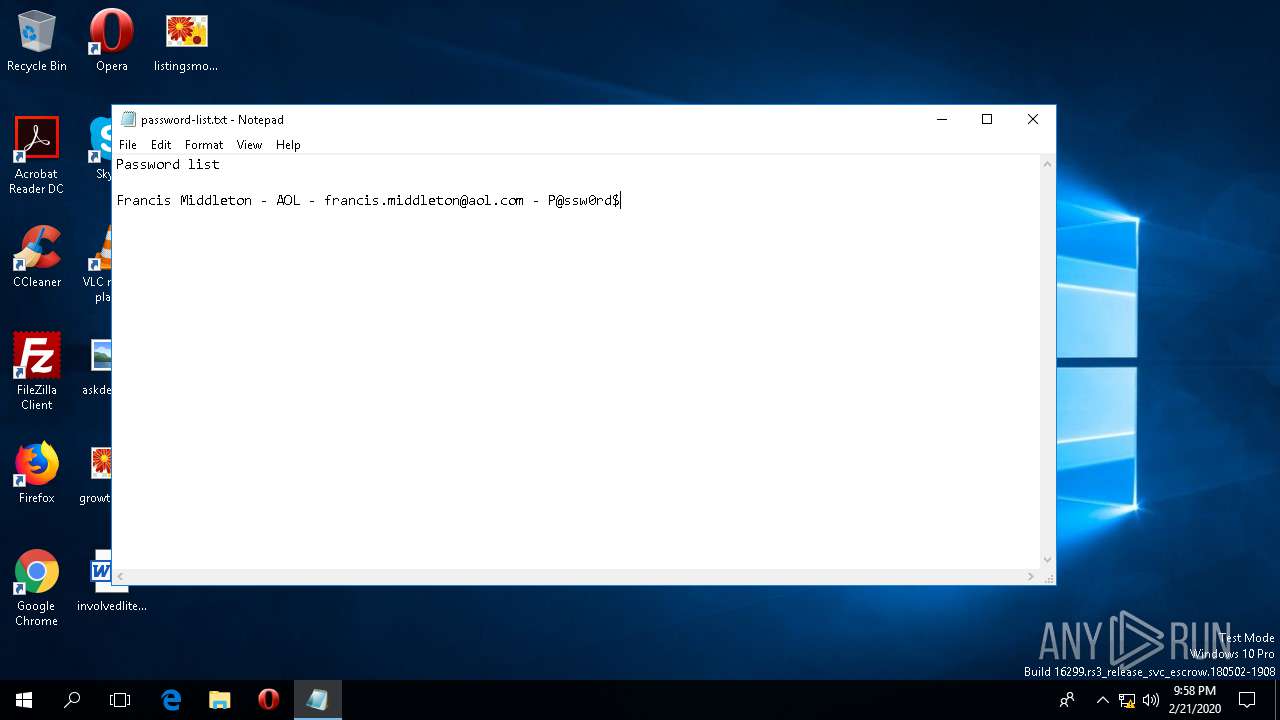
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5532 | notepad.exe | C:\Users\admin\Documents\readme.txt | text | |
MD5:— | SHA256:— | |||
| 5396 | notepad.exe | C:\Users\admin\Documents\password-list.txt | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
2
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5876 | svchost.exe | 52.158.29.237:443 | settings-win-ppe.data.microsoft.com | Microsoft Corporation | IE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
self.events.data.microsoft.com |
| whitelisted |
settings-win-ppe.data.microsoft.com |
| whitelisted |
Threats
Process | Message |
|---|---|
conhost.exe | InitSideBySide failed create an activation context. Error: 1814 |
Caff54e1.exe | OQvNmQmSEicZpzqEqMEJAVXRjsLREUVbwLdYKiuUmAXiKOtyv |
Caff54e1.exe | HKoXyqswGeTfnJAqUsgZXBRdsAZqzOqKGDXFETfwTCPRUiIUpAZnnFzkkuBrDATFw |
Caff54e1.exe | VSzbwOudBSUYeVAEQPYvMBeINKhLWDyqkqInwbSiZZFRihRHtCuuqBj |
Caff54e1.exe | rPMUppUQahBhrDpEngjmkTekZodyGUeQbNuaCVKjOAaboiAKEOpzR |
Caff54e1.exe | CCwaqQSKonzNbqloPCcNIUvqVFfZSUY |
Caff54e1.exe | HulLAlypcKTcEgYgvhjyPWYdiTcXurTCVqKgIUMfiQPXegl |
Caff54e1.exe | kmsEhNoxInrwgRoSzpvSNjrZpTooBIMzkEtfOjDTrxduqlVSHnIVFsflTNbjNdYl |
Caff54e1.exe | AlmqlVZywzNOHAsTuIVNlJjCABRooDfvoHMaSydtEXheoIKgNRKA |
Caff54e1.exe | oGYIQdXFuAaepoQOmSrFULZzVCqZsSIJRuYVkcWOtHBHlKEBDSxNzuvCtvGAFVWlAAXcayO |