| File name: | 03c5a8408af5b654880802218a6639059e83d9b8300a802f3ad5ada61707c2cc |
| Full analysis: | https://app.any.run/tasks/983ef184-02a6-41fc-8c47-acdc333ed0f6 |
| Verdict: | Malicious activity |
| Analysis date: | December 01, 2024, 04:06:37 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
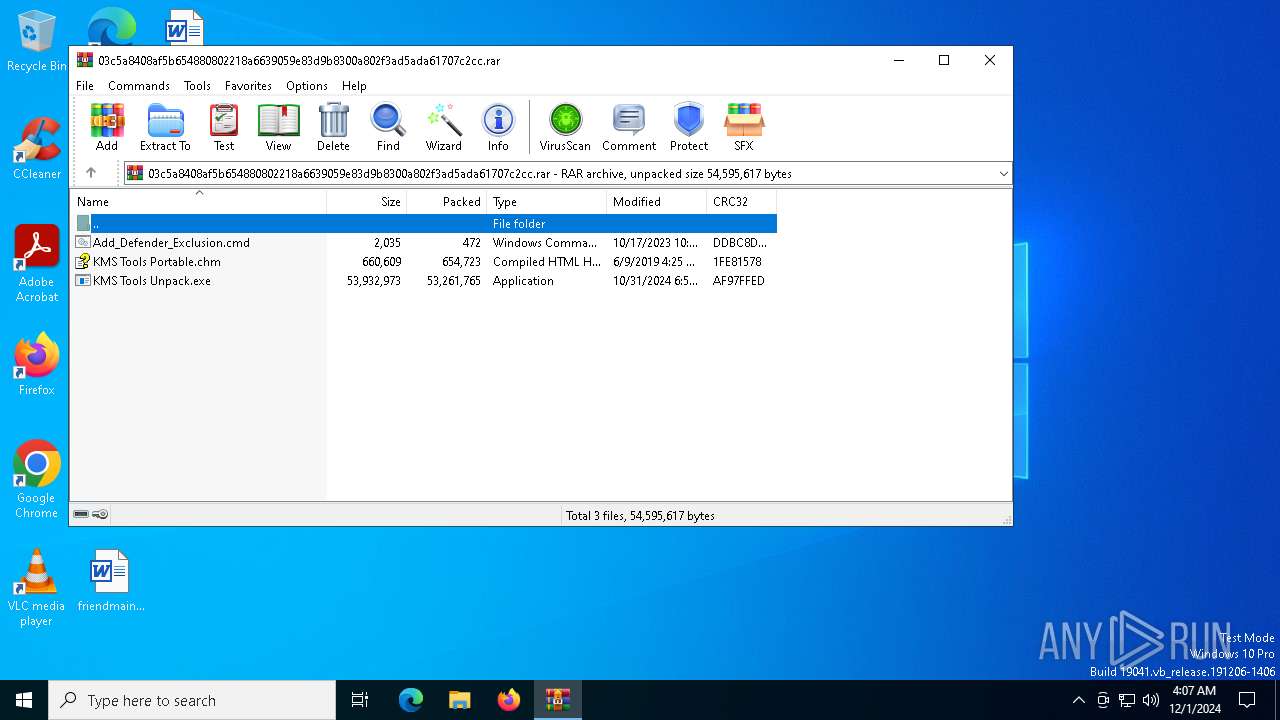
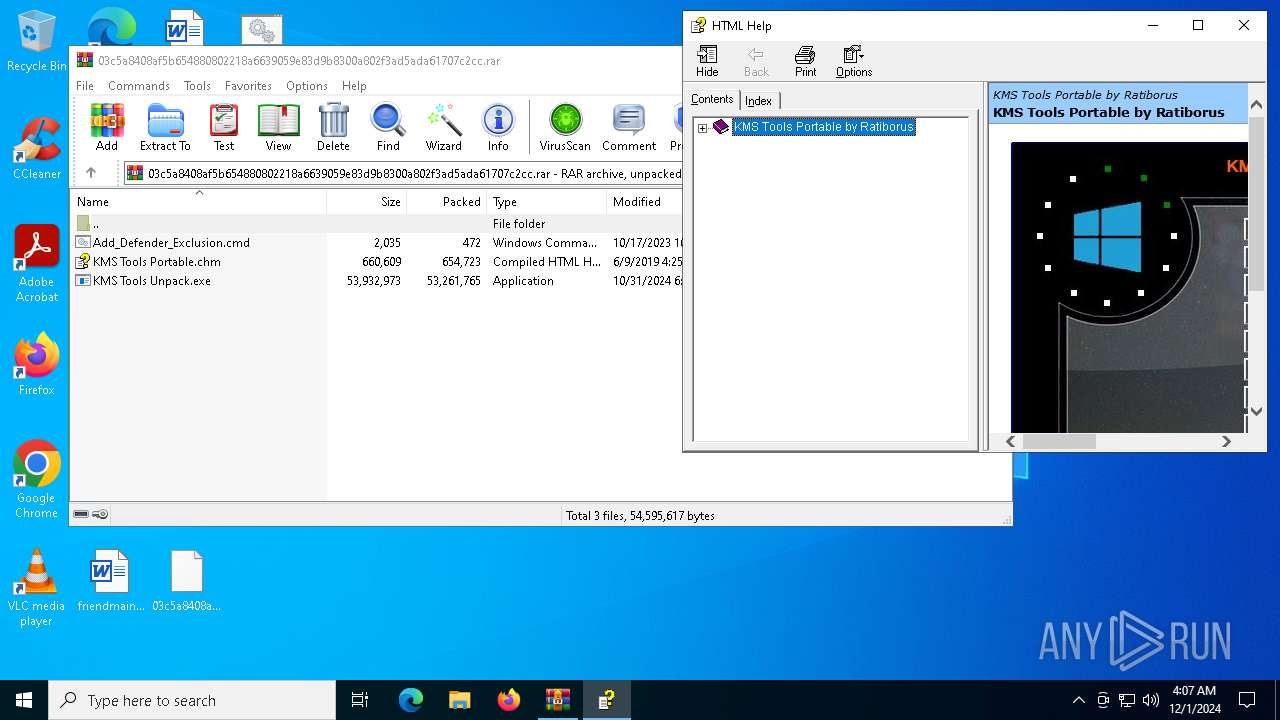
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 1F8D5AC5EAB9031D712F5F2624E01245 |
| SHA1: | D4DF11FC2294B412534CEDA91D38AD670D330330 |
| SHA256: | 03C5A8408AF5B654880802218A6639059E83D9B8300A802F3AD5ADA61707C2CC |
| SSDEEP: | 393216:4RFzH3pbcZ3Ij6+b13rkoOALFvmtSPk+V14gDhOrewqflS7XF2MKCU4M:EyYj6a13BGSPk+V14gorewqtyVACdM |
MALICIOUS
Run PowerShell with an invisible window
- powershell.exe (PID: 3080)
- powershell.exe (PID: 6772)
Adds path to the Windows Defender exclusion list
- cmd.exe (PID: 6672)
SUSPICIOUS
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 4824)
- cmd.exe (PID: 6672)
Starts process via Powershell
- powershell.exe (PID: 3080)
Script adds exclusion path to Windows Defender
- cmd.exe (PID: 6672)
The process hides Powershell's copyright startup banner
- cmd.exe (PID: 6672)
Executing commands from ".cmd" file
- powershell.exe (PID: 3080)
Starts CMD.EXE for commands execution
- powershell.exe (PID: 3080)
Found strings related to reading or modifying Windows Defender settings
- powershell.exe (PID: 3080)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 4824)
- cmd.exe (PID: 6672)
Script uses the treat ID number to allow Windows Defender to execute it
- cmd.exe (PID: 6672)
The process hide an interactive prompt from the user
- cmd.exe (PID: 6672)
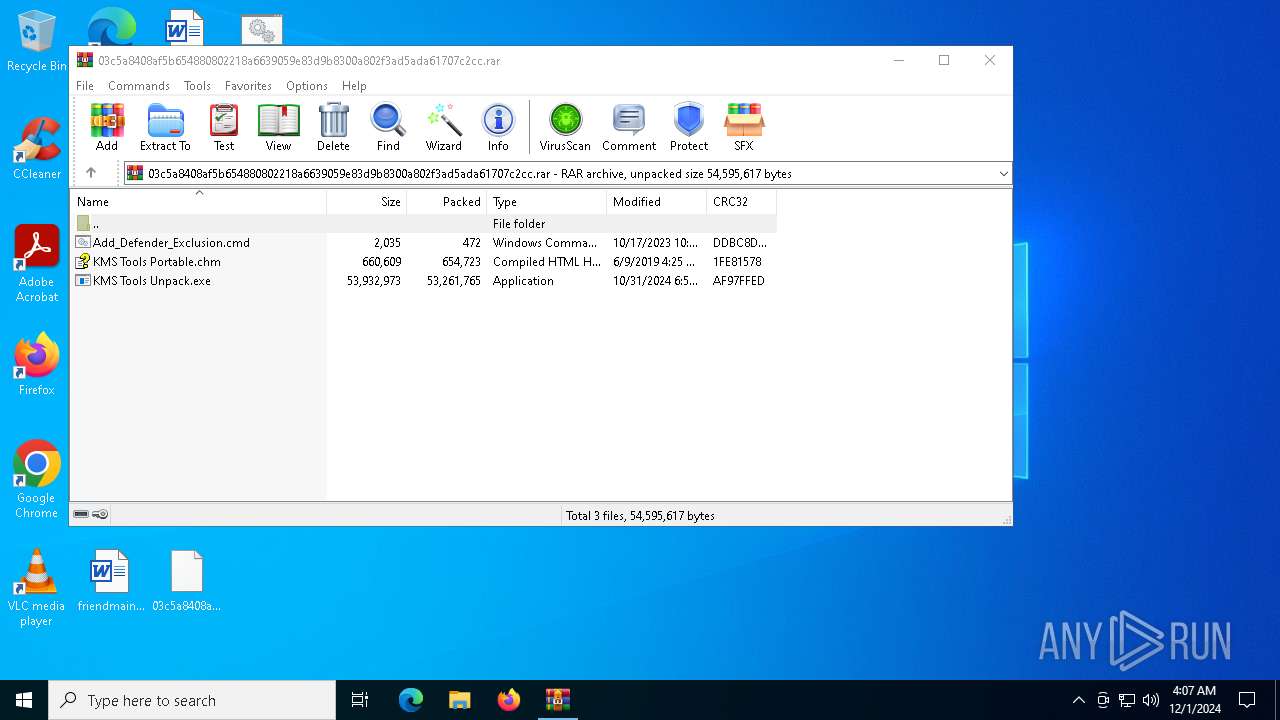
Executable content was dropped or overwritten
- KMS Tools Unpack.exe (PID: 6984)
Reads Microsoft Outlook installation path
- hh.exe (PID: 7060)
Reads Internet Explorer settings
- hh.exe (PID: 7060)
INFO
The process uses the downloaded file
- powershell.exe (PID: 3080)
- hh.exe (PID: 7060)
Manual execution by a user
- cmd.exe (PID: 4824)
- KMS Tools Unpack.exe (PID: 6984)
- hh.exe (PID: 7060)
Checks supported languages
- KMS Tools Unpack.exe (PID: 6984)
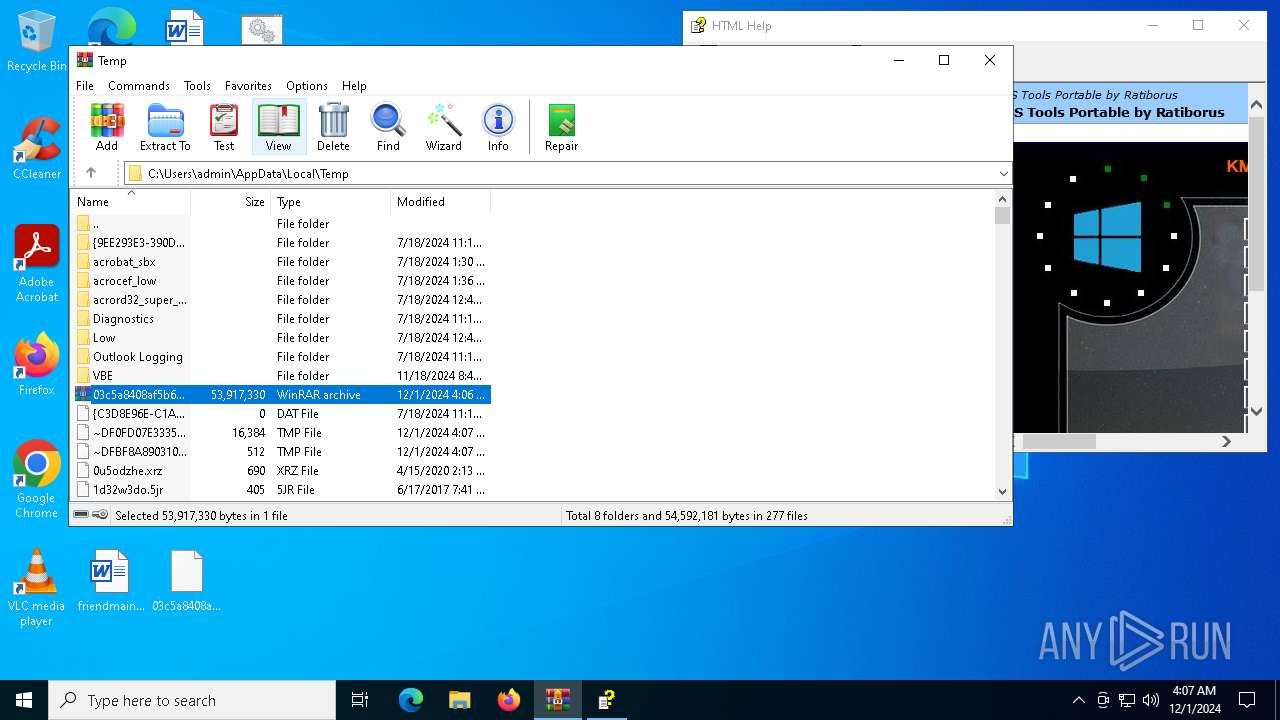
Create files in a temporary directory
- KMS Tools Unpack.exe (PID: 6984)
- hh.exe (PID: 7060)
Creates files or folders in the user directory
- KMS Tools Unpack.exe (PID: 6984)
- hh.exe (PID: 7060)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 6772)
Reads the computer name
- KMS Tools Unpack.exe (PID: 6984)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 6772)
Checks proxy server information
- hh.exe (PID: 7060)
Reads security settings of Internet Explorer
- hh.exe (PID: 7060)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
EXIF
ZIP
| FileVersion: | RAR v5 |
|---|---|
| CompressedSize: | 472 |
| UncompressedSize: | 2035 |
| OperatingSystem: | Win32 |
| ArchivedFileName: | Add_Defender_Exclusion.cmd |
Total processes
138
Monitored processes
13
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 536 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2940 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3080 | powershell.exe -windowstyle hidden -noprofile "Start-Process 'C:\Users\admin\Desktop\Add_Defender_Exclusion.cmd' -Verb RunAs" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4824 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\Desktop\Add_Defender_Exclusion.cmd" " | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5080 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6444 | reg query "HKU\S-1-5-19\Environment" | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6516 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\03c5a8408af5b654880802218a6639059e83d9b8300a802f3ad5ada61707c2cc.rar | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 6672 | "C:\WINDOWS\System32\cmd.exe" /C "C:\Users\admin\Desktop\Add_Defender_Exclusion.cmd" | C:\Windows\System32\cmd.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6700 | reg query "HKU\S-1-5-19\Environment" | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6772 | Powershell -nologo -noninteractive -windowStyle hidden -noprofile -command Add-MpPreference -ThreatIDDefaultAction_Ids 2147685180 -ThreatIDDefaultAction_Actions Allow -Force; Add-MpPreference -ThreatIDDefaultAction_Ids 2147735507 -ThreatIDDefaultAction_Actions Allow -Force; Add-MpPreference -ThreatIDDefaultAction_Ids 2147736914 -ThreatIDDefaultAction_Actions Allow -Force; Add-MpPreference -ThreatIDDefaultAction_Ids 2147743522 -ThreatIDDefaultAction_Actions Allow -Force; Add-MpPreference -ThreatIDDefaultAction_Ids 2147734094 -ThreatIDDefaultAction_Actions Allow -Force; Add-MpPreference -ThreatIDDefaultAction_Ids 2147743421 -ThreatIDDefaultAction_Actions Allow -Force; Add-MpPreference -ThreatIDDefaultAction_Ids 2147765679 -ThreatIDDefaultAction_Actions Allow -Force; Add-MpPreference -ThreatIDDefaultAction_Ids 2147783203 -ThreatIDDefaultAction_Actions Allow -Force; Add-MpPreference -ThreatIDDefaultAction_Ids 251873 -ThreatIDDefaultAction_Actions Allow -Force; Add-MpPreference -ThreatIDDefaultAction_Ids 213927 -ThreatIDDefaultAction_Actions Allow -Force; Add-MpPreference -ThreatIDDefaultAction_Ids 2147722906 -ThreatIDDefaultAction_Actions Allow -Force; Add-MpPreference -ExclusionPath C:\Windows\KMSAutoS -Force; Add-MpPreference -ExclusionPath C:\Windows\System32\SppExtComObjHook.dll -Force; Add-MpPreference -ExclusionPath C:\Windows\System32\SppExtComObjPatcher.exe -Force; Add-MpPreference -ExclusionPath C:\Windows\AAct_Tools -Force; Add-MpPreference -ExclusionPath C:\Windows\AAct_Tools\AAct_x64.exe -Force; Add-MpPreference -ExclusionPath C:\Windows\AAct_Tools\AAct_files\KMSSS.exe -Force; Add-MpPreference -ExclusionPath C:\Windows\AAct_Tools\AAct_files -Force; Add-MpPreference -ExclusionPath C:\Windows\KMS -Force; | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
14 106
Read events
14 086
Write events
20
Delete events
0
Modification events
| (PID) Process: | (6516) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (6516) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (6516) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (6516) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\03c5a8408af5b654880802218a6639059e83d9b8300a802f3ad5ada61707c2cc.rar | |||
| (PID) Process: | (6516) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6516) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6516) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6516) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3080) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\WINDOWS\System32\cmd.exe.FriendlyAppName |
Value: Windows Command Processor | |||
| (PID) Process: | (3080) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\WINDOWS\System32\cmd.exe.ApplicationCompany |
Value: Microsoft Corporation | |||
Executable files
1
Suspicious files
2
Text files
6
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6984 | KMS Tools Unpack.exe | C:\Users\admin\Desktop\kms tools unpack.exe | — | |
MD5:— | SHA256:— | |||
| 3080 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_sqomfrha.q5q.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6772 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_q5mkl5ag.nd1.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 3080 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:8999426E478A5D54159D15B2009A3CC3 | SHA256:55B95AF1C8A6AAE62120761F494DA35F9C55347A346DB22FA7BF4A12A0652C78 | |||
| 3080 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_3fvx4mgo.mgw.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6772 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_erfyi0te.140.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6984 | KMS Tools Unpack.exe | C:\Users\admin\AppData\Local\icsys.icn.exe | executable | |
MD5:5FB73538B75DF99F42395B27C7051B6F | SHA256:A7FD1350004BF71F48CD394234FC81E5511CDA0AD64E44384AD8B5F18970342A | |||
| 6984 | KMS Tools Unpack.exe | C:\Users\admin\AppData\Local\Temp\~DF190DB9EDC61A39A0.TMP | binary | |
MD5:1FBAA4E3BA3E6EEDF2E742AFCA8EAA25 | SHA256:EEE8394286500149672FCE867CF1C245FFDBAFF900656B2A5C4245C7C4D36E79 | |||
| 7060 | hh.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\RR3E01RZ\_template[1].css | text | |
MD5:AB5BE7866083FC6233445F8AC51AB57C | SHA256:C0254BDDB7DAC7B1E7902A9A5313F2BCF9790113EEE8833E2AD01E377C6C79E0 | |||
| 7060 | hh.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\KCV3KQBA\12[1].JPG | image | |
MD5:E2F19317D305496857C1213EB1E6F7F8 | SHA256:527D2F2FE980D90CB6CA317AA93BC113643D70C3E7C6A426CF7F274A2A8167D3 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
33
DNS requests
20
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7012 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7012 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5200 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4712 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 23.216.77.6:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5064 | SearchApp.exe | 104.126.37.128:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
1176 | svchost.exe | 40.126.31.73:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
1176 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |