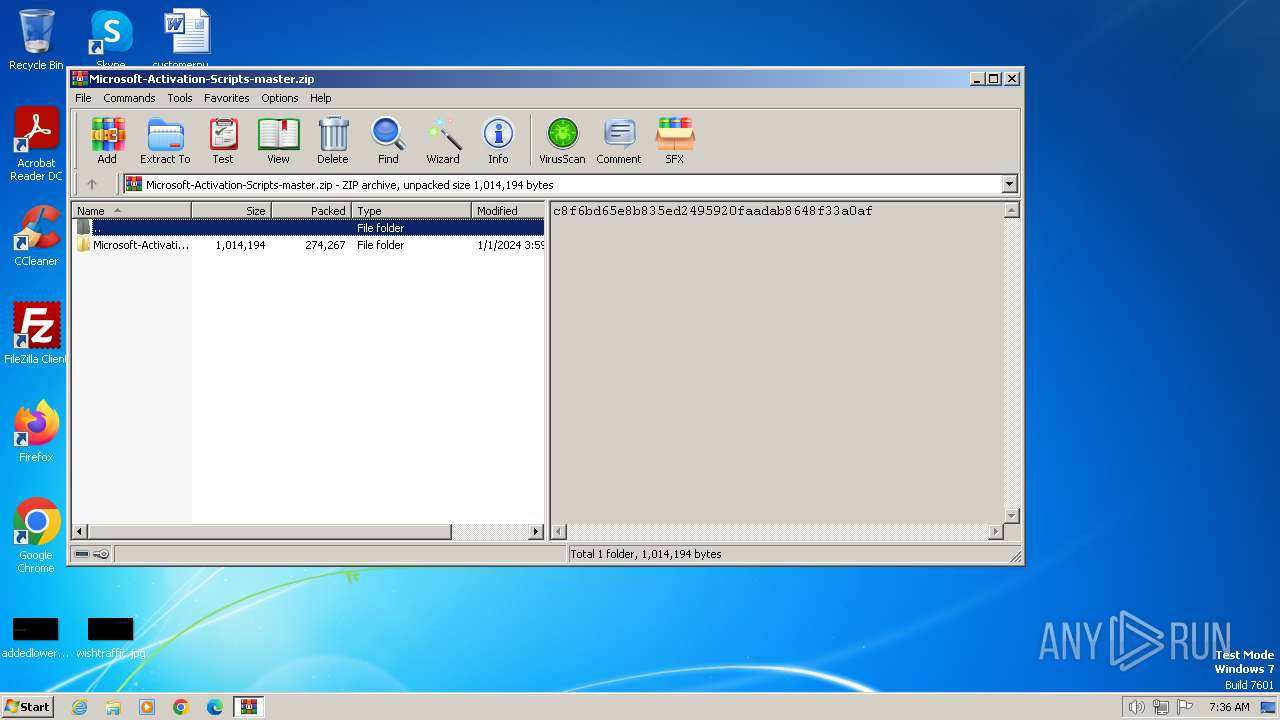
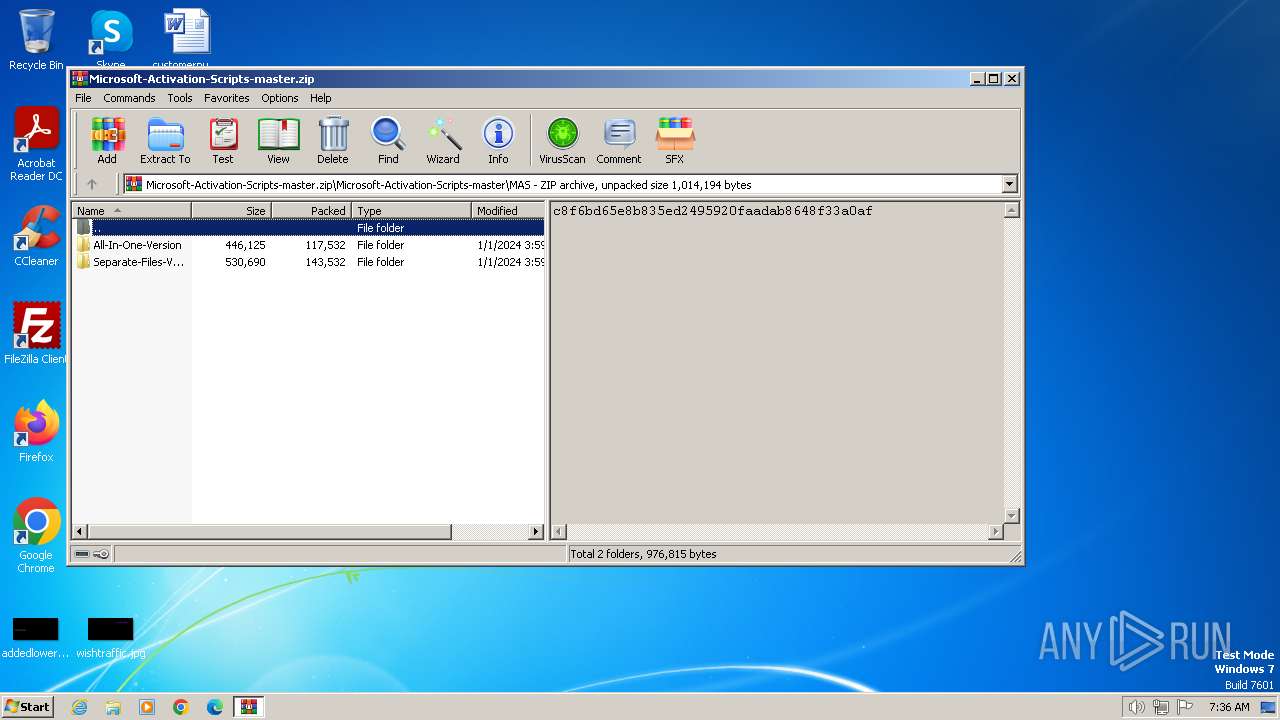
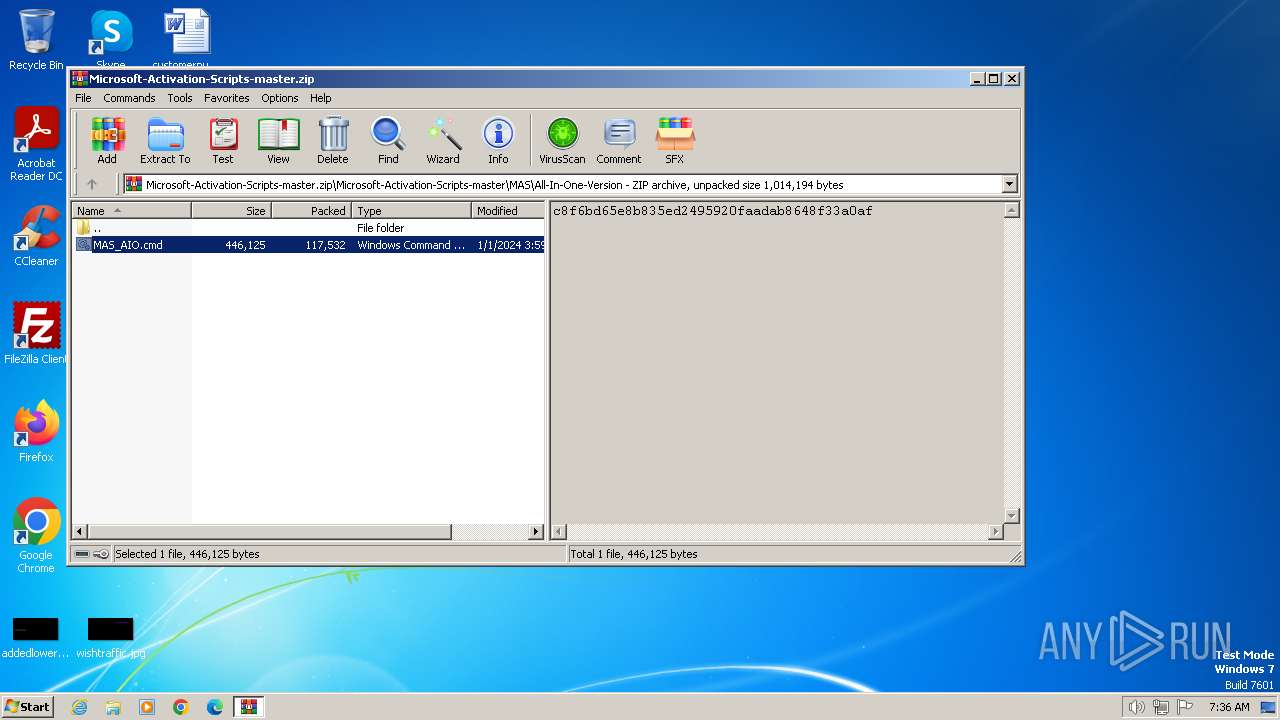
| File name: | Microsoft-Activation-Scripts-master.zip |
| Full analysis: | https://app.any.run/tasks/8fc47803-ed65-4706-a246-117d3fb8650c |
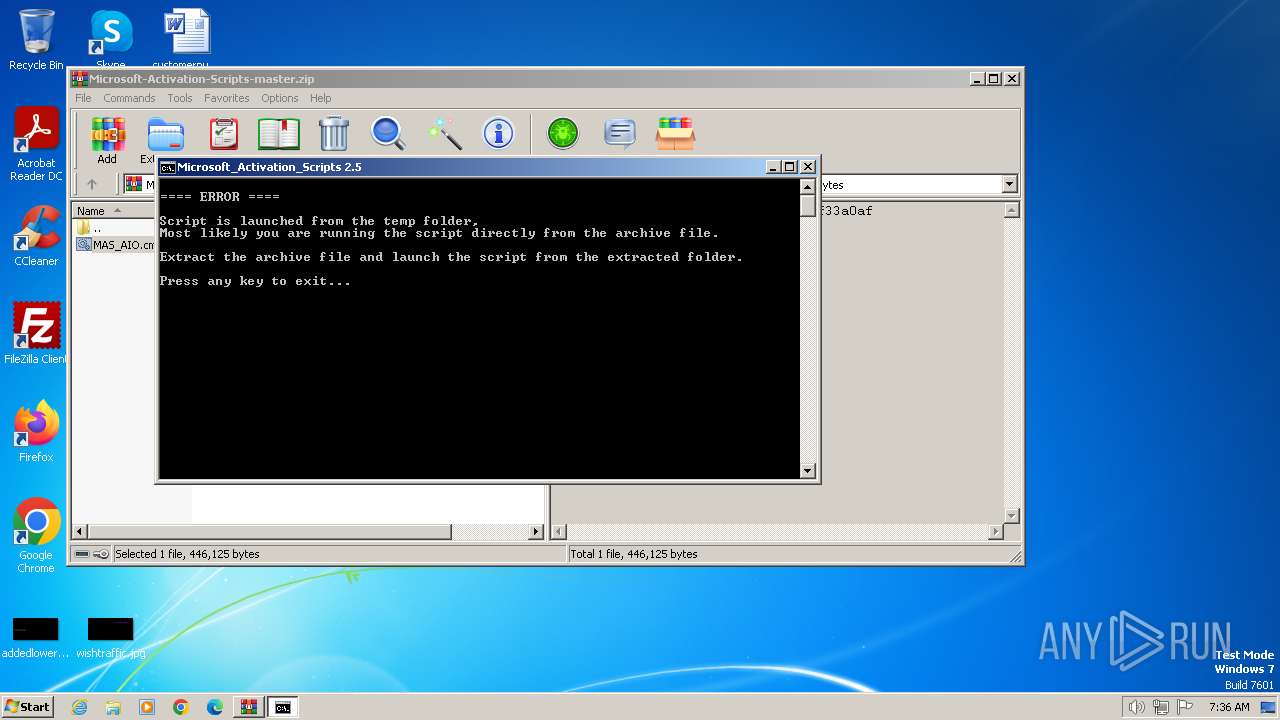
| Verdict: | Malicious activity |
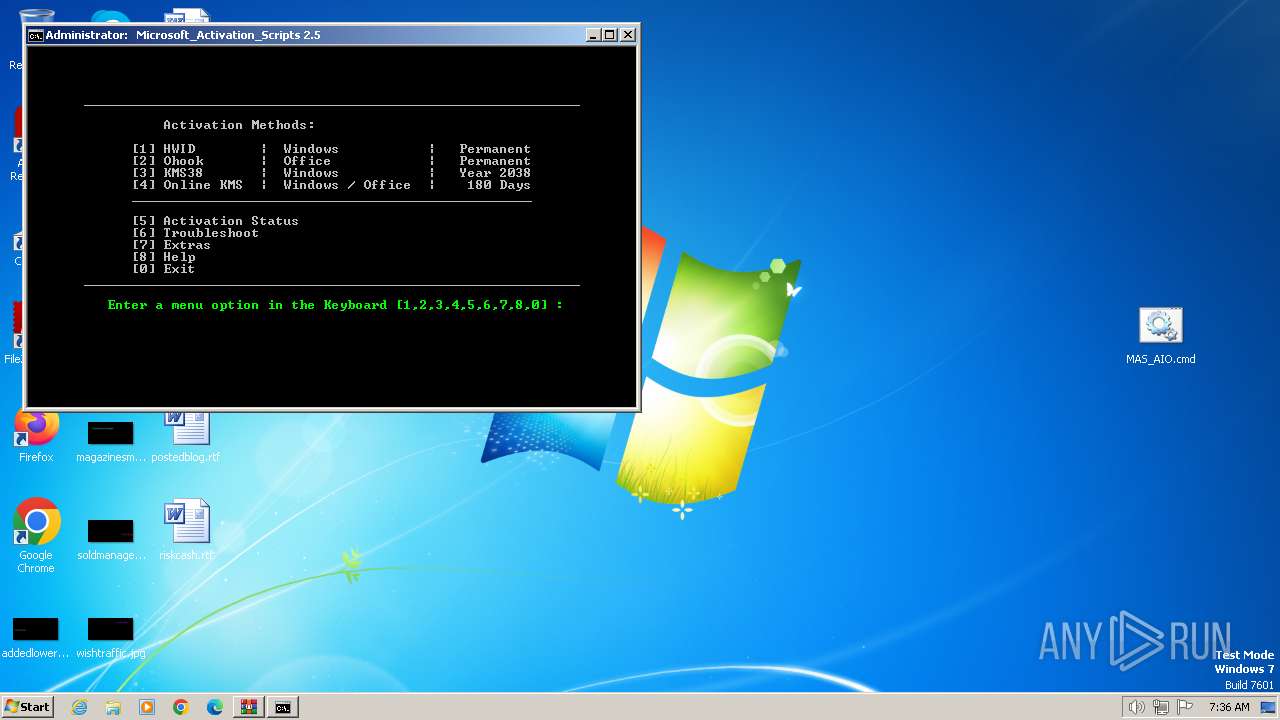
| Analysis date: | January 16, 2024, 07:36:10 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract |
| MD5: | FA9B9F21A71866EC87E20C721B4E8865 |
| SHA1: | 12AE9DB9978260855A6E1B952529BB94969309CA |
| SHA256: | 03C131348540BE1F489820F440B5E71F5E5464262CEA6BDF894BE029F73306DC |
| SSDEEP: | 12288:RadWw4HIyb2/0kK9W9De4HbJp1j+Ltzi4cYxhkll:RmWw4HIyb2/0kK9W9De4HbJp1j+Lt+4q |
MALICIOUS
No malicious indicators.SUSPICIOUS
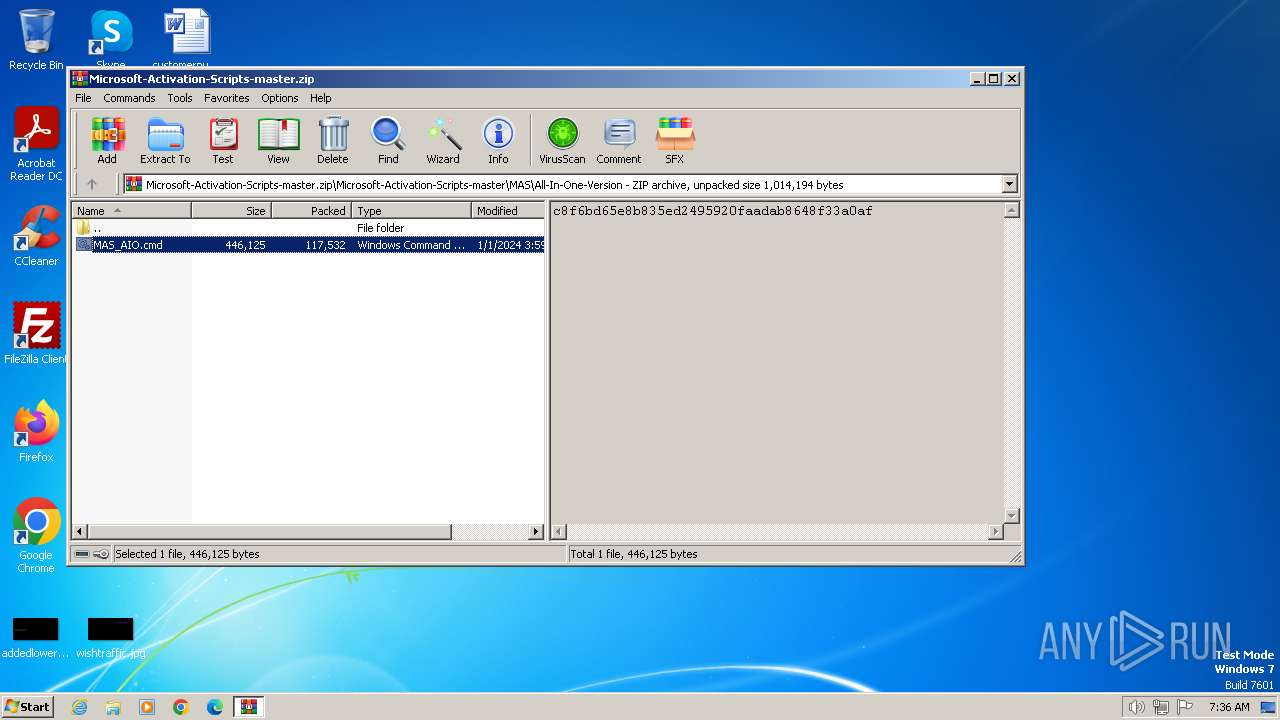
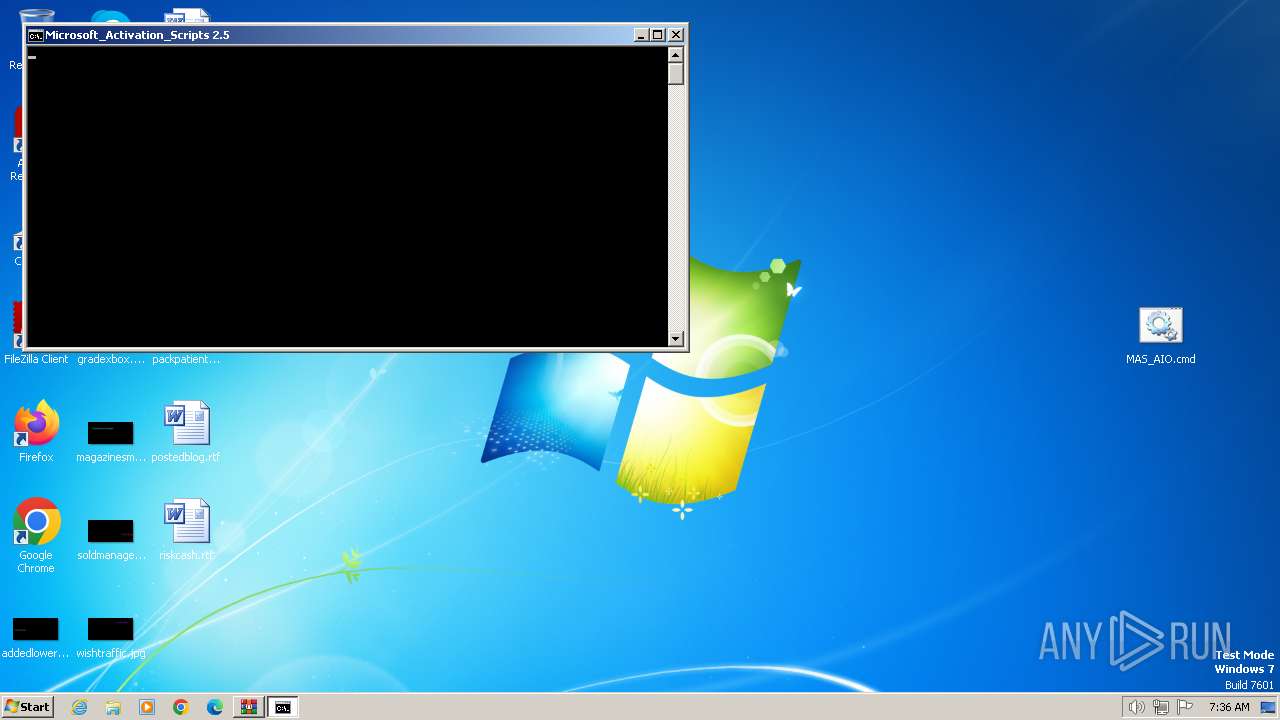
Executing commands from ".cmd" file
- cmd.exe (PID: 1840)
- cmd.exe (PID: 1288)
- WinRAR.exe (PID: 116)
- powershell.exe (PID: 844)
- cmd.exe (PID: 2628)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 1840)
- cmd.exe (PID: 1288)
- WinRAR.exe (PID: 116)
- powershell.exe (PID: 844)
- cmd.exe (PID: 2628)
Starts SC.EXE for service management
- cmd.exe (PID: 1840)
- cmd.exe (PID: 1288)
- cmd.exe (PID: 2628)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 1840)
- cmd.exe (PID: 1288)
- cmd.exe (PID: 2628)
Application launched itself
- cmd.exe (PID: 1840)
- cmd.exe (PID: 1288)
- cmd.exe (PID: 2628)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 1840)
- cmd.exe (PID: 2628)
Reads the Internet Settings
- powershell.exe (PID: 844)
INFO
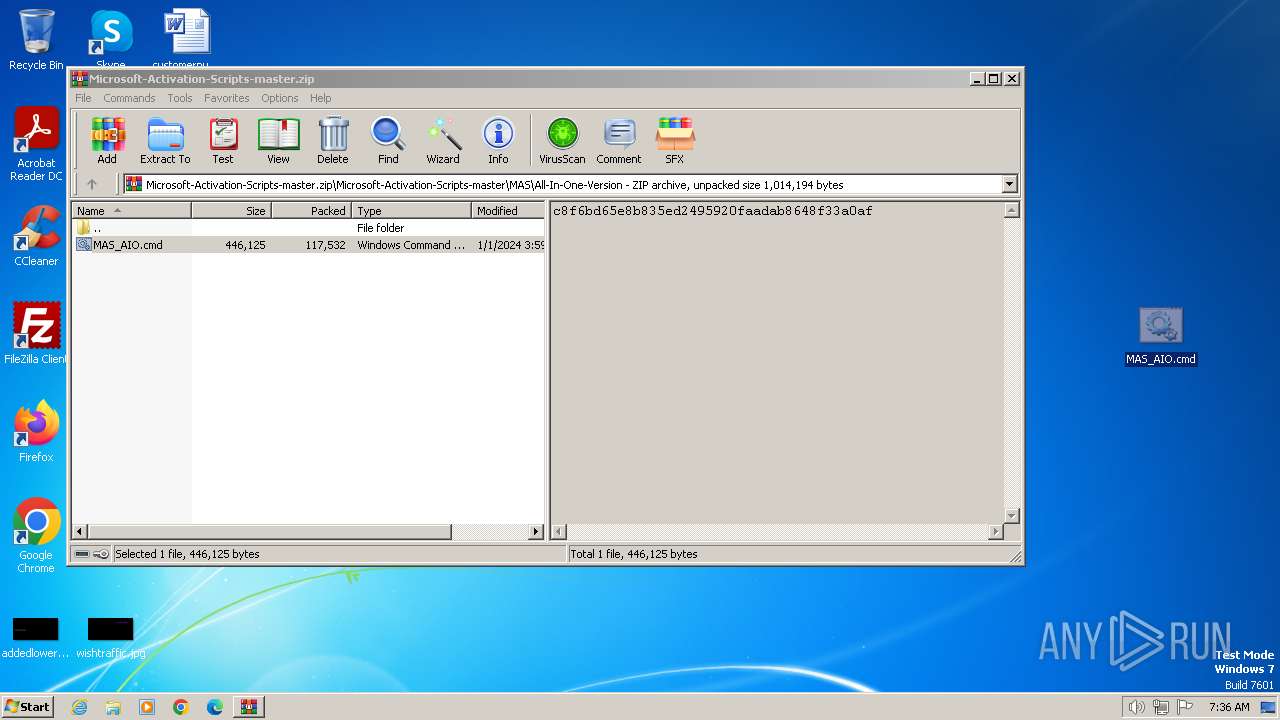
Manual execution by a user
- cmd.exe (PID: 1840)
Checks operating system version
- cmd.exe (PID: 1288)
- cmd.exe (PID: 1840)
- cmd.exe (PID: 2628)
Checks supported languages
- mode.com (PID: 2888)
- mode.com (PID: 2972)
- mode.com (PID: 3180)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2023:12:31 19:59:26 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | Microsoft-Activation-Scripts-master/ |
Total processes
101
Monitored processes
62
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Microsoft-Activation-Scripts-master.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 148 | C:\Windows\system32\cmd.exe /S /D /c" echo "-el" " | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 376 | findstr /v "f7f81a39-5f63-5b42-9efd-1f13b5431005quot; "MAS_AIO.cmd" | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (QGREP) Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 452 | find /i "RUNNING" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 604 | choice /C:123456780 /N | C:\Windows\System32\choice.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Offers the user a choice Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 664 | C:\Windows\system32\cmd.exe /c "prompt $H&for %B in (1) do rem" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 844 | powershell.exe "start cmd.exe -arg '/c \""""C:\Users\admin\Desktop\MAS_AIO.cmd""" -el \"' -verb runas" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 980 | C:\Windows\system32\cmd.exe /c ping -4 -n 1 updatecheck.massgrave.dev | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 984 | reg query HKCU\Console /v QuickEdit | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1220 | powershell.exe write-host -back '"Red"' -fore '"white"' '"==== ERROR ===="' | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
Total events
4 897
Read events
4 871
Write events
26
Delete events
0
Modification events
| (PID) Process: | (116) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (116) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (116) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (116) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (116) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\curl-8.5.0_1-win32-mingw.zip | |||
| (PID) Process: | (116) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (116) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (116) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (116) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (116) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
12
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1220 | powershell.exe | C:\Users\admin\AppData\Local\Temp\vknldmi4.zsv.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 2628 | cmd.exe | C:\Windows\Temp\' | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
| 844 | powershell.exe | C:\Users\admin\AppData\Local\Temp\hdnahfbu.55v.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 844 | powershell.exe | C:\Users\admin\AppData\Local\Temp\ljaxlosp.22w.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 2840 | powershell.exe | C:\Users\admin\AppData\Local\Temp\ifix2b0q.cfs.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 844 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:446DD1CF97EABA21CF14D03AEBC79F27 | SHA256:A7DE5177C68A64BD48B36D49E2853799F4EBCFA8E4761F7CC472F333DC5F65CF | |||
| 3040 | powershell.exe | C:\Users\admin\AppData\Local\Temp\j1pbxvzg.gzp.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 2628 | cmd.exe | C:\Windows\Temp\`.txt | text | |
MD5:C48DE30A6D93DE10929A00F17D725A24 | SHA256:96BA30BF853B79CD26E5399DB76DEF0F6BE3C936FC1263232937FBC8A0C8C5B5 | |||
| 2840 | powershell.exe | C:\Users\admin\AppData\Local\Temp\jmj3abv3.det.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 1220 | powershell.exe | C:\Users\admin\AppData\Local\Temp\ckxho0jw.4jy.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
updatecheck.massgrave.dev |
| unknown |