| File name: | 03a236d2edf54ccc11d7adec65dd02c3ee4d7dff6226ceb83c5b9be4472939f3.exe |
| Full analysis: | https://app.any.run/tasks/d84c934e-1111-41ba-83c6-257bb6725336 |
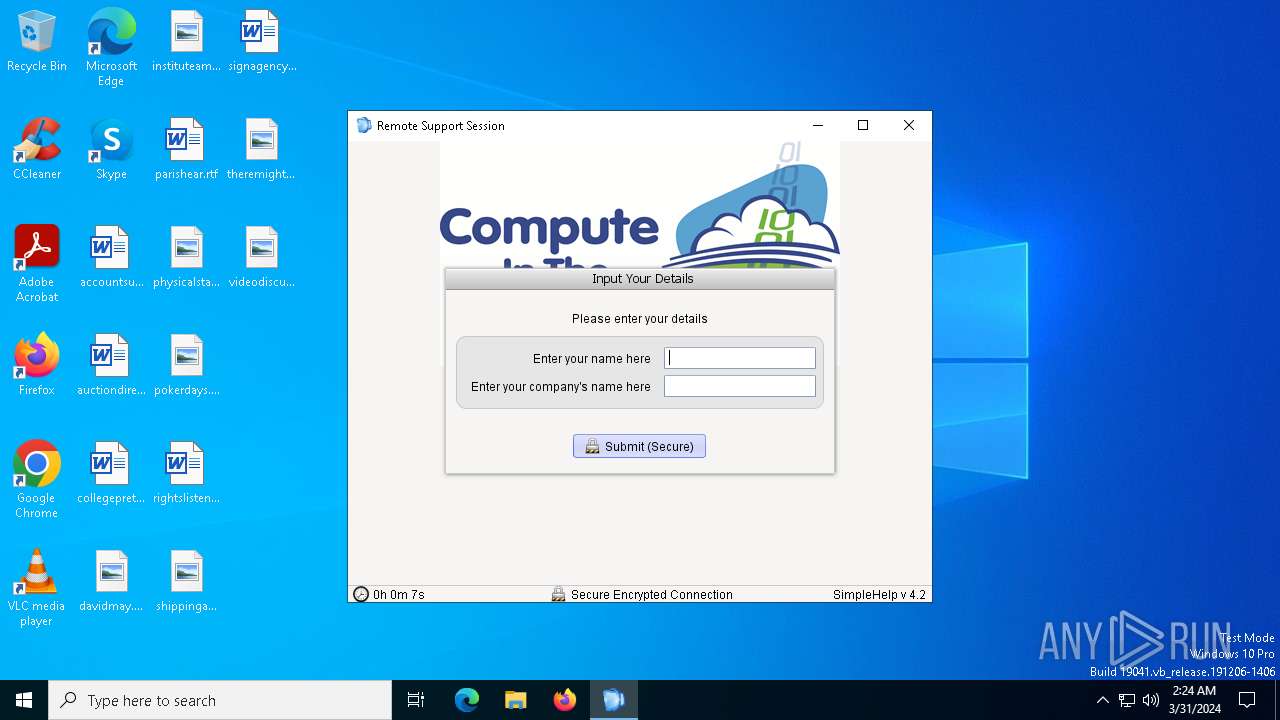
| Verdict: | Malicious activity |
| Analysis date: | March 31, 2024, 02:23:37 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 5096BEA0BADB422849E9306CF9A8DA9C |
| SHA1: | 770AFBD27B0062F0587F70A4C5363A28E6A54063 |
| SHA256: | 03A236D2EDF54CCC11D7ADEC65DD02C3EE4D7DFF6226CEB83C5B9BE4472939F3 |
| SSDEEP: | 49152:tyg2G6PidgKt60jKHLHuSNbR0VqPWBuEjMYmnG0ZiM9X/hFurlQ4UtULo:Ig2GklKvj4jn5a3BqYp0ZiW5Z45o |
MALICIOUS
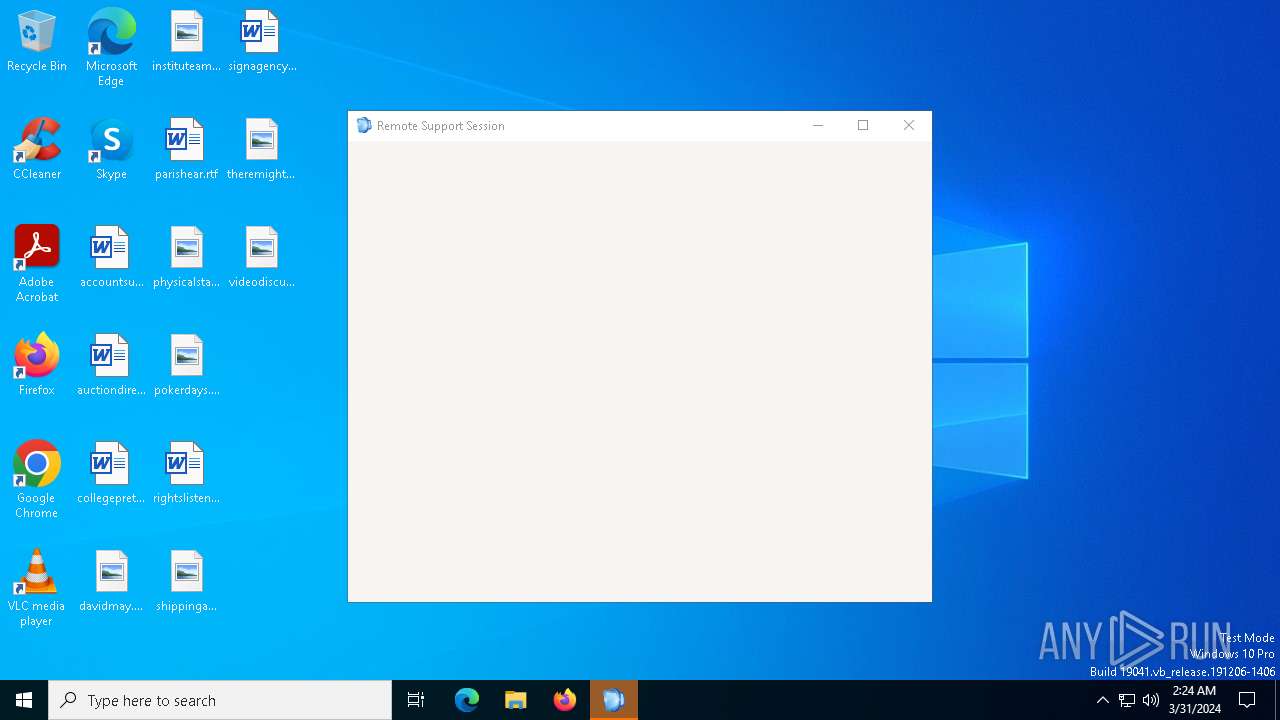
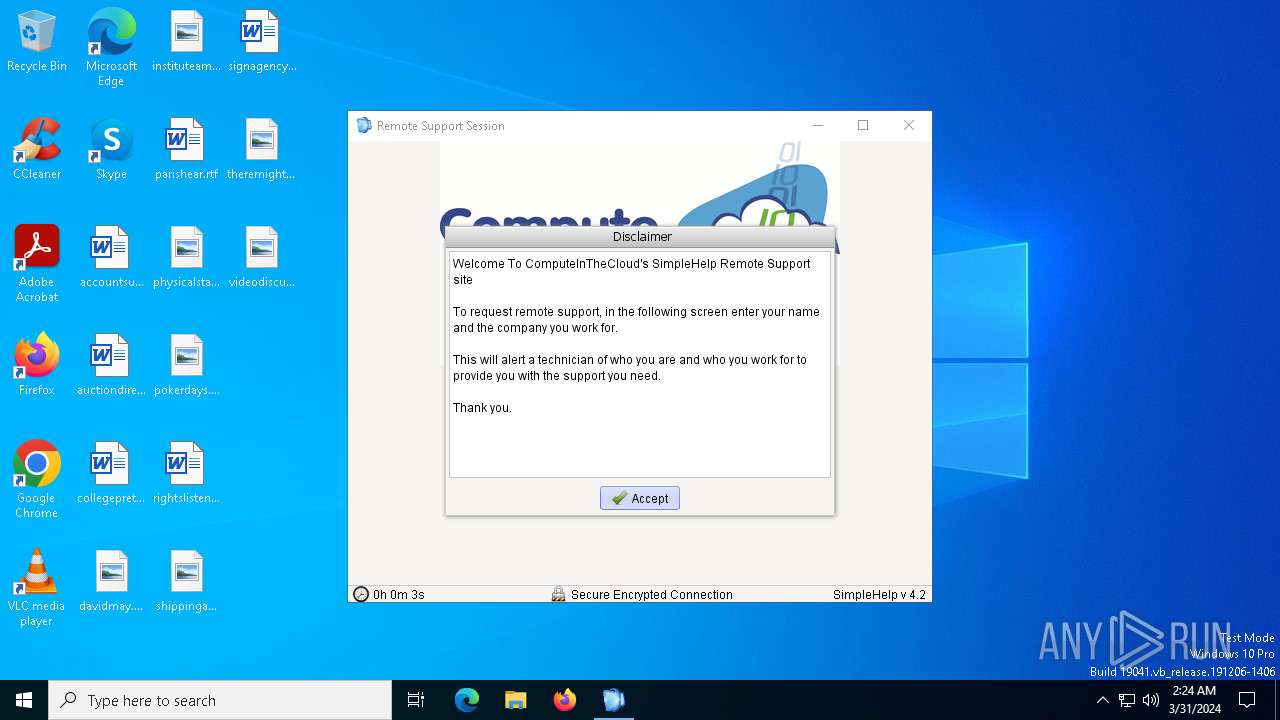
Drops the executable file immediately after the start
- 03a236d2edf54ccc11d7adec65dd02c3ee4d7dff6226ceb83c5b9be4472939f3.exe (PID: 6480)
- Remote Support.exe (PID: 5828)
Deletes the SafeBoot registry key
- SimpleService.exe (PID: 3652)
SUSPICIOUS
Process drops legitimate windows executable
- 03a236d2edf54ccc11d7adec65dd02c3ee4d7dff6226ceb83c5b9be4472939f3.exe (PID: 6480)
Reads security settings of Internet Explorer
- 03a236d2edf54ccc11d7adec65dd02c3ee4d7dff6226ceb83c5b9be4472939f3.exe (PID: 6480)
- elev_win.exe (PID: 6488)
- elev_win.exe (PID: 3836)
Checks for Java to be installed
- 03a236d2edf54ccc11d7adec65dd02c3ee4d7dff6226ceb83c5b9be4472939f3.exe (PID: 6480)
- Remote Support.exe (PID: 5828)
- javaw.exe (PID: 7016)
- javaw.exe (PID: 3100)
Uses ICACLS.EXE to modify access control lists
- 03a236d2edf54ccc11d7adec65dd02c3ee4d7dff6226ceb83c5b9be4472939f3.exe (PID: 6480)
- Remote SupportECompatibility.exe (PID: 1688)
- Remote Support.exe (PID: 5828)
Reads the date of Windows installation
- elev_win.exe (PID: 6488)
- elev_win.exe (PID: 3836)
Application launched itself
- elev_win.exe (PID: 6488)
- SimpleService.exe (PID: 3936)
- javaw.exe (PID: 3100)
Executes as Windows Service
- SimpleService.exe (PID: 3936)
INFO
Checks supported languages
- 03a236d2edf54ccc11d7adec65dd02c3ee4d7dff6226ceb83c5b9be4472939f3.exe (PID: 6480)
- lzma.exe (PID: 5116)
- unpack200.exe (PID: 5904)
- lzma.exe (PID: 7024)
- unpack200.exe (PID: 7156)
- unpack200.exe (PID: 7052)
- javaw.exe (PID: 7048)
- Remote SupportECompatibility.exe (PID: 1688)
- elev_win.exe (PID: 6488)
- Remote Support.exe (PID: 5828)
- SimpleService.exe (PID: 4976)
- SimpleService.exe (PID: 3652)
- SimpleService.exe (PID: 3936)
- session_win.exe (PID: 6496)
- javaw.exe (PID: 3100)
- elev_win.exe (PID: 3836)
- javaw.exe (PID: 7016)
Checks proxy server information
- 03a236d2edf54ccc11d7adec65dd02c3ee4d7dff6226ceb83c5b9be4472939f3.exe (PID: 6480)
- BackgroundTransferHost.exe (PID: 4416)
- slui.exe (PID: 2388)
Reads the computer name
- 03a236d2edf54ccc11d7adec65dd02c3ee4d7dff6226ceb83c5b9be4472939f3.exe (PID: 6480)
- Remote Support.exe (PID: 5828)
- elev_win.exe (PID: 6488)
- SimpleService.exe (PID: 3936)
- SimpleService.exe (PID: 4976)
- SimpleService.exe (PID: 3652)
- session_win.exe (PID: 6496)
- elev_win.exe (PID: 3836)
Creates files or folders in the user directory
- 03a236d2edf54ccc11d7adec65dd02c3ee4d7dff6226ceb83c5b9be4472939f3.exe (PID: 6480)
- lzma.exe (PID: 7024)
- lzma.exe (PID: 5116)
- unpack200.exe (PID: 7156)
- unpack200.exe (PID: 5904)
- unpack200.exe (PID: 7052)
- javaw.exe (PID: 7048)
- Remote SupportECompatibility.exe (PID: 1688)
- BackgroundTransferHost.exe (PID: 4416)
- Remote Support.exe (PID: 5828)
Create files in a temporary directory
- javaw.exe (PID: 7048)
- Remote SupportECompatibility.exe (PID: 1688)
- 03a236d2edf54ccc11d7adec65dd02c3ee4d7dff6226ceb83c5b9be4472939f3.exe (PID: 6480)
- Remote Support.exe (PID: 5828)
Reads the time zone
- 03a236d2edf54ccc11d7adec65dd02c3ee4d7dff6226ceb83c5b9be4472939f3.exe (PID: 6480)
- Remote SupportECompatibility.exe (PID: 1688)
- Remote Support.exe (PID: 5828)
- javaw.exe (PID: 3100)
- javaw.exe (PID: 7016)
Reads the machine GUID from the registry
- 03a236d2edf54ccc11d7adec65dd02c3ee4d7dff6226ceb83c5b9be4472939f3.exe (PID: 6480)
- Remote Support.exe (PID: 5828)
Reads security settings of Internet Explorer
- BackgroundTransferHost.exe (PID: 6068)
- BackgroundTransferHost.exe (PID: 6148)
- BackgroundTransferHost.exe (PID: 4416)
- BackgroundTransferHost.exe (PID: 4720)
- BackgroundTransferHost.exe (PID: 6180)
Reads the software policy settings
- BackgroundTransferHost.exe (PID: 4416)
- slui.exe (PID: 2388)
Creates files in the program directory
- Remote Support.exe (PID: 5828)
Process checks computer location settings
- elev_win.exe (PID: 6488)
- elev_win.exe (PID: 3836)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2014:11:19 16:00:00+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 176128 |
| InitializedDataSize: | 98304 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1ba88 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
177
Monitored processes
47
Malicious processes
2
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 900 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cacls.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1068 | cacls "C:\Users\admin\AppData\Roaming\JWrapper-Remote Support\JWrapper-Windows32JRE-00028603591-complete\jwLastRun" /t /e /g "Users":F | C:\Windows\SysWOW64\cacls.exe | — | 03a236d2edf54ccc11d7adec65dd02c3ee4d7dff6226ceb83c5b9be4472939f3.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Control ACLs Program Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1080 | cacls "C:\Users\admin\AppData\Roaming\JWrapper-Remote Support\JWAppsSharedConfig\DetectedProxies" /t /e /g "Users":F | C:\Windows\SysWOW64\cacls.exe | — | 03a236d2edf54ccc11d7adec65dd02c3ee4d7dff6226ceb83c5b9be4472939f3.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Control ACLs Program Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1080 | cacls "C:\ProgramData\SimpleHelp\ElevateSH\*.*" /t /e /g "Users":f | C:\Windows\SysWOW64\cacls.exe | — | Remote Support.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Control ACLs Program Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1092 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cacls.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1496 | cacls "C:\Users\admin\AppData\Roaming\JWrapper-Remote Support\JWAppsSharedConfig\ProxyCredentials" /t /e /g "Users":F | C:\Windows\SysWOW64\cacls.exe | — | 03a236d2edf54ccc11d7adec65dd02c3ee4d7dff6226ceb83c5b9be4472939f3.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Control ACLs Program Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1688 | "C:\Users\admin\AppData\Roaming\JWrapper-Remote Support\JWrapper-Windows32JRE-00028603591-complete\bin\Remote SupportECompatibility.exe" -cp "C:\Users\admin\AppData\Roaming\JWrapper-Remote Support\JWrapperTemp-1711851841698-5\customer.jar;C:\Users\admin\AppData\Roaming\JWrapper-Remote Support\JWrapperTemp-1711851841698-5\liquidlnf.jar;C:\Users\admin\AppData\Roaming\JWrapper-Remote Support\JWrapperTemp-1711851841698-5\sevenzip.jar;C:\Users\admin\AppData\Roaming\JWrapper-Remote Support\JWrapperTemp-1711851841698-5\jwrapper_utils.jar;" -Xmx256m -XX:MinHeapFreeRatio=15 -XX:MaxHeapFreeRatio=30 -Djava.util.Arrays.useLegacyMergeSort=true -Djava.net.preferIPv4Stack=true -Dsun.java2d.dpiaware=true jwrapper.JWrapper "C:\Users\admin\AppData\Roaming\JWrapper-Remote Support\JWrapperTemp-1711851841698-5\JWLaunchProperties-1711851851901-41" | C:\Users\admin\AppData\Roaming\JWrapper-Remote Support\JWrapper-Windows32JRE-00028603591-complete\bin\Remote SupportECompatibility.exe | — | 03a236d2edf54ccc11d7adec65dd02c3ee4d7dff6226ceb83c5b9be4472939f3.exe | |||||||||||
User: admin Company: Sun Microsystems, Inc. Integrity Level: MEDIUM Description: Java(TM) 2 Platform Standard Edition binary Exit code: 72 Version: 5.0.220.3 Modules
| |||||||||||||||
| 2012 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cacls.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2388 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3100 | "C:\Users\admin\AppData\Roaming\JWrapper-Remote Support\JWrapper-Windows32JRE-00028603591-complete\bin\javaw.exe" "-cp" "C:\Users\admin\AppData\Roaming\JWrapper-Remote Support\JWrapper-Remote Support-00032144476-complete\customer.jar;C:\Users\admin\AppData\Roaming\JWrapper-Remote Support\JWrapper-Remote Support-00032144476-complete\liquidlnf.jar;C:\Users\admin\AppData\Roaming\JWrapper-Remote Support\JWrapper-Remote Support-00032144476-complete\sevenzip.jar;C:\Users\admin\AppData\Roaming\JWrapper-Remote Support\JWrapper-Remote Support-00032144476-complete\jwrapper_utils.jar;" "-Dsun.java2d.dpiaware=false" "-Djava.library.path=C:\Users\admin\AppData\Roaming\JWrapper-Remote Support\JWrapper-Remote Support-00032144476-complete" "com.aem.sdesktop.util.MouseMover" "127.0.0.1" "49764" "127.0.0.1" "49765" "elevated" | C:\Users\admin\AppData\Roaming\JWrapper-Remote Support\JWrapper-Windows32JRE-00028603591-complete\bin\javaw.exe | — | session_win.exe | |||||||||||
User: SYSTEM Company: Sun Microsystems, Inc. Integrity Level: SYSTEM Description: Java(TM) 2 Platform Standard Edition binary Version: 5.0.220.3 Modules
| |||||||||||||||
Total events
12 041
Read events
11 992
Write events
47
Delete events
2
Modification events
| (PID) Process: | (6480) 03a236d2edf54ccc11d7adec65dd02c3ee4d7dff6226ceb83c5b9be4472939f3.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (6480) 03a236d2edf54ccc11d7adec65dd02c3ee4d7dff6226ceb83c5b9be4472939f3.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (6480) 03a236d2edf54ccc11d7adec65dd02c3ee4d7dff6226ceb83c5b9be4472939f3.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (6480) 03a236d2edf54ccc11d7adec65dd02c3ee4d7dff6226ceb83c5b9be4472939f3.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (6480) 03a236d2edf54ccc11d7adec65dd02c3ee4d7dff6226ceb83c5b9be4472939f3.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (6480) 03a236d2edf54ccc11d7adec65dd02c3ee4d7dff6226ceb83c5b9be4472939f3.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (6480) 03a236d2edf54ccc11d7adec65dd02c3ee4d7dff6226ceb83c5b9be4472939f3.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (6068) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (6068) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (6068) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
Executable files
66
Suspicious files
35
Text files
90
Unknown types
492
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6480 | 03a236d2edf54ccc11d7adec65dd02c3ee4d7dff6226ceb83c5b9be4472939f3.exe | C:\Users\admin\AppData\Roaming\JWrapper-Remote Support\JWrapperTemp-1711851824-0-app\lzma.exe | executable | |
MD5:— | SHA256:— | |||
| 6480 | 03a236d2edf54ccc11d7adec65dd02c3ee4d7dff6226ceb83c5b9be4472939f3.exe | C:\Users\admin\AppData\Roaming\JWrapper-Remote Support\JWrapperTemp-1711851824-0-app\nativesplash.png | image | |
MD5:— | SHA256:— | |||
| 6480 | 03a236d2edf54ccc11d7adec65dd02c3ee4d7dff6226ceb83c5b9be4472939f3.exe | C:\Users\admin\AppData\Roaming\JWrapper-Remote Support\JWrapperTemp-1711851824-0-app\JWrapper-JWrapper-00032144438-archive.p2.l2 | binary | |
MD5:— | SHA256:— | |||
| 7024 | lzma.exe | C:\Users\admin\AppData\Roaming\JWrapper-Remote Support\JWrapperTemp-1711851824-0-app\JWrapper-JWrapper-00032144438-archive.p2 | binary | |
MD5:— | SHA256:— | |||
| 6480 | 03a236d2edf54ccc11d7adec65dd02c3ee4d7dff6226ceb83c5b9be4472939f3.exe | C:\Users\admin\AppData\Roaming\JWrapper-Remote Support\JWrapperTemp-1711851824-0-app\jwrapperlib\jwstandalonelaunch.jar | java | |
MD5:— | SHA256:— | |||
| 6480 | 03a236d2edf54ccc11d7adec65dd02c3ee4d7dff6226ceb83c5b9be4472939f3.exe | C:\Users\admin\AppData\Roaming\JWrapper-Remote Support\JWrapperTemp-1711851824-0-app\jwrapperlib\jwstandalone.jar | java | |
MD5:— | SHA256:— | |||
| 6480 | 03a236d2edf54ccc11d7adec65dd02c3ee4d7dff6226ceb83c5b9be4472939f3.exe | C:\Users\admin\AppData\Roaming\JWrapper-Remote Support\JWrapperTemp-1711851824-0-app\jwrapperlib\sevenzip.jar | java | |
MD5:— | SHA256:— | |||
| 6480 | 03a236d2edf54ccc11d7adec65dd02c3ee4d7dff6226ceb83c5b9be4472939f3.exe | C:\Users\admin\AppData\Roaming\JWrapper-Remote Support\JWrapperTemp-1711851824-0-app\JWrapper-Remote Support-splash.png | image | |
MD5:— | SHA256:— | |||
| 6480 | 03a236d2edf54ccc11d7adec65dd02c3ee4d7dff6226ceb83c5b9be4472939f3.exe | C:\Users\admin\AppData\Roaming\JWrapper-Remote Support\JWrapperTemp-1711851824-0-app\JWrapper-Remote Support-ICNS.icns | binary | |
MD5:— | SHA256:— | |||
| 6480 | 03a236d2edf54ccc11d7adec65dd02c3ee4d7dff6226ceb83c5b9be4472939f3.exe | C:\Users\admin\AppData\Roaming\JWrapper-Remote Support\JWrapperTemp-1711851824-0-app\jwutils_win32.dll | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
22
TCP/UDP connections
55
DNS requests
12
Threats
15
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6480 | 03a236d2edf54ccc11d7adec65dd02c3ee4d7dff6226ceb83c5b9be4472939f3.exe | GET | — | 54.243.180.93:80 | http://help.supportinthecloud.com/customer/JWrapper-Windows32JRE-00028603591-archive.p2.l2 | unknown | — | — | unknown |
6480 | 03a236d2edf54ccc11d7adec65dd02c3ee4d7dff6226ceb83c5b9be4472939f3.exe | GET | 200 | 54.243.180.93:80 | http://help.supportinthecloud.com/customer/JWrapper-Windows32JRE-version.txt | unknown | — | — | unknown |
6480 | 03a236d2edf54ccc11d7adec65dd02c3ee4d7dff6226ceb83c5b9be4472939f3.exe | GET | 200 | 54.243.180.93:80 | http://help.supportinthecloud.com/customer/JWrapper-Windows32JRE-version.txt | unknown | — | — | unknown |
6480 | 03a236d2edf54ccc11d7adec65dd02c3ee4d7dff6226ceb83c5b9be4472939f3.exe | GET | — | 54.243.180.93:80 | http://help.supportinthecloud.com/customer/JWrapper-Windows32JRE-00028603591-archive.p2.l2 | unknown | — | — | unknown |
6480 | 03a236d2edf54ccc11d7adec65dd02c3ee4d7dff6226ceb83c5b9be4472939f3.exe | GET | 200 | 54.243.180.93:80 | http://help.supportinthecloud.com/customer/JWrapper-Windows32JRE-version.txt | unknown | — | — | unknown |
6480 | 03a236d2edf54ccc11d7adec65dd02c3ee4d7dff6226ceb83c5b9be4472939f3.exe | GET | 200 | 54.243.180.93:80 | http://help.supportinthecloud.com/customer/JWrapper-Windows32JRE-00028603591-archive.p2.l2 | unknown | — | — | unknown |
6480 | 03a236d2edf54ccc11d7adec65dd02c3ee4d7dff6226ceb83c5b9be4472939f3.exe | GET | 200 | 54.243.180.93:80 | http://help.supportinthecloud.com/customer/JWrapper-Remote%20Support-version.txt | unknown | — | — | unknown |
6480 | 03a236d2edf54ccc11d7adec65dd02c3ee4d7dff6226ceb83c5b9be4472939f3.exe | GET | 200 | 54.243.180.93:80 | http://help.supportinthecloud.com/customer/JWrapper-Remote%20Support-version.txt | unknown | — | — | unknown |
6480 | 03a236d2edf54ccc11d7adec65dd02c3ee4d7dff6226ceb83c5b9be4472939f3.exe | GET | 200 | 54.243.180.93:80 | http://help.supportinthecloud.com/customer/JWrapper-Remote%20Support-00032144476-archive.p2.l2 | unknown | — | — | unknown |
3996 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4828 | svchost.exe | 239.255.255.250:1900 | — | — | — | unknown |
3808 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
1280 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
3996 | svchost.exe | 20.190.159.23:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
6480 | 03a236d2edf54ccc11d7adec65dd02c3ee4d7dff6226ceb83c5b9be4472939f3.exe | 54.243.180.93:80 | help.supportinthecloud.com | AMAZON-AES | US | unknown |
3996 | svchost.exe | 20.190.159.71:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3996 | svchost.exe | 192.229.221.95:80 | — | EDGECAST | US | whitelisted |
1740 | SIHClient.exe | 40.127.169.103:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
1740 | SIHClient.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | unknown |
1740 | SIHClient.exe | 13.95.31.18:443 | fe3cr.delivery.mp.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
help.supportinthecloud.com |
| unknown |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
www.bing.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6480 | 03a236d2edf54ccc11d7adec65dd02c3ee4d7dff6226ceb83c5b9be4472939f3.exe | Potentially Bad Traffic | ET USER_AGENTS Observed Suspicious User-Agent (JWrapperDownloader) |
6480 | 03a236d2edf54ccc11d7adec65dd02c3ee4d7dff6226ceb83c5b9be4472939f3.exe | Potentially Bad Traffic | ET USER_AGENTS Observed Suspicious User-Agent (JWrapperDownloader) |
6480 | 03a236d2edf54ccc11d7adec65dd02c3ee4d7dff6226ceb83c5b9be4472939f3.exe | Misc activity | ET INFO Simplehelp Remote Administration Suite HTTP Server Value in Response |
6480 | 03a236d2edf54ccc11d7adec65dd02c3ee4d7dff6226ceb83c5b9be4472939f3.exe | Potentially Bad Traffic | ET USER_AGENTS Observed Suspicious User-Agent (JWrapperDownloader) |
6480 | 03a236d2edf54ccc11d7adec65dd02c3ee4d7dff6226ceb83c5b9be4472939f3.exe | Potentially Bad Traffic | ET USER_AGENTS Observed Suspicious User-Agent (JWrapperDownloader) |
6480 | 03a236d2edf54ccc11d7adec65dd02c3ee4d7dff6226ceb83c5b9be4472939f3.exe | Potentially Bad Traffic | ET USER_AGENTS Observed Suspicious User-Agent (JWrapperDownloader) |
6480 | 03a236d2edf54ccc11d7adec65dd02c3ee4d7dff6226ceb83c5b9be4472939f3.exe | Potentially Bad Traffic | ET USER_AGENTS Observed Suspicious User-Agent (JWrapperDownloader) |
— | — | Potentially Bad Traffic | ET POLICY Vulnerable Java Version 1.5.x Detected |
— | — | Potentially Bad Traffic | ET POLICY Vulnerable Java Version 1.5.x Detected |
6 ETPRO signatures available at the full report