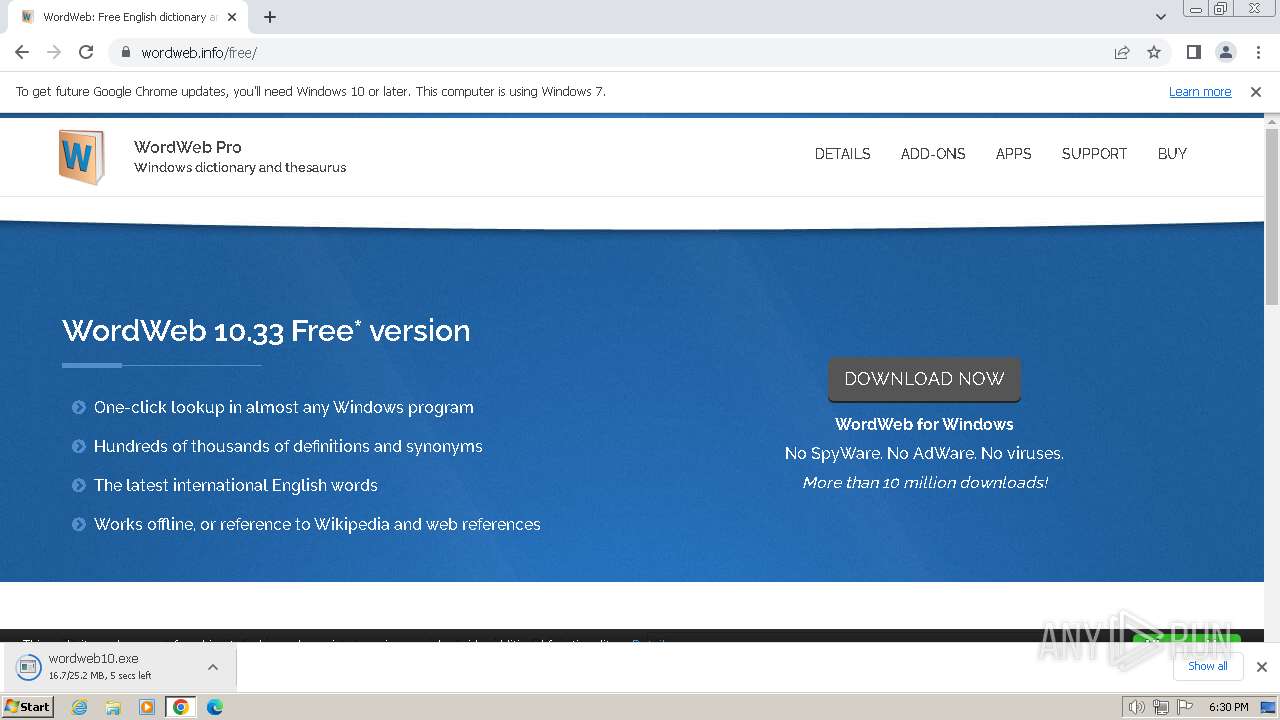
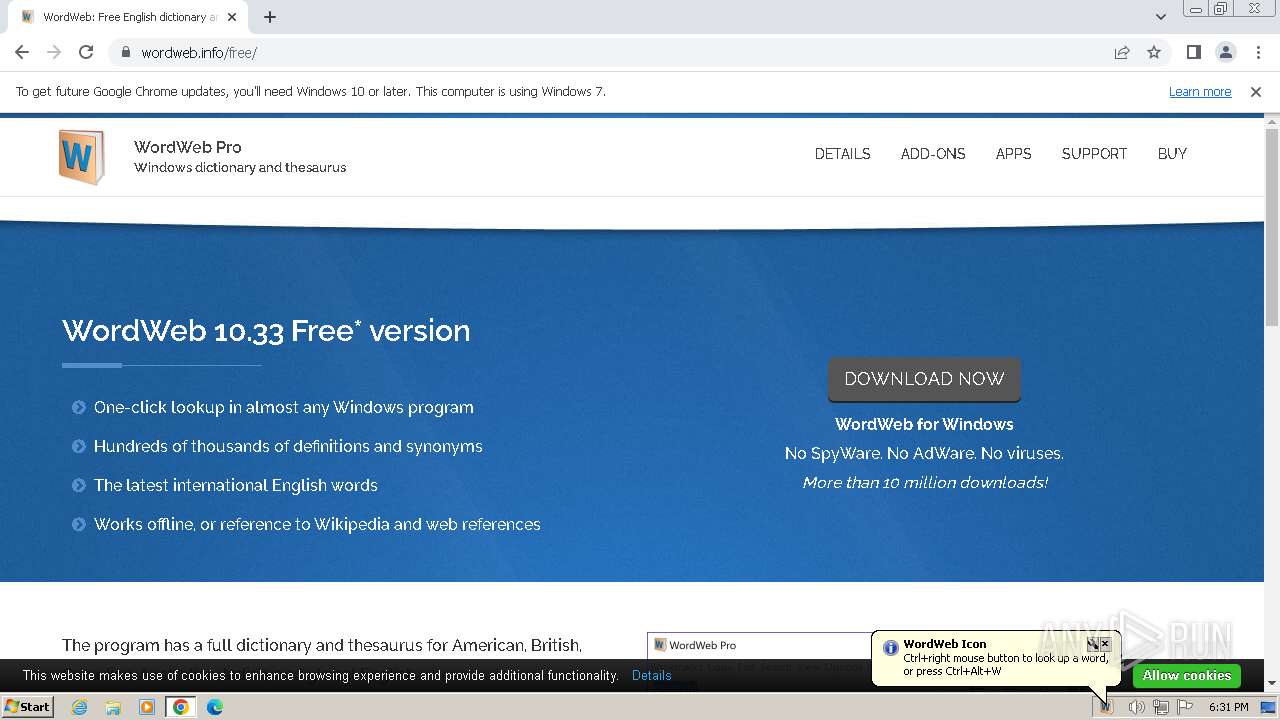
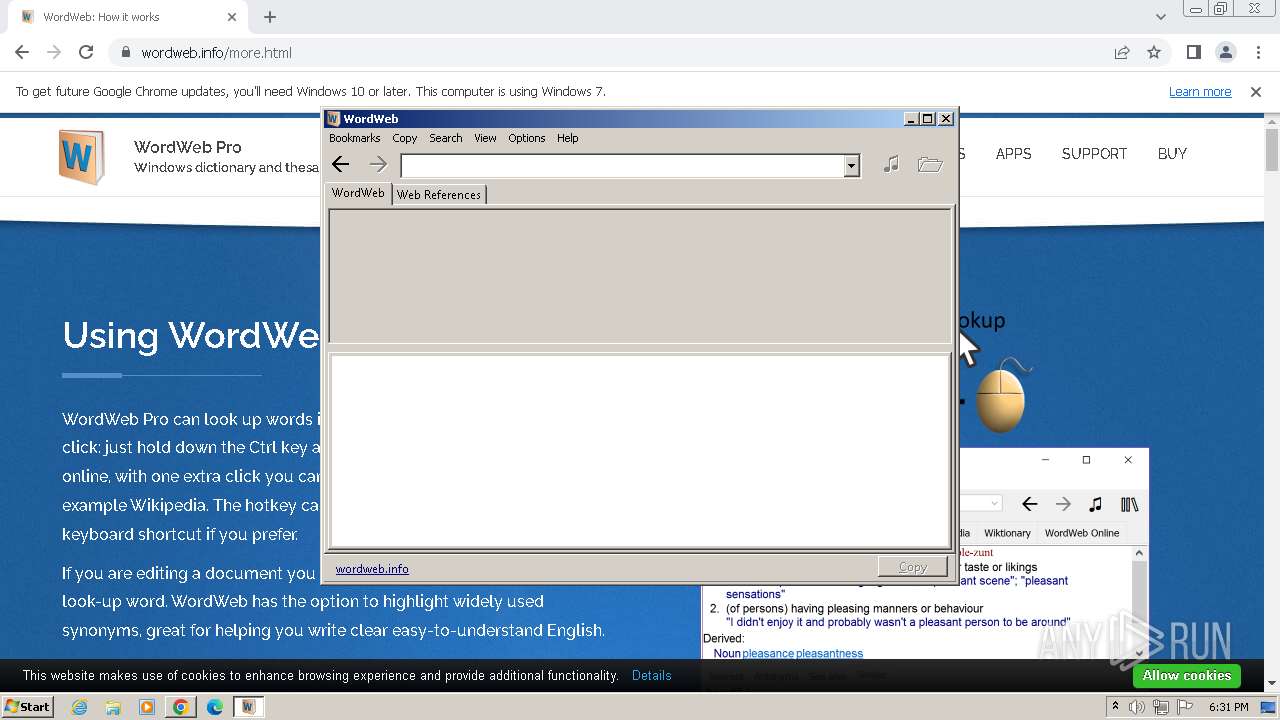
| URL: | https://wordweb.info/ |
| Full analysis: | https://app.any.run/tasks/1a97cd4e-dcd7-41bb-88bf-971a8320f088 |
| Verdict: | Malicious activity |
| Analysis date: | February 06, 2024, 18:30:24 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 1D03C4CCB883B5318A60AA66FAF92C55 |
| SHA1: | 16CB9B30B18C02040298B70C8D241DA39C98F6BA |
| SHA256: | 0390BEDBEBDBDB2AF0CCC9CD8D880BB8685898910D07B0196DBBD2571472C7D4 |
| SSDEEP: | 3:N8bXBrLMhn:2pK |
MALICIOUS
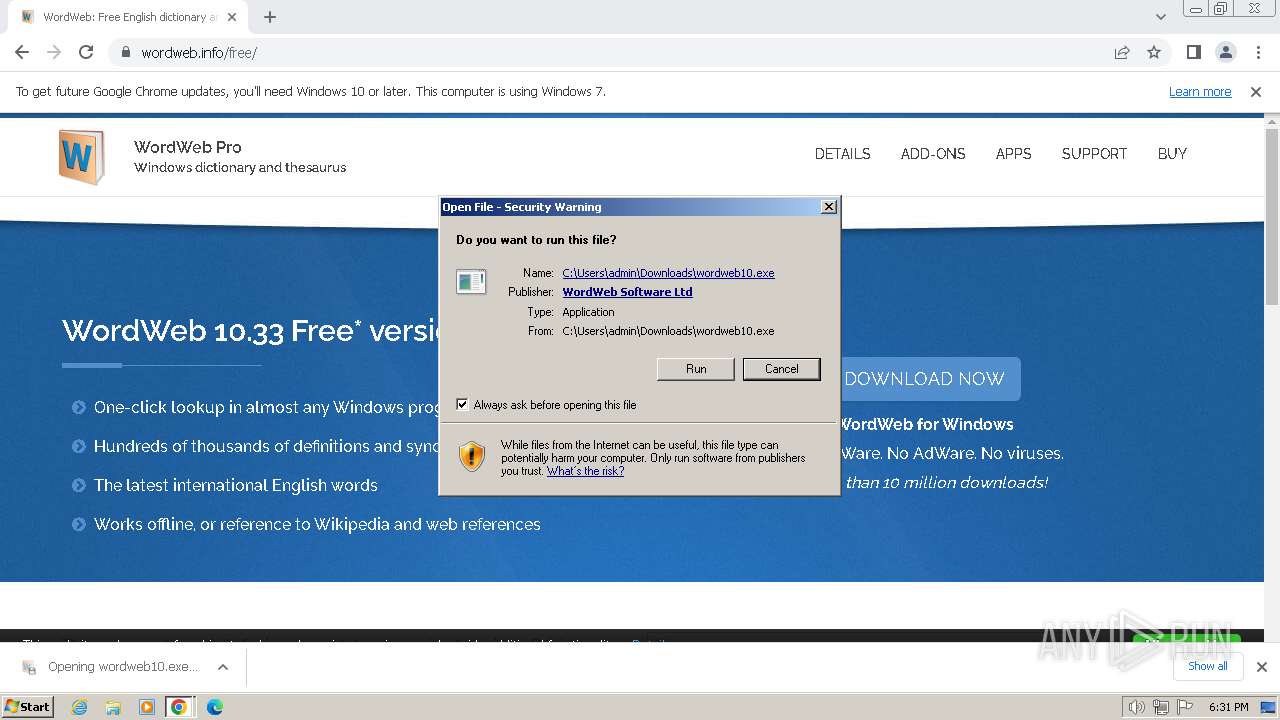
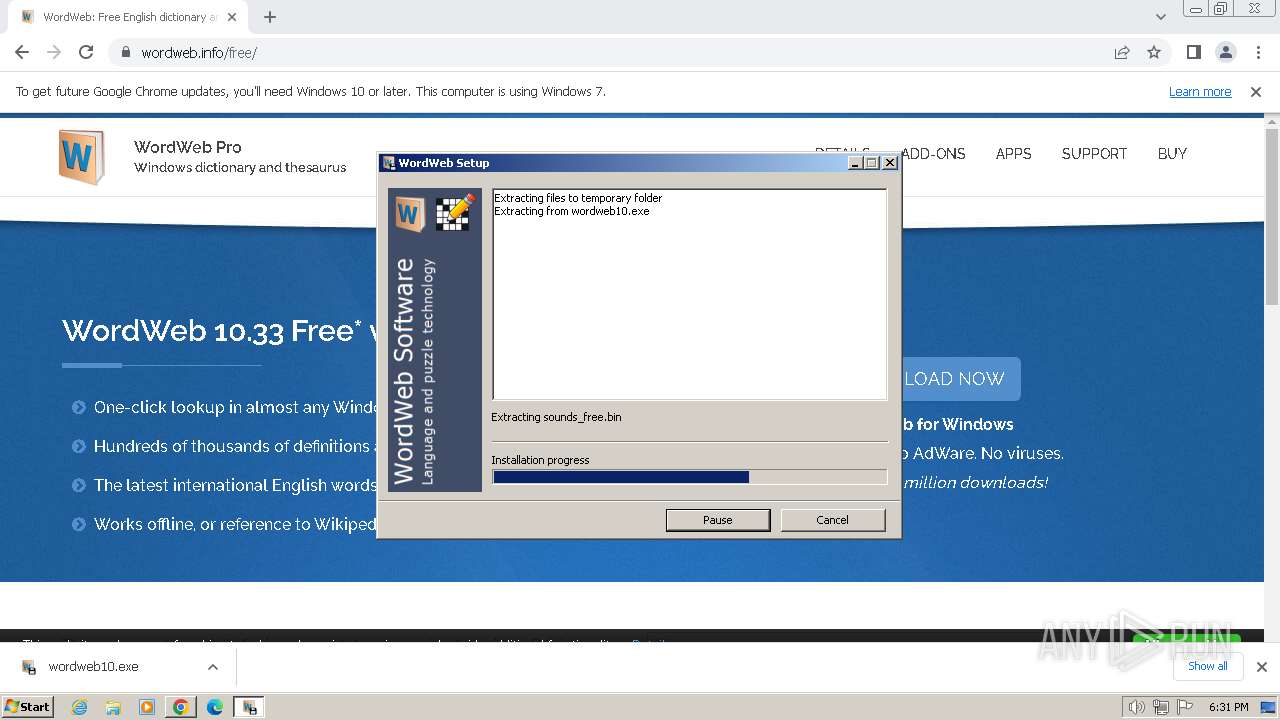
Drops the executable file immediately after the start
- wordweb10.exe (PID: 3304)
- uninst.exe (PID: 2064)
Creates a writable file in the system directory
- uninst.exe (PID: 2064)
Registers / Runs the DLL via REGSVR32.EXE
- uninst.exe (PID: 2064)
SUSPICIOUS
Process drops legitimate windows executable
- wordweb10.exe (PID: 3304)
- uninst.exe (PID: 2064)
Executable content was dropped or overwritten
- wordweb10.exe (PID: 3304)
- uninst.exe (PID: 2064)
Reads Internet Explorer settings
- wordweb10.exe (PID: 3304)
Reads Microsoft Outlook installation path
- wordweb10.exe (PID: 3304)
Reads the Internet Settings
- wordweb10.exe (PID: 3304)
- uninst.exe (PID: 2064)
Uses RUNDLL32.EXE to load library
- uninst.exe (PID: 2064)
INFO
Creates files in the program directory
- uninst.exe (PID: 2064)
Checks supported languages
- uninst.exe (PID: 2064)
- wordweb10.exe (PID: 3304)
- wweb32.exe (PID: 748)
- wweb32.exe (PID: 2900)
Create files in a temporary directory
- wordweb10.exe (PID: 3304)
Reads the machine GUID from the registry
- wordweb10.exe (PID: 3304)
Checks proxy server information
- wordweb10.exe (PID: 3304)
Drops the executable file immediately after the start
- chrome.exe (PID: 1588)
Reads the computer name
- wordweb10.exe (PID: 3304)
- uninst.exe (PID: 2064)
- wweb32.exe (PID: 748)
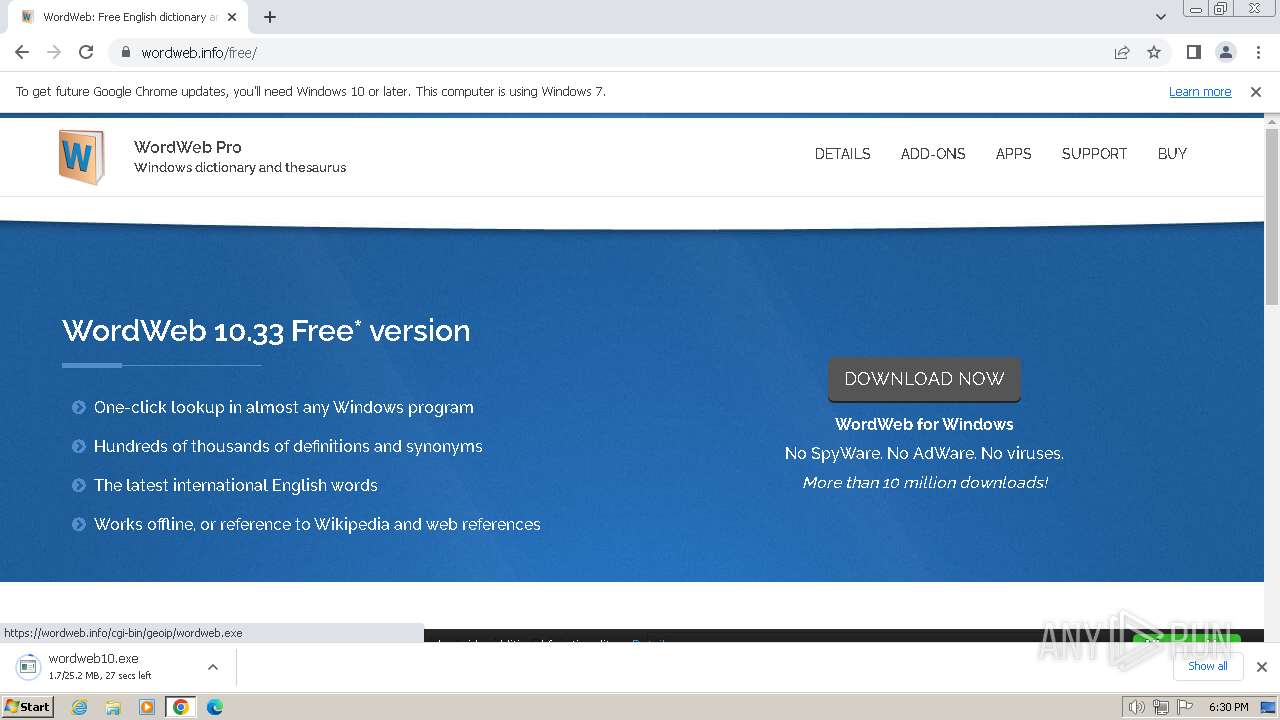
The process uses the downloaded file
- chrome.exe (PID: 1588)
- chrome.exe (PID: 1384)
Executable content was dropped or overwritten
- chrome.exe (PID: 1588)
Application launched itself
- chrome.exe (PID: 1588)
Creates files or folders in the user directory
- uninst.exe (PID: 2064)
Manual execution by a user
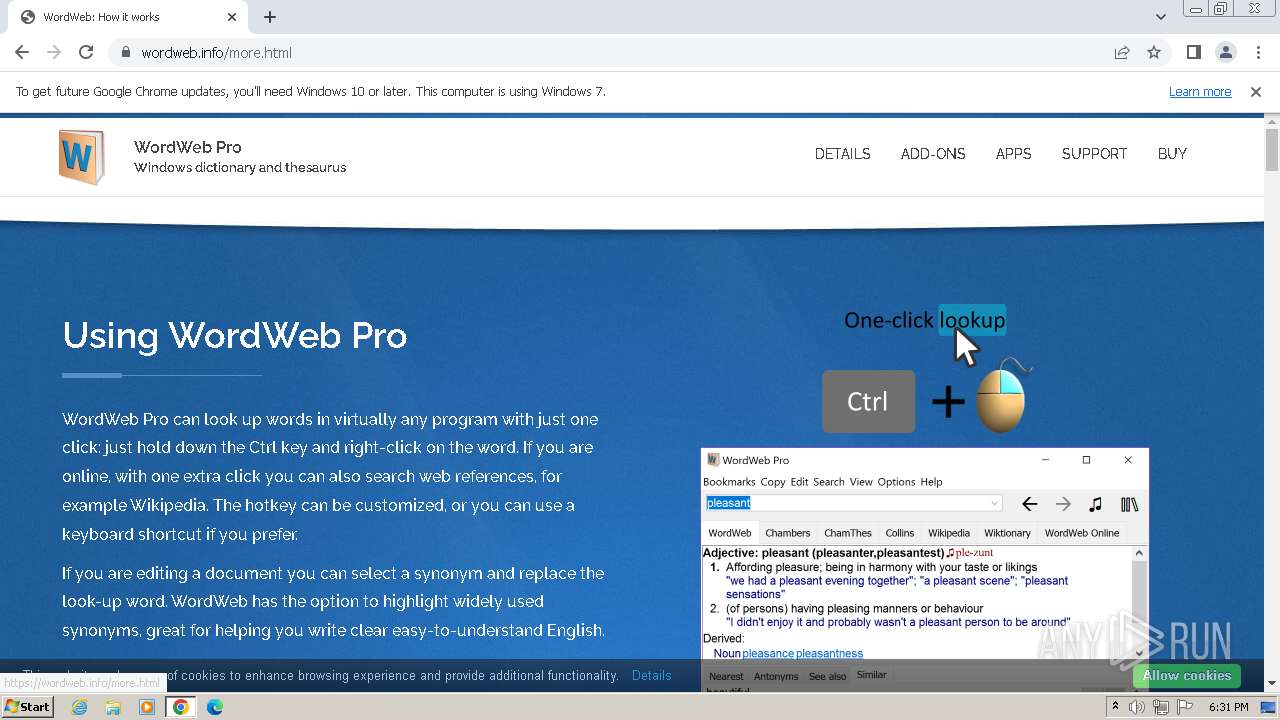
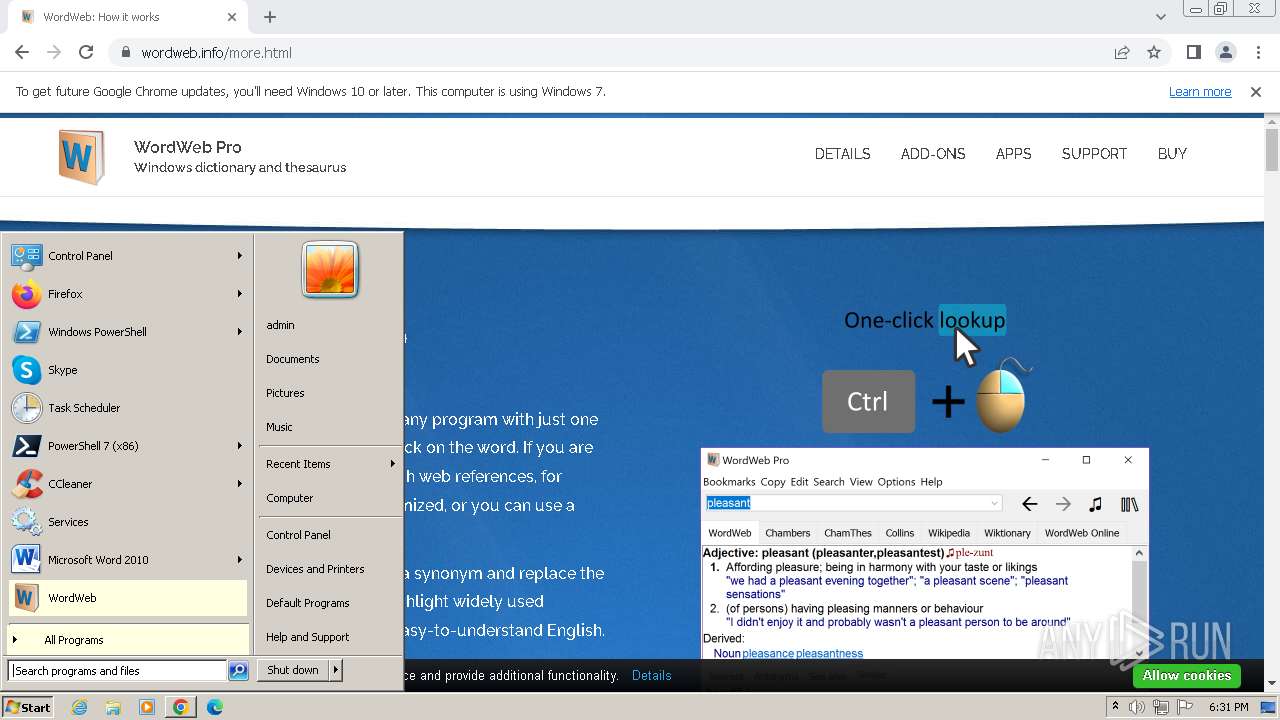
- wweb32.exe (PID: 748)
- wweb32.exe (PID: 2900)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
62
Monitored processes
23
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 748 | "C:\Program Files\WordWeb\wweb32.exe" | C:\Program Files\WordWeb\wweb32.exe | — | explorer.exe | |||||||||||
User: admin Company: WordWeb Software Integrity Level: MEDIUM Description: WordWeb Exit code: 0 Version: 10.3.0.0 Modules
| |||||||||||||||
| 1192 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --disable-quic --mojo-platform-channel-handle=3532 --field-trial-handle=1136,i,16372864791119195356,4949845391601437434,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1384 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=3844 --field-trial-handle=1136,i,16372864791119195356,4949845391601437434,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1588 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking --disable-features=OptimizationGuideModelDownloading,OptimizationHintsFetching,OptimizationTargetPrediction,OptimizationHints "https://wordweb.info/" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1812 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=3232 --field-trial-handle=1136,i,16372864791119195356,4949845391601437434,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1976 | RunDll32.exe "C:\Program Files\WordWeb\VistaLib32.dll",RunNonElevated "C:\Program Files\WordWeb\wweb32.exe" | C:\Windows\System32\rundll32.exe | — | uninst.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
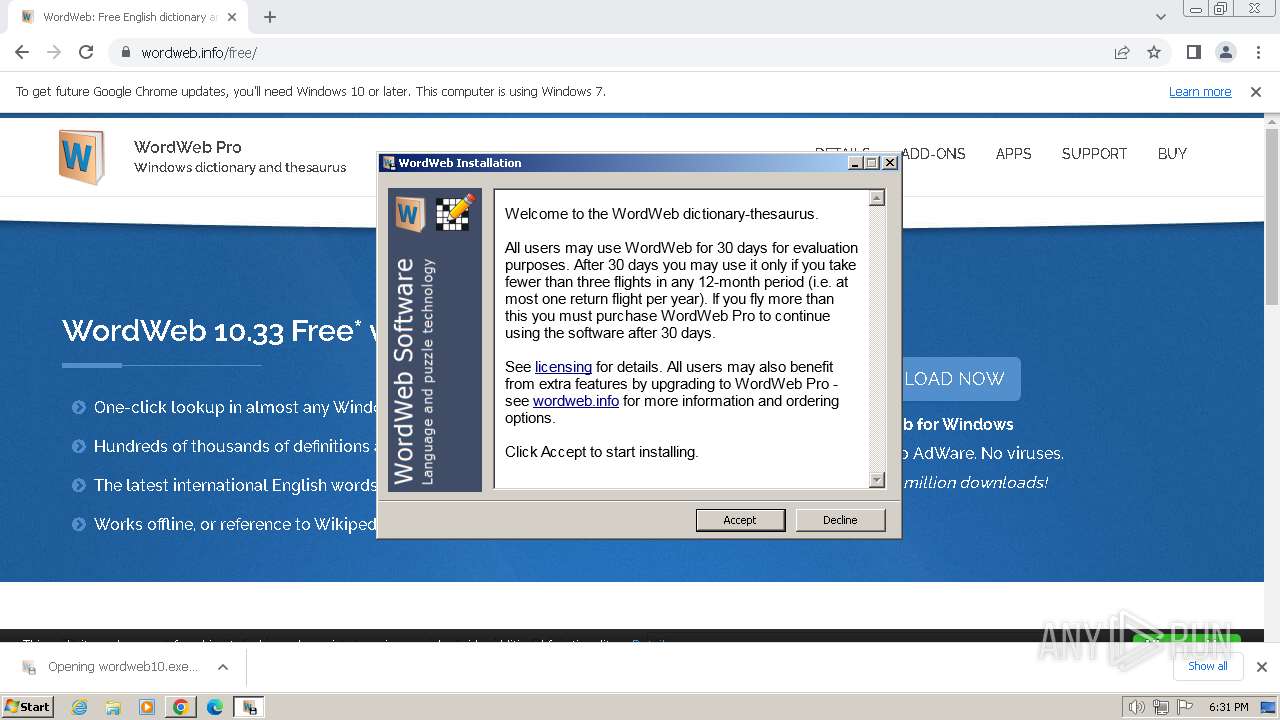
| 2064 | "C:\Users\admin\AppData\Local\Temp\RarSFX0\uninst.exe" -i | C:\Users\admin\AppData\Local\Temp\RarSFX0\uninst.exe | wordweb10.exe | ||||||||||||
User: admin Company: Antony Lewis Integrity Level: HIGH Description: WordWeb thesaurus/dictionary install program Exit code: 0 Version: 8.0.0.0 Modules
| |||||||||||||||
| 2508 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=1496 --field-trial-handle=1136,i,16372864791119195356,4949845391601437434,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2524 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --disable-quic --mojo-platform-channel-handle=3648 --field-trial-handle=1136,i,16372864791119195356,4949845391601437434,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2572 | "C:\Users\admin\AppData\Local\Temp\RarSFX0\uninst.exe" -i | C:\Users\admin\AppData\Local\Temp\RarSFX0\uninst.exe | — | wordweb10.exe | |||||||||||
User: admin Company: Antony Lewis Integrity Level: MEDIUM Description: WordWeb thesaurus/dictionary install program Exit code: 3221226540 Version: 8.0.0.0 Modules
| |||||||||||||||
Total events
7 948
Read events
7 840
Write events
107
Delete events
1
Modification events
| (PID) Process: | (1588) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1588) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1588) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1588) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1588) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1588) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 1 | |||
| (PID) Process: | (1588) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1588) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (1588) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
| (PID) Process: | (1588) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_enableddate |
Value: 0 | |||
Executable files
58
Suspicious files
40
Text files
24
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1588 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF1636b4.TMP | — | |
MD5:— | SHA256:— | |||
| 1588 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1588 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 1588 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Variations | binary | |
MD5:961E3604F228B0D10541EBF921500C86 | SHA256:F7B24F2EB3D5EB0550527490395D2F61C3D2FE74BB9CB345197DAD81B58B5FED | |||
| 1588 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF1636b4.TMP | text | |
MD5:05CF4C3C5148DA6355D3561A9EAA5E8A | SHA256:8D720243F6876898E4F197C8867C4CEE69F1C7335C55B8A29C120B1028D93E41 | |||
| 1588 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:ECD3386BCC950E73B86EB128A5F57622 | SHA256:C9A068EAFBC587EDFC89392F64DDD350EEB96C5CF195CDB030BAB8F6DD33833B | |||
| 1588 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF163d8a.TMP | — | |
MD5:— | SHA256:— | |||
| 1588 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1588 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF1636b4.TMP | text | |
MD5:ADB669AB4CD1C63883C64FB0DBA2C7DA | SHA256:18BFF89047EC5B122573D089B3DC7A7DD14A5A7A515B2D8141584B41E723253F | |||
| 1588 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\AutofillStrikeDatabase\LOG.old~RF164a1d.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
33
DNS requests
34
Threats
3
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1588 | chrome.exe | 239.255.255.250:1900 | — | — | — | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3244 | chrome.exe | 66.102.1.84:443 | accounts.google.com | GOOGLE | US | unknown |
3244 | chrome.exe | 66.39.137.29:443 | wordweb.info | PAIR-NETWORKS | US | unknown |
3244 | chrome.exe | 104.18.10.207:443 | maxcdn.bootstrapcdn.com | CLOUDFLARENET | — | unknown |
3244 | chrome.exe | 142.250.184.234:443 | fonts.googleapis.com | GOOGLE | US | whitelisted |
3244 | chrome.exe | 151.101.2.137:443 | code.jquery.com | FASTLY | US | unknown |
3244 | chrome.exe | 172.64.206.38:443 | use.fontawesome.com | CLOUDFLARENET | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
wordweb.info |
| whitelisted |
maxcdn.bootstrapcdn.com |
| whitelisted |
uk.wordwebsoftware.com |
| unknown |
fonts.googleapis.com |
| whitelisted |
code.jquery.com |
| whitelisted |
use.fontawesome.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
cdn.jsdelivr.net |
| whitelisted |
www.crossword-compiler.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3244 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code.jquery .com) |
3244 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] A free CDN for open source projects (jsdelivr .net) |
3244 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] A free CDN for open source projects (jsdelivr .net) |