| File name: | 03.exe.exe |
| Full analysis: | https://app.any.run/tasks/2b1f895e-0e69-4e28-af5c-ce414e4df3bc |
| Verdict: | Malicious activity |
| Analysis date: | May 11, 2025, 02:27:27 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 4 sections |
| MD5: | EF9AA4D03A69E69BBC44867F8436001D |
| SHA1: | 57DB1F7070D71B752C4A8457D53908752A6C23C6 |
| SHA256: | 0379D402A94F960380D7D91E3BFA106EEAC01CD39AE7B0BA5010BA737088A215 |
| SSDEEP: | 6144:A/TLLtKUmyP+3hZzbmQA/3fVf8lYImAvxJkNdxAQk:AbtmyG3hpbmQA/tklYXNbg |
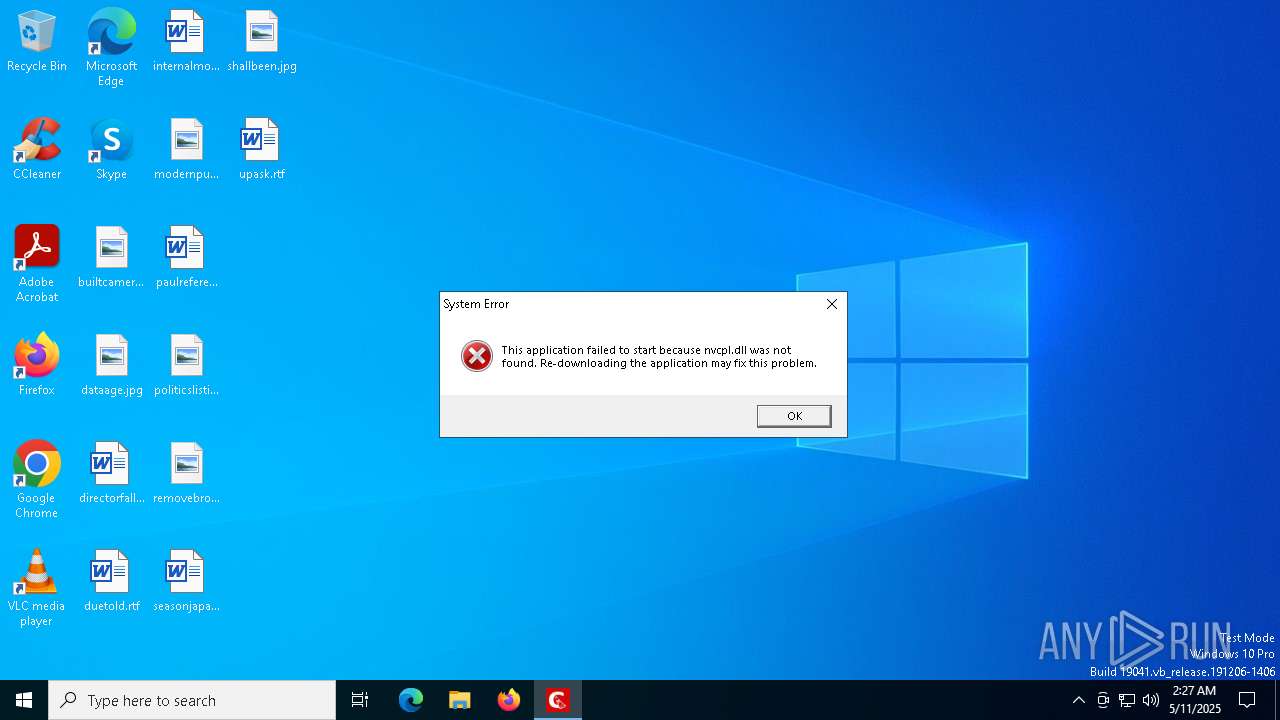
MALICIOUS
ONLYLOGGER has been detected (YARA)
- 03.exe.exe (PID: 7220)
SUSPICIOUS
Executes application which crashes
- 03.exe.exe (PID: 7220)
Reads security settings of Internet Explorer
- 03.exe.exe (PID: 7220)
INFO
Creates files or folders in the user directory
- WerFault.exe (PID: 7528)
- WerFault.exe (PID: 7832)
- WerFault.exe (PID: 7696)
- WerFault.exe (PID: 7904)
- WerFault.exe (PID: 7976)
- WerFault.exe (PID: 8068)
- WerFault.exe (PID: 8144)
- WerFault.exe (PID: 4428)
- WerFault.exe (PID: 7036)
- WerFault.exe (PID: 4988)
Checks supported languages
- 03.exe.exe (PID: 7220)
Reads the computer name
- 03.exe.exe (PID: 7220)
Checks proxy server information
- 03.exe.exe (PID: 7220)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (72.3) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (11.8) |
| .exe | | | Clipper DOS Executable (5.2) |
| .exe | | | Generic Win/DOS Executable (5.2) |
| .exe | | | DOS Executable Generic (5.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:09:07 06:03:30+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 181248 |
| InitializedDataSize: | 42273792 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1fcd6 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 85.0.0.0 |
| ProductVersionNumber: | 40.0.0.0 |
| FileFlagsMask: | 0x005f |
| FileFlags: | Private build |
| FileOS: | Unknown (0x40324) |
| ObjectFileType: | Static library |
| FileSubtype: | 86 |
Total processes
155
Monitored processes
13
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4428 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 7220 -s 1276 | C:\Windows\SysWOW64\WerFault.exe | — | 03.exe.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4988 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 7220 -s 1912 | C:\Windows\SysWOW64\WerFault.exe | — | 03.exe.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7036 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 7220 -s 920 | C:\Windows\SysWOW64\WerFault.exe | — | 03.exe.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7220 | "C:\Users\admin\AppData\Local\Temp\03.exe.exe" | C:\Users\admin\AppData\Local\Temp\03.exe.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 7420 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7528 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 7220 -s 500 | C:\Windows\SysWOW64\WerFault.exe | — | 03.exe.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7696 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 7220 -s 548 | C:\Windows\SysWOW64\WerFault.exe | — | 03.exe.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7832 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 7220 -s 640 | C:\Windows\SysWOW64\WerFault.exe | — | 03.exe.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7904 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 7220 -s 700 | C:\Windows\SysWOW64\WerFault.exe | — | 03.exe.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
16 954
Read events
16 954
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
28
Text files
11
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7528 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportQueue\AppCrash_03.exe.exe_c6cc7ced5dc4359f09234f3aed519865117abf3_0337d69a_3bbdfe52-7e34-497b-82a9-e11adcccfdd6\Report.wer | — | |
MD5:— | SHA256:— | |||
| 7696 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportQueue\AppCrash_03.exe.exe_c6cc7ced5dc4359f09234f3aed519865117abf3_0337d69a_5a1c3bdd-ac7a-4fa5-b5dc-df027f29f3ab\Report.wer | — | |
MD5:— | SHA256:— | |||
| 7832 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportQueue\AppCrash_03.exe.exe_c6cc7ced5dc4359f09234f3aed519865117abf3_0337d69a_521af664-e300-4eba-ac3e-cac81cb27351\Report.wer | — | |
MD5:— | SHA256:— | |||
| 7904 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportQueue\AppCrash_03.exe.exe_c6cc7ced5dc4359f09234f3aed519865117abf3_0337d69a_3d542d19-29a8-4cd3-a62b-a8414acb1452\Report.wer | — | |
MD5:— | SHA256:— | |||
| 7976 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportQueue\AppCrash_03.exe.exe_c6cc7ced5dc4359f09234f3aed519865117abf3_0337d69a_0bdb1998-a960-41c8-80f0-3c2cf50014f2\Report.wer | — | |
MD5:— | SHA256:— | |||
| 7528 | WerFault.exe | C:\Users\admin\AppData\Local\CrashDumps\03.exe.exe.7220.dmp | binary | |
MD5:17D51DEB94F81E7B6CDC21D0966C8D95 | SHA256:A768C231C9E0892F9E5AFA32F40358C627946A9AEE4FCF0CBECA30469A23AA40 | |||
| 7528 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WERC5A4.tmp.WERInternalMetadata.xml | binary | |
MD5:6B43CE69AC2DFBCA75CBC9009BB7BD8C | SHA256:F443374B8391C8E61E48A06481F1307A3FB8665A39ED6F0CB248A5BFAF270494 | |||
| 7528 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WERC855.tmp.xml | xml | |
MD5:3423E4C4154BD12EF7352E4D76D90198 | SHA256:59A591A6FD7063A6359B26B0AE0550D5035DE76E625A7679791B3DEF8BECCC85 | |||
| 7696 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WERCF89.tmp.xml | xml | |
MD5:59D757B16A606AF9107AEFCA1ADADAFE | SHA256:8AAC17F2C32BE00D84B7FAE7A935D47B92936CE8D5012586207E78EE4B34E9FA | |||
| 8068 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportQueue\AppCrash_03.exe.exe_c6cc7ced5dc4359f09234f3aed519865117abf3_0337d69a_16071405-e78f-4f2f-a7bc-f682cce120e1\Report.wer | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
22
DNS requests
39
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.19.11.105:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.19.11.105:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6540 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6540 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.19.11.105:80 | crl.microsoft.com | Elisa Oyj | NL | whitelisted |
— | — | 2.19.11.105:80 | crl.microsoft.com | Elisa Oyj | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.219.150.101:80 | www.microsoft.com | AKAMAI-AS | CL | whitelisted |
— | — | 23.219.150.101:80 | www.microsoft.com | AKAMAI-AS | CL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 20.190.160.4:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
gc-prtnrs.top |
| unknown |
gcc-prtnrs.top |
| unknown |
slscr.update.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
2196 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
2196 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
2196 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |