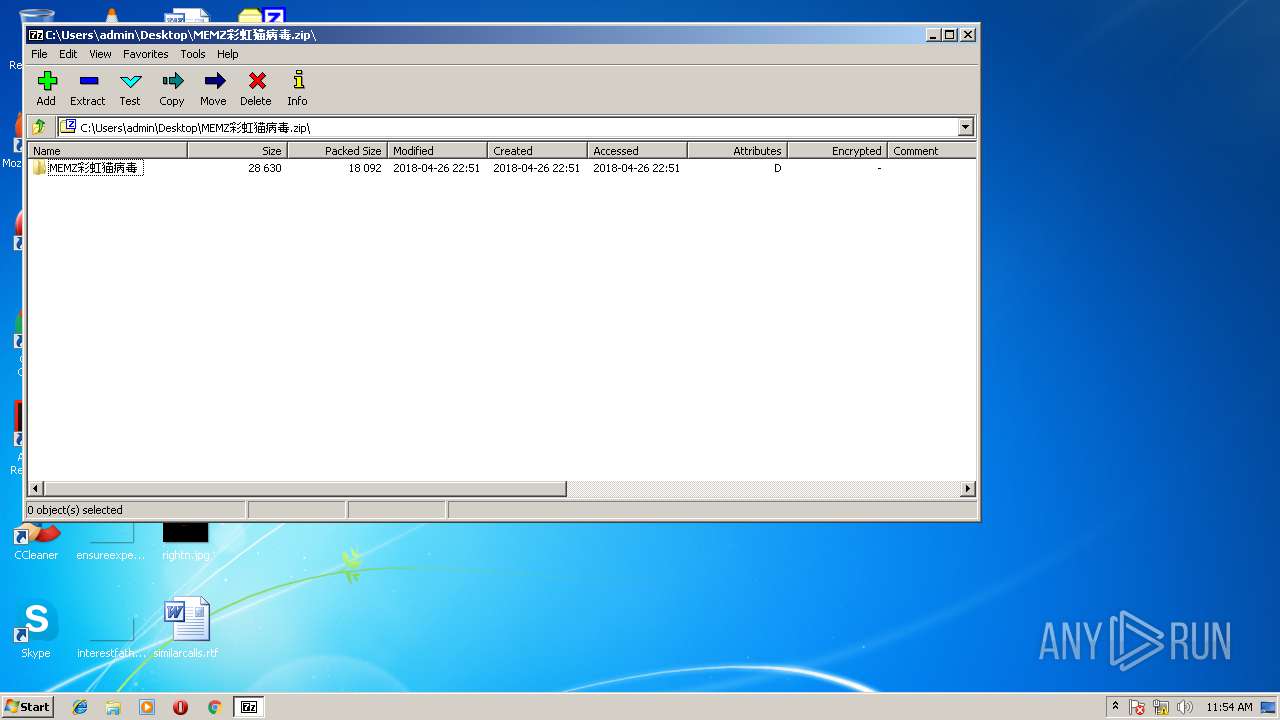
| File name: | MEMZ彩虹猫病毒.zip |
| Full analysis: | https://app.any.run/tasks/fe2b28c6-a7fc-4a4f-8352-c71dc5cb2ad3 |
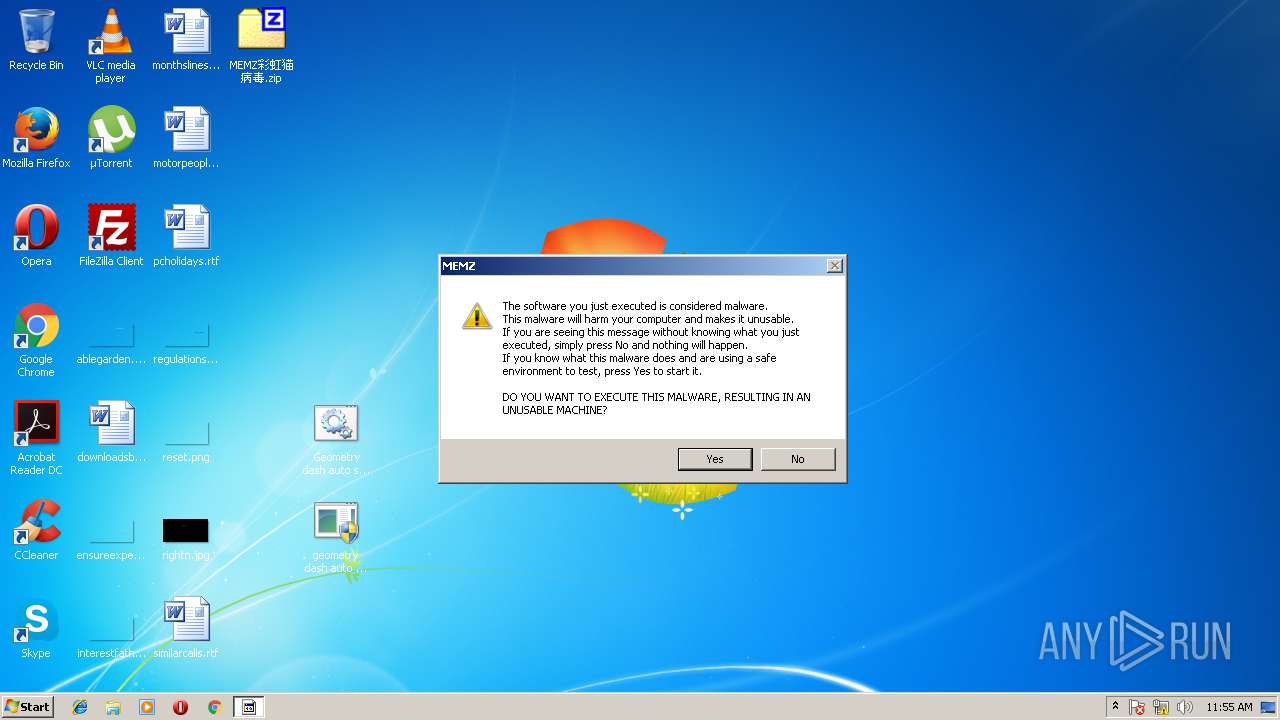
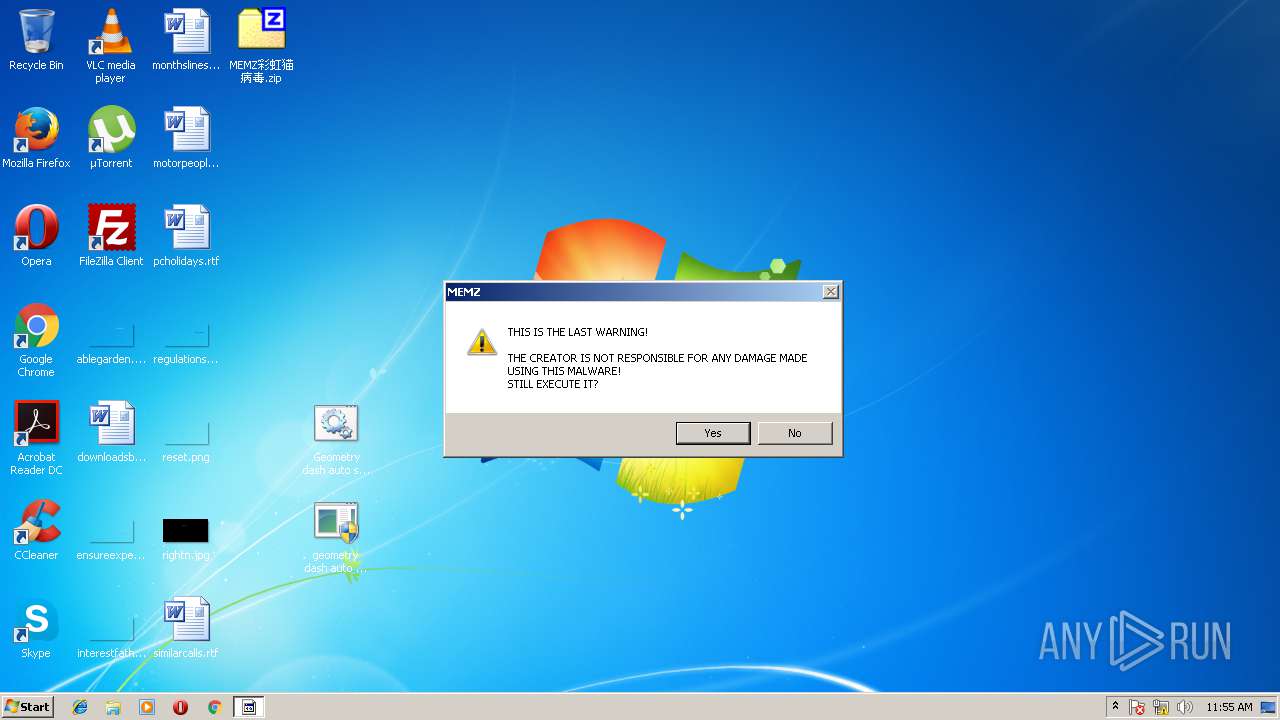
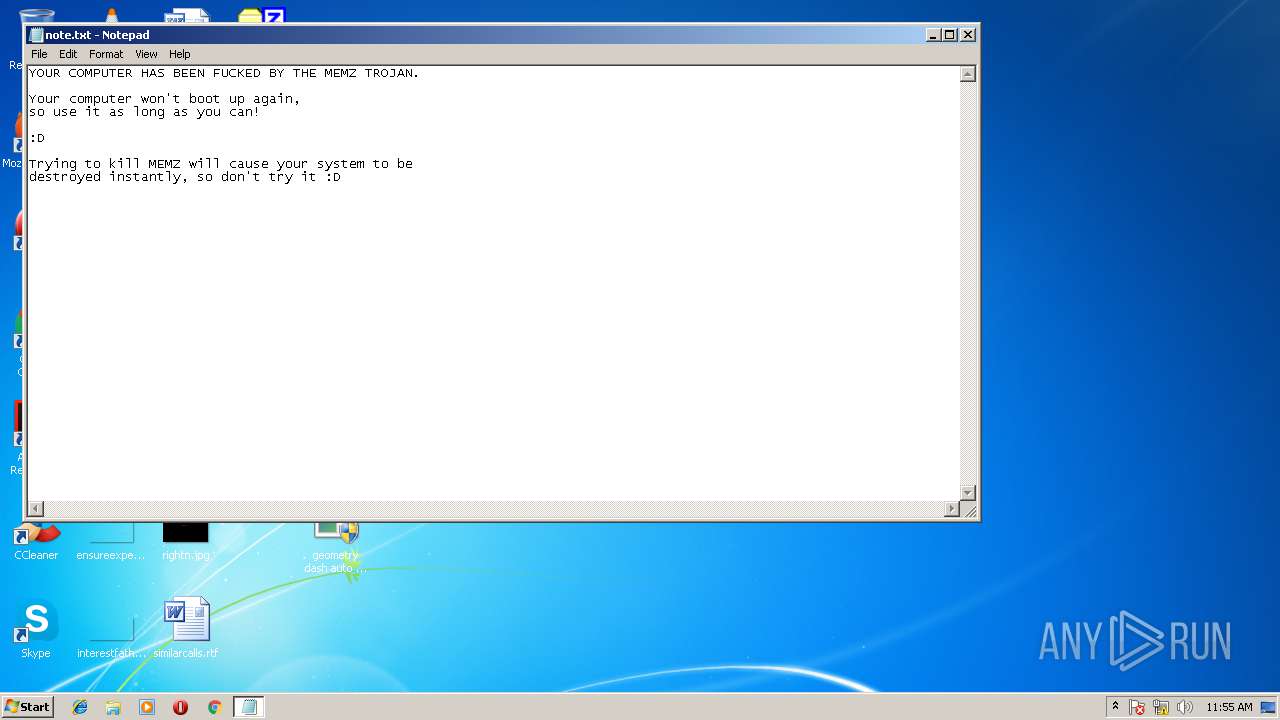
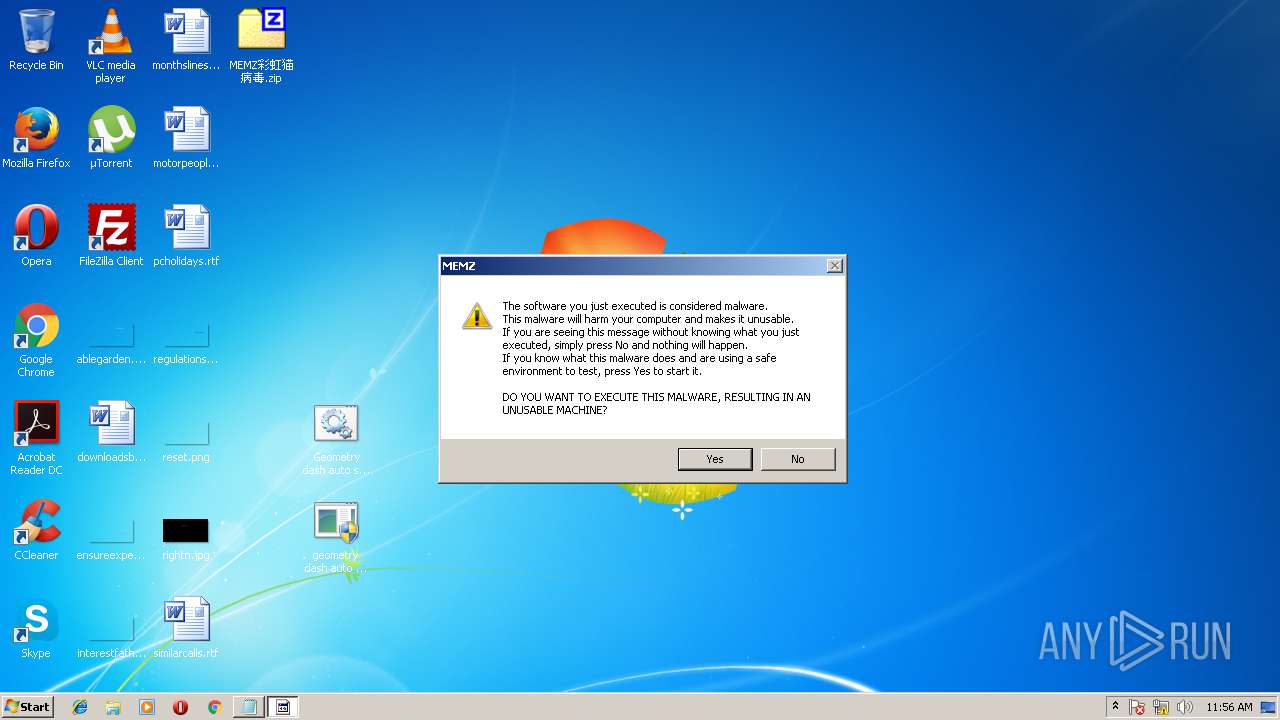
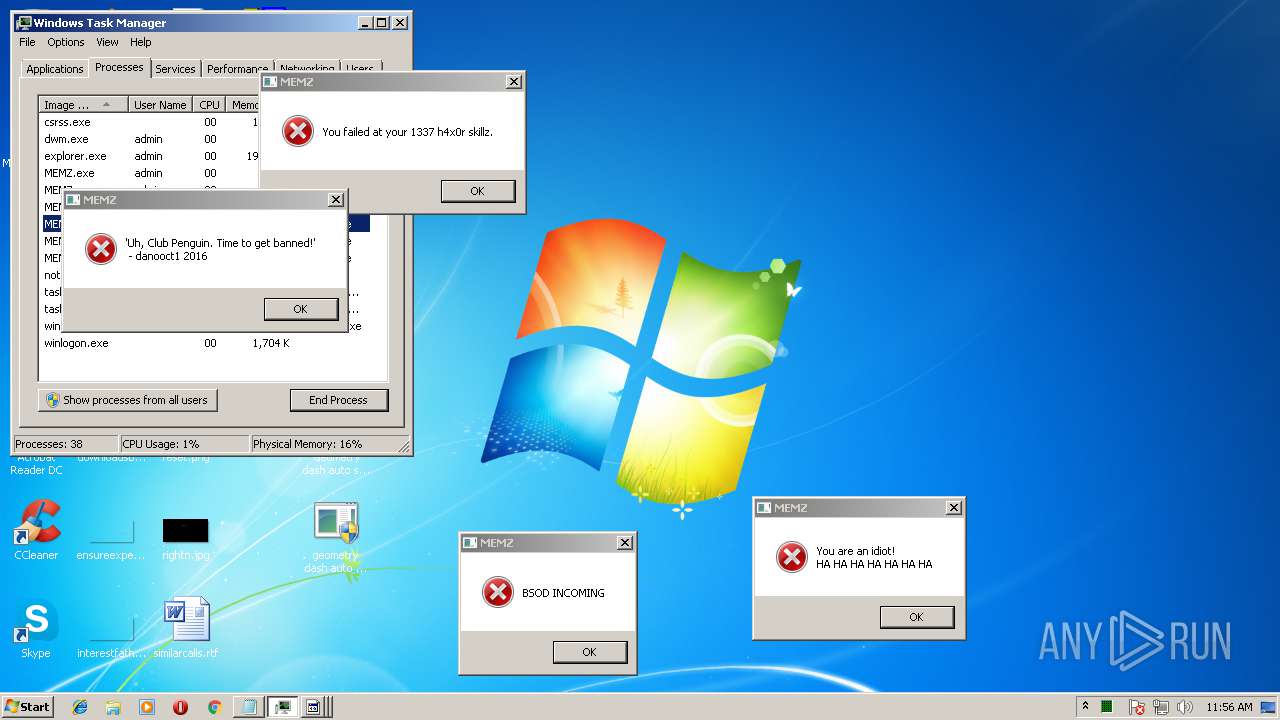
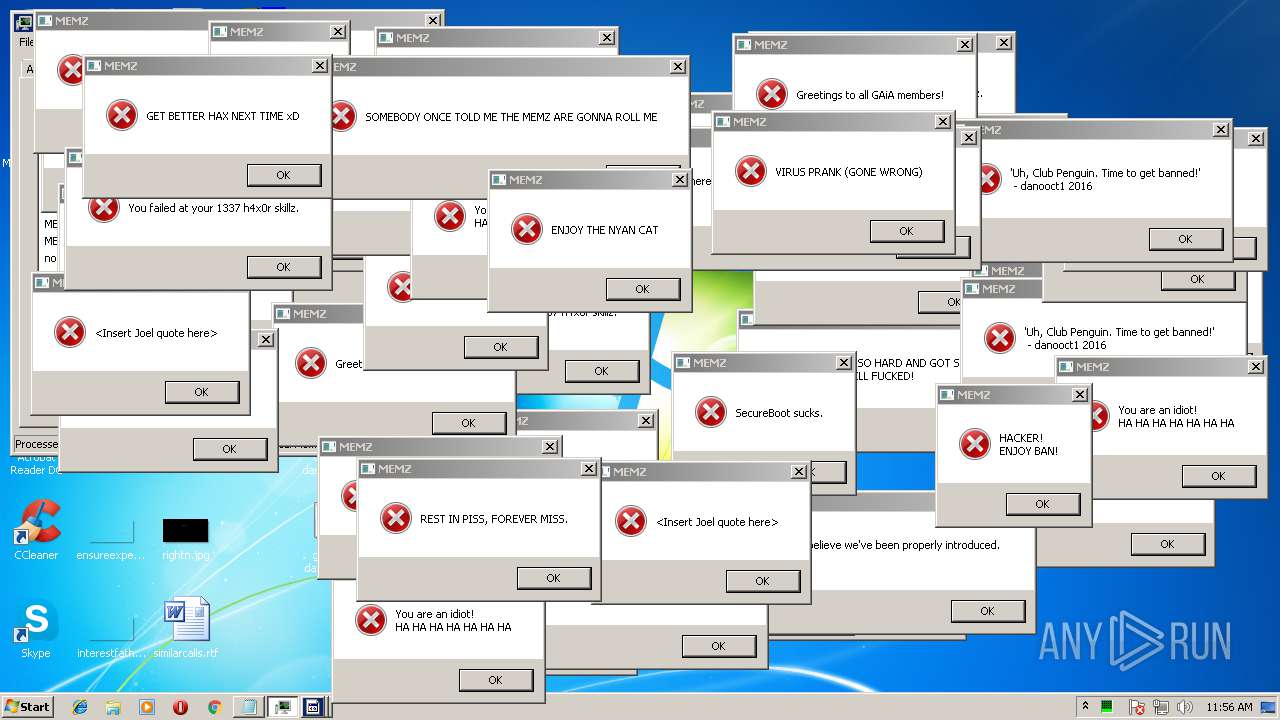
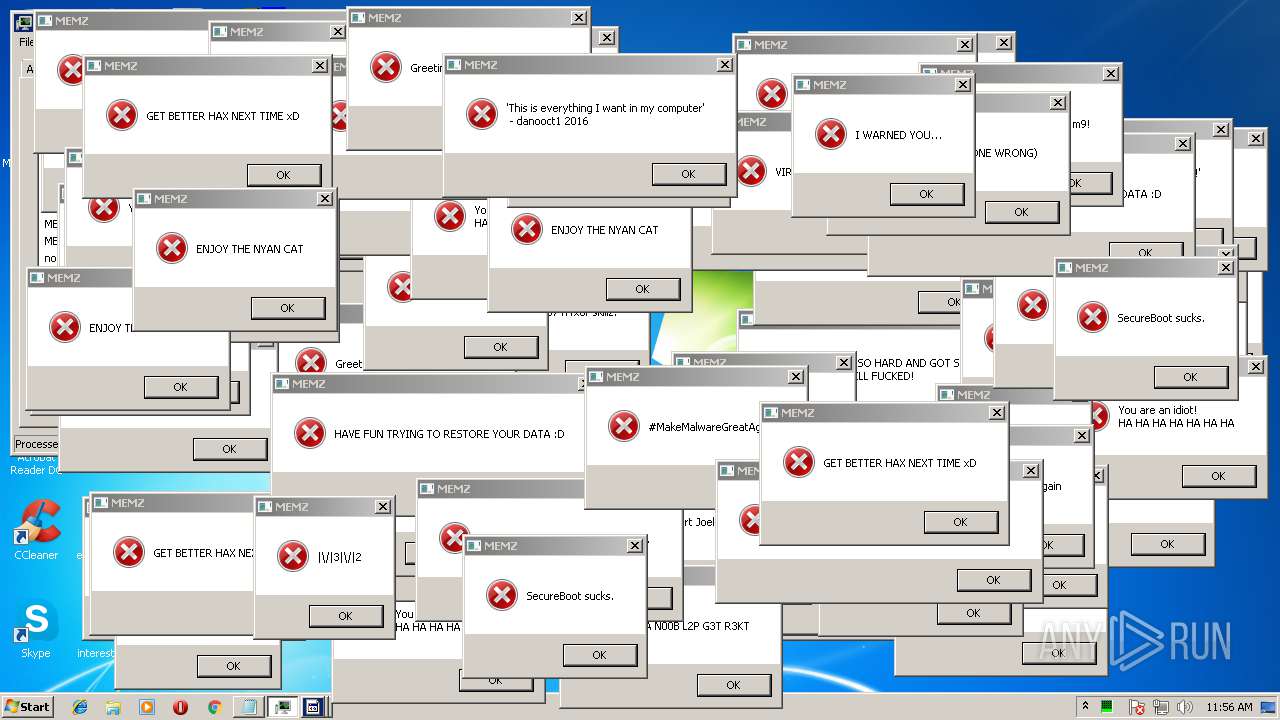
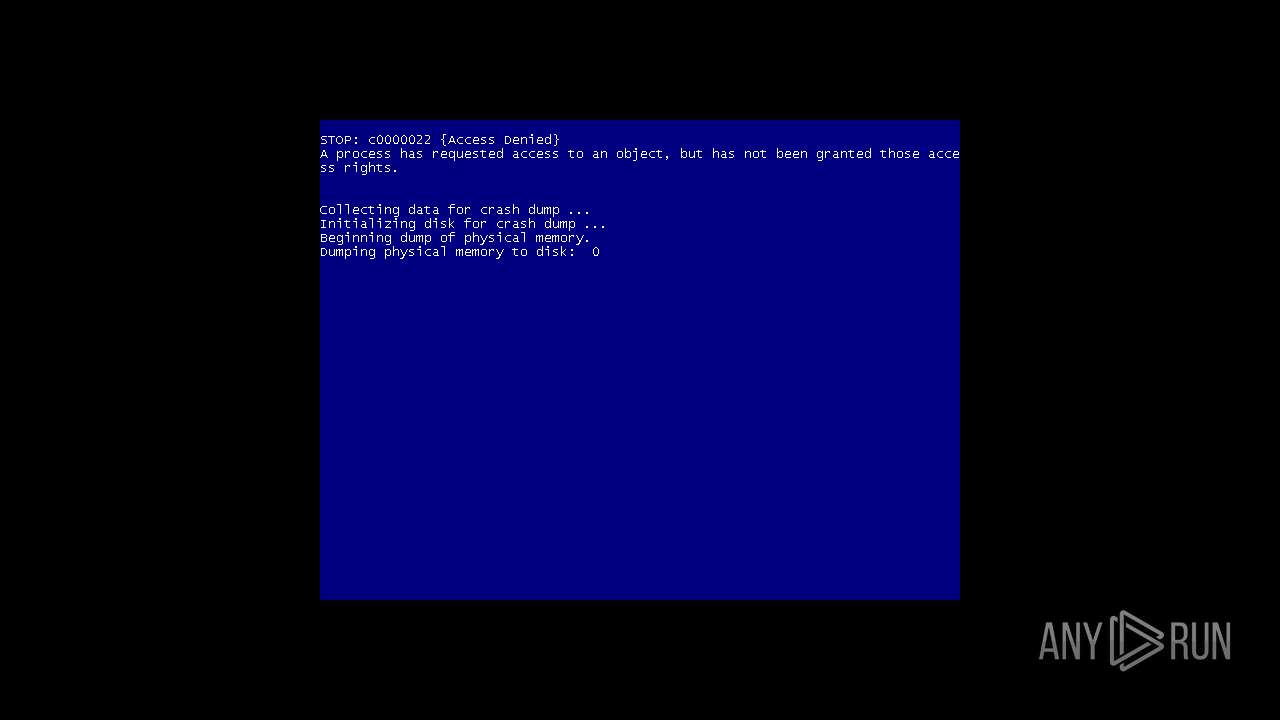
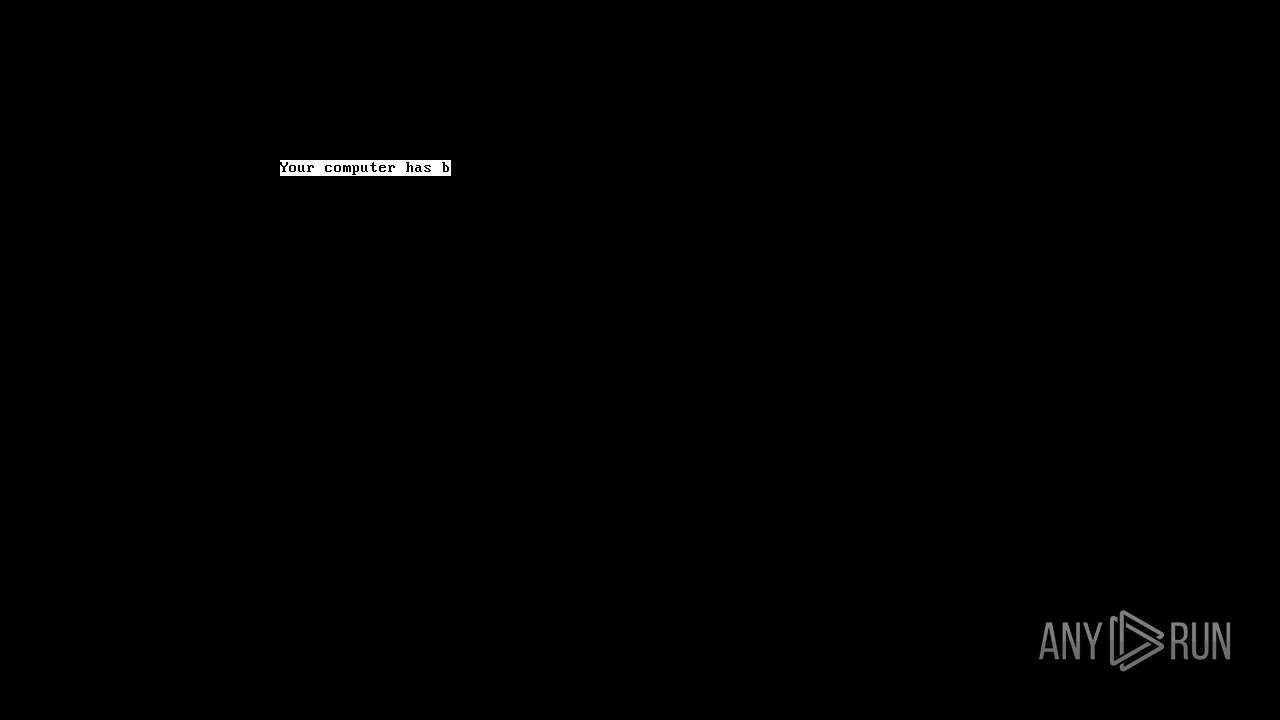
| Verdict: | Malicious activity |
| Analysis date: | May 31, 2018, 10:54:30 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract |
| MD5: | D8BF1DD634B01F71B3D201A8EB2C5D0B |
| SHA1: | E7A90DF2520DEAB1B156476AA1439961AEB1DD40 |
| SHA256: | 037171C0BFD60EB438EAB7F1BF51AC77DFFCC137963F1120AD041DD6A55D50B9 |
| SSDEEP: | 384:eq5w0zFWCFzBtLD+MGuemdZs7n52mbFimtuckPXEKyuGSXCfAKH:Lq0ECFzBsMG/7nFXoXEKyuZSAg |
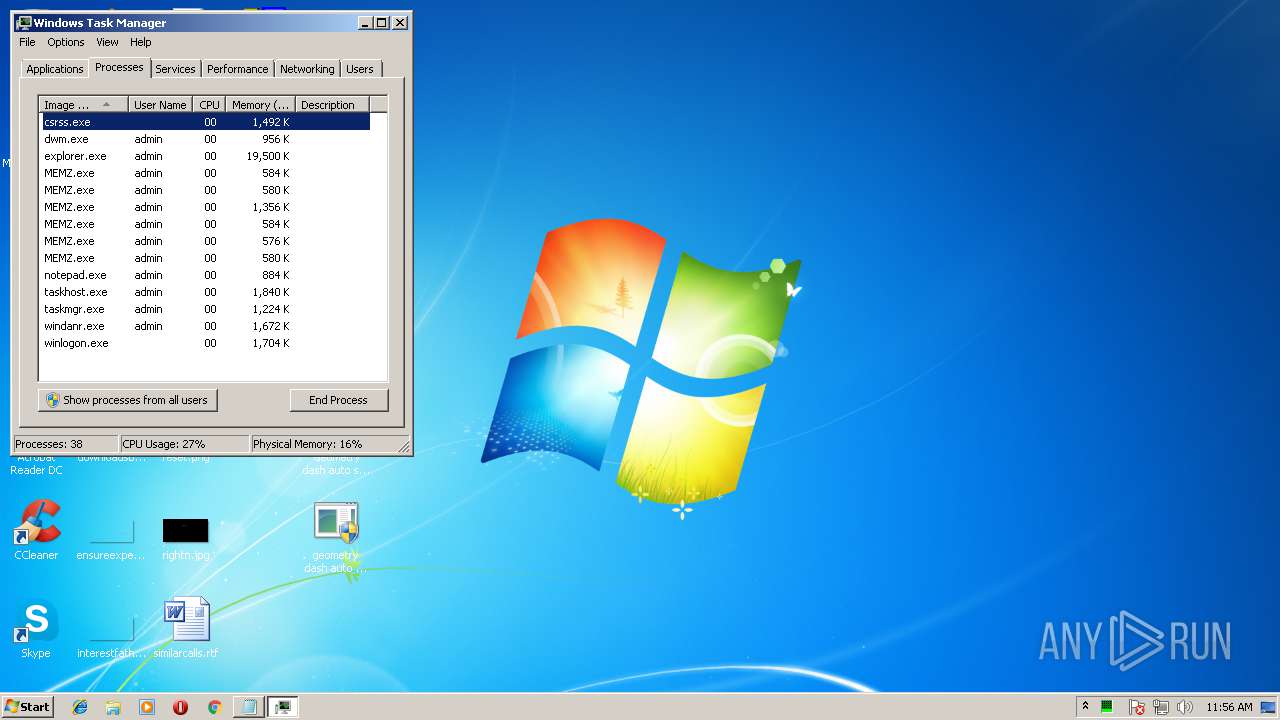
MALICIOUS
Application was dropped or rewritten from another process
- MEMZ.exe (PID: 1952)
- MEMZ.exe (PID: 2920)
- MEMZ.exe (PID: 2624)
- MEMZ.exe (PID: 1284)
- MEMZ.exe (PID: 3280)
- MEMZ.exe (PID: 860)
- MEMZ.exe (PID: 2632)
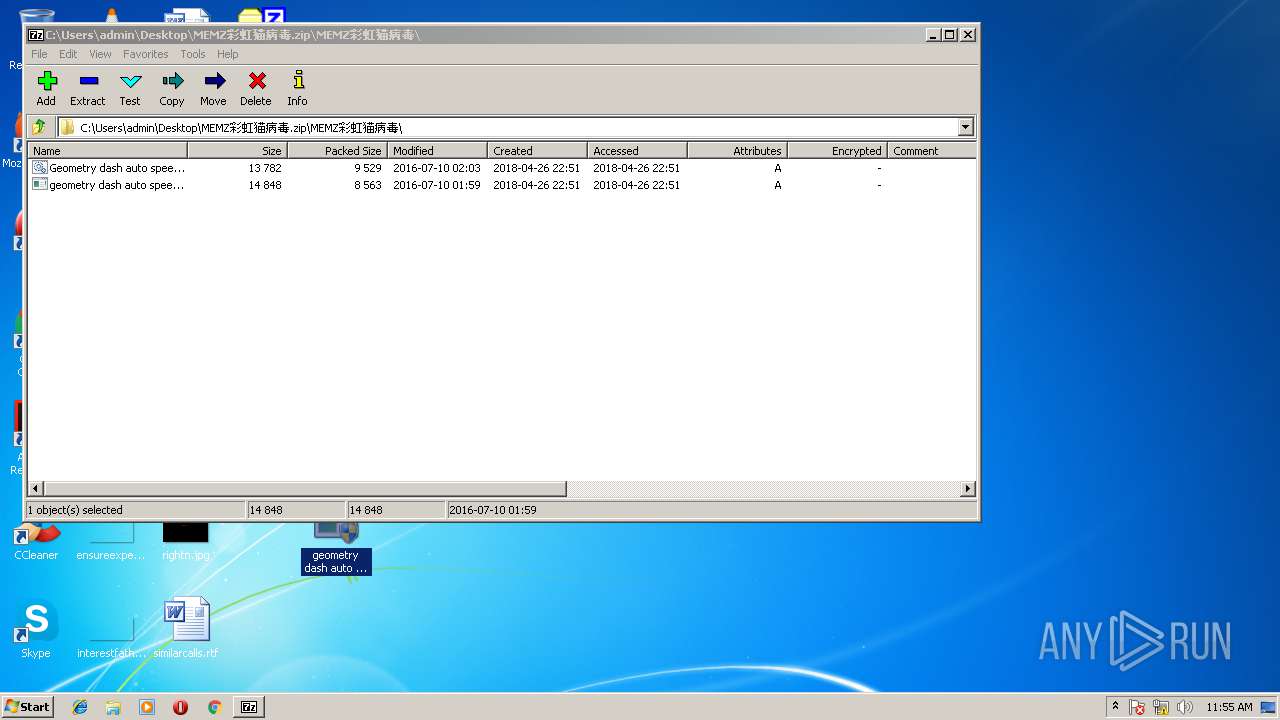
- geometry dash auto speedhack.exe (PID: 3952)
- geometry dash auto speedhack.exe (PID: 3632)
- MEMZ.exe (PID: 2668)
- MEMZ.exe (PID: 3820)
Low-level write access rights to disk partition
- MEMZ.exe (PID: 2632)
SUSPICIOUS
Executes scripts
- cmd.exe (PID: 3892)
Executable content was dropped or overwritten
- cscript.exe (PID: 3300)
Creates files in the user directory
- cscript.exe (PID: 3300)
Low-level read access rights to disk partition
- MEMZ.exe (PID: 2632)
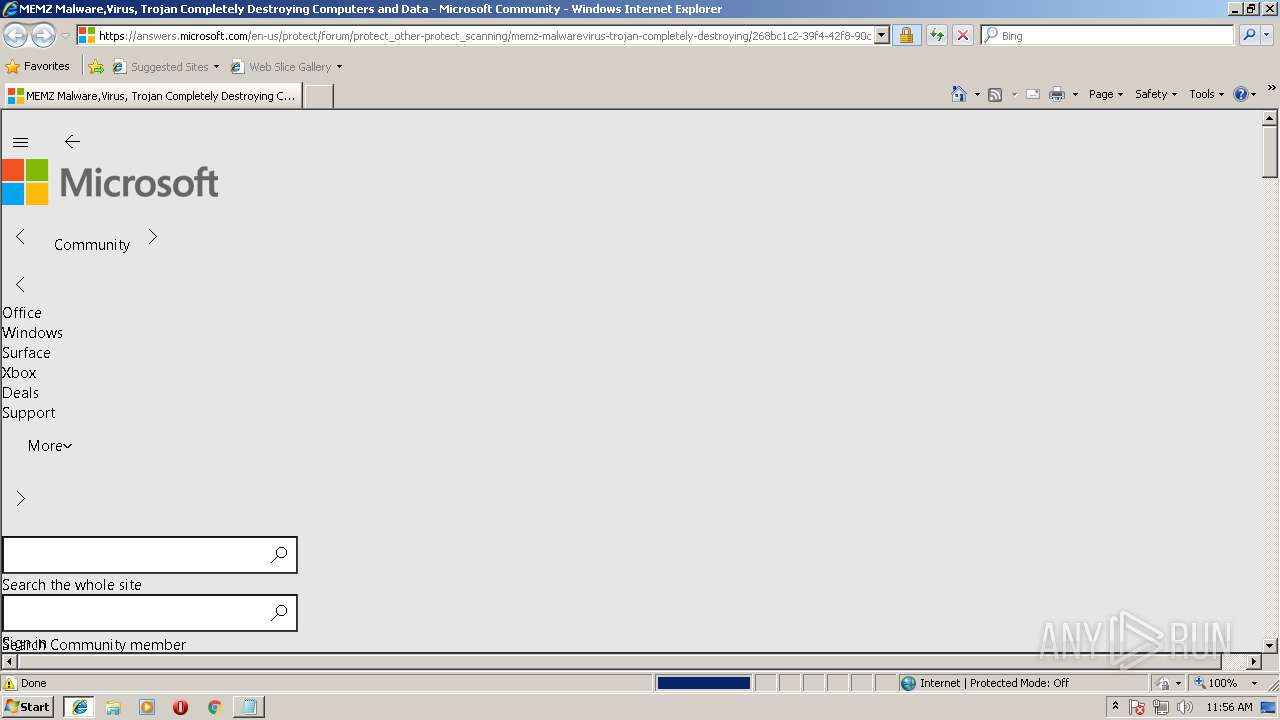
Starts Internet Explorer
- MEMZ.exe (PID: 2632)
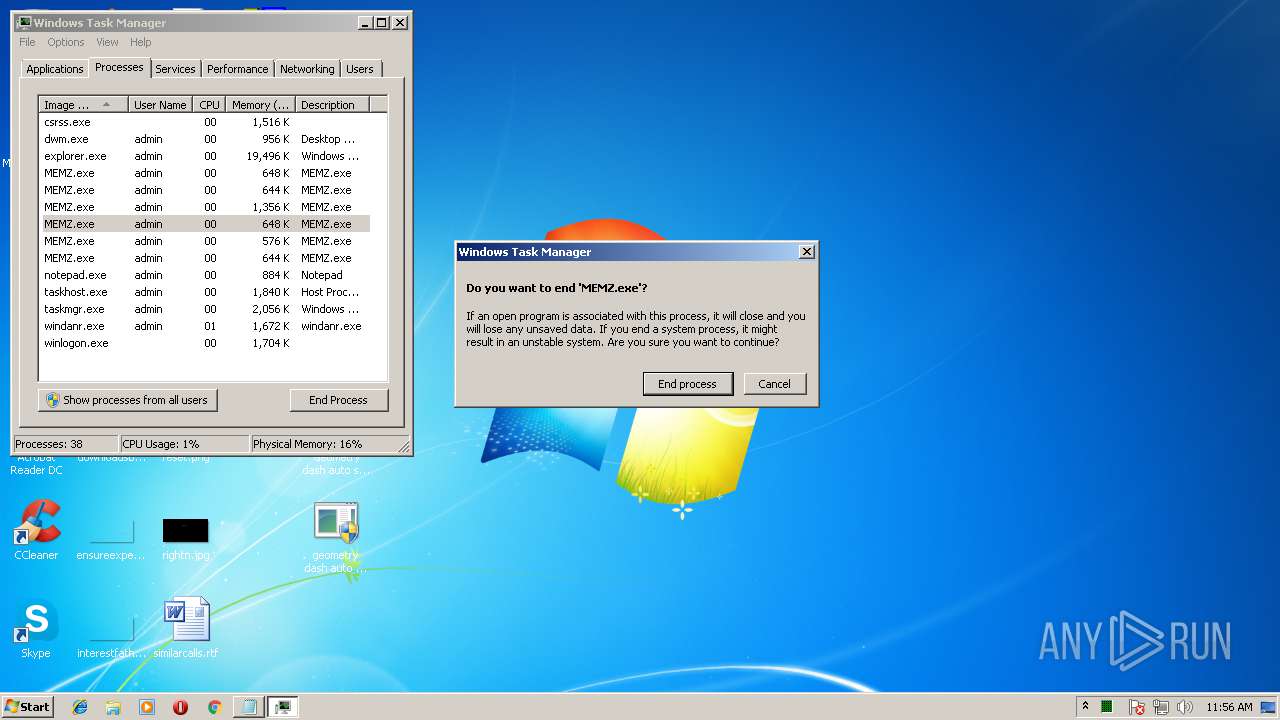
Application launched itself
- MEMZ.exe (PID: 2624)
INFO
Dropped object may contain URL's
- cscript.exe (PID: 3300)
- iexplore.exe (PID: 2892)
- iexplore.exe (PID: 3900)
Changes internet zones settings
- iexplore.exe (PID: 2892)
Changes settings of System certificates
- iexplore.exe (PID: 3900)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3900)
Reads internet explorer settings
- iexplore.exe (PID: 3900)
Creates files in the user directory
- iexplore.exe (PID: 3900)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
Total processes
58
Monitored processes
18
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 860 | "C:\Users\admin\AppData\Roaming\MEMZ.exe" /watchdog | C:\Users\admin\AppData\Roaming\MEMZ.exe | — | MEMZ.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1284 | "C:\Users\admin\AppData\Roaming\MEMZ.exe" /watchdog | C:\Users\admin\AppData\Roaming\MEMZ.exe | — | MEMZ.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1952 | "C:\Users\admin\AppData\Roaming\MEMZ.exe" | C:\Users\admin\AppData\Roaming\MEMZ.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 2624 | "C:\Users\admin\AppData\Roaming\MEMZ.exe" | C:\Users\admin\AppData\Roaming\MEMZ.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2632 | "C:\Users\admin\AppData\Roaming\MEMZ.exe" /main | C:\Users\admin\AppData\Roaming\MEMZ.exe | MEMZ.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2668 | "C:\Users\admin\AppData\Roaming\MEMZ.exe" /watchdog | C:\Users\admin\AppData\Roaming\MEMZ.exe | — | MEMZ.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 1 Modules
| |||||||||||||||
| 2892 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | MEMZ.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2920 | "C:\Users\admin\AppData\Roaming\MEMZ.exe" | C:\Users\admin\AppData\Roaming\MEMZ.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 3280 | "C:\Users\admin\AppData\Roaming\MEMZ.exe" /watchdog | C:\Users\admin\AppData\Roaming\MEMZ.exe | — | MEMZ.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3300 | cscript x.js | C:\Windows\system32\cscript.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Console Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
Total events
1 376
Read events
1 269
Write events
106
Delete events
1
Modification events
| (PID) Process: | (3664) 7zFM.exe | Key: | HKEY_CURRENT_USER\Software\7-Zip\FM |
| Operation: | write | Name: | FolderShortcuts |
Value: | |||
| (PID) Process: | (3664) 7zFM.exe | Key: | HKEY_CURRENT_USER\Software\7-Zip\FM |
| Operation: | write | Name: | FolderHistory |
Value: 43003A005C00550073006500720073005C00610064006D0069006E005C004400650073006B0074006F0070005C004D0045004D005A00695F79862B73C575D26B2E007A00690070005C004D0045004D005A00695F79862B73C575D26B5C00000043003A005C00550073006500720073005C00610064006D0069006E005C004400650073006B0074006F0070005C004D0045004D005A00695F79862B73C575D26B2E007A00690070005C000000 | |||
| (PID) Process: | (3664) 7zFM.exe | Key: | HKEY_CURRENT_USER\Software\7-Zip\FM |
| Operation: | write | Name: | PanelPath0 |
Value: C:\Users\admin\Desktop\ | |||
| (PID) Process: | (3664) 7zFM.exe | Key: | HKEY_CURRENT_USER\Software\7-Zip\FM |
| Operation: | write | Name: | FlatViewArc0 |
Value: 0 | |||
| (PID) Process: | (3664) 7zFM.exe | Key: | HKEY_CURRENT_USER\Software\7-Zip\FM |
| Operation: | write | Name: | PanelPath1 |
Value: | |||
| (PID) Process: | (3664) 7zFM.exe | Key: | HKEY_CURRENT_USER\Software\7-Zip\FM |
| Operation: | write | Name: | FlatViewArc1 |
Value: 0 | |||
| (PID) Process: | (3664) 7zFM.exe | Key: | HKEY_CURRENT_USER\Software\7-Zip\FM |
| Operation: | write | Name: | ListMode |
Value: 771 | |||
| (PID) Process: | (3664) 7zFM.exe | Key: | HKEY_CURRENT_USER\Software\7-Zip\FM |
| Operation: | write | Name: | Position |
Value: 1600000016000000D60300000B02000000000000 | |||
| (PID) Process: | (3664) 7zFM.exe | Key: | HKEY_CURRENT_USER\Software\7-Zip\FM |
| Operation: | write | Name: | Panels |
Value: 0100000000000000DA010000 | |||
| (PID) Process: | (3300) cscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
1
Suspicious files
4
Text files
81
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3664 | 7zFM.exe | C:\Users\admin\AppData\Local\Temp\7zE05E47654\Geometry dash auto speedhack.bat | — | |
MD5:— | SHA256:— | |||
| 3664 | 7zFM.exe | C:\Users\admin\AppData\Local\Temp\7zE05E47654\geometry dash auto speedhack.exe | — | |
MD5:— | SHA256:— | |||
| 2892 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\2LKO8ICX\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2892 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3900 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LM4BD81N\268bc1c2-39f4-42f8-90c2-597a673b6b45[1].txt | — | |
MD5:— | SHA256:— | |||
| 3900 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Cab3561.tmp | — | |
MD5:— | SHA256:— | |||
| 3900 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Cab3563.tmp | — | |
MD5:— | SHA256:— | |||
| 3900 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Tar3564.tmp | — | |
MD5:— | SHA256:— | |||
| 3900 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Tar3562.tmp | — | |
MD5:— | SHA256:— | |||
| 3900 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Cab3565.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
17
DNS requests
12
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2892 | iexplore.exe | GET | 200 | 204.79.197.229:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
3900 | iexplore.exe | GET | 301 | 184.31.82.138:80 | http://answers.microsoft.com/en-us/protect/forum/protect_other-protect_scanning/memz-malwarevirus-trojan-completely-destroying/268bc1c2-39f4-42f8-90c2-597a673b6b45 | NL | html | 287 b | whitelisted |
3900 | iexplore.exe | GET | 304 | 2.16.186.56:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | unknown | — | — | whitelisted |
3900 | iexplore.exe | GET | 304 | 2.16.186.56:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2892 | iexplore.exe | 204.79.197.229:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3900 | iexplore.exe | 184.31.82.138:80 | answers.microsoft.com | Akamai International B.V. | NL | whitelisted |
3900 | iexplore.exe | 184.31.82.138:443 | answers.microsoft.com | Akamai International B.V. | NL | whitelisted |
3900 | iexplore.exe | 23.67.129.120:443 | uhf.microsoft.com | Akamai International B.V. | NL | whitelisted |
3900 | iexplore.exe | 2.16.186.56:80 | www.download.windowsupdate.com | Akamai International B.V. | — | whitelisted |
3900 | iexplore.exe | 2.16.186.26:443 | statics-uhf-neu.akamaized.net | Akamai International B.V. | — | whitelisted |
3900 | iexplore.exe | 23.211.9.92:443 | www.microsoft.com | Akamai Technologies, Inc. | NL | whitelisted |
3900 | iexplore.exe | 2.16.186.40:443 | img-prod-cms-rt-microsoft-com.akamaized.net | Akamai International B.V. | — | whitelisted |
3900 | iexplore.exe | 152.199.19.160:443 | az725175.vo.msecnd.net | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3900 | iexplore.exe | 23.45.96.252:443 | answersstaticfilecdn.azureedge.net | Akamai International B.V. | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
answers.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
statics-uhf-neu.akamaized.net |
| whitelisted |
answersstaticfilecdn.azureedge.net |
| whitelisted |
uhf.microsoft.com |
| whitelisted |
www.download.windowsupdate.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
img-prod-cms-rt-microsoft-com.akamaized.net |
| whitelisted |
filestore.community.support.microsoft.com |
| whitelisted |
mem.gfx.ms |
| whitelisted |