| File name: | HelloFont_2.6.0.1.exe |
| Full analysis: | https://app.any.run/tasks/a1881ef5-5821-4601-98c0-43e5faae27aa |
| Verdict: | Malicious activity |
| Analysis date: | February 19, 2024, 01:54:00 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 54B88952728B70AEC1953745DFCE15F9 |
| SHA1: | CA2F597712A7A8AF9DD6BFF44DBDE318B478FF43 |
| SHA256: | 035B603EBCB92EE106CFD7F1D768F6564B88660ABF8955C51FBD8680B652186F |
| SSDEEP: | 98304:/V7fEEWqJzK00u0sFiGckYrLm+Y0PRD5Pz637kYIhdHDL1VEBqDqFrMCKibKY48r:/f33+60 |
MALICIOUS
Drops the executable file immediately after the start
- HelloFont_2.6.0.1.exe (PID: 3672)
Changes the autorun value in the registry
- HelloFont_2.6.0.1.exe (PID: 3672)
SUSPICIOUS
Changes Internet Explorer settings (feature browser emulation)
- HelloFont_2.6.0.1.exe (PID: 3672)
Reads Internet Explorer settings
- HelloFont_2.6.0.1.exe (PID: 3672)
Reads the Internet Settings
- HelloFont_2.6.0.1.exe (PID: 3672)
Reads Microsoft Outlook installation path
- HelloFont_2.6.0.1.exe (PID: 3672)
Connects to the server without a host name
- HelloFont_2.6.0.1.exe (PID: 3672)
Reads security settings of Internet Explorer
- HelloFont_2.6.0.1.exe (PID: 3672)
Checks Windows Trust Settings
- HelloFont_2.6.0.1.exe (PID: 3672)
Reads settings of System Certificates
- HelloFont_2.6.0.1.exe (PID: 3672)
INFO
Checks supported languages
- HelloFont_2.6.0.1.exe (PID: 3672)
Reads the computer name
- HelloFont_2.6.0.1.exe (PID: 3672)
Checks proxy server information
- HelloFont_2.6.0.1.exe (PID: 3672)
Reads the machine GUID from the registry
- HelloFont_2.6.0.1.exe (PID: 3672)
Reads Environment values
- HelloFont_2.6.0.1.exe (PID: 3672)
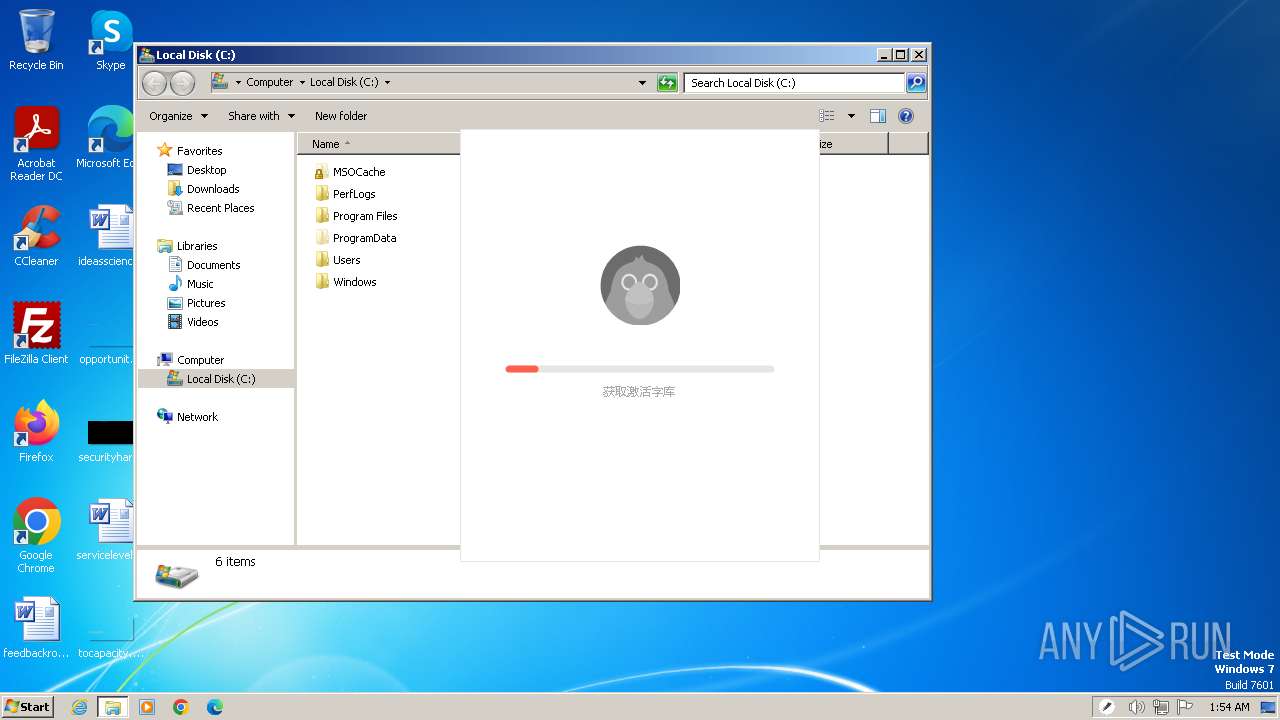
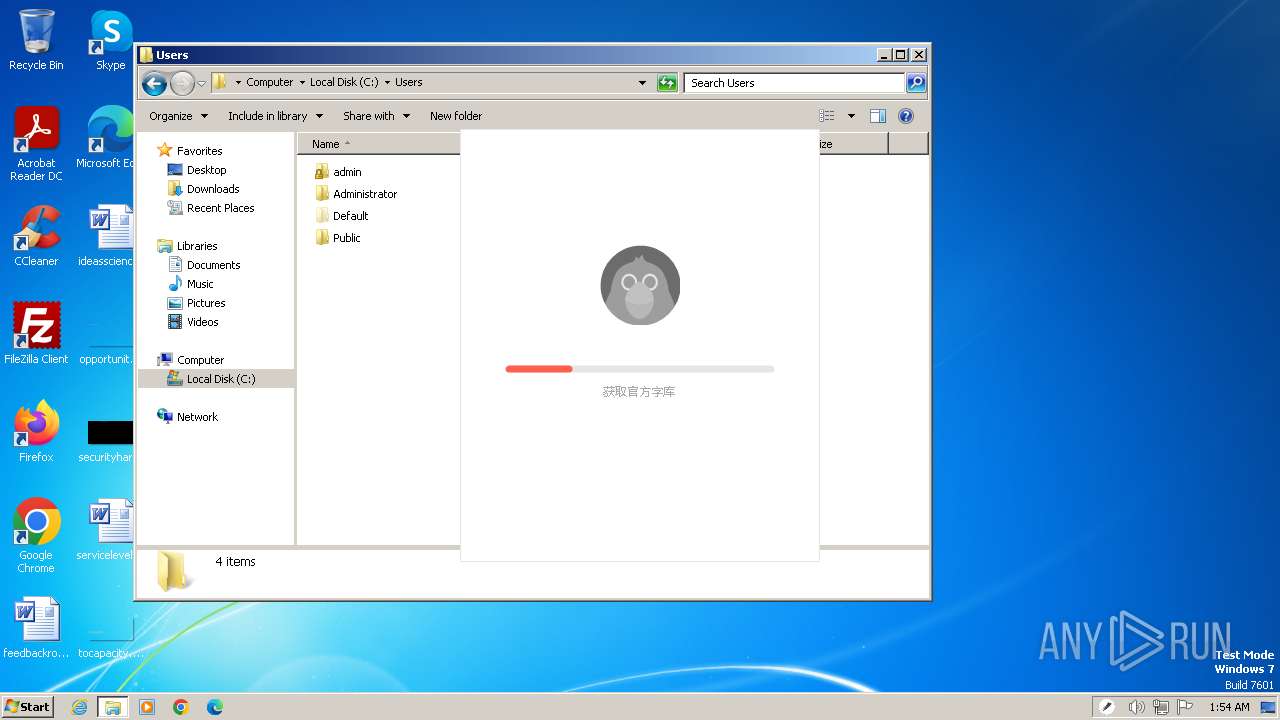
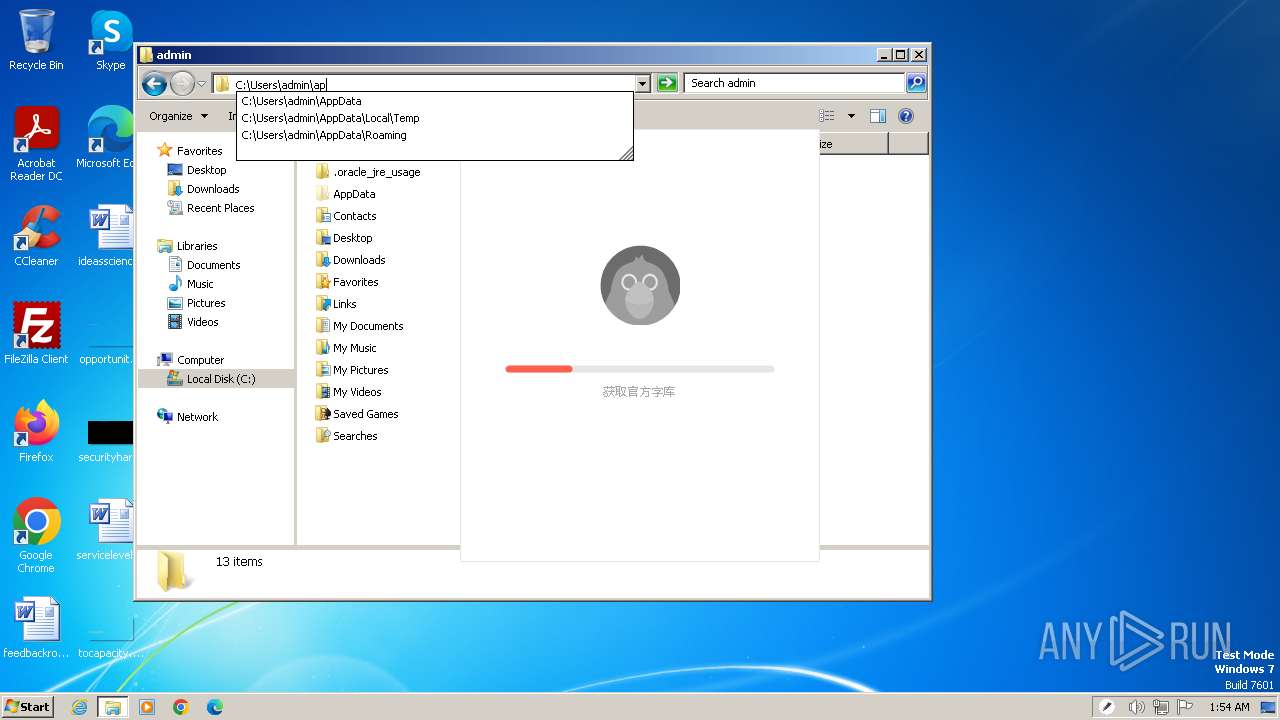
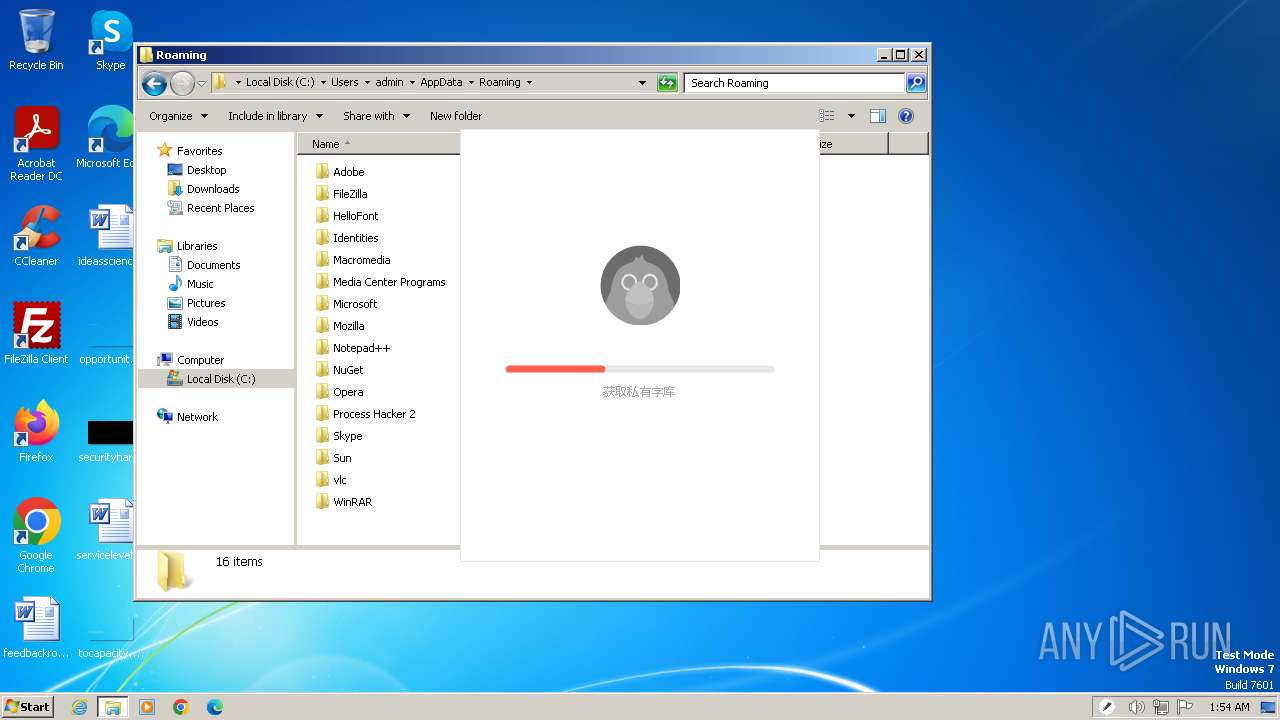
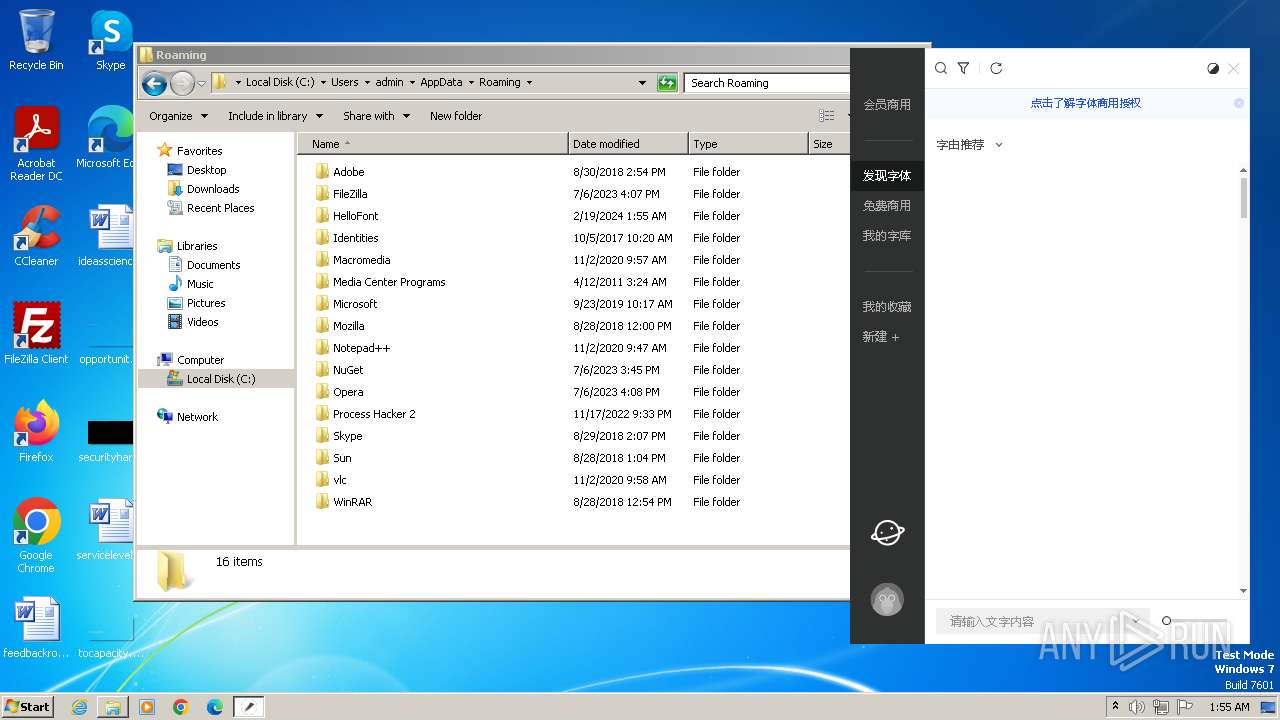
Creates files or folders in the user directory
- HelloFont_2.6.0.1.exe (PID: 3672)
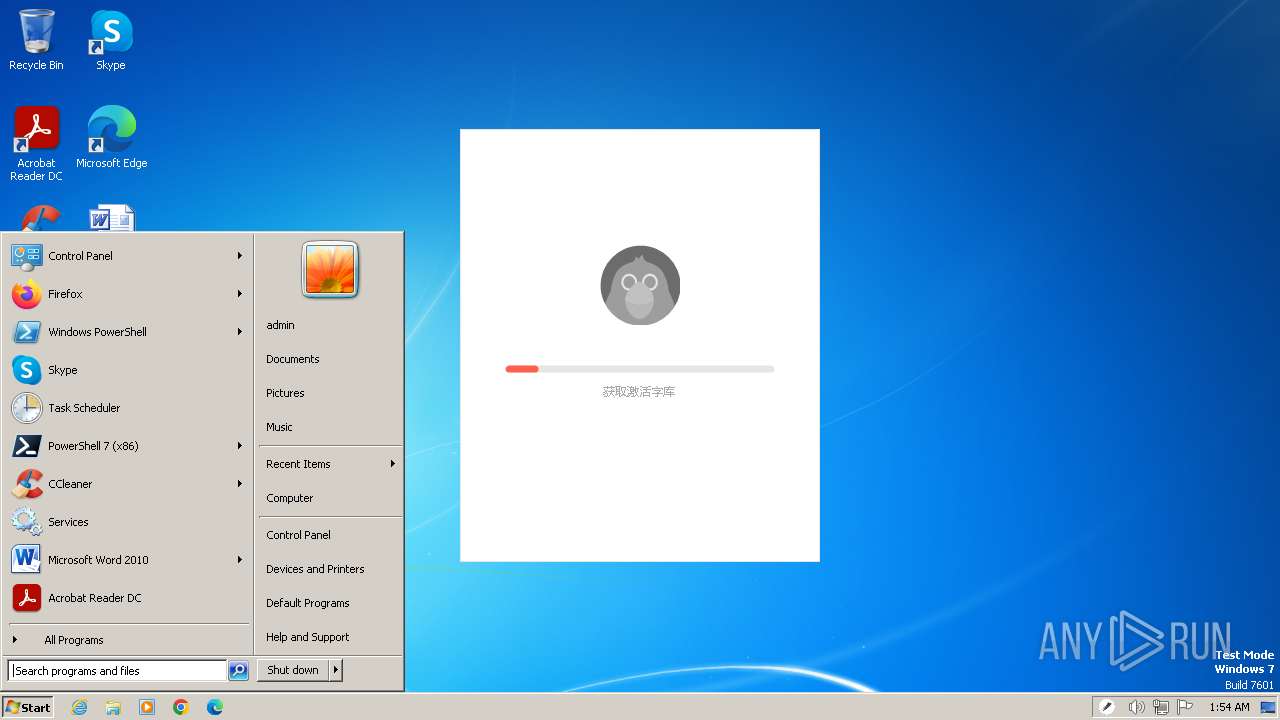
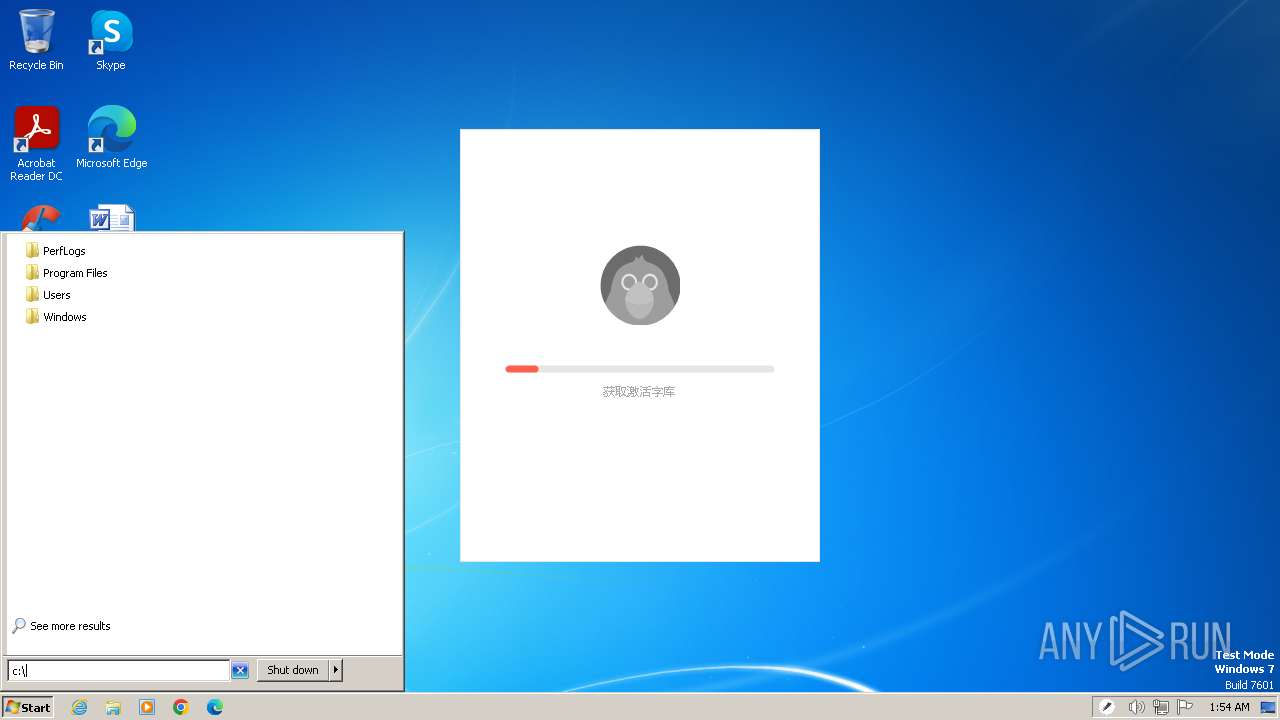
Manual execution by a user
- verclsid.exe (PID: 3940)
Reads the software policy settings
- HelloFont_2.6.0.1.exe (PID: 3672)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (45.1) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (19.2) |
| .exe | | | Win64 Executable (generic) (17) |
| .scr | | | Windows screen saver (8) |
| .dll | | | Win32 Dynamic Link Library (generic) (4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:07:02 08:44:05+00:00 |
| ImageFileCharacteristics: | Executable, No line numbers, No symbols, Large address aware, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 10869248 |
| InitializedDataSize: | 364032 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xa5f99e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.6.0.1 |
| ProductVersionNumber: | 2.6.0.1 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | 字由开发组 |
| FileDescription: | 字由 |
| FileVersion: | 2.6.0.1 |
| InternalName: | HelloFont.exe |
| LegalCopyright: | Copyright © 字由开发组 2015 |
| LegalTrademarks: | - |
| OriginalFileName: | HelloFont.exe |
| ProductName: | HelloFont |
| ProductVersion: | 2.6.0.1 |
| AssemblyVersion: | 2.6.0.1 |
Total processes
40
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3672 | "C:\Users\admin\AppData\Local\Temp\HelloFont_2.6.0.1.exe" | C:\Users\admin\AppData\Local\Temp\HelloFont_2.6.0.1.exe | explorer.exe | ||||||||||||
User: admin Company: 字由开发组 Integrity Level: MEDIUM Description: 字由 Exit code: 0 Version: 2.6.0.1 Modules
| |||||||||||||||
| 3940 | "C:\Windows\system32\verclsid.exe" /S /C {0B2C9183-C9FA-4C53-AE21-C900B0C39965} /I {0C733A8A-2A1C-11CE-ADE5-00AA0044773D} /X 0x401 | C:\Windows\System32\verclsid.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Extension CLSID Verification Host Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
6 793
Read events
6 726
Write events
58
Delete events
9
Modification events
| (PID) Process: | (3672) HelloFont_2.6.0.1.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | HelloFont |
Value: C:\Users\admin\AppData\Local\Temp\HelloFont_2.6.0.1.exe | |||
| (PID) Process: | (3672) HelloFont_2.6.0.1.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3672) HelloFont_2.6.0.1.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3672) HelloFont_2.6.0.1.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3672) HelloFont_2.6.0.1.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3672) HelloFont_2.6.0.1.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3672) HelloFont_2.6.0.1.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | delete value | Name: | ProxyServer |
Value: | |||
| (PID) Process: | (3672) HelloFont_2.6.0.1.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | delete value | Name: | ProxyOverride |
Value: | |||
| (PID) Process: | (3672) HelloFont_2.6.0.1.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | delete value | Name: | AutoConfigURL |
Value: | |||
| (PID) Process: | (3672) HelloFont_2.6.0.1.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | delete value | Name: | AutoDetect |
Value: | |||
Executable files
0
Suspicious files
5
Text files
20
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3672 | HelloFont_2.6.0.1.exe | C:\Users\admin\AppData\Roaming\HelloFont\ClientFont.cfg | — | |
MD5:— | SHA256:— | |||
| 3672 | HelloFont_2.6.0.1.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\041zKv2V3IMU0w34[1].jpg | image | |
MD5:BC39BB648E341398C0E216CB3F057895 | SHA256:AA14889C8032B379CC3B9E8E1024ECB02FEB69F3DBE841AB5D9E0EFF7308587E | |||
| 3672 | HelloFont_2.6.0.1.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\AD5F118F7897046E8CA970AE6A6AB70B_9B8670363F58B4643EB28A4A03EE9887 | binary | |
MD5:722863A7E9DE0ADD6C5AA2831AD4D75C | SHA256:C6F7BFFC64095700E63BC8BB501DA56550790844B6F9E5E5ADDEEE14D84D5900 | |||
| 3672 | HelloFont_2.6.0.1.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\AD5F118F7897046E8CA970AE6A6AB70B_9B8670363F58B4643EB28A4A03EE9887 | binary | |
MD5:EAD47115545FB3242F7D48EF677C7583 | SHA256:5750B5BAA5DAAE94D1DC12E111ABC3F4CBC2A774734FDA8C4F97C8D313C50220 | |||
| 3672 | HelloFont_2.6.0.1.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\weui.min[1].css | text | |
MD5:0B45637C03C1A7336E60999B903037B7 | SHA256:CF26F39C60020FEE1EF4149EA6C7D22D4D6AFC533505CACEF8CC3A364B37EAB0 | |||
| 3672 | HelloFont_2.6.0.1.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\eb891745f5ce5971ec7c64dfb6f37c09[1].css | text | |
MD5:EB891745F5CE5971EC7C64DFB6F37C09 | SHA256:E7E5D19C9F2FB5D9652E32F582FC72E9F004C6AA0B7BB17FE6FD02540253A912 | |||
| 3672 | HelloFont_2.6.0.1.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\jquery.min[1].js | text | |
MD5:F03E5A3BF534F4A738BC350631FD05BD | SHA256:AEC3D419D50F05781A96F223E18289AEB52598B5DB39BE82A7B71DC67D6A7947 | |||
| 3672 | HelloFont_2.6.0.1.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\AD5F118F7897046E8CA970AE6A6AB70B_E651713E4557F0364906DDC1B2674A2E | binary | |
MD5:C49074D3D8FF3D68E747D1727CEB0597 | SHA256:E32C4913D961C9C09FF24FF0172A03D19CA122EA65B551E2065B76CBEF2F1943 | |||
| 3672 | HelloFont_2.6.0.1.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\AD5F118F7897046E8CA970AE6A6AB70B_E651713E4557F0364906DDC1B2674A2E | binary | |
MD5:6915EBD98D4056A3418876BC7BBD3725 | SHA256:1B7E39ACC129A1BF53B4BFB56C920BCA3D82BDC34E8C16924307849905712A45 | |||
| 3672 | HelloFont_2.6.0.1.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:429DB78509B56B661F3A3EF47EC74773 | SHA256:DA04E3AC103E2B88E3948D09734EEF32E7F9A0A2AC23692B6EAAABC563C6DB2D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
21
TCP/UDP connections
25
DNS requests
7
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 163.181.131.227:80 | http://ocsp.digicert.cn/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAbJNRrm8KxusAb7DCqnMkE%3D | unknown | binary | 471 b | unknown |
3672 | HelloFont_2.6.0.1.exe | GET | 304 | 87.248.202.1:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?3eb62bd5d68144a3 | unknown | — | — | unknown |
3672 | HelloFont_2.6.0.1.exe | GET | 200 | 163.181.131.227:80 | http://ocsp.digicert.cn/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQhnxEBNL9LgIhfSsTcHsrTt204QgQURNnISjOO01KNp5KUYR%2BayKW37MsCEApQk7nHM8Ze2%2F0DZfo83lU%3D | unknown | binary | 471 b | unknown |
3672 | HelloFont_2.6.0.1.exe | POST | 200 | 47.93.163.171:80 | http://47.93.163.171/ziyou/ClientManagement20200608/api/Trial/Trial | unknown | binary | 79 b | unknown |
3672 | HelloFont_2.6.0.1.exe | POST | 200 | 47.93.163.171:80 | http://back2.hellofont.cn/ziyou/FontActivateManagement/FontActivateManagerHandler.ashx | unknown | binary | 83 b | unknown |
— | — | GET | 200 | 163.181.131.227:80 | http://ocsp.digicert.cn/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQhnxEBNL9LgIhfSsTcHsrTt204QgQURNnISjOO01KNp5KUYR%2BayKW37MsCEAzveKgxR25ARAL57KqbI7E%3D | unknown | binary | 471 b | unknown |
3672 | HelloFont_2.6.0.1.exe | GET | 200 | 163.181.131.227:80 | http://ocsp.digicert.cn/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQhnxEBNL9LgIhfSsTcHsrTt204QgQURNnISjOO01KNp5KUYR%2BayKW37MsCEARG%2BkY12ZetlA459vQU5KE%3D | unknown | binary | 471 b | unknown |
3672 | HelloFont_2.6.0.1.exe | POST | 200 | 47.93.163.171:80 | http://back2.hellofont.cn/ziyou/FontGroupManagement/FontGroupManagerHandler.ashx | unknown | binary | 83 b | unknown |
1080 | svchost.exe | GET | 200 | 87.248.202.1:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?1b8fee253118cbef | unknown | compressed | 65.2 Kb | unknown |
1080 | svchost.exe | GET | 304 | 87.248.202.1:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?3e412f7b4eff0943 | unknown | compressed | 65.2 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3672 | HelloFont_2.6.0.1.exe | 203.205.232.110:443 | open.weixin.qq.com | Tencent Building, Kejizhongyi Avenue | HK | unknown |
3672 | HelloFont_2.6.0.1.exe | 47.93.163.171:80 | back2.hellofont.cn | Hangzhou Alibaba Advertising Co.,Ltd. | CN | unknown |
3672 | HelloFont_2.6.0.1.exe | 87.248.202.1:80 | ctldl.windowsupdate.com | LLNW | NL | unknown |
3672 | HelloFont_2.6.0.1.exe | 163.181.131.227:80 | ocsp.digicert.cn | — | US | unknown |
3672 | HelloFont_2.6.0.1.exe | 43.152.26.104:443 | res.wx.qq.com | ACE | DE | unknown |
3672 | HelloFont_2.6.0.1.exe | 109.244.216.15:443 | lp.open.weixin.qq.com | Shenzhen Tencent Computer Systems Company Limited | CN | unknown |
1080 | svchost.exe | 87.248.202.1:80 | ctldl.windowsupdate.com | LLNW | NL | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
open.weixin.qq.com |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.cn |
| whitelisted |
res.wx.qq.com |
| whitelisted |
lp.open.weixin.qq.com |
| unknown |
back2.hellofont.cn |
| unknown |
hellofontpreview.oss-cn-beijing.aliyuncs.com |
| unknown |