| File name: | file.dll |
| Full analysis: | https://app.any.run/tasks/a5bac4be-b1cd-4c89-8b3b-06bec92d1c85 |
| Verdict: | Malicious activity |
| Analysis date: | January 07, 2026, 13:00:31 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (DLL) (GUI) x86-64, for MS Windows, 6 sections |
| MD5: | 2FA6E8BDF785BF8557A30C0C78D6E0EA |
| SHA1: | 7FCC04A769E5ACE308A14EFFE841B9901021E8AE |
| SHA256: | 0355D064E205480122D3FC15B79D7F9C880A27690DE7F448401C3C34CCEB04D4 |
| SSDEEP: | 98304:vDb5hFmTc/TboIsLaezTfNm+dsz8S9k8BjaFTcCIpOjiIlYjPI4G2nUog5E8yvSV:/e18 |
MALICIOUS
Loads dropped or rewritten executable
- conhost.exe (PID: 7612)
- lsass.exe (PID: 804)
- rundll32.exe (PID: 7580)
- svchost.exe (PID: 6508)
- svchost.exe (PID: 5600)
- conhost.exe (PID: 7860)
- svchost.exe (PID: 7956)
- RUXIMICS.exe (PID: 7984)
- WaaSMedicAgent.exe (PID: 7772)
- MusNotificationUx.exe (PID: 8020)
- PLUGScheduler.exe (PID: 3344)
- svchost.exe (PID: 6712)
- taskhostw.exe (PID: 8168)
- slui.exe (PID: 6000)
- SIHClient.exe (PID: 6424)
- WmiPrvSE.exe (PID: 6640)
- slui.exe (PID: 4624)
- slui.exe (PID: 5156)
- slui.exe (PID: 5632)
- slui.exe (PID: 3112)
- MusNotifyIcon.exe (PID: 8108)
- svchost.exe (PID: 7260)
SUSPICIOUS
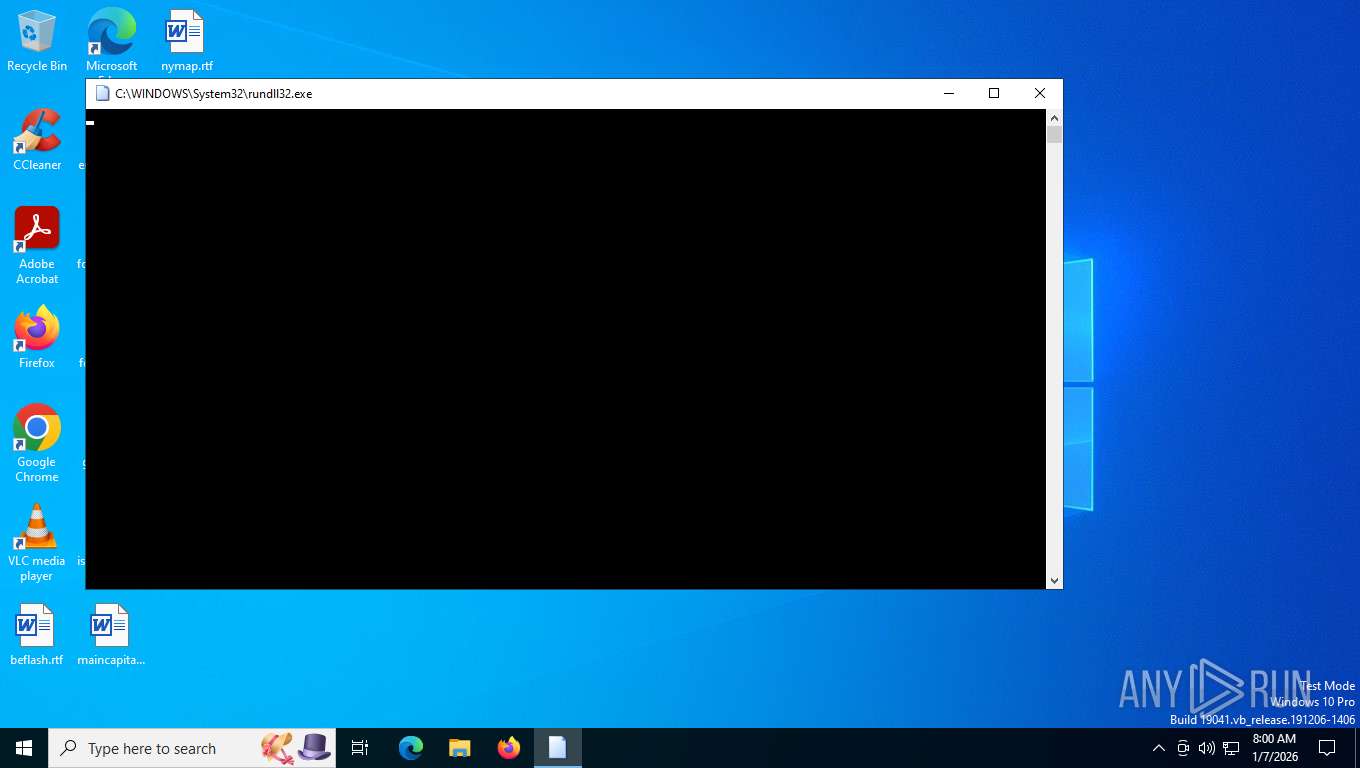
Runs a DLL function by ordinal number
- rundll32.exe (PID: 7580)
The process creates files with name similar to system file names
- rundll32.exe (PID: 7580)
Executable content was dropped or overwritten
- rundll32.exe (PID: 7580)
INFO
The sample compiled with english language support
- rundll32.exe (PID: 7580)
Creates files in the program directory
- MusNotificationUx.exe (PID: 8020)
- RUXIMICS.exe (PID: 7984)
- MusNotifyIcon.exe (PID: 8108)
Reads the computer name
- PLUGScheduler.exe (PID: 3344)
Checks supported languages
- RUXIMICS.exe (PID: 7984)
Reads the time zone
- MusNotificationUx.exe (PID: 8020)
- MusNotifyIcon.exe (PID: 8108)
- WmiPrvSE.exe (PID: 6640)
The sample compiled with german language support
- rundll32.exe (PID: 7580)
The sample compiled with spanish language support
- rundll32.exe (PID: 7580)
The sample compiled with chinese language support
- rundll32.exe (PID: 7580)
The sample compiled with french language support
- rundll32.exe (PID: 7580)
The sample compiled with Italian language support
- rundll32.exe (PID: 7580)
The sample compiled with korean language support
- rundll32.exe (PID: 7580)
The sample compiled with japanese language support
- rundll32.exe (PID: 7580)
The sample compiled with russian language support
- rundll32.exe (PID: 7580)
Checks proxy server information
- slui.exe (PID: 5156)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (57.6) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (36.9) |
| .exe | | | Generic Win/DOS Executable (2.6) |
| .exe | | | DOS Executable Generic (2.6) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2026:01:05 13:23:41+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware, DLL |
| PEType: | PE32+ |
| LinkerVersion: | 2.5 |
| CodeSize: | 2891776 |
| InitializedDataSize: | 3502080 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2bc214 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
Total processes
146
Monitored processes
22
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 804 | C:\WINDOWS\system32\lsass.exe | C:\Windows\System32\lsass.exe | — | wininit.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Local Security Authority Process Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3112 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=NetworkAvailable | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3344 | "C:\Program Files\RUXIM\PLUGscheduler.exe" | C:\Program Files\RUXIM\PLUGScheduler.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Update LifeCycle Component Scheduler Exit code: 0 Version: 10.0.19041.3623 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4624 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=NetworkAvailable | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5156 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5600 | C:\WINDOWS\system32\svchost.exe -k netsvcs -p -s wlidsvc | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5632 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6000 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=NetworkAvailable | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6424 | C:\WINDOWS\System32\sihclient.exe /cv NEg8tTRvXE2gVZzSxOLVaA.0.2 | C:\Windows\System32\SIHClient.exe | upfc.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: SIH Client Exit code: 2379777 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6508 | C:\WINDOWS\system32\svchost.exe -k wusvcs -p -s WaaSMedicSvc | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
33 140
Read events
32 621
Write events
357
Delete events
162
Modification events
| (PID) Process: | (6508) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\WaaS\WaaSMedic\Configuration |
| Operation: | delete value | Name: | ETag |
Value: "66A2A386BBA04BD5A6331A0AD7AF8FD8389BA07DAF02CB8E5F846CAC" | |||
| (PID) Process: | (6508) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\WaaS\WaaSMedic\Configuration |
| Operation: | write | Name: | refreshAfter |
Value: 668AC5CC9E80DC01 | |||
| (PID) Process: | (5600) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\IdentityCRL\ClockData |
| Operation: | write | Name: | ClockTimeSeconds |
Value: FC585E6900000000 | |||
| (PID) Process: | (5600) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\IdentityCRL\ClockData |
| Operation: | write | Name: | TickCount |
Value: 09F70F0000000000 | |||
| (PID) Process: | (6508) svchost.exe | Key: | HKEY_USERS\.DEFAULT\Software\Microsoft\IdentityCRL\Immersive\production\Token\{76236E1A-74C6-4CC0-93CB-9D3E85E5138F} |
| Operation: | write | Name: | DeviceTicket |
Value: 0100000001000000D08C9DDF0115D1118C7A00C04FC297EB0100000063D11DE81CCCDC48974B2C06180EDC5D000000000200000000001066000000010000200000001FB9A3E4F4C2A962F7E2FA68824BEF86F618251DD1CFE04B5D7E68BE9A52B6CB000000000E80000000020000200000003F70337B19AA2D4424EE734896EB7B7FC2803070554B4B2224E2BD3E5197745620060000E71C540662988BFCDD863BBA636527B7B99CC136DAEC170B6869E07FAAFBA4BCED4EB7E955BE46CB4FCAC1C43ED5EA6CAF560DB0F17541441587ADE8014538BF963533249EAB38A1AB8D922B1E98FEEC27862E521A4F92A6BE73771FD22296590B7939581C7A84ED189D8D5E205459D147025F612F4C49A828EE87544E9ED756312B950DE1347A72DB5FBC943F80B8B3743C2A0E7B7D71B15D84F7E7945F710C6DCF9F4126627589A09C1BE798F0BE0A0C7AFC65EF566D4743BAAAF39636CB2B67821CB8658BE56F312D18399078870D569D7A38515834746DFF19C1629B2E25BD077CEF9A065E31D43B857CDBADBEDBC5C738B85E8741D1F8CDE0D2772C5F612F3E4F39AC8FEDABD4F544DBC94EFFB98E84027FC191332CDE08D5CC9070518FFF7C664F543F3D224E36D768D56901BC3AA708638A59D9C5929E7498B417A28352DD3A68B9EC24FADAD11BD416F0B14F6174176657A3A7C1B0ADF209F1B8A38388AD6F3BA26DFC7AC36C5E2CB9008A064F059E179F6A10BEA2BB00FDBCDBF3A2EAF47B81C1733787B4B17A1D5EBFE16BAB5C90E7A1950E9D427DC0D47E8DF0F736FE3405A411764DF0BE91596FF30A2D07E8B92BE6FB9D99D2EB466C45CD647E2D75EE4995EB381BA90A5504B03C6214DA4836D3F03198227FA20B5A56C075B51E13BC0EDCCDB13ED18D766C4CE01AAE12ECE82D9E250CE495038B97579BBEFE36AF40815B6A293CF5B8D8C943E12B71544B138F4C5E9C732E78106F20FF7CA93F14761EF5642E75F2194E3DE5737CC3756DFBD6AB2C3E1996C3D32A7B57F6ACD22366627B340B41C8EC116E21A9BF7695E87F96C347F7326404A132AA9E87FDFC951D35DB386A3D4FDBDD17EA5D0F1ABDD686529B6CD29208EB16F9A82590D918349AD21D2D39AC7FC99664427E7DF6C965A8265BD6055FDFFFE92E4C6357F7524769C4D871C7A4238EF378F92BE57A246E04A8429B8BF1F2E5D9861D13F8BF923A04AC28D9454F5895AB417219CE2BCAE35215302BC1CACD72461F940244A98D368D38CB3B47E583AF0711E25D2286FB7A96ED7A142289729CD68BE530A8E1FD91B98F515FD34C04913FBE2B719C8419E2730145A91E49571DD8C9D256FA1AD302835A44B542B7972FDE8A92E1E22E55F0AF4CCB3E310E39D56C7B0DD2F474E6127A4001B9F488FBD999F66CB41B258A921266CF9C474C0446A0CC83376064F272B44DA0EE38EF4AFBA6B3EF64BDAA40616F625A7AF310CE37045B28AF656CFA3077D63CDD78F16C9617C6634E08372CAD91428623022B774FC59871146DCDD25C1C5FEA87E416819931067B5A92793E3E184F5E1A8F8481FE0A294F972F2A0226D31C2017DFC65BF4C9D8C7BE2F93521A67A559800101179BFBB79ED05F8250B1372721CF5A78EB74F1DA80278A96ECA51CE1CAB8E9B789BED0D6B5D7C57A5BD329B02BCCCDFCEF32A5E1D806C5D1D7306FBDA51D0F6D8FFF1DB3026134F5DA7CBE4402FBB4C25A5F67D24E61E05B07A25514F3EC668F577427916C52FDBA82C39D886EB2D039F9ED5F6C1D56DDF169C665DC3B3EF421B9C2BB4D3B68832CFA81538E73B9BD2108CCD679407DDAC7273B24CD261F828876D3628B29C1AB9B30E830DFA939945EF356CAAF254B035BE99CB3D16F5FD8F75F002E2A6D67179F40DB692269EF30583F0F08DB88C83C2C4D43129D7D90D720553D8334613CEB15A2B2B0EB1BB468DB5A6917EE3EDB8EDDAB7B90564C5654D29CB0FD56BD5B63D712003B01F3EDD0162E03E1EFC09001F78A20524CC5CD1DADB7455A4102AA0BA6A48AEE5CAA69714DE9F5B610A8E312F87160BE73BC1EF08E2CA20AB5787591D29BF478F085693FA8E955DF72B583F666F031269925839B5DED48FEDBDCC842786BF6988D3638D447AB93B8BEFB9C307143B13EE13CDB0B4A18CF5B758516E03A507E2D376ACA470F66267E7AF85F427B3827977F895109EDAAF1300A0CA140ACB9EC993B940423A2CD38270DAC7F3E5D97FEC4D7636F90B155F8404E02782F48B3E0C1C1C9E8E4ACFFD79BCB7574B2D5E439652D67A29D7217A88A47181D03745EE899D03BB739A106014B22A08277DA8FCF941132C9FBFDF5A717AD853CAB6093566694B5007F1045690F3A96408BE91314072D5FEAB9DC5BEDDA50E379D4B4E73D1612E90D7E4814A75869E907CAB19DC78C8AE4DBE19781AC46105A93E44940000000B799ED8298735DE75FB98C1EFED333A4E94BAAE459093587D5AC31EED352049F3665AEE72329DFE7A84EEC469D290686F794B023922480DA74F131256A208F56 | |||
| (PID) Process: | (6508) svchost.exe | Key: | HKEY_USERS\.DEFAULT\Software\Microsoft\IdentityCRL\Immersive\production\Token\{76236E1A-74C6-4CC0-93CB-9D3E85E5138F} |
| Operation: | write | Name: | DeviceId |
Value: 00188014E9A99BE7 | |||
| (PID) Process: | (6508) svchost.exe | Key: | HKEY_USERS\.DEFAULT\Software\Microsoft\IdentityCRL\Immersive\production\Token\{76236E1A-74C6-4CC0-93CB-9D3E85E5138F} |
| Operation: | write | Name: | ApplicationFlags |
Value: 1 | |||
| (PID) Process: | (6508) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\WaaSAssessment |
| Operation: | write | Name: | ETag |
Value: "66A2A38650E5456CA23FBFE2547B163A:40DC28F3:2F2BF702C4" | |||
| (PID) Process: | (6508) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\WaaSAssessment |
| Operation: | write | Name: | refreshInterval |
Value: 360 | |||
| (PID) Process: | (6508) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\WaaSAssessment |
| Operation: | write | Name: | refreshAfter |
Value: 231DBCED0780DC01 | |||
Executable files
2 075
Suspicious files
213
Text files
79
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7580 | rundll32.exe | C:\Users\admin\startup_input\6bea57fb-8dfb-4177-9ae8-42e8b3529933_RuntimeDeviceInstall.dll | executable | |
MD5:8FC840B45813CC5C2A07E3630B62DB34 | SHA256:C407A7D3920DFAC893F61A6205B910DBBF1AA2A013FDDE8137E5614CFB14803C | |||
| 7580 | rundll32.exe | C:\Users\admin\startup_input\@AppHelpToast.png | image | |
MD5:D6F8DD9F561B8A67FFAC2BAD7E989770 | SHA256:89EC548C14582B2BDC7739BC0FA007EA5FD648E1690564638FDC6264103098A7 | |||
| 7580 | rundll32.exe | C:\Users\admin\startup_input\@BackgroundAccessToastIcon.png | image | |
MD5:8E4B25CC8E98F63DBD54176DFAB539E0 | SHA256:66071DBDE879F56F5B4D8EE204FDA2AADCF7E759E3A3C812F33FE3F0B37FB74C | |||
| 7580 | rundll32.exe | C:\Users\admin\startup_input\@bitlockertoastimage.png | image | |
MD5:3937359E324E15F6A7A7092D4DAEBD64 | SHA256:F3B178AD338023AA3CBCB071CC006616E916B5EE31295C19F79C38E0547B4BF6 | |||
| 7580 | rundll32.exe | C:\Users\admin\startup_input\@AudioToastIcon.png | image | |
MD5:82C37C3E27020AF6C2E018E944284676 | SHA256:0B99B2576F1FA0689FF6E03462076F4CA2C36D3B198511F7497FB9C89615C445 | |||
| 7580 | rundll32.exe | C:\Users\admin\startup_input\@EnrollmentToastIcon.png | image | |
MD5:495C1F072039B434827A5FE0D9761E4D | SHA256:1170EBA51C0737181FEE01DF67D3DF68305BD0BDF15779195C2CFA03CA78456E | |||
| 7580 | rundll32.exe | C:\Users\admin\startup_input\@language_notification_icon.png | image | |
MD5:C2A332DE50FE519DA21AFB8BD6E134F4 | SHA256:C08B1B157991539AABAF7936F8BB618A6C5CEA0E2CFAFD7B0723BC7E9461E091 | |||
| 7580 | rundll32.exe | C:\Users\admin\startup_input\@edptoastimage.png | image | |
MD5:2E04FA797218711D9ED5958CD2B656AB | SHA256:383D8CBFCD078B3D661655A816676F86AD6C6C5D61A67767E0AFF47C292BD42E | |||
| 7580 | rundll32.exe | C:\Users\admin\startup_input\@StorageSenseToastIcon.png | image | |
MD5:A3437673F5766635A8378F67645B81C0 | SHA256:6B05FB9F09FDB608DCCE58226B9B7E246A30873906AF8A5FEAC124C371BDA37E | |||
| 7580 | rundll32.exe | C:\Users\admin\startup_input\@VpnToastIcon.png | image | |
MD5:1622DE67156496C78D6B7BE9B471645B | SHA256:22FFCF7B1AA6E0F1DAA4CED8A08FBB8EECE12C3D5E2681EC2C57539A8900C186 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
26
TCP/UDP connections
28
DNS requests
16
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6768 | MoUsoCoreWorker.exe | GET | 304 | 51.124.78.146:443 | https://settings-win.data.microsoft.com/settings/v3.0/OneSettings/Client?OSVersionFull=10.0.19045.4046.amd64fre.vb_release.191206-1406&LocalDeviceID=s%3ABAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&FlightRing=Retail&AttrDataVer=186&OSUILocale=en-US&OSSkuId=48&App=WOSC&AppVer=&IsFlightingEnabled=0&TelemetryLevel=1&DeviceFamily=Windows.Desktop | US | — | — | whitelisted |
6768 | MoUsoCoreWorker.exe | GET | 304 | 51.124.78.146:443 | https://settings-win.data.microsoft.com/settings/v3.0/wsd/muse?ProcessorClockSpeed=3094&FlightIds=&UpdateOfferedDays=4294967295&BranchReadinessLevel=CB&OEMManufacturerName=DELL&IsCloudDomainJoined=0&ProcessorIdentifier=AMD64%20Family%2023%20Model%201%20Stepping%202&sku=48&ActivationChannel=Retail&AttrDataVer=186&IsMDMEnrolled=0&ProcessorCores=6&ProcessorModel=AMD%20Ryzen%205%203500%206-Core%20Processor&TotalPhysicalRAM=6144&PrimaryDiskType=4294967295&FlightingBranchName=&ChassisTypeId=1&OEMModelNumber=DELL&SystemVolumeTotalCapacity=260281&sampleId=95271487&deviceClass=Windows.Desktop&App=muse&DisableDualScan=0&AppVer=10.0&OEMSubModel=J5CR&locale=en-US&IsAlwaysOnAlwaysConnectedCapable=0&ms=0&DefaultUserRegion=244&UpdateServiceUrl=http%3A%2F%2Fneverupdatewindows10.com&osVer=10.0.19045.4046.amd64fre.vb_release.191206-1406&os=windows&deviceId=s%3ABAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&DeferQualityUpdatePeriodInDays=0&ring=Retail&DeferFeatureUpdatePeriodInDays=30 | US | — | — | whitelisted |
6424 | SIHClient.exe | GET | 200 | 13.95.31.18:443 | https://fe3cr.delivery.mp.microsoft.com/clientwebservice/ping | US | — | — | whitelisted |
6424 | SIHClient.exe | GET | 200 | 74.178.240.61:443 | https://slscr.update.microsoft.com/sls/ping | US | — | — | whitelisted |
5600 | svchost.exe | POST | 200 | 20.190.160.4:443 | https://login.live.com/RST2.srf | US | xml | 10.3 Kb | whitelisted |
6508 | svchost.exe | GET | 200 | 40.127.240.158:443 | https://settings-win.data.microsoft.com/settings/v3.0/WSD/WaaSAssessment?os=Windows&osVer=10.0.19041.1.amd64fre.vb_release.191206-&ring=Retail&sku=48&deviceClass=Windows.Desktop&locale=en-US&deviceId=BAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&FlightRing=Retail&TelemetryLevel=1&HidOverGattReg=C%3A%5CWINDOWS%5CSystem32%5CDriverStore%5CFileRepository%5Chidbthle.inf_amd64_9610b4821fdf82a5%5CMicrosoft.Bluetooth.Profiles.HidOverGatt.dll&AppVer=10.0&ProcessorIdentifier=AMD64%20Family%2023%20Model%201%20Stepping%202&OEMModel=DELL&UpdateOfferedDays=562&ProcessorManufacturer=AuthenticAMD&InstallDate=1661339444&OEMModelBaseBoard=&BranchReadinessLevel=CB&OEMSubModel=J5CR&IsCloudDomainJoined=0&DeferFeatureUpdatePeriodInDays=30&IsDeviceRetailDemo=0&FlightingBranchName=&OSUILocale=en-US&DeviceFamily=Windows.Desktop&WuClientVer=10.0.19041.3996&UninstallActive=1&IsFlightingEnabled=0&OSSkuId=48&ProcessorClockSpeed=3094&TotalPhysicalRAM=6144&SecureBootCapable=0&App=WaaSAssessment&ProcessorCores=6&CurrentBranch=vb_release&InstallLanguage=en-US&DeferQualityUpdatePeriodInDays=0&ServicingBranch=CB&OEMName_Uncleaned=DELL&TPMVersion=0&PrimaryDiskTotalCapacity=262144&InstallationType=Client&AttrDataVer=186&ProcessorModel=AMD%20Ryzen%205%203500%206-Core%20Processor&IsEdgeWithChromiumInstalled=1&OSVersion=10.0.19045.4046&IsMDMEnrolled=0&ActivationChannel=Retail&HonorWUfBDeferrals=0&FirmwareVersion=A.40&TrendInstalledKey=1&OSArchitecture=AMD64&DefaultUserRegion=244&UpdateManagementGroup=2 | US | text | 5.48 Kb | whitelisted |
6424 | SIHClient.exe | GET | 304 | 74.178.240.61:443 | https://slscr.update.microsoft.com/SLS/%7BE7A50285-D08D-499D-9FF8-180FDC2332BC%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | US | — | — | whitelisted |
5600 | svchost.exe | POST | 200 | 20.190.160.4:443 | https://login.live.com/RST2.srf | US | xml | 11.0 Kb | whitelisted |
5600 | svchost.exe | POST | 200 | 20.190.160.4:443 | https://login.live.com/RST2.srf | US | xml | 10.3 Kb | whitelisted |
6768 | MoUsoCoreWorker.exe | GET | 200 | 51.124.78.146:443 | https://settings-win.data.microsoft.com/settings/v3.0/FlightSettings/FSService?ProcessorClockSpeed=3094&IsRetailOS=1&OEMManufacturerName=DELL&FlightingPolicyValue=3&EnablePreviewBuilds=4294967295&OSVersionFull=10.0.19045.4046.amd64fre.vb_release.191206-1406&ManagePreviewBuilds=3&BranchReadinessLevelSource=0&AttrDataVer=186&ProcessorCores=6&BranchReadinessLevelRaw=16&TotalPhysicalRAM=6144&TPMVersion=0&OEMModelNumber=DELL&SystemVolumeTotalCapacity=260281&DeviceId=s%3ABAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&App=FSS&AppVer=10.0&SmartActiveHoursState=1&ActiveHoursStart=20&SecureBootCapable=0&ActiveHoursEnd=13&DeviceFamily=Windows.Desktop | US | text | 87.3 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6508 | svchost.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
6768 | MoUsoCoreWorker.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1176 | RUXIMICS.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
3412 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5600 | svchost.exe | 20.190.160.4:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5600 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
6508 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6508 | svchost.exe | 23.216.77.36:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |