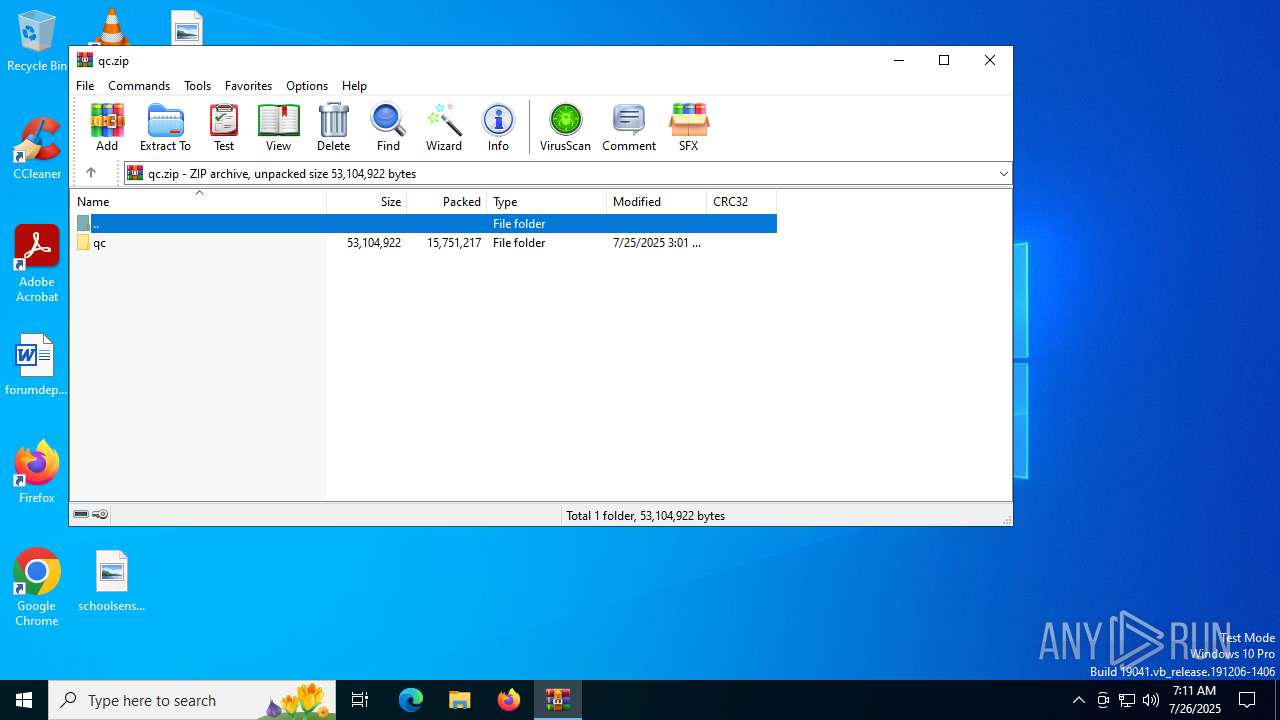
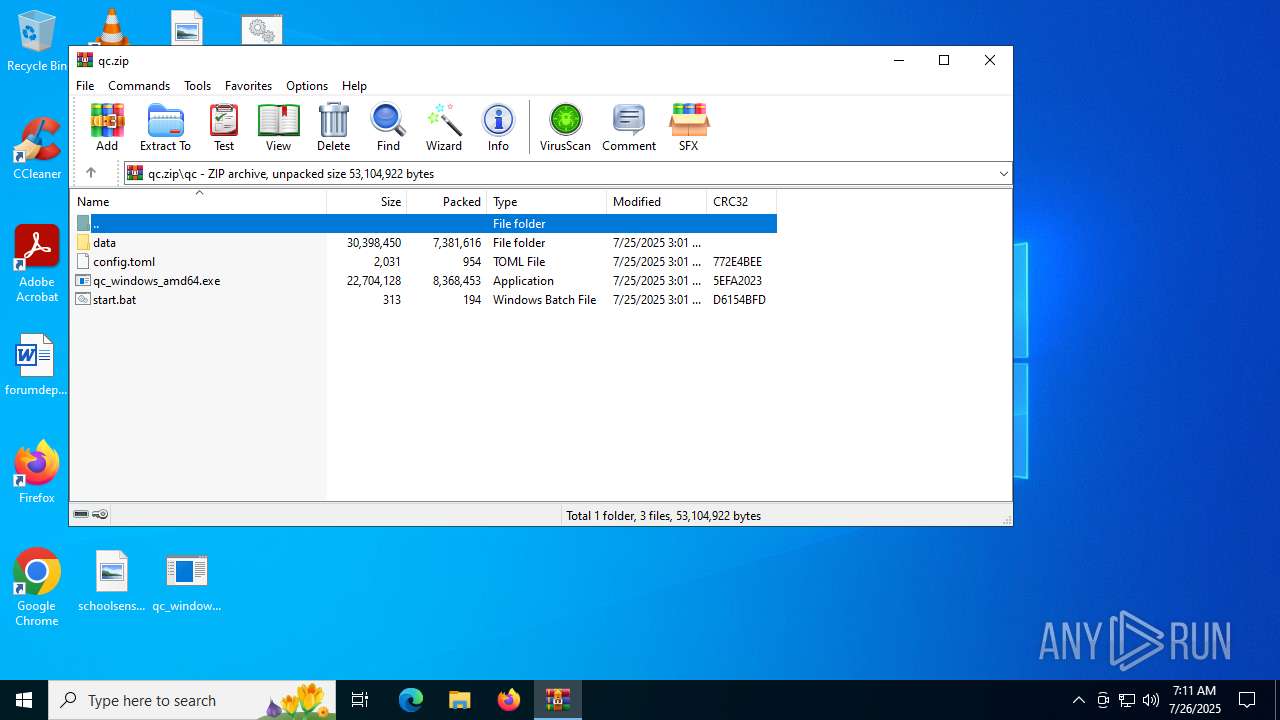
| File name: | qc.zip |
| Full analysis: | https://app.any.run/tasks/4e8c5f92-b296-4dfb-9cdb-c25f9f8084b8 |
| Verdict: | Malicious activity |
| Analysis date: | July 26, 2025, 07:11:14 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract, compression method=store |
| MD5: | D963103CC7BE7E0C0FD7ABFC243E78EC |
| SHA1: | 5073AB73E967E2F6189A661CDEBF1936B205C589 |
| SHA256: | 03519778B609D4F7AAF6A01FE5ACEC44944B96250B244FB5F4750D2BE30EBB92 |
| SSDEEP: | 196608:+5xS/3bh9uf17NISE9PY4rJx9nOVzZFw2N:j3tU1ZISEdVr5OTFwG |
MALICIOUS
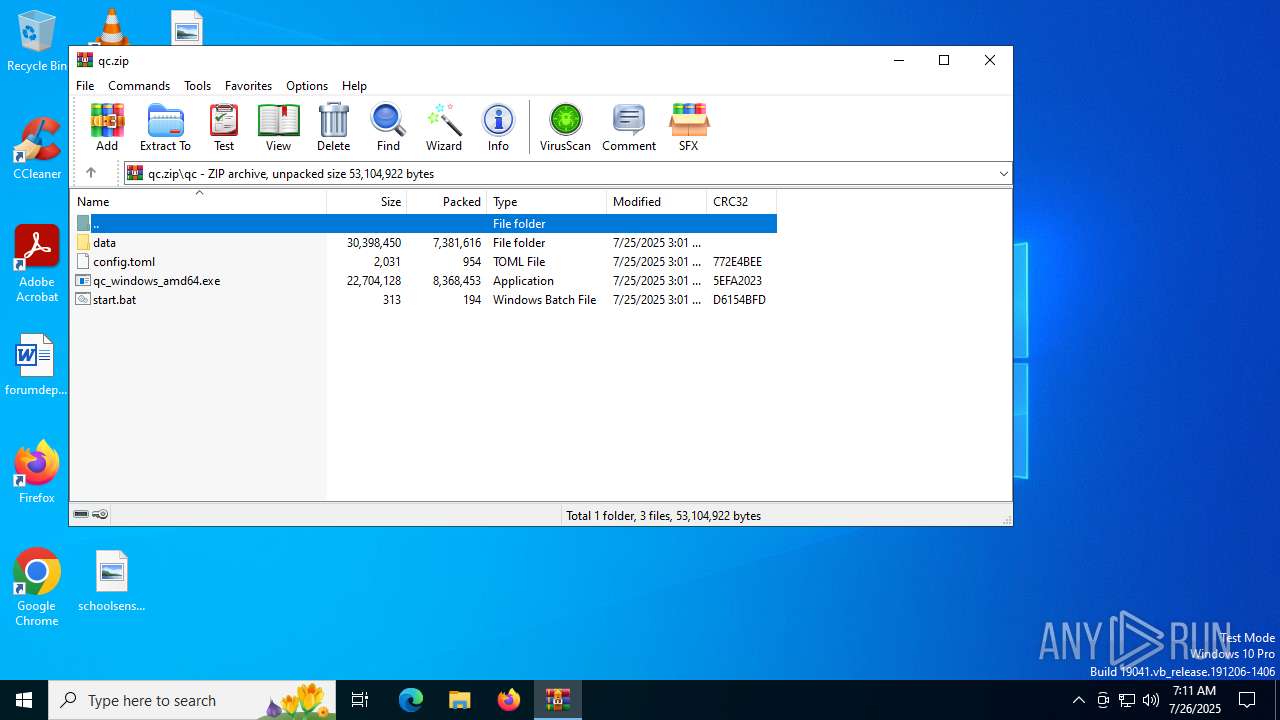
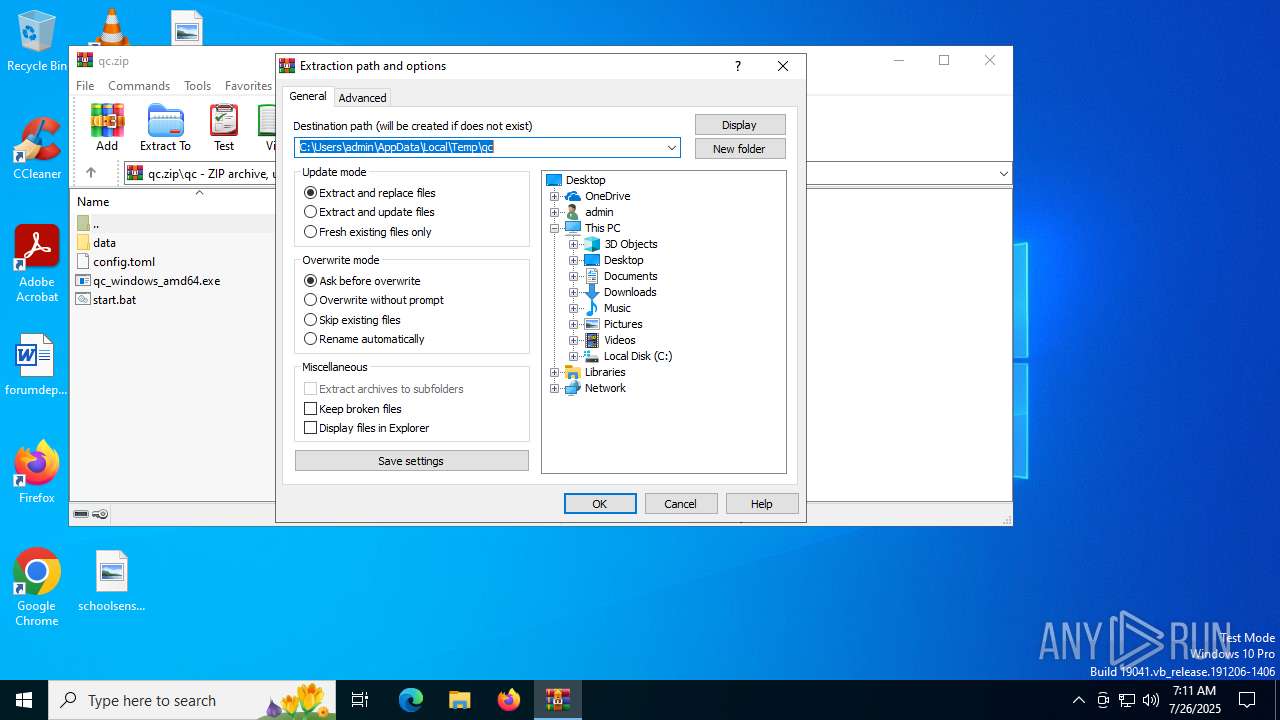
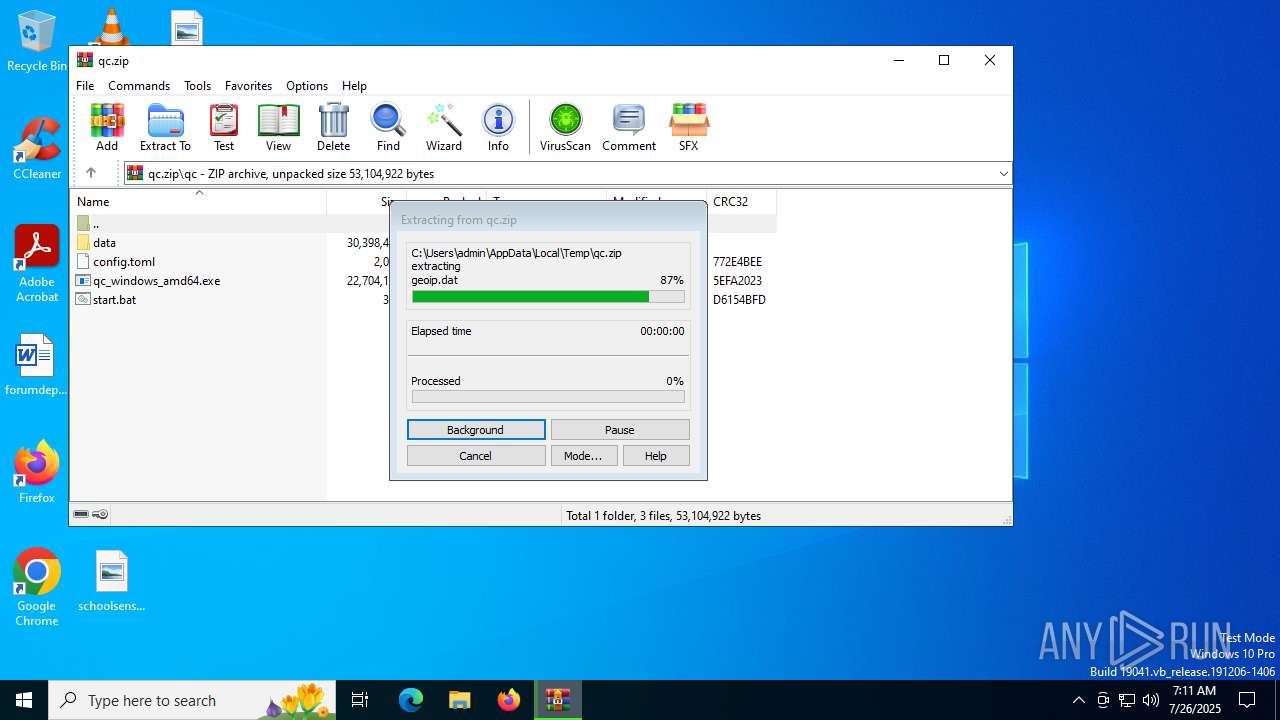
Generic archive extractor
- WinRAR.exe (PID: 2848)
Run PowerShell with an invisible window
- powershell.exe (PID: 6668)
SUSPICIOUS
Connects to unusual port
- qc_windows_amd64.exe (PID: 6344)
- qc_windows_amd64.exe (PID: 6756)
Checks for external IP
- qc_windows_amd64.exe (PID: 6344)
- qc_windows_amd64.exe (PID: 6756)
There is functionality for taking screenshot (YARA)
- qc_windows_amd64.exe (PID: 6344)
There is functionality for VM detection antiVM strings (YARA)
- qc_windows_amd64.exe (PID: 6344)
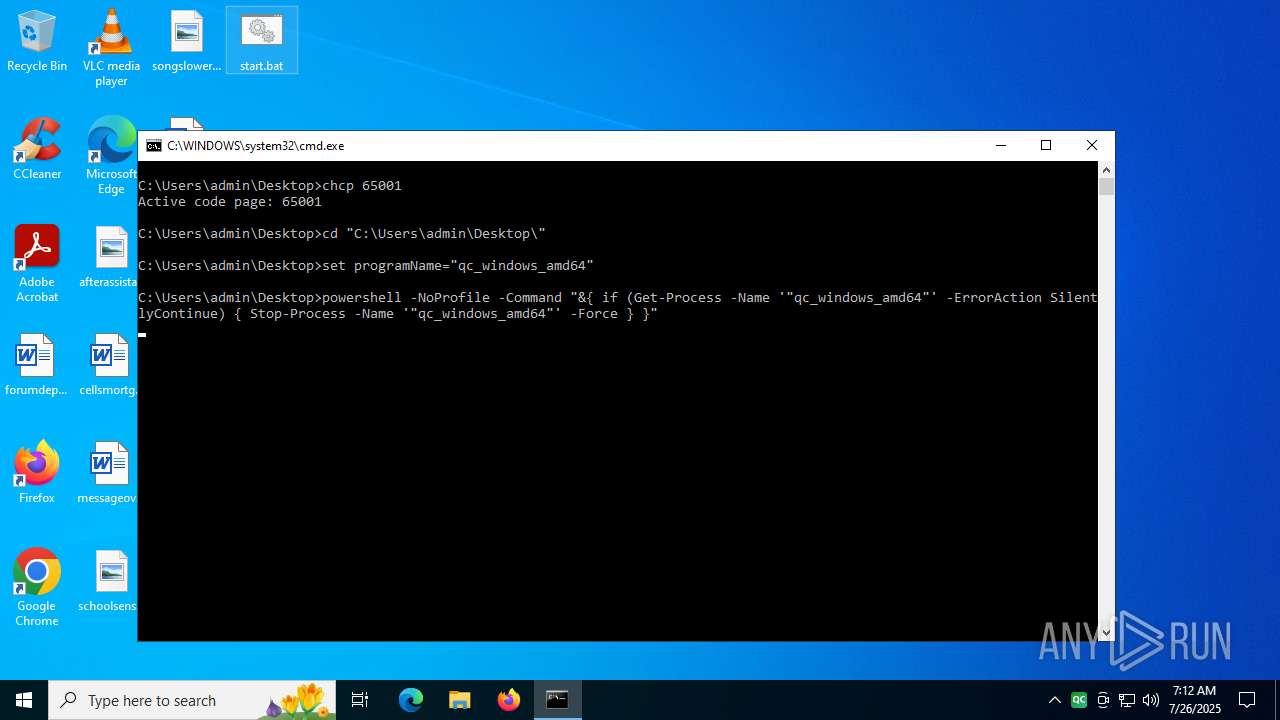
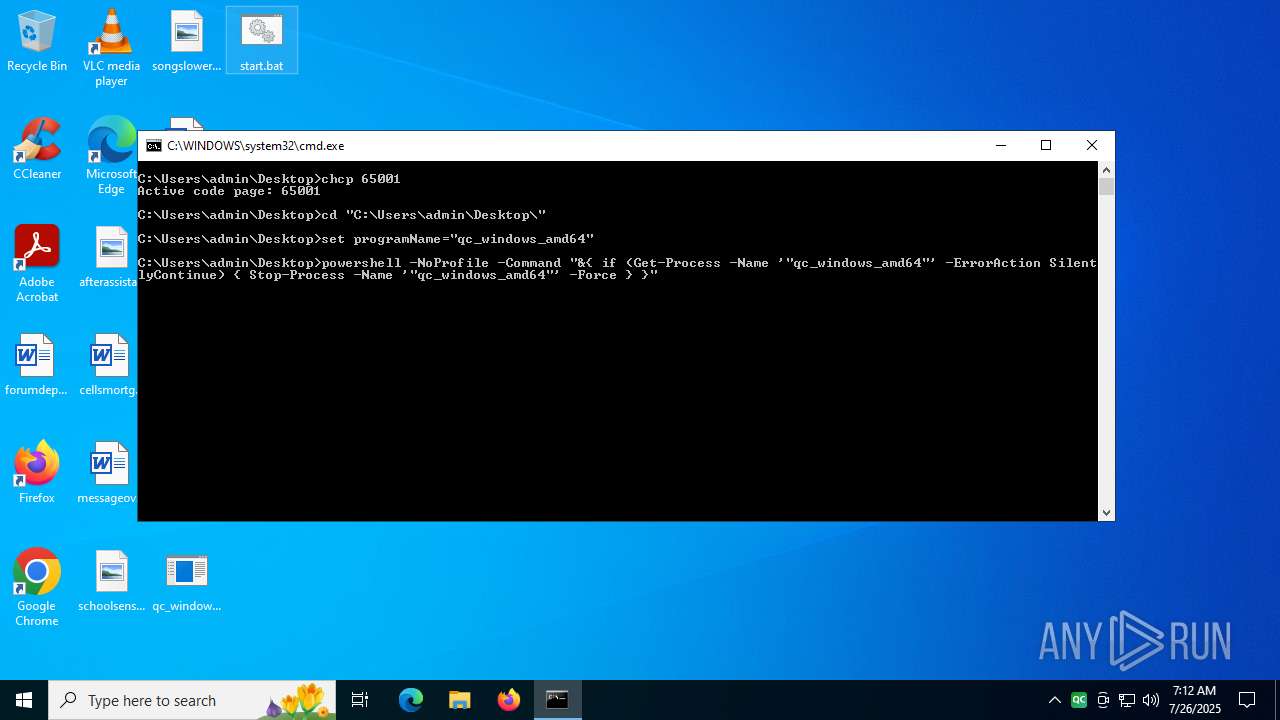
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 3836)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 3836)
Starts process via Powershell
- powershell.exe (PID: 6668)
Kill processes via PowerShell
- powershell.exe (PID: 7000)
Hides errors and continues executing the command without stopping
- powershell.exe (PID: 7000)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 3836)
Starts application with an unusual extension
- cmd.exe (PID: 3836)
Get information on the list of running processes
- cmd.exe (PID: 3836)
INFO
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2848)
Manual execution by a user
- qc_windows_amd64.exe (PID: 6344)
- cmd.exe (PID: 3836)
Reads the software policy settings
- qc_windows_amd64.exe (PID: 6344)
- qc_windows_amd64.exe (PID: 6756)
Checks supported languages
- qc_windows_amd64.exe (PID: 6344)
- qc_windows_amd64.exe (PID: 6756)
- chcp.com (PID: 6808)
Reads the computer name
- qc_windows_amd64.exe (PID: 6344)
- qc_windows_amd64.exe (PID: 6756)
Reads the machine GUID from the registry
- qc_windows_amd64.exe (PID: 6344)
- qc_windows_amd64.exe (PID: 6756)
Create files in a temporary directory
- qc_windows_amd64.exe (PID: 6344)
Attempting to connect via WebSocket
- qc_windows_amd64.exe (PID: 6344)
- qc_windows_amd64.exe (PID: 6756)
Application based on Golang
- qc_windows_amd64.exe (PID: 6344)
Detects GO elliptic curve encryption (YARA)
- qc_windows_amd64.exe (PID: 6344)
Changes the display of characters in the console
- cmd.exe (PID: 3836)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2025:07:25 23:01:32 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | qc/ |
Total processes
148
Monitored processes
12
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2148 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | qc_windows_amd64.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2848 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\qc.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 3836 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\Desktop\start.bat" " | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5300 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5684 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6344 | "C:\Users\admin\Desktop\qc_windows_amd64.exe" | C:\Users\admin\Desktop\qc_windows_amd64.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221225786 Modules
| |||||||||||||||
| 6668 | powershell -NoProfile -Command "&{ Start-Process './"qc_windows_amd64"' -WindowStyle Hidden }" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6756 | "C:\Users\admin\Desktop\qc_windows_amd64.exe" | C:\Users\admin\Desktop\qc_windows_amd64.exe | powershell.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 6808 | chcp 65001 | C:\Windows\System32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Change CodePage Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6812 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | qc_windows_amd64.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
22 564
Read events
22 528
Write events
23
Delete events
13
Modification events
| (PID) Process: | (2848) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2848) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2848) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (2848) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (2848) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (2848) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\qc.zip | |||
| (PID) Process: | (2848) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2848) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2848) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2848) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
1
Suspicious files
1
Text files
8
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2848 | WinRAR.exe | C:\Users\admin\Desktop\data\geoip.dat | — | |
MD5:— | SHA256:— | |||
| 2848 | WinRAR.exe | C:\Users\admin\Desktop\data\geosite.dat | — | |
MD5:— | SHA256:— | |||
| 2848 | WinRAR.exe | C:\Users\admin\Desktop\qc_windows_amd64.exe | executable | |
MD5:AE86CC4CAF04D10D2225AE416A28319E | SHA256:EF33252AD12E635DFE864191FAA2DD739F40D10D2F5CF00B3E2A31E8E7540DBB | |||
| 2848 | WinRAR.exe | C:\Users\admin\Desktop\config.toml | text | |
MD5:D75F71321B4B66C937218C7012E5440A | SHA256:C73C0EA67B57B557FD3FE3482E8336BDACB3EAEE348F83288F237A21F61F7FE1 | |||
| 6344 | qc_windows_amd64.exe | C:\Users\admin\AppData\Local\Temp\systray_temp_icon_205824fc9cbce20a89232e8a7e1dc45c | image | |
MD5:205824FC9CBCE20A89232E8A7E1DC45C | SHA256:CF985E90B7C56A4514B79C5959FA991FBFB6CF4B46C36B9FDB140DD88D712D06 | |||
| 6668 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_ld0xl51f.dzt.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7000 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:11CCEBCE9C509DCDA563D21CFD820413 | SHA256:5CDF02579BA73C4F29FC455F1DA49A3CB99116CD3A6A98D742E4F86D97E6FF92 | |||
| 7000 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_trb4y4vn.no2.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6668 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_sall1hop.amf.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 2848 | WinRAR.exe | C:\Users\admin\Desktop\start.bat | text | |
MD5:50DDD8CD34CC6CFA0C4F751869C10FEC | SHA256:B282F0C68430839745D9D0E3C9B35F5AC59D4C2B173DA75260A3E6B3FF04F029 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1 145
TCP/UDP connections
3 131
DNS requests
219
Threats
1 900
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4032 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6344 | qc_windows_amd64.exe | GET | 101 | 156.238.18.239:8880 | http://yd.laoyoutiao.link:8880/TelegramU0001F1E8U0001F1F3%20@MxlShare%20@WangCai2%20/ | unknown | — | — | unknown |
6344 | qc_windows_amd64.exe | GET | 400 | 104.19.222.79:2096 | http://wwwspeedtestnetwhiteberinsistomd6625996s08.gorgeserver1.ir:2096/security=tls | unknown | — | — | unknown |
6344 | qc_windows_amd64.exe | GET | 101 | 156.238.18.76:8880 | http://yd.laoyoutiao.link:8880/Telegram%F0%9F%87%A8%F0%9F%87%B3%20@MxlShare%20@WangCai2%20/?ed=2560fp=chrome | unknown | — | — | unknown |
6344 | qc_windows_amd64.exe | GET | 400 | 104.19.223.79:2096 | http://wwwspeedtestnetwhiteberinsistomd6625996s08.gorgeserver1.ir:2096/security=tls | unknown | — | — | unknown |
6344 | qc_windows_amd64.exe | GET | 101 | 156.238.18.106:8880 | http://yd.laoyoutiao.link:8880/Telegram%F0%9F%87%A8%F0%9F%87%B3%20@MxlShare%20@WangCai2%20/?ed=2560fp=chrome | unknown | — | — | unknown |
6344 | qc_windows_amd64.exe | GET | 101 | 104.17.148.22:2082 | http://novinsoft.ir.oradoshop.com.persiangsm.ir.digikala.com.abadis.ir.shad.ir.divar.ir.downloadly.com.aparat.com.cafebazar.ir.varzesh3.com.ninisite.com.abadis.ir.bama.ir.p30download.ir.telewebion.bmi.ir.shad.ir.mayket.com.ninisite.top.:2082/@spikevpn-@spikevpn-@spikevpn-@spikevpn-@spikevpn-@spikevpn | unknown | — | — | unknown |
6344 | qc_windows_amd64.exe | GET | 404 | 104.17.148.22:80 | http://Www.speedtest.net.developsp.ir.vegaskala.com./@Shh_Proxy----@Shh_Proxy----@Shh_Proxy----@Shh_Proxy----@Shh_Proxy----@Shh_Proxy----@Shh_Proxy----@Shh_Proxy----@Shh_Proxy----@Shh_Proxy----@Shh_Proxy----@Shh_Proxy | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
7008 | RUXIMICS.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5944 | MoUsoCoreWorker.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4032 | svchost.exe | 20.190.159.73:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4032 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
1268 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1268 | svchost.exe | 23.216.77.6:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
hub.gitmirror.com |
| unknown |
ignacio.ns.cloudflare.com |
| whitelisted |
sullivan.ns.cloudflare.com |
| whitelisted |
thaddeus.ns.cloudflare.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
6344 | qc_windows_amd64.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (whatismyipaddress .com) |
6344 | qc_windows_amd64.exe | Not Suspicious Traffic | INFO [ANY.RUN] Websocket Upgrade Request |
6344 | qc_windows_amd64.exe | Not Suspicious Traffic | INFO [ANY.RUN] Websocket Upgrade Request |
6344 | qc_windows_amd64.exe | Not Suspicious Traffic | INFO [ANY.RUN] Websocket Upgrade Request |
6344 | qc_windows_amd64.exe | Not Suspicious Traffic | INFO [ANY.RUN] Websocket Upgrade Request |
6344 | qc_windows_amd64.exe | Not Suspicious Traffic | INFO [ANY.RUN] Websocket Upgrade Request |
6344 | qc_windows_amd64.exe | Not Suspicious Traffic | INFO [ANY.RUN] Websocket Upgrade Request |
6344 | qc_windows_amd64.exe | Not Suspicious Traffic | INFO [ANY.RUN] Websocket Upgrade Request |
6344 | qc_windows_amd64.exe | Not Suspicious Traffic | INFO [ANY.RUN] Websocket Upgrade Request |