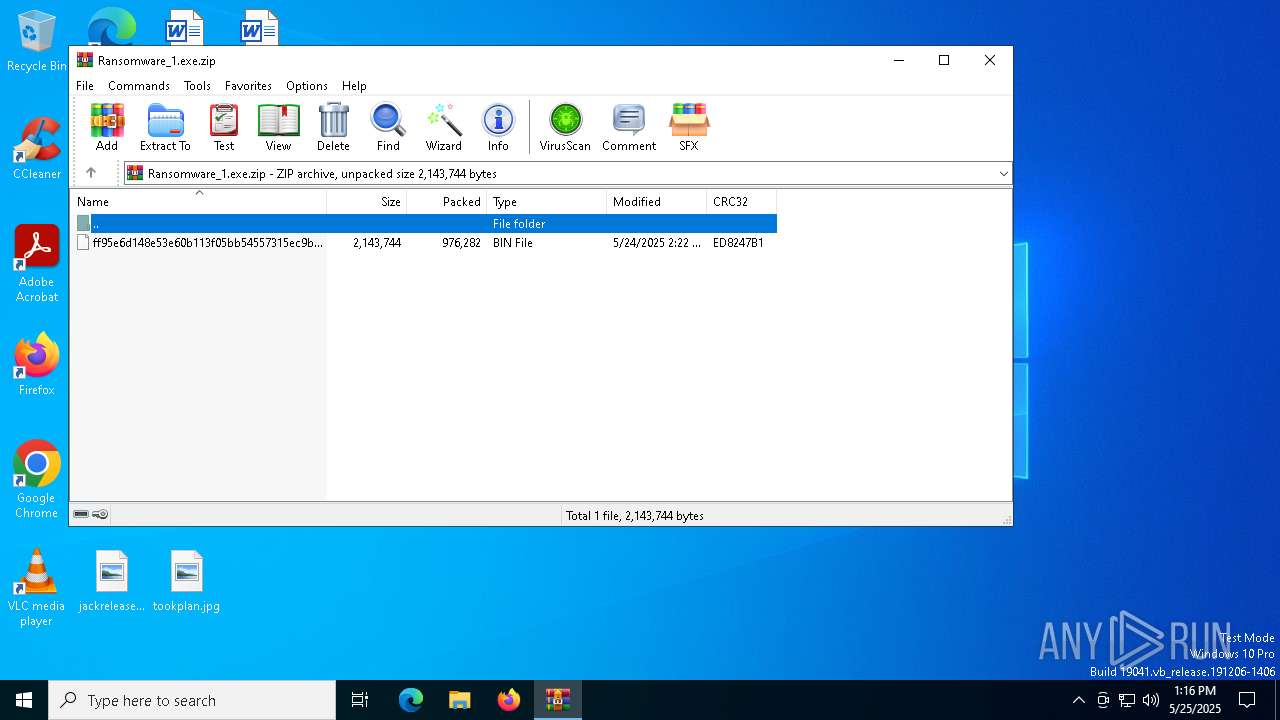
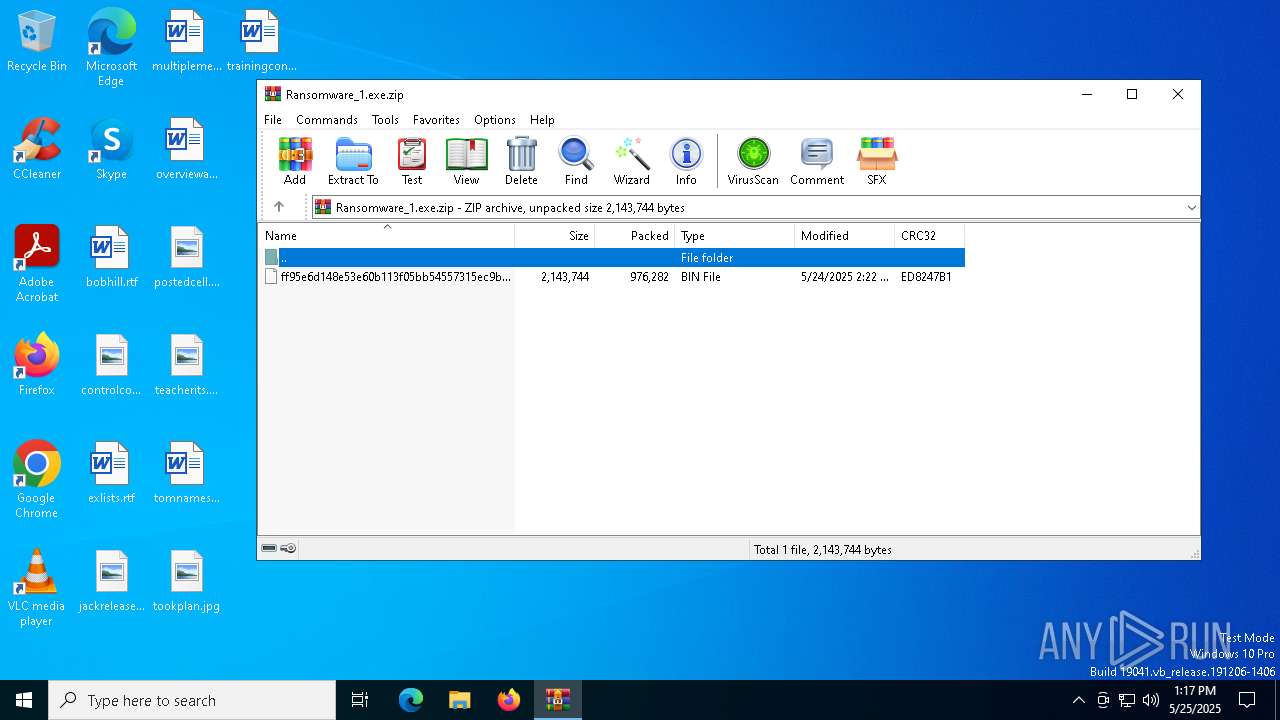
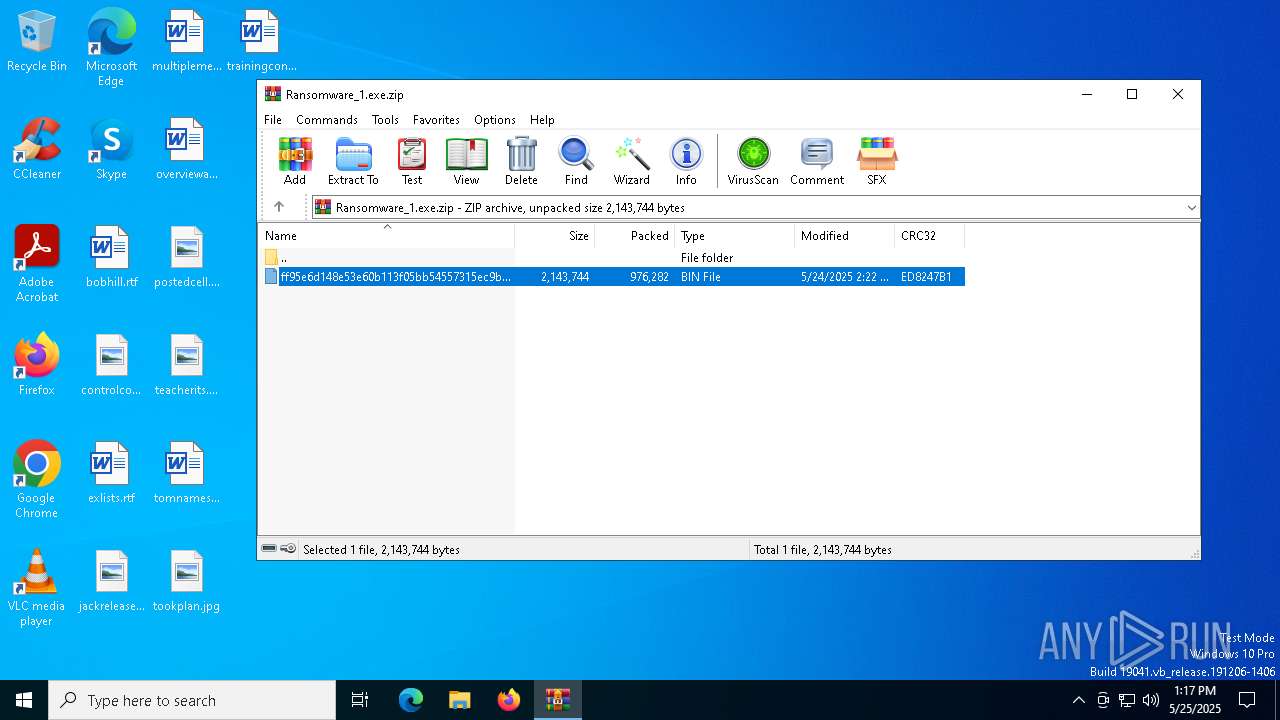
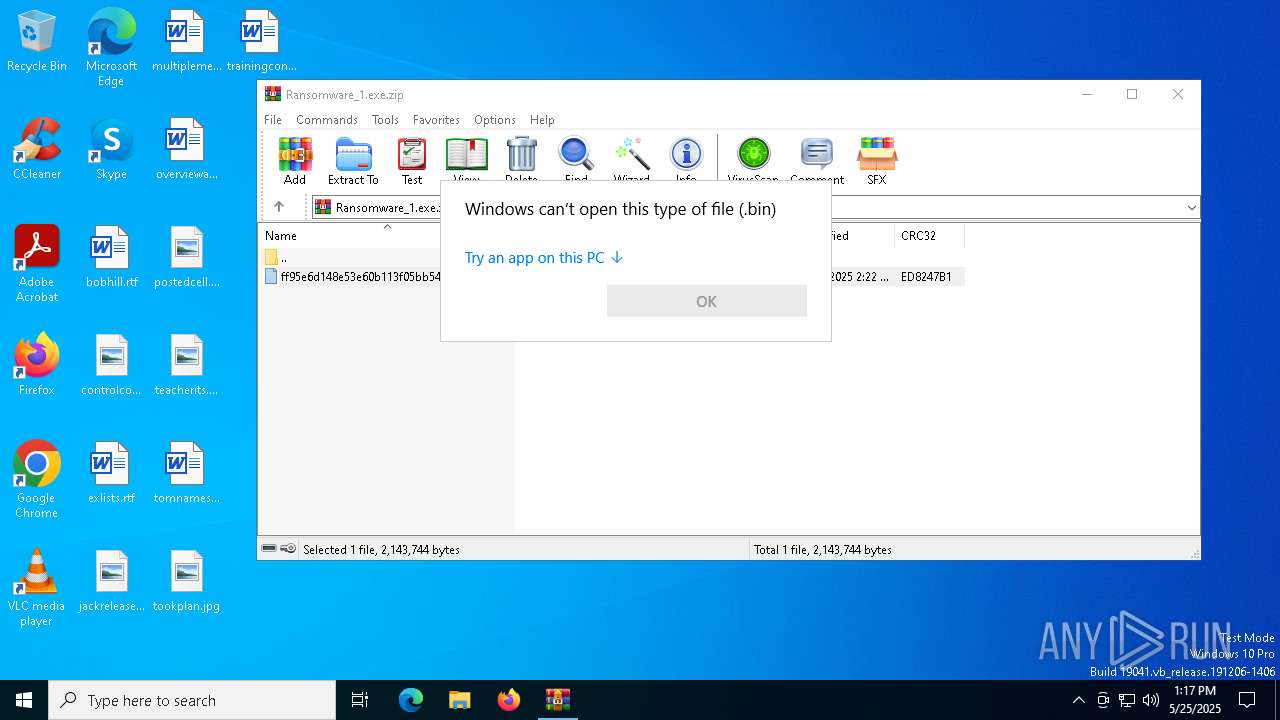
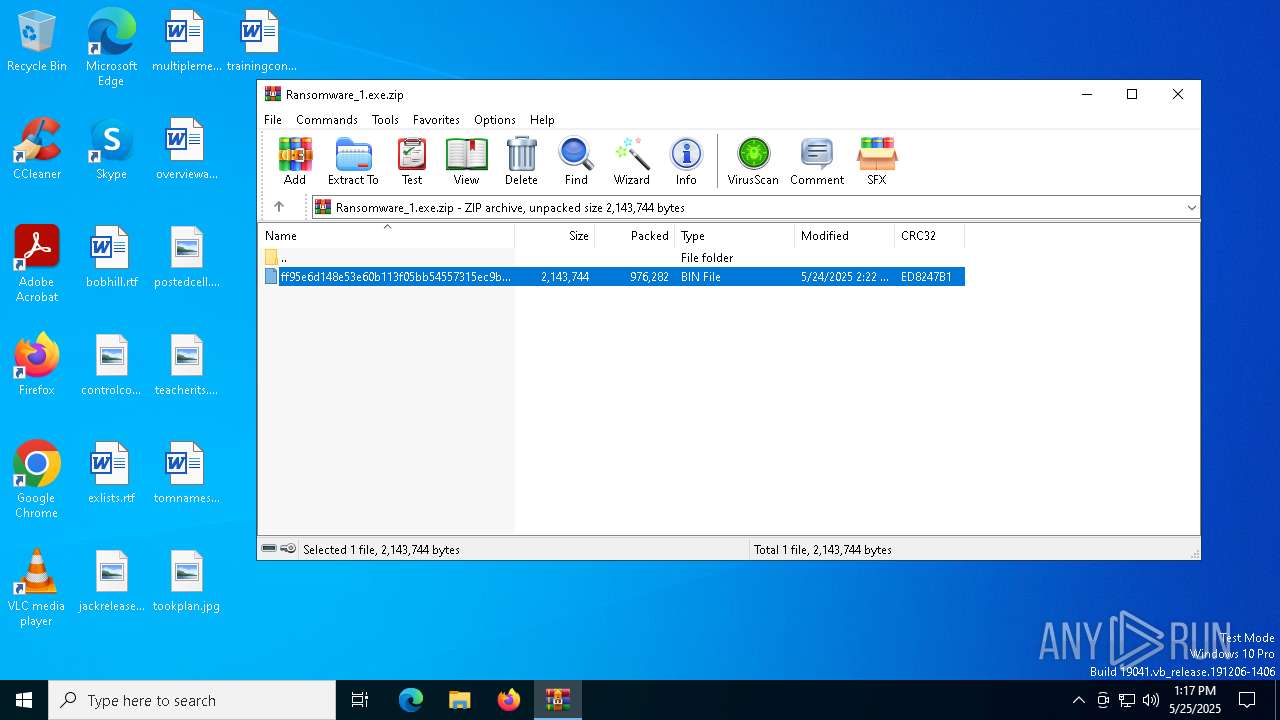
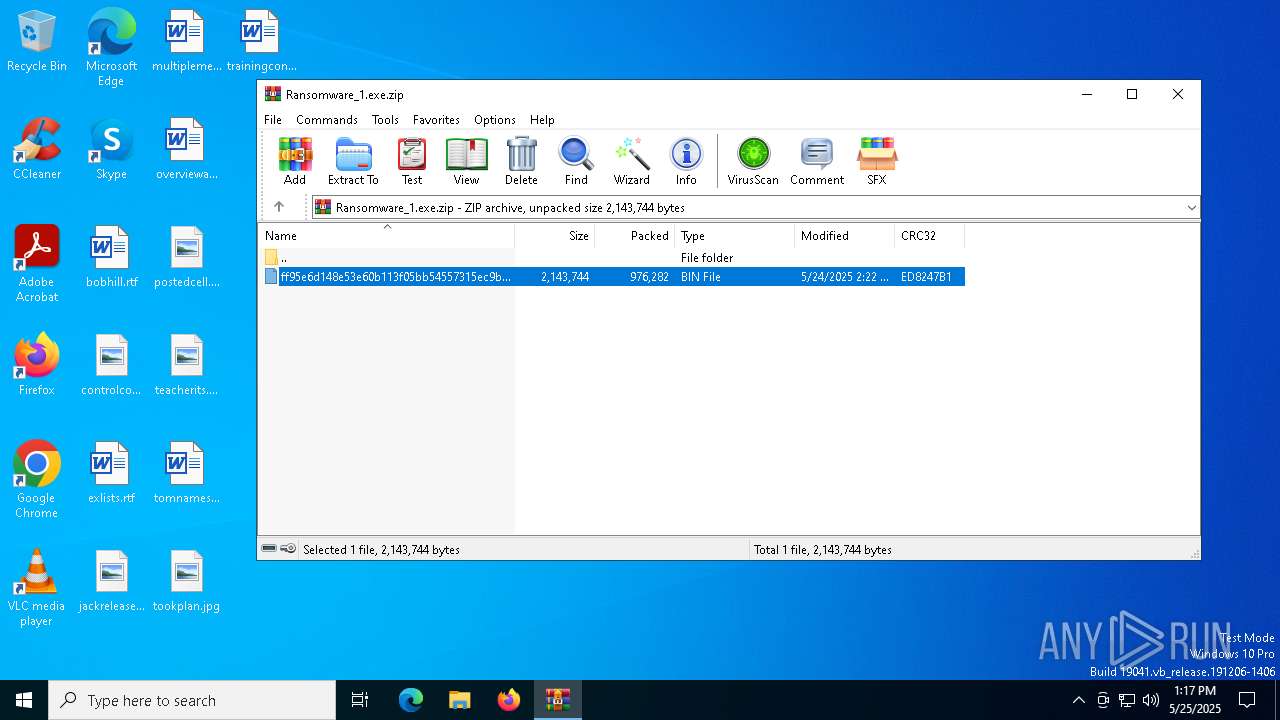
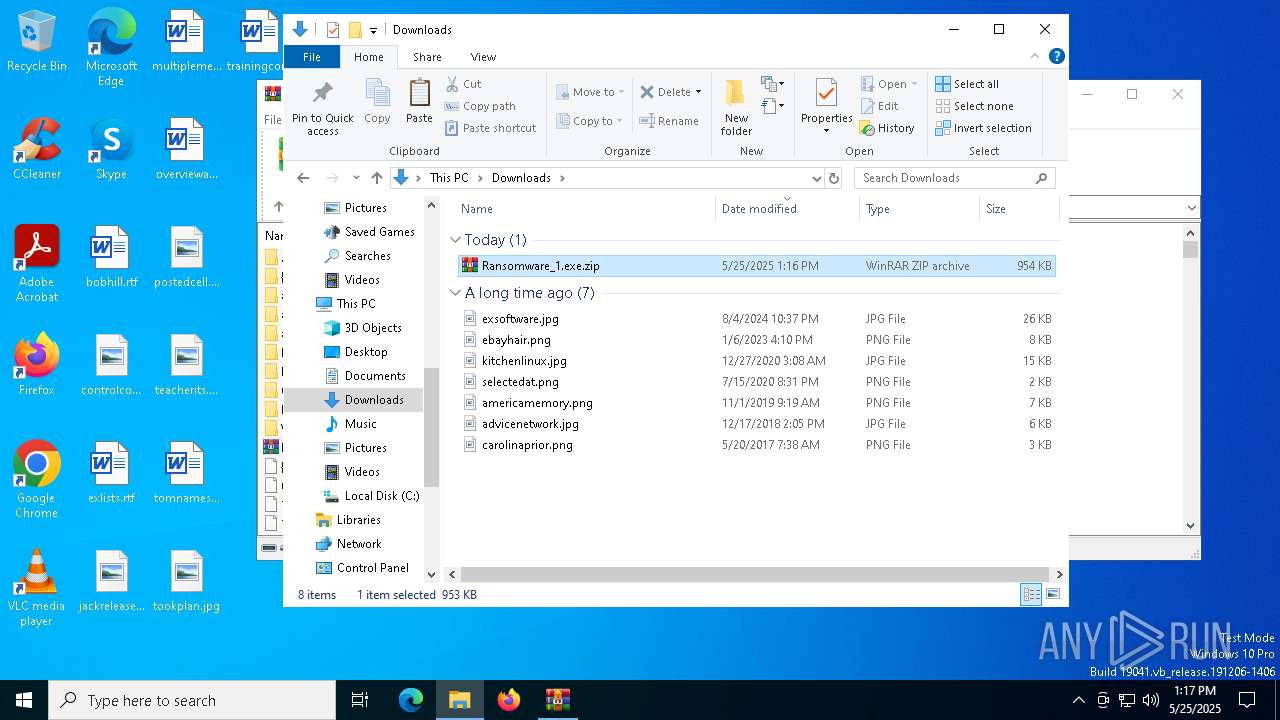
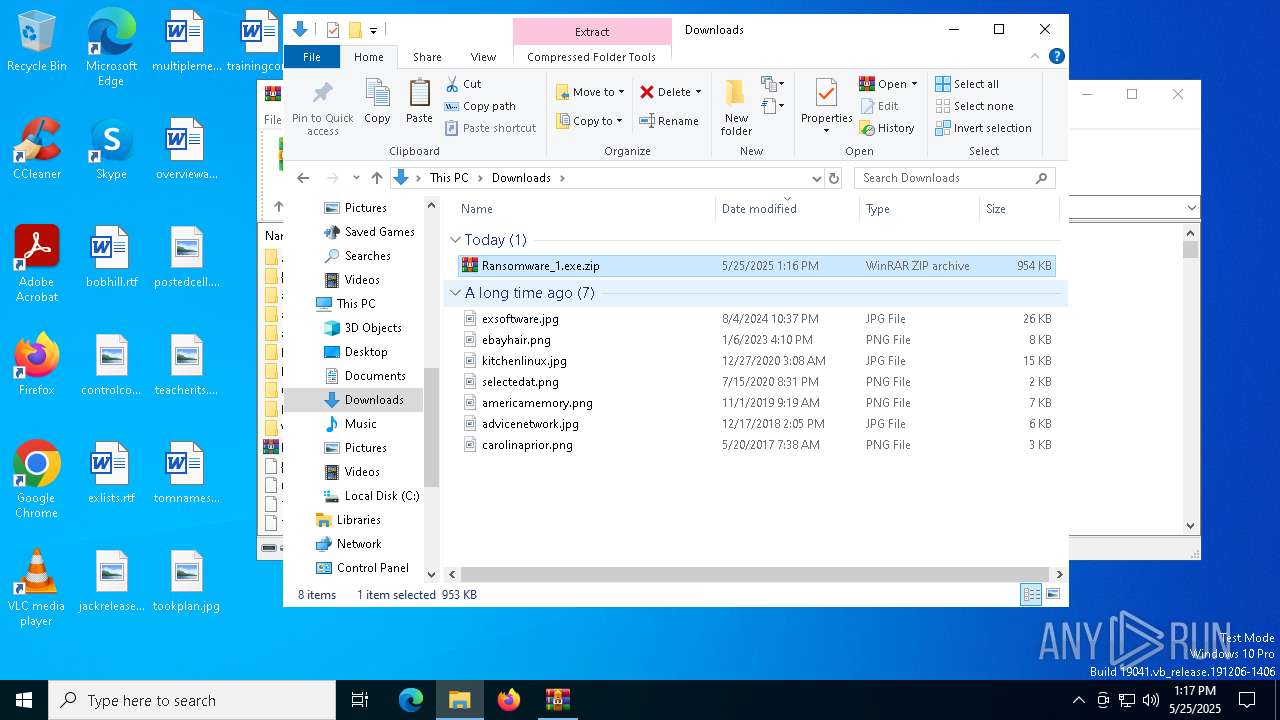
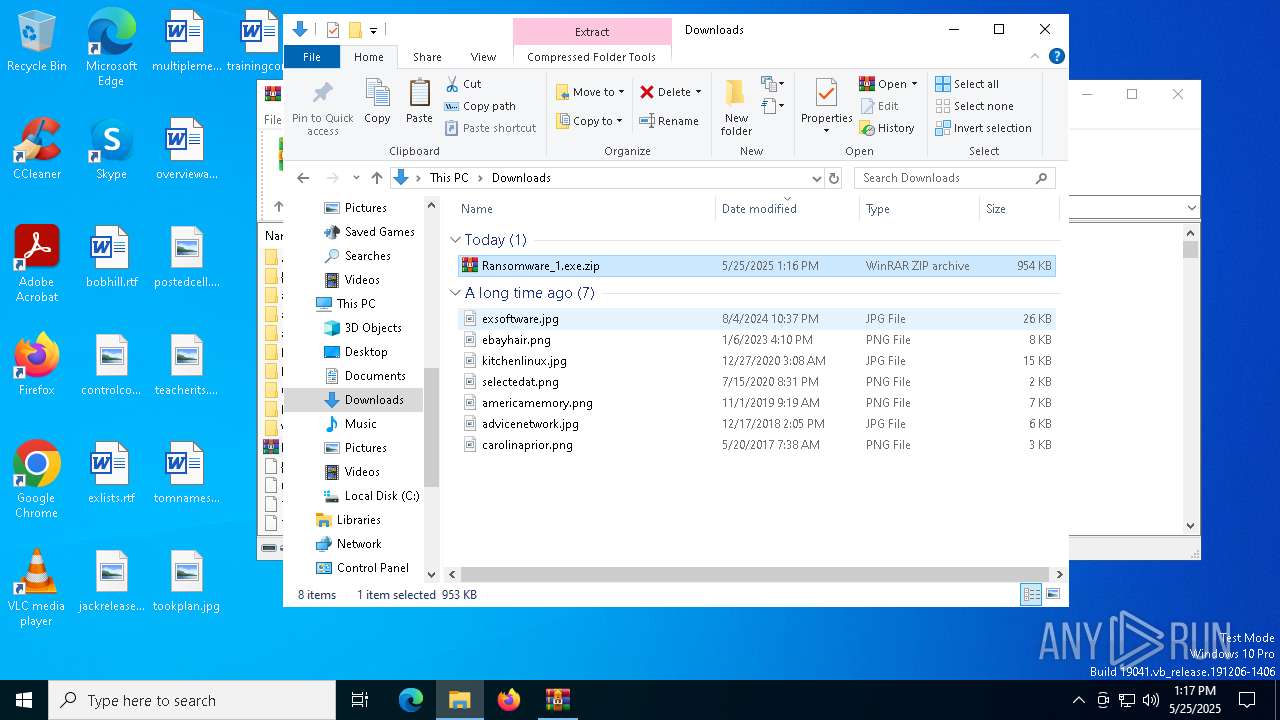
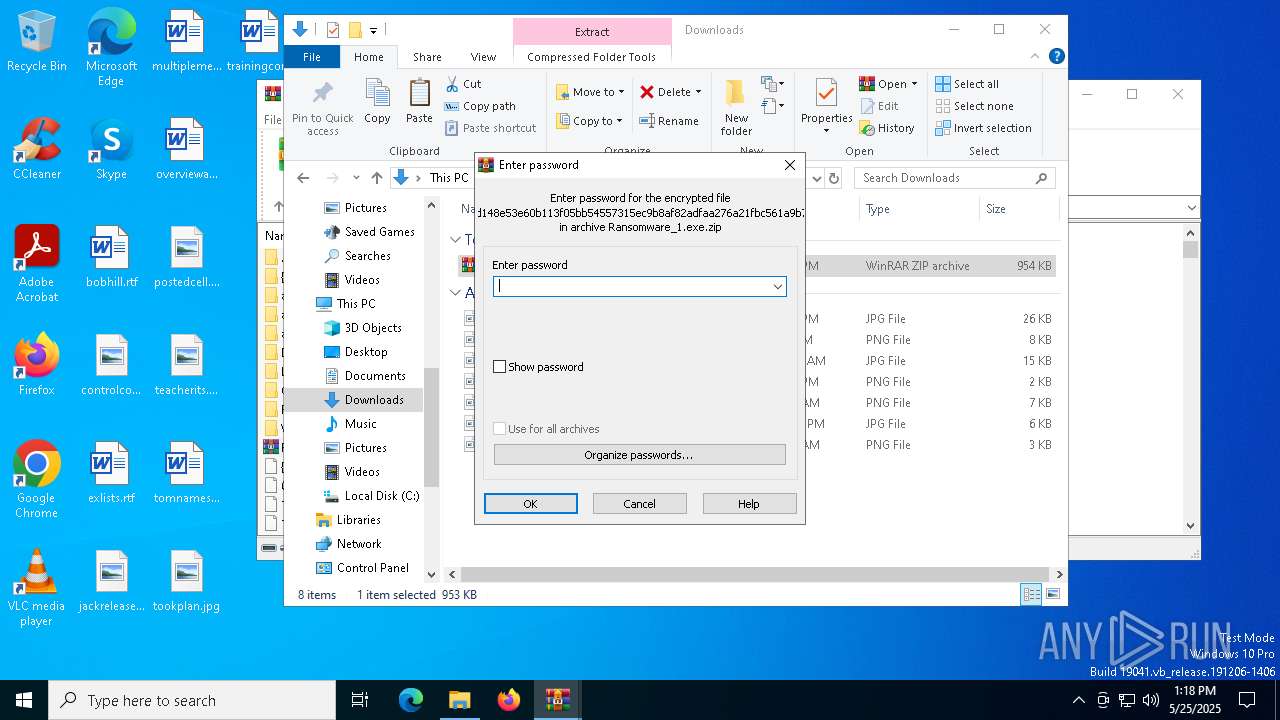
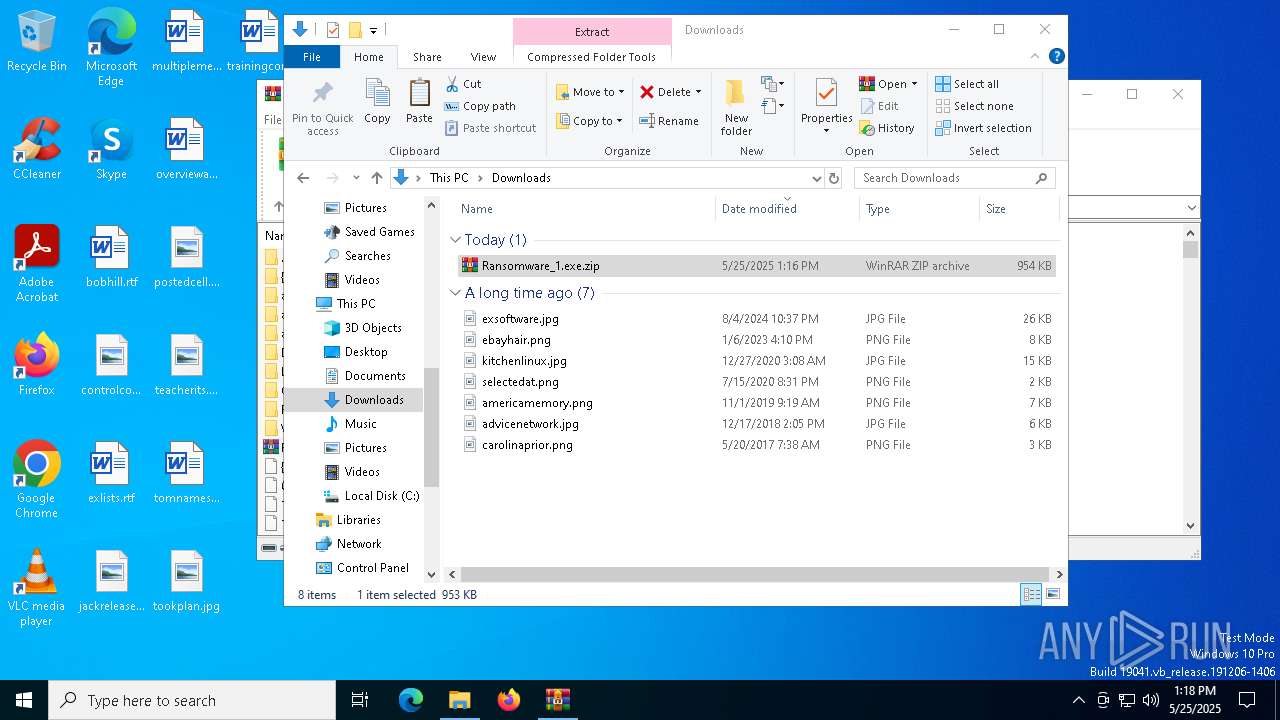
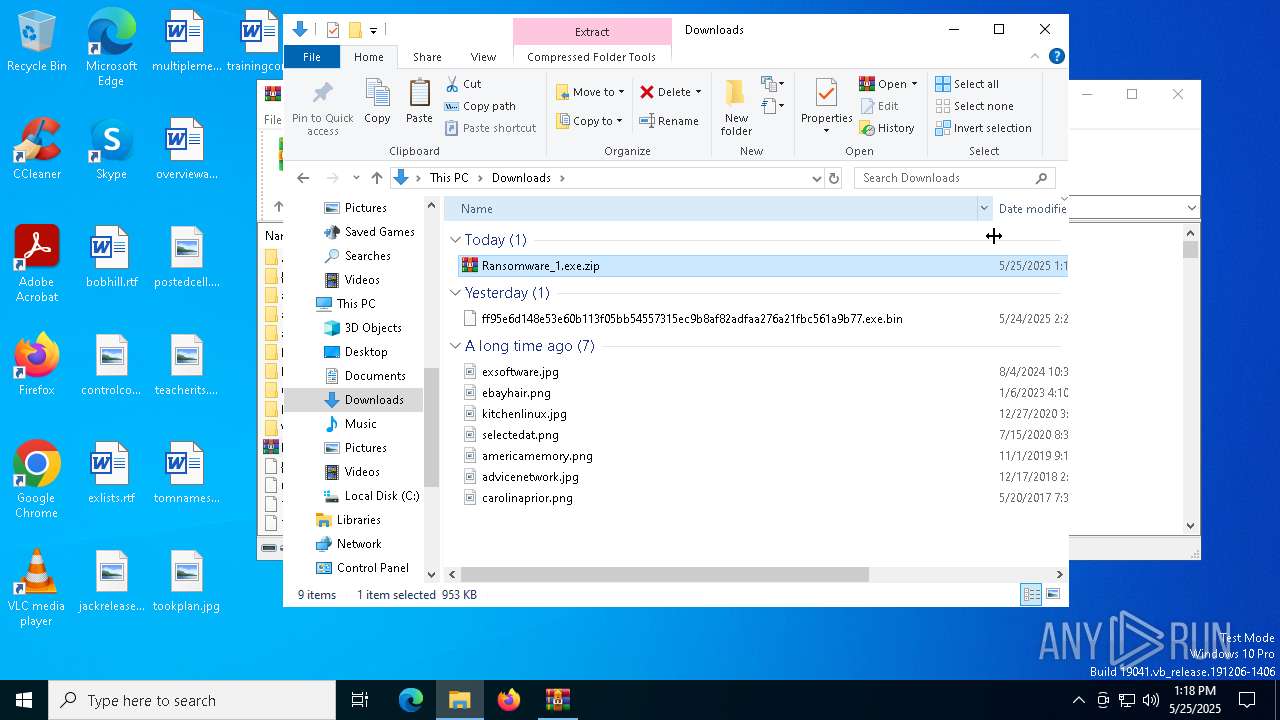
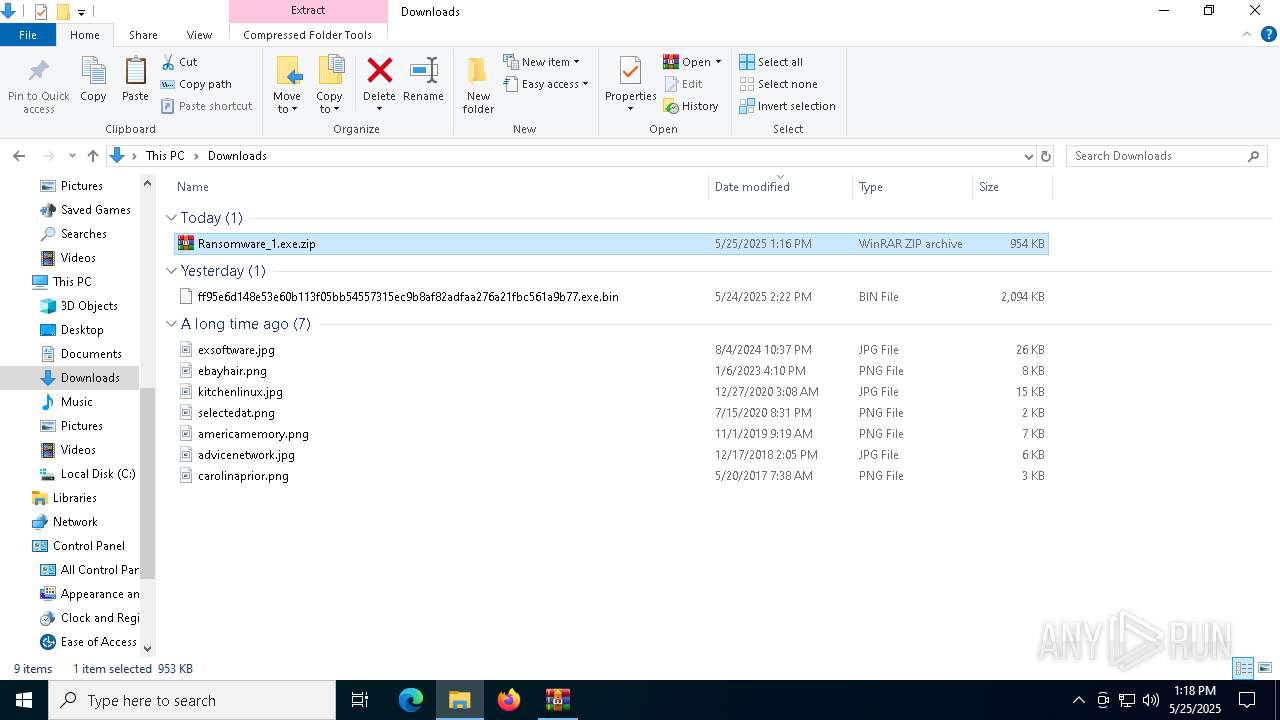
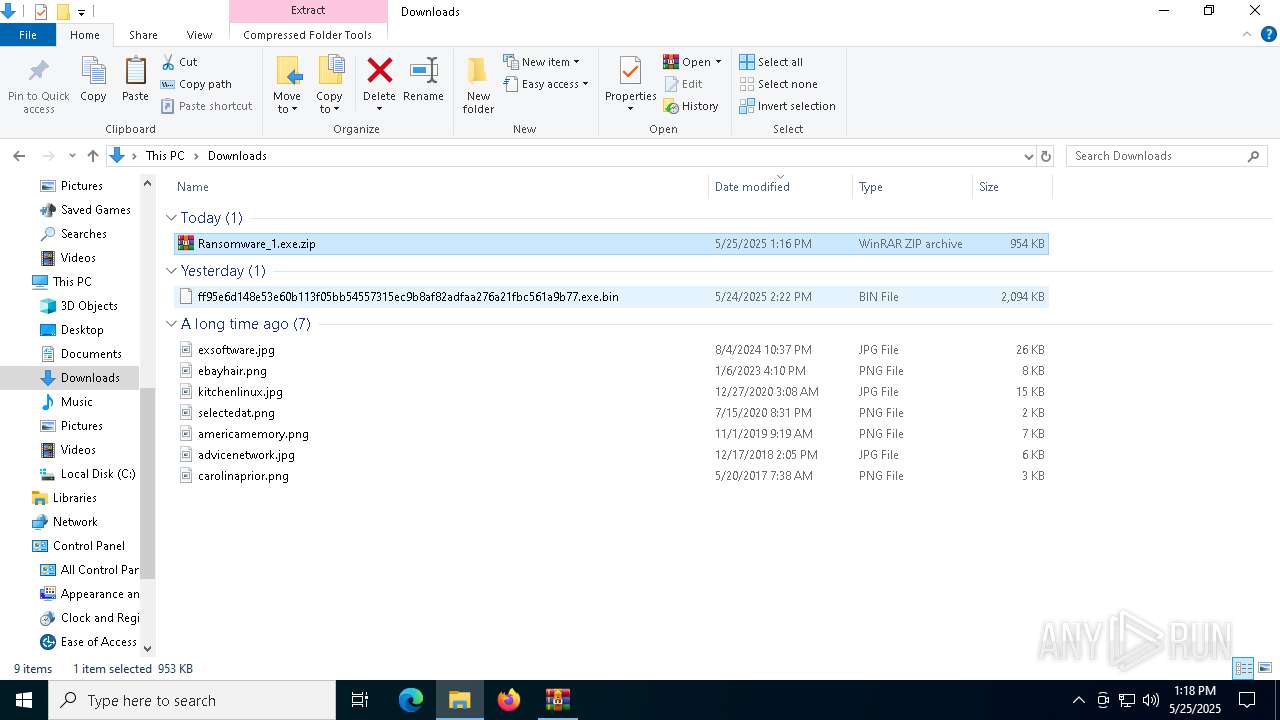
| File name: | Ransomware_1.exe.zip |
| Full analysis: | https://app.any.run/tasks/a3f262d5-636d-471a-b2b3-83553776ffa7 |
| Verdict: | Malicious activity |
| Threats: | LockBit, a ransomware variant, encrypts data on infected machines, demanding a ransom payment for decryption. Used in targeted attacks, It's a significant risk to organizations. |
| Analysis date: | May 25, 2025, 13:16:40 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
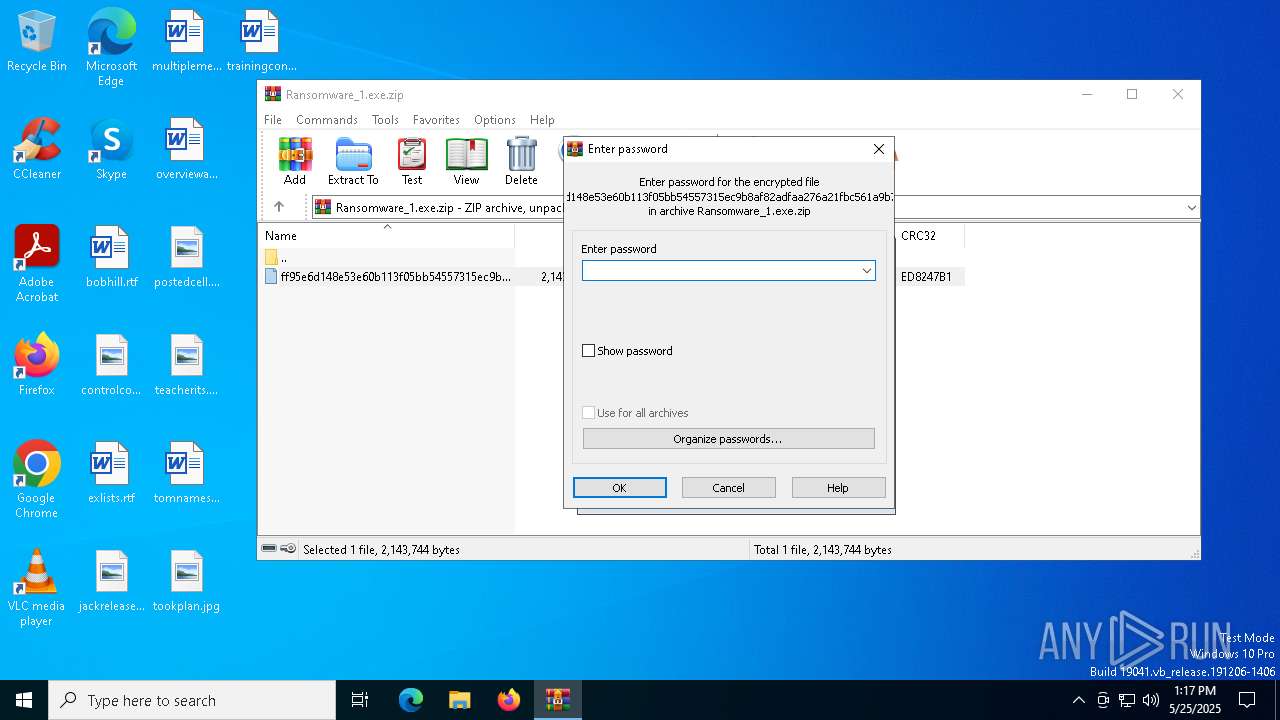
| File info: | Zip archive data, at least v5.1 to extract, compression method=AES Encrypted |
| MD5: | 12D869E16104852603631CC573E37E16 |
| SHA1: | 13A4CE1844FE843F058E773F8BBB40A819E79B9B |
| SHA256: | 03513A31C3424FBF5D46C232F0DD70606D8142F3ED0B7945BBFC873E24A42BA3 |
| SSDEEP: | 49152:Stx9xjQb+7ZLwSCRcmbNbPeQ/33luNvrWK0CviojgCPk2ECcHQelxkr3XLtNY9Sf:I9rLwSsPeQ/3kxWPA5jgsEFqZK9FDj54 |
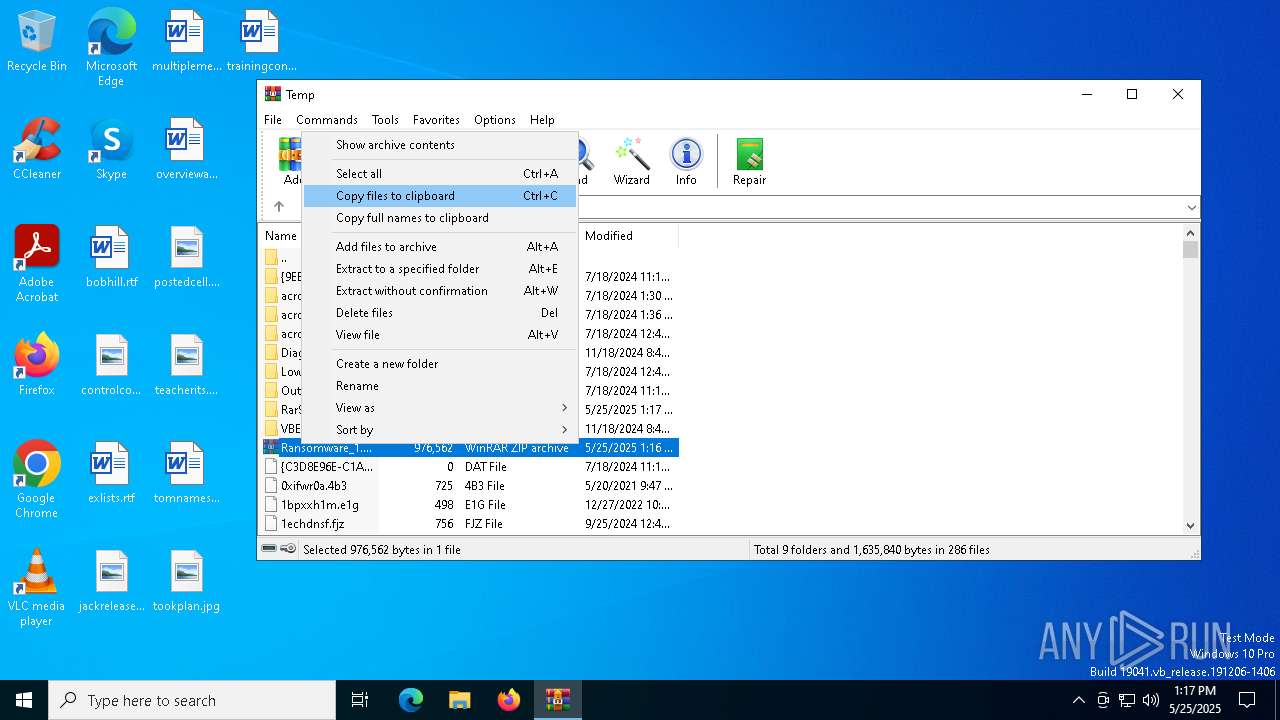
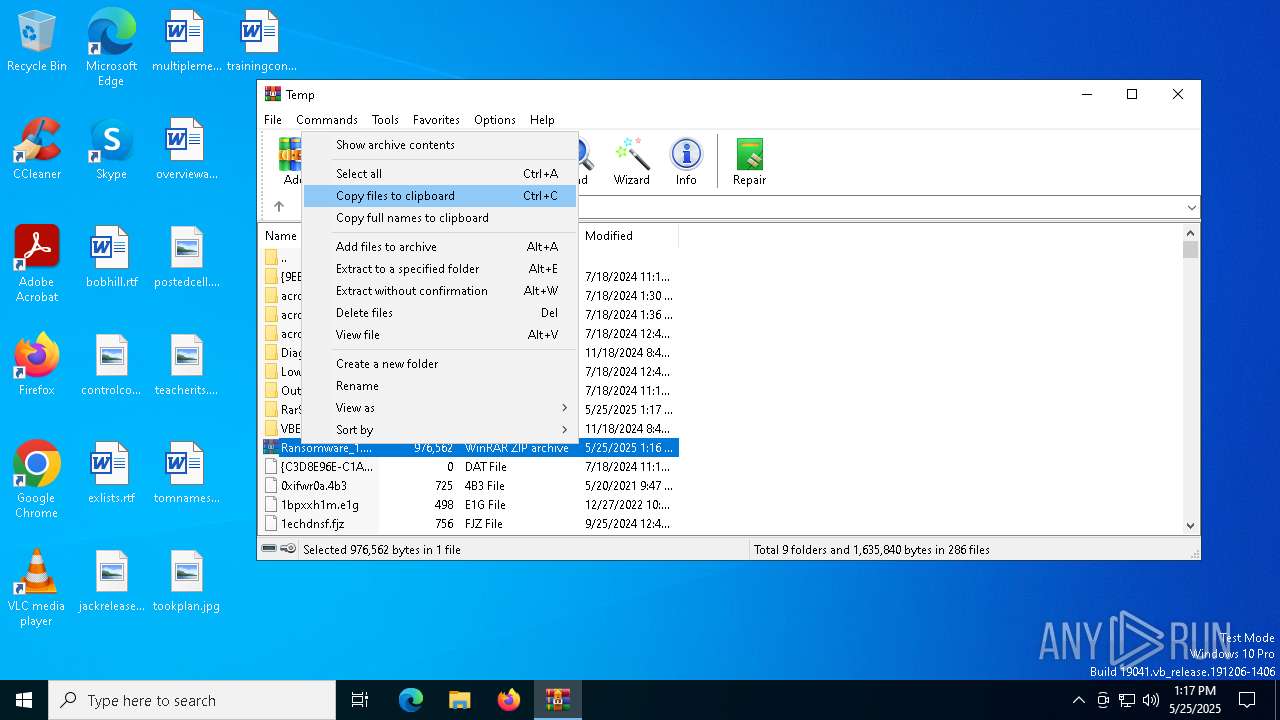
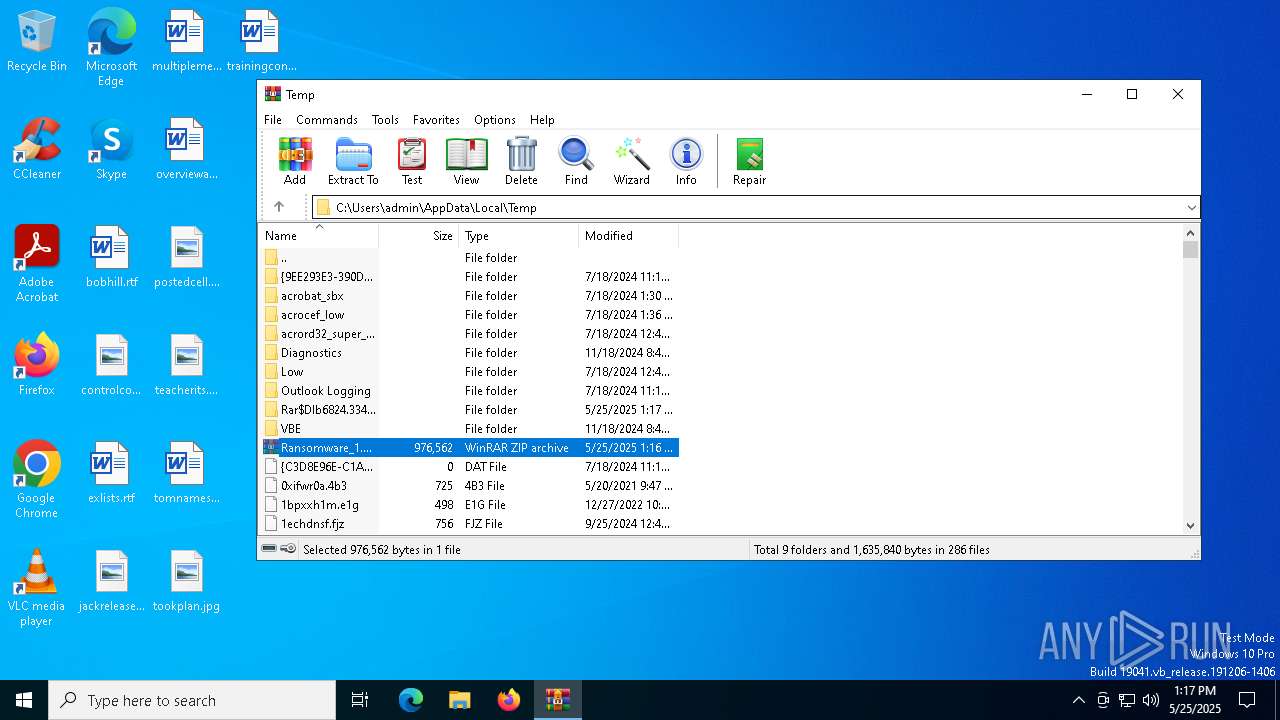
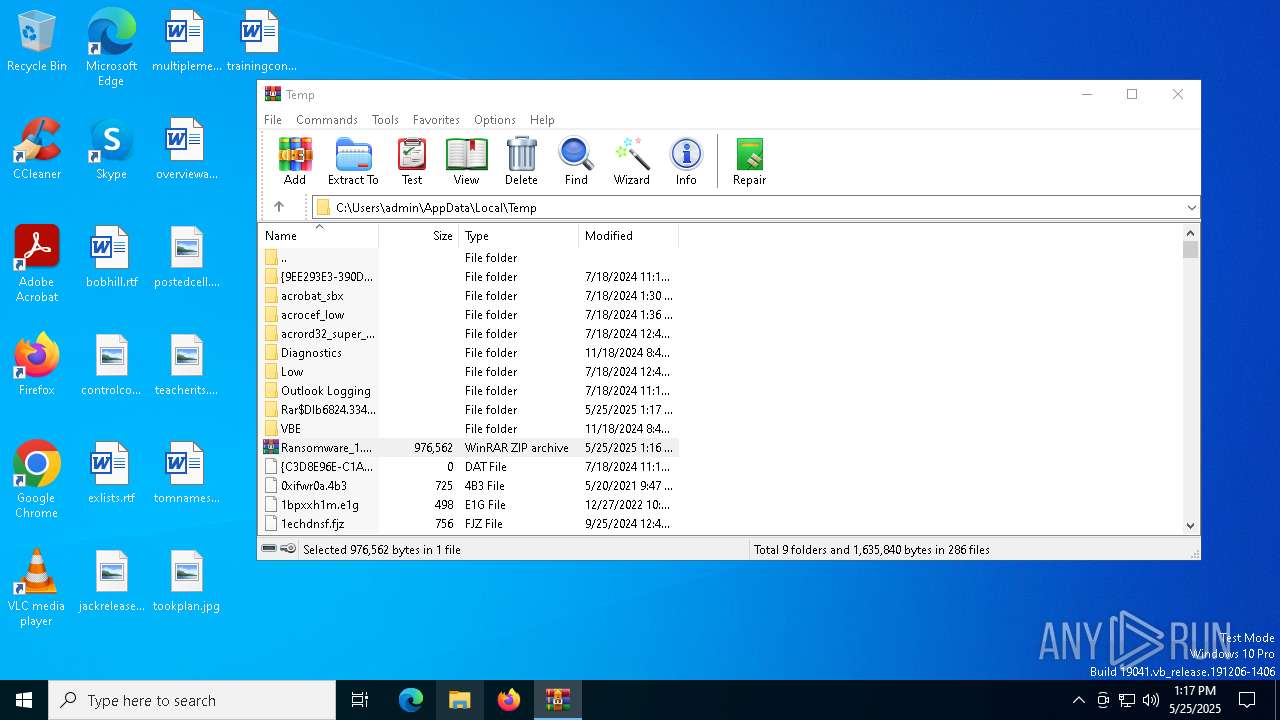
MALICIOUS
Generic archive extractor
- WinRAR.exe (PID: 6824)
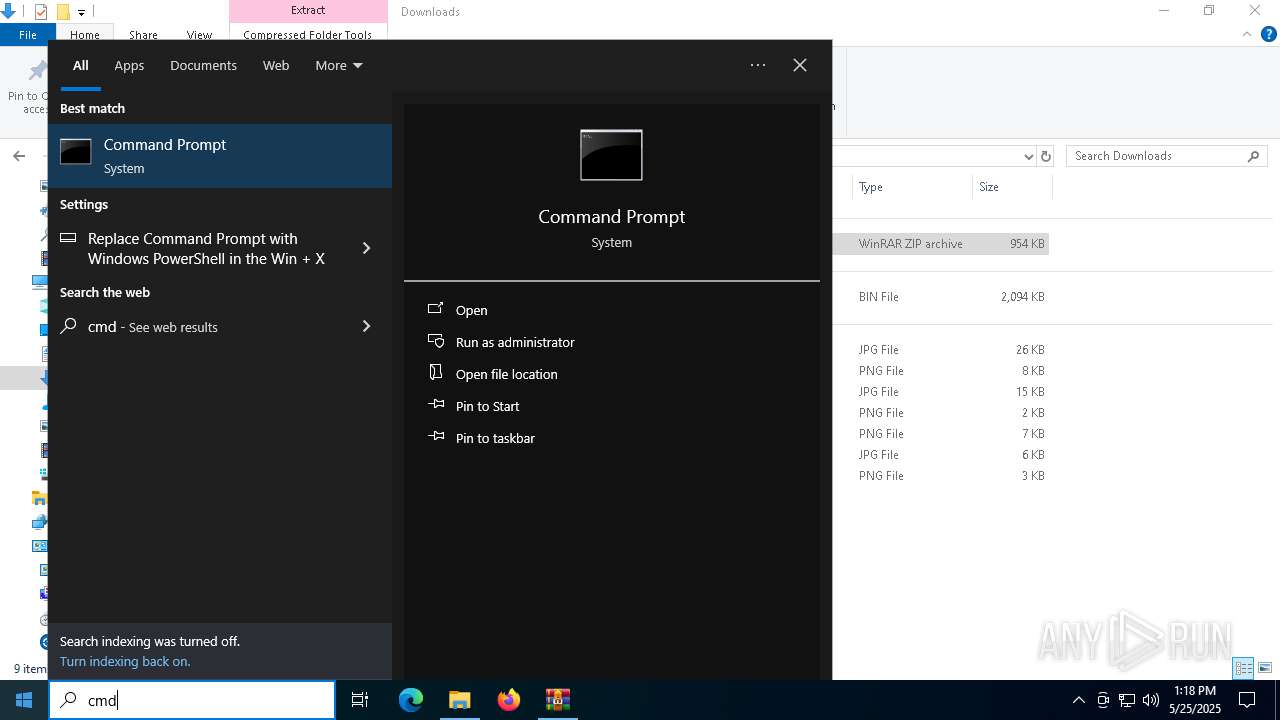
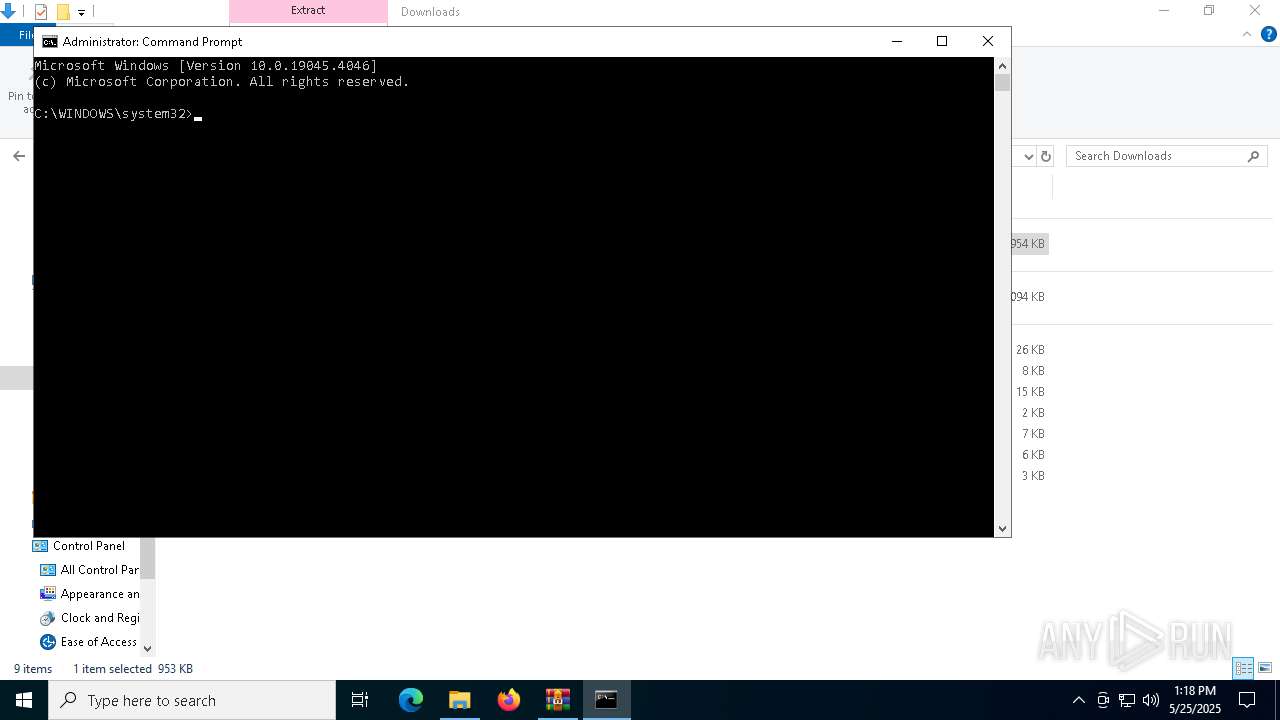
Changes powershell execution policy (Bypass)
- cmd.exe (PID: 5960)
- powershell.exe (PID: 3396)
Bypass execution policy to execute commands
- powershell.exe (PID: 3396)
- powershell.exe (PID: 8180)
Run PowerShell with an invisible window
- powershell.exe (PID: 3396)
- powershell.exe (PID: 8180)
Starts NET.EXE for service management
- cmd.exe (PID: 536)
- net.exe (PID: 2516)
- cmd.exe (PID: 4980)
- cmd.exe (PID: 6148)
- cmd.exe (PID: 5156)
- cmd.exe (PID: 4428)
- cmd.exe (PID: 5416)
- cmd.exe (PID: 904)
- cmd.exe (PID: 6080)
- cmd.exe (PID: 3140)
- cmd.exe (PID: 5232)
- cmd.exe (PID: 2568)
- cmd.exe (PID: 6960)
- cmd.exe (PID: 7424)
- cmd.exe (PID: 4628)
- net.exe (PID: 4348)
- net.exe (PID: 7264)
- net.exe (PID: 7376)
- net.exe (PID: 7360)
- cmd.exe (PID: 7480)
- net.exe (PID: 7328)
- cmd.exe (PID: 7280)
- cmd.exe (PID: 7576)
- net.exe (PID: 7304)
- net.exe (PID: 7368)
- cmd.exe (PID: 7812)
- cmd.exe (PID: 7288)
- cmd.exe (PID: 7472)
- net.exe (PID: 8020)
- net.exe (PID: 7384)
- net.exe (PID: 7536)
- net.exe (PID: 4120)
- cmd.exe (PID: 7240)
- net.exe (PID: 7852)
- net.exe (PID: 7860)
- net.exe (PID: 7888)
- net.exe (PID: 8560)
- net.exe (PID: 8080)
- cmd.exe (PID: 7456)
- net.exe (PID: 8536)
- net.exe (PID: 8672)
- net.exe (PID: 9028)
- net.exe (PID: 8608)
- net.exe (PID: 8432)
Uses NET.EXE to stop Windows Security Center service
- cmd.exe (PID: 7424)
- net.exe (PID: 8020)
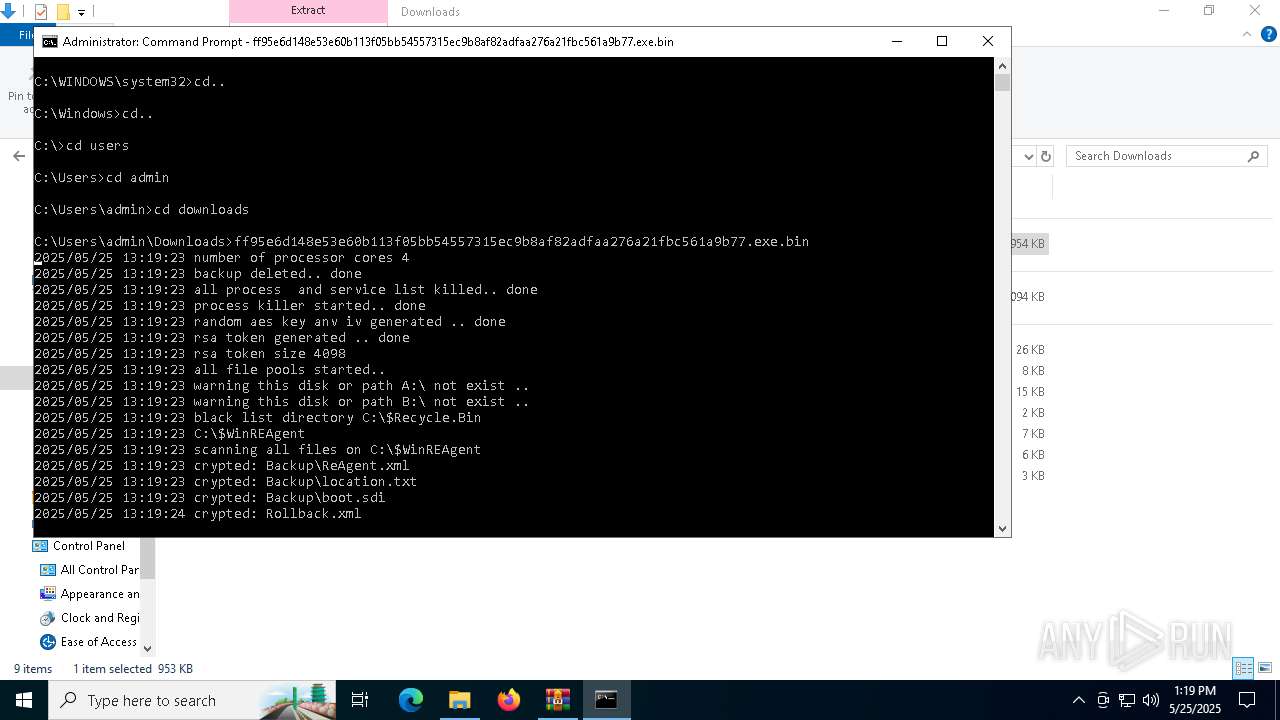
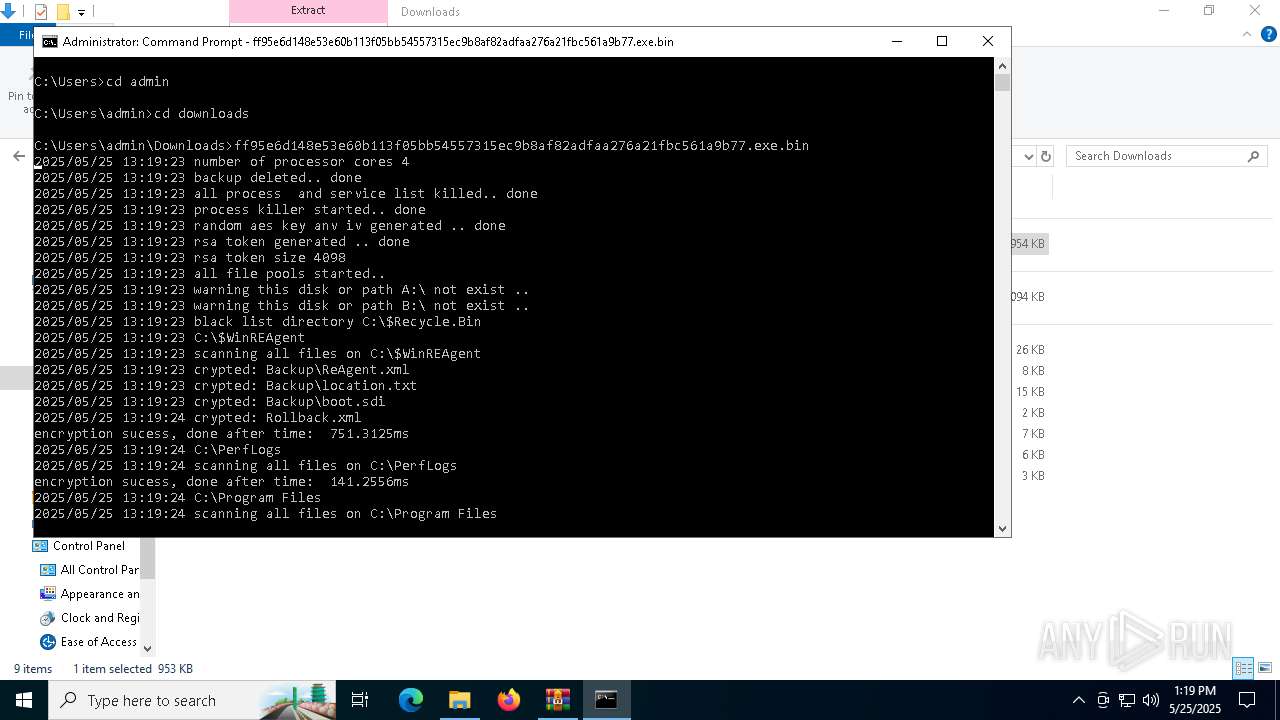
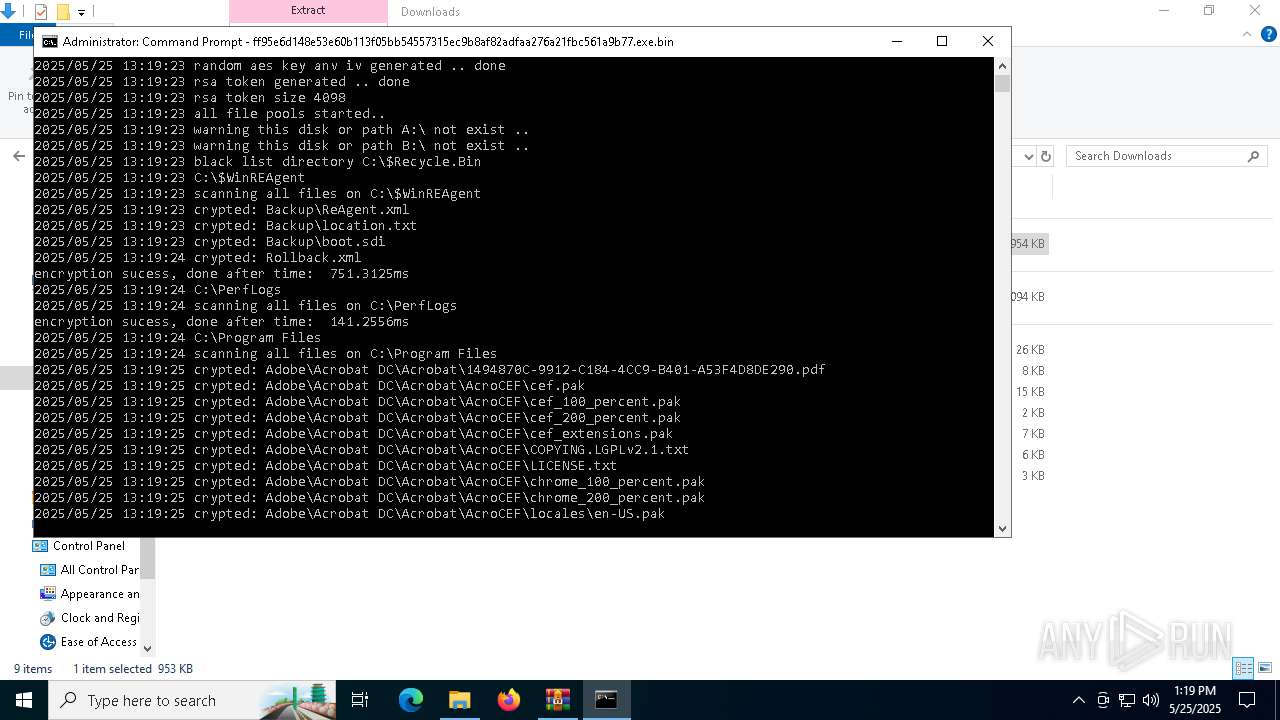
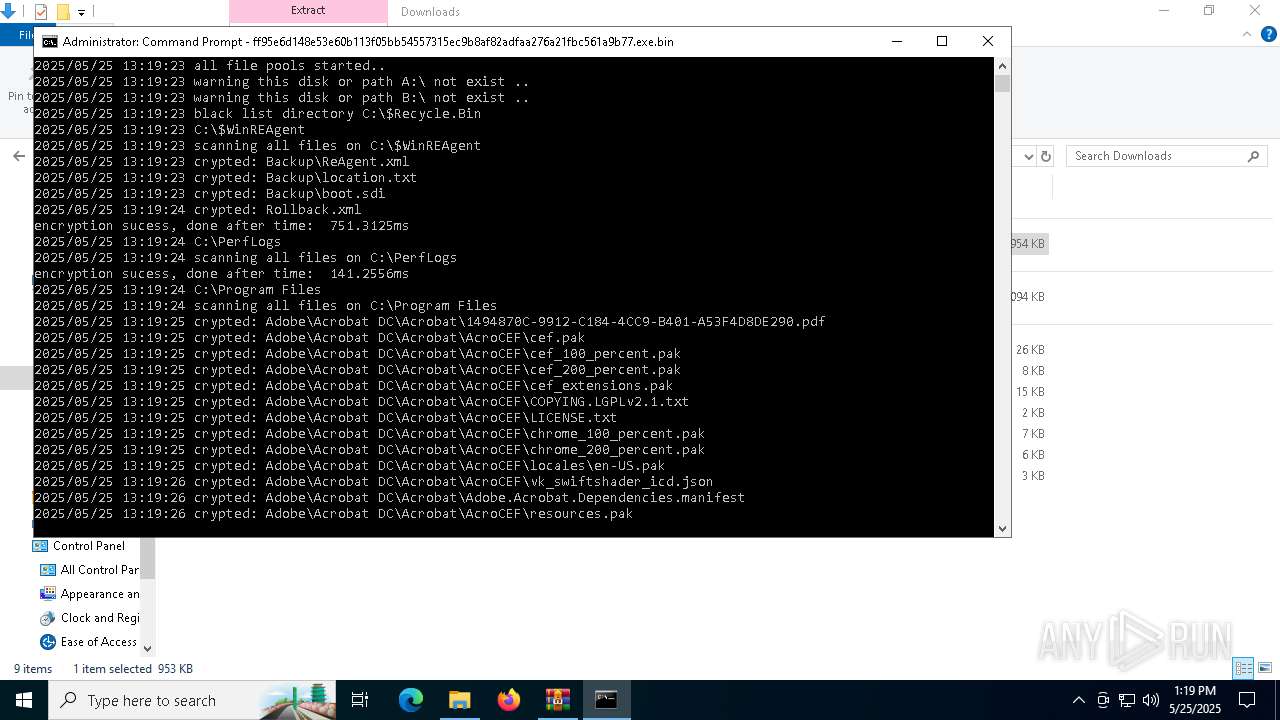
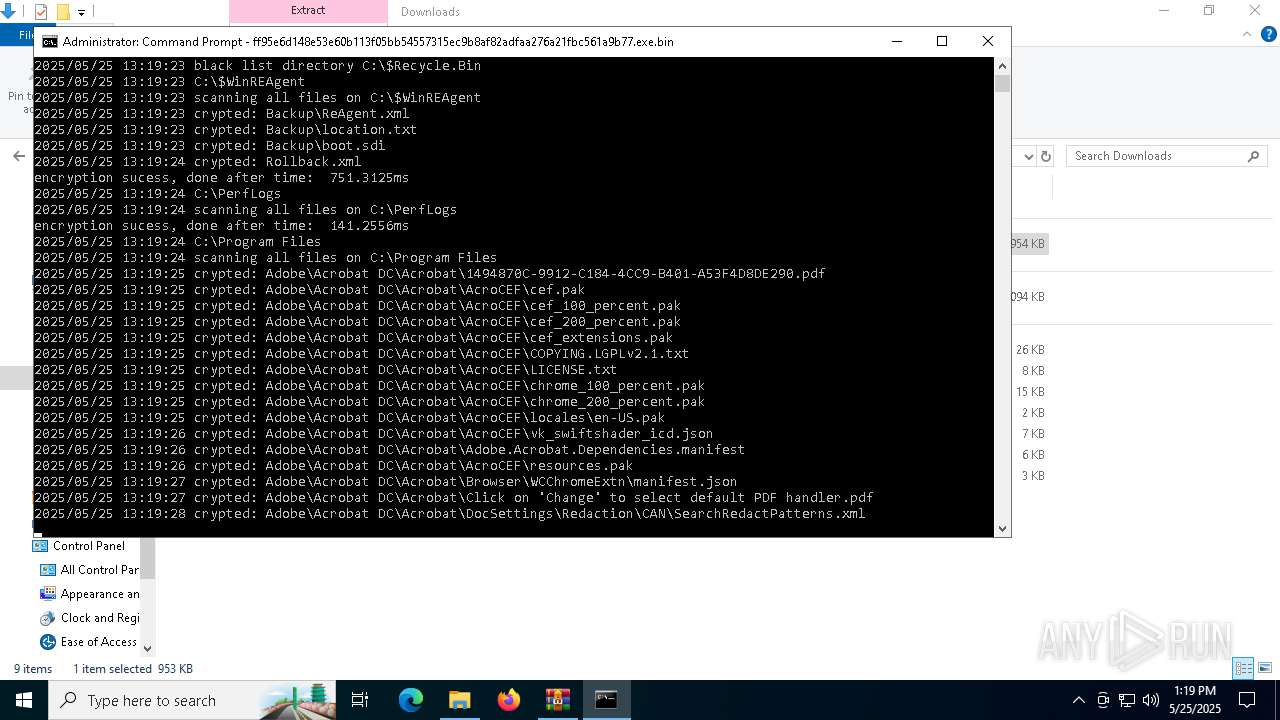
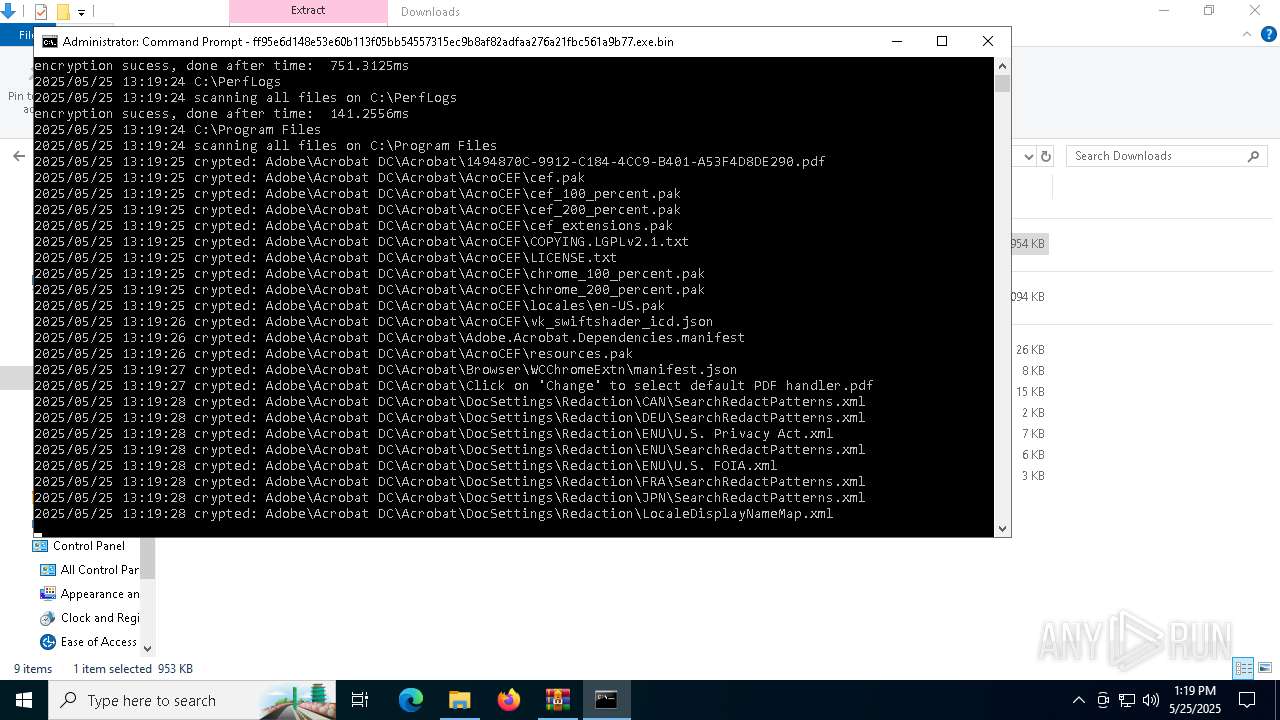
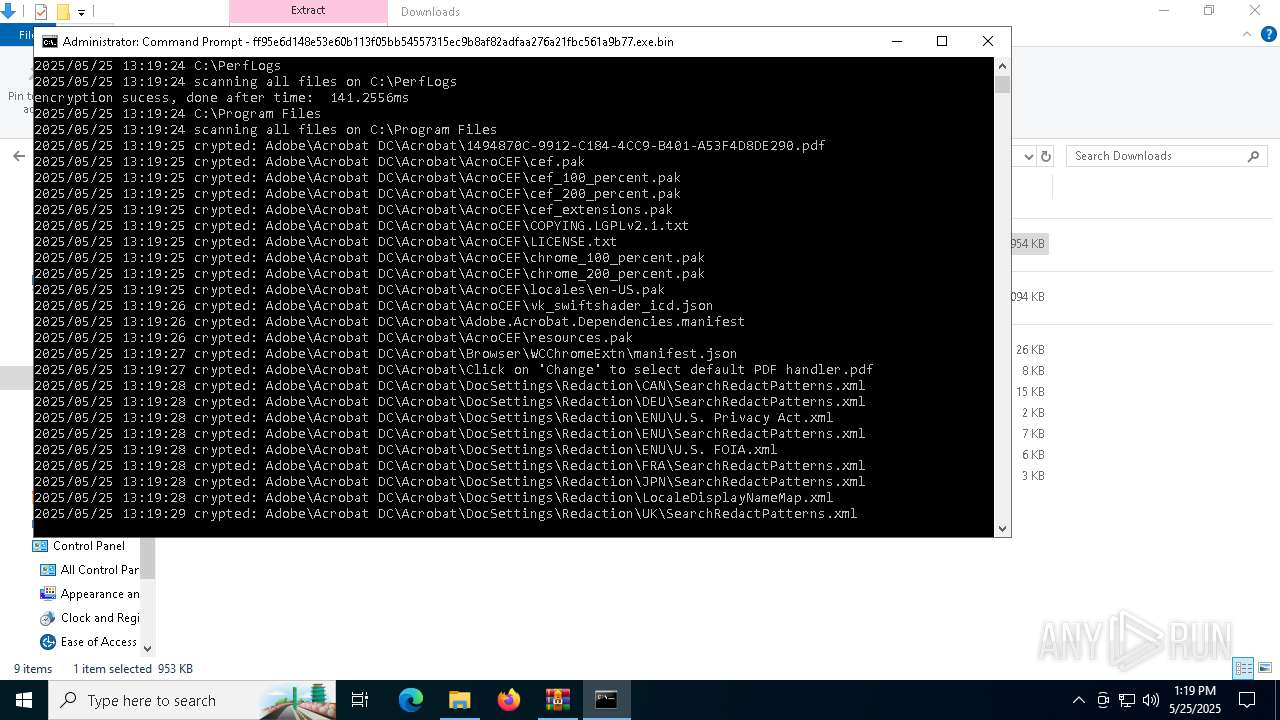
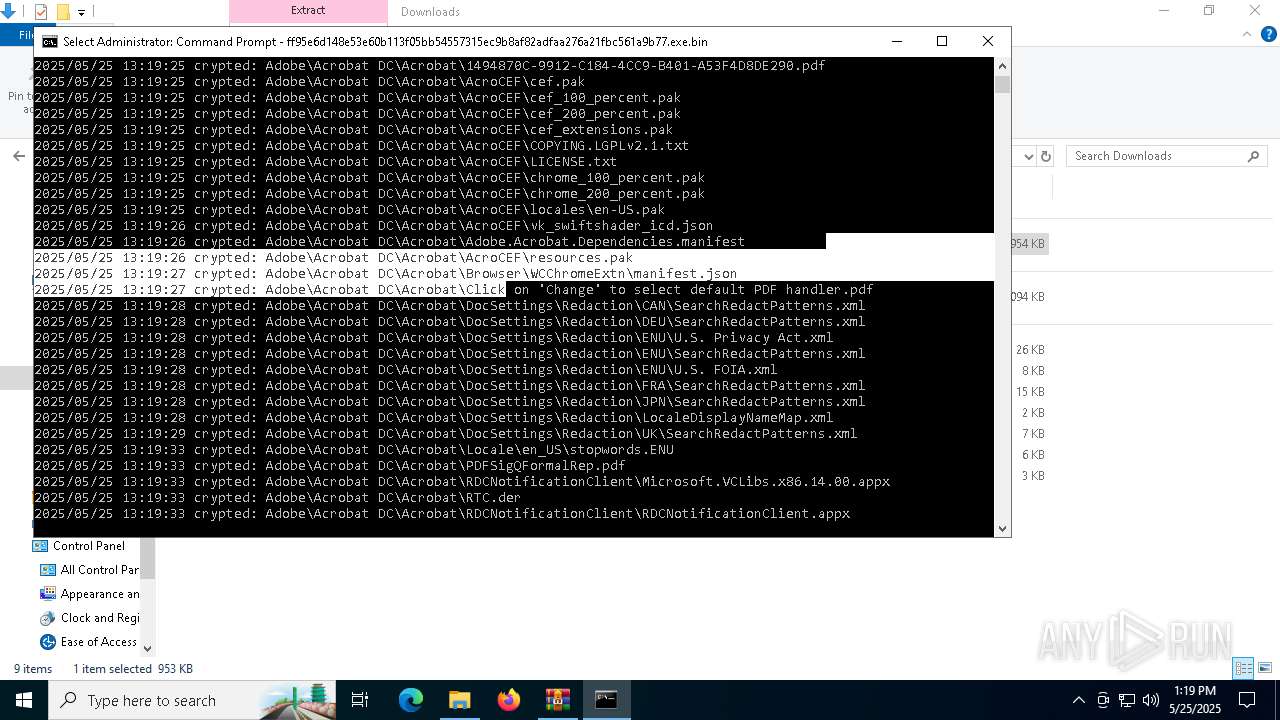
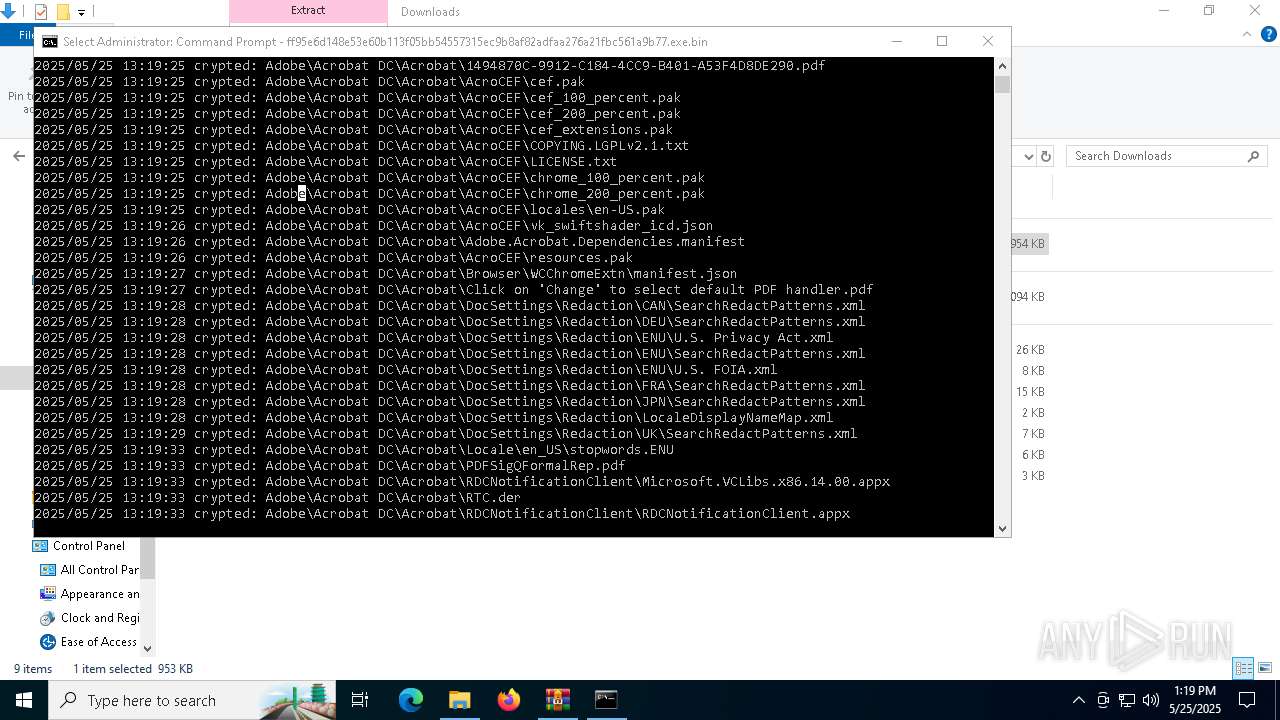
[YARA] LockBit is detected
- ff95e6d148e53e60b113f05bb54557315ec9b8af82adfaa276a21fbc561a9b77.exe.bin (PID: 4008)
Uses TASKKILL.EXE to kill security tools
- powershell.exe (PID: 8180)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 6824)
Starts application with an unusual extension
- cmd.exe (PID: 6620)
Base64-obfuscated command line is found
- cmd.exe (PID: 5960)
- powershell.exe (PID: 3396)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 5960)
- powershell.exe (PID: 3396)
BASE64 encoded PowerShell command has been detected
- cmd.exe (PID: 5960)
- powershell.exe (PID: 3396)
Starts process via Powershell
- powershell.exe (PID: 3396)
Uses WEVTUTIL.EXE to cleanup log
- cmd.exe (PID: 6564)
- cmd.exe (PID: 5528)
- cmd.exe (PID: 4120)
- cmd.exe (PID: 7820)
- cmd.exe (PID: 7828)
- cmd.exe (PID: 7632)
Starts CMD.EXE for commands execution
- ff95e6d148e53e60b113f05bb54557315ec9b8af82adfaa276a21fbc561a9b77.exe.bin (PID: 4008)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 684)
- cmd.exe (PID: 2664)
- cmd.exe (PID: 5680)
- cmd.exe (PID: 1912)
- cmd.exe (PID: 3156)
- cmd.exe (PID: 4572)
- cmd.exe (PID: 7172)
- cmd.exe (PID: 6208)
- cmd.exe (PID: 4884)
- cmd.exe (PID: 7192)
- cmd.exe (PID: 7184)
- cmd.exe (PID: 6572)
- cmd.exe (PID: 7392)
- cmd.exe (PID: 7400)
- cmd.exe (PID: 7416)
- cmd.exe (PID: 7320)
- cmd.exe (PID: 7256)
- cmd.exe (PID: 7340)
- cmd.exe (PID: 7232)
- cmd.exe (PID: 7248)
- cmd.exe (PID: 7528)
- cmd.exe (PID: 7508)
- cmd.exe (PID: 7436)
- cmd.exe (PID: 7496)
- powershell.exe (PID: 8180)
Uses TASKKILL.EXE to kill Office Apps
- cmd.exe (PID: 536)
- cmd.exe (PID: 7444)
Application launched itself
- powershell.exe (PID: 3396)
Get information on the list of running processes
- powershell.exe (PID: 8180)
INFO
Reads the software policy settings
- slui.exe (PID: 6268)
- slui.exe (PID: 732)
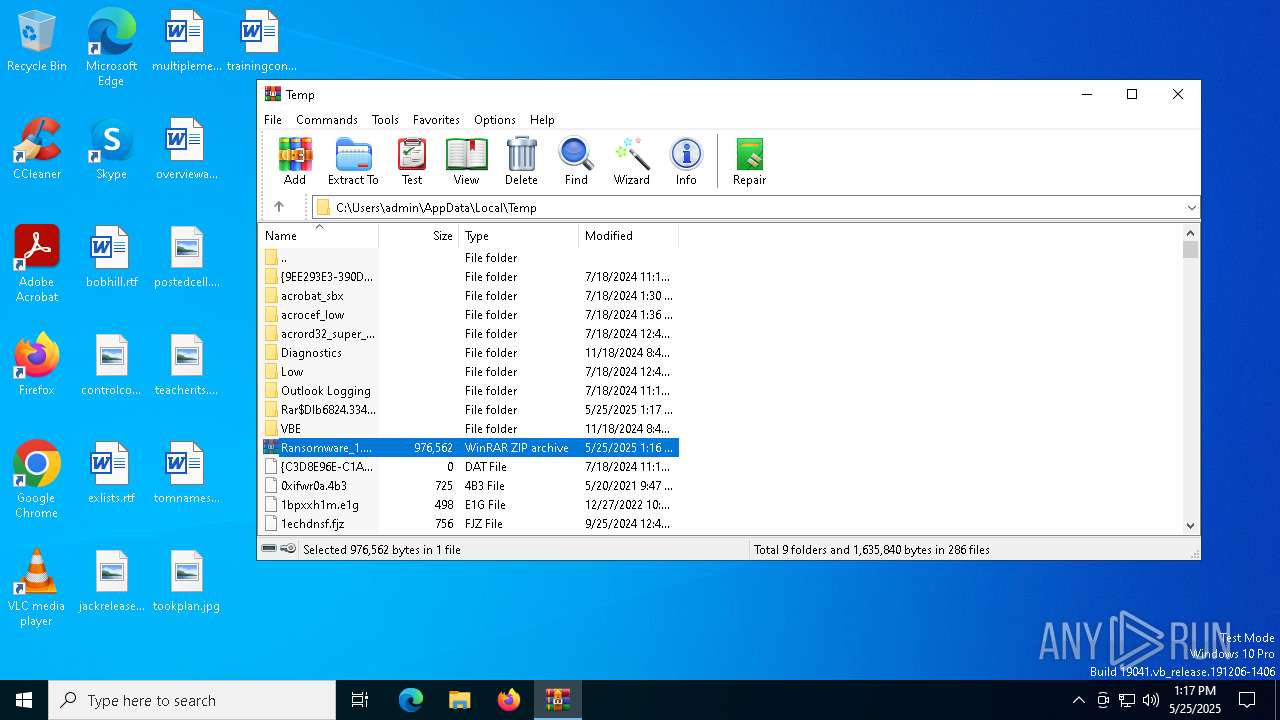
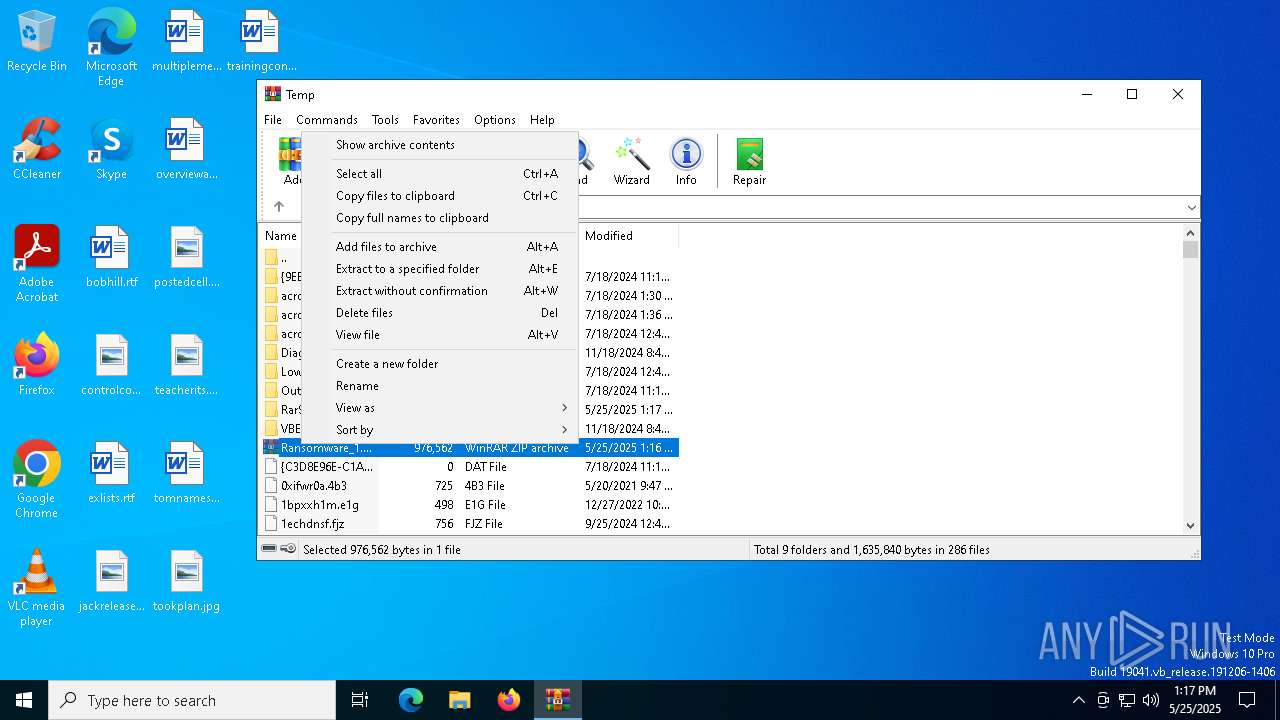
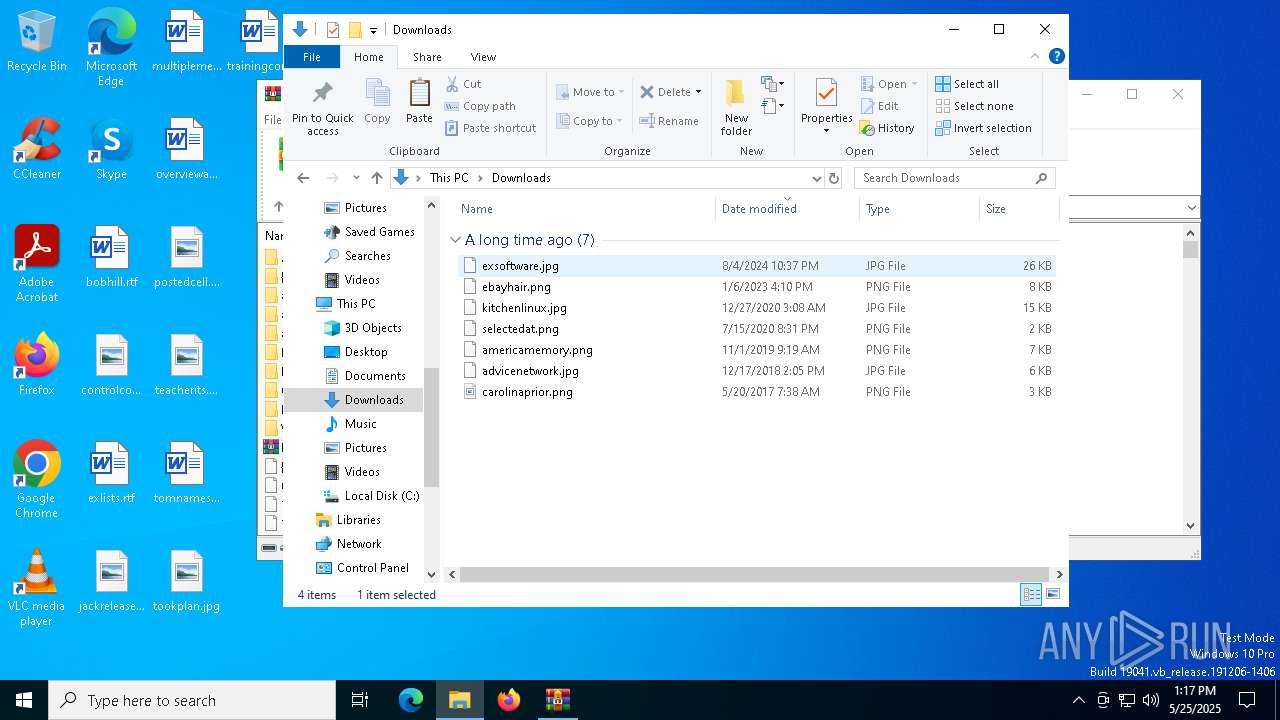
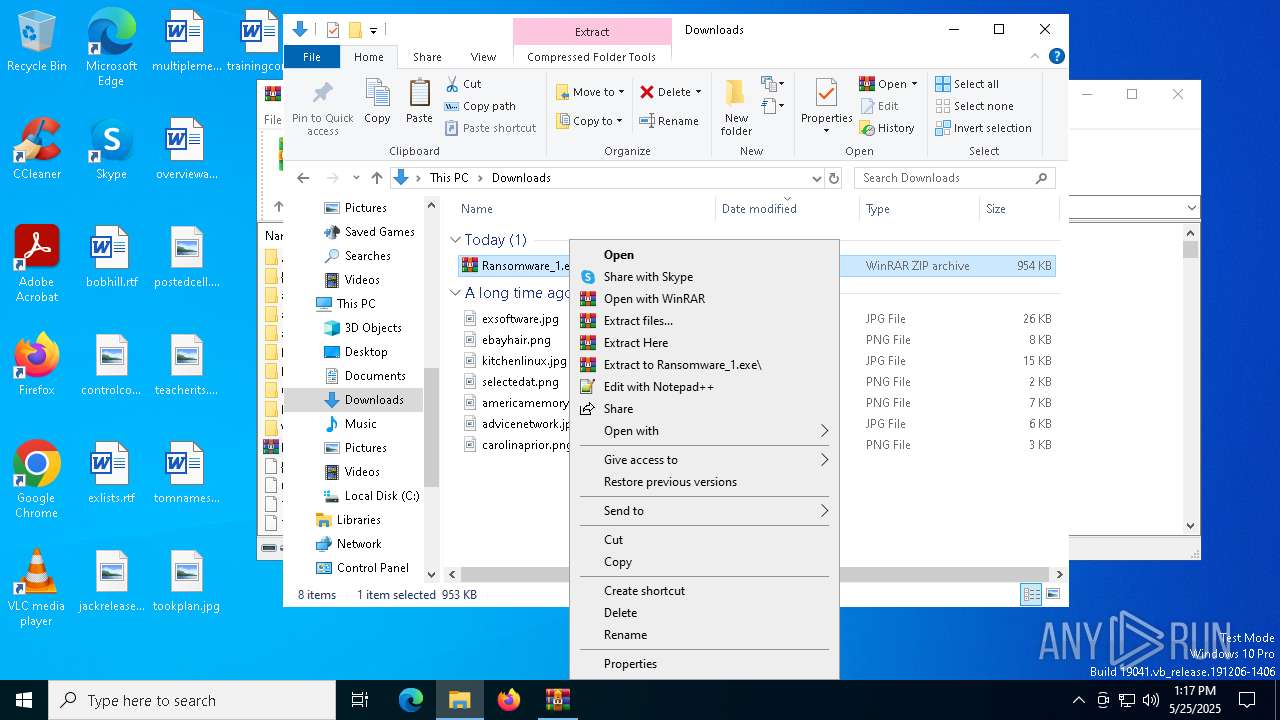
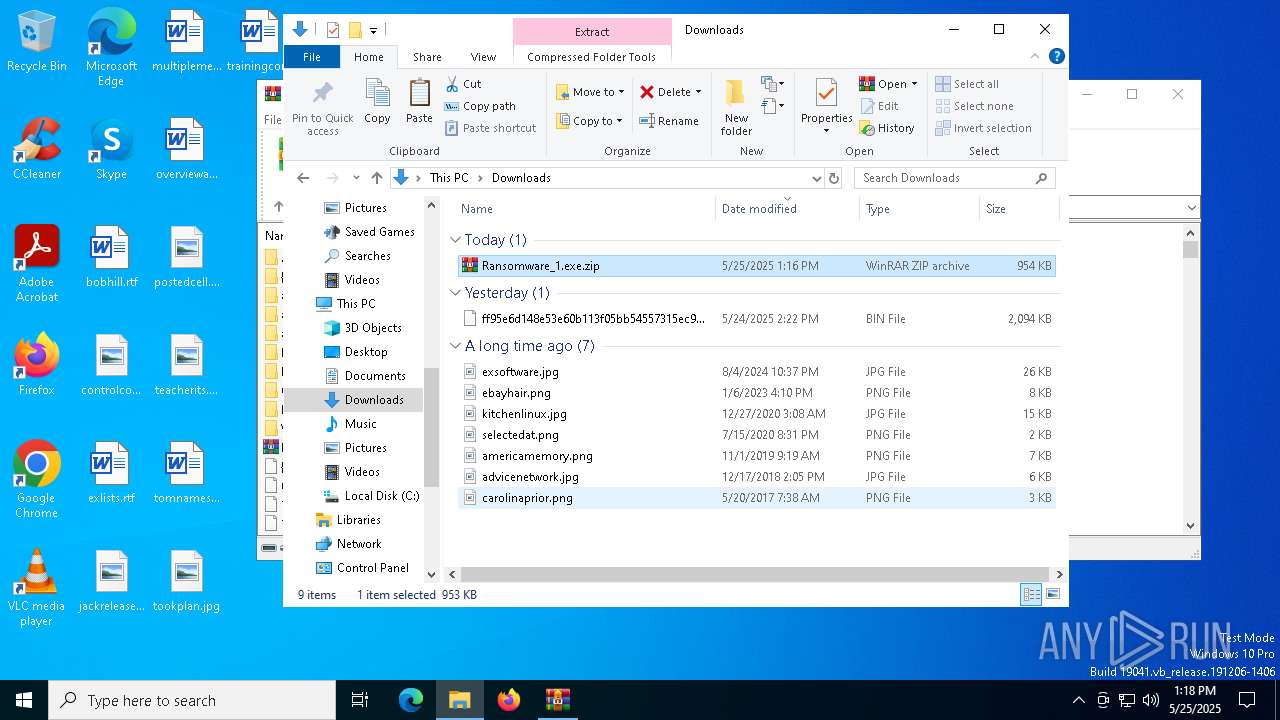
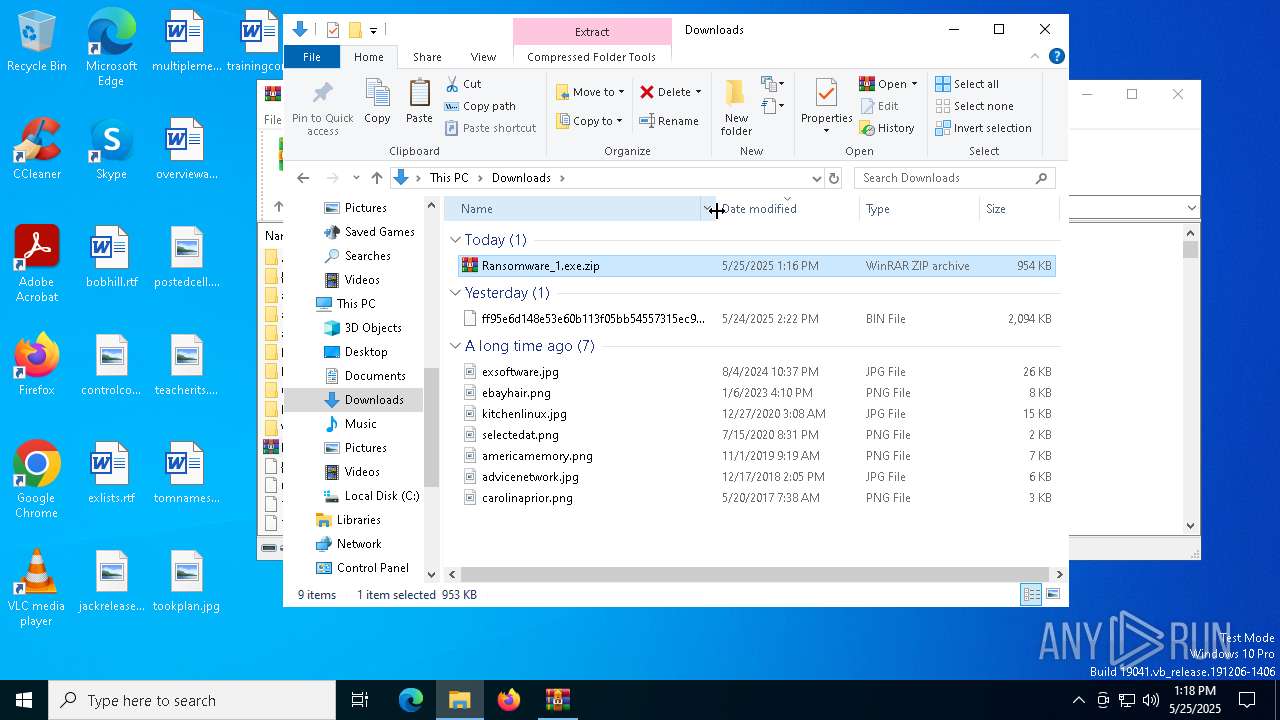
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6824)
- WinRAR.exe (PID: 864)
Reads Microsoft Office registry keys
- OpenWith.exe (PID: 3240)
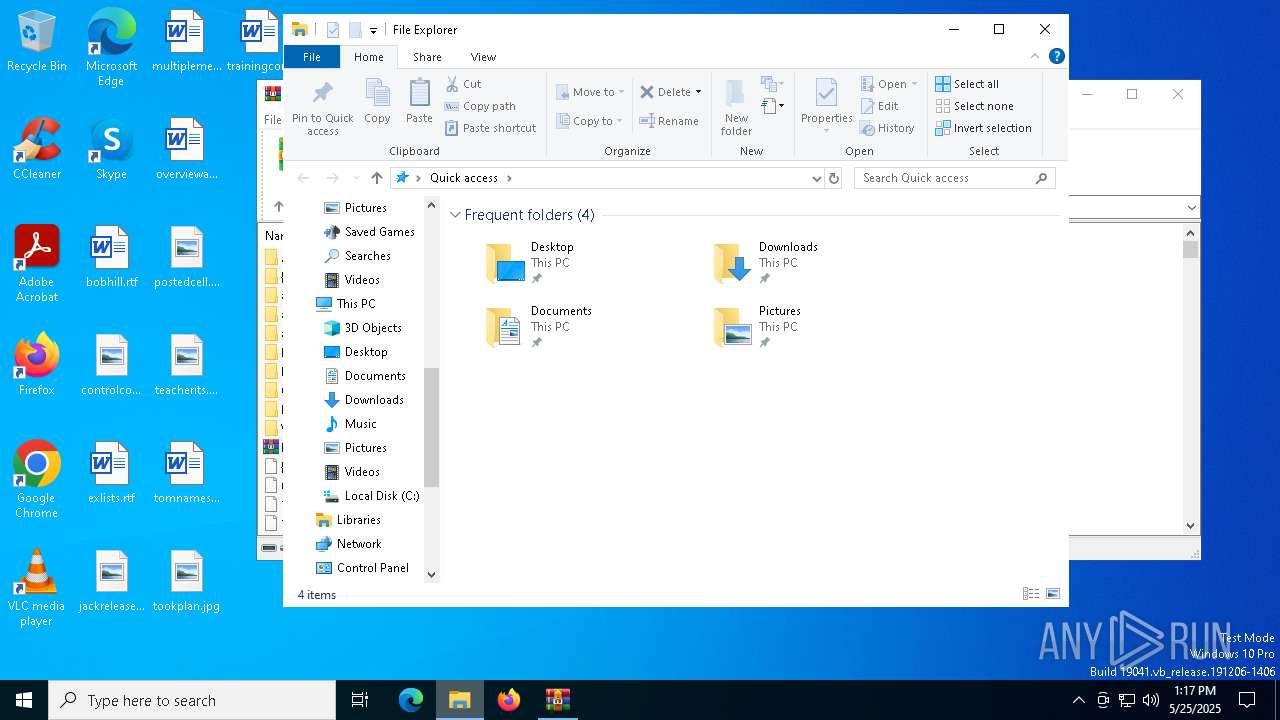
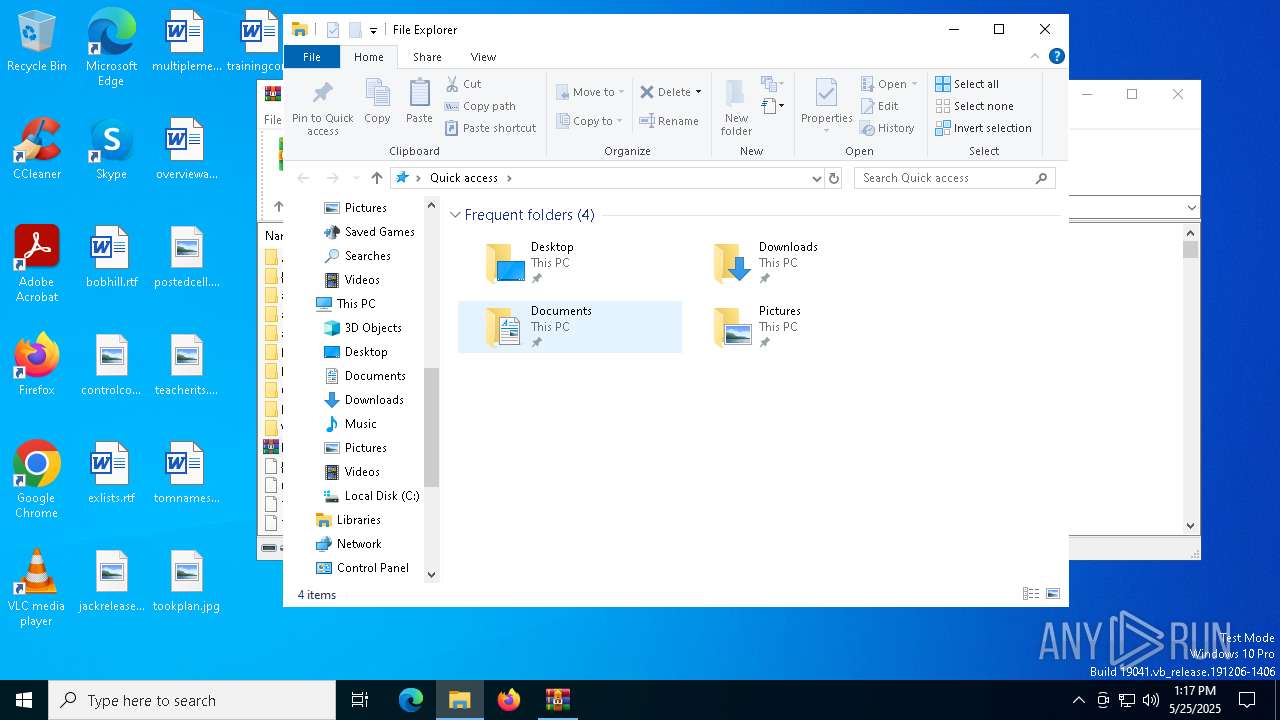
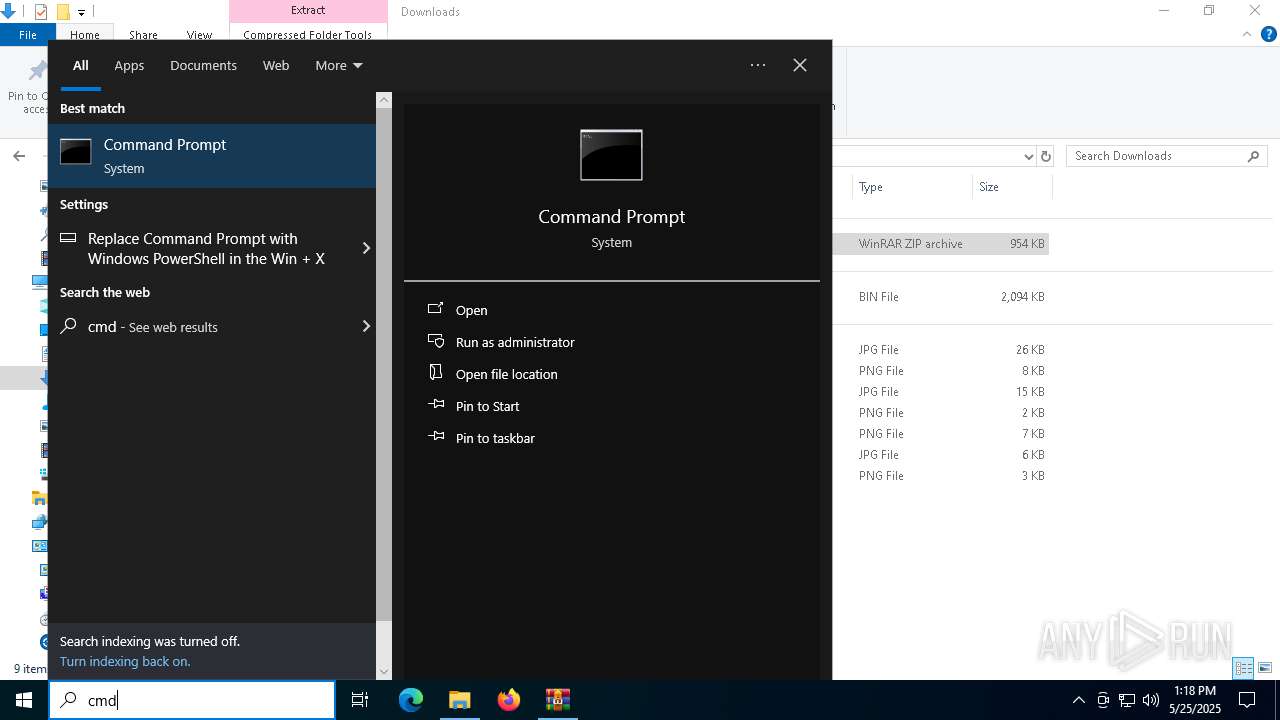
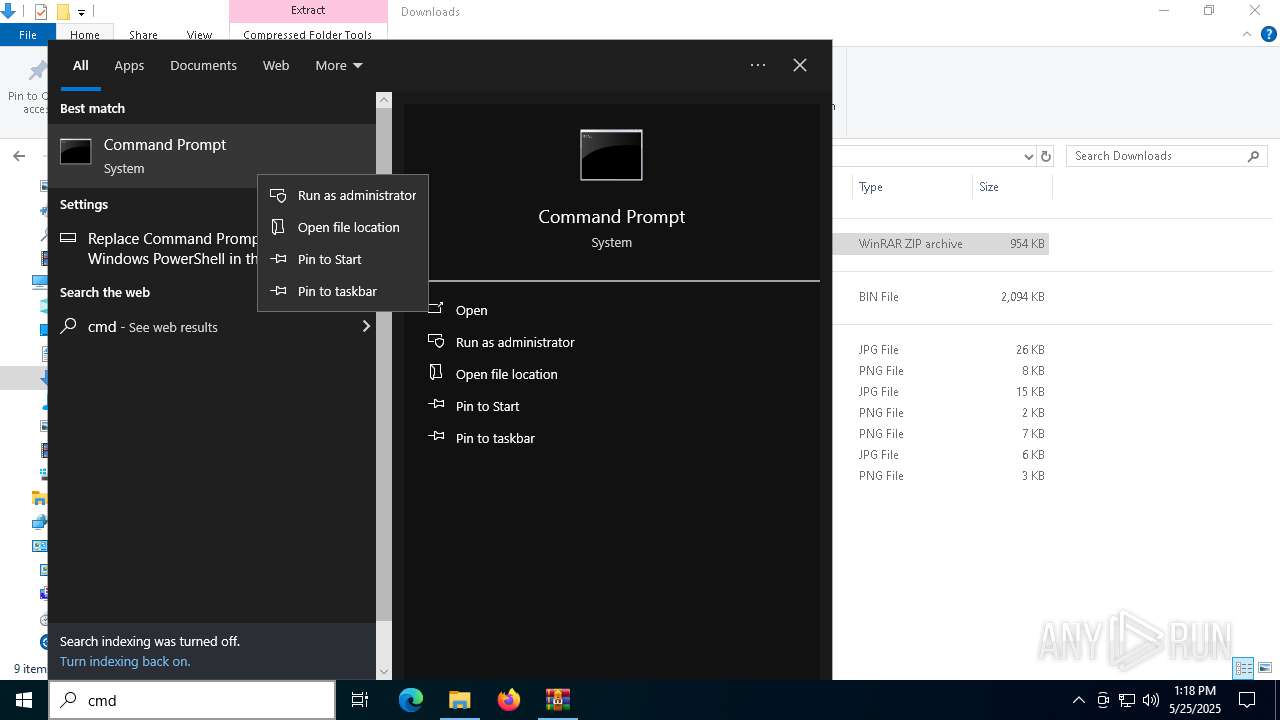
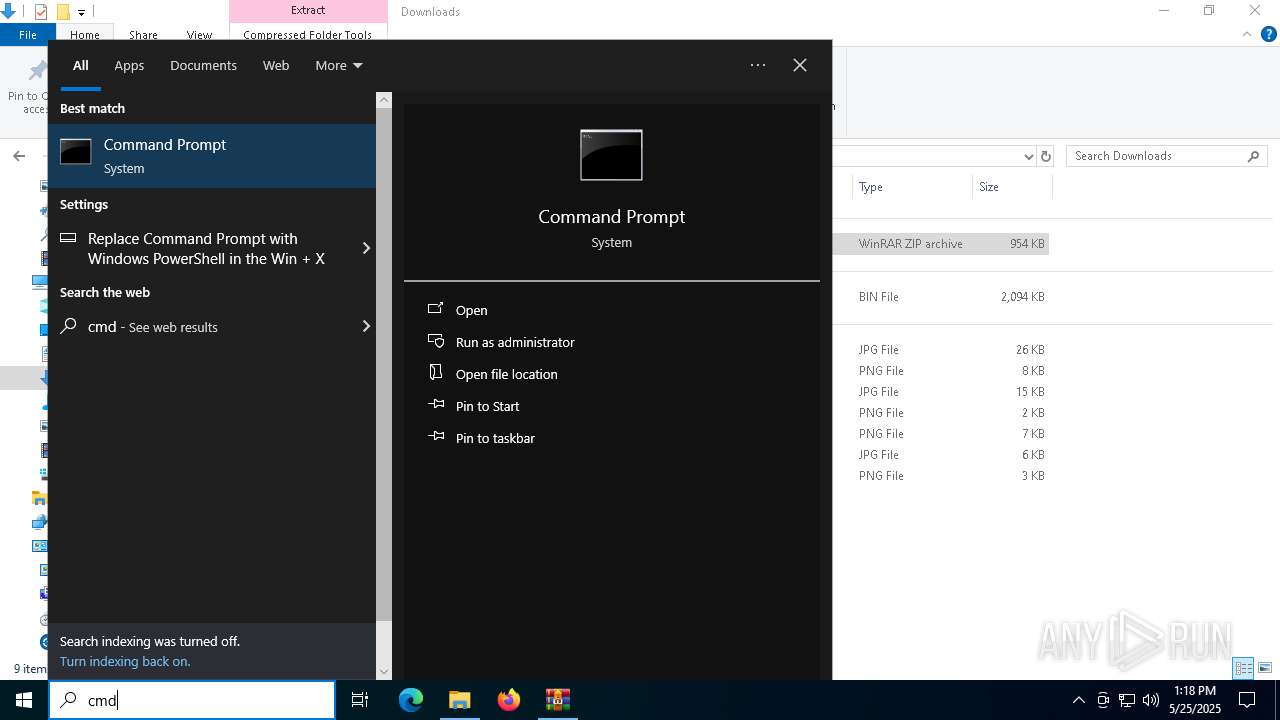
Manual execution by a user
- WinRAR.exe (PID: 2244)
- WinRAR.exe (PID: 864)
- cmd.exe (PID: 6620)
Checks proxy server information
- slui.exe (PID: 6268)
Drops encrypted JS script (Microsoft Script Encoder)
- ff95e6d148e53e60b113f05bb54557315ec9b8af82adfaa276a21fbc561a9b77.exe.bin (PID: 4008)
Checks supported languages
- ff95e6d148e53e60b113f05bb54557315ec9b8af82adfaa276a21fbc561a9b77.exe.bin (PID: 4008)
Application based on Golang
- ff95e6d148e53e60b113f05bb54557315ec9b8af82adfaa276a21fbc561a9b77.exe.bin (PID: 4008)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
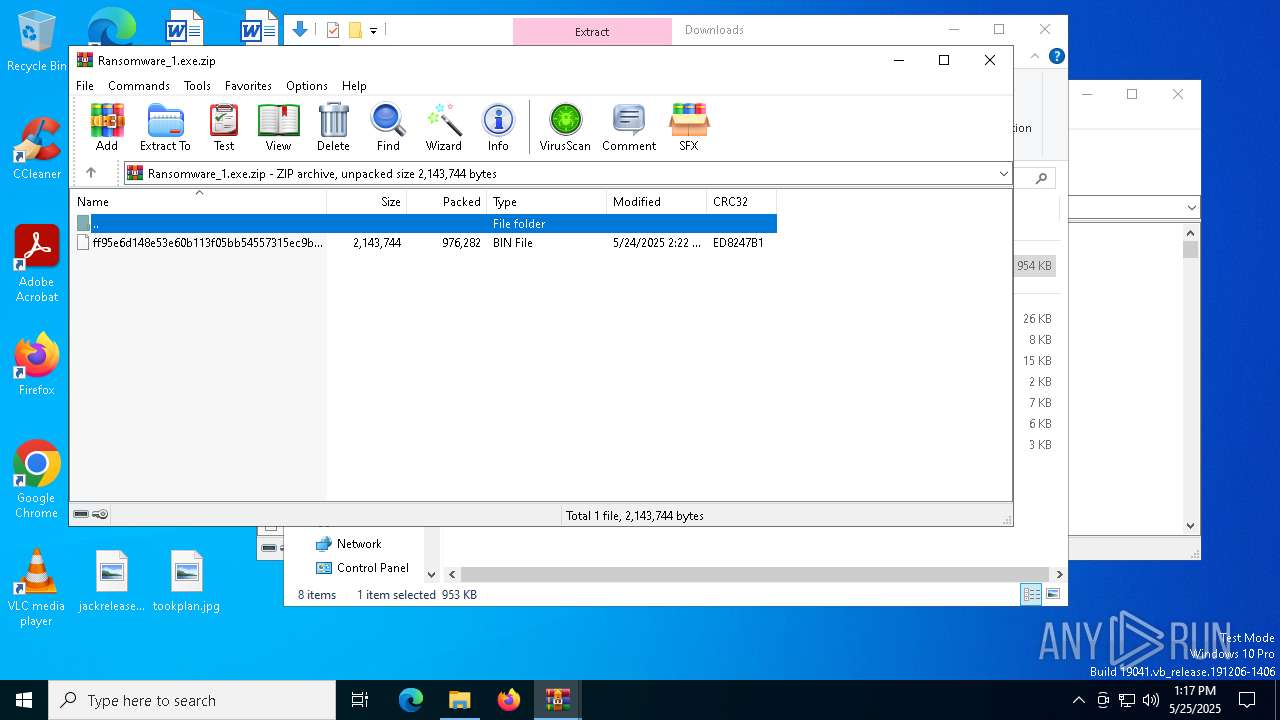
| ZipRequiredVersion: | 51 |
|---|---|
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Unknown (99) |
| ZipModifyDate: | 2025:05:24 14:22:28 |
| ZipCRC: | 0xed8247b1 |
| ZipCompressedSize: | 976282 |
| ZipUncompressedSize: | 2143744 |
| ZipFileName: | ff95e6d148e53e60b113f05bb54557315ec9b8af82adfaa276a21fbc561a9b77.exe.bin |
Total processes
478
Monitored processes
345
Malicious processes
6
Suspicious processes
18
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 536 | cmd.exe /c "net stop iVPAgent /y" | C:\Windows\SysWOW64\cmd.exe | — | ff95e6d148e53e60b113f05bb54557315ec9b8af82adfaa276a21fbc561a9b77.exe.bin | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 2 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 536 | cmd.exe /c "taskkill /f /im Winword.exe" | C:\Windows\SysWOW64\cmd.exe | — | ff95e6d148e53e60b113f05bb54557315ec9b8af82adfaa276a21fbc561a9b77.exe.bin | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 128 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 684 | cmd.exe /c "taskkill /f /im Steam.exe" | C:\Windows\SysWOW64\cmd.exe | — | ff95e6d148e53e60b113f05bb54557315ec9b8af82adfaa276a21fbc561a9b77.exe.bin | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 128 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 728 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 732 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 776 | "C:\WINDOWS\system32\taskkill.exe" /f /im regedit.exe | C:\Windows\SysWOW64\taskkill.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 856 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 864 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Downloads\Ransomware_1.exe.zip" C:\Users\admin\Downloads\ | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 904 | C:\WINDOWS\system32\net1 stop iVPAgent /y | C:\Windows\SysWOW64\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 904 | cmd.exe /c "net stop TMBMServer /y" | C:\Windows\SysWOW64\cmd.exe | — | ff95e6d148e53e60b113f05bb54557315ec9b8af82adfaa276a21fbc561a9b77.exe.bin | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 2 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
37 411
Read events
37 373
Write events
38
Delete events
0
Modification events
| (PID) Process: | (6824) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (6824) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (6824) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (6824) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Ransomware_1.exe.zip | |||
| (PID) Process: | (6824) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6824) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6824) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6824) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6824) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (6824) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 256 | |||
Executable files
2
Suspicious files
60
Text files
807
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4008 | ff95e6d148e53e60b113f05bb54557315ec9b8af82adfaa276a21fbc561a9b77.exe.bin | C:\$WinREAgent\Backup\README_TO_DECRYPT.txt | text | |
MD5:6DDDE195C70E2AE3ACDA3137CCA97199 | SHA256:D436E835759629AB1394D19DFE03CA2A2E7EEFD1057E7283CF98C05B91C9E3D2 | |||
| 4008 | ff95e6d148e53e60b113f05bb54557315ec9b8af82adfaa276a21fbc561a9b77.exe.bin | C:\$WinREAgent\Backup\ReAgent.xml | binary | |
MD5:25A2393D4CD44D4810EDA63E13AC0DA9 | SHA256:DD4E0E69701E4C67AE6C3CC366C1312C068D17ED22D541725BB6FBA3C15792DE | |||
| 864 | WinRAR.exe | C:\Users\admin\Downloads\ff95e6d148e53e60b113f05bb54557315ec9b8af82adfaa276a21fbc561a9b77.exe.bin | executable | |
MD5:02FDE0D62506C483203C5E67490893B5 | SHA256:FF95E6D148E53E60B113F05BB54557315EC9B8AF82ADFAA276A21FBC561A9B77 | |||
| 4008 | ff95e6d148e53e60b113f05bb54557315ec9b8af82adfaa276a21fbc561a9b77.exe.bin | C:\$WinREAgent\README_TO_DECRYPT.txt | text | |
MD5:6DDDE195C70E2AE3ACDA3137CCA97199 | SHA256:D436E835759629AB1394D19DFE03CA2A2E7EEFD1057E7283CF98C05B91C9E3D2 | |||
| 4008 | ff95e6d148e53e60b113f05bb54557315ec9b8af82adfaa276a21fbc561a9b77.exe.bin | C:\$WinREAgent\Rollback.xml | binary | |
MD5:0619EC5B6357BDD191398AECC03D01F6 | SHA256:C61043230CCE3482CBA8B540F964CE8AAAB8136E681AAC7A4546068B148569DB | |||
| 4008 | ff95e6d148e53e60b113f05bb54557315ec9b8af82adfaa276a21fbc561a9b77.exe.bin | C:\PerfLogs\README_TO_DECRYPT.txt | text | |
MD5:6DDDE195C70E2AE3ACDA3137CCA97199 | SHA256:D436E835759629AB1394D19DFE03CA2A2E7EEFD1057E7283CF98C05B91C9E3D2 | |||
| 4008 | ff95e6d148e53e60b113f05bb54557315ec9b8af82adfaa276a21fbc561a9b77.exe.bin | C:\$WinREAgent\Rollback\README_TO_DECRYPT.txt | text | |
MD5:6DDDE195C70E2AE3ACDA3137CCA97199 | SHA256:D436E835759629AB1394D19DFE03CA2A2E7EEFD1057E7283CF98C05B91C9E3D2 | |||
| 4008 | ff95e6d148e53e60b113f05bb54557315ec9b8af82adfaa276a21fbc561a9b77.exe.bin | C:\Program Files\Adobe\Acrobat DC\Acrobat\README_TO_DECRYPT.txt | text | |
MD5:6DDDE195C70E2AE3ACDA3137CCA97199 | SHA256:D436E835759629AB1394D19DFE03CA2A2E7EEFD1057E7283CF98C05B91C9E3D2 | |||
| 4008 | ff95e6d148e53e60b113f05bb54557315ec9b8af82adfaa276a21fbc561a9b77.exe.bin | C:\$WinREAgent\Scratch\WimTempPath\README_TO_DECRYPT.txt | text | |
MD5:6DDDE195C70E2AE3ACDA3137CCA97199 | SHA256:D436E835759629AB1394D19DFE03CA2A2E7EEFD1057E7283CF98C05B91C9E3D2 | |||
| 4008 | ff95e6d148e53e60b113f05bb54557315ec9b8af82adfaa276a21fbc561a9b77.exe.bin | C:\Program Files\README_TO_DECRYPT.txt | text | |
MD5:6DDDE195C70E2AE3ACDA3137CCA97199 | SHA256:D436E835759629AB1394D19DFE03CA2A2E7EEFD1057E7283CF98C05B91C9E3D2 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
31
DNS requests
19
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1812 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
1812 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 40.126.31.3:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1812 | SIHClient.exe | 20.109.210.53:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |