| File name: | 80.exe |
| Full analysis: | https://app.any.run/tasks/f7613608-1387-4a3f-8ce3-ee55d9426c85 |
| Verdict: | Malicious activity |
| Threats: | A loader is malicious software that infiltrates devices to deliver malicious payloads. This malware is capable of infecting victims’ computers, analyzing their system information, and installing other types of threats, such as trojans or stealers. Criminals usually deliver loaders through phishing emails and links by relying on social engineering to trick users into downloading and running their executables. Loaders employ advanced evasion and persistence tactics to avoid detection. |
| Analysis date: | March 25, 2025, 06:15:52 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 5 sections |
| MD5: | 06A143D6FB0FD06DE5AB2FB828866B57 |
| SHA1: | 6BE0FEA9DD9A271FF1CD3A0D8AD8BD93396E3ED5 |
| SHA256: | 034D6ECB85D1AD5EF8B0F75DD5012436265827083EEBFAC015561981EEF74015 |
| SSDEEP: | 49152:1BZ1paWQbTU6jt04TPkux/0IcApb3op4957axRf9JOcZZ8mHL7kFjhYBwDqLcf/r:H97OU6jt04TPH/bcYoy57cfJVZx/kFtz |
MALICIOUS
VIDAR has been detected (SURICATA)
- 80.exe (PID: 4776)
SUSPICIOUS
There is functionality for taking screenshot (YARA)
- 80.exe (PID: 4776)
Reads security settings of Internet Explorer
- 80.exe (PID: 4776)
Process requests binary or script from the Internet
- 80.exe (PID: 4776)
INFO
Checks proxy server information
- 80.exe (PID: 4776)
- slui.exe (PID: 6760)
The sample compiled with english language support
- 80.exe (PID: 4776)
Reads the machine GUID from the registry
- 80.exe (PID: 4776)
Checks supported languages
- 80.exe (PID: 4776)
Reads the computer name
- 80.exe (PID: 4776)
Creates files in the program directory
- 80.exe (PID: 4776)
Reads the software policy settings
- slui.exe (PID: 6760)
- slui.exe (PID: 2140)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:08:30 18:13:47+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 600576 |
| InitializedDataSize: | 686592 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x7a968 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.2.8.4 |
| ProductVersionNumber: | 1.2.8.4 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| Languages: | English |
| PrivateBuild: | 1.2.8.4 |
| OriginalFileName: | Succumb.exe |
| FileDescription: | Distribute Ipconfig Links Url |
| LegalTrademarks: | FileVersion Copyright © 2000 - 2014 KG and its Licensors |
| LegalCopyright: | FileVersion Copyright © 2000 - 2014 KG and its Licensors |
| CompanyName: | FileVersion |
| ProductName: | Succumb |
| ProductVersion: | 1.2.8.4 |
Total processes
148
Monitored processes
5
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2140 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4776 | "C:\Users\admin\AppData\Local\Temp\80.exe" | C:\Users\admin\AppData\Local\Temp\80.exe | explorer.exe | ||||||||||||
User: admin Company: FileVersion Integrity Level: MEDIUM Description: Distribute Ipconfig Links Url Modules
| |||||||||||||||
| 5596 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6760 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
7 190
Read events
7 187
Write events
3
Delete events
0
Modification events
| (PID) Process: | (4776) 80.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (4776) 80.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (4776) 80.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
Executable files
0
Suspicious files
0
Text files
6
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
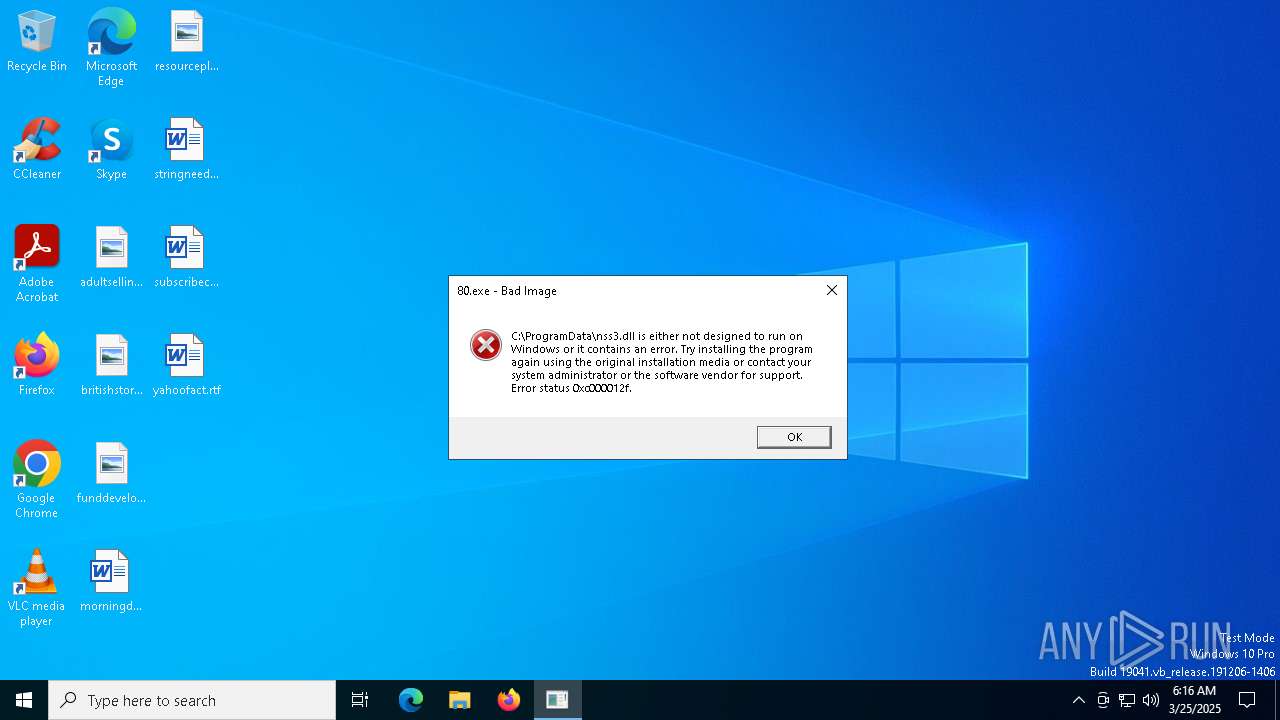
| 4776 | 80.exe | C:\ProgramData\freebl3.dll | xml | |
MD5:1EC31972EC65A65470D3B5D790C1F401 | SHA256:664F2B1654C363A6348B688D5D475ED9EC0E7EF3C72F6F315F37FE97A2FE63EB | |||
| 4776 | 80.exe | C:\ProgramData\nss3.dll | xml | |
MD5:1EC31972EC65A65470D3B5D790C1F401 | SHA256:664F2B1654C363A6348B688D5D475ED9EC0E7EF3C72F6F315F37FE97A2FE63EB | |||
| 4776 | 80.exe | C:\ProgramData\mozglue.dll | xml | |
MD5:1EC31972EC65A65470D3B5D790C1F401 | SHA256:664F2B1654C363A6348B688D5D475ED9EC0E7EF3C72F6F315F37FE97A2FE63EB | |||
| 4776 | 80.exe | C:\ProgramData\softokn3.dll | xml | |
MD5:1EC31972EC65A65470D3B5D790C1F401 | SHA256:664F2B1654C363A6348B688D5D475ED9EC0E7EF3C72F6F315F37FE97A2FE63EB | |||
| 4776 | 80.exe | C:\ProgramData\vcruntime140.dll | xml | |
MD5:1EC31972EC65A65470D3B5D790C1F401 | SHA256:664F2B1654C363A6348B688D5D475ED9EC0E7EF3C72F6F315F37FE97A2FE63EB | |||
| 4776 | 80.exe | C:\ProgramData\msvcp140.dll | xml | |
MD5:1EC31972EC65A65470D3B5D790C1F401 | SHA256:664F2B1654C363A6348B688D5D475ED9EC0E7EF3C72F6F315F37FE97A2FE63EB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
50
DNS requests
26
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4776 | 80.exe | POST | 404 | 49.13.77.253:80 | http://eroomia.com/288 | unknown | — | — | malicious |
4776 | 80.exe | GET | 404 | 49.13.77.253:80 | http://eroomia.com/freebl3.dll | unknown | — | — | unknown |
4776 | 80.exe | GET | 404 | 49.13.77.253:80 | http://eroomia.com/mozglue.dll | unknown | — | — | unknown |
4776 | 80.exe | GET | 404 | 49.13.77.253:80 | http://eroomia.com/msvcp140.dll | unknown | — | — | unknown |
4776 | 80.exe | GET | 404 | 49.13.77.253:80 | http://eroomia.com/softokn3.dll | unknown | — | — | unknown |
4776 | 80.exe | GET | 404 | 49.13.77.253:80 | http://eroomia.com/nss3.dll | unknown | — | — | unknown |
4776 | 80.exe | GET | 404 | 49.13.77.253:80 | http://eroomia.com/vcruntime140.dll | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2112 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2104 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4776 | 80.exe | 49.13.77.253:80 | eroomia.com | Hetzner Online GmbH | DE | malicious |
3216 | svchost.exe | 40.113.110.67:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 20.190.159.130:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6592 | backgroundTaskHost.exe | 20.31.169.57:443 | arc.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3216 | svchost.exe | 40.113.103.199:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
eroomia.com |
| malicious |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
arc.msn.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
206.23.85.13.in-addr.arpa |
| unknown |
d.3.0.0.0.0.0.0.0.0.0.0.0.0.0.0.7.0.0.0.8.0.4.0.0.3.0.1.3.0.6.2.ip6.arpa |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4776 | 80.exe | A suspicious filename was detected | ET HUNTING HTTP GET Request for freebl3.dll - Possible Infostealer Activity |
4776 | 80.exe | A suspicious filename was detected | ET HUNTING HTTP GET Request for softokn3.dll - Possible Infostealer Activity |
4776 | 80.exe | A suspicious filename was detected | ET HUNTING HTTP GET Request for nss3.dll - Possible Infostealer Activity |
4776 | 80.exe | A suspicious filename was detected | ET HUNTING HTTP GET Request for mozglue.dll - Possible Infostealer Activity |
4776 | 80.exe | A Network Trojan was detected | ET MALWARE Vidar/Arkei/Megumin/Oski Stealer HTTP POST Pattern |
4776 | 80.exe | A suspicious filename was detected | ET HUNTING HTTP GET Request for vcruntime140.dll - Possible Infostealer Activity |