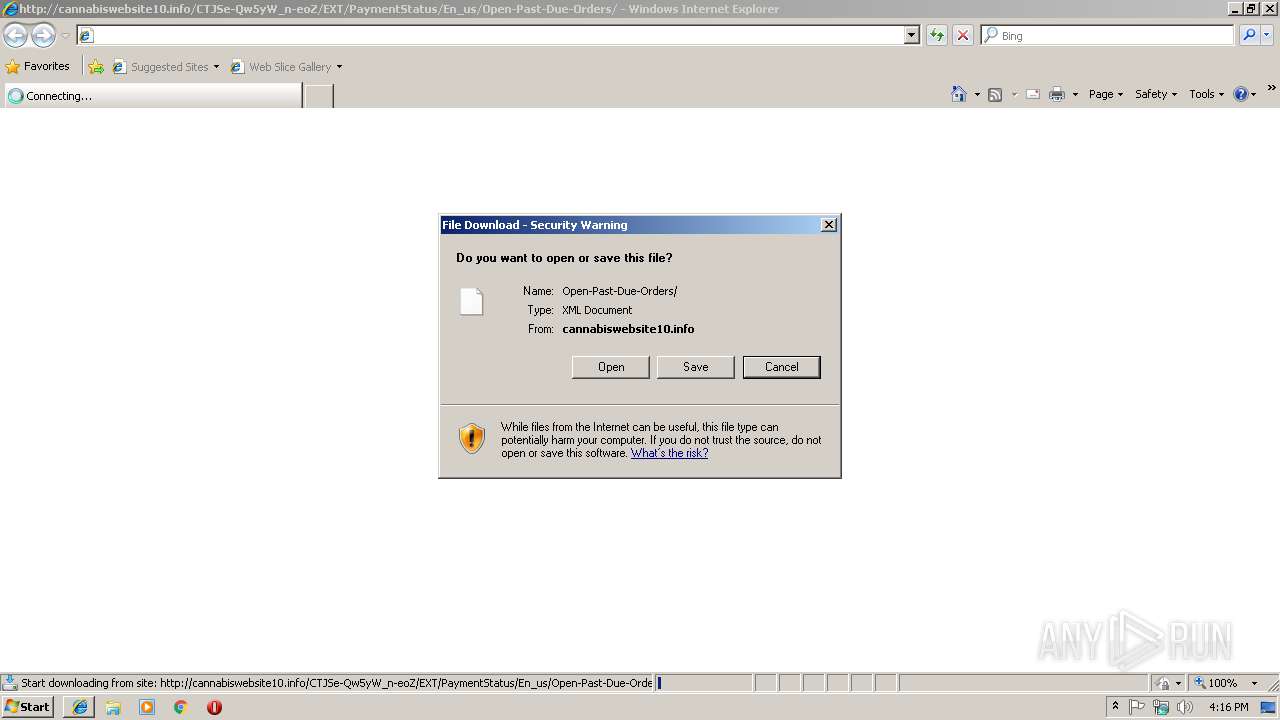
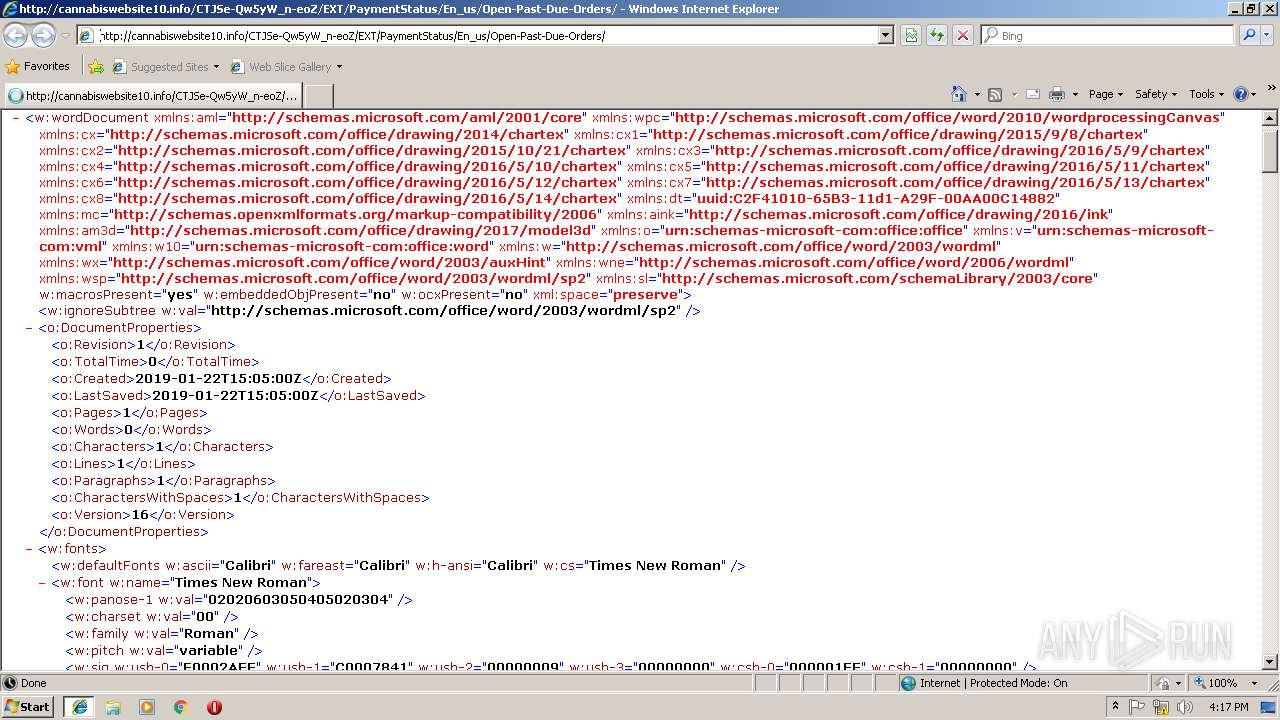
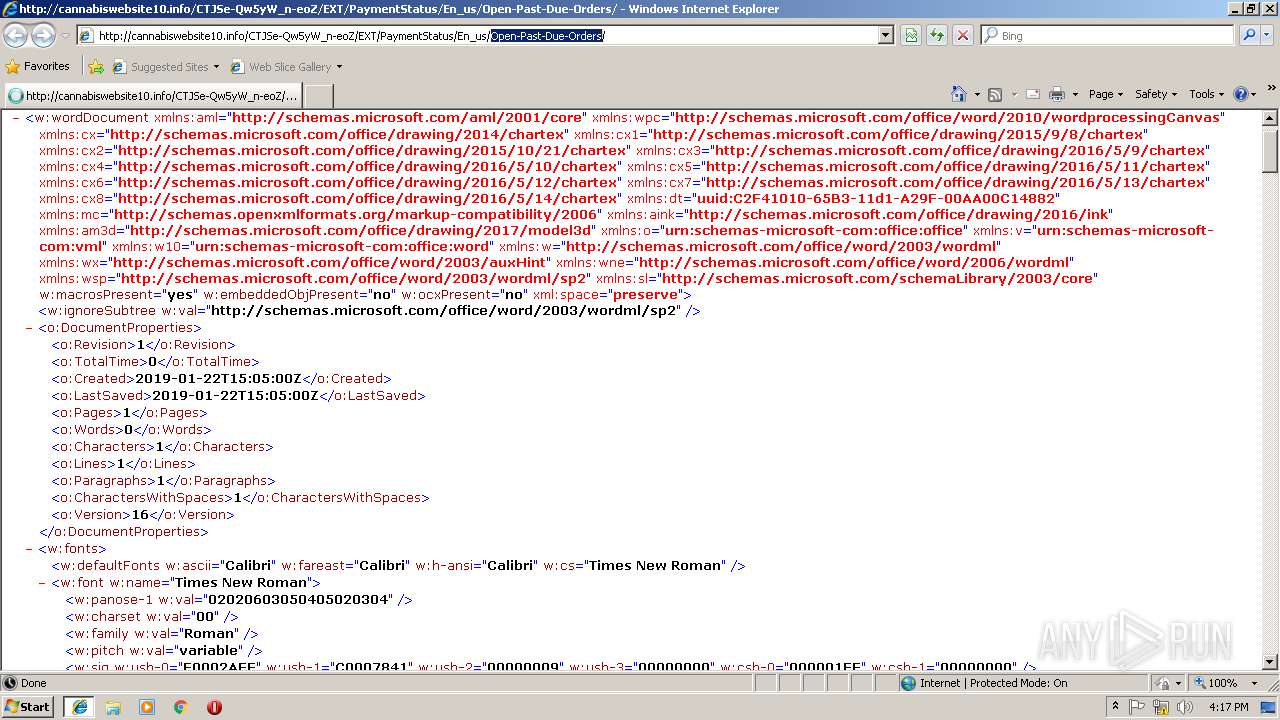
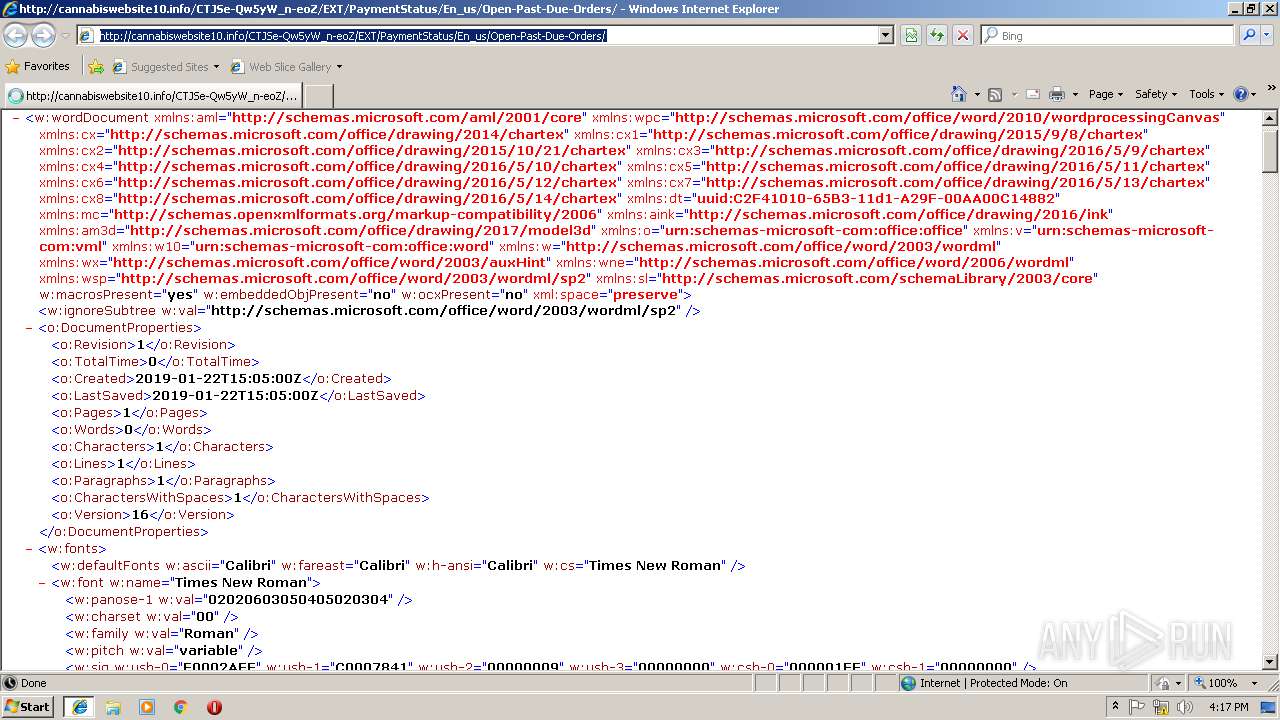
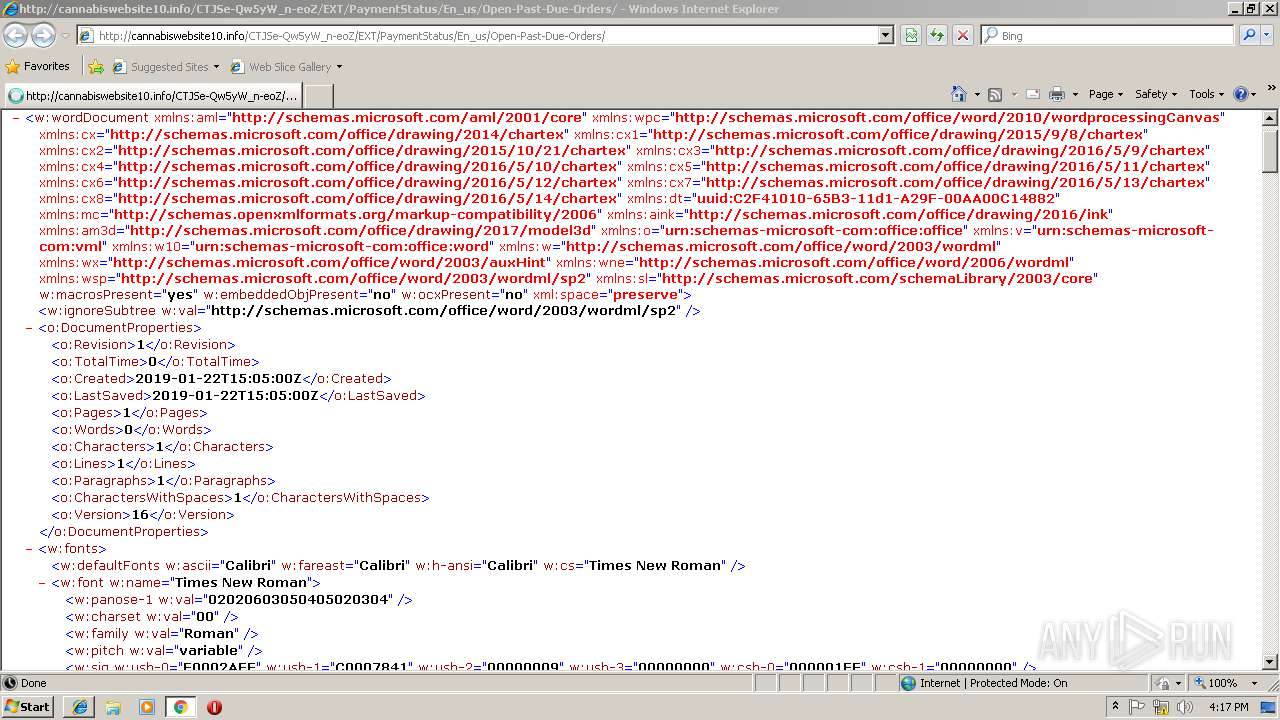
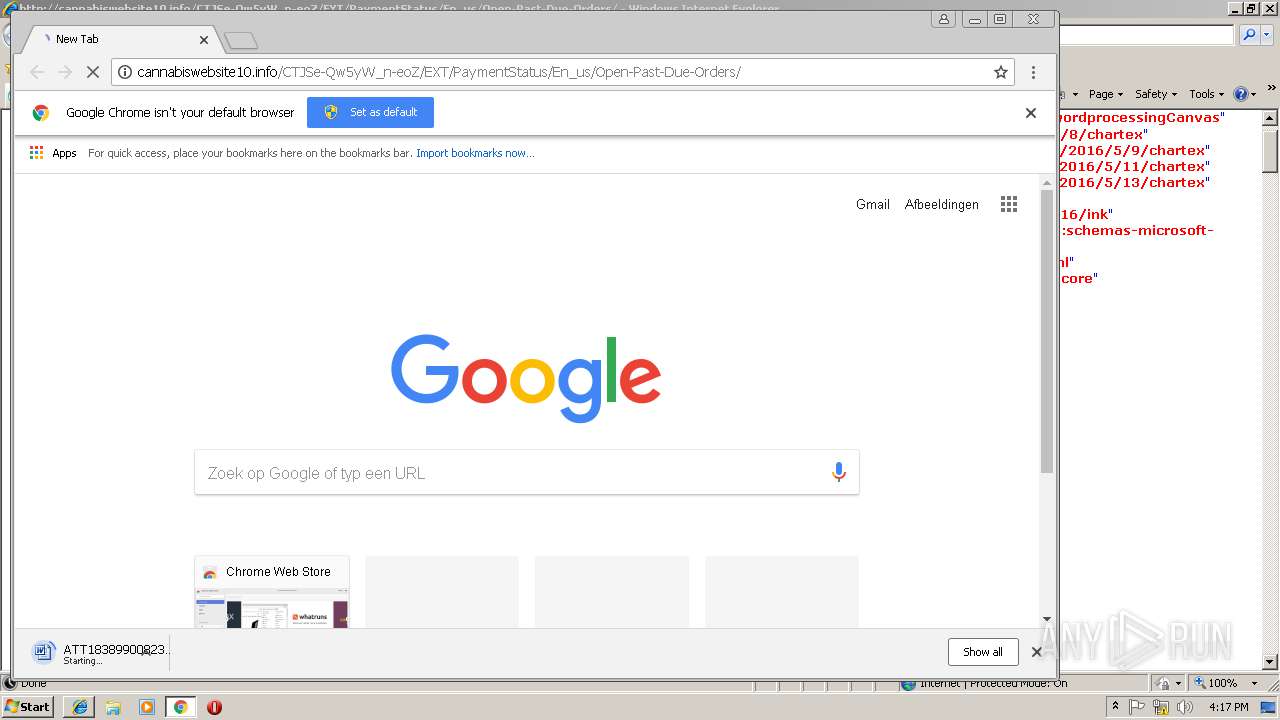
| URL: | http://cannabiswebsite10.info/CTJSe-Qw5yW_n-eoZ/EXT/PaymentStatus/En_us/Open-Past-Due-Orders |
| Full analysis: | https://app.any.run/tasks/09108f8b-c000-47f6-9465-77f15fd3aac9 |
| Verdict: | Malicious activity |
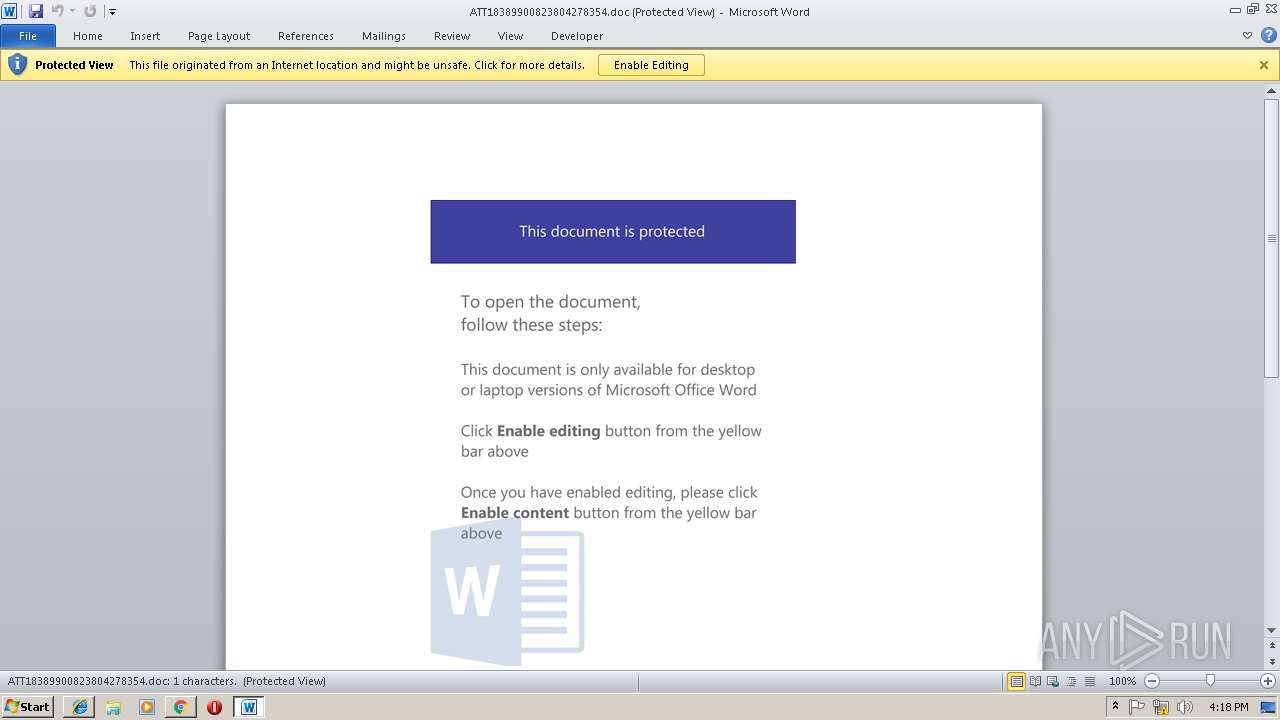
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | January 22, 2019, 16:15:54 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | C59D706CB10817ACC6C786792F387D80 |
| SHA1: | 2BD2B0CF7024507F58EE8401F2835A3459F0E948 |
| SHA256: | 033F48846C0F92E00FD4C2E8EB48D4918BB993483B1A7DD72780394487362680 |
| SSDEEP: | 3:N1KdE/EiGHYRmthcy6m3ut2yOnHOWIhVIFG:CGMqAt/XnuWIGG |
MALICIOUS
No malicious indicators.SUSPICIOUS
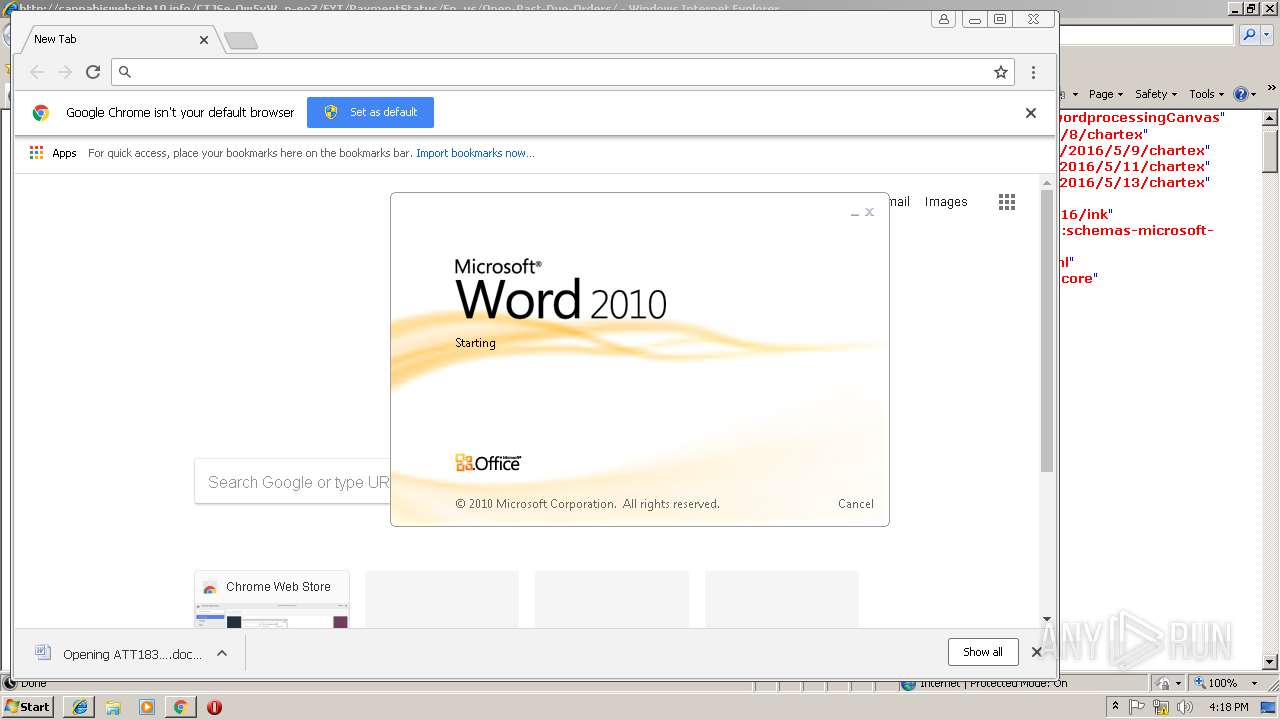
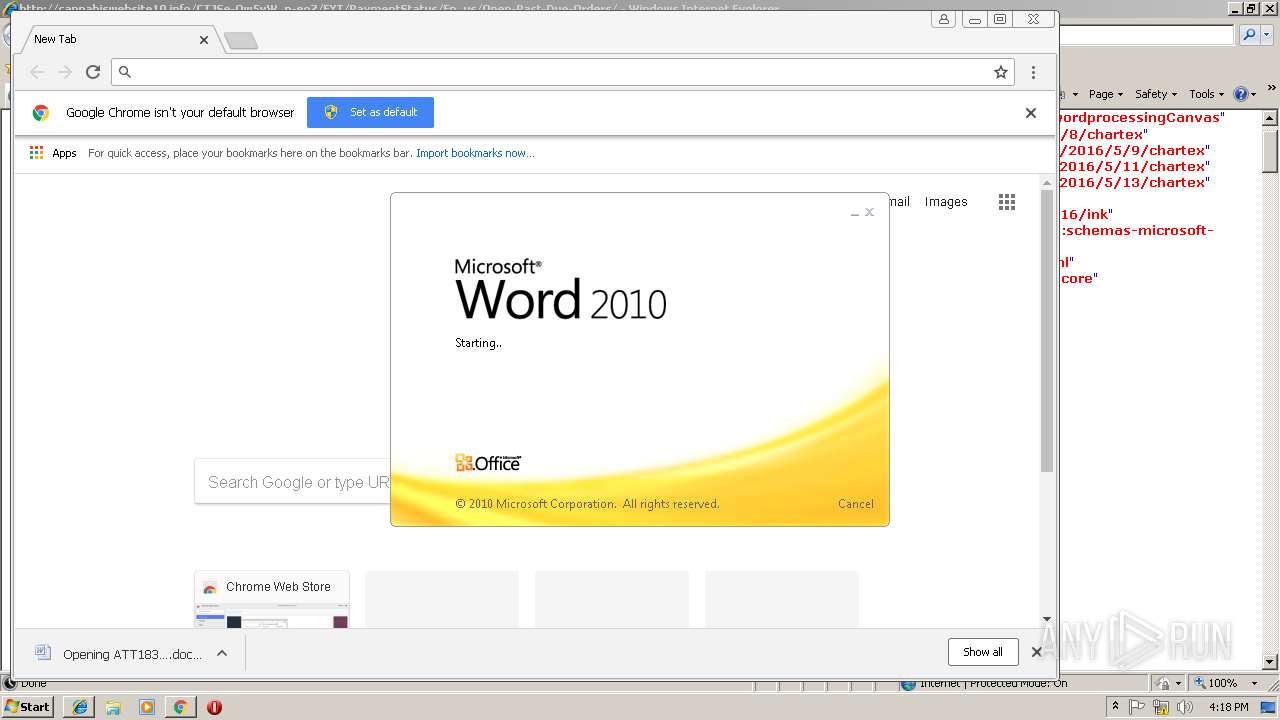
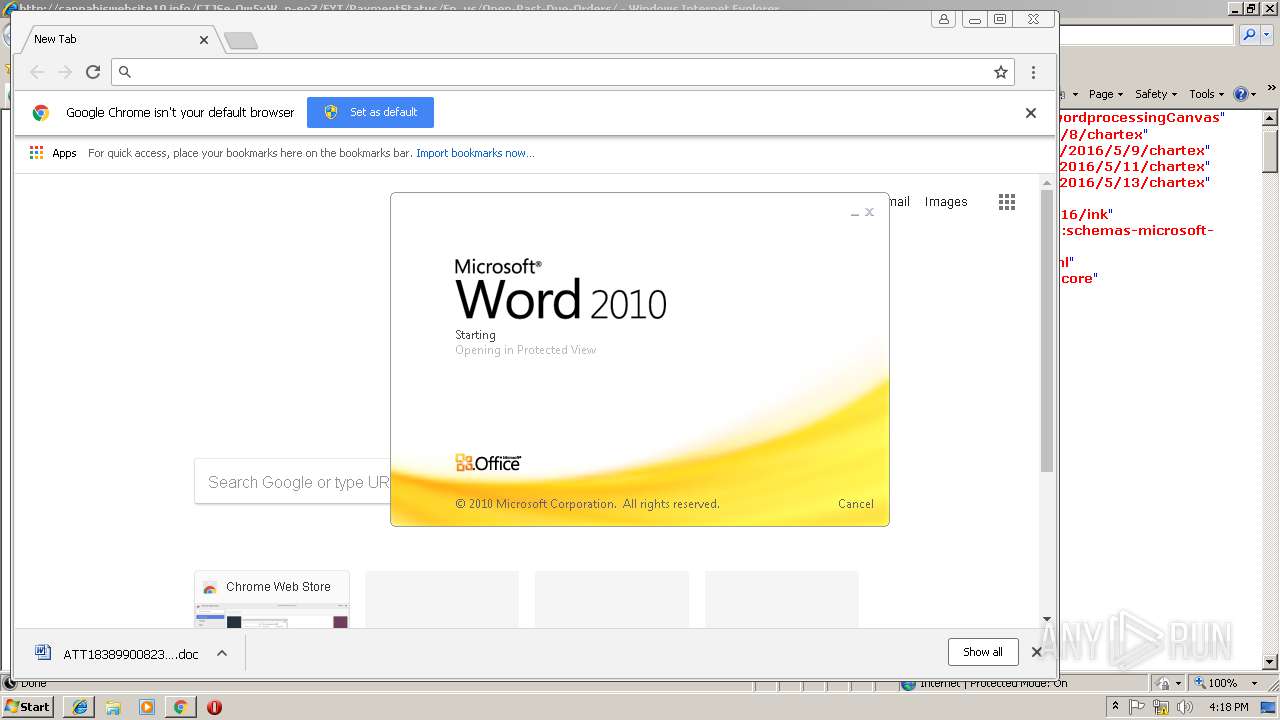
Starts Microsoft Office Application
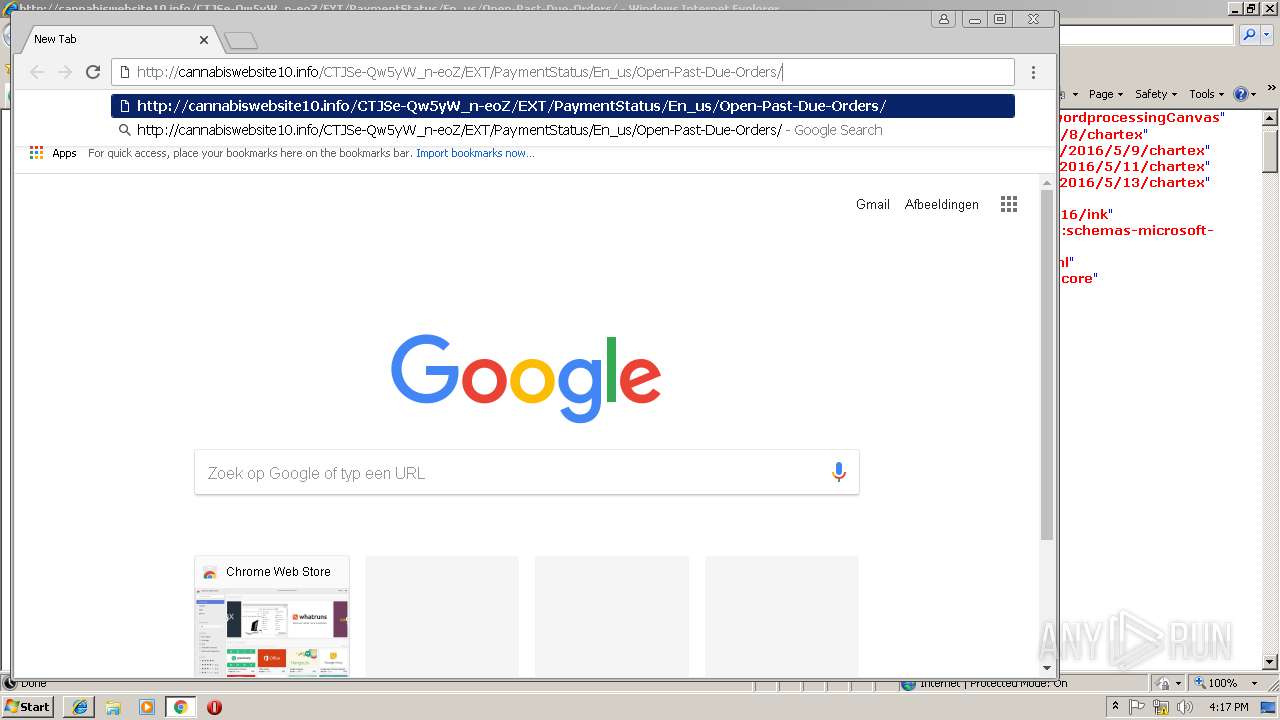
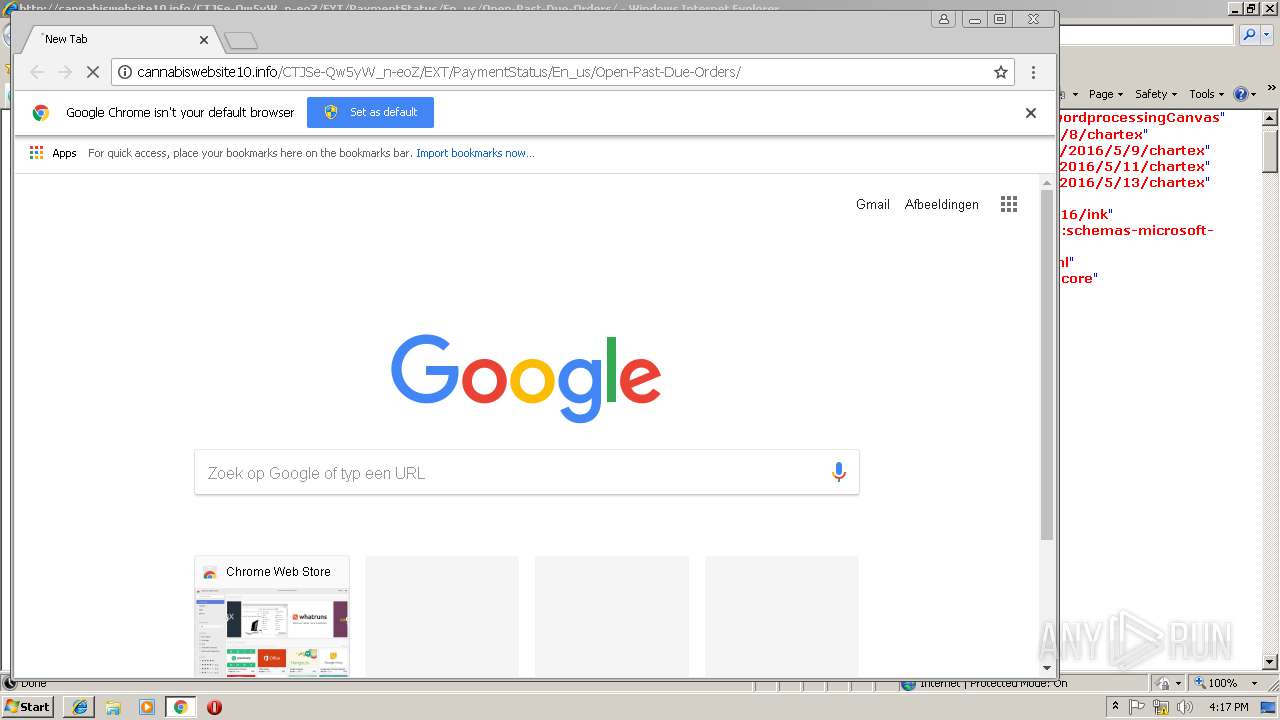
- chrome.exe (PID: 1104)
- WINWORD.EXE (PID: 3076)
Application launched itself
- WINWORD.EXE (PID: 3076)
INFO
Application launched itself
- iexplore.exe (PID: 2984)
- chrome.exe (PID: 1104)
Changes internet zones settings
- iexplore.exe (PID: 2984)
Reads internet explorer settings
- iexplore.exe (PID: 3264)
Reads Internet Cache Settings
- chrome.exe (PID: 1104)
- iexplore.exe (PID: 3264)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3076)
- WINWORD.EXE (PID: 2536)
Creates files in the user directory
- WINWORD.EXE (PID: 3076)
Reads settings of System Certificates
- chrome.exe (PID: 1104)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
49
Monitored processes
16
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1044 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,9929272544047055351,629949129359091420,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=D810C1B5BCC9A2ADAD45451F5CEFCEA8 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=D810C1B5BCC9A2ADAD45451F5CEFCEA8 --renderer-client-id=8 --mojo-platform-channel-handle=3812 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1104 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1780 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1004,9929272544047055351,629949129359091420,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=F74CD59AC143F157334D1F464280219A --mojo-platform-channel-handle=976 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1848 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,9929272544047055351,629949129359091420,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=E196CB801EAD1914265AADAC11CEC1B5 --mojo-platform-channel-handle=4028 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1964 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,9929272544047055351,629949129359091420,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=AF131D898E777BC0DE42765A313366AF --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=AF131D898E777BC0DE42765A313366AF --renderer-client-id=6 --mojo-platform-channel-handle=3536 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2392 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1004,9929272544047055351,629949129359091420,131072 --enable-features=PasswordImport --disable-gpu-sandbox --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=DC99B74B60C493841F7BEEAFA9D535F0 --mojo-platform-channel-handle=4004 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2404 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,9929272544047055351,629949129359091420,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=81638C9B1FCAF97F566B4AEDC97B93D5 --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=81638C9B1FCAF97F566B4AEDC97B93D5 --renderer-client-id=7 --mojo-platform-channel-handle=3408 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2536 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2620 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,9929272544047055351,629949129359091420,131072 --enable-features=PasswordImport --service-pipe-token=4B69DF131B69165F6B319A7A2CDDA37D --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4B69DF131B69165F6B319A7A2CDDA37D --renderer-client-id=5 --mojo-platform-channel-handle=1928 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2820 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2852 --on-initialized-event-handle=304 --parent-handle=308 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
2 589
Read events
2 143
Write events
433
Delete events
13
Modification events
| (PID) Process: | (2984) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2984) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2984) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2984) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2984) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2984) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000069000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2984) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {07B4EF33-1E61-11E9-AA93-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (2984) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (2984) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 3 | |||
| (PID) Process: | (2984) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E307010002001600100010000B00BB01 | |||
Executable files
0
Suspicious files
43
Text files
65
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2984 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2984 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 1104 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\127463d7-6148-4730-8964-c13a4dfc3663.tmp | — | |
MD5:— | SHA256:— | |||
| 1104 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1104 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3264 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\Low\History.IE5\MSHist012019012220190123\index.dat | dat | |
MD5:— | SHA256:— | |||
| 1104 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\e0dea4cd-c6ea-43f5-8d2f-699daa25de2e.tmp | — | |
MD5:— | SHA256:— | |||
| 1104 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:— | SHA256:— | |||
| 2984 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\favicon[3].png | image | |
MD5:9FB559A691078558E77D6848202F6541 | SHA256:6D8A01DC7647BC218D003B58FE04049E24A9359900B7E0CEBAE76EDF85B8B914 | |||
| 2984 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\History.IE5\MSHist012019012220190123\index.dat | dat | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
21
DNS requests
14
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
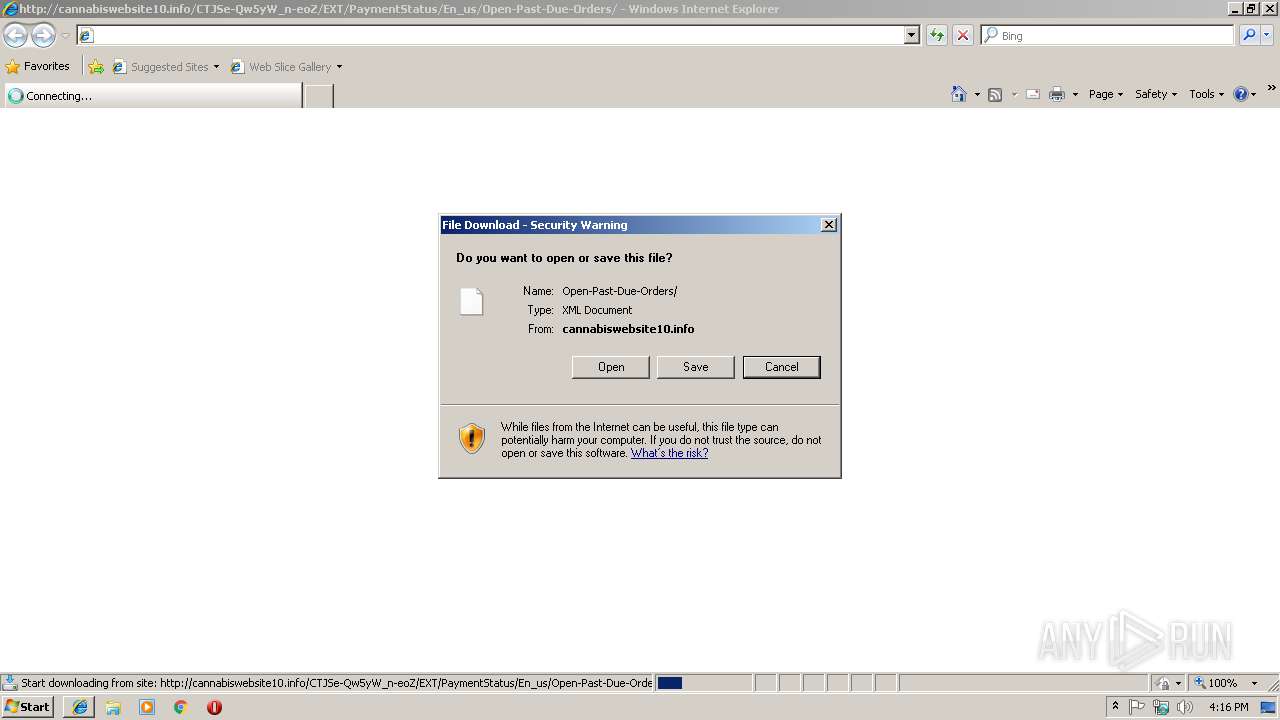
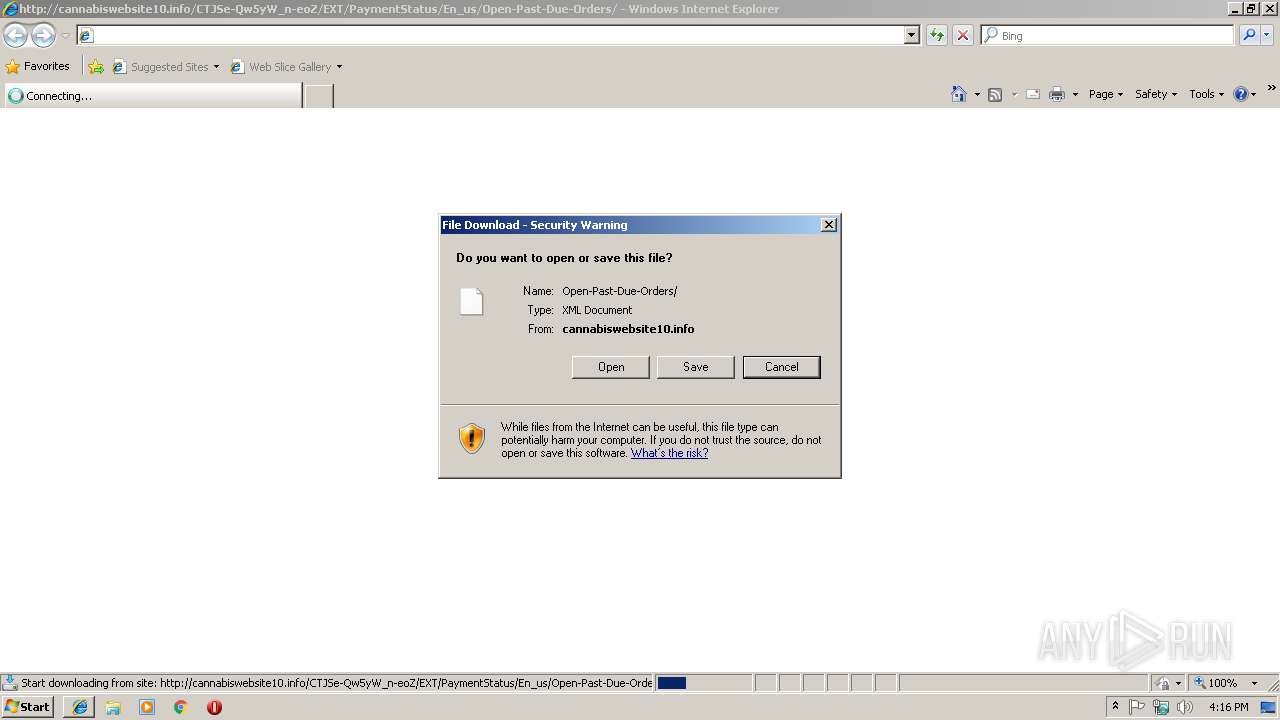
3264 | iexplore.exe | GET | — | 66.117.4.100:80 | http://cannabiswebsite10.info/CTJSe-Qw5yW_n-eoZ/EXT/PaymentStatus/En_us/Open-Past-Due-Orders/ | US | — | — | malicious |
3264 | iexplore.exe | GET | — | 66.117.4.100:80 | http://cannabiswebsite10.info/CTJSe-Qw5yW_n-eoZ/EXT/PaymentStatus/En_us/Open-Past-Due-Orders/ | US | — | — | malicious |
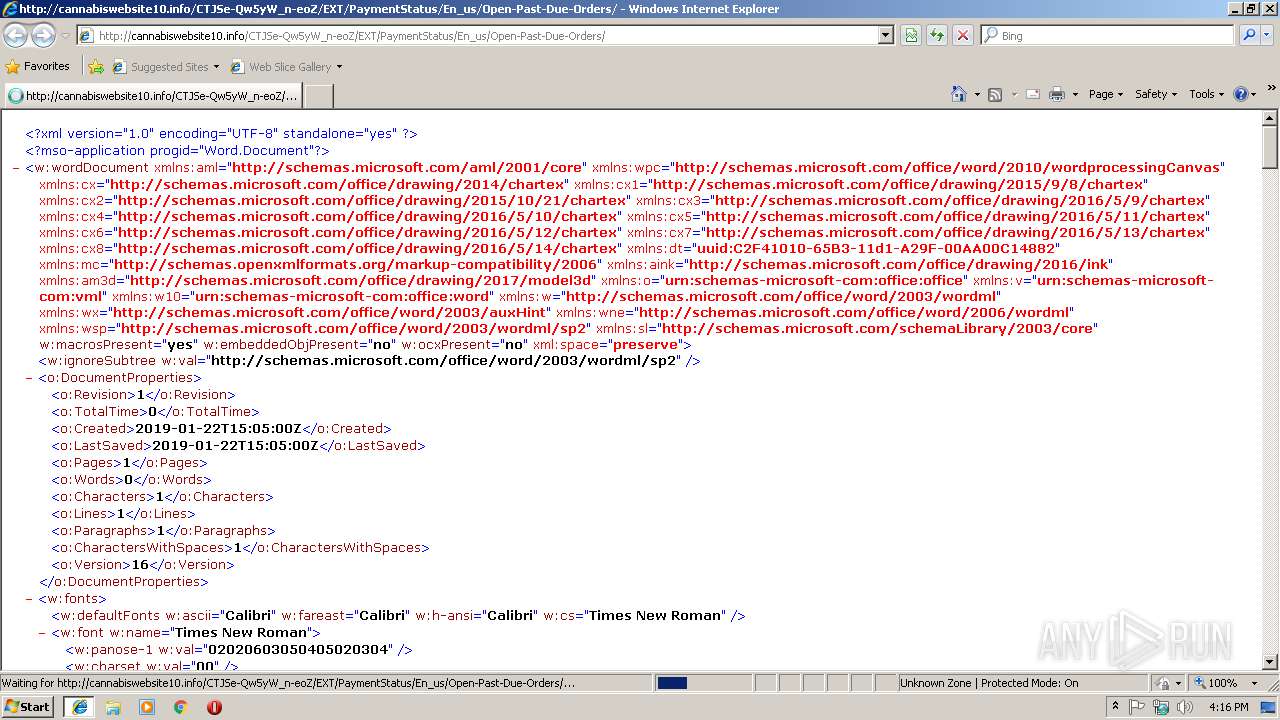
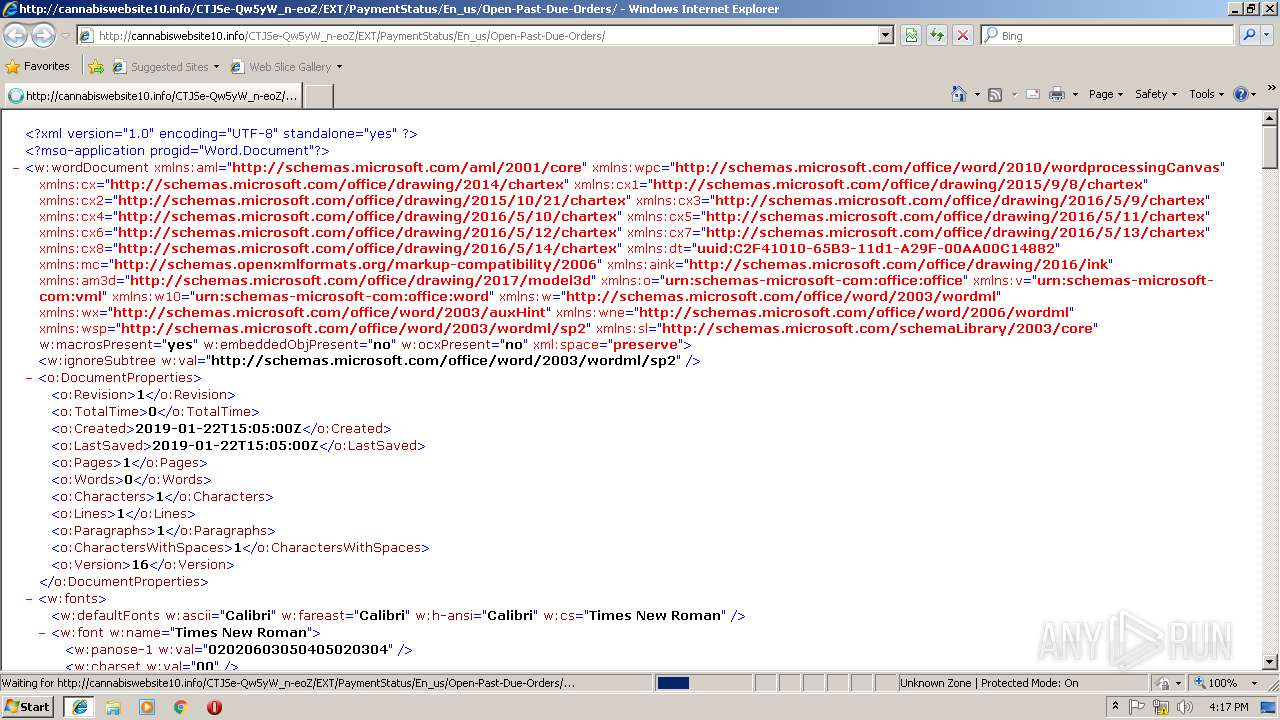
1104 | chrome.exe | GET | 200 | 66.117.4.100:80 | http://cannabiswebsite10.info/CTJSe-Qw5yW_n-eoZ/EXT/PaymentStatus/En_us/Open-Past-Due-Orders/ | US | xml | 199 Kb | malicious |
3264 | iexplore.exe | GET | 301 | 66.117.4.100:80 | http://cannabiswebsite10.info/CTJSe-Qw5yW_n-eoZ/EXT/PaymentStatus/En_us/Open-Past-Due-Orders | US | html | 301 b | malicious |
2984 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2984 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3264 | iexplore.exe | 66.117.4.100:80 | cannabiswebsite10.info | InMotion Hosting, Inc. | US | malicious |
1104 | chrome.exe | 216.58.208.35:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1104 | chrome.exe | 172.217.16.163:443 | www.google.de | Google Inc. | US | whitelisted |
1104 | chrome.exe | 216.58.206.10:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
1104 | chrome.exe | 172.217.18.109:443 | accounts.google.com | Google Inc. | US | suspicious |
1104 | chrome.exe | 172.217.18.174:443 | apis.google.com | Google Inc. | US | whitelisted |
1104 | chrome.exe | 66.117.4.100:80 | cannabiswebsite10.info | InMotion Hosting, Inc. | US | malicious |
1104 | chrome.exe | 216.58.207.35:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
1104 | chrome.exe | 172.217.18.3:443 | www.google.nl | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
cannabiswebsite10.info |
| malicious |
clientservices.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
www.google.de |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
ssl.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
www.google.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3264 | iexplore.exe | A Network Trojan was detected | ET TROJAN Possible malicious Office doc hidden in XML file |
1104 | chrome.exe | A Network Trojan was detected | ET TROJAN Possible malicious Office doc hidden in XML file |