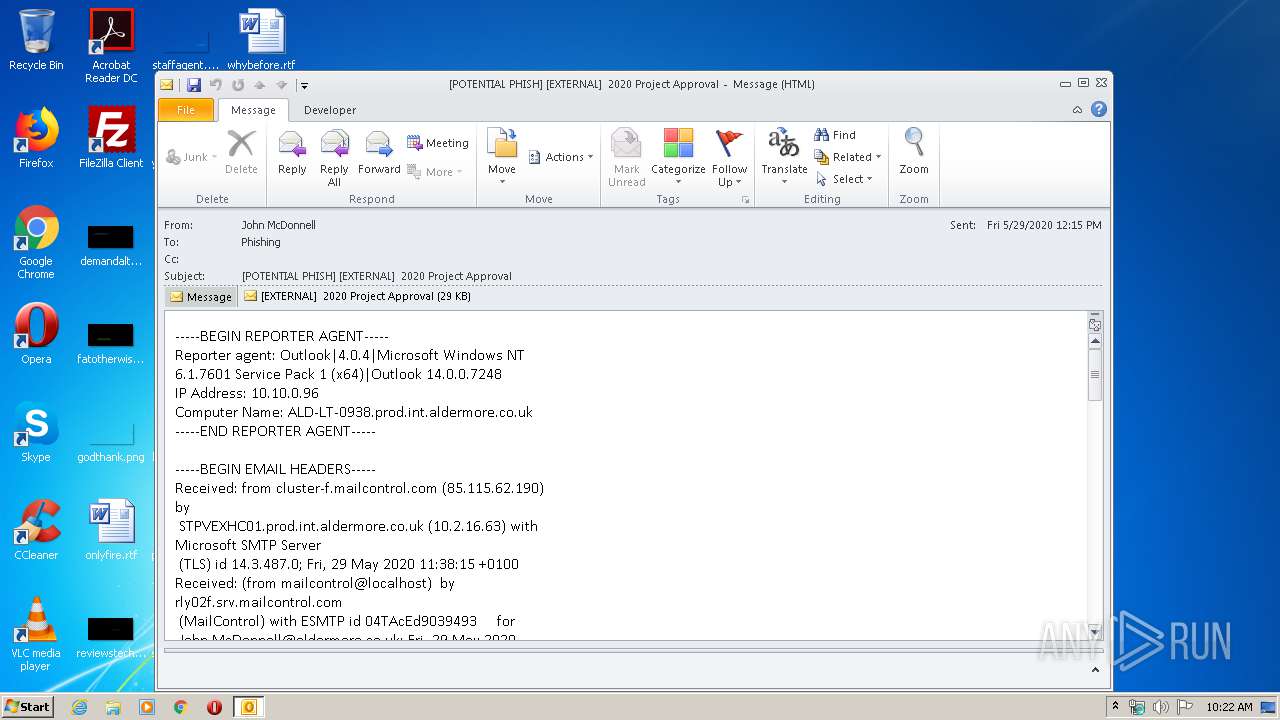
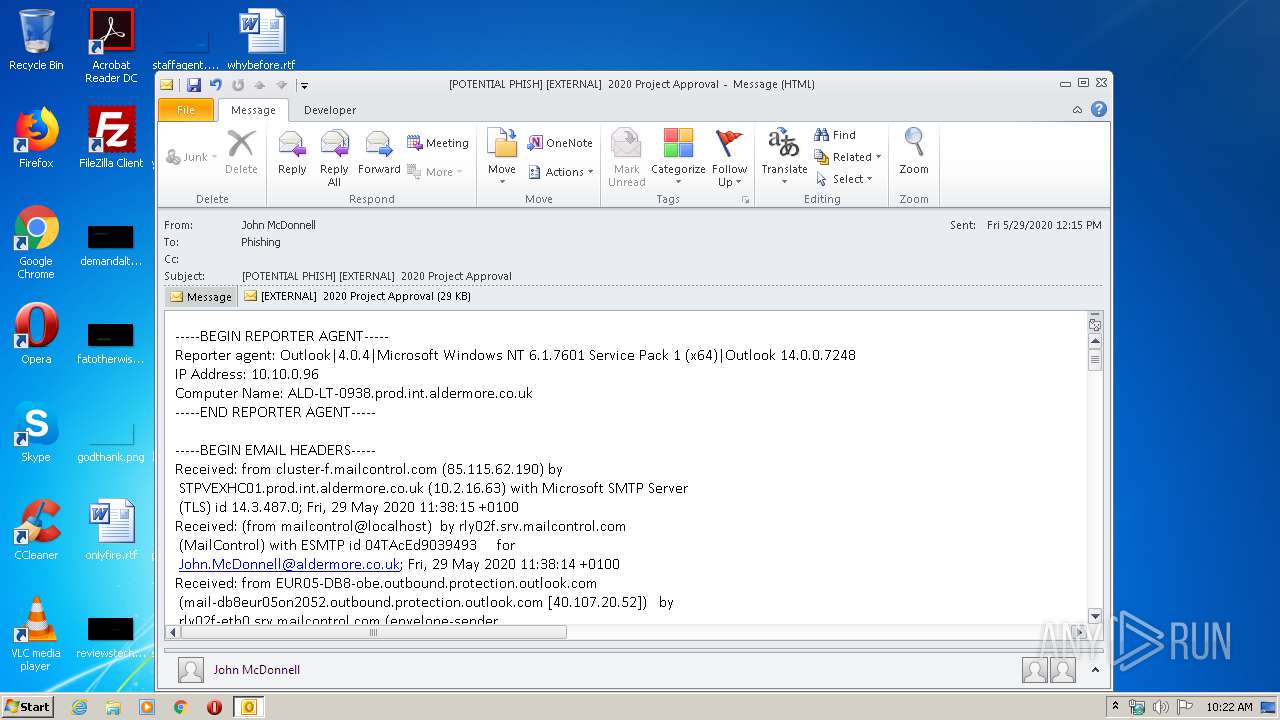
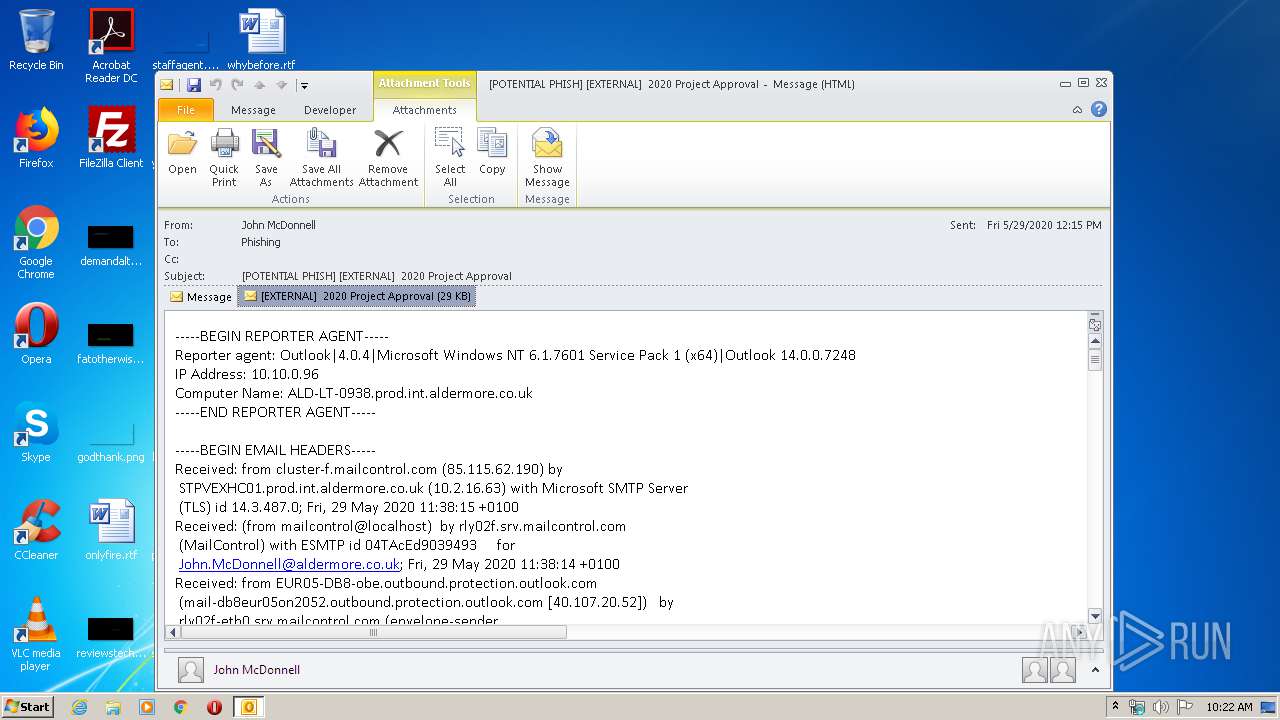
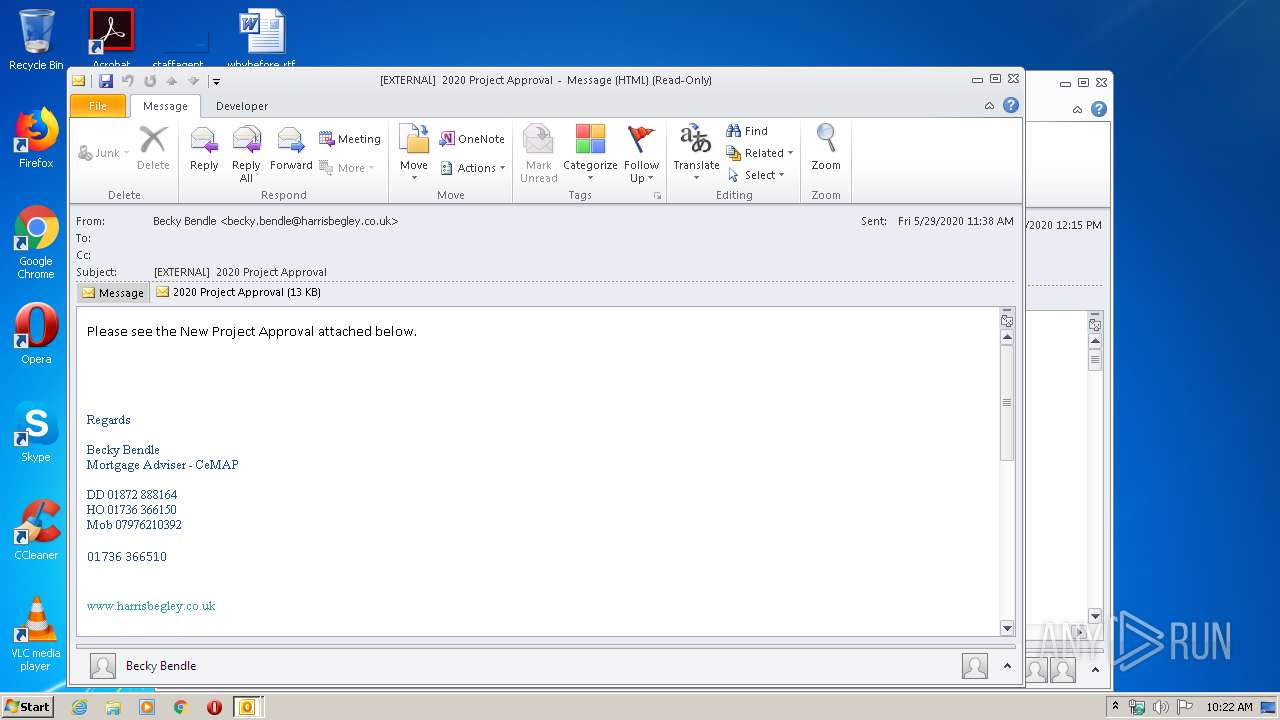
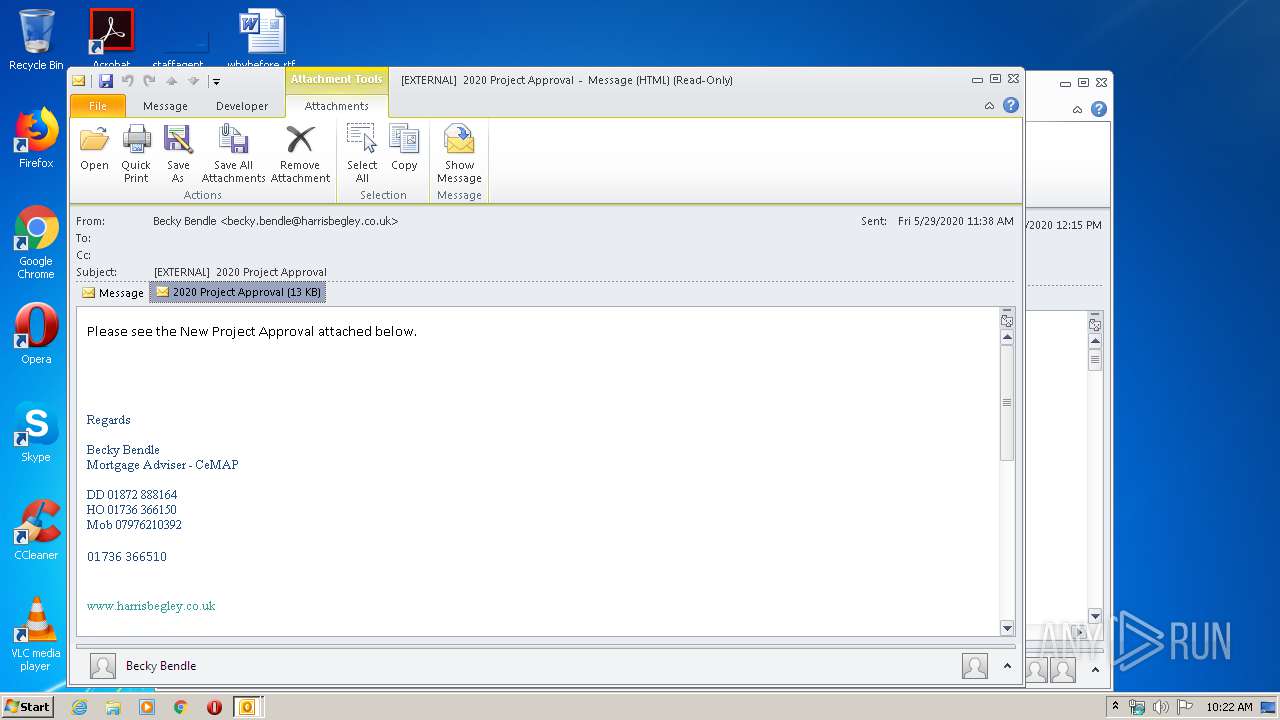
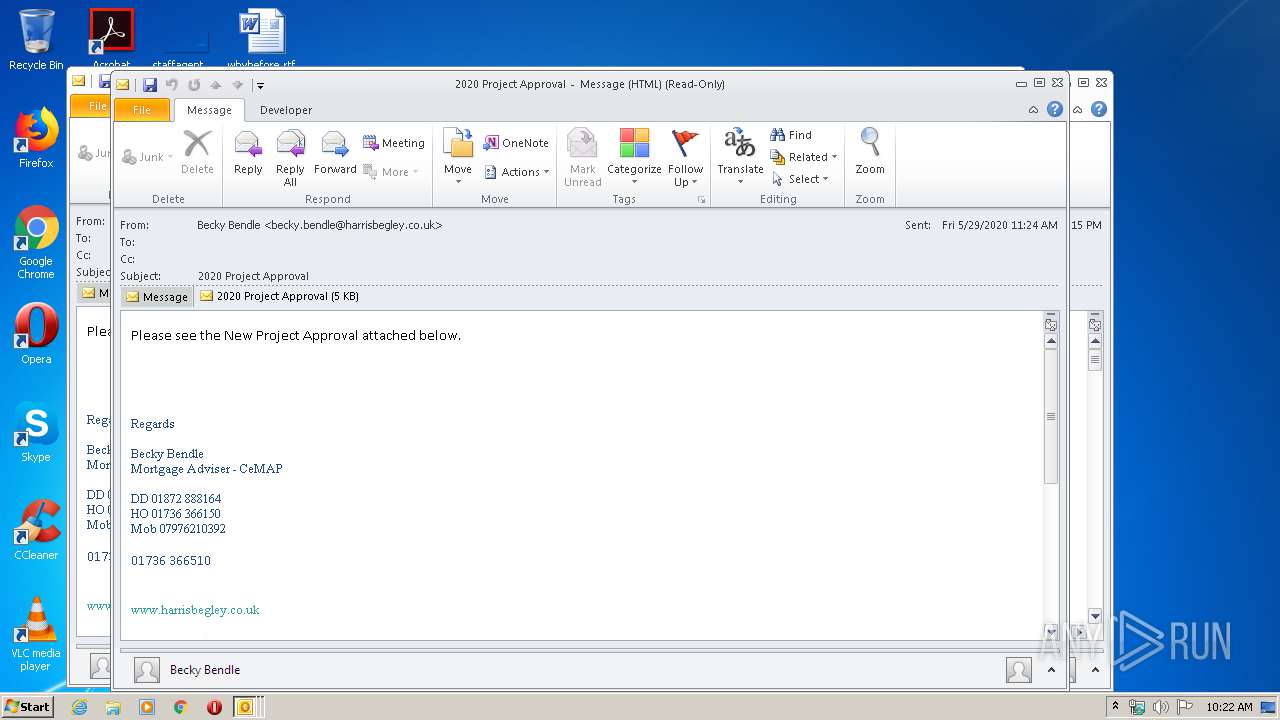
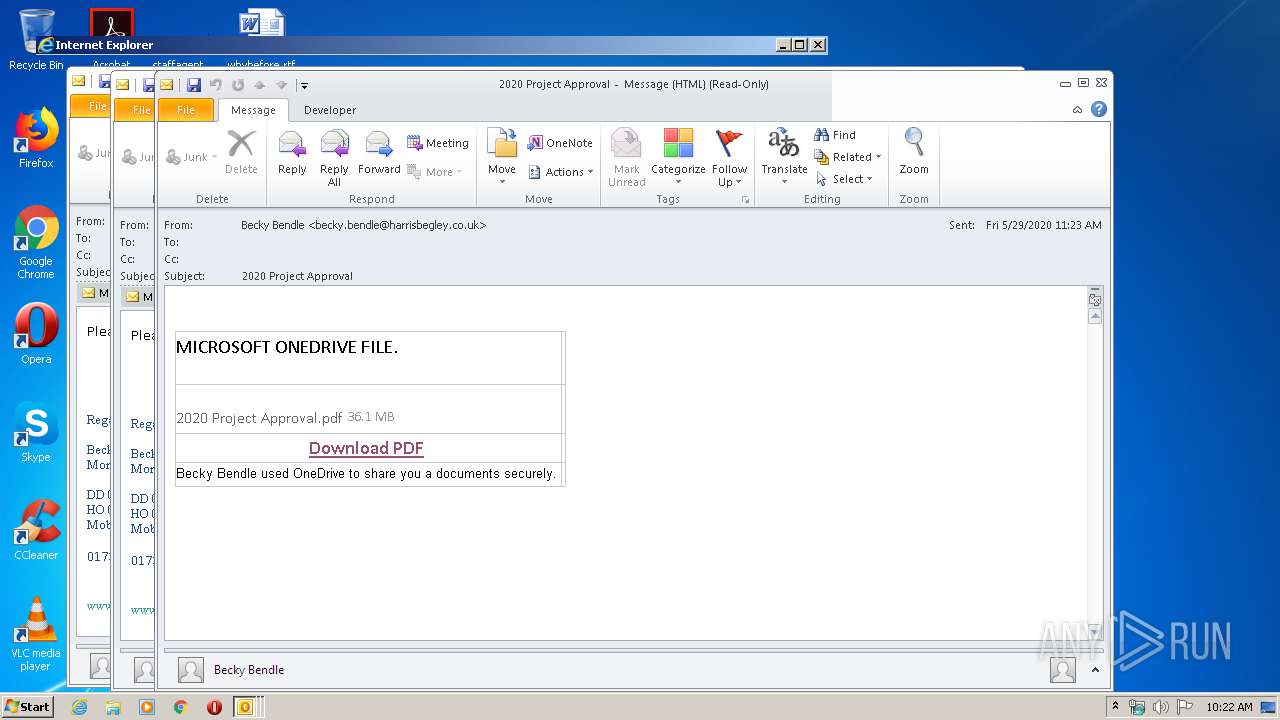
| File name: | POTENTIAL PHISH EXTERNAL 2020 Project Approval.msg |
| Full analysis: | https://app.any.run/tasks/6b0af056-6124-4a73-b303-25888854793e |
| Verdict: | Malicious activity |
| Analysis date: | May 30, 2020, 09:21:54 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | 06B7115B49ACCA13156DC4D6DE99989B |
| SHA1: | 2A96712CA565AD61A754682CEF205185A69A6EA5 |
| SHA256: | 032F285CF82AD7DF0FCB123FCEEC6FA73E39A239118151CEE9D390F742022C7C |
| SSDEEP: | 3072:xVQh+HlbrsHfK07bqTuNoxF5JhSMrKk+tgf1x+Ix:xVo+HaHfK07mTAM2kj+Y |
MALICIOUS
Unusual execution from Microsoft Office
- OUTLOOK.EXE (PID: 2456)
SUSPICIOUS
Creates files in the user directory
- OUTLOOK.EXE (PID: 2456)
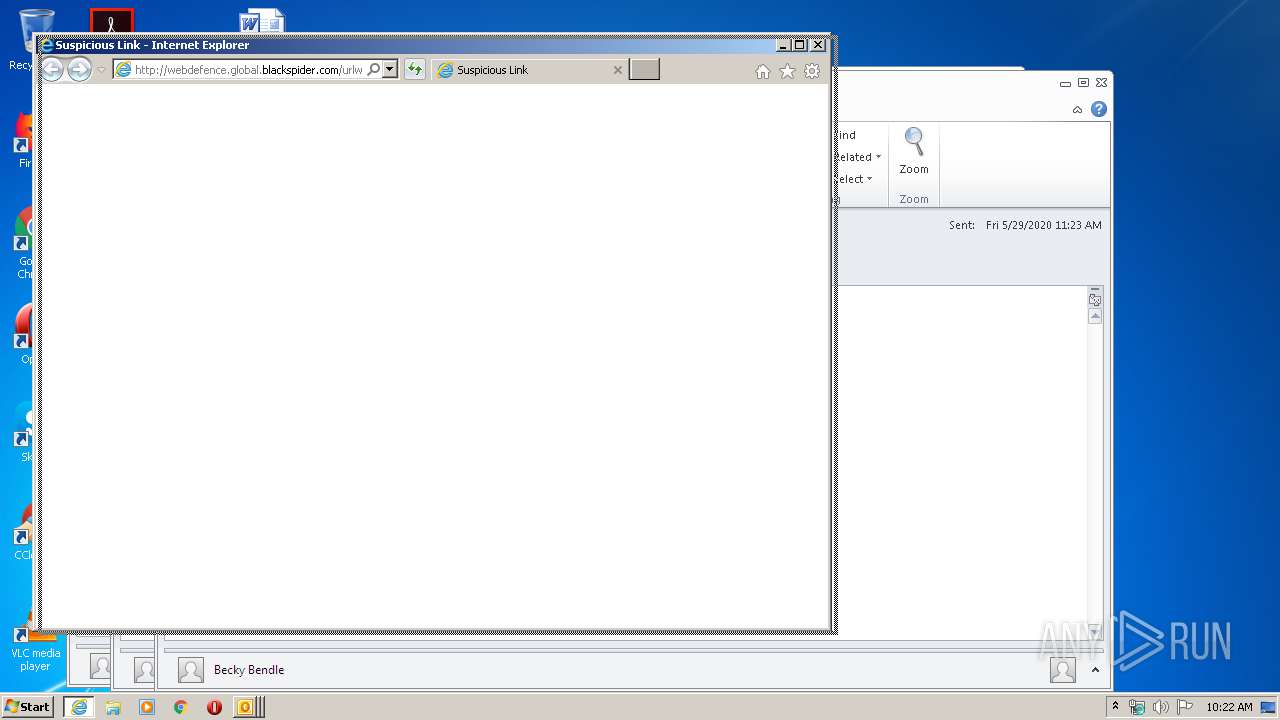
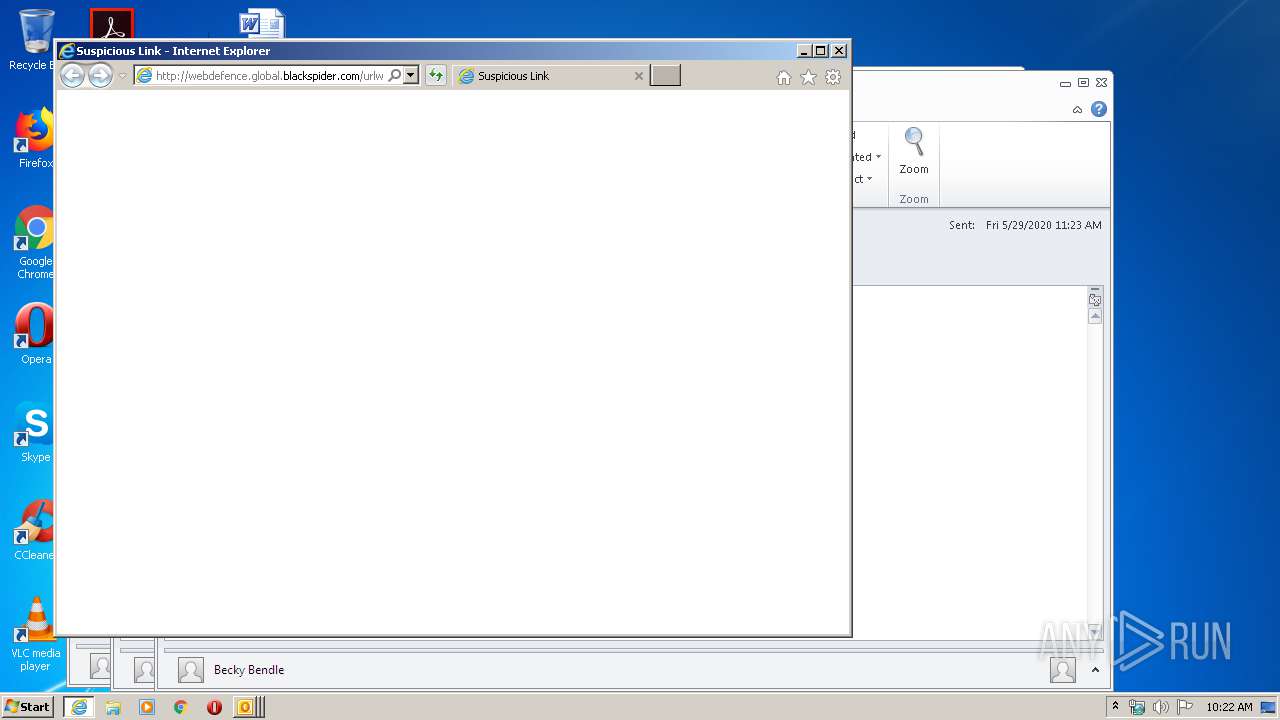
Starts Internet Explorer
- OUTLOOK.EXE (PID: 2456)
INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 1672)
- OUTLOOK.EXE (PID: 2456)
- iexplore.exe (PID: 1692)
Reads settings of System Certificates
- iexplore.exe (PID: 1692)
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 2456)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1692)
Changes settings of System certificates
- iexplore.exe (PID: 1692)
Reads internet explorer settings
- iexplore.exe (PID: 1672)
Changes internet zones settings
- iexplore.exe (PID: 1692)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (58.9) |
|---|---|---|
| .oft | | | Outlook Form Template (34.4) |
Total processes
40
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1672 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1692 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1692 | "C:\Program Files\Internet Explorer\iexplore.exe" http://webdefence.global.blackspider.com/urlwrap/?q=AXicbc2xTsMwFEDR15WuTEz8QO0oFBEiIVqUItIqBUrVIpbINU5i1fYLz05Q-AY-GtjZ79EdjeD7FODsHIDMEMUV89QzK7SR6AKhYRItRNPtXCbXj9FFEl_GsMTGsUJm6JwyZibMuyKLpH5b1h2hCaH1Keceu9B8Kh8qYbUZemE65aWWEzsw3whSLWoX_gY8PaS85q0ij04YLknouvzXl0h12R35YtNvlvsqS_Iwt19v1aqYvuxdcbd9iu71lV5MVlmCa3p4raXMn2_VTZbTB-4A4GQM8APyylM5&Z | C:\Program Files\Internet Explorer\iexplore.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2456 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\Users\admin\AppData\Local\Temp\POTENTIAL PHISH EXTERNAL 2020 Project Approval.msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
Total events
5 227
Read events
1 447
Write events
2 843
Delete events
937
Modification events
| (PID) Process: | (2456) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2456) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2456) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2456) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2456) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2456) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2456) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2456) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2456) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
| (PID) Process: | (2456) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1055 |
Value: Off | |||
Executable files
0
Suspicious files
3
Text files
37
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2456 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVRD461.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2456 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 1692 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2456 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\6A54E560.dat | image | |
MD5:— | SHA256:— | |||
| 1692 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2456 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\A013E5E1.dat | image | |
MD5:— | SHA256:— | |||
| 2456 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{5705AAB2-429E-4EFA-9EAB-ED06F03B2E87}.tmp | — | |
MD5:— | SHA256:— | |||
| 2456 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{192F6782-A41F-4406-BF97-1B0E041EAA0B}.tmp | — | |
MD5:— | SHA256:— | |||
| 2456 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\~DF987280E7555B32A0.TMP | — | |
MD5:— | SHA256:— | |||
| 1672 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\urlwrap[1].htm | html | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
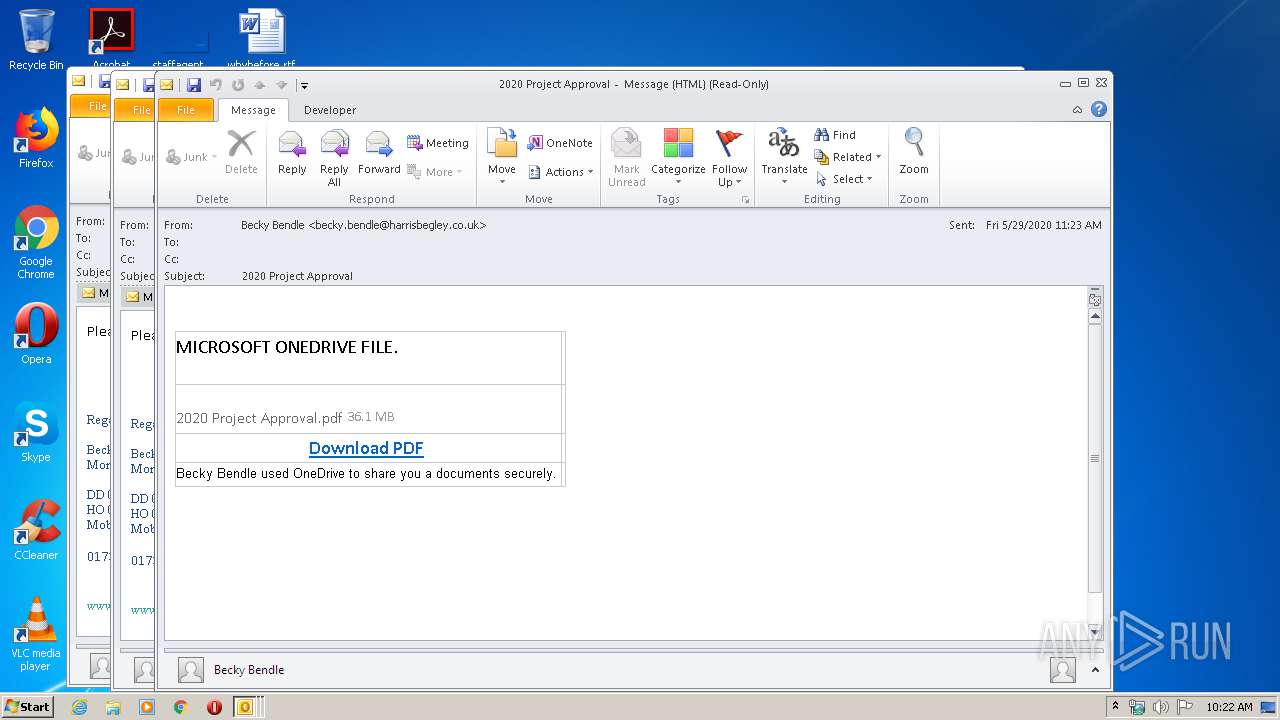
HTTP(S) requests
24
TCP/UDP connections
27
DNS requests
9
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2456 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
1672 | iexplore.exe | GET | 304 | 85.115.52.220:80 | http://www.mailcontrol.com/http-resources/bootstrap/css/bootstrap-responsive.css | GB | — | — | whitelisted |
1672 | iexplore.exe | GET | 304 | 85.115.52.220:80 | http://www.mailcontrol.com/http-resources/notification-pages/icons60/warning.png | GB | — | — | whitelisted |
1672 | iexplore.exe | GET | 304 | 85.115.52.220:80 | http://www.mailcontrol.com/http-resources/notification-pages/empty.js | GB | — | — | whitelisted |
1672 | iexplore.exe | GET | 304 | 85.115.52.220:80 | http://www.mailcontrol.com/http-resources/bootstrap/css/bootstrap.css | GB | — | — | whitelisted |
1672 | iexplore.exe | GET | 304 | 85.115.52.220:80 | http://www.mailcontrol.com/http-resources/bootstrap/css/bootstrap-responsive.css | GB | — | — | whitelisted |
1672 | iexplore.exe | GET | 200 | 85.115.56.180:80 | http://webdefence.global.blackspider.com/urlwrap/?q=AXicbc2xTsMwFEDR15WuTEz8QO0oFBEiIVqUItIqBUrVIpbINU5i1fYLz05Q-AY-GtjZ79EdjeD7FODsHIDMEMUV89QzK7SR6AKhYRItRNPtXCbXj9FFEl_GsMTGsUJm6JwyZibMuyKLpH5b1h2hCaH1Keceu9B8Kh8qYbUZemE65aWWEzsw3whSLWoX_gY8PaS85q0ij04YLknouvzXl0h12R35YtNvlvsqS_Iwt19v1aqYvuxdcbd9iu71lV5MVlmCa3p4raXMn2_VTZbTB-4A4GQM8APyylM5&Z | DE | html | 5.58 Kb | whitelisted |
1672 | iexplore.exe | GET | 304 | 85.115.52.220:80 | http://www.mailcontrol.com/http-resources/notification-pages/notification.css | GB | — | — | whitelisted |
1672 | iexplore.exe | GET | — | 85.115.52.220:80 | http://www.mailcontrol.com/http-resources/notification-pages/icons60/warning.png | GB | — | — | whitelisted |
1672 | iexplore.exe | GET | — | 85.115.52.220:80 | http://www.mailcontrol.com/http-resources/notification-pages/notification.css | GB | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2456 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
1672 | iexplore.exe | 85.115.56.180:80 | webdefence.global.blackspider.com | Forcepoint Cloud Ltd | DE | unknown |
1672 | iexplore.exe | 85.115.52.220:80 | www.mailcontrol.com | Forcepoint Cloud Ltd | GB | unknown |
1672 | iexplore.exe | 149.126.77.250:80 | www.aldermore.co.uk | Incapsula Inc | DE | unknown |
1692 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
1692 | iexplore.exe | 85.115.56.180:80 | webdefence.global.blackspider.com | Forcepoint Cloud Ltd | DE | unknown |
— | — | 85.115.52.220:80 | www.mailcontrol.com | Forcepoint Cloud Ltd | GB | unknown |
1692 | iexplore.exe | 72.21.81.200:443 | r20swj13mr.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1692 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
webdefence.global.blackspider.com |
| whitelisted |
www.mailcontrol.com |
| whitelisted |
www.aldermore.co.uk |
| unknown |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |