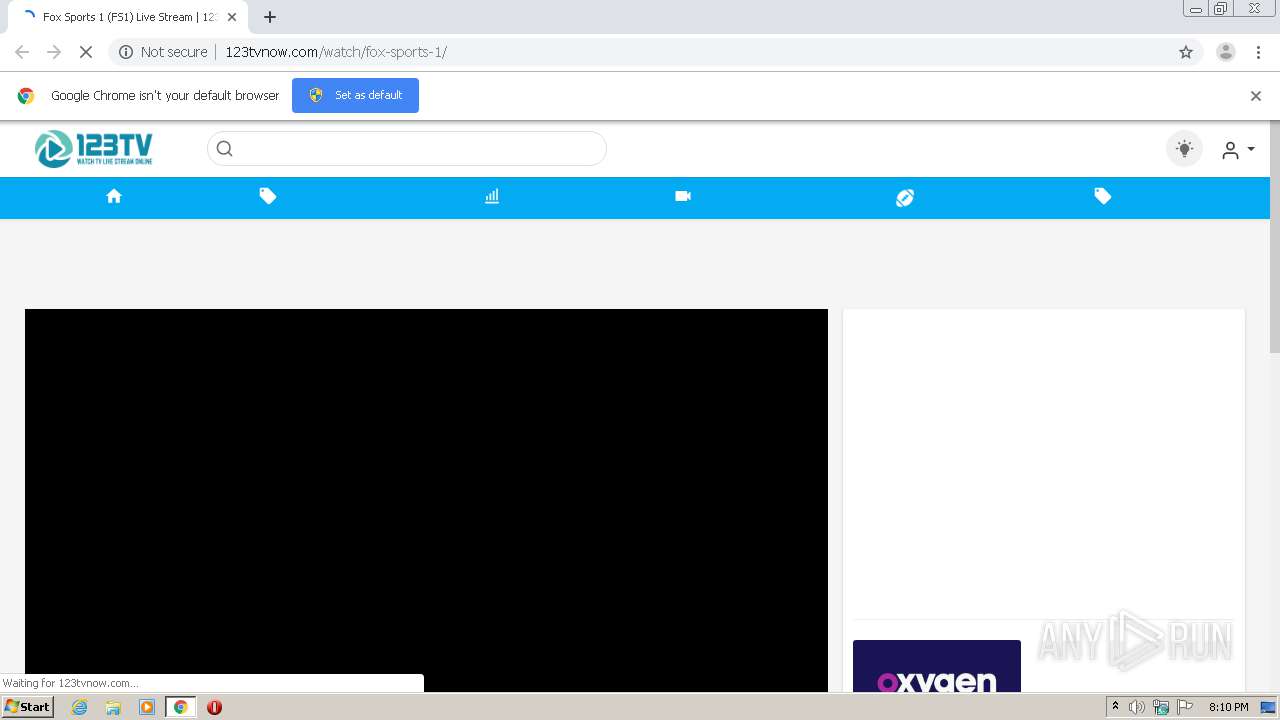
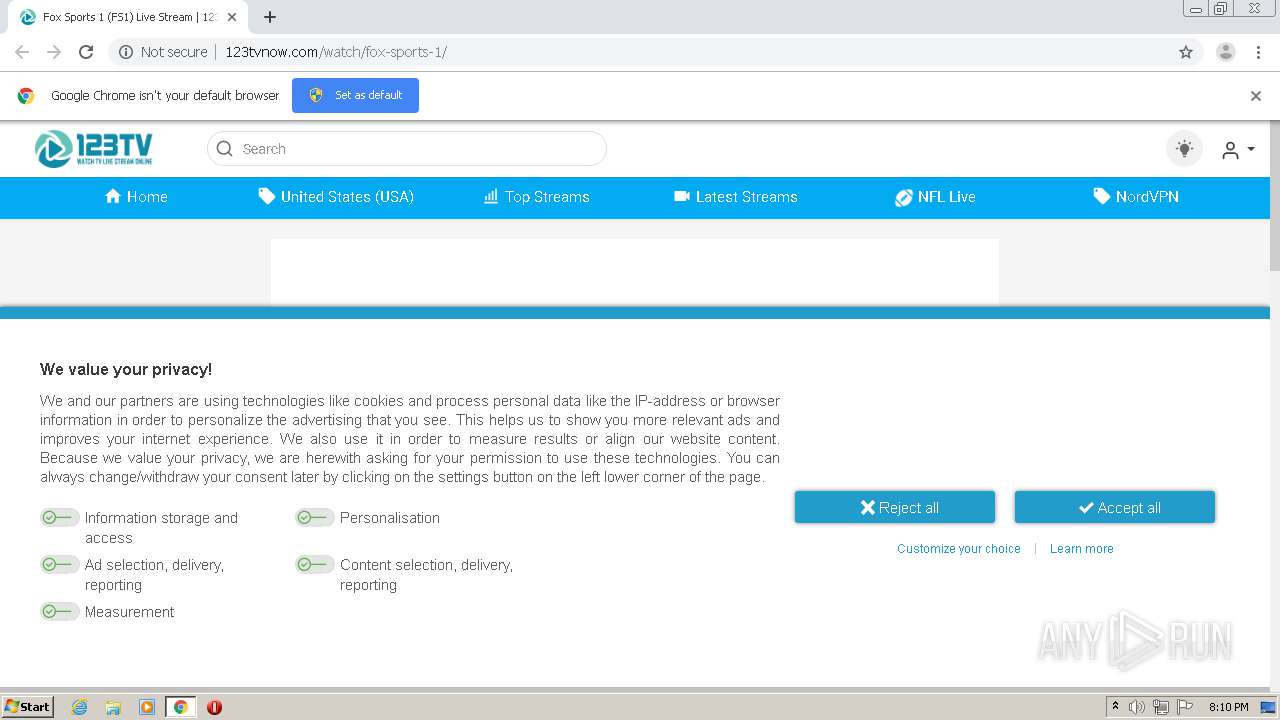
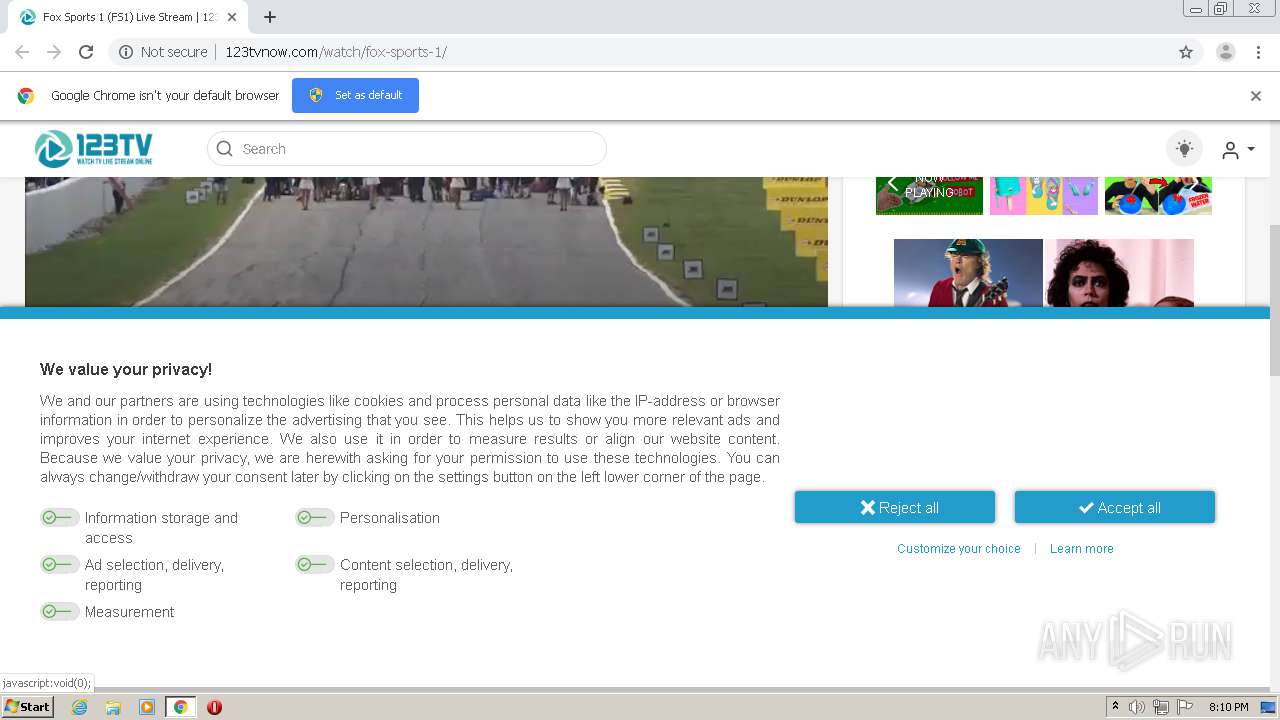
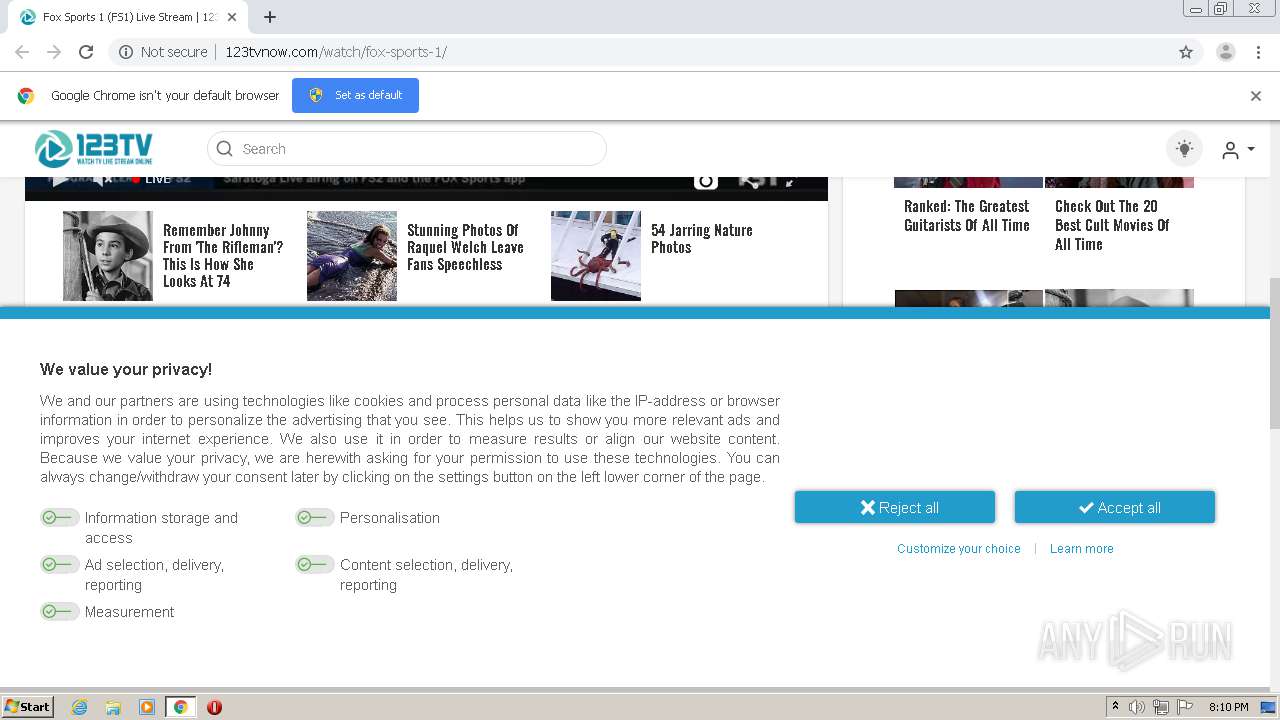
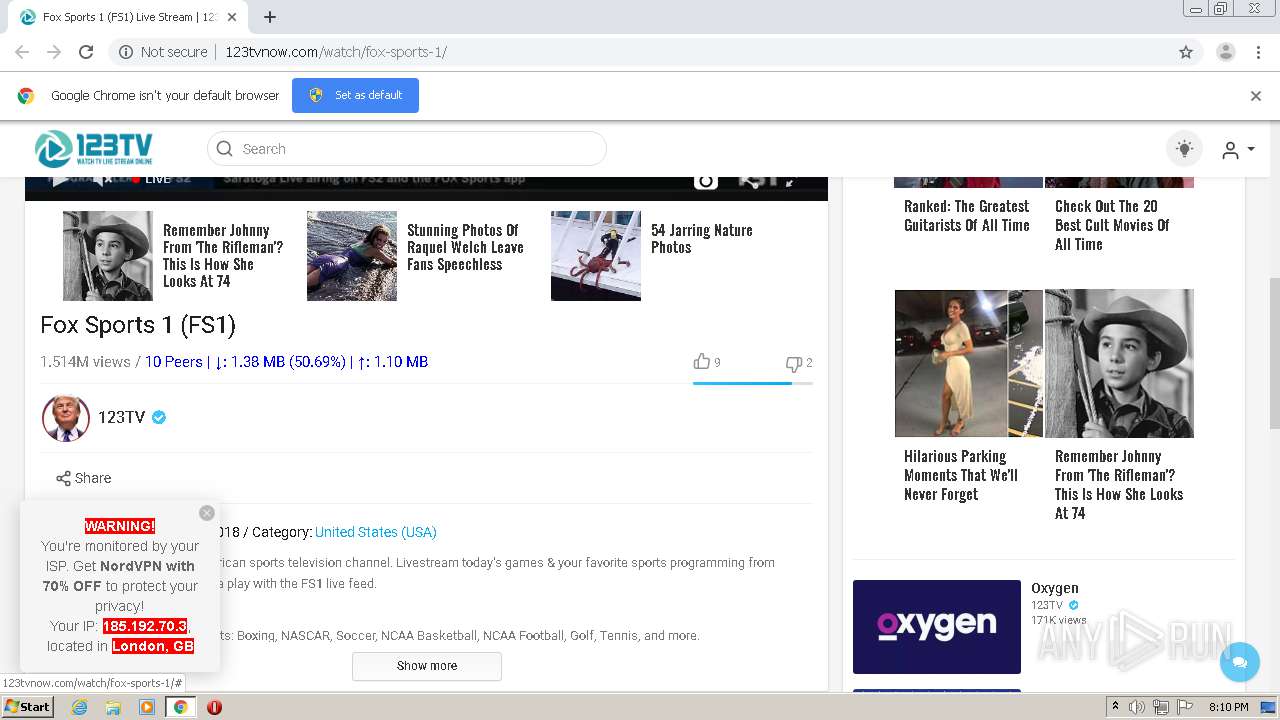
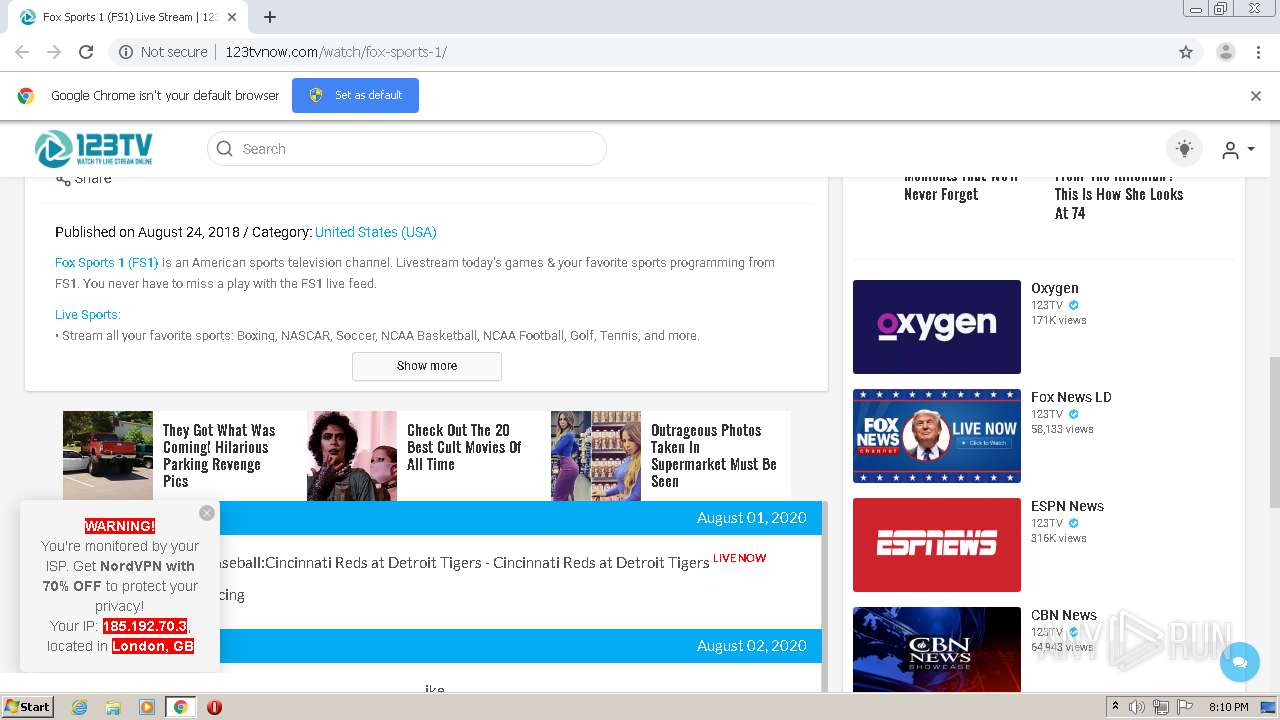
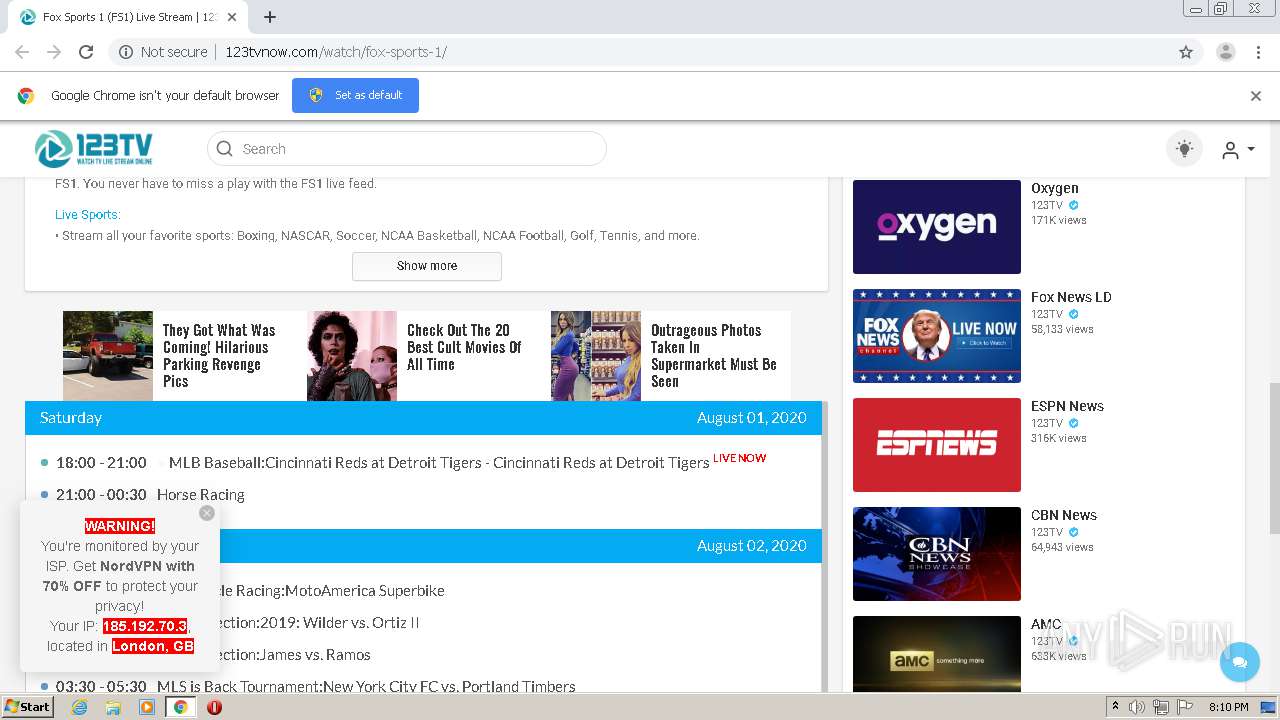
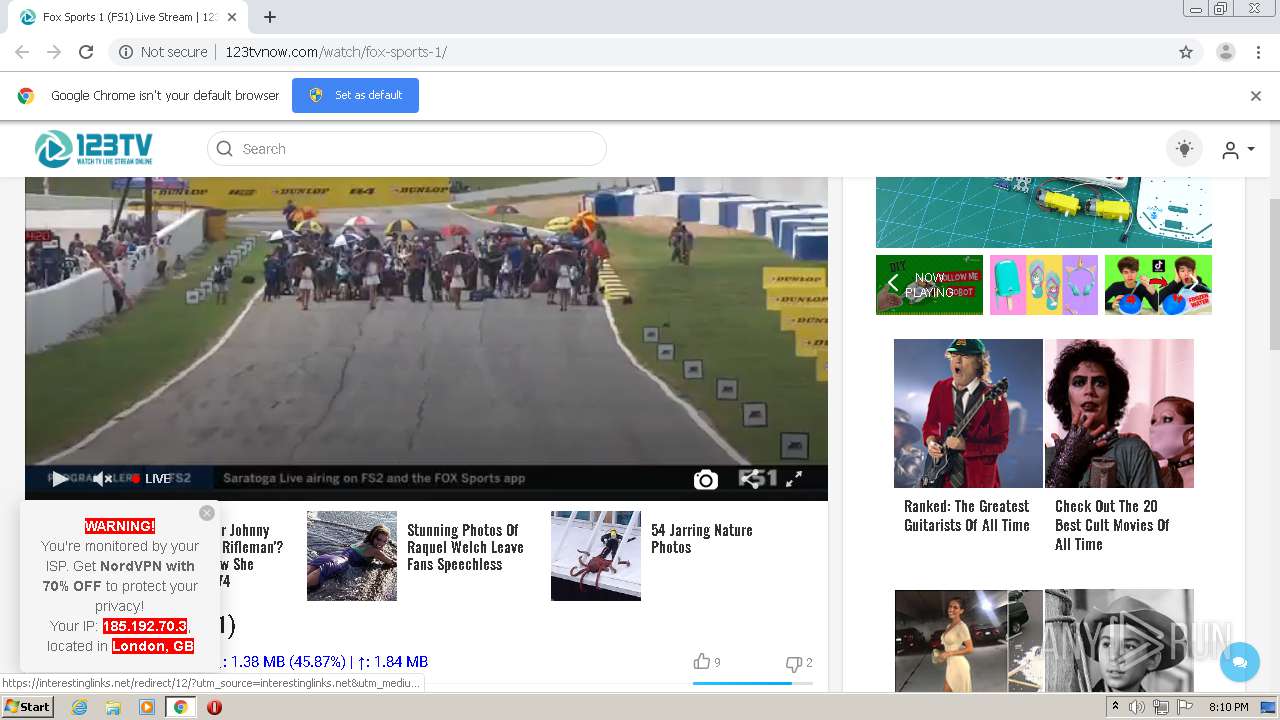
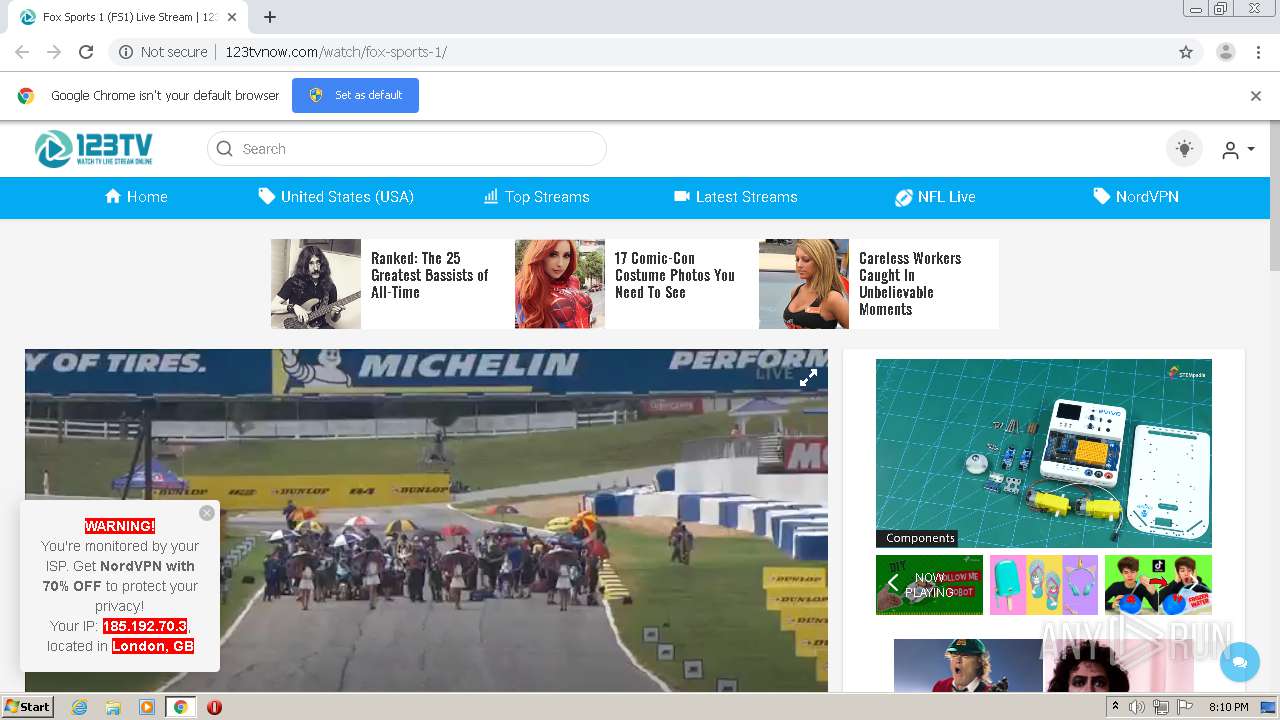
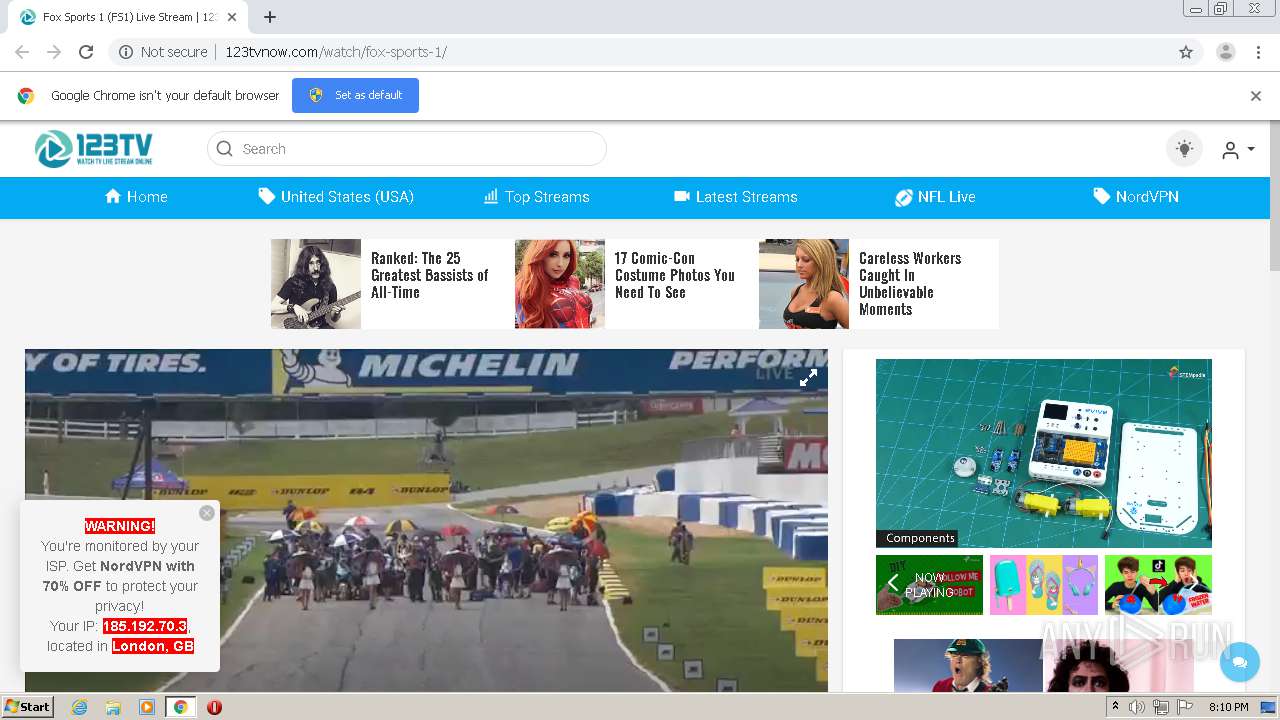
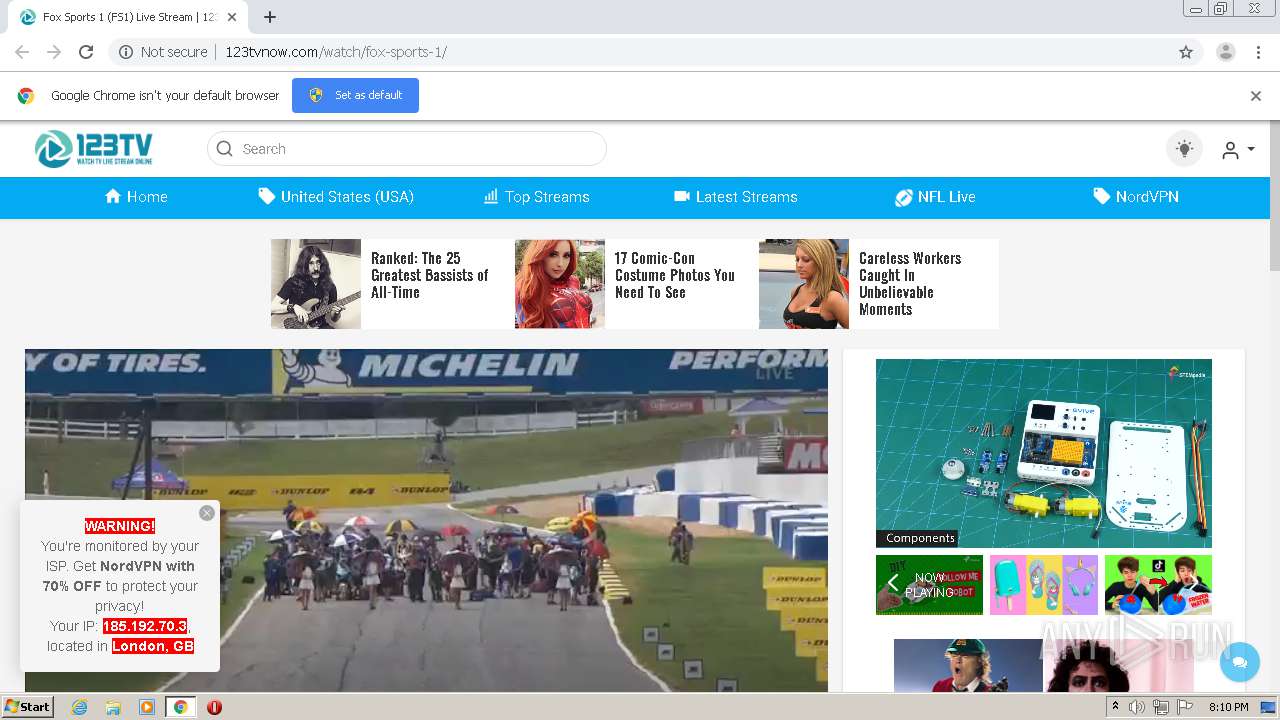
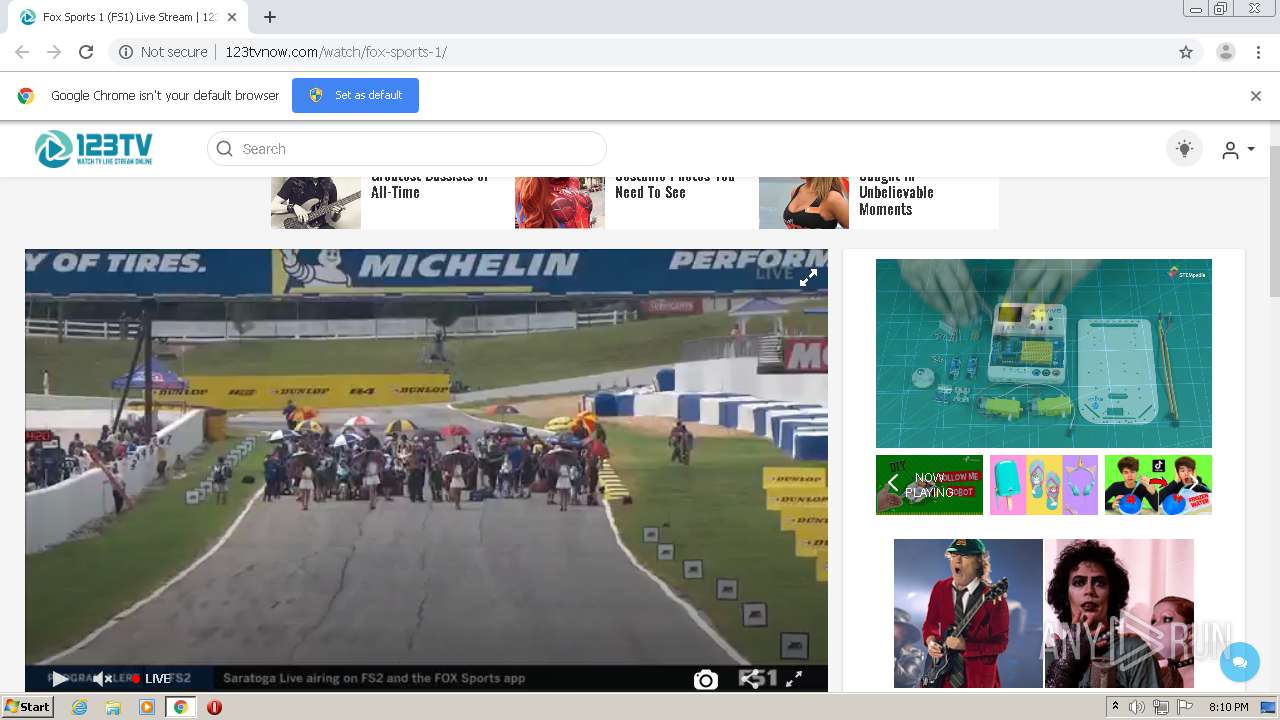
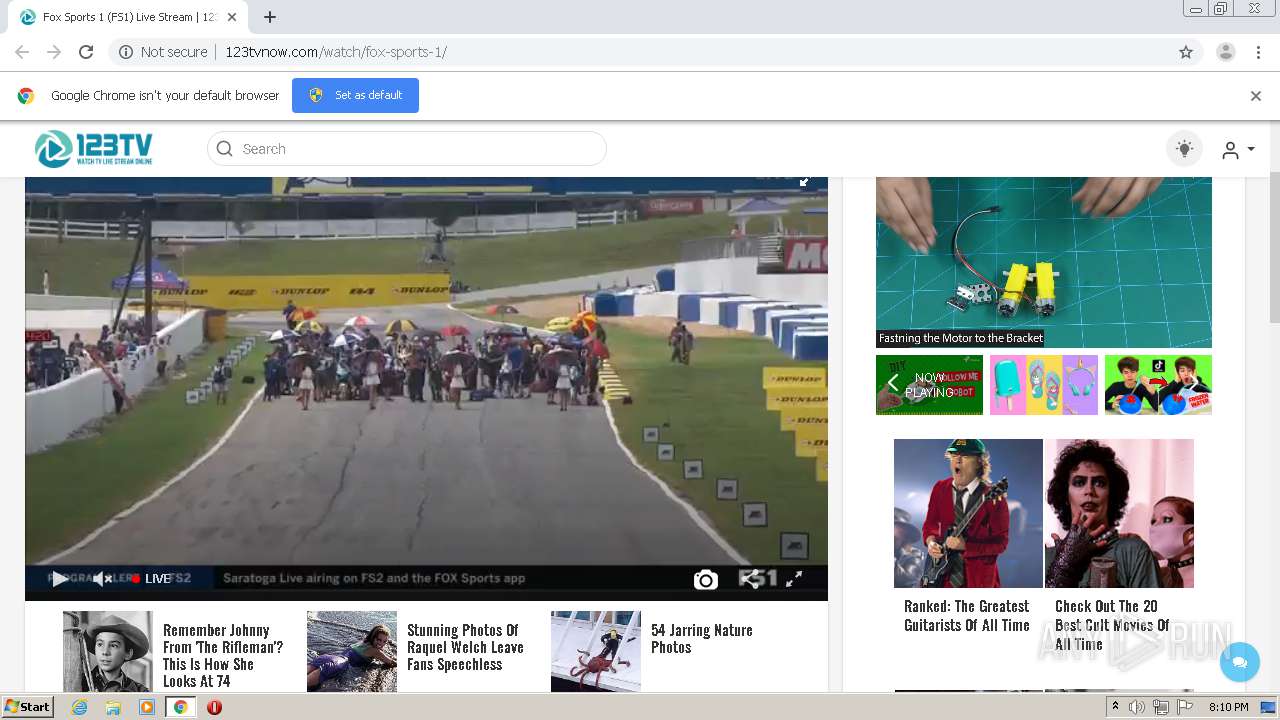
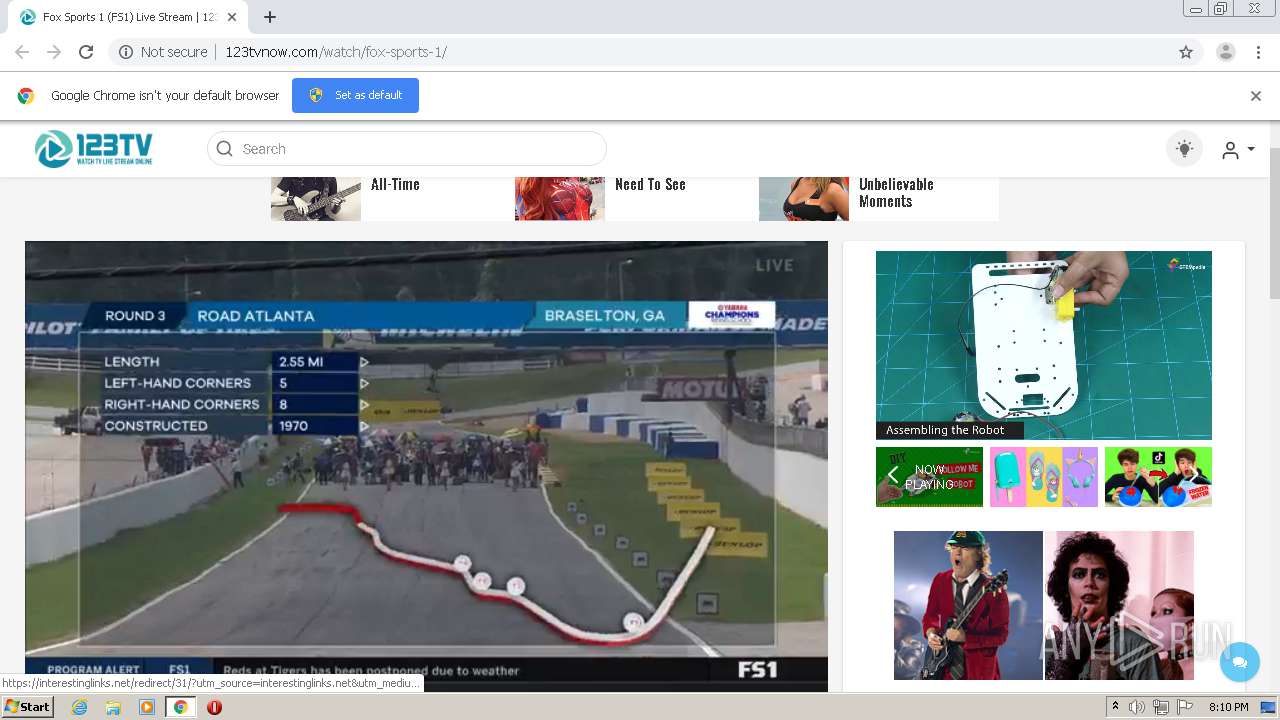
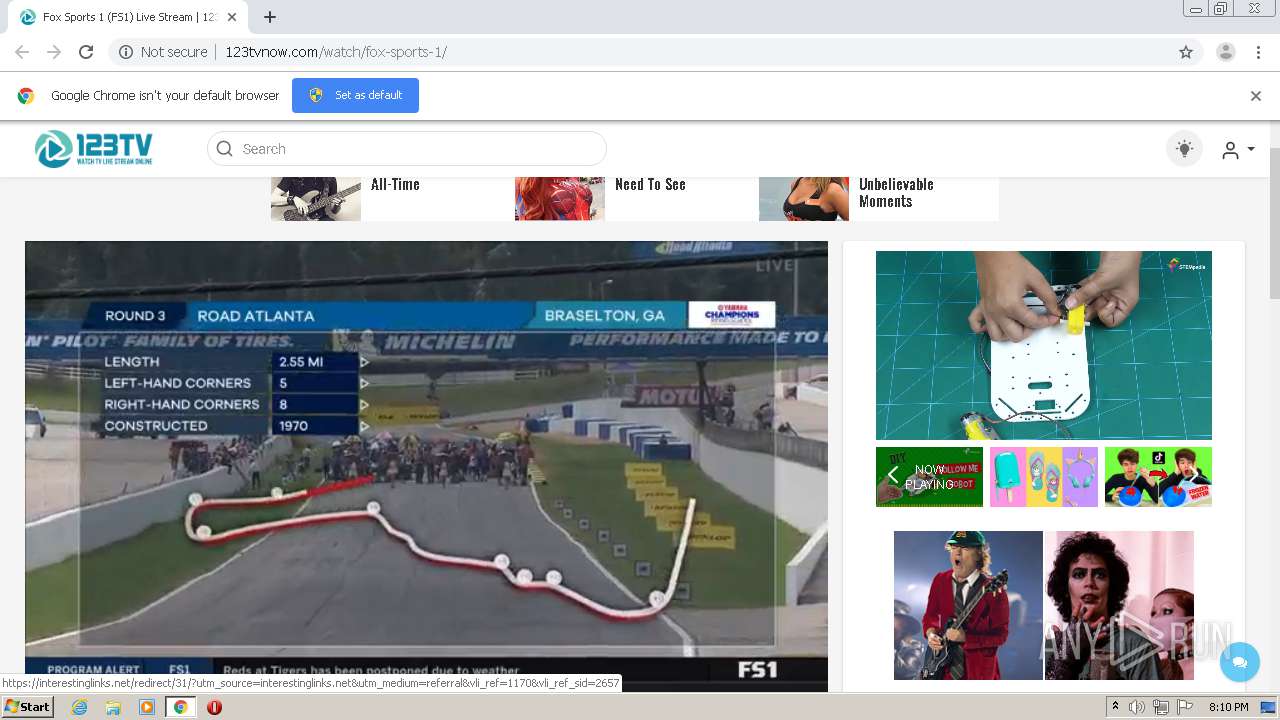
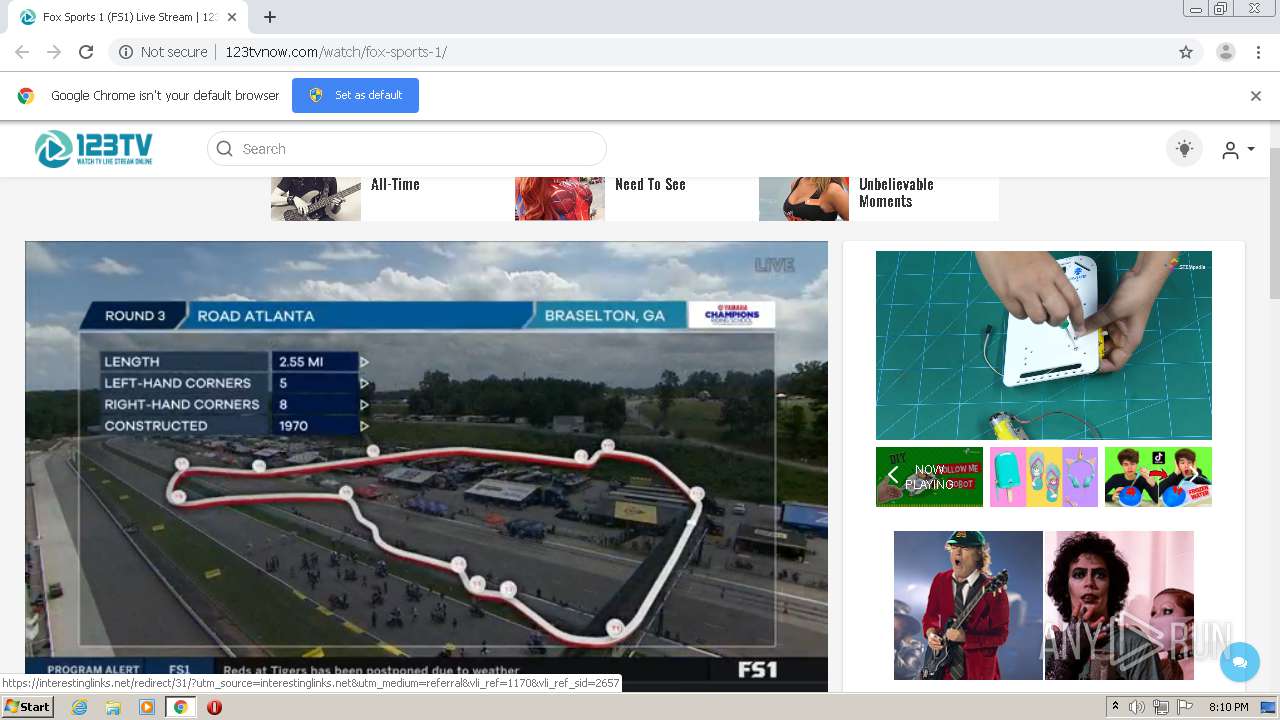
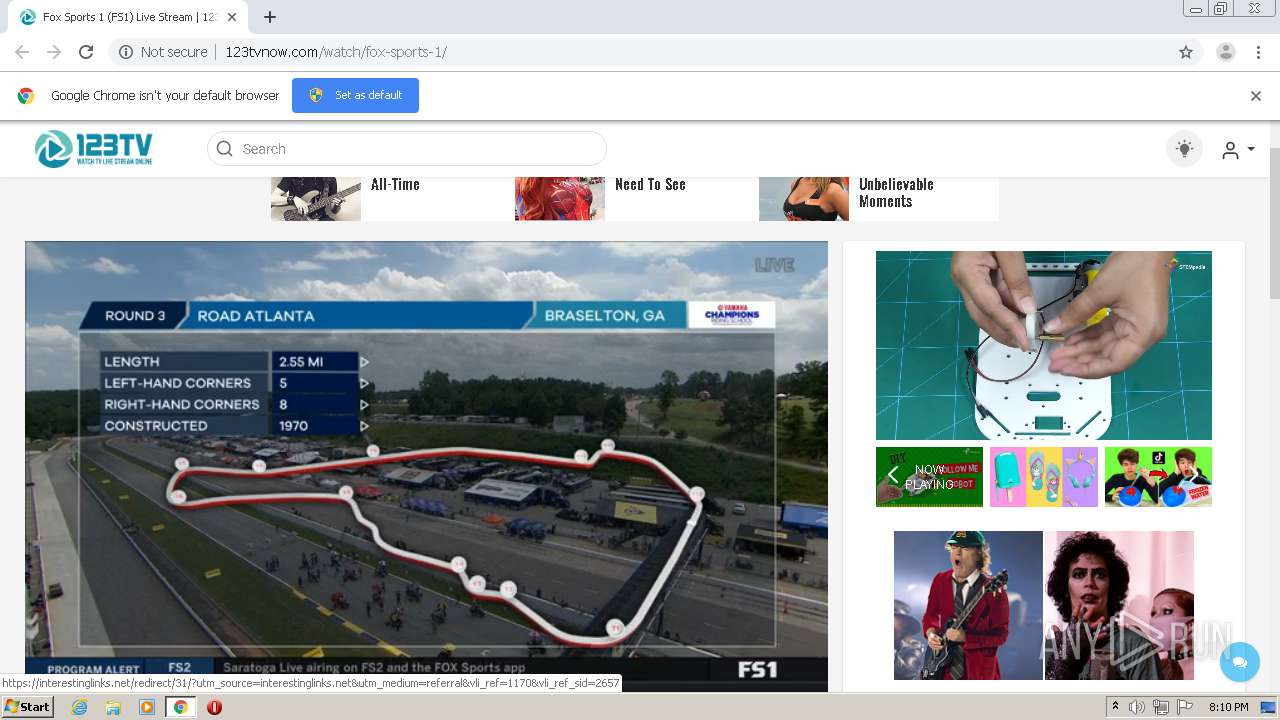
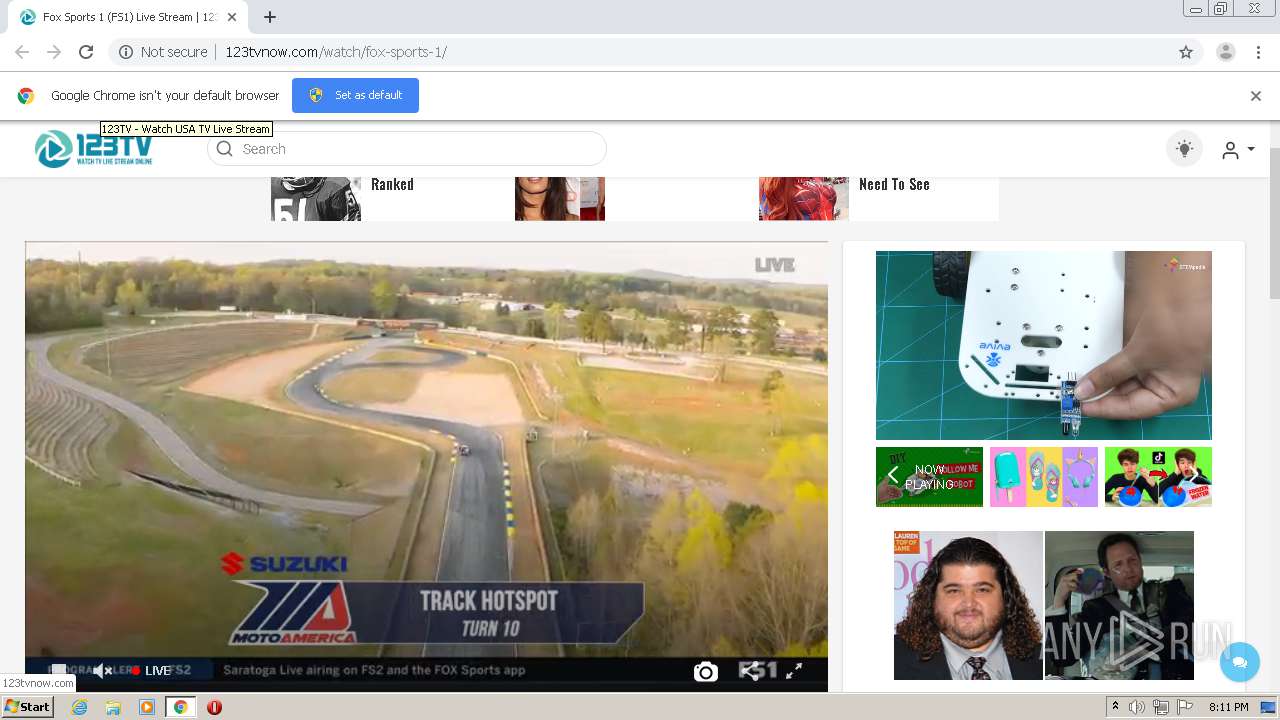
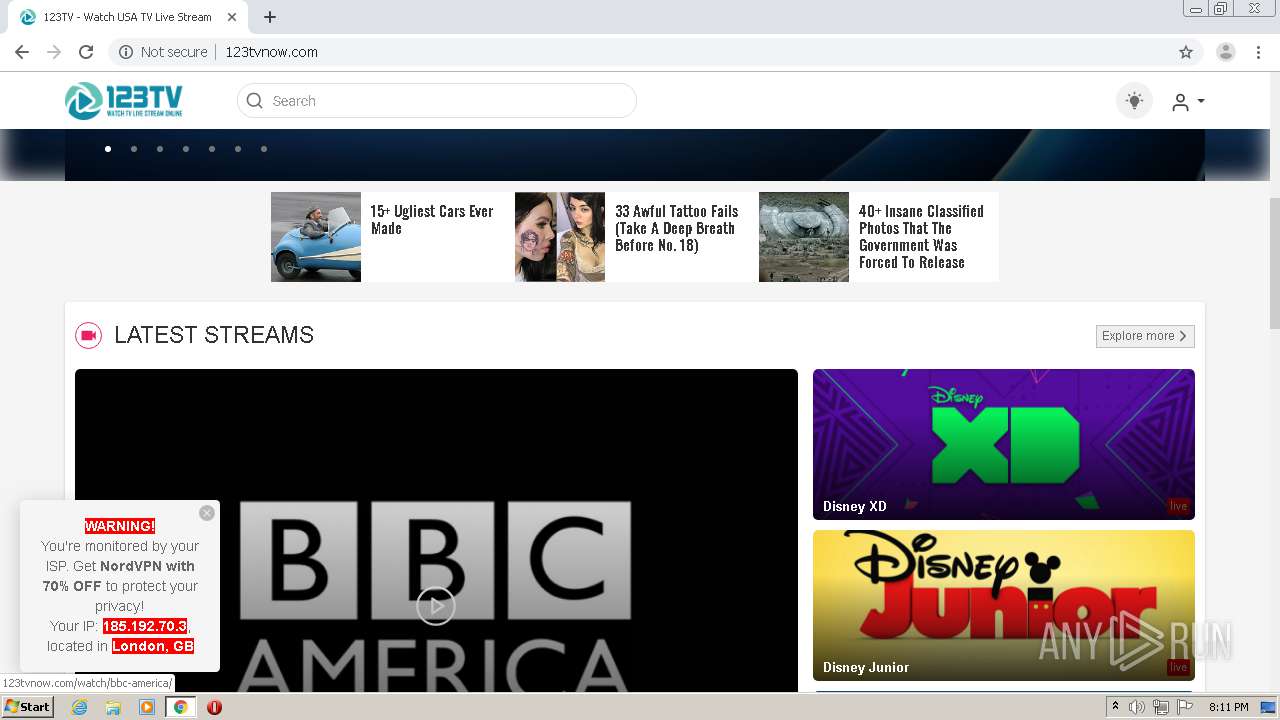
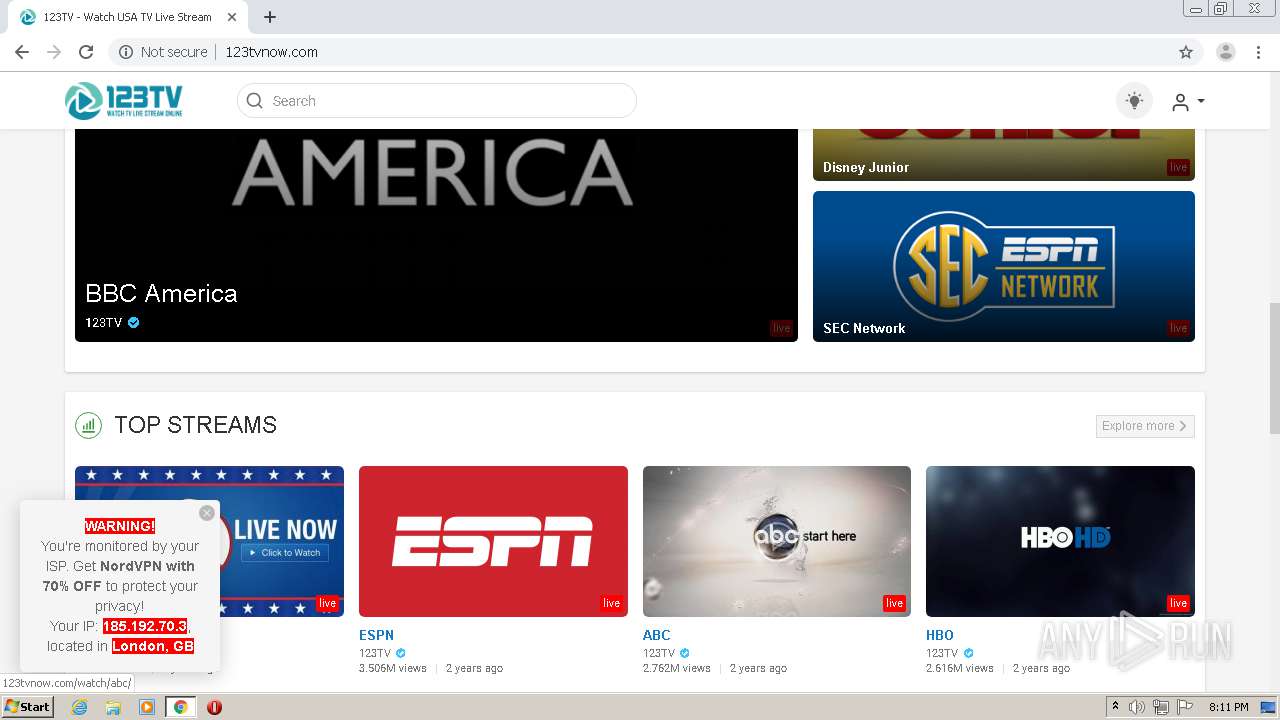
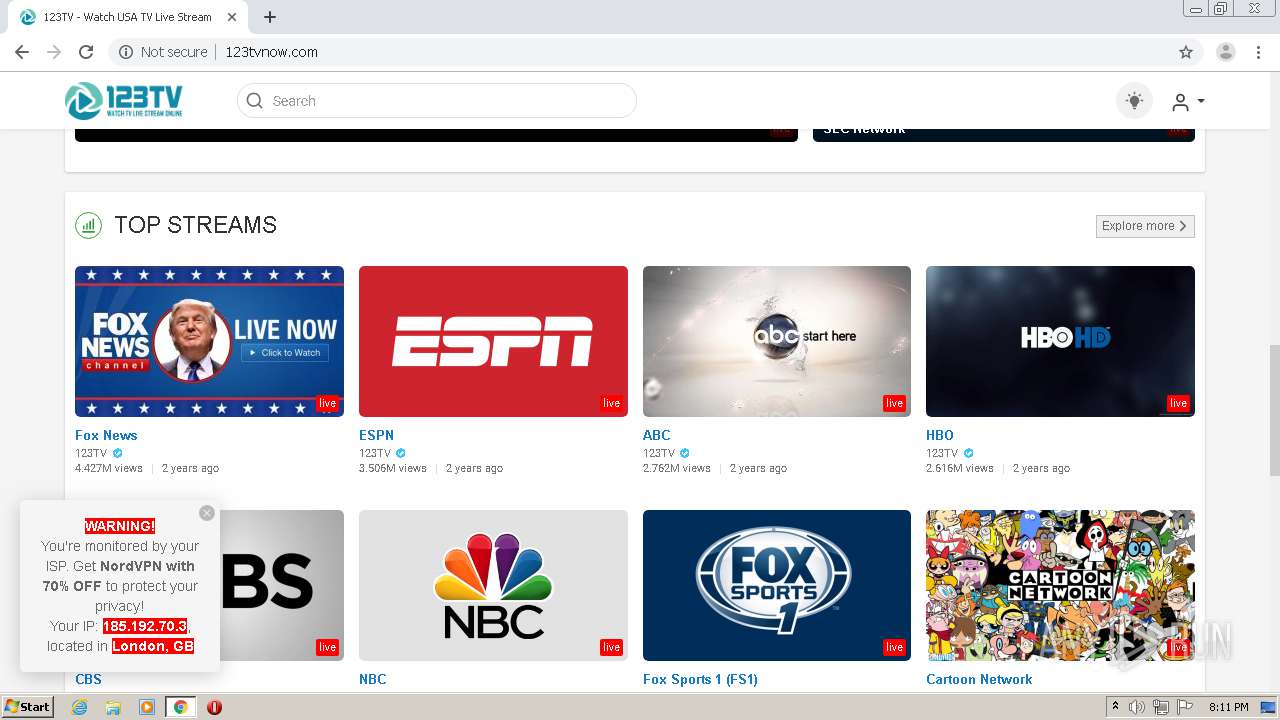
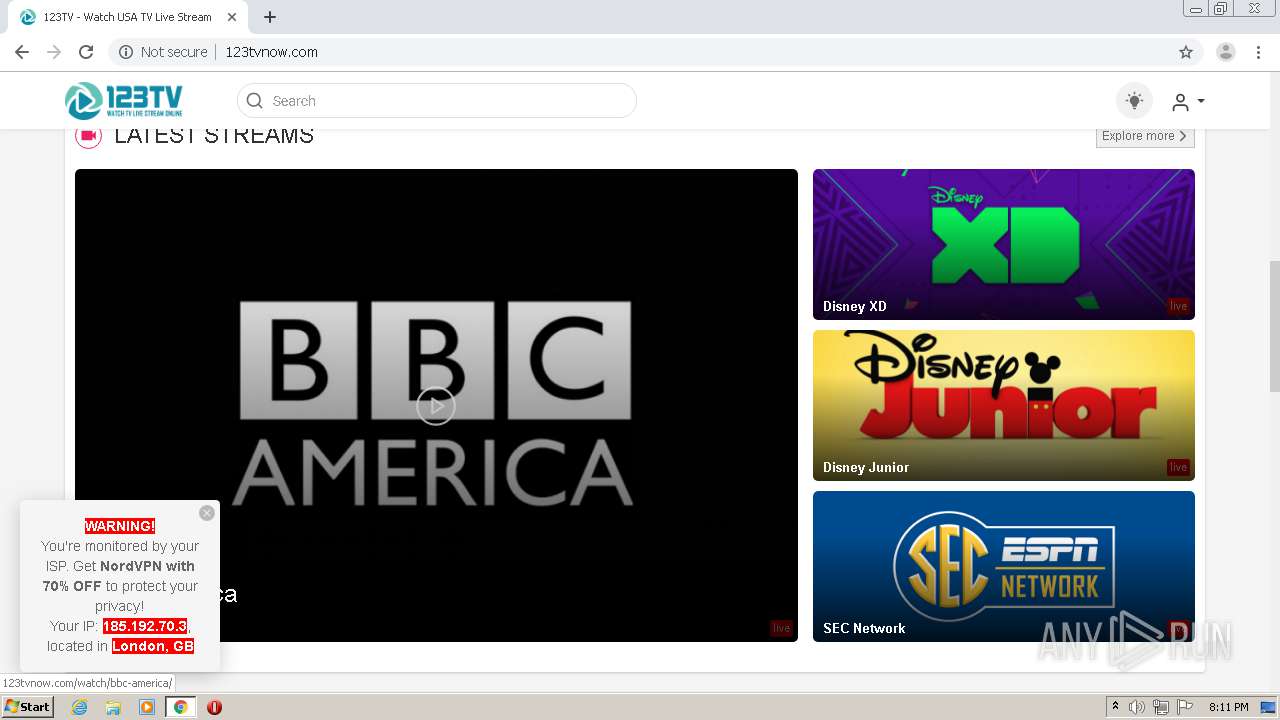
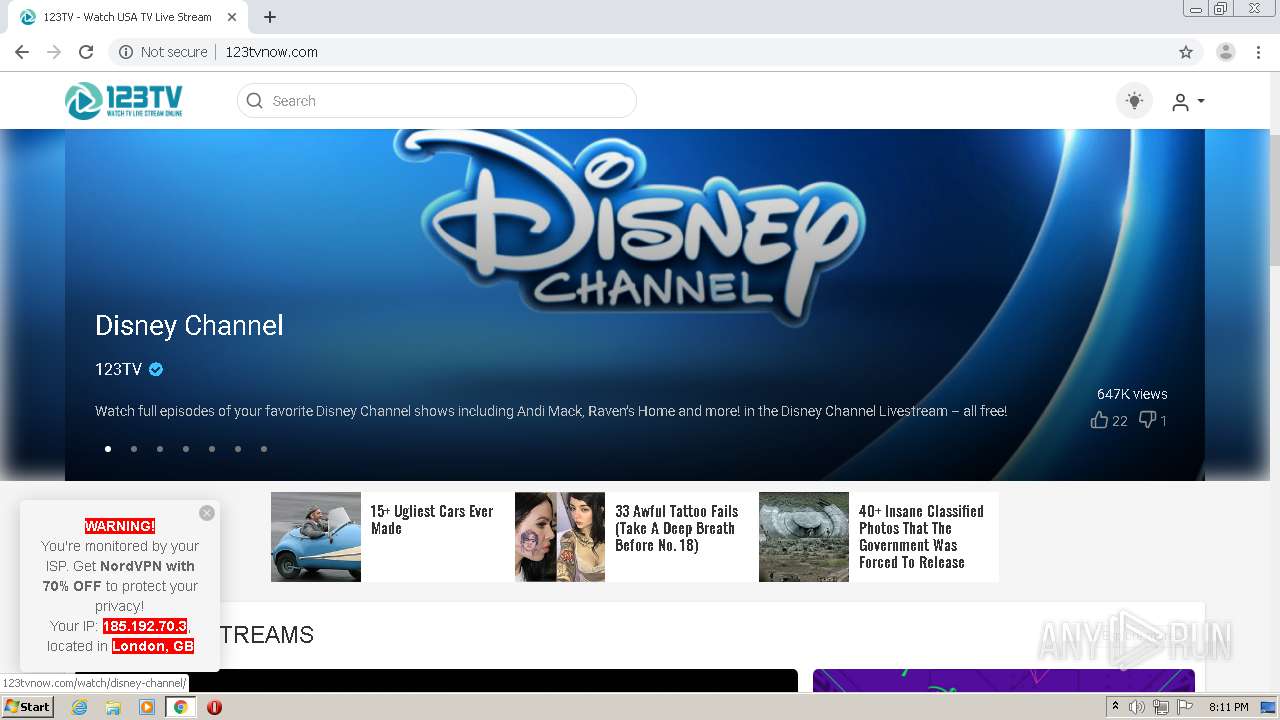
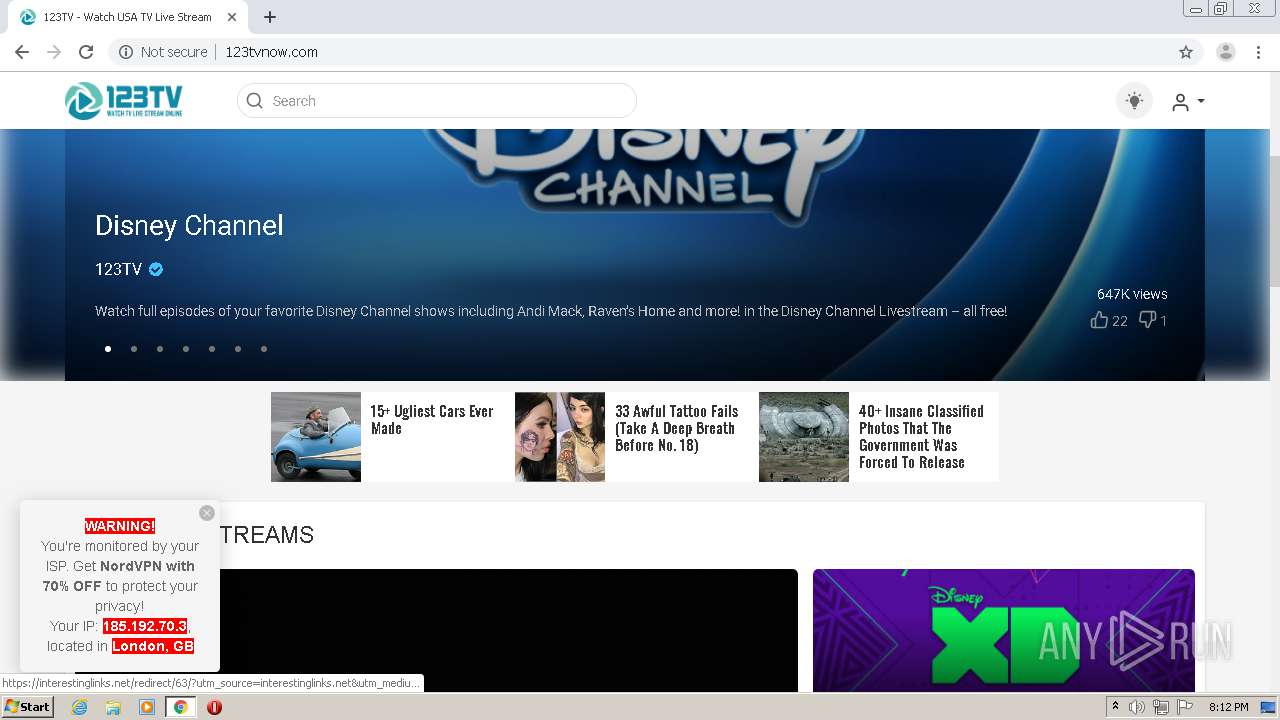
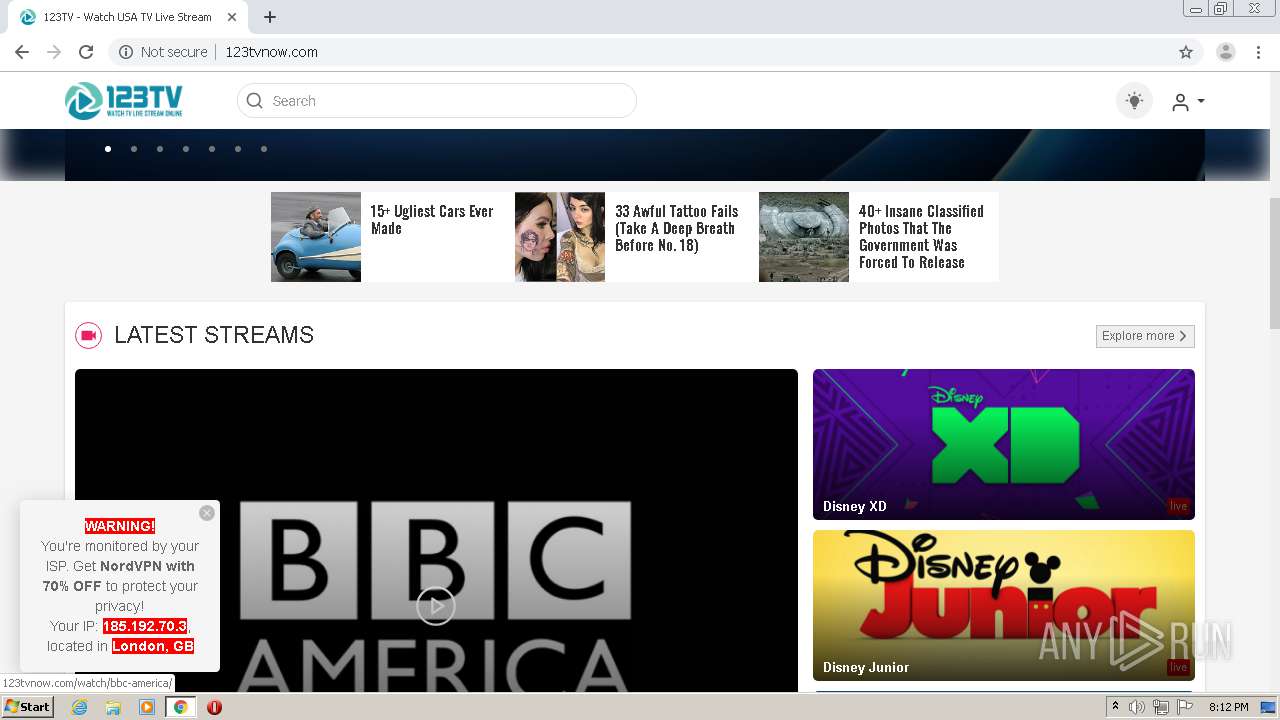
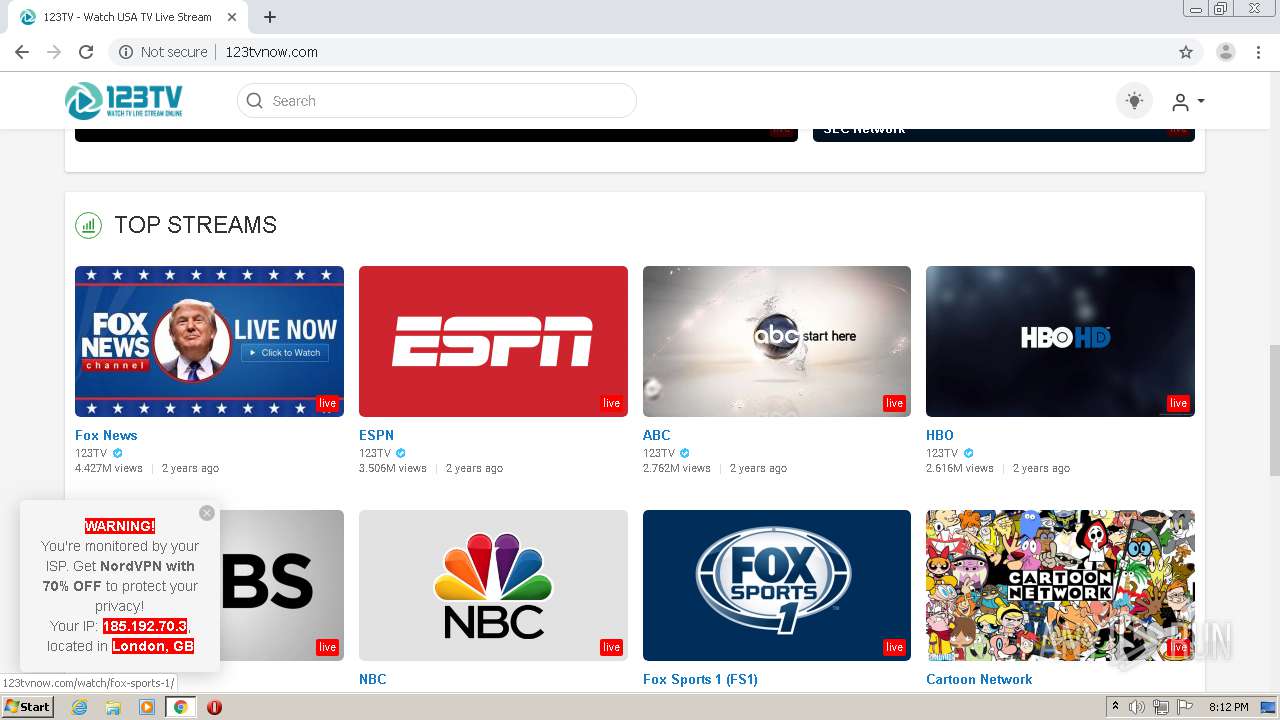
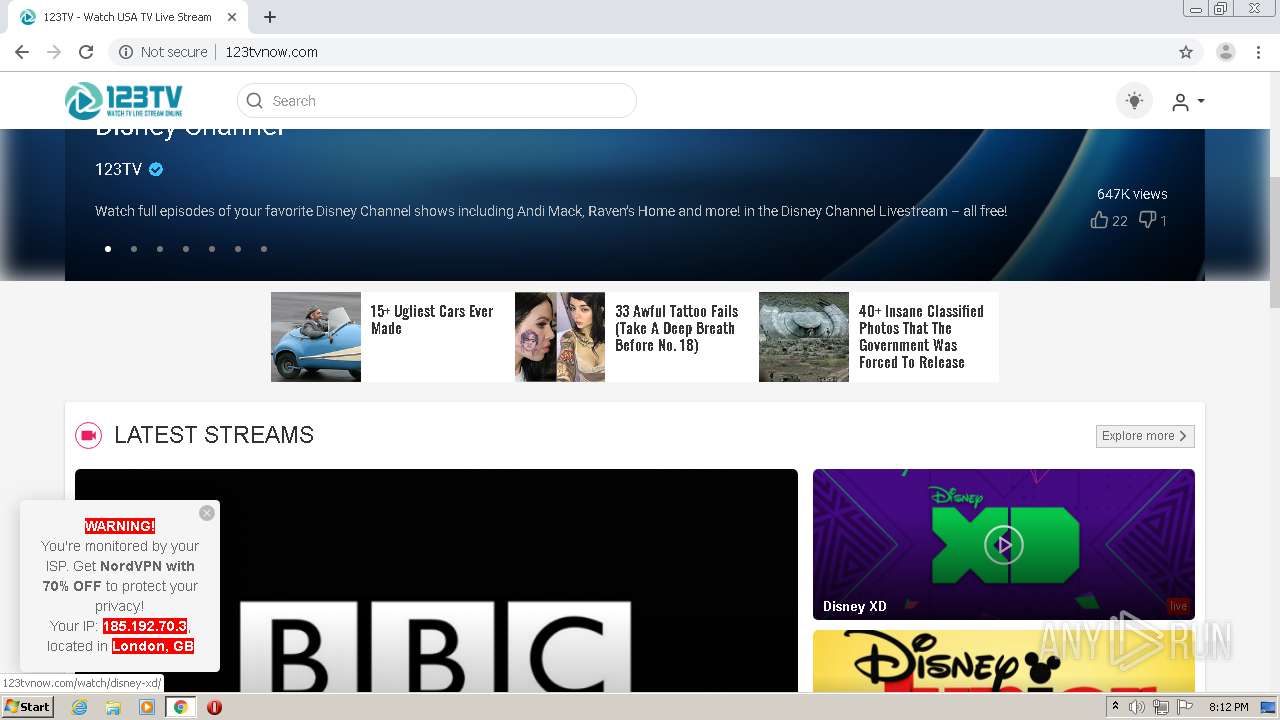
| URL: | http://123tvnow.com/watch/fox-sports-1/ |
| Full analysis: | https://app.any.run/tasks/29b8dbfa-3606-40a8-aef3-0a638a42eab6 |
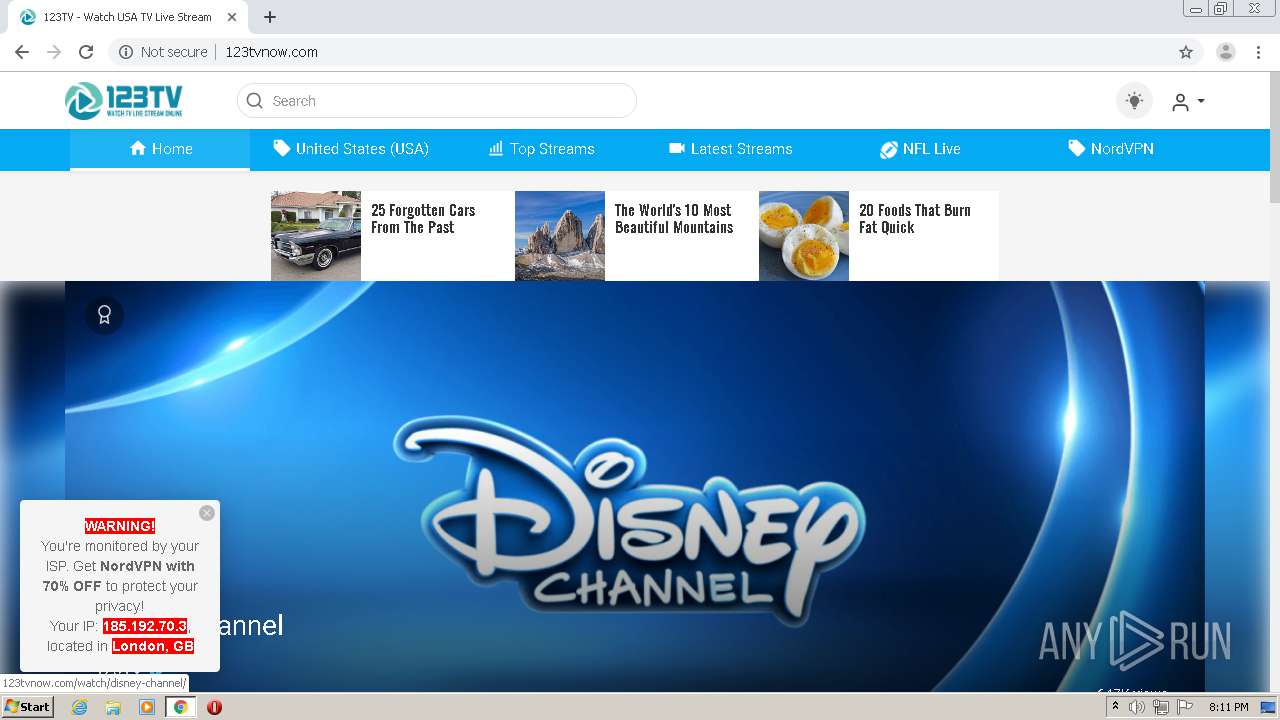
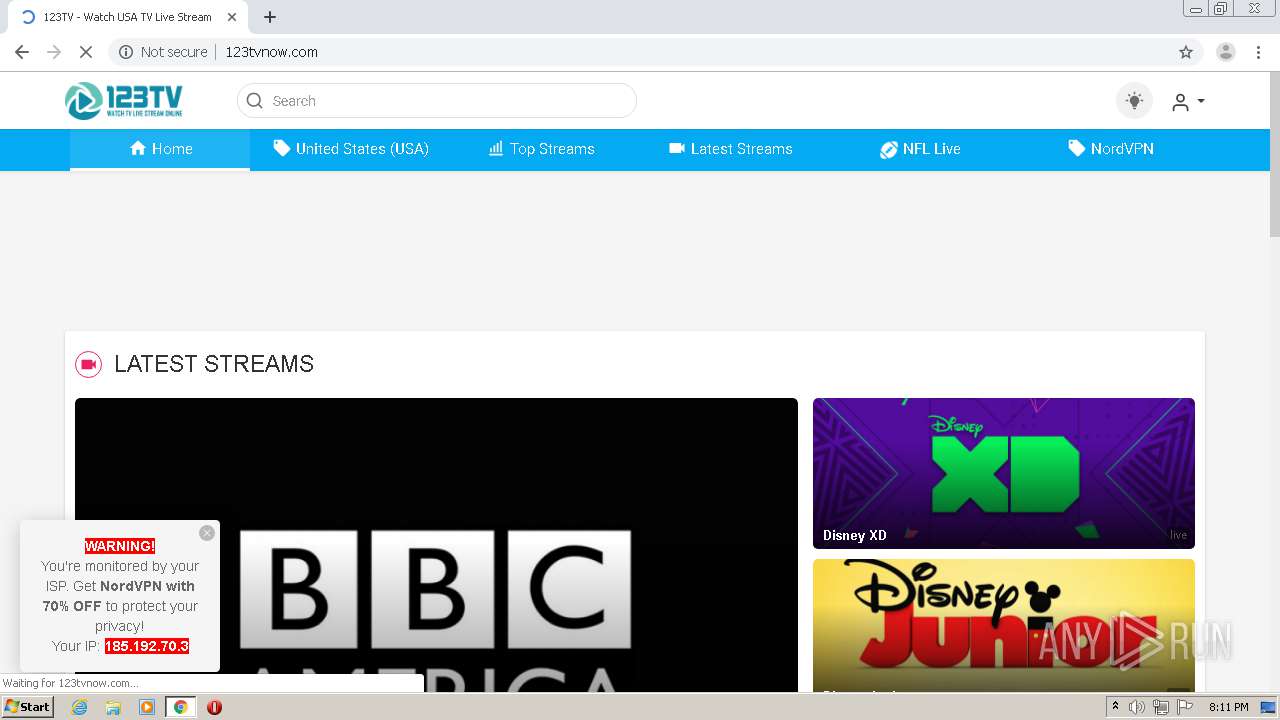
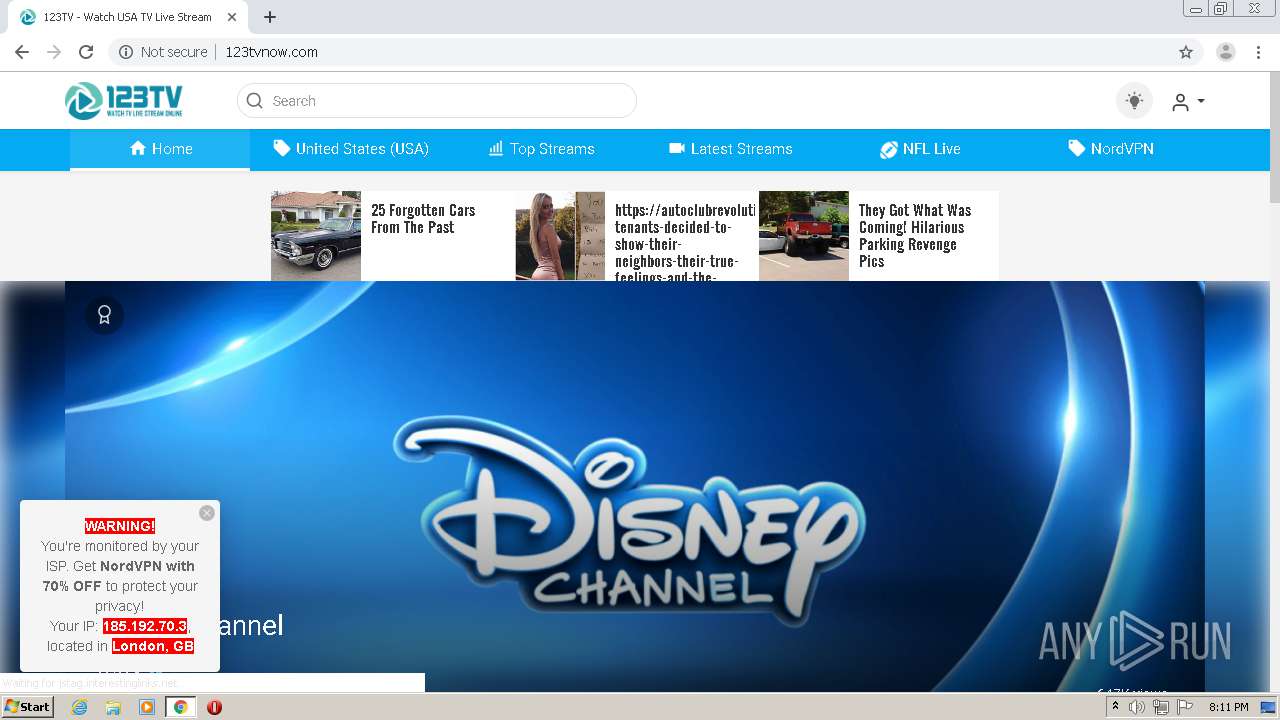
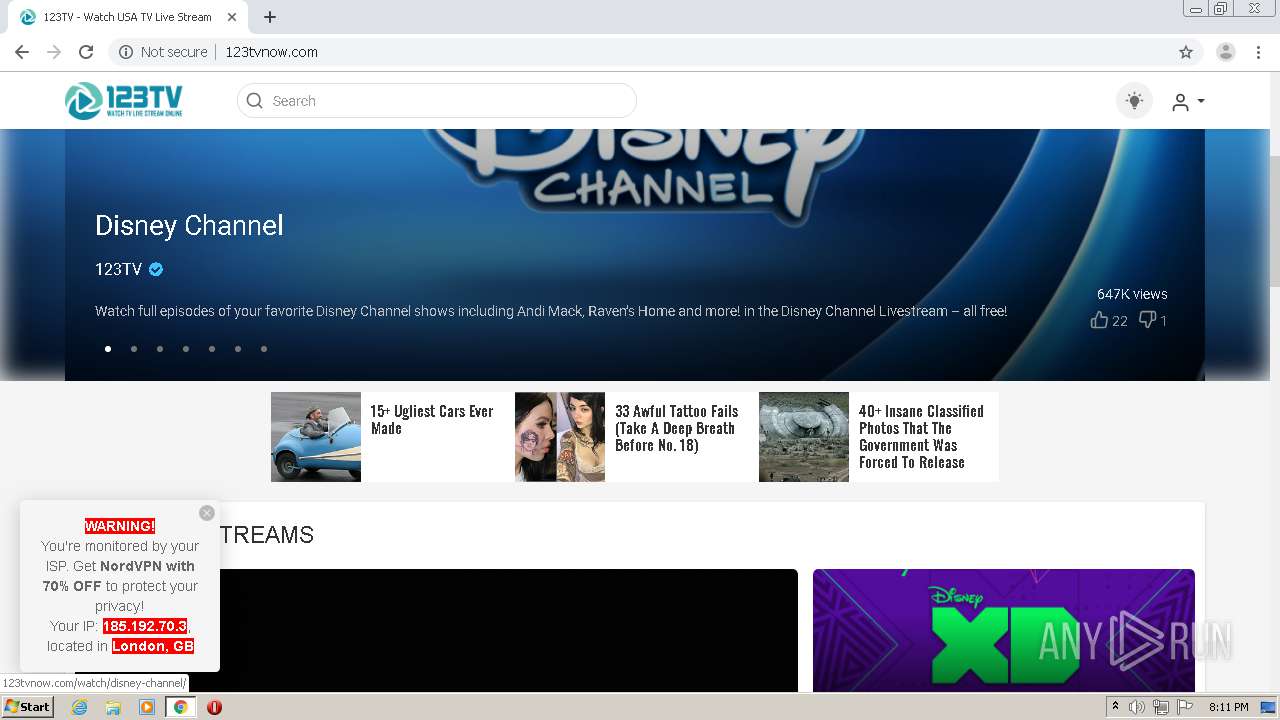
| Verdict: | Malicious activity |
| Analysis date: | August 01, 2020, 19:09:51 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 643794FA91D75FFD3910760C87943D82 |
| SHA1: | C88F83DCE99289C86E1ED727D48E177C2E5B612D |
| SHA256: | 032ACF2CC48420D3E7778CD40ED467177F11E4D456F6FED3F338E7D5C53F51CC |
| SSDEEP: | 3:N1KvWqL+IYmkn:C+qfYmkn |
MALICIOUS
No malicious indicators.SUSPICIOUS
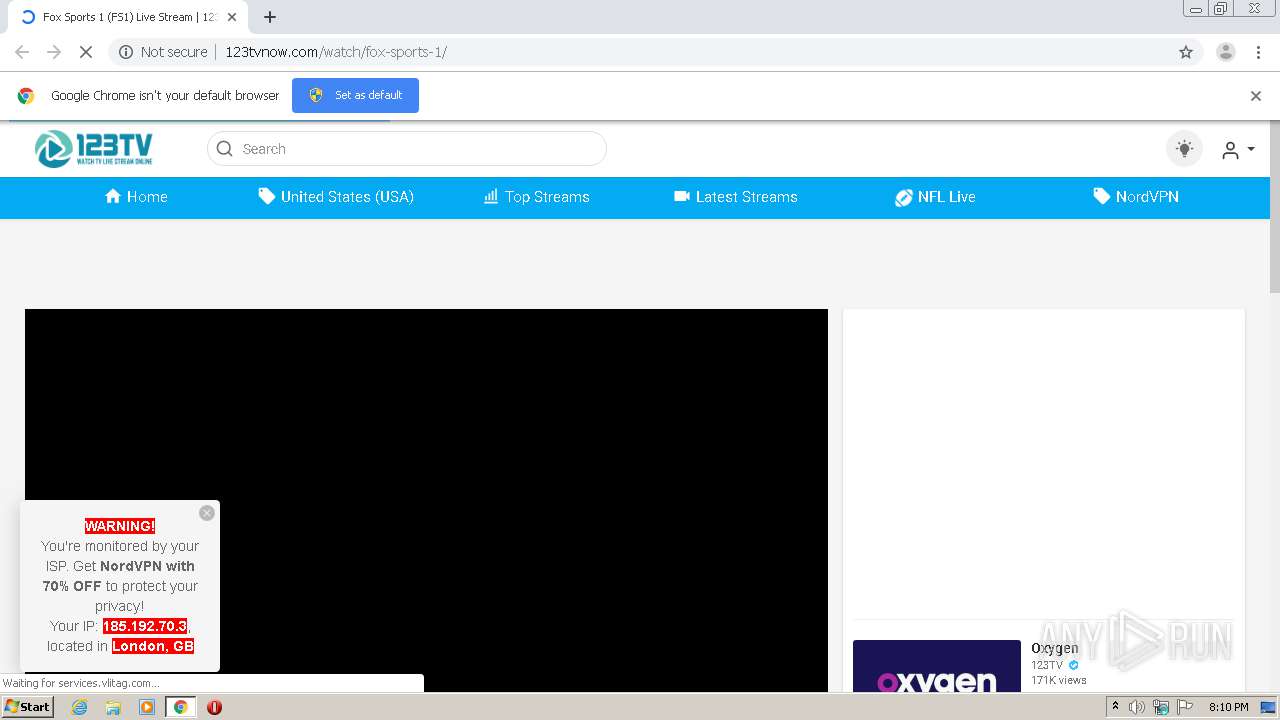
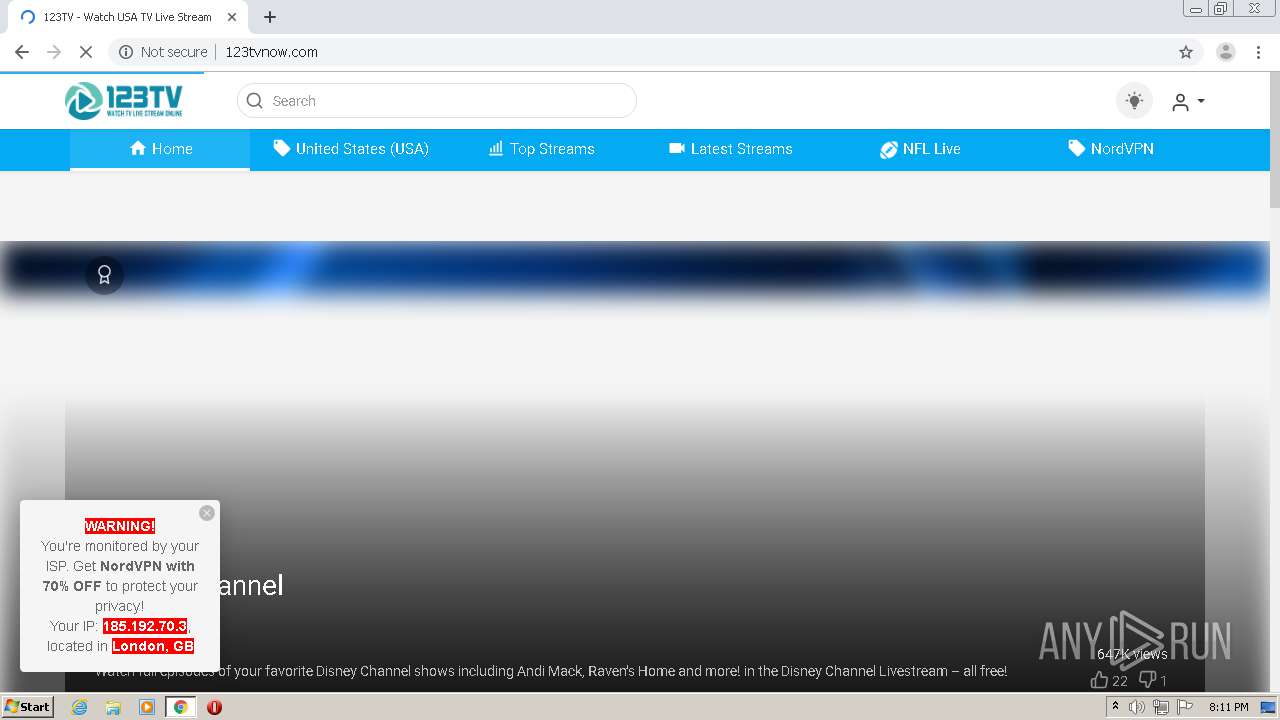
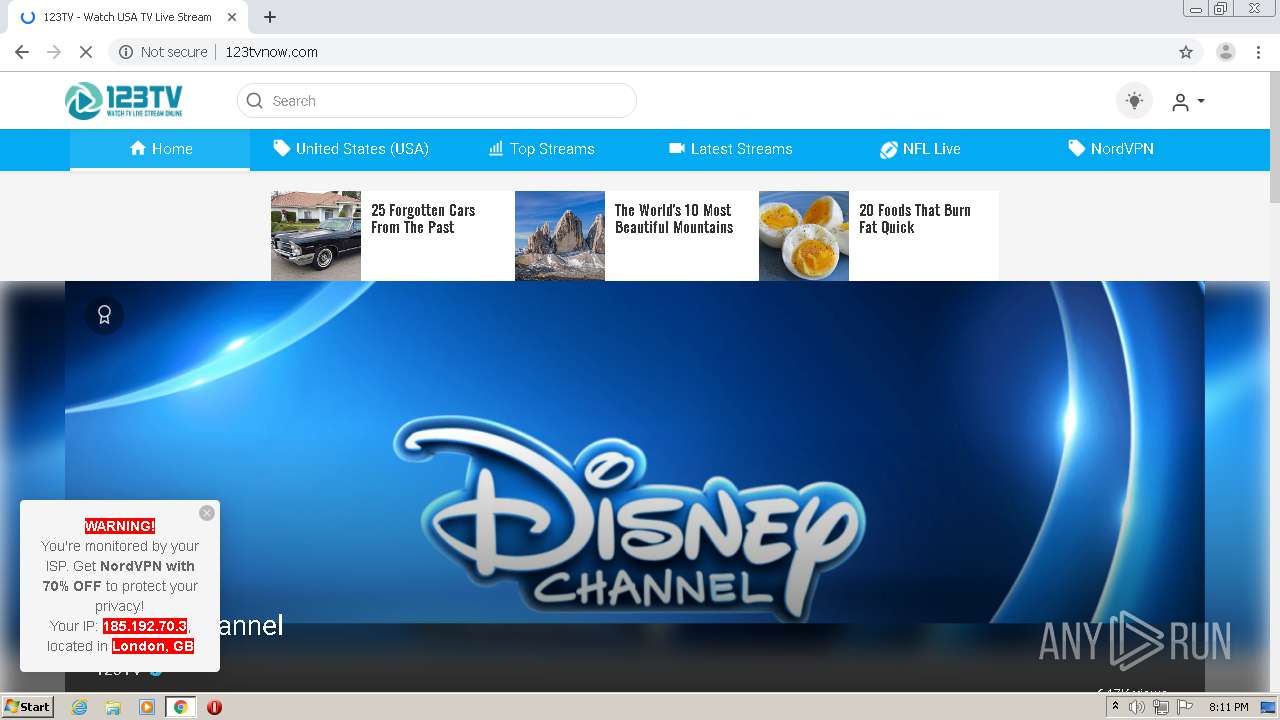
Checks for external IP
- chrome.exe (PID: 3952)
INFO
Reads the hosts file
- chrome.exe (PID: 1880)
- chrome.exe (PID: 3952)
Application launched itself
- chrome.exe (PID: 1880)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
87
Monitored processes
52
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 372 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1044,2390348339723527439,7354679419385536160,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=9568946993182159764 --mojo-platform-channel-handle=5176 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 660 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,2390348339723527439,7354679419385536160,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9064959013998806176 --renderer-client-id=34 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1524 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 896 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,2390348339723527439,7354679419385536160,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1803420234429979319 --renderer-client-id=11 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4184 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1064 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,2390348339723527439,7354679419385536160,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7040696010776903979 --renderer-client-id=39 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3956 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1296 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,2390348339723527439,7354679419385536160,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7503081000330281998 --renderer-client-id=47 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4488 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1336 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1044,2390348339723527439,7354679419385536160,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=18228316317291584423 --mojo-platform-channel-handle=4688 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1340 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,2390348339723527439,7354679419385536160,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13392140908280737246 --renderer-client-id=32 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2328 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1376 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,2390348339723527439,7354679419385536160,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7812436688584427924 --renderer-client-id=19 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5108 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1408 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,2390348339723527439,7354679419385536160,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1655015496867788870 --renderer-client-id=16 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4280 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1488 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,2390348339723527439,7354679419385536160,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12237927234582092502 --renderer-client-id=18 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4904 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
684
Read events
558
Write events
121
Delete events
5
Modification events
| (PID) Process: | (1880) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1880) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1880) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1880) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1880) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2220) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 1880-13240782606138625 |
Value: 259 | |||
| (PID) Process: | (1880) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1880) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1880) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2832-13239195546717773 |
Value: 0 | |||
| (PID) Process: | (1880) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
157
Text files
169
Unknown types
17
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1880 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000032.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1880 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\248996d9-b48c-453d-bcc9-cb5fbfd9f63c.tmp | — | |
MD5:— | SHA256:— | |||
| 1880 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RFd6ddd.TMP | text | |
MD5:— | SHA256:— | |||
| 1880 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFd6dae.TMP | text | |
MD5:— | SHA256:— | |||
| 1880 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1880 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1880 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\AutofillStrikeDatabase\000001.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1880 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1880 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFd6dae.TMP | text | |
MD5:— | SHA256:— | |||
| 1880 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\metadata\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
191
TCP/UDP connections
304
DNS requests
133
Threats
34
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3952 | chrome.exe | GET | — | 151.101.2.109:80 | http://cdn.jsdelivr.net/npm/p2p-media-loader-hlsjs@latest/build/p2p-media-loader-hlsjs.min.js | US | — | — | whitelisted |
3952 | chrome.exe | GET | — | 151.101.2.109:80 | http://cdn.jsdelivr.net/npm/hls.js@latest | US | — | — | whitelisted |
3952 | chrome.exe | GET | 301 | 151.101.2.109:80 | http://cdn.jsdelivr.net/npm/p2p-media-loader-core@latest/build/p2p-media-loader-core.min.js | US | — | — | whitelisted |
3952 | chrome.exe | GET | 200 | 104.31.2.191:80 | http://123tvnow.com/wp-content/litespeed/cssjs/d8f06.css | US | text | 541 b | malicious |
3952 | chrome.exe | GET | 200 | 104.31.2.191:80 | http://123tvnow.com/wp-content/litespeed/cssjs/71248.css | US | text | 6.64 Kb | malicious |
3952 | chrome.exe | GET | 200 | 104.31.2.191:80 | http://123tvnow.com/wp-content/litespeed/cssjs/4cad6.js | US | text | 5.65 Kb | malicious |
3952 | chrome.exe | GET | 200 | 104.31.2.191:80 | http://123tvnow.com/wp-content/litespeed/cssjs/8b321.css | US | text | 18.7 Kb | malicious |
3952 | chrome.exe | GET | 200 | 104.31.2.191:80 | http://123tvnow.com/wp-content/litespeed/cssjs/69b20.css | US | text | 24.5 Kb | malicious |
3952 | chrome.exe | GET | 200 | 104.31.2.191:80 | http://123tvnow.com/wp-content/litespeed/cssjs/2c6f1.css | US | text | 7.39 Kb | malicious |
3952 | chrome.exe | GET | 200 | 104.31.2.191:80 | http://123tvnow.com/wp-content/litespeed/cssjs/99a31.css | US | text | 6.54 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3952 | chrome.exe | 172.217.22.35:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3952 | chrome.exe | 104.31.2.191:80 | 123tvnow.com | Cloudflare Inc | US | unknown |
3952 | chrome.exe | 209.197.3.15:443 | netdna.bootstrapcdn.com | Highwinds Network Group, Inc. | US | whitelisted |
3952 | chrome.exe | 172.217.21.234:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3952 | chrome.exe | 151.101.2.109:80 | cdn.jsdelivr.net | Fastly | US | suspicious |
3952 | chrome.exe | 151.101.2.114:443 | ssl.p.jwpcdn.com | Fastly | US | suspicious |
3952 | chrome.exe | 151.101.2.109:443 | cdn.jsdelivr.net | Fastly | US | suspicious |
3952 | chrome.exe | 104.26.15.238:80 | services.vlitag.com | Cloudflare Inc | US | suspicious |
3952 | chrome.exe | 172.217.18.99:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3952 | chrome.exe | 35.201.115.74:80 | moneymakercdn.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
123tvnow.com |
| malicious |
accounts.google.com |
| shared |
netdna.bootstrapcdn.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
cdn.jsdelivr.net |
| whitelisted |
ssl.p.jwpcdn.com |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
s.w.org |
| whitelisted |
services.vlitag.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3952 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup ip-api.com |
3952 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
3952 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
3952 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
3952 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
3952 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
3952 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
3952 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
1052 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
3952 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |