| File name: | 5280_36.xlsm |
| Full analysis: | https://app.any.run/tasks/8e69c340-4c89-4c95-b85c-a41f3c5b6b4a |
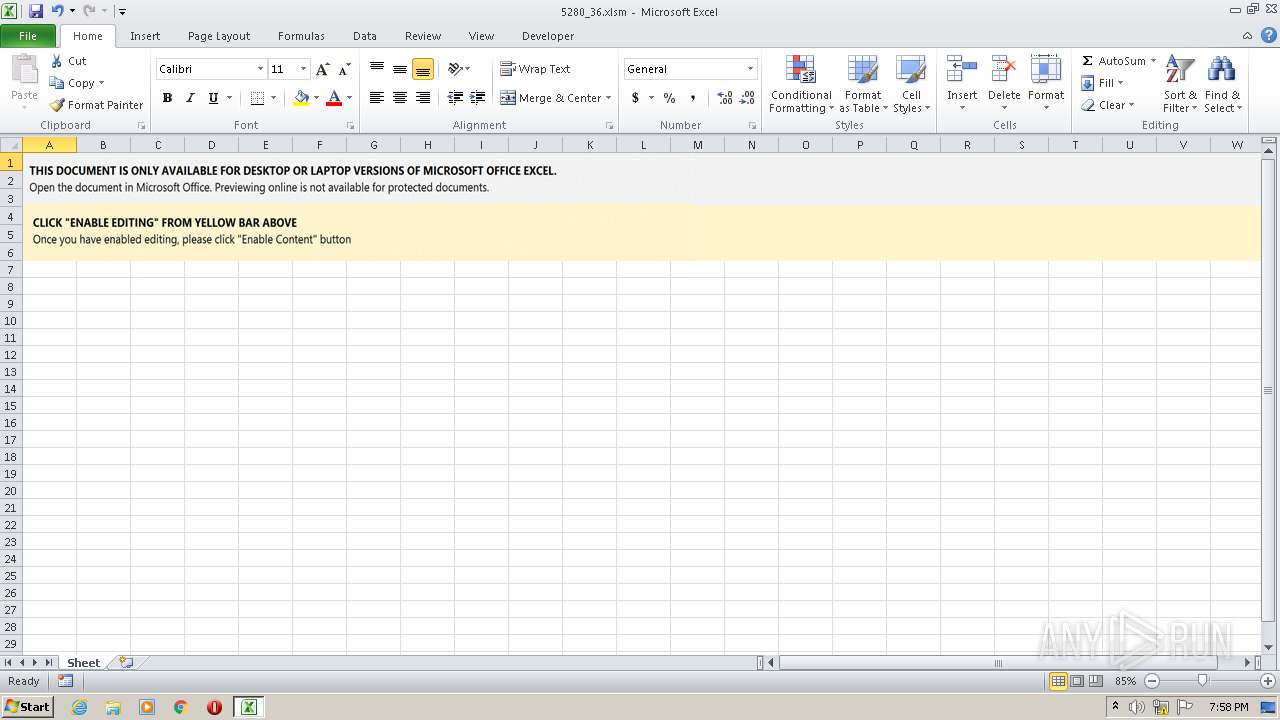
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | January 14, 2022, 19:58:38 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.openxmlformats-officedocument.spreadsheetml.sheet |
| File info: | Microsoft Excel 2007+ |
| MD5: | E30CEA246A3807BE6924C3EA52E10079 |
| SHA1: | FFC27600E071E38E78A29174FC885D4E2BBDB0AD |
| SHA256: | 02FEF2F393DFA1693167AF8424FF91F298D3C12BAD8411580F82548C7876CDFD |
| SSDEEP: | 1536:OW5FiLysqxG/+CbEcWeu3XDXeoiHwt/uE1d7mT6SrPag3HtQVASgV+:t5kiG/+CbE9H78wt2E1d7e6STa6SH |
MALICIOUS
Executable content was dropped or overwritten
- EXCEL.EXE (PID: 1252)
Connects to CnC server
- rundll32.exe (PID: 3504)
Loads dropped or rewritten executable
- rundll32.exe (PID: 3504)
- rundll32.exe (PID: 3004)
- SearchProtocolHost.exe (PID: 4080)
- rundll32.exe (PID: 3816)
- rundll32.exe (PID: 3120)
Unusual execution from Microsoft Office
- EXCEL.EXE (PID: 1252)
Changes the autorun value in the registry
- rundll32.exe (PID: 3504)
SUSPICIOUS
Reads default file associations for system extensions
- SearchProtocolHost.exe (PID: 4080)
- rundll32.exe (PID: 3120)
Uses RUNDLL32.EXE to load library
- EXCEL.EXE (PID: 1252)
- rundll32.exe (PID: 3816)
- rundll32.exe (PID: 3120)
- rundll32.exe (PID: 3004)
Drops a file with a compile date too recent
- EXCEL.EXE (PID: 1252)
- rundll32.exe (PID: 3120)
Starts itself from another location
- rundll32.exe (PID: 3816)
Executable content was dropped or overwritten
- rundll32.exe (PID: 3120)
Application launched itself
- rundll32.exe (PID: 3120)
- rundll32.exe (PID: 3004)
INFO
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 1252)
Checks supported languages
- EXCEL.EXE (PID: 1252)
- rundll32.exe (PID: 3120)
- rundll32.exe (PID: 3816)
- rundll32.exe (PID: 3004)
- rundll32.exe (PID: 3504)
Reads the computer name
- EXCEL.EXE (PID: 1252)
- rundll32.exe (PID: 3120)
- rundll32.exe (PID: 3504)
Creates files in the user directory
- EXCEL.EXE (PID: 1252)
Reads settings of System Certificates
- rundll32.exe (PID: 3504)
Checks Windows Trust Settings
- rundll32.exe (PID: 3504)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .xlsx | | | Excel Microsoft Office Open XML Format document (61.2) |
|---|---|---|
| .zip | | | Open Packaging Conventions container (31.5) |
| .zip | | | ZIP compressed archive (7.2) |
EXIF
XML
| AppVersion: | 16.03 |
|---|---|
| HyperlinksChanged: | No |
| SharedDoc: | No |
| LinksUpToDate: | No |
| Company: | - |
| TitlesOfParts: |
|
| HeadingPairs: |
|
| ScaleCrop: | No |
| DocSecurity: | None |
| Application: | Microsoft Excel |
| ModifyDate: | 2022:01:14 07:23:02Z |
| CreateDate: | 2015:06:05 18:19:34Z |
| LastModifiedBy: | Admin |
XMP
| Creator: | Admin |
|---|
ZIP
| ZipFileName: | [Content_Types].xml |
|---|---|
| ZipUncompressedSize: | 1943 |
| ZipCompressedSize: | 457 |
| ZipCRC: | 0x332b8ba7 |
| ZipModifyDate: | 1980:01:01 00:00:00 |
| ZipCompression: | Deflated |
| ZipBitFlag: | 0x0006 |
| ZipRequiredVersion: | 20 |
Total processes
41
Monitored processes
6
Malicious processes
2
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1252 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" /dde | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3004 | C:\Windows\system32\rundll32.exe "C:\Users\admin\AppData\Local\Ldjxcnf\ionoqo.acq",YrPLRXHU | C:\Windows\system32\rundll32.exe | — | rundll32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3120 | C:\Windows\system32\rundll32.exe "C:\Users\admin\erum.ocx",DllRegisterServer | C:\Windows\system32\rundll32.exe | rundll32.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3504 | C:\Windows\system32\rundll32.exe "C:\Users\admin\AppData\Local\Ldjxcnf\ionoqo.acq",DllRegisterServer | C:\Windows\system32\rundll32.exe | rundll32.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3816 | C:\Windows\SysWow64\rundll32.exe ..\erum.ocx,D"&"l"&"lR"&"egister"&"Serve"&"r | C:\Windows\SysWow64\rundll32.exe | — | EXCEL.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 4080 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe3_ Global\UsGthrCtrlFltPipeMssGthrPipe3 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\system32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7601.24542 (win7sp1_ldr_escrow.191209-2211) Modules
| |||||||||||||||
Total events
7 280
Read events
7 176
Write events
92
Delete events
12
Modification events
| (PID) Process: | (1252) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | write | Name: | <c9 |
Value: 3C633900E4040000010000000000000000000000 | |||
| (PID) Process: | (1252) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (1252) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (1252) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (1252) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (1252) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (1252) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (1252) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (1252) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (1252) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
3
Suspicious files
5
Text files
1
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1252 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVRE3AC.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1252 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\Tmho7DmakD[1].dll | executable | |
MD5:— | SHA256:— | |||
| 3504 | rundll32.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 1252 | EXCEL.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\JBRLR9CF.txt | text | |
MD5:— | SHA256:— | |||
| 3504 | rundll32.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:F7DCB24540769805E5BB30D193944DCE | SHA256:6B88C6AC55BBD6FEA0EBE5A760D1AD2CFCE251C59D0151A1400701CB927E36EA | |||
| 3120 | rundll32.exe | C:\Users\admin\AppData\Local\Ldjxcnf\ionoqo.acq | executable | |
MD5:— | SHA256:— | |||
| 3504 | rundll32.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\77EC63BDA74BD0D0E0426DC8F8008506 | binary | |
MD5:— | SHA256:— | |||
| 3504 | rundll32.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\77EC63BDA74BD0D0E0426DC8F8008506 | compressed | |
MD5:ACAEDA60C79C6BCAC925EEB3653F45E0 | SHA256:6B0CECCF0103AFD89844761417C1D23ACC41F8AEBF3B7230765209B61EEE5658 | |||
| 3504 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\Cab8432.tmp | compressed | |
MD5:ACAEDA60C79C6BCAC925EEB3653F45E0 | SHA256:6B0CECCF0103AFD89844761417C1D23ACC41F8AEBF3B7230765209B61EEE5658 | |||
| 3504 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\Tar8433.tmp | cat | |
MD5:D99661D0893A52A0700B8AE68457351A | SHA256:BDD5111162A6FA25682E18FA74E37E676D49CAFCB5B7207E98E5256D1EF0D003 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
7
DNS requests
2
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1252 | EXCEL.EXE | GET | 200 | 104.21.57.10:80 | http://badmakeup.biz/dhl/3ez4GMS65Gk6Bgxd/ | US | executable | 574 Kb | suspicious |
3504 | rundll32.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?4c24a92f440efddd | US | compressed | 59.9 Kb | whitelisted |
3504 | rundll32.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?728cb08b1e0fdde4 | US | compressed | 4.70 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3504 | rundll32.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1252 | EXCEL.EXE | 104.21.57.10:80 | badmakeup.biz | Cloudflare Inc | US | suspicious |
3504 | rundll32.exe | 45.138.98.34:80 | — | — | — | malicious |
3504 | rundll32.exe | 69.16.218.101:8080 | — | Liquid Web, L.L.C | US | malicious |
— | — | 45.138.98.34:80 | — | — | — | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
badmakeup.biz |
| suspicious |
ctldl.windowsupdate.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |
1252 | EXCEL.EXE | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
1252 | EXCEL.EXE | A Network Trojan was detected | ET CURRENT_EVENTS Likely Evil EXE download from MSXMLHTTP non-exe extension M2 |
1252 | EXCEL.EXE | Misc activity | ET INFO Possible EXE Download From Suspicious TLD |
1252 | EXCEL.EXE | Misc activity | ET INFO EXE - Served Attached HTTP |
3504 | rundll32.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 17 |
3504 | rundll32.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 20 |
2 ETPRO signatures available at the full report