| File name: | HncOfficeEngine.vbe |
| Full analysis: | https://app.any.run/tasks/601123b5-7090-4216-a16f-1af04fd2e101 |
| Verdict: | Malicious activity |
| Analysis date: | April 25, 2019, 11:58:52 |
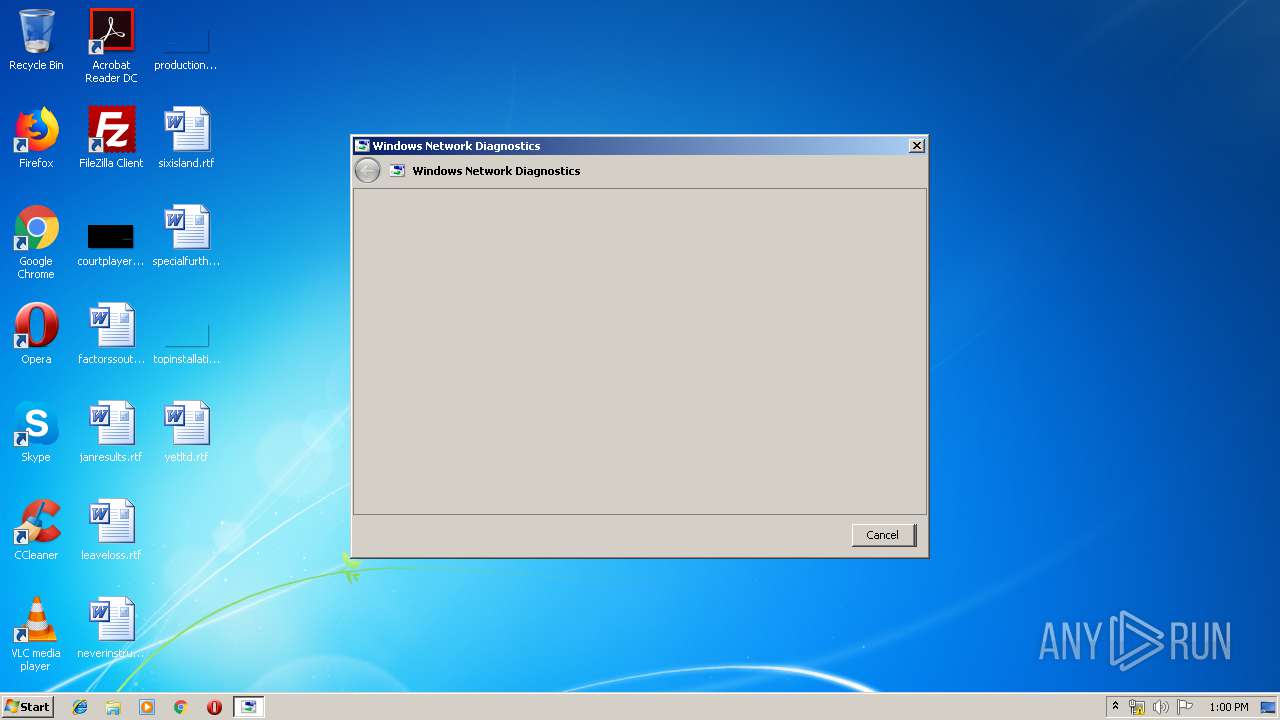
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/octet-stream |
| File info: | data |
| MD5: | 2C871BF3508899DF439019F70430C00A |
| SHA1: | D8DFC75959D8C0E20E5A9CA92B43A9AD117D4ED1 |
| SHA256: | 02FB01AF6F8024D6FC24B6106FBC3BABBE2C3C21368B6D130BFCDEE76C2EFBFD |
| SSDEEP: | 96:/SSHurwRwUX40b3MOn+MKxO7VxAfQdT0sdDAcx:4UPMkvxVxAfitDHx |
MALICIOUS
Loads dropped or rewritten executable
- sdiagnhost.exe (PID: 2600)
SUSPICIOUS
Executable content was dropped or overwritten
- msdt.exe (PID: 2440)
- msdt.exe (PID: 2564)
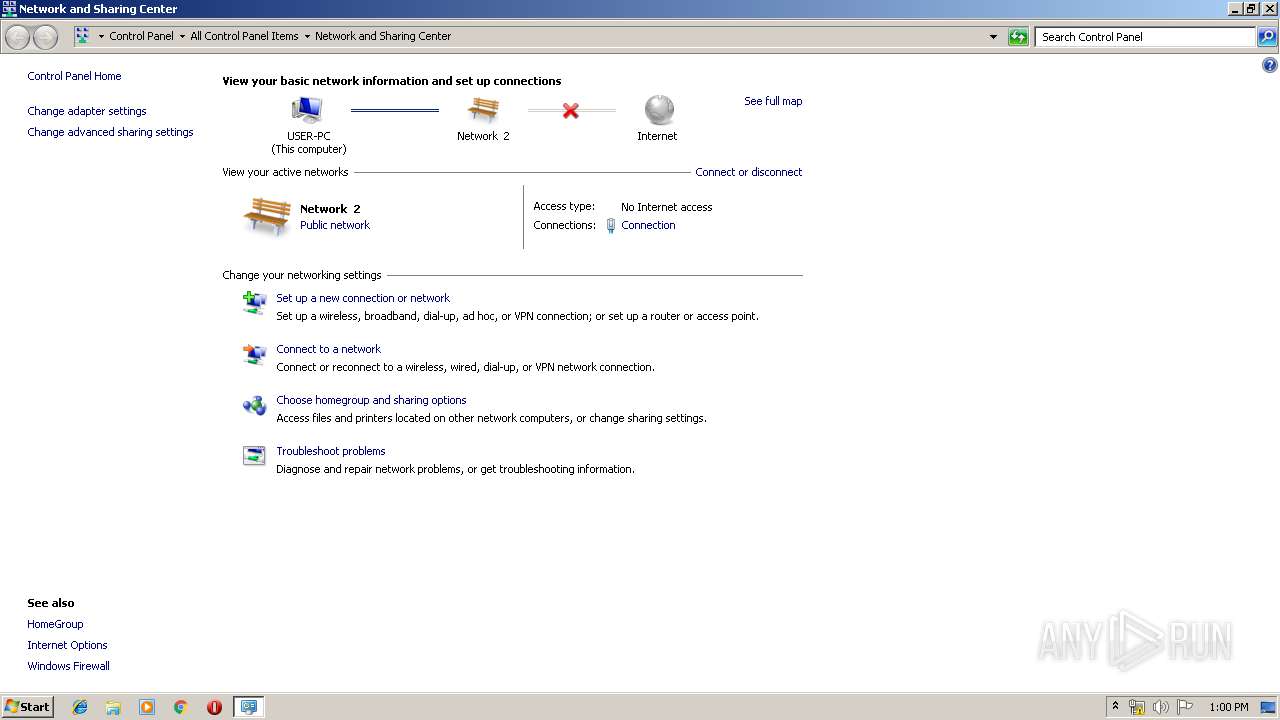
Uses IPCONFIG.EXE to discover IP address
- sdiagnhost.exe (PID: 2696)
- sdiagnhost.exe (PID: 2600)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .vbe | | | VBScript Encoded script (100) |
|---|
Total processes
57
Monitored processes
23
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1628 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RESFA14.tmp" "c:\Users\admin\AppData\Local\Temp\CSCFA13.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 8.00.50727.4940 (Win7SP1.050727-5400) Modules
| |||||||||||||||
| 1740 | "C:\Windows\system32\makecab.exe" /f NetworkConfiguration.ddf | C:\Windows\system32\makecab.exe | — | sdiagnhost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Cabinet Maker Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2364 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RES3BD0.tmp" "c:\Users\admin\AppData\Local\Temp\CSC3BCF.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 8.00.50727.4940 (Win7SP1.050727-5400) Modules
| |||||||||||||||
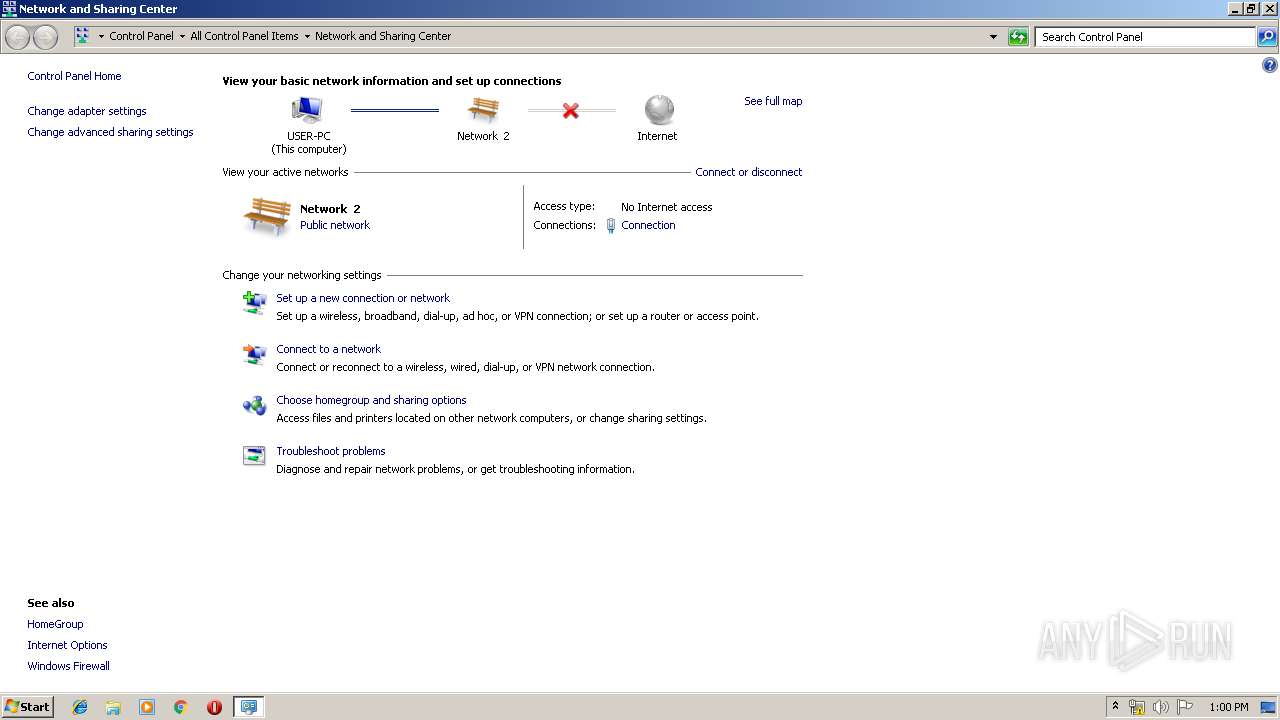
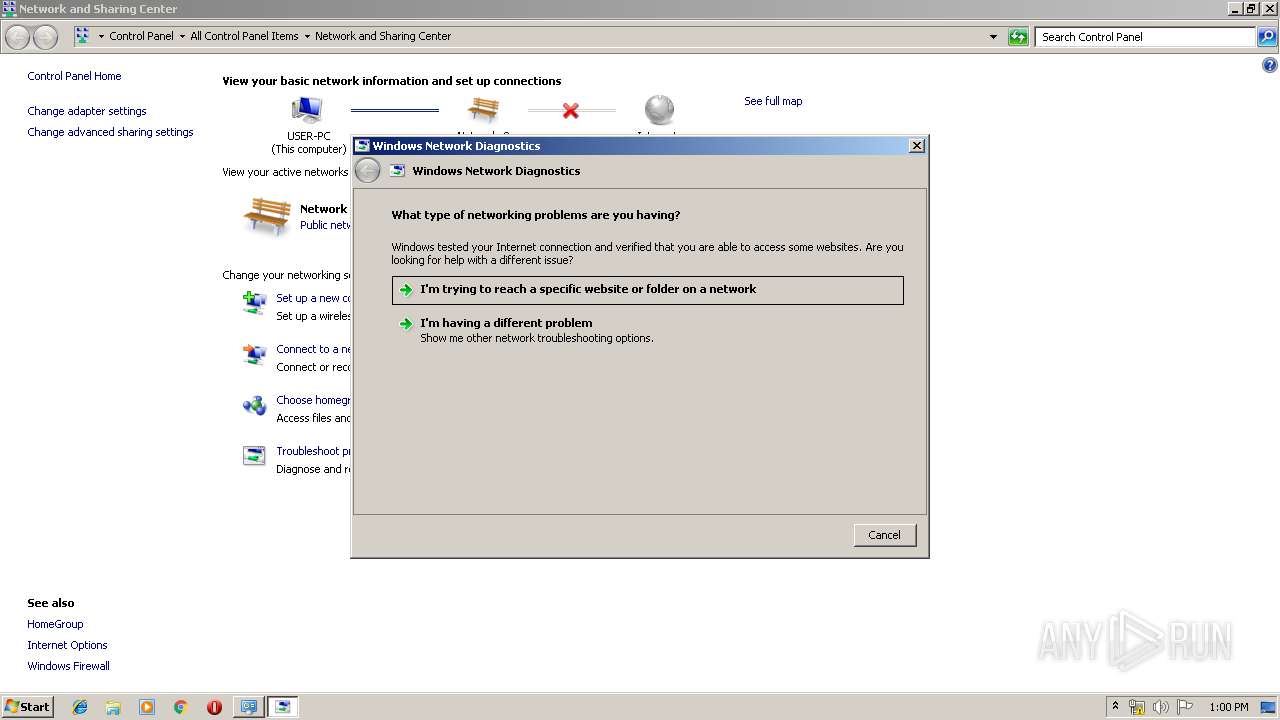
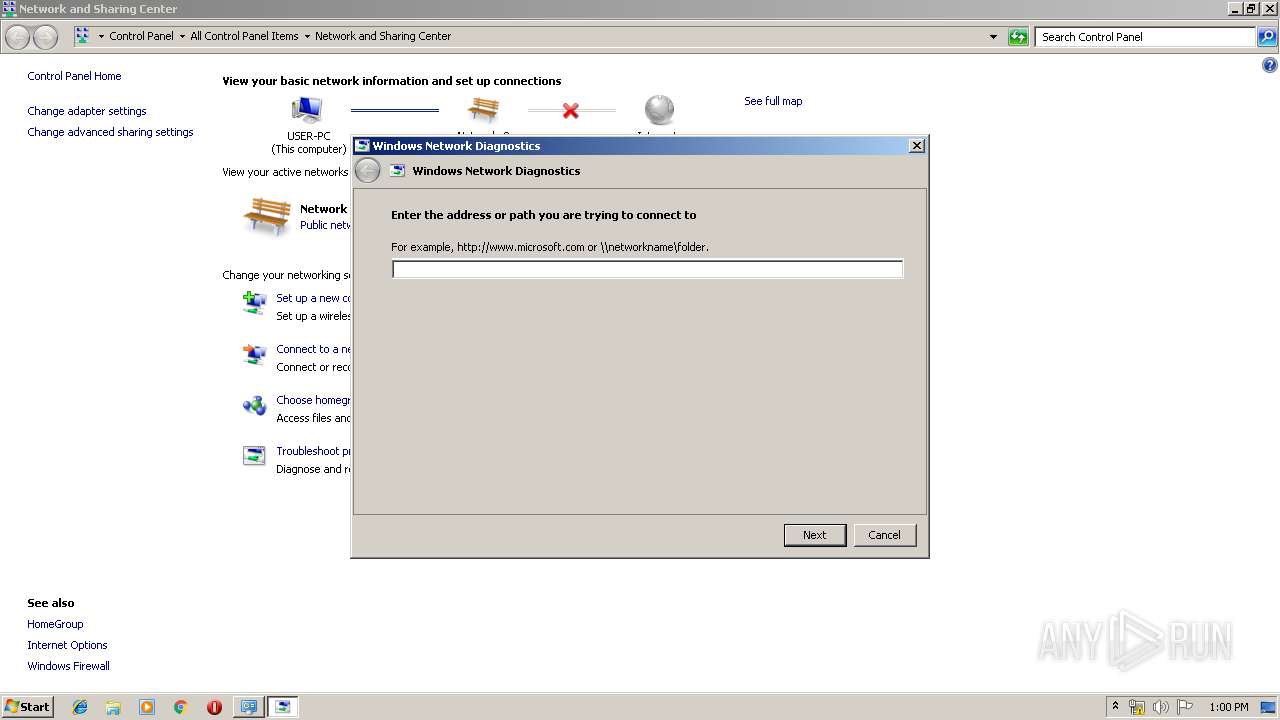
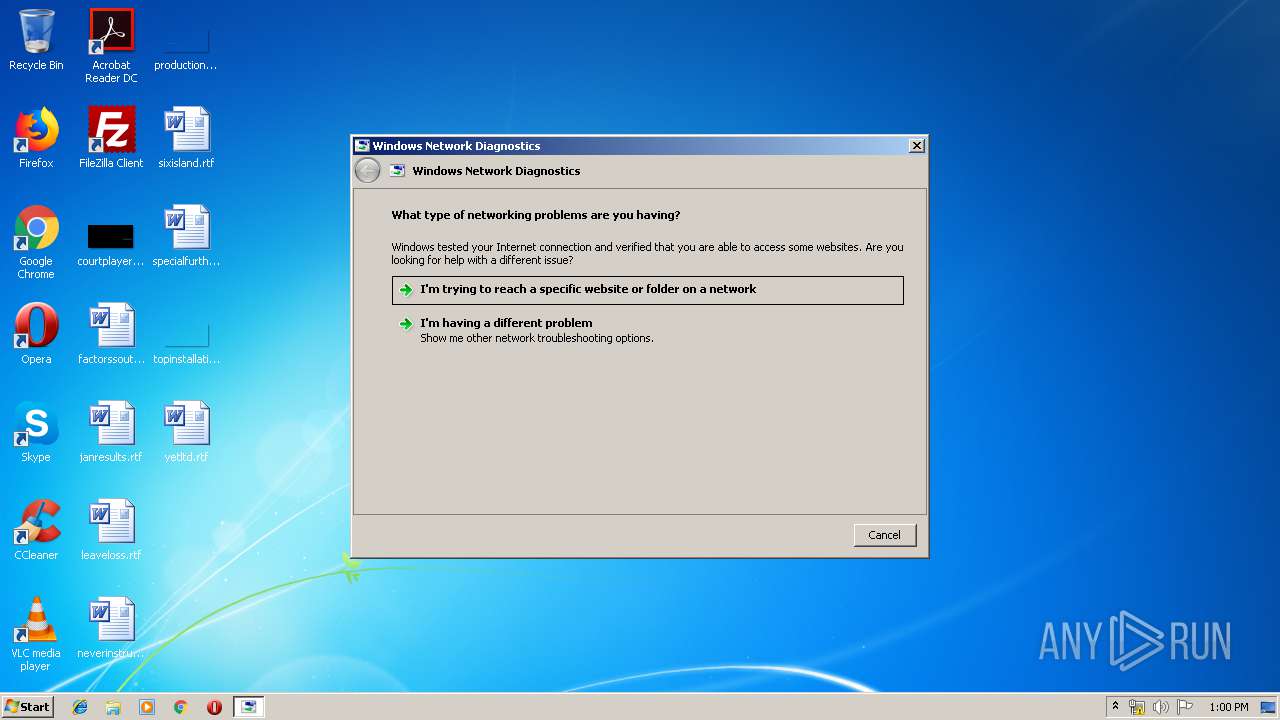
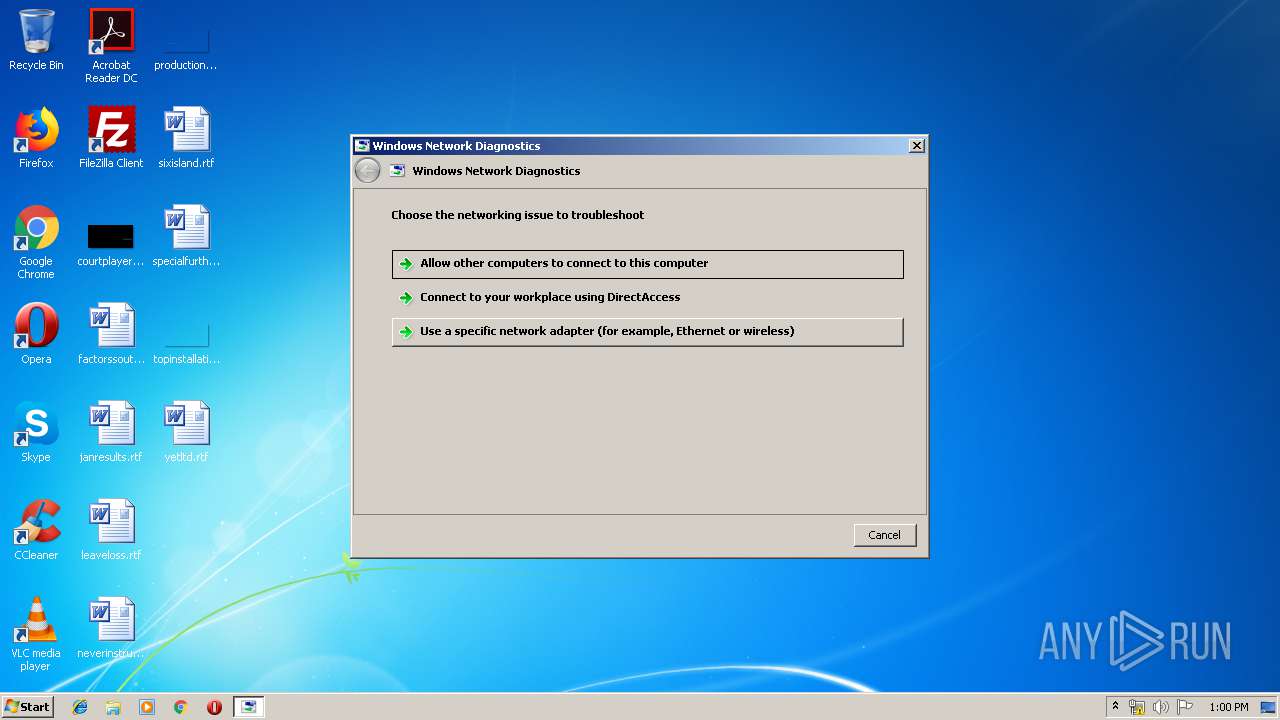
| 2436 | "C:\Windows\System32\msdt.exe" -skip TRUE -path C:\Windows\diagnostics\system\networking -ep NetworkDiagnosticsNetworkMiniMap | C:\Windows\System32\msdt.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Diagnostics Troubleshooting Wizard Exit code: 4294967295 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2440 | "C:\Windows\System32\msdt.exe" -skip TRUE -path C:\Windows\diagnostics\system\networking -ep NetworkDiagnosticsNetworkMiniMap | C:\Windows\System32\msdt.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Diagnostics Troubleshooting Wizard Exit code: 4294967295 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2464 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\p2hyogvz.cmdline" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe | sdiagnhost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Exit code: 0 Version: 8.0.50727.4927 (NetFXspW7.050727-4900) Modules
| |||||||||||||||
| 2480 | "C:\Windows\system32\ROUTE.EXE" print | C:\Windows\system32\ROUTE.EXE | — | sdiagnhost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Route Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2564 | "C:\Windows\System32\msdt.exe" -skip TRUE -path C:\Windows\diagnostics\system\networking -ep NetworkDiagnosticsNetworkMiniMap | C:\Windows\System32\msdt.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Diagnostics Troubleshooting Wizard Exit code: 4294967295 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2600 | C:\Windows\System32\sdiagnhost.exe -Embedding | C:\Windows\System32\sdiagnhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Scripted Diagnostics Native Host Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2696 | C:\Windows\System32\sdiagnhost.exe -Embedding | C:\Windows\System32\sdiagnhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Scripted Diagnostics Native Host Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
200
Read events
164
Write events
36
Delete events
0
Modification events
| (PID) Process: | (2440) msdt.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2696) sdiagnhost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2696) sdiagnhost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2564) msdt.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2600) sdiagnhost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2600) sdiagnhost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2600) sdiagnhost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2600) sdiagnhost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | @DiagPackage.dll,-10012 |
Value: Share files or folders | |||
| (PID) Process: | (2600) sdiagnhost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | @DiagPackage.dll,-10013 |
Value: Connect to this computer using Remote Desktop Connection | |||
| (PID) Process: | (2600) sdiagnhost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | @DiagPackage.dll,-10014 |
Value: Find this computer on the network | |||
Executable files
4
Suspicious files
6
Text files
38
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3108 | csc.exe | C:\Users\admin\AppData\Local\Temp\CSCFA13.tmp | — | |
MD5:— | SHA256:— | |||
| 3108 | csc.exe | C:\Users\admin\AppData\Local\Temp\iwowlpl_.pdb | — | |
MD5:— | SHA256:— | |||
| 1628 | cvtres.exe | C:\Users\admin\AppData\Local\Temp\RESFA14.tmp | — | |
MD5:— | SHA256:— | |||
| 3108 | csc.exe | C:\Users\admin\AppData\Local\Temp\iwowlpl_.dll | — | |
MD5:— | SHA256:— | |||
| 3108 | csc.exe | C:\Users\admin\AppData\Local\Temp\iwowlpl_.out | — | |
MD5:— | SHA256:— | |||
| 2696 | sdiagnhost.exe | C:\Users\admin\AppData\Local\Temp\tmpFD8D.tmp\ipconfig.all.txt | — | |
MD5:— | SHA256:— | |||
| 2696 | sdiagnhost.exe | C:\Users\admin\AppData\Local\Temp\tmpFD8D.tmp\route.print.txt | — | |
MD5:— | SHA256:— | |||
| 2696 | sdiagnhost.exe | C:\Users\admin\AppData\Local\Temp\tmpFD8D.tmp\NetworkConfiguration.ddf | — | |
MD5:— | SHA256:— | |||
| 1740 | makecab.exe | C:\Users\admin\AppData\Local\Temp\cab_1740_5 | — | |
MD5:— | SHA256:— | |||
| 1740 | makecab.exe | C:\Users\admin\AppData\Local\Temp\cab_1740_6 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
1
DNS requests
2
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
976 | svchost.exe | GET | 200 | 2.23.106.83:80 | http://www.microsoft.com/ | unknown | html | 1020 b | whitelisted |
976 | svchost.exe | GET | 200 | 2.23.106.83:80 | http://www.microsoft.com/ | unknown | html | 1020 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
976 | svchost.exe | 2.23.106.83:80 | www.microsoft.com | Akamai International B.V. | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
976 | svchost.exe | A Network Trojan was detected | ET POLICY Microsoft user-agent automated process response to automated request |
Process | Message |
|---|---|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|