| File name: | Microsoft Windows XP.vbox |
| Full analysis: | https://app.any.run/tasks/f40a4e84-0655-4273-bc00-56f9ab85eec5 |
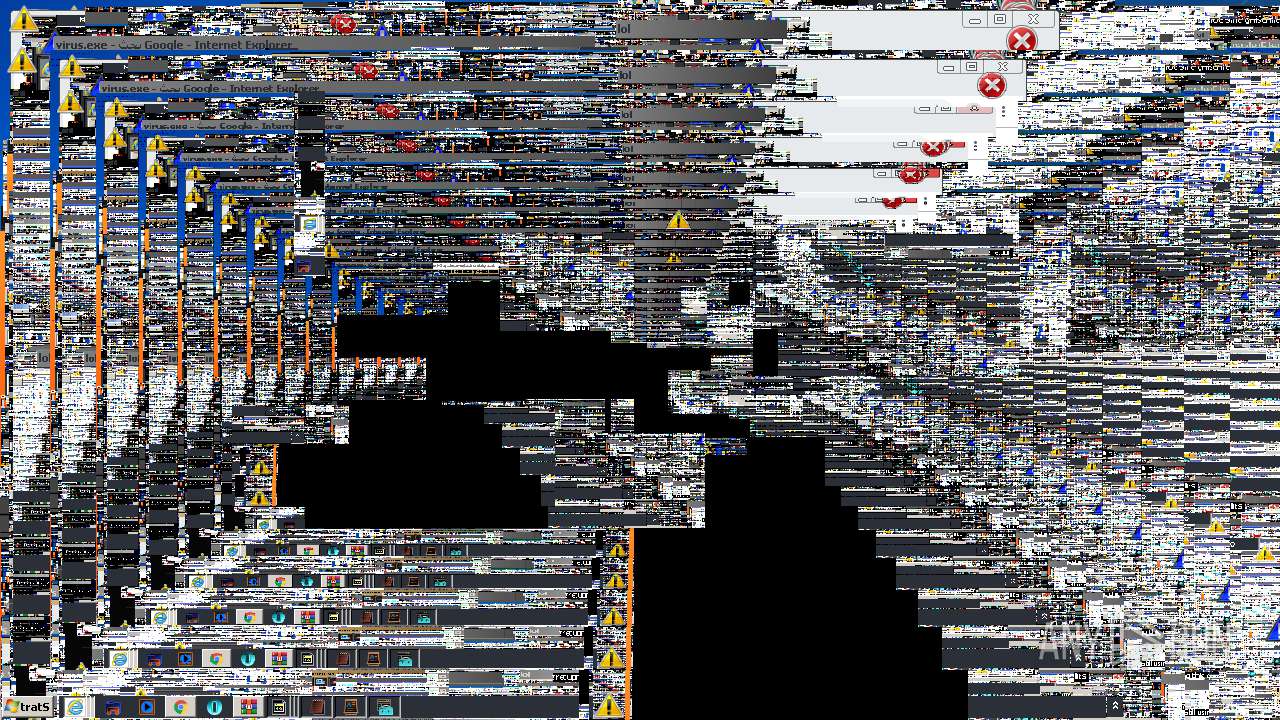
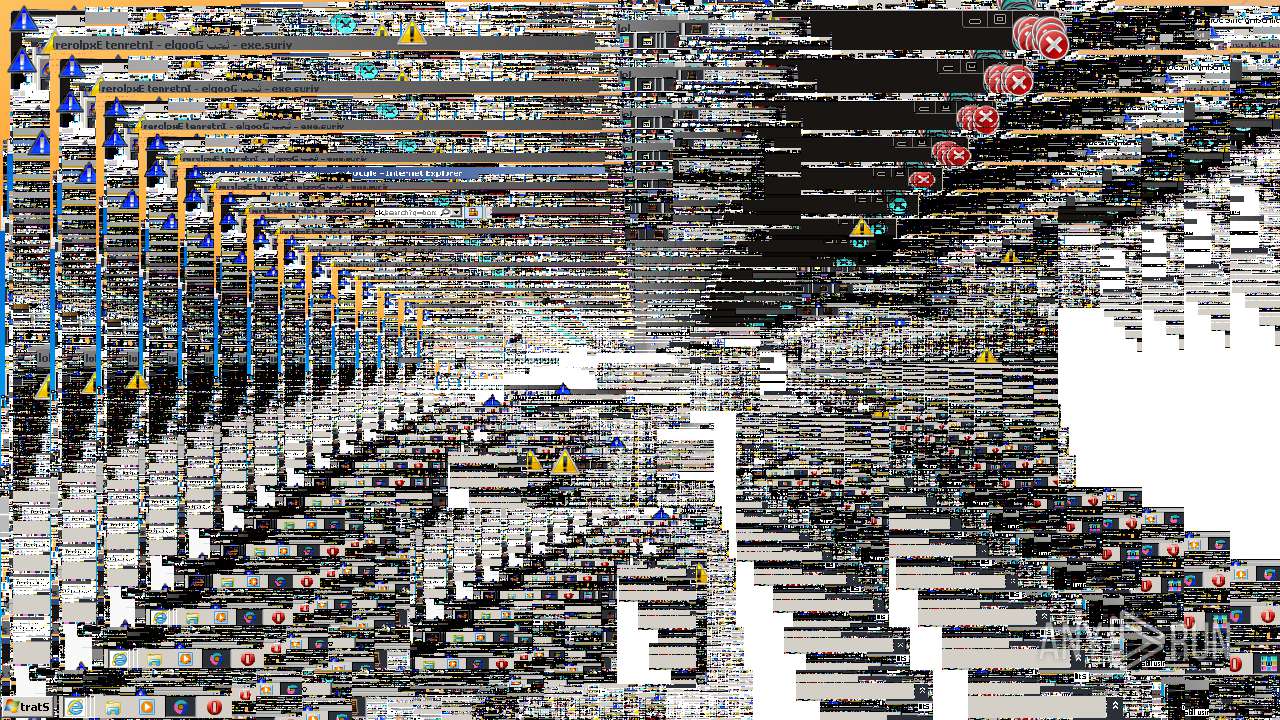
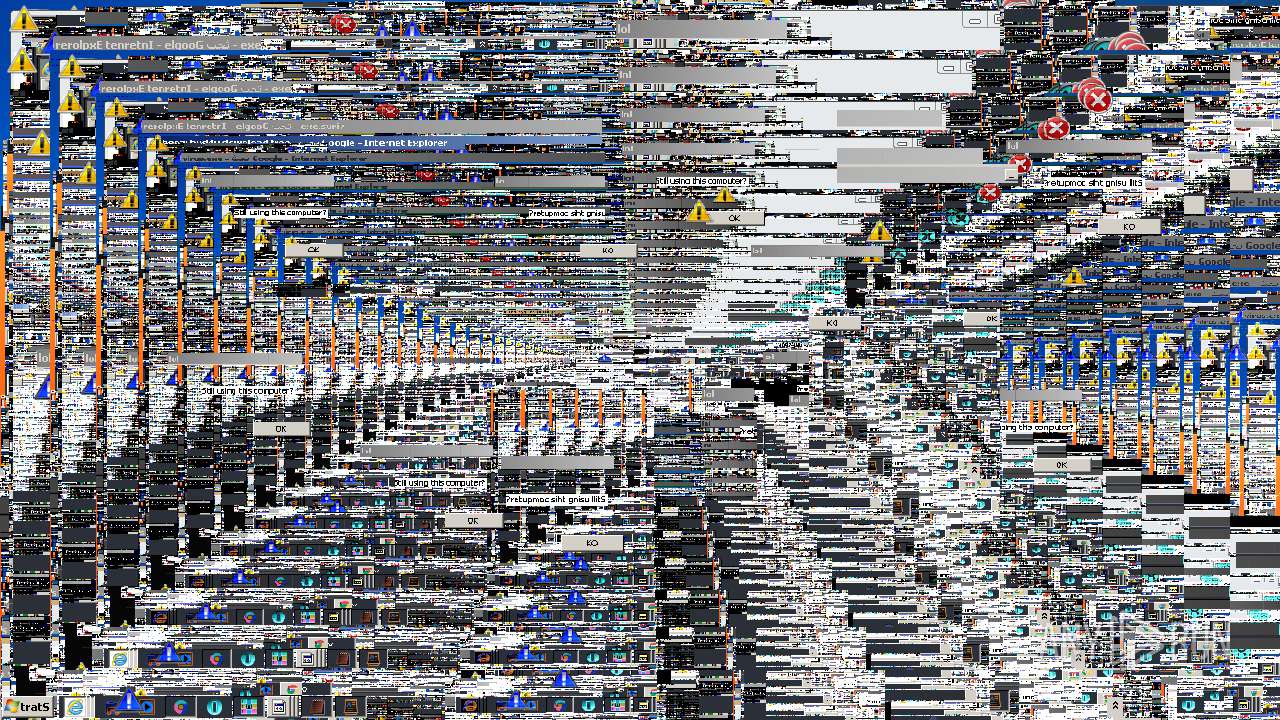
| Verdict: | Malicious activity |
| Analysis date: | August 08, 2020, 17:19:52 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/xml |
| File info: | XML 1.0 document, ASCII text |
| MD5: | FA48B680DBDCE166AEA3D3E54186974A |
| SHA1: | 72155CDCA368CBF4FBC6FA0879A9D6B54EE438AA |
| SHA256: | 02F73ECED81396C1EE13414C5A6EAAE81141C8CAB10083054793DDA5289A40E2 |
| SSDEEP: | 48:e3GIvzR+aF8jBCGC2GWJ1fUj+Rh3+x3aVXujJDpBG:e2cIaFwBCGC2GOFoFCCJtBG |
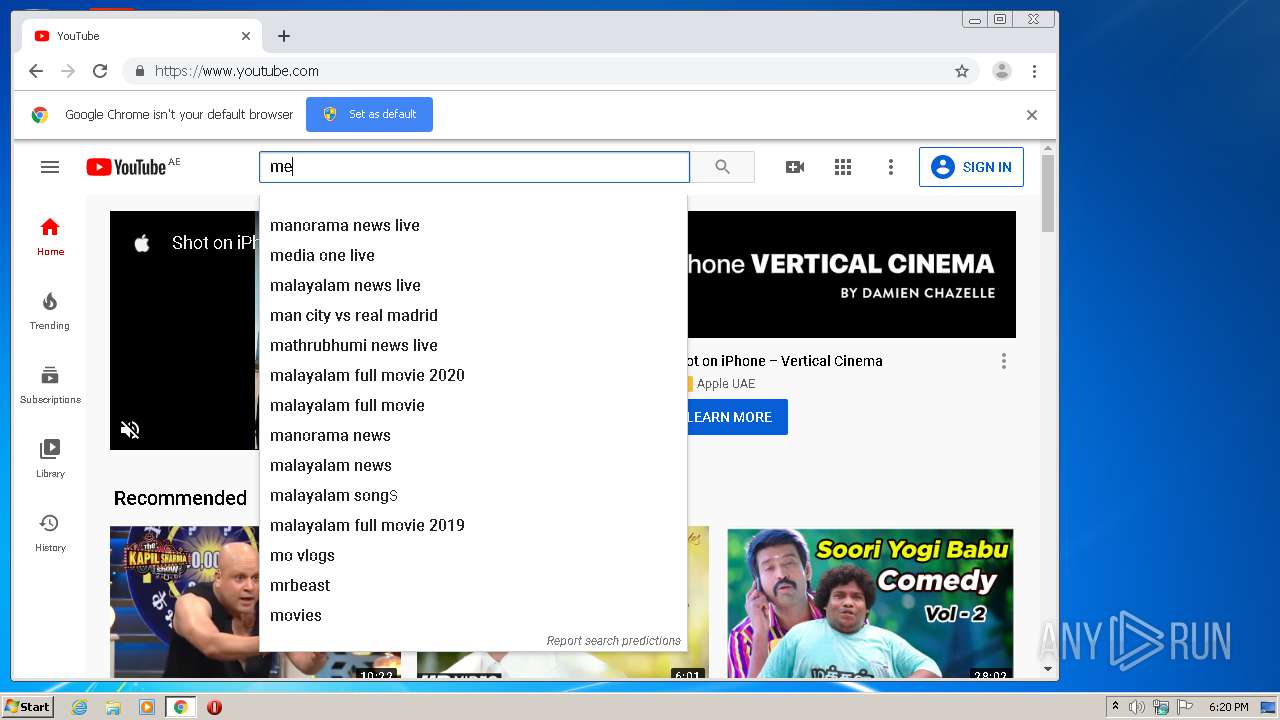
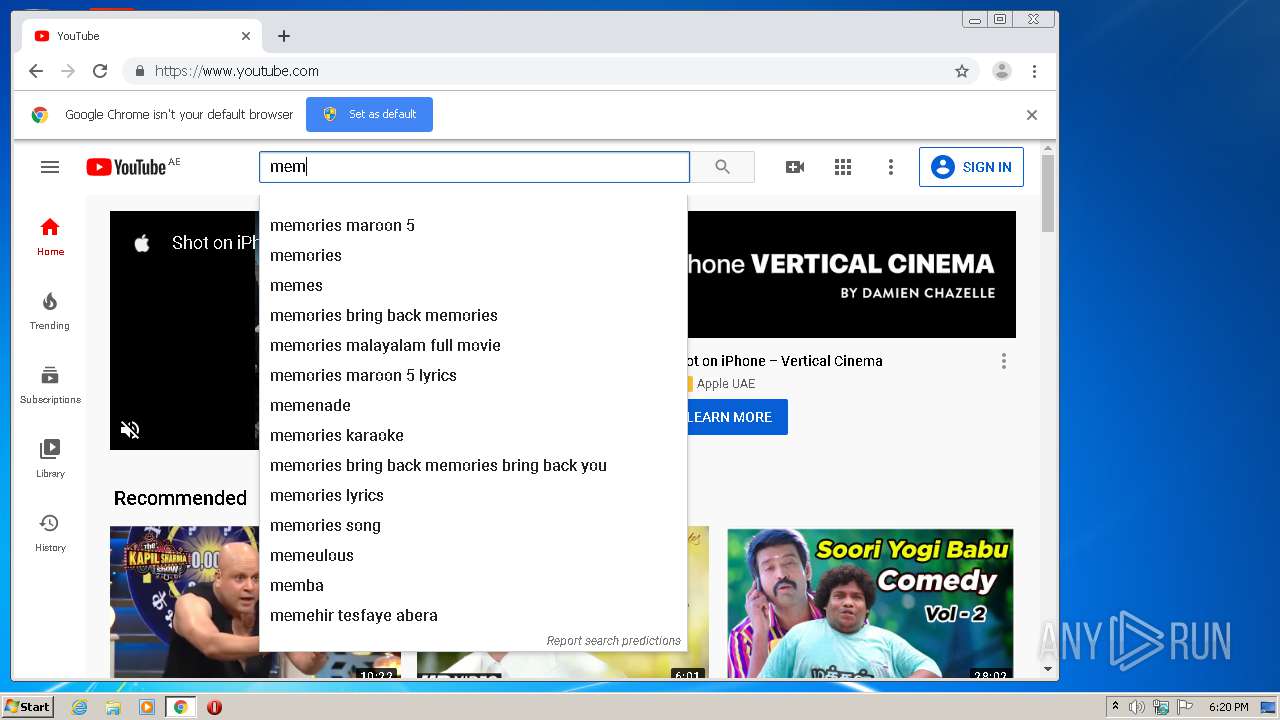
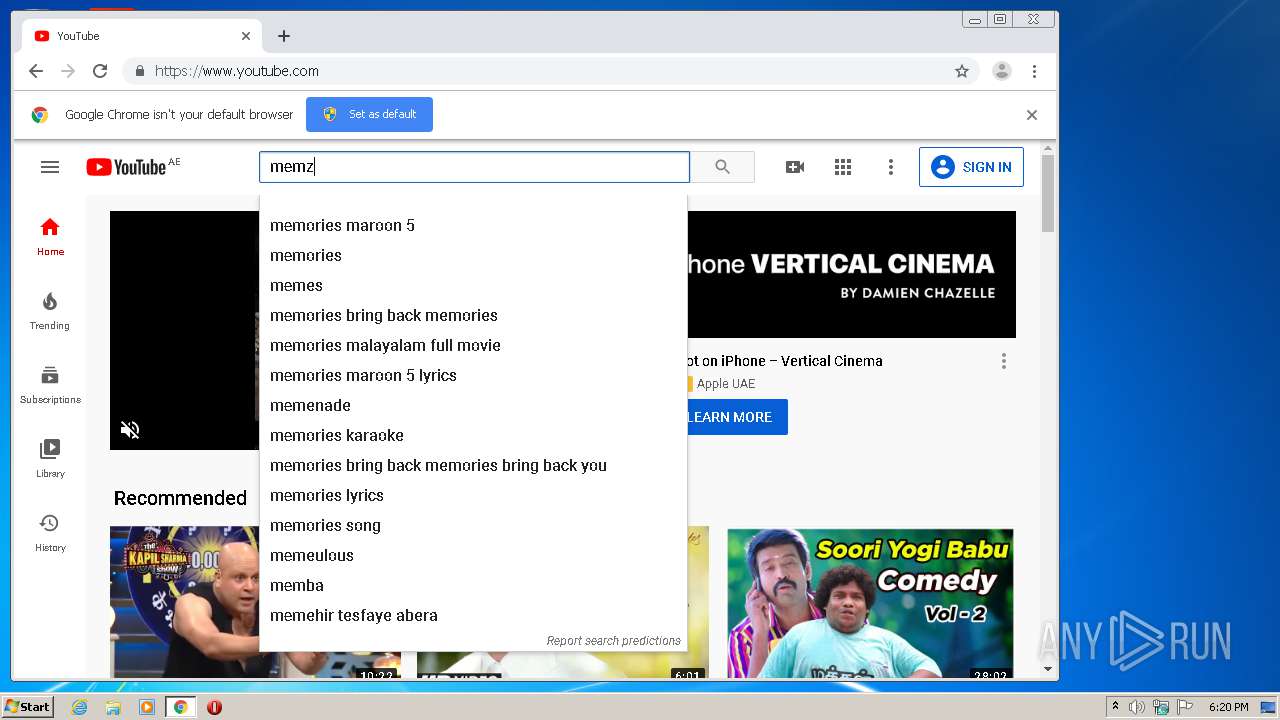
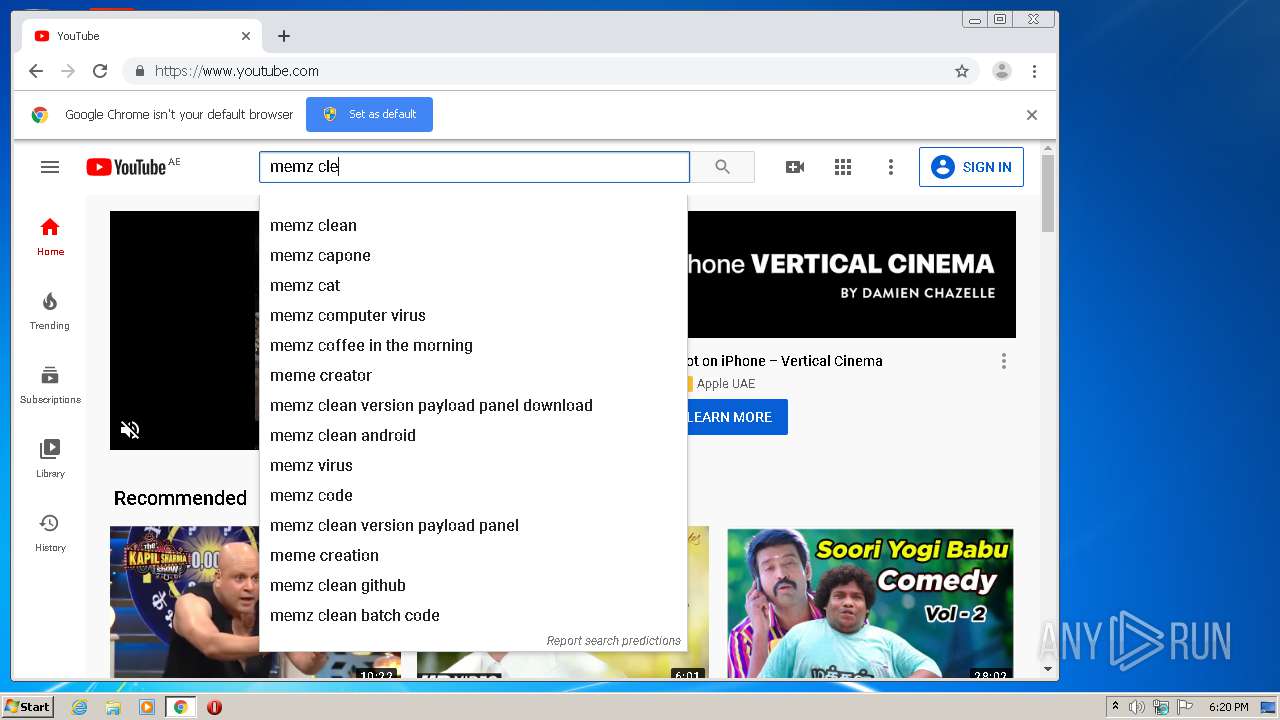
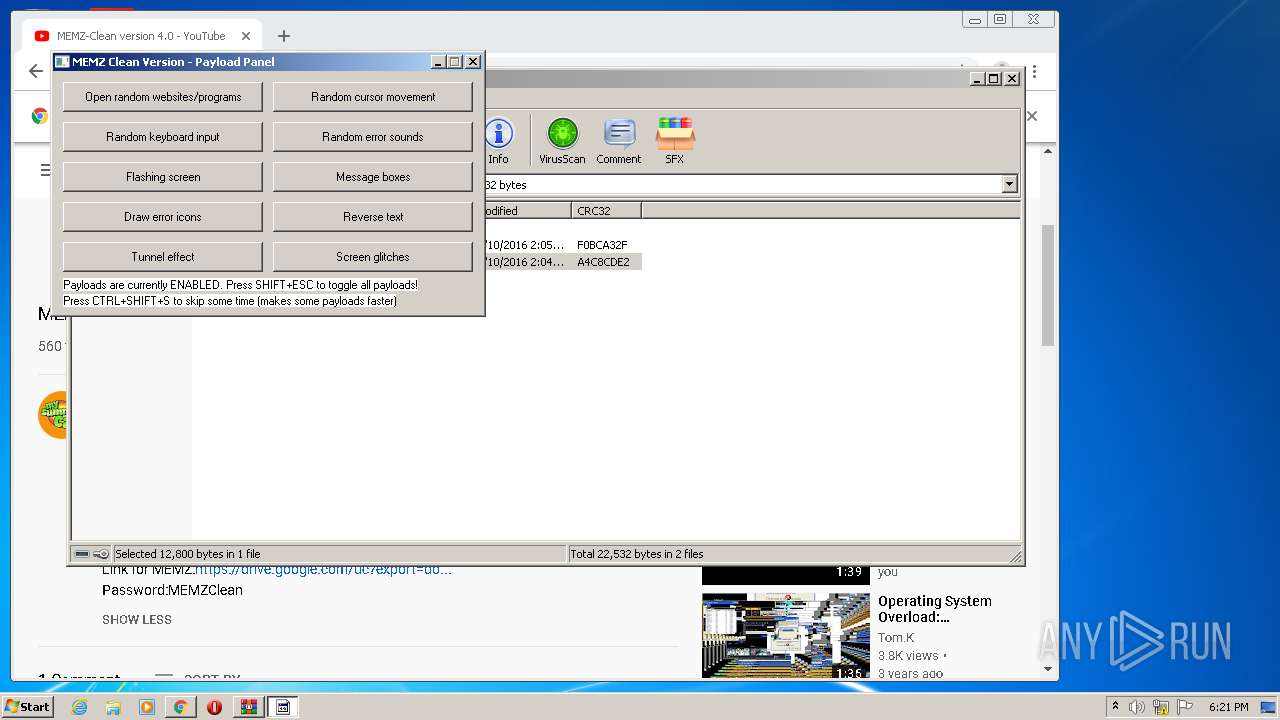
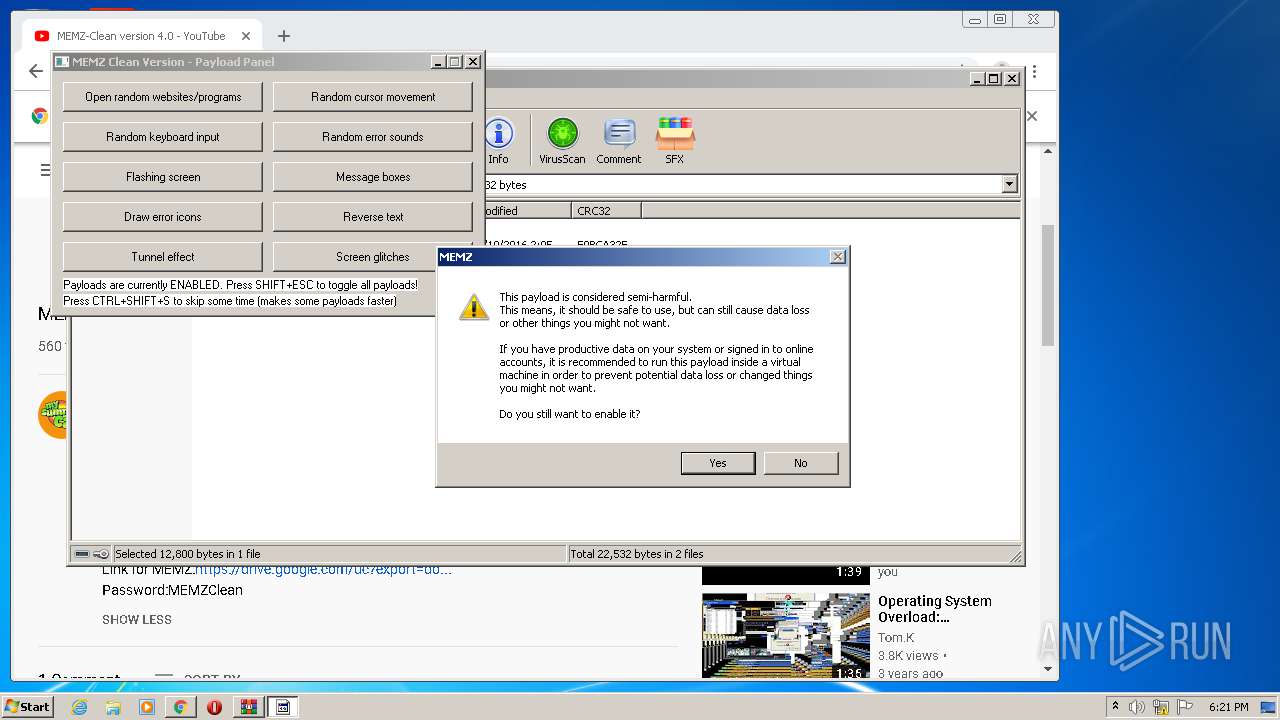
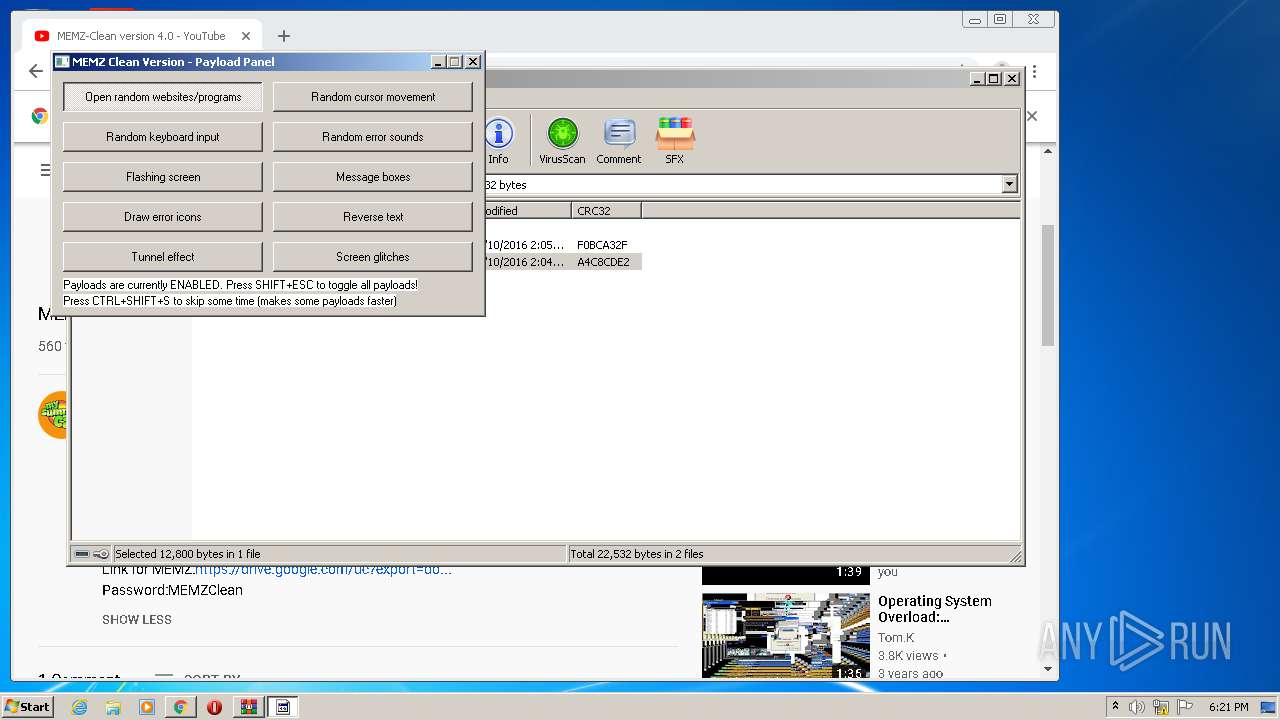
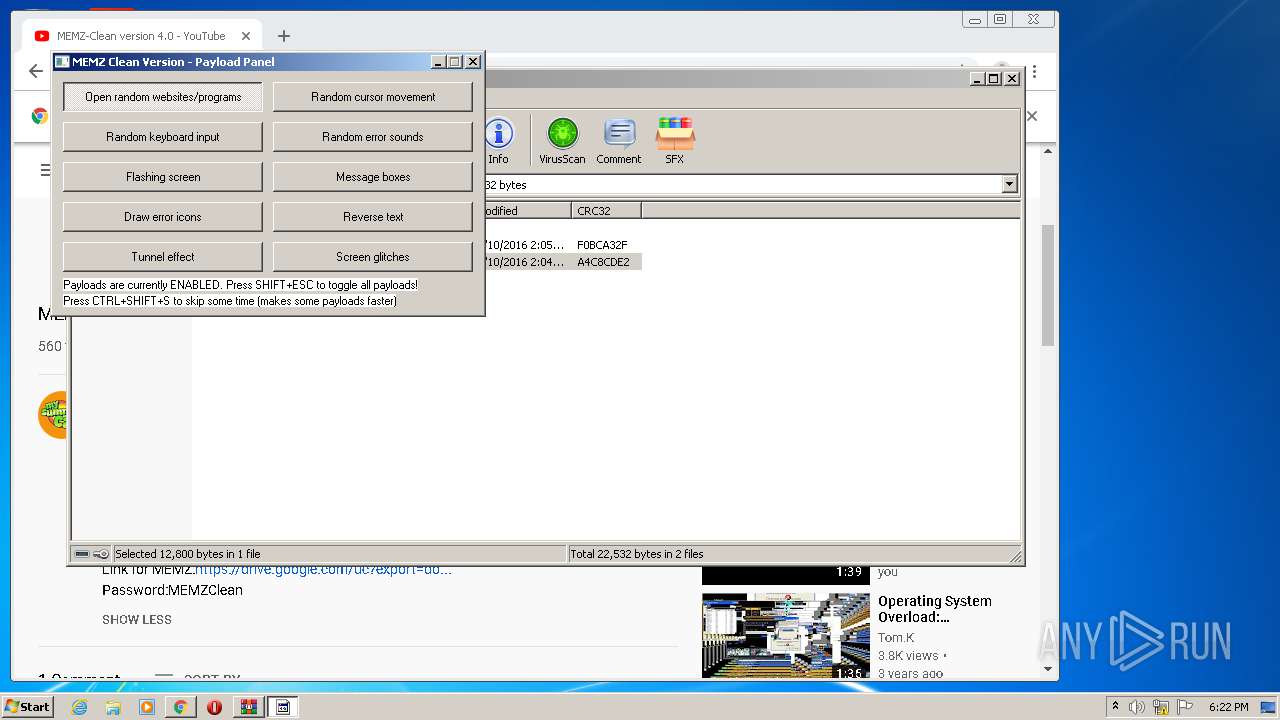
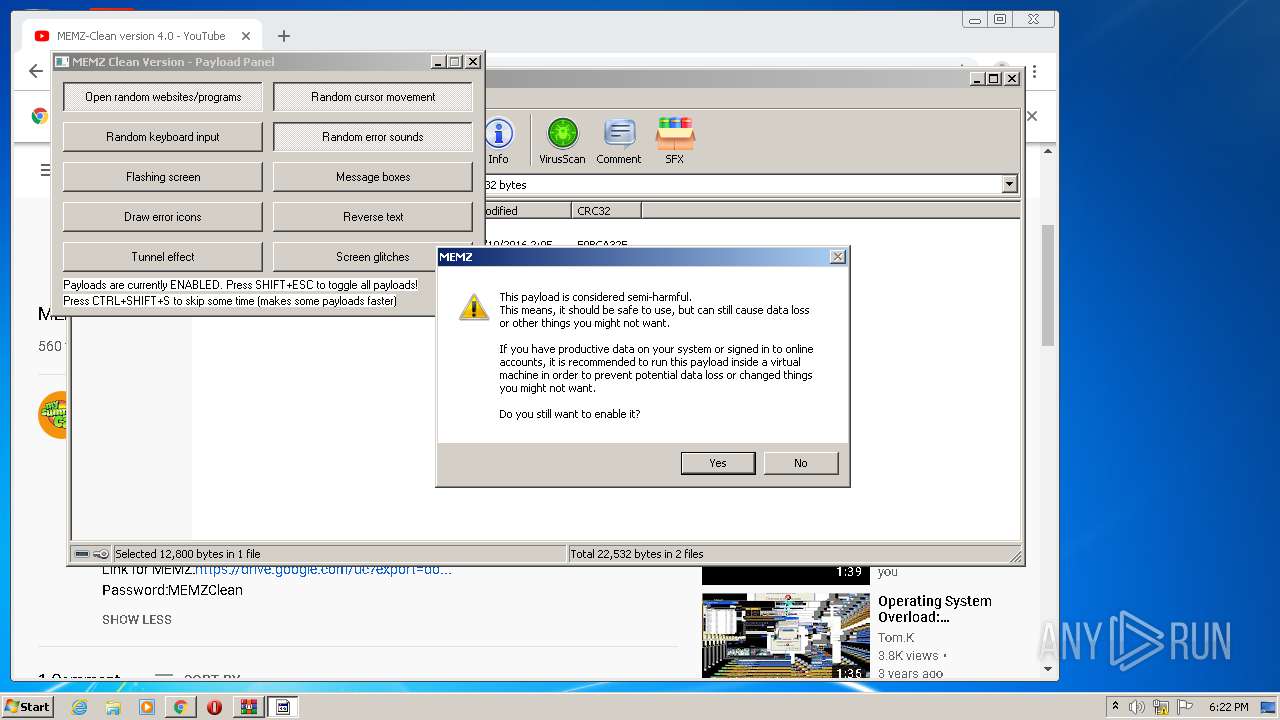
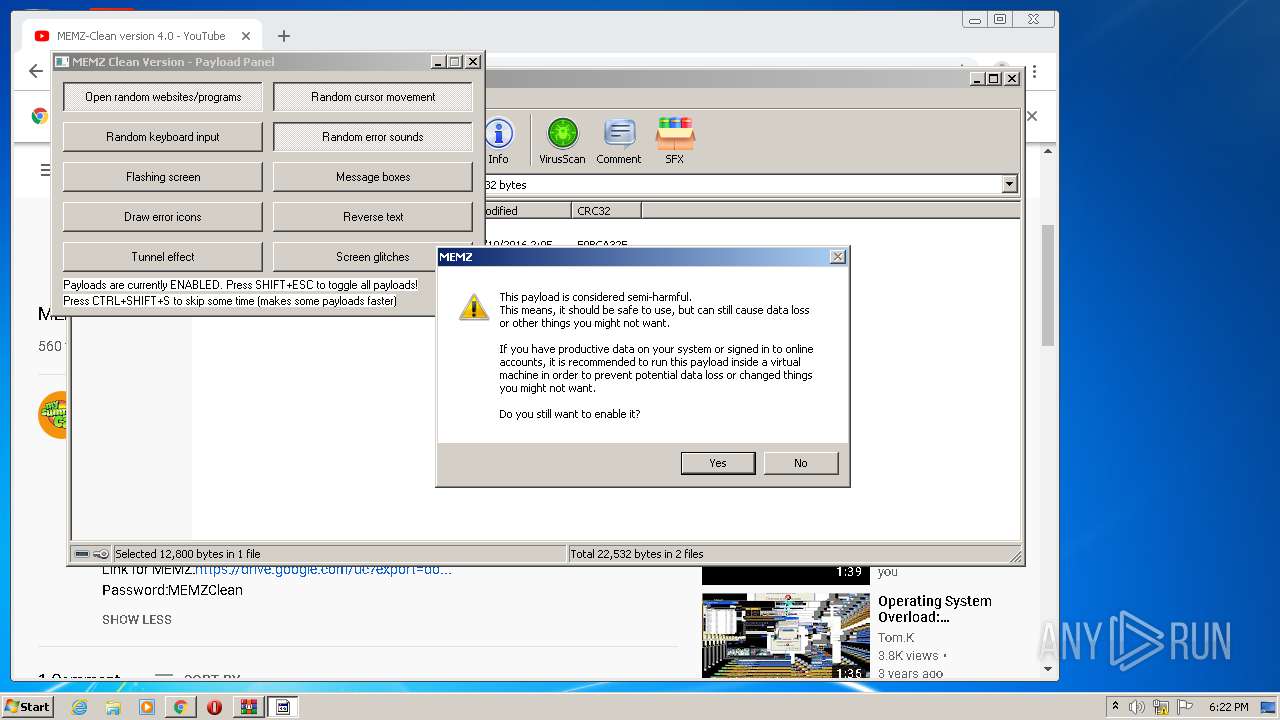
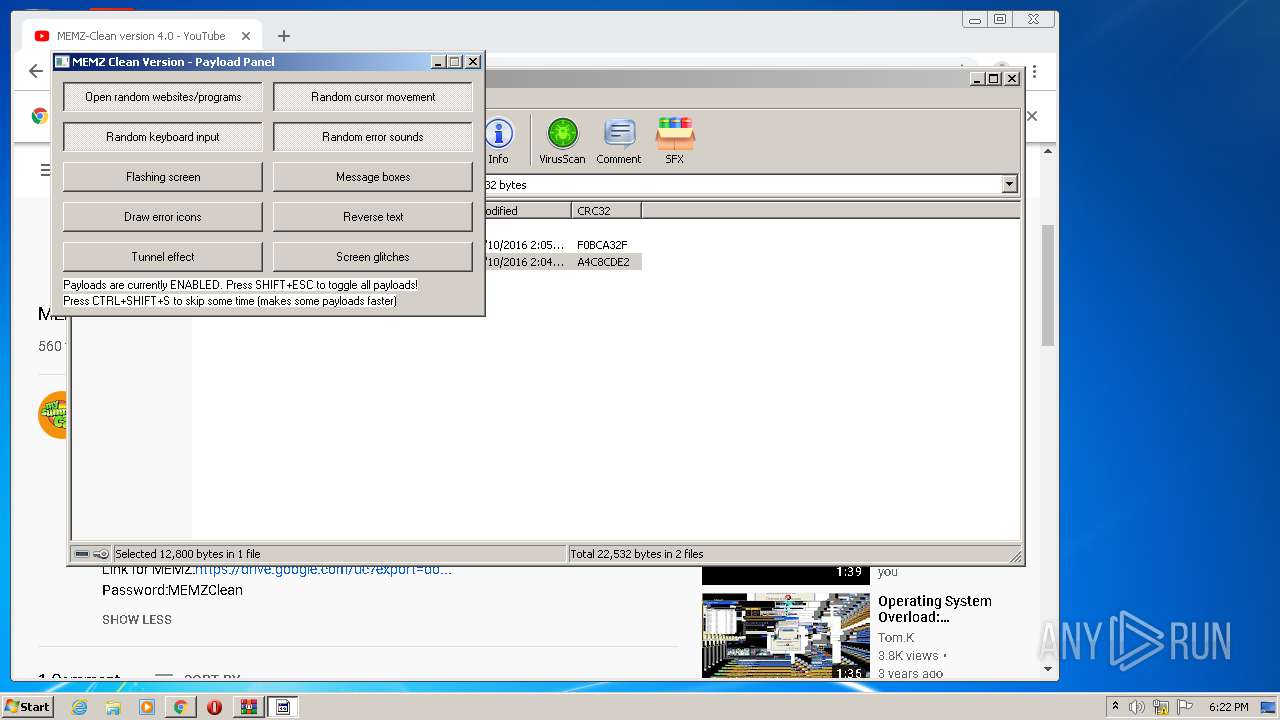
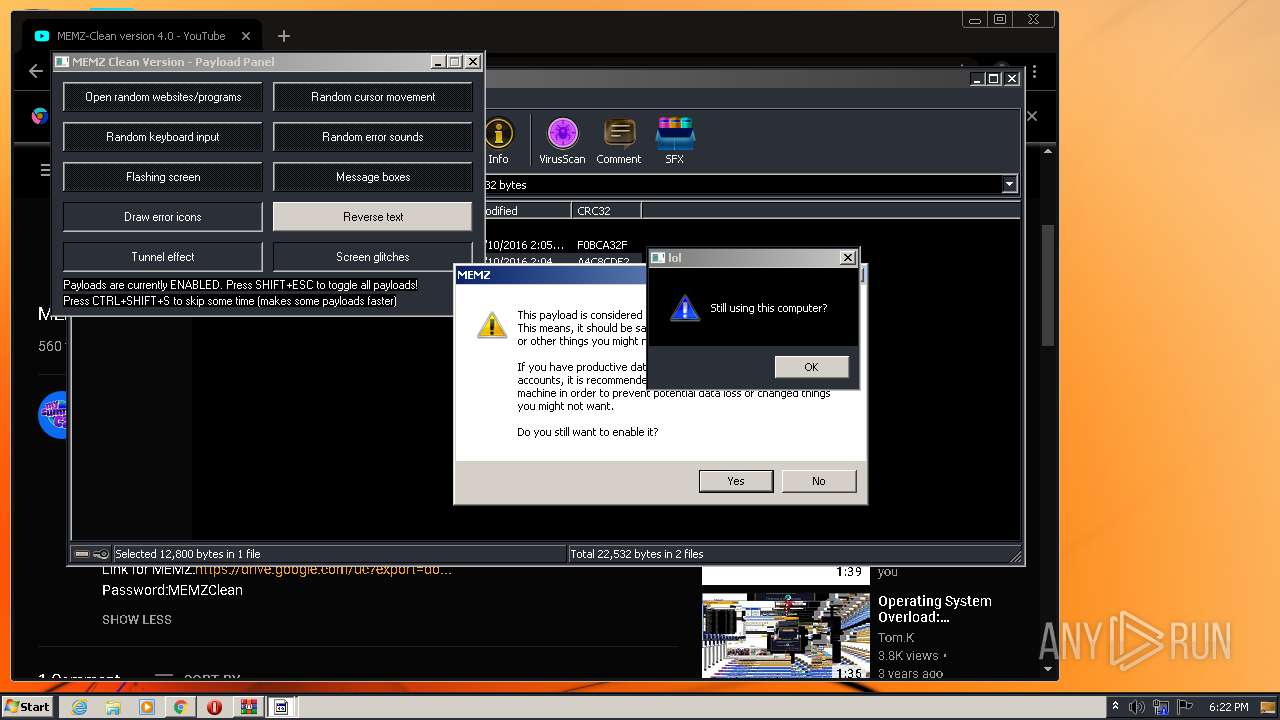
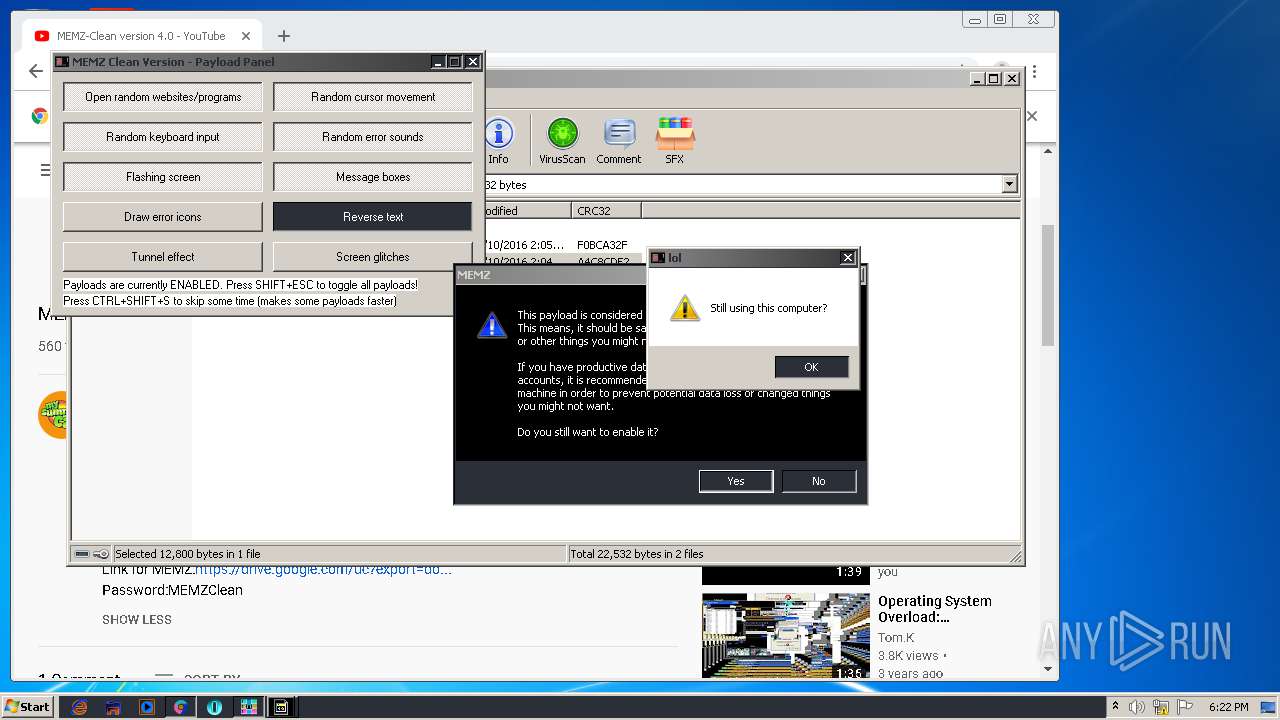
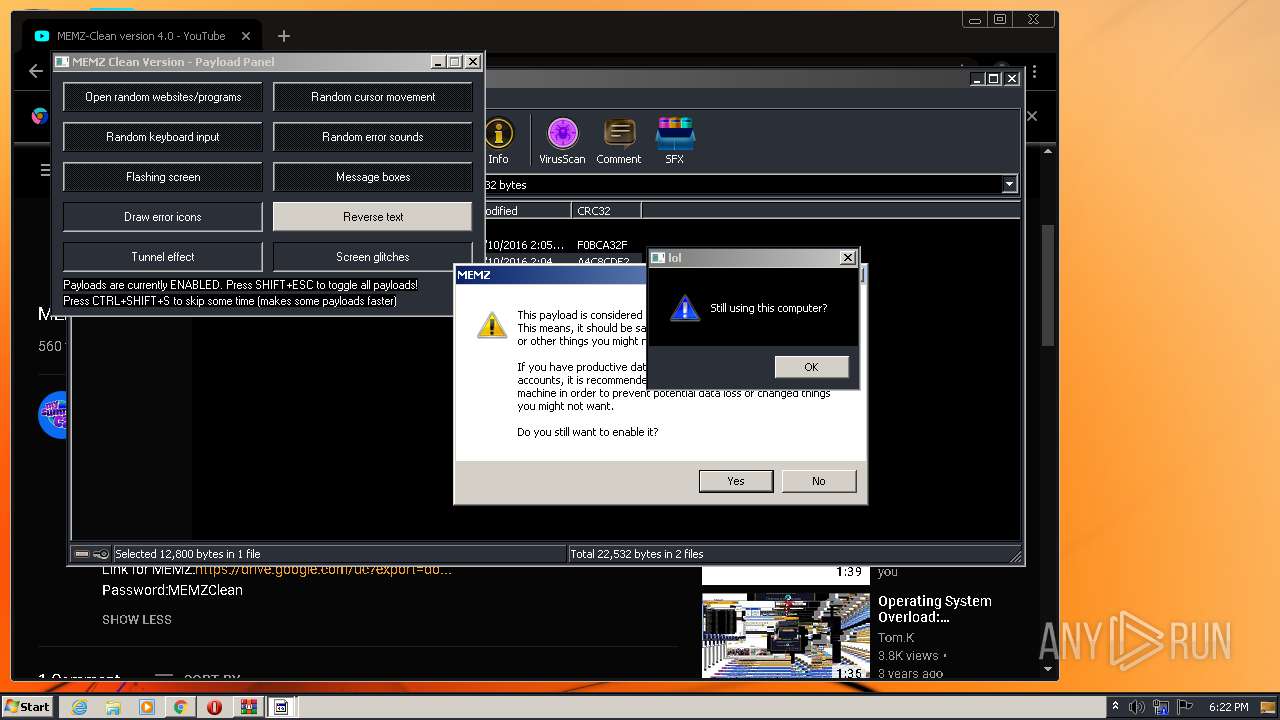
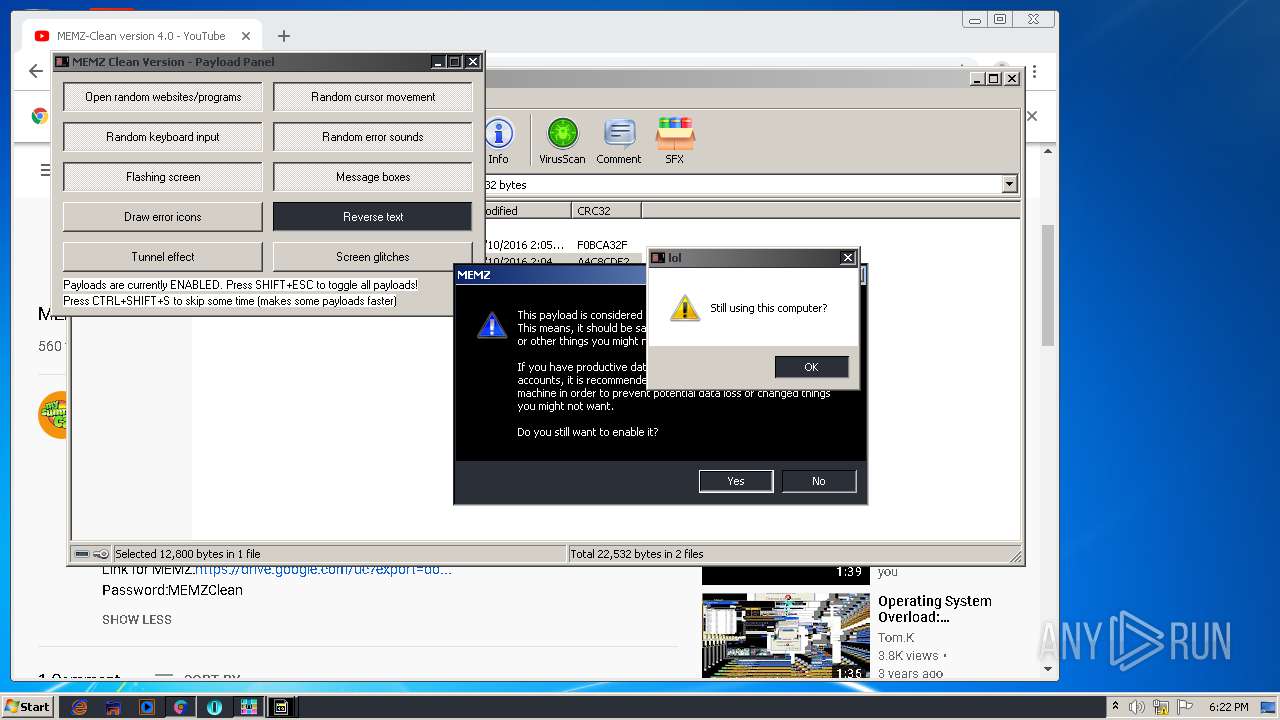
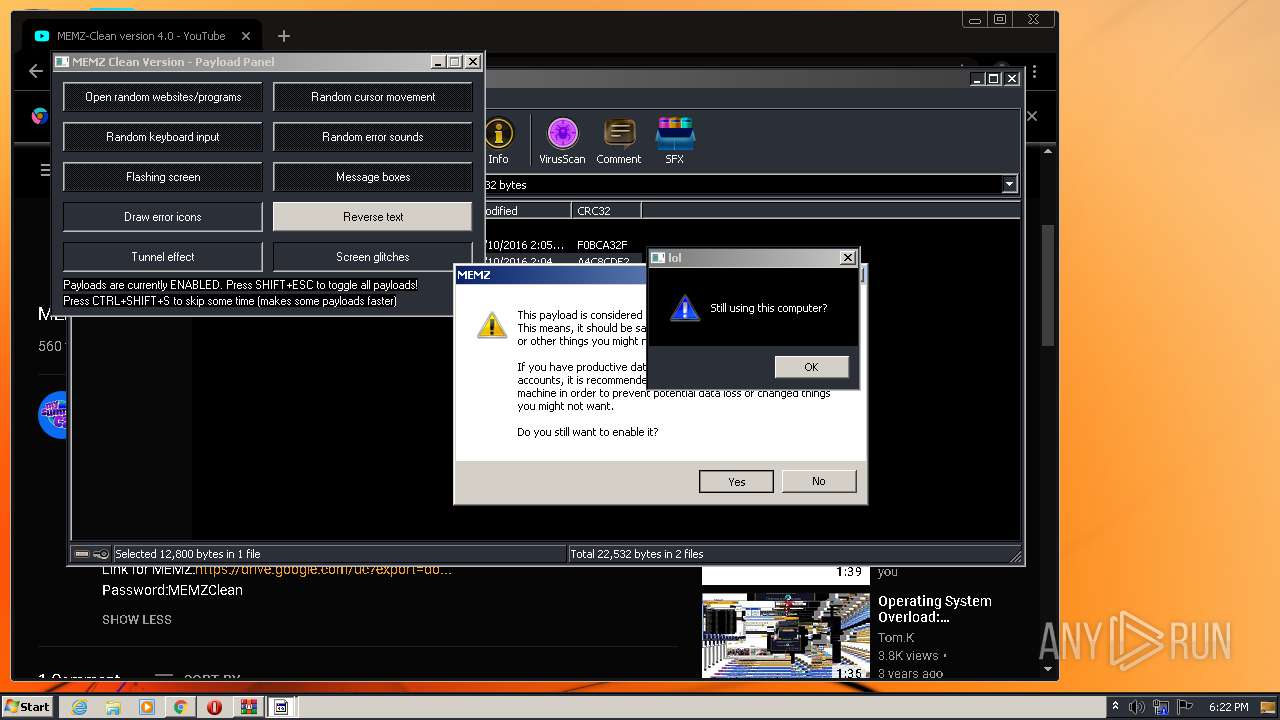
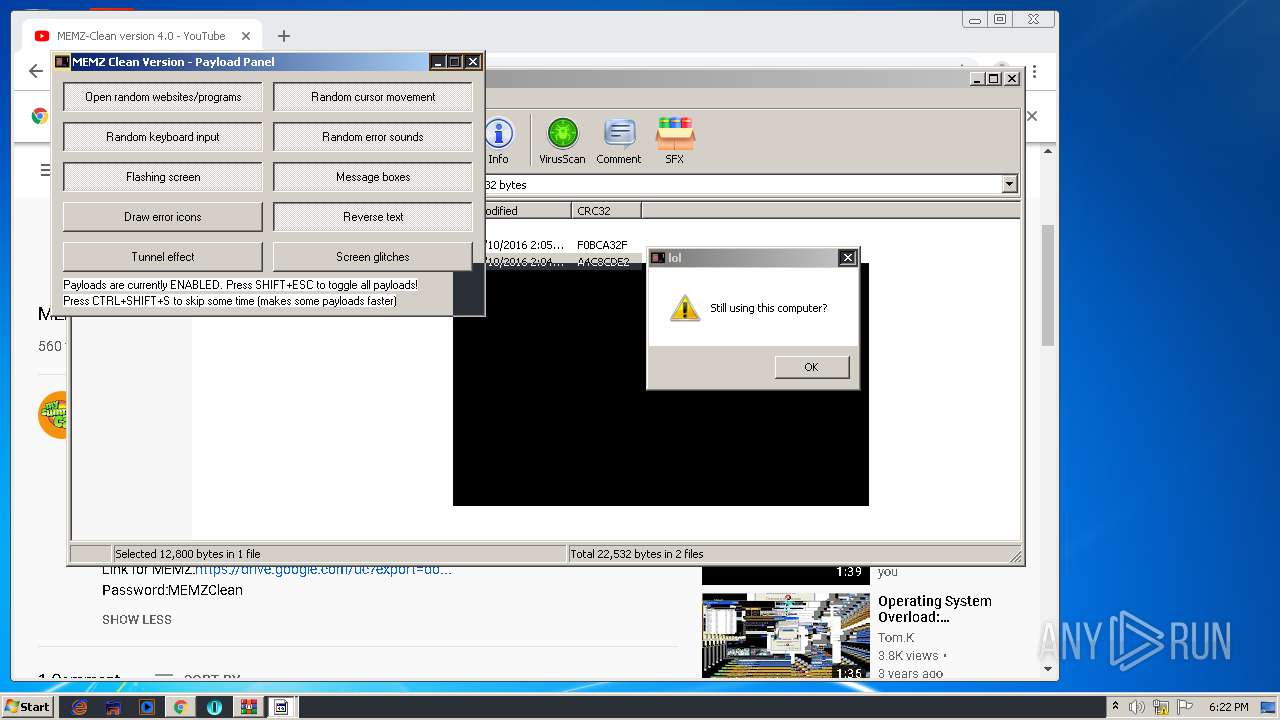
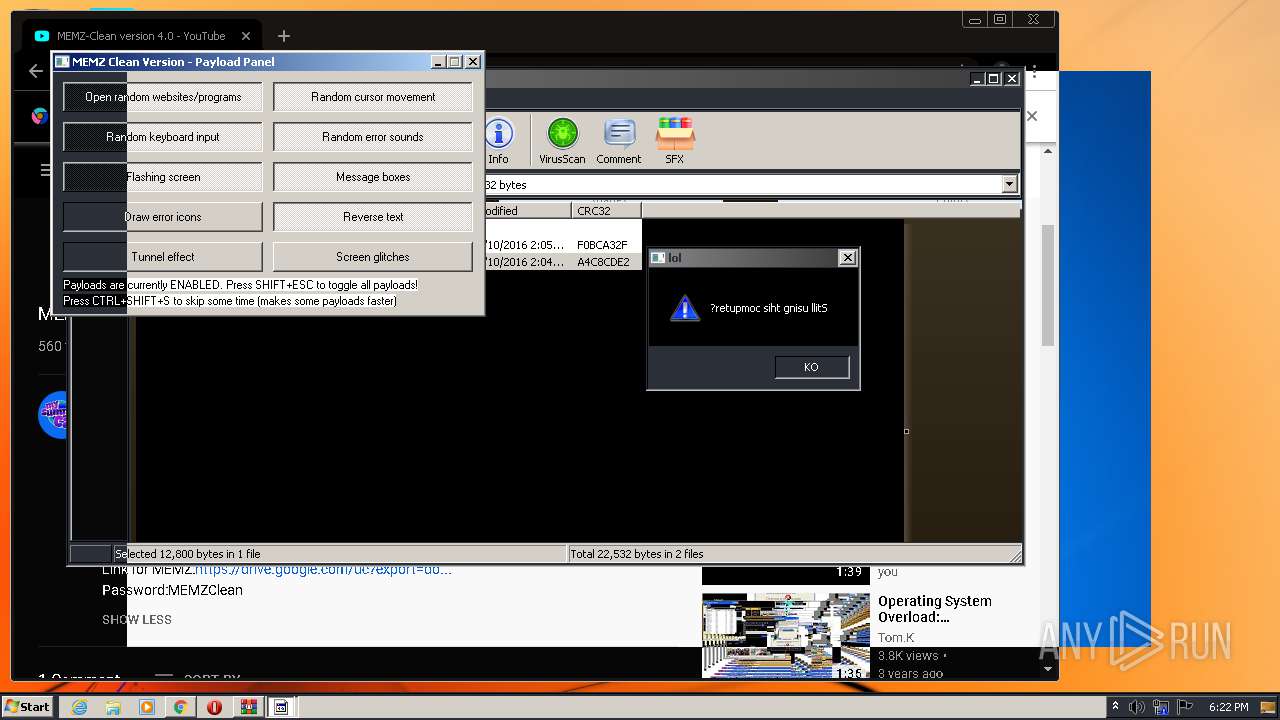
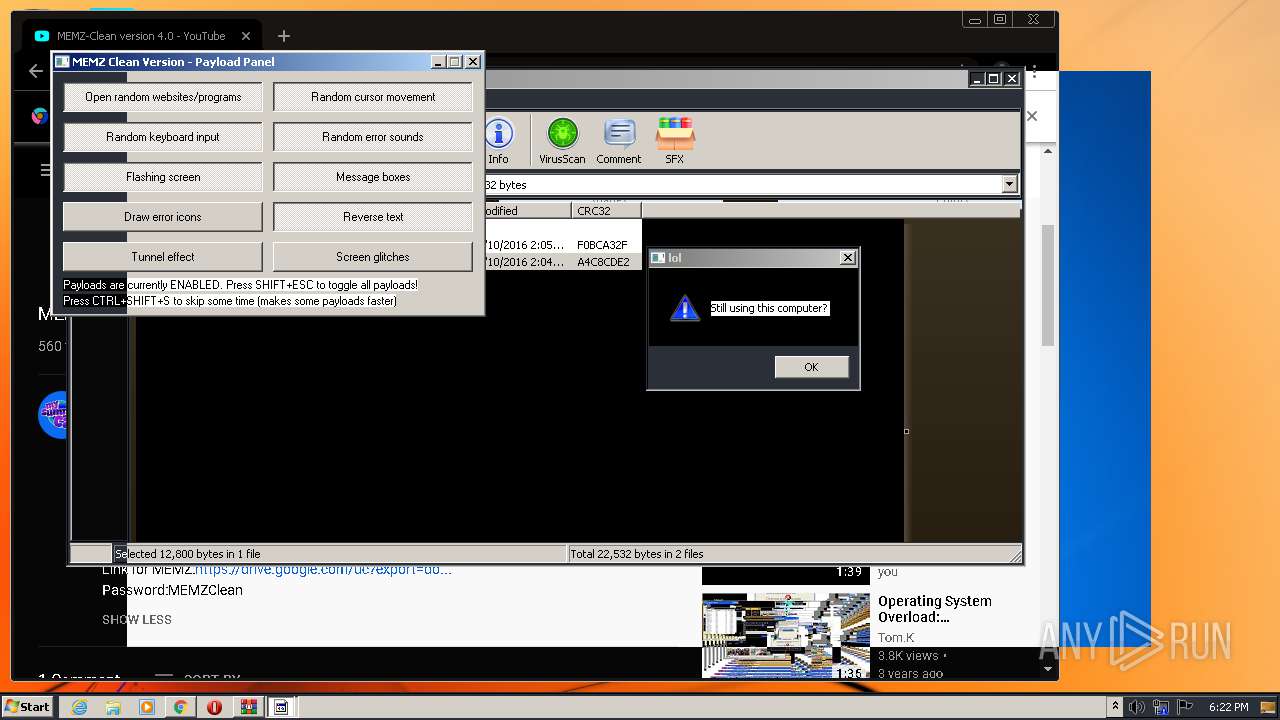
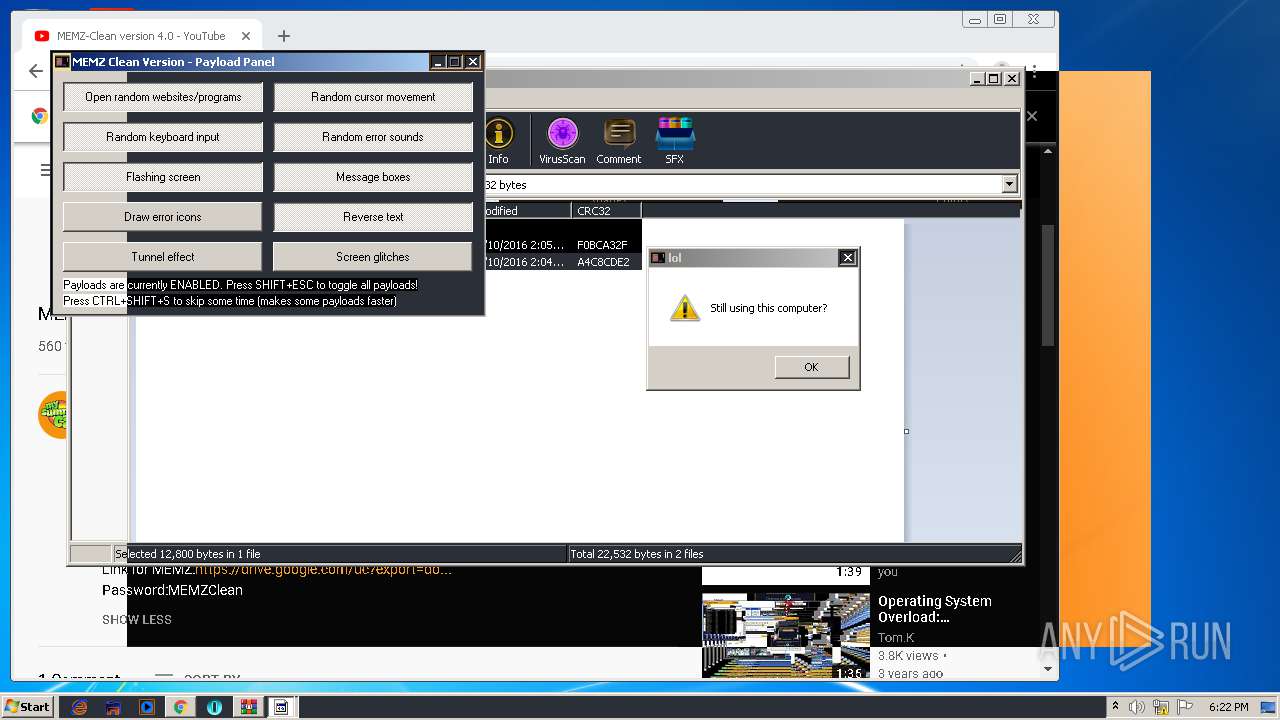
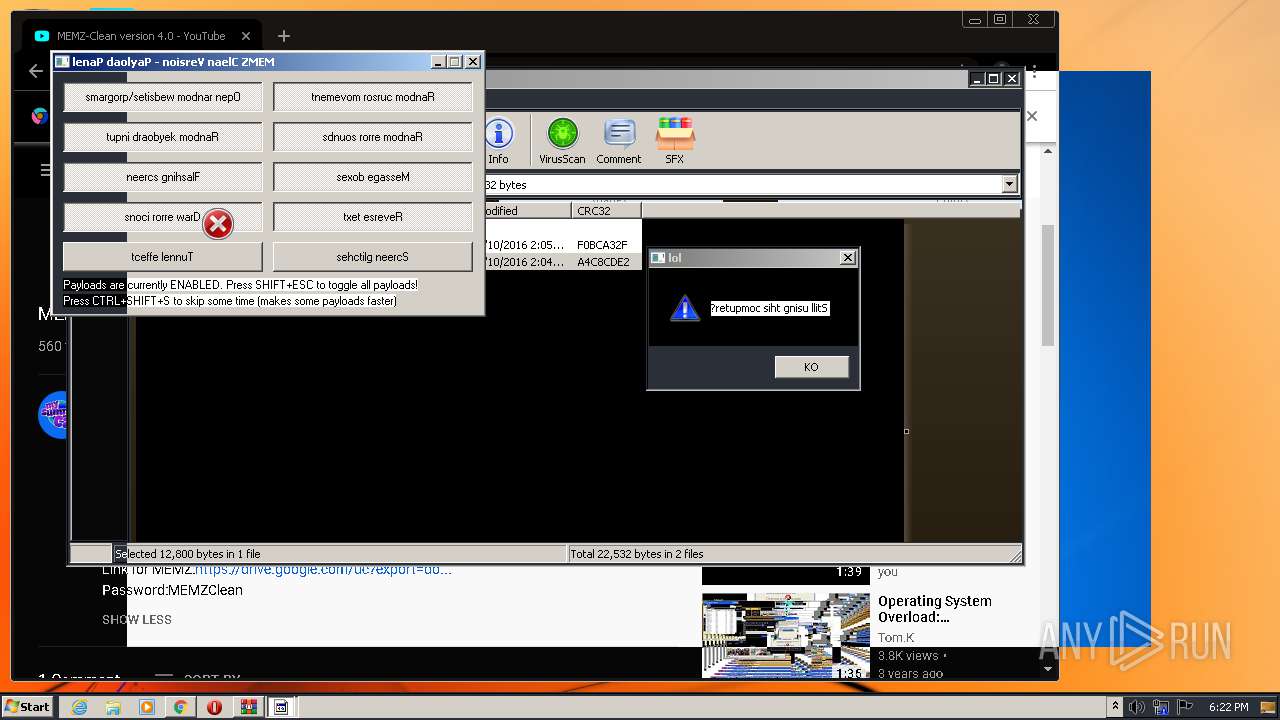
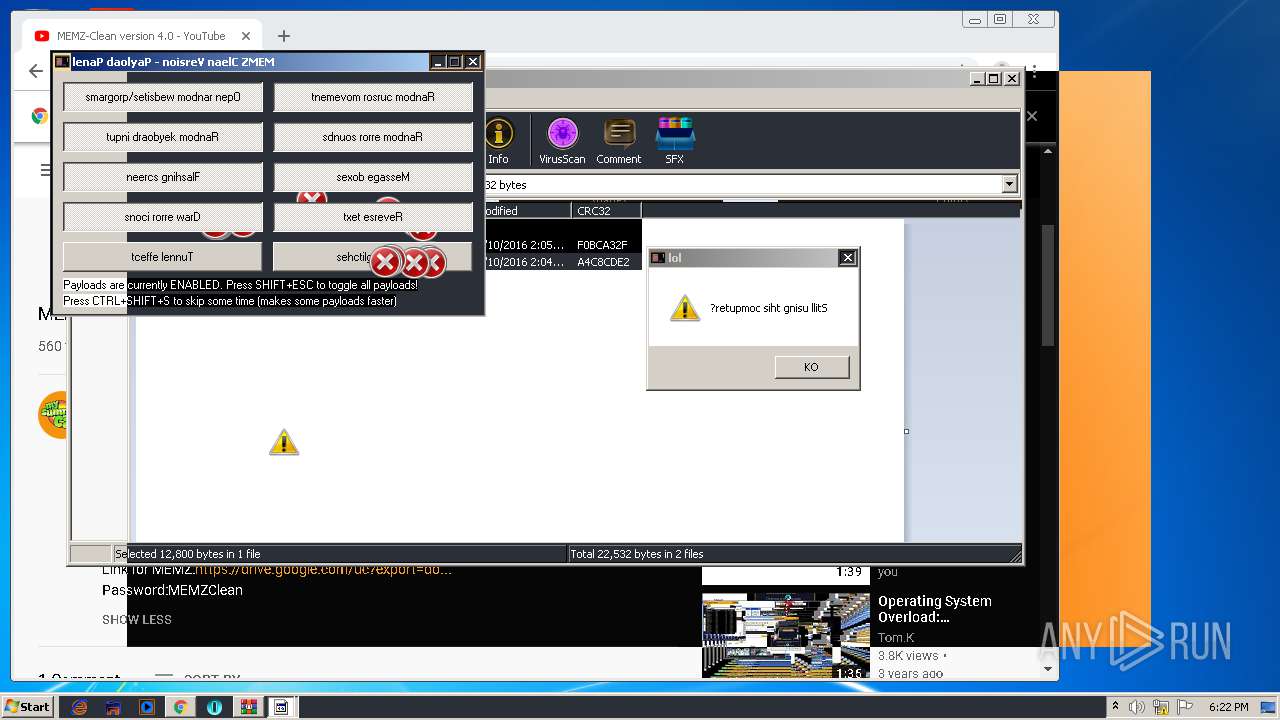
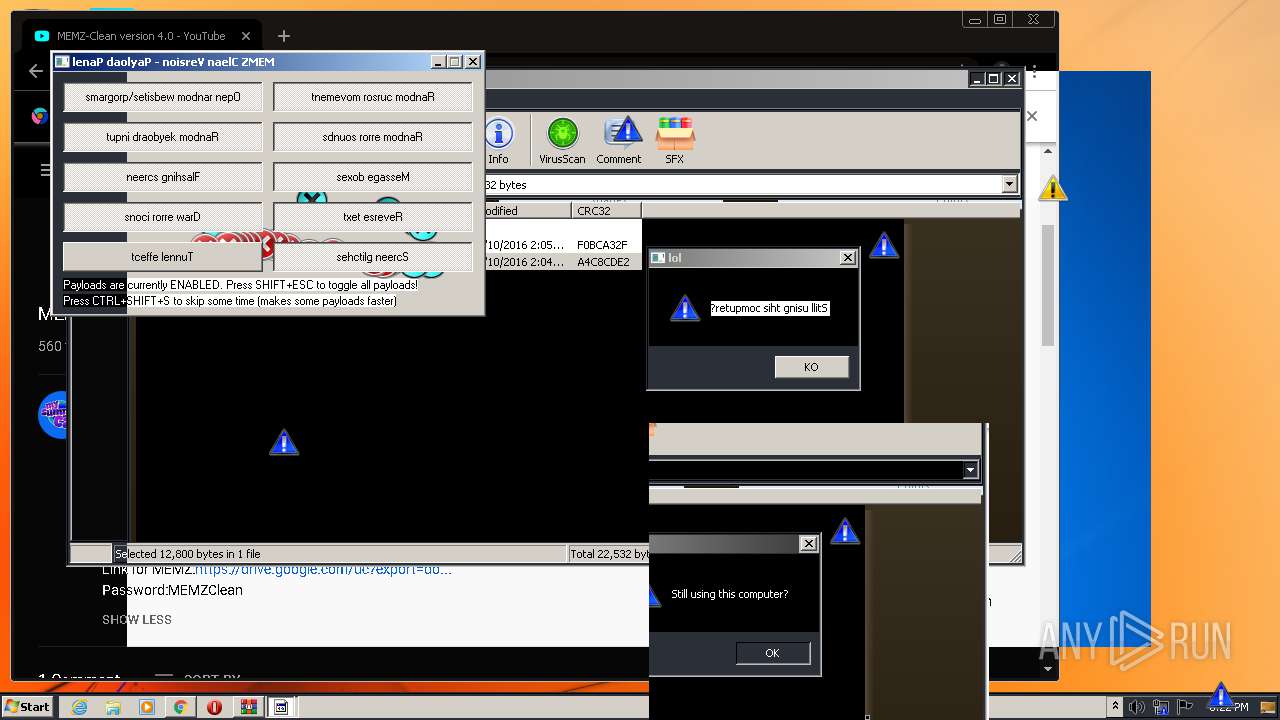
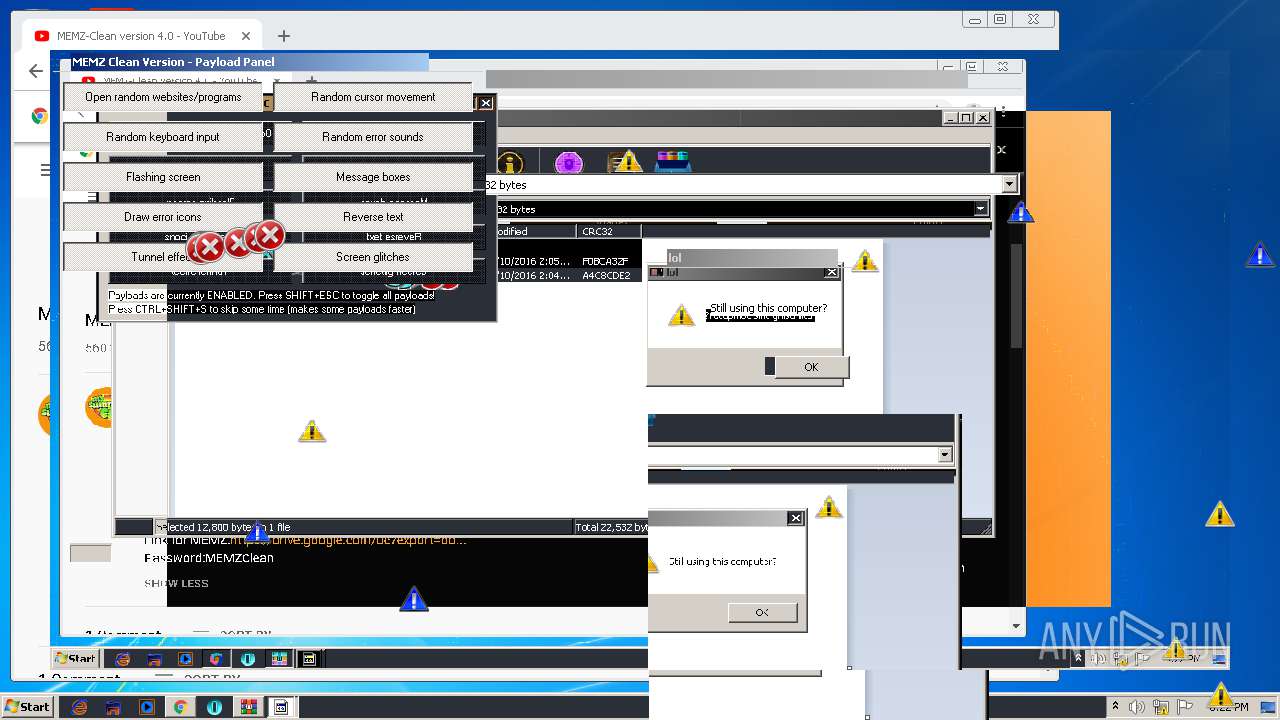
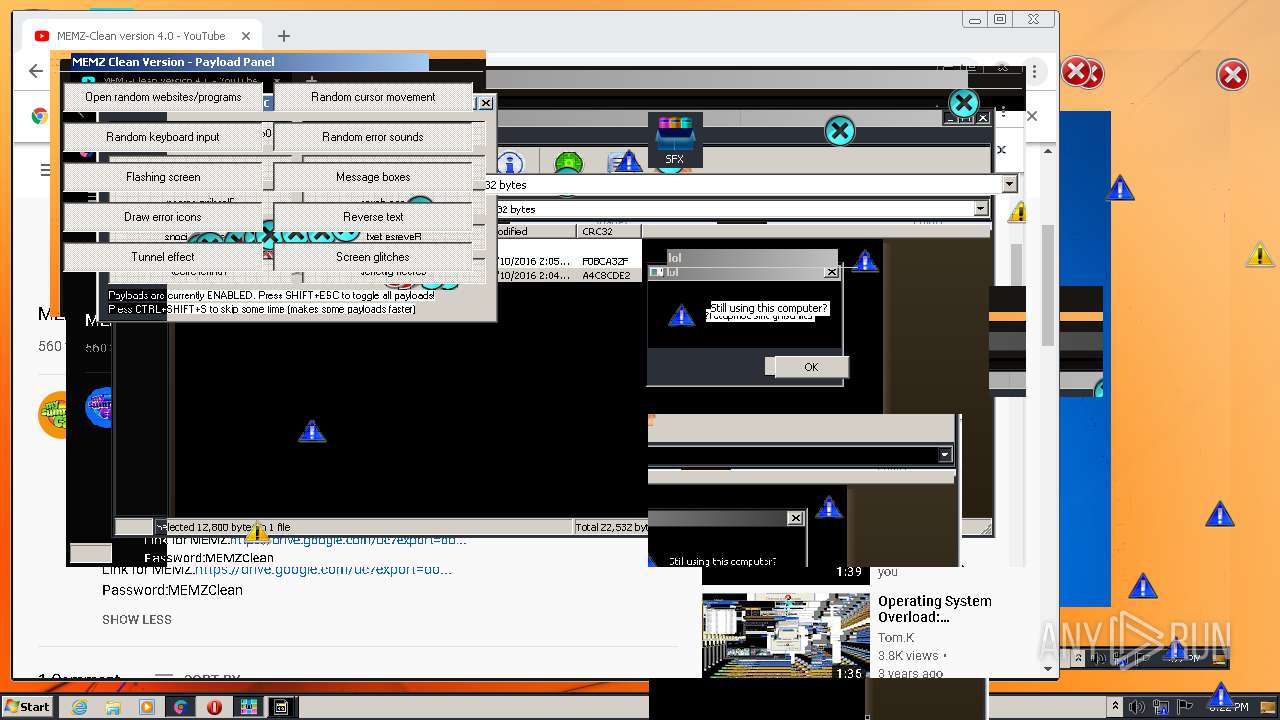
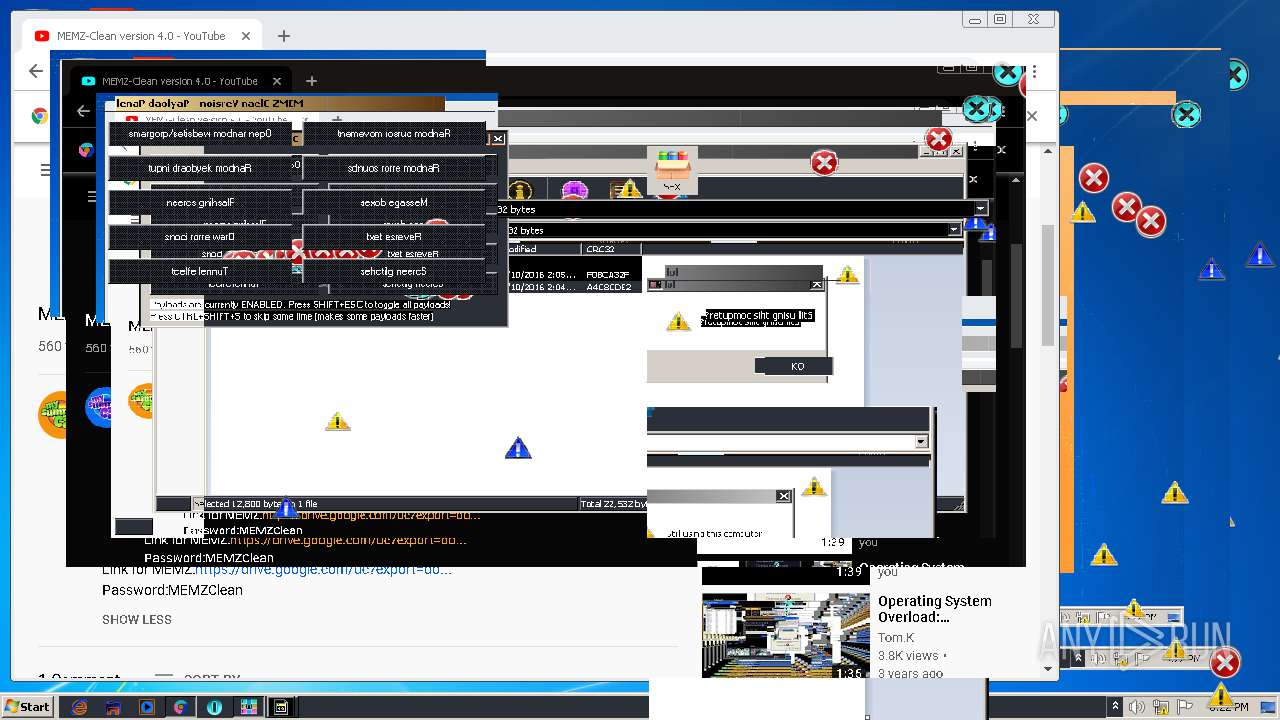
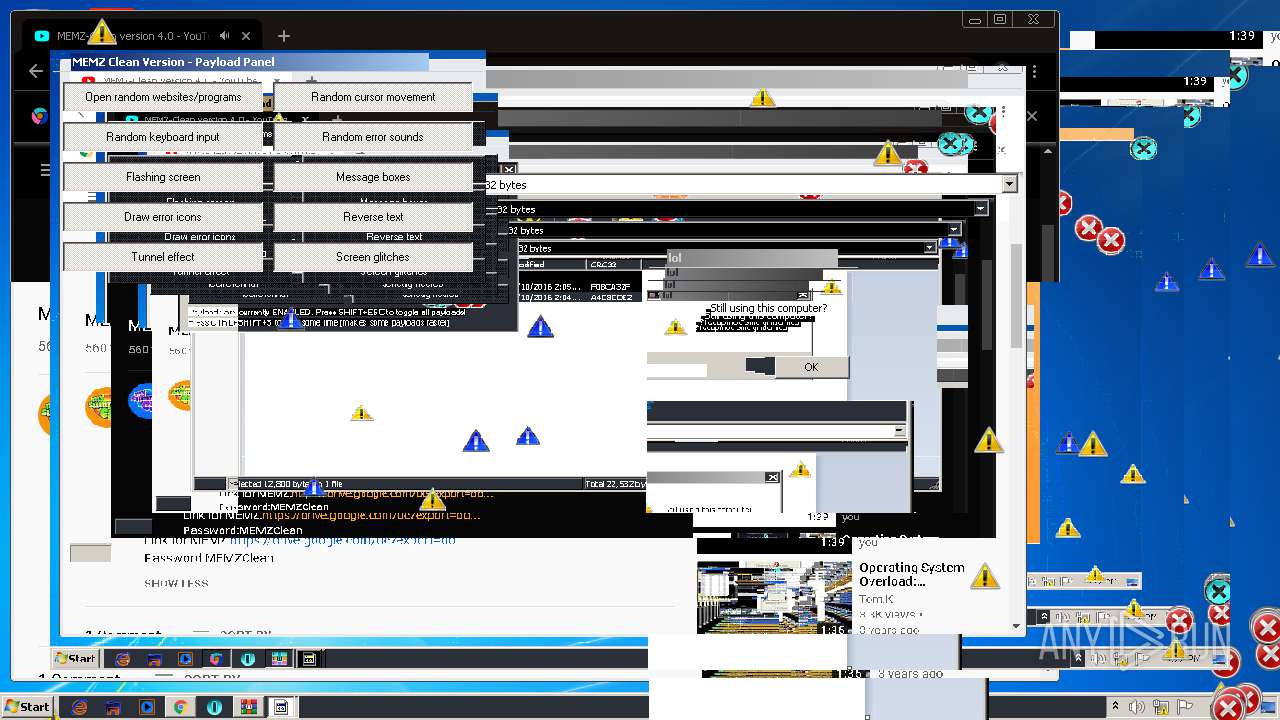
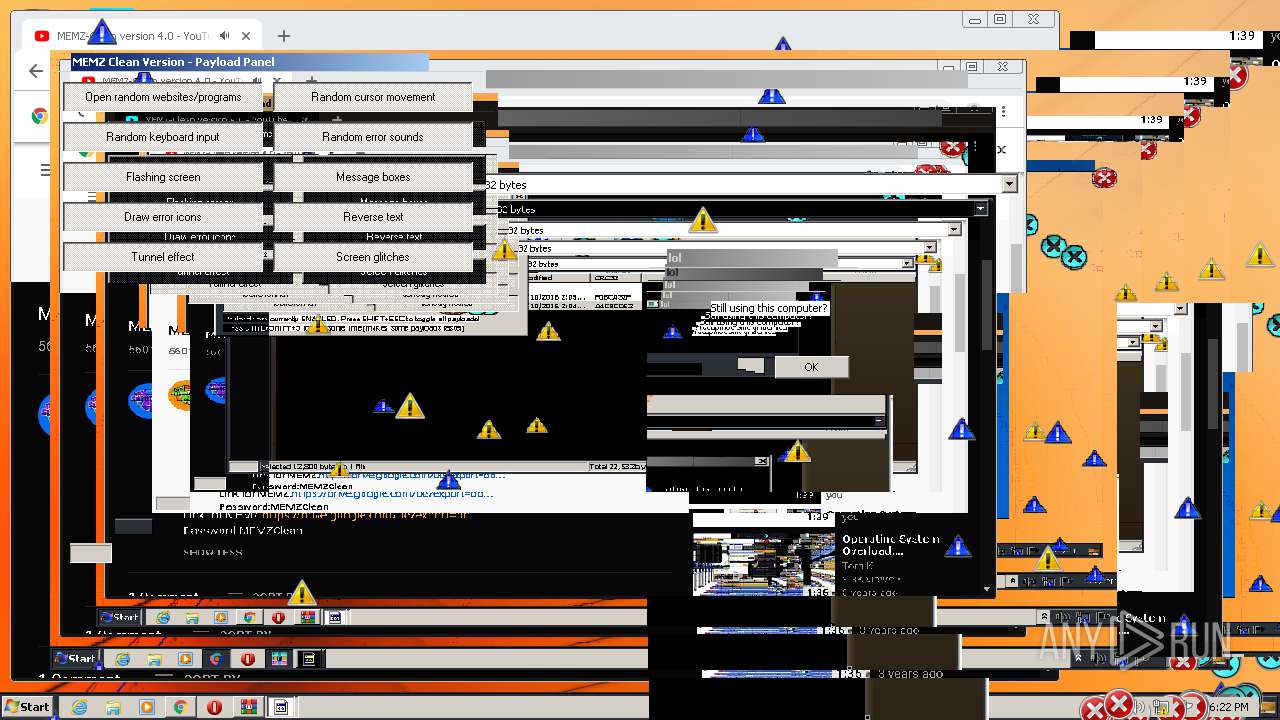
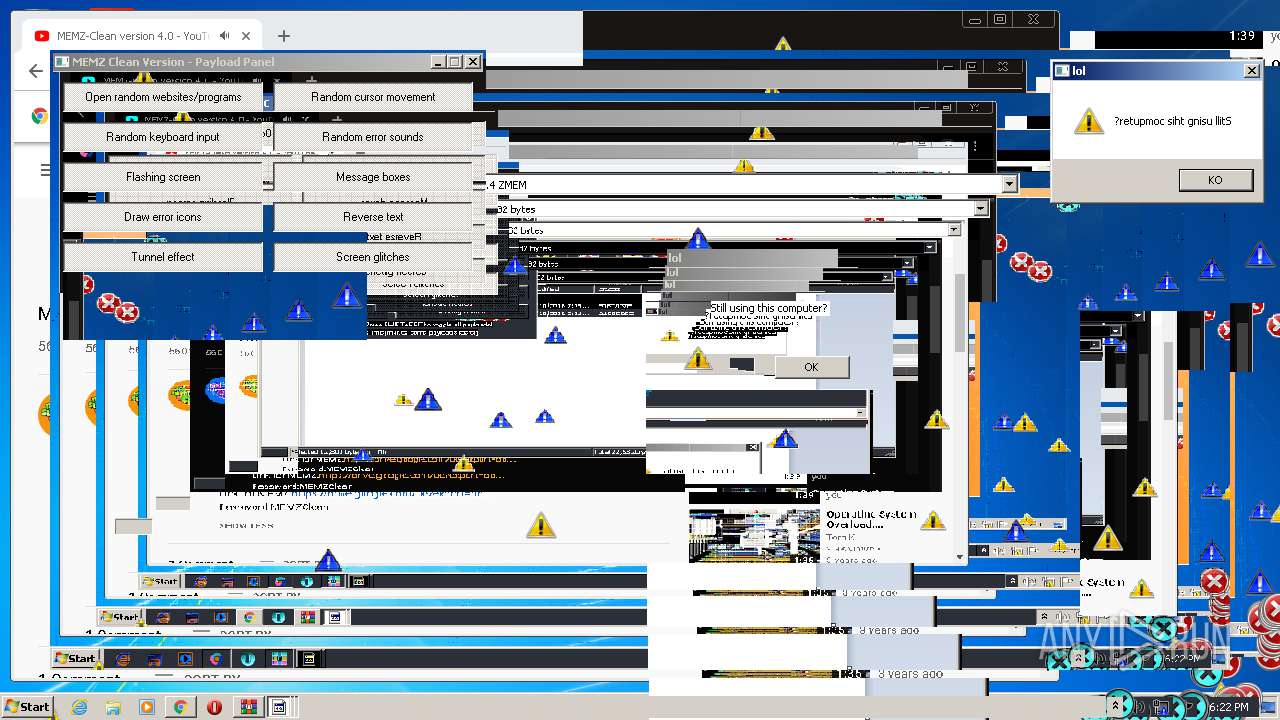
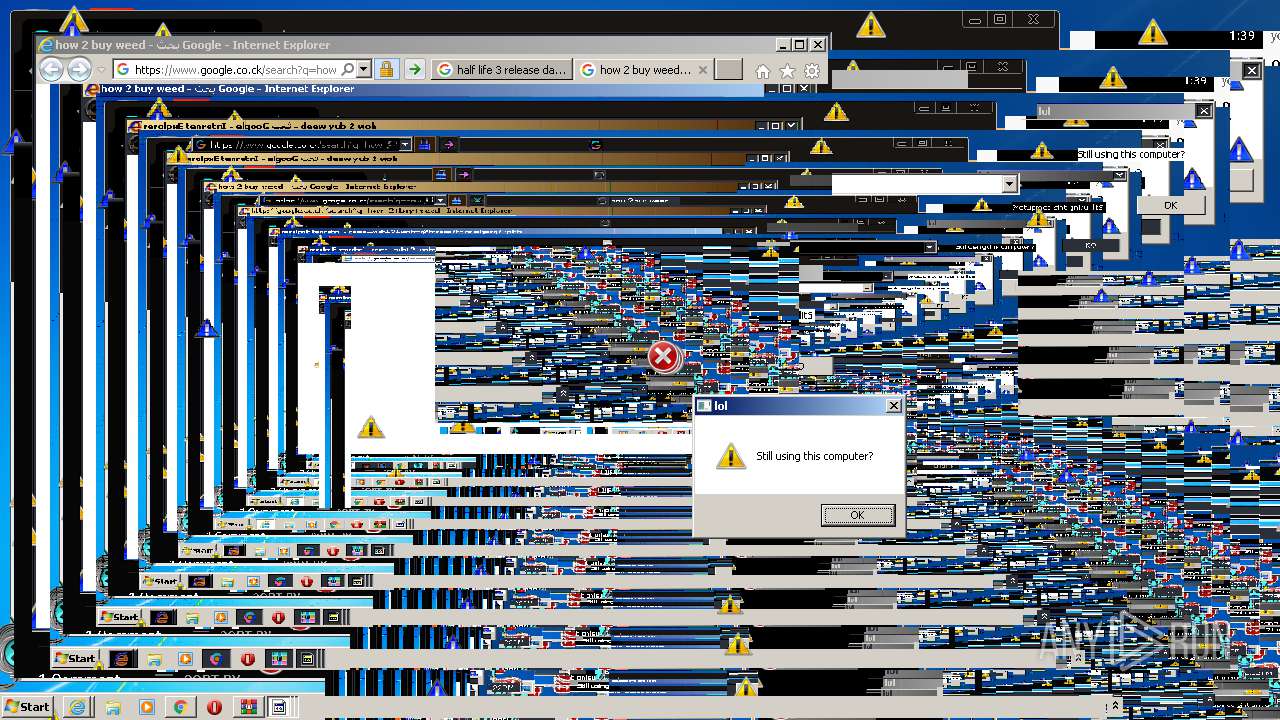
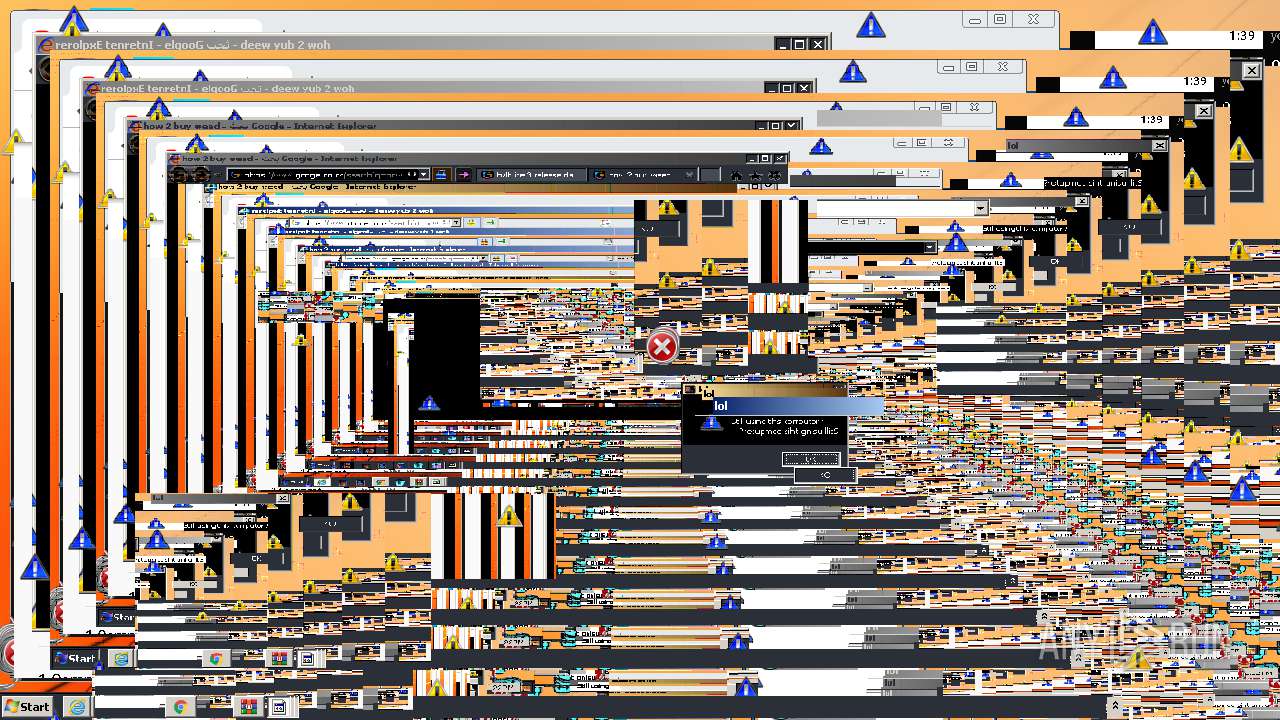
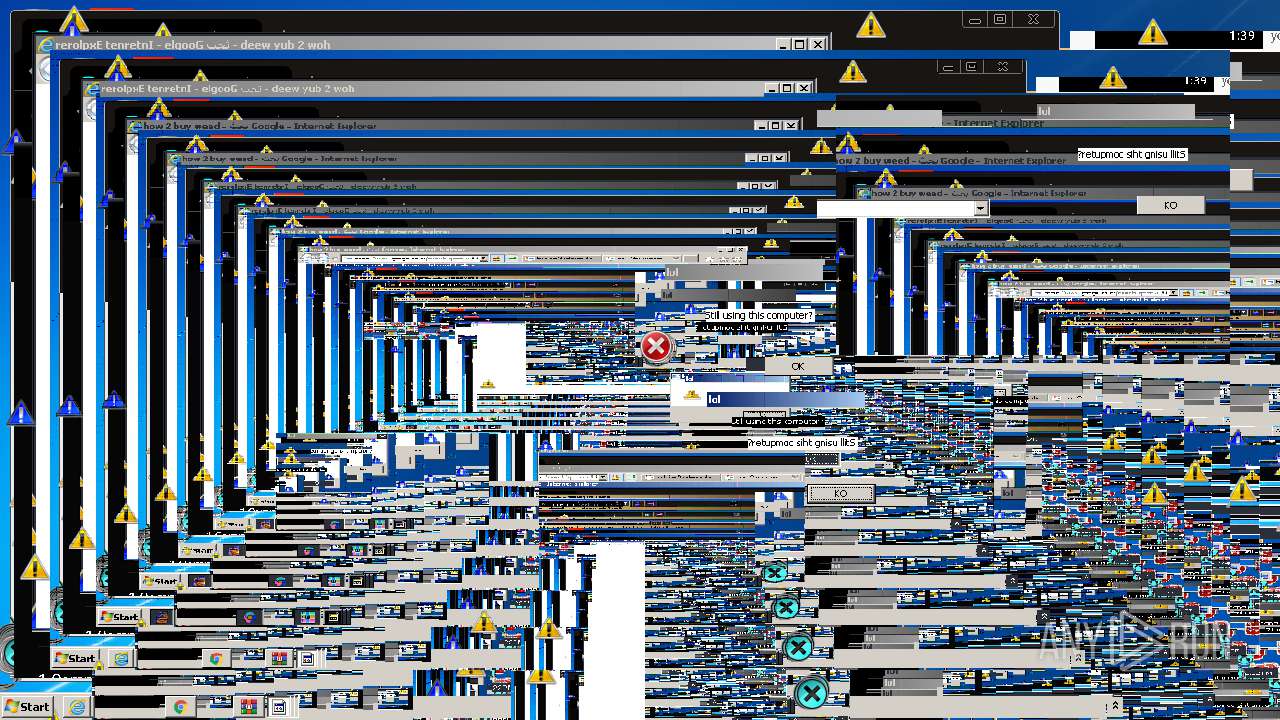
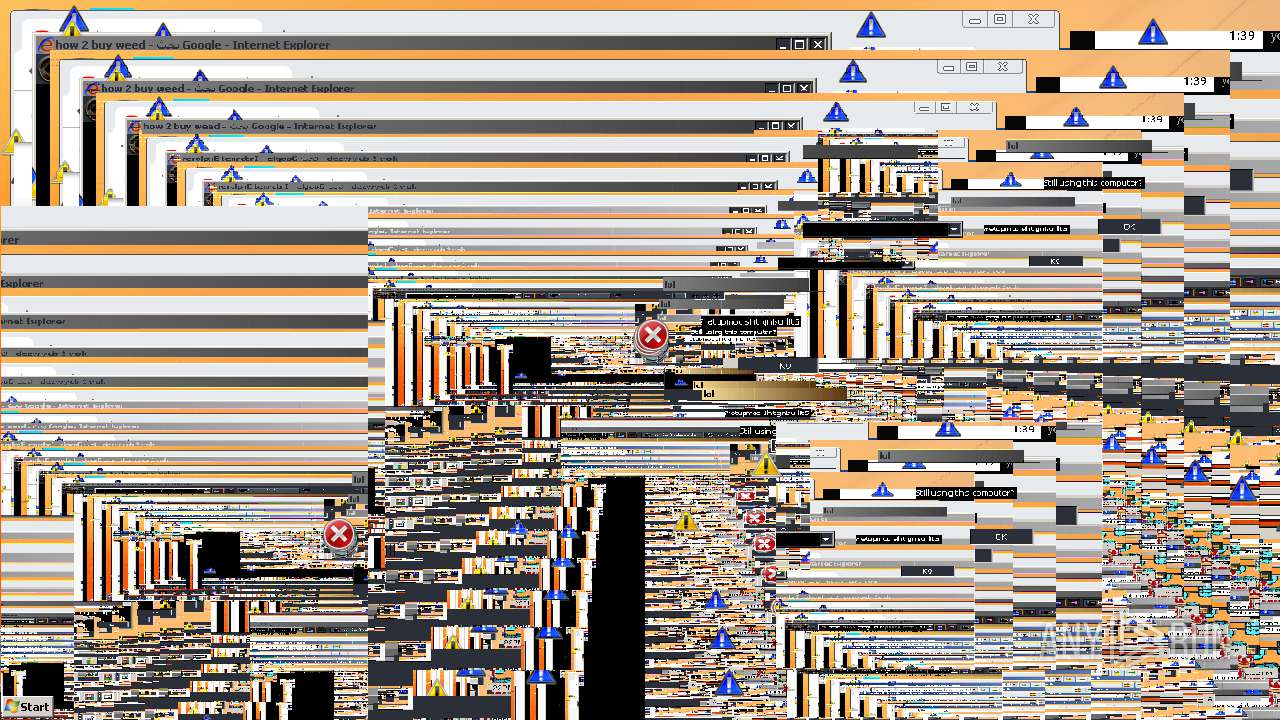
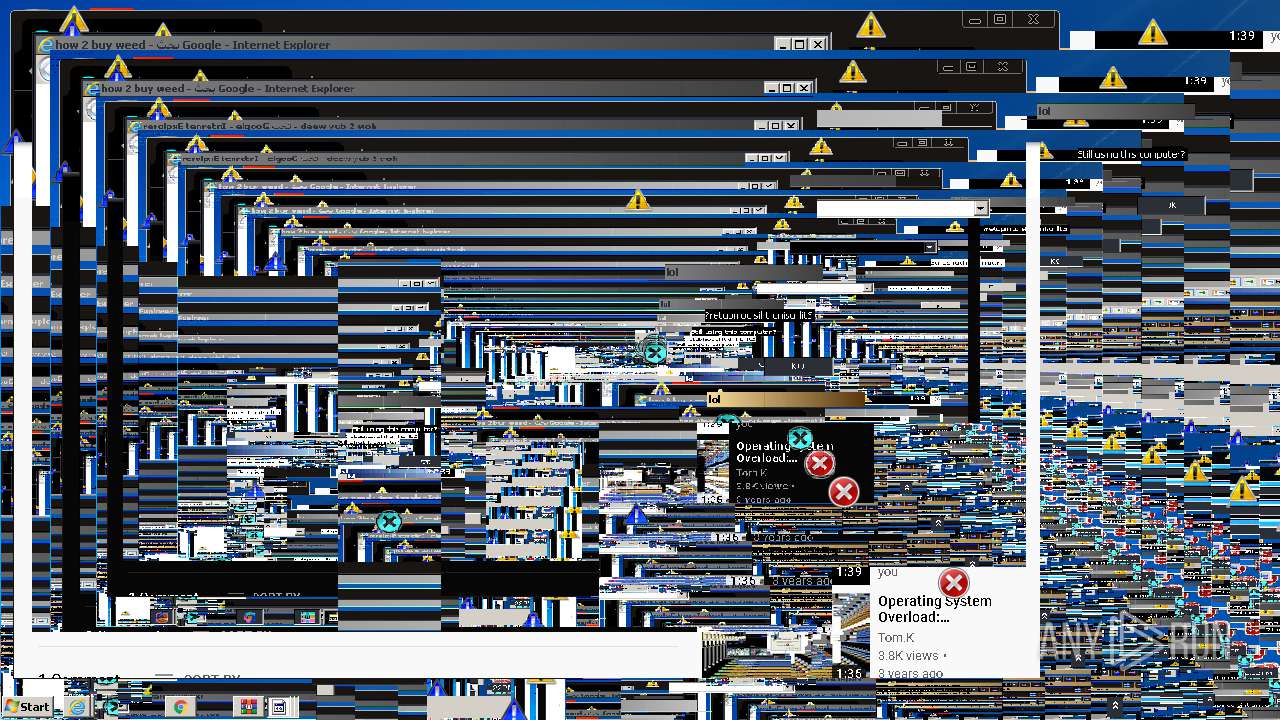
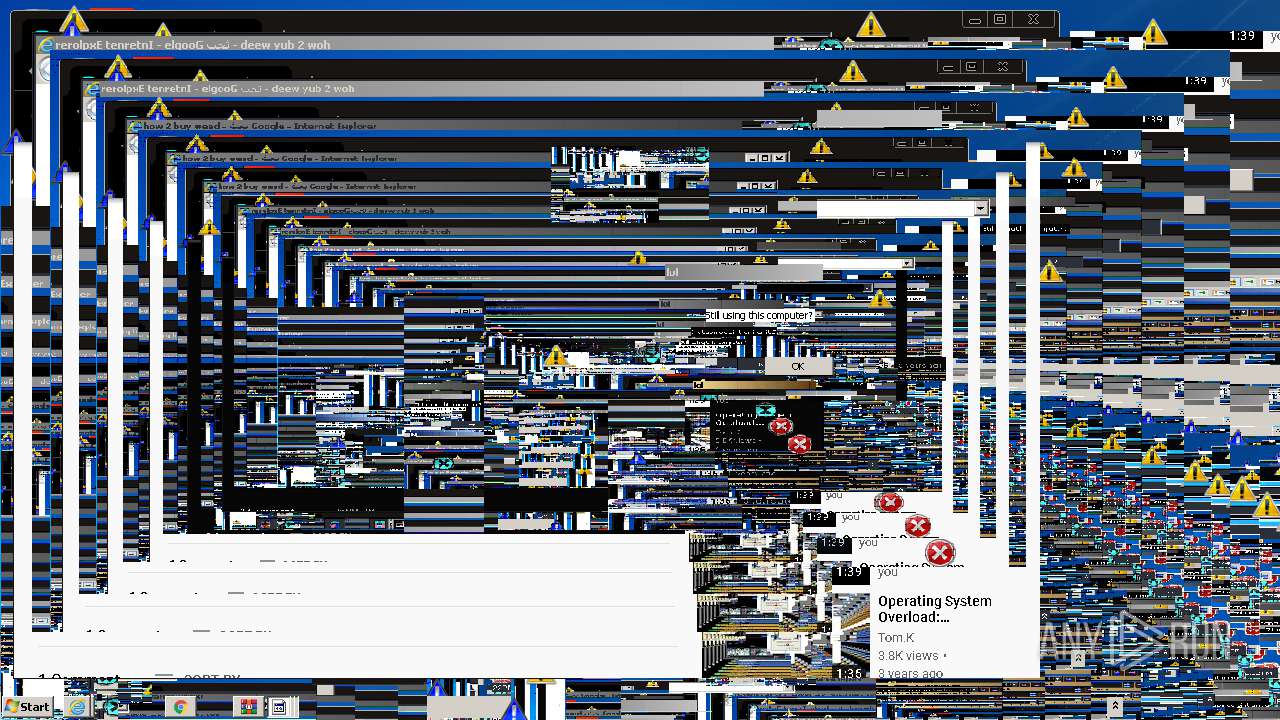
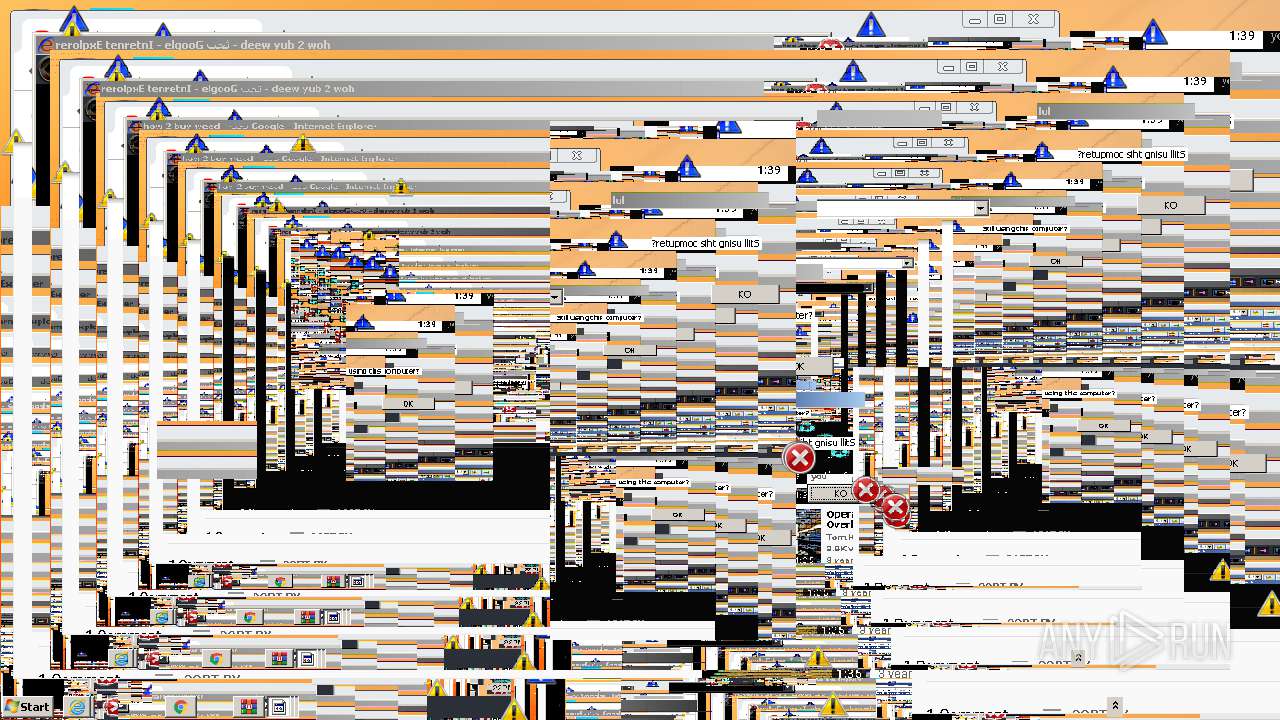
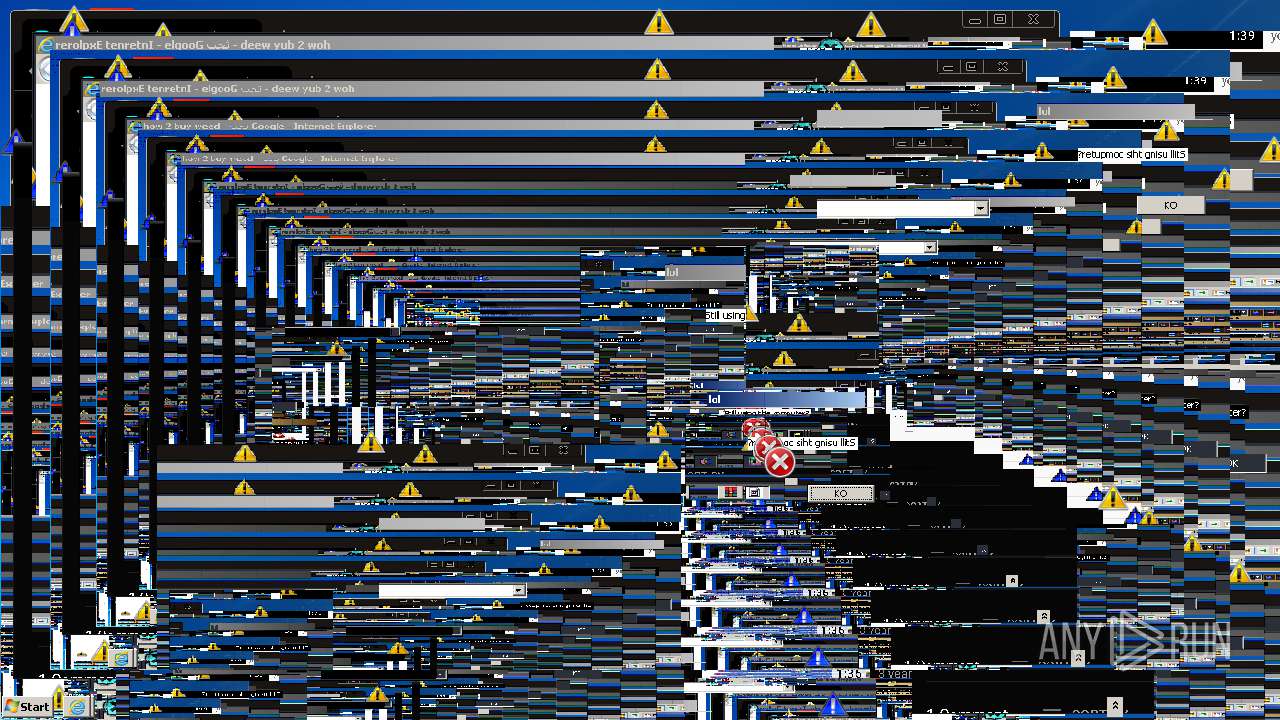
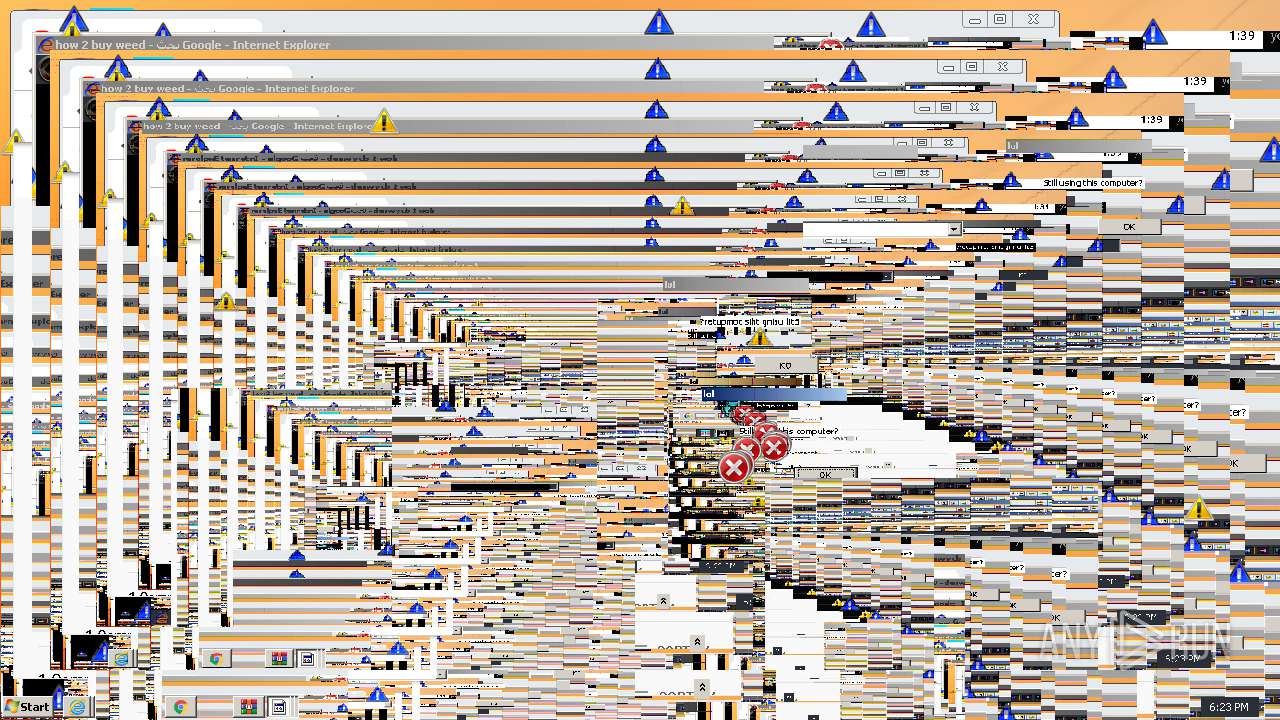
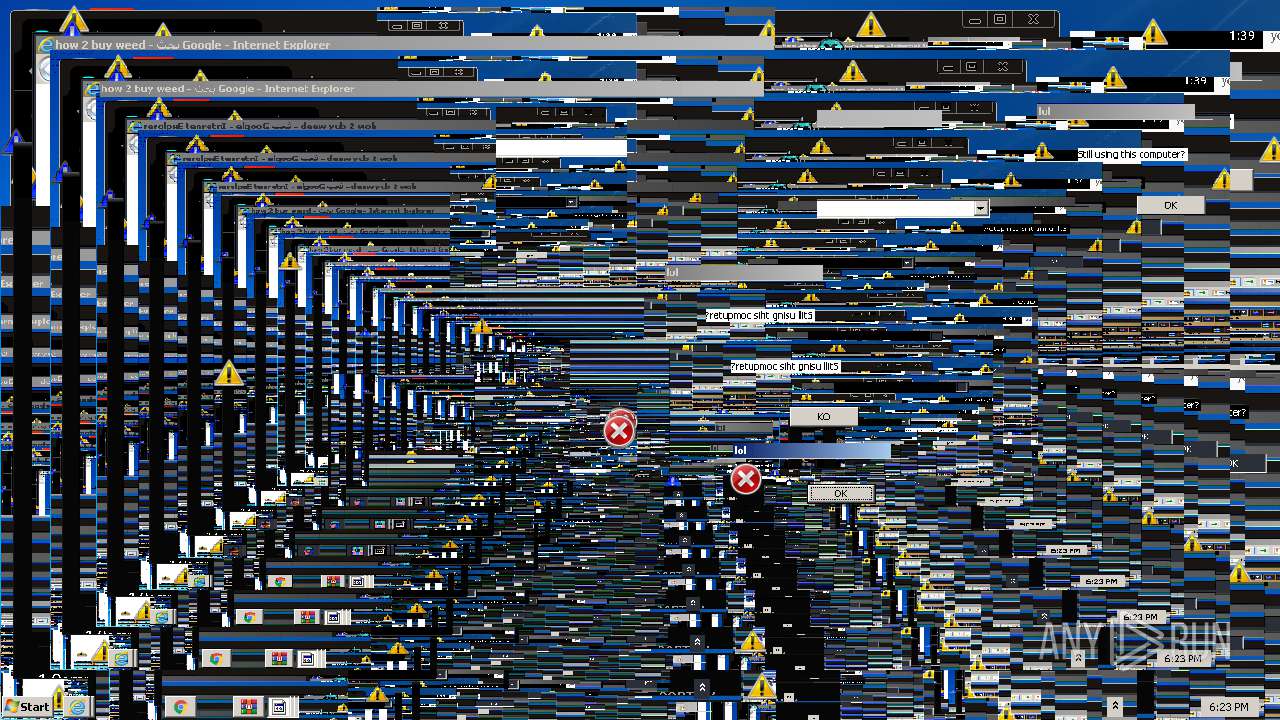
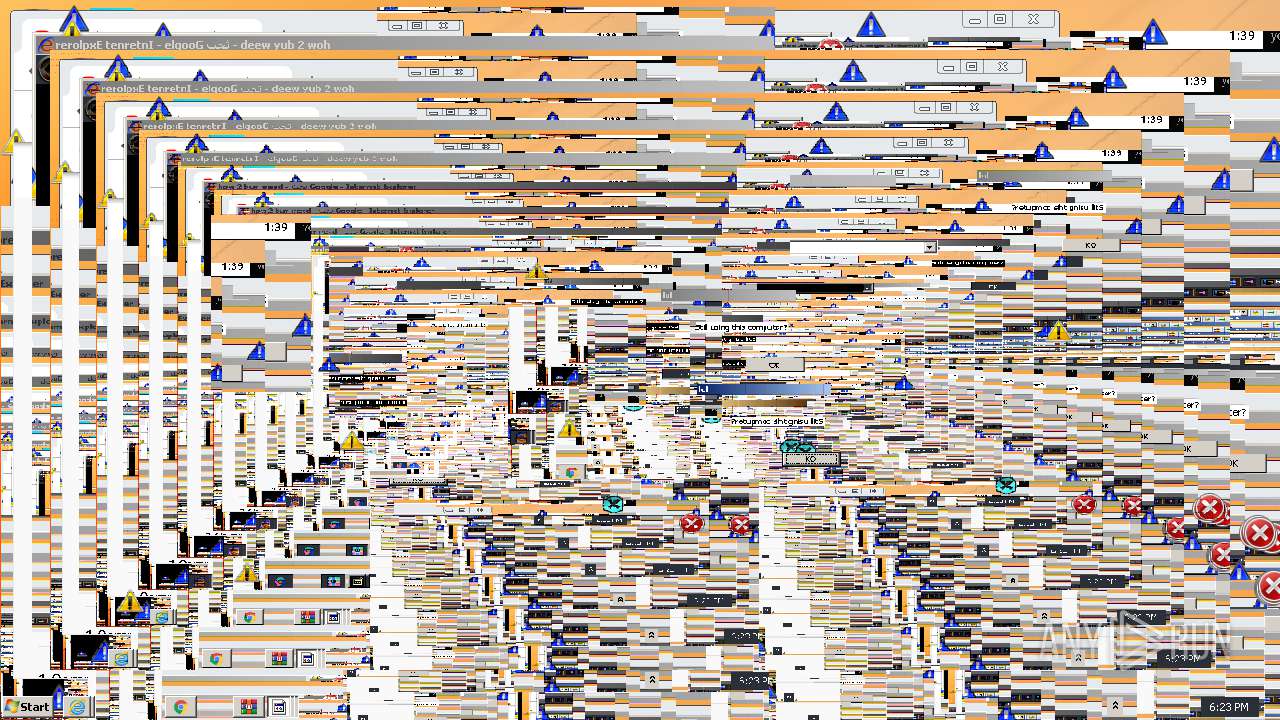
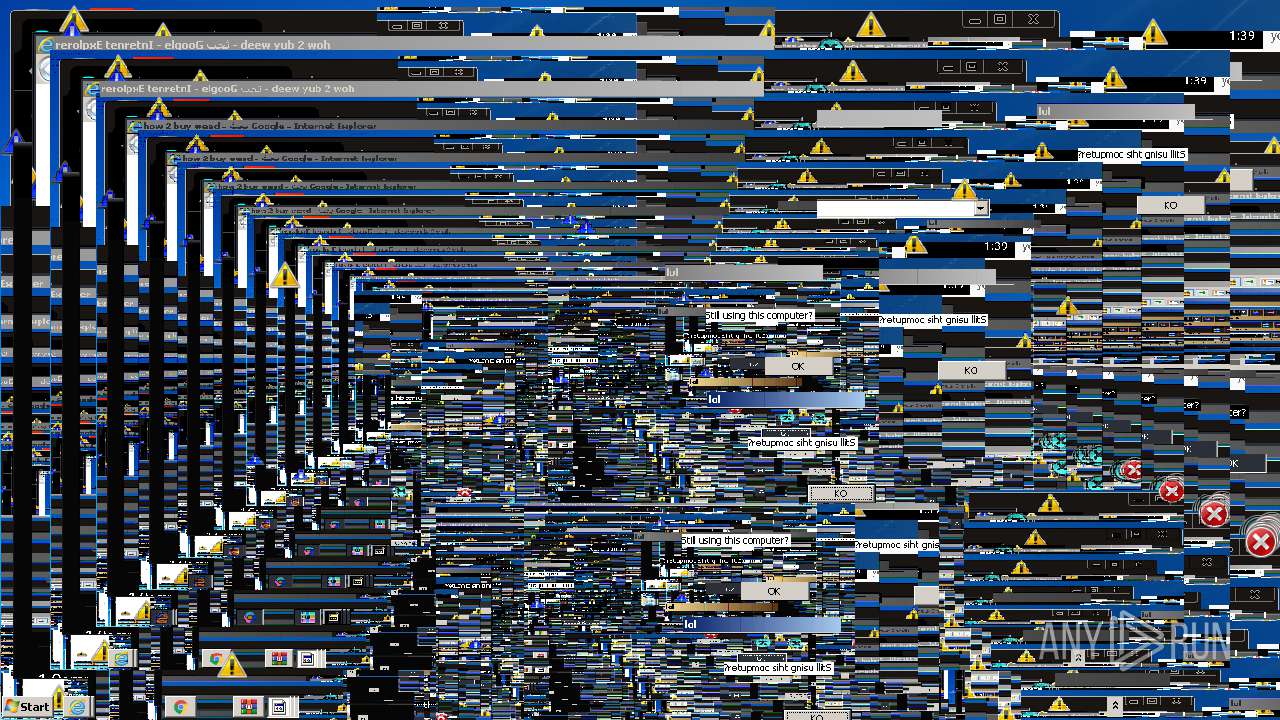
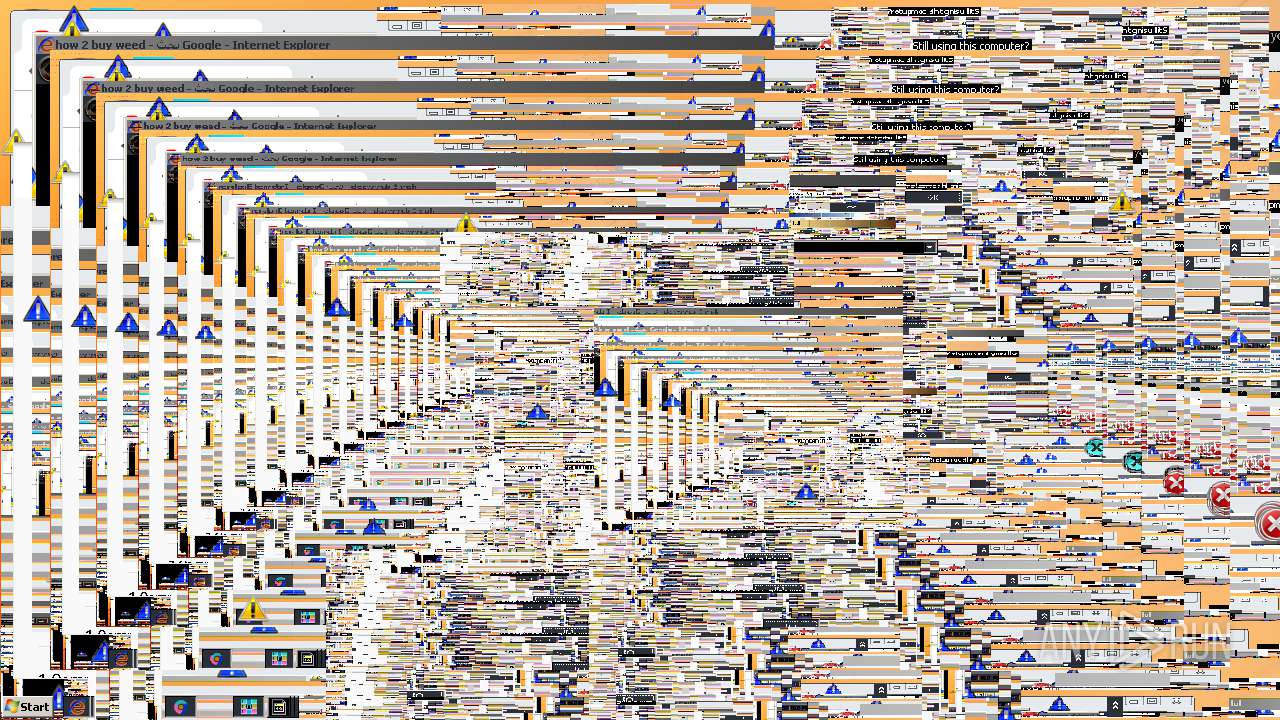
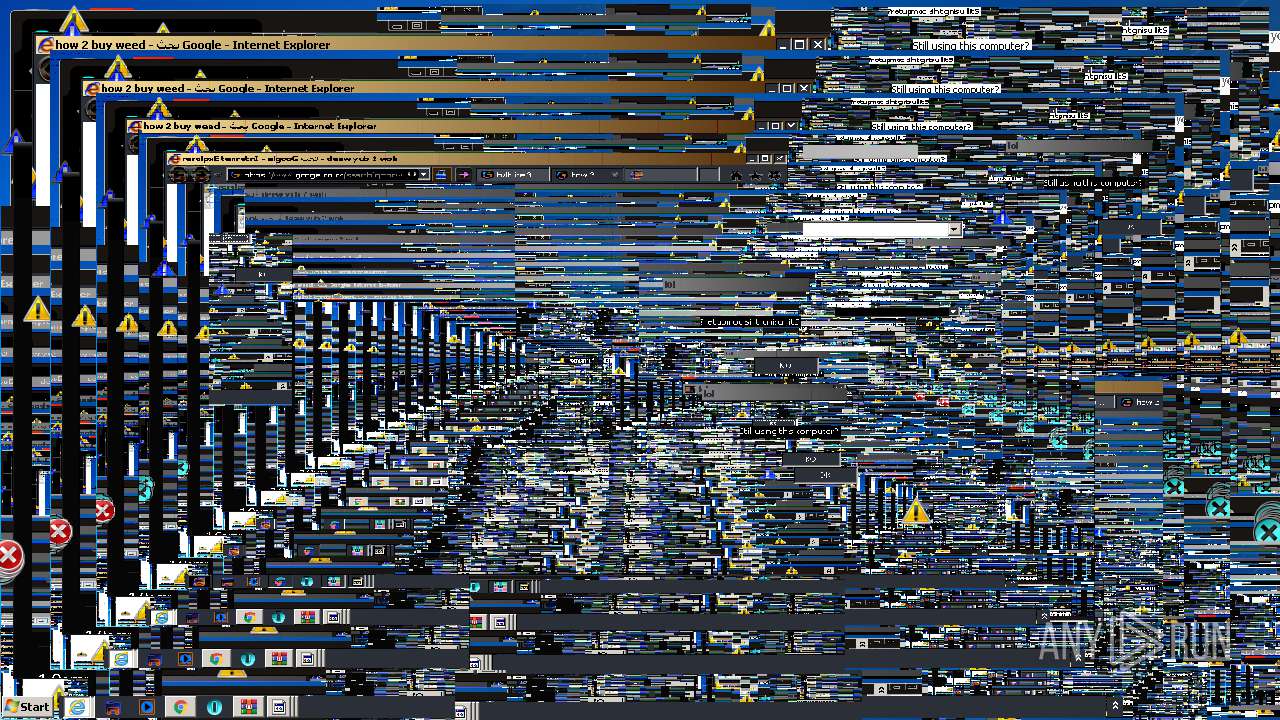
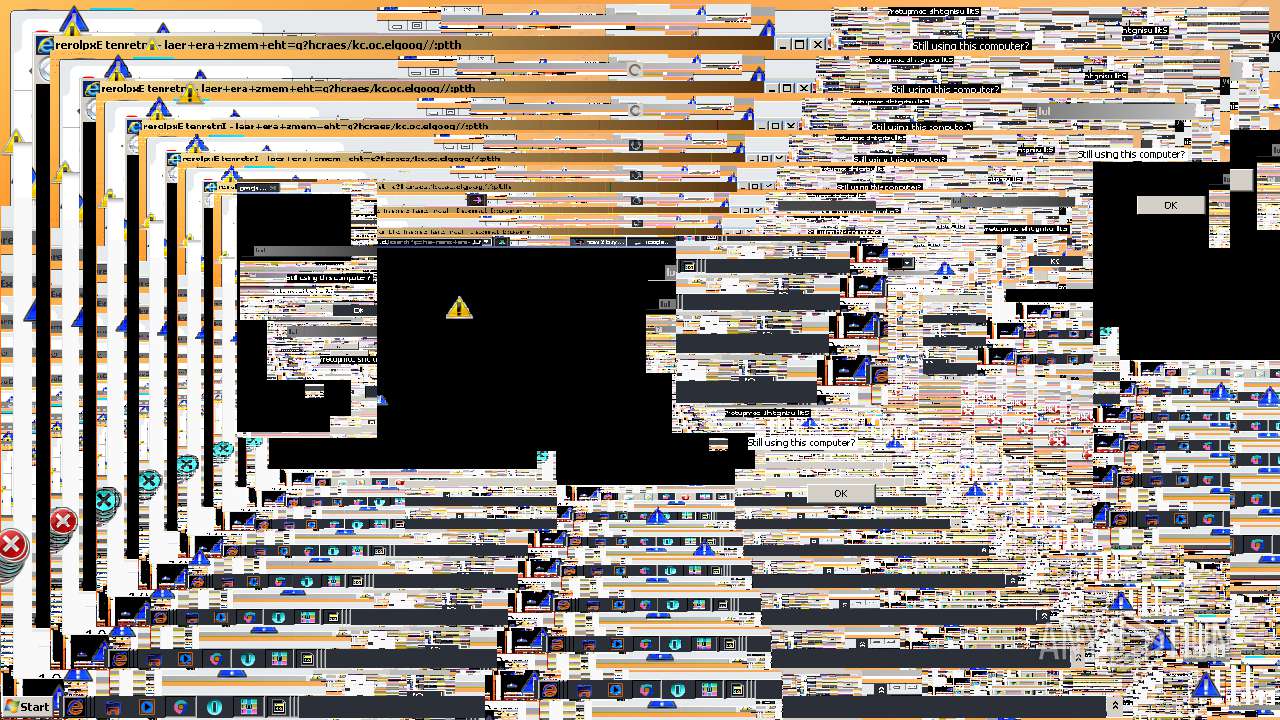
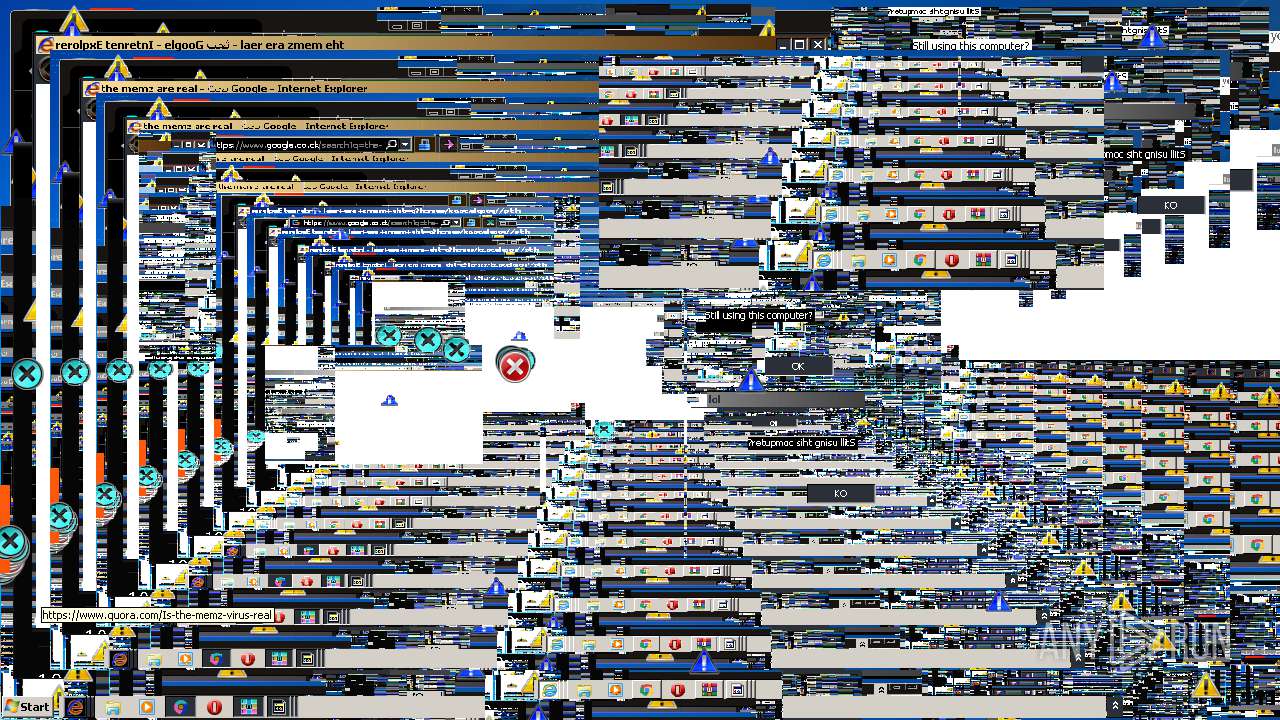
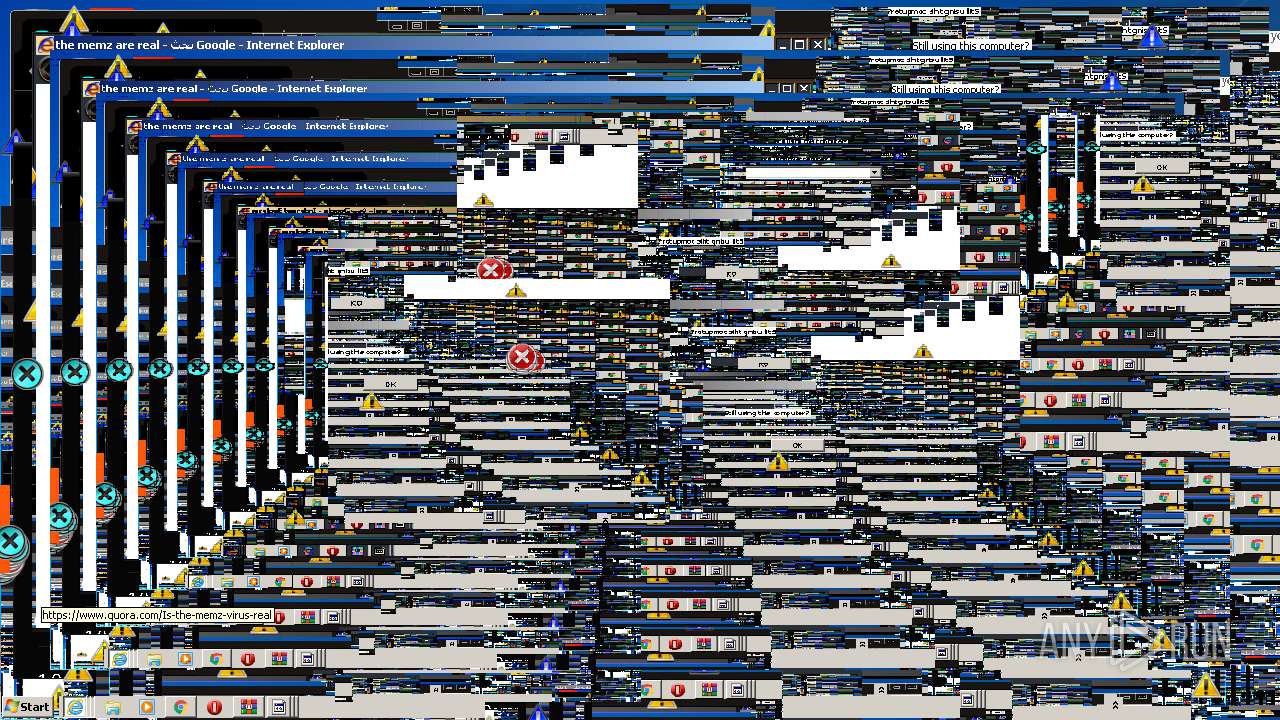
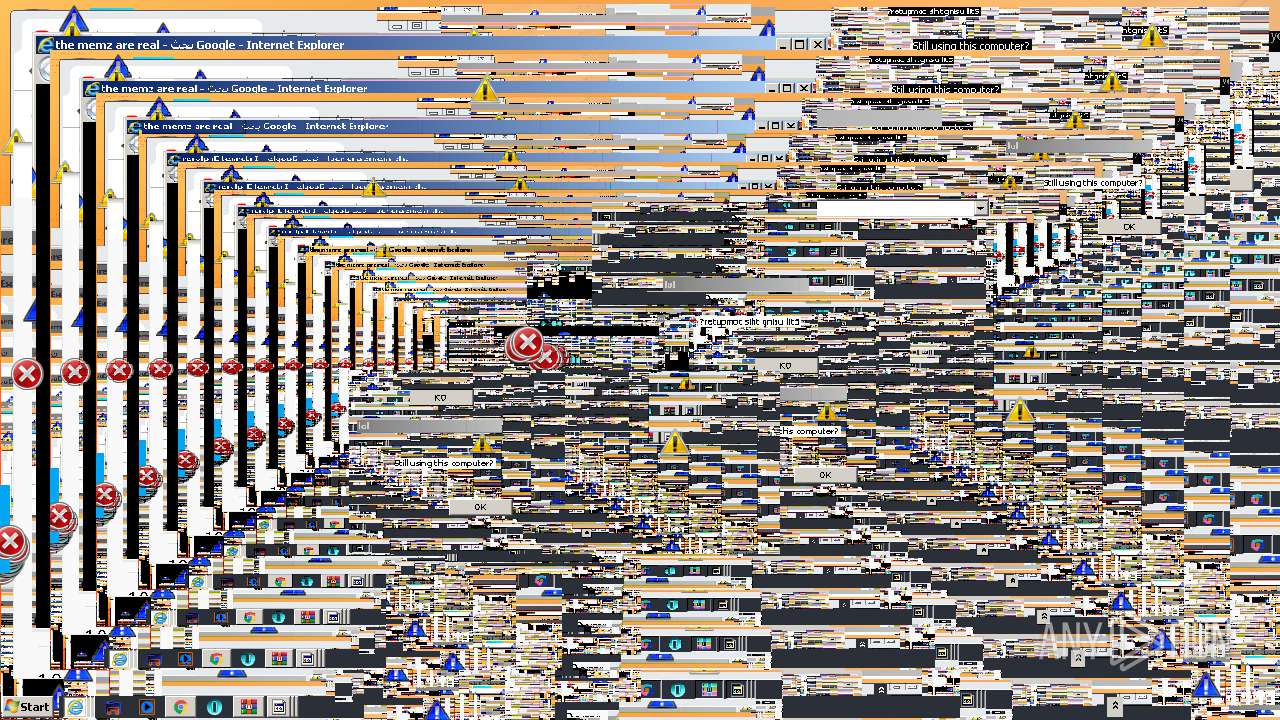
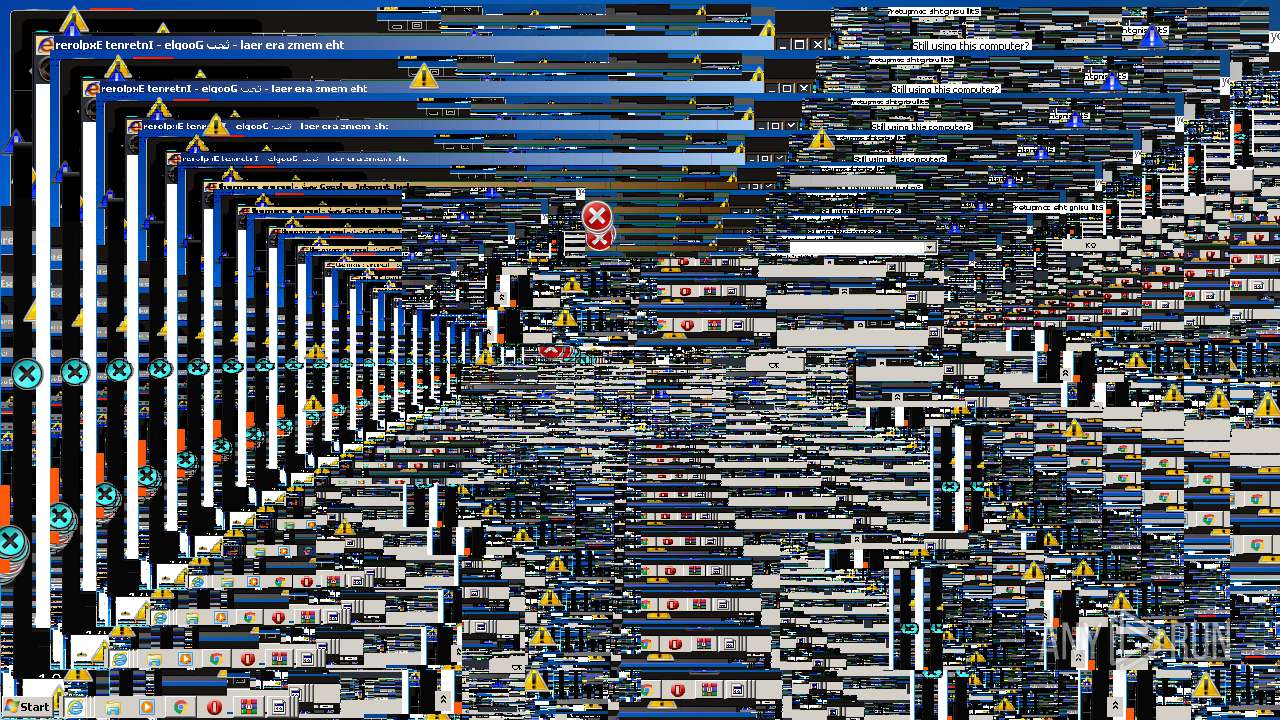
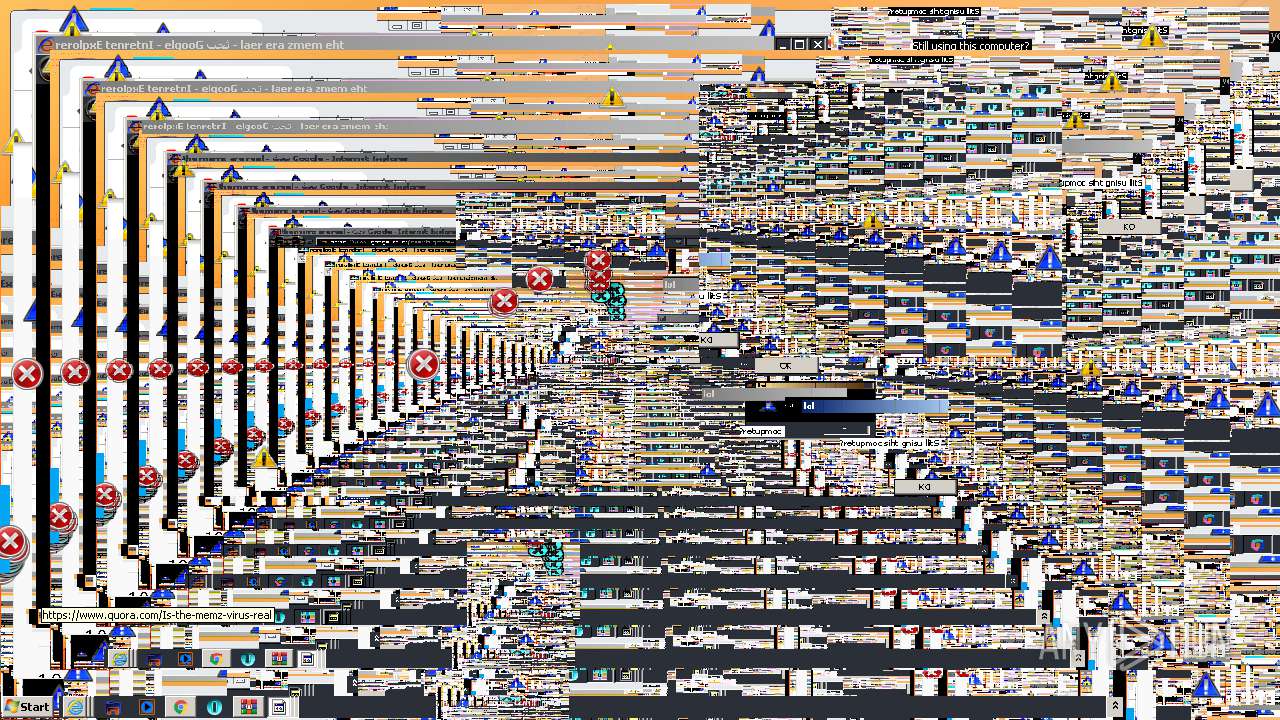
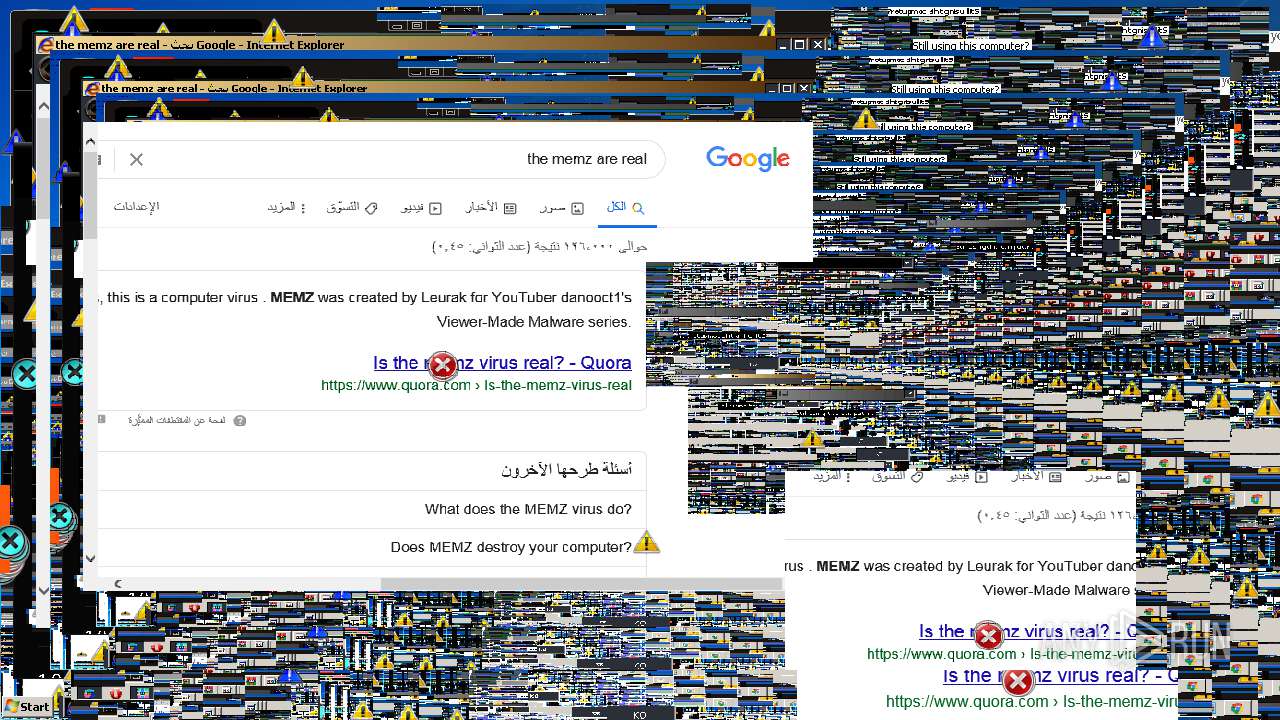
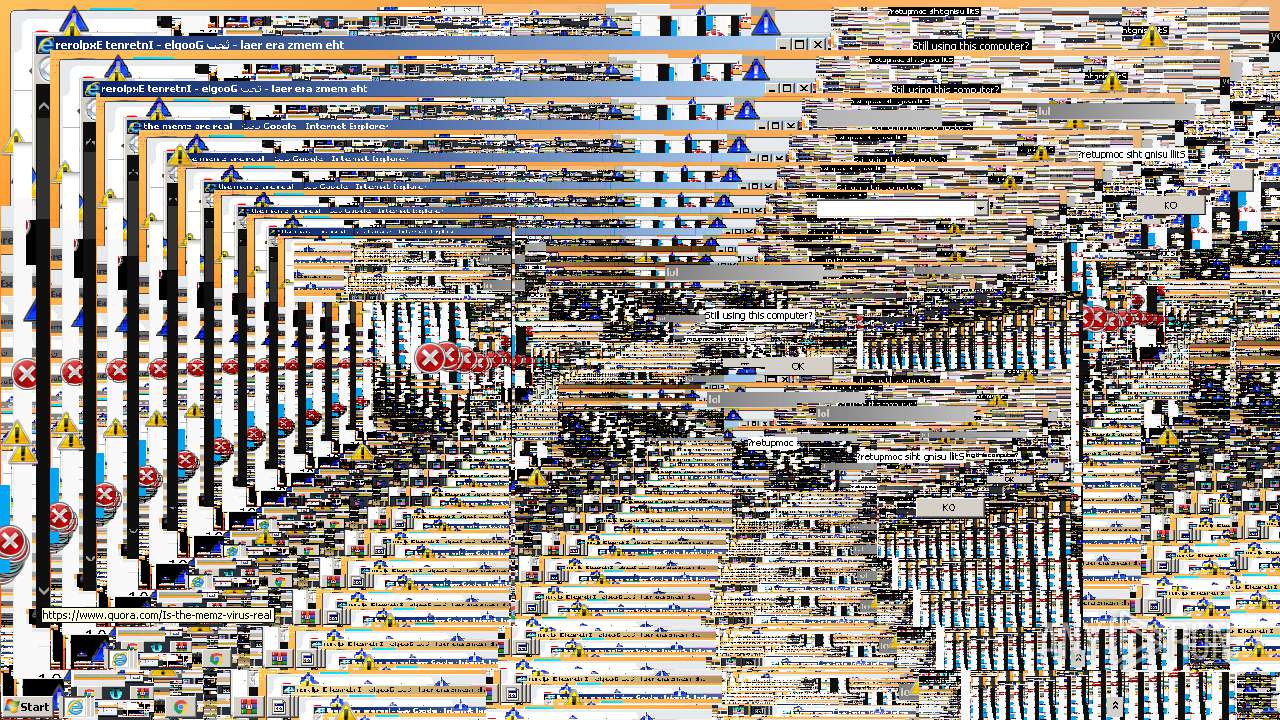
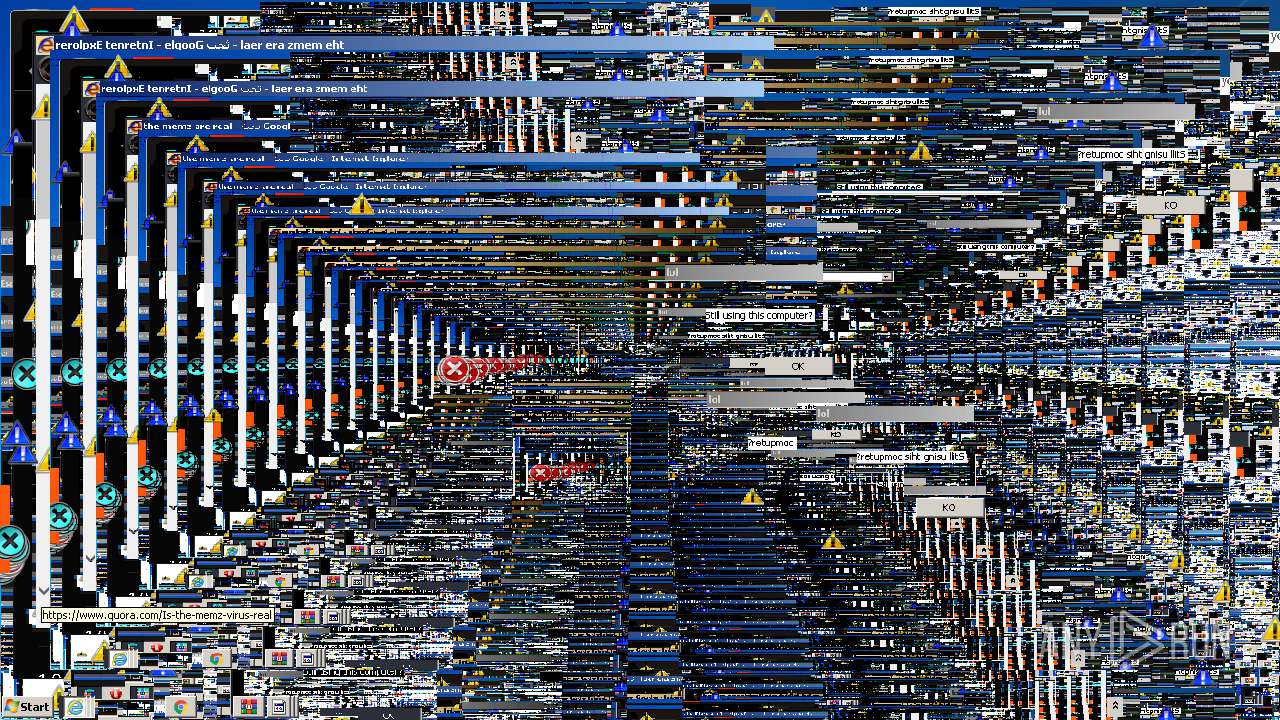
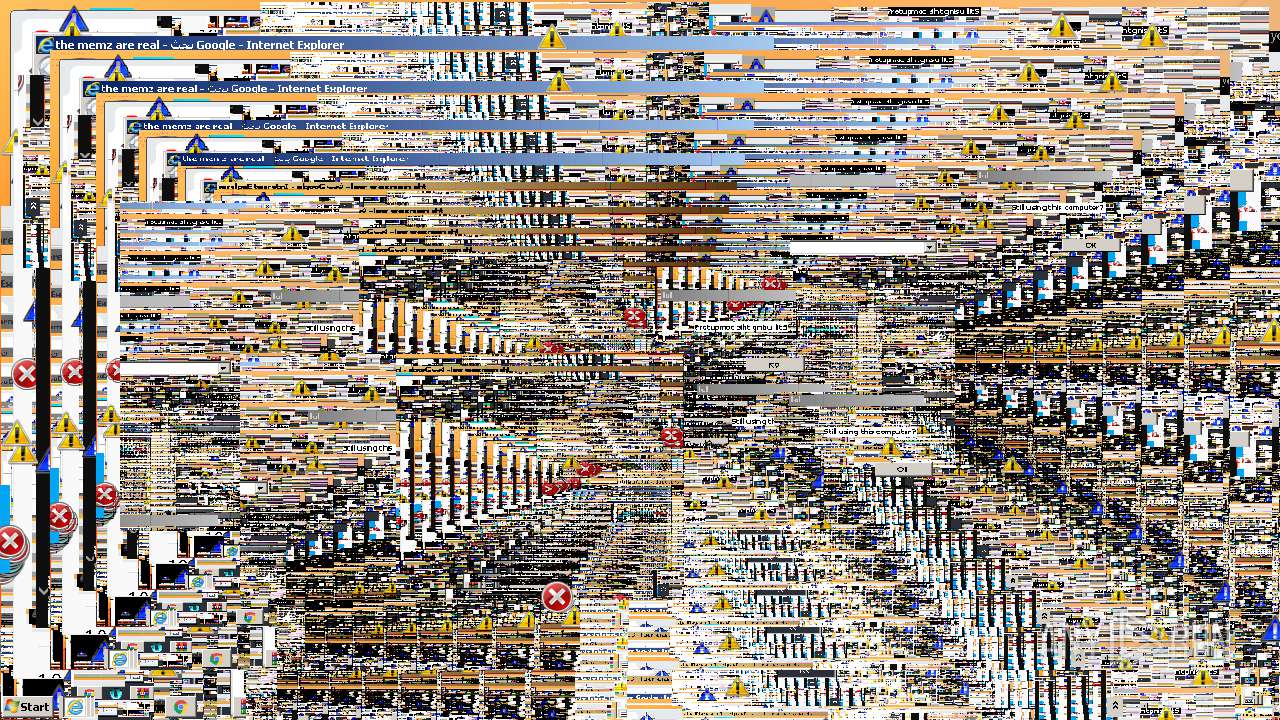
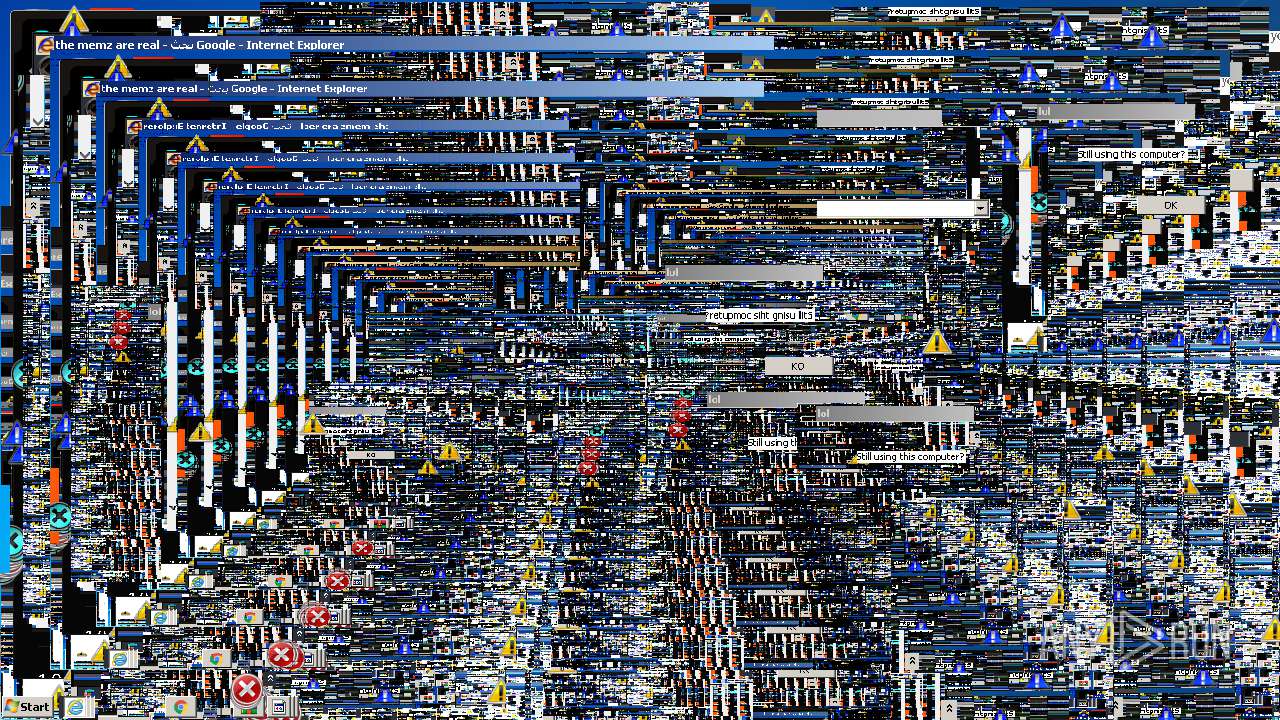
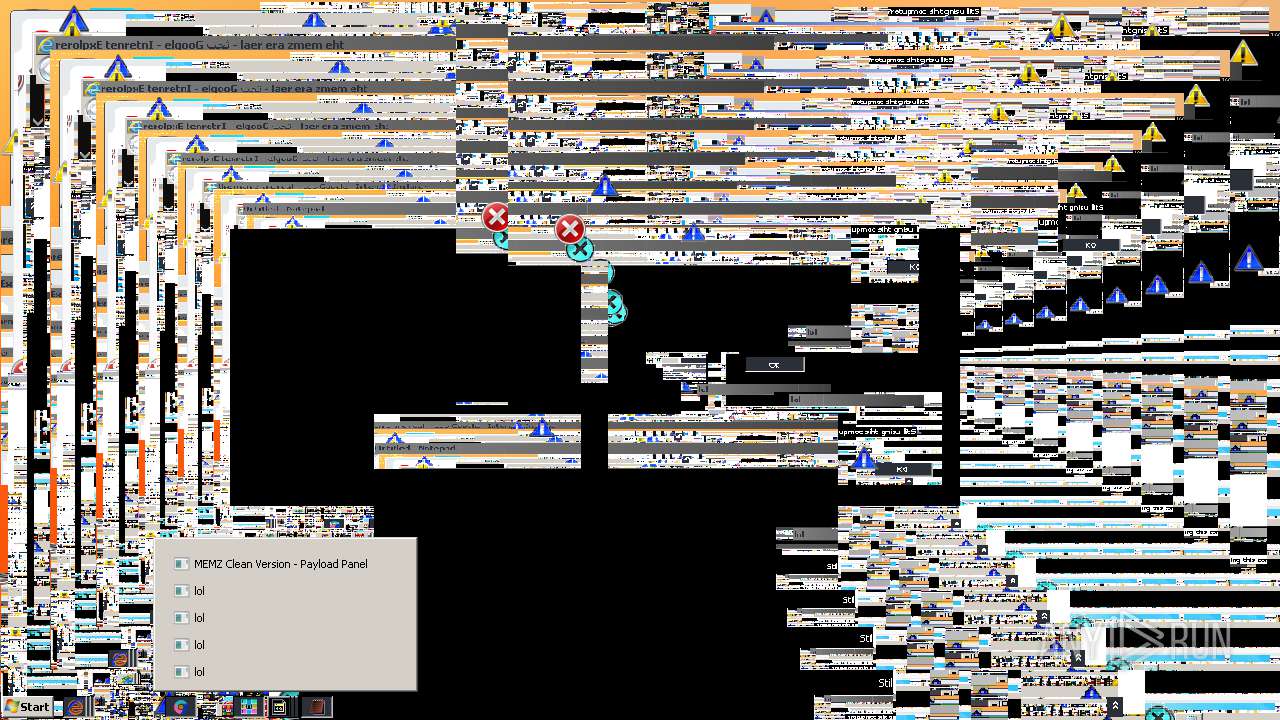
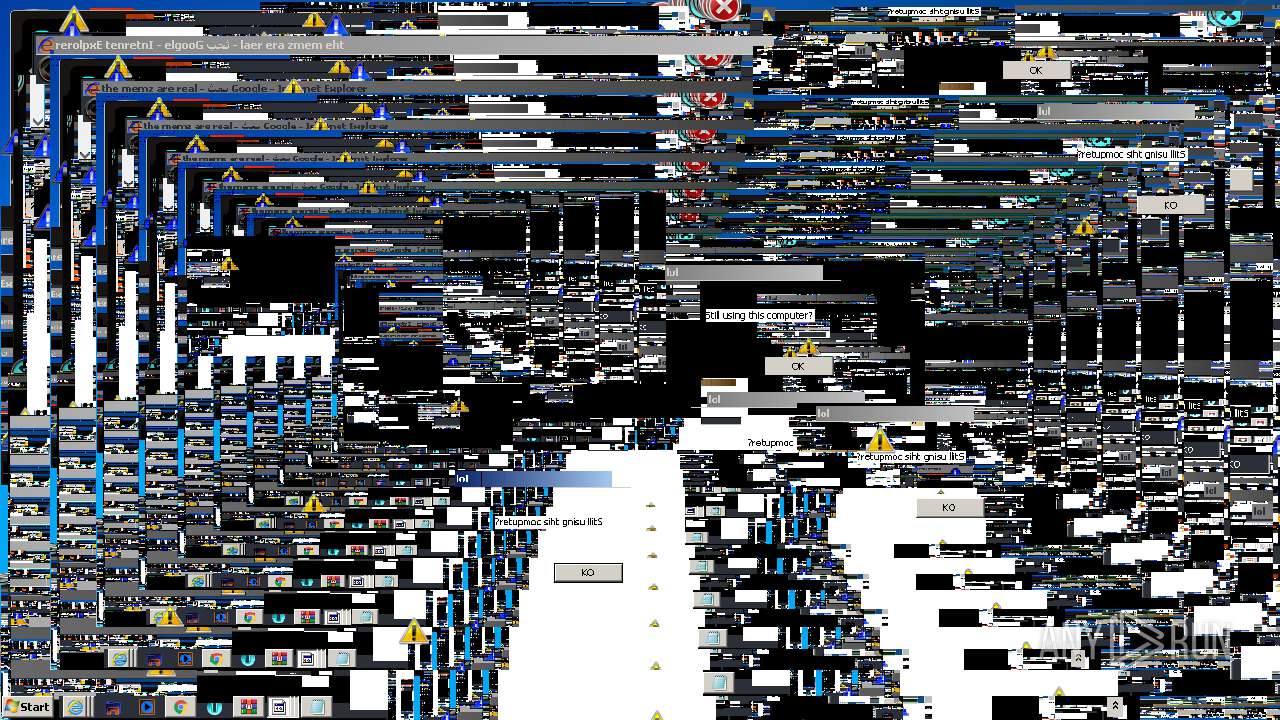
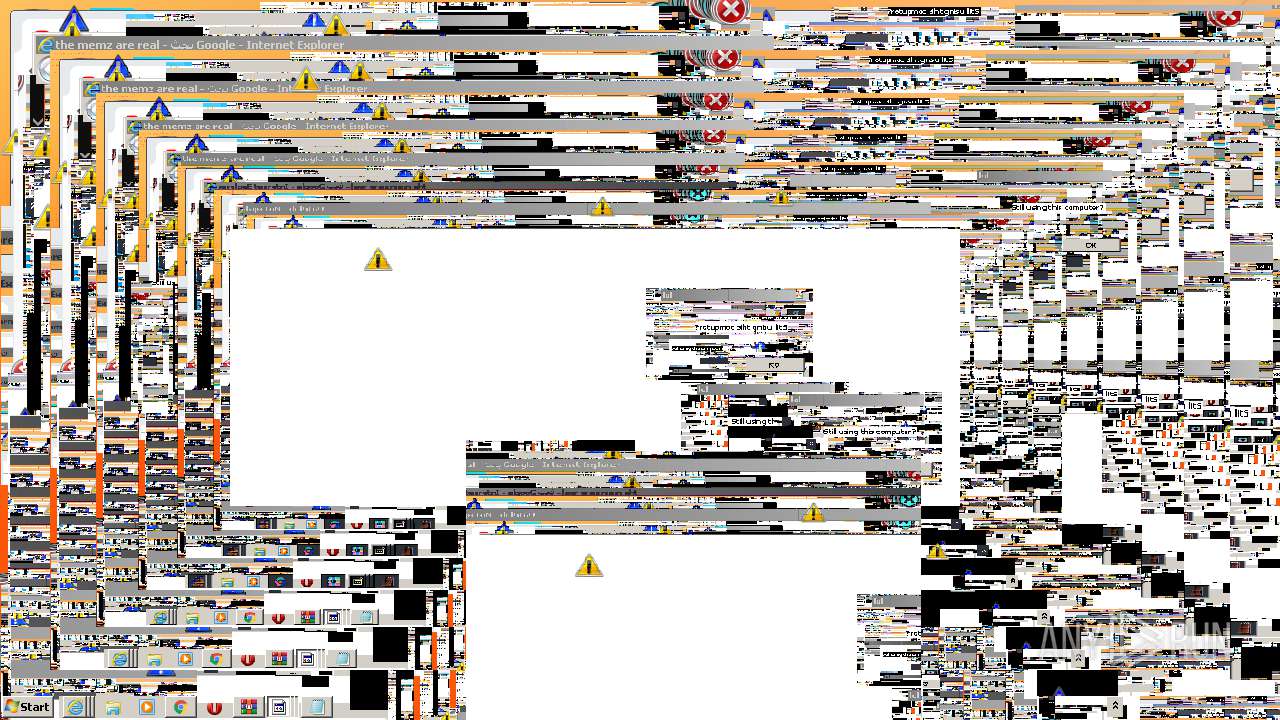
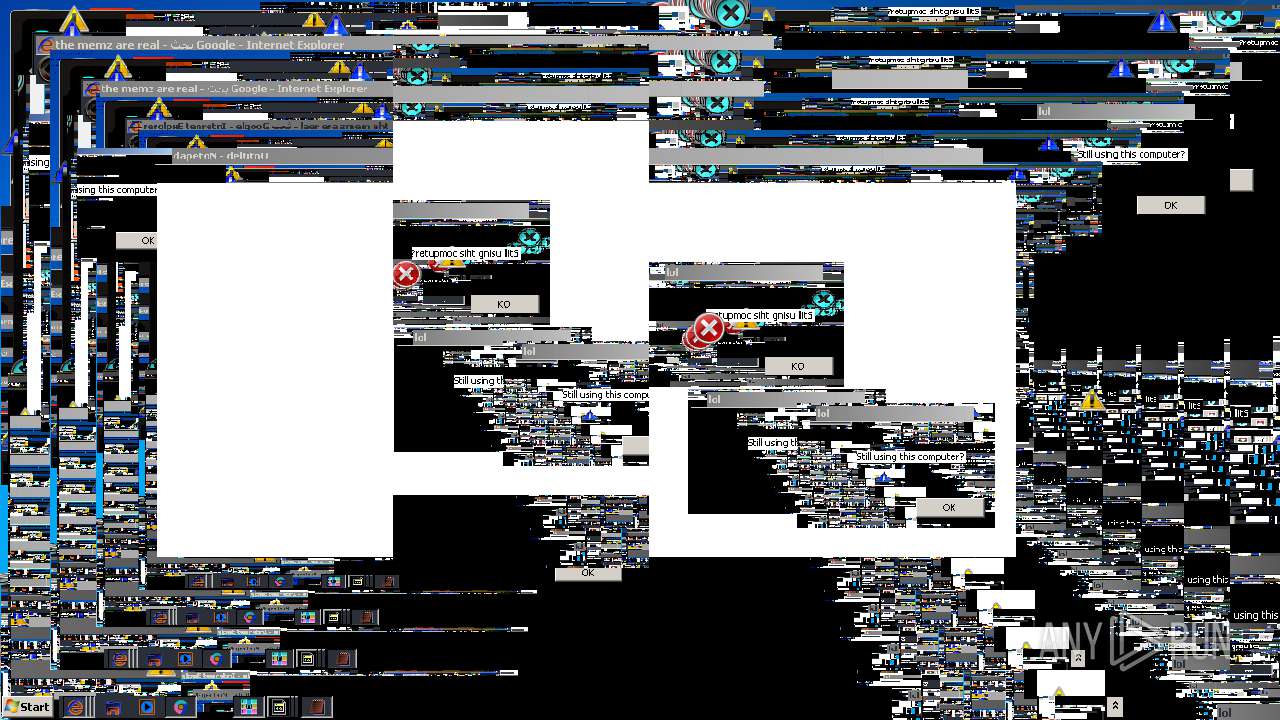
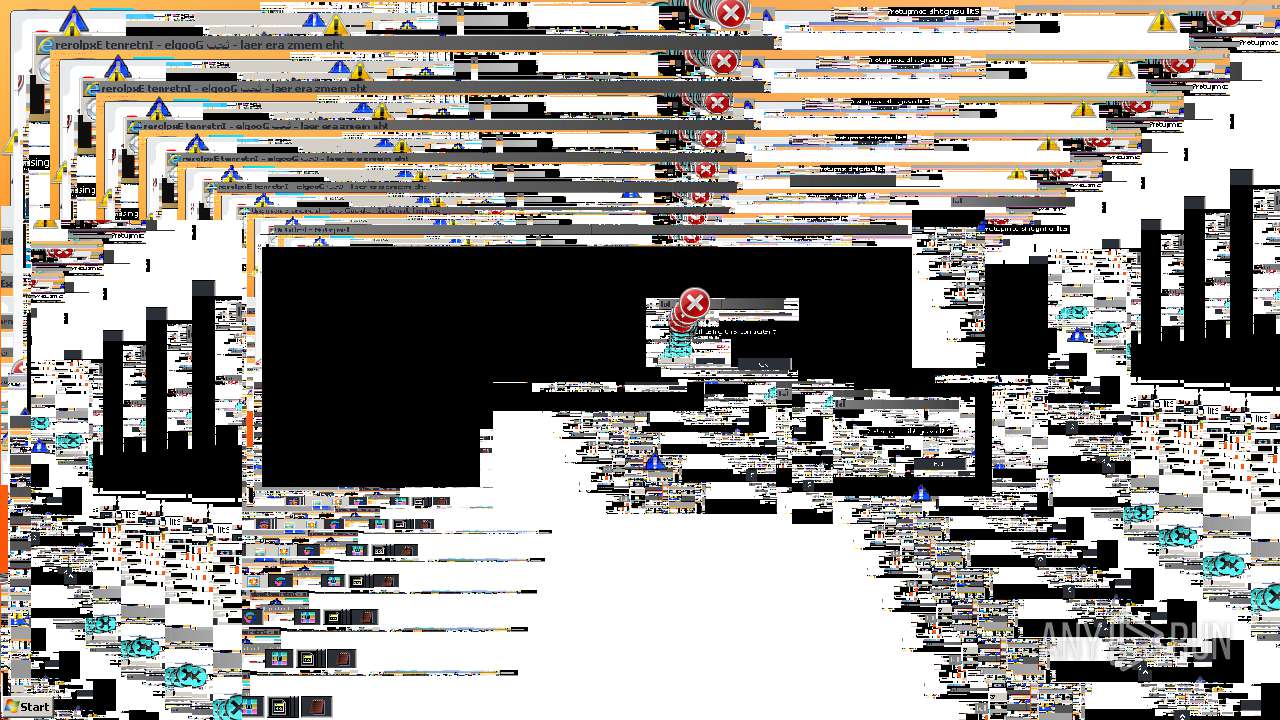
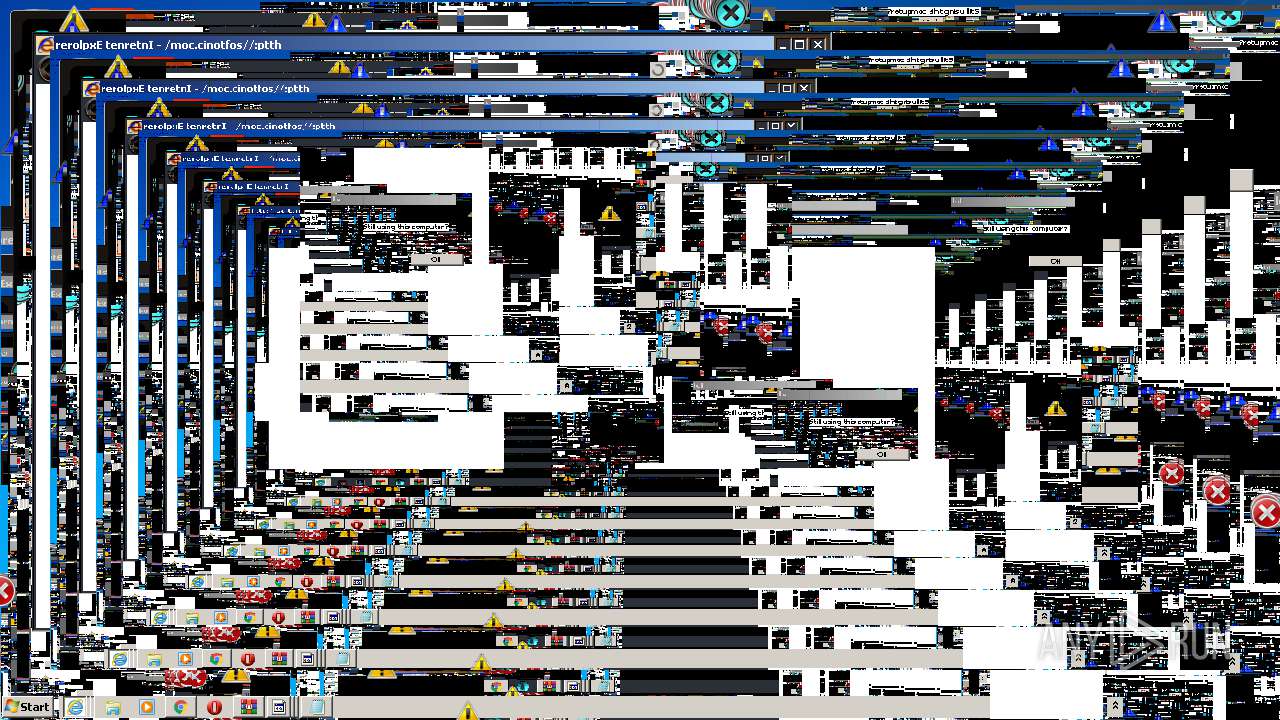
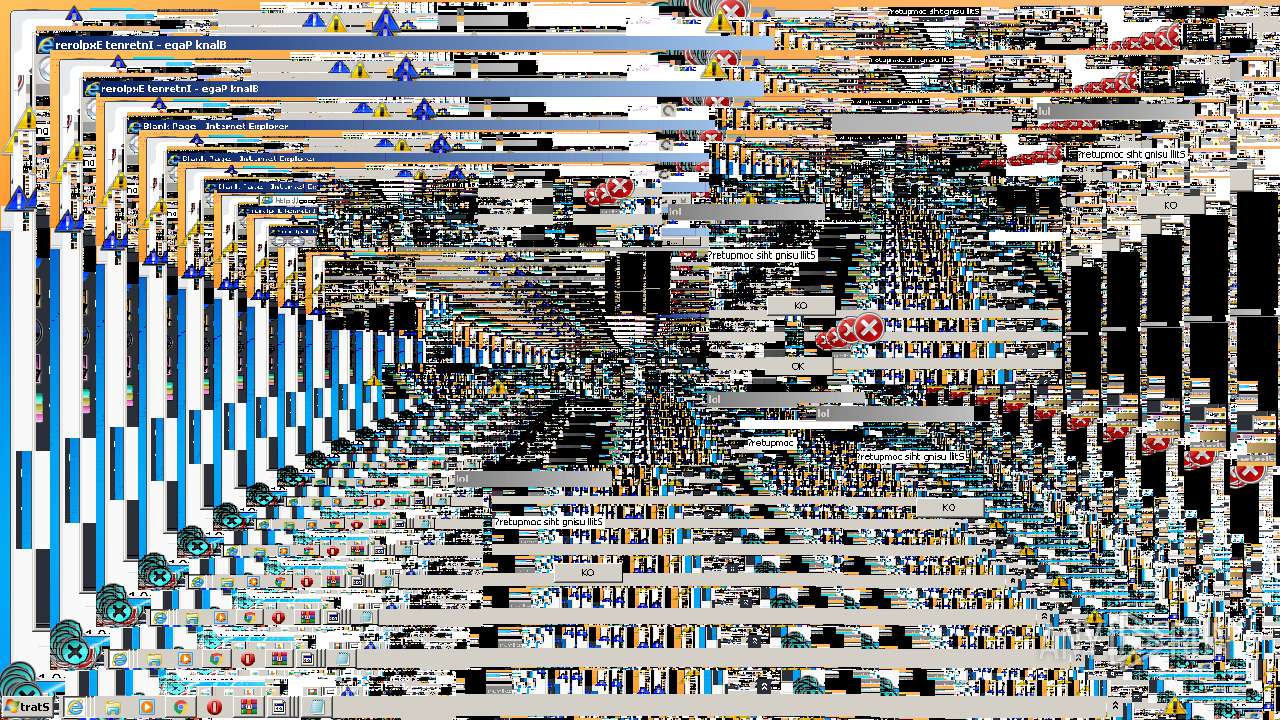
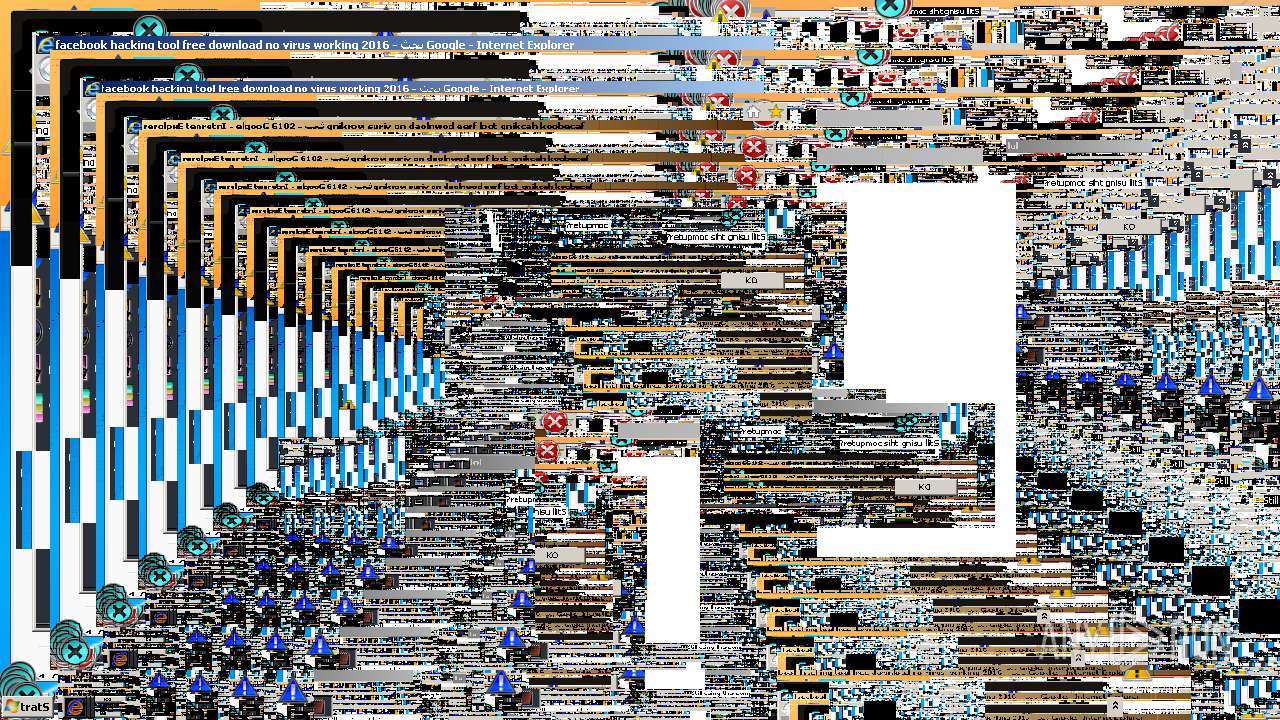
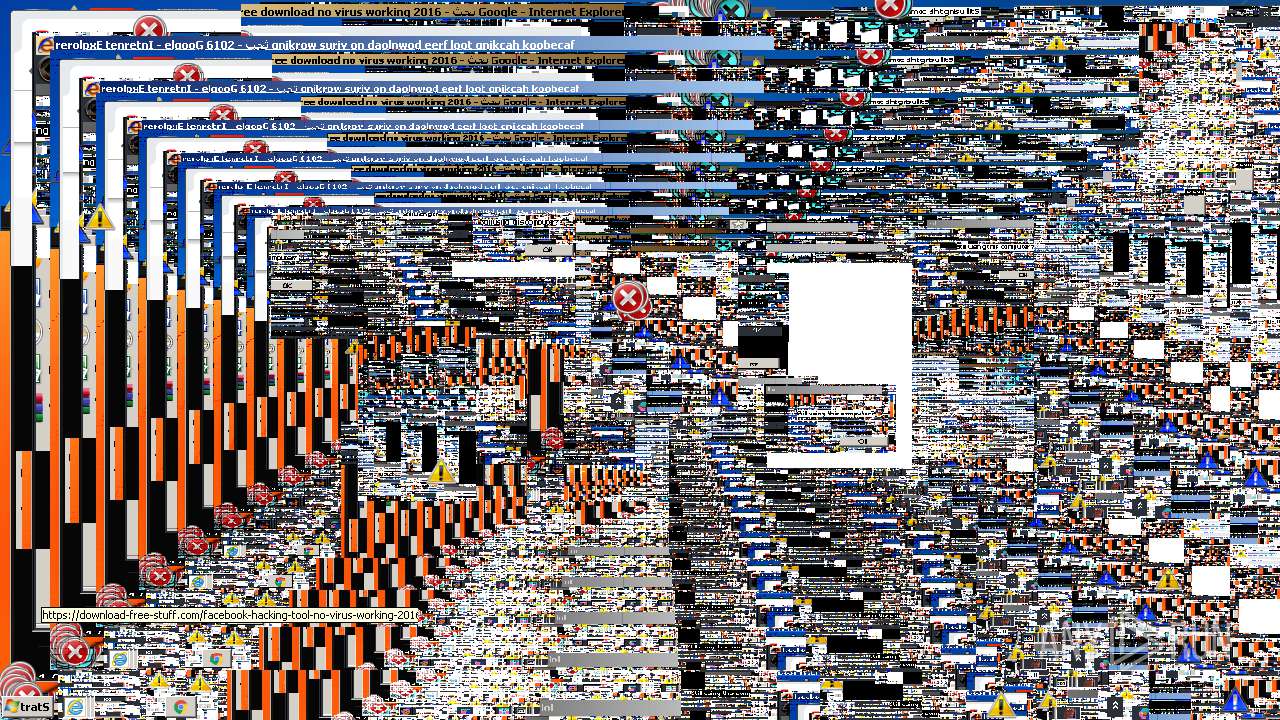
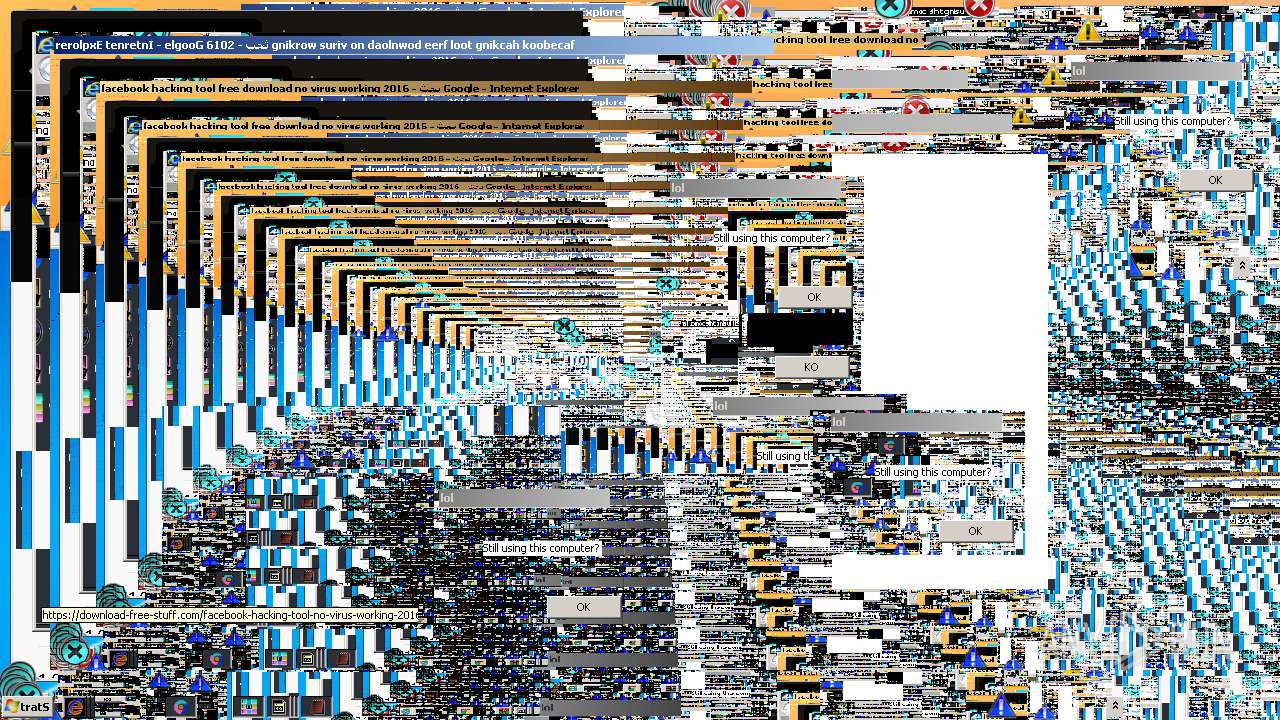
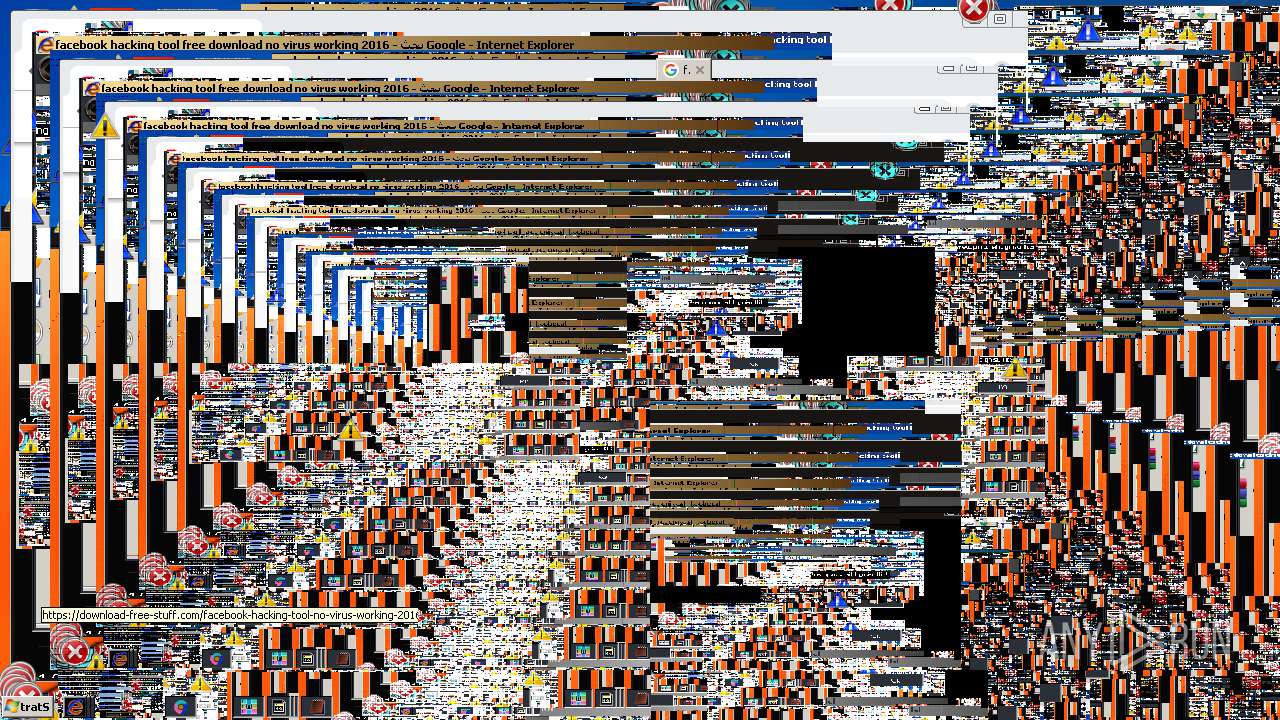
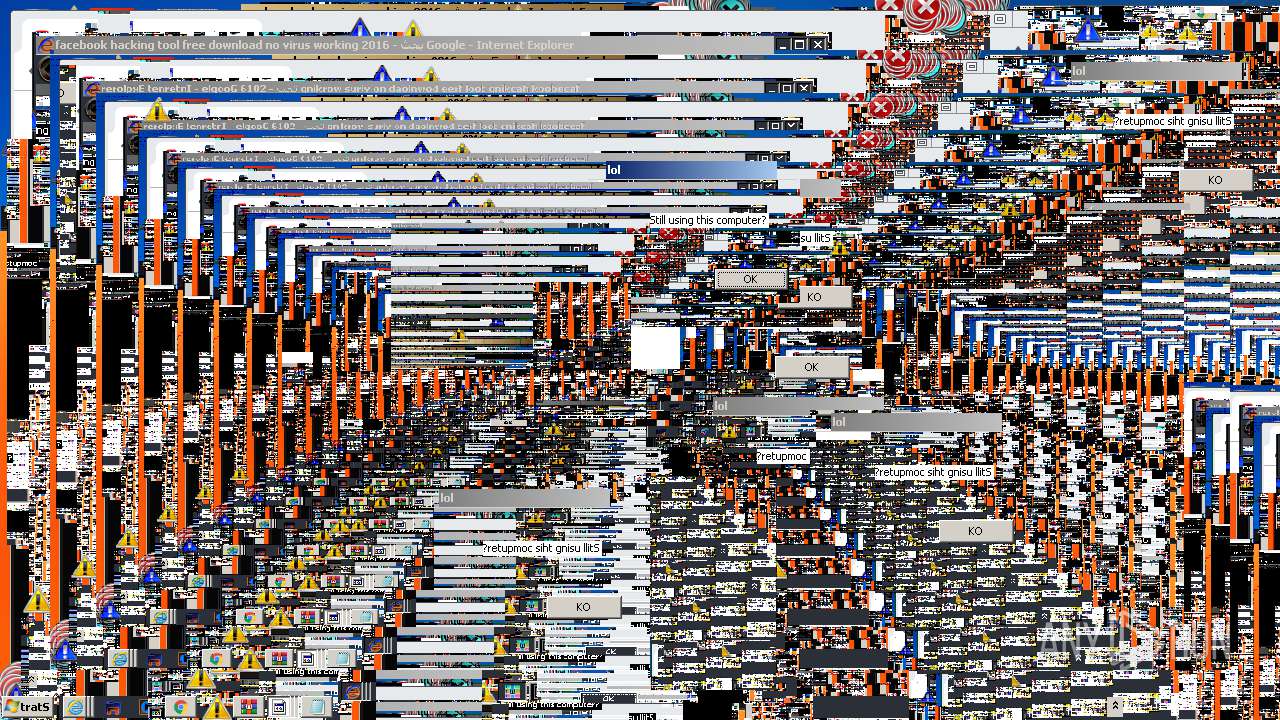
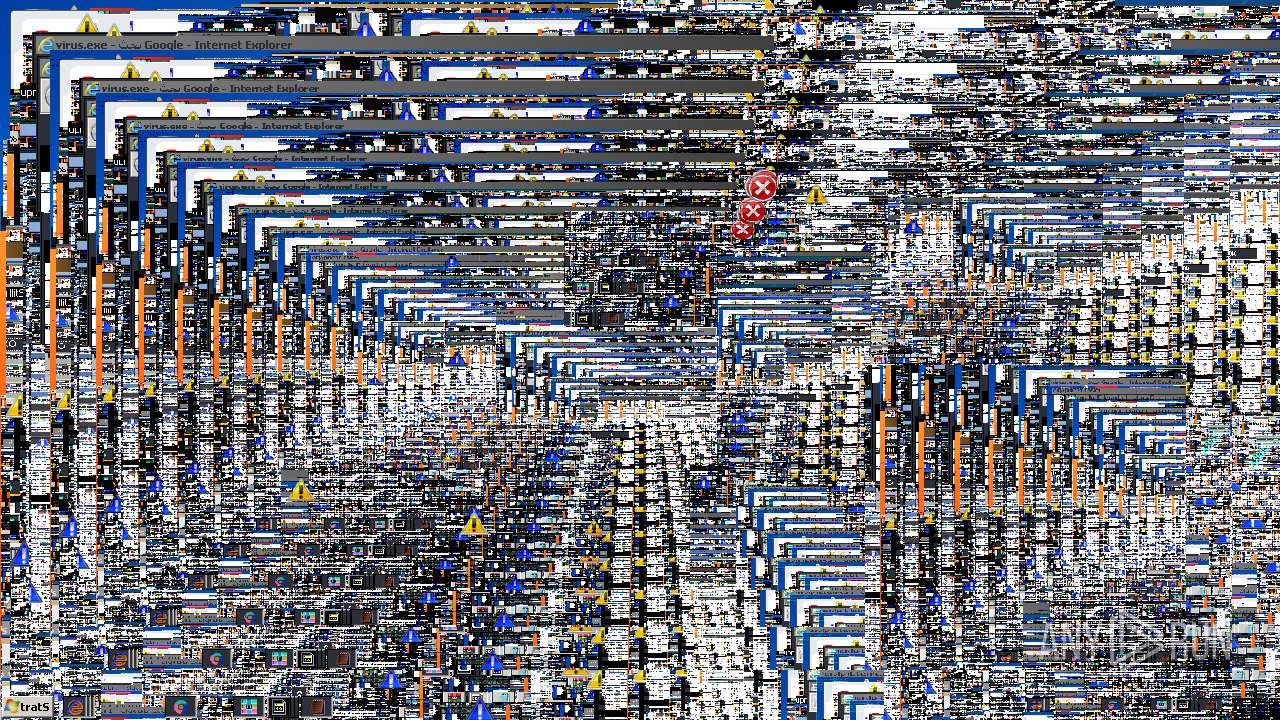
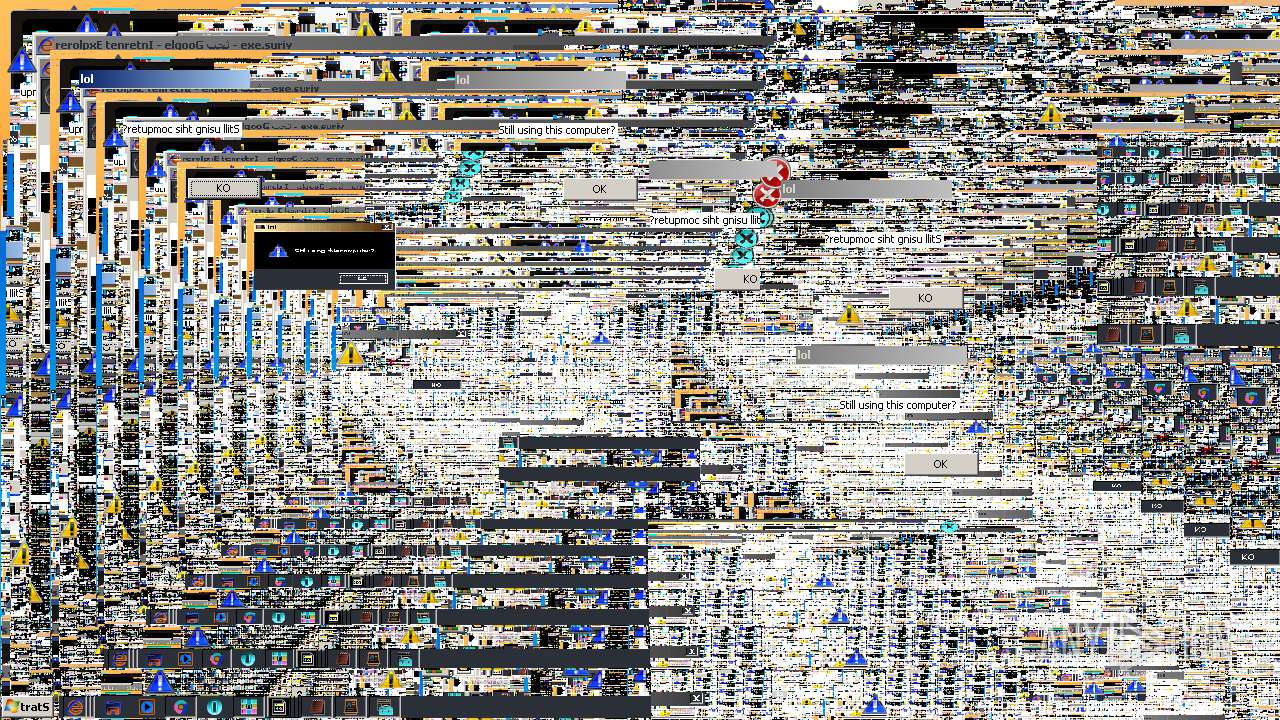
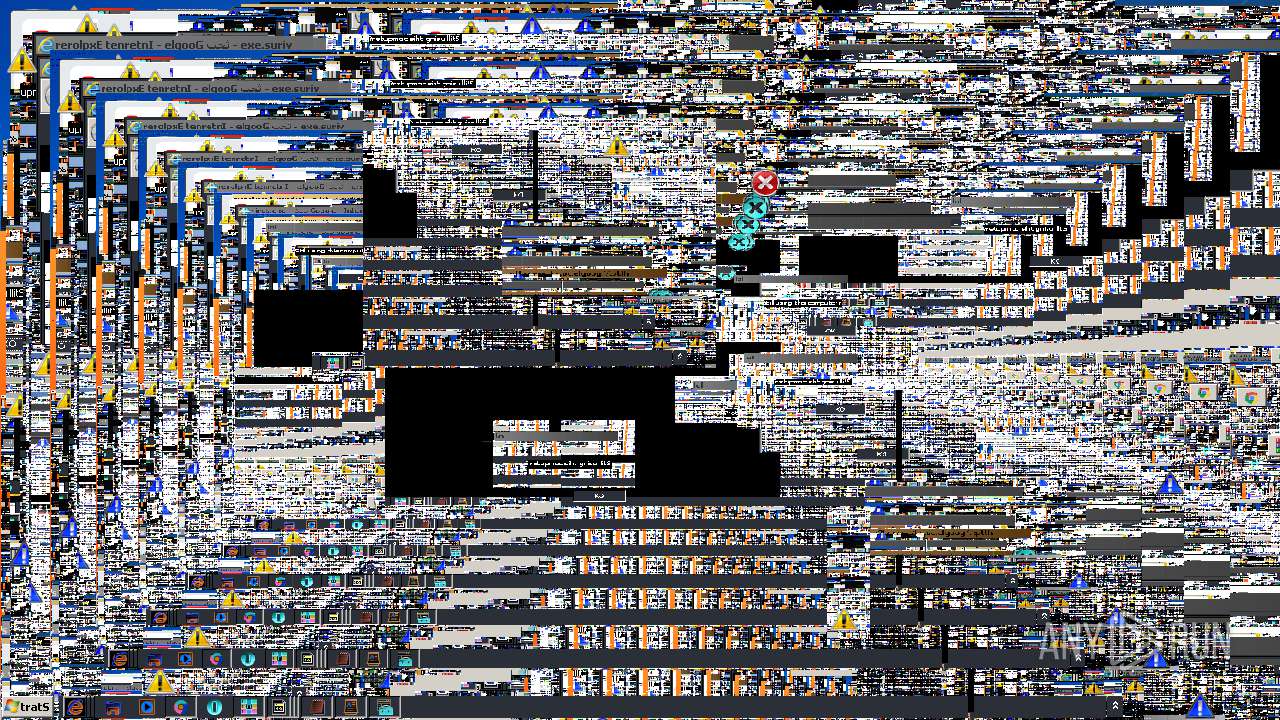
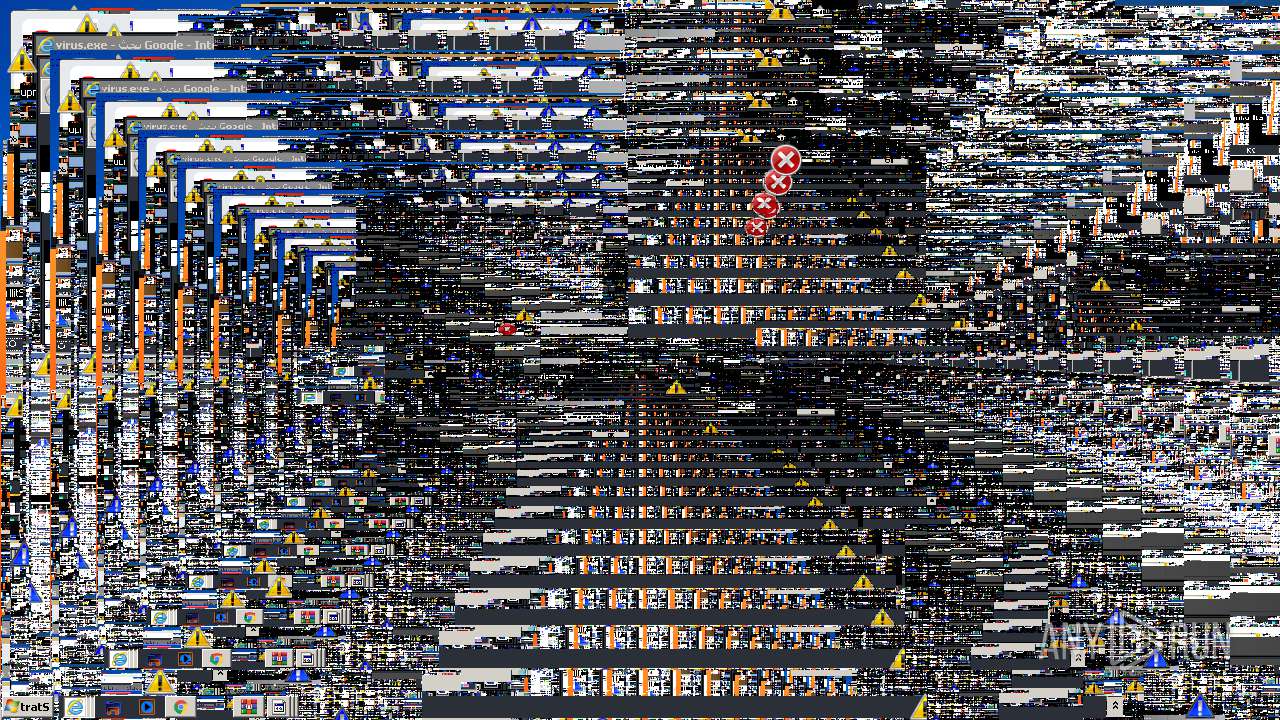
MALICIOUS
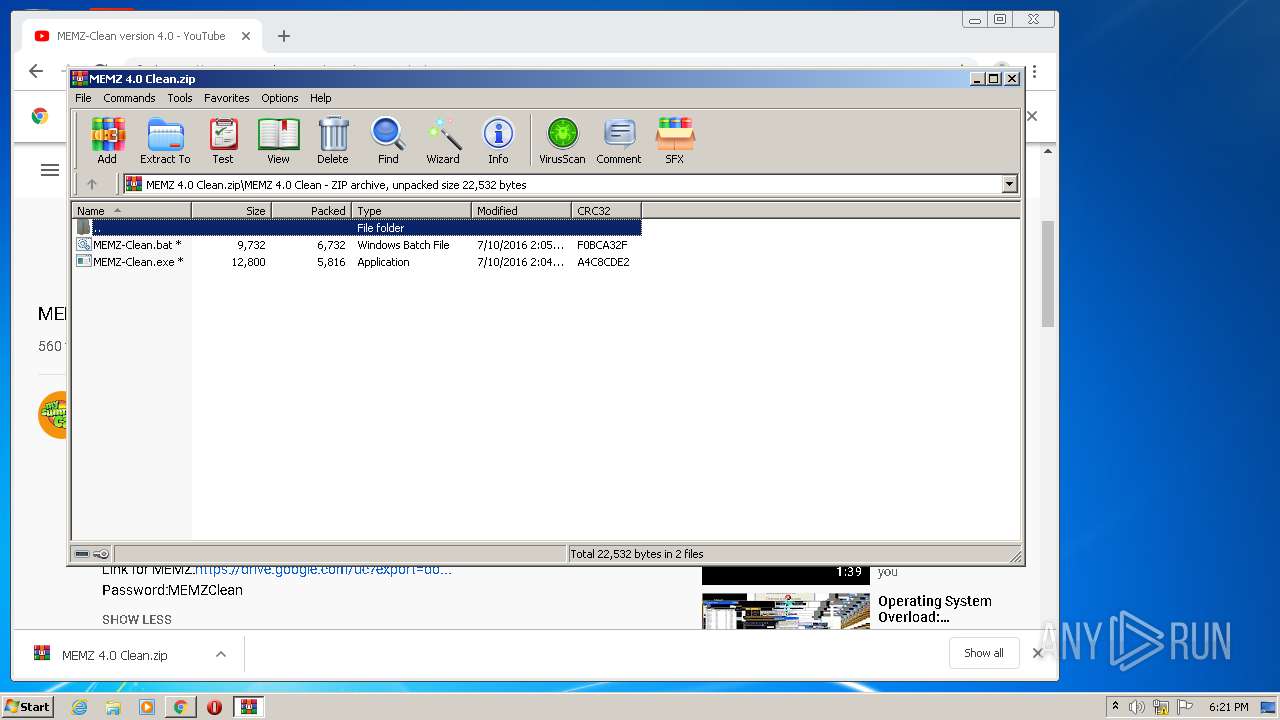
Application was dropped or rewritten from another process
- MEMZ-Clean.exe (PID: 2268)
Runs app for hidden code execution
- MEMZ-Clean.exe (PID: 2268)
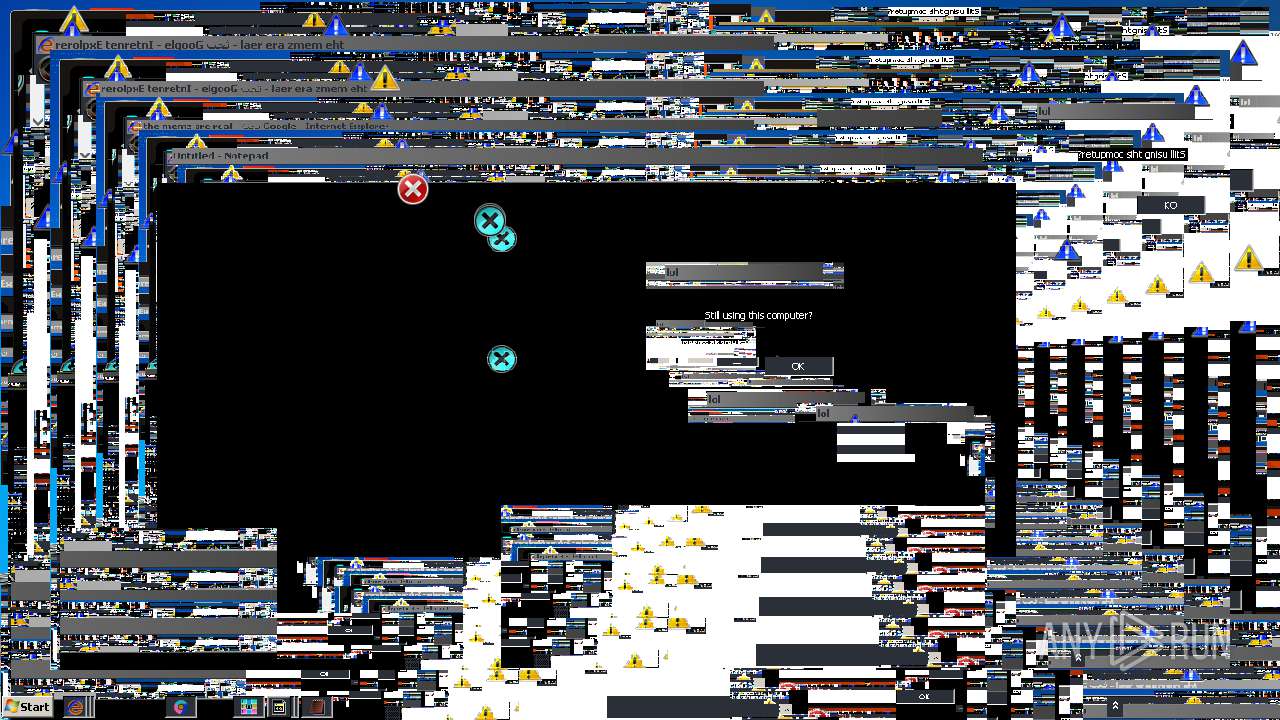
SUSPICIOUS
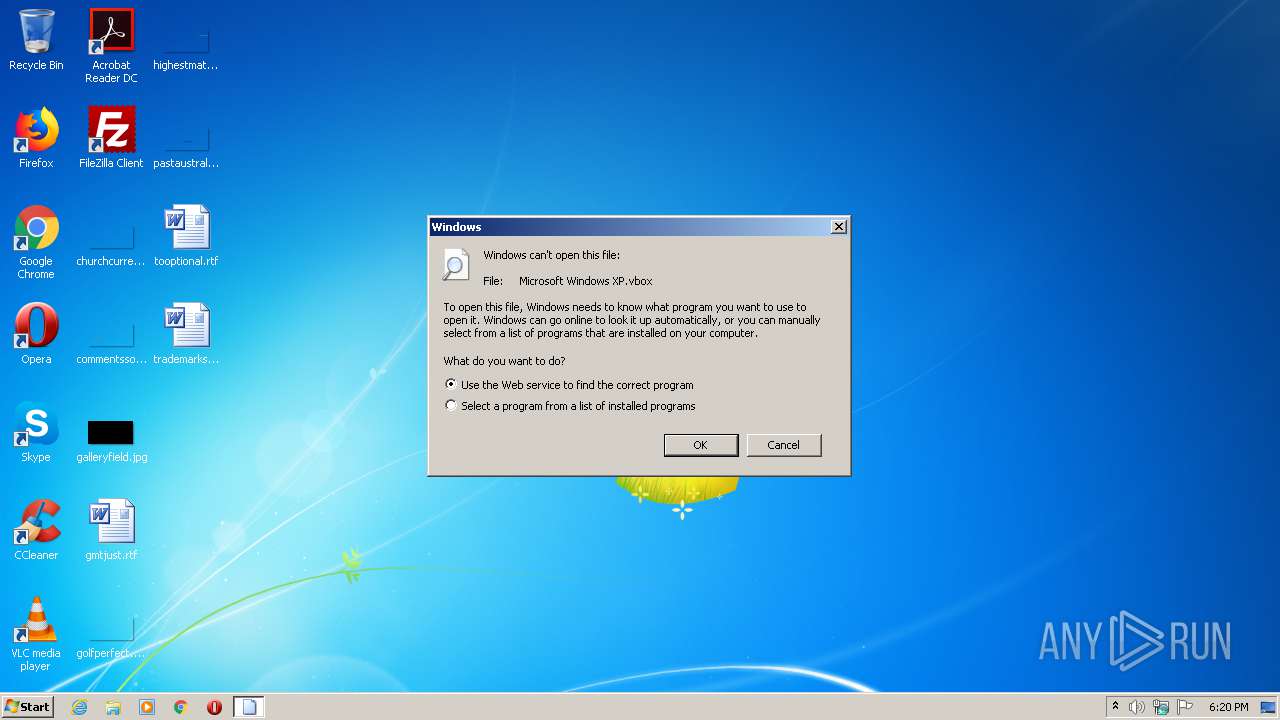
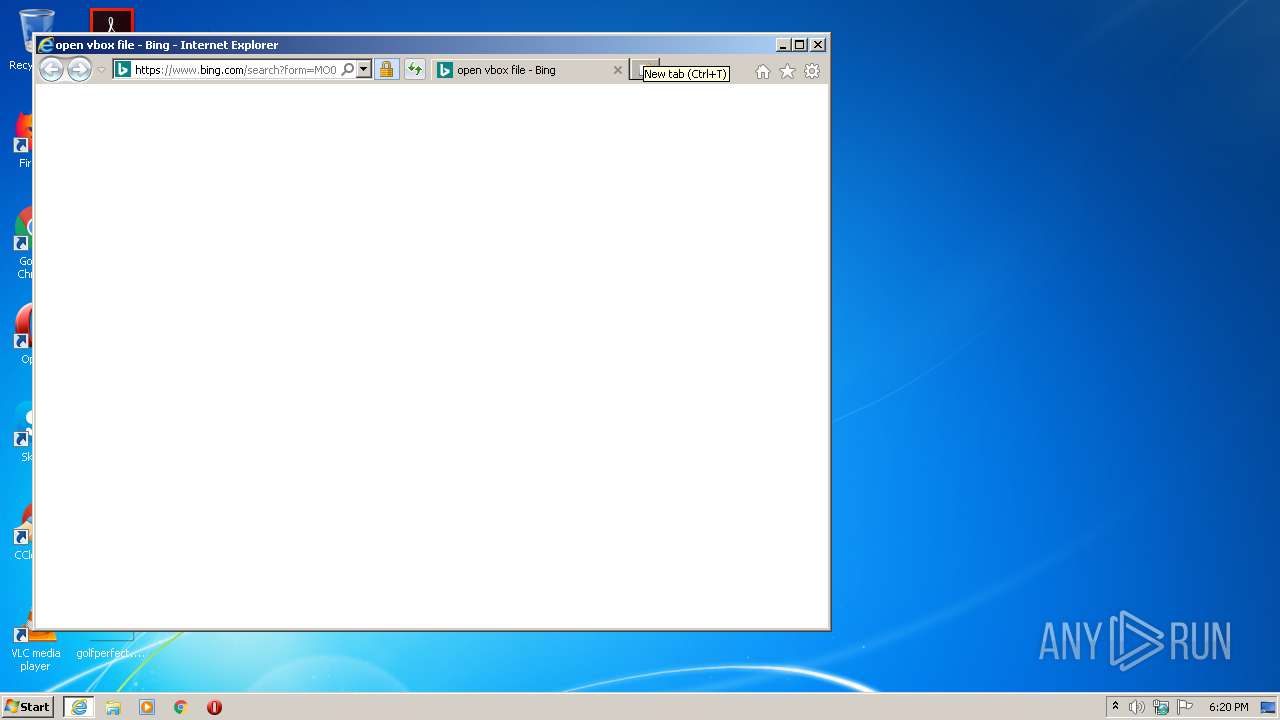
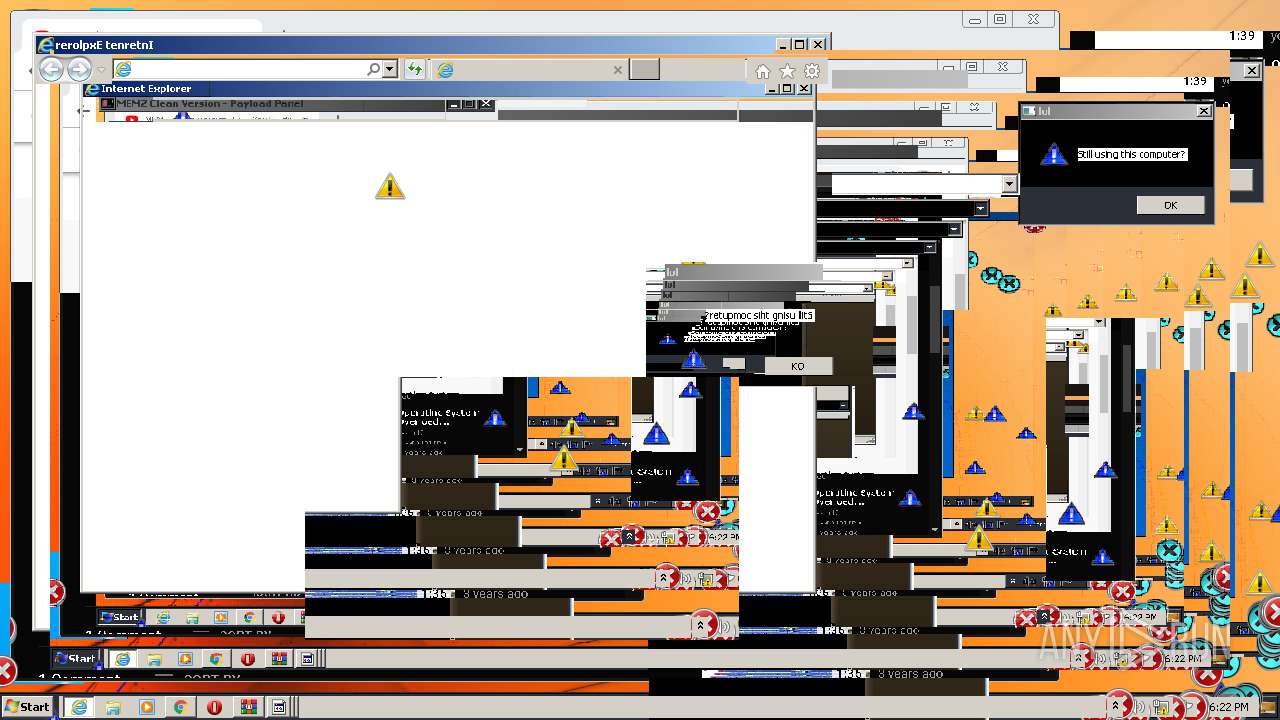
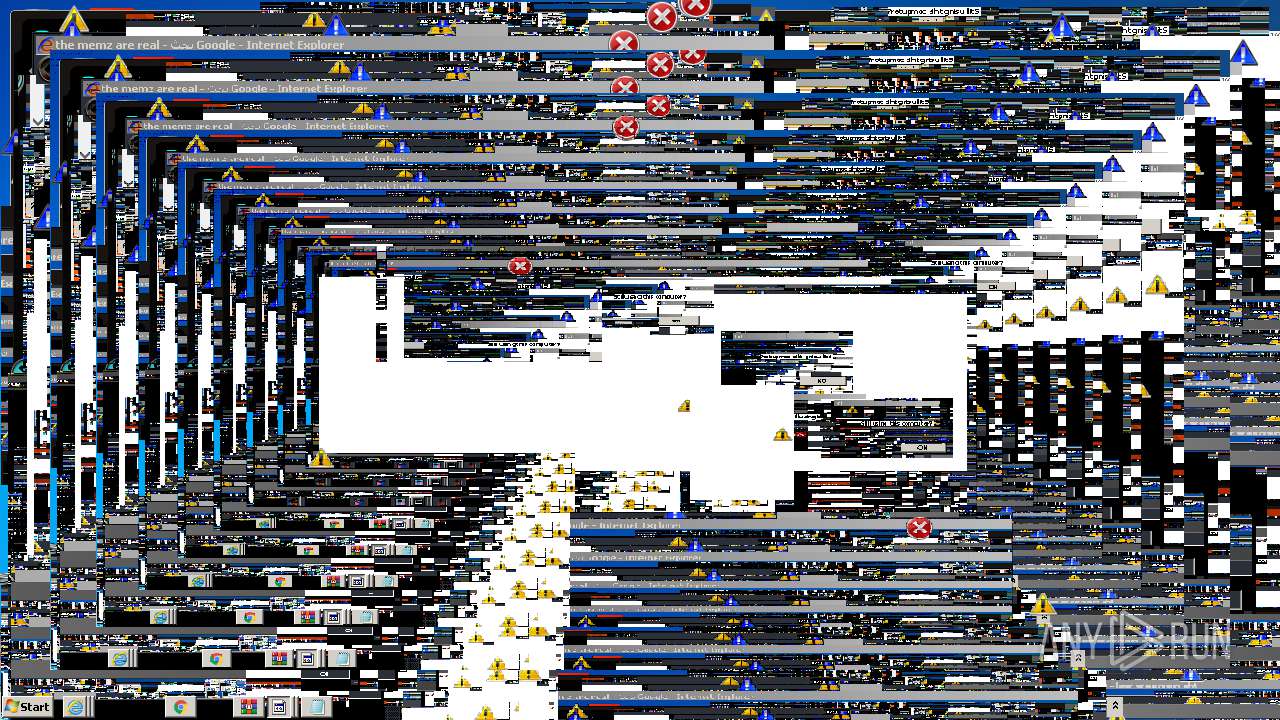
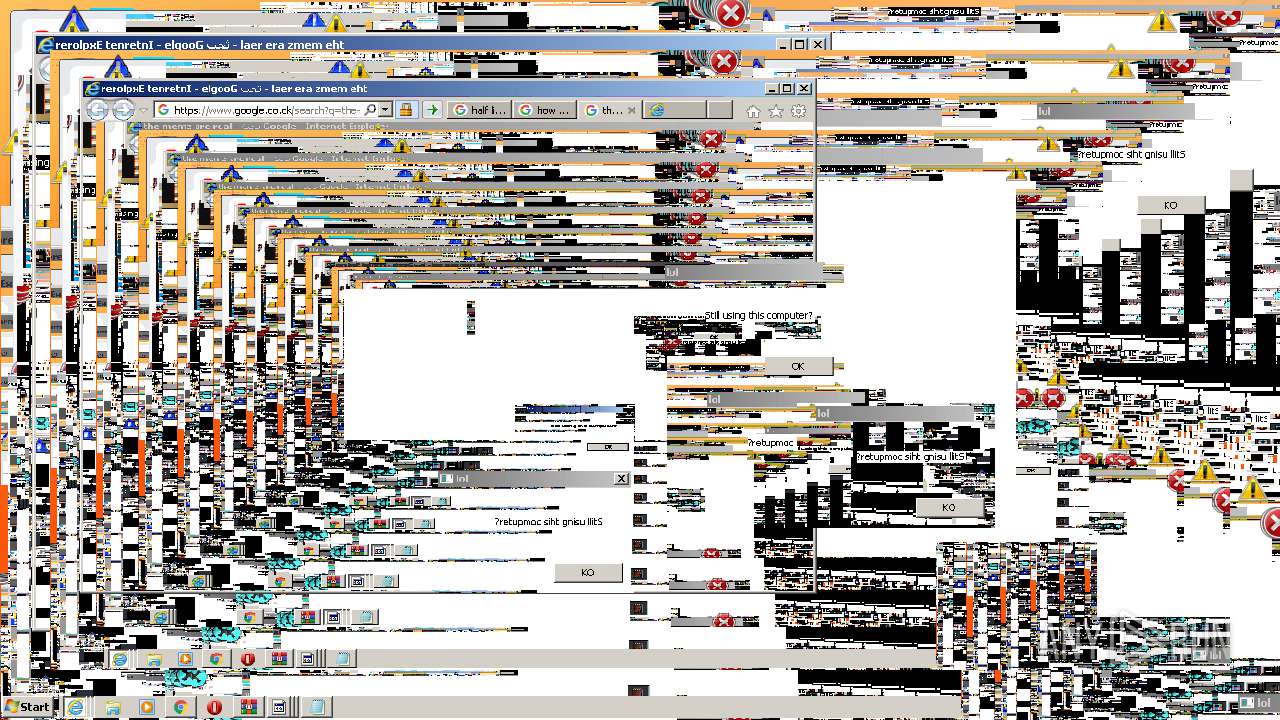
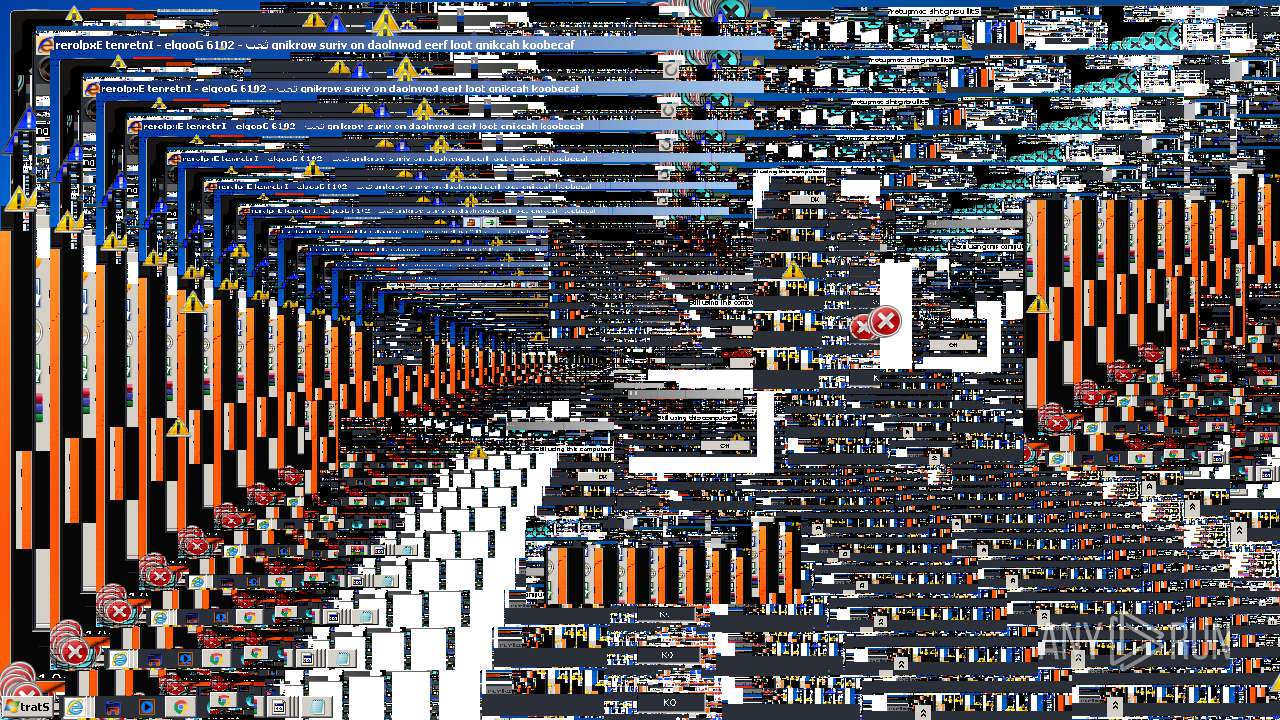
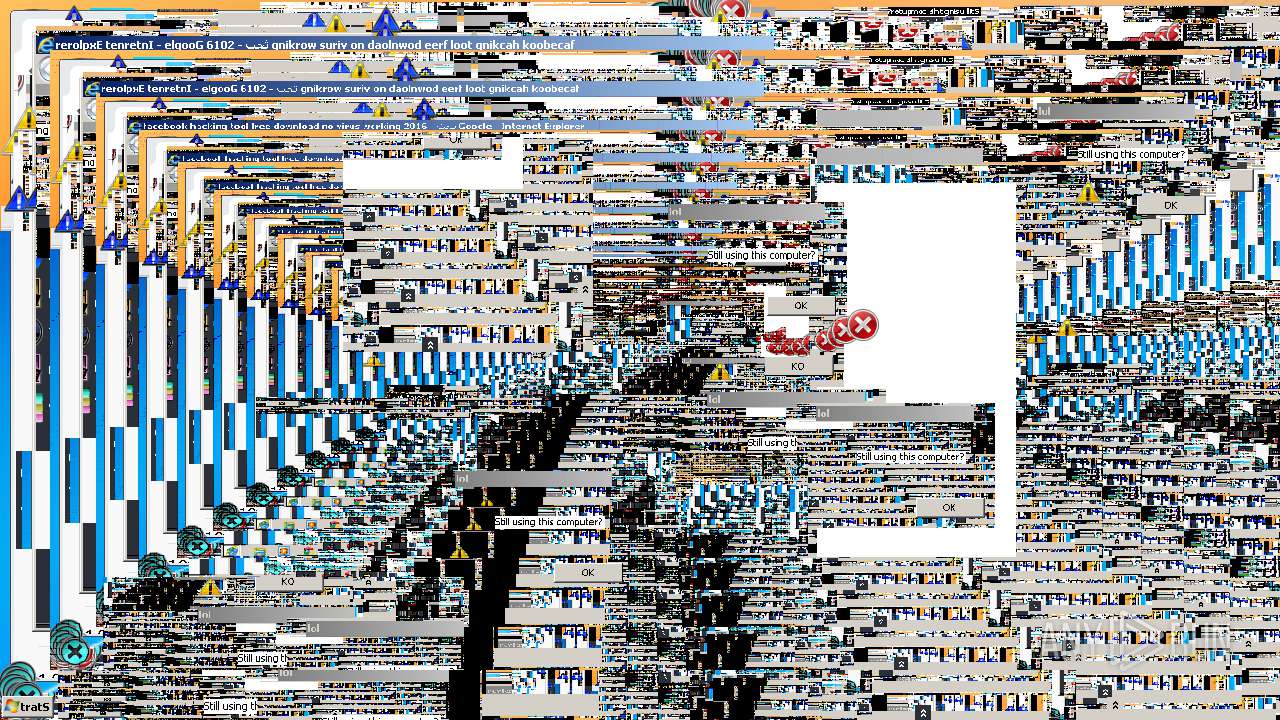
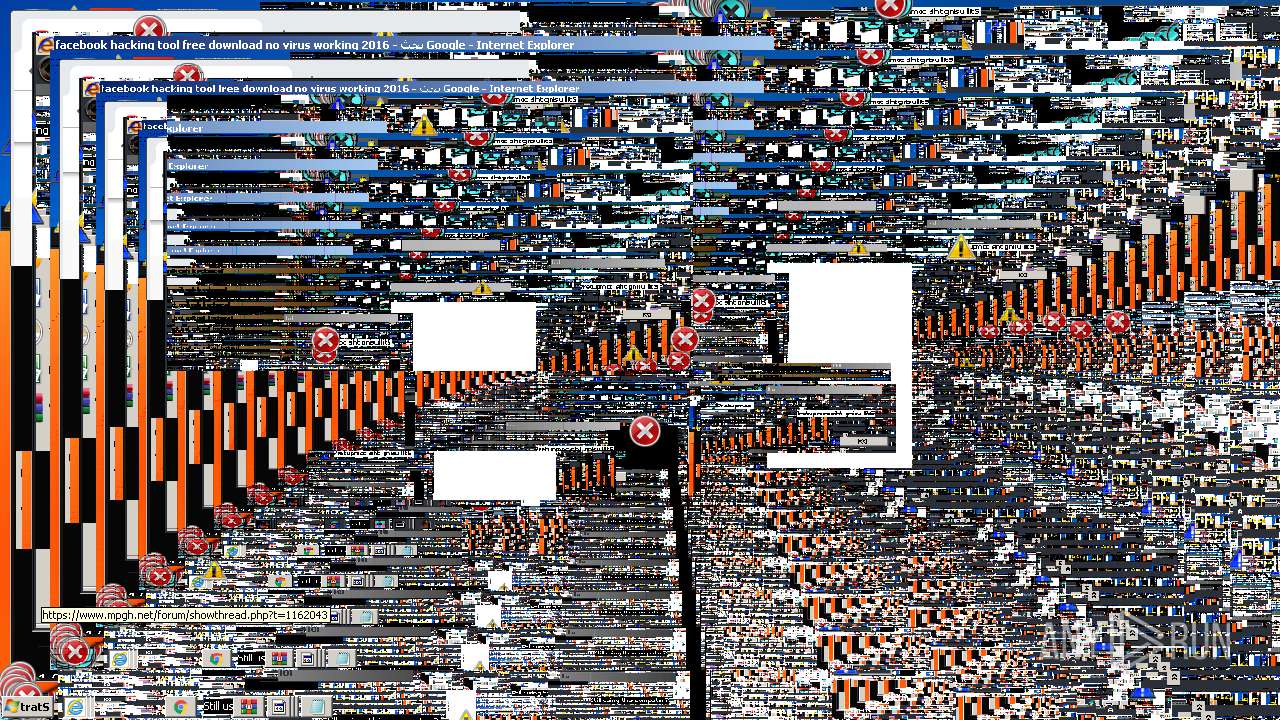
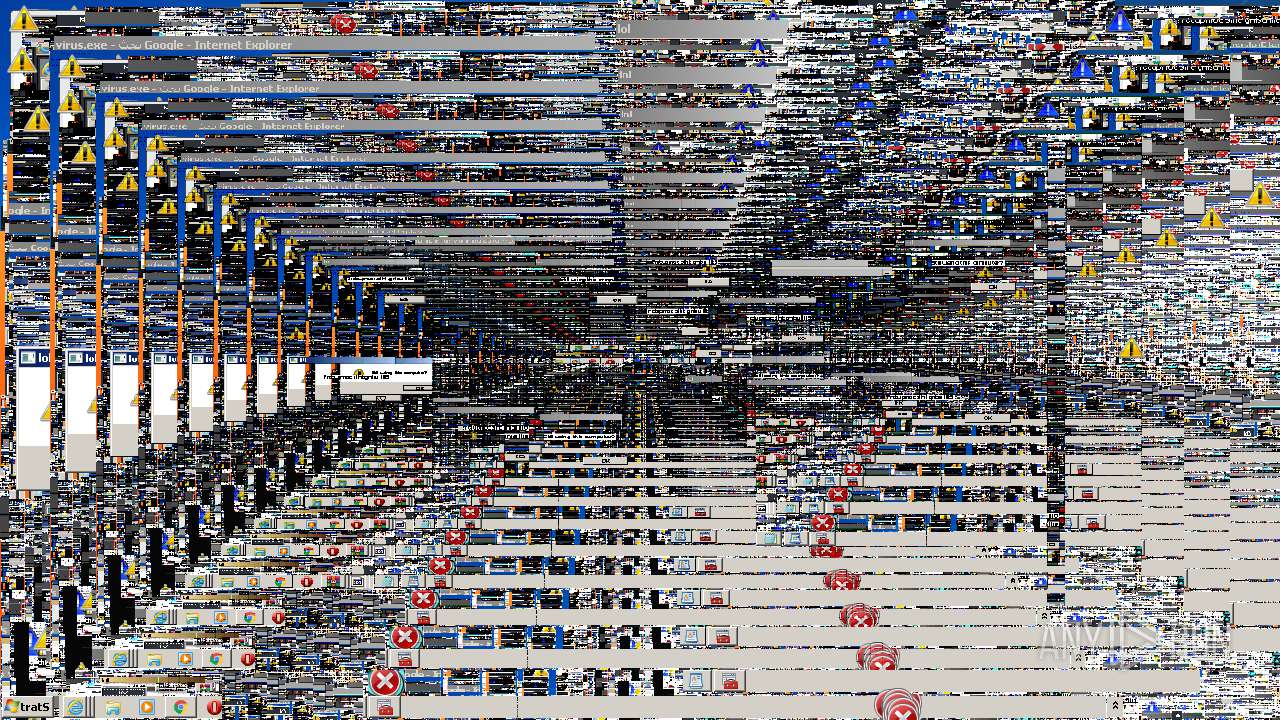
Starts Internet Explorer
- rundll32.exe (PID: 2780)
- MEMZ-Clean.exe (PID: 2268)
Executable content was dropped or overwritten
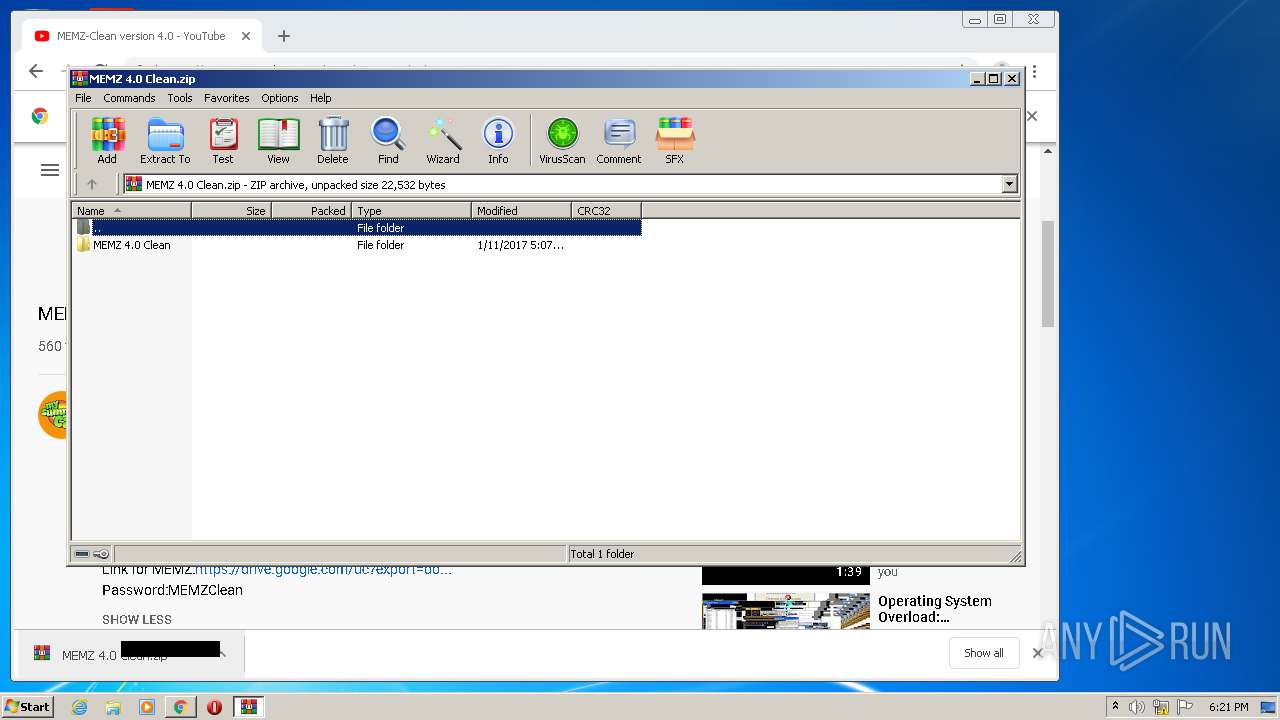
- WinRAR.exe (PID: 3700)
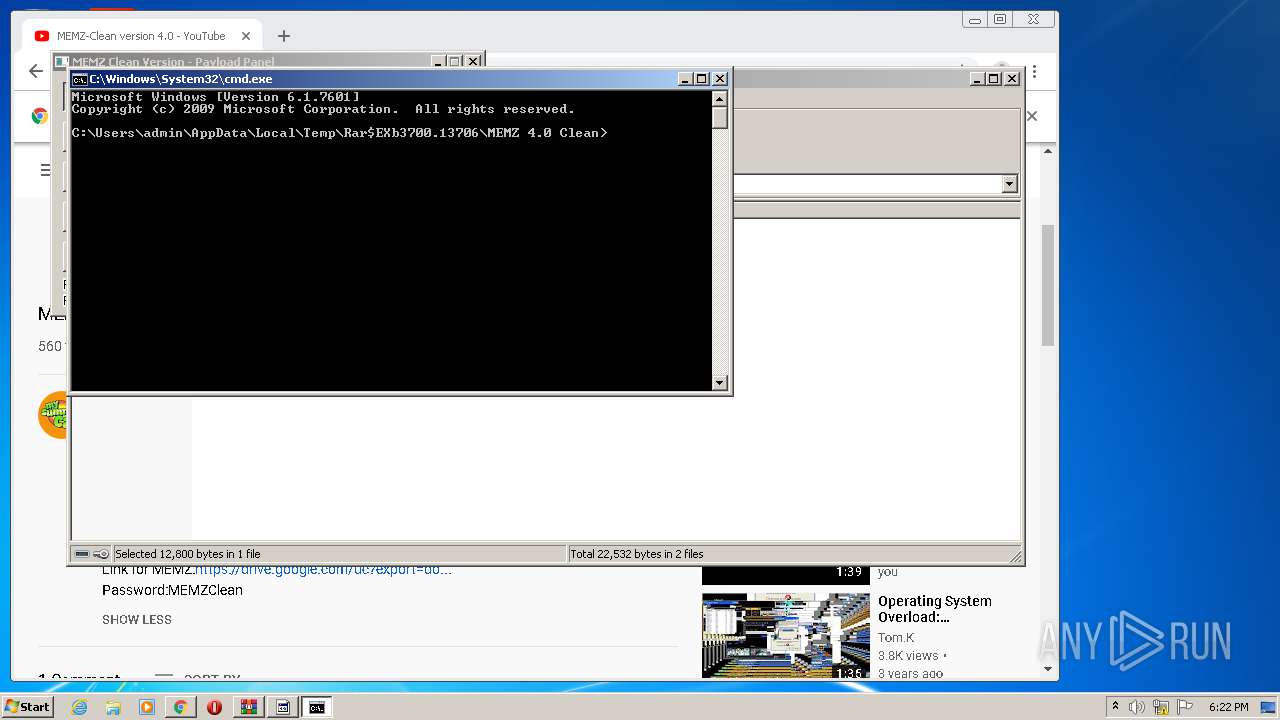
Starts CMD.EXE for commands execution
- MEMZ-Clean.exe (PID: 2268)
INFO
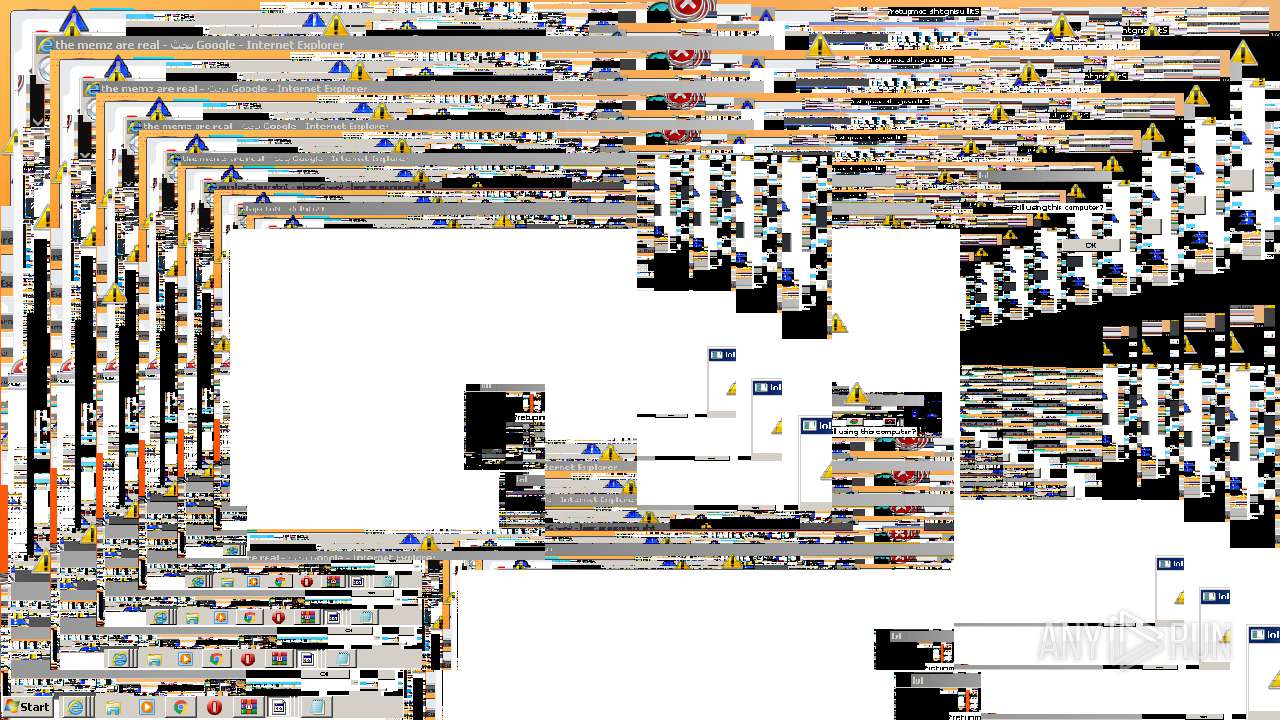
Reads Internet Cache Settings
- iexplore.exe (PID: 2652)
- iexplore.exe (PID: 2468)
- chrome.exe (PID: 2100)
- iexplore.exe (PID: 2196)
- iexplore.exe (PID: 2188)
- iexplore.exe (PID: 2556)
- iexplore.exe (PID: 2976)
- iexplore.exe (PID: 1824)
- iexplore.exe (PID: 2668)
- iexplore.exe (PID: 1460)
- iexplore.exe (PID: 2432)
Changes internet zones settings
- iexplore.exe (PID: 2468)
- iexplore.exe (PID: 2196)
Changes settings of System certificates
- iexplore.exe (PID: 2468)
- iexplore.exe (PID: 2196)
Reads settings of System Certificates
- iexplore.exe (PID: 2652)
- iexplore.exe (PID: 2468)
- chrome.exe (PID: 2456)
- iexplore.exe (PID: 2196)
Creates files in the user directory
- iexplore.exe (PID: 2652)
- iexplore.exe (PID: 2188)
- iexplore.exe (PID: 2976)
- iexplore.exe (PID: 2556)
- iexplore.exe (PID: 1824)
- iexplore.exe (PID: 2668)
- iexplore.exe (PID: 2196)
- iexplore.exe (PID: 1460)
- iexplore.exe (PID: 2432)
Application launched itself
- iexplore.exe (PID: 2468)
- chrome.exe (PID: 2100)
- iexplore.exe (PID: 2196)
Reads internet explorer settings
- iexplore.exe (PID: 2652)
- iexplore.exe (PID: 2188)
- iexplore.exe (PID: 2976)
- iexplore.exe (PID: 2556)
- iexplore.exe (PID: 1824)
- iexplore.exe (PID: 2432)
- iexplore.exe (PID: 2668)
- iexplore.exe (PID: 1460)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2468)
- iexplore.exe (PID: 2196)
Reads the hosts file
- chrome.exe (PID: 2456)
- chrome.exe (PID: 2100)
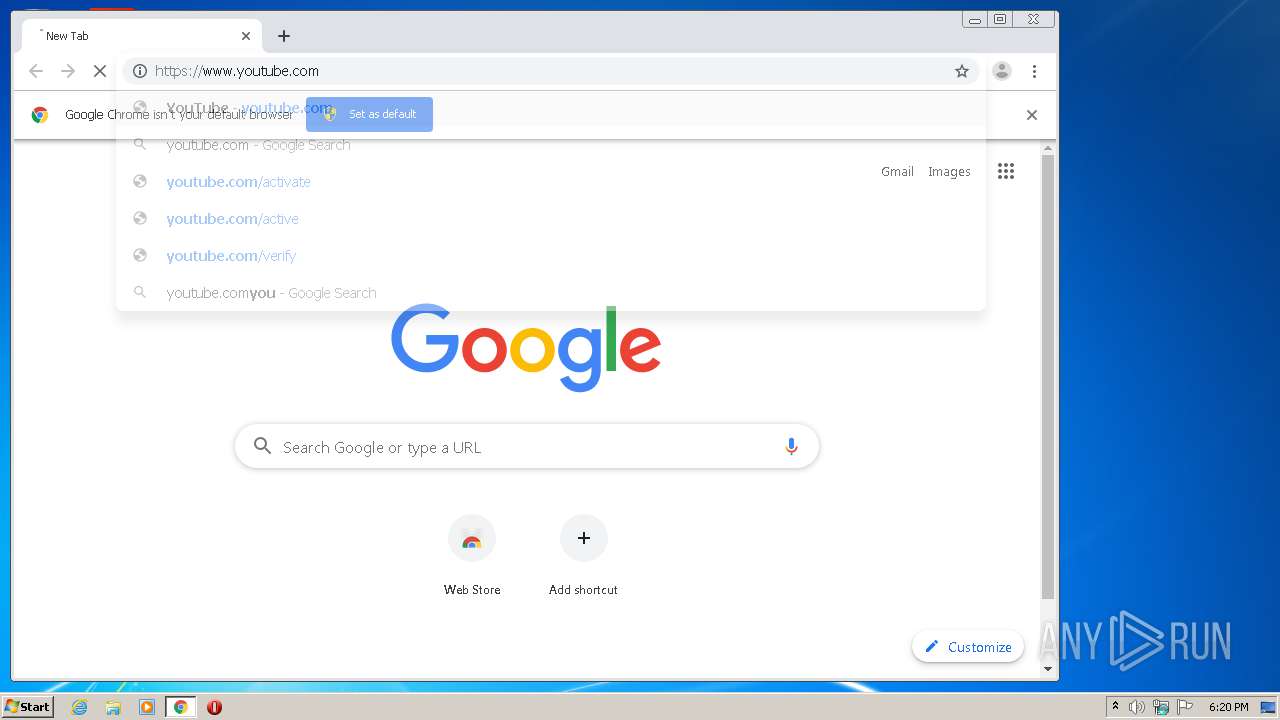
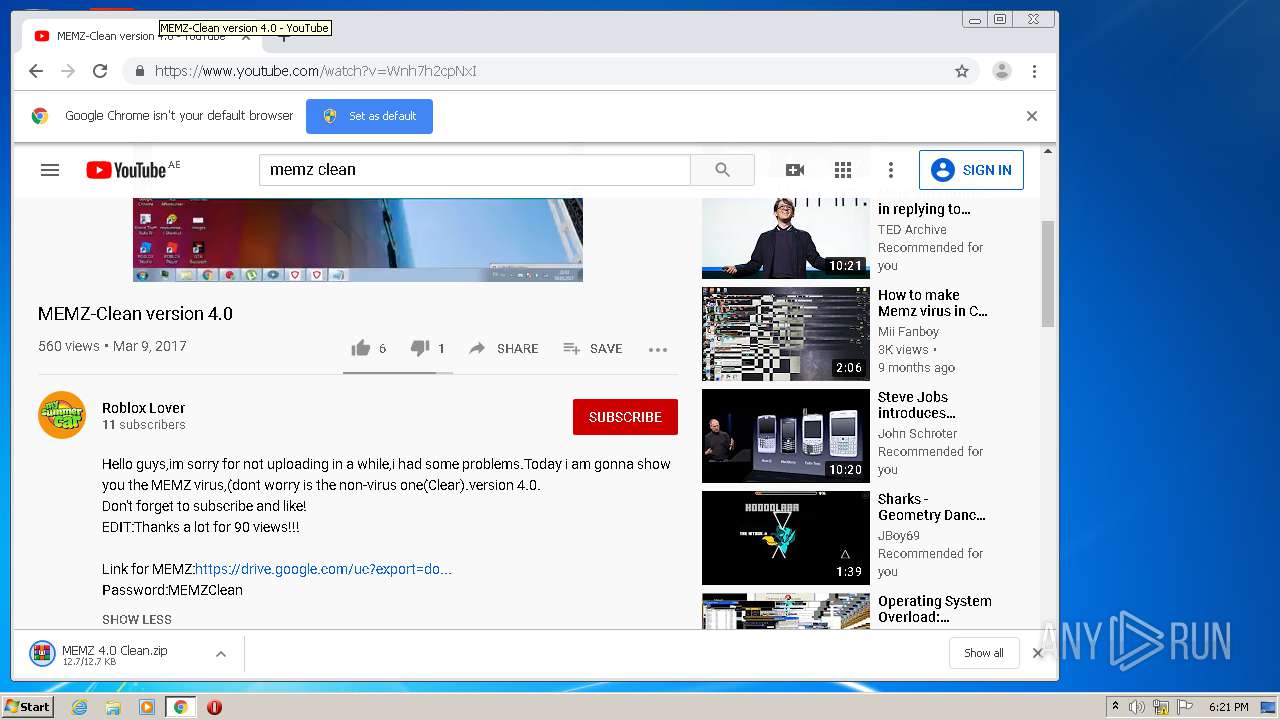
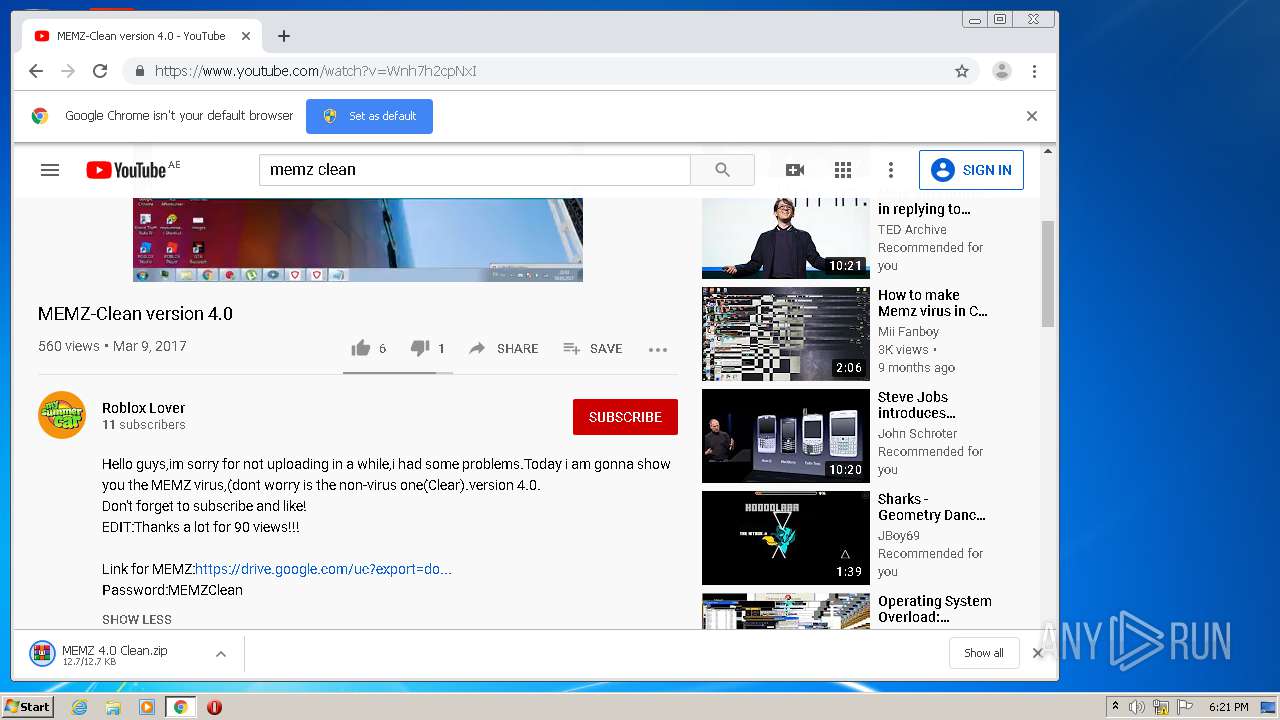
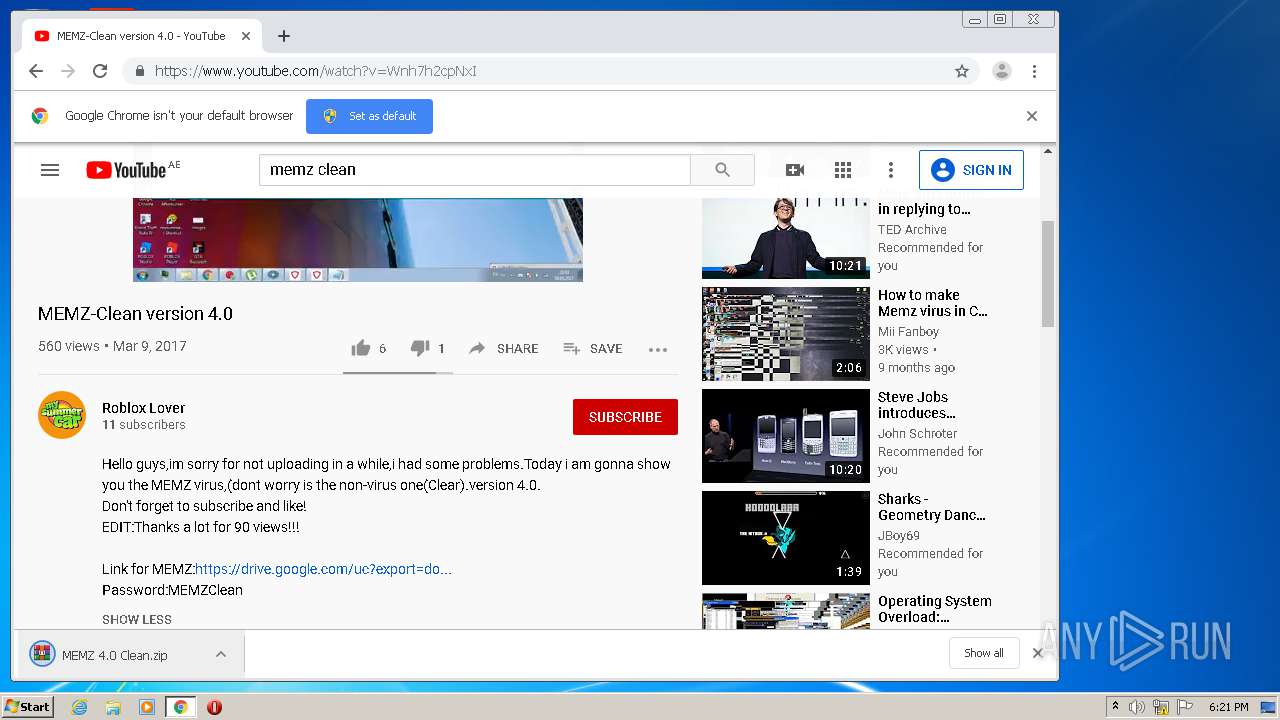
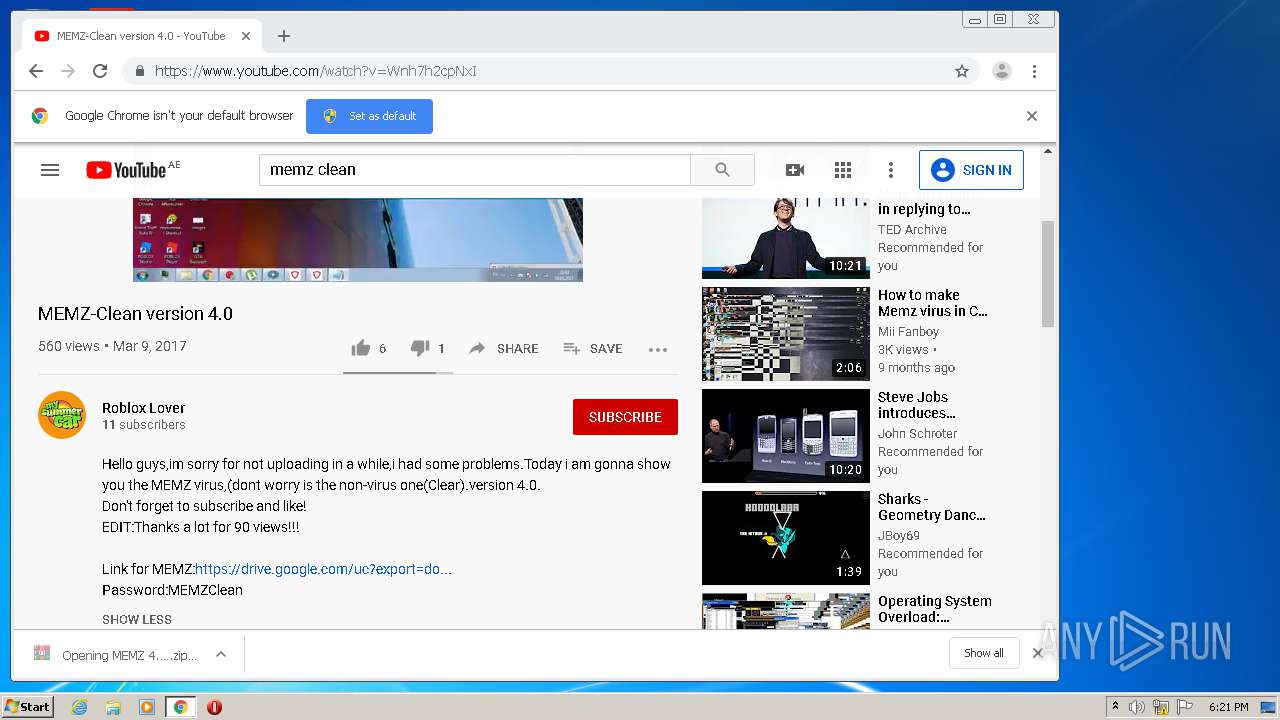
Manual execution by user
- chrome.exe (PID: 2100)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .xml | | | Generic XML (ASCII) (100) |
|---|
EXIF
XMP
| VirtualBoxXmlns: | http://www.virtualbox.org/ |
|---|---|
| VirtualBoxVersion: | 1.15-windows |
| VirtualBoxMachineUuid: | {8119f33c-9776-49ba-9278-2d98c4d0ff2b} |
| VirtualBoxMachineName: | Microsoft Windows XP |
| VirtualBoxMachineOSType: | WindowsXP |
| VirtualBoxMachineSnapshotFolder: | Snapshots |
| VirtualBoxMachineLastStateChange: | 2019:12:30 04:35:29Z |
| VirtualBoxMachineExtraDataExtraDataItemName: | GUI/LastCloseAction |
| VirtualBoxMachineExtraDataExtraDataItemValue: | PowerOff |
| VirtualBoxMachineHardwareCpuPaeEnabled: | - |
| VirtualBoxMachineHardwareCpuLongModeEnabled: | - |
| VirtualBoxMachineHardwareCpuHardwareVirtExLargePagesEnabled: | |
| VirtualBoxMachineHardwareMemoryRAMSize: | 1216 |
| VirtualBoxMachineHardwareHidPointing: | USBTablet |
| VirtualBoxMachineHardwareParavirtProvider: | Default |
| VirtualBoxMachineHardwareDisplayVRAMSize: | 18 |
| VirtualBoxMachineHardwareVideoCaptureScreens: | 1 |
| VirtualBoxMachineHardwareVideoCaptureFile: | . |
| VirtualBoxMachineHardwareVideoCaptureFps: | 25 |
| VirtualBoxMachineHardwareRemoteDisplayEnabled: | - |
| VirtualBoxMachineHardwareBiosSmbiosUuidLittleEndianEnabled: | |
| VirtualBoxMachineHardwareUsbControllersControllerName: | OHCI |
| VirtualBoxMachineHardwareUsbControllersControllerType: | OHCI |
| VirtualBoxMachineHardwareNetworkAdapterSlot: | - |
| VirtualBoxMachineHardwareNetworkAdapterEnabled: | |
| VirtualBoxMachineHardwareNetworkAdapterMACAddress: | 080027ADA8FD |
| VirtualBoxMachineHardwareNetworkAdapterCable: | |
| VirtualBoxMachineHardwareNetworkAdapterType: | 82543GC |
| VirtualBoxMachineHardwareNetworkAdapterNat: | - |
| VirtualBoxMachineHardwareAudioAdapterDriver: | DirectSound |
| VirtualBoxMachineHardwareAudioAdapterEnabled: | |
| VirtualBoxMachineHardwareAudioAdapterEnabledIn: | - |
| VirtualBoxMachineHardwareClipboard: | - |
| VirtualBoxMachineHardwareGuestPropertiesGuestPropertyName: | /VirtualBox/HostInfo/GUI/LanguageID |
| VirtualBoxMachineHardwareGuestPropertiesGuestPropertyValue: | en_US |
| VirtualBoxMachineHardwareGuestPropertiesGuestPropertyTimestamp: | 1577680530240555300 |
| VirtualBoxMachineHardwareGuestPropertiesGuestPropertyFlags: | - |
| VirtualBoxMachineStorageControllersStorageControllerName: | IDE |
| VirtualBoxMachineStorageControllersStorageControllerType: | PIIX4 |
| VirtualBoxMachineStorageControllersStorageControllerPortCount: | 2 |
| VirtualBoxMachineStorageControllersStorageControllerUseHostIOCache: | |
| VirtualBoxMachineStorageControllersStorageControllerBootable: | |
| VirtualBoxMachineStorageControllersStorageControllerAttachedDevicePassthrough: | - |
| VirtualBoxMachineStorageControllersStorageControllerAttachedDeviceType: | DVD |
| VirtualBoxMachineStorageControllersStorageControllerAttachedDeviceHotpluggable: | - |
| VirtualBoxMachineStorageControllersStorageControllerAttachedDevicePort: | 1 |
| VirtualBoxMachineStorageControllersStorageControllerAttachedDeviceDevice: | - |
| VirtualBoxMachineStorageControllersStorageControllerAttachedDeviceImageUuid: | {6da10e50-4e21-46ce-951e-e1910420434b} |
Total processes
92
Monitored processes
43
Malicious processes
1
Suspicious processes
2
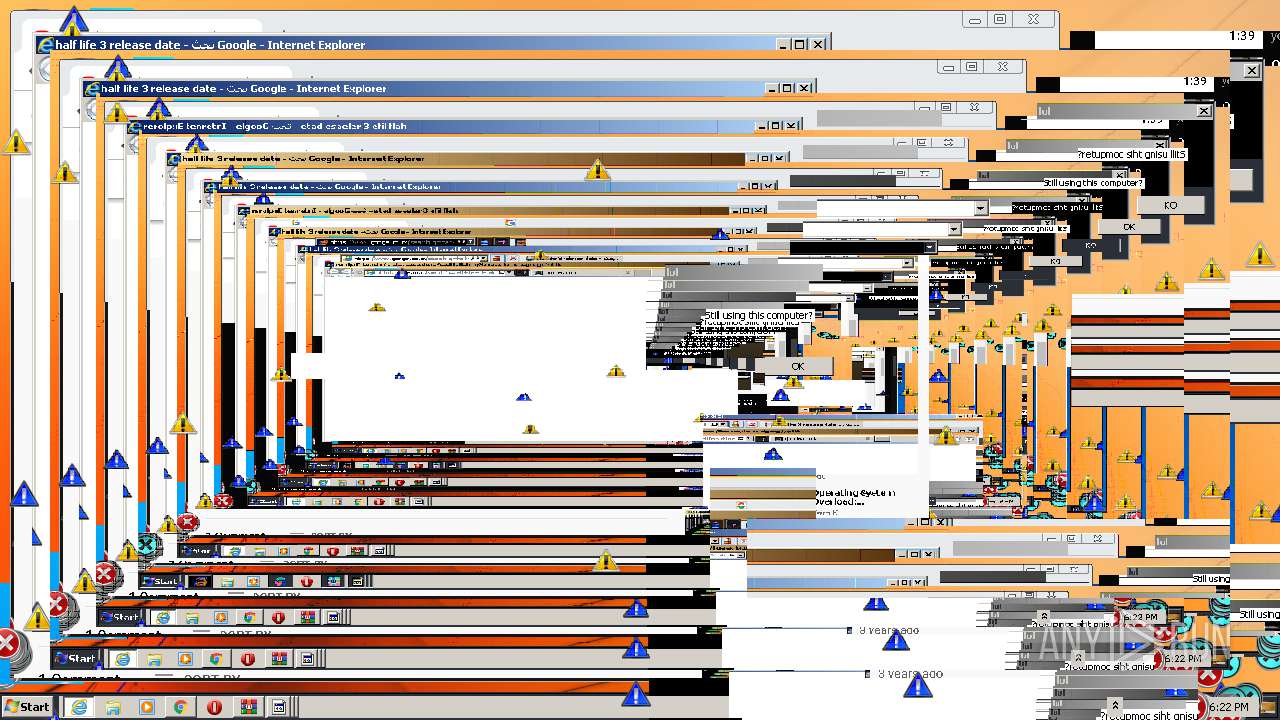
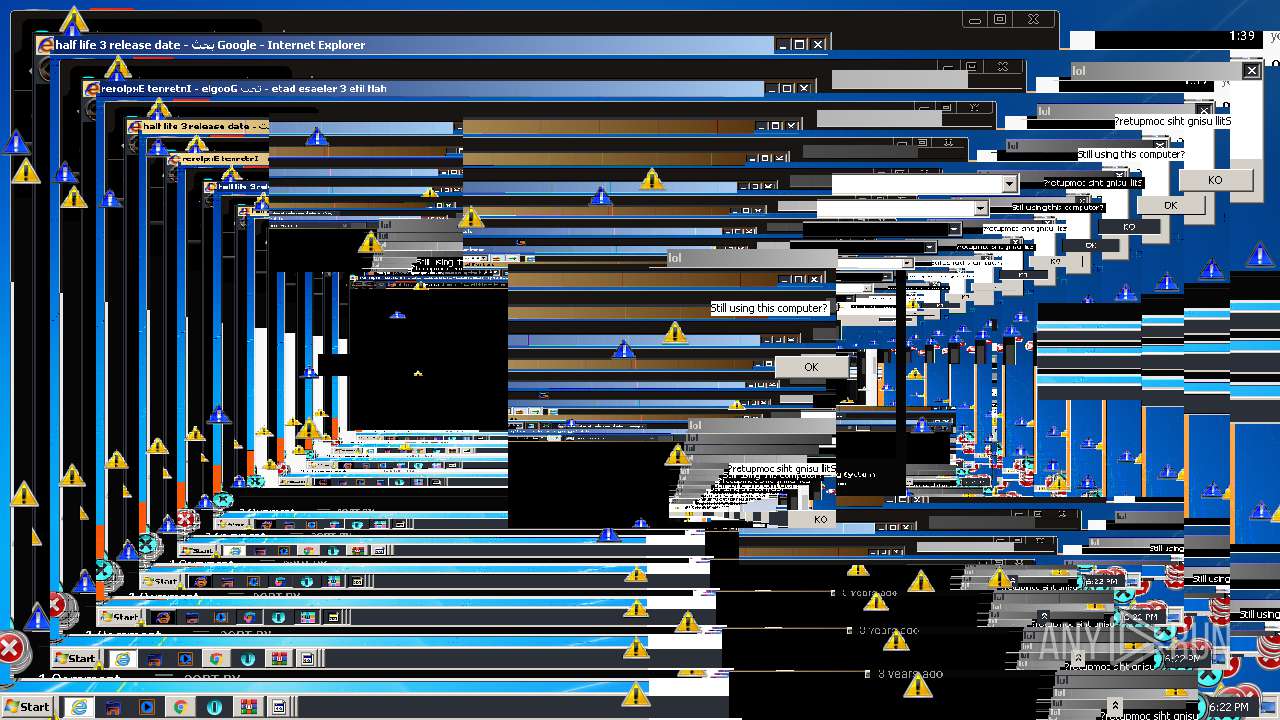
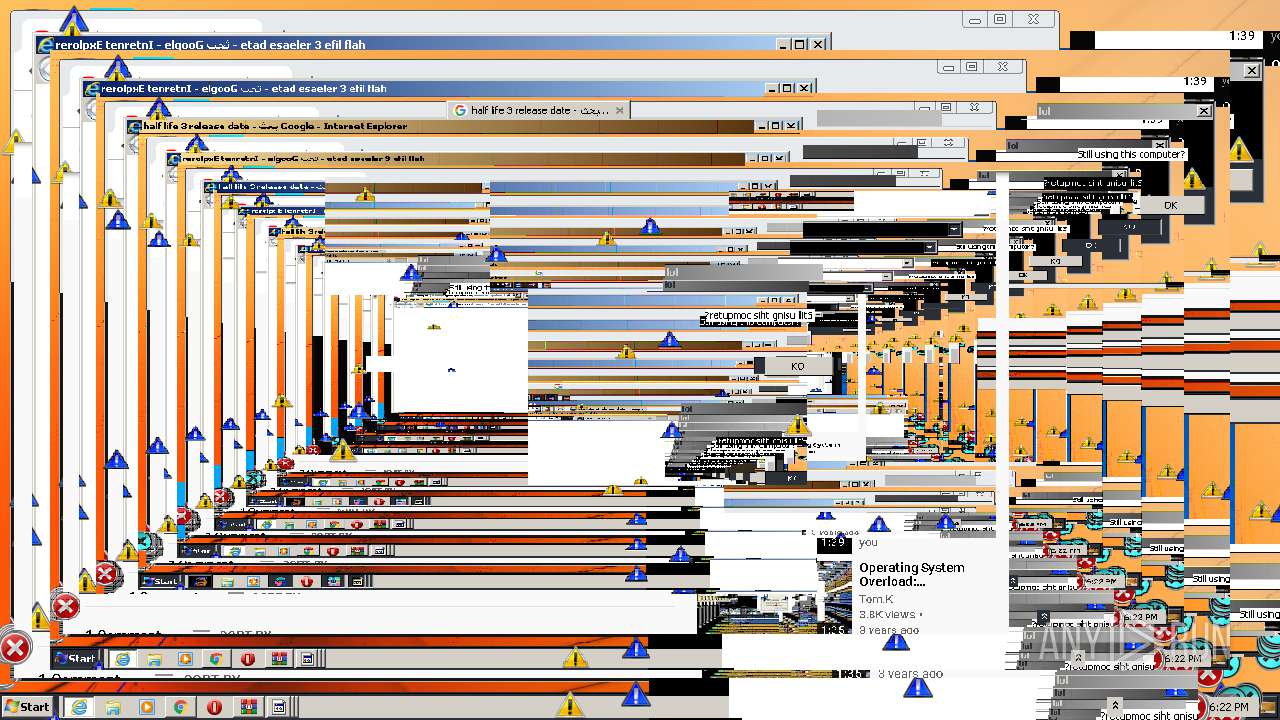
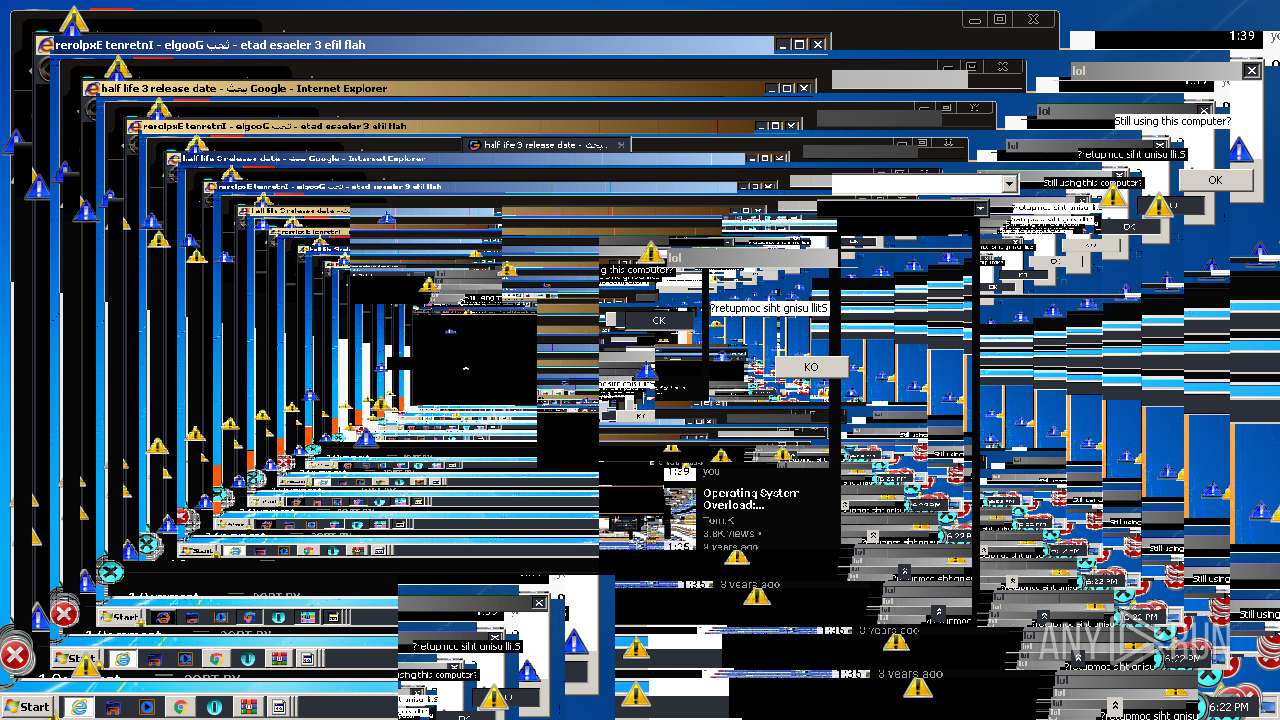
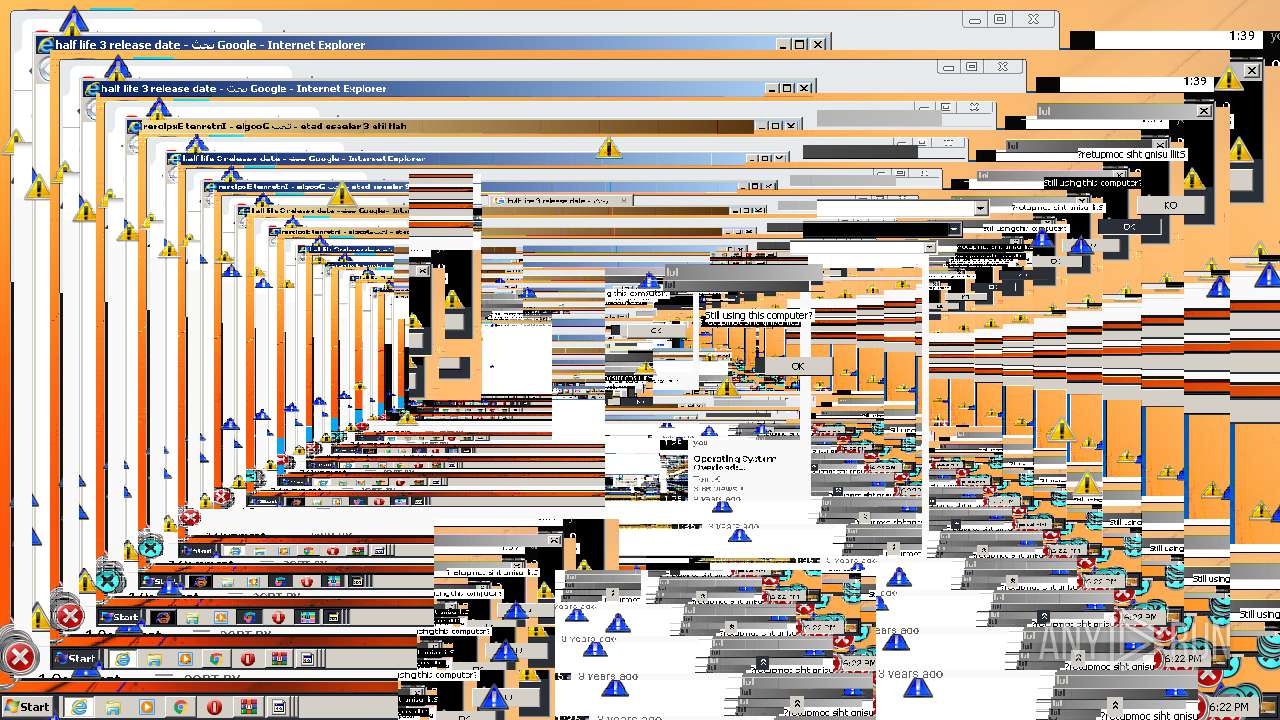
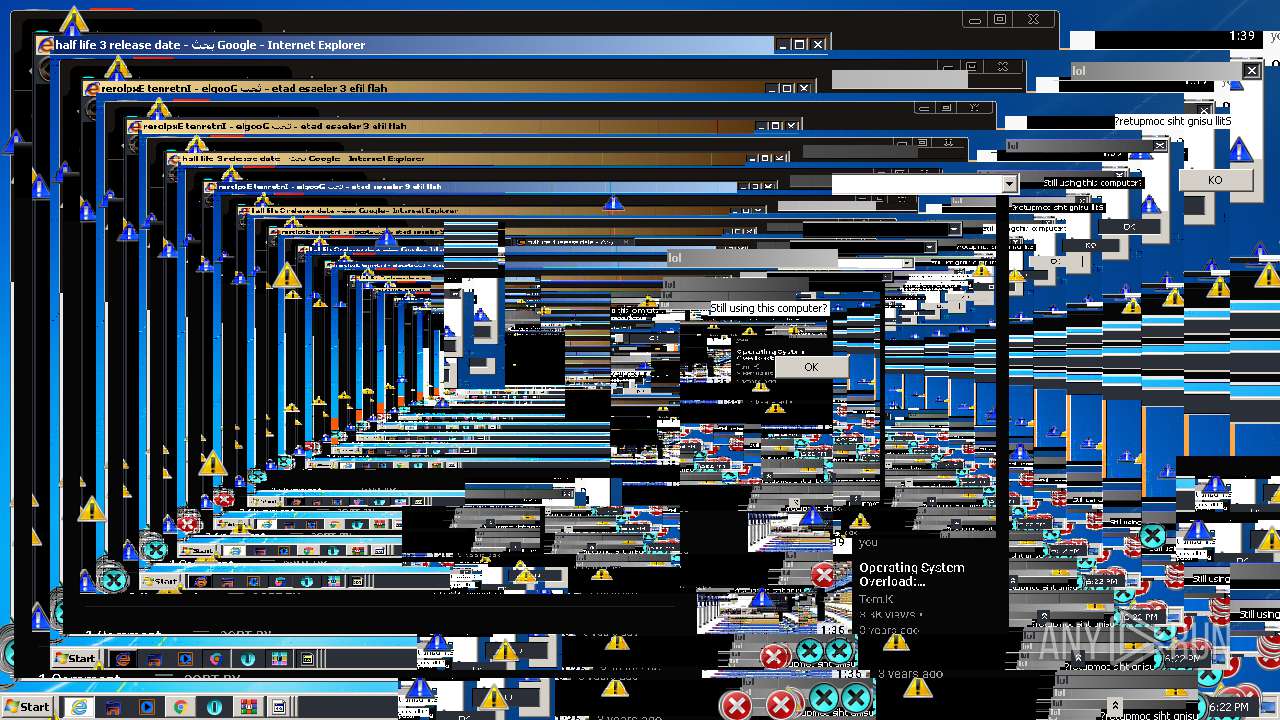
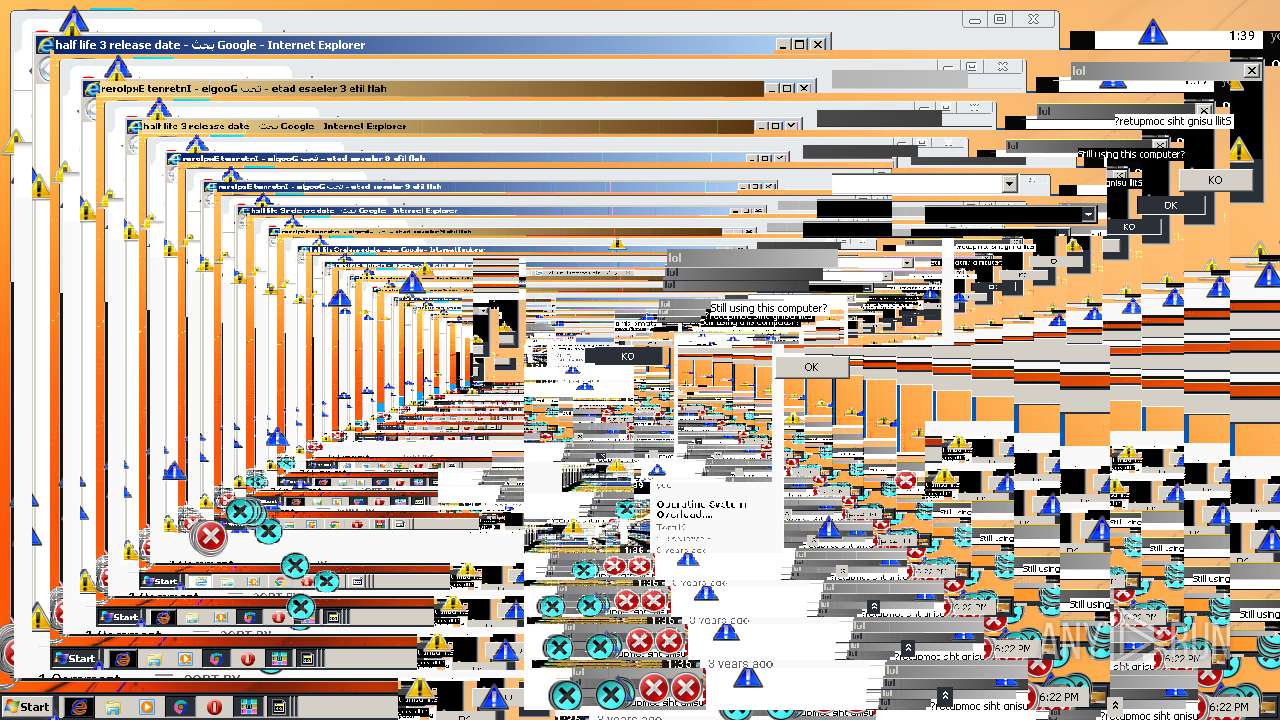
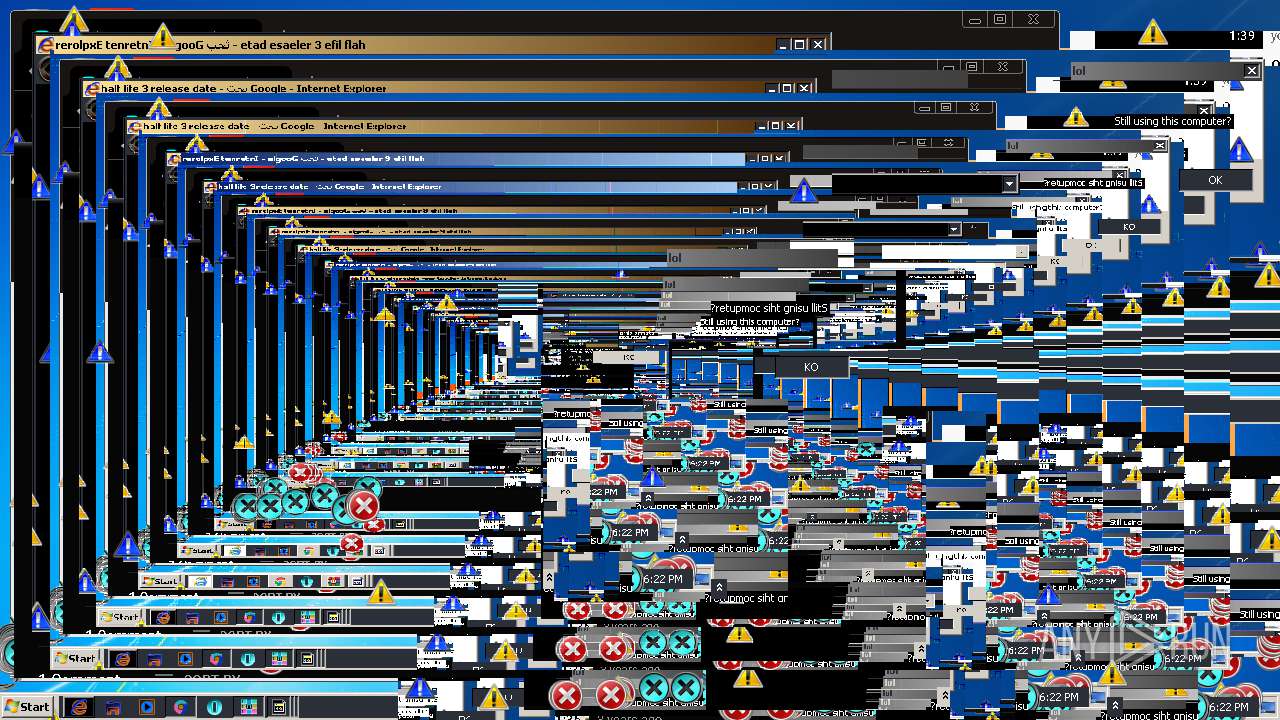
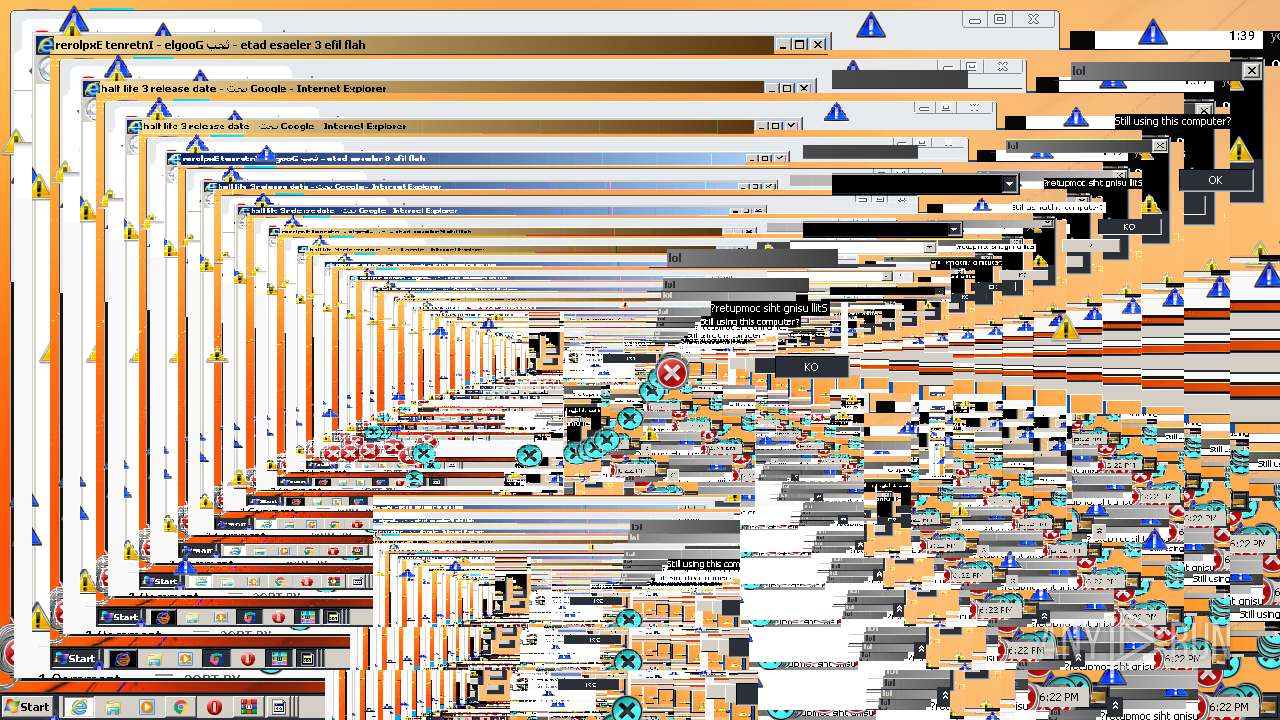
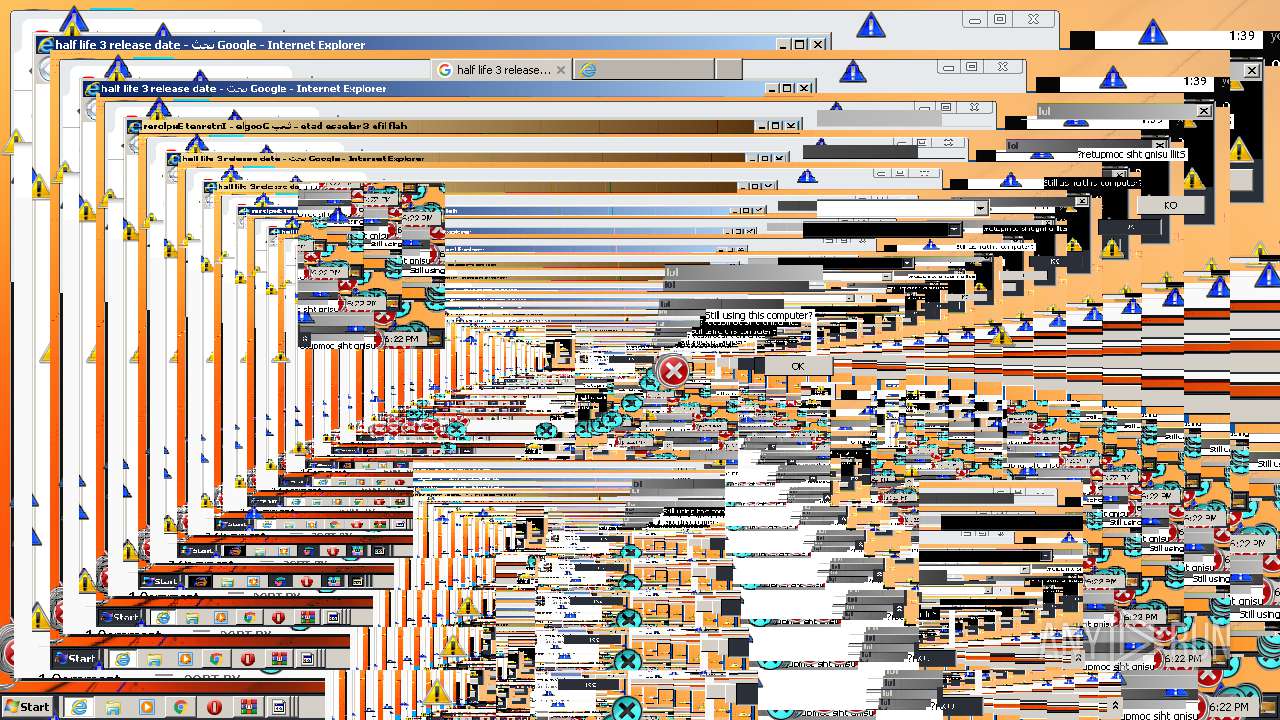
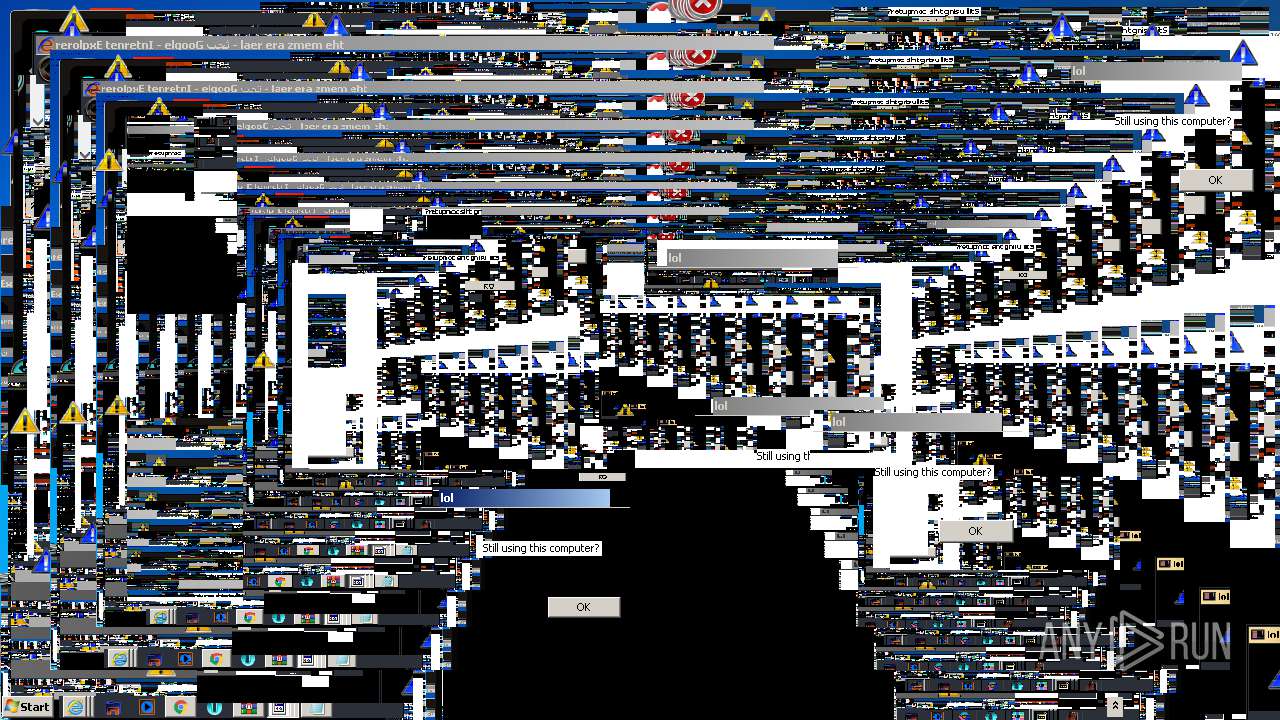
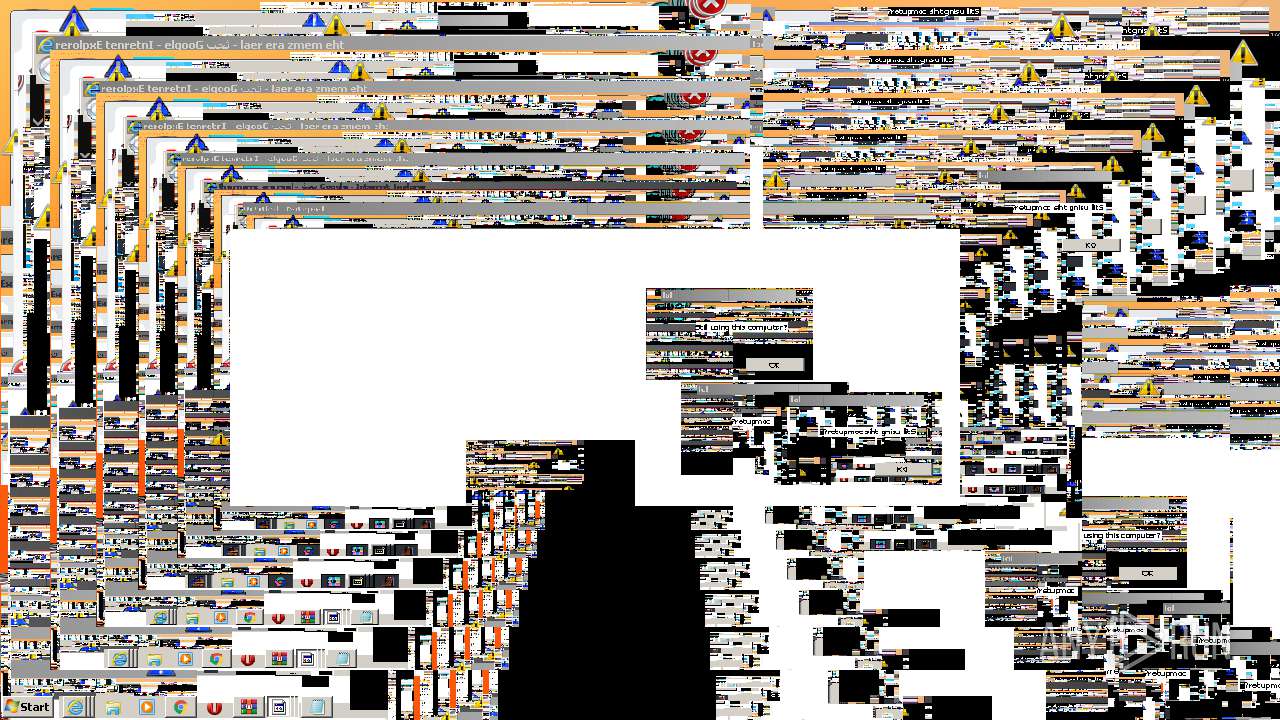
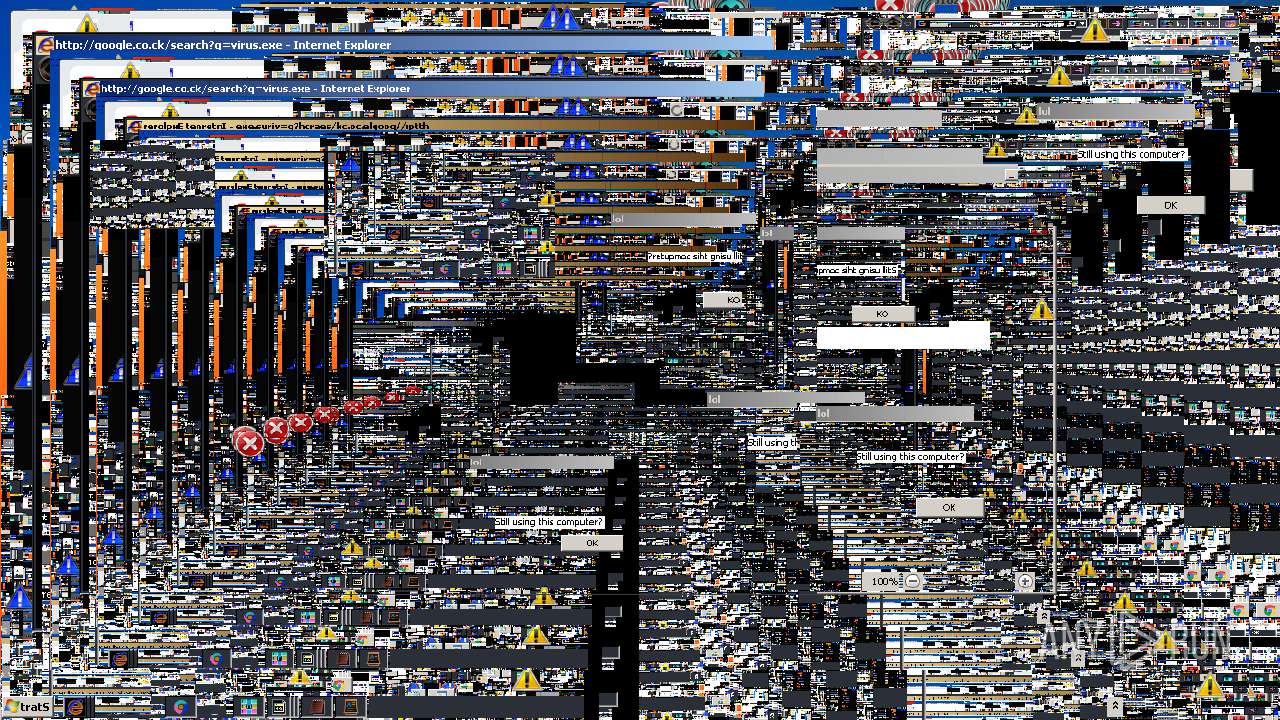
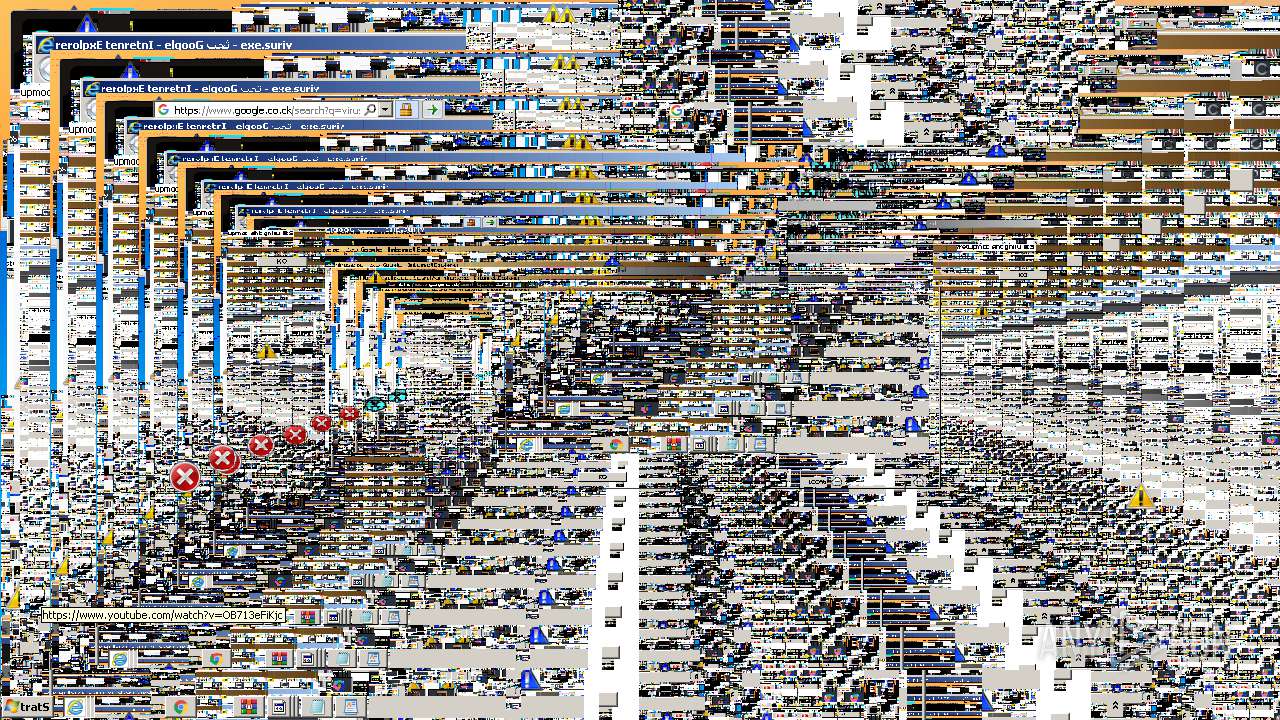
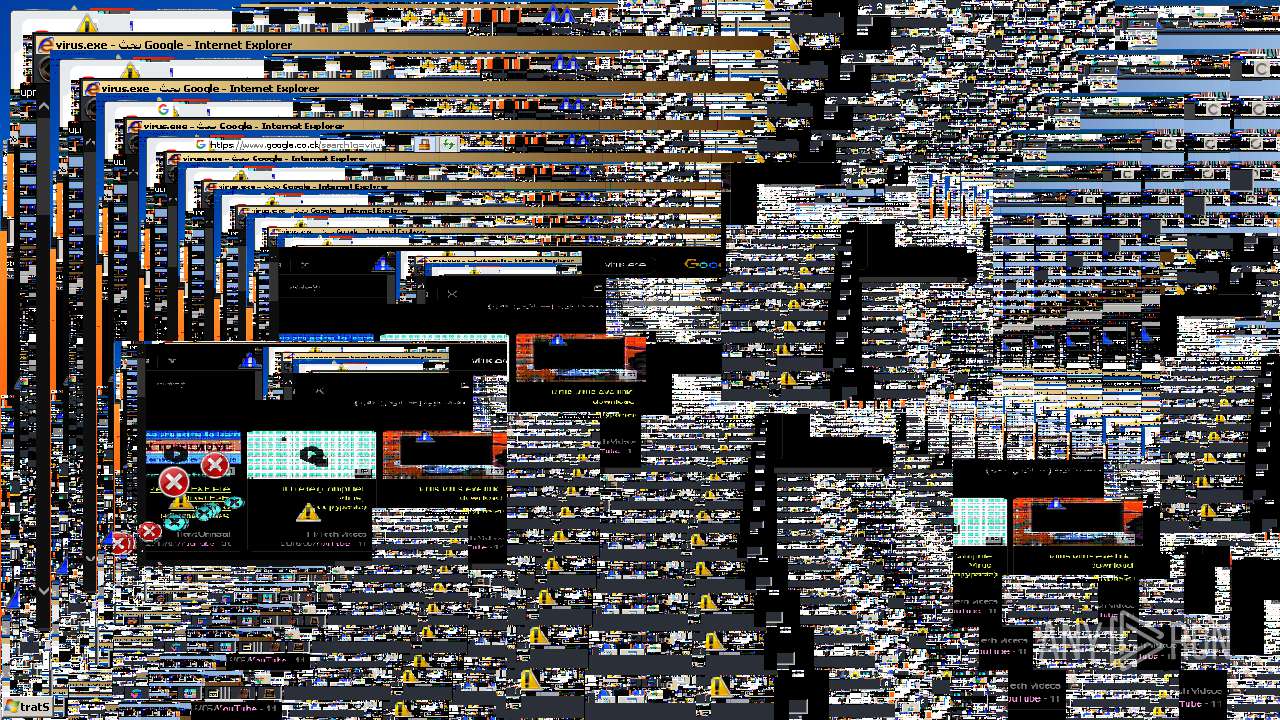
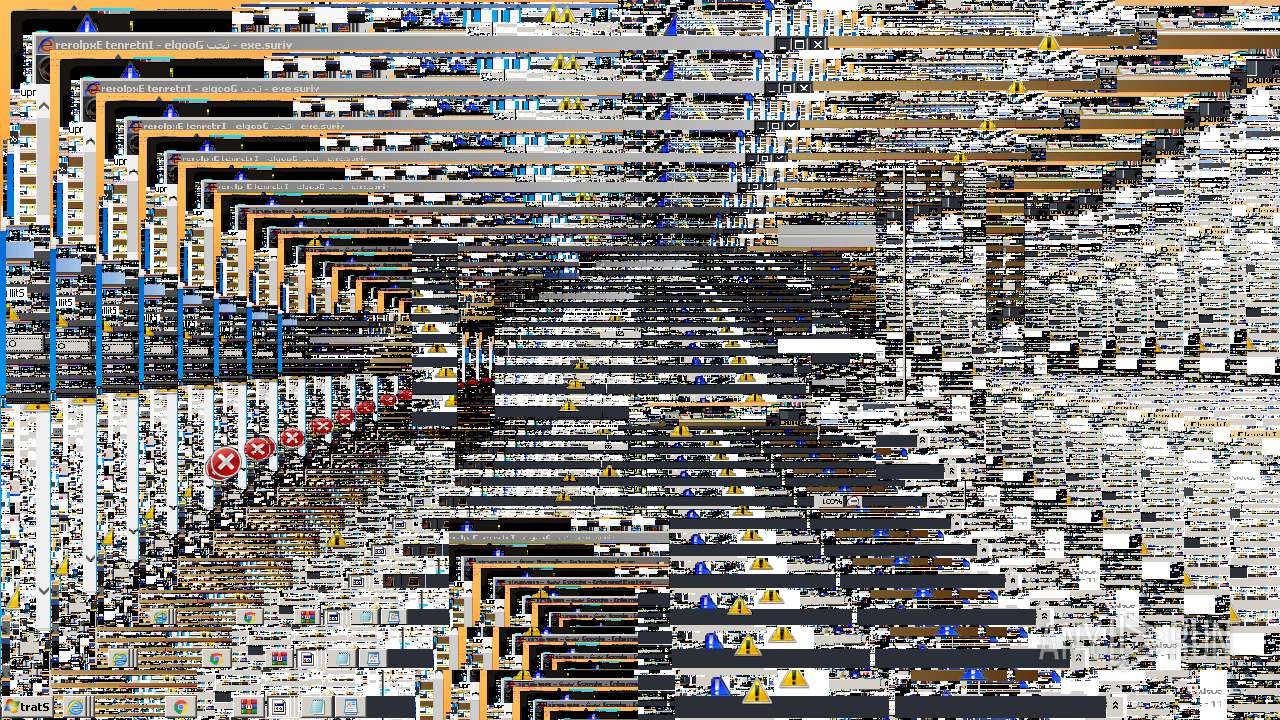
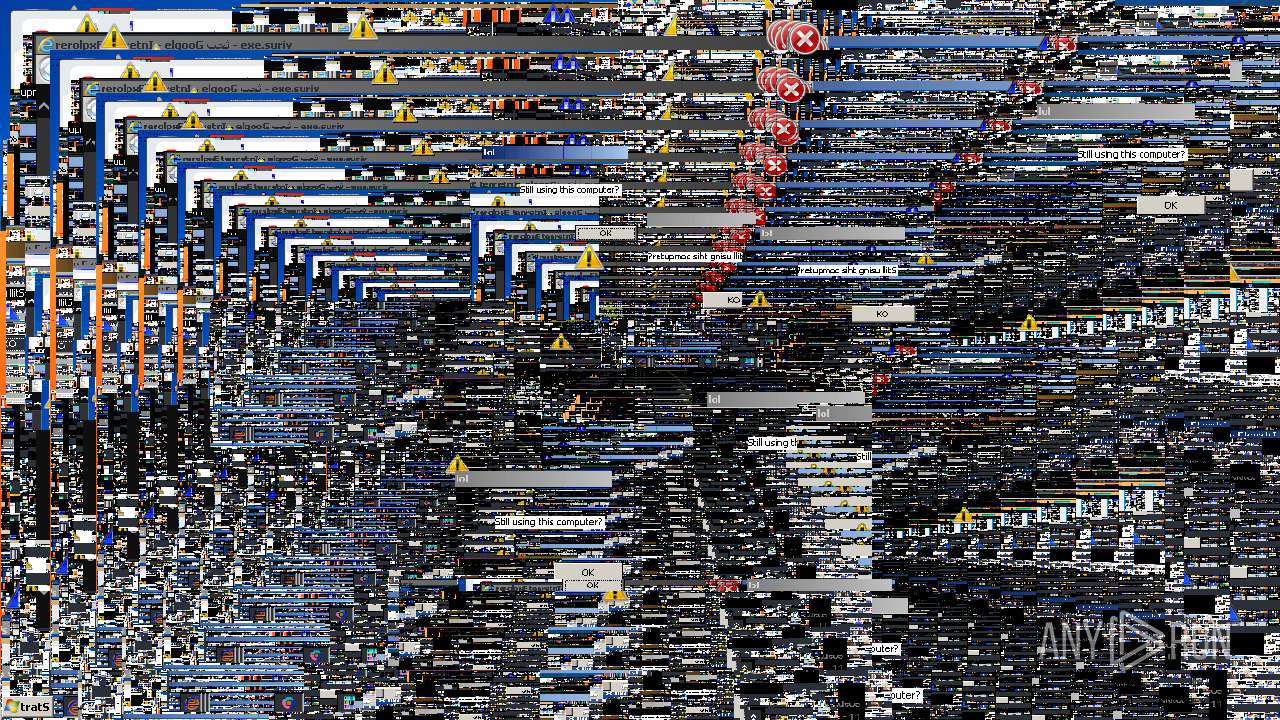
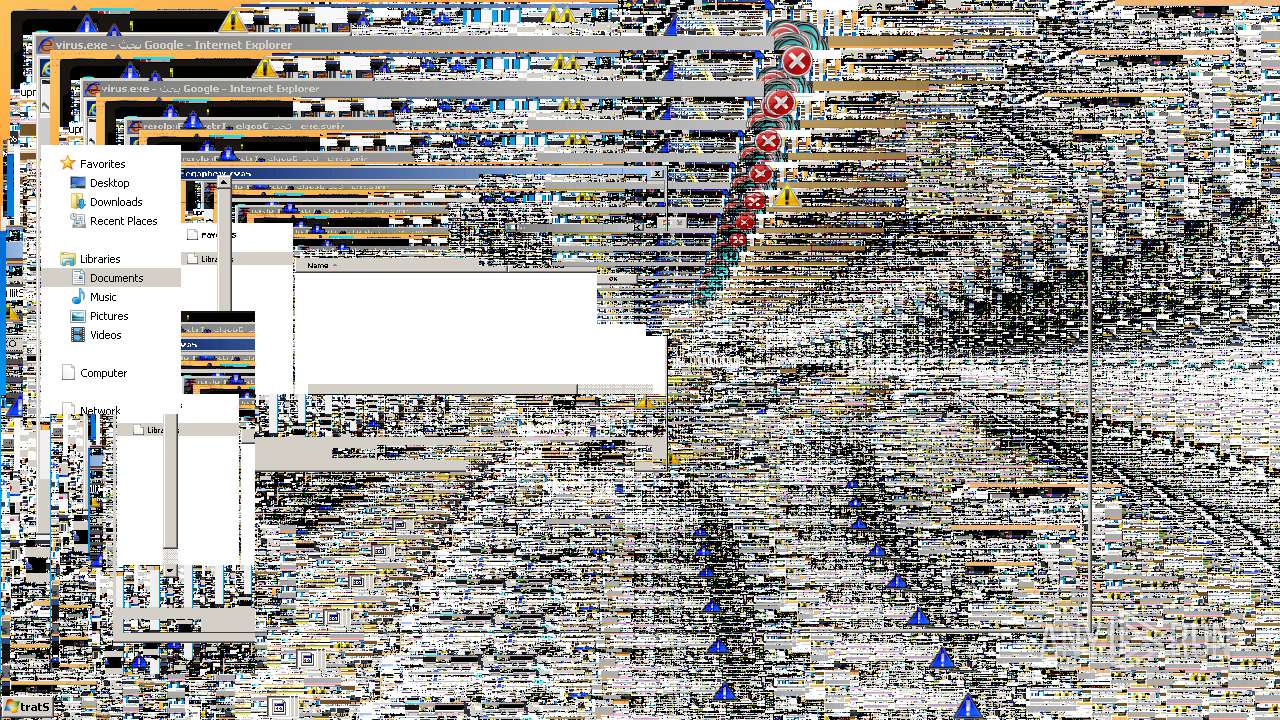
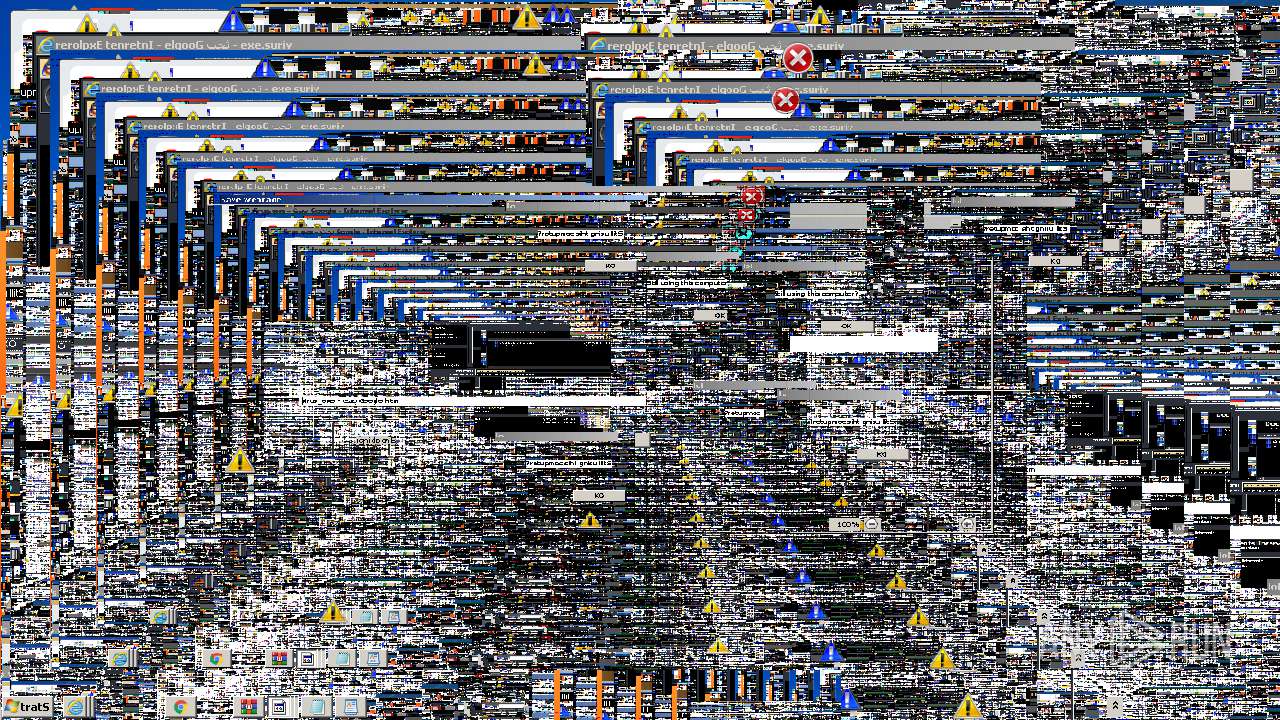
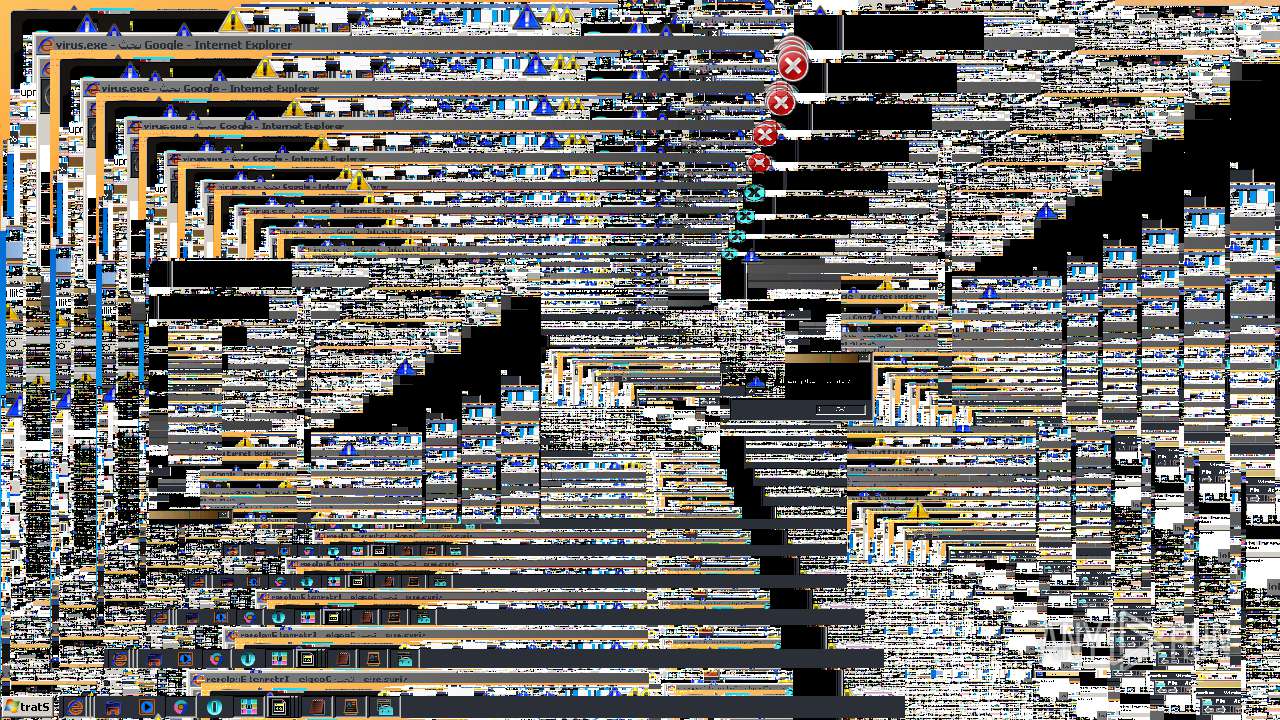
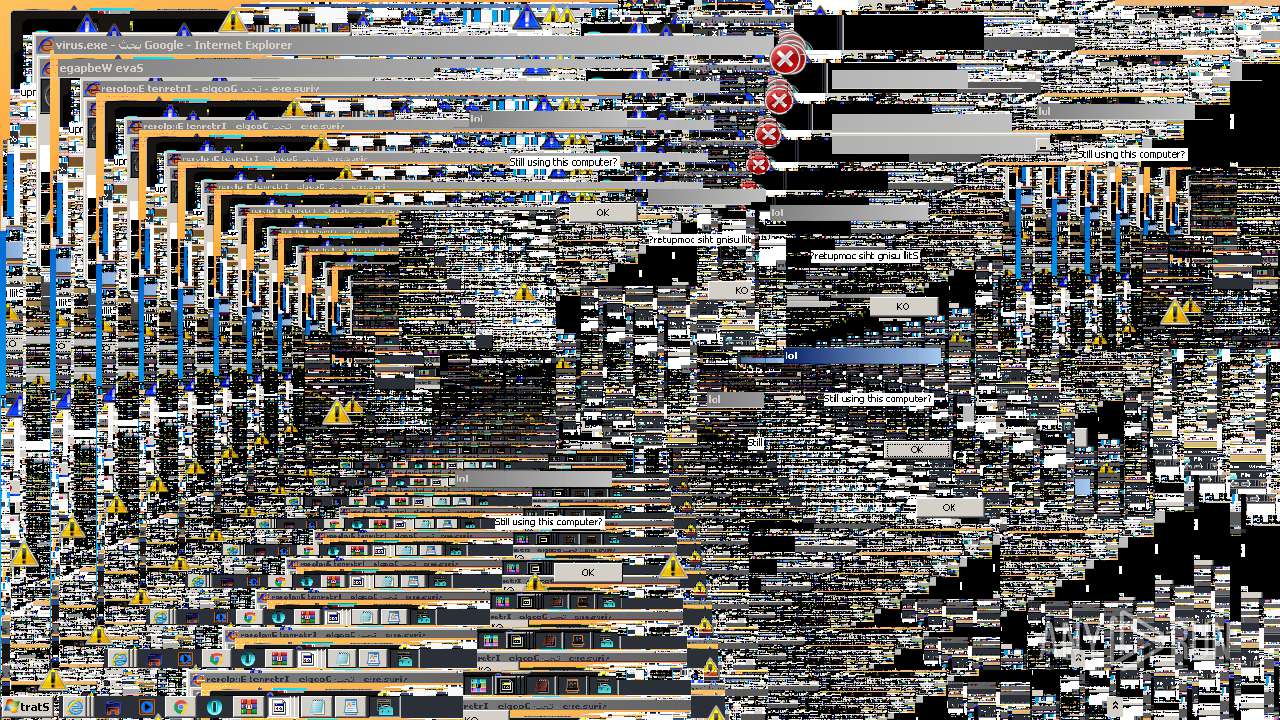
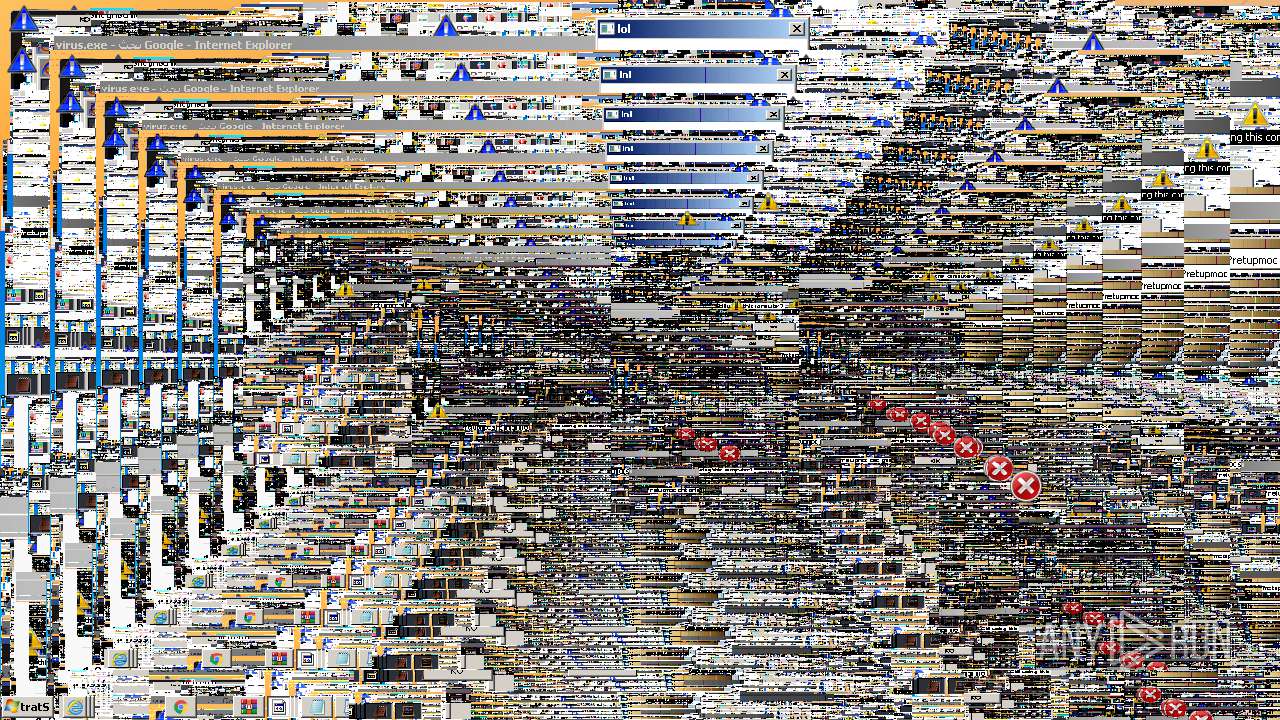
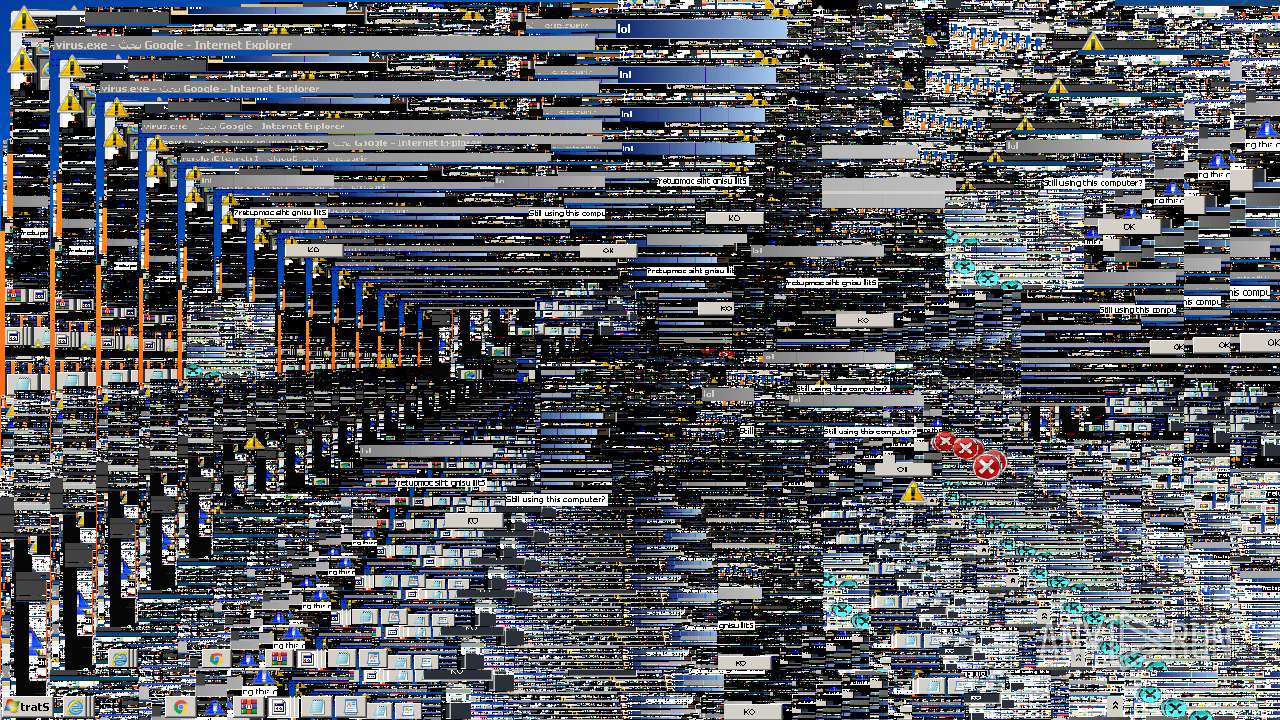
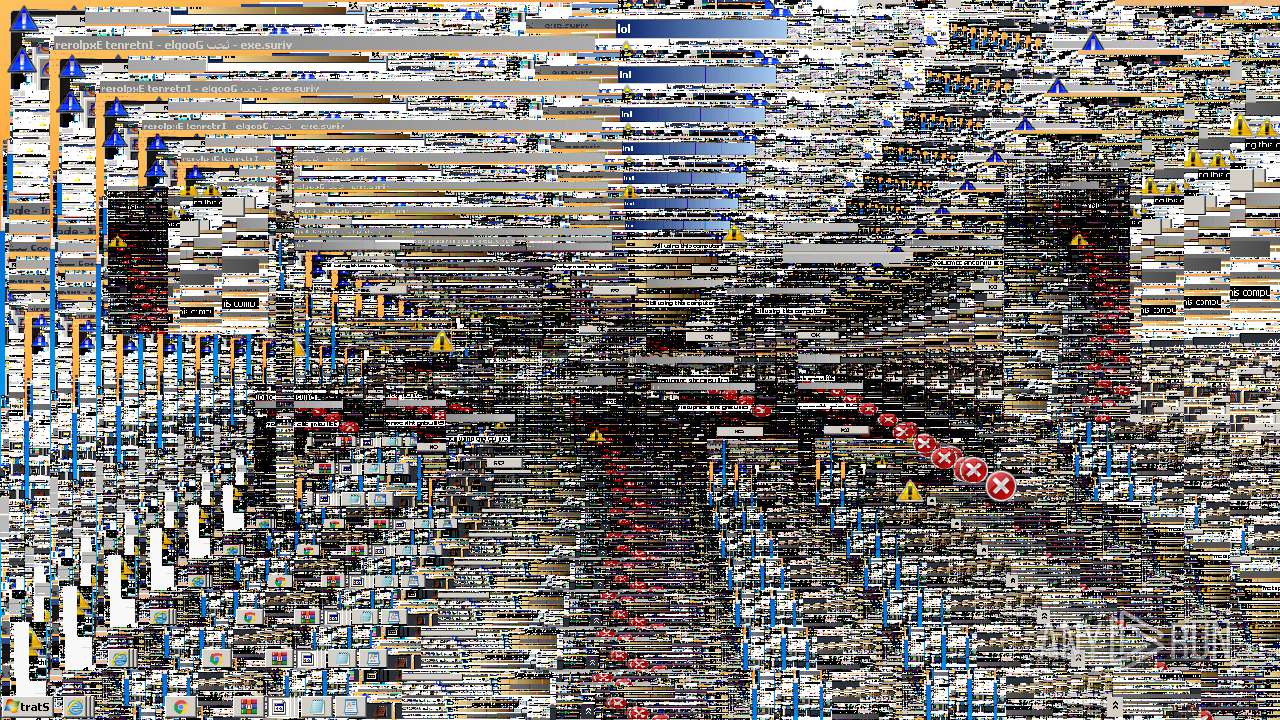
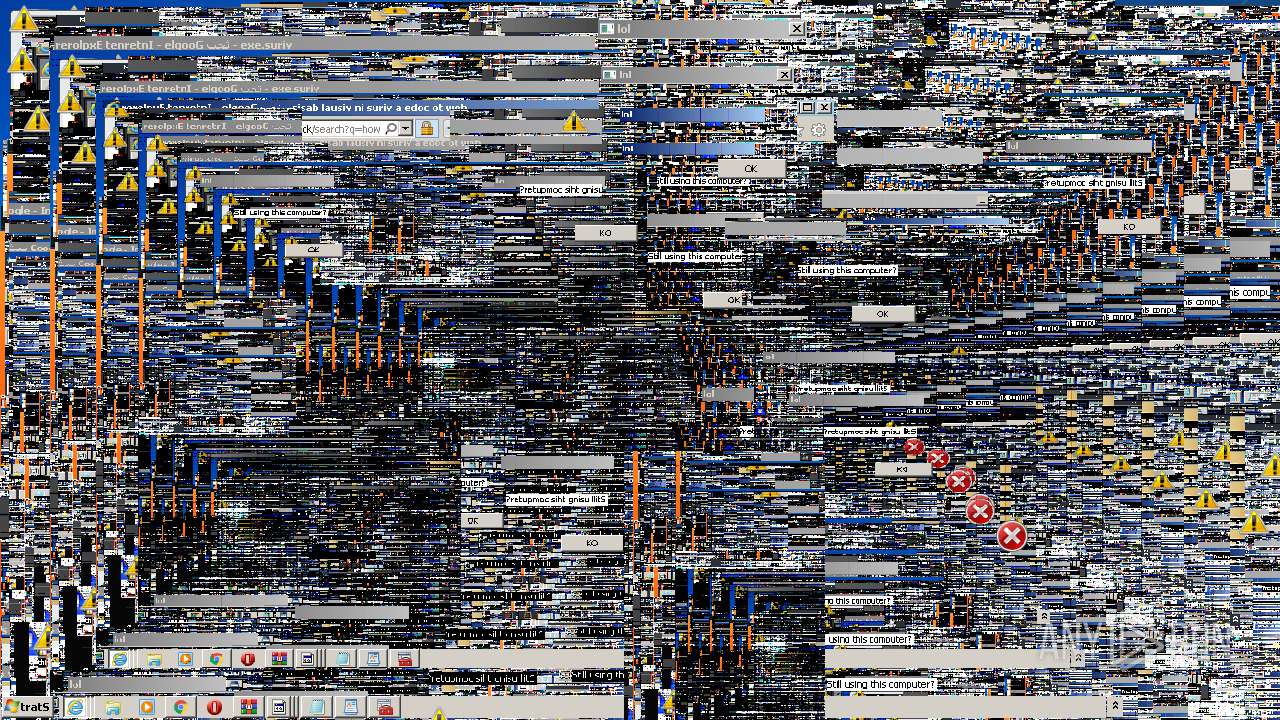
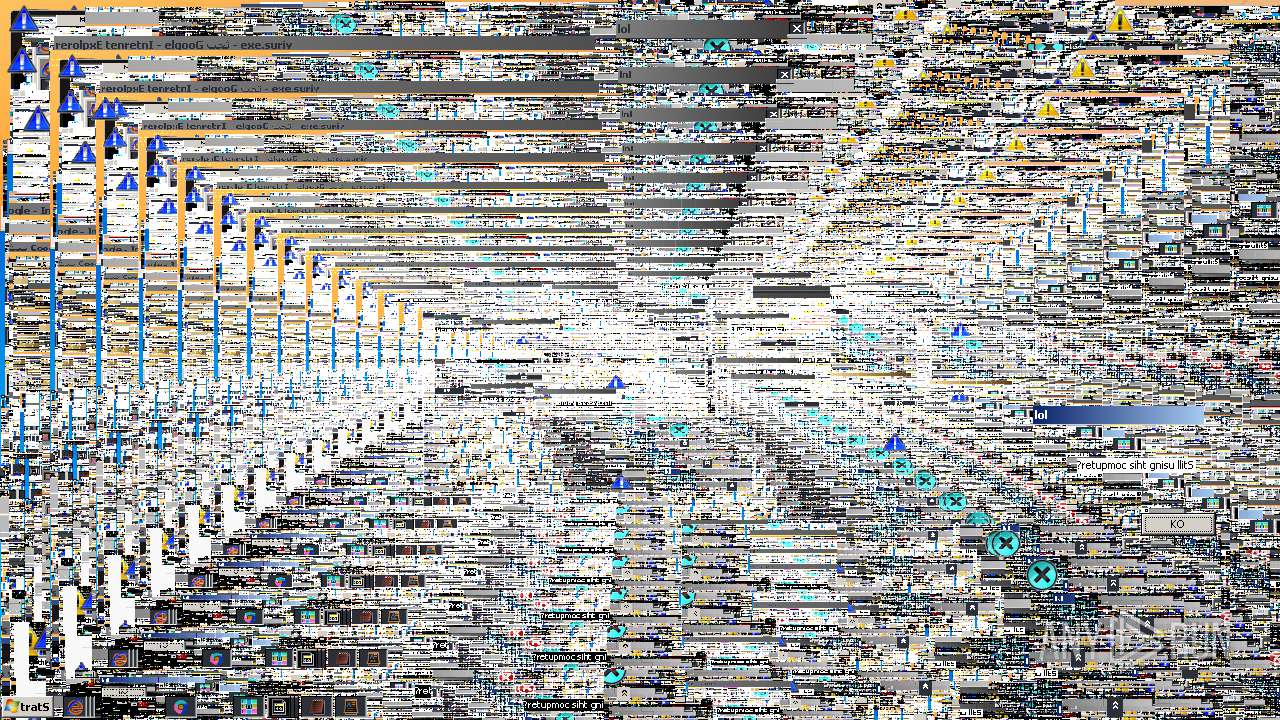
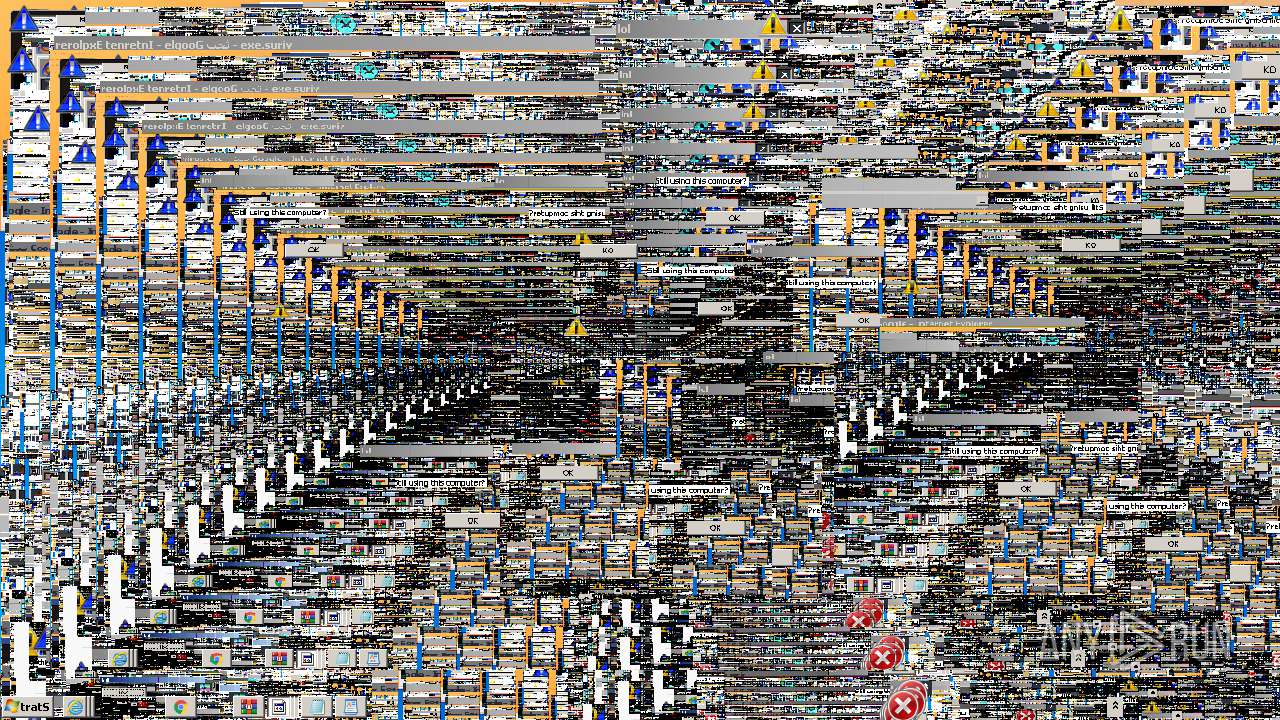
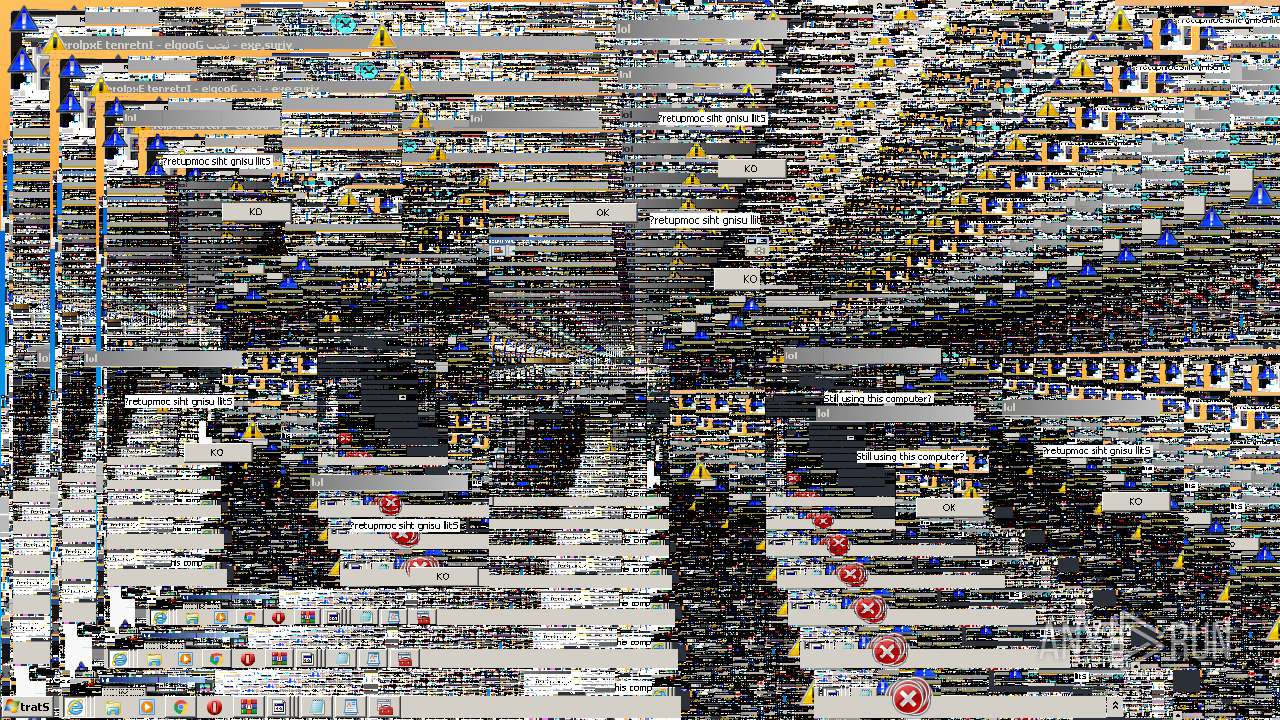
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
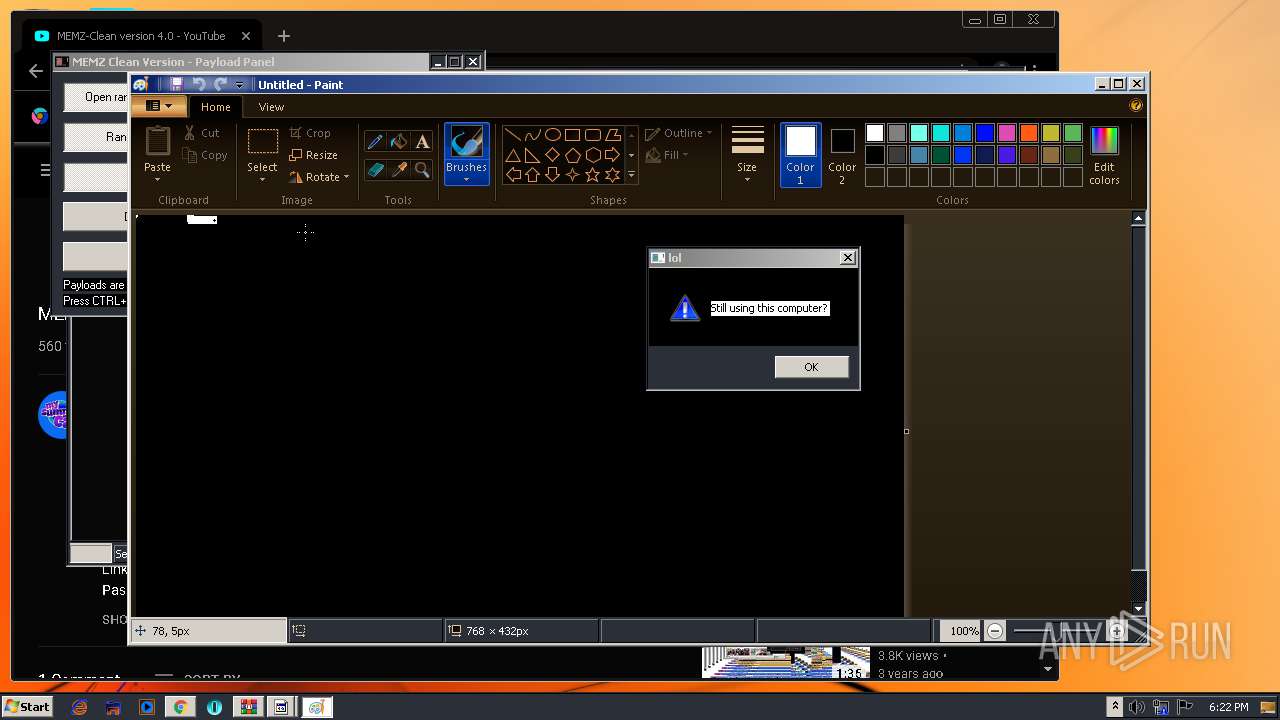
| 756 | "C:\Windows\System32\mspaint.exe" | C:\Windows\System32\mspaint.exe | — | MEMZ-Clean.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Paint Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 772 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1024,6141220517945480218,15120567054801018527,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=15305683942798716201 --mojo-platform-channel-handle=3464 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1272 | "C:\Windows\System32\mmc.exe" | C:\Windows\System32\mmc.exe | MEMZ-Clean.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Management Console Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1460 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2196 CREDAT:2692384 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1488 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,6141220517945480218,15120567054801018527,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=6703677170570589471 --mojo-platform-channel-handle=2580 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1804 | "C:\Windows\System32\cmd.exe" | C:\Windows\System32\cmd.exe | — | MEMZ-Clean.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 3221225786 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1824 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2196 CREDAT:2168083 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2100 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2112 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,6141220517945480218,15120567054801018527,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=6788449466769630201 --mojo-platform-channel-handle=2816 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
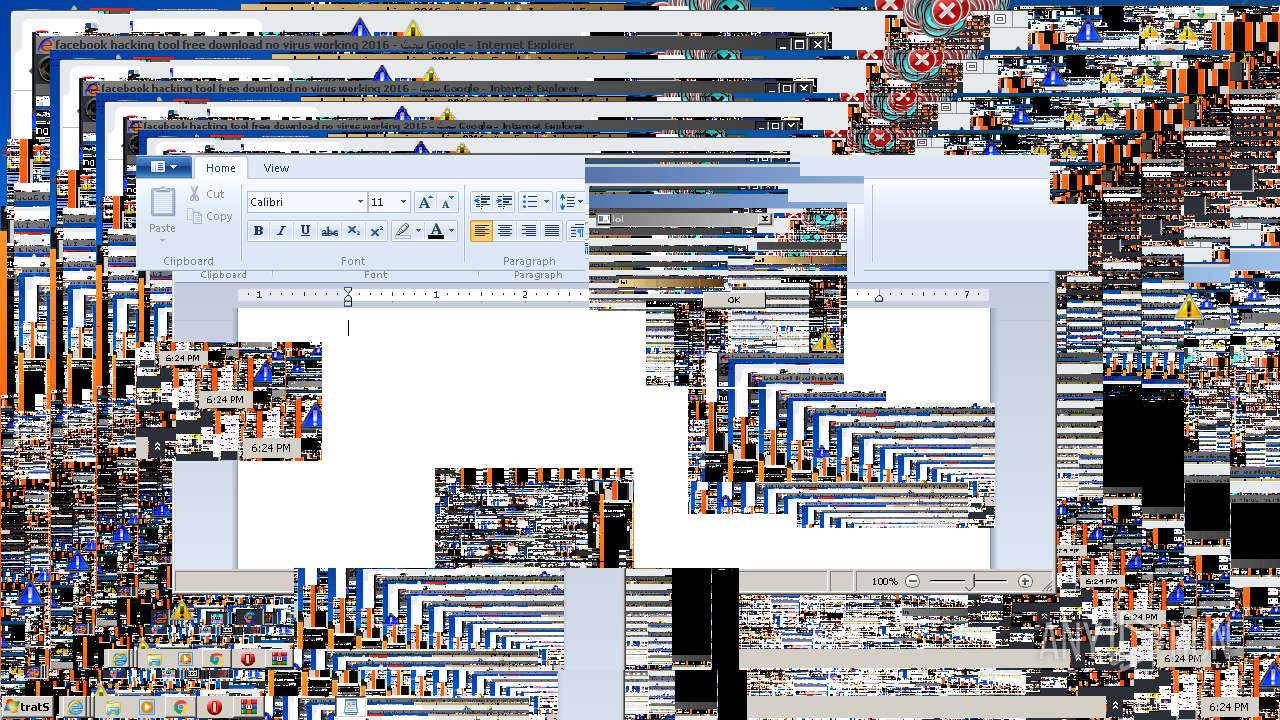
| 2116 | "C:\Program Files\Windows NT\Accessories\wordpad.exe" | C:\Program Files\Windows NT\Accessories\wordpad.exe | — | MEMZ-Clean.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Wordpad Application Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
4 362
Read events
3 775
Write events
571
Delete events
16
Modification events
| (PID) Process: | (2780) rundll32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {17FE9752-0B5A-4665-84CD-569794602F5C} {7F9185B0-CB92-43C5-80A9-92277A4F7B54} 0xFFFF |
Value: 01000000000000009E12CE2EA86DD601 | |||
| (PID) Process: | (2468) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 1086507118 | |||
| (PID) Process: | (2468) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30829992 | |||
| (PID) Process: | (2468) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2468) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2468) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2468) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2468) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2468) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A3000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2468) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
1
Suspicious files
253
Text files
277
Unknown types
59
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2652 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabE88C.tmp | — | |
MD5:— | SHA256:— | |||
| 2652 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarE88D.tmp | — | |
MD5:— | SHA256:— | |||
| 2652 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\IXSFJA1T.txt | — | |
MD5:— | SHA256:— | |||
| 2652 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\RDDMPRBV.txt | — | |
MD5:— | SHA256:— | |||
| 2652 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\YSMEUAOF.txt | — | |
MD5:— | SHA256:— | |||
| 2652 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\G8T2TZBI.txt | — | |
MD5:— | SHA256:— | |||
| 2468 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2468 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\CabED4E.tmp | — | |
MD5:— | SHA256:— | |||
| 2468 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\TarED4F.tmp | — | |
MD5:— | SHA256:— | |||
| 2468 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFB1A3794750AD1D93.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
92
TCP/UDP connections
230
DNS requests
91
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2652 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
2188 | iexplore.exe | GET | 200 | 172.217.22.67:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQCUy%2Fu%2FkFcMdAIAAAAAc80y | US | der | 472 b | whitelisted |
2188 | iexplore.exe | GET | 200 | 172.217.22.67:80 | http://ocsp.pki.goog/gts1o1core/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEDdE1cf4Gvu%2FAgAAAABzzNg%3D | US | der | 471 b | whitelisted |
2188 | iexplore.exe | GET | 200 | 172.217.22.67:80 | http://ocsp.pki.goog/gts1o1core/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEDdE1cf4Gvu%2FAgAAAABzzNg%3D | US | der | 471 b | whitelisted |
2188 | iexplore.exe | GET | 200 | 172.217.22.67:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQCwP4ezsGXRpgIAAAAAc80W | US | der | 472 b | whitelisted |
2188 | iexplore.exe | GET | 200 | 172.217.22.67:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQCwP4ezsGXRpgIAAAAAc80W | US | der | 472 b | whitelisted |
1824 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.sectigo.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRDC9IOTxN6GmyRjyTl2n4yTUczyAQUjYxexFStiuF36Zv5mwXhuAGNYeECEEHB063uNMc6dPCqTOMgIPs%3D | US | der | 471 b | whitelisted |
1824 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | US | der | 727 b | whitelisted |
2188 | iexplore.exe | GET | 301 | 172.217.23.100:80 | http://google.co.ck/search?q=half+life+3+release+date | US | html | 254 b | whitelisted |
2188 | iexplore.exe | GET | 302 | 172.217.23.131:80 | http://www.google.co.ck/search?q=half+life+3+release+date | US | html | 270 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2652 | iexplore.exe | 23.66.21.99:80 | go.microsoft.com | Akamai Technologies, Inc. | NL | whitelisted |
2652 | iexplore.exe | 2.16.186.27:80 | shell.windows.com | Akamai International B.V. | — | whitelisted |
2652 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
2652 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2468 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2468 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
2456 | chrome.exe | 172.217.16.141:443 | accounts.google.com | Google Inc. | US | suspicious |
2456 | chrome.exe | 172.217.23.100:443 | www.google.com | Google Inc. | US | whitelisted |
2456 | chrome.exe | 172.217.22.35:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2456 | chrome.exe | 216.58.207.78:443 | apis.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
go.microsoft.com |
| whitelisted |
shell.windows.com |
| whitelisted |
www.bing.com |
| whitelisted |
api.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |