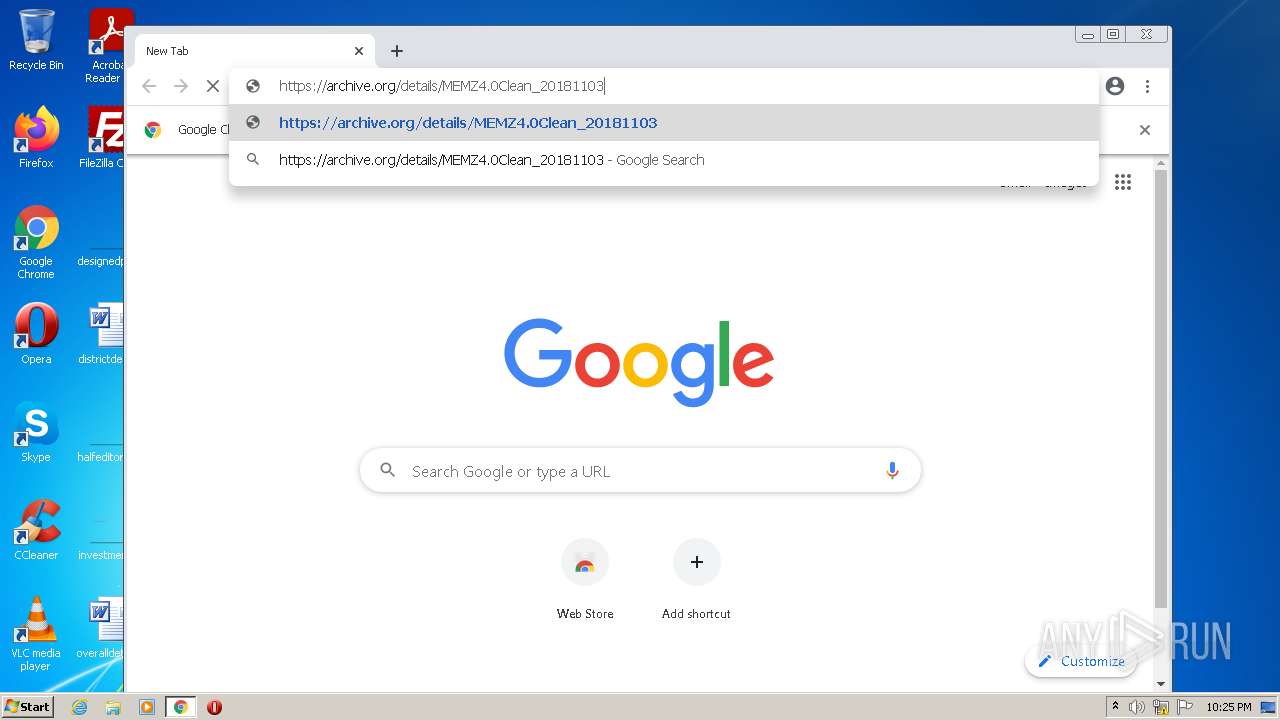
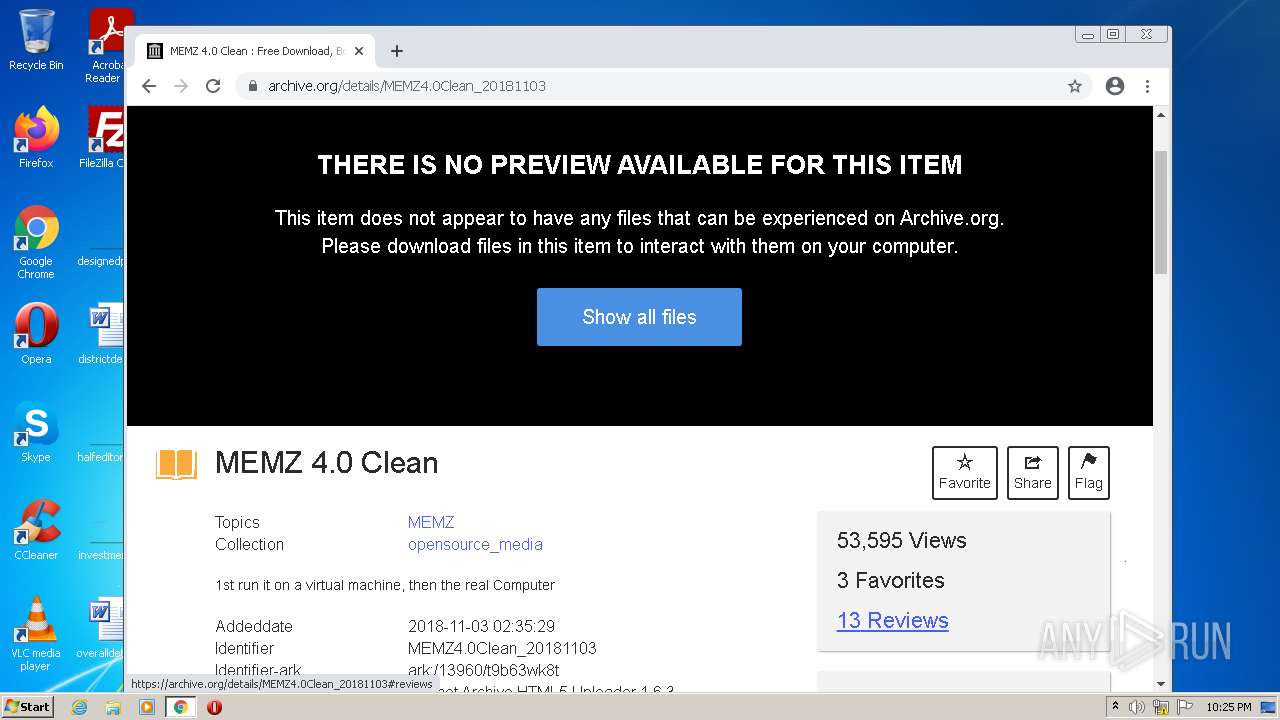
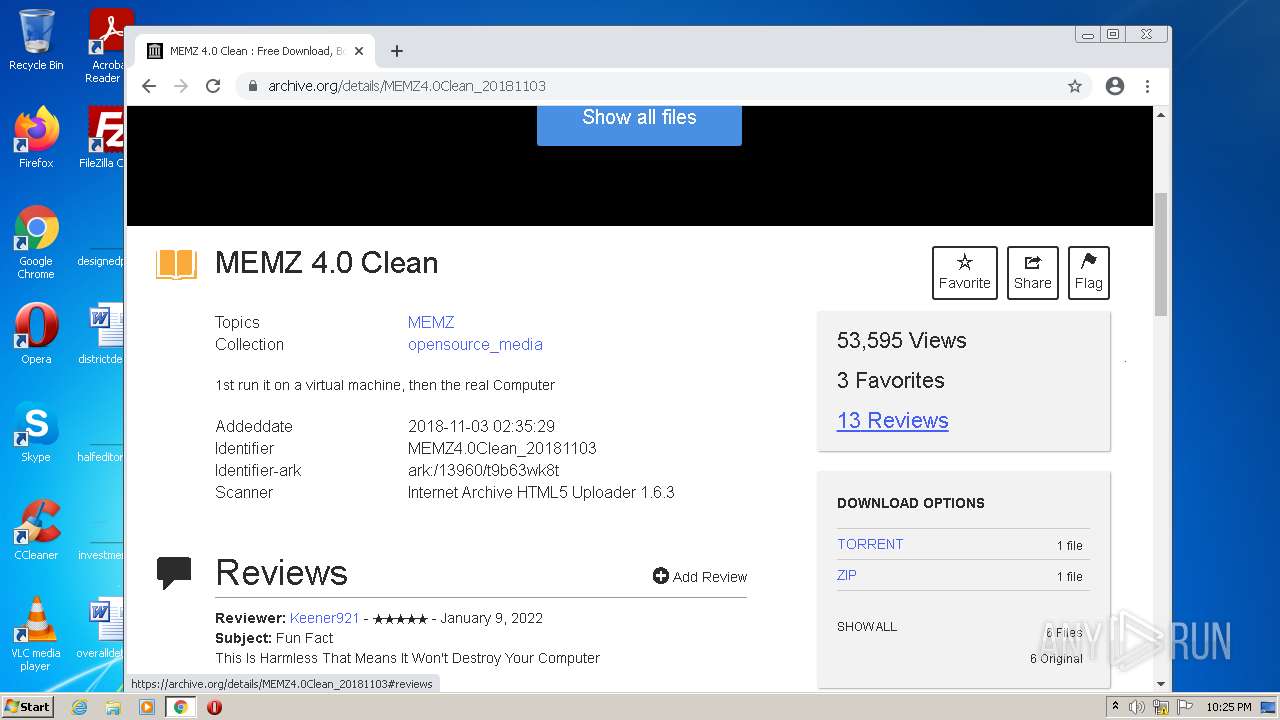
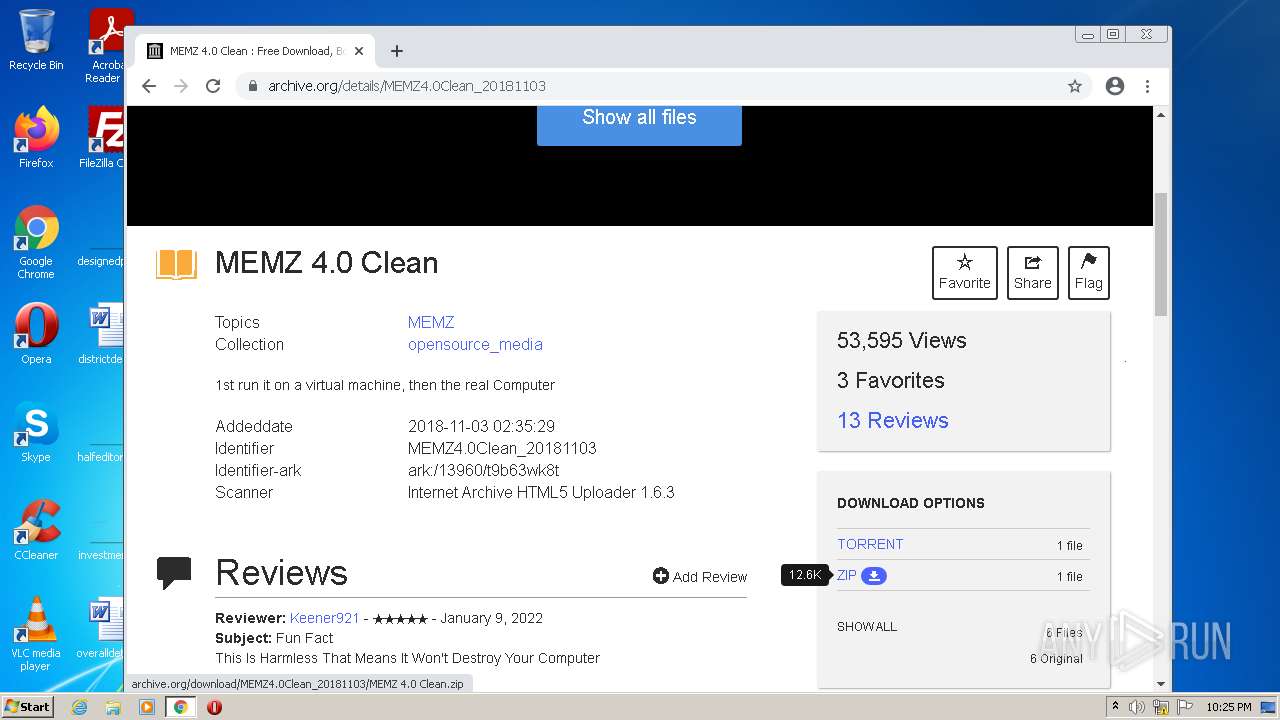
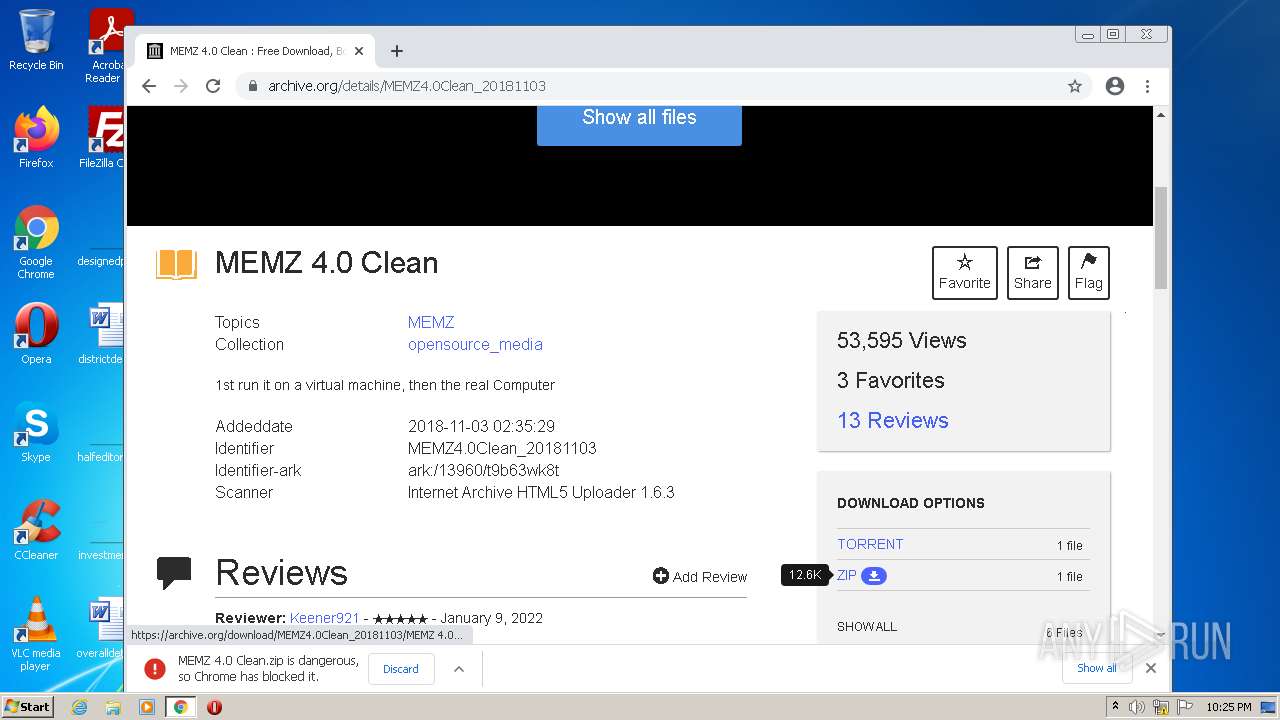
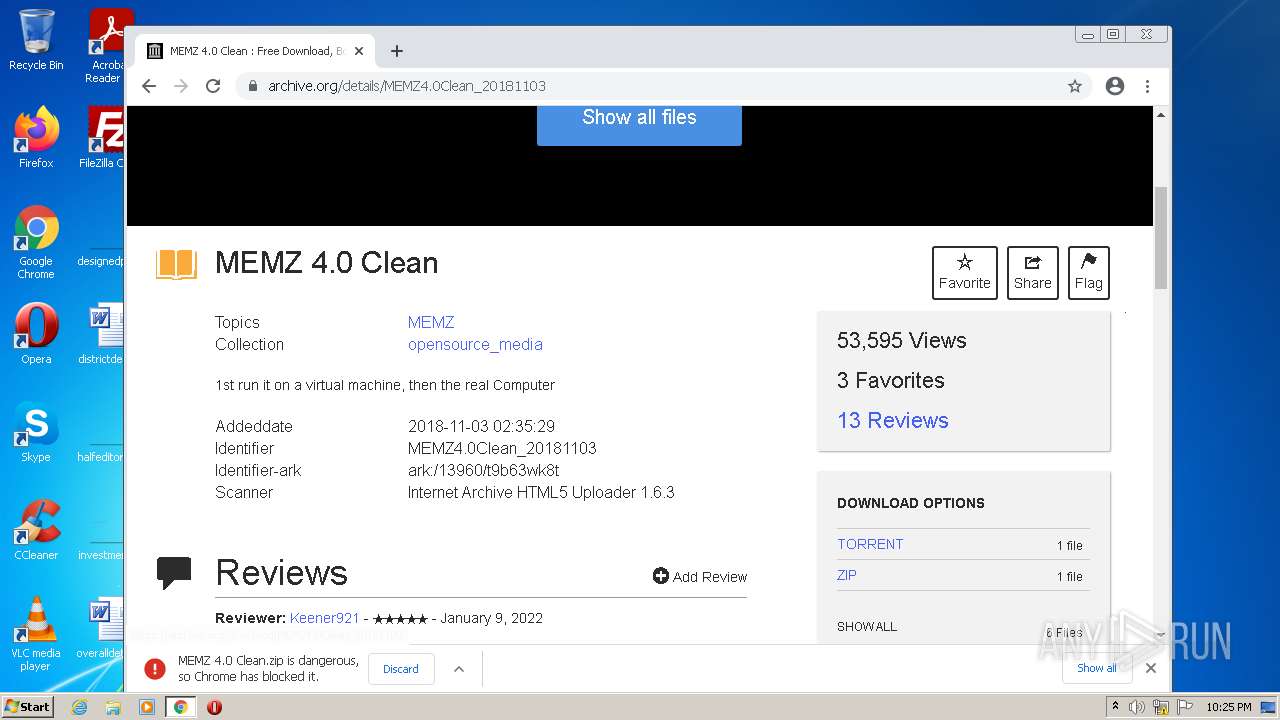
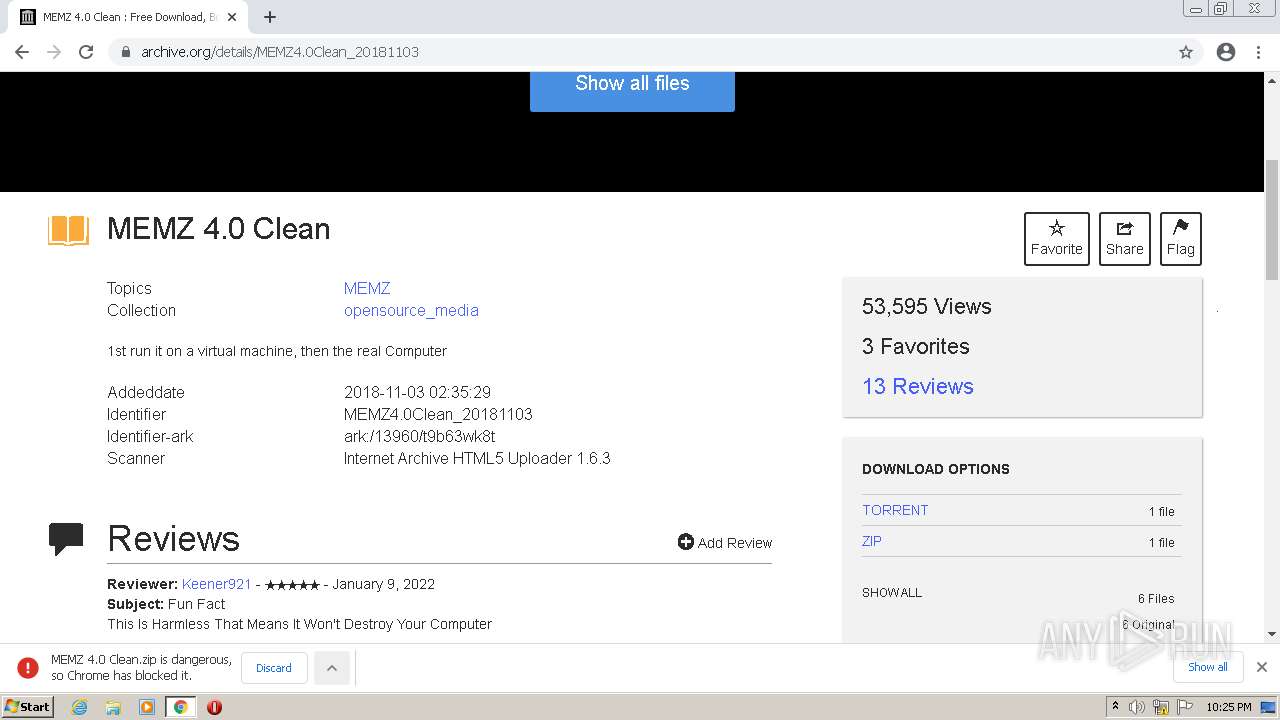
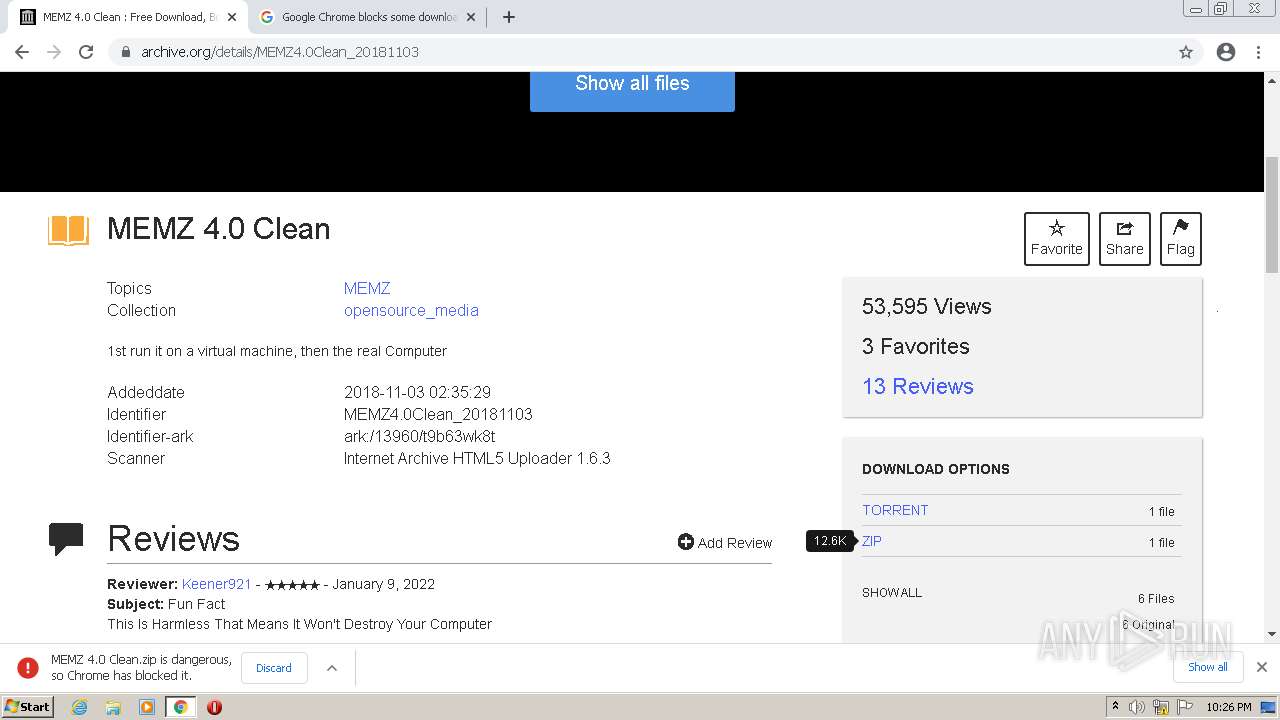
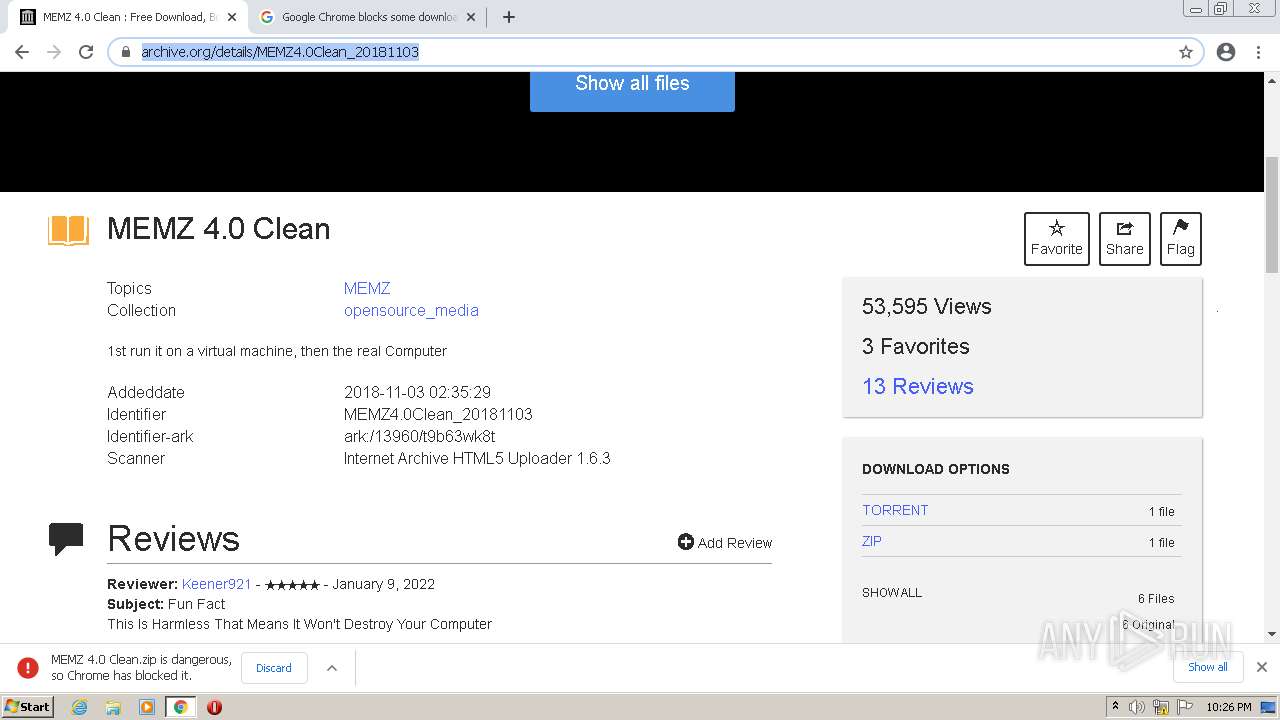
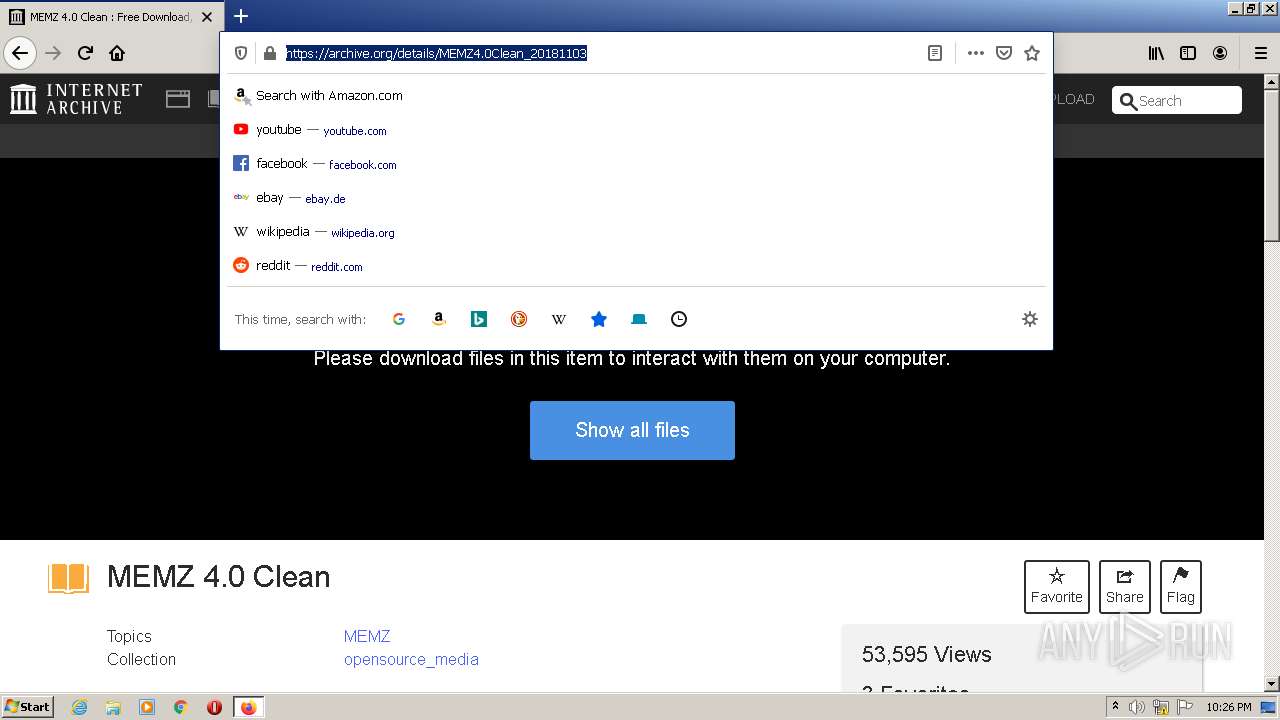
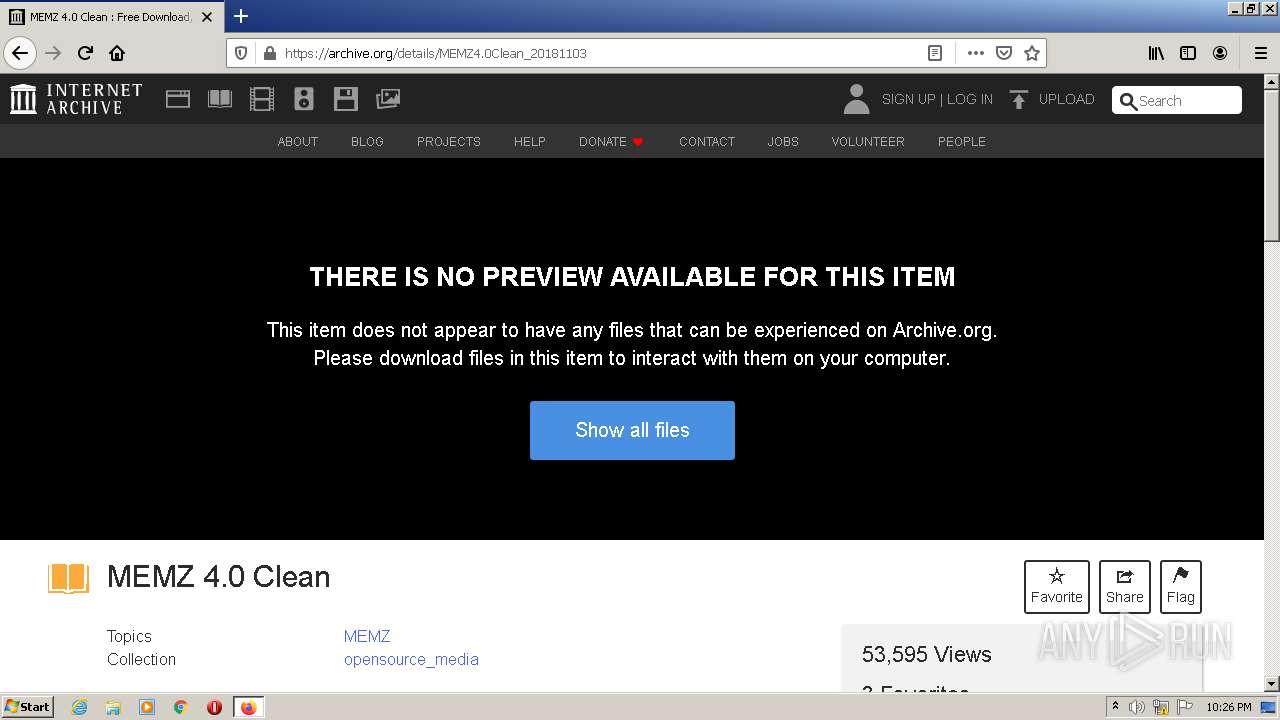
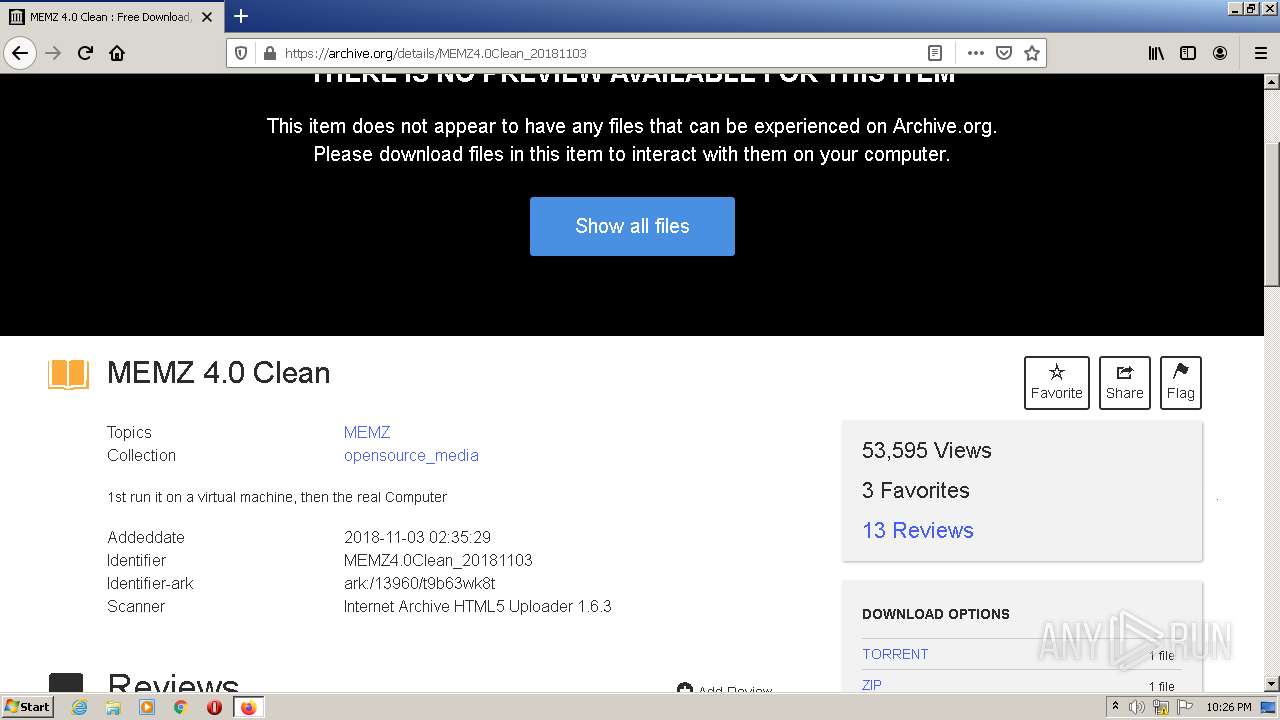
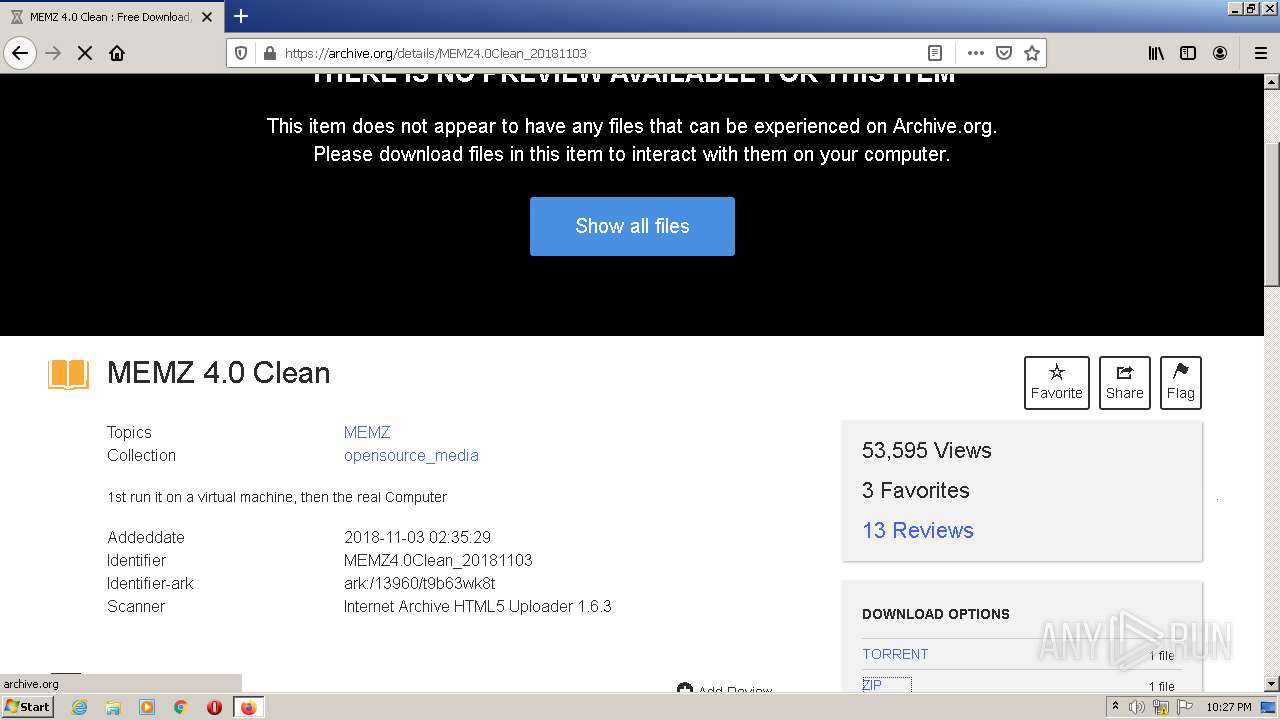
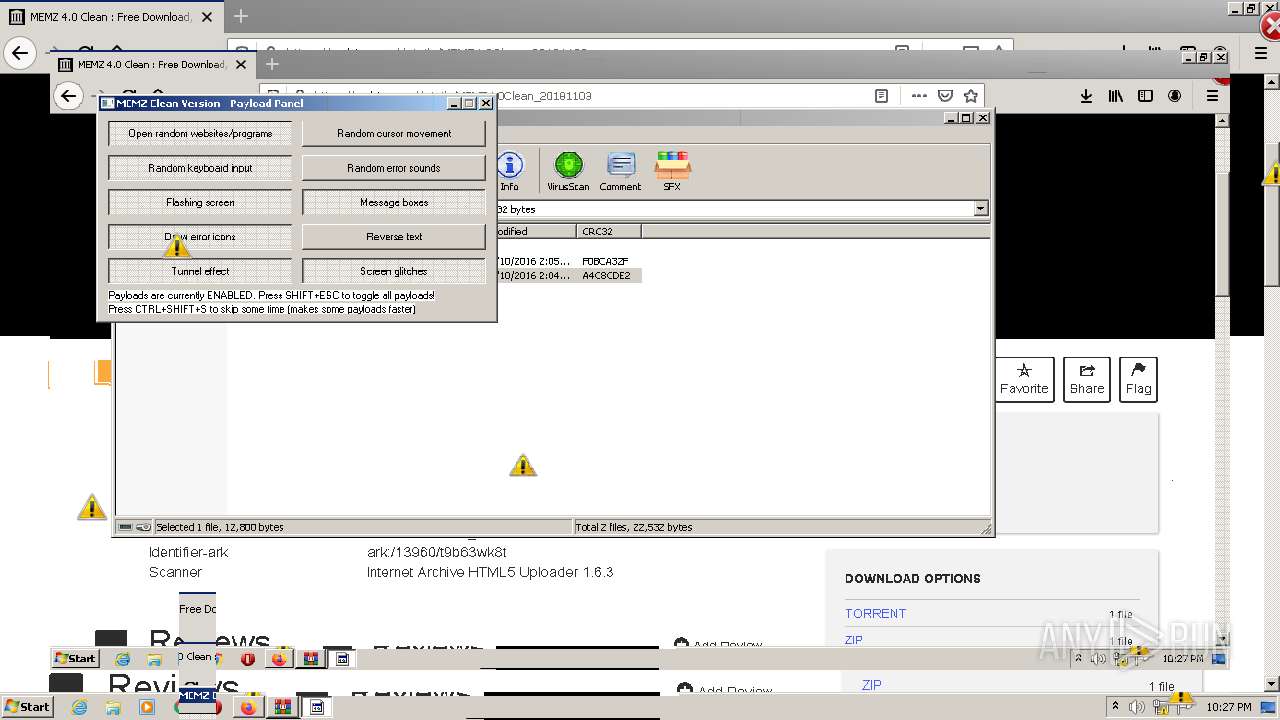
| URL: | https://archive.org/details/MEMZ4.0Clean_20181103 |
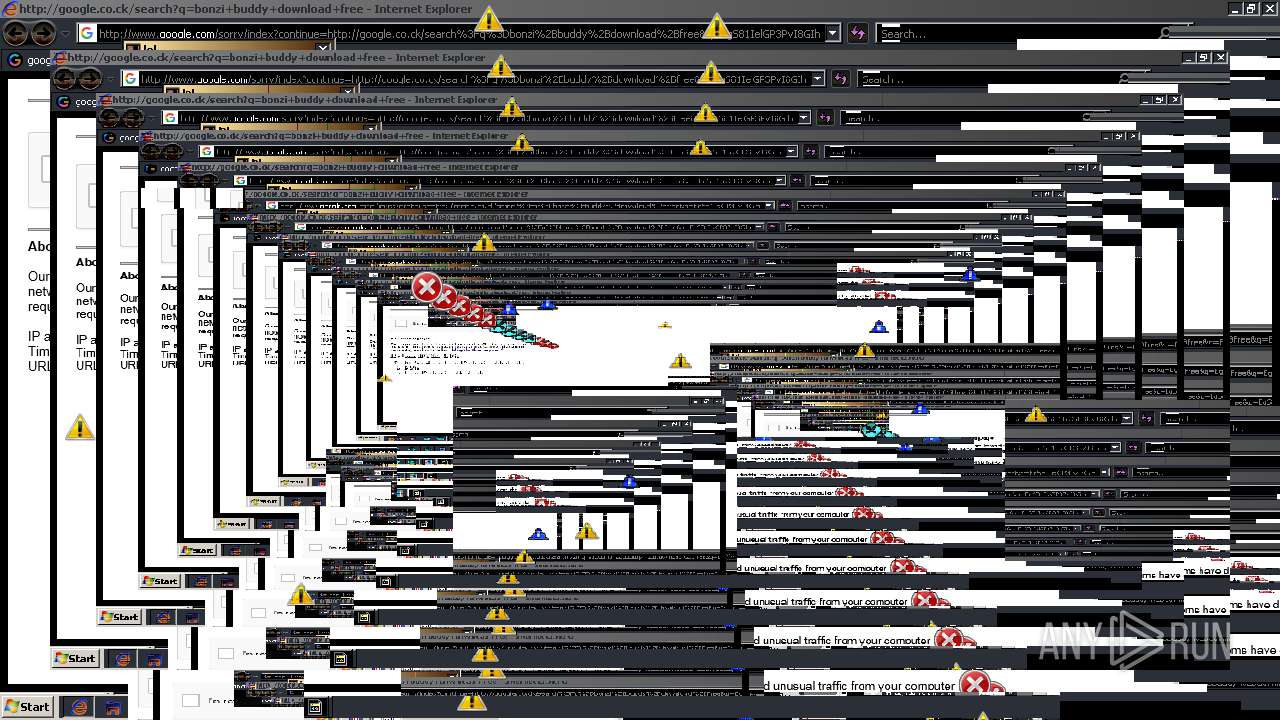
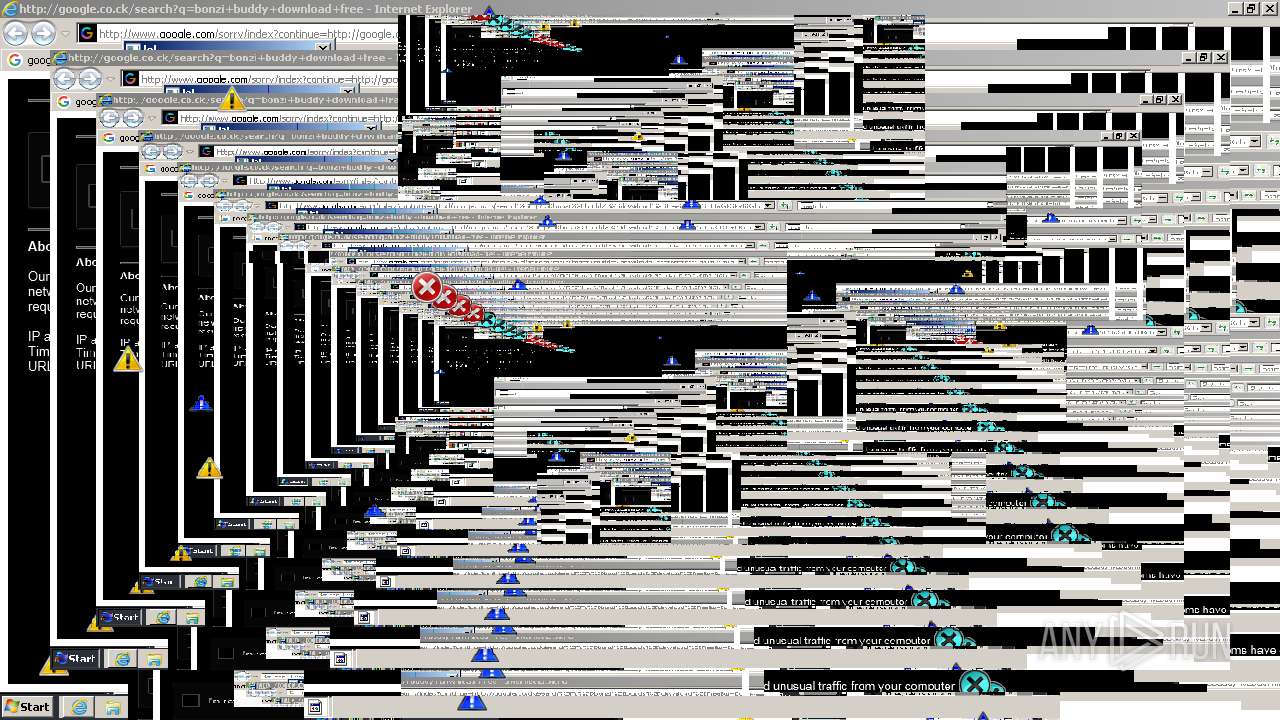
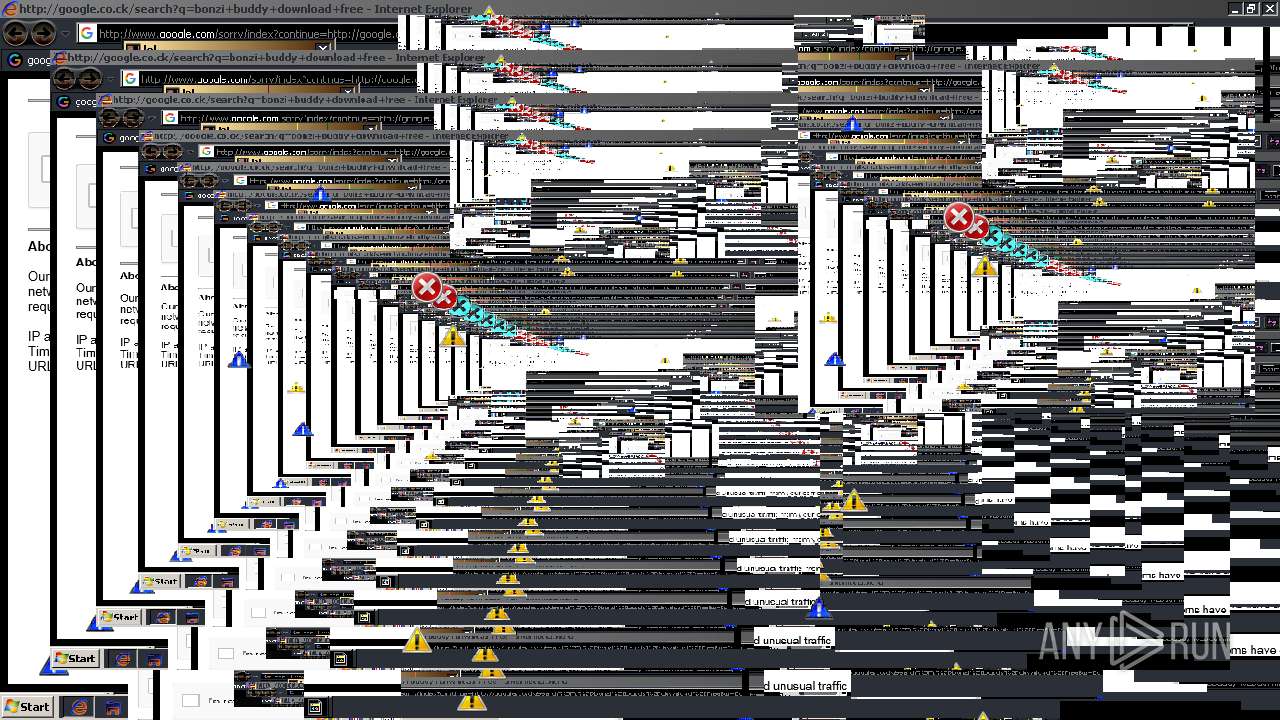
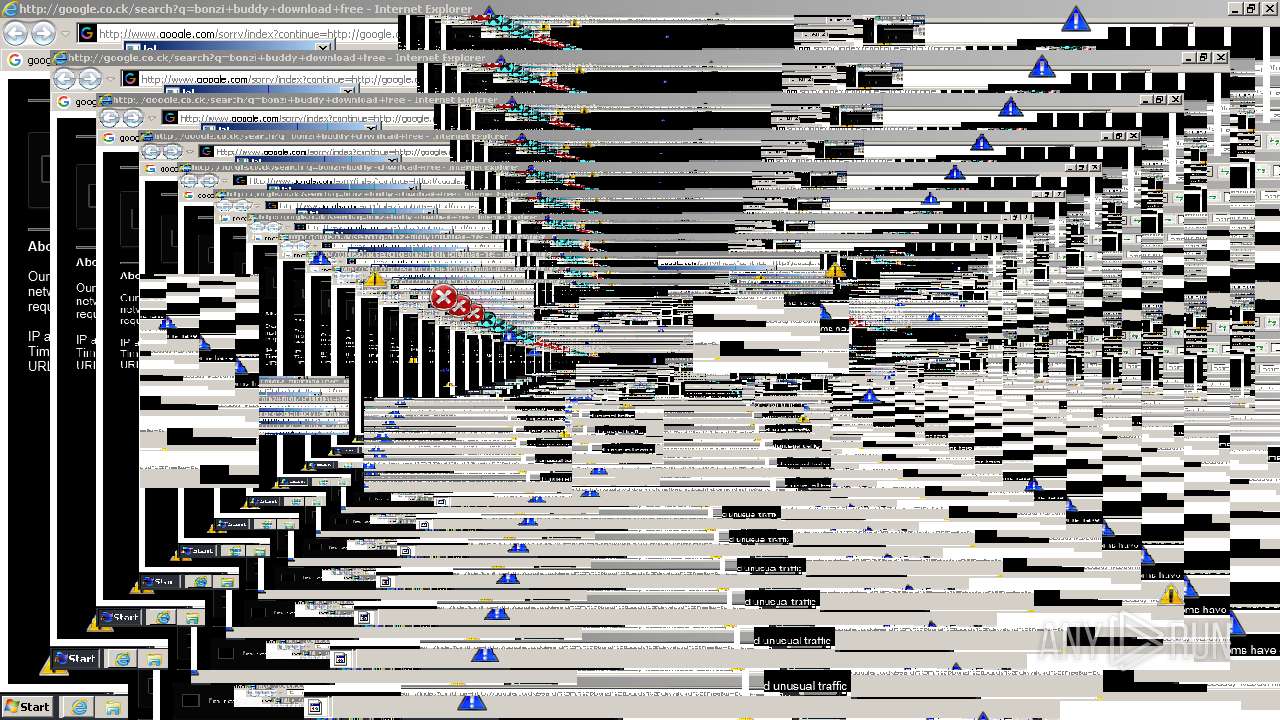
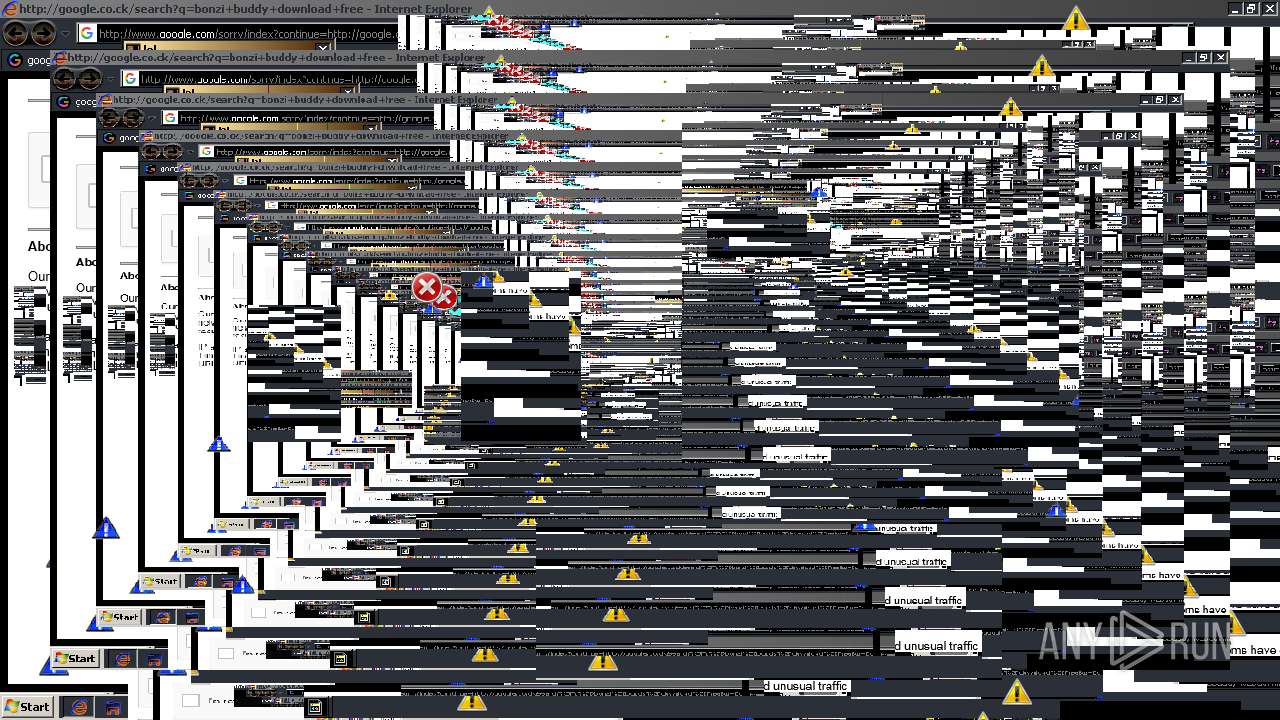
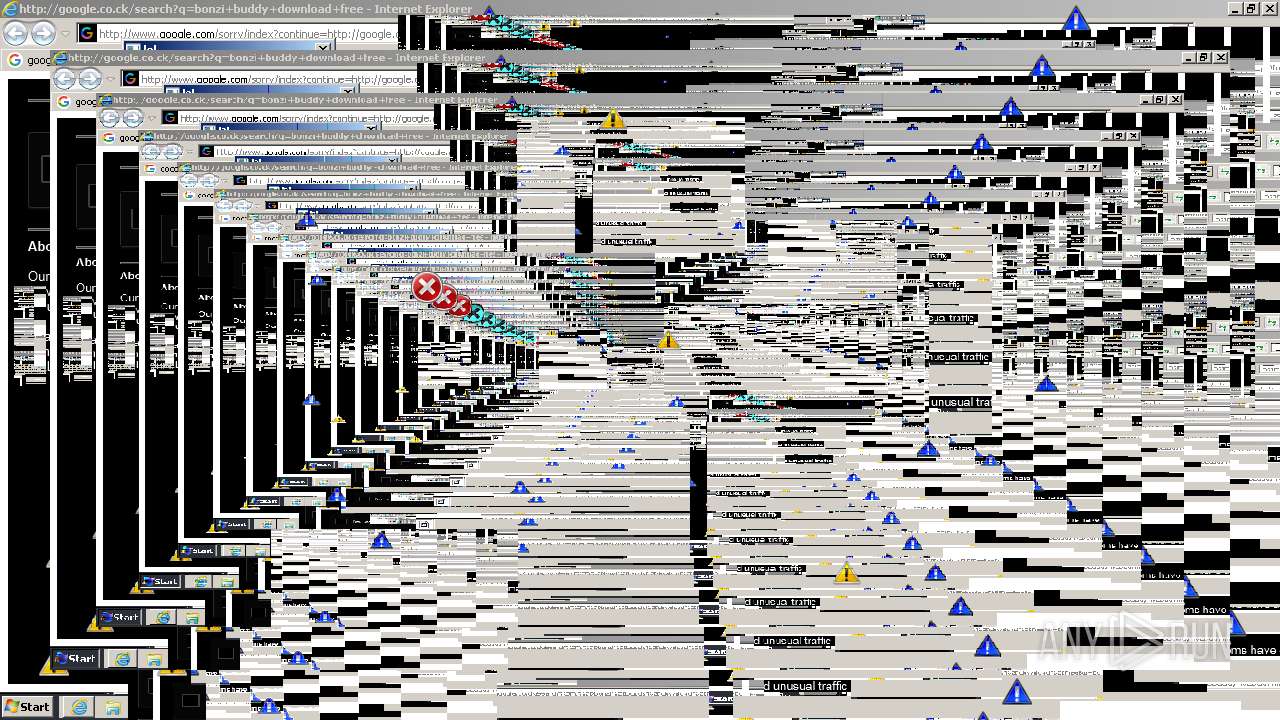
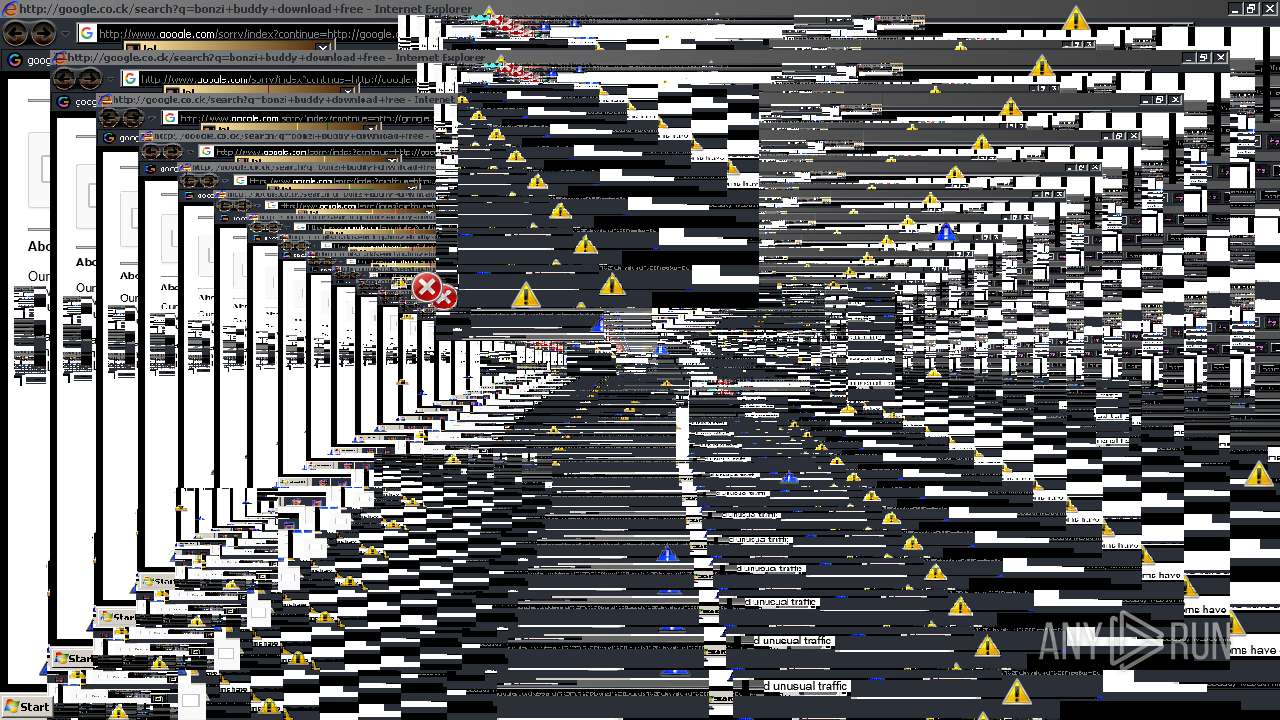
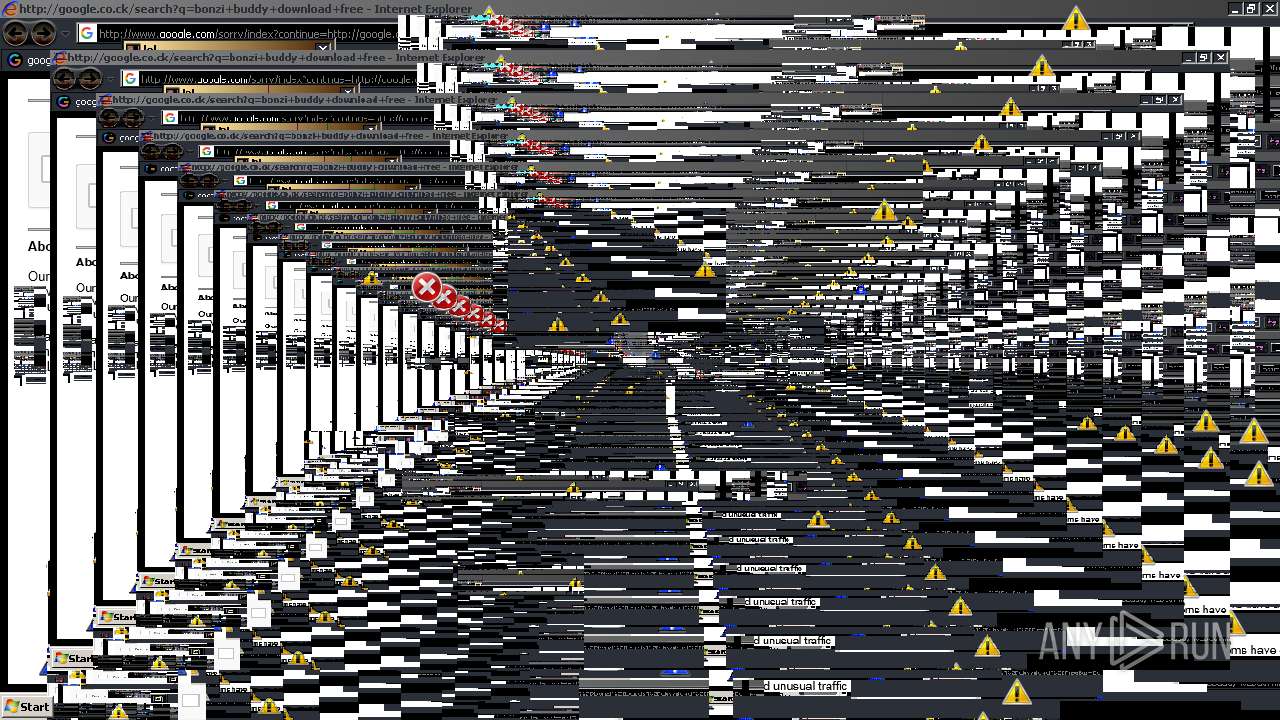
| Full analysis: | https://app.any.run/tasks/9766929f-696e-48c2-8f7a-2e588bd13924 |
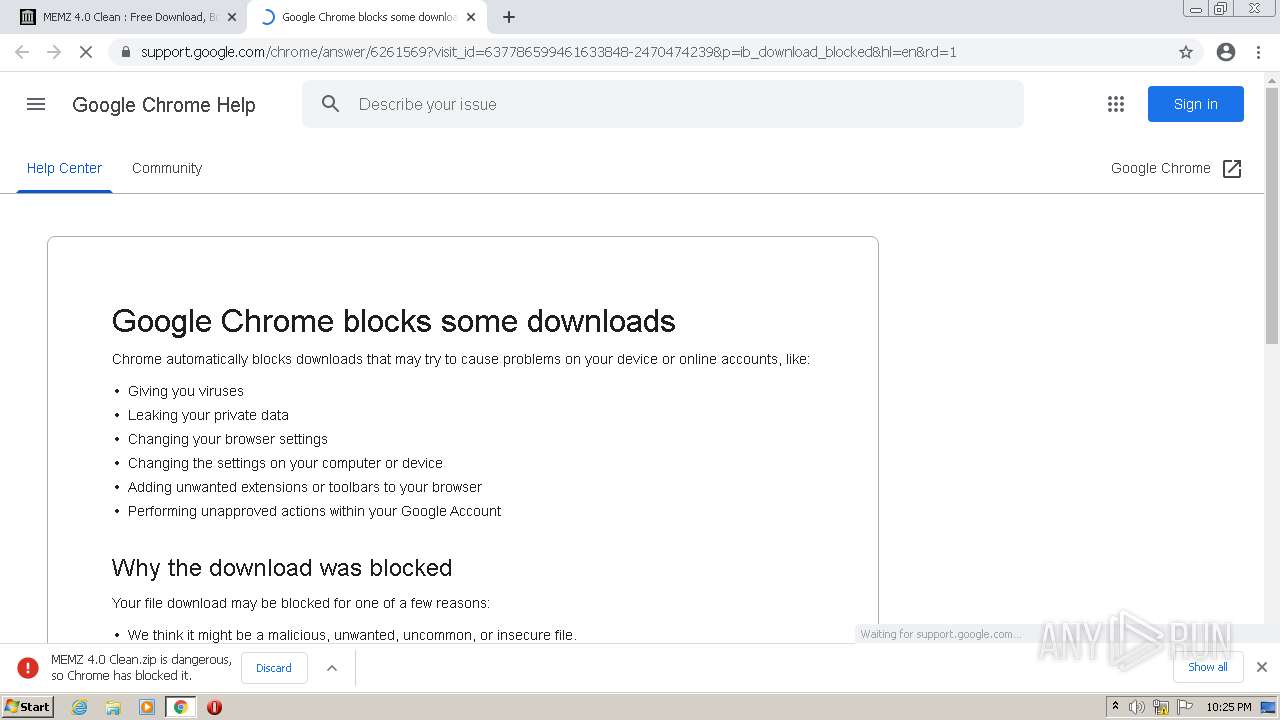
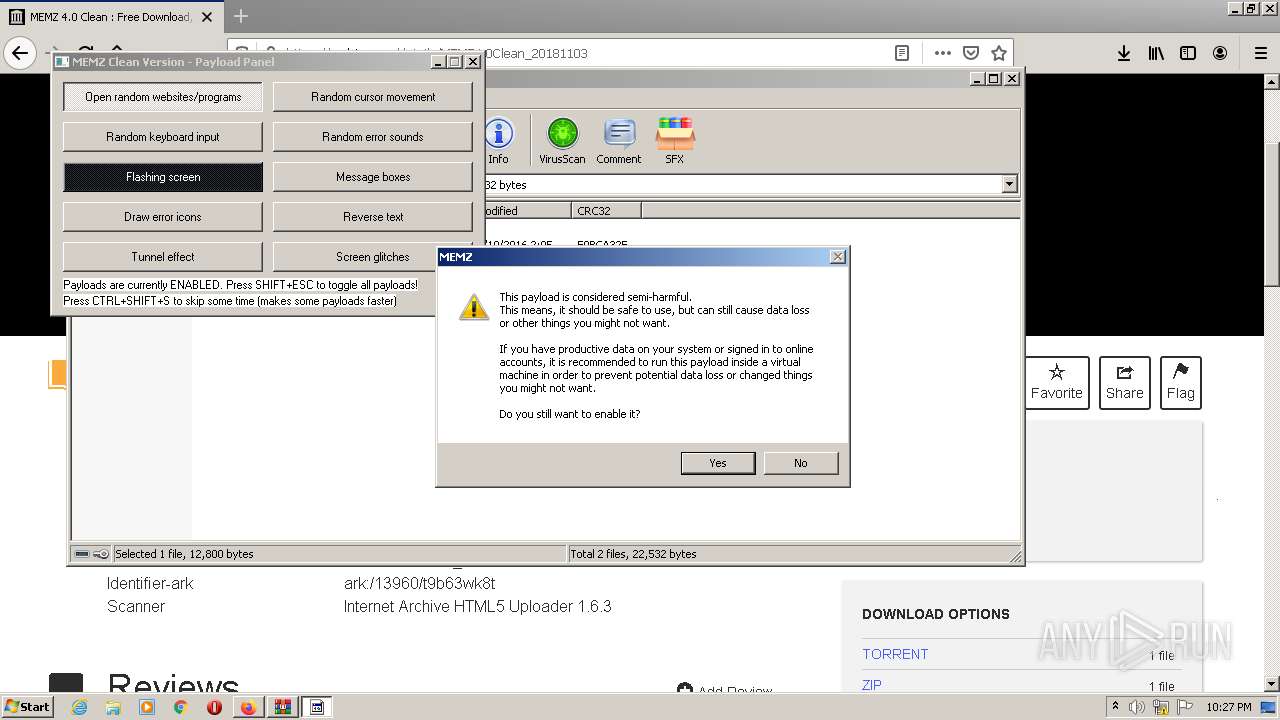
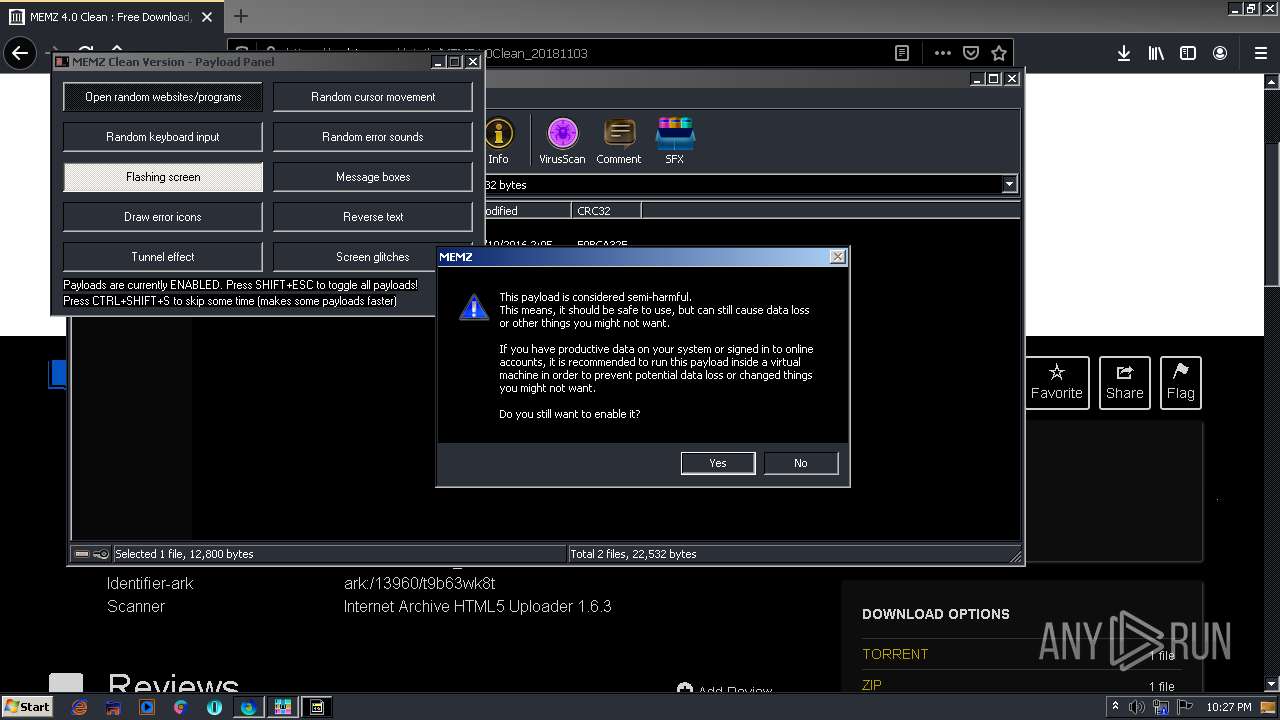
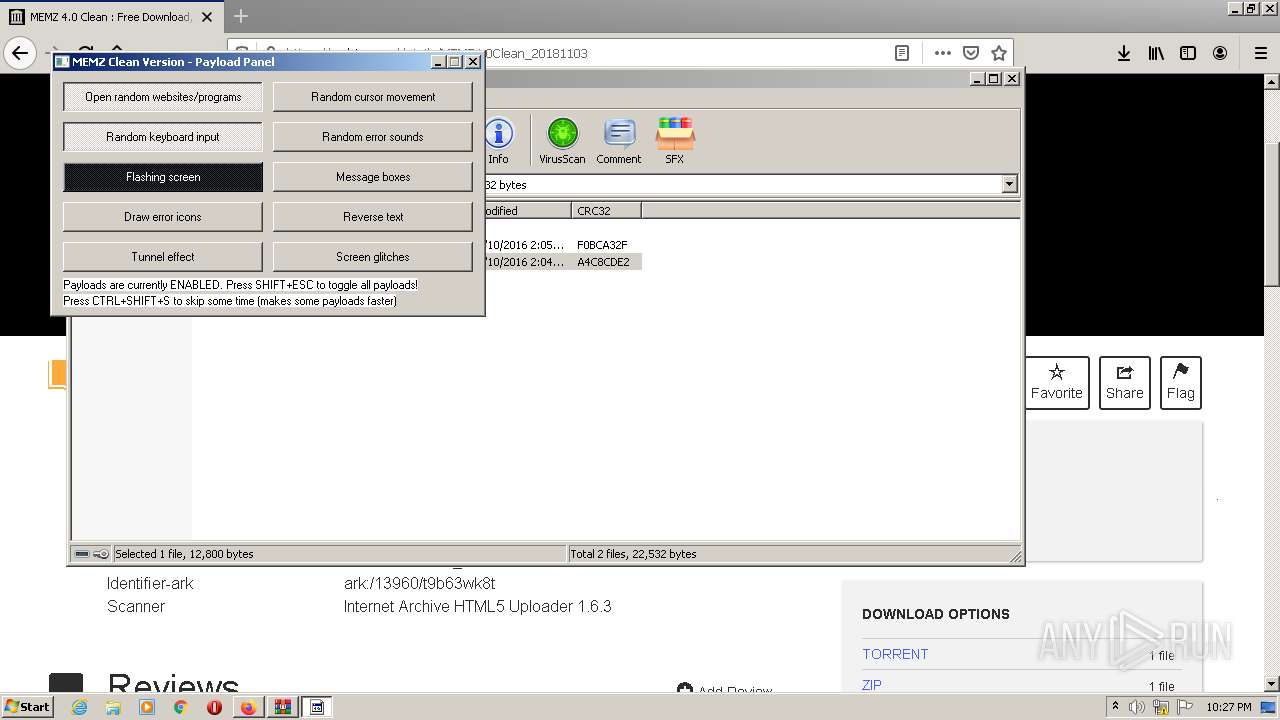
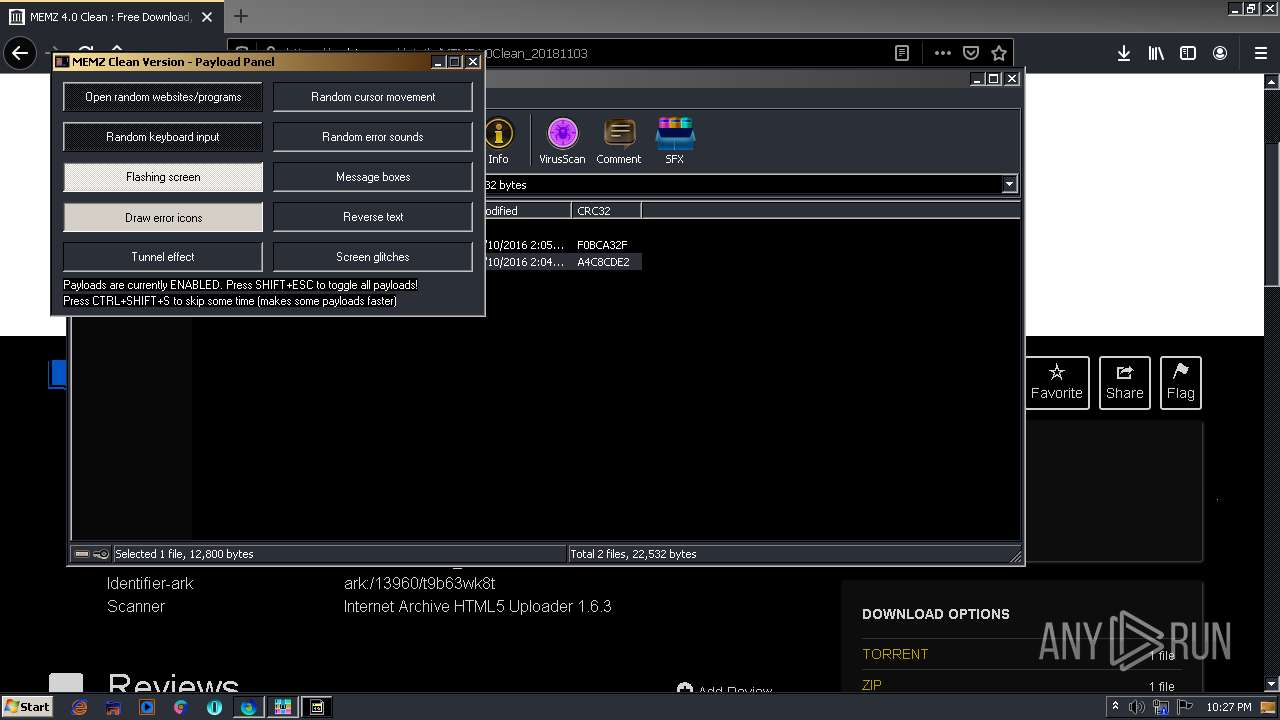
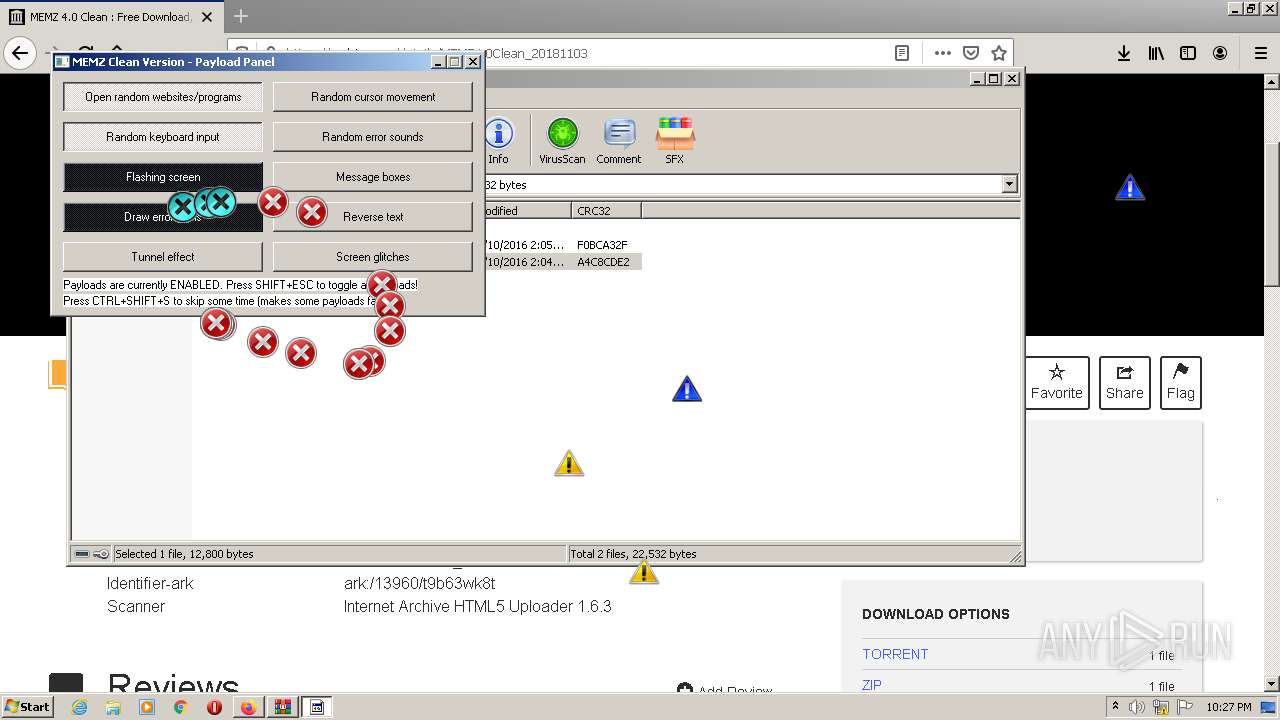
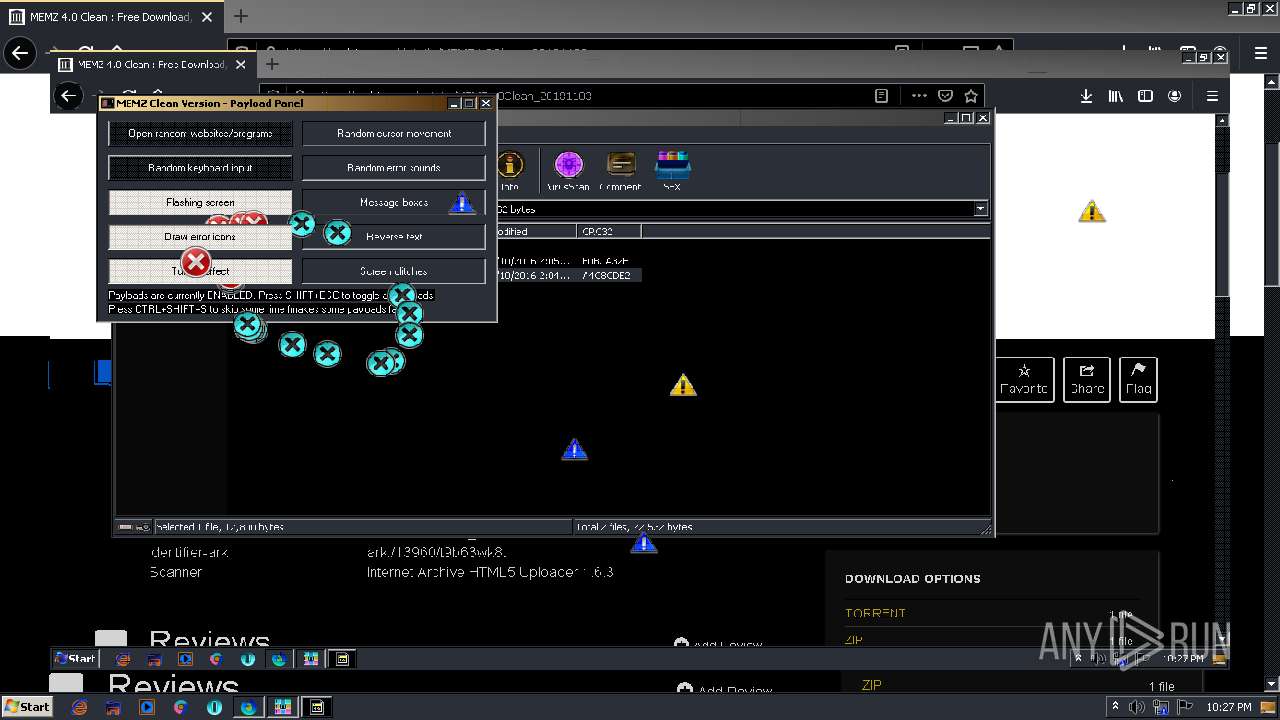
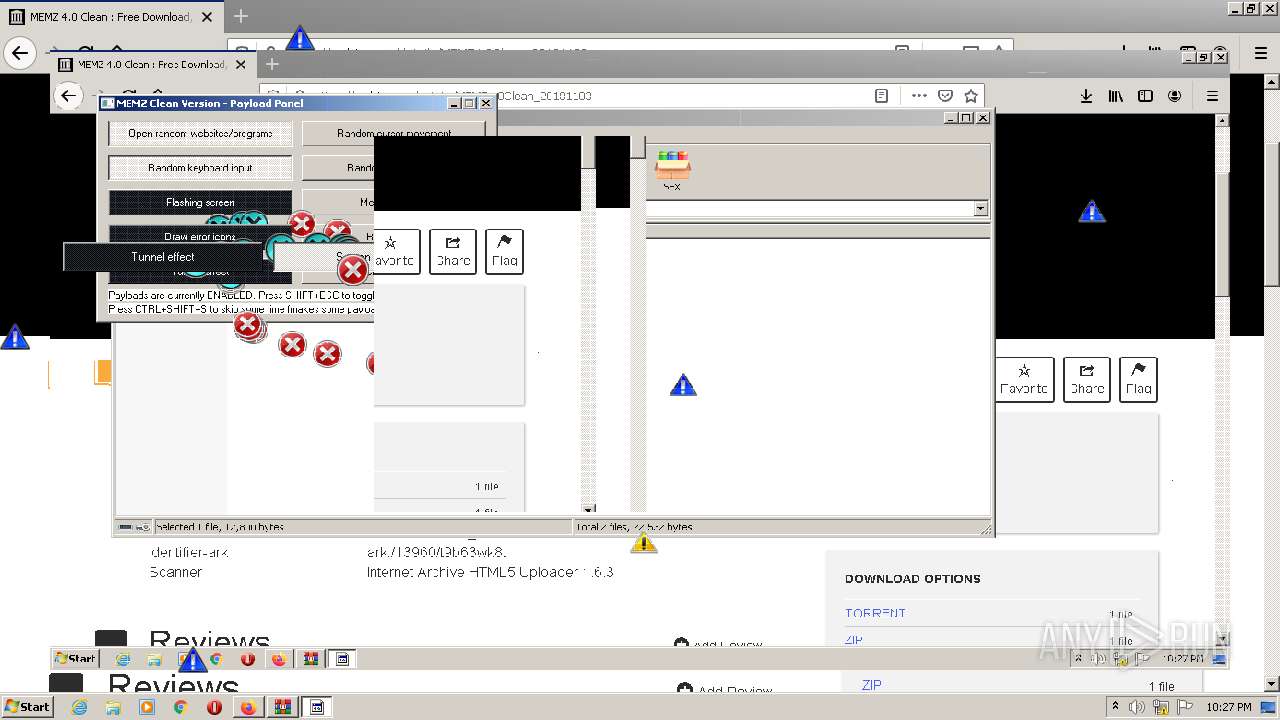
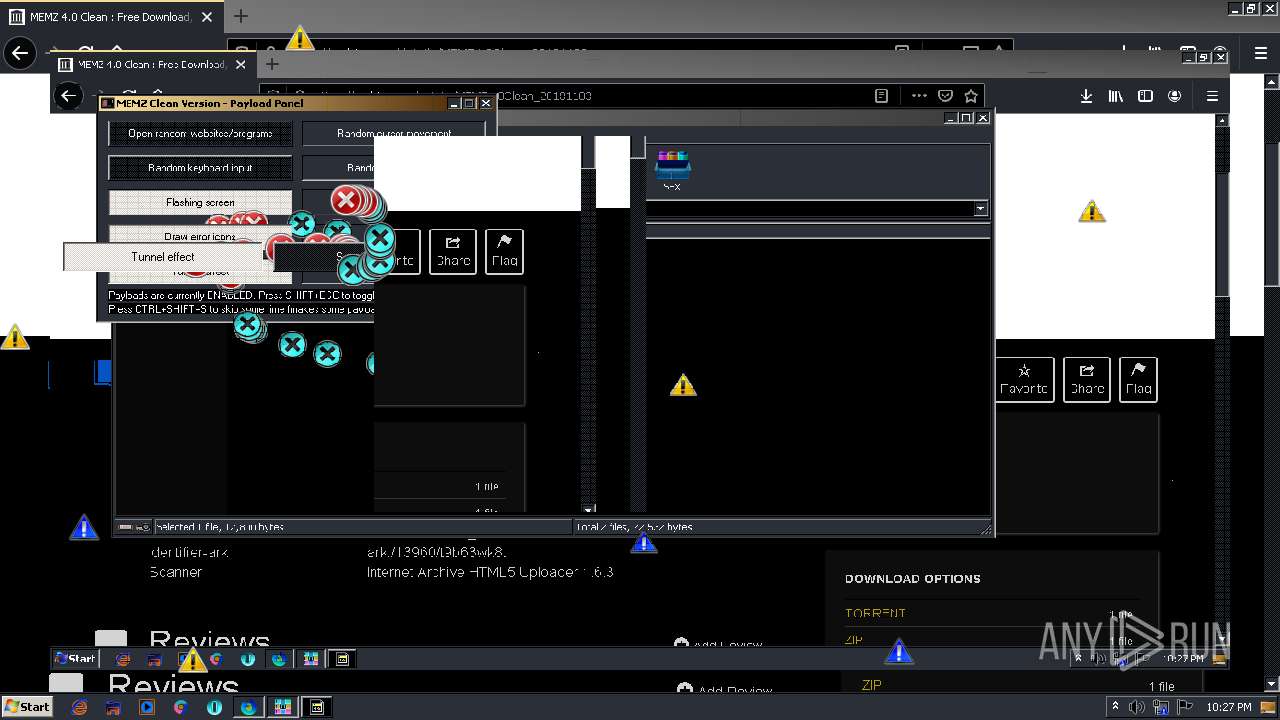
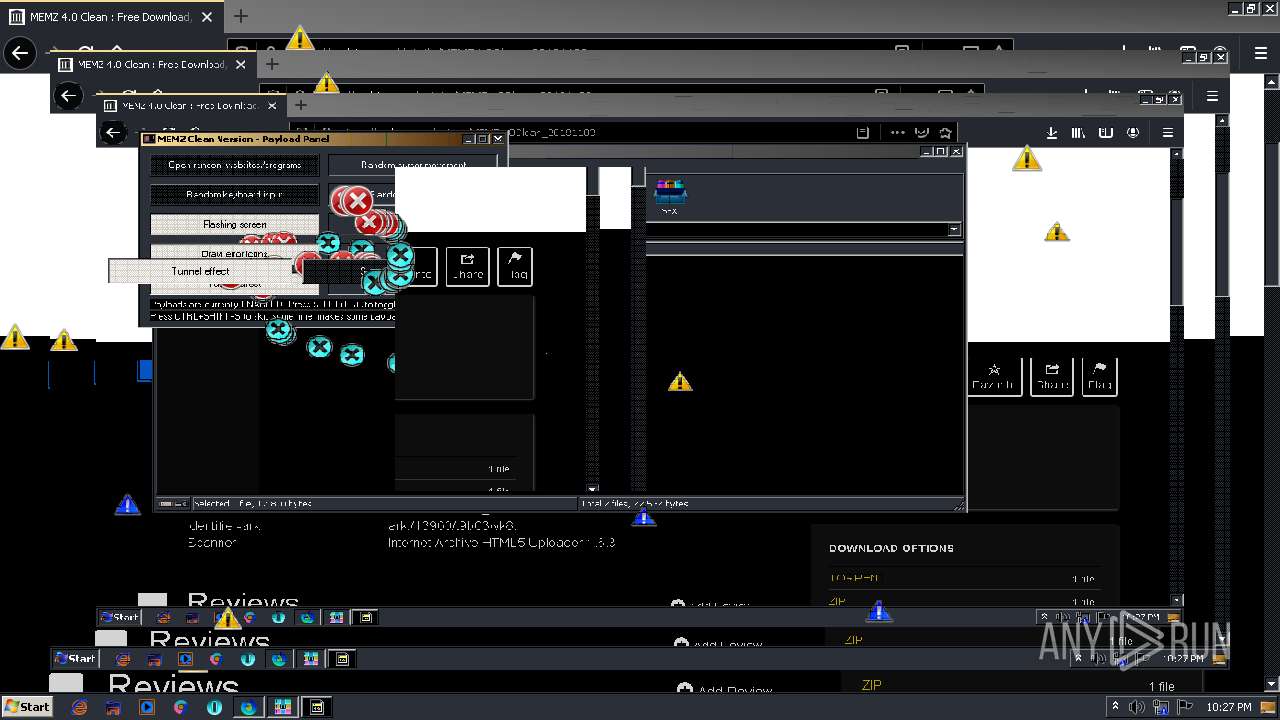
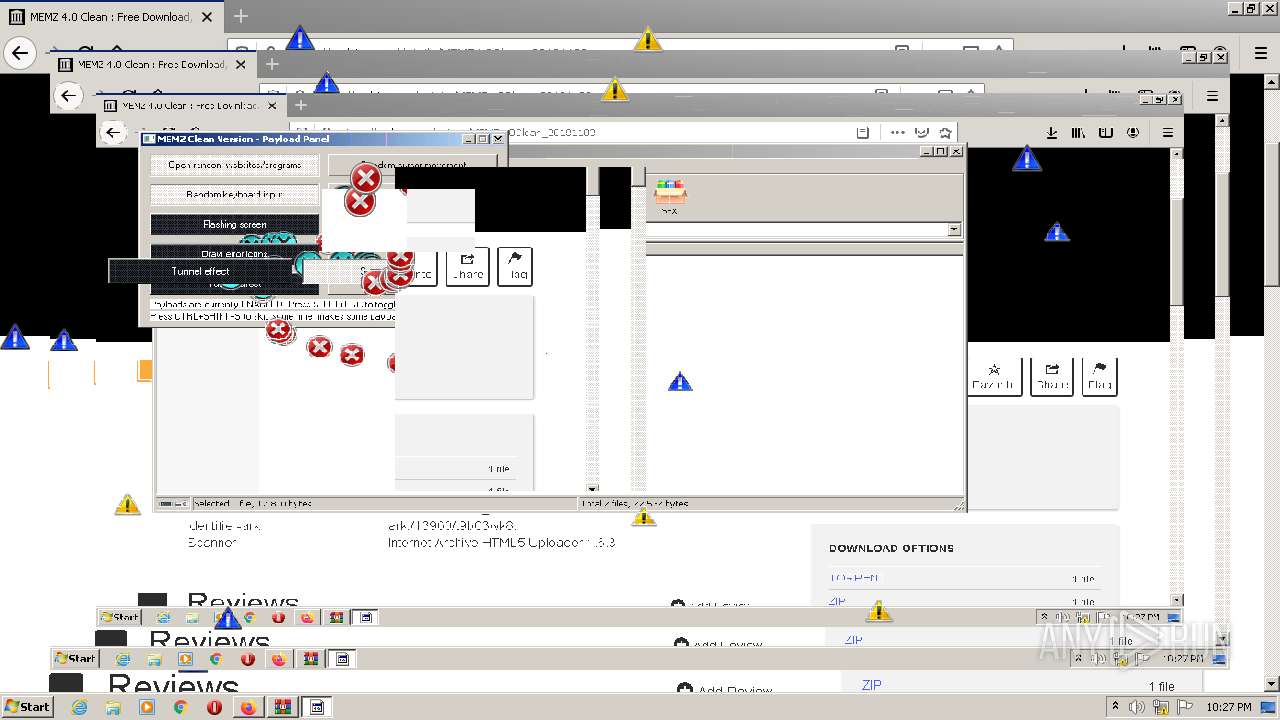
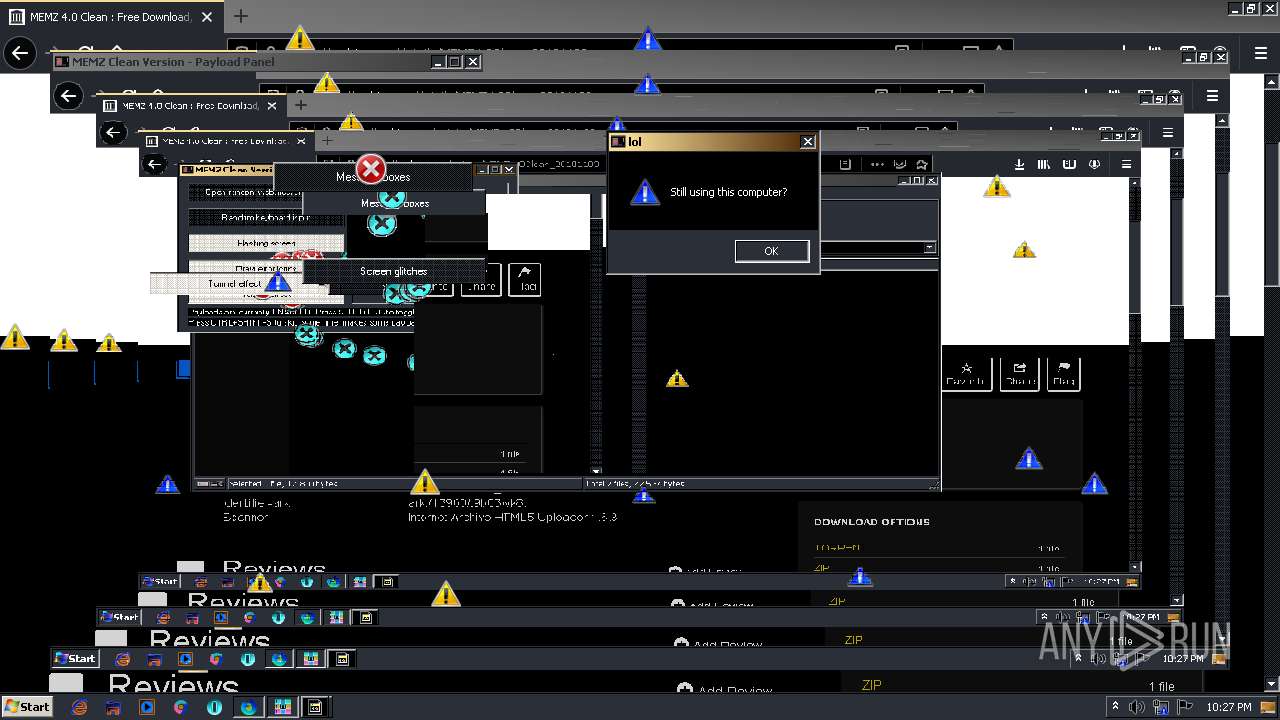
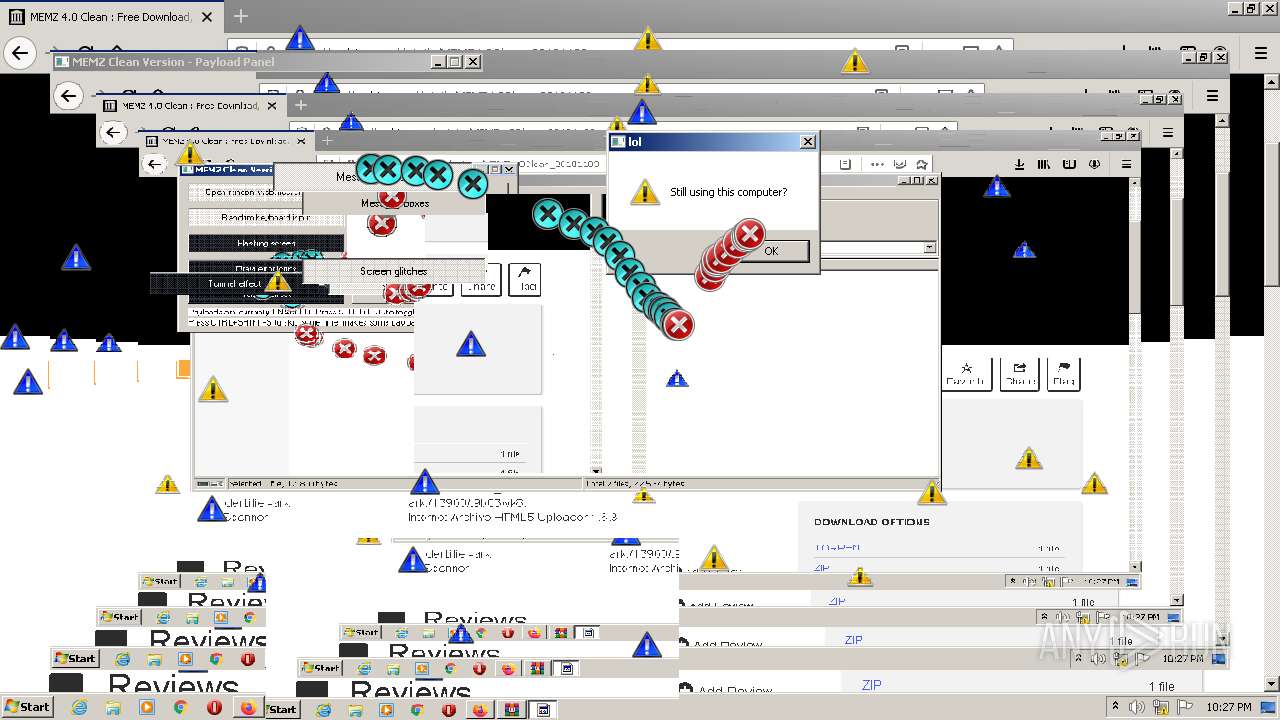
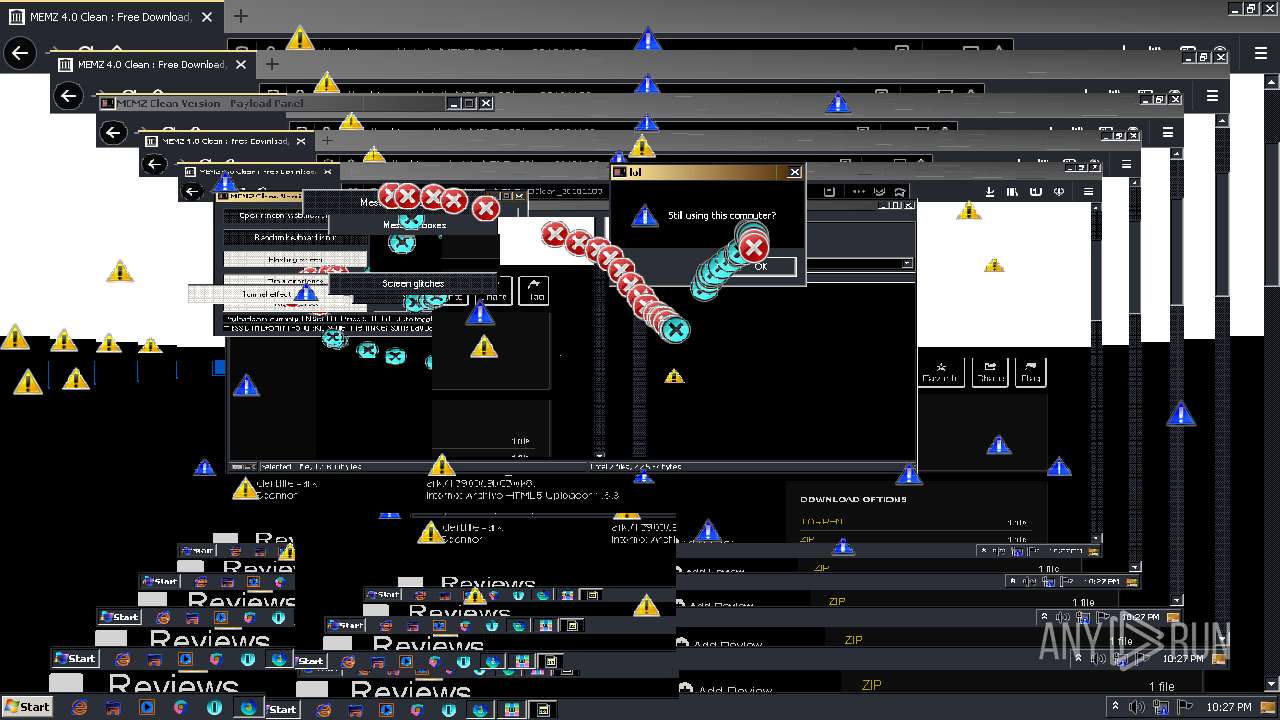
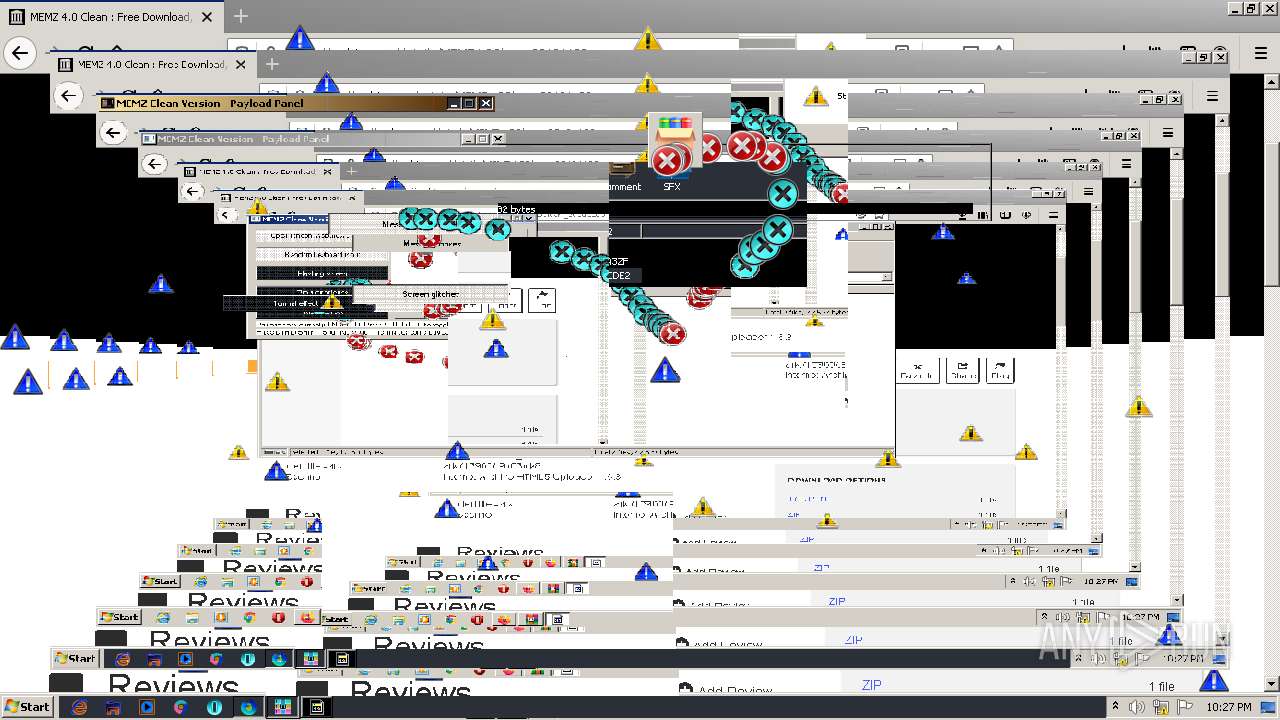
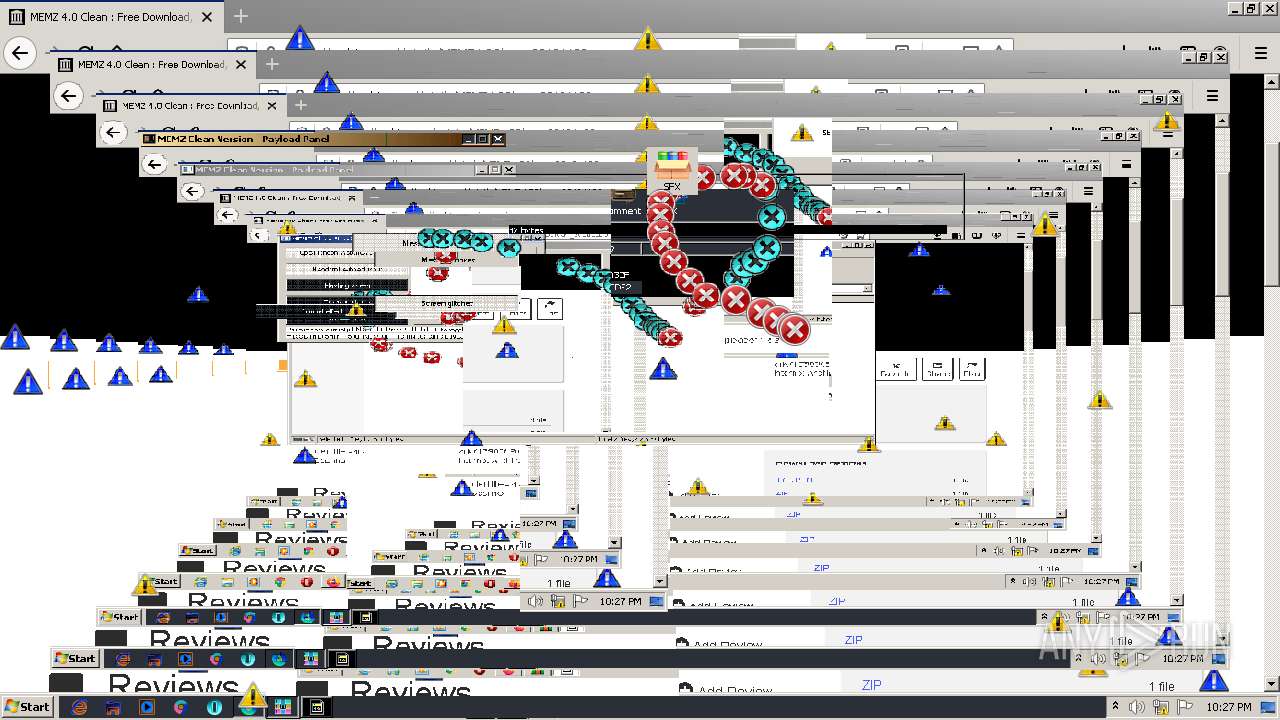
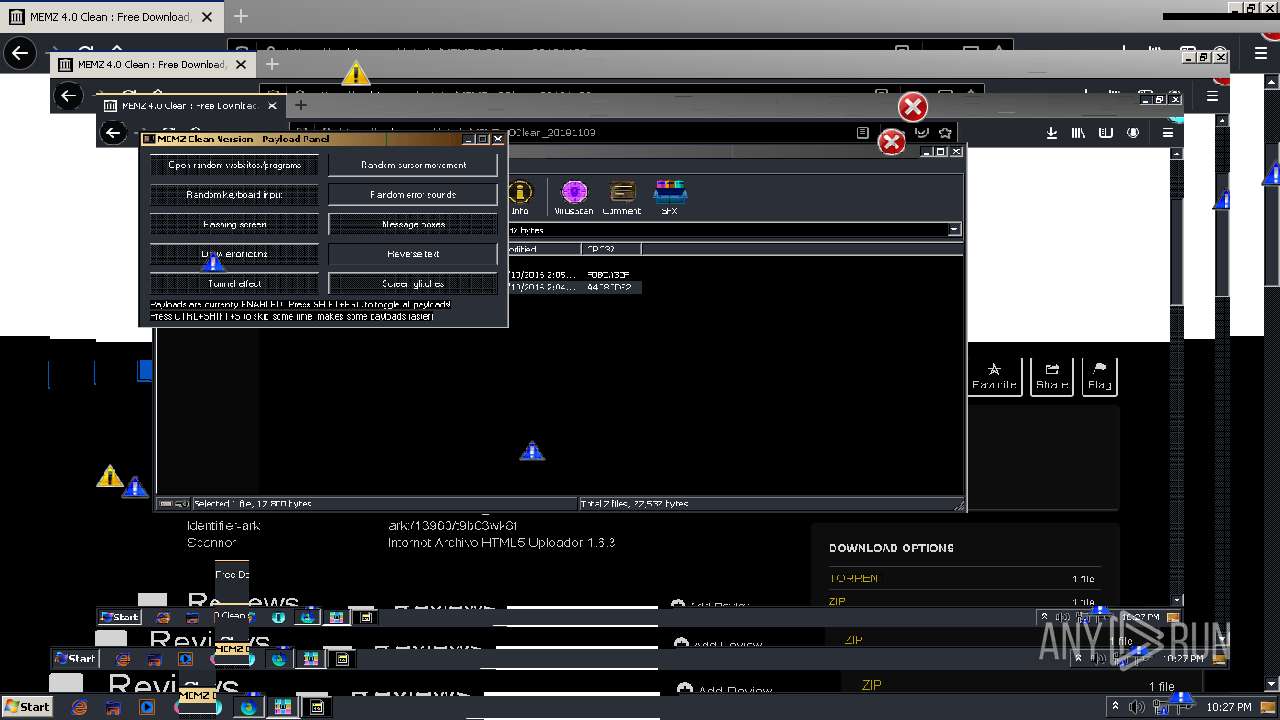
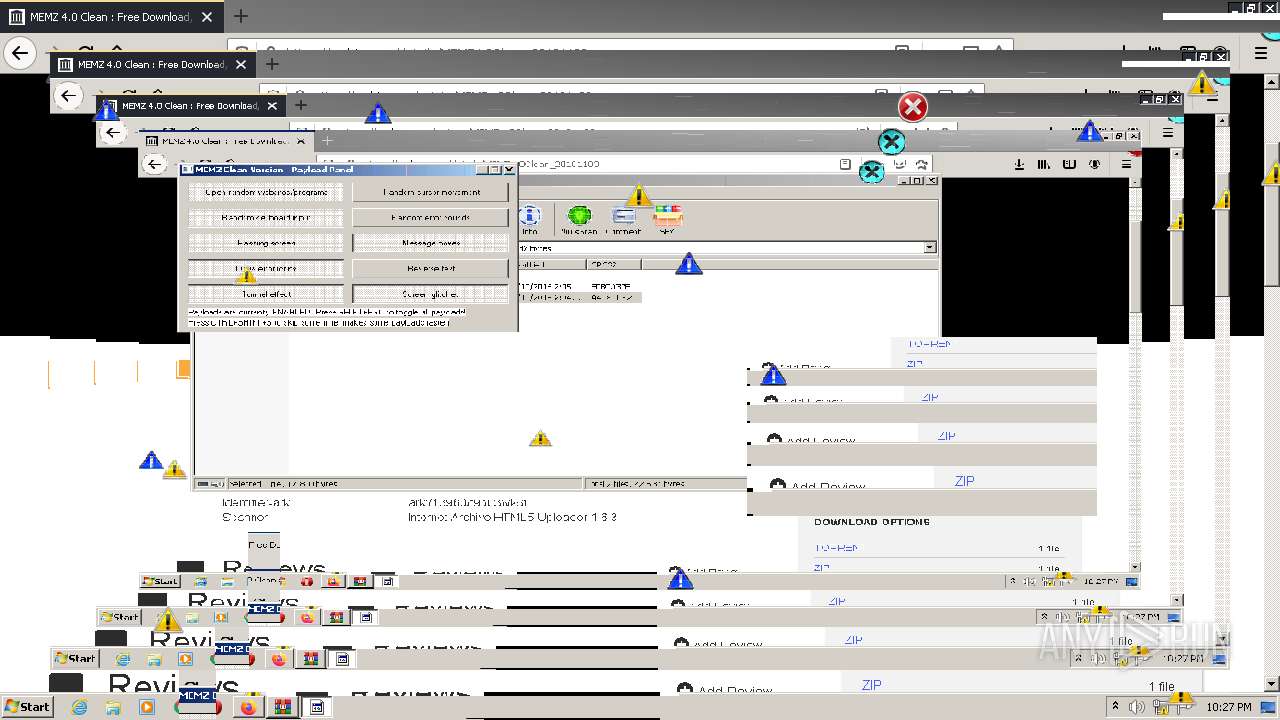
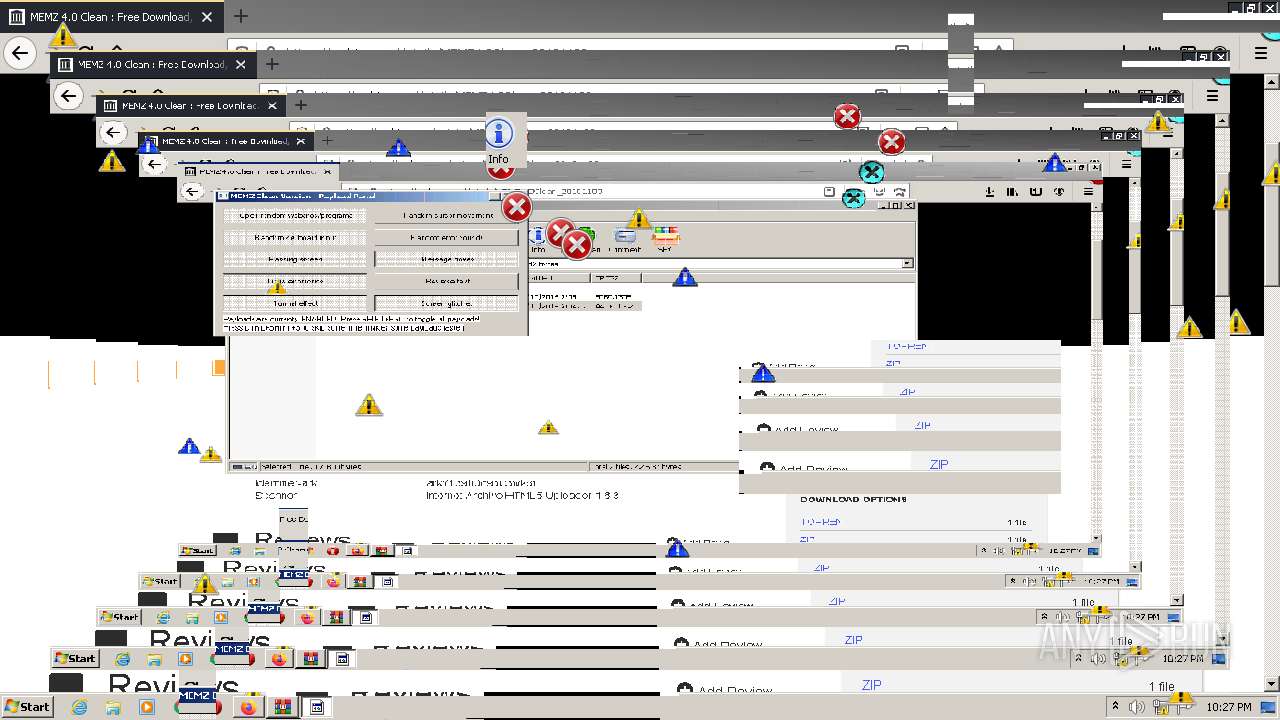
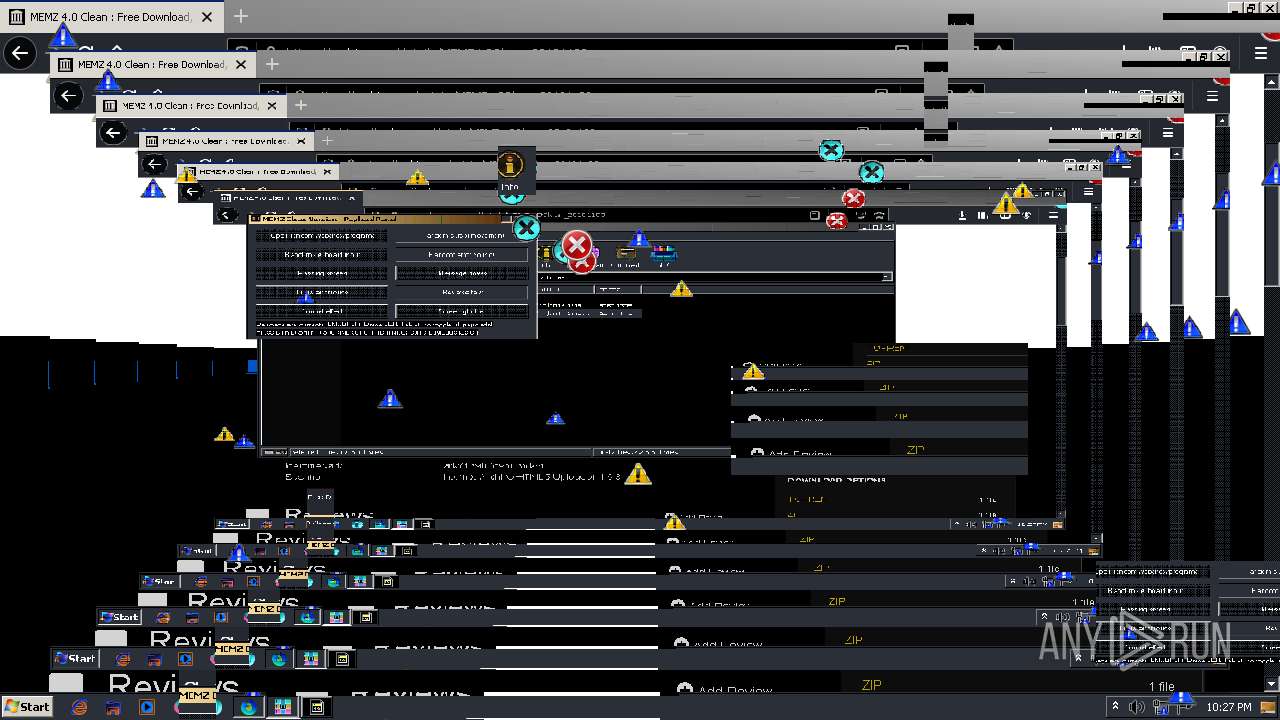
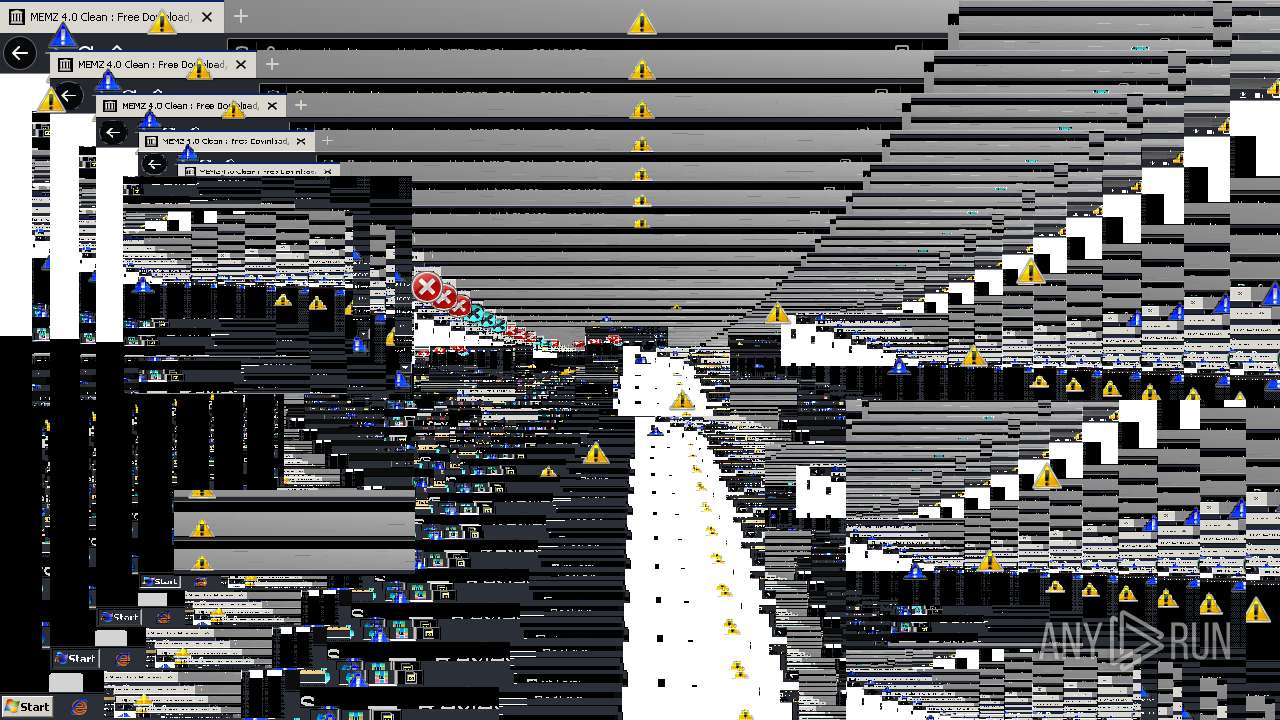
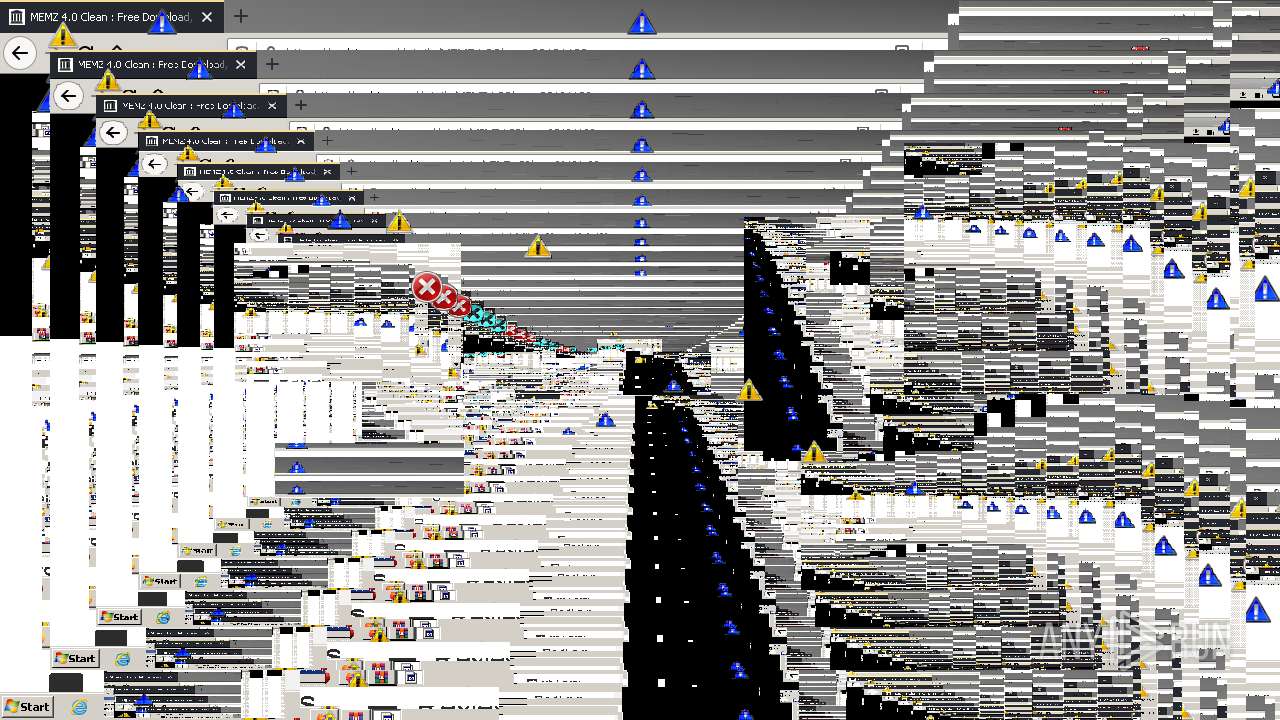
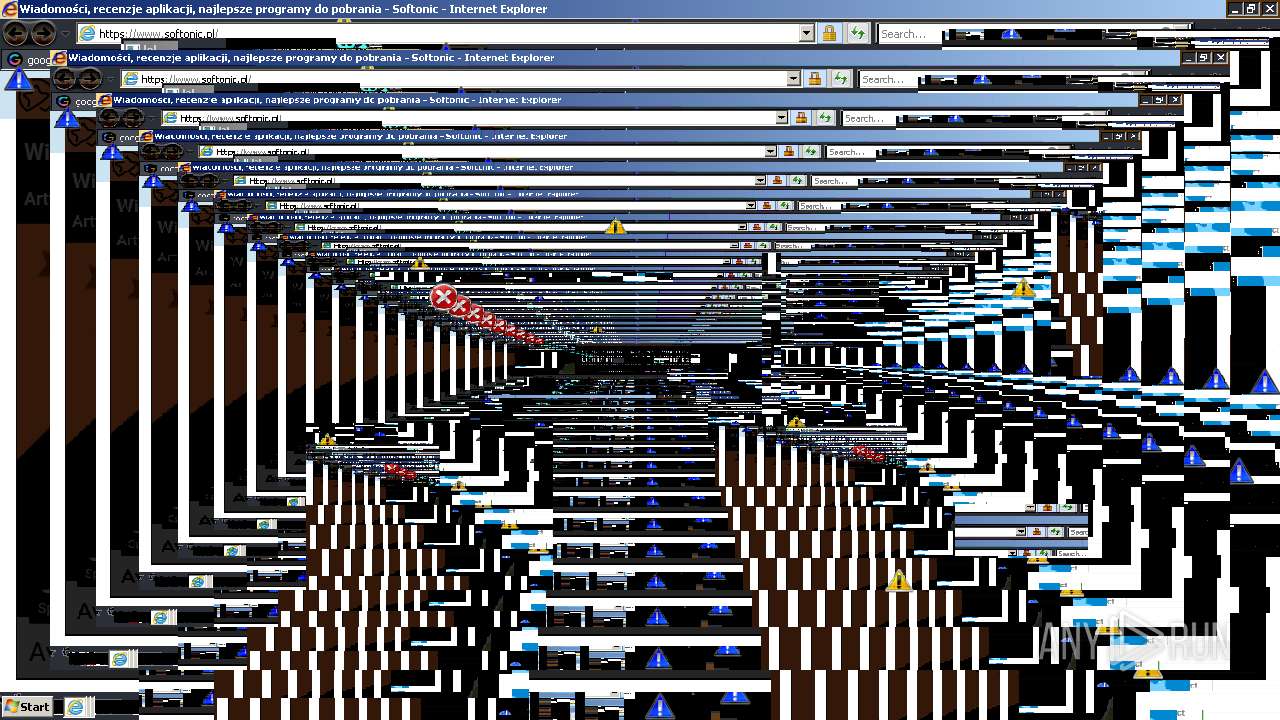
| Verdict: | Malicious activity |
| Analysis date: | January 24, 2022, 22:24:39 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 9BB3A88963C90A08131B84CA5436E9EE |
| SHA1: | 60316091C88027ED25F631CA4576C39E60E26F57 |
| SHA256: | 02EF86868E264EBE687F59964DA796A1082A3A7BFE13BEA4E3E47CDB6B388D1C |
| SSDEEP: | 3:N8MFXJwJNY8dcX:2MFXeNzdu |
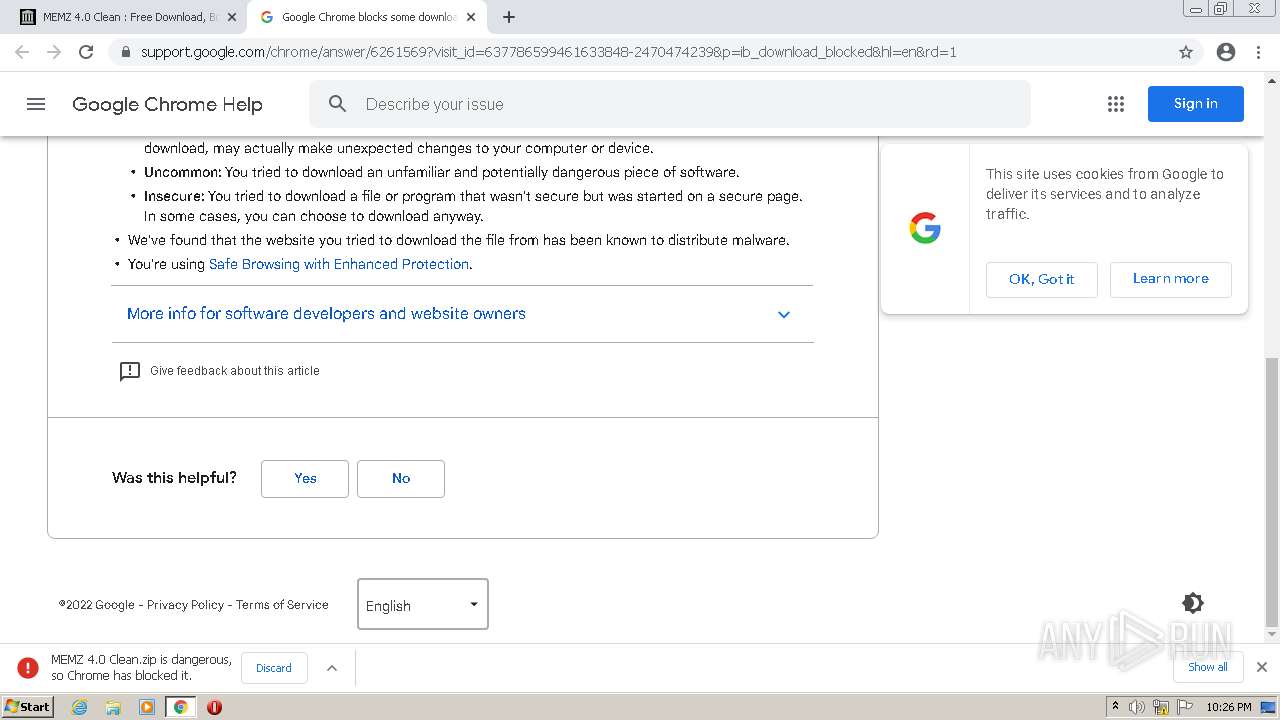
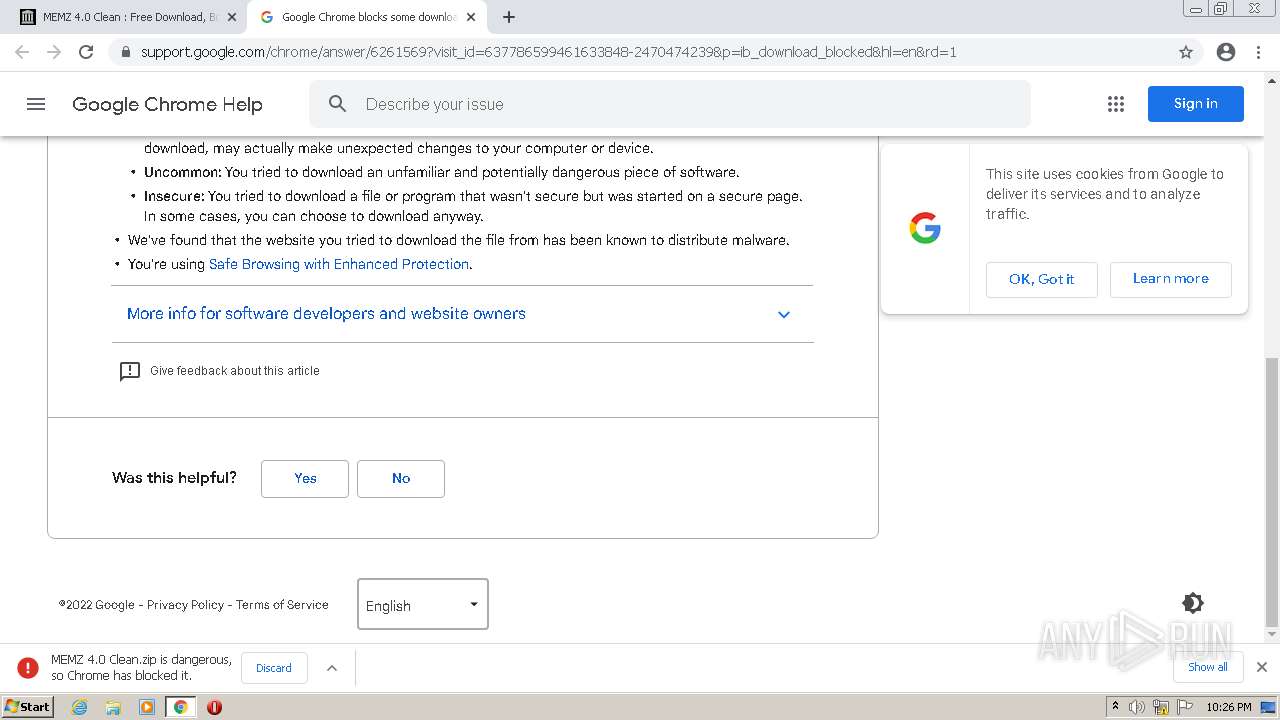
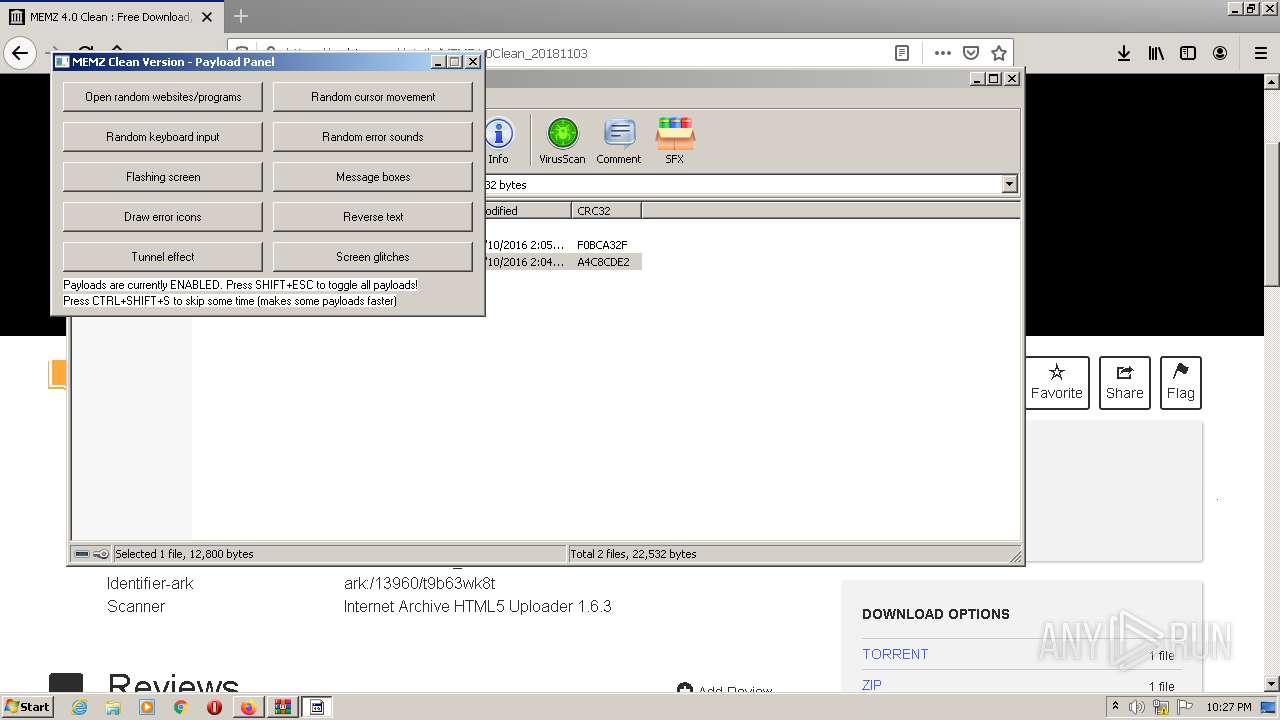
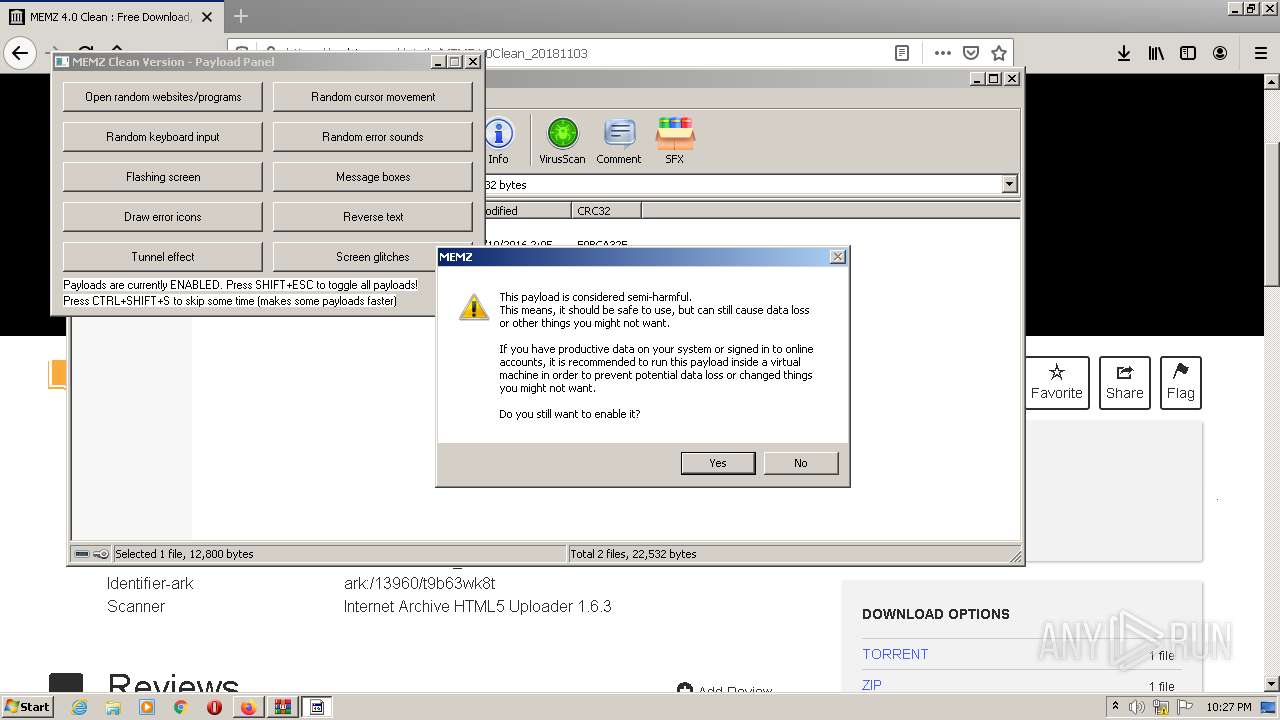
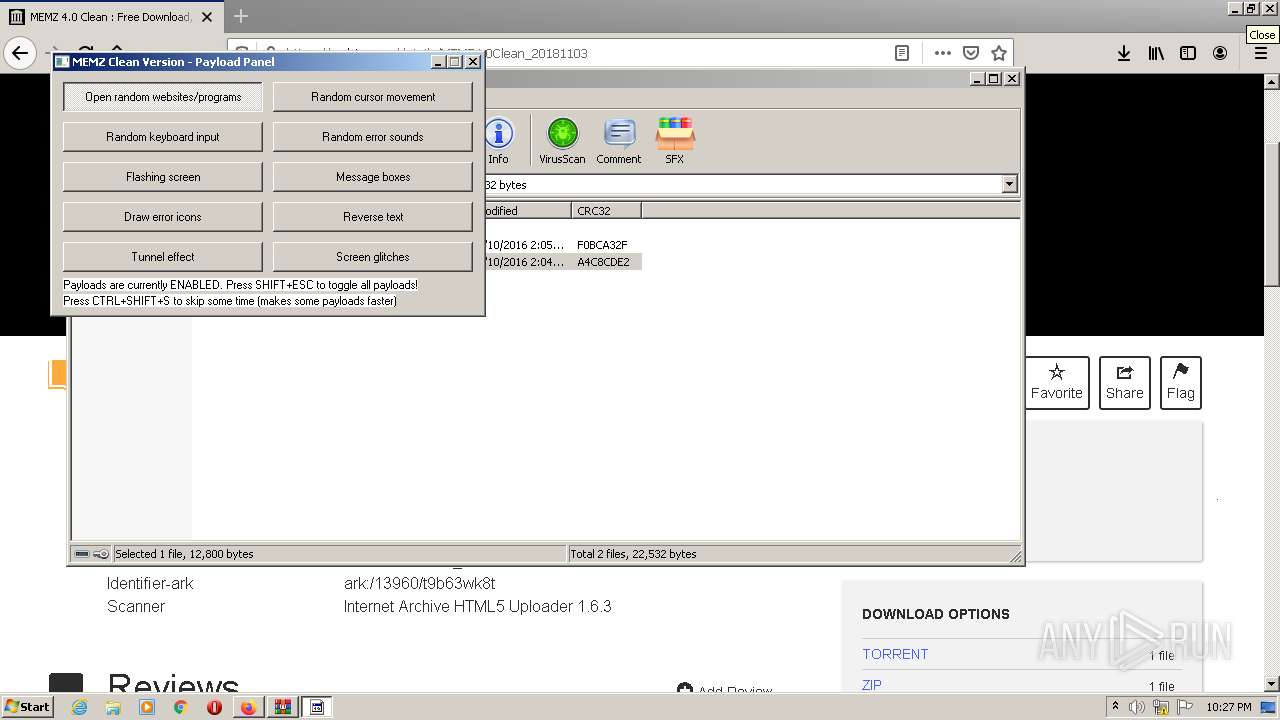
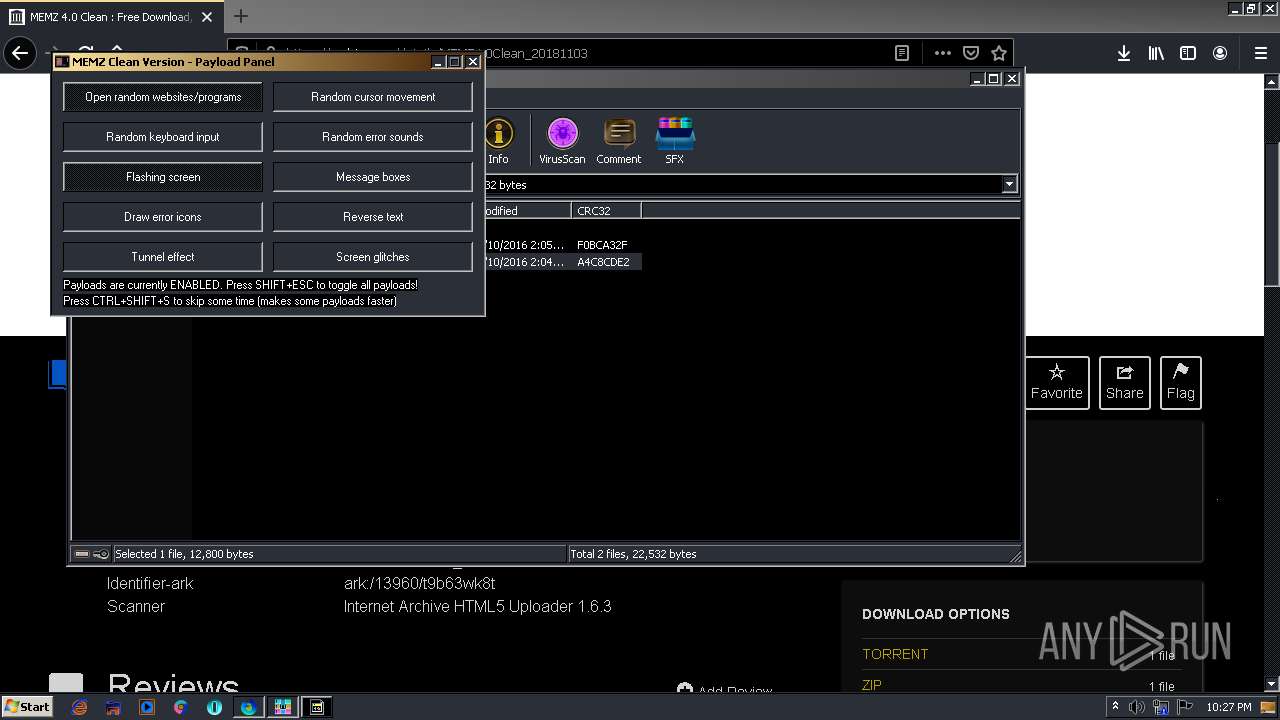
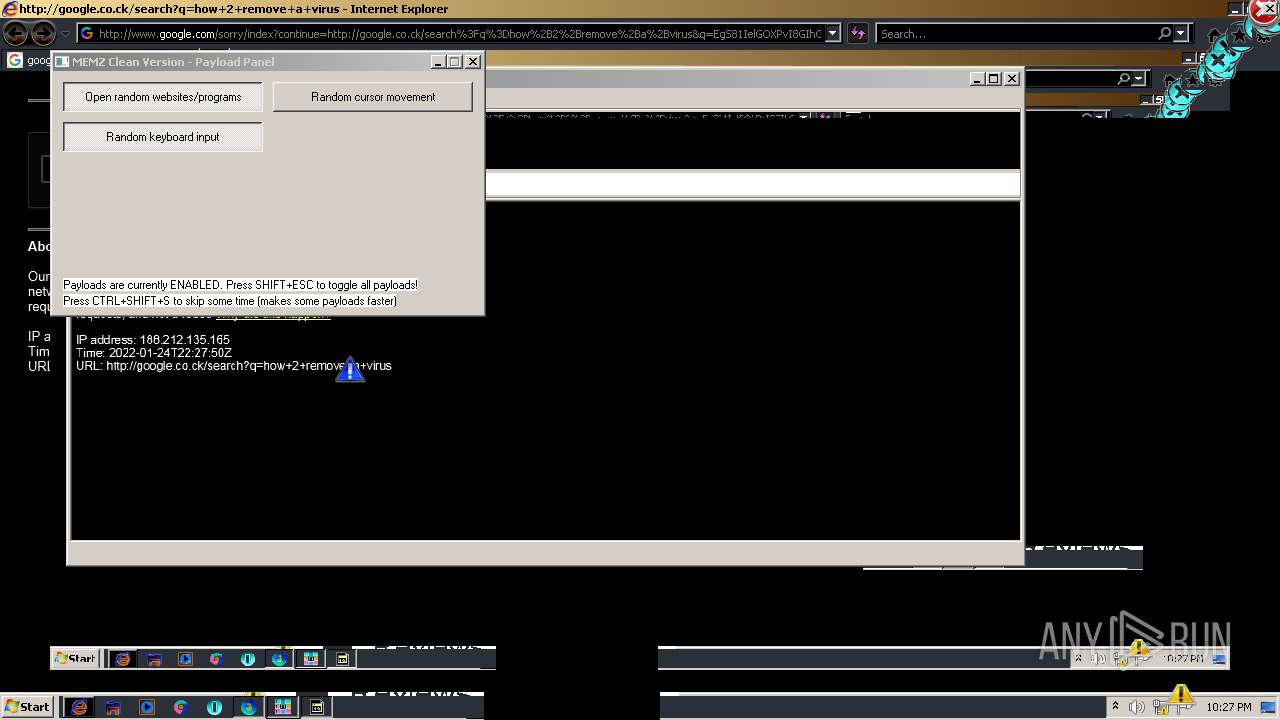
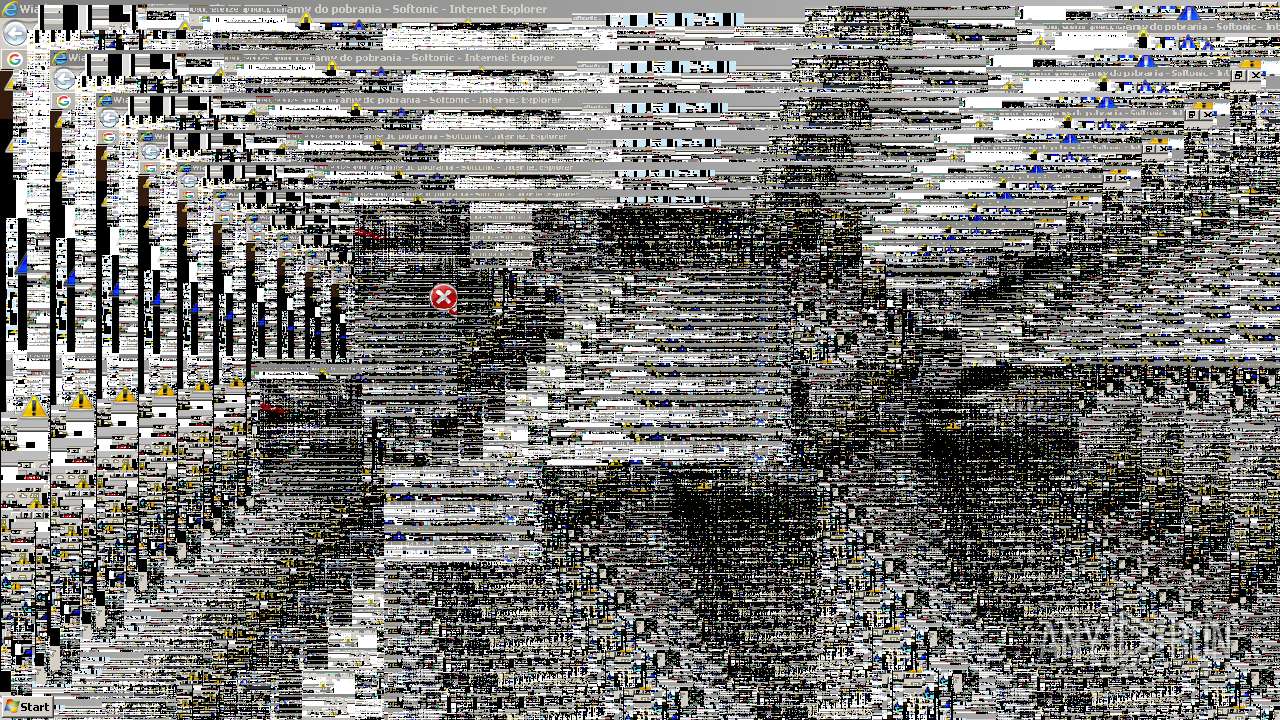
MALICIOUS
Drops executable file immediately after starts
- chrome.exe (PID: 3980)
Application was dropped or rewritten from another process
- MEMZ-Clean.exe (PID: 1420)
SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3748)
- iexplore.exe (PID: 3552)
- iexplore.exe (PID: 2312)
- iexplore.exe (PID: 3704)
- iexplore.exe (PID: 2788)
- iexplore.exe (PID: 3224)
- iexplore.exe (PID: 2740)
Modifies files in Chrome extension folder
- chrome.exe (PID: 2092)
Executable content was dropped or overwritten
- chrome.exe (PID: 3980)
- WinRAR.exe (PID: 3884)
- firefox.exe (PID: 344)
Checks supported languages
- WinRAR.exe (PID: 3884)
- MEMZ-Clean.exe (PID: 1420)
Reads the computer name
- WinRAR.exe (PID: 3884)
- MEMZ-Clean.exe (PID: 1420)
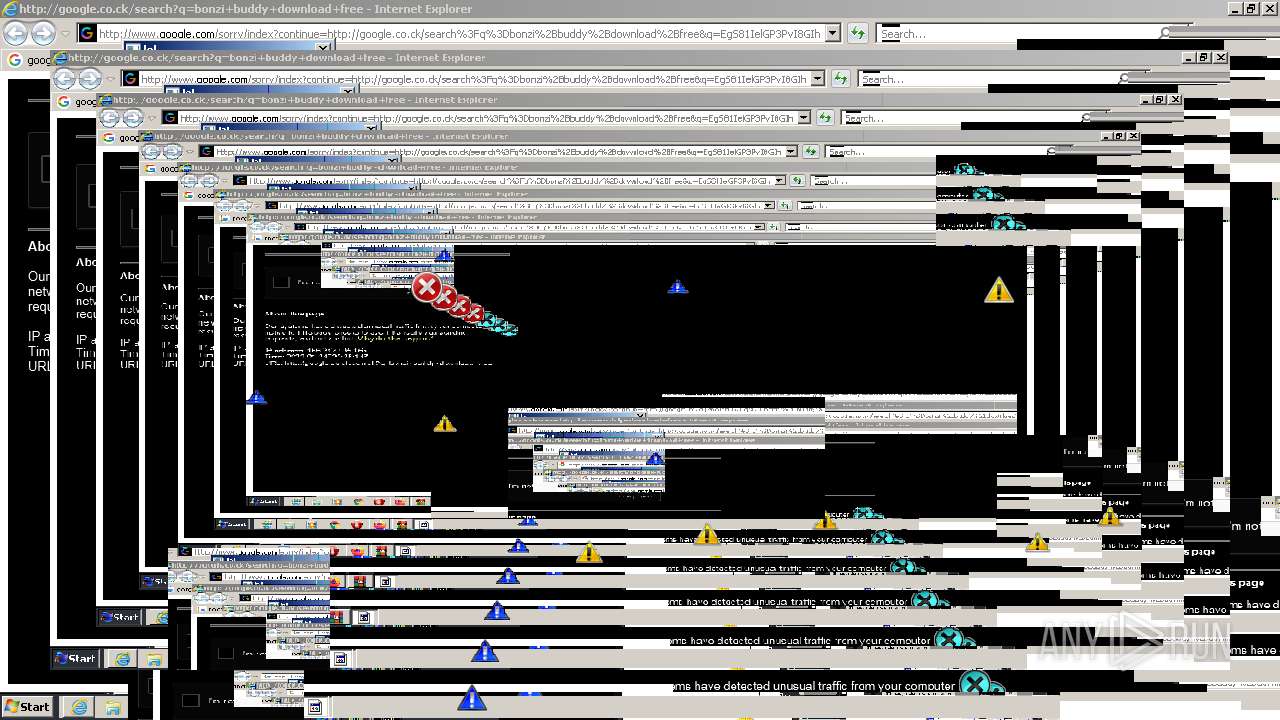
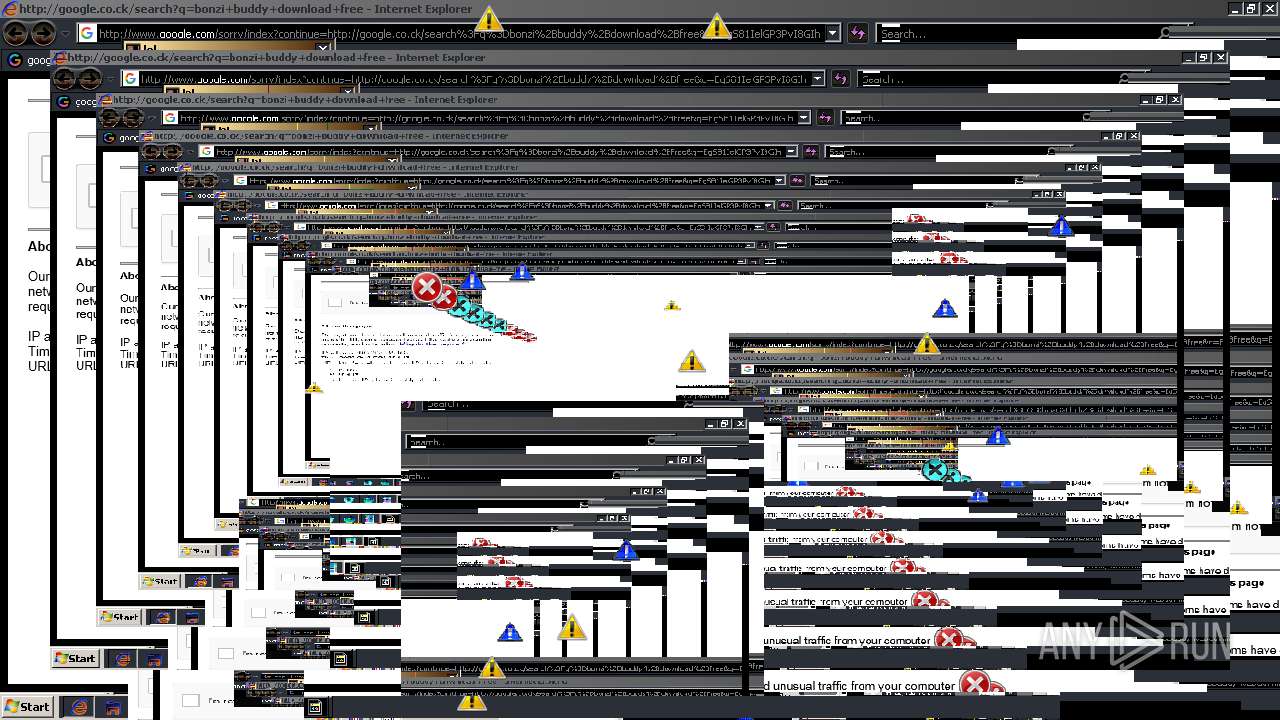
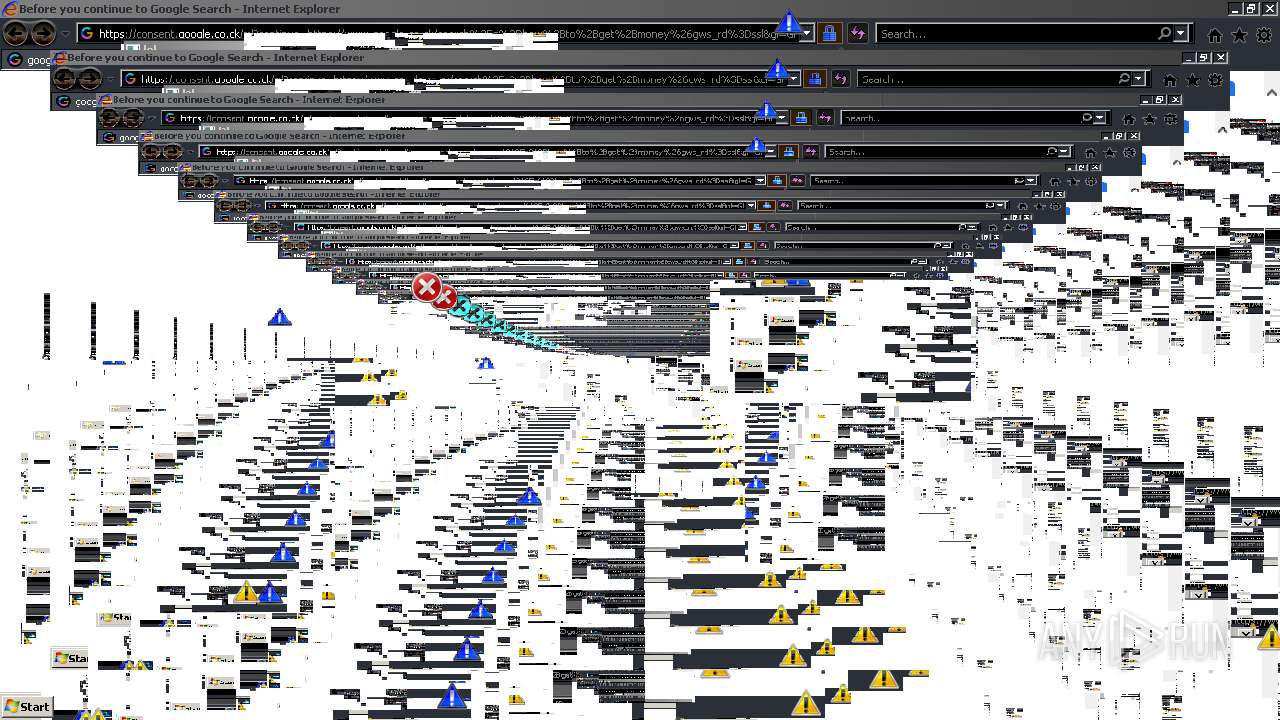
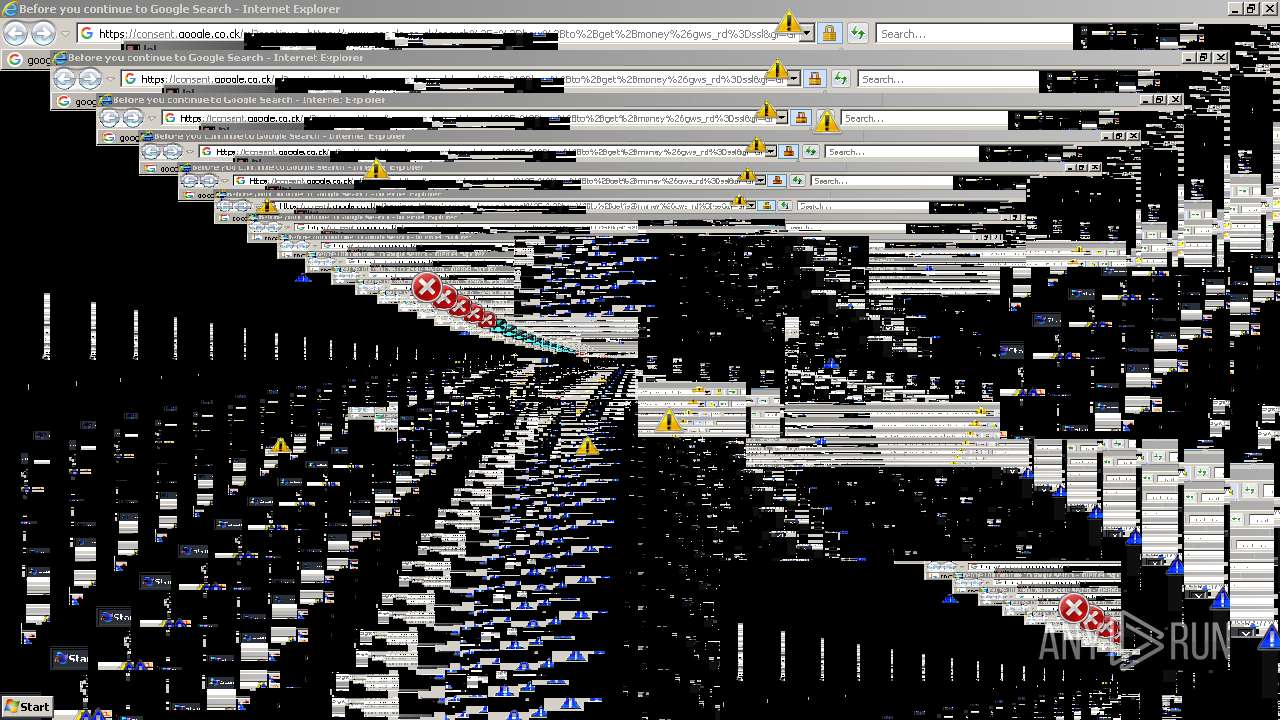
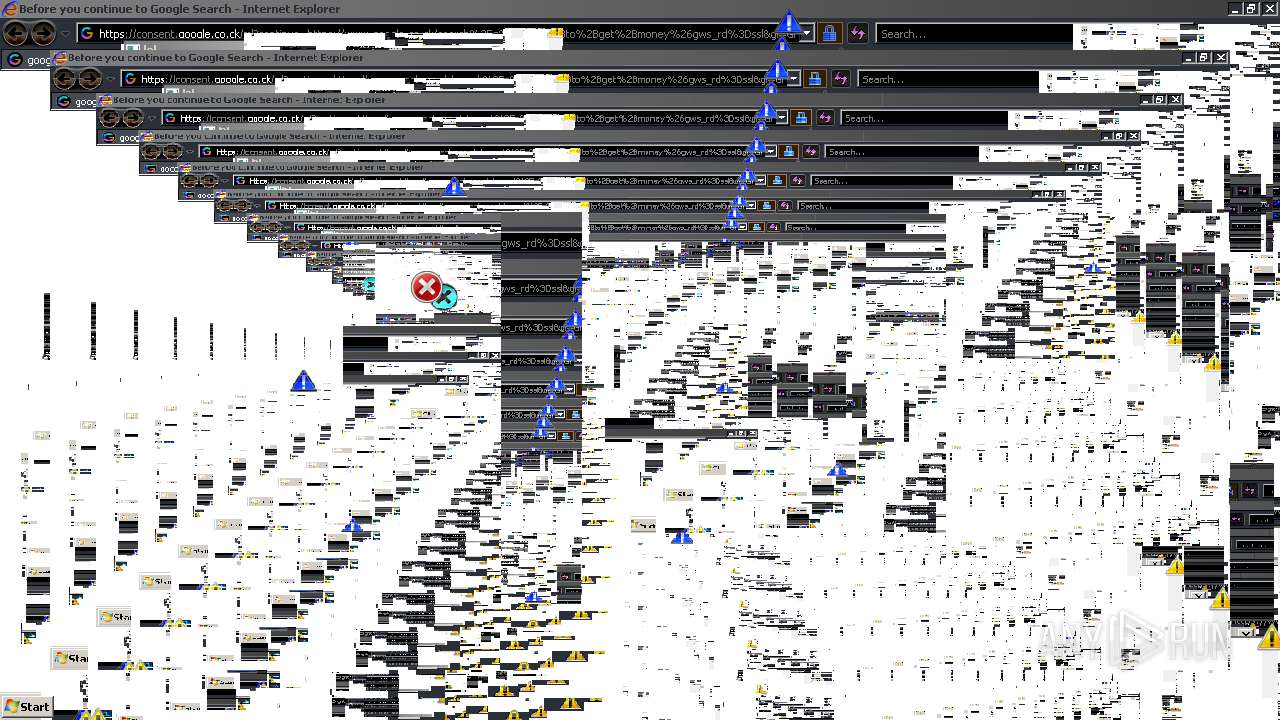
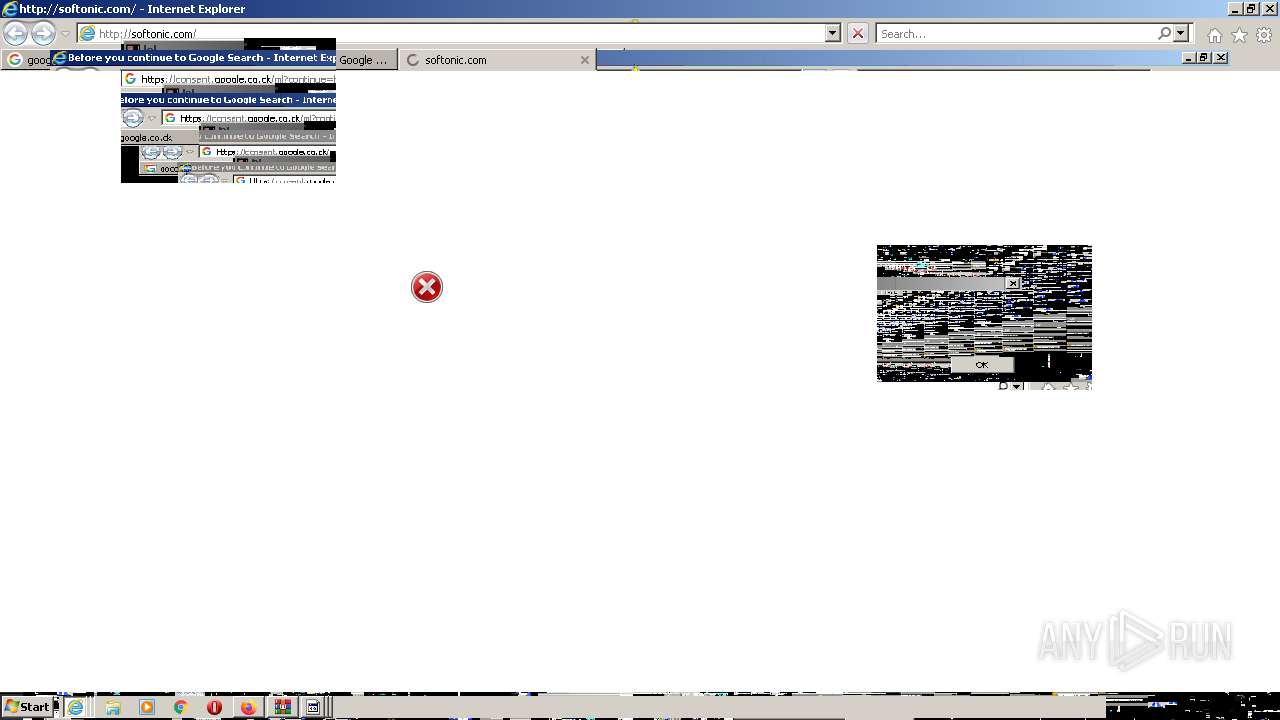
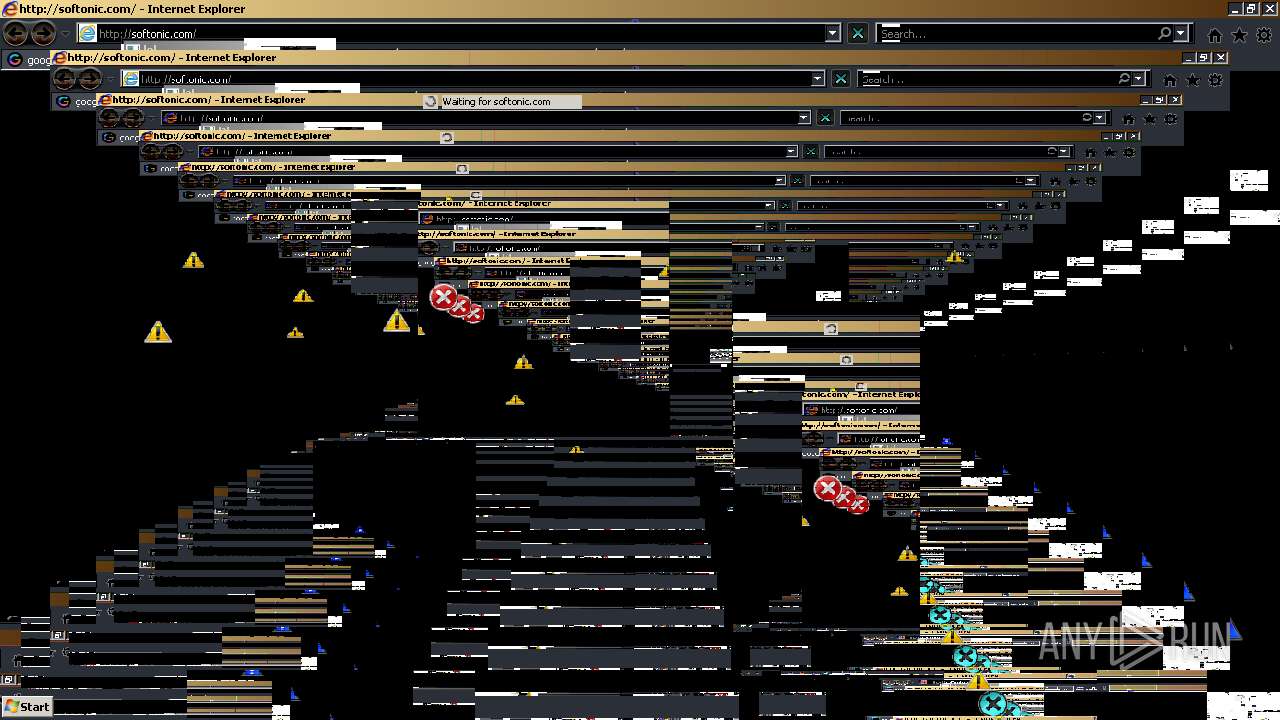
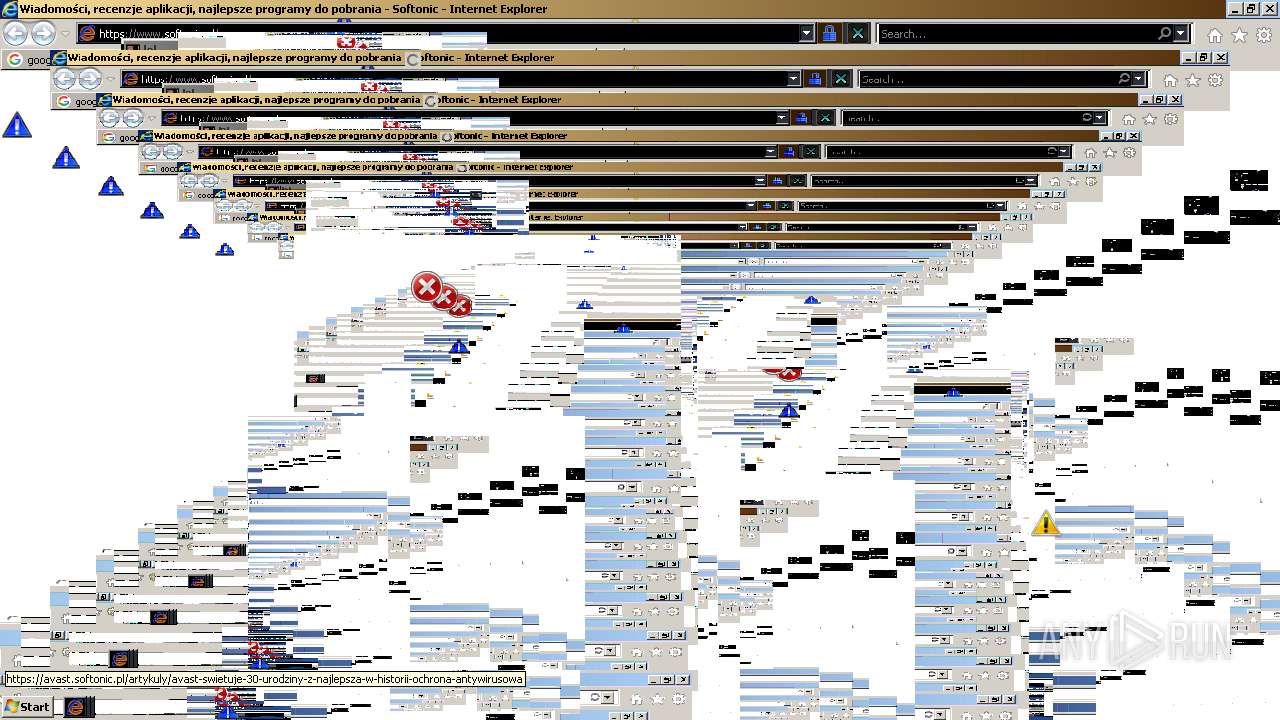
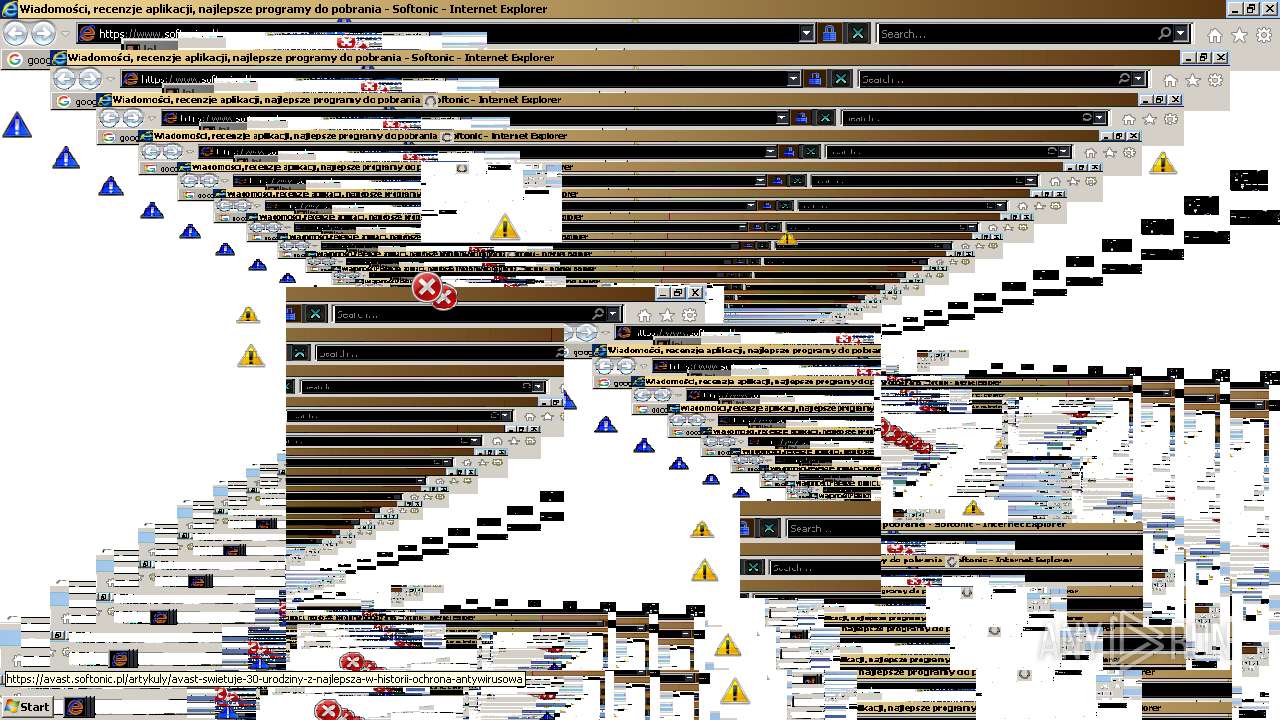
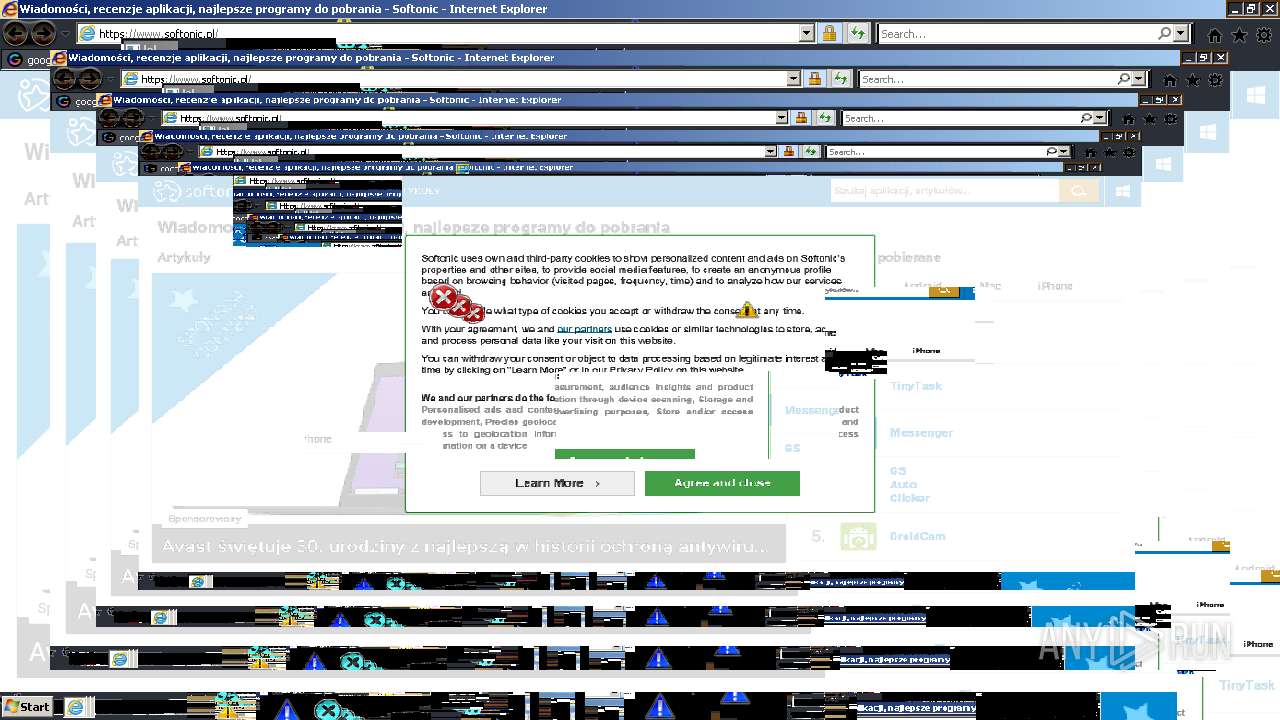
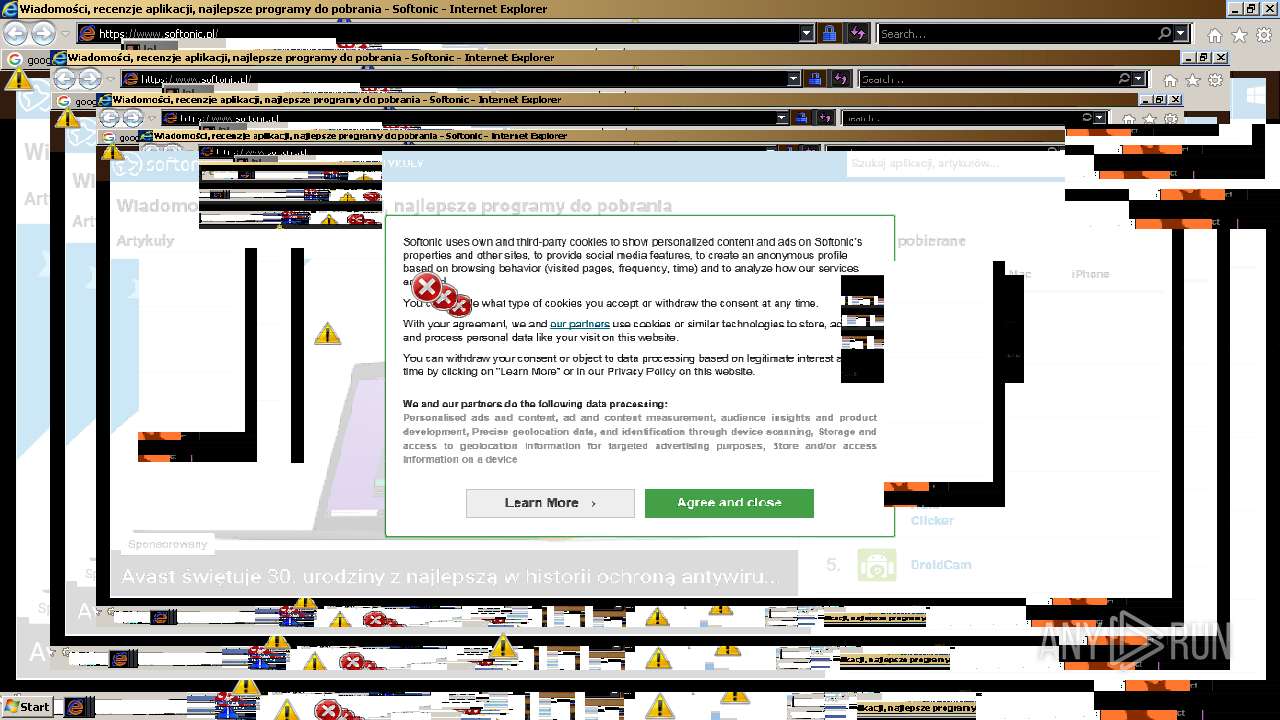
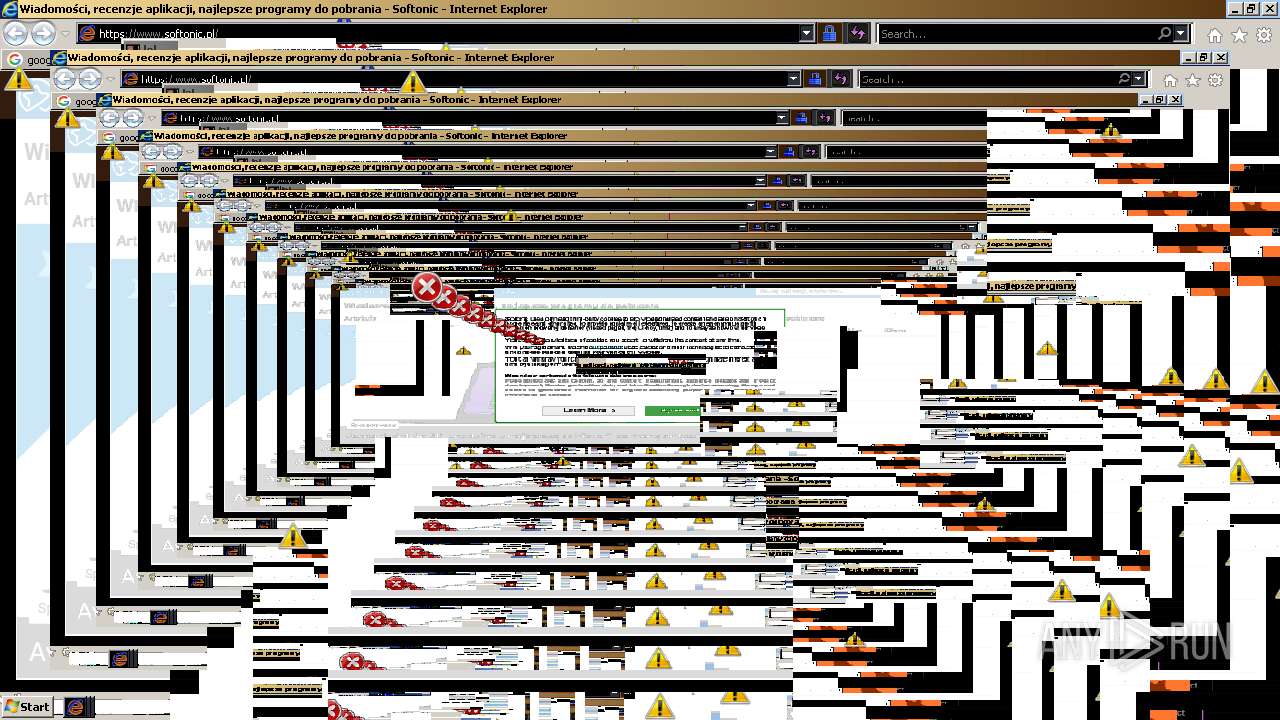
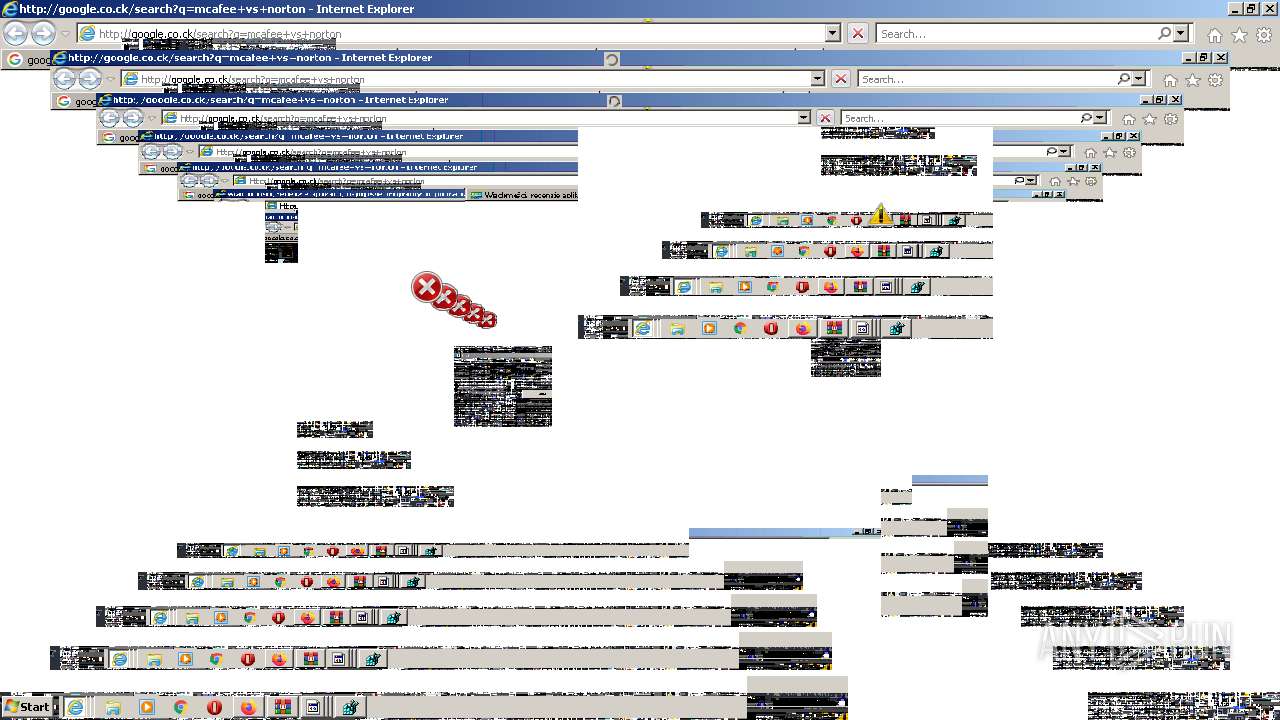
Starts Internet Explorer
- MEMZ-Clean.exe (PID: 1420)
Drops a file that was compiled in debug mode
- firefox.exe (PID: 344)
INFO
Reads the computer name
- iexplore.exe (PID: 2184)
- iexplore.exe (PID: 3748)
- chrome.exe (PID: 2092)
- chrome.exe (PID: 3432)
- chrome.exe (PID: 3532)
- chrome.exe (PID: 2656)
- chrome.exe (PID: 3392)
- chrome.exe (PID: 2784)
- chrome.exe (PID: 2132)
- firefox.exe (PID: 344)
- chrome.exe (PID: 3628)
- firefox.exe (PID: 1056)
- firefox.exe (PID: 3512)
- firefox.exe (PID: 2520)
- firefox.exe (PID: 3140)
- firefox.exe (PID: 592)
- firefox.exe (PID: 3460)
- firefox.exe (PID: 1324)
- iexplore.exe (PID: 3592)
- iexplore.exe (PID: 3552)
- iexplore.exe (PID: 348)
- iexplore.exe (PID: 2312)
- iexplore.exe (PID: 3704)
- iexplore.exe (PID: 1820)
- iexplore.exe (PID: 2788)
- iexplore.exe (PID: 3224)
- iexplore.exe (PID: 2740)
Application launched itself
- iexplore.exe (PID: 2184)
- chrome.exe (PID: 2092)
- firefox.exe (PID: 2052)
- firefox.exe (PID: 344)
- iexplore.exe (PID: 3592)
- iexplore.exe (PID: 348)
- iexplore.exe (PID: 1820)
Checks supported languages
- iexplore.exe (PID: 2184)
- iexplore.exe (PID: 3748)
- chrome.exe (PID: 2092)
- chrome.exe (PID: 1300)
- chrome.exe (PID: 3432)
- chrome.exe (PID: 3532)
- chrome.exe (PID: 636)
- chrome.exe (PID: 2668)
- chrome.exe (PID: 4076)
- chrome.exe (PID: 2656)
- chrome.exe (PID: 924)
- chrome.exe (PID: 3272)
- chrome.exe (PID: 3700)
- chrome.exe (PID: 1908)
- chrome.exe (PID: 2888)
- chrome.exe (PID: 3392)
- chrome.exe (PID: 4020)
- chrome.exe (PID: 3980)
- chrome.exe (PID: 2784)
- chrome.exe (PID: 3628)
- chrome.exe (PID: 2132)
- chrome.exe (PID: 3120)
- chrome.exe (PID: 4064)
- firefox.exe (PID: 2052)
- firefox.exe (PID: 344)
- firefox.exe (PID: 1056)
- firefox.exe (PID: 3512)
- firefox.exe (PID: 2520)
- firefox.exe (PID: 592)
- firefox.exe (PID: 3140)
- firefox.exe (PID: 3460)
- firefox.exe (PID: 1324)
- iexplore.exe (PID: 3592)
- iexplore.exe (PID: 3552)
- iexplore.exe (PID: 348)
- iexplore.exe (PID: 2312)
- iexplore.exe (PID: 1820)
- iexplore.exe (PID: 3704)
- iexplore.exe (PID: 2788)
- iexplore.exe (PID: 3224)
- regedit.exe (PID: 2852)
- iexplore.exe (PID: 2740)
Checks Windows Trust Settings
- iexplore.exe (PID: 3748)
- iexplore.exe (PID: 2184)
- firefox.exe (PID: 344)
- iexplore.exe (PID: 3552)
- iexplore.exe (PID: 2312)
- iexplore.exe (PID: 348)
- iexplore.exe (PID: 3704)
- iexplore.exe (PID: 2788)
- iexplore.exe (PID: 1820)
- iexplore.exe (PID: 3224)
- iexplore.exe (PID: 2740)
Changes internet zones settings
- iexplore.exe (PID: 2184)
- iexplore.exe (PID: 3592)
- iexplore.exe (PID: 348)
- iexplore.exe (PID: 1820)
Creates files in the user directory
- iexplore.exe (PID: 3748)
- firefox.exe (PID: 344)
- iexplore.exe (PID: 3552)
- iexplore.exe (PID: 2788)
- iexplore.exe (PID: 3224)
- iexplore.exe (PID: 1820)
Reads the date of Windows installation
- iexplore.exe (PID: 2184)
- chrome.exe (PID: 2132)
- iexplore.exe (PID: 3592)
- firefox.exe (PID: 344)
- iexplore.exe (PID: 348)
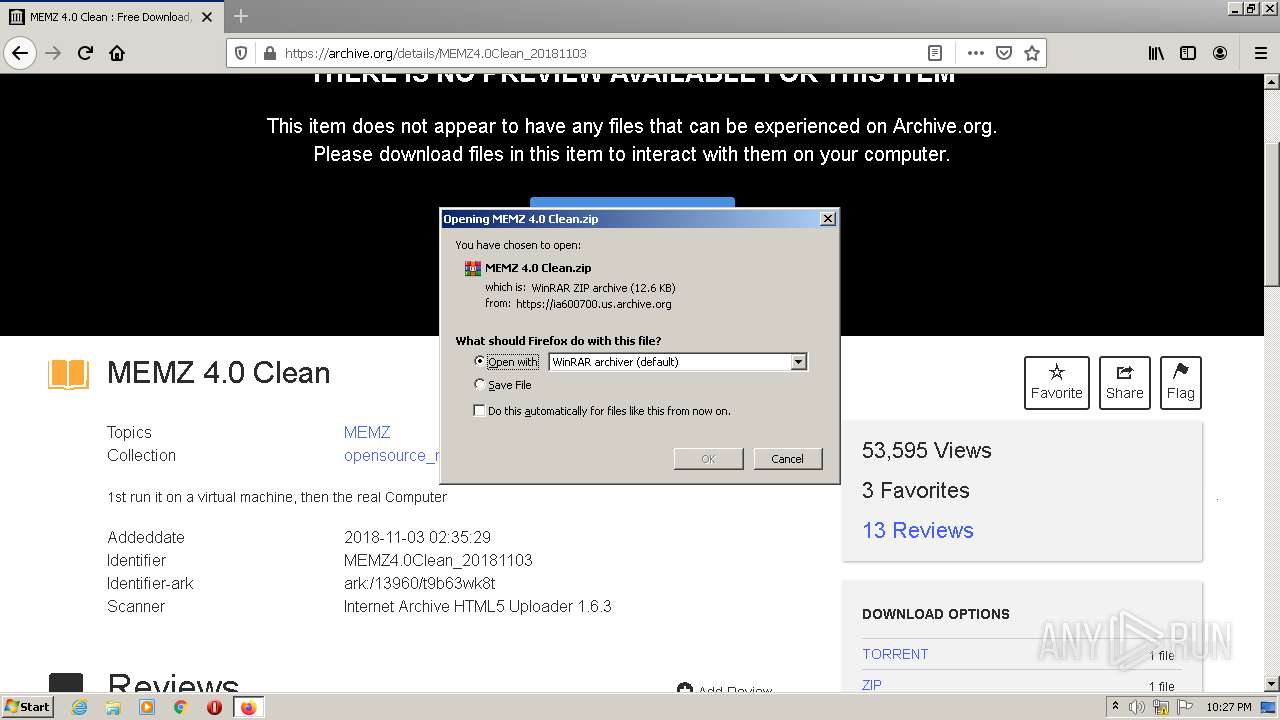
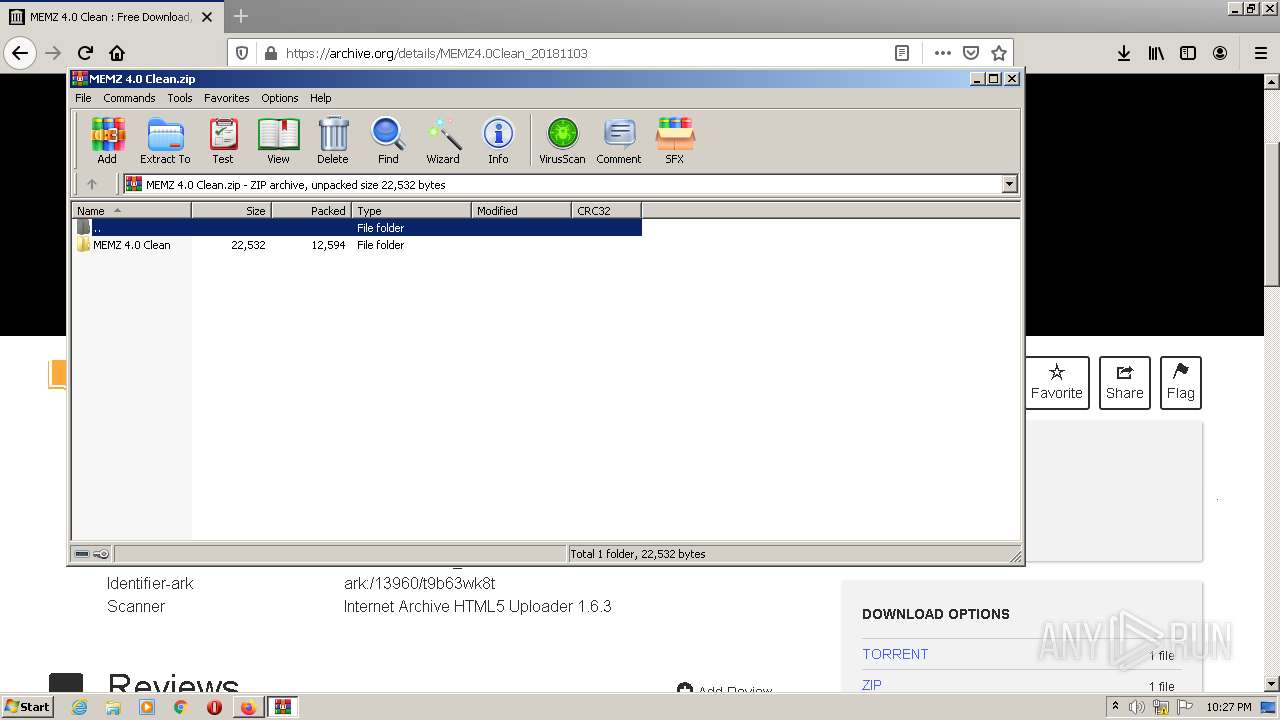
Manual execution by user
- chrome.exe (PID: 2092)
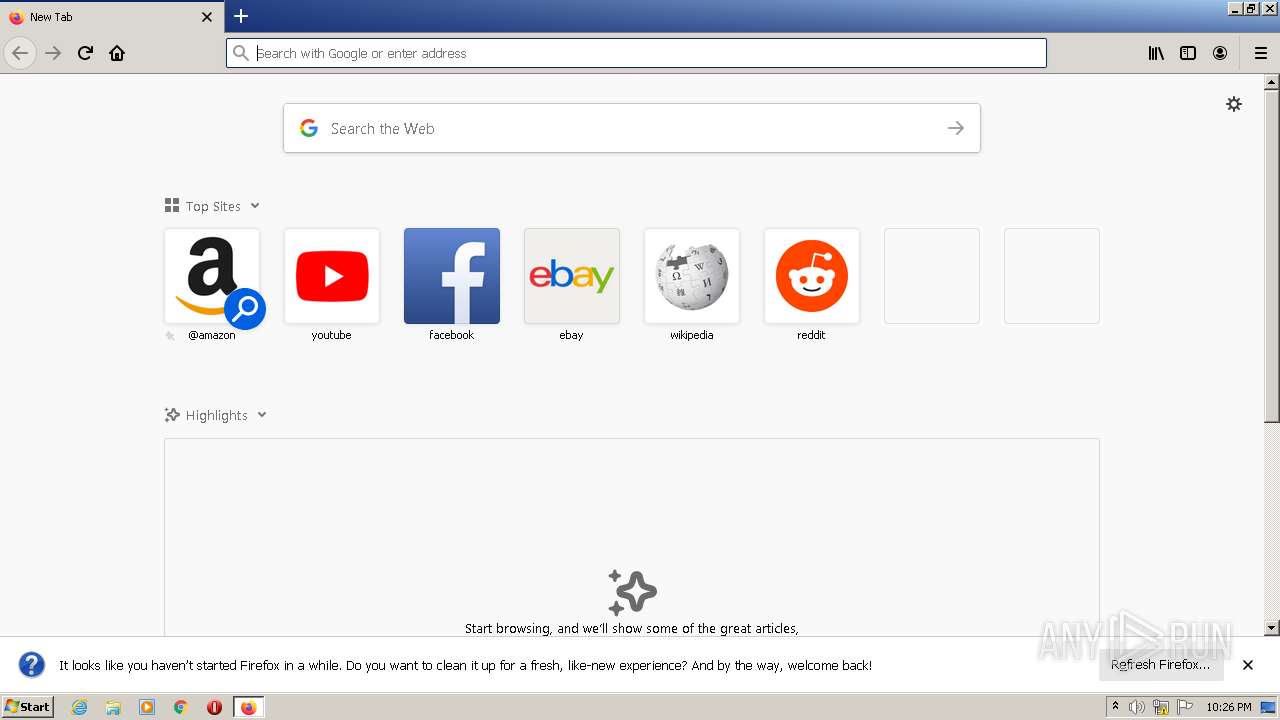
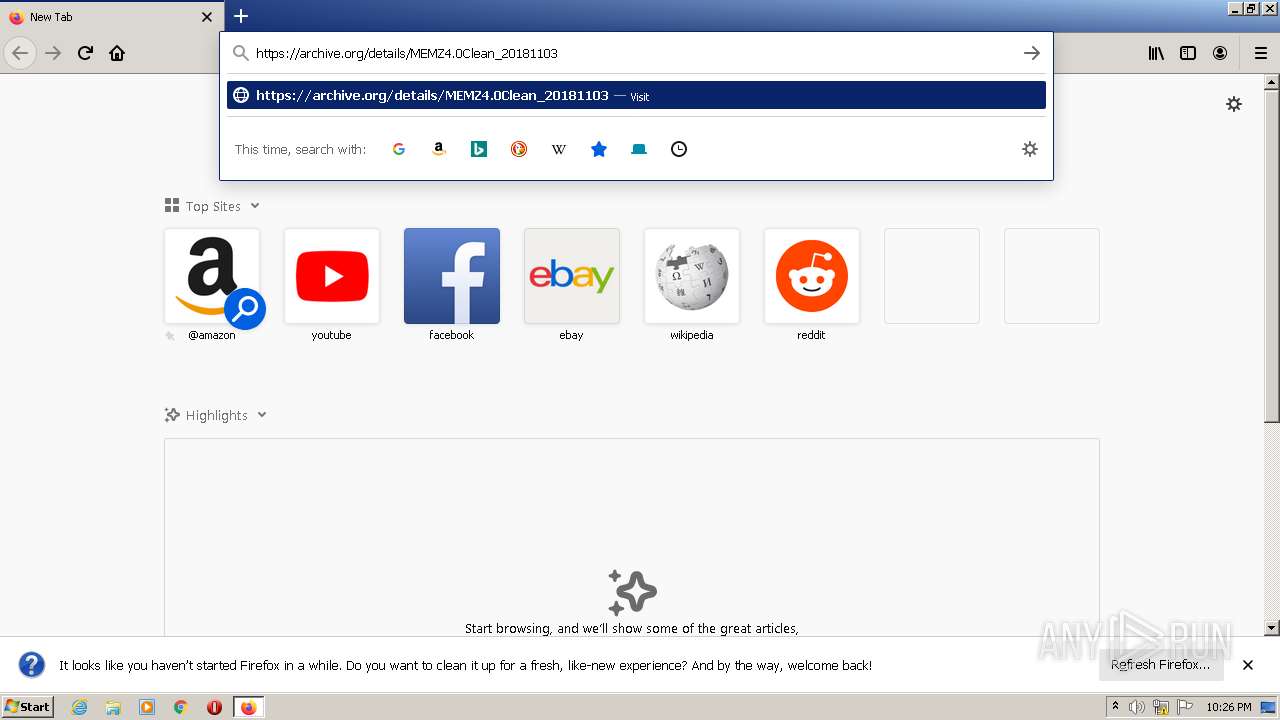
- firefox.exe (PID: 2052)
- WinRAR.exe (PID: 3884)
Reads settings of System Certificates
- iexplore.exe (PID: 2184)
- iexplore.exe (PID: 3748)
- chrome.exe (PID: 3532)
- iexplore.exe (PID: 3552)
- iexplore.exe (PID: 2312)
- iexplore.exe (PID: 348)
- iexplore.exe (PID: 3704)
- iexplore.exe (PID: 2788)
- iexplore.exe (PID: 1820)
- iexplore.exe (PID: 3224)
- iexplore.exe (PID: 2740)
Reads internet explorer settings
- iexplore.exe (PID: 3748)
- iexplore.exe (PID: 3552)
- iexplore.exe (PID: 2312)
- iexplore.exe (PID: 3704)
- iexplore.exe (PID: 2788)
- iexplore.exe (PID: 3224)
- iexplore.exe (PID: 2740)
Reads the hosts file
- chrome.exe (PID: 2092)
- chrome.exe (PID: 3532)
Reads CPU info
- firefox.exe (PID: 344)
Creates files in the program directory
- firefox.exe (PID: 344)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1820)
Changes settings of System certificates
- iexplore.exe (PID: 1820)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 1820)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
89
Monitored processes
45
Malicious processes
1
Suspicious processes
1
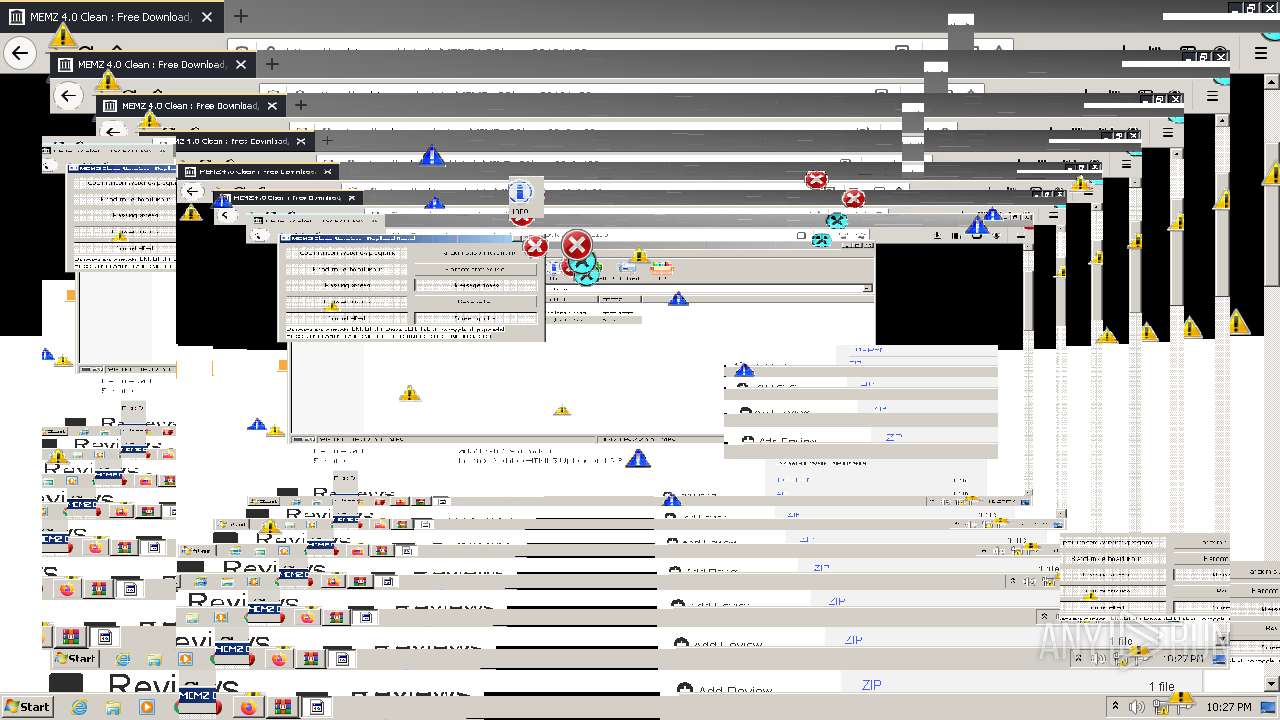
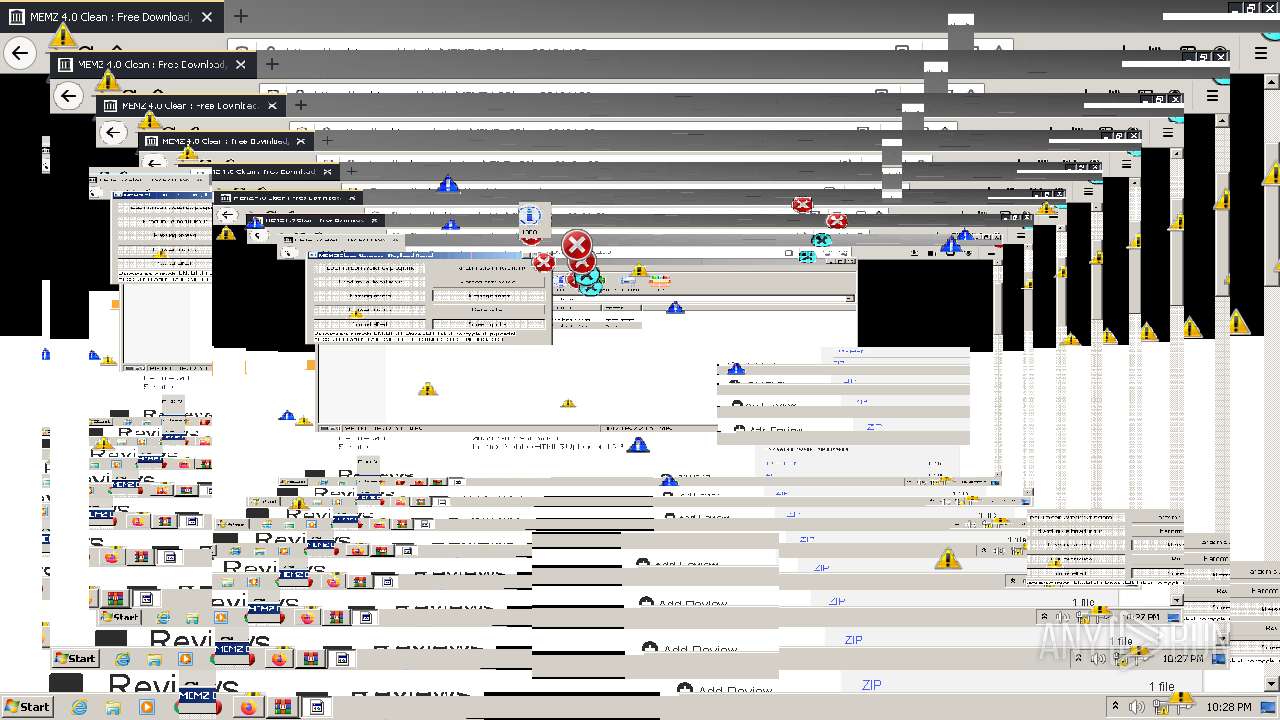
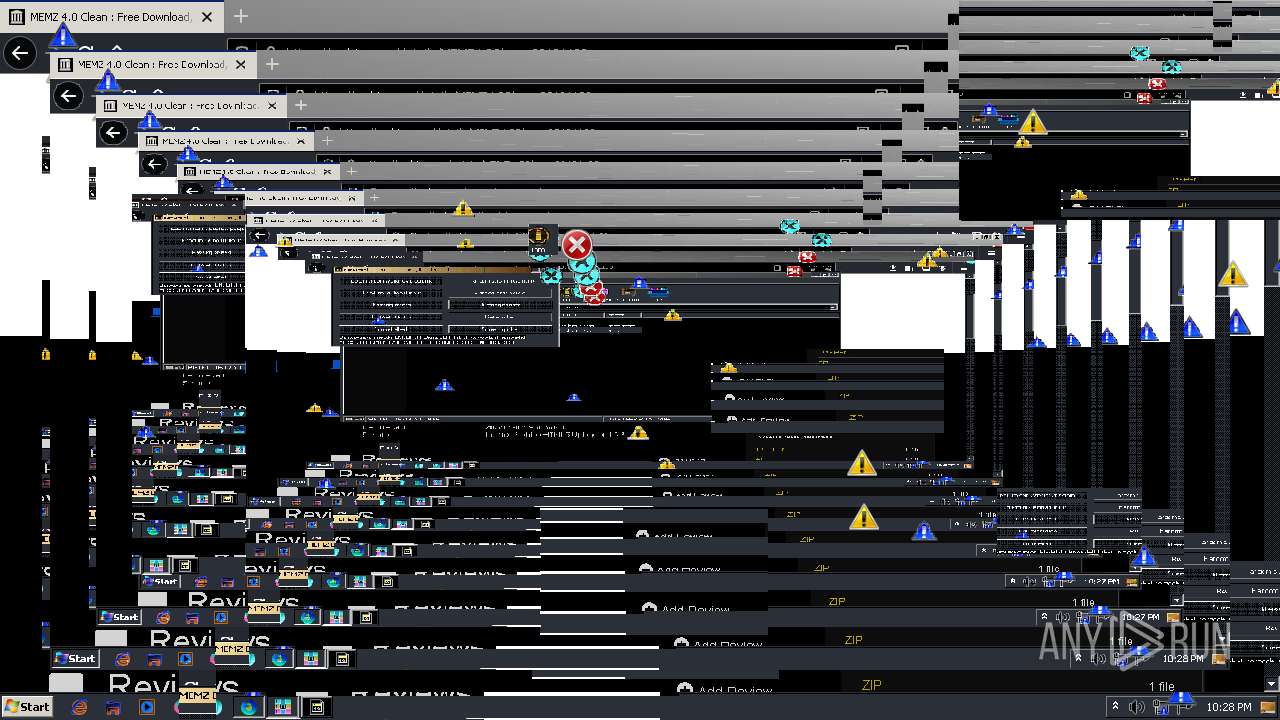
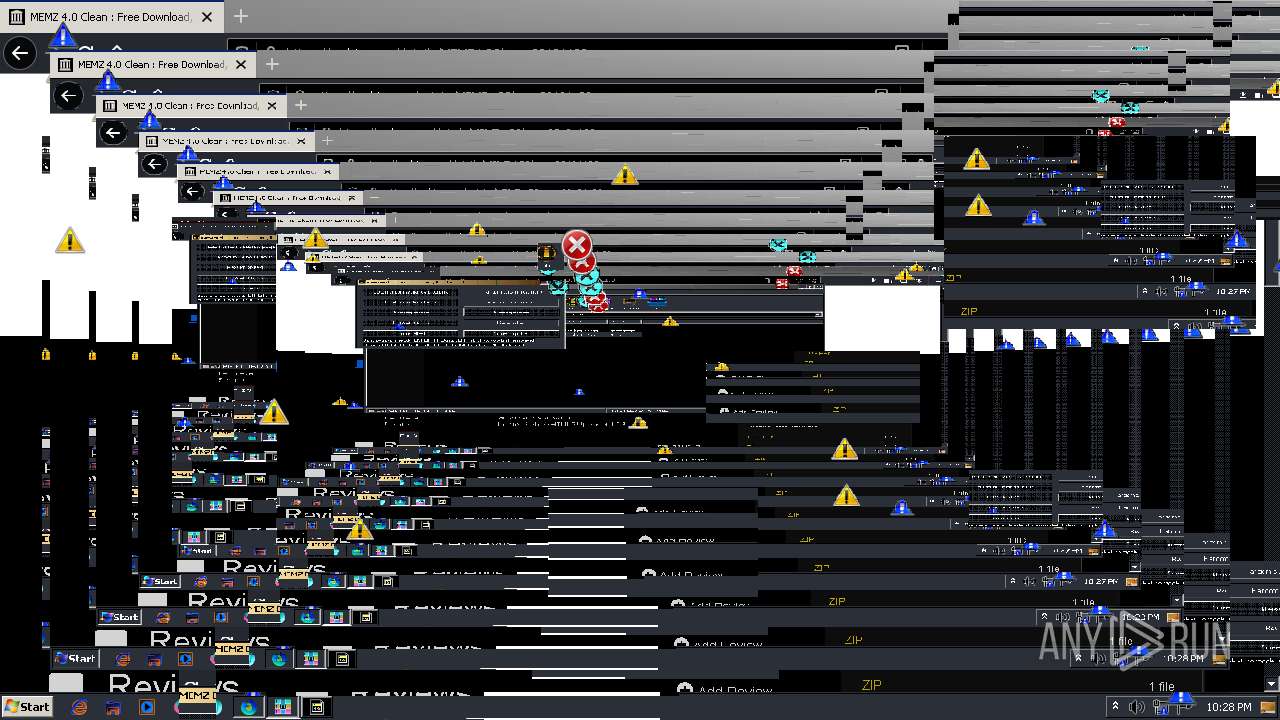
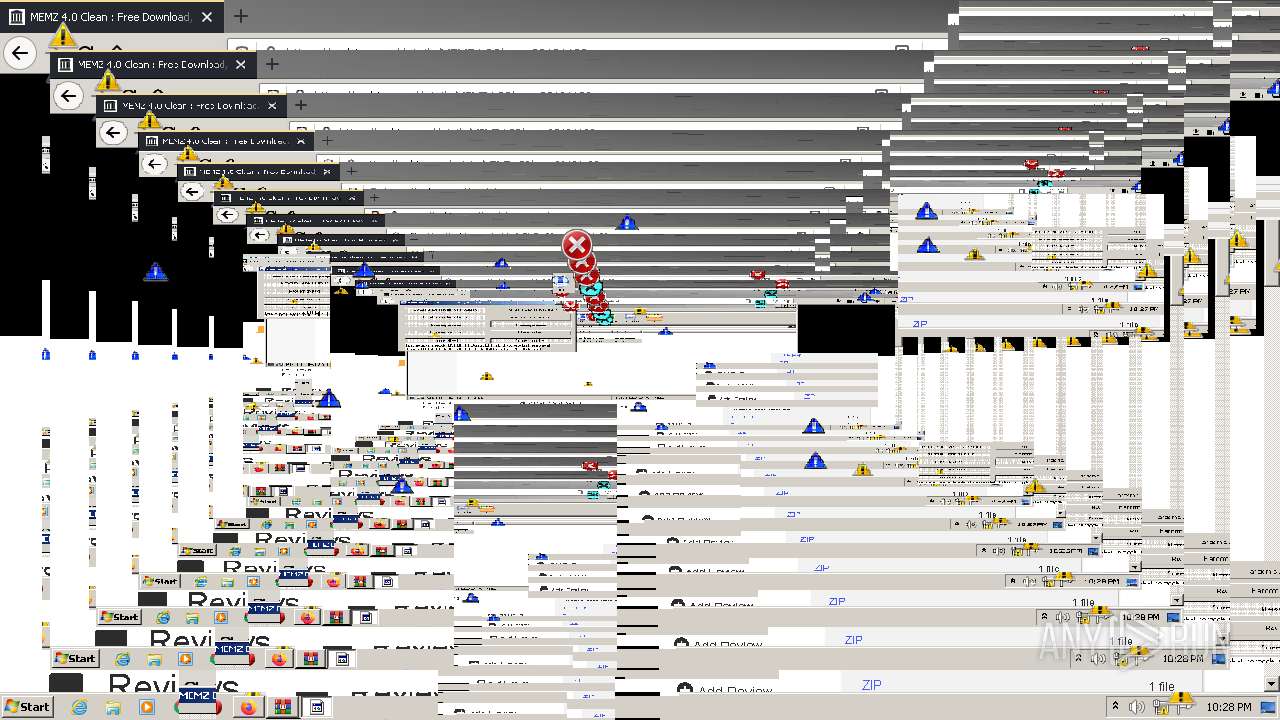
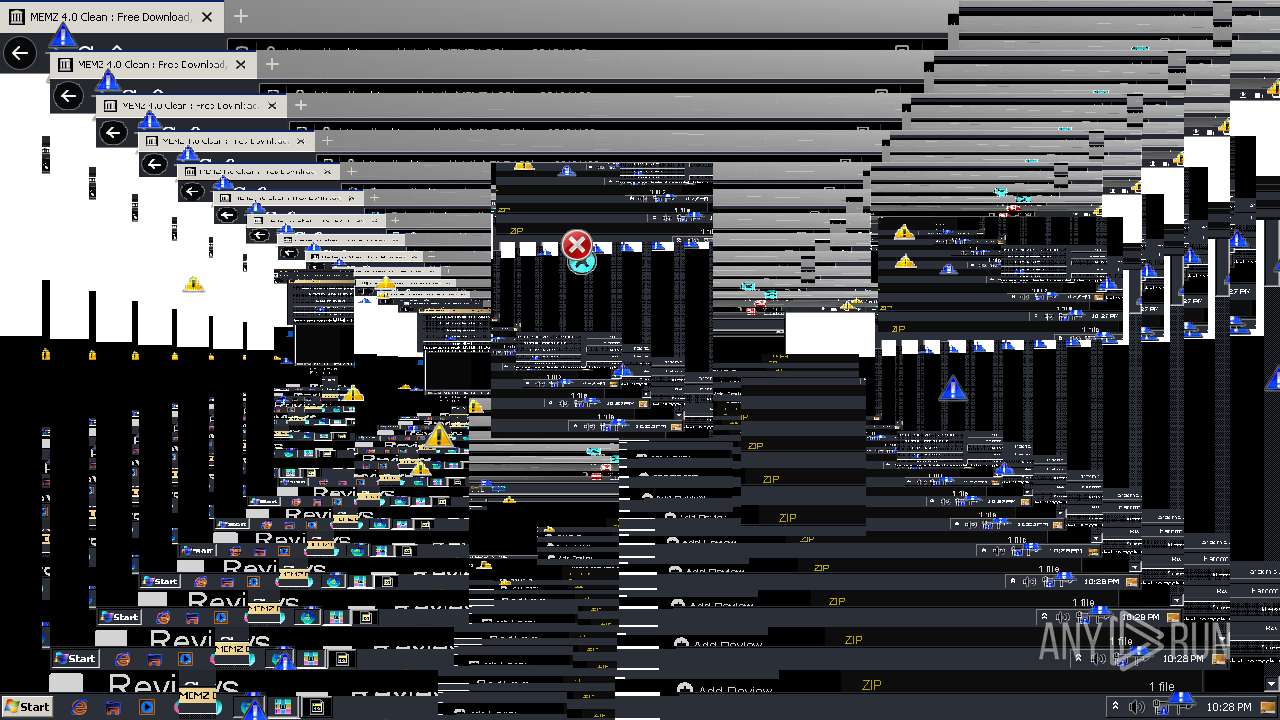
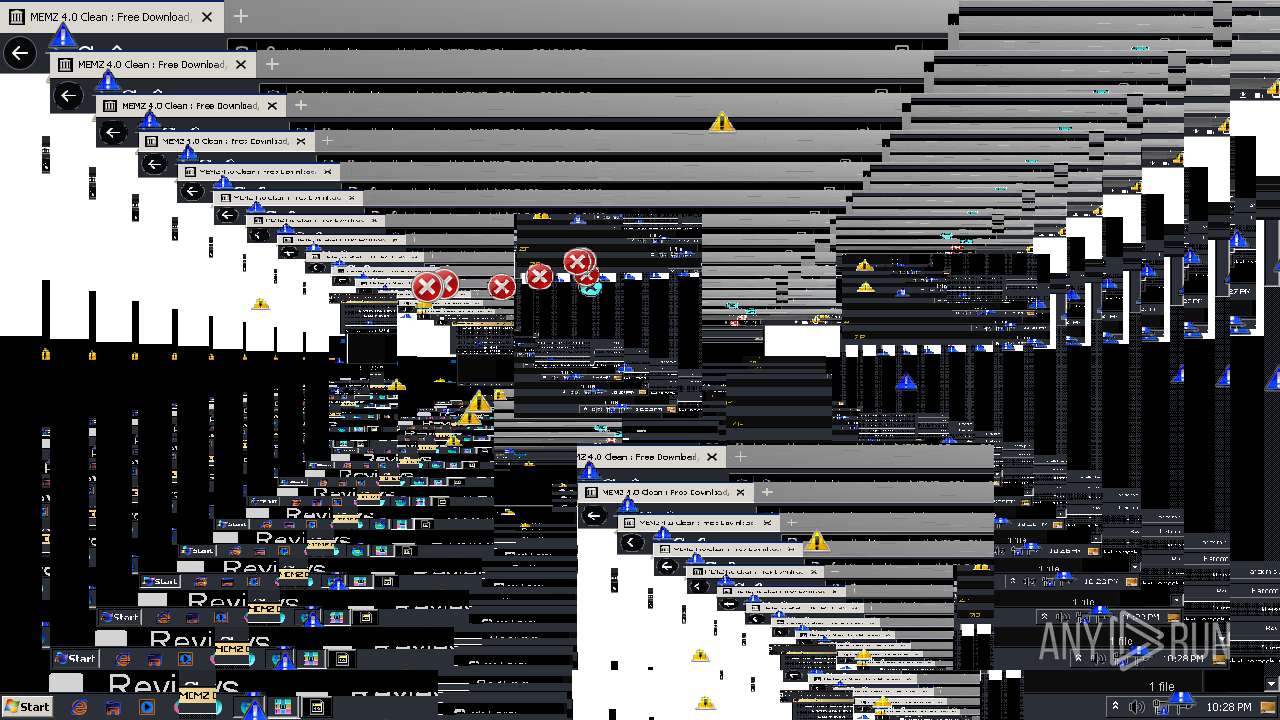
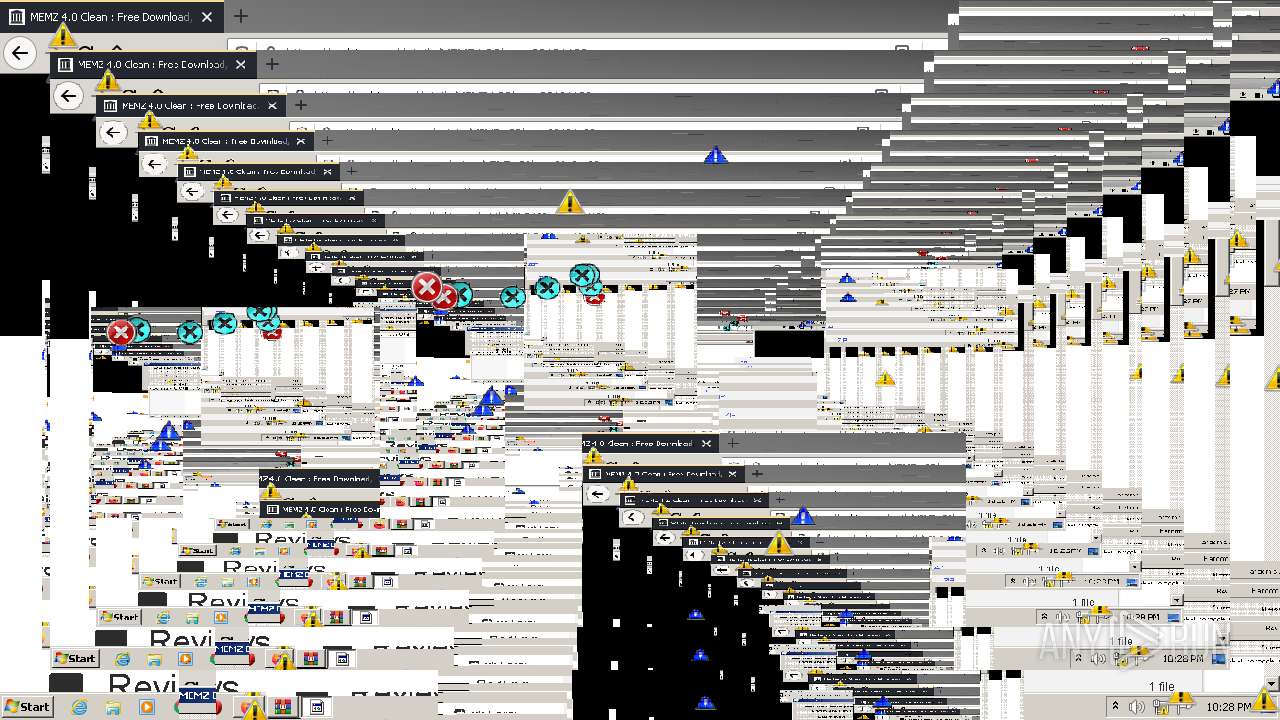
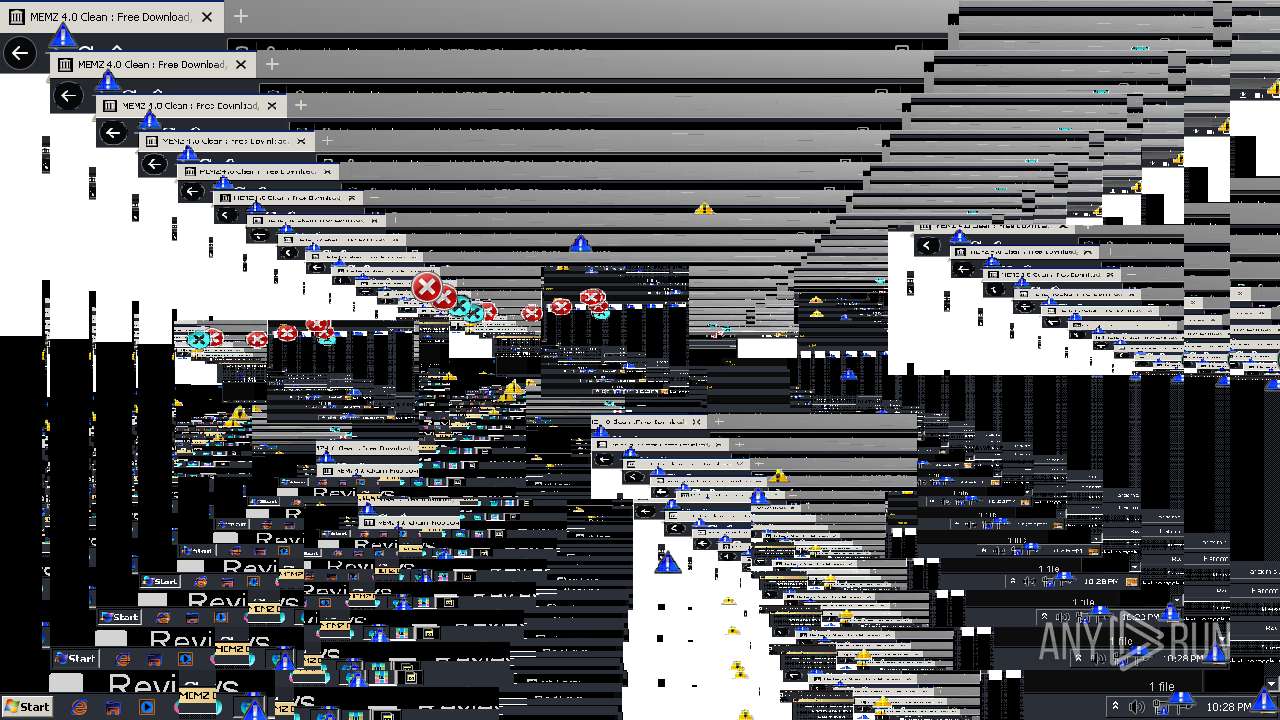
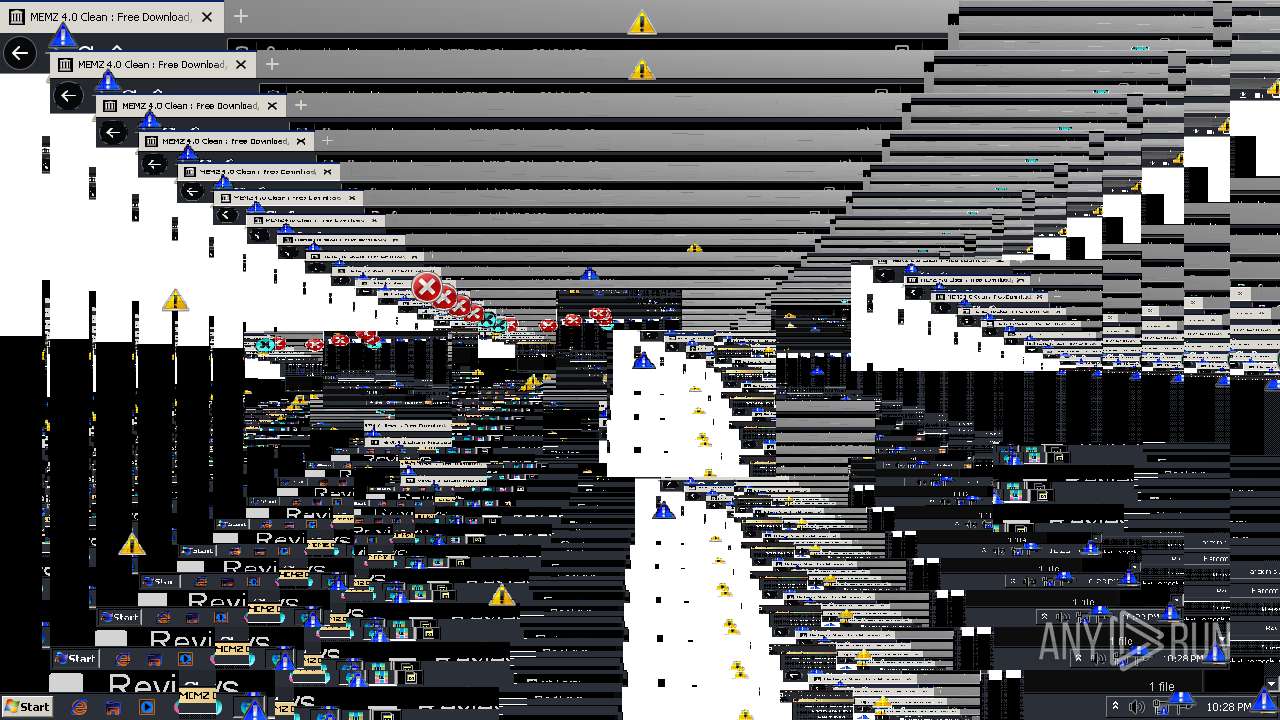
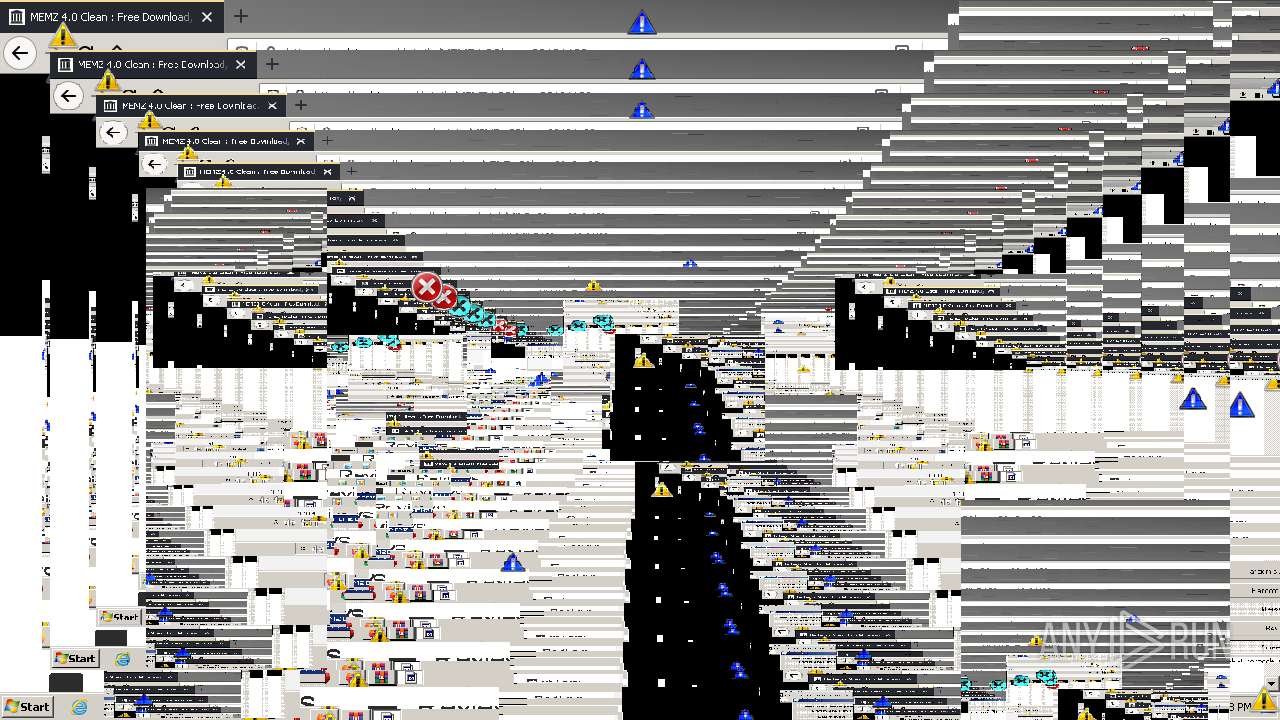
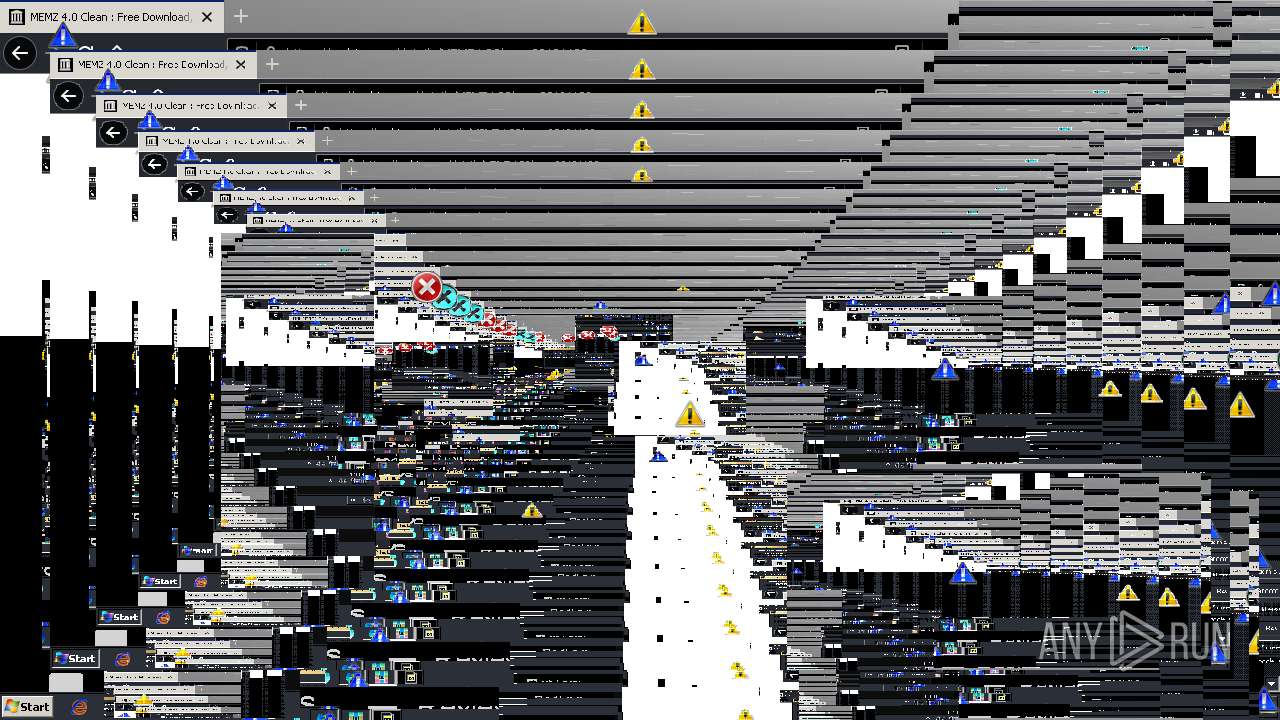
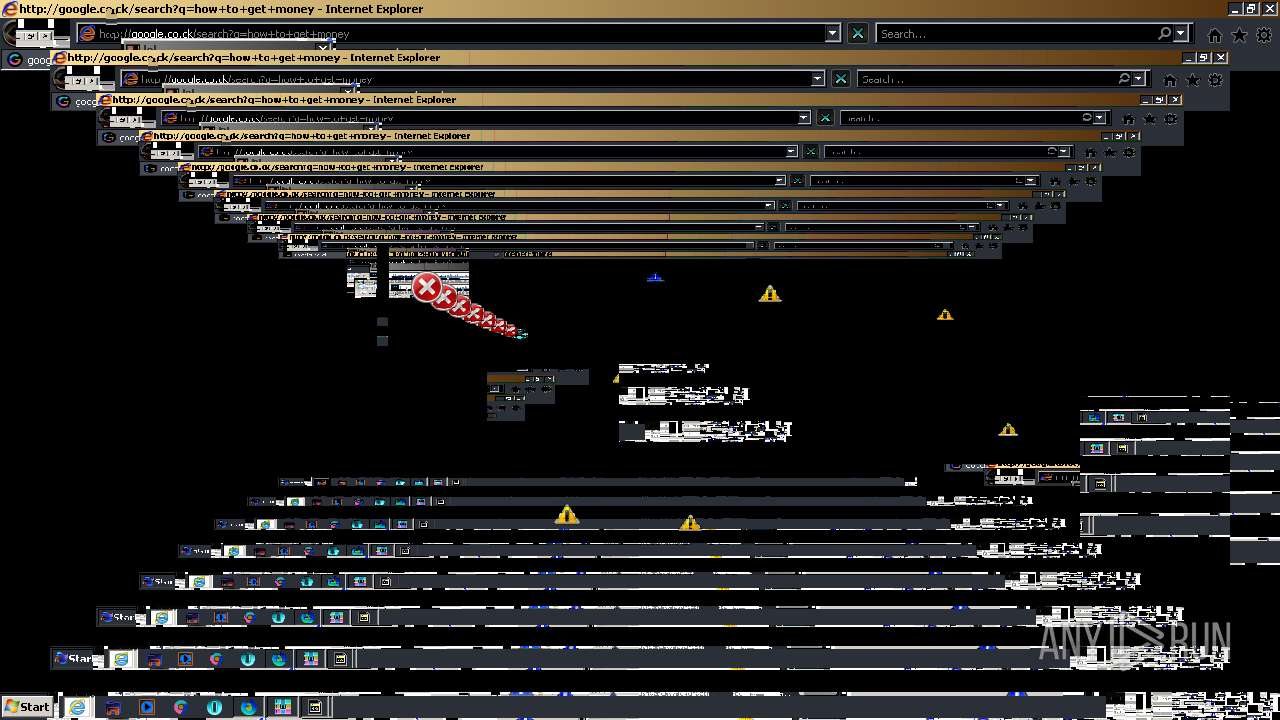
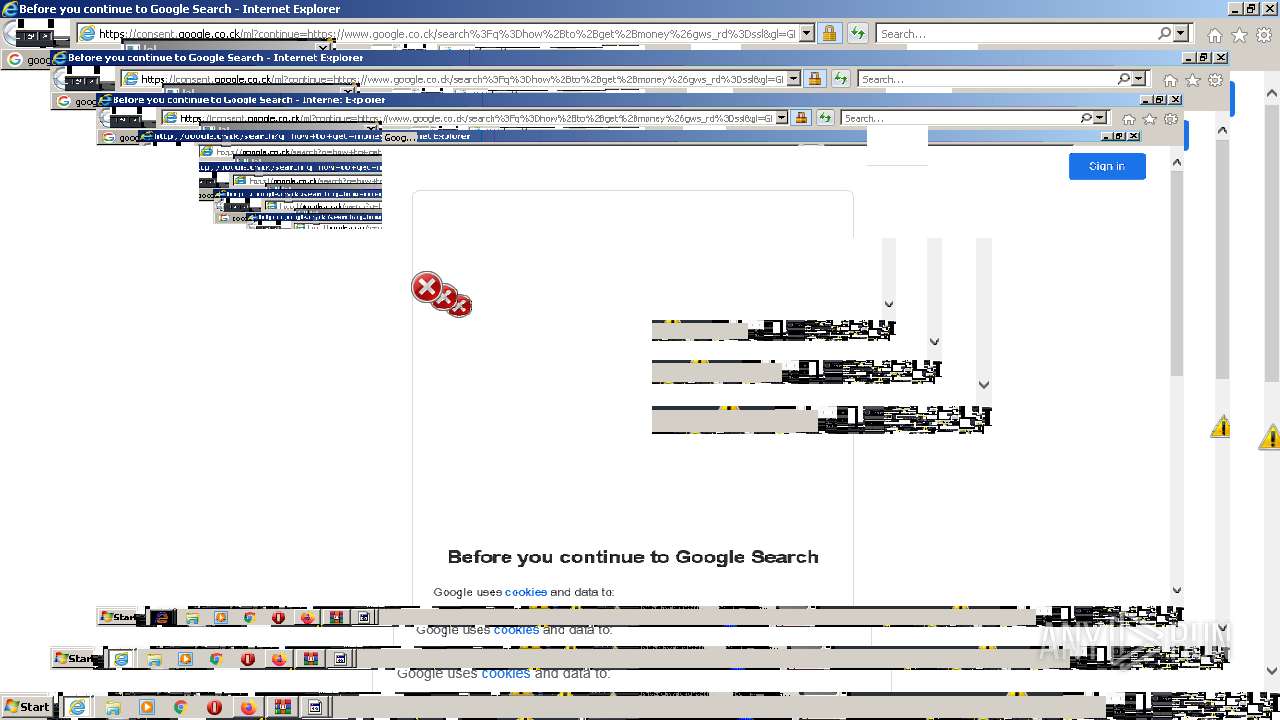
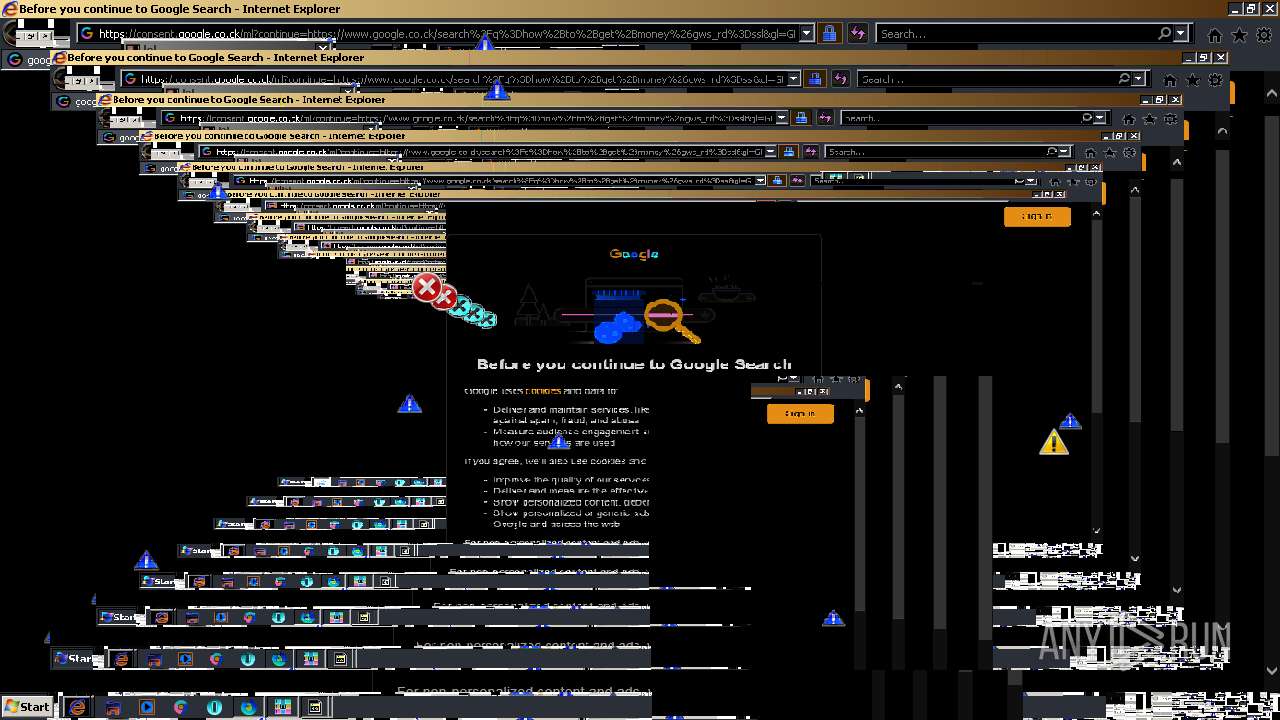
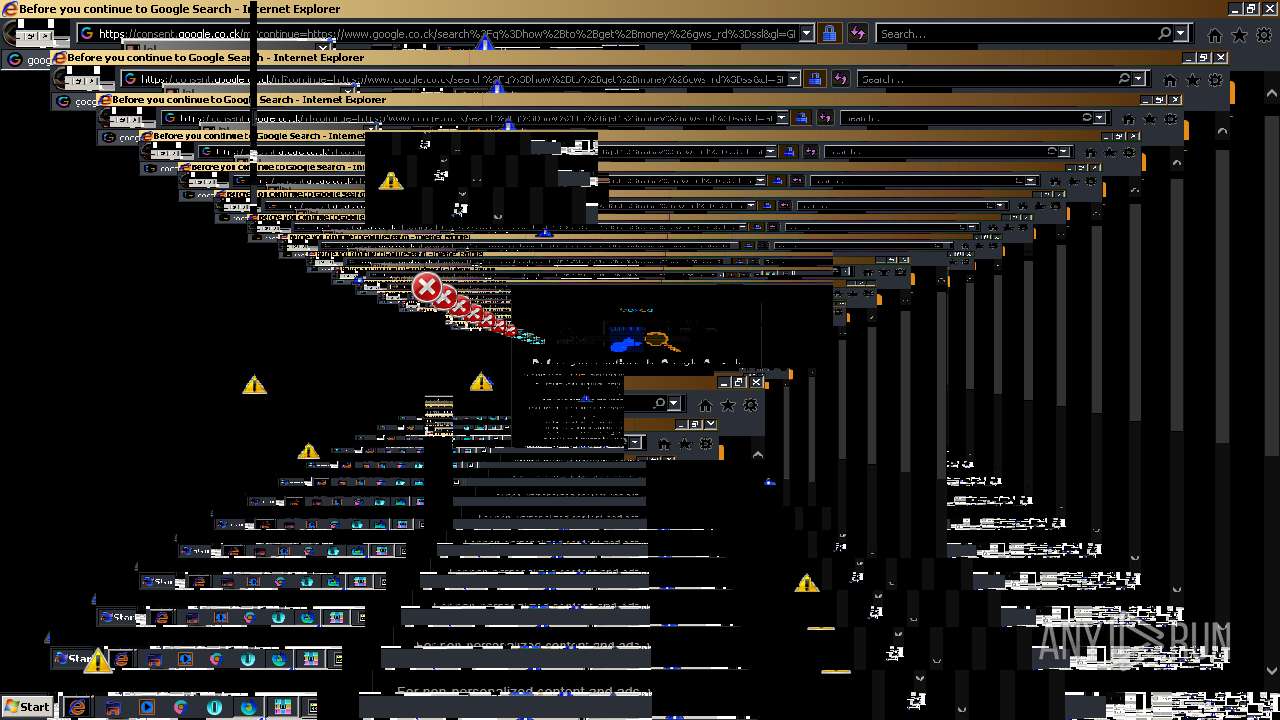
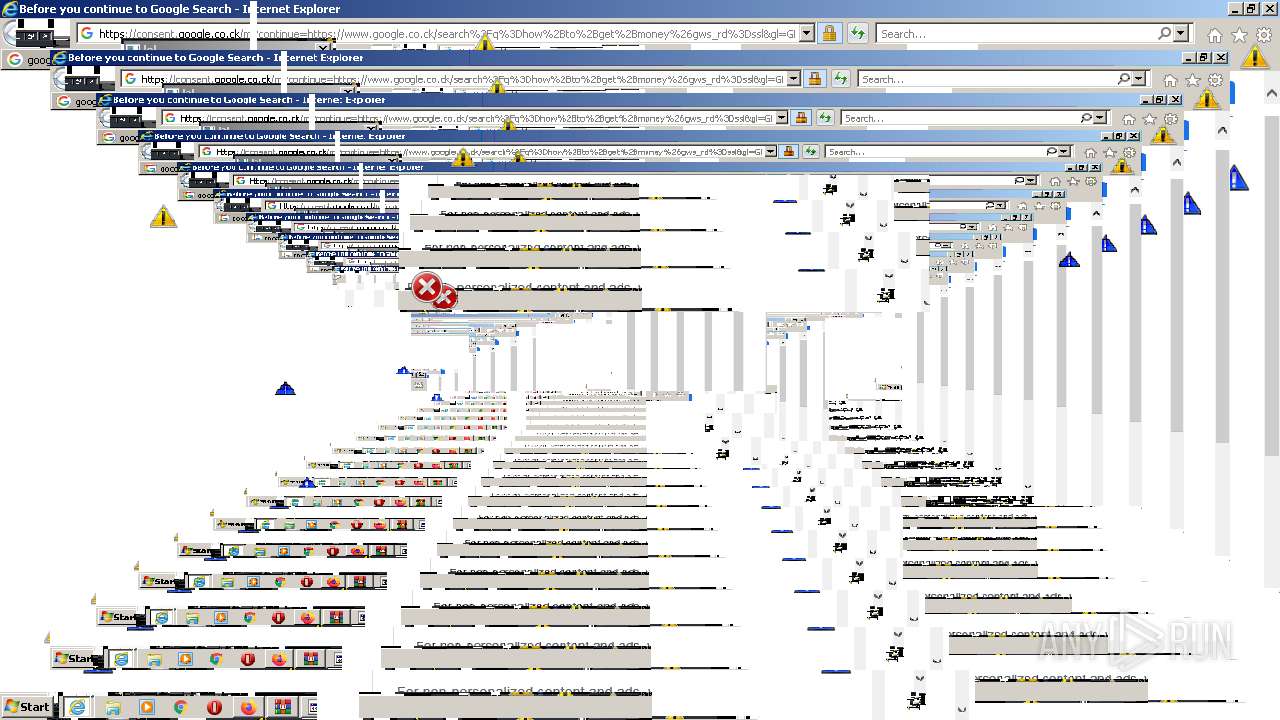
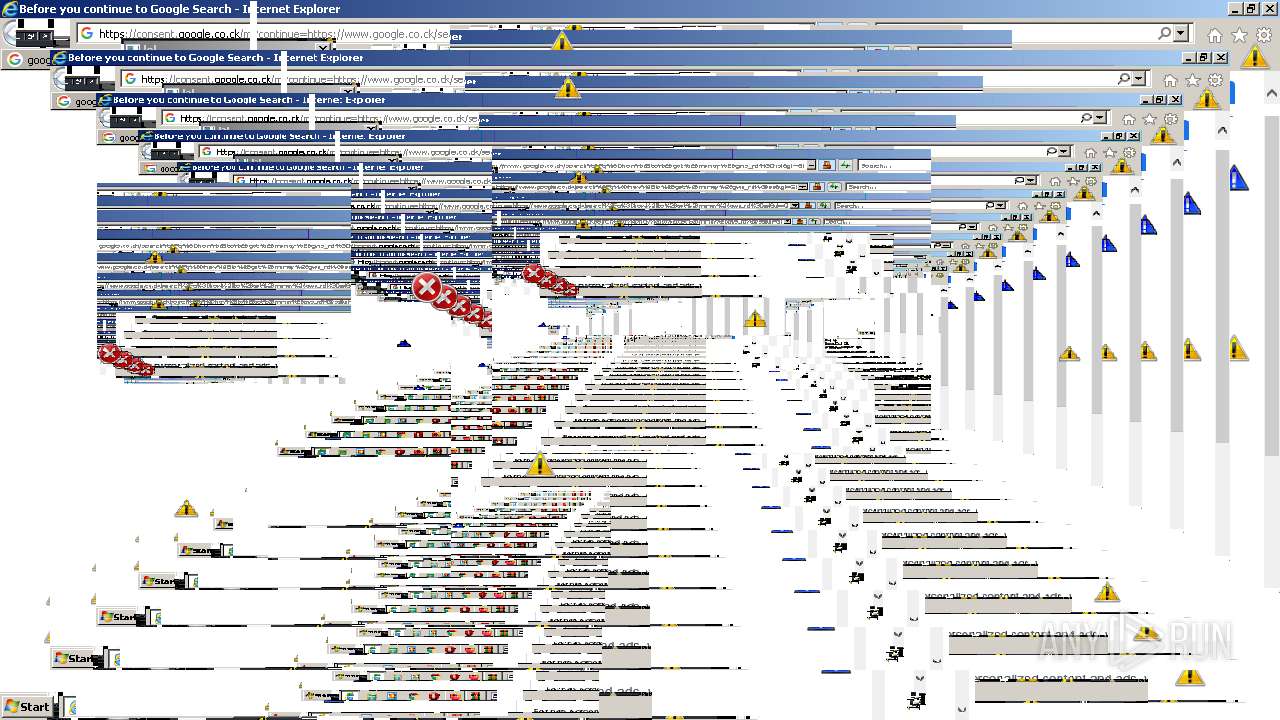
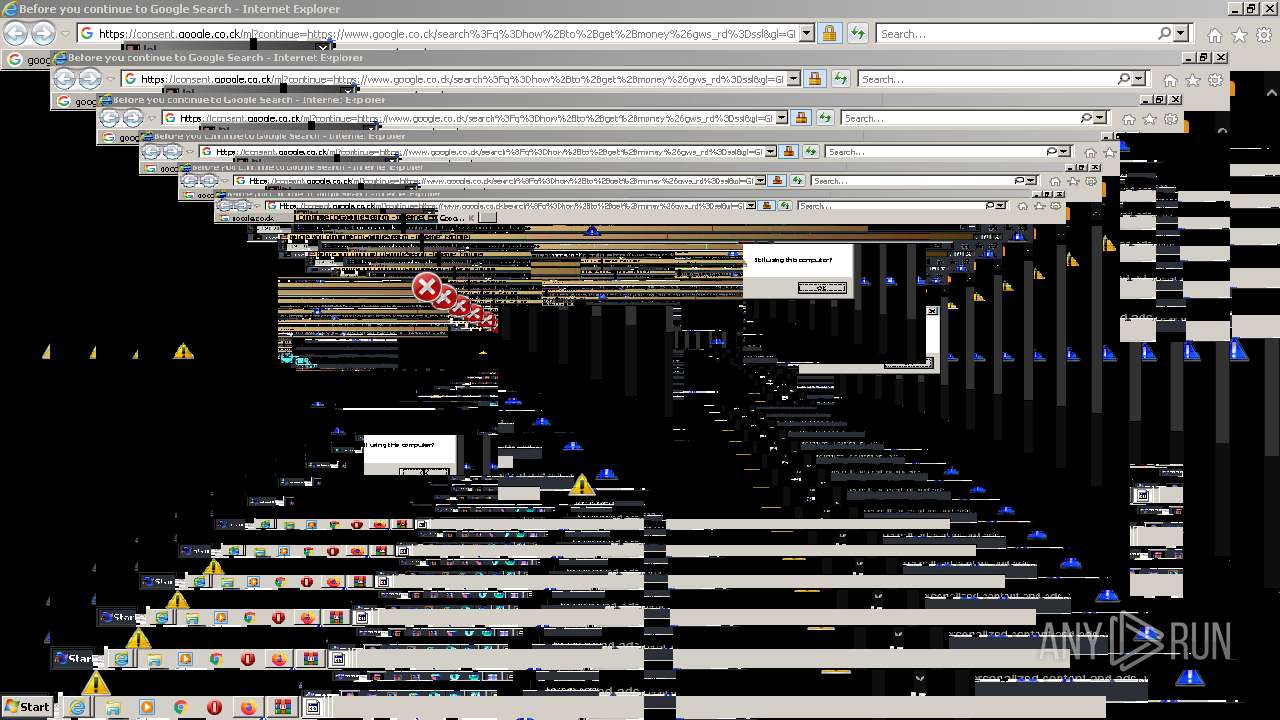
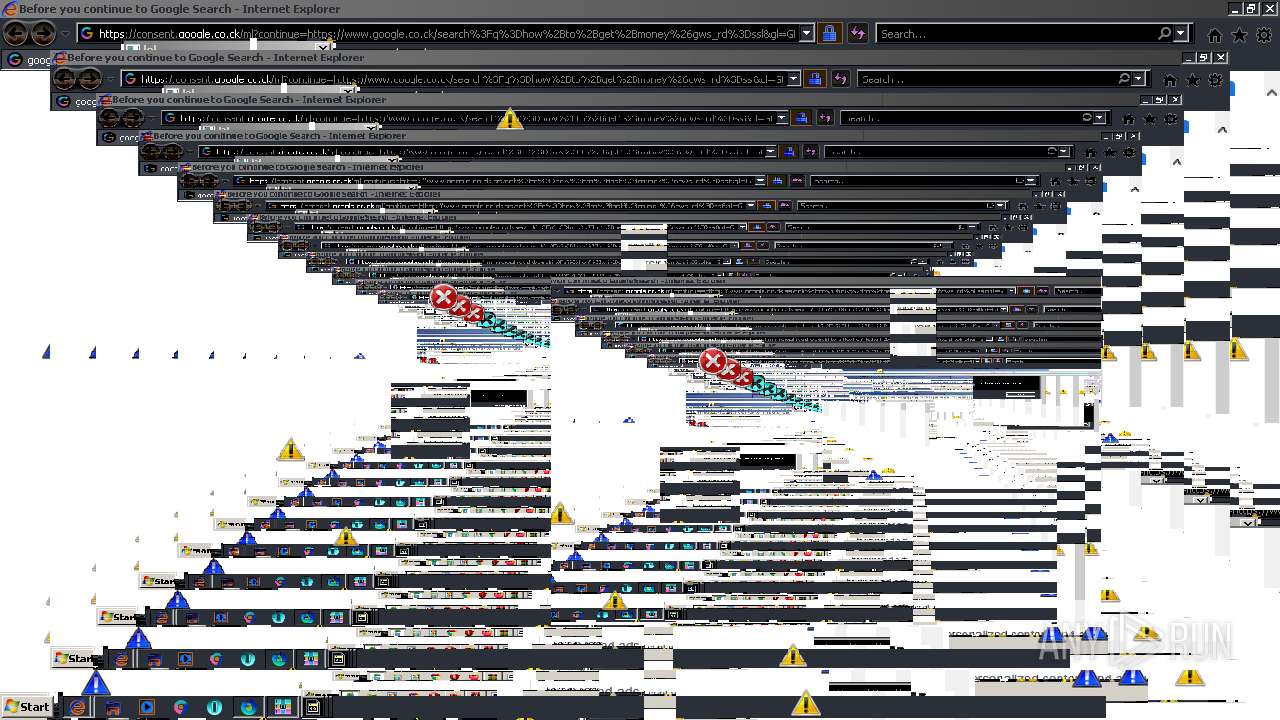
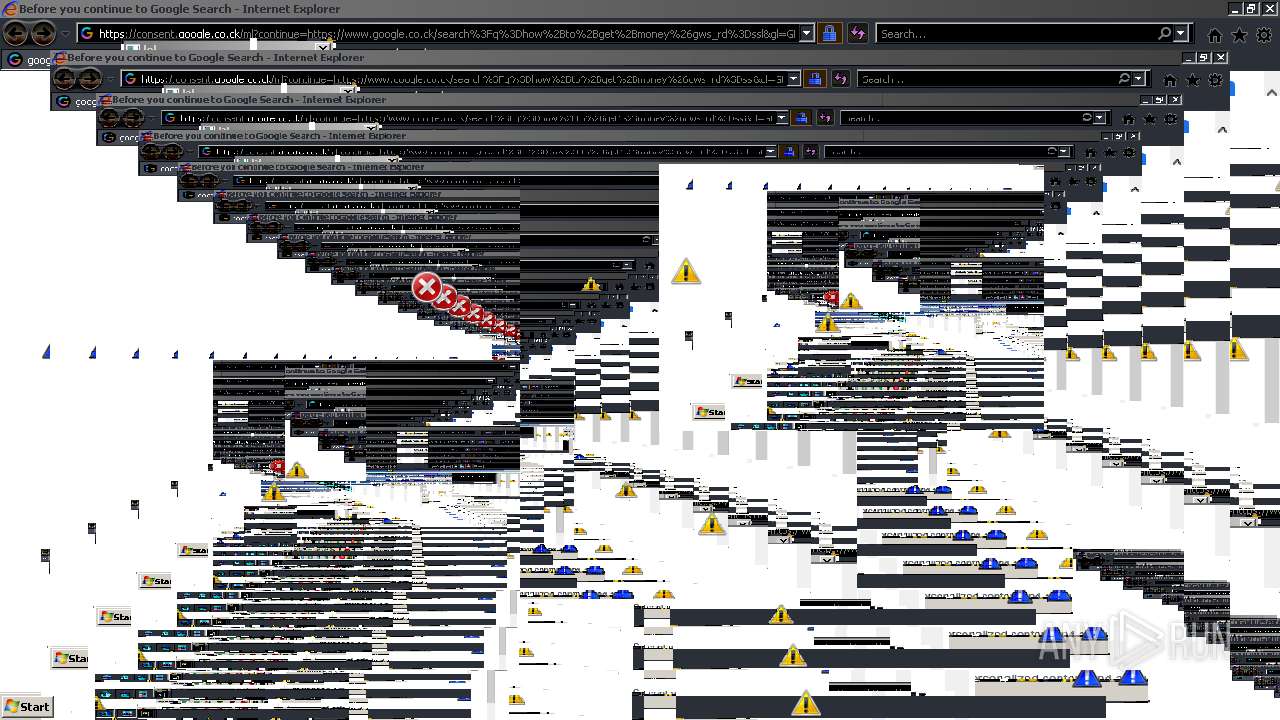
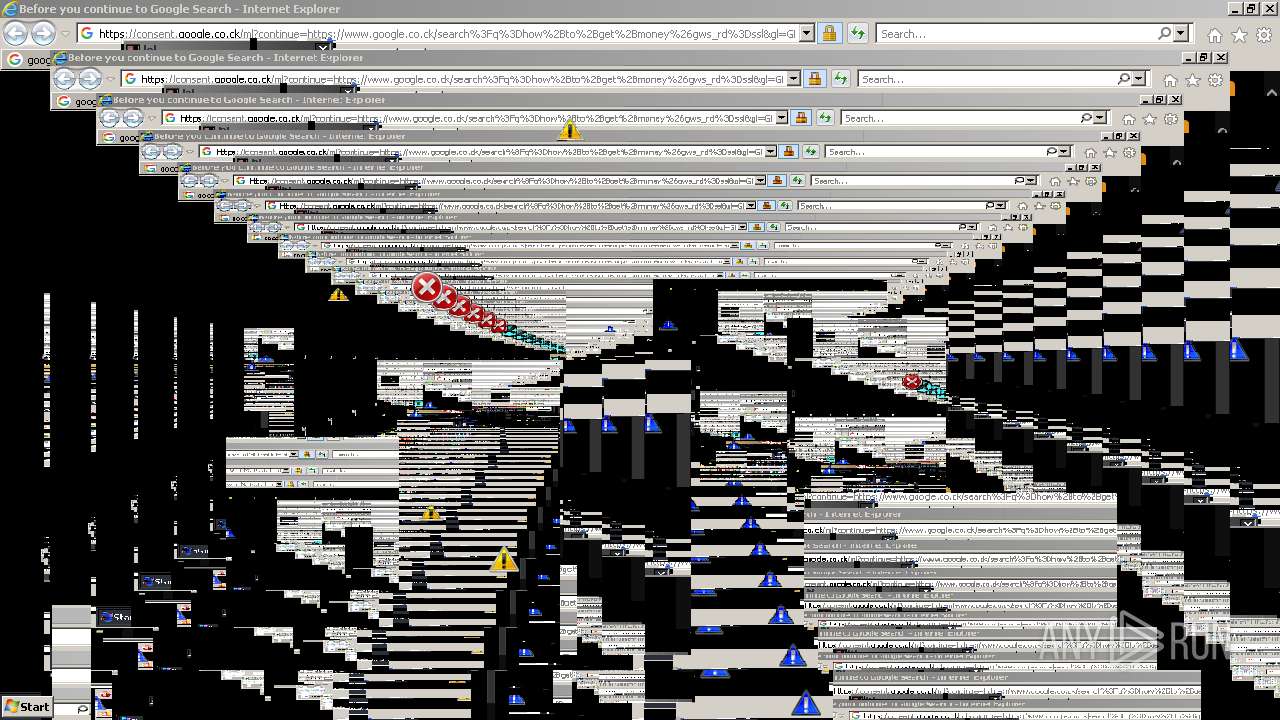
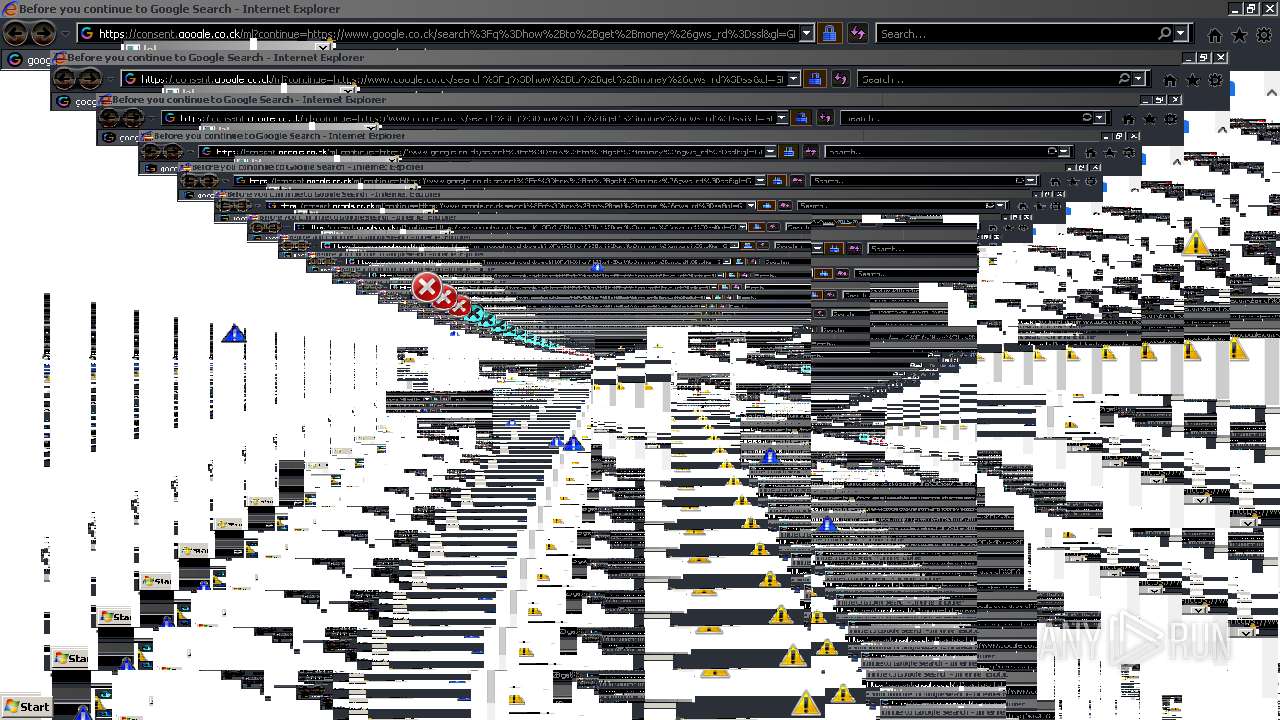
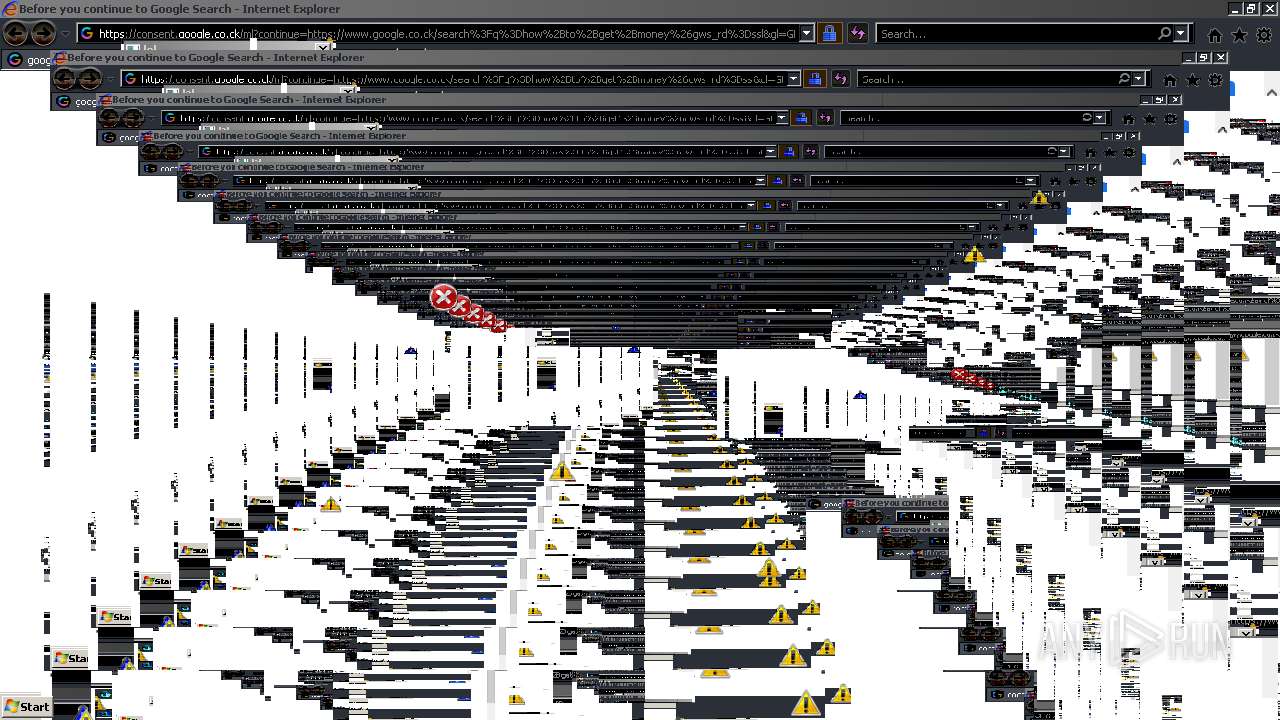
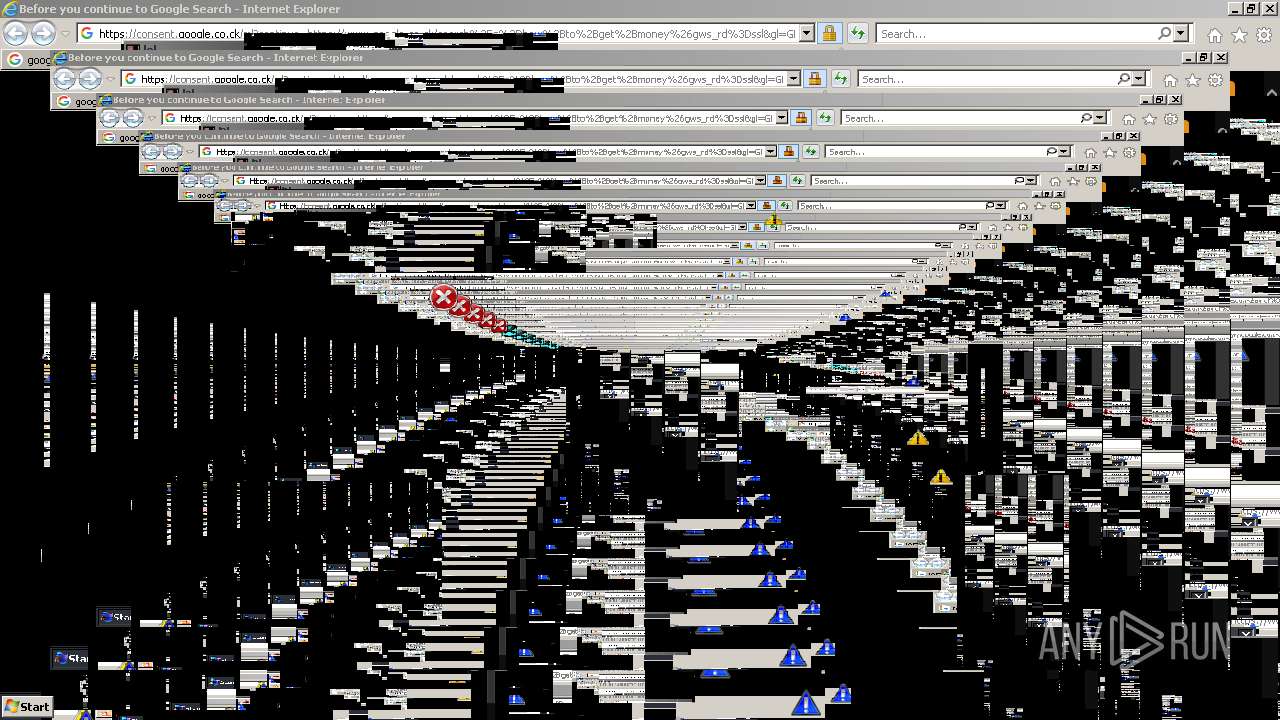
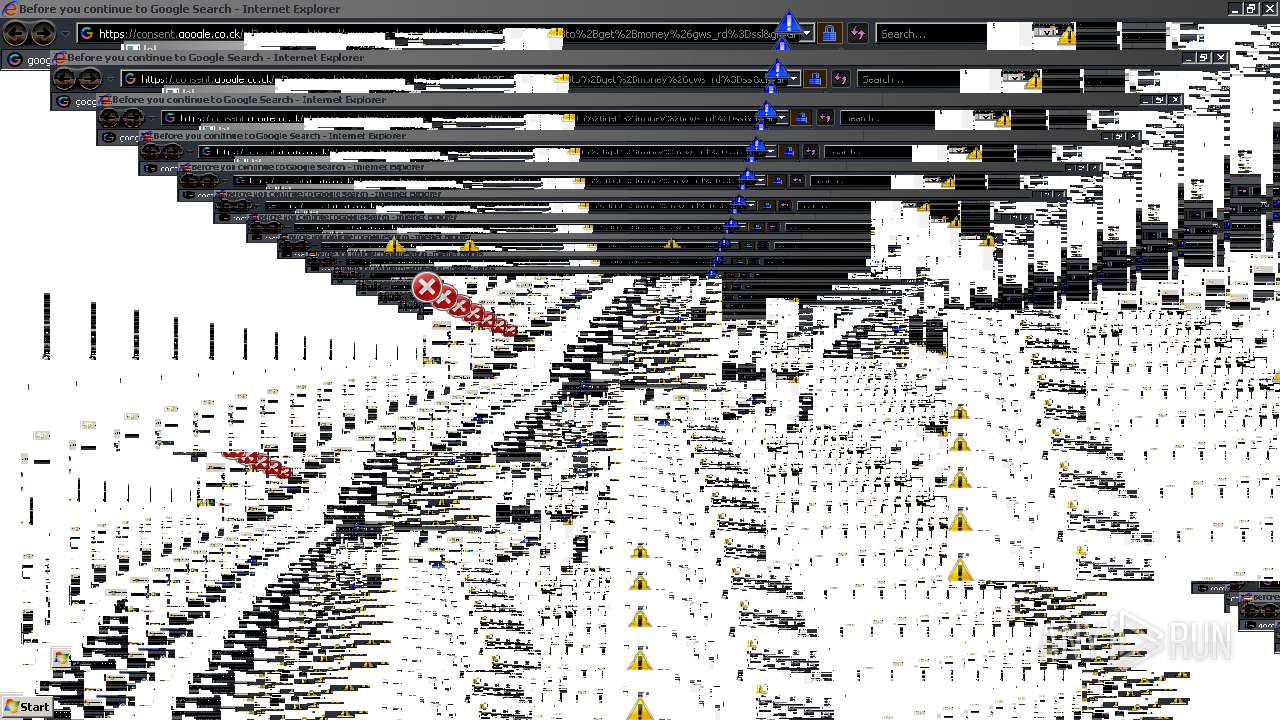
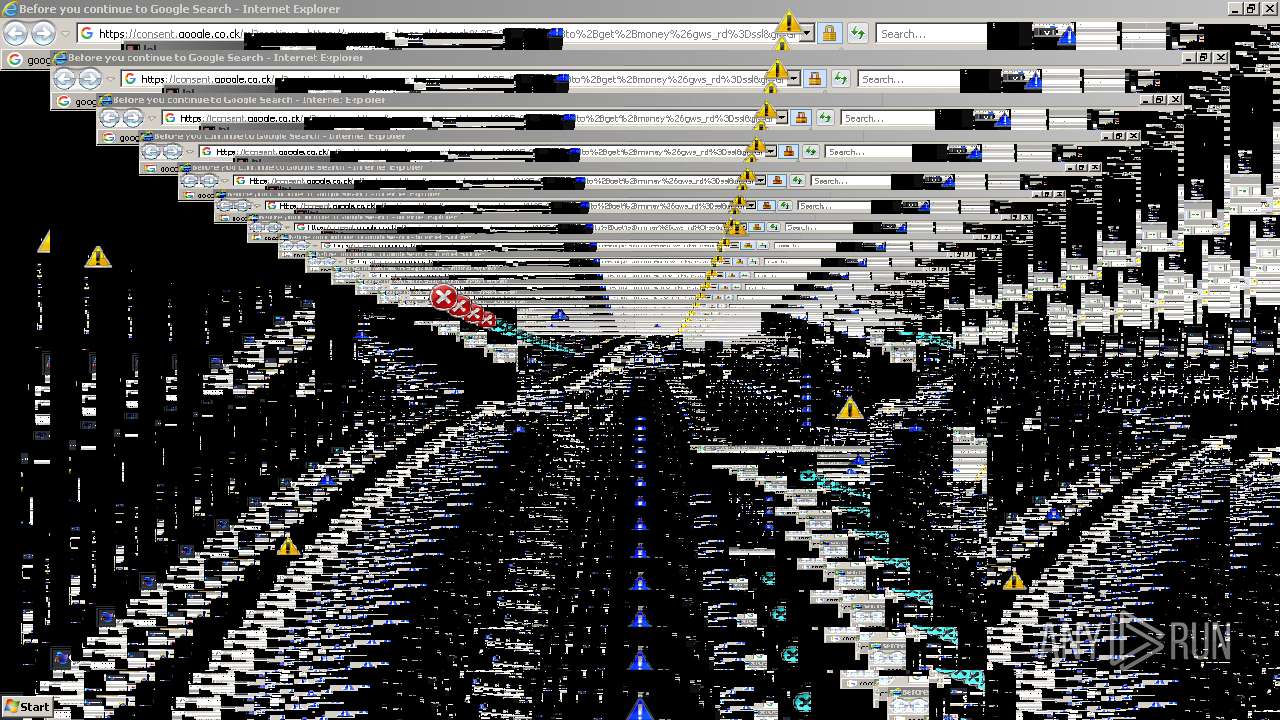
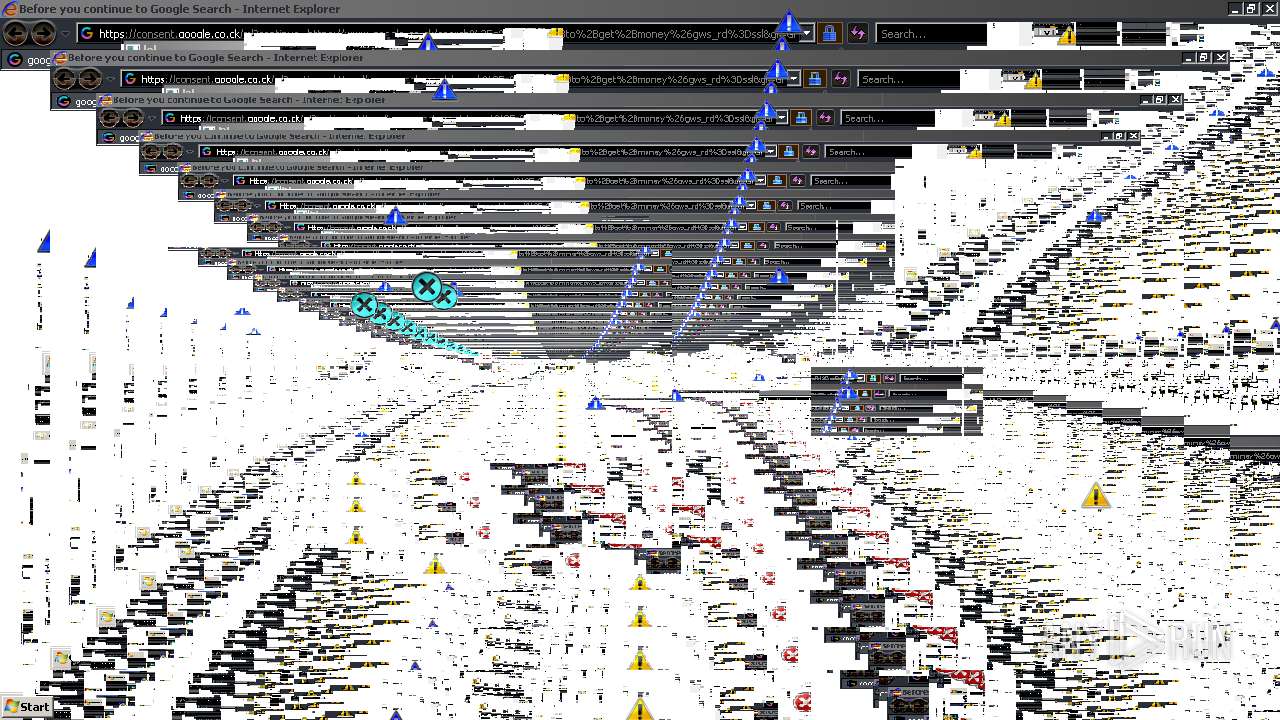
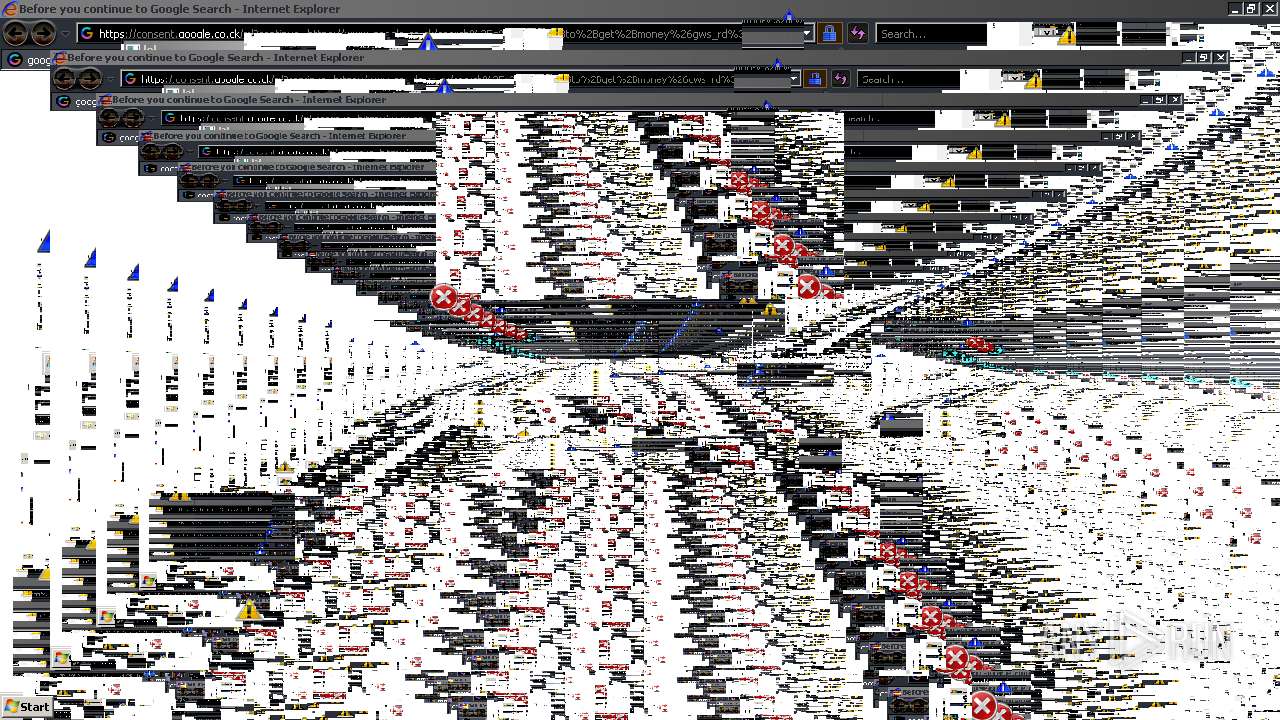
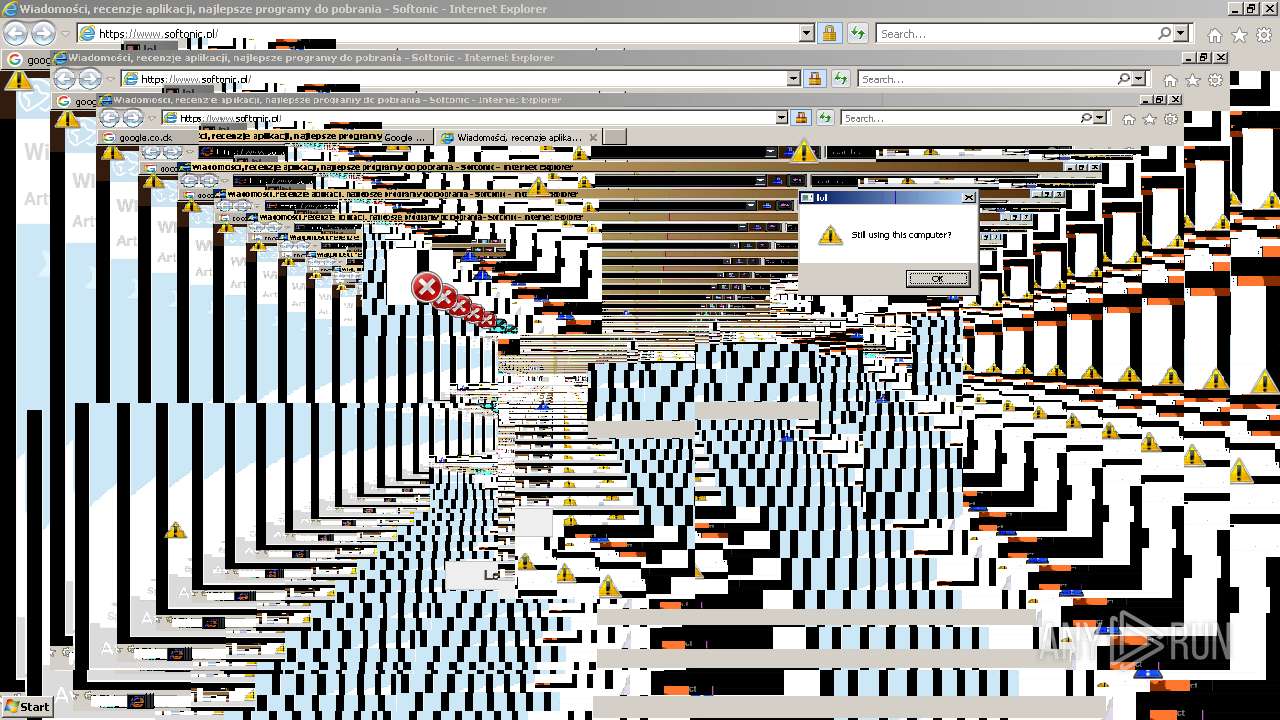
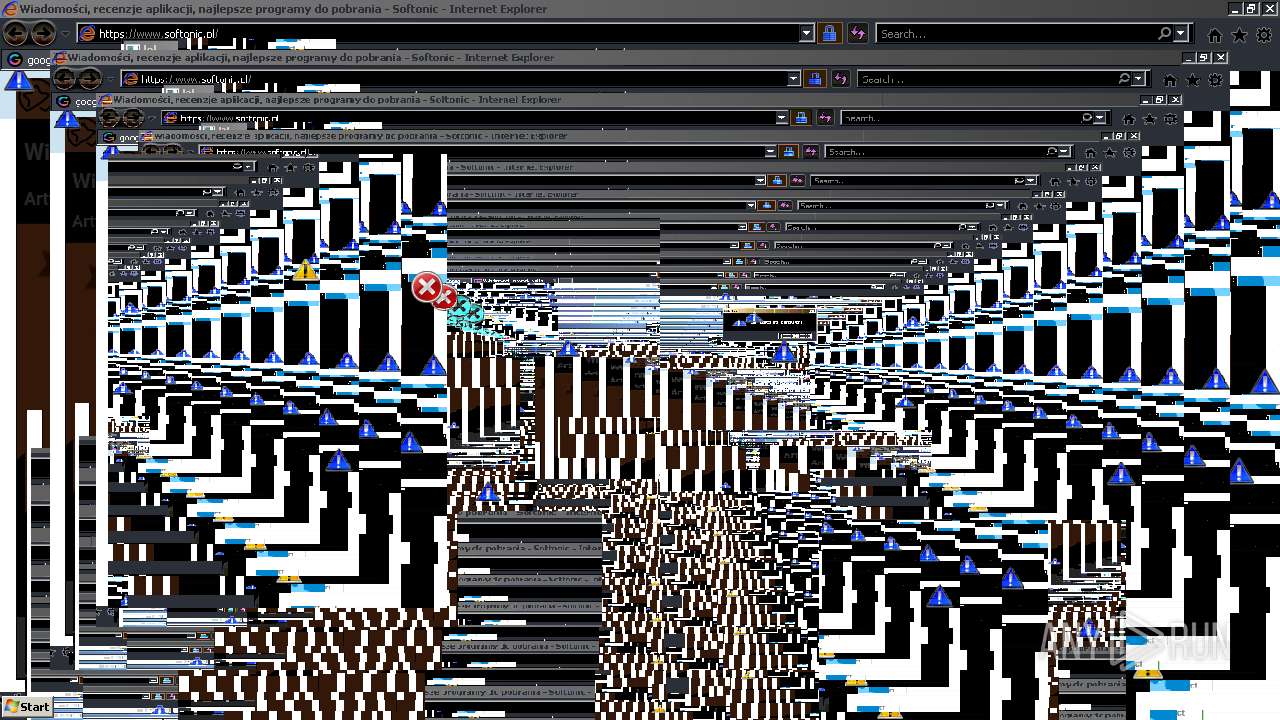
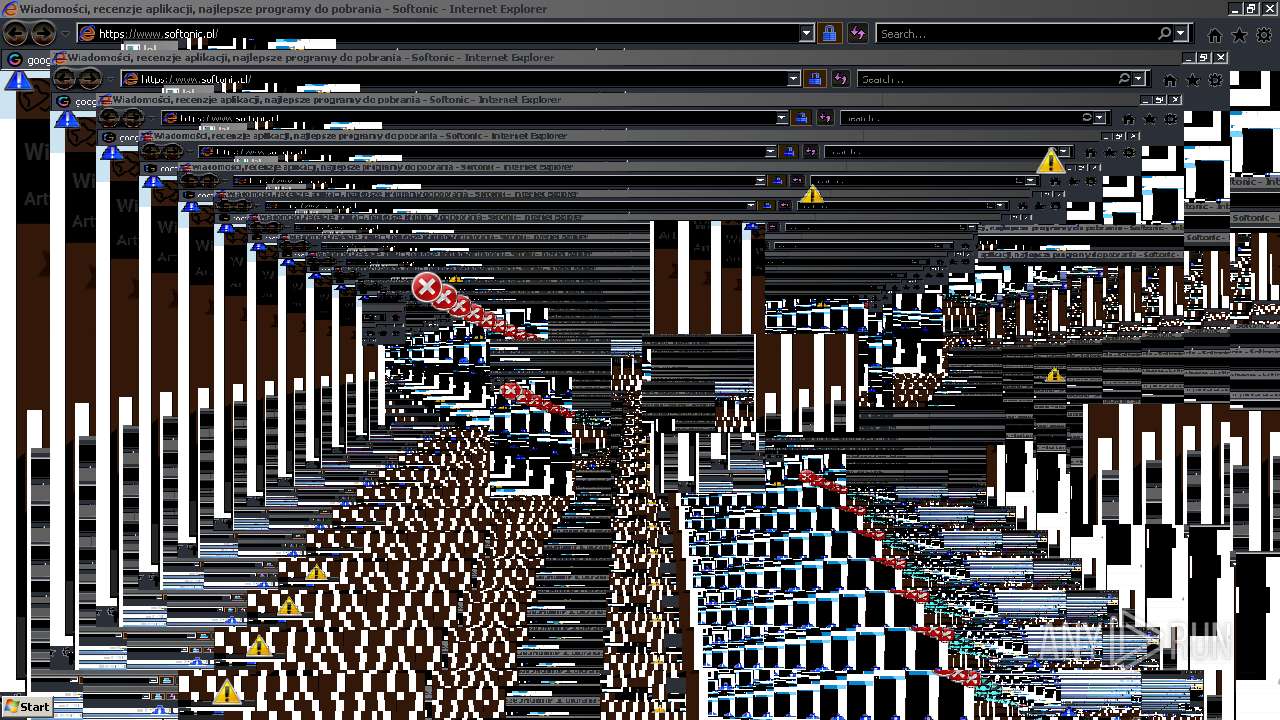
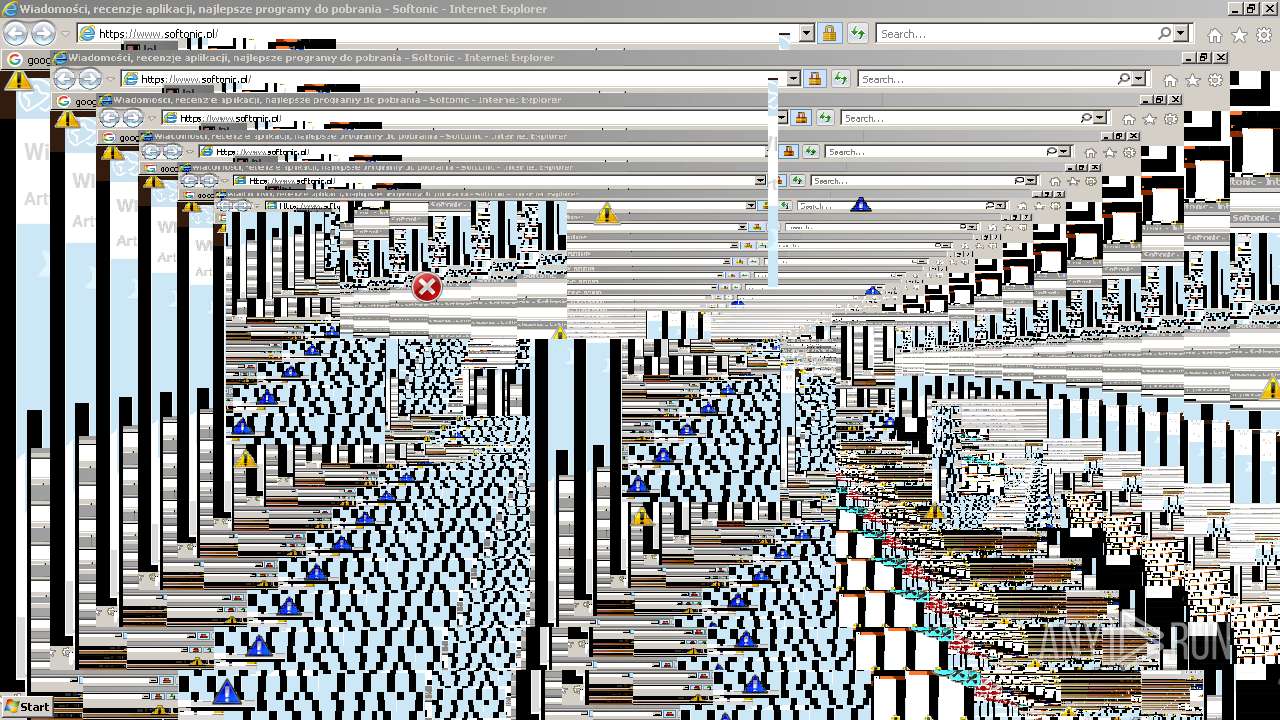
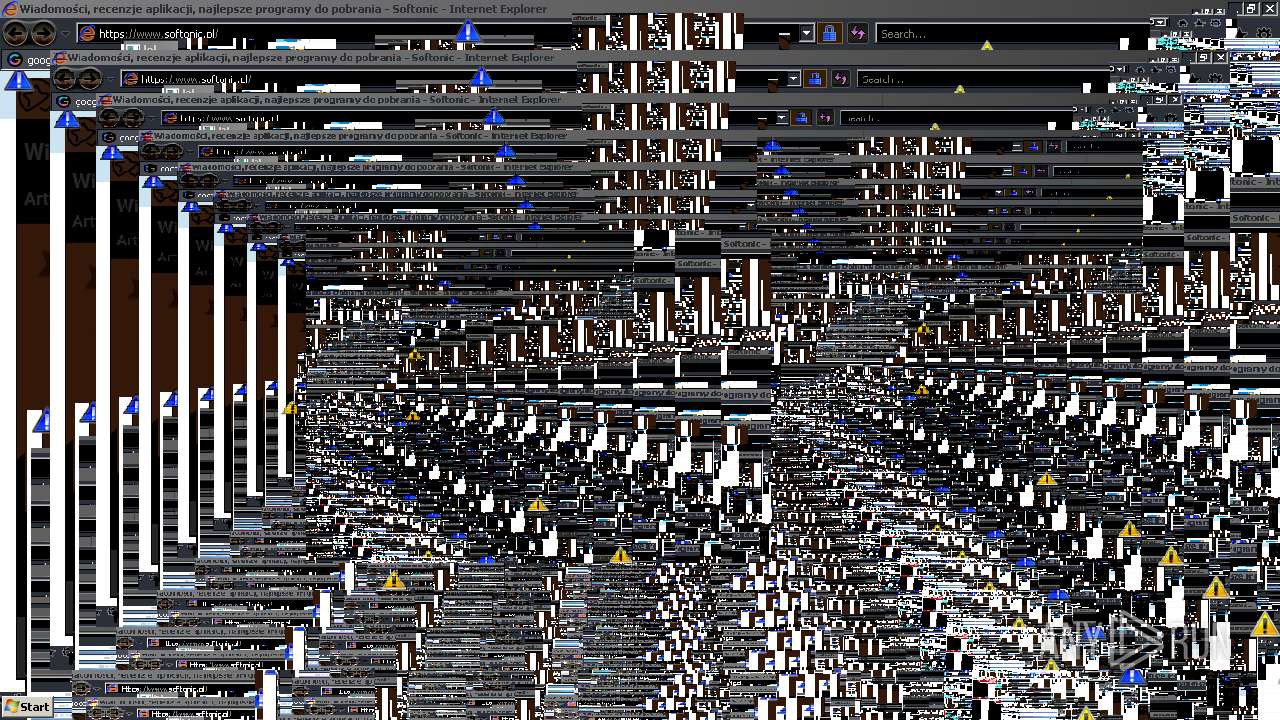
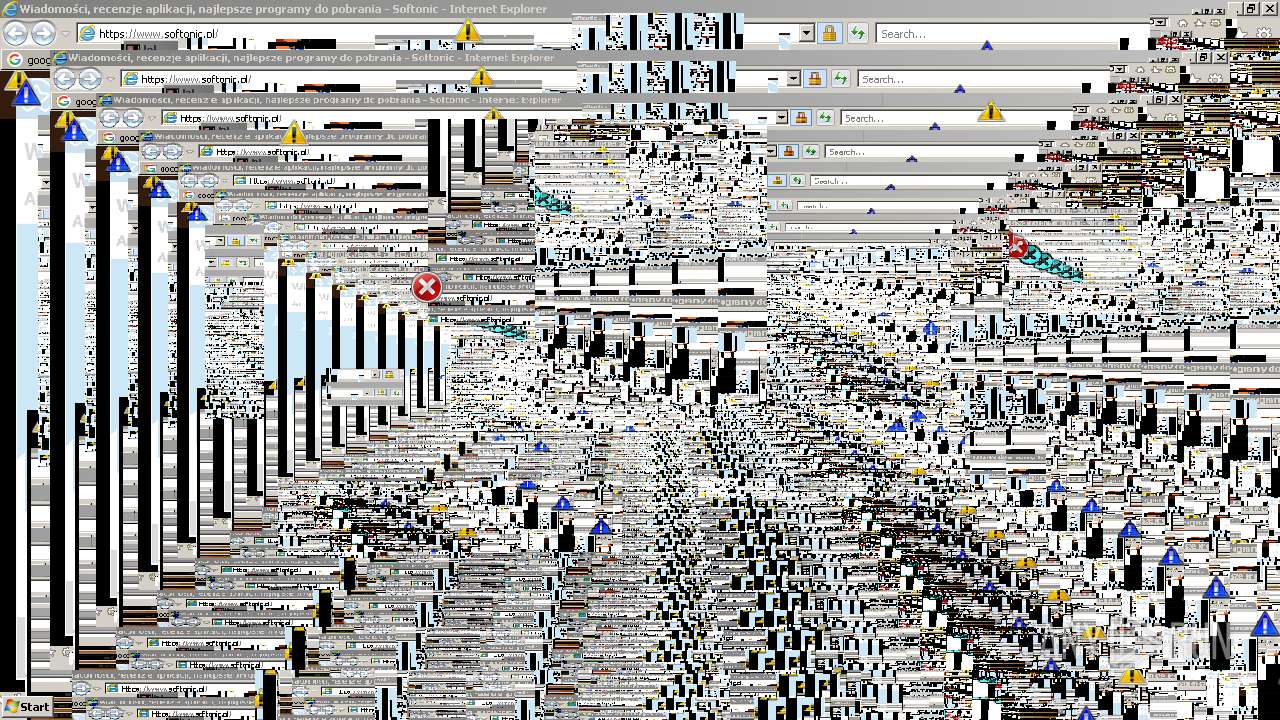
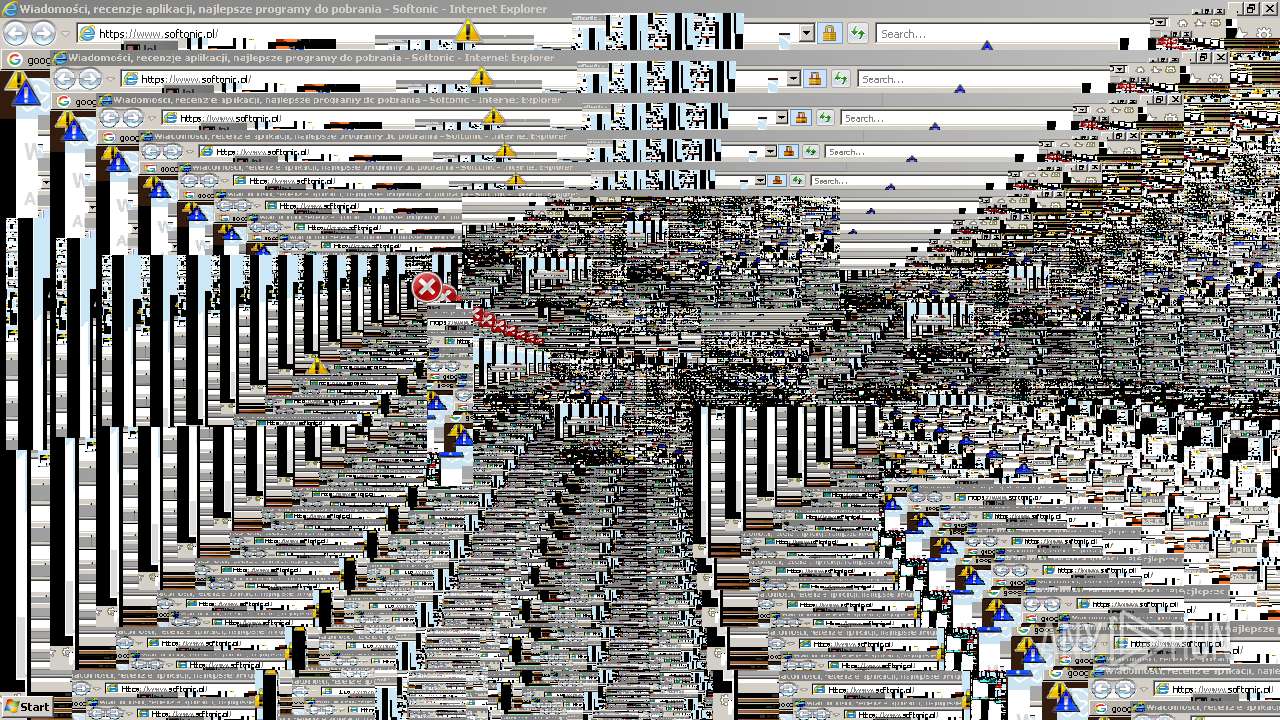
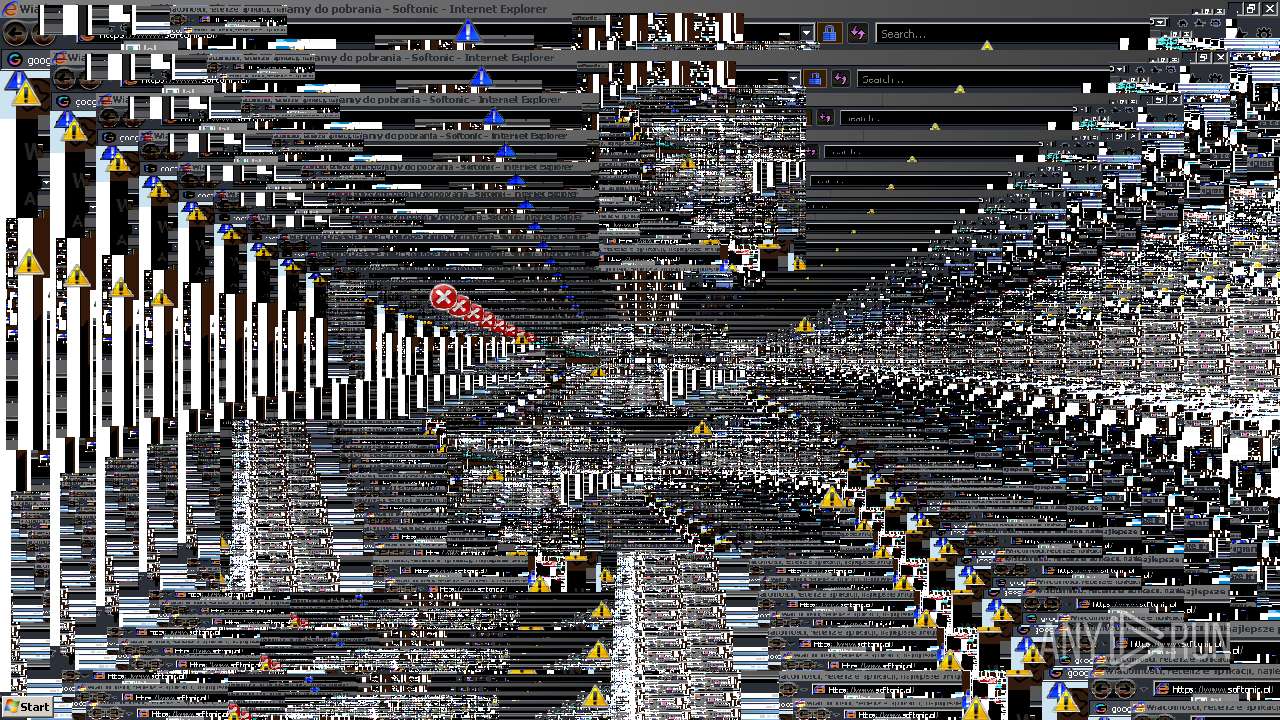
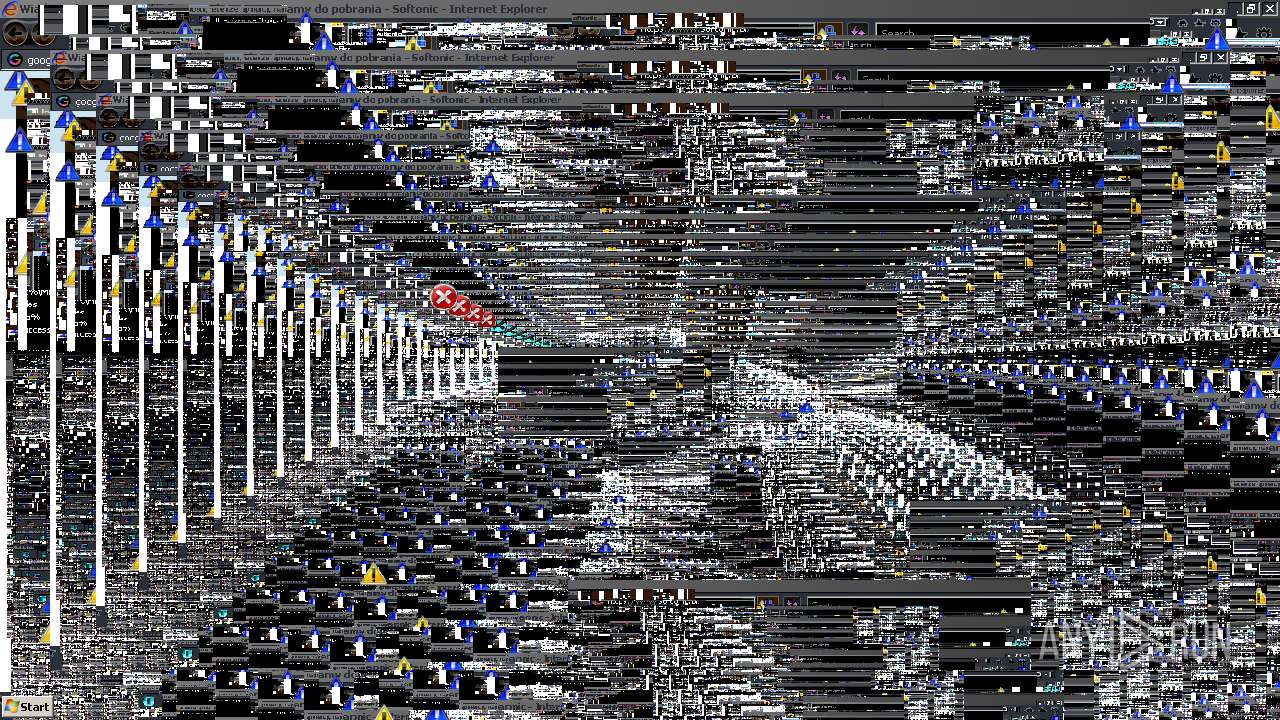
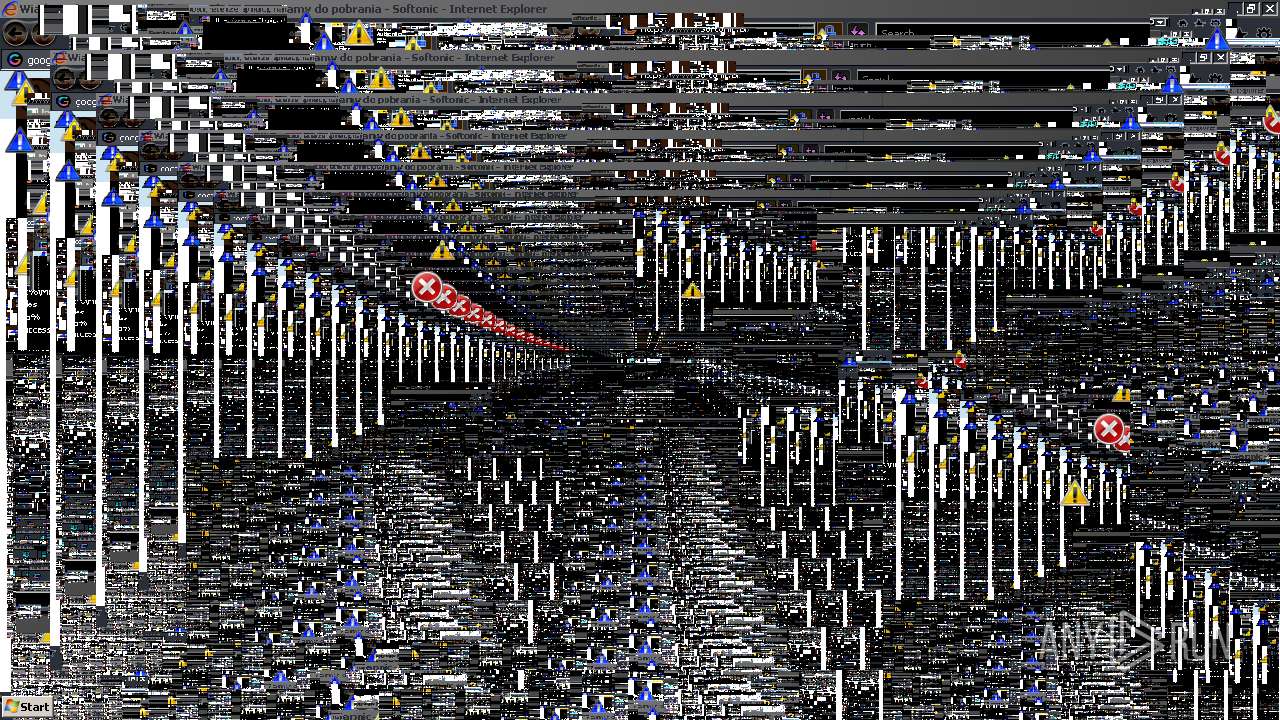
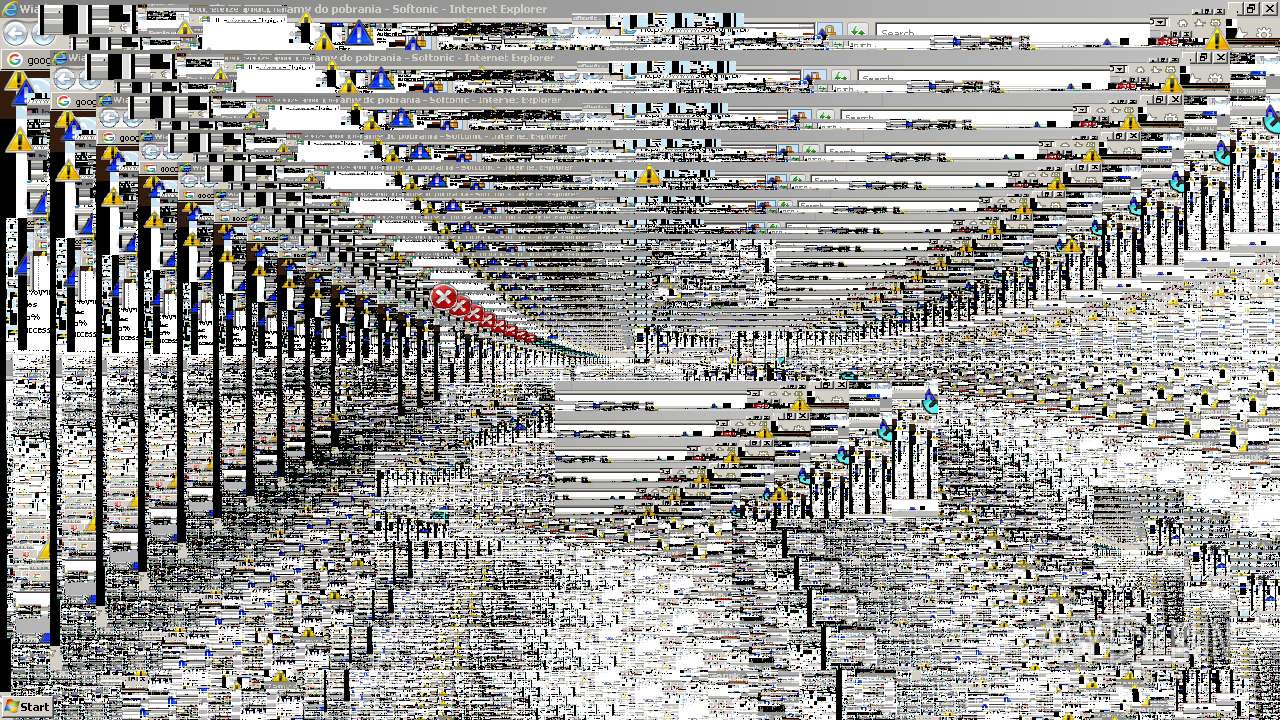
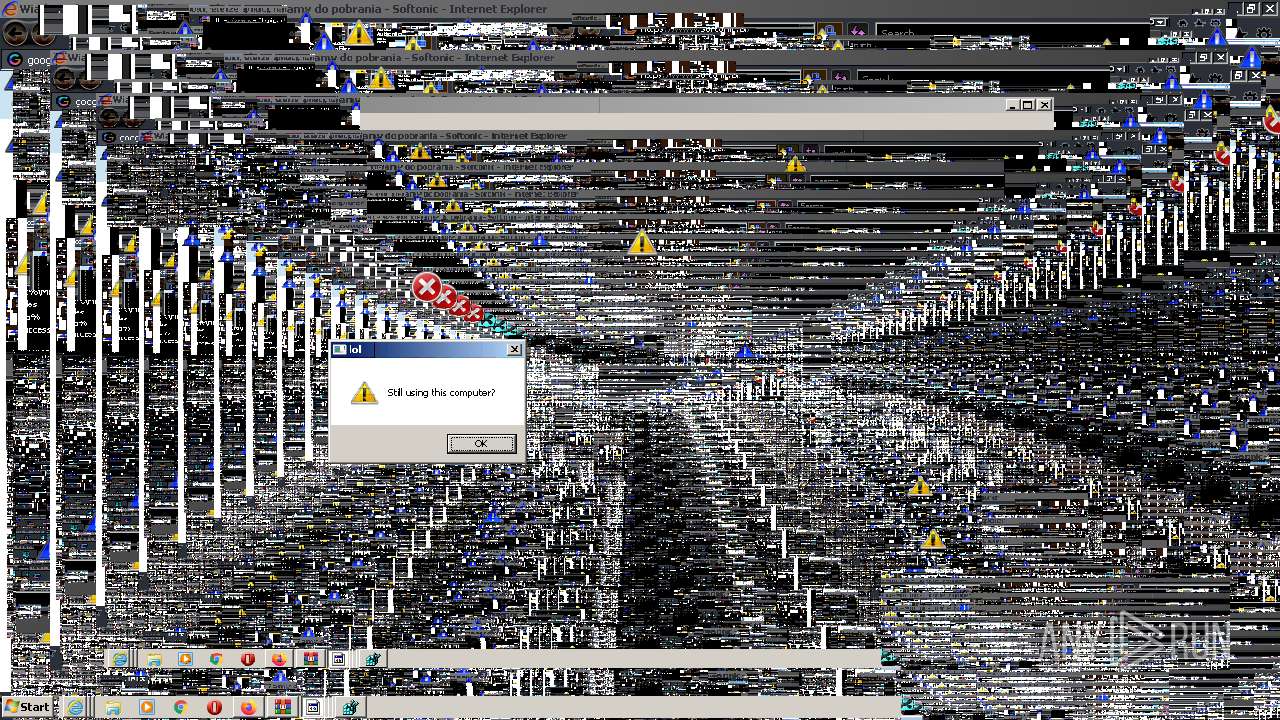
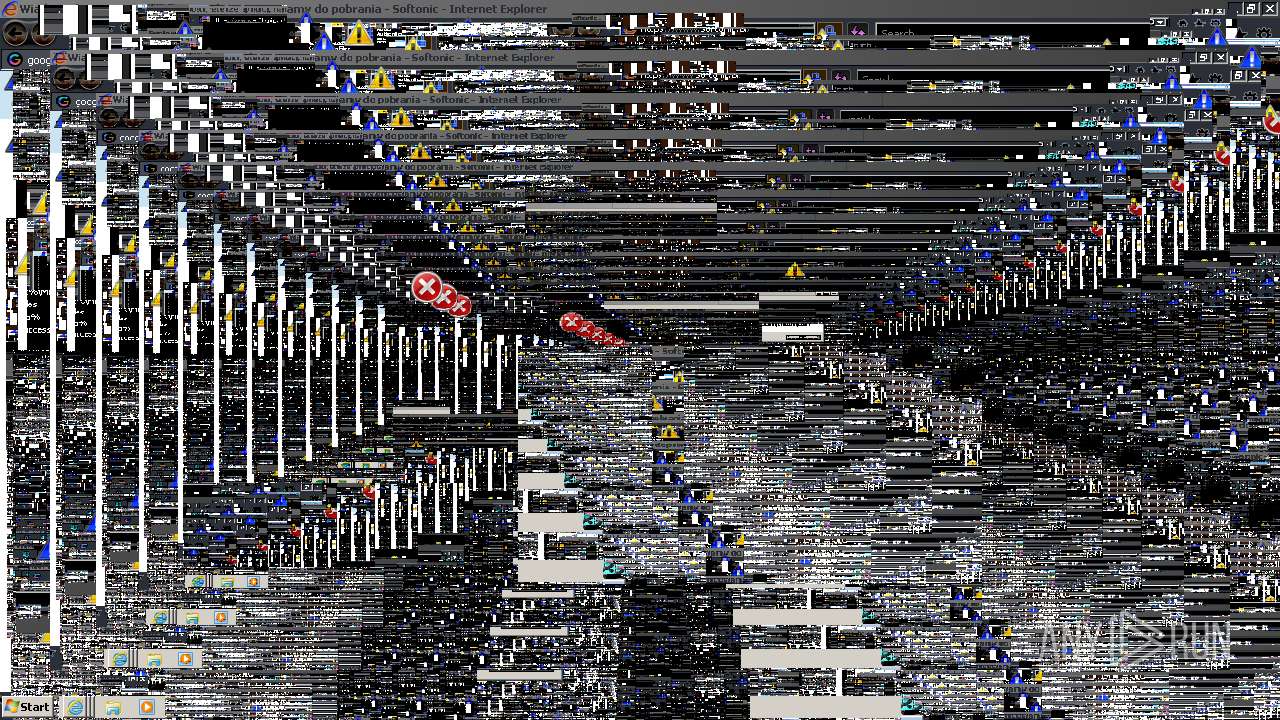
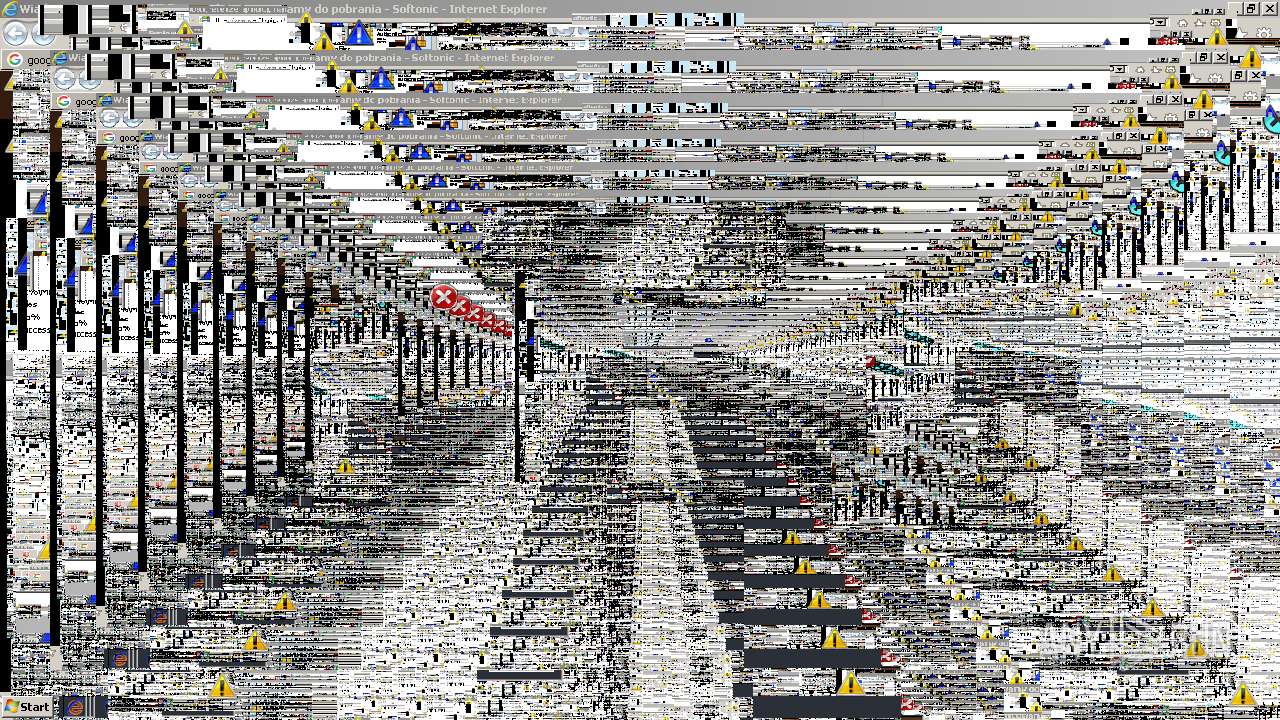
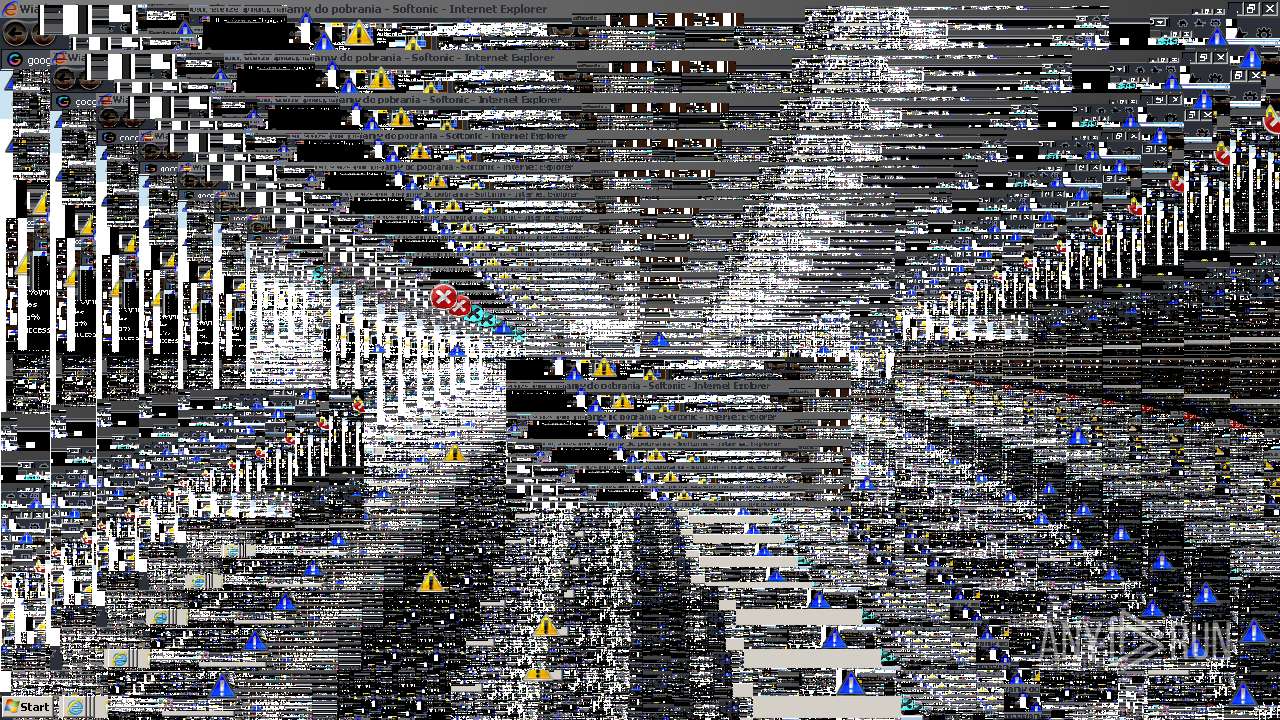
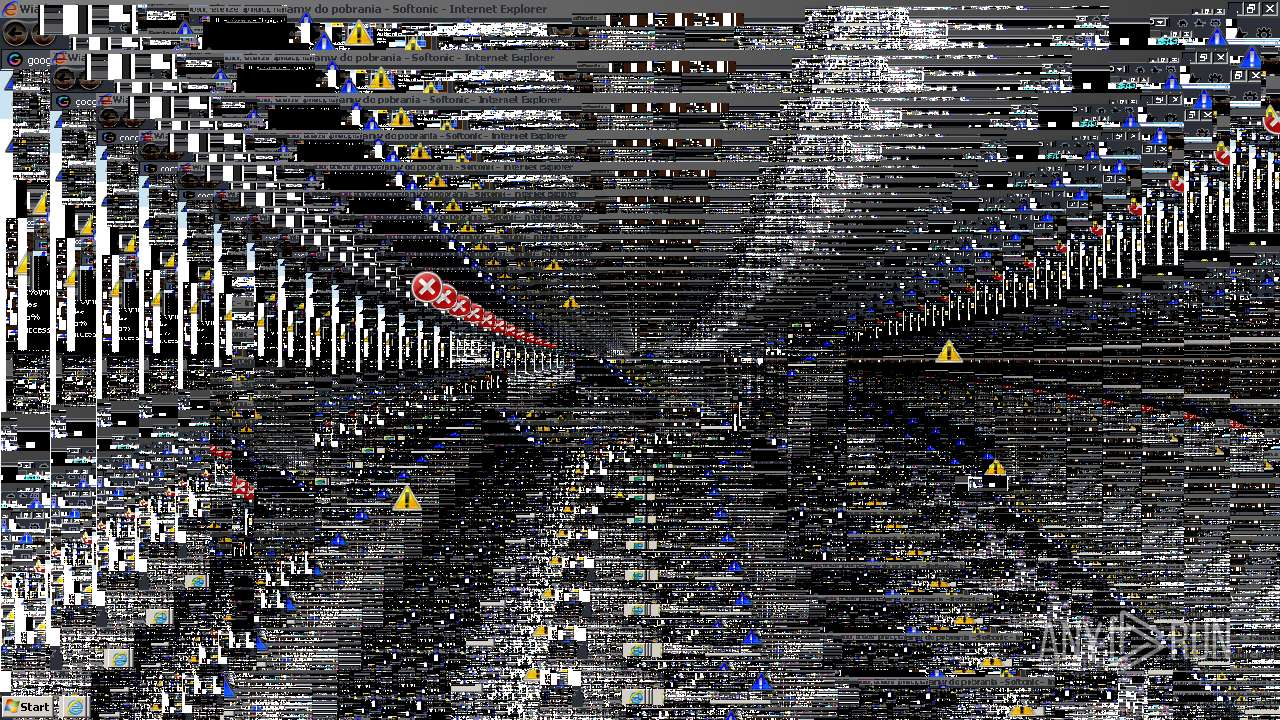
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 344 | "C:\Program Files\Mozilla Firefox\firefox.exe" | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 83.0 Modules
| |||||||||||||||
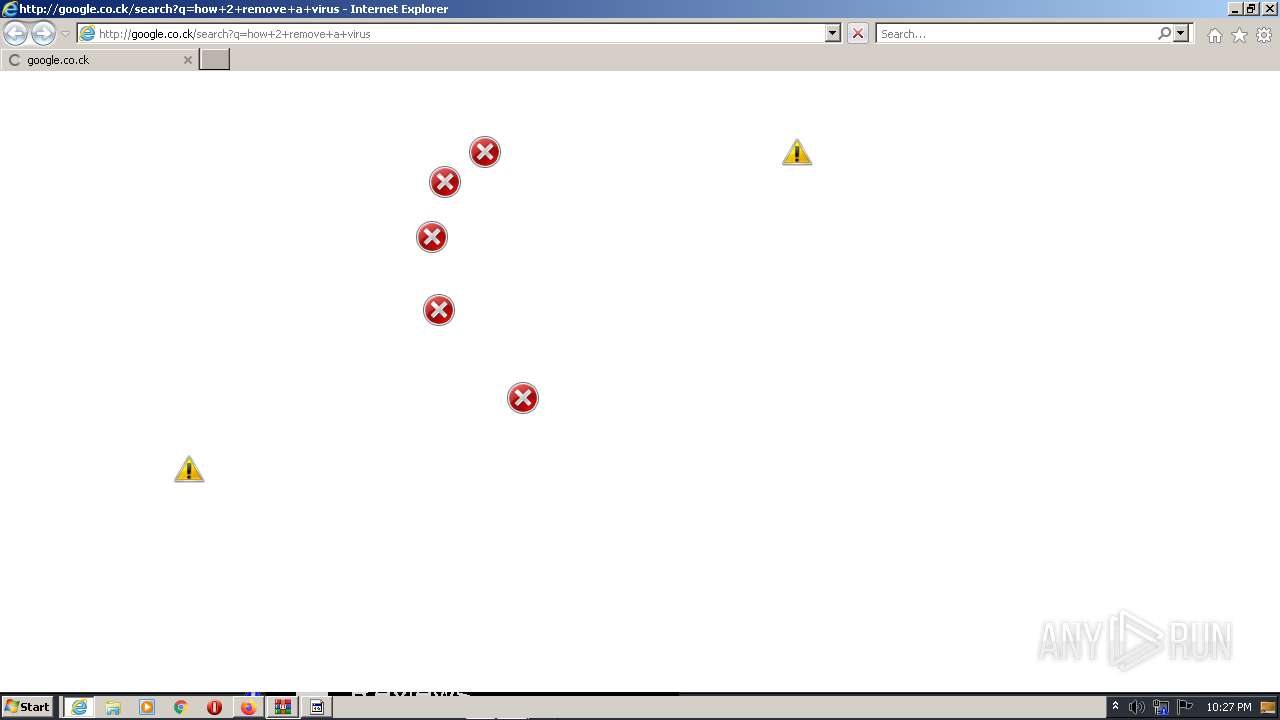
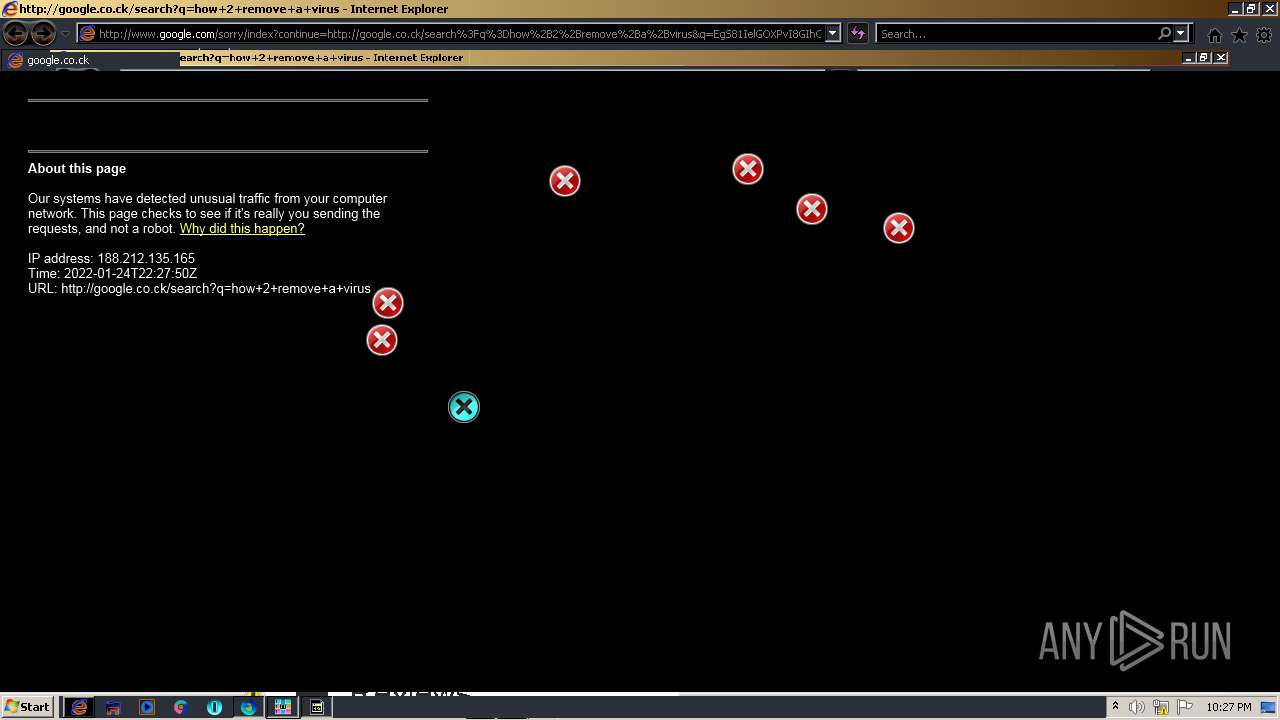
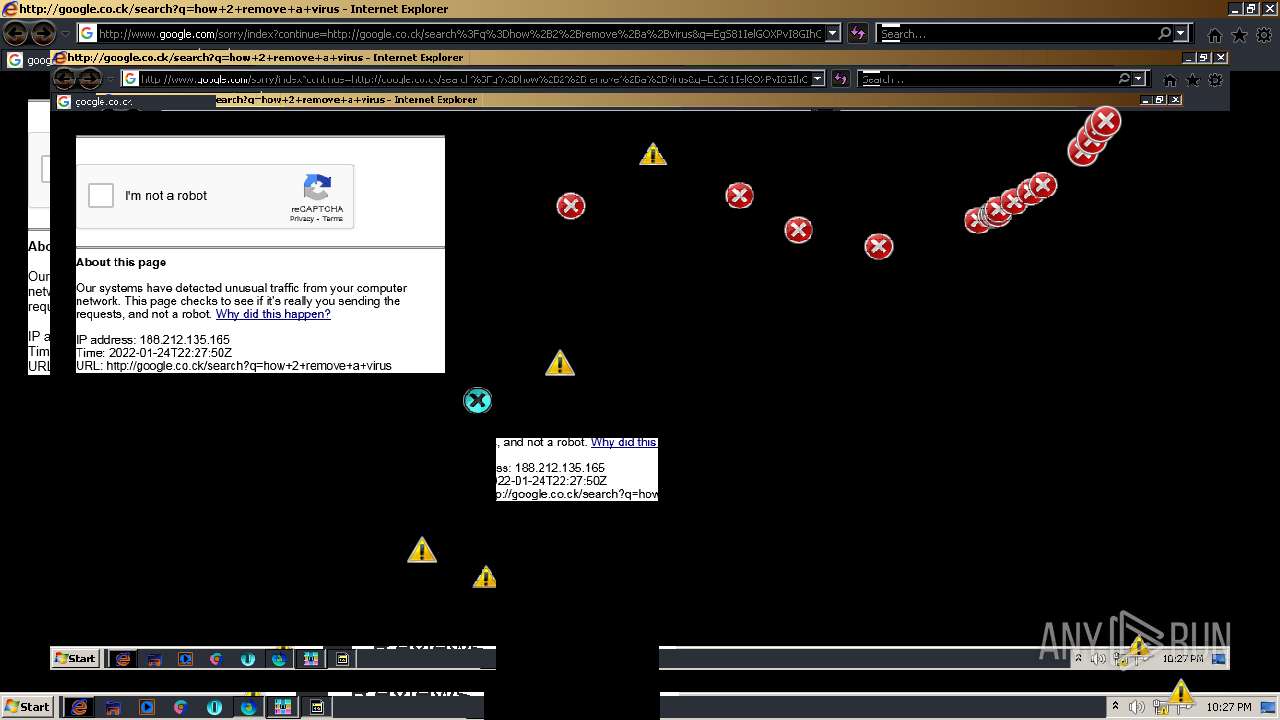
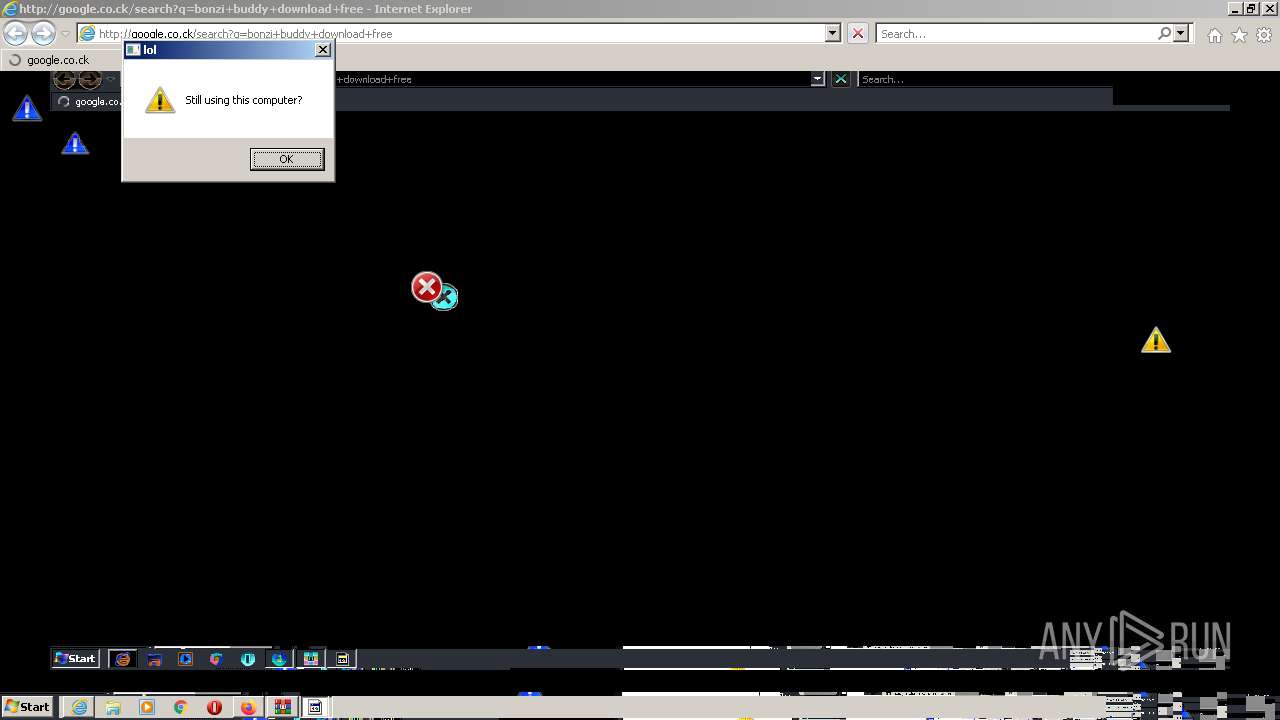
| 348 | "C:\Program Files\Internet Explorer\iexplore.exe" http://google.co.ck/search?q=how+2+remove+a+virus | C:\Program Files\Internet Explorer\iexplore.exe | MEMZ-Clean.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 592 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="344.20.167976199\469218391" -childID 3 -isForBrowser -prefsHandle 3848 -prefMapHandle 3844 -prefsLen 7640 -prefMapSize 238726 -parentBuildID 20201112153044 -appdir "C:\Program Files\Mozilla Firefox\browser" - 344 "\\.\pipe\gecko-crash-server-pipe.344" 3868 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 83.0 Modules
| |||||||||||||||
| 636 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1052,13083390889939420471,6982144772469661430,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1892 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 924 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1052,13083390889939420471,6982144772469661430,131072 --enable-features=PasswordImport --lang=en-US --instant-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1952 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1056 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="344.0.227940179\1433989468" -parentBuildID 20201112153044 -prefsHandle 1120 -prefMapHandle 1112 -prefsLen 1 -prefMapSize 238726 -appdir "C:\Program Files\Mozilla Firefox\browser" - 344 "\\.\pipe\gecko-crash-server-pipe.344" 1204 gpu | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 83.0 Modules
| |||||||||||||||
| 1300 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=86.0.4240.198 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6e7ed988,0x6e7ed998,0x6e7ed9a4 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1324 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="344.41.1638028738\474129104" -childID 6 -isForBrowser -prefsHandle 4528 -prefMapHandle 4524 -prefsLen 9489 -prefMapSize 238726 -parentBuildID 20201112153044 -appdir "C:\Program Files\Mozilla Firefox\browser" - 344 "\\.\pipe\gecko-crash-server-pipe.344" 4540 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 83.0 Modules
| |||||||||||||||
| 1420 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3884.39065\MEMZ 4.0 Clean\MEMZ-Clean.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3884.39065\MEMZ 4.0 Clean\MEMZ-Clean.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
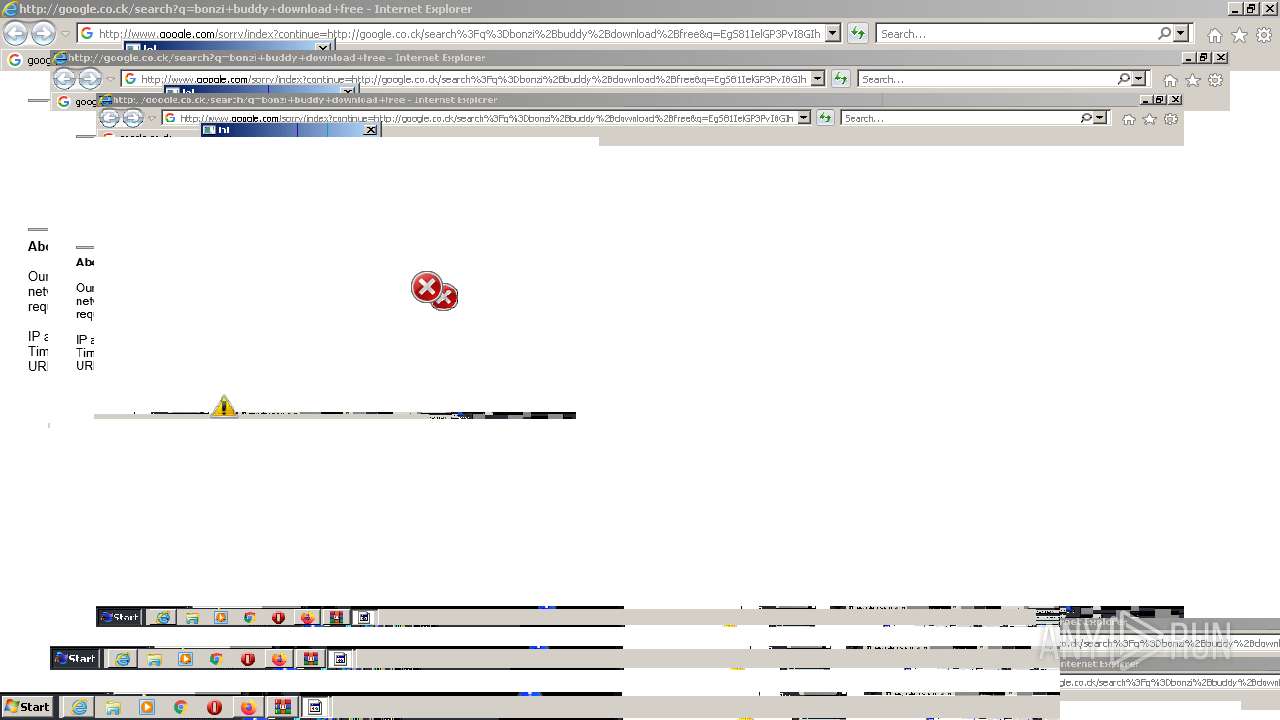
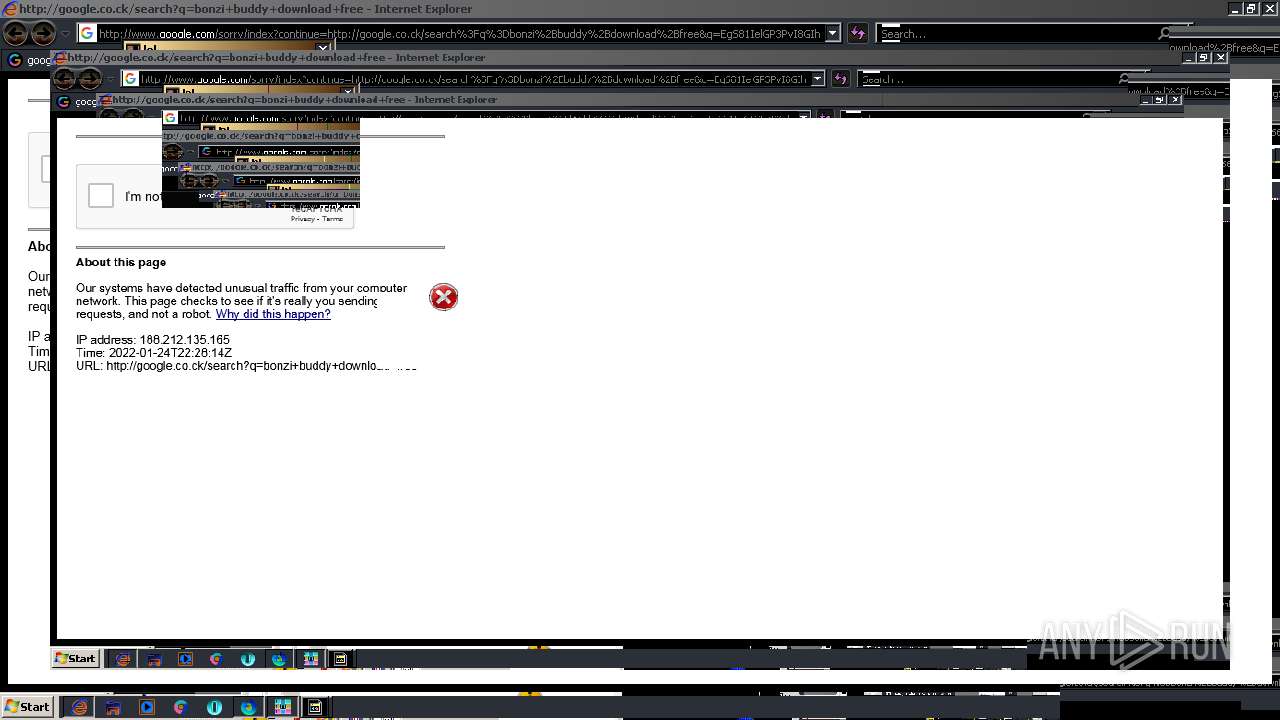
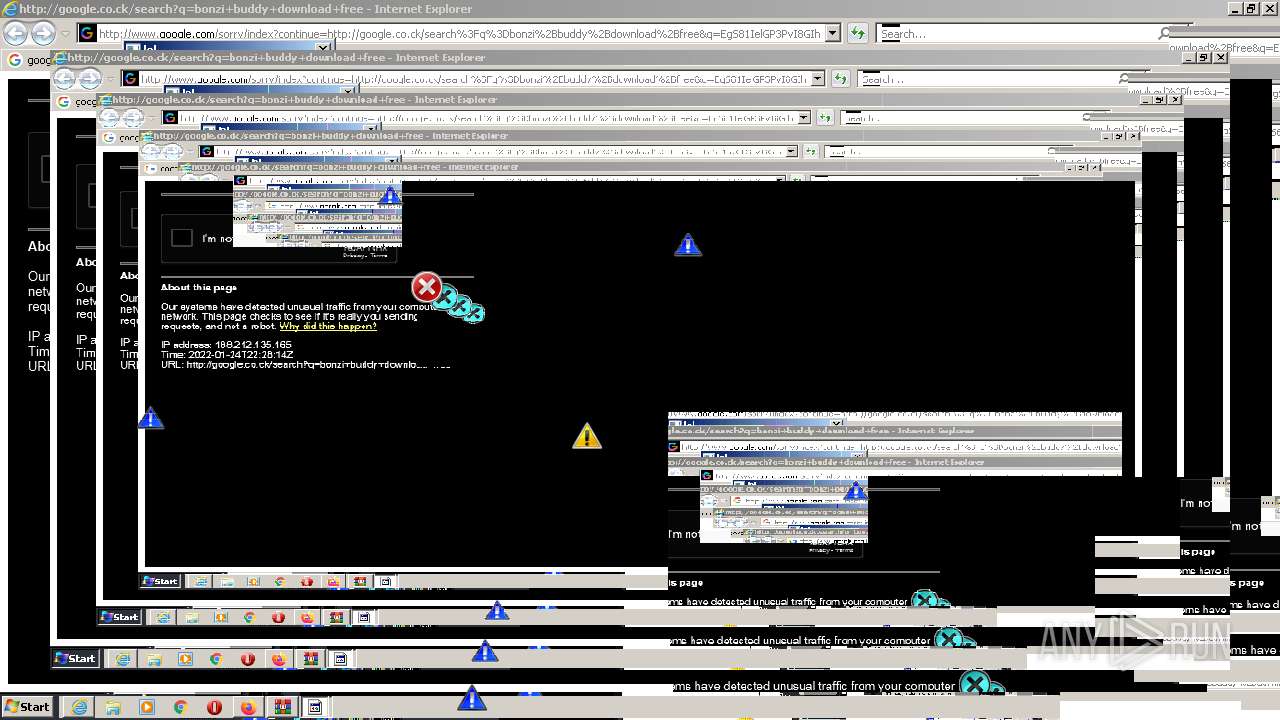
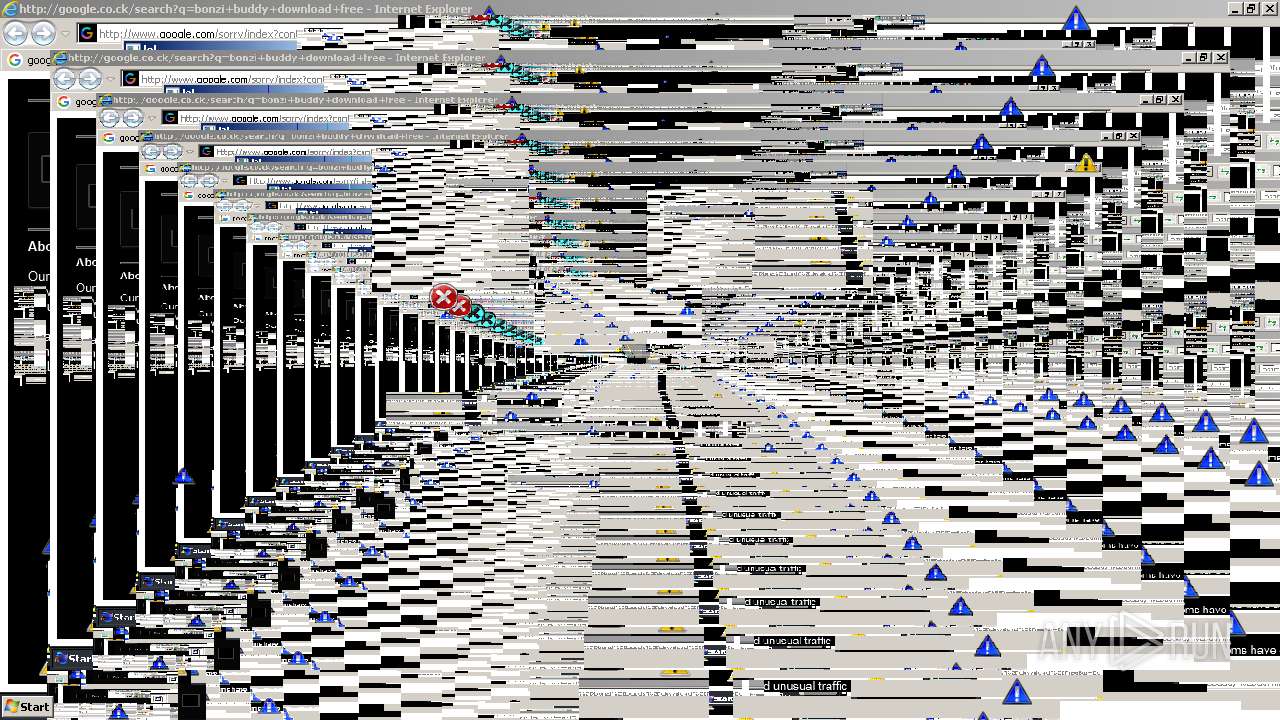
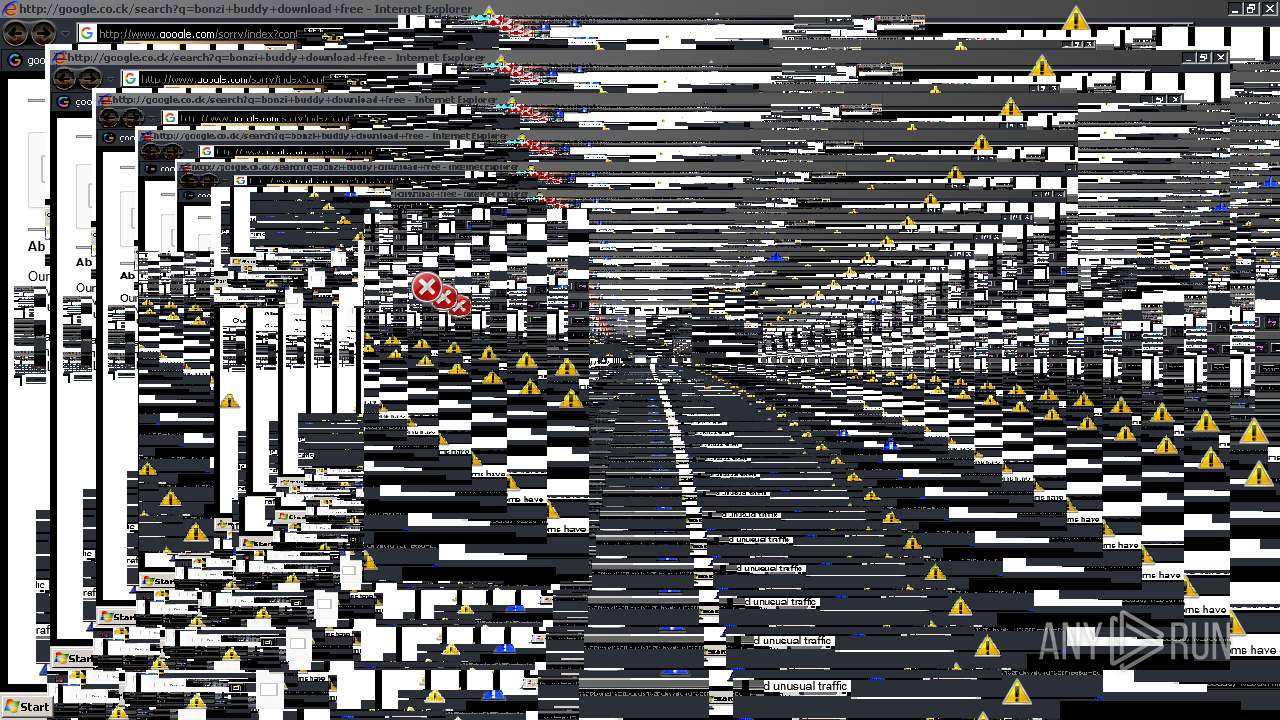
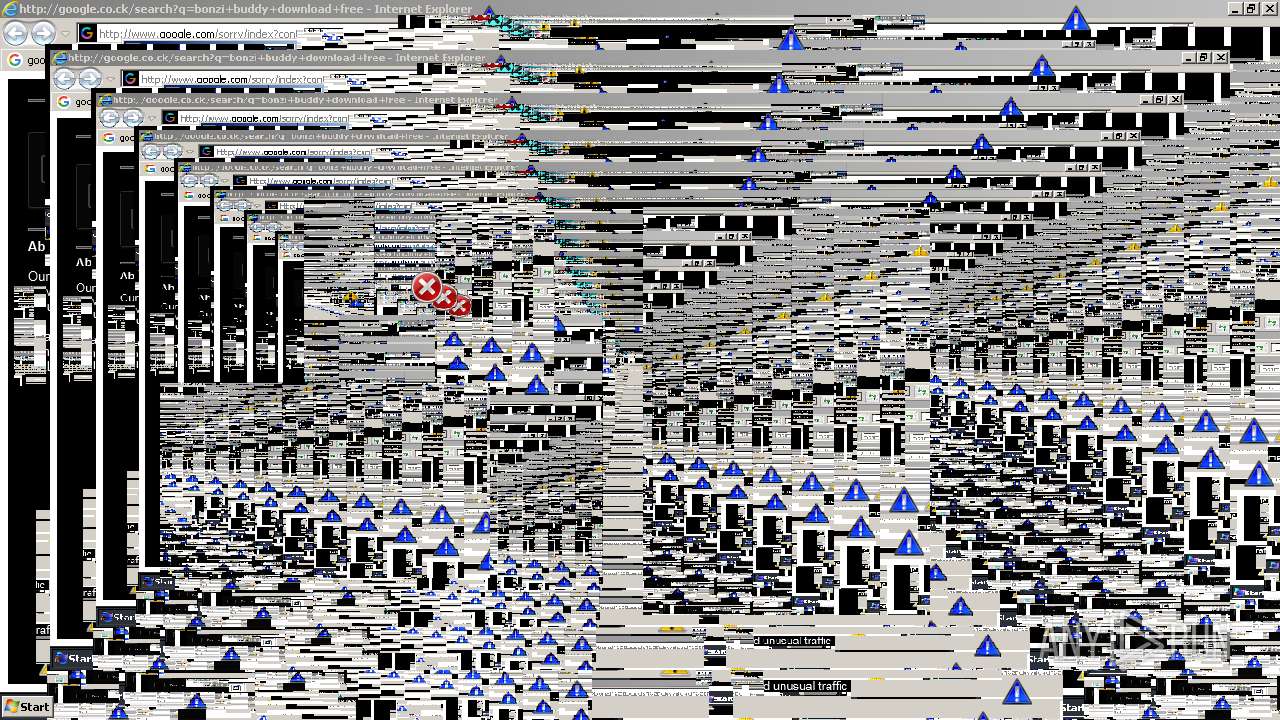
| 1820 | "C:\Program Files\Internet Explorer\iexplore.exe" http://google.co.ck/search?q=bonzi+buddy+download+free | C:\Program Files\Internet Explorer\iexplore.exe | MEMZ-Clean.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
88 791
Read events
88 083
Write events
691
Delete events
17
Modification events
| (PID) Process: | (2184) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (2184) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: 792543728 | |||
| (PID) Process: | (2184) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30937457 | |||
| (PID) Process: | (2184) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (2184) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30937457 | |||
| (PID) Process: | (2184) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2184) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2184) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2184) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2184) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
6
Suspicious files
356
Text files
370
Unknown types
96
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3748 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 3748 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\223DE96EE265046957A660ED7C9DD9E7_EFF9B9BA98DEAA773F261FA85A0B1771 | der | |
MD5:— | SHA256:— | |||
| 2184 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | der | |
MD5:— | SHA256:— | |||
| 3748 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\223DE96EE265046957A660ED7C9DD9E7_EFF9B9BA98DEAA773F261FA85A0B1771 | binary | |
MD5:— | SHA256:— | |||
| 3748 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\5UN2S66J.txt | text | |
MD5:— | SHA256:— | |||
| 3748 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\EB2C4AB8B68FFA4B7733A9139239A396_D76DB901EE986B889F30D8CC06229E2D | binary | |
MD5:— | SHA256:— | |||
| 3748 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\EB2C4AB8B68FFA4B7733A9139239A396_D76DB901EE986B889F30D8CC06229E2D | der | |
MD5:— | SHA256:— | |||
| 2184 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | binary | |
MD5:— | SHA256:— | |||
| 3748 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\MEMZ4[1].htm | html | |
MD5:— | SHA256:— | |||
| 3748 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\U9R27NMU.txt | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
57
TCP/UDP connections
235
DNS requests
168
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3552 | iexplore.exe | GET | 301 | 151.101.1.132:80 | http://motherboard.vice.com/read/watch-this-malware-turn-a-computer-into-a-digital-hellscape | US | — | — | whitelisted |
2184 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
3748 | iexplore.exe | GET | 200 | 192.124.249.41:80 | http://ocsp.godaddy.com//MEIwQDA%2BMDwwOjAJBgUrDgMCGgUABBQdI2%2BOBkuXH93foRUj4a7lAr4rGwQUOpqFBxBnKLbv9r0FQW4gwZTaD94CAQc%3D | US | der | 1.69 Kb | whitelisted |
3748 | iexplore.exe | GET | 200 | 192.124.249.41:80 | http://ocsp.godaddy.com//MEowSDBGMEQwQjAJBgUrDgMCGgUABBS2CA1fbGt26xPkOKX4ZguoUjM0TgQUQMK9J47MNIMwojPX%2B2yz8LQsgM4CCQCB%2BJkTOHdrdg%3D%3D | US | der | 1.74 Kb | whitelisted |
344 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
344 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
344 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
344 | firefox.exe | POST | 200 | 172.217.18.99:80 | http://ocsp.pki.goog/gts1c3 | US | der | 472 b | whitelisted |
3552 | iexplore.exe | GET | 200 | 172.217.18.99:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | der | 1.41 Kb | whitelisted |
3552 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAbY2QTVWENG9oovp1QifsQ%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3748 | iexplore.exe | 207.241.224.2:443 | archive.org | Internet Archive | US | malicious |
2184 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
3748 | iexplore.exe | 23.32.238.201:80 | ctldl.windowsupdate.com | XO Communications | US | suspicious |
3748 | iexplore.exe | 192.124.249.41:80 | ocsp.godaddy.com | Sucuri | US | suspicious |
2184 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3748 | iexplore.exe | 207.241.239.242:443 | polyfill.archive.org | Internet Archive | US | suspicious |
3748 | iexplore.exe | 207.241.225.102:443 | analytics.archive.org | Internet Archive | US | suspicious |
3532 | chrome.exe | 142.250.186.174:443 | clients2.google.com | Google Inc. | US | whitelisted |
3532 | chrome.exe | 142.250.186.68:443 | www.google.com | Google Inc. | US | whitelisted |
3532 | chrome.exe | 142.250.185.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
archive.org |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.godaddy.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
polyfill.archive.org |
| suspicious |
analytics.archive.org |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
clients2.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
344 | firefox.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
344 | firefox.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
344 | firefox.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
344 | firefox.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |