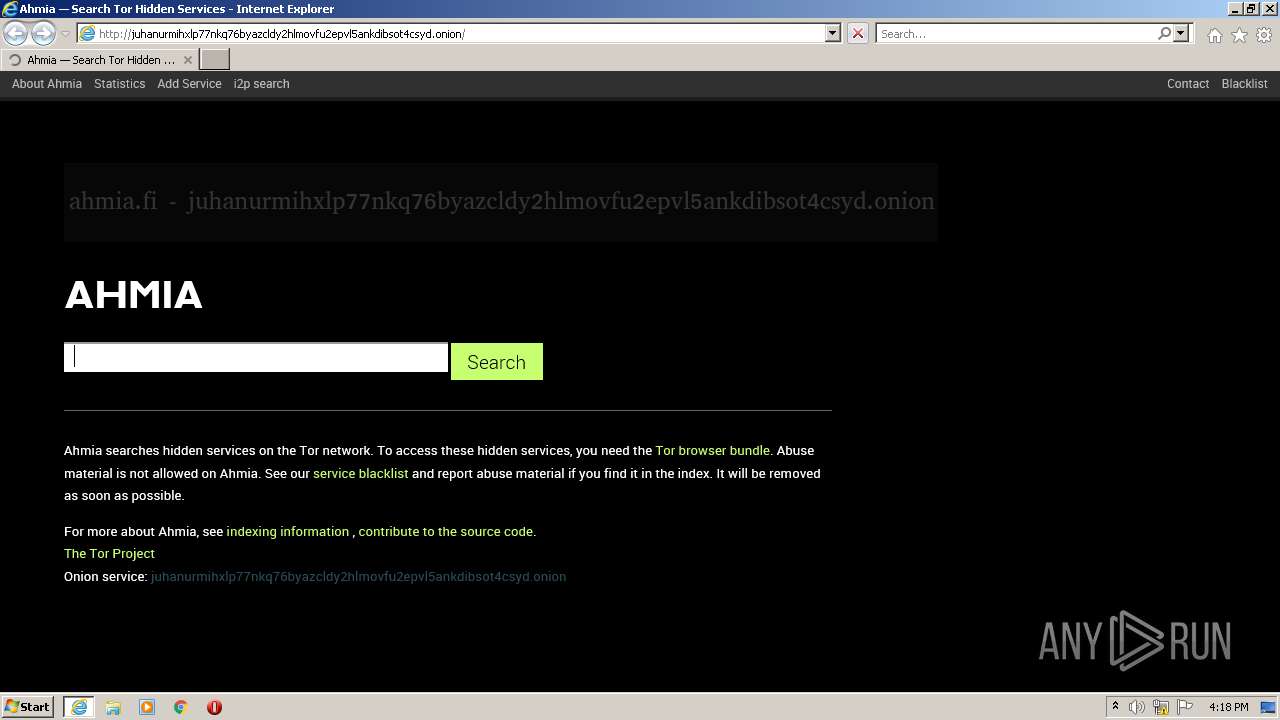
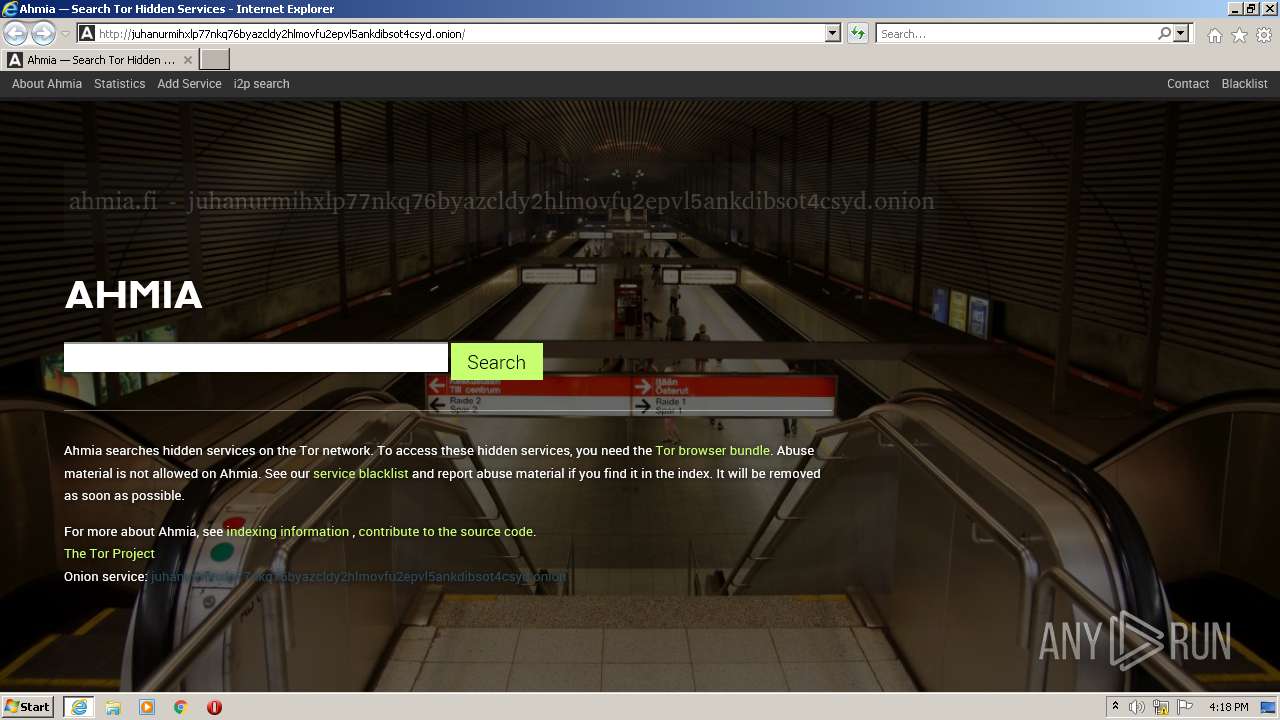
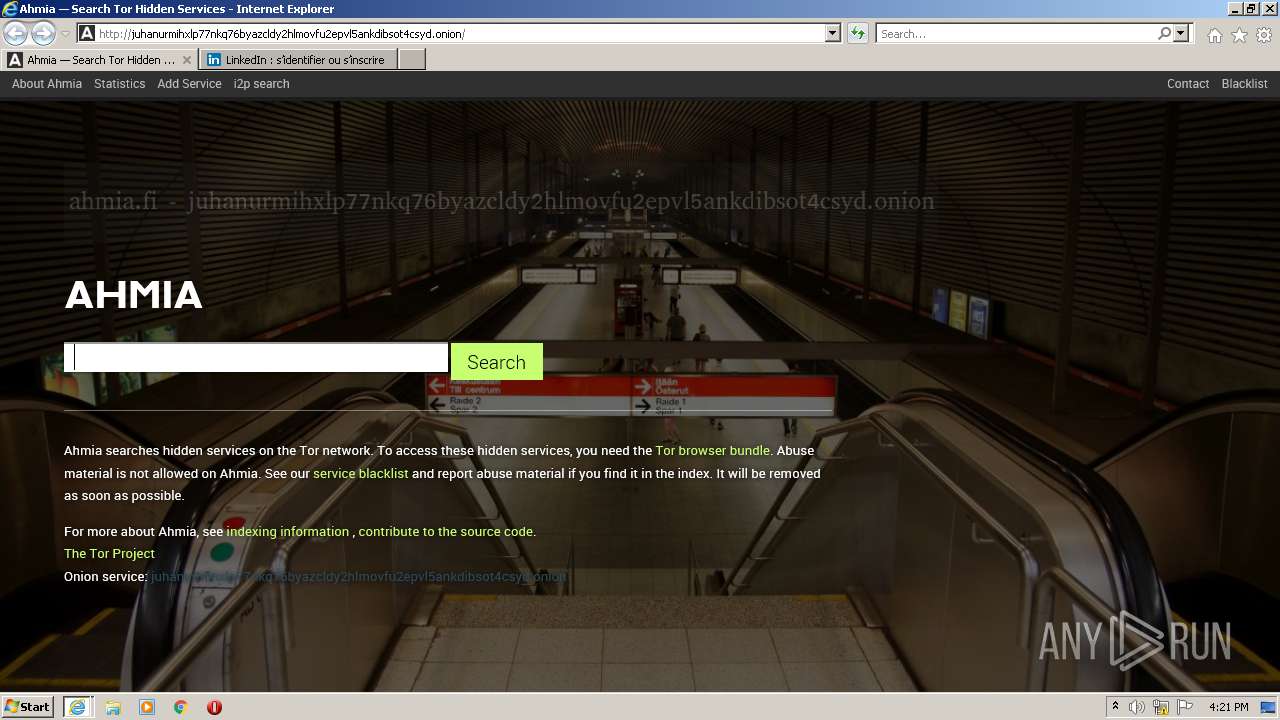
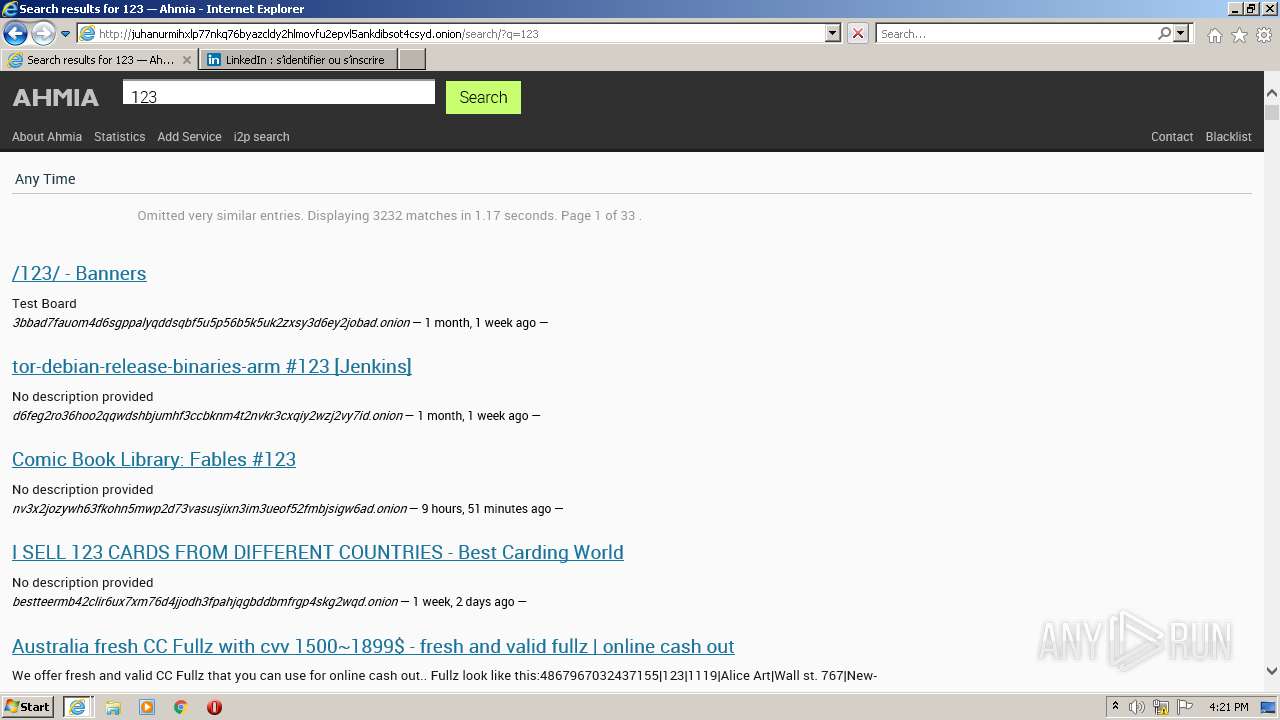
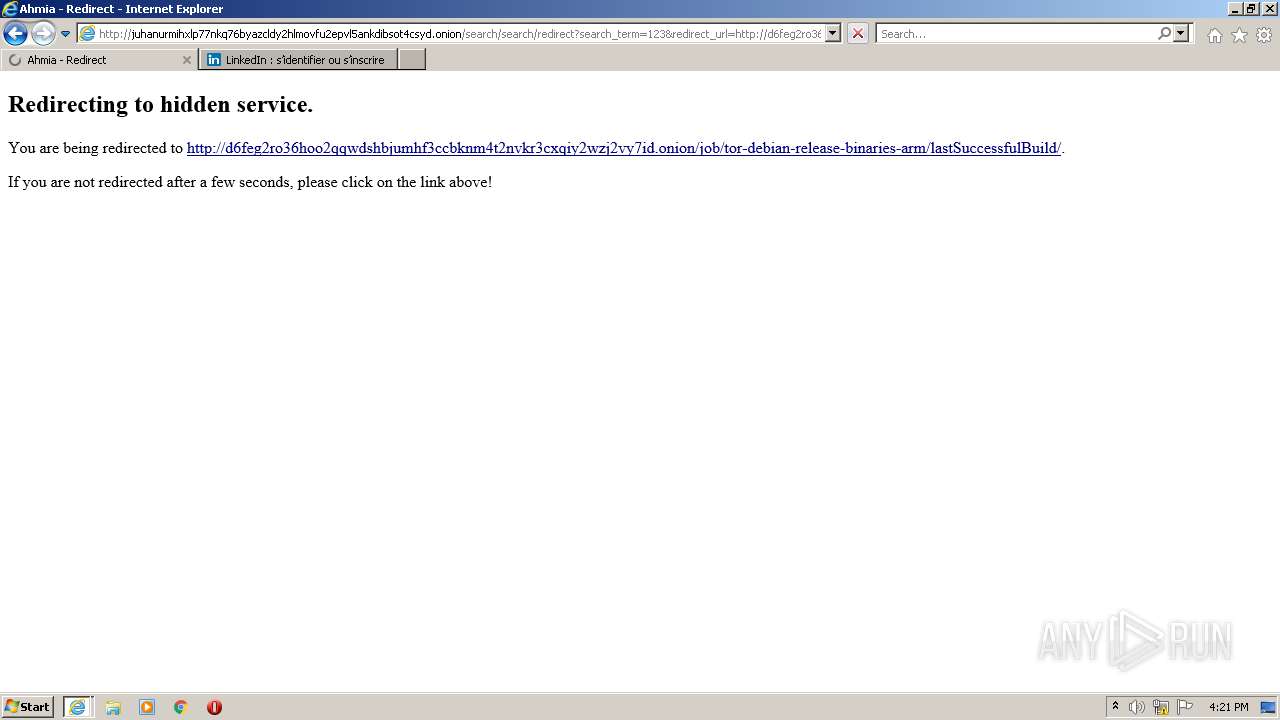
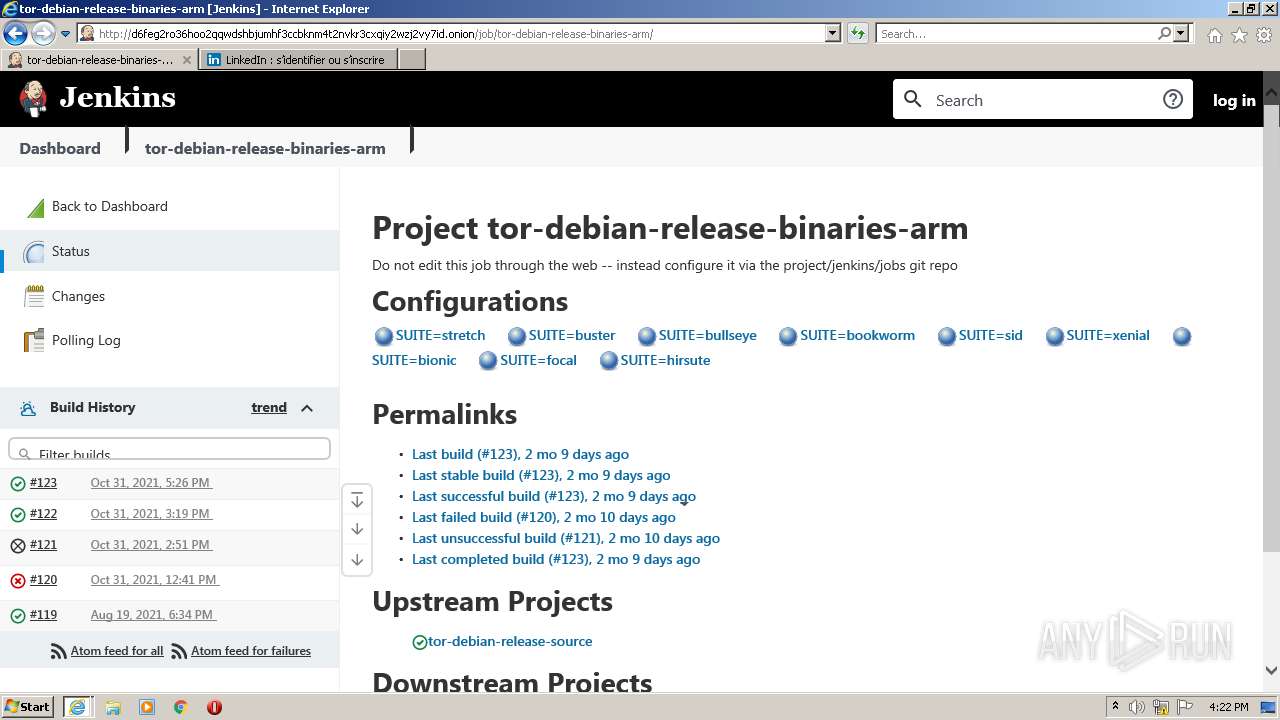
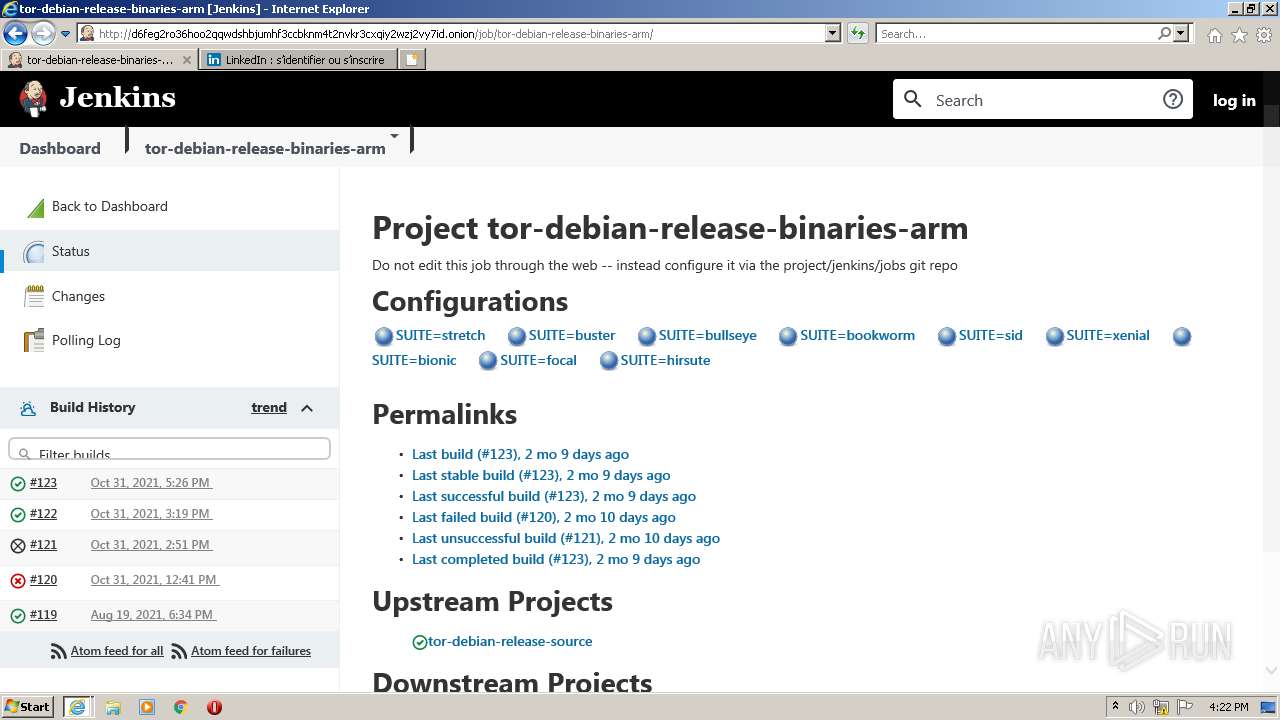
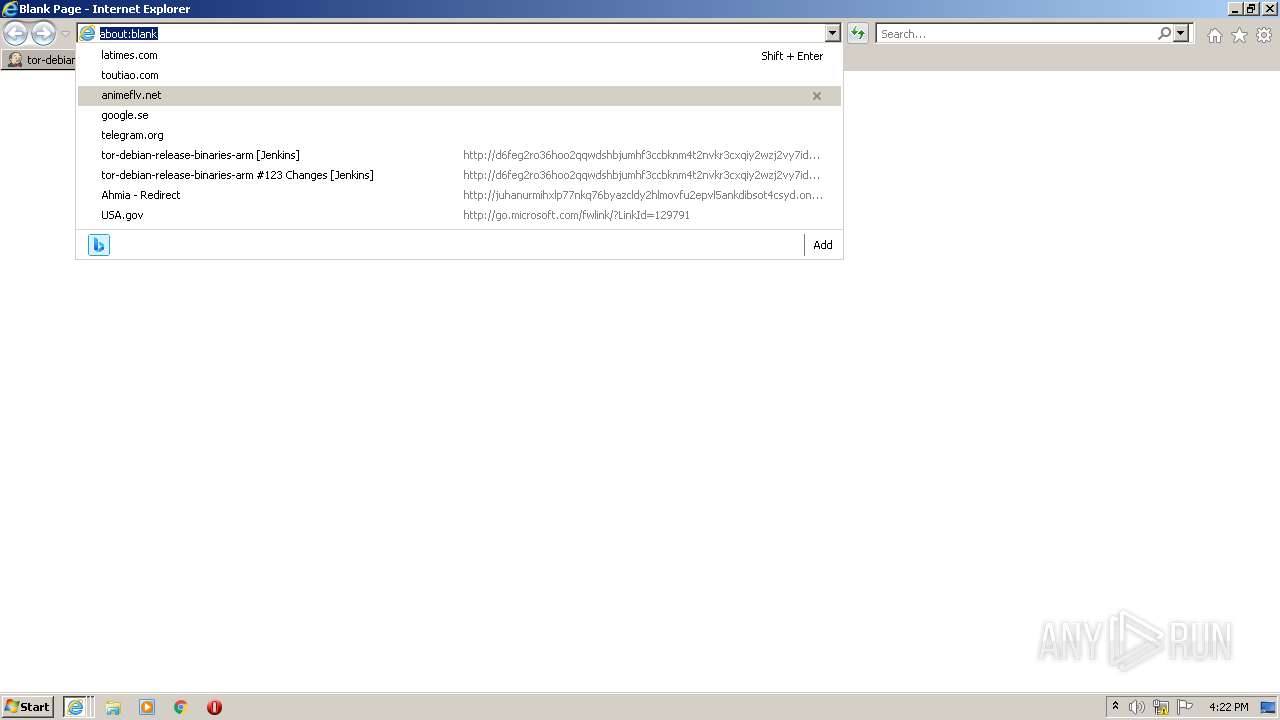
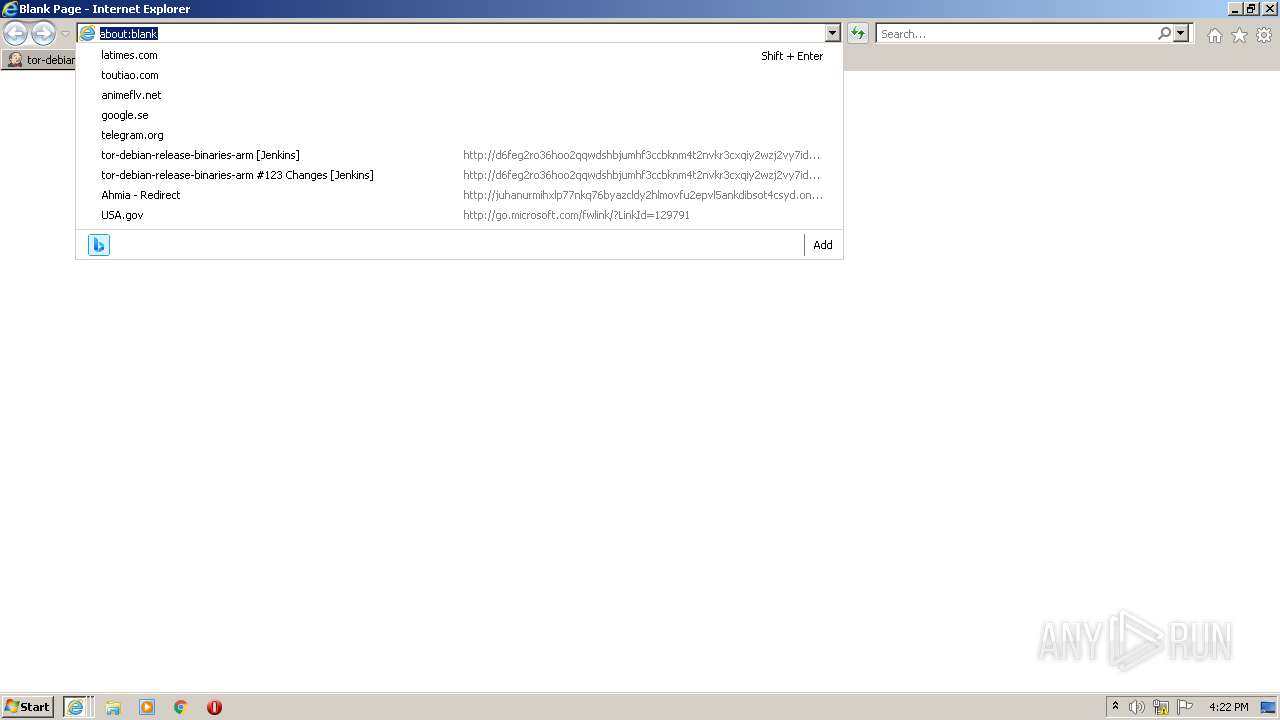
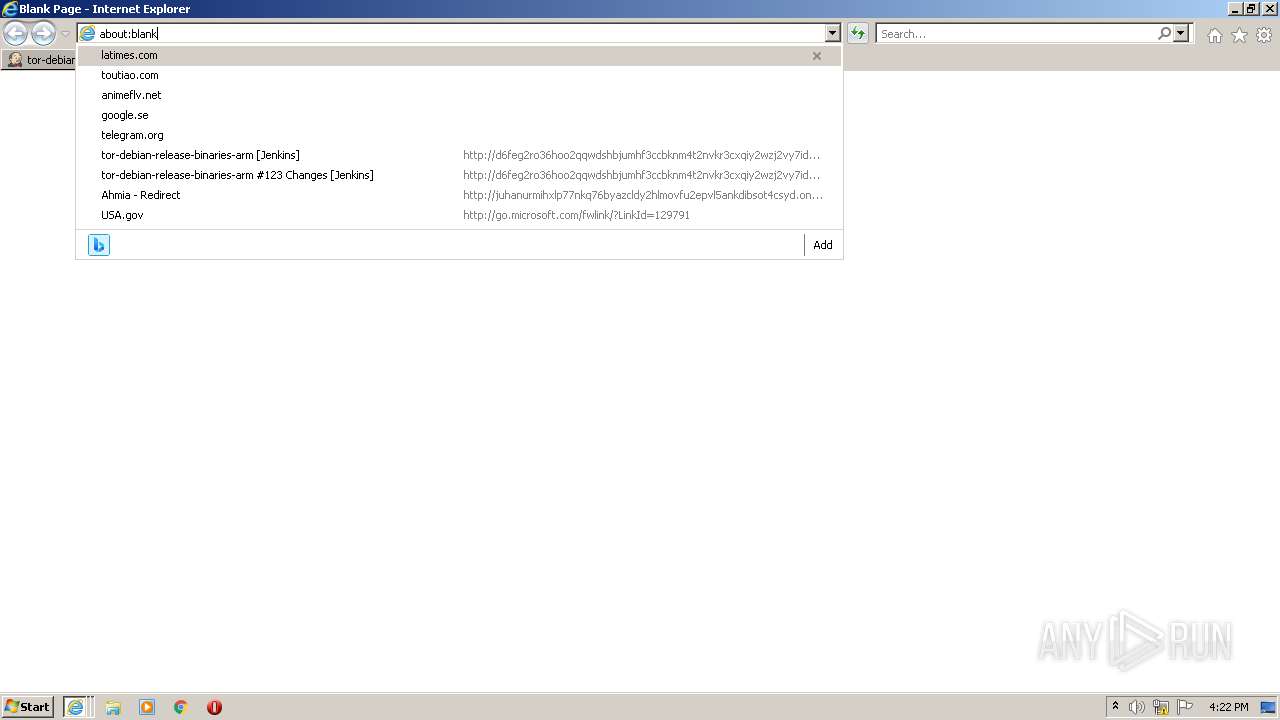
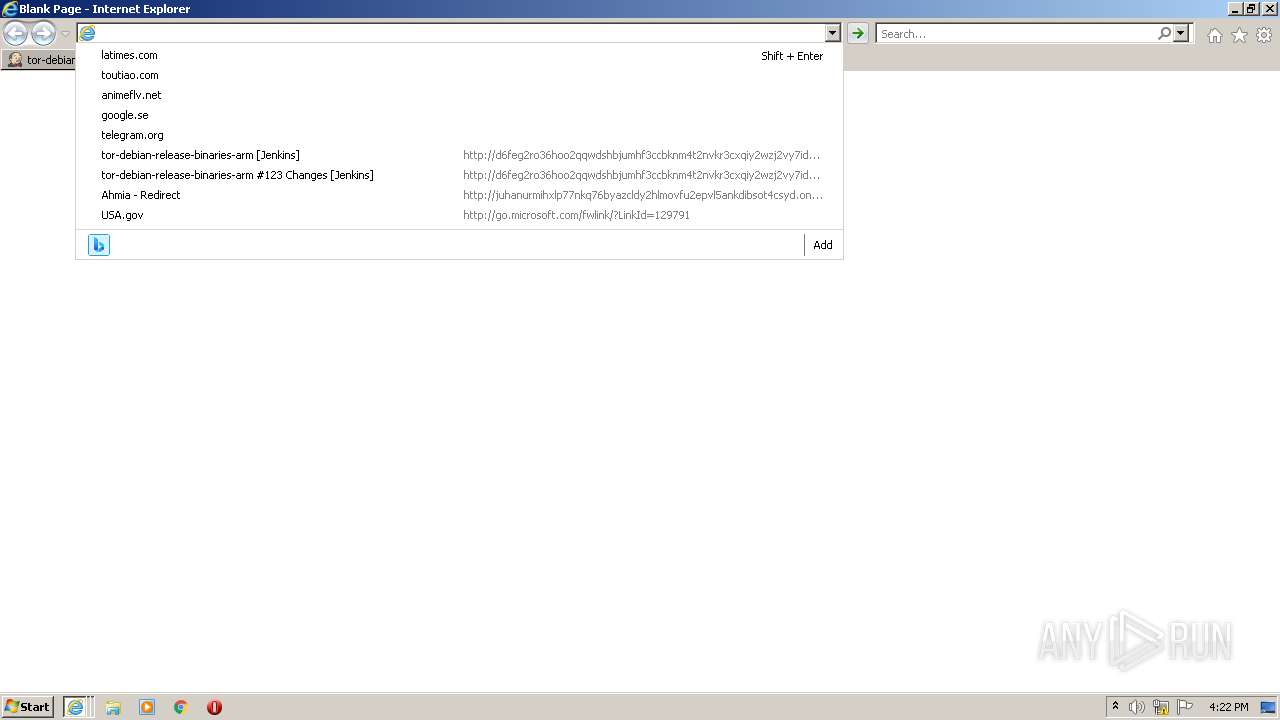
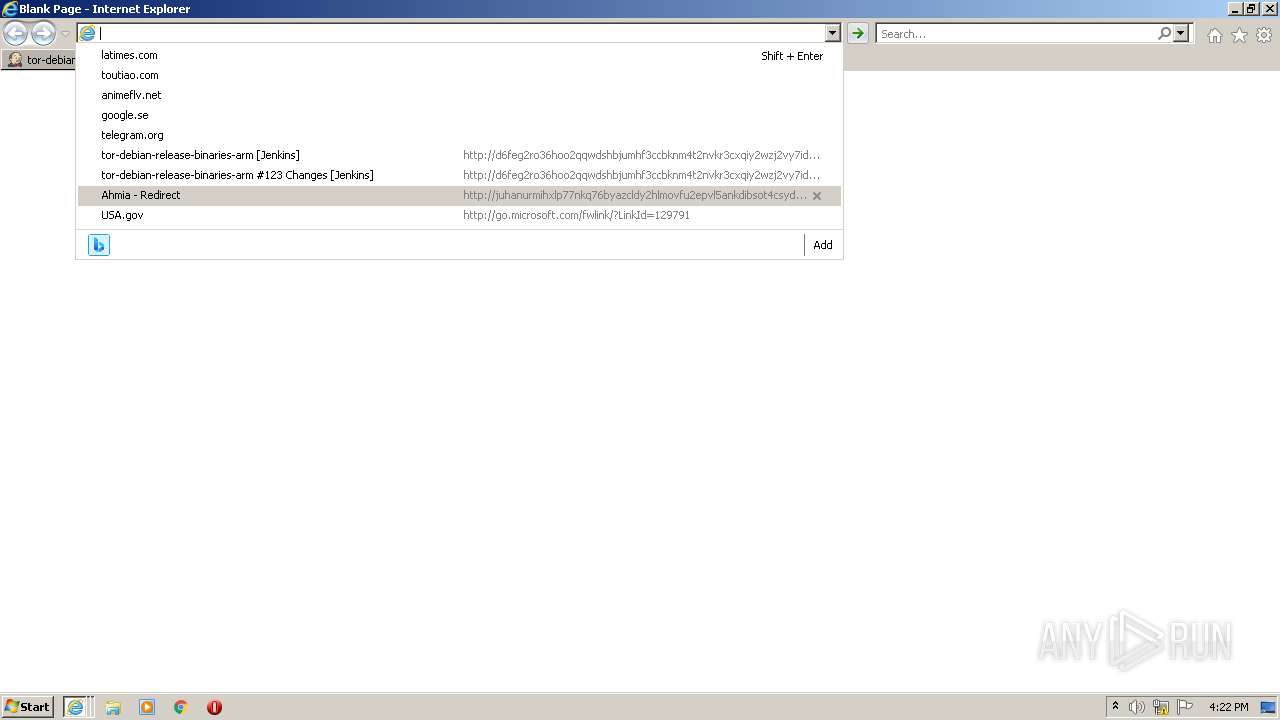
| URL: | http://juhanurmihxlp77nkq76byazcldy2hlmovfu2epvl5ankdibsot4csyd.onion |
| Full analysis: | https://app.any.run/tasks/a55dd846-b75a-4a11-9bd5-ed789b9cdb7d |
| Verdict: | Malicious activity |
| Analysis date: | January 09, 2022, 16:18:24 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | BB13071F66A92179BD6D7877B9F0ECE1 |
| SHA1: | 73E73397CF284ED79D2C95557525D08942E198B7 |
| SHA256: | 02E9CBFCE58542D51FD5843FBCE191C8791D834DFEFEB8BC060840B7427271FD |
| SSDEEP: | 3:N1KUpXMTxEb8Q5bLDtRRG3Q:CUJYxEbRLvp |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3632)
- iexplore.exe (PID: 1540)
- iexplore.exe (PID: 3520)
- iexplore.exe (PID: 1376)
- mmc.exe (PID: 2612)
Reads internet explorer settings
- mmc.exe (PID: 2612)
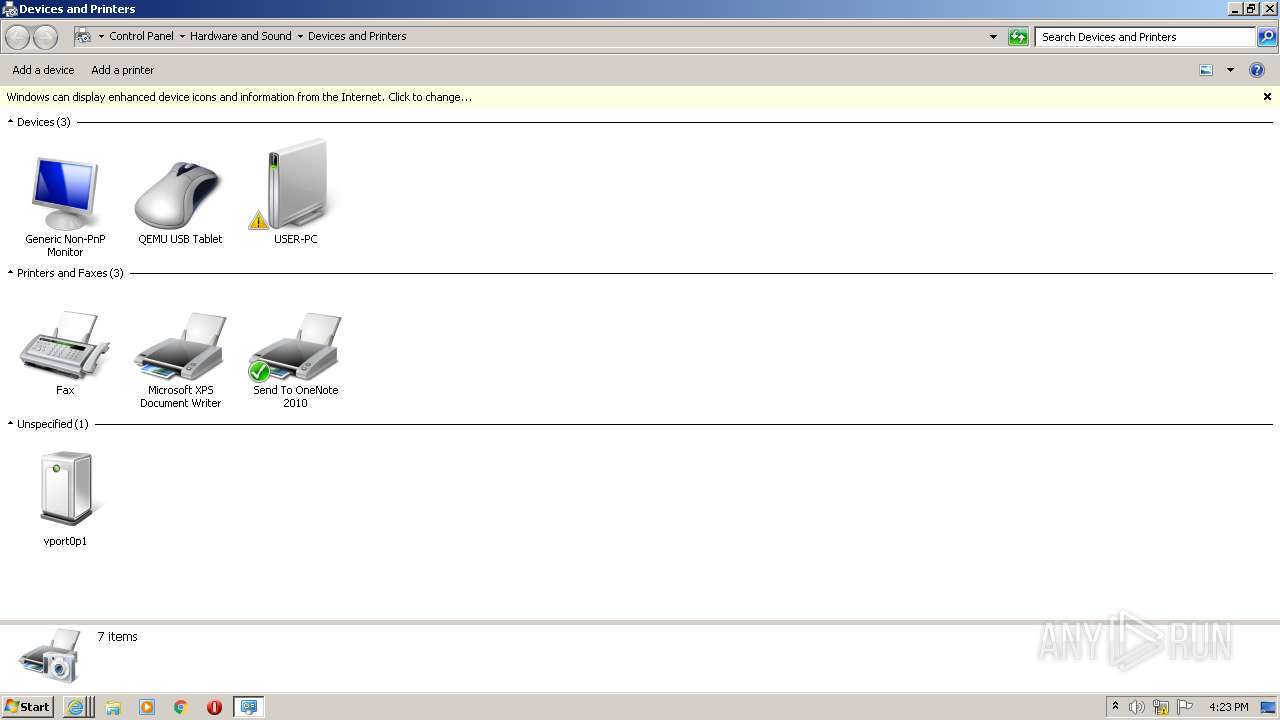
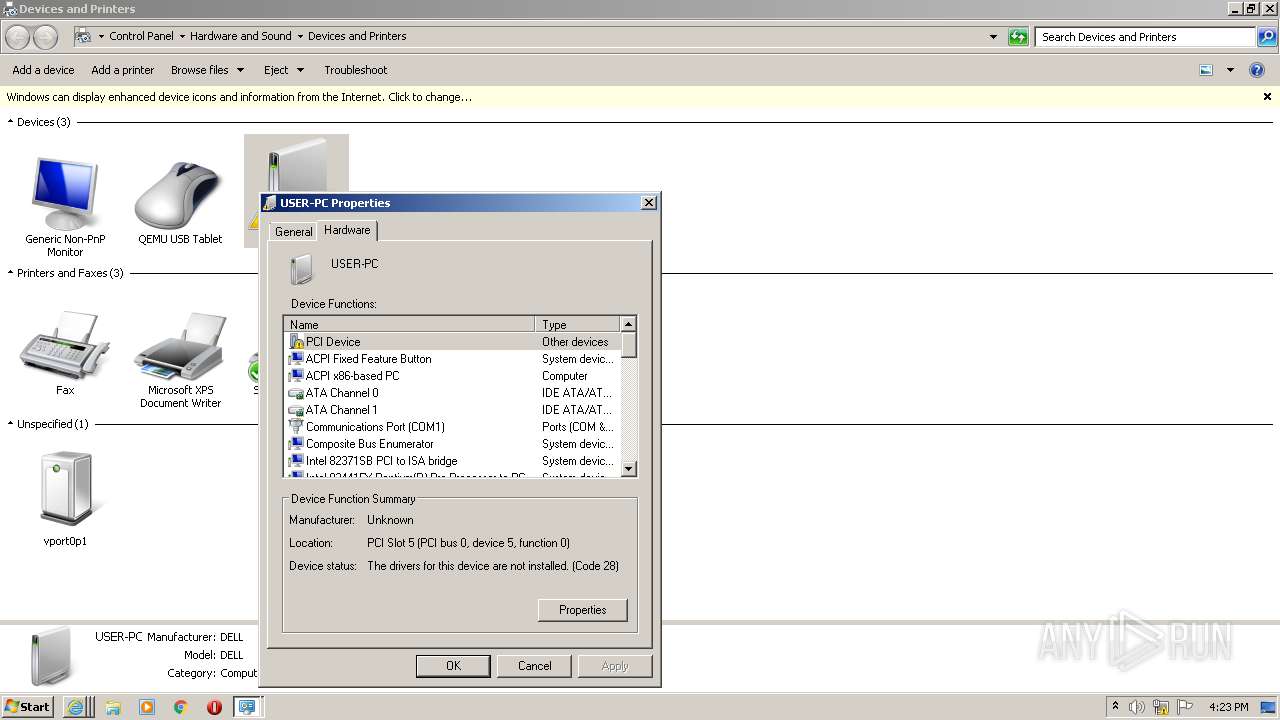
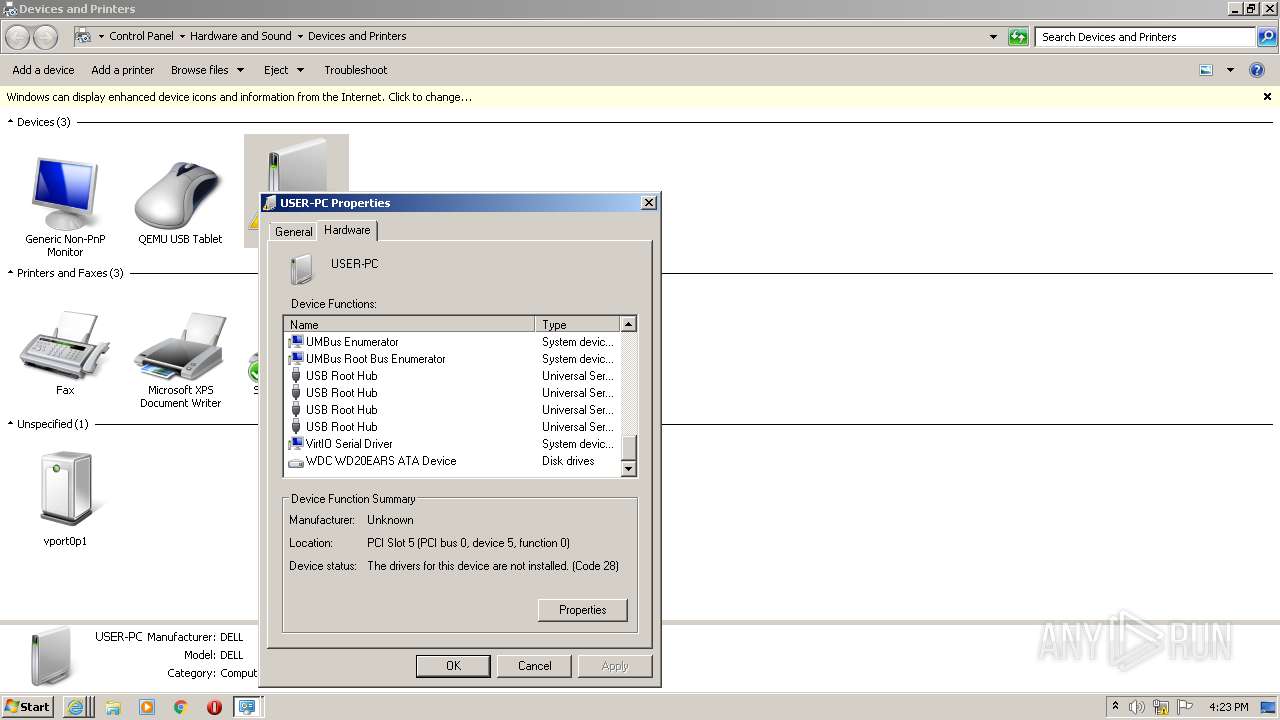
Executed via COM
- DeviceDisplayObjectProvider.exe (PID: 2784)
INFO
Checks supported languages
- iexplore.exe (PID: 1540)
- iexplore.exe (PID: 3632)
- iexplore.exe (PID: 3520)
- iexplore.exe (PID: 1376)
- DeviceDisplayObjectProvider.exe (PID: 2784)
- mmc.exe (PID: 2612)
Reads internet explorer settings
- iexplore.exe (PID: 3632)
- iexplore.exe (PID: 3520)
- iexplore.exe (PID: 1376)
Reads the computer name
- iexplore.exe (PID: 3520)
- iexplore.exe (PID: 3632)
- iexplore.exe (PID: 1540)
- iexplore.exe (PID: 1376)
- mmc.exe (PID: 2612)
- DeviceDisplayObjectProvider.exe (PID: 2784)
Application launched itself
- iexplore.exe (PID: 1540)
Checks Windows Trust Settings
- iexplore.exe (PID: 1540)
- iexplore.exe (PID: 3632)
- iexplore.exe (PID: 3520)
- iexplore.exe (PID: 1376)
Creates files in the user directory
- iexplore.exe (PID: 1540)
- iexplore.exe (PID: 3520)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1540)
Changes internet zones settings
- iexplore.exe (PID: 1540)
Reads settings of System Certificates
- iexplore.exe (PID: 1540)
- iexplore.exe (PID: 3632)
- iexplore.exe (PID: 3520)
- iexplore.exe (PID: 1376)
Changes settings of System certificates
- iexplore.exe (PID: 1540)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 3632)
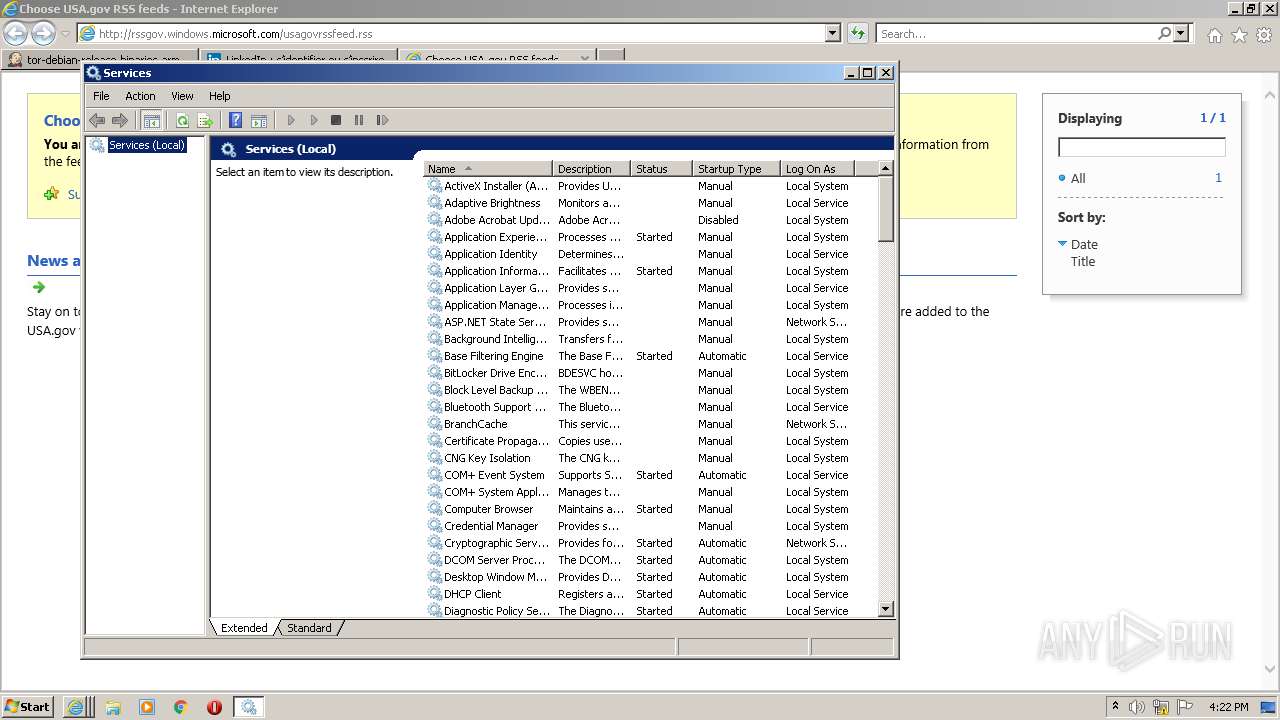
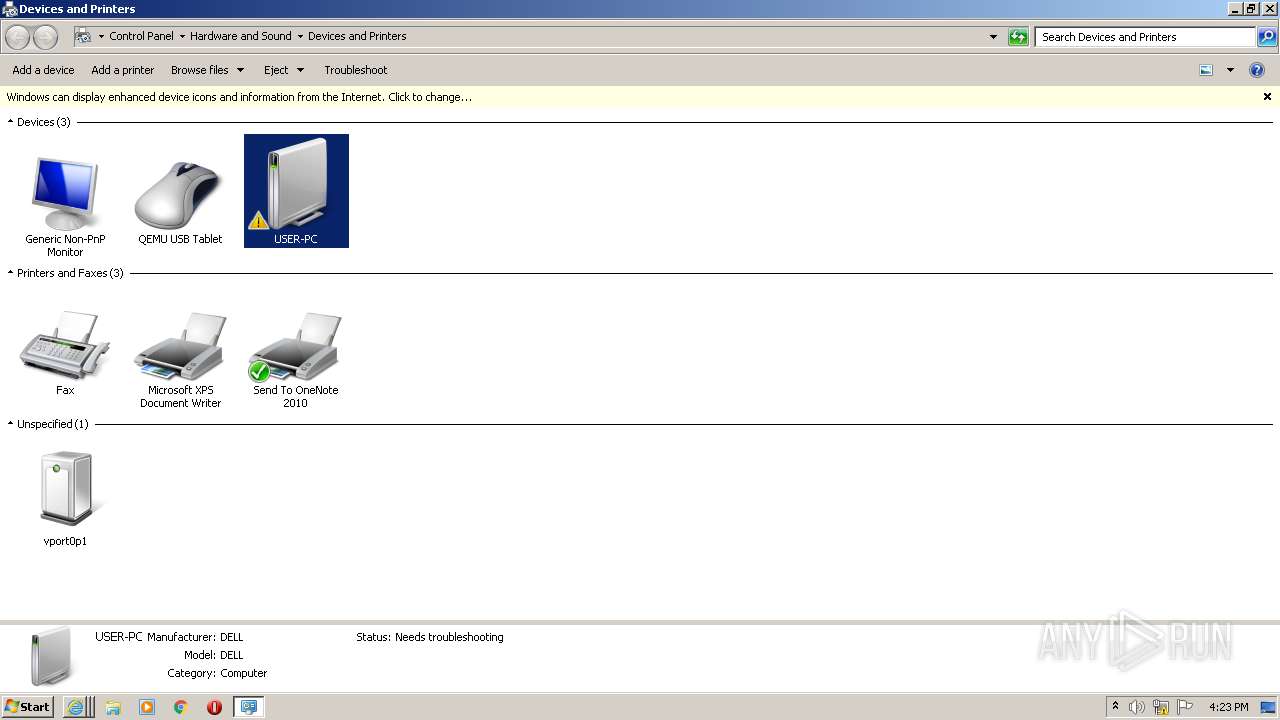
Manual execution by user
- mmc.exe (PID: 3508)
- mmc.exe (PID: 2612)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
51
Monitored processes
7
Malicious processes
0
Suspicious processes
1
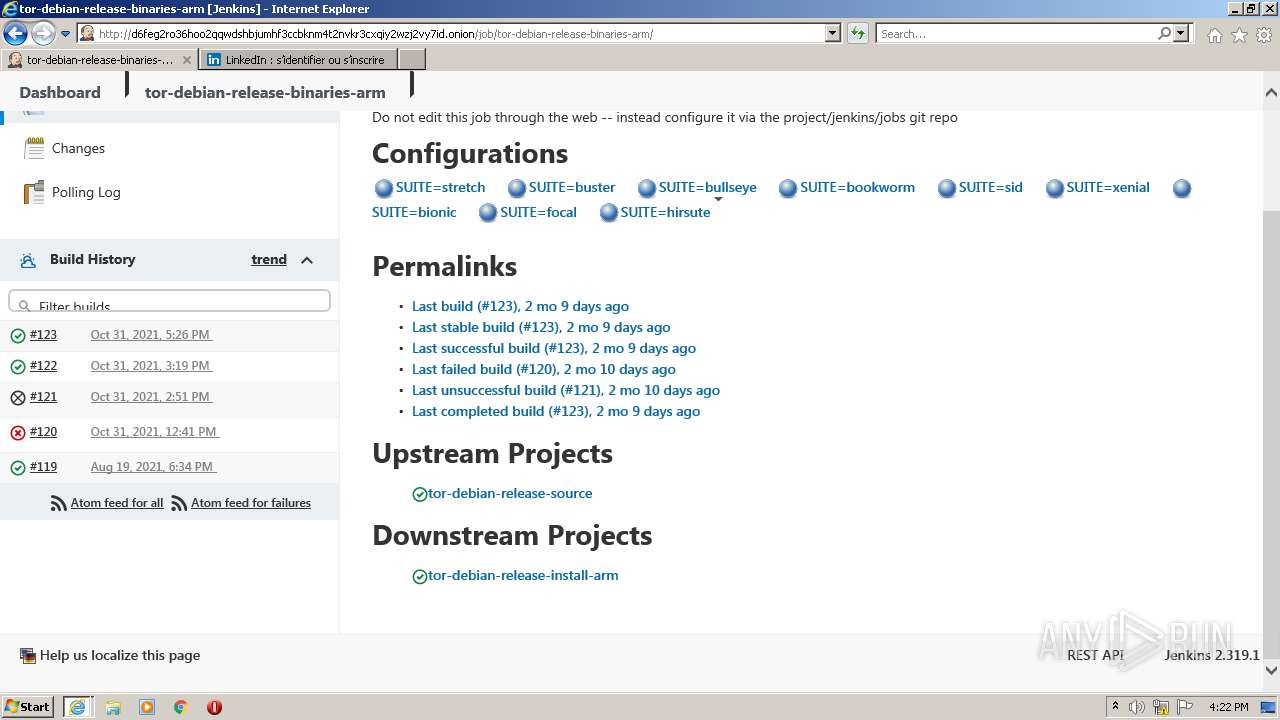
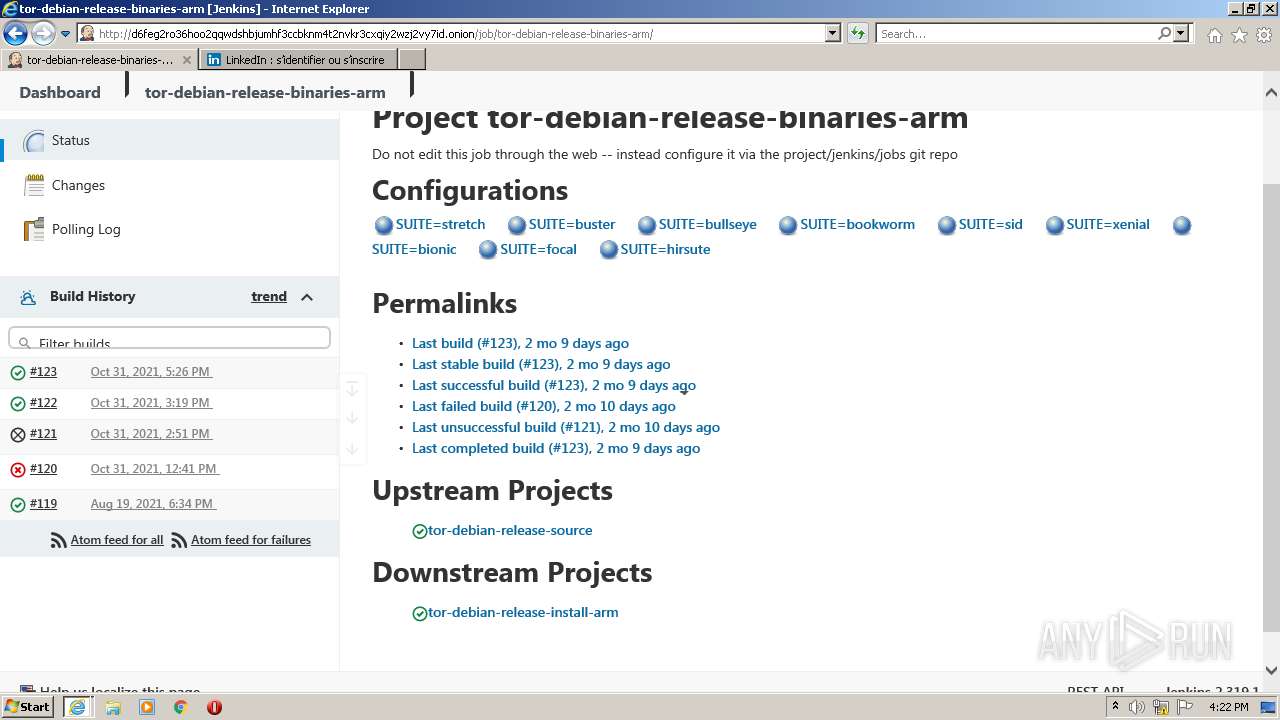
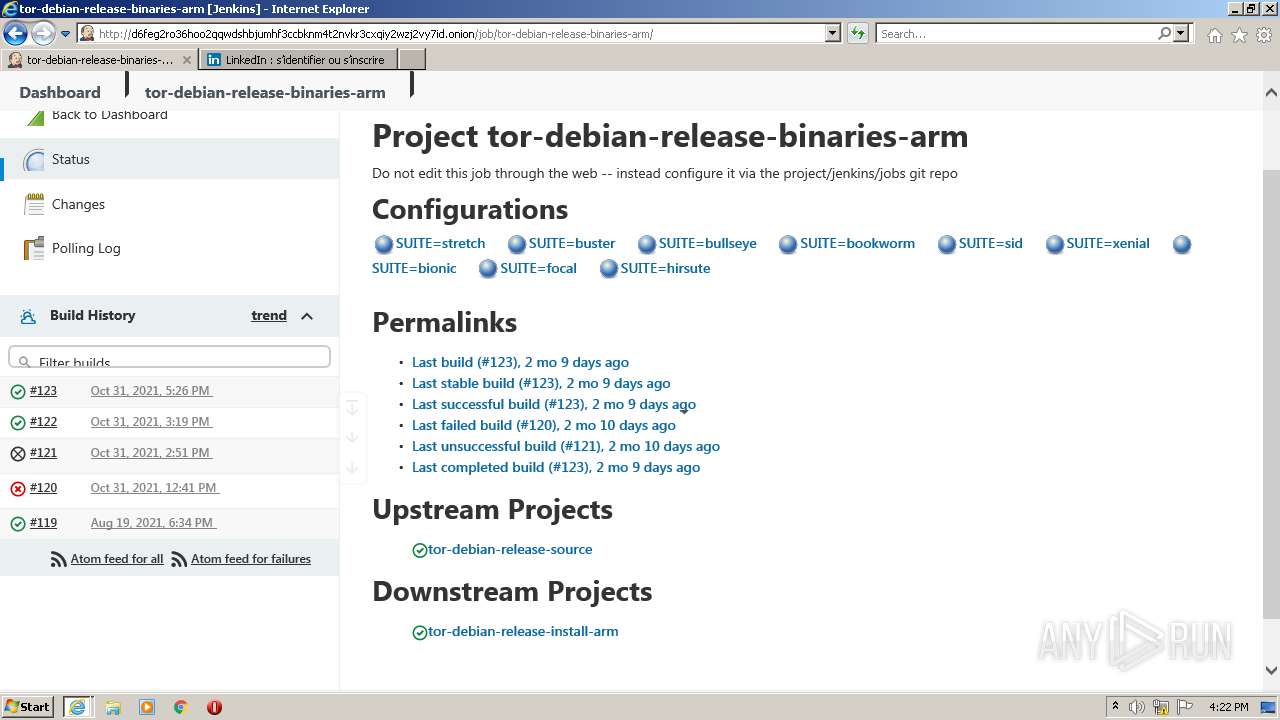
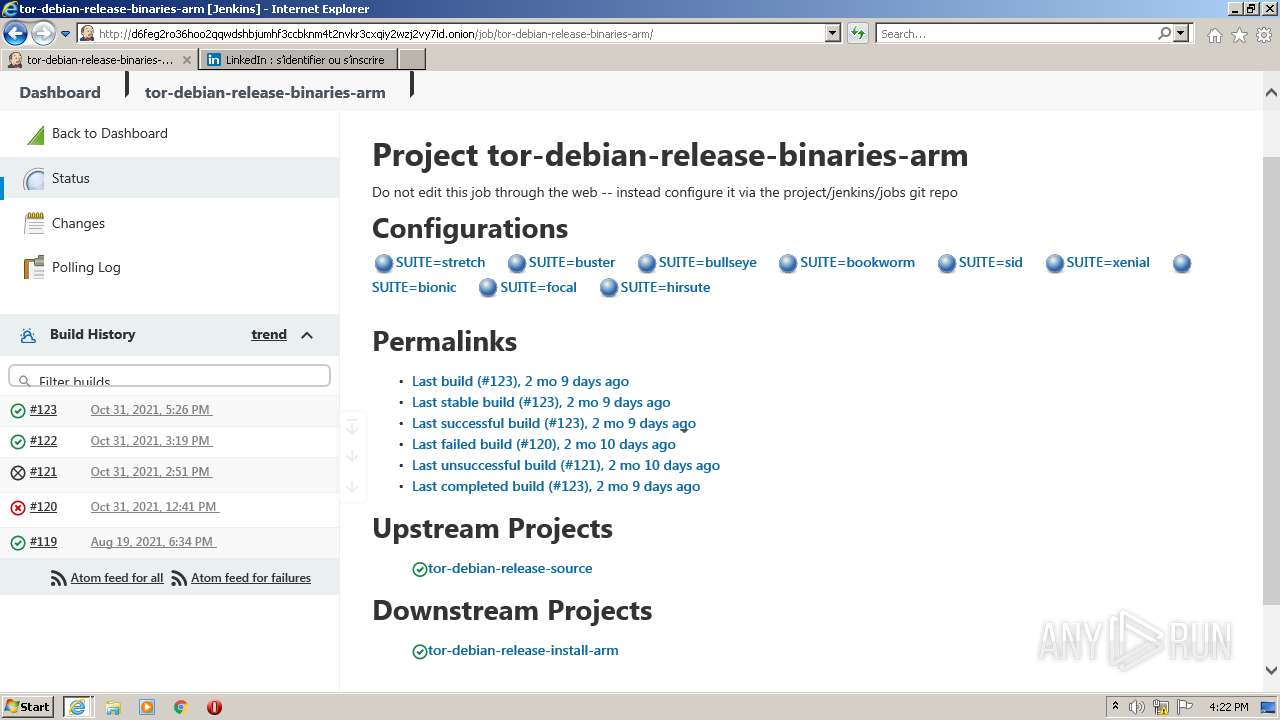
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
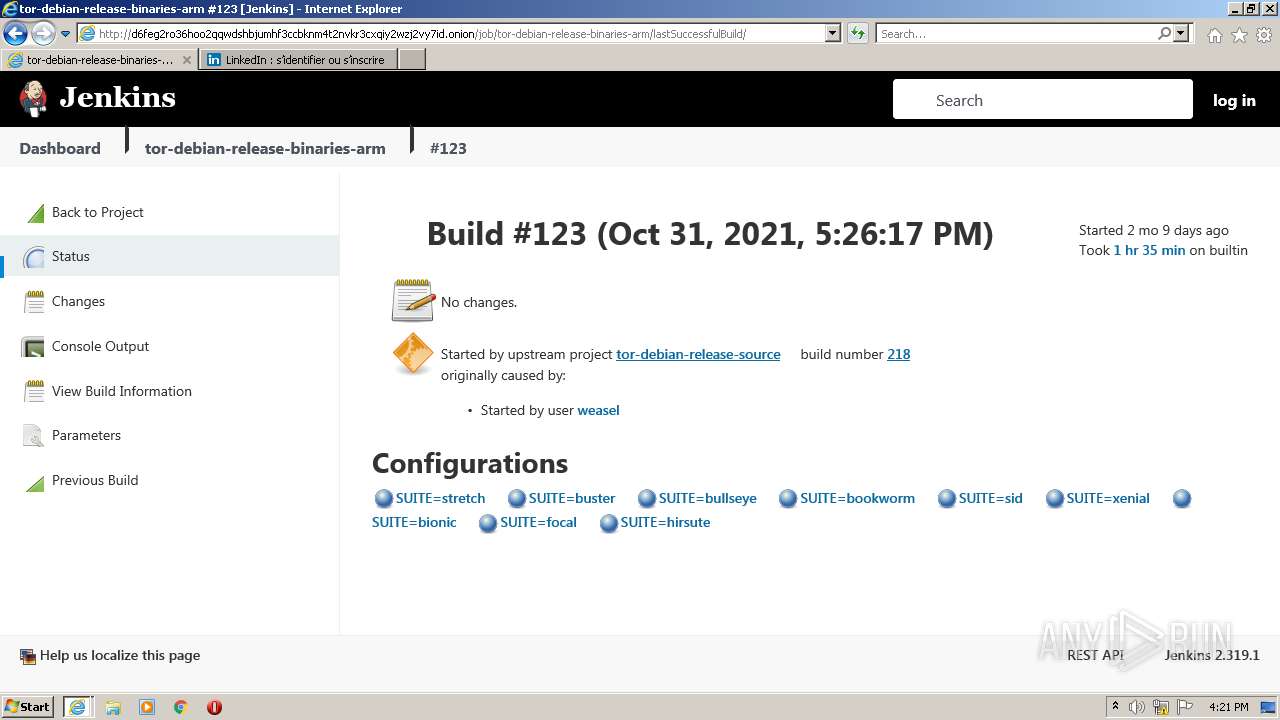
| 1376 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1540 CREDAT:1512766 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
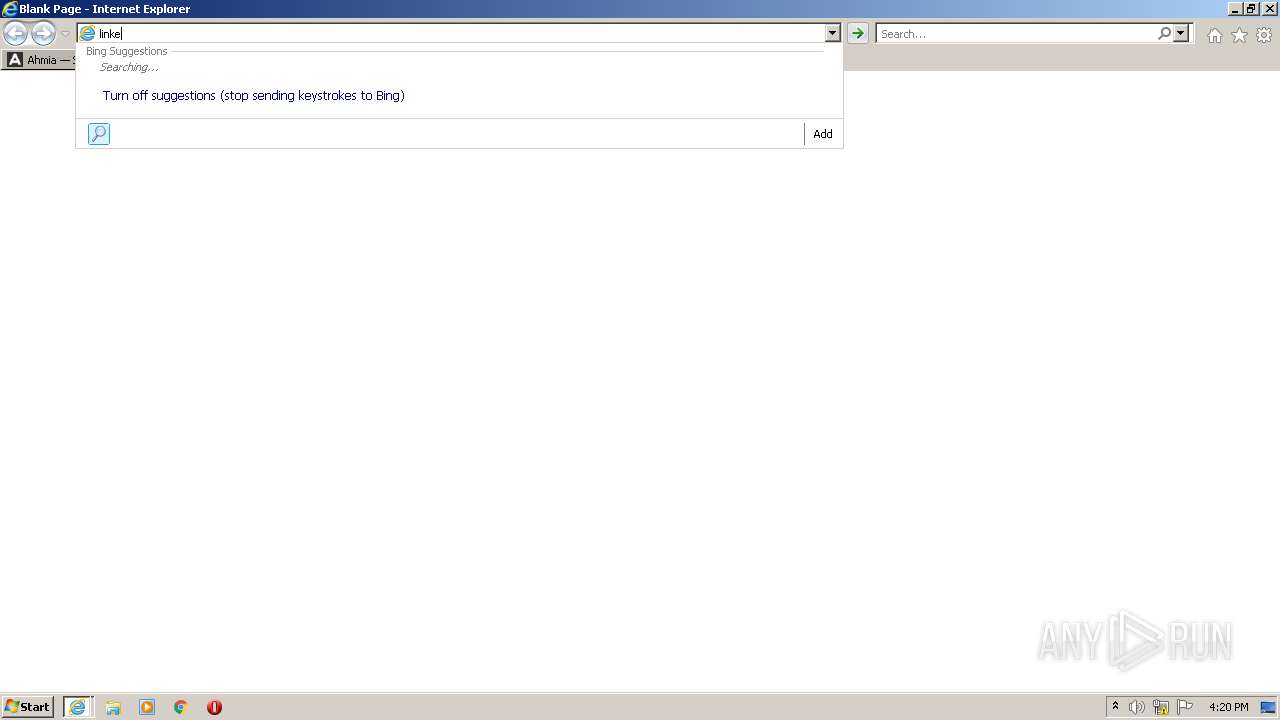
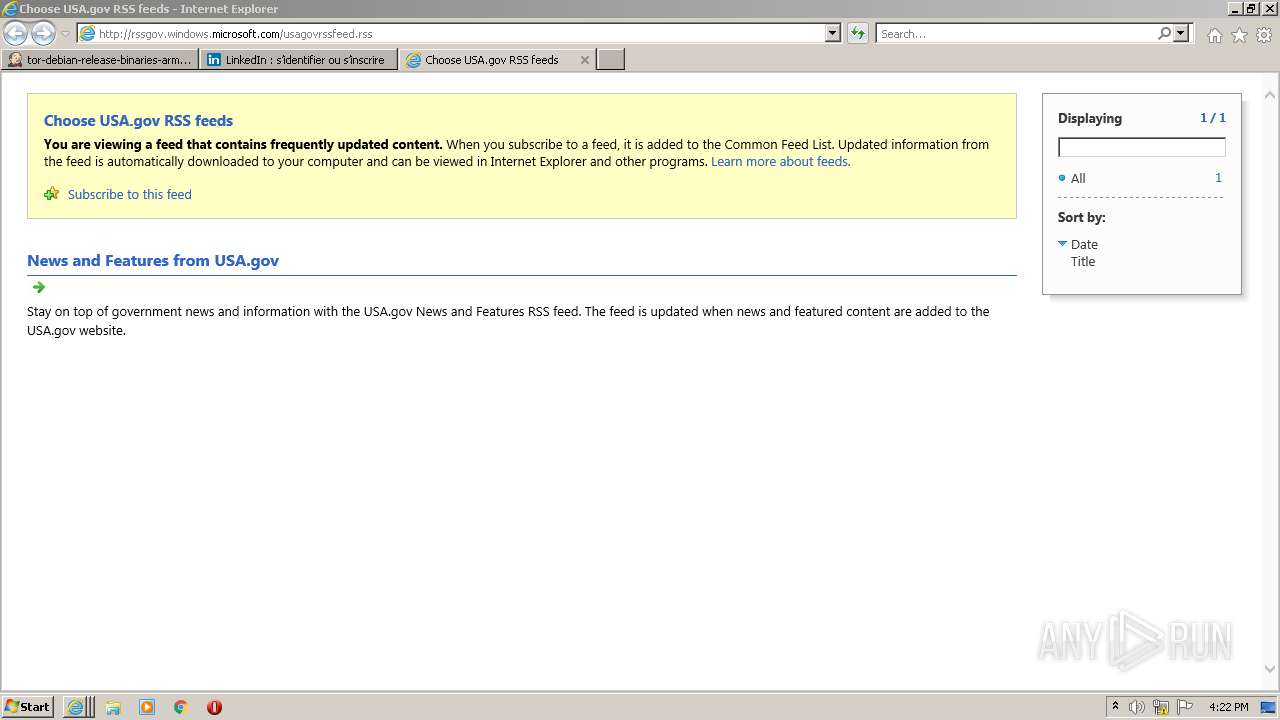
| 1540 | "C:\Program Files\Internet Explorer\iexplore.exe" "http://juhanurmihxlp77nkq76byazcldy2hlmovfu2epvl5ankdibsot4csyd.onion" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2612 | "C:\Windows\system32\mmc.exe" "C:\Windows\system32\services.msc" | C:\Windows\system32\mmc.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Management Console Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
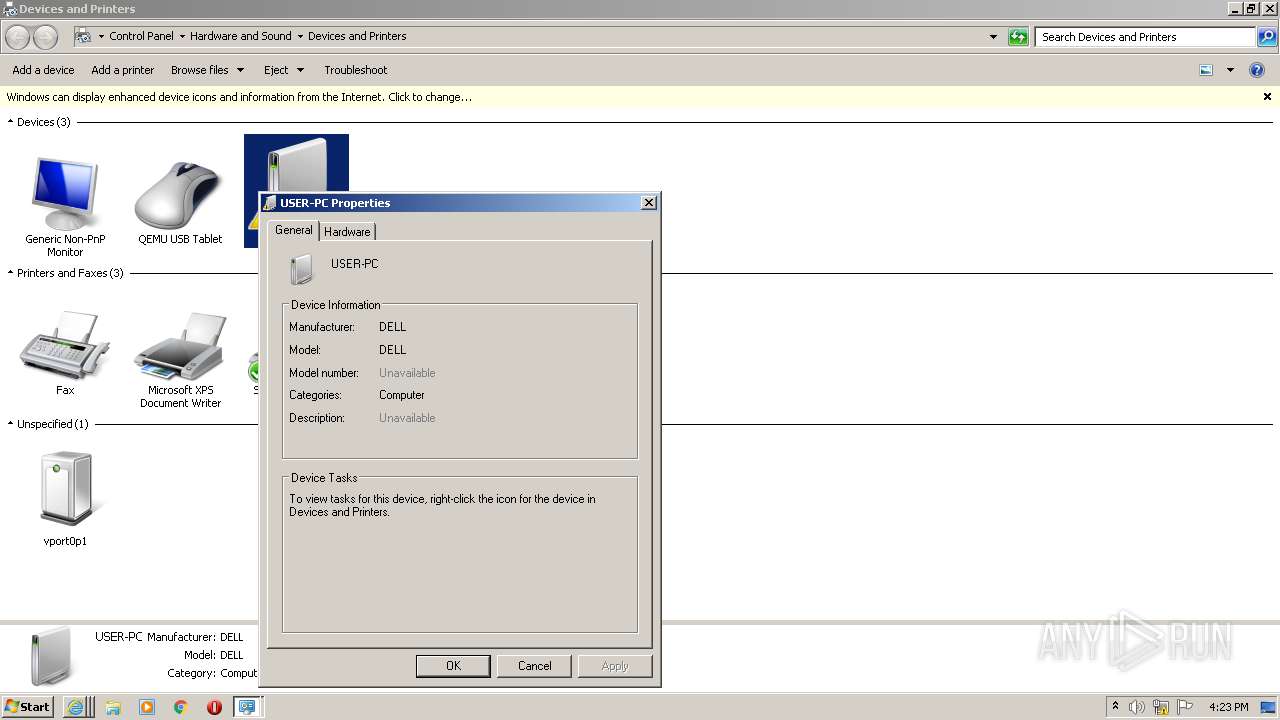
| 2784 | C:\Windows\system32\DeviceDisplayObjectProvider.exe -Embedding | C:\Windows\system32\DeviceDisplayObjectProvider.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Device Display Object Function Discovery Provider Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3508 | "C:\Windows\system32\mmc.exe" "C:\Windows\system32\services.msc" | C:\Windows\system32\mmc.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Management Console Exit code: 3221226540 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3520 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1540 CREDAT:2954505 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3632 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1540 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
23 189
Read events
22 860
Write events
326
Delete events
3
Modification events
| (PID) Process: | (1540) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (1540) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (1540) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30934388 | |||
| (PID) Process: | (1540) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (1540) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30934388 | |||
| (PID) Process: | (1540) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1540) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1540) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1540) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1540) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
18
Text files
183
Unknown types
13
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3632 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\KYV1IV0W.htm | html | |
MD5:7B4EB99A0AED035942FCFFEFECB7F809 | SHA256:773508C1B5FA60D0E5619A95E8E09442621A22753BCD467E63AE0C5BE72F8D8E | |||
| 3632 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\alfphabet-iv-webfont[1].eot | eot | |
MD5:639A180B8CAEA09048678F2FE2DC4F3E | SHA256:02B7F25EFCECBC1CE7FE87AAE6A040A7CBC993DBF4CD965C569DA95F73566C25 | |||
| 1540 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:B2F5EEF718A7EC115BAC05DED7AFBB4E | SHA256:6324F7EDCB1649B555FB75FD99627E4D26F5B1C589B95B91F5B61C5EE77D6563 | |||
| 1540 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\imagestore\f7ruq93\imagestore.dat | binary | |
MD5:666EE97FA94F268621E077C4703F8F51 | SHA256:1480270170E0CA1CE79F64365F0742DAA83AF1F354087627835F8F0EDB4CC7AC | |||
| 3632 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\less.min[1].js | html | |
MD5:27940A5D1564005C48146DC2B762CFC7 | SHA256:8705C88622B603EE8BEC638EB01A685915C99133F4849D61BFE17435CDAF0131 | |||
| 3632 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\jquery.scrollTo[1].js | text | |
MD5:FD33D053AF9DA859280CA0C74FA1A443 | SHA256:217861F56370722232DB7868661783023F2902BFA74BDD5B6C9C051B5D40B3F0 | |||
| 3632 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\Roboto-Light-webfont[1].eot | eot | |
MD5:A990F611F2305DC12965F186C2EF2690 | SHA256:2517B97E2C0E1E6C8CEB9DD007015F897926BC504154137281EEC4C1A9F9BDC9 | |||
| 3632 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\metro[1].jpg | image | |
MD5:E10DFC961D82CE542284A5FD25CAF18C | SHA256:02A499688CAA0F2C370EB2D93F3F3981DC7A566C317D19CBC62FFF7D4C0E3243 | |||
| 3632 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\modernizr[1].js | html | |
MD5:CEA343AED760A85CE611690112C842A1 | SHA256:AB292789C477798AE95E7241F91535B9789122661A094F3C0DCFD3730185C055 | |||
| 3632 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\ahmiafi_black[1].png | image | |
MD5:2A1C794F94BF6CF5DFCEFA9C88112720 | SHA256:6F9B37349901077033DE3771EF79CA20BFF4AFB48D0218DD3AD1DCAF8FF00B37 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
91
TCP/UDP connections
89
DNS requests
32
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
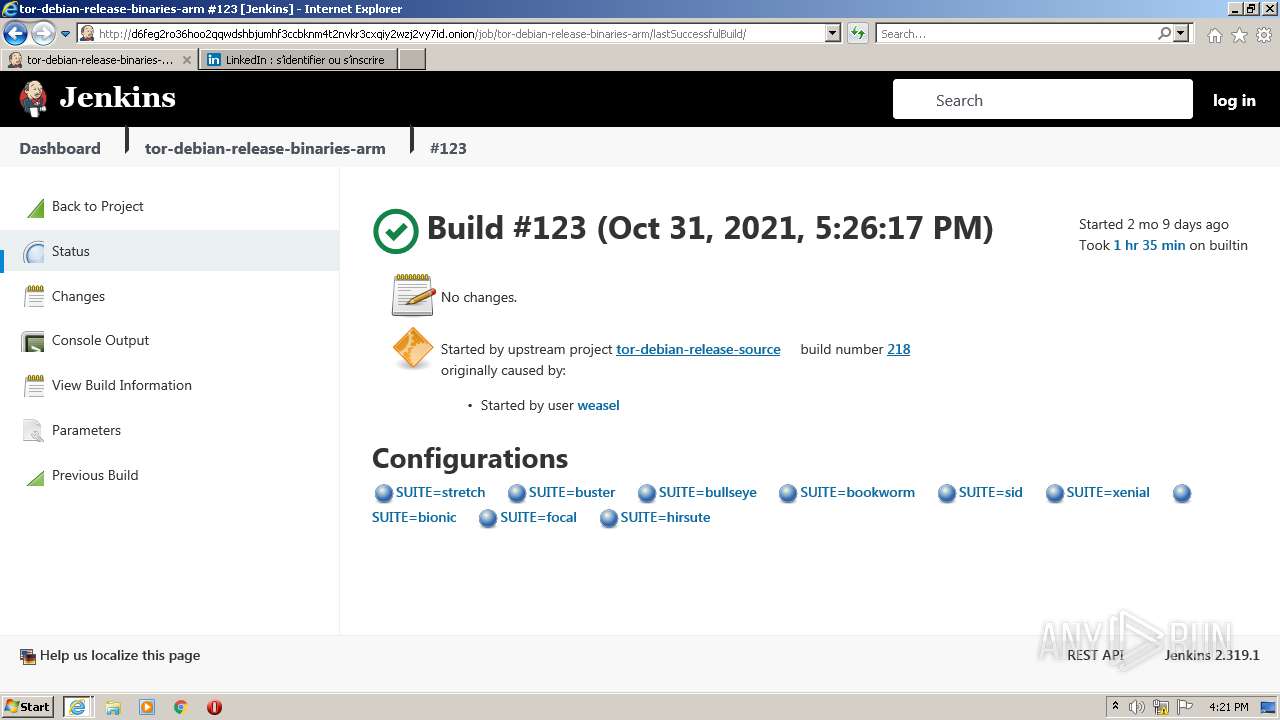
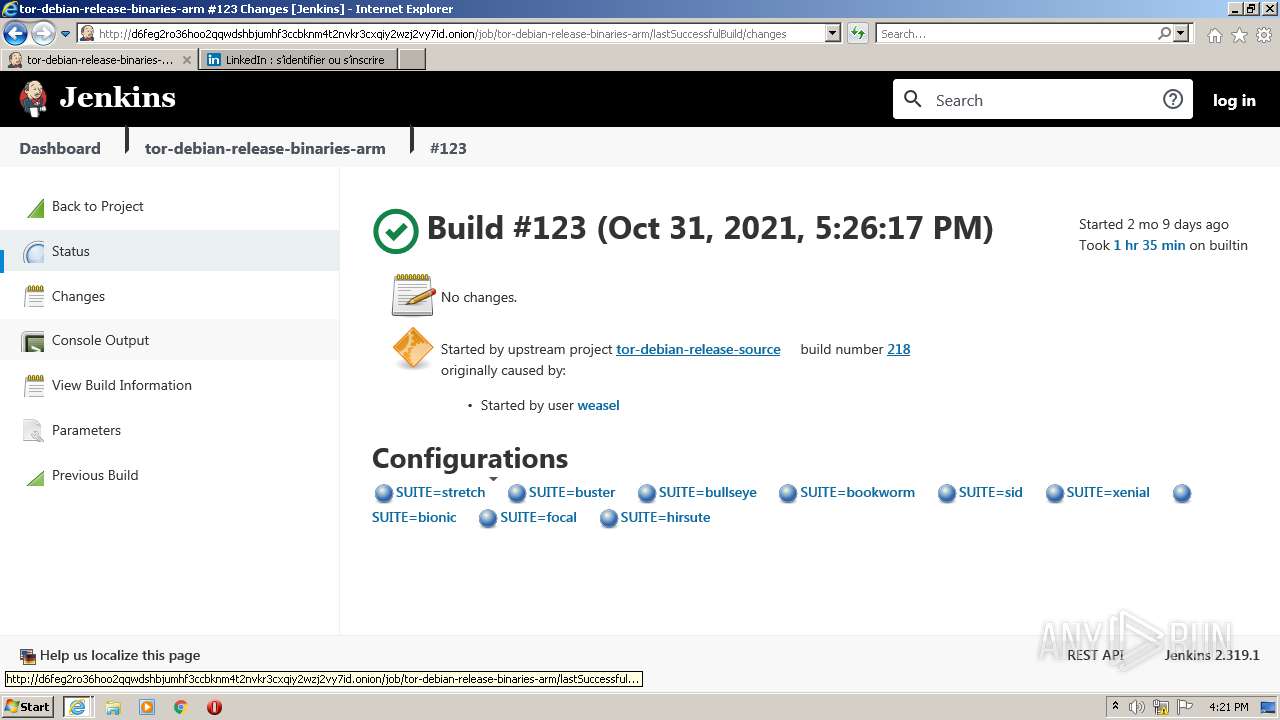
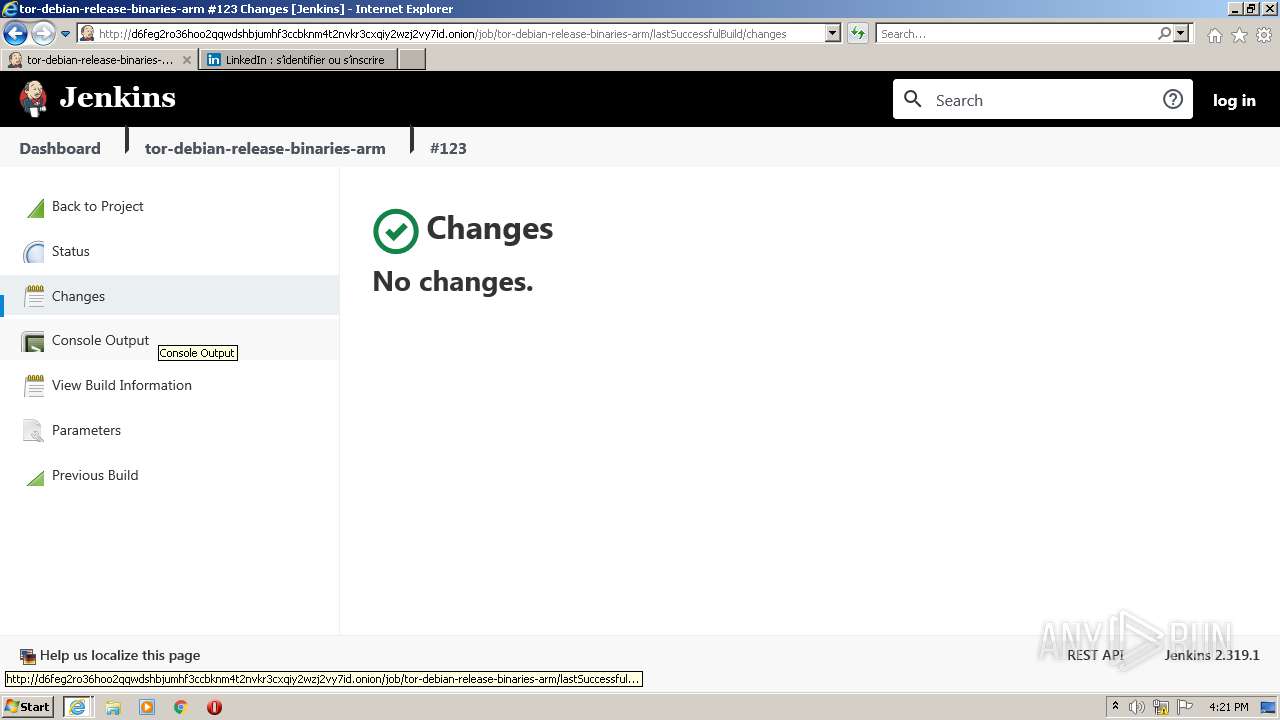
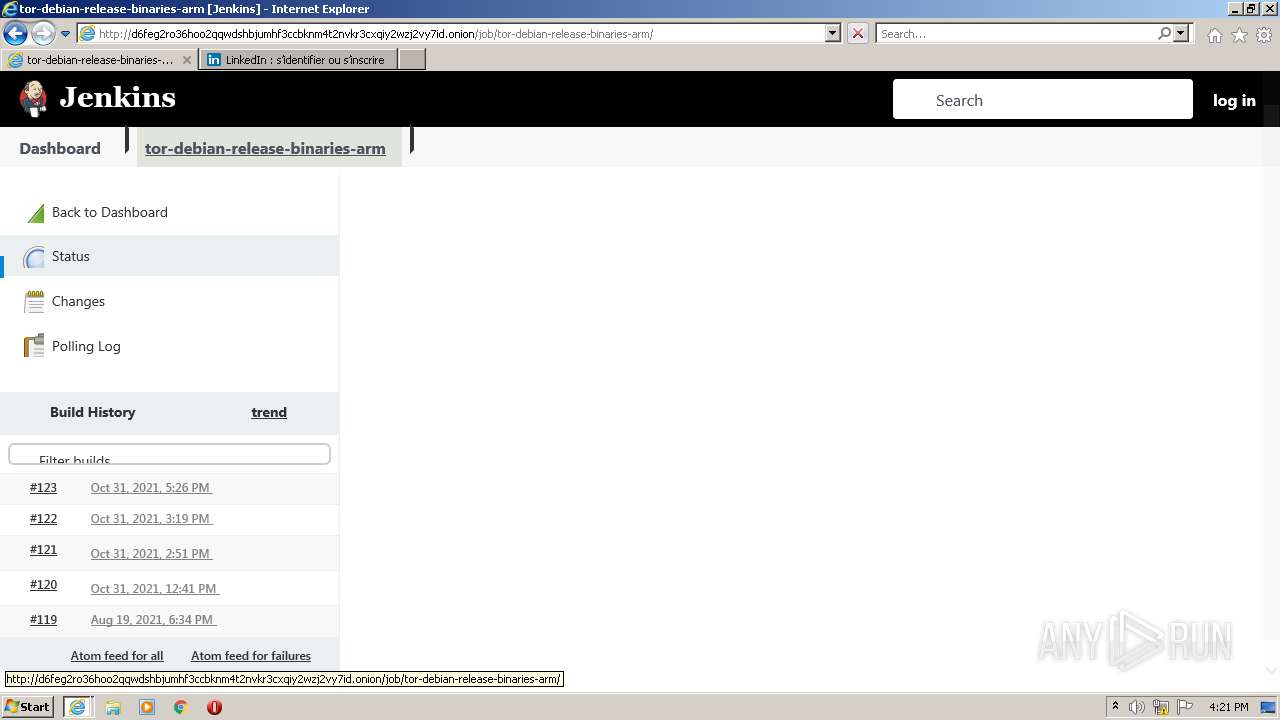
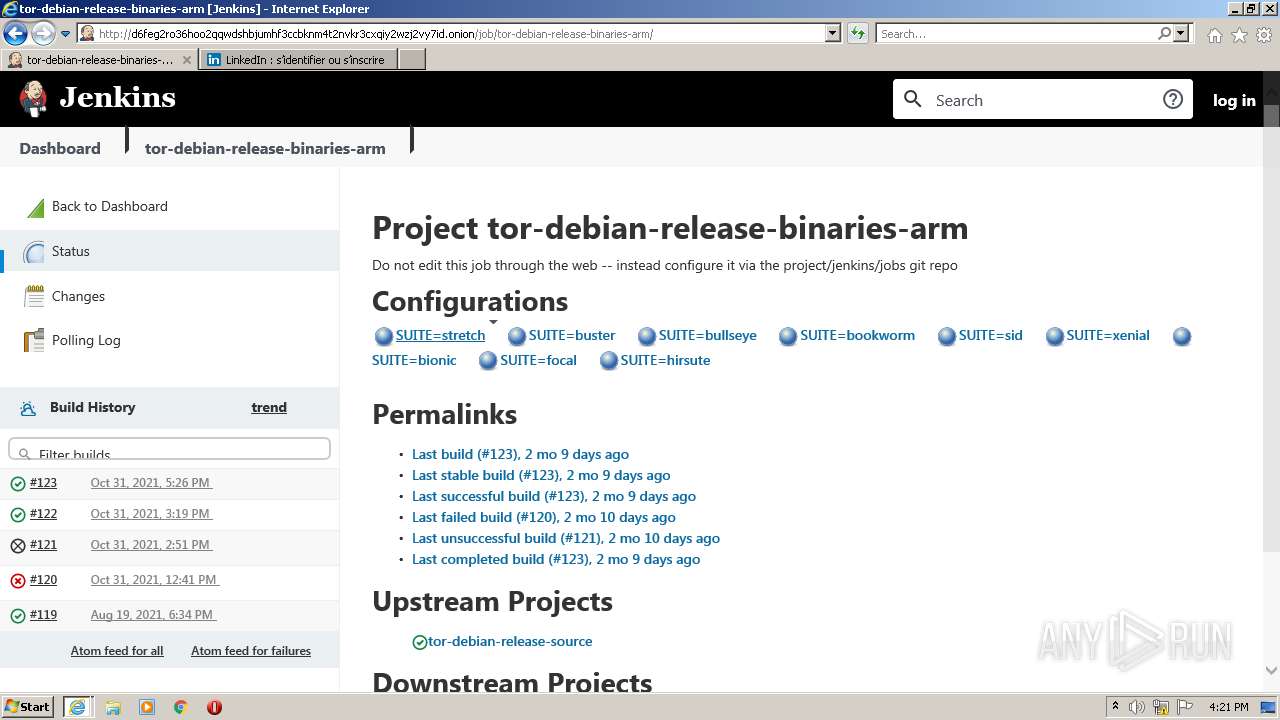
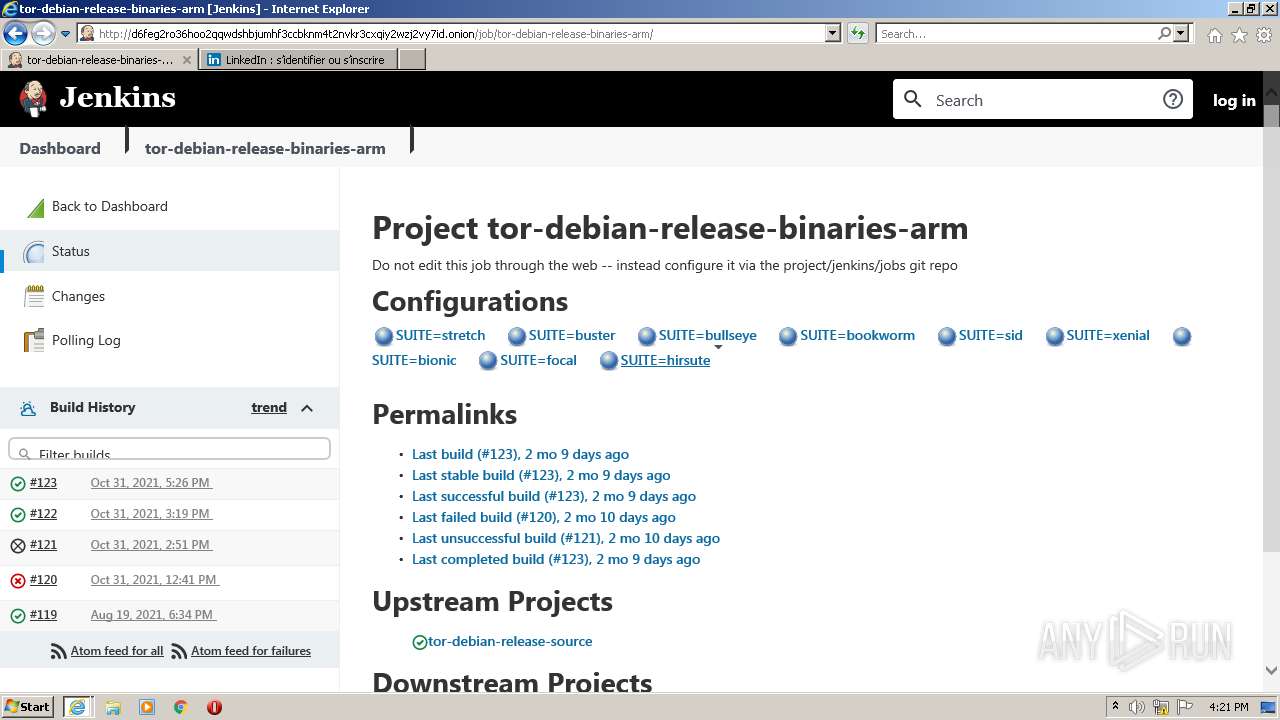
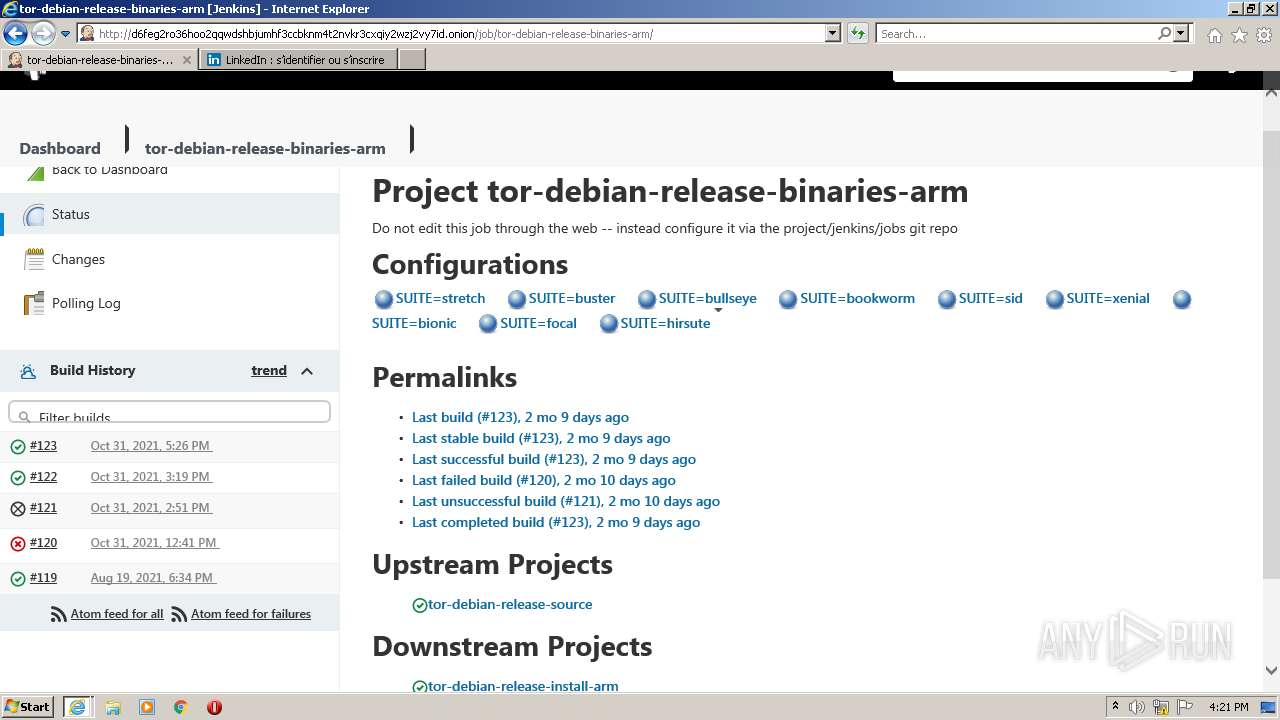
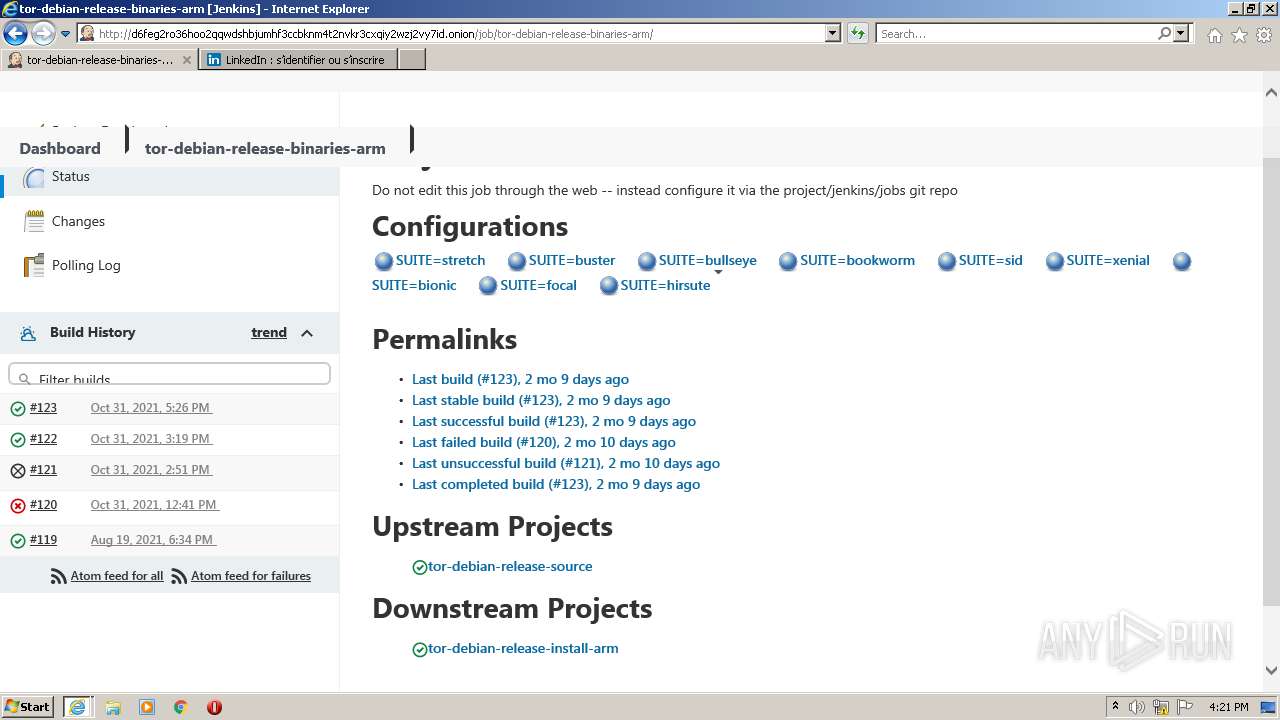
3632 | iexplore.exe | GET | 200 | 10.223.45.99:80 | http://juhanurmihxlp77nkq76byazcldy2hlmovfu2epvl5ankdibsot4csyd.onion/ | unknown | html | 2.15 Kb | unknown |
3632 | iexplore.exe | GET | 200 | 10.223.45.99:80 | http://juhanurmihxlp77nkq76byazcldy2hlmovfu2epvl5ankdibsot4csyd.onion/static/css/normalize.css | unknown | text | 2.91 Kb | unknown |
3632 | iexplore.exe | GET | 200 | 10.223.45.99:80 | http://juhanurmihxlp77nkq76byazcldy2hlmovfu2epvl5ankdibsot4csyd.onion/static/js/jquery.min.js | unknown | text | 84.0 Kb | unknown |
3632 | iexplore.exe | GET | 200 | 10.223.45.99:80 | http://juhanurmihxlp77nkq76byazcldy2hlmovfu2epvl5ankdibsot4csyd.onion/static/less/style.css | unknown | text | 4.23 Kb | unknown |
3632 | iexplore.exe | GET | 200 | 10.223.45.99:80 | http://juhanurmihxlp77nkq76byazcldy2hlmovfu2epvl5ankdibsot4csyd.onion/static/js/jquery.scrollTo.js | unknown | text | 5.59 Kb | unknown |
3632 | iexplore.exe | GET | 200 | 10.223.45.99:80 | http://juhanurmihxlp77nkq76byazcldy2hlmovfu2epvl5ankdibsot4csyd.onion/static/js/sha256.js | unknown | text | 8.11 Kb | unknown |
3632 | iexplore.exe | GET | 200 | 10.223.45.99:80 | http://juhanurmihxlp77nkq76byazcldy2hlmovfu2epvl5ankdibsot4csyd.onion/static/fonts/roboto/roboto_regular_macroman/Roboto-Regular-webfont.eot? | unknown | eot | 20.8 Kb | unknown |
3632 | iexplore.exe | GET | 200 | 10.223.45.99:80 | http://juhanurmihxlp77nkq76byazcldy2hlmovfu2epvl5ankdibsot4csyd.onion/static/fonts/alfphabet/alfphabet-iv-webfont.eot? | unknown | eot | 12.0 Kb | unknown |
1540 | iexplore.exe | GET | 200 | 10.223.45.99:80 | http://juhanurmihxlp77nkq76byazcldy2hlmovfu2epvl5ankdibsot4csyd.onion/static/images/favicon.ico | unknown | image | 1.12 Kb | unknown |
1540 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3632 | iexplore.exe | 10.223.45.99:80 | juhanurmihxlp77nkq76byazcldy2hlmovfu2epvl5ankdibsot4csyd.onion | — | — | unknown |
1540 | iexplore.exe | 10.223.45.99:80 | juhanurmihxlp77nkq76byazcldy2hlmovfu2epvl5ankdibsot4csyd.onion | — | — | unknown |
1540 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
1540 | iexplore.exe | 104.110.191.133:80 | ctldl.windowsupdate.com | Akamai Technologies, Inc. | US | unknown |
1540 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1540 | iexplore.exe | 23.2.175.10:443 | go.microsoft.com | Akamai International B.V. | US | malicious |
1540 | iexplore.exe | 204.79.197.203:443 | www.msn.com | Microsoft Corporation | US | malicious |
1540 | iexplore.exe | 13.92.246.37:443 | query.prod.cms.msn.com | Microsoft Corporation | US | whitelisted |
3632 | iexplore.exe | 13.107.13.80:443 | api.bing.com | Microsoft Corporation | US | whitelisted |
3520 | iexplore.exe | 20.190.160.73:443 | login.microsoftonline.com | Microsoft Corporation | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
juhanurmihxlp77nkq76byazcldy2hlmovfu2epvl5ankdibsot4csyd.onion |
| unknown |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
ieonline.microsoft.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
www.msn.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potential Corporate Privacy Violation | ET POLICY DNS Query for TOR Hidden Domain .onion Accessible Via TOR |
— | — | Potential Corporate Privacy Violation | AV POLICY DNS Query for .onion Domain Via TOR - Not Google |
— | — | Potential Corporate Privacy Violation | ET POLICY DNS Query for TOR Hidden Domain .onion Accessible Via TOR |
— | — | Potential Corporate Privacy Violation | AV POLICY DNS Query for .onion Domain Via TOR - Not Google |