| File name: | TC_Medecine.exe |
| Full analysis: | https://app.any.run/tasks/93f9019e-ef54-4ed8-ba3b-c44e05969e19 |
| Verdict: | Malicious activity |
| Analysis date: | February 12, 2024, 12:30:30 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 8F522A22433CAED27287716C94FFDCFC |
| SHA1: | A16518AEDEE4F8509011A64557FCE58F741B141D |
| SHA256: | 02C3F176B04A511BA0F125513A23D236B8FFFE3E53A3EAA5BD2A8F06D122BB4B |
| SSDEEP: | 196608:TQ8EVktc+tbRhYsM9DHTn7LPbazBuYlRQZ/Yy03/KujOO7eun:k8Cec+hws0Tn7TmzBuYHQxS/Knun |
MALICIOUS
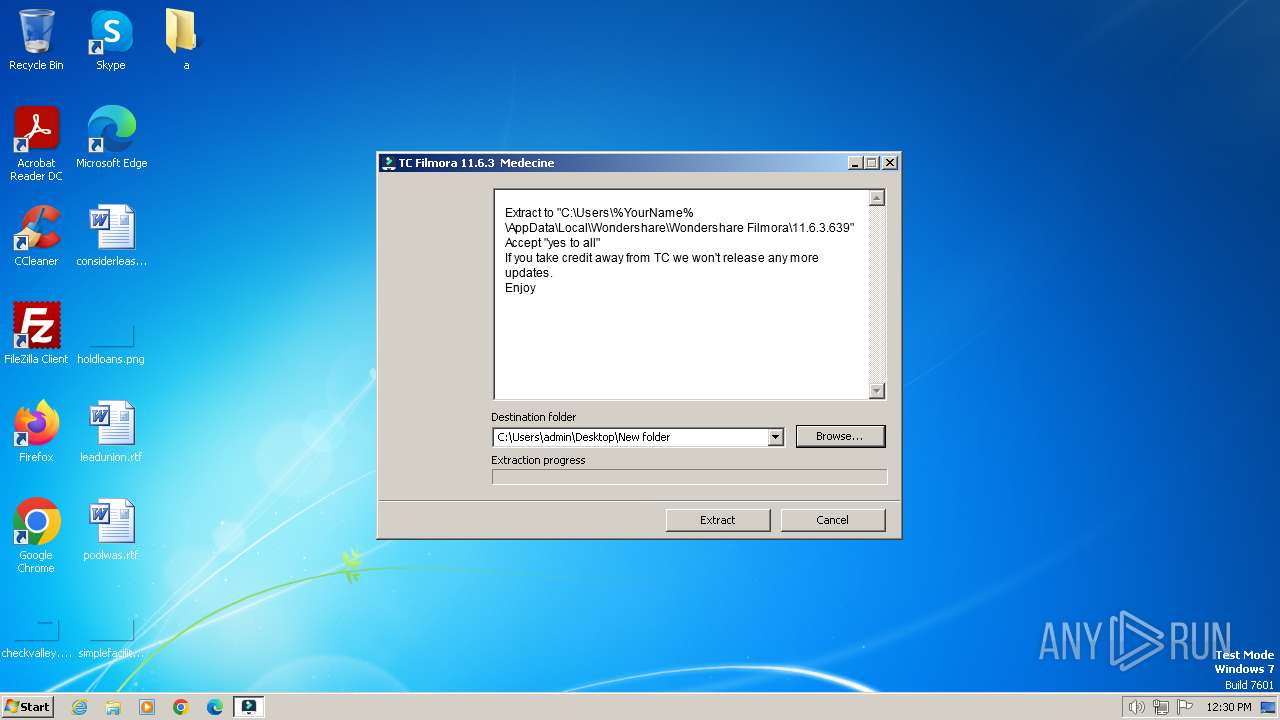
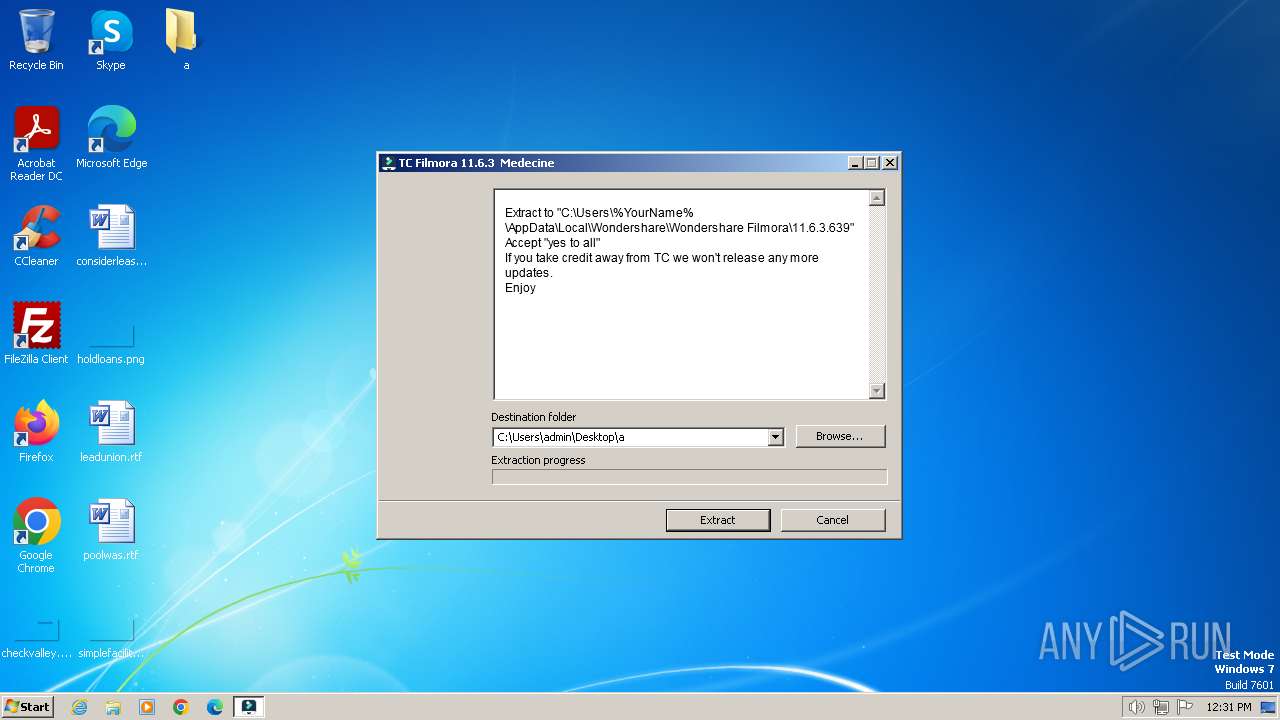
Drops the executable file immediately after the start
- TC_Medecine.exe (PID: 3864)
SUSPICIOUS
Reads security settings of Internet Explorer
- TC_Medecine.exe (PID: 3864)
Reads the Internet Settings
- TC_Medecine.exe (PID: 3864)
Reads Microsoft Outlook installation path
- TC_Medecine.exe (PID: 3864)
Reads Internet Explorer settings
- TC_Medecine.exe (PID: 3864)
Executable content was dropped or overwritten
- TC_Medecine.exe (PID: 3864)
INFO
Checks supported languages
- TC_Medecine.exe (PID: 3864)
- wmpnscfg.exe (PID: 3936)
Reads the computer name
- TC_Medecine.exe (PID: 3864)
- wmpnscfg.exe (PID: 3936)
Checks proxy server information
- TC_Medecine.exe (PID: 3864)
Reads the machine GUID from the registry
- TC_Medecine.exe (PID: 3864)
Manual execution by a user
- wmpnscfg.exe (PID: 3936)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2022:03:03 13:15:57+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.3 |
| CodeSize: | 203776 |
| InitializedDataSize: | 262144 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1f530 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Total processes
39
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3864 | "C:\Users\admin\AppData\Local\Temp\TC_Medecine.exe" | C:\Users\admin\AppData\Local\Temp\TC_Medecine.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3936 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
4 807
Read events
4 773
Write events
32
Delete events
2
Modification events
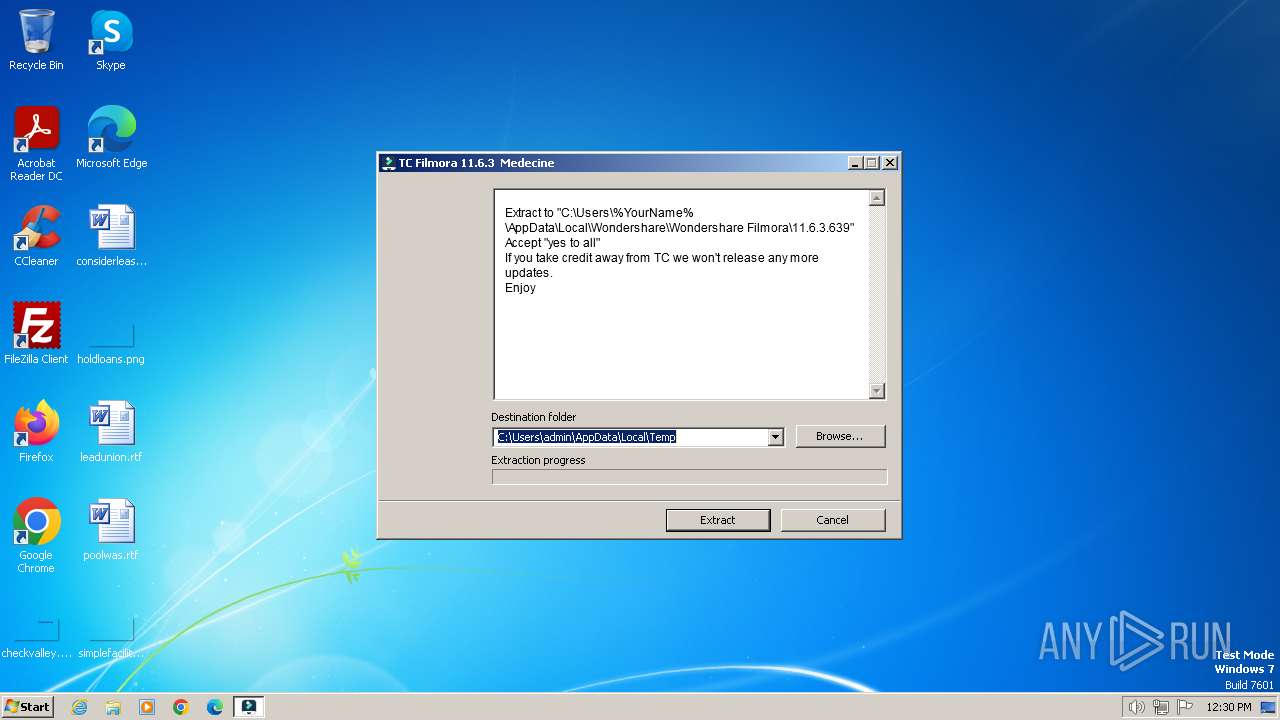
| (PID) Process: | (3864) TC_Medecine.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3864) TC_Medecine.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3864) TC_Medecine.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3864) TC_Medecine.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3864) TC_Medecine.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3864) TC_Medecine.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3864) TC_Medecine.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3864) TC_Medecine.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3864) TC_Medecine.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\NetworkExplorer.dll,-2 |
Value: Access the computers and devices that are on your network. | |||
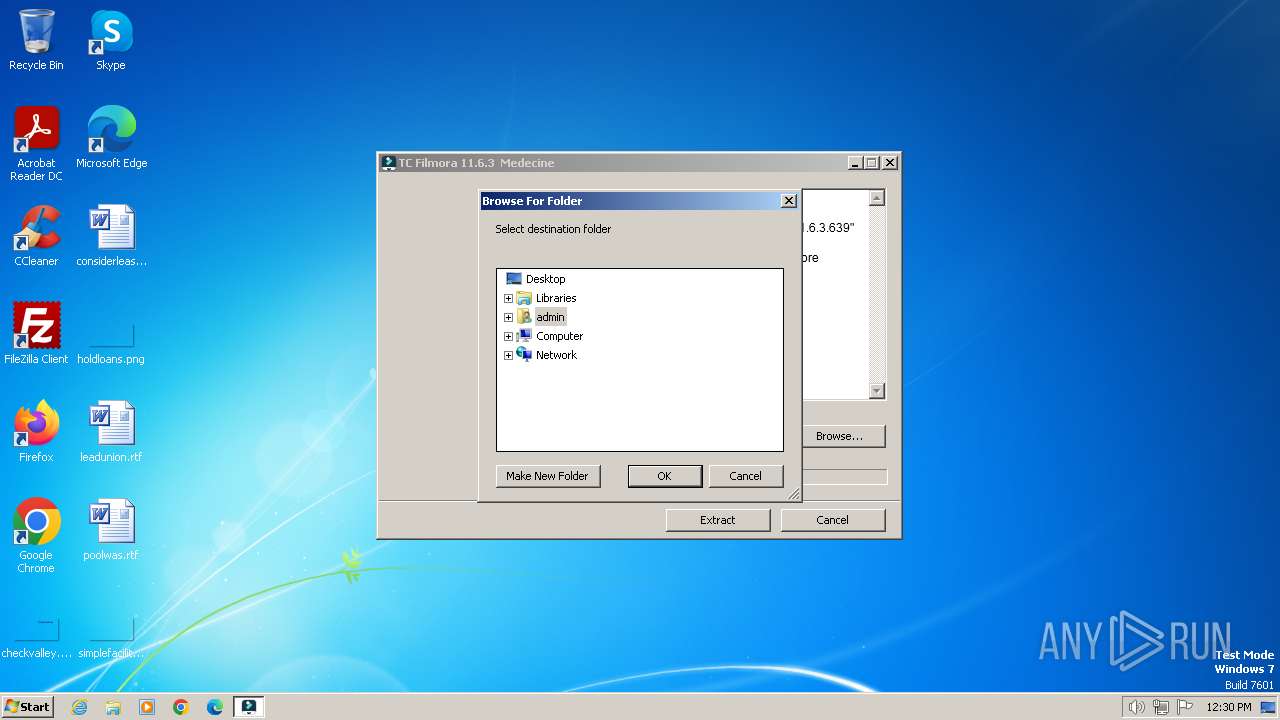
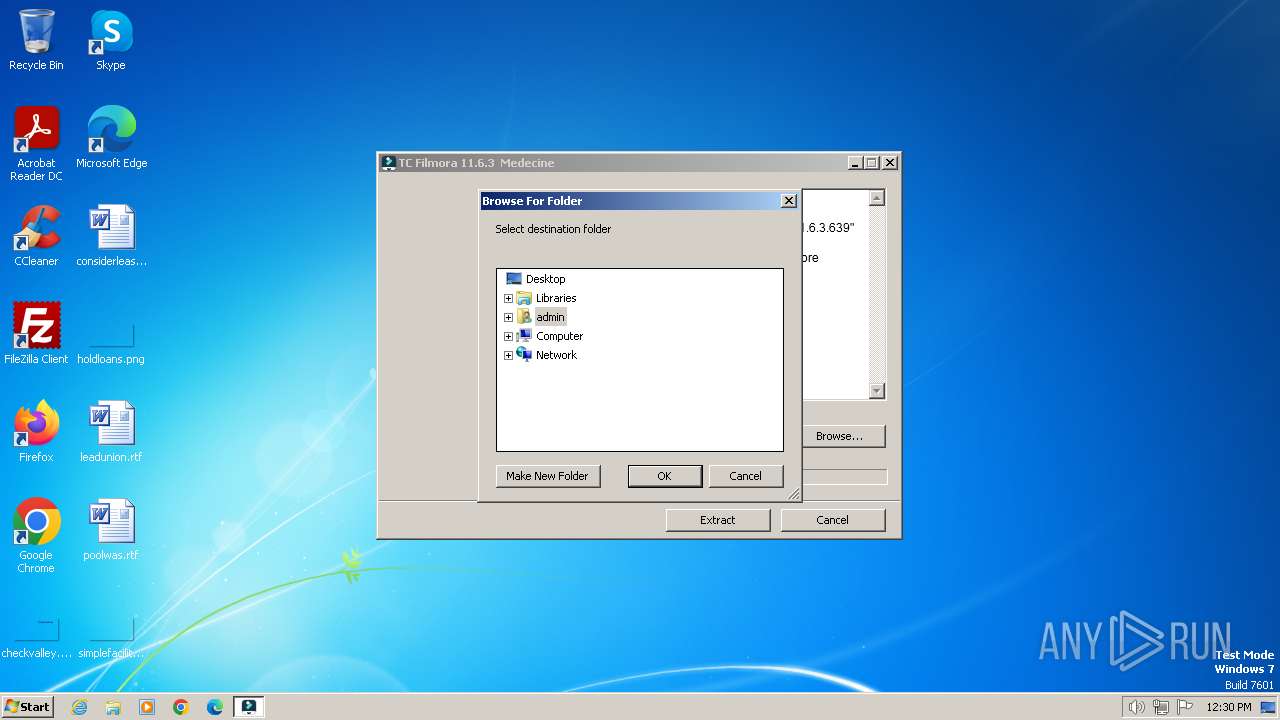
| (PID) Process: | (3864) TC_Medecine.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer |
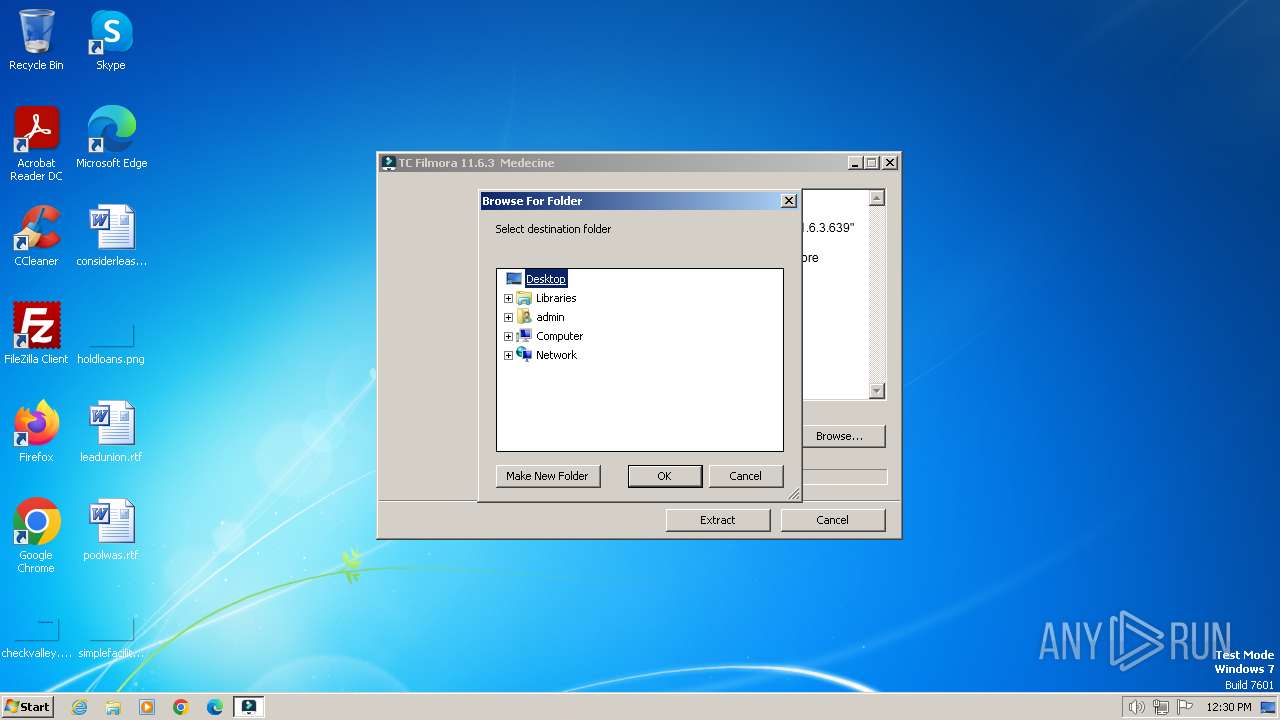
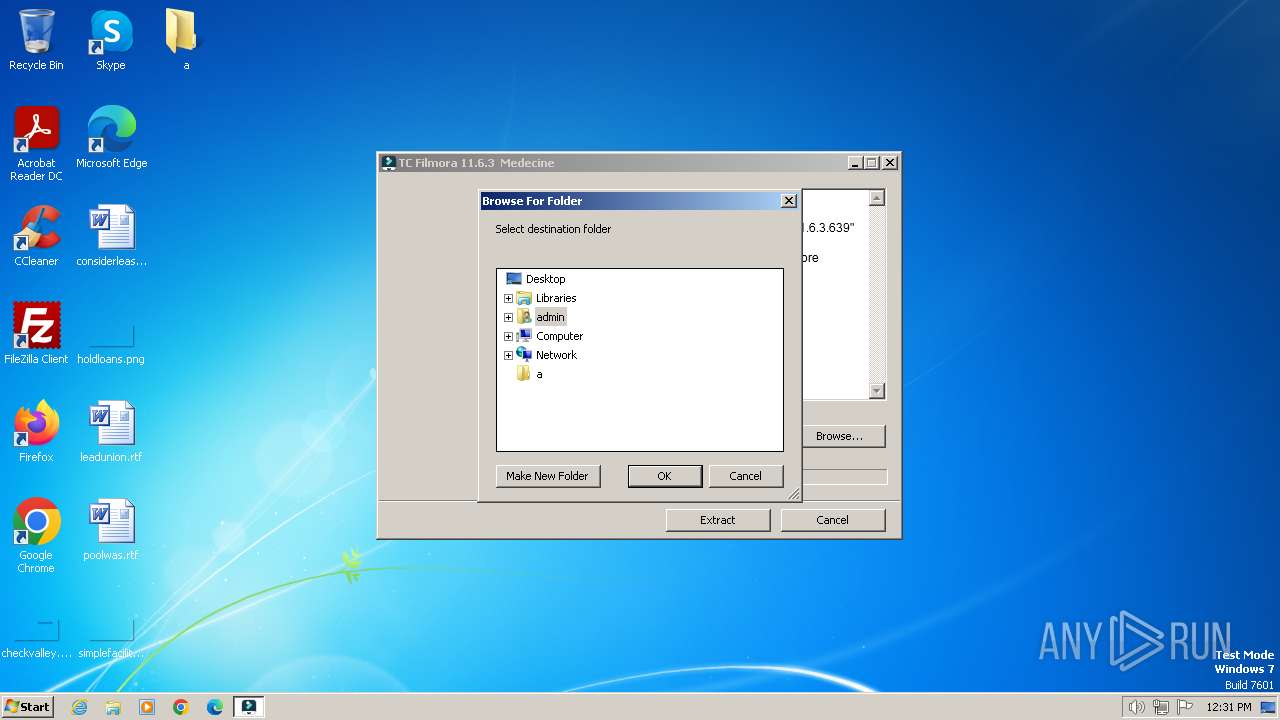
| Operation: | write | Name: | Browse For Folder Width |
Value: 318 | |||
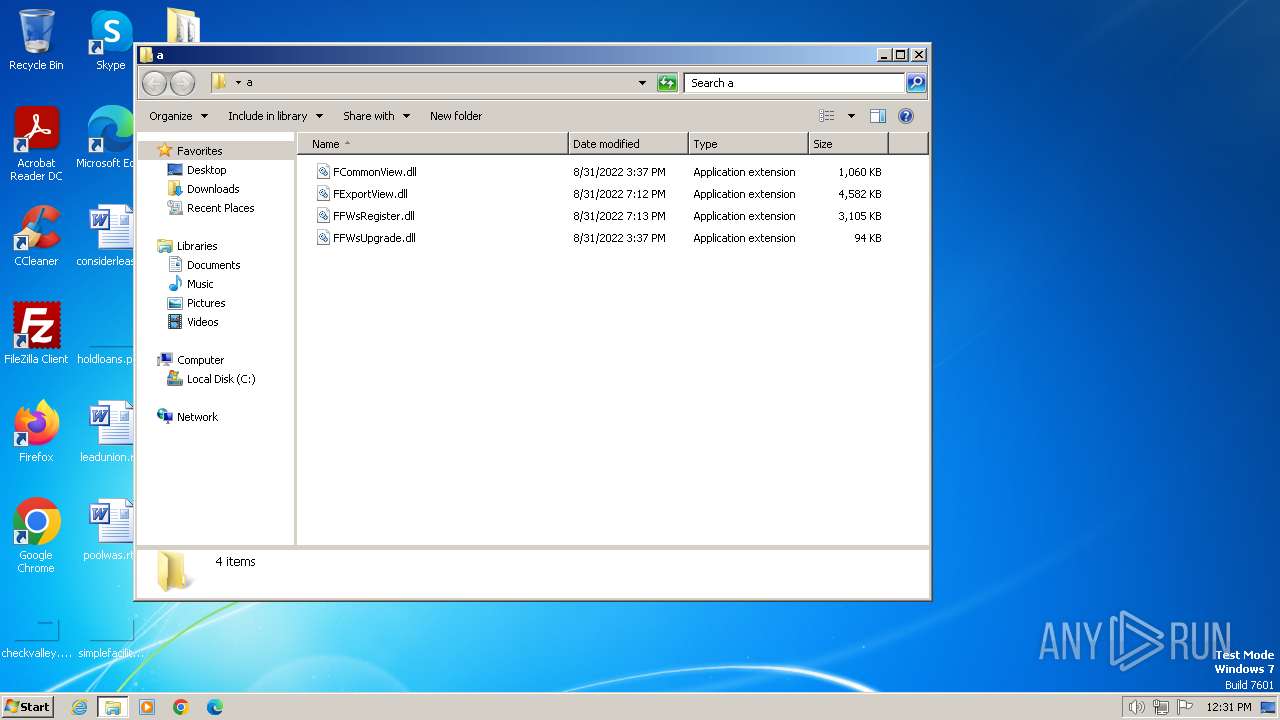
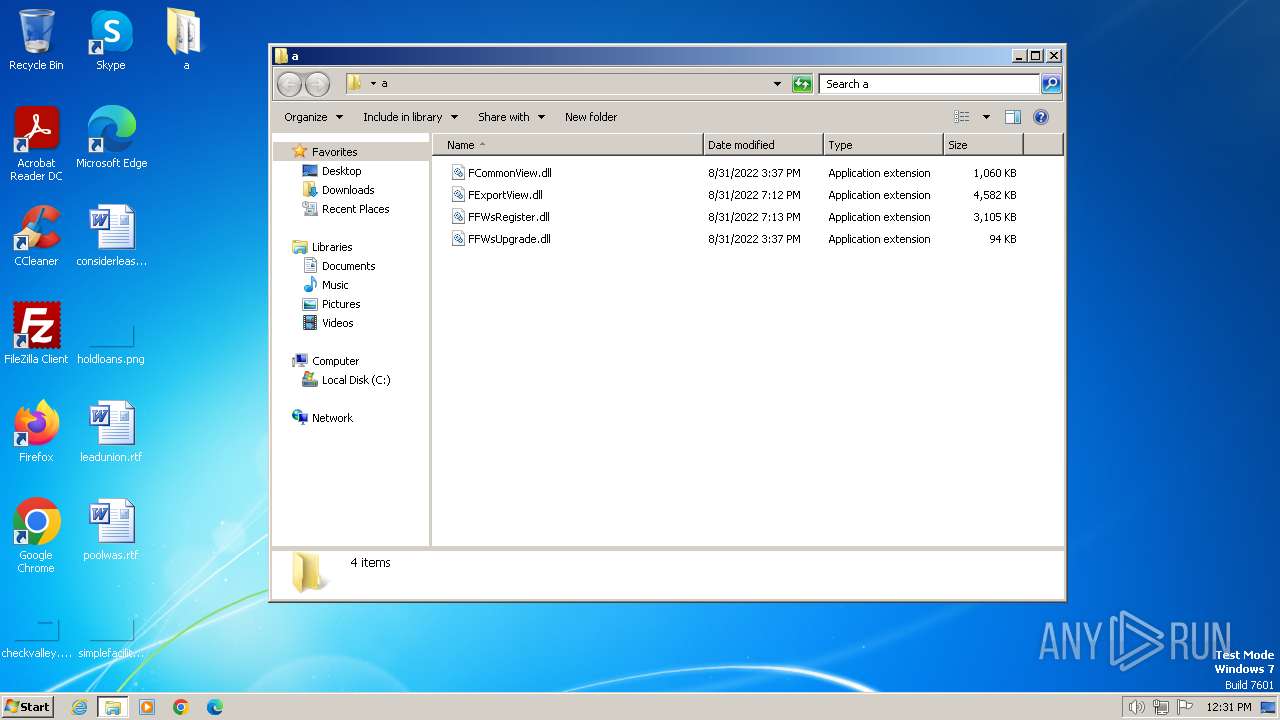
Executable files
4
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
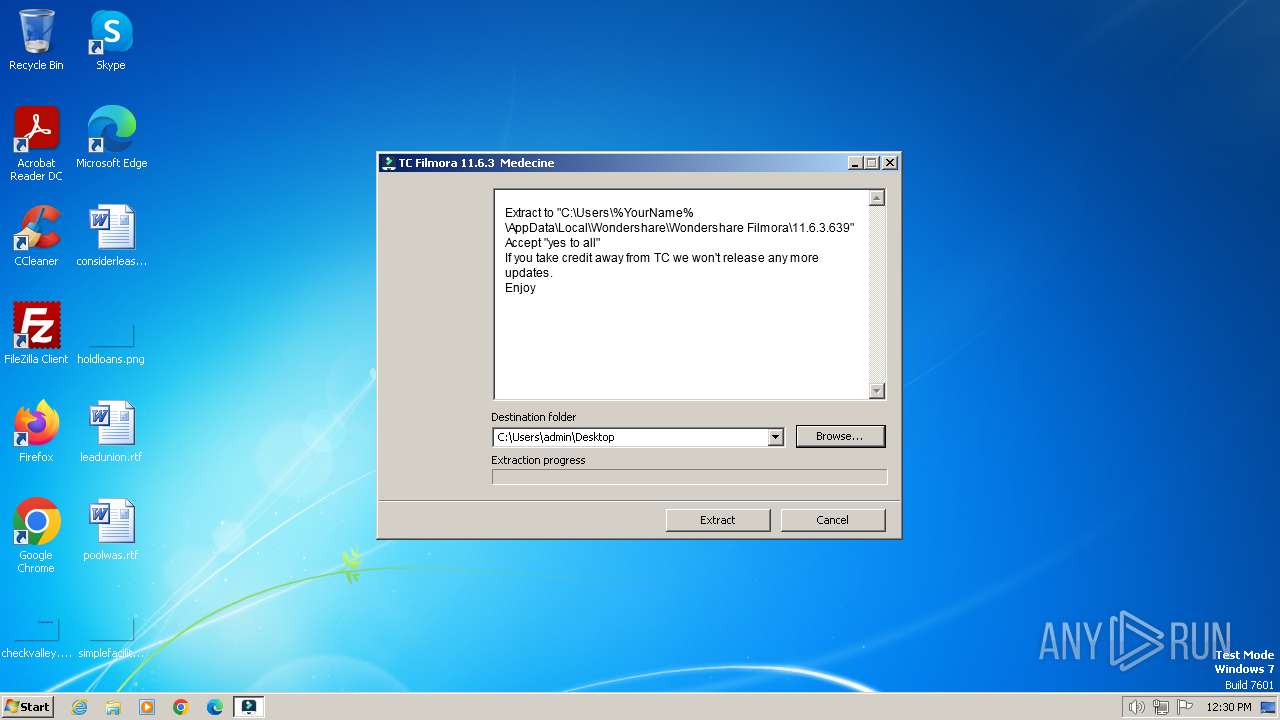
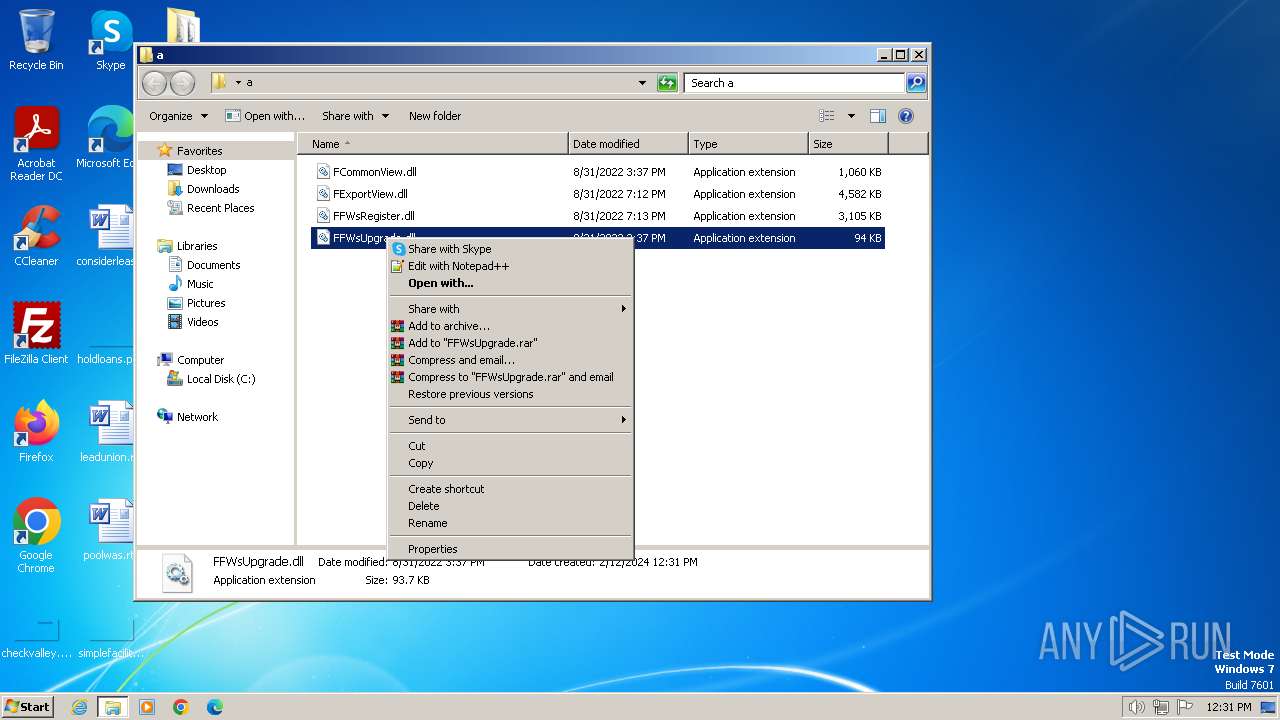
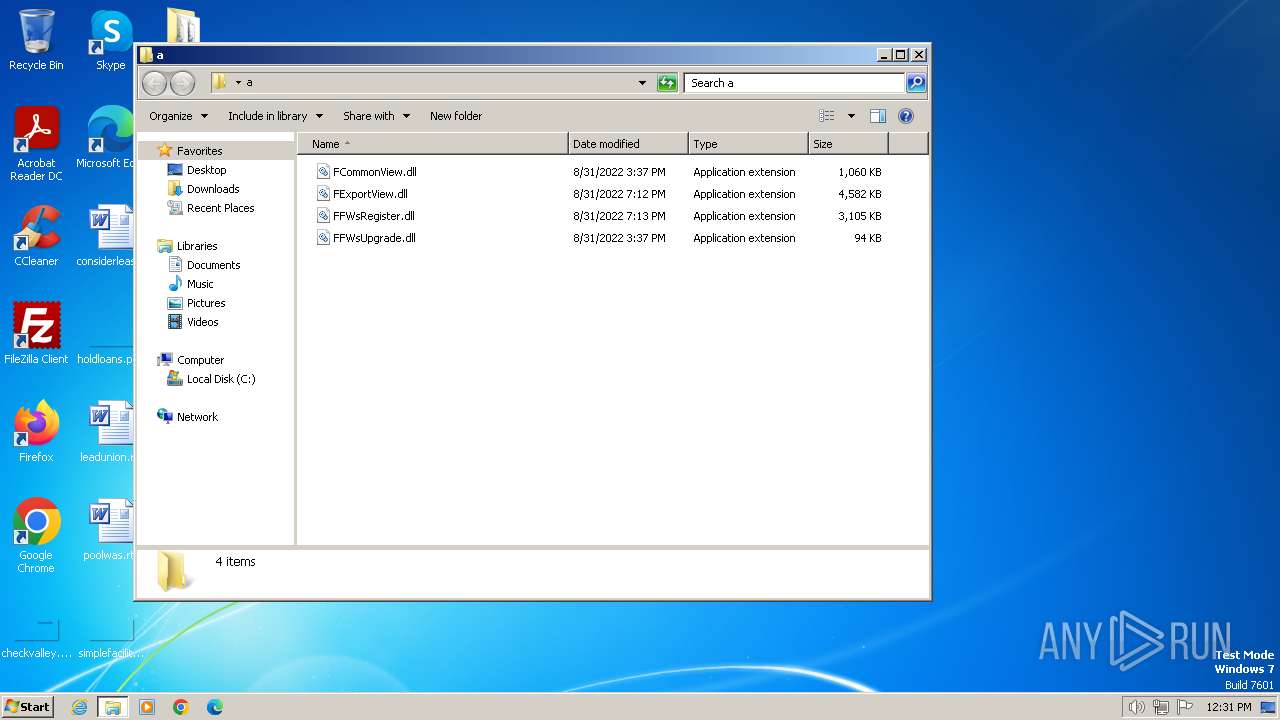
| 3864 | TC_Medecine.exe | C:\Users\admin\Desktop\a\FExportView.dll | executable | |
MD5:8510563F8EA97D2867C5DAC7CE0A7D23 | SHA256:98B4015F13407BBA114C546057086B2A21D0161D7C343582E56A43EC5280CD23 | |||
| 3864 | TC_Medecine.exe | C:\Users\admin\Desktop\a\FFWsRegister.dll | executable | |
MD5:9F47352CB6BF9DB71D1A80BD07D7D027 | SHA256:0E302DCA43B4956C58F2951868CF2C2DE998CB35D9D85E21B42793C02C8413B3 | |||
| 3864 | TC_Medecine.exe | C:\Users\admin\Desktop\a\FCommonView.dll | executable | |
MD5:1F27DD26AC677C270C63DE11C6C3B699 | SHA256:50C4620F33EE1E79994BD2817A2C6647A34367A0202ECD77023606899E67F83A | |||
| 3864 | TC_Medecine.exe | C:\Users\admin\Desktop\a\FFWsUpgrade.dll | executable | |
MD5:88CF8A48DAF253DC7CE876A5B12704AC | SHA256:4AD44CDBF62D8B8BC8CE300133F32C2444D619654105EFE2246D27089072F4CA | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |