| File name: | x02bfa3919c8a58709514ef093061621394e5fb7eb4526c7baae8e07985568352.exe |
| Full analysis: | https://app.any.run/tasks/bff0bad2-abd7-40ad-bb24-eeebb1e7a1ee |
| Verdict: | Malicious activity |
| Threats: | DCrat, also known as Dark Crystal RAT, is a remote access trojan (RAT), which was first introduced in 2018. It is a modular malware that can be customized to perform different tasks. For instance, it can steal passwords, crypto wallet information, hijack Telegram and Steam accounts, and more. Attackers may use a variety of methods to distribute DCrat, but phishing email campaigns are the most common. |
| Analysis date: | April 24, 2026, 05:12:36 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 4 sections |
| MD5: | 535F532F5FFA22C6CB1C393B4B4BE4F6 |
| SHA1: | 1819C9BC28F1E1FE44CD982D5FC66343DEEA1D6F |
| SHA256: | 02BFA3919C8A58709514EF093061621394E5FB7EB4526C7BAAE8E07985568352 |
| SSDEEP: | 98304:5Af1O5iGuEfKpLDNX5LcBNO/M2AEqm6CnKdVdQbzQg+CrsqGXHDaNQcEBakTt5JP:pr |
MALICIOUS
DCRAT mutex has been found
- x02bfa3919c8a58709514ef093061621394e5fb7eb4526c7baae8e07985568352.exe (PID: 4524)
- x02bfa3919c8a58709514ef093061621394e5fb7eb4526c7baae8e07985568352.exe (PID: 4112)
Changes the autorun value in the registry
- x02bfa3919c8a58709514ef093061621394e5fb7eb4526c7baae8e07985568352.exe (PID: 4112)
Changes Windows Defender settings
- x02bfa3919c8a58709514ef093061621394e5fb7eb4526c7baae8e07985568352.exe (PID: 4112)
Adds path to the Windows Defender exclusion list
- x02bfa3919c8a58709514ef093061621394e5fb7eb4526c7baae8e07985568352.exe (PID: 4112)
SUSPICIOUS
Starts CMD.EXE for commands execution
- cmd.exe (PID: 7724)
- cmd.exe (PID: 3140)
Modifies hosts file to alter network resolution
- x02bfa3919c8a58709514ef093061621394e5fb7eb4526c7baae8e07985568352.exe (PID: 4112)
The process creates files with name similar to system file names
- x02bfa3919c8a58709514ef093061621394e5fb7eb4526c7baae8e07985568352.exe (PID: 4112)
Executed via WMI
- schtasks.exe (PID: 7840)
- schtasks.exe (PID: 664)
- schtasks.exe (PID: 1116)
- schtasks.exe (PID: 5704)
- schtasks.exe (PID: 4916)
- schtasks.exe (PID: 7420)
Executable content was dropped or overwritten
- x02bfa3919c8a58709514ef093061621394e5fb7eb4526c7baae8e07985568352.exe (PID: 4112)
Creates scheduled task with highest privileges
- schtasks.exe (PID: 664)
- schtasks.exe (PID: 5704)
- schtasks.exe (PID: 4916)
- schtasks.exe (PID: 7420)
Adds exclusion path to Windows Defender (POWERSHELL)
- x02bfa3919c8a58709514ef093061621394e5fb7eb4526c7baae8e07985568352.exe (PID: 4112)
Starts POWERSHELL.EXE for commands execution
- x02bfa3919c8a58709514ef093061621394e5fb7eb4526c7baae8e07985568352.exe (PID: 4112)
Executing commands from a ".bat" file
- x02bfa3919c8a58709514ef093061621394e5fb7eb4526c7baae8e07985568352.exe (PID: 4112)
Probably delay the execution using 'w32tm.exe'
- cmd.exe (PID: 3140)
- w32tm.exe (PID: 4656)
INFO
Reads security settings of Internet Explorer
- x02bfa3919c8a58709514ef093061621394e5fb7eb4526c7baae8e07985568352.exe (PID: 4524)
- x02bfa3919c8a58709514ef093061621394e5fb7eb4526c7baae8e07985568352.exe (PID: 4112)
Process checks whether UAC notifications are on
- x02bfa3919c8a58709514ef093061621394e5fb7eb4526c7baae8e07985568352.exe (PID: 4524)
- x02bfa3919c8a58709514ef093061621394e5fb7eb4526c7baae8e07985568352.exe (PID: 4112)
Checks supported languages
- x02bfa3919c8a58709514ef093061621394e5fb7eb4526c7baae8e07985568352.exe (PID: 4524)
- x02bfa3919c8a58709514ef093061621394e5fb7eb4526c7baae8e07985568352.exe (PID: 4112)
- RuntimeBroker.exe (PID: 6684)
- winrshost.exe (PID: 5524)
- winrshost.exe (PID: 4396)
- winrshost.exe (PID: 2680)
- x02bfa3919c8a58709514ef093061621394e5fb7eb4526c7baae8e07985568352.exe (PID: 4692)
- RuntimeBroker.exe (PID: 6732)
Reads the computer name
- x02bfa3919c8a58709514ef093061621394e5fb7eb4526c7baae8e07985568352.exe (PID: 4112)
- x02bfa3919c8a58709514ef093061621394e5fb7eb4526c7baae8e07985568352.exe (PID: 4524)
- winrshost.exe (PID: 5524)
- RuntimeBroker.exe (PID: 6684)
- winrshost.exe (PID: 2680)
- winrshost.exe (PID: 4396)
- RuntimeBroker.exe (PID: 6732)
- x02bfa3919c8a58709514ef093061621394e5fb7eb4526c7baae8e07985568352.exe (PID: 4692)
Reads the machine GUID from the registry
- x02bfa3919c8a58709514ef093061621394e5fb7eb4526c7baae8e07985568352.exe (PID: 4524)
- x02bfa3919c8a58709514ef093061621394e5fb7eb4526c7baae8e07985568352.exe (PID: 4112)
- winrshost.exe (PID: 5524)
- winrshost.exe (PID: 2680)
- winrshost.exe (PID: 4396)
- RuntimeBroker.exe (PID: 6684)
- RuntimeBroker.exe (PID: 6732)
- x02bfa3919c8a58709514ef093061621394e5fb7eb4526c7baae8e07985568352.exe (PID: 4692)
The sample compiled with english language support
- x02bfa3919c8a58709514ef093061621394e5fb7eb4526c7baae8e07985568352.exe (PID: 4524)
- x02bfa3919c8a58709514ef093061621394e5fb7eb4526c7baae8e07985568352.exe (PID: 4112)
Process checks computer location settings
- x02bfa3919c8a58709514ef093061621394e5fb7eb4526c7baae8e07985568352.exe (PID: 4524)
- x02bfa3919c8a58709514ef093061621394e5fb7eb4526c7baae8e07985568352.exe (PID: 4112)
Launching a file from a Registry key
- x02bfa3919c8a58709514ef093061621394e5fb7eb4526c7baae8e07985568352.exe (PID: 4112)
Manual execution by a user
- winrshost.exe (PID: 5524)
- RuntimeBroker.exe (PID: 6684)
- winrshost.exe (PID: 4396)
- RuntimeBroker.exe (PID: 6732)
- winrshost.exe (PID: 2680)
Create files in a temporary directory
- x02bfa3919c8a58709514ef093061621394e5fb7eb4526c7baae8e07985568352.exe (PID: 4112)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 5420)
- powershell.exe (PID: 2436)
- powershell.exe (PID: 684)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 2436)
- powershell.exe (PID: 684)
- powershell.exe (PID: 5420)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2012:07:13 22:47:16+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, Large address aware, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 104448 |
| InitializedDataSize: | 1973248 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xcd2f |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 5.15.2.0 |
| ProductVersionNumber: | 5.15.2.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Dynamic link library |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| FileVersion: | 5.15.2.0 |
| OriginalFileName: | libGLESv2.dll |
| ProductName: | libGLESv2 |
| ProductVersion: | 5.15.2.0 |
Total processes
164
Monitored processes
27
Malicious processes
3
Suspicious processes
4
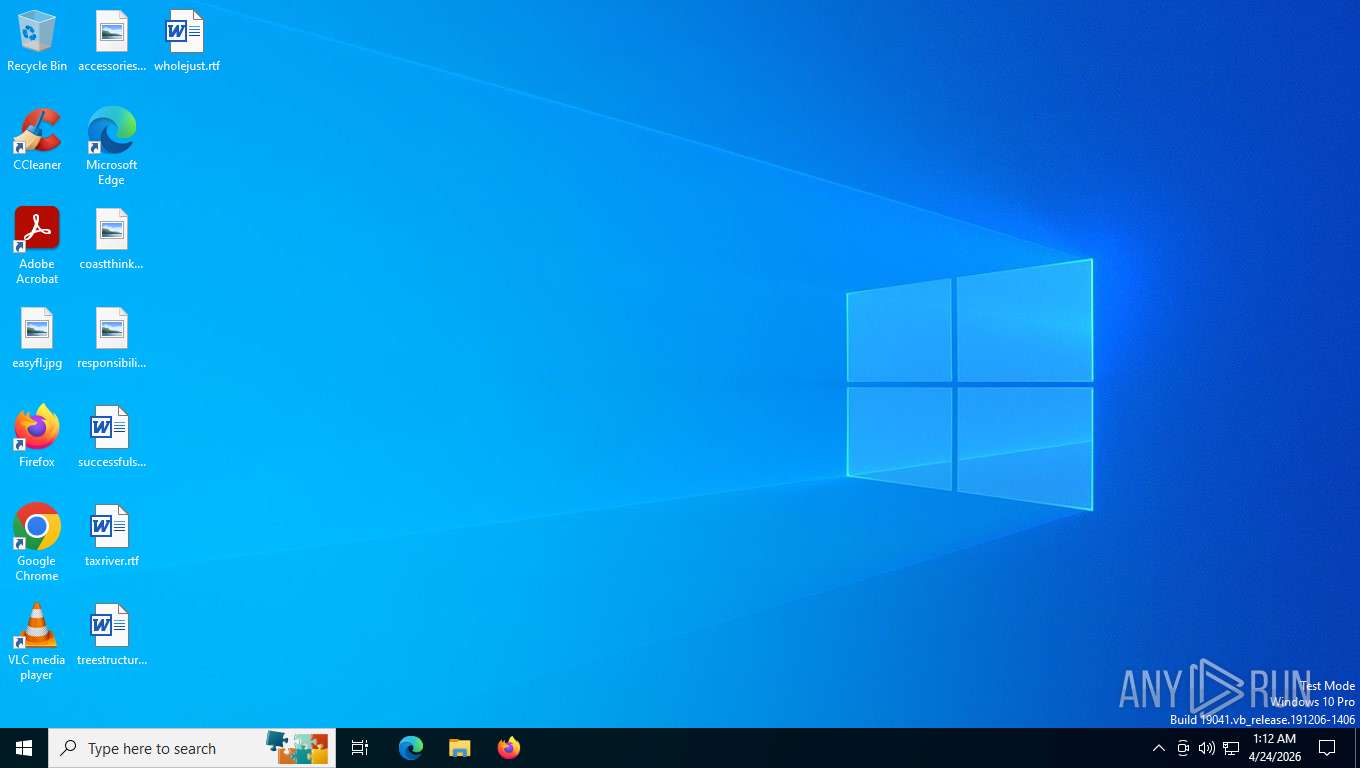
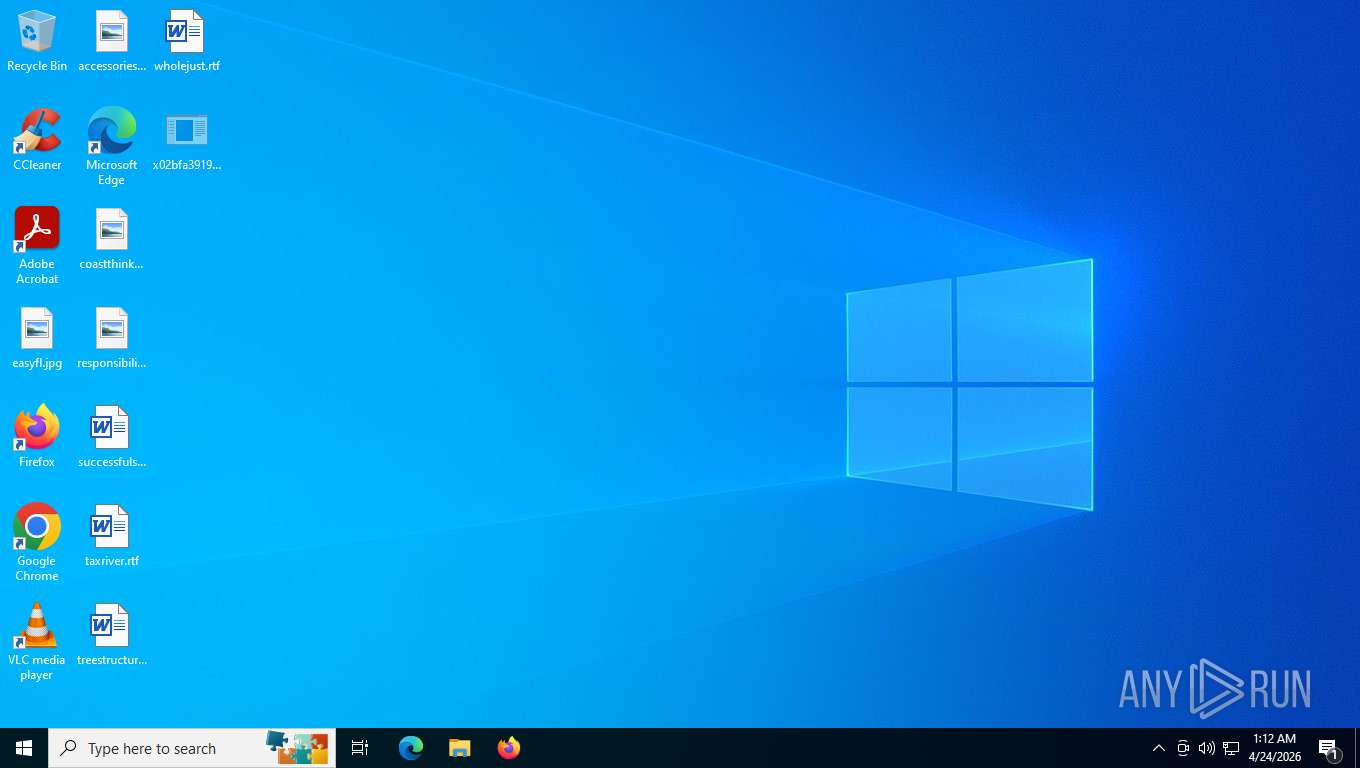
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 664 | schtasks.exe /create /tn "winrshost" /sc ONLOGON /tr "'C:\Program Files (x86)\MSBuild\winrshost.exe'" /rl HIGHEST /f | C:\Windows\System32\schtasks.exe | — | WmiPrvSE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 684 | "powershell" -Command Add-MpPreference -ExclusionPath 'C:\Users\admin\Desktop\x02bfa3919c8a58709514ef093061621394e5fb7eb4526c7baae8e07985568352.exe' | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | x02bfa3919c8a58709514ef093061621394e5fb7eb4526c7baae8e07985568352.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1116 | schtasks.exe /create /tn "RuntimeBrokerR" /sc MINUTE /mo 10 /tr "'C:\Users\Default User\RuntimeBroker.exe'" /f | C:\Windows\System32\schtasks.exe | — | WmiPrvSE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2436 | "powershell" -Command Add-MpPreference -ExclusionPath 'C:\Users\Default User\RuntimeBroker.exe' | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | x02bfa3919c8a58709514ef093061621394e5fb7eb4526c7baae8e07985568352.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2456 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2680 | "C:\Program Files (x86)\MSBuild\winrshost.exe" | C:\Program Files (x86)\MSBuild\winrshost.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 5.15.2.0 Modules
| |||||||||||||||
| 3112 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3140 | "C:\WINDOWS\System32\cmd.exe" /C "C:\Users\admin\AppData\Local\Temp\eMIZxK0WIh.bat" | C:\Windows\SysWOW64\cmd.exe | — | x02bfa3919c8a58709514ef093061621394e5fb7eb4526c7baae8e07985568352.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4112 | C:\Users\admin\Desktop\x02bfa3919c8a58709514ef093061621394e5fb7eb4526c7baae8e07985568352.exe | C:\Users\admin\Desktop\x02bfa3919c8a58709514ef093061621394e5fb7eb4526c7baae8e07985568352.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 5.15.2.0 Modules
| |||||||||||||||
| 4312 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
21 726
Read events
21 712
Write events
14
Delete events
0
Modification events
| (PID) Process: | (4524) x02bfa3919c8a58709514ef093061621394e5fb7eb4526c7baae8e07985568352.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | EnableLUA |
Value: 0 | |||
| (PID) Process: | (4112) x02bfa3919c8a58709514ef093061621394e5fb7eb4526c7baae8e07985568352.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | EnableLUA |
Value: 0 | |||
| (PID) Process: | (4112) x02bfa3919c8a58709514ef093061621394e5fb7eb4526c7baae8e07985568352.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | ConsentPromptBehaviorAdmin |
Value: 0 | |||
| (PID) Process: | (4112) x02bfa3919c8a58709514ef093061621394e5fb7eb4526c7baae8e07985568352.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | PromptOnSecureDesktop |
Value: 0 | |||
| (PID) Process: | (4112) x02bfa3919c8a58709514ef093061621394e5fb7eb4526c7baae8e07985568352.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Action Center\Checks\{C8E6F269-B90A-4053-A3BE-499AFCEC98C4}.check.0 |
| Operation: | write | Name: | CheckSetting |
Value: 23004100430042006C006F00620000000000000000000000010000000000000000000000 | |||
| (PID) Process: | (4112) x02bfa3919c8a58709514ef093061621394e5fb7eb4526c7baae8e07985568352.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\9b90c88d90d65a05eea12d70abda15b8 |
| Operation: | write | Name: | 9b90c88d90d65a05eea12d70abda15b8 |
Value: 9b90c88d90d65a05eea12d70abda15b8 | |||
| (PID) Process: | (4312) slui.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\3d\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\System32\sppcomapi.dll,-3200 |
Value: Software Licensing | |||
| (PID) Process: | (4112) x02bfa3919c8a58709514ef093061621394e5fb7eb4526c7baae8e07985568352.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | winrshost |
Value: "C:\Program Files (x86)\MSBuild\winrshost.exe" | |||
| (PID) Process: | (4112) x02bfa3919c8a58709514ef093061621394e5fb7eb4526c7baae8e07985568352.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | winrshost |
Value: "C:\Program Files (x86)\MSBuild\winrshost.exe" | |||
| (PID) Process: | (4112) x02bfa3919c8a58709514ef093061621394e5fb7eb4526c7baae8e07985568352.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\0e08e9d007e8d42975f2c42a8a78b72ea0bf6b0f |
| Operation: | write | Name: | fa2a311864357add774543e88843ad16e81ec867 |
Value: WyJDOlxcVXNlcnNcXGFkbWluXFxEZXNrdG9wXFx4MDJiZmEzOTE5YzhhNTg3MDk1MTRlZjA5MzA2MTYyMTM5NGU1ZmI3ZWI0NTI2YzdiYWFlOGUwNzk4NTU2ODM1Mi5leGUiLCJDOlxcUHJvZ3JhbSBGaWxlcyAoeDg2KVxcTVNCdWlsZFxcd2lucnNob3N0LmV4ZSIsIkM6XFxVc2Vyc1xcRGVmYXVsdCBVc2VyXFxSdW50aW1lQnJva2VyLmV4ZSJd | |||
Executable files
9
Suspicious files
1
Text files
17
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4112 | x02bfa3919c8a58709514ef093061621394e5fb7eb4526c7baae8e07985568352.exe | — | ||
MD5:— | SHA256:— | |||
| 4112 | x02bfa3919c8a58709514ef093061621394e5fb7eb4526c7baae8e07985568352.exe | C:\Windows\System32\drivers\etc\hosts | text | |
MD5:8FF960C5E3473174DC546F28C2079177 | SHA256:4B36853D385A7B865724AE482717AEDE1C3E69481C3BB69293C04FCAA4B9827B | |||
| 4112 | x02bfa3919c8a58709514ef093061621394e5fb7eb4526c7baae8e07985568352.exe | C:\Users\Default\RuntimeBroker.exe | executable | |
MD5:535F532F5FFA22C6CB1C393B4B4BE4F6 | SHA256:02BFA3919C8A58709514EF093061621394E5FB7EB4526C7BAAE8E07985568352 | |||
| 4112 | x02bfa3919c8a58709514ef093061621394e5fb7eb4526c7baae8e07985568352.exe | C:\Program Files (x86)\MSBuild\RCX19FF.tmp | executable | |
MD5:535F532F5FFA22C6CB1C393B4B4BE4F6 | SHA256:02BFA3919C8A58709514EF093061621394E5FB7EB4526C7BAAE8E07985568352 | |||
| 4112 | x02bfa3919c8a58709514ef093061621394e5fb7eb4526c7baae8e07985568352.exe | C:\Users\admin\AppData\Local\Temp\eMIZxK0WIh.bat | text | |
MD5:149A7F4C629A61DC607BA9297B9C3AB8 | SHA256:0329E6A606380348C33EF0CE9291FEA9D7D13A5AA58191D20437D7E0BB5A56E5 | |||
| 4112 | x02bfa3919c8a58709514ef093061621394e5fb7eb4526c7baae8e07985568352.exe | C:\Users\admin\Desktop\RCX17EA.tmp | executable | |
MD5:359D8EBD0D46161F33E53E26CA2C7922 | SHA256:11A3C0A1AB6C320103D01626DD4BA0A7DED4F9D23625FF0991F5AE161ADFF2FB | |||
| 4112 | x02bfa3919c8a58709514ef093061621394e5fb7eb4526c7baae8e07985568352.exe | C:\Users\admin\Desktop\RCX17BA.tmp | executable | |
MD5:FD79F1DCD8970A72A3ECD39262C54914 | SHA256:982638CB6D51B5741EA6A8E6CCFED938EDCD1983878772F5650CB12992B33CE5 | |||
| 4112 | x02bfa3919c8a58709514ef093061621394e5fb7eb4526c7baae8e07985568352.exe | C:\Program Files (x86)\MSBuild\RCX19EE.tmp | executable | |
MD5:5166EE4E5E63F0029DF3F6C54D274E11 | SHA256:268D4A04140A0EB0C4212203A6A50EA742D4BB48CA5174F0000CFD609B3B1E73 | |||
| 4112 | x02bfa3919c8a58709514ef093061621394e5fb7eb4526c7baae8e07985568352.exe | C:\Program Files (x86)\MSBuild\winrshost.exe | executable | |
MD5:535F532F5FFA22C6CB1C393B4B4BE4F6 | SHA256:02BFA3919C8A58709514EF093061621394E5FB7EB4526C7BAAE8E07985568352 | |||
| 5420 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_5rbza3pv.eq0.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
52
TCP/UDP connections
38
DNS requests
19
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5276 | MoUsoCoreWorker.exe | GET | 304 | 40.127.240.158:443 | https://settings-win.data.microsoft.com/settings/v3.0/wsd/muse?ProcessorClockSpeed=3094&FlightIds=&UpdateOfferedDays=4294967295&BranchReadinessLevel=CB&OEMManufacturerName=DELL&IsCloudDomainJoined=0&ProcessorIdentifier=AMD64%20Family%2023%20Model%201%20Stepping%202&sku=48&ActivationChannel=Retail&AttrDataVer=186&IsMDMEnrolled=0&ProcessorCores=6&ProcessorModel=AMD%20Ryzen%205%203500%206-Core%20Processor&TotalPhysicalRAM=6144&PrimaryDiskType=4294967295&FlightingBranchName=&ChassisTypeId=1&OEMModelNumber=DELL&SystemVolumeTotalCapacity=260281&sampleId=95271487&deviceClass=Windows.Desktop&App=muse&DisableDualScan=0&AppVer=10.0&OEMSubModel=J5CR&locale=en-US&IsAlwaysOnAlwaysConnectedCapable=0&ms=0&DefaultUserRegion=244&UpdateServiceUrl=http%3A%2F%2Fneverupdatewindows10.com&osVer=10.0.19045.4046.amd64fre.vb_release.191206-1406&os=windows&deviceId=s%3ABAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&DeferQualityUpdatePeriodInDays=0&ring=Retail&DeferFeatureUpdatePeriodInDays=30 | US | — | — | whitelisted |
7428 | SIHClient.exe | GET | 304 | 74.178.240.61:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | US | — | — | whitelisted |
5276 | MoUsoCoreWorker.exe | GET | 200 | 23.52.181.212:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | US | binary | 814 b | whitelisted |
3352 | svchost.exe | GET | 200 | 2.16.164.49:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
3352 | svchost.exe | GET | 200 | 23.52.181.212:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | US | binary | 814 b | whitelisted |
3352 | svchost.exe | GET | 200 | 40.127.240.158:443 | https://settings-win.data.microsoft.com/settings/v3.0/WSD/WaasMedic?os=Windows&osVer=10.0.19041.1.amd64fre.vb_release.191206-&appVer=10.0.19041.3758&ring=Retail&sku=48&deviceClass=Windows.Desktop&locale=en-US&deviceId=BAD99146-31D3-4EC6-A1A4-BE76F32BA5D4 | US | text | 3.41 Kb | whitelisted |
4312 | slui.exe | POST | 500 | 48.192.1.64:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | US | xml | 512 b | whitelisted |
5316 | svchost.exe | POST | 200 | 20.190.160.20:443 | https://login.live.com/RST2.srf | US | xml | 1.24 Kb | whitelisted |
5316 | svchost.exe | POST | 200 | 40.126.32.133:443 | https://login.live.com/RST2.srf | US | xml | 1.24 Kb | whitelisted |
— | — | POST | 400 | 20.190.160.20:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | US | text | 204 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3352 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
5276 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
8040 | slui.exe | 48.192.1.64:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
3352 | svchost.exe | 2.16.164.49:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
3352 | svchost.exe | 23.52.181.212:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
5276 | MoUsoCoreWorker.exe | 23.52.181.212:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
5208 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3352 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3352 | svchost.exe | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |