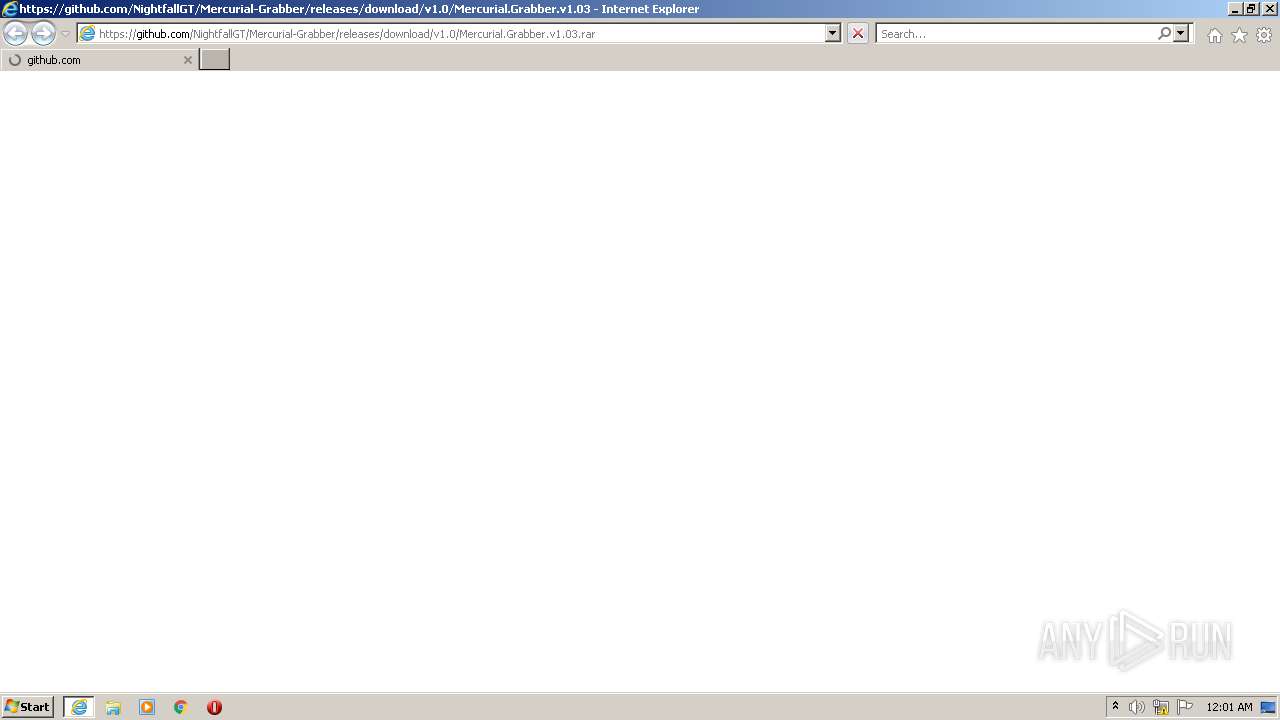
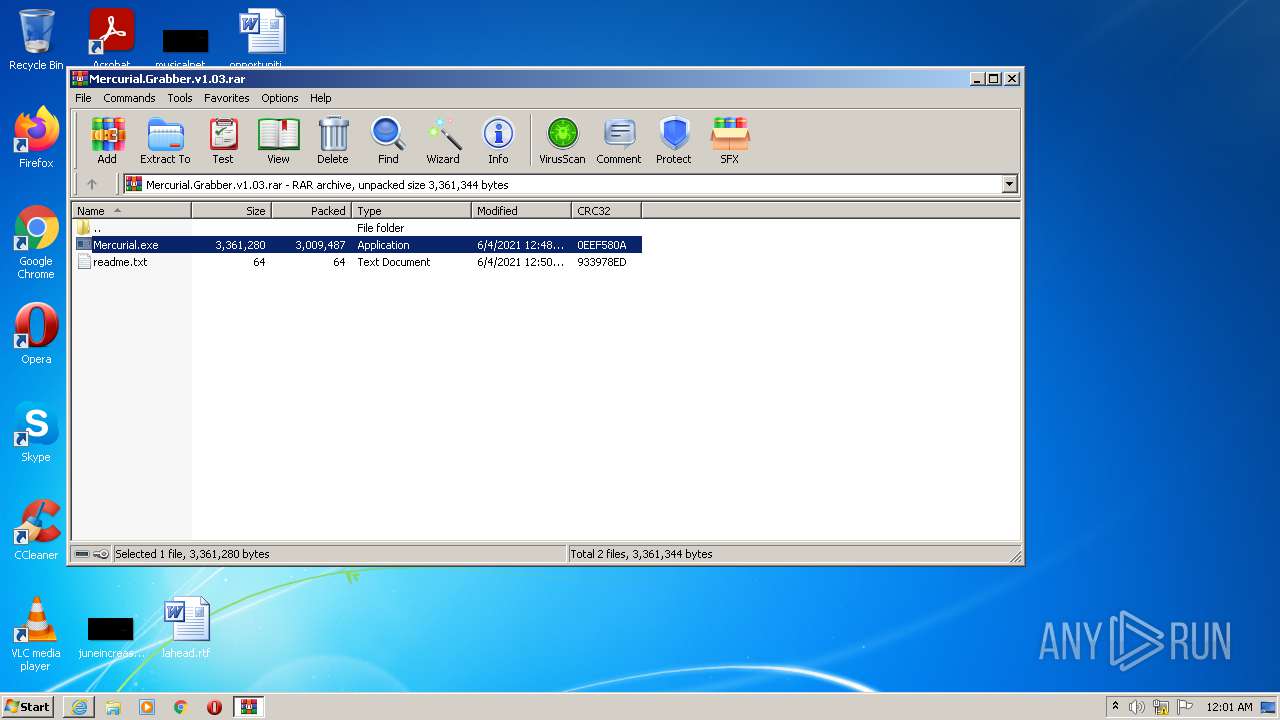
| URL: | https://github.com/NightfallGT/Mercurial-Grabber/releases/download/v1.0/Mercurial.Grabber.v1.03.rar |
| Full analysis: | https://app.any.run/tasks/2e860ef8-30b6-4c92-9330-64b9a1c68a9c |
| Verdict: | Malicious activity |
| Analysis date: | July 14, 2021, 23:00:41 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 23E8B47C5B2E64BF564732A7BD835AC5 |
| SHA1: | 51407166017CEE45170732B365F91BD25CA87BCF |
| SHA256: | 02BA13BD104729AAB9D872FA6A776CEA69142BED3040D83E3FEC0CBC576B1292 |
| SSDEEP: | 3:N8tEdo+DgAVCkdyKcAE2kCmty3niUHHAXLThLOn:2ue8FXdy/ArsrXLTdOn |
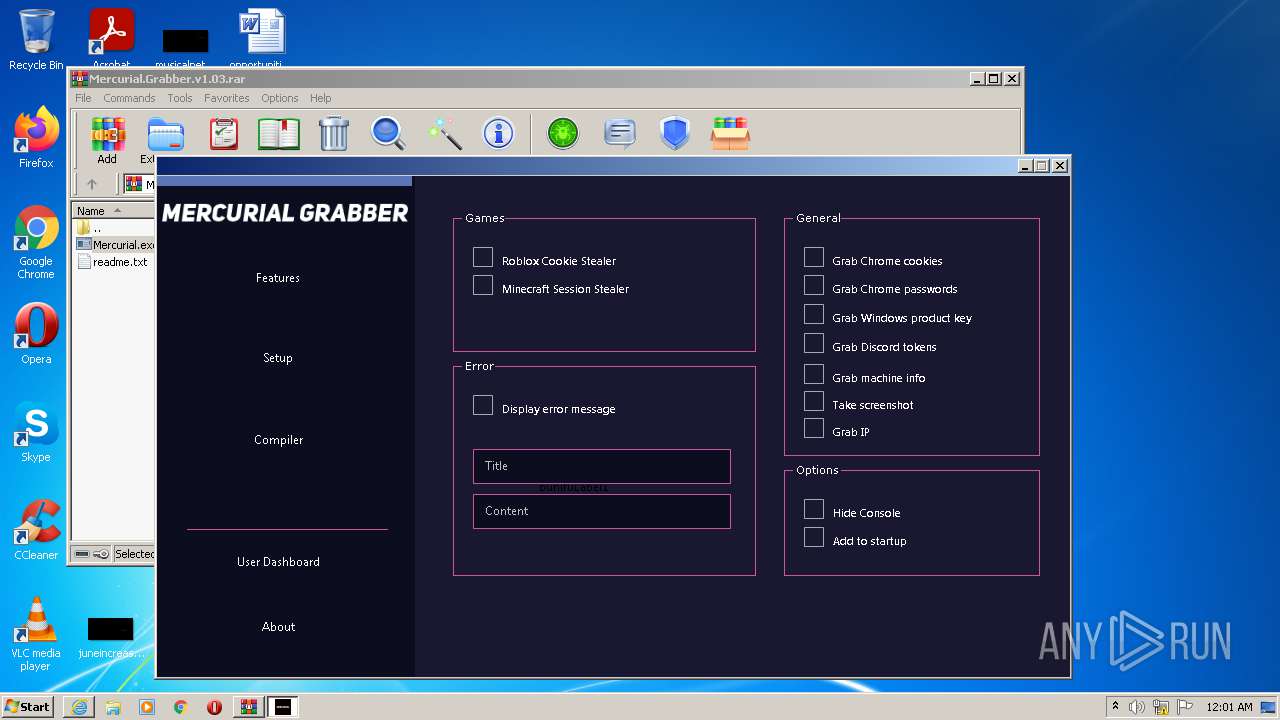
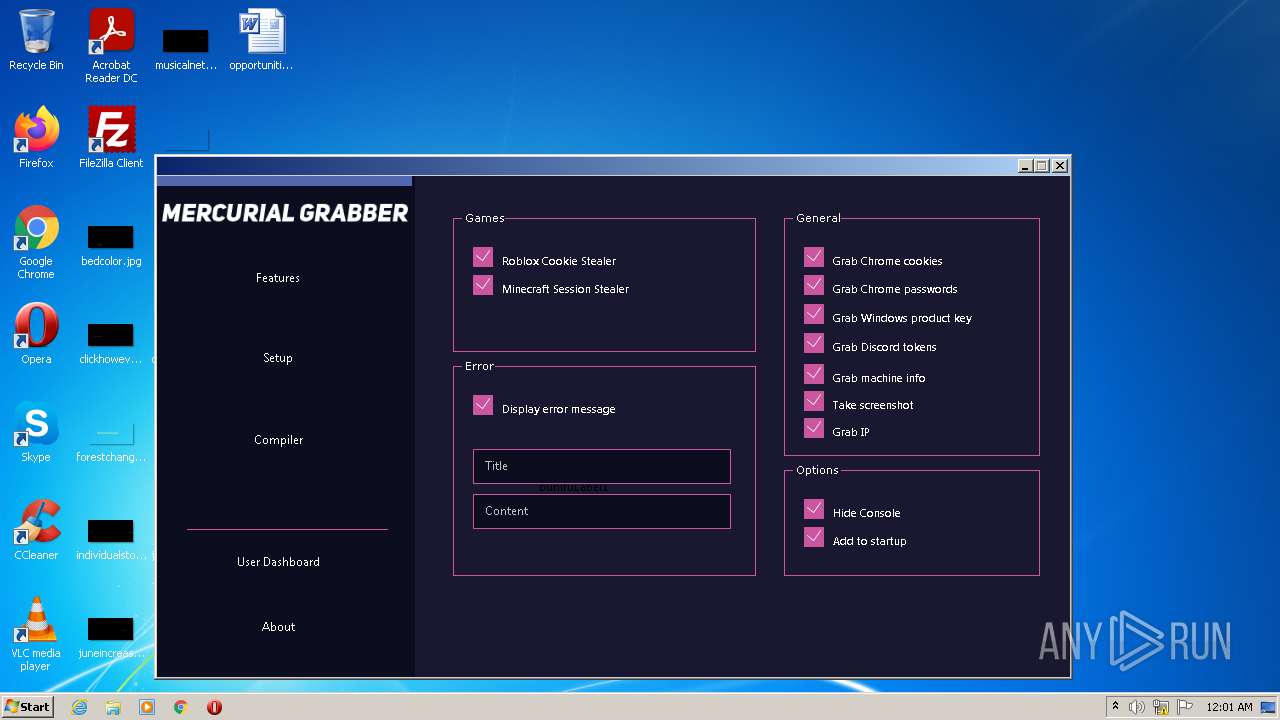
MALICIOUS
Application was dropped or rewritten from another process
- Mercurial.exe (PID: 2700)
Changes the autorun value in the registry
- reg.exe (PID: 3340)
SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 276)
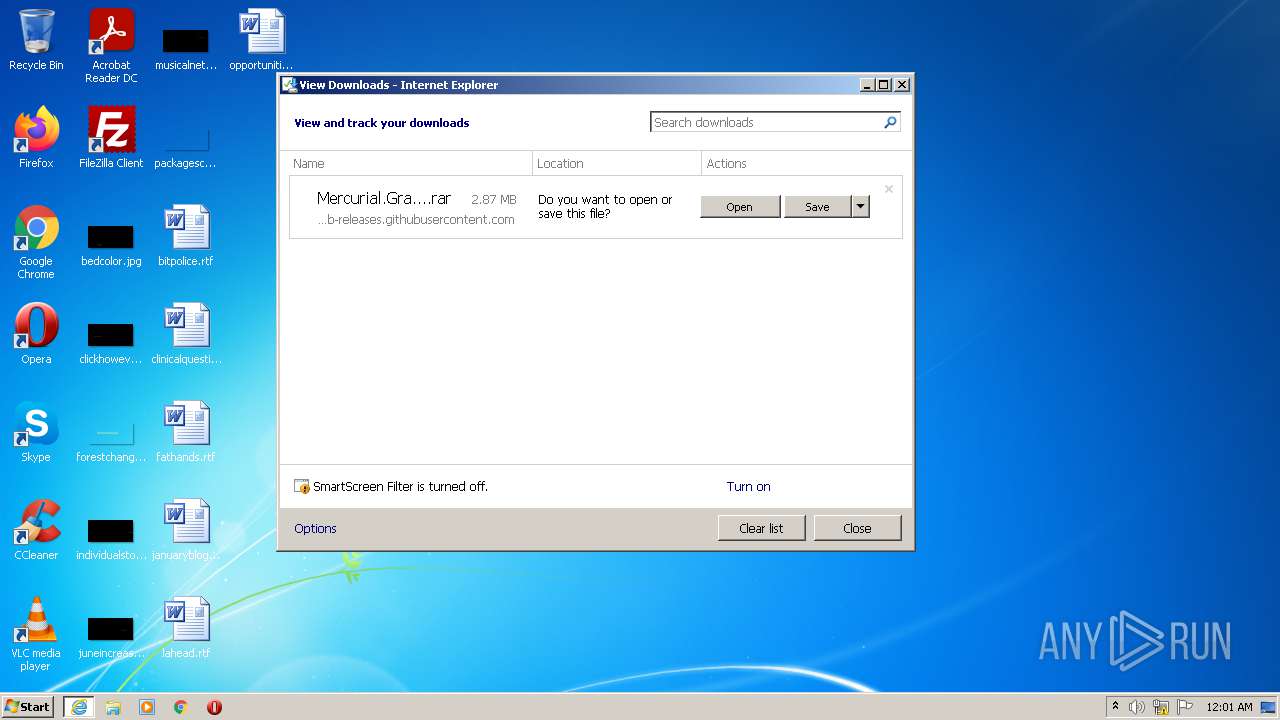
Executable content was dropped or overwritten
- WinRAR.exe (PID: 416)
Checks supported languages
- WinRAR.exe (PID: 416)
- Mercurial.exe (PID: 2700)
- Skype.exe (PID: 2268)
- Skype.exe (PID: 2340)
- Skype.exe (PID: 2916)
- Skype.exe (PID: 288)
- Skype.exe (PID: 3356)
- Skype.exe (PID: 2876)
Drops a file that was compiled in debug mode
- WinRAR.exe (PID: 416)
Drops a file with too old compile date
- WinRAR.exe (PID: 416)
Reads the computer name
- WinRAR.exe (PID: 416)
- Mercurial.exe (PID: 2700)
- Skype.exe (PID: 2268)
- Skype.exe (PID: 2340)
- Skype.exe (PID: 288)
- Skype.exe (PID: 2916)
- Skype.exe (PID: 3356)
- Skype.exe (PID: 2876)
Application launched itself
- Skype.exe (PID: 2268)
- Skype.exe (PID: 2916)
- Skype.exe (PID: 3356)
Changes default file association
- Skype.exe (PID: 2268)
Reads CPU info
- Skype.exe (PID: 2268)
Uses REG.EXE to modify Windows registry
- Skype.exe (PID: 2268)
Creates files in the user directory
- Skype.exe (PID: 2268)
- Skype.exe (PID: 2916)
- Skype.exe (PID: 3356)
INFO
Reads the computer name
- iexplore.exe (PID: 1804)
- iexplore.exe (PID: 276)
- WINWORD.EXE (PID: 948)
Checks supported languages
- iexplore.exe (PID: 276)
- iexplore.exe (PID: 1804)
- WINWORD.EXE (PID: 948)
- reg.exe (PID: 3340)
- reg.exe (PID: 3164)
Checks Windows Trust Settings
- iexplore.exe (PID: 276)
- iexplore.exe (PID: 1804)
Application launched itself
- iexplore.exe (PID: 1804)
Changes internet zones settings
- iexplore.exe (PID: 1804)
Reads the date of Windows installation
- iexplore.exe (PID: 1804)
Modifies the phishing filter of IE
- iexplore.exe (PID: 1804)
Reads settings of System Certificates
- iexplore.exe (PID: 276)
- Skype.exe (PID: 2268)
Manual execution by user
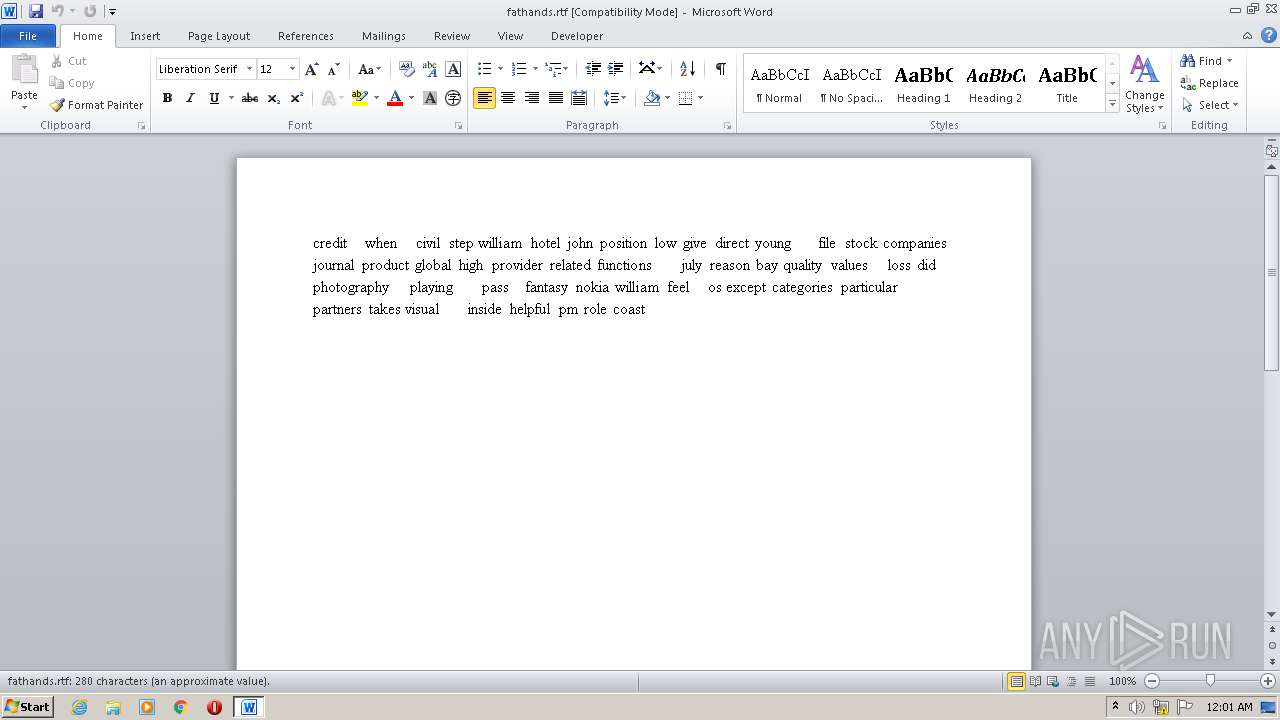
- WINWORD.EXE (PID: 948)
- Skype.exe (PID: 2268)
Creates files in the user directory
- WINWORD.EXE (PID: 948)
Reads the hosts file
- Skype.exe (PID: 2268)
Dropped object may contain Bitcoin addresses
- Skype.exe (PID: 2268)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 948)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
50
Monitored processes
13
Malicious processes
1
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 276 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1804 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 288 | "C:\Program Files\Microsoft\Skype for Desktop\Skype.exe" --reporter-url=https://rink.hockeyapp.net/api/2/apps/a741743329d94bc08826af367733939d/crashes/upload --application-name=skype-preview "--crashes-directory=C:\Users\admin\AppData\Local\Temp\skype-preview Crashes" --v=1 | C:\Program Files\Microsoft\Skype for Desktop\Skype.exe | — | Skype.exe | |||||||||||
User: admin Company: Skype Technologies S.A. Integrity Level: MEDIUM Description: Skype Exit code: 2 Version: 8.29.0.50 Modules
| |||||||||||||||
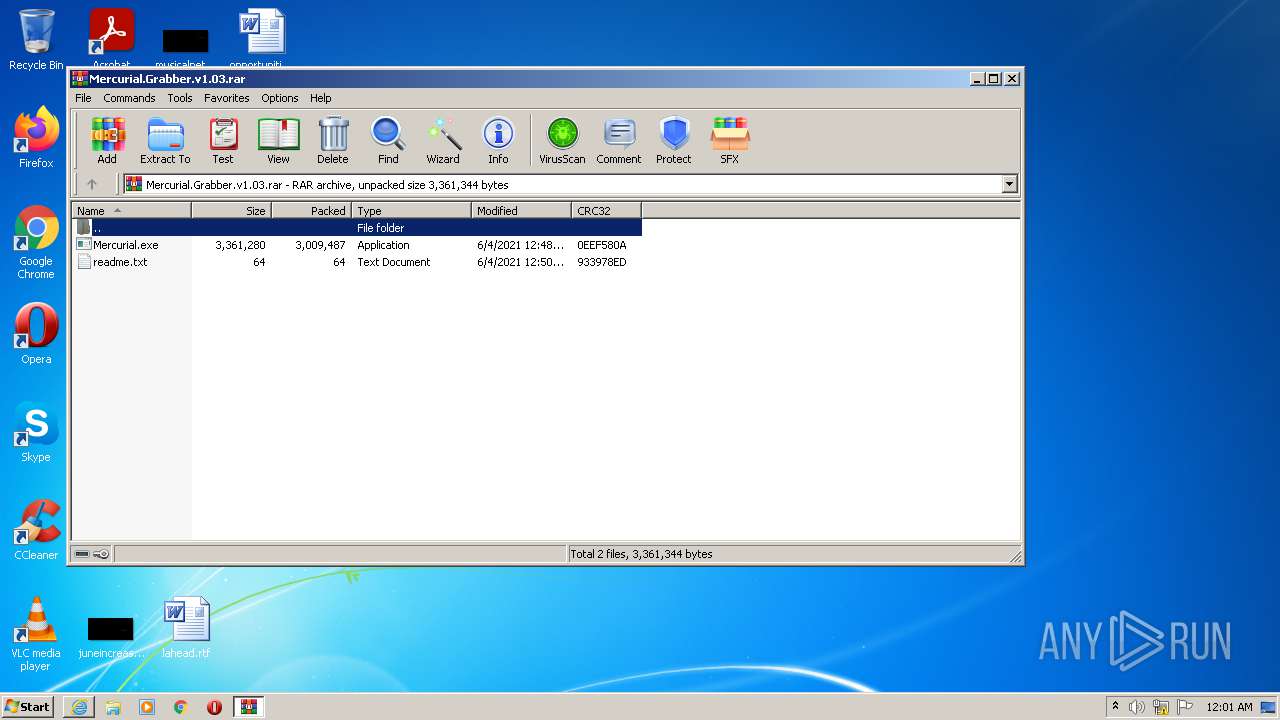
| 416 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\Mercurial.Grabber.v1.03.rar" | C:\Program Files\WinRAR\WinRAR.exe | iexplore.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
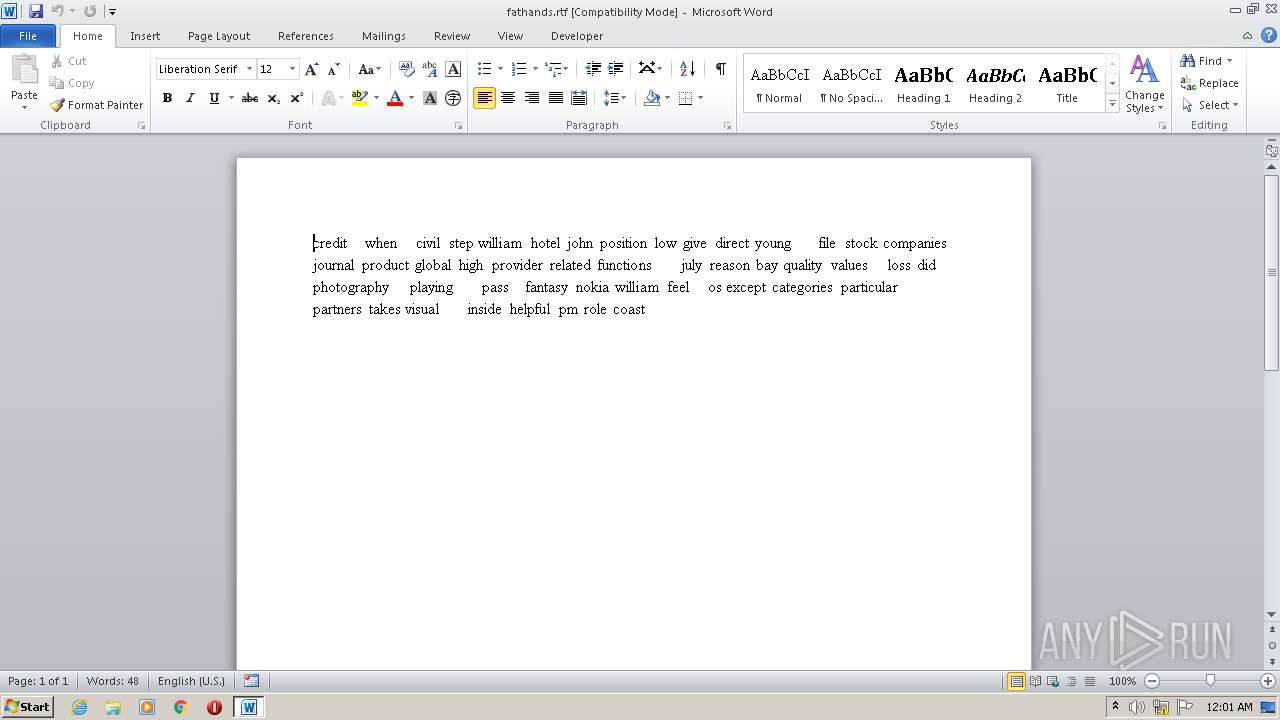
| 948 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\fathands.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
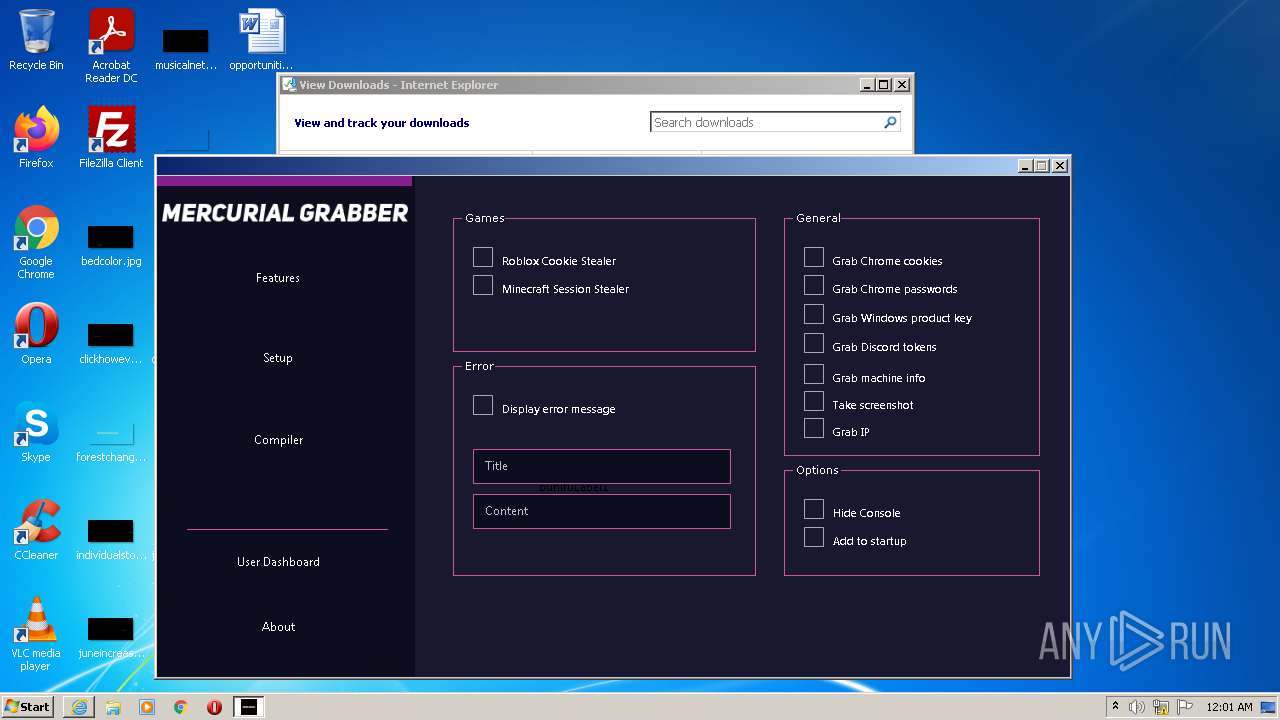
| 1804 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://github.com/NightfallGT/Mercurial-Grabber/releases/download/v1.0/Mercurial.Grabber.v1.03.rar" | C:\Program Files\Internet Explorer\iexplore.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2268 | "C:\Program Files\Microsoft\Skype for Desktop\Skype.exe" | C:\Program Files\Microsoft\Skype for Desktop\Skype.exe | Explorer.EXE | ||||||||||||
User: admin Company: Skype Technologies S.A. Integrity Level: MEDIUM Description: Skype Exit code: 0 Version: 8.29.0.50 Modules
| |||||||||||||||
| 2340 | "C:\Program Files\Microsoft\Skype for Desktop\Skype.exe" --reporter-url=https://rink.hockeyapp.net/api/2/apps/a741743329d94bc08826af367733939d/crashes/upload --application-name=skype-preview "--crashes-directory=C:\Users\admin\AppData\Local\Temp\skype-preview Crashes" --v=1 | C:\Program Files\Microsoft\Skype for Desktop\Skype.exe | — | Skype.exe | |||||||||||
User: admin Company: Skype Technologies S.A. Integrity Level: MEDIUM Description: Skype Exit code: 0 Version: 8.29.0.50 Modules
| |||||||||||||||
| 2700 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa416.49726\Mercurial.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa416.49726\Mercurial.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Mercurial Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2876 | "C:\Program Files\Microsoft\Skype for Desktop\Skype.exe" --reporter-url=https://rink.hockeyapp.net/api/2/apps/a741743329d94bc08826af367733939d/crashes/upload --application-name=skype-preview "--crashes-directory=C:\Users\admin\AppData\Local\Temp\skype-preview Crashes" --v=1 | C:\Program Files\Microsoft\Skype for Desktop\Skype.exe | — | Skype.exe | |||||||||||
User: admin Company: Skype Technologies S.A. Integrity Level: MEDIUM Description: Skype Exit code: 2 Version: 8.29.0.50 Modules
| |||||||||||||||
| 2916 | "C:\Program Files\Microsoft\Skype for Desktop\Skype.exe" --type=renderer --ms-disable-indexeddb-transaction-timeout --no-sandbox --service-pipe-token=D0ABB73BA0C4655A21144B7AC90160FF --lang=en-US --app-user-model-id=Microsoft.Skype.SkypeDesktop --app-path="C:\Program Files\Microsoft\Skype for Desktop\resources\app.asar" --node-integration=false --webview-tag=true --no-sandbox --preload="C:\Program Files\Microsoft\Skype for Desktop\resources\app.asar\Preload.js" --context-id=2 --enable-pinch --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --content-image-texture-target=0,0,3553;0,1,3553;0,2,3553;0,3,3553;0,4,3553;0,5,3553;0,6,3553;0,7,3553;0,8,3553;0,9,3553;0,10,3553;0,11,3553;0,12,3553;0,13,3553;0,14,3553;0,15,3553;0,16,3553;0,17,3553;1,0,3553;1,1,3553;1,2,3553;1,3,3553;1,4,3553;1,5,3553;1,6,3553;1,7,3553;1,8,3553;1,9,3553;1,10,3553;1,11,3553;1,12,3553;1,13,3553;1,14,3553;1,15,3553;1,16,3553;1,17,3553;2,0,3553;2,1,3553;2,2,3553;2,3,3553;2,4,3553;2,5,3553;2,6,3553;2,7,3553;2,8,3553;2,9,3553;2,10,3553;2,11,3553;2,12,3553;2,13,3553;2,14,3553;2,15,3553;2,16,3553;2,17,3553;3,0,3553;3,1,3553;3,2,3553;3,3,3553;3,4,3553;3,5,3553;3,6,3553;3,7,3553;3,8,3553;3,9,3553;3,10,3553;3,11,3553;3,12,3553;3,13,3553;3,14,3553;3,15,3553;3,16,3553;3,17,3553;4,0,3553;4,1,3553;4,2,3553;4,3,3553;4,4,3553;4,5,3553;4,6,3553;4,7,3553;4,8,3553;4,9,3553;4,10,3553;4,11,3553;4,12,3553;4,13,3553;4,14,3553;4,15,3553;4,16,3553;4,17,3553 --disable-accelerated-video-decode --disable-gpu-compositing --enable-gpu-async-worker-context --service-request-channel-token=D0ABB73BA0C4655A21144B7AC90160FF --renderer-client-id=3 --mojo-platform-channel-handle=1592 /prefetch:1 | C:\Program Files\Microsoft\Skype for Desktop\Skype.exe | — | Skype.exe | |||||||||||
User: admin Company: Skype Technologies S.A. Integrity Level: MEDIUM Description: Skype Exit code: 0 Version: 8.29.0.50 Modules
| |||||||||||||||
Total events
15 106
Read events
14 668
Write events
288
Delete events
150
Modification events
| (PID) Process: | (1804) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (1804) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: 478250944 | |||
| (PID) Process: | (1804) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30898436 | |||
| (PID) Process: | (1804) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 778260241 | |||
| (PID) Process: | (1804) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30898436 | |||
| (PID) Process: | (1804) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1804) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1804) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1804) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1804) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
1
Suspicious files
17
Text files
13
Unknown types
11
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 948 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRAC22.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 276 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:F7DCB24540769805E5BB30D193944DCE | SHA256:6B88C6AC55BBD6FEA0EBE5A760D1AD2CFCE251C59D0151A1400701CB927E36EA | |||
| 276 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\Mercurial.Grabber.v1.03[1].rar | compressed | |
MD5:— | SHA256:— | |||
| 1804 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{5A224C2C-E4F7-11EB-B7EE-12A9866C77DE}.dat | binary | |
MD5:— | SHA256:— | |||
| 276 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\EDC238BFF48A31D55A97E1E93892934B_C20E0DA2D0F89FE526E1490F4A2EE5AB | der | |
MD5:— | SHA256:— | |||
| 276 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\2A7611428D62805A3E4E5BC4103D82E4_D0FA13DADFB59BDF00C474952E166CC1 | der | |
MD5:— | SHA256:— | |||
| 276 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\12B578593FDE07EC53D020B1D5DEBF3B_5D74C2DB556F94499BCD6D74A36958A3 | binary | |
MD5:— | SHA256:— | |||
| 1804 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF5E5B3279F7742F27.TMP | gmc | |
MD5:— | SHA256:— | |||
| 1804 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF3C02BA416885EF76.TMP | gmc | |
MD5:— | SHA256:— | |||
| 2268 | Skype.exe | C:\Users\admin\AppData\Local\Temp\fdbdb6ea-0f9d-4dad-b0dc-d0298a781f66.tmp.ico | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
14
DNS requests
12
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
276 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTGMlruL6P9M9B3if1rTM7wyj%2FQKQQUUGGmoNI1xBEqII0fD6xC8M0pz0sCEA6L83cNktGW8Lth%2BTxBZr4%3D | US | der | 279 b | whitelisted |
276 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEAZnA1u7FP1jr8DWqFNO%2FhY%3D | US | der | 471 b | whitelisted |
276 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEATh56TcXPLzbcArQrhdFZ8%3D | US | der | 471 b | whitelisted |
276 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?8415dabc7c7f26a1 | US | compressed | 4.70 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
276 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
276 | iexplore.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
276 | iexplore.exe | 185.199.108.154:443 | github-releases.githubusercontent.com | GitHub, Inc. | NL | suspicious |
2268 | Skype.exe | 52.114.128.75:443 | pipe.skype.com | Microsoft Corporation | US | unknown |
2268 | Skype.exe | 52.174.193.75:443 | get.skype.com | Microsoft Corporation | NL | whitelisted |
2268 | Skype.exe | 13.107.42.23:443 | a.config.skype.com | Microsoft Corporation | US | suspicious |
2268 | Skype.exe | 23.47.208.146:443 | download.skype.com | NTT DOCOMO, INC. | US | unknown |
2268 | Skype.exe | 142.250.185.234:443 | www.googleapis.com | Google Inc. | US | whitelisted |
2268 | Skype.exe | 152.199.19.160:443 | bot-framework.azureedge.net | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
276 | iexplore.exe | 140.82.121.3:443 | github.com | — | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
github.com |
| malicious |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
github-releases.githubusercontent.com |
| whitelisted |
get.skype.com |
| whitelisted |
a.config.skype.com |
| whitelisted |
pipe.skype.com |
| whitelisted |
download.skype.com |
| whitelisted |
www.googleapis.com |
| whitelisted |
avatar.skype.com |
| whitelisted |