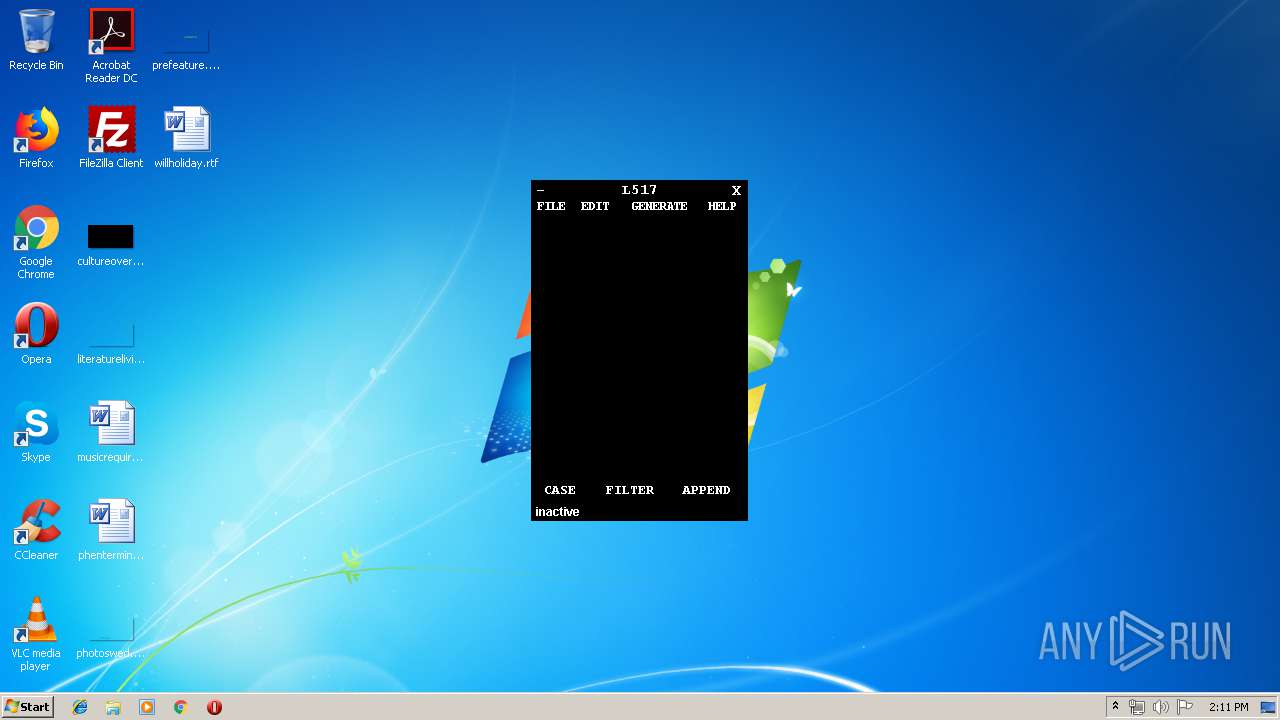
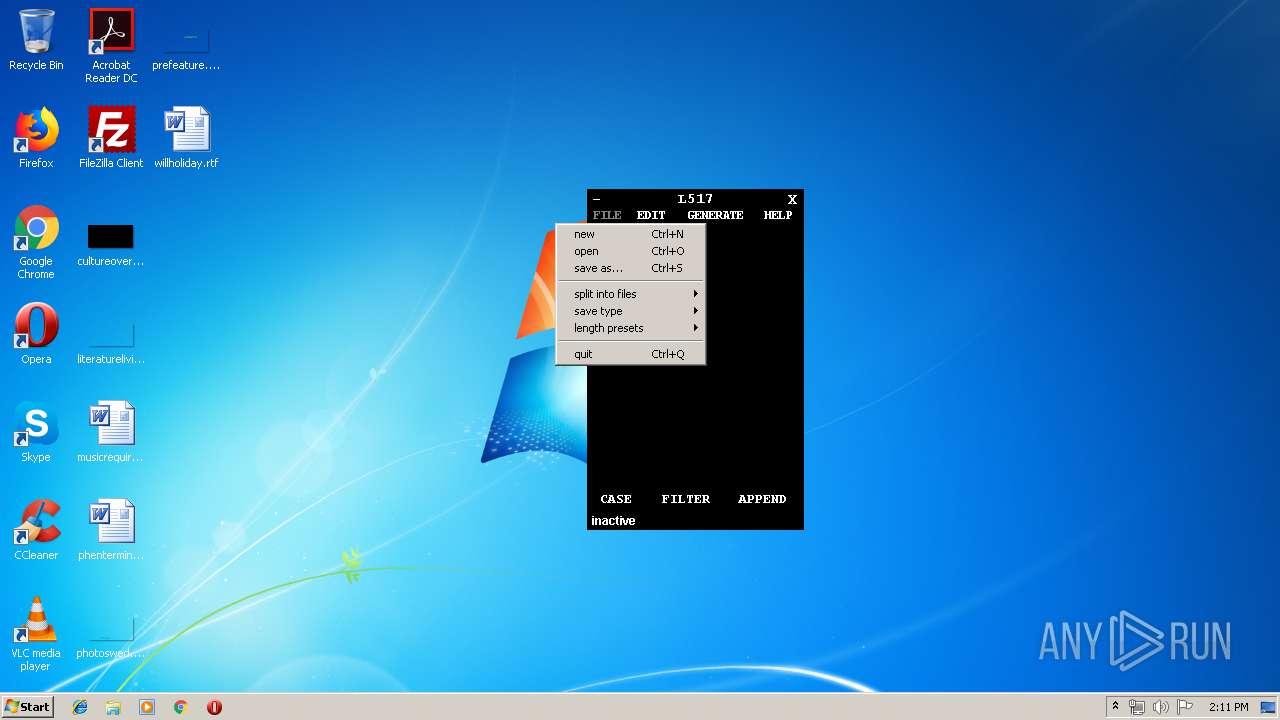
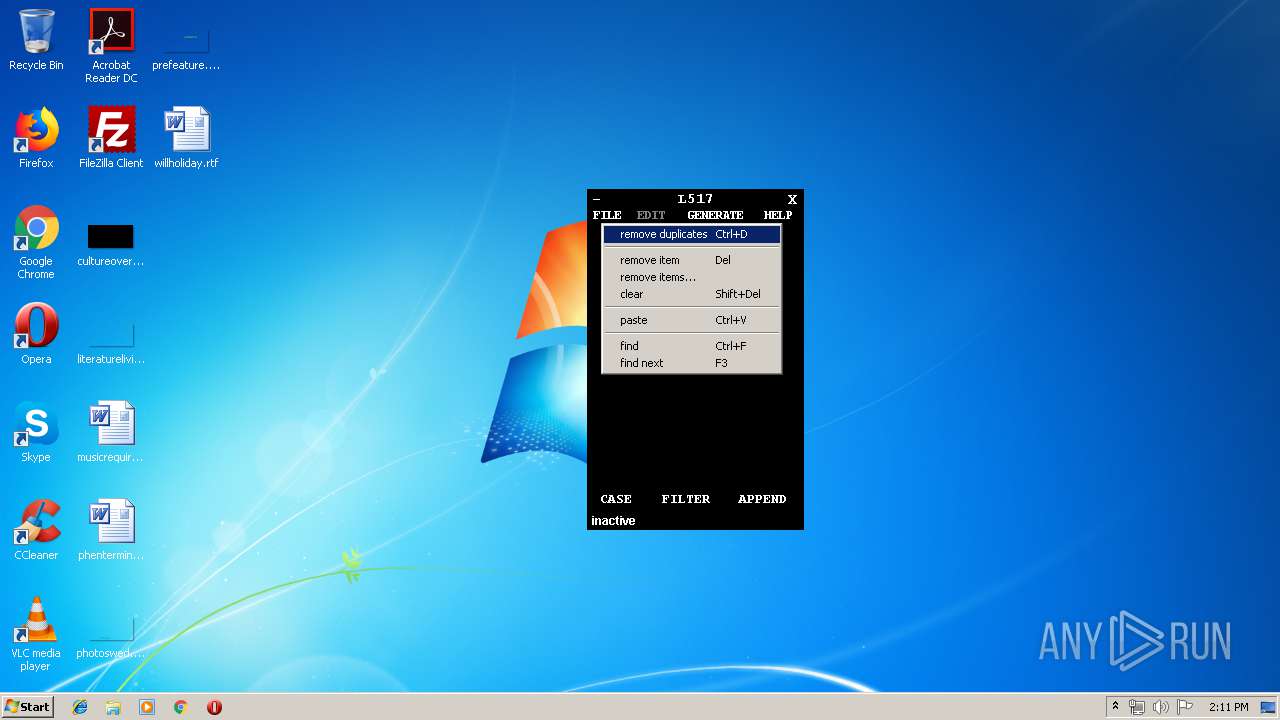
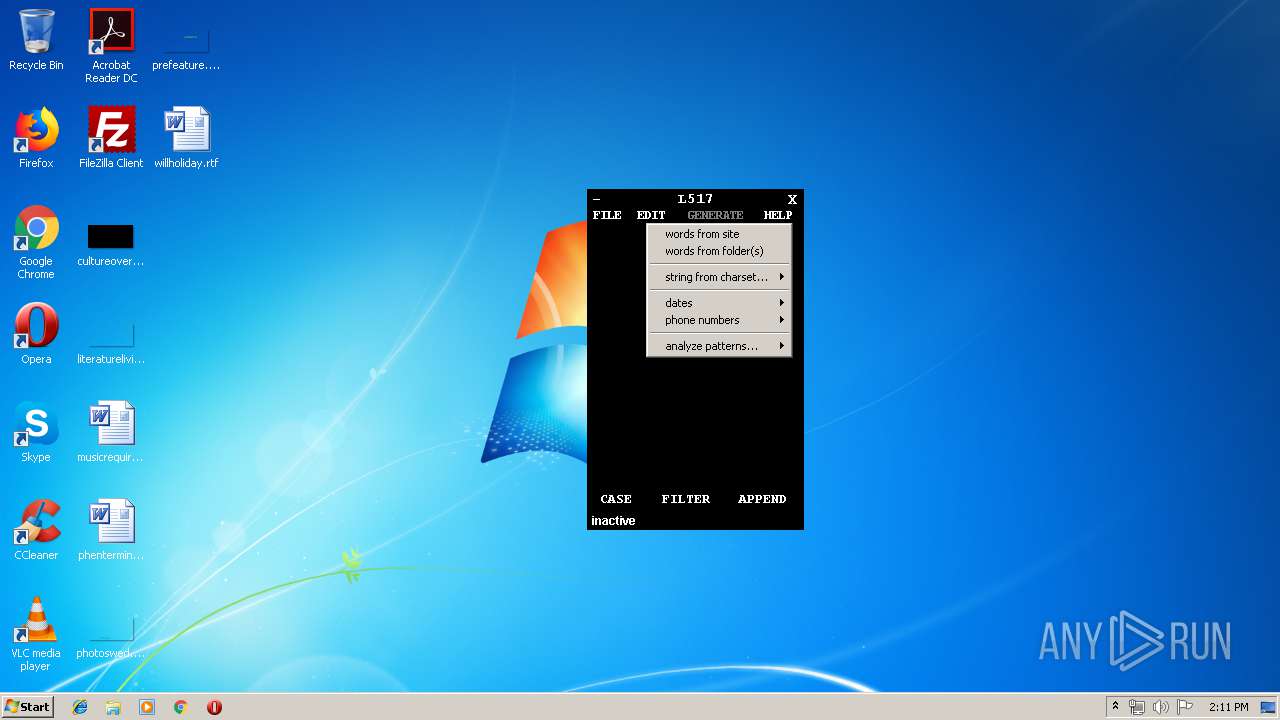
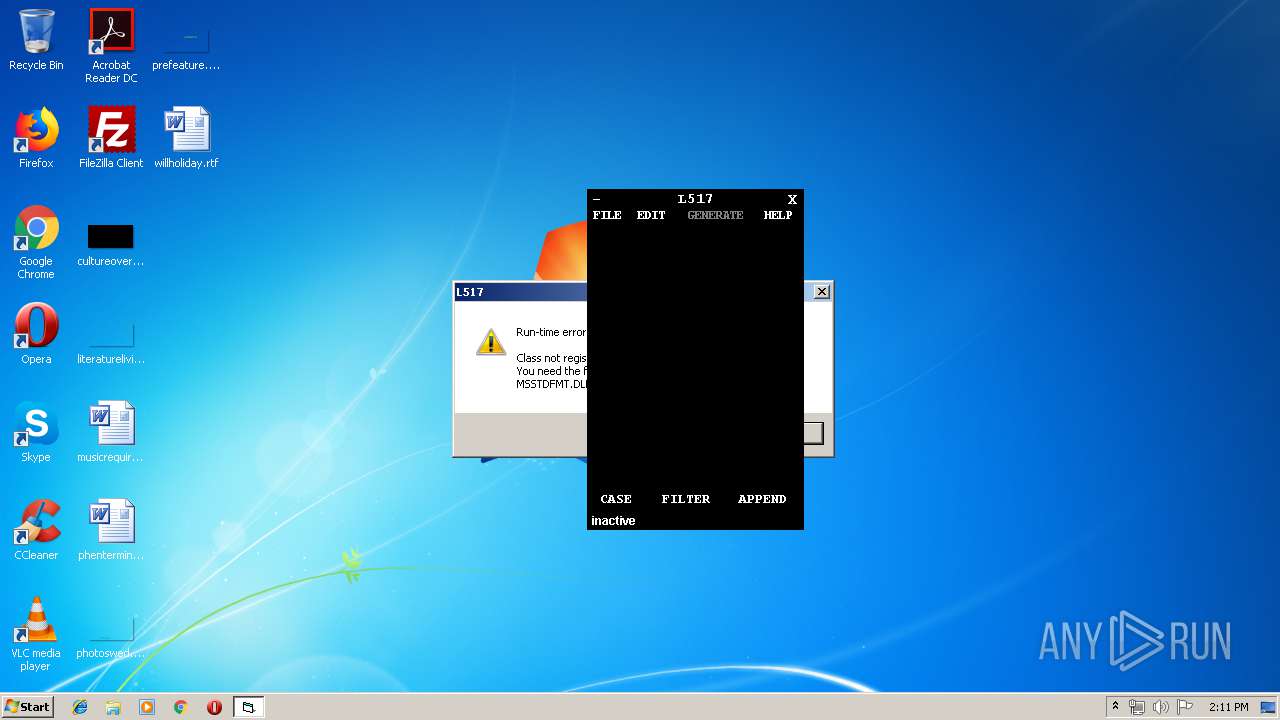
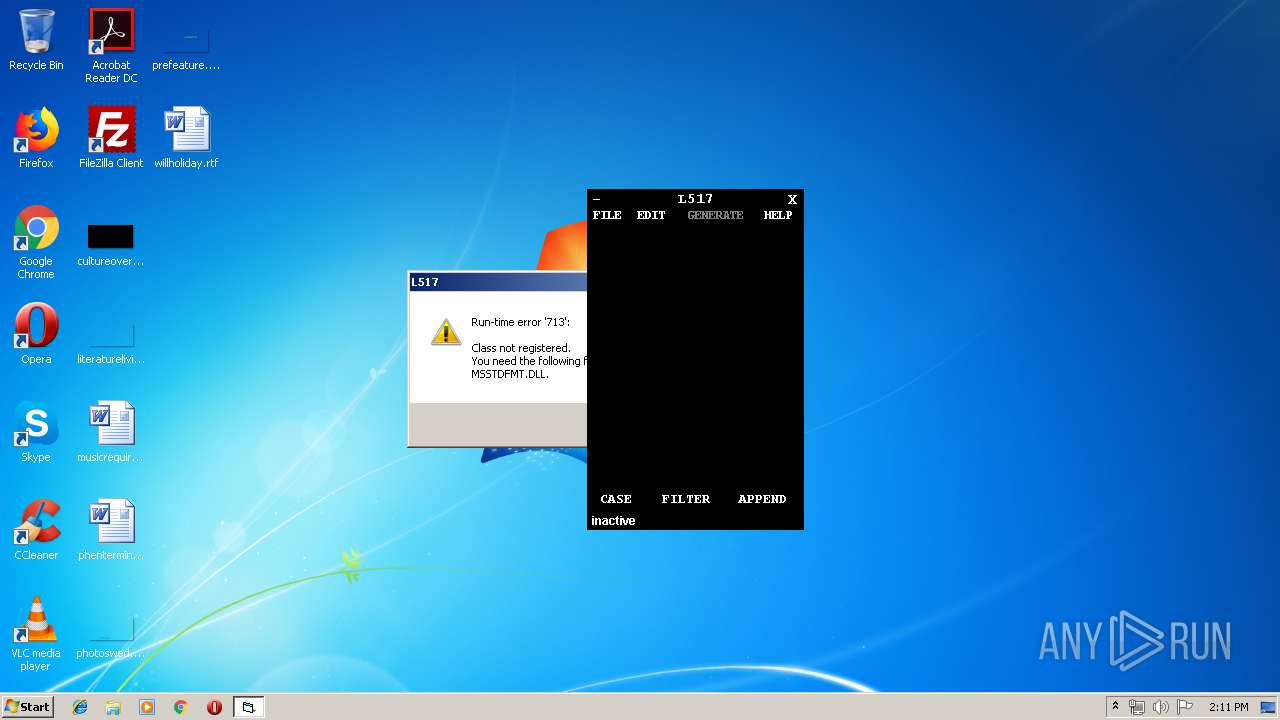
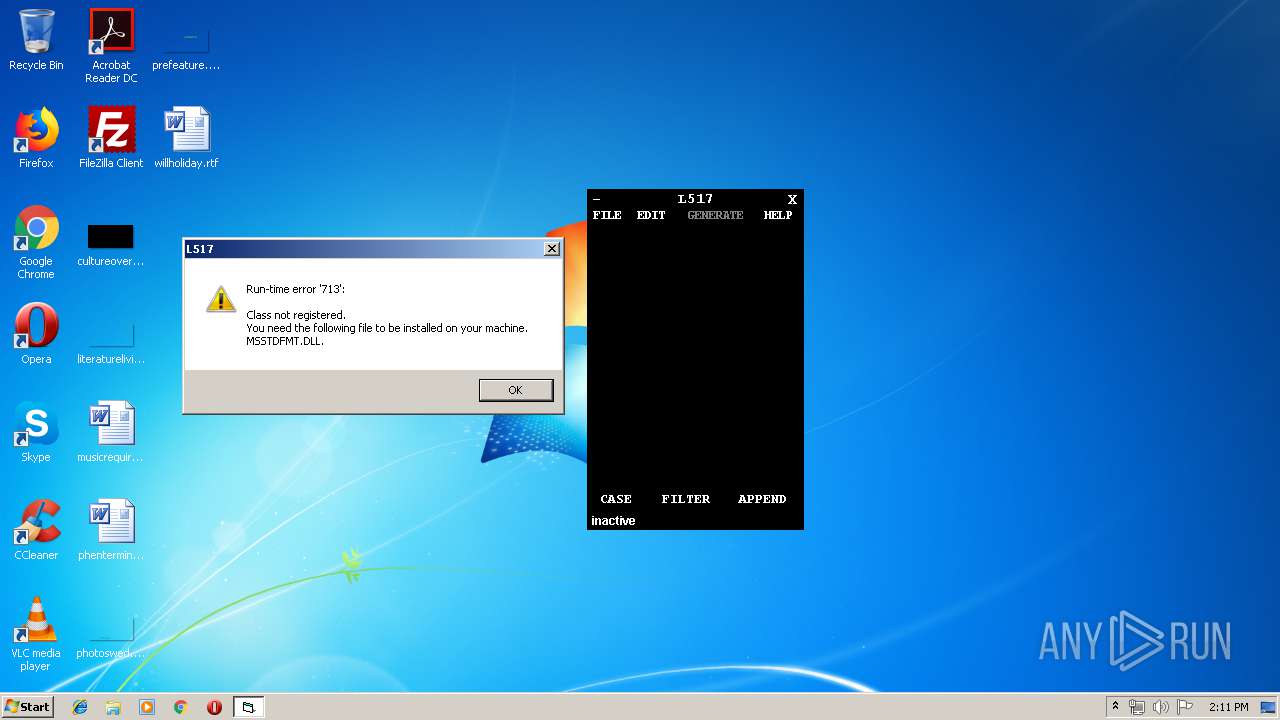
| File name: | L517 v0.994.exe |
| Full analysis: | https://app.any.run/tasks/b8a4cefc-04d8-4432-865f-b4dce92e8018 |
| Verdict: | No threats detected |
| Analysis date: | August 11, 2019, 13:10:48 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 06B53FED103F458FC133D73C6260C20E |
| SHA1: | 27CE2180A9BDA718AB47E57130747605BC1C32A9 |
| SHA256: | 02A2E1A808E7BFBC4C86ECE742D205255260324E6AD67B730AC12E9B9F5828AE |
| SSDEEP: | 24576:ggQYMcIULwDtKvVgRC41j9KmqPlDTQL2s:dvMuLSKduZYXP |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Microsoft Visual Basic 6 (42.9) |
|---|---|---|
| .exe | | | Win32 EXE PECompact compressed (generic) (21.7) |
| .exe | | | Win32 Executable MS Visual C++ (generic) (16.3) |
| .exe | | | Win64 Executable (generic) (14.4) |
| .exe | | | Win32 Executable (generic) (2.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2012:02:25 21:19:36+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 507904 |
| InitializedDataSize: | 679936 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2b44 |
| OSVersion: | 4 |
| ImageVersion: | 0.9 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.9.0.94 |
| ProductVersionNumber: | 0.9.0.94 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| Comments: | 0.994: Fixed removal of first character |
| CompanyName: | derv82@gmail.com |
| LegalCopyright: | open source. code available @ code.google.com/p/l517 |
| ProductName: | L517 |
| FileVersion: | 0.09.0094 |
| ProductVersion: | 0.09.0094 |
| InternalName: | L517 v0.9994 |
| OriginalFileName: | L517 v0.9994.exe |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 25-Feb-2012 20:19:36 |
| Detected languages: |
|
| Comments: | 0.994: Fixed removal of first character |
| CompanyName: | derv82@gmail.com |
| LegalCopyright: | open source. code available @ code.google.com/p/l517 |
| ProductName: | L517 |
| FileVersion: | 0.09.0094 |
| ProductVersion: | 0.09.0094 |
| InternalName: | L517 v0.9994 |
| OriginalFilename: | L517 v0.9994.exe |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000B8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 25-Feb-2012 20:19:36 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0007BF28 | 0x0007C000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.76887 |
.data | 0x0007D000 | 0x00002C94 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00080000 | 0x000A2A48 | 0x000A3000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.25668 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.40761 | 824 | Unicode (UTF 16LE) | English - United States | RT_VERSION |
101 | 6.27348 | 663552 | Unicode (UTF 16LE) | English - United States | EXE |
30001 | 2.57965 | 304 | Unicode (UTF 16LE) | UNKNOWN | RT_ICON |
30002 | 1.76987 | 744 | Unicode (UTF 16LE) | UNKNOWN | RT_ICON |
30003 | 2.07177 | 296 | Unicode (UTF 16LE) | UNKNOWN | RT_ICON |
Imports
MSVBVM60.DLL |
Total processes
34
Monitored processes
1
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 4024 | "C:\Users\admin\AppData\Local\Temp\L517 v0.994.exe" | C:\Users\admin\AppData\Local\Temp\L517 v0.994.exe | — | explorer.exe | |||||||||||
User: admin Company: derv82@gmail.com Integrity Level: MEDIUM Exit code: 0 Version: 0.09.0094 Modules
| |||||||||||||||
Total events
230
Read events
226
Write events
4
Delete events
0
Modification events
| (PID) Process: | (4024) L517 v0.994.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductNonBootFiles |
Value: 1326120961 | |||
| (PID) Process: | (4024) L517 v0.994.exe | Key: | HKEY_CURRENT_USER\Software\VB and VBA Program Settings\L517 |
| Operation: | write | Name: | leetspeak |
Value: a=a,4,@
b=b,8
c=c,(
d=d
e=e,3
f=f
g=g,9
h=h,#
i=i,1,|,!
j=j
k=k
l=l,7,1,|,!
m=m
n=n
o=o,0
p=p
q=q
r=r
s=s,5,$
t=t,7,+
u=u
v=v
w=w
x=x
y=y
z=z,2
| |||
| (PID) Process: | (4024) L517 v0.994.exe | Key: | HKEY_CURRENT_USER\Software\VB and VBA Program Settings\L517 |
| Operation: | write | Name: | charset |
Value: numeric = [0123456789]
numeric-space = [0123456789 ]
ualpha = [ABCDEFGHIJKLMNOPQRSTUVWXYZ]
ualpha-space = [ABCDEFGHIJKLMNOPQRSTUVWXYZ ]
ualpha-numeric = [ABCDEFGHIJKLMNOPQRSTUVWXYZ0123456789]
ualpha-numeric-space = [ABCDEFGHIJKLMNOPQRSTUVWXYZ0123456789 ]
ualpha-numeric-symbol = [ABCDEFGHIJKLMNOPQRSTUVWXYZ0123456789!@#$%^&*()-_+=]
ualpha-numeric-symbol-space = [ABCDEFGHIJKLMNOPQRSTUVWXYZ0123456789!@#$%^&*()-_+= ]
ualpha-numeric-all = [ABCDEFGHIJKLMNOPQRSTUVWXYZ0123456789!@#$%^&*()-_+=~`[]{}|\:;"'<>,.?/]
ualpha-numeric-all-space = [ABCDEFGHIJKLMNOPQRSTUVWXYZ0123456789!@#$%^&*()-_+=~`[]{}|\:;"'<>,.?/ ]
lalpha = [abcdefghijklmnopqrstuvwxyz]
lalpha-space = [abcdefghijklmnopqrstuvwxyz ]
lalpha-numeric = [abcdefghijklmnopqrstuvwxyz0123456789]
lalpha-numeric-space = [abcdefghijklmnopqrstuvwxyz0123456789 ]
lalpha-numeric-symbol = [abcdefghijklmnopqrstuvwxyzäöüß0123456789!@#$%^&*()-_+="]
lalpha-numeric-symbol-space = [abcdefghijklmnopqrstuvwxyzäöüß0123456789!@#$%^&*()-_+=" ]
lalpha-numeric-all = [abcdefghijklmnopqrstuvwxyzäöüß0123456789!@#$%^&*()-_+=~`[]{}|\:;"'<>,.?/]
lalpha-numeric-all-space = [abcdefghijklmnopqrstuvwxyzäöüß0123456789!@#$%^&*()-_+=~`[]{}|\:;"'<>,.?/ ]
mixalpha = [abcdefghijklmnopqrstuvwxyzABCDEFGHIJKLMNOPQRSTUVWXYZ]
mixalpha-space = [abcdefghijklmnopqrstuvwxyzABCDEFGHIJKLMNOPQRSTUVWXYZ ]
mixalpha-numeric = [abcdefghijklmnopqrstuvwxyzABCDEFGHIJKLMNOPQRSTUVWXYZ0123456789]
mixalpha-numeric-space = [abcdefghijklmnopqrstuvwxyzABCDEFGHIJKLMNOPQRSTUVWXYZ0123456789 ]
mixalpha-numeric-symbol = [abcdefghijklmnopqrstuvwxyzABCDEFGHIJKLMNOPQRSTUVWXYZ0123456789!@#$%^&*()-_+=]
mixalpha-numeric-symbol-space = [abcdefghijklmnopqrstuvwxyzABCDEFGHIJKLMNOPQRSTUVWXYZ0123456789!@#$%^&*()-_+= ]
mixalpha-numeric-all = [abcdefghijklmnopqrstuvwxyzABCDEFGHIJKLMNOPQRSTUVWXYZ0123456789!@#$%^&*()-_+=~`[]{}|\:;"'<>,.?/]
mixalpha-numeric-all-space = [abcdefghijklmnopqrstuvwxyzABCDEFGHIJKLMNOPQRSTUVWXYZ0123456789!@#$%^&*()-_+=~`[]{}|\:;"'<>,.?/ ] | |||
| (PID) Process: | (4024) L517 v0.994.exe | Key: | HKEY_CURRENT_USER\Software\VB and VBA Program Settings\L517 |
| Operation: | write | Name: | firstload? |
Value: Not_anymore | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report