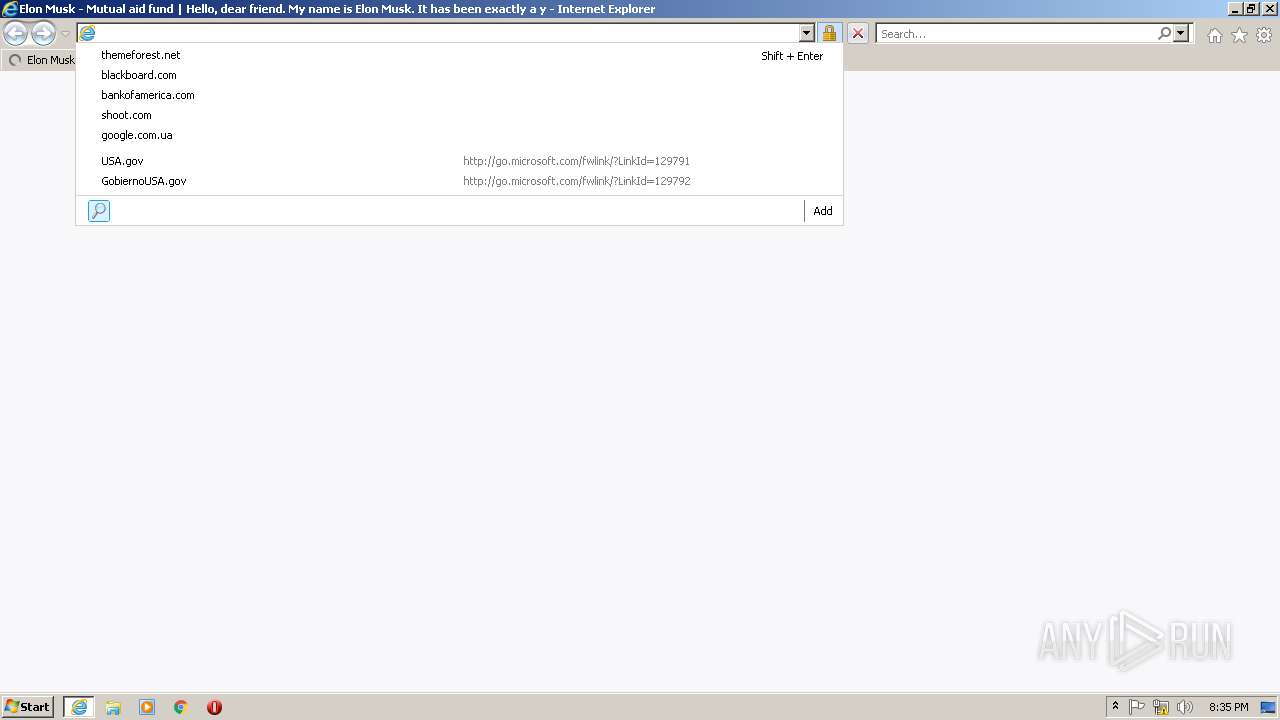
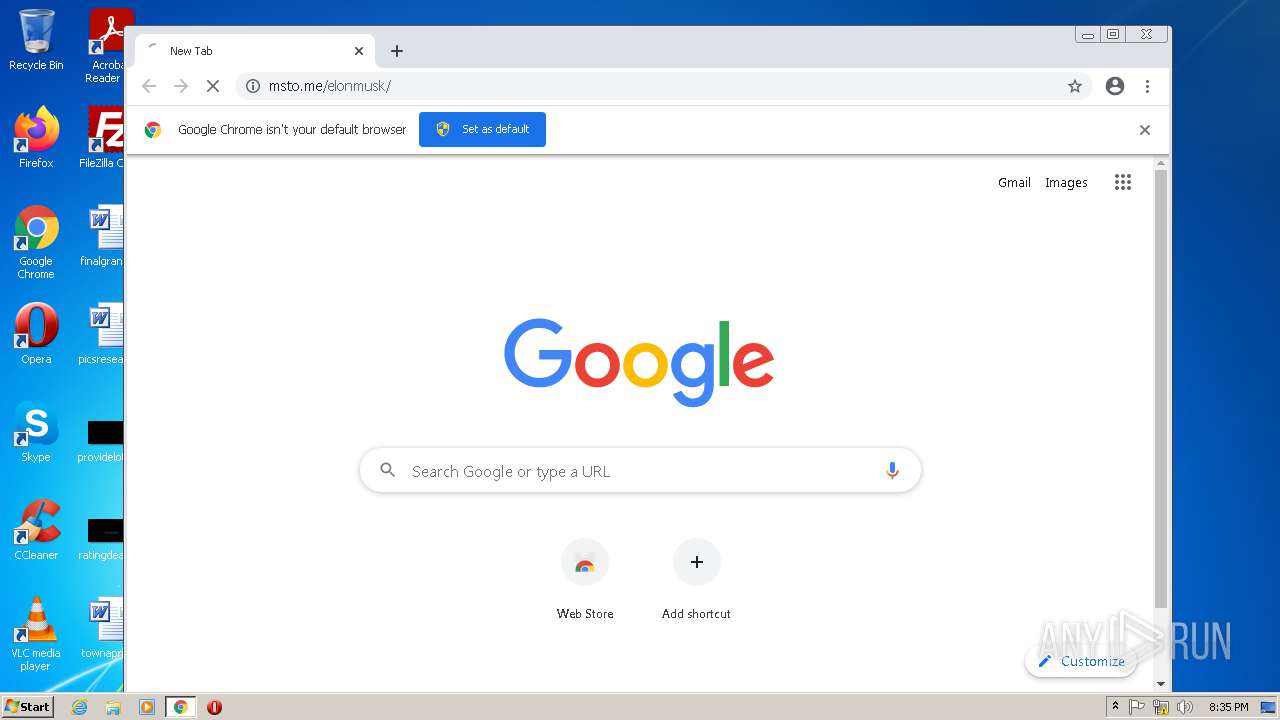
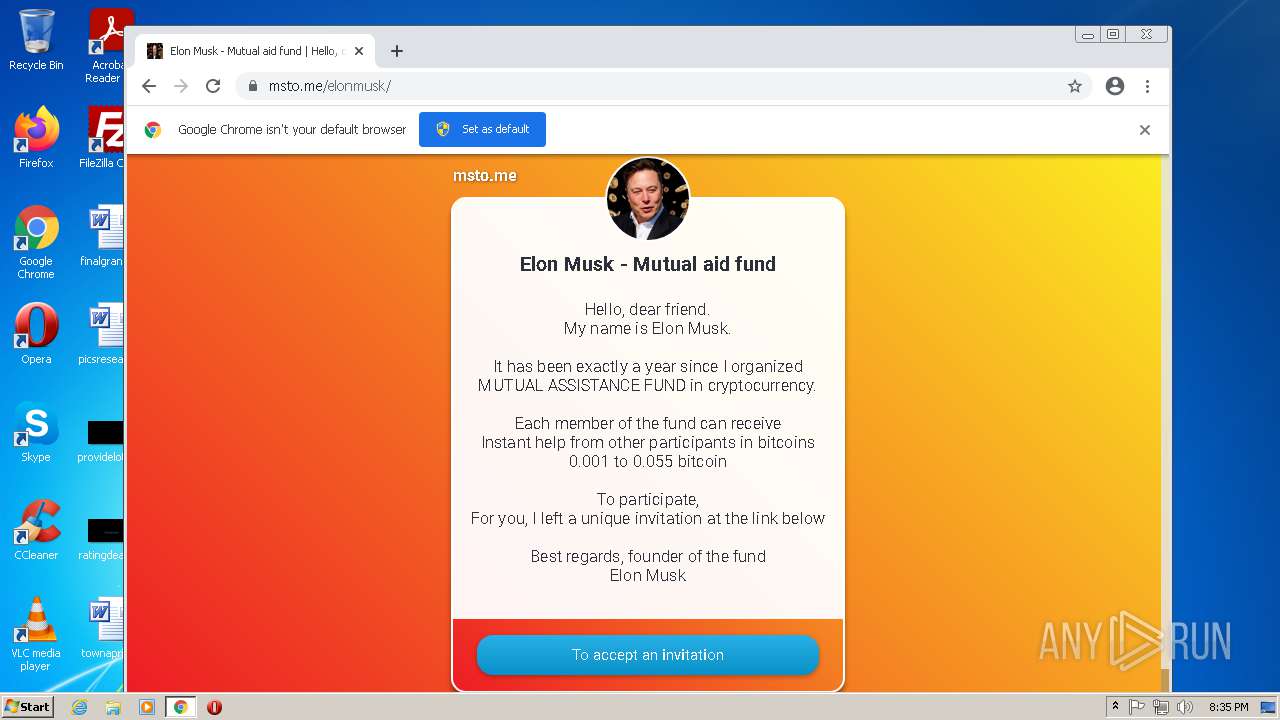
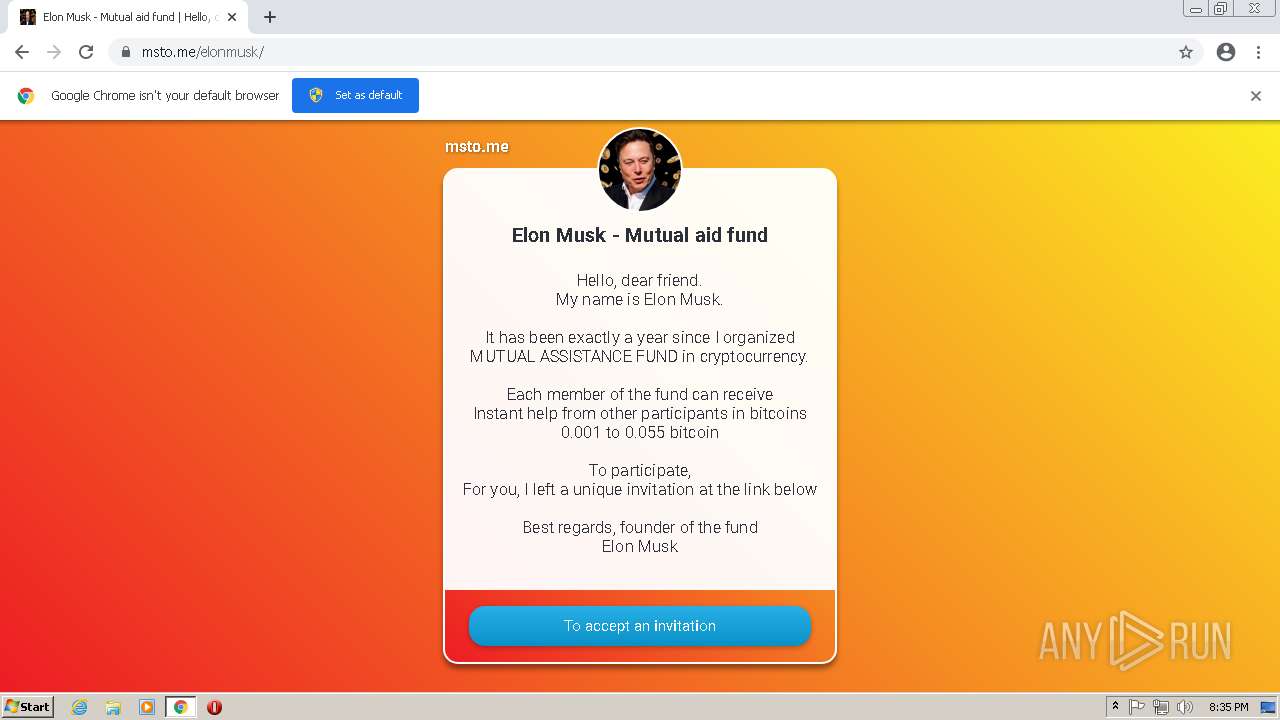
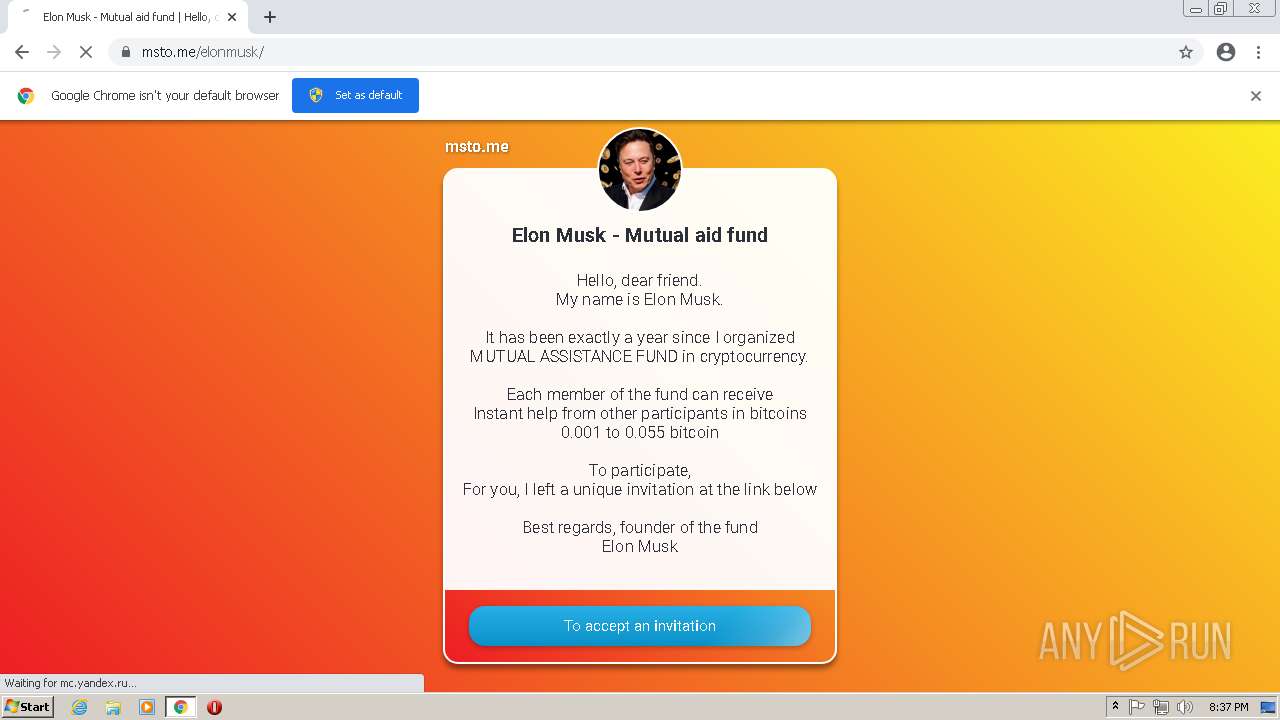
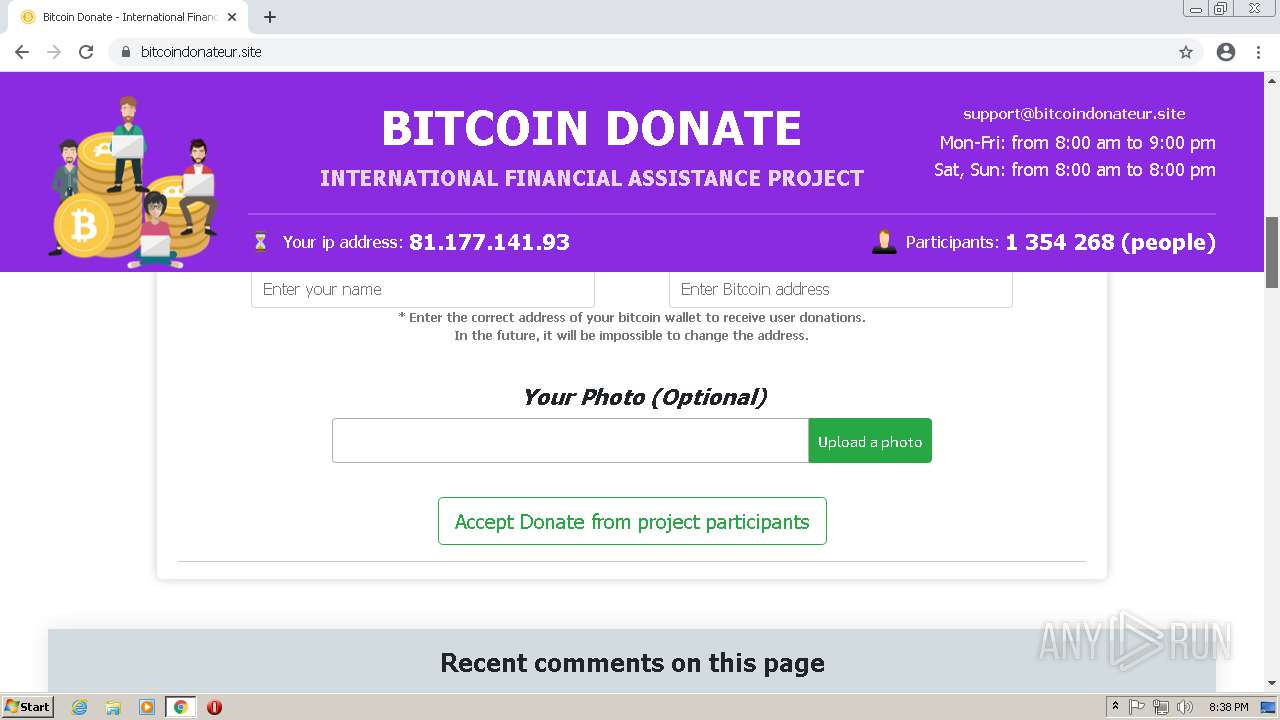
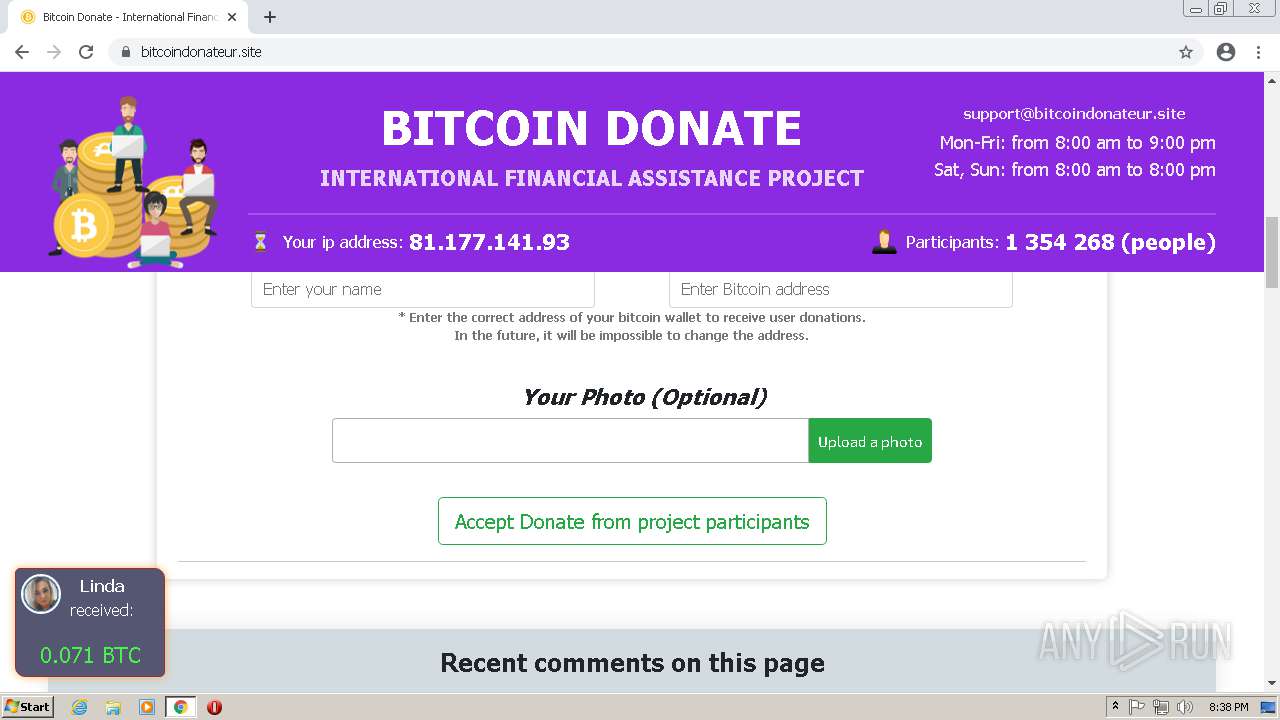
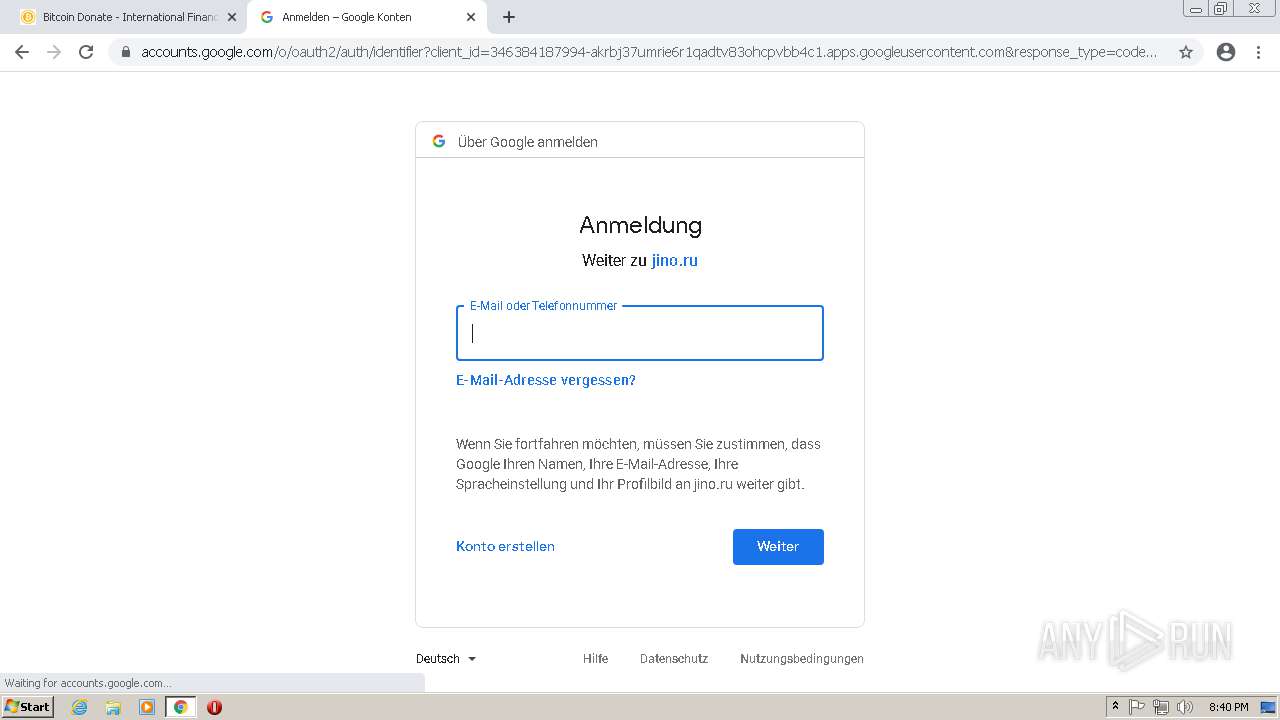
| URL: | https://msto.me/elonmusk/ |
| Full analysis: | https://app.any.run/tasks/29e4da3b-78a2-4240-82b1-9c8a3388d7a2 |
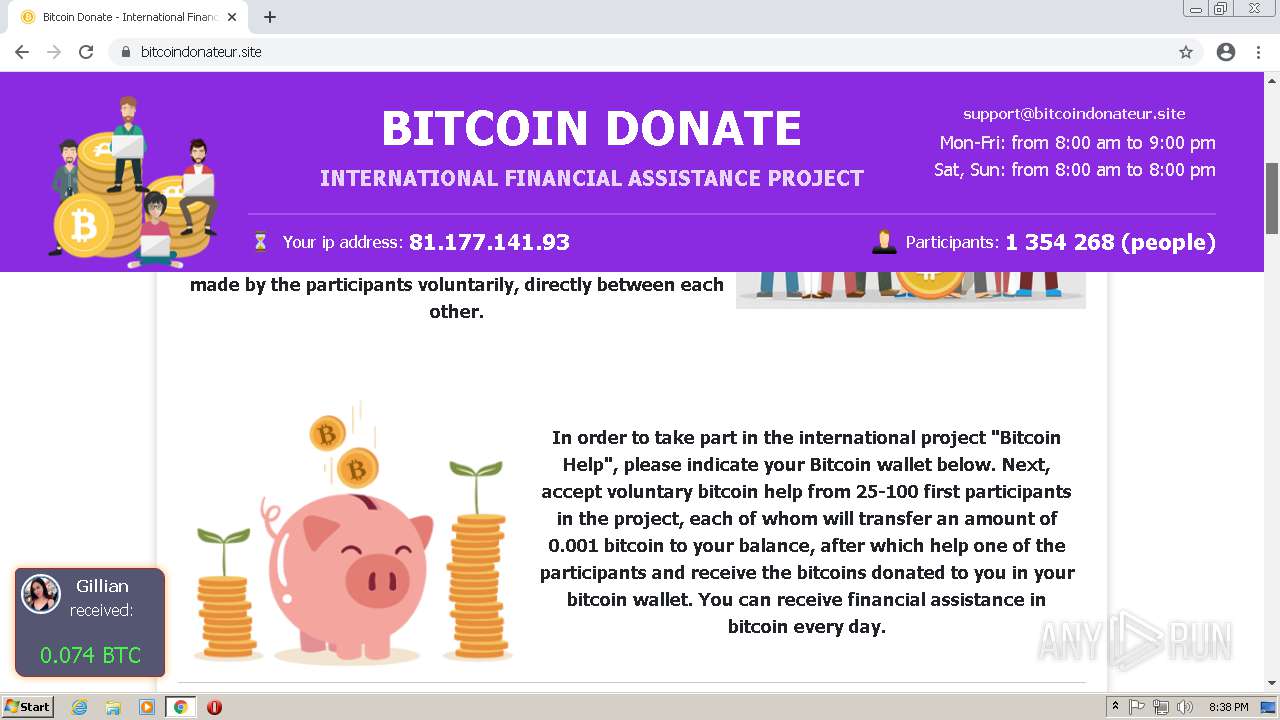
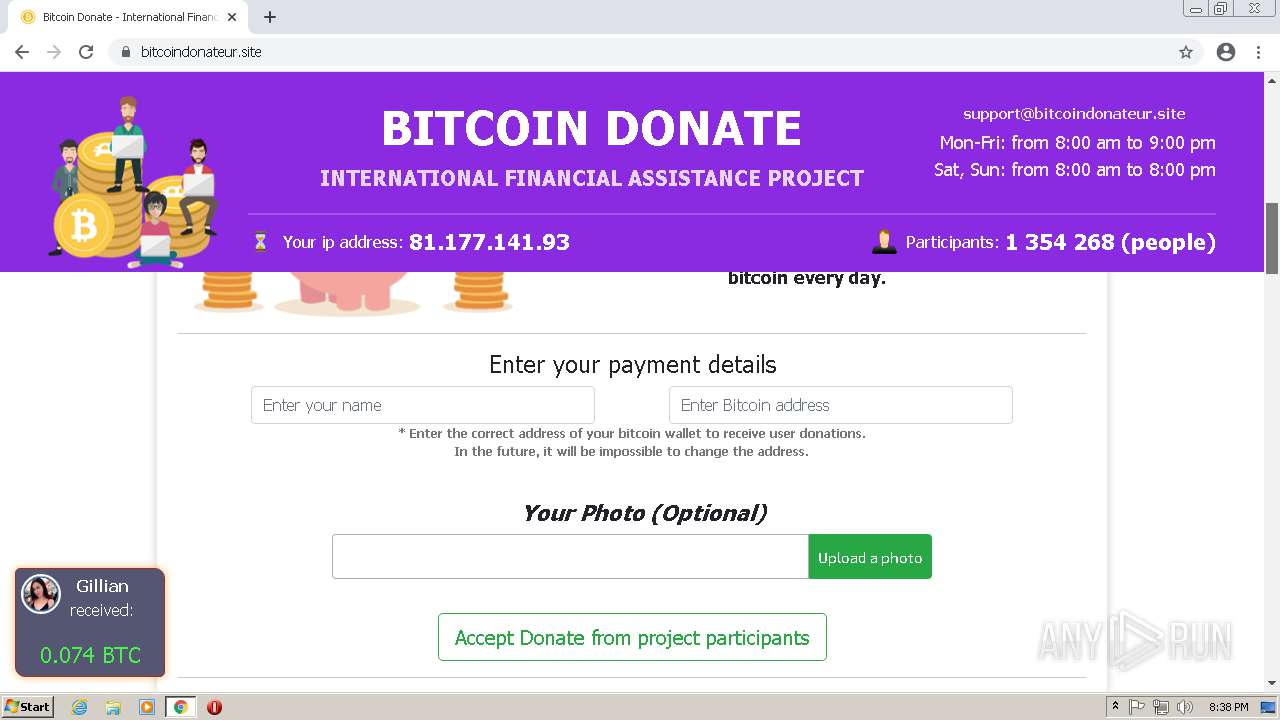
| Verdict: | Malicious activity |
| Analysis date: | September 15, 2021, 19:35:22 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 869A8D8CE2104CD2D7CDD38B85A1B4A6 |
| SHA1: | 32171828A070B43AE4B2D8B67E8555C365346104 |
| SHA256: | 029D071ADC7CFC35874E330D557D3C0C7A10F91535011ABDD8D2C9E71F88B4AF |
| SSDEEP: | 3:N8HQIA4+:2w++ |
MALICIOUS
Drops executable file immediately after starts
- chrome.exe (PID: 2448)
SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 1608)
Modifies files in Chrome extension folder
- chrome.exe (PID: 1832)
Executable content was dropped or overwritten
- chrome.exe (PID: 2448)
Drops a file that was compiled in debug mode
- chrome.exe (PID: 2448)
INFO
Reads the computer name
- iexplore.exe (PID: 2576)
- iexplore.exe (PID: 1608)
- chrome.exe (PID: 1832)
- chrome.exe (PID: 644)
- chrome.exe (PID: 2392)
- chrome.exe (PID: 3792)
- chrome.exe (PID: 3992)
- chrome.exe (PID: 3012)
- chrome.exe (PID: 2112)
- chrome.exe (PID: 3376)
- chrome.exe (PID: 1848)
- chrome.exe (PID: 3212)
- chrome.exe (PID: 124)
Checks supported languages
- iexplore.exe (PID: 2576)
- iexplore.exe (PID: 1608)
- chrome.exe (PID: 1832)
- chrome.exe (PID: 188)
- chrome.exe (PID: 644)
- chrome.exe (PID: 2532)
- chrome.exe (PID: 2956)
- chrome.exe (PID: 2392)
- chrome.exe (PID: 1008)
- chrome.exe (PID: 3792)
- chrome.exe (PID: 3992)
- chrome.exe (PID: 2716)
- chrome.exe (PID: 756)
- chrome.exe (PID: 2764)
- chrome.exe (PID: 2592)
- chrome.exe (PID: 624)
- chrome.exe (PID: 2352)
- chrome.exe (PID: 3276)
- chrome.exe (PID: 3012)
- chrome.exe (PID: 2112)
- chrome.exe (PID: 3376)
- chrome.exe (PID: 1440)
- chrome.exe (PID: 1848)
- chrome.exe (PID: 3264)
- chrome.exe (PID: 4012)
- chrome.exe (PID: 3016)
- chrome.exe (PID: 3864)
- chrome.exe (PID: 3700)
- chrome.exe (PID: 1908)
- chrome.exe (PID: 2896)
- chrome.exe (PID: 3528)
- chrome.exe (PID: 752)
- chrome.exe (PID: 3456)
- chrome.exe (PID: 708)
- chrome.exe (PID: 2996)
- chrome.exe (PID: 3556)
- chrome.exe (PID: 2448)
- chrome.exe (PID: 2112)
- chrome.exe (PID: 124)
- chrome.exe (PID: 3224)
- chrome.exe (PID: 3212)
- chrome.exe (PID: 124)
- chrome.exe (PID: 3412)
- chrome.exe (PID: 3272)
- chrome.exe (PID: 1976)
- chrome.exe (PID: 372)
Changes internet zones settings
- iexplore.exe (PID: 2576)
Reads settings of System Certificates
- iexplore.exe (PID: 1608)
- iexplore.exe (PID: 2576)
- chrome.exe (PID: 2392)
Application launched itself
- iexplore.exe (PID: 2576)
- chrome.exe (PID: 1832)
Creates files in the user directory
- iexplore.exe (PID: 1608)
Reads internet explorer settings
- iexplore.exe (PID: 1608)
Reads the date of Windows installation
- iexplore.exe (PID: 2576)
- chrome.exe (PID: 2112)
Manual execution by user
- chrome.exe (PID: 1832)
Checks Windows Trust Settings
- iexplore.exe (PID: 1608)
- iexplore.exe (PID: 2576)
Reads the hosts file
- chrome.exe (PID: 1832)
- chrome.exe (PID: 2392)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
81
Monitored processes
46
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 124 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1056,3765461498800828892,6582256617557339479,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3572 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 124 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1056,3765461498800828892,6582256617557339479,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=2780 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 188 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=86.0.4240.198 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6e0ad988,0x6e0ad998,0x6e0ad9a4 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 372 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1056,3765461498800828892,6582256617557339479,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=29 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2456 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 624 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1056,3765461498800828892,6582256617557339479,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2952 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 644 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1056,3765461498800828892,6582256617557339479,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgAAAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --mojo-platform-channel-handle=1036 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 708 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1056,3765461498800828892,6582256617557339479,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3700 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 752 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1056,3765461498800828892,6582256617557339479,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=30 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3640 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 756 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1056,3765461498800828892,6582256617557339479,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=10 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2924 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1008 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1056,3765461498800828892,6582256617557339479,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2924 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
28 099
Read events
27 860
Write events
230
Delete events
9
Modification events
| (PID) Process: | (2576) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (2576) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (2576) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30911080 | |||
| (PID) Process: | (2576) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (2576) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30911080 | |||
| (PID) Process: | (2576) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2576) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2576) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2576) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2576) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
1
Suspicious files
175
Text files
379
Unknown types
43
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1608 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:29ACDBFBDFCF01CC9E0A64FCF6516445 | SHA256:A208069D6ADDB4DDF30EF63F279319ECFDA62FEBB5CB441E7DBD983232380396 | |||
| 1608 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\card[1].js | text | |
MD5:0BEEE1C256F886B6EF3397AEFFBFECDC | SHA256:92CF25B13AA1452BBA71916E09EE41327BFF8F06461CC08614A9A0DFEE1EBE5B | |||
| 1608 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\CAF4703619713E3F18D8A9D5D88D6288_A7725538C46DE2D0088EE44974E2CEBA | der | |
MD5:DE27664DA1E04C94901FCC3880064613 | SHA256:7E59CE8A2D7D1E1201E535A3175BFAF239B9F5DA7BE265C18C5FF1E1BC696282 | |||
| 1608 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\elonmusk[1].htm | html | |
MD5:7010869E5D6558707E44093C77D8AE6C | SHA256:F48D1D046B1ACC297926E1AD55F9280258943005E00A26E8560A8C041B371269 | |||
| 1608 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\103621DE9CD5414CC2538780B4B75751 | binary | |
MD5:77CA8547BCD6395A2E3D3E416FFE1C24 | SHA256:C14205F93D7F9BD64A17ABB1D5458302080A766C9C3C86BD9688E4967A8E73D2 | |||
| 1608 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\card20210915223544[1].css | text | |
MD5:397693435F33C3F494732EDA1D26F8AA | SHA256:E3BE0FAE48D55416ABD250B6E4E8CBCE5298A1654291FB44500B5FF782EEC713 | |||
| 1608 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:C62B2253EA8697558AC6324A38254C93 | SHA256:A99172E4D35E63662C1C468F60BDDBDDCBEAE0F5973D66AA02DAC8D586B044C5 | |||
| 1608 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\644B8874112055B5E195ECB0E8F243A4 | binary | |
MD5:FC2C4B51F3617120FA384912525442D7 | SHA256:83E6E07D21D78D1E33D5C1E4A37ED72A79361F02B174947A00A657078FC51FD9 | |||
| 1608 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\EDC238BFF48A31D55A97E1E93892934B_C20E0DA2D0F89FE526E1490F4A2EE5AB | binary | |
MD5:8A26D25736A1690D193262DF9F3CCAFF | SHA256:60343721415DC4346367A978007E274E0BD8FB37CDA8F67BE8CEA0B732F3467B | |||
| 1608 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\644B8874112055B5E195ECB0E8F243A4 | der | |
MD5:DF9D36B73932F7D0866708AA05FB6441 | SHA256:B66F1A261FE4BE988FD7CE26D1E5BB91469466CA19DF602644BEB37DC0E0BC53 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
89
TCP/UDP connections
157
DNS requests
106
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1608 | iexplore.exe | GET | 200 | 104.89.32.83:80 | http://x1.c.lencr.org/ | NL | der | 717 b | whitelisted |
1608 | iexplore.exe | GET | 200 | 209.197.3.8:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?54cfa1e73b16afee | US | compressed | 4.70 Kb | whitelisted |
1608 | iexplore.exe | GET | 200 | 95.101.89.75:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgPrSBAD11yJcWE9MuTEfblnZQ%3D%3D | unknown | der | 503 b | shared |
1608 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEATh56TcXPLzbcArQrhdFZ8%3D | US | der | 471 b | whitelisted |
1608 | iexplore.exe | GET | 200 | 95.101.89.35:80 | http://crl.identrust.com/DSTROOTCAX3CRL.crl | unknown | der | 1.16 Kb | whitelisted |
2576 | iexplore.exe | GET | 304 | 209.197.3.8:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?44f091639166dd34 | US | — | — | whitelisted |
1608 | iexplore.exe | GET | 200 | 142.250.185.195:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQDOOuOfV4qUFgoAAAAA%2B3tK | US | der | 472 b | whitelisted |
2392 | chrome.exe | GET | 302 | 142.250.185.174:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzI0QUFXNV9zT2RvdUwyMERESEZGVmJnQQ/1.0.0.6_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 592 b | whitelisted |
— | — | GET | 302 | 142.250.185.174:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/ac7y3pd55n533gqiwnv4gjrkib4a_2697/jflookgnkcckhobaglndicnbbgbonegd_2697_all_acuwwciadg5xuwmiw5gvwaawxg3a.crx3 | US | html | 564 b | whitelisted |
1608 | iexplore.exe | GET | 200 | 142.250.185.195:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | der | 1.41 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1608 | iexplore.exe | 83.220.173.134:443 | msto.me | JSC ISPsystem | RU | unknown |
1608 | iexplore.exe | 209.197.3.8:80 | ctldl.windowsupdate.com | Highwinds Network Group, Inc. | US | whitelisted |
1608 | iexplore.exe | 104.89.32.83:80 | x1.c.lencr.org | Akamai Technologies, Inc. | NL | suspicious |
1608 | iexplore.exe | 95.101.89.75:80 | r3.o.lencr.org | Akamai International B.V. | — | unknown |
1608 | iexplore.exe | 95.101.89.35:80 | crl.identrust.com | Akamai International B.V. | — | suspicious |
1608 | iexplore.exe | 172.217.19.106:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
1608 | iexplore.exe | 142.250.186.104:443 | www.googletagmanager.com | Google Inc. | US | suspicious |
2576 | iexplore.exe | 209.197.3.8:80 | ctldl.windowsupdate.com | Highwinds Network Group, Inc. | US | whitelisted |
2576 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2392 | chrome.exe | 142.250.180.195:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
msto.me |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
crl.identrust.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
r3.o.lencr.org |
| shared |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
connect.facebook.net |
| whitelisted |