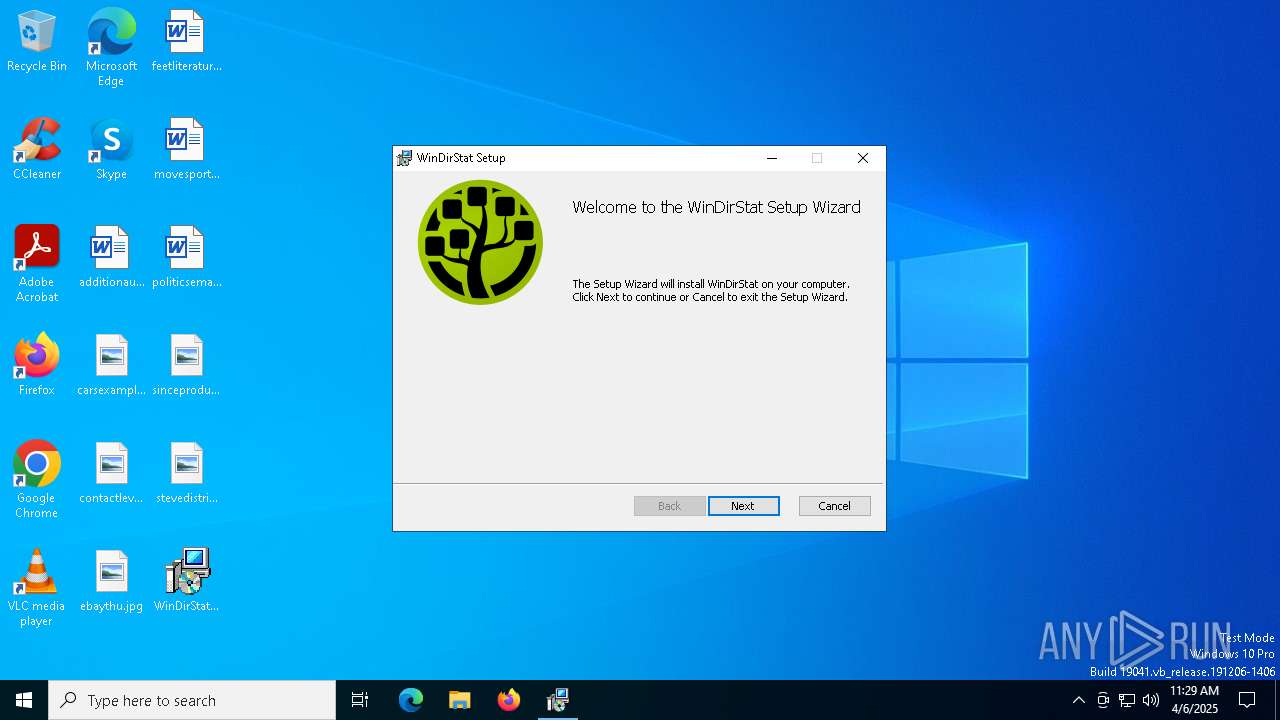
| File name: | WinDirStat-x64.msi |
| Full analysis: | https://app.any.run/tasks/5e22e0fe-ca96-4484-a4f8-6493ef22217c |
| Verdict: | Malicious activity |
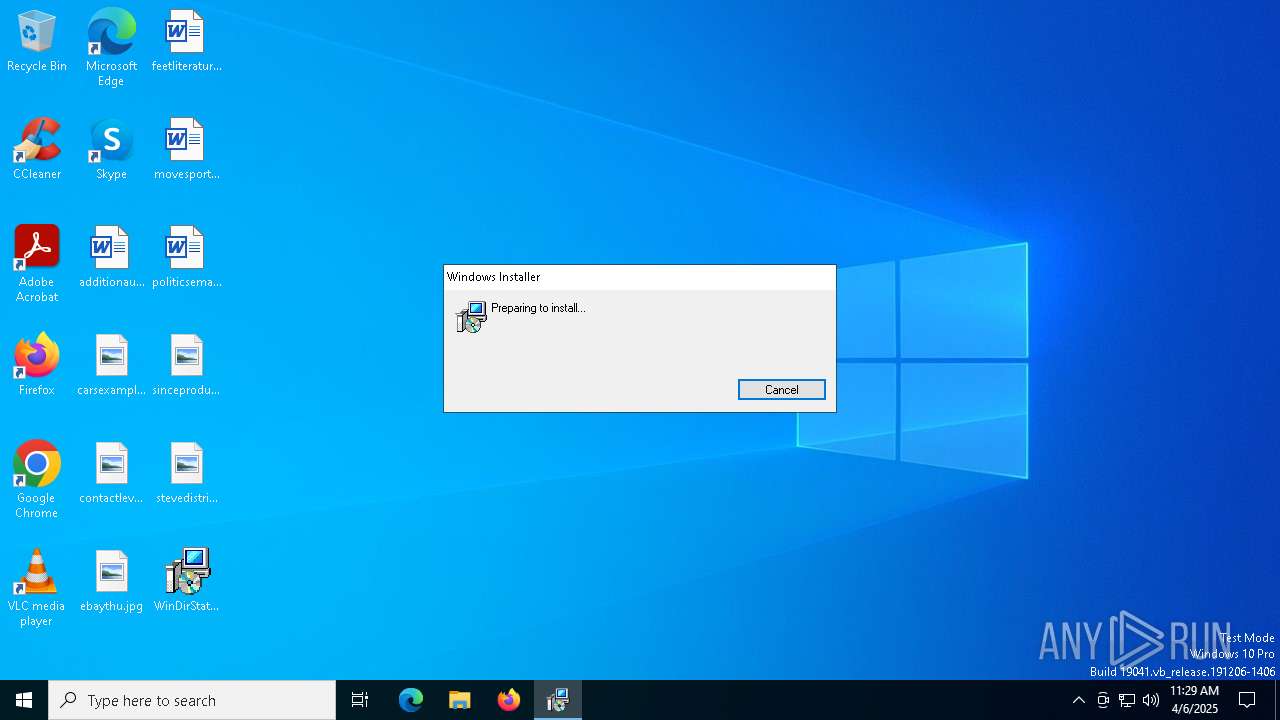
| Analysis date: | April 06, 2025, 11:28:55 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-msi |
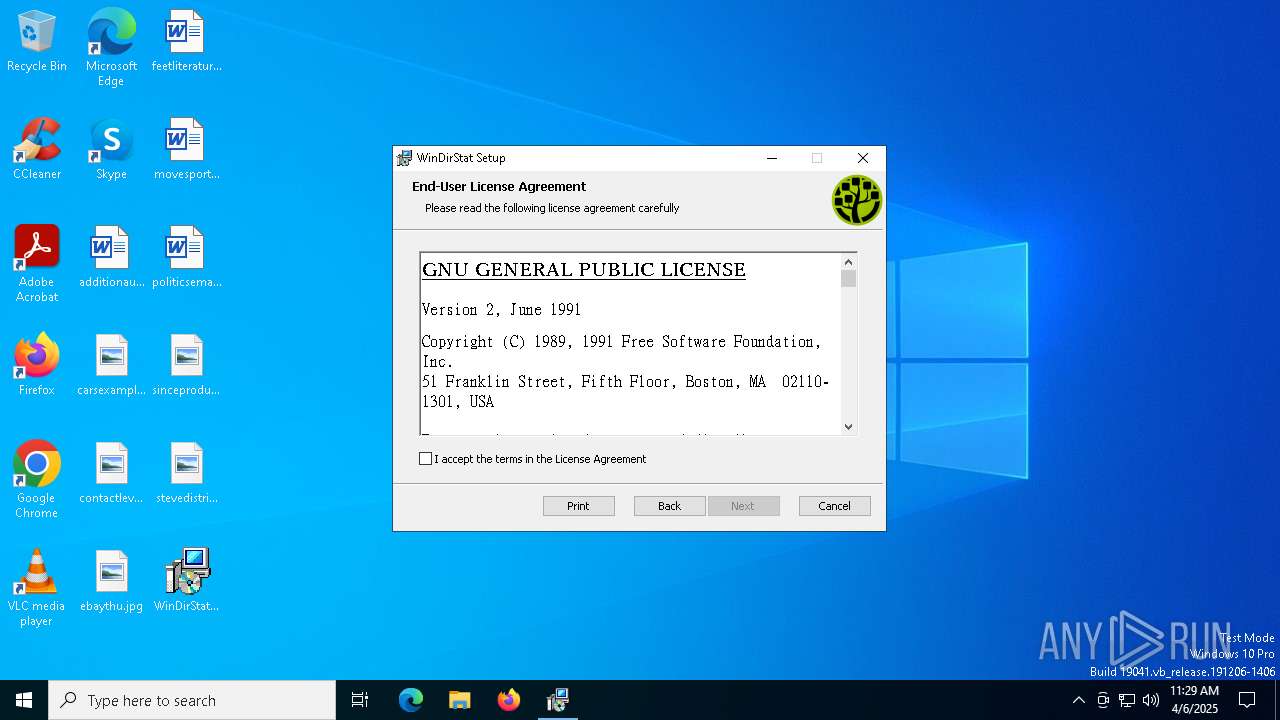
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, MSI Installer, Code page: 1252, Title: Installation Database, Subject: WinDirStat, Author: WinDirStat Team, Keywords: Installer, Comments: WinDirStat 2.2.2 (x64), Template: x64;1033, Revision Number: {9EBE4D37-CA39-4030-BC42-D113938DEAE5}, Create Time/Date: Fri Jan 17 23:11:20 2025, Last Saved Time/Date: Fri Jan 17 23:11:20 2025, Number of Pages: 500, Number of Words: 2, Name of Creating Application: Windows Installer XML Toolset (3.14.1.8722), Security: 2 |
| MD5: | 1CF2DDBA0D045BC053529B2759AAF8C8 |
| SHA1: | EA0A5AF18F008EE7DDE34C2A1CF8F625A3FBF165 |
| SHA256: | 029CC7158D5E2D475243B36AE207921D8205C1296E24C2CAB13F142AEFBA473D |
| SSDEEP: | 98304:VZNtuX4x5tWLbdOHooP5x6ZVyeM+LNFfh4l3kOBXDomY7hQi9VKlJyTFQPLLcdGO:m |
MALICIOUS
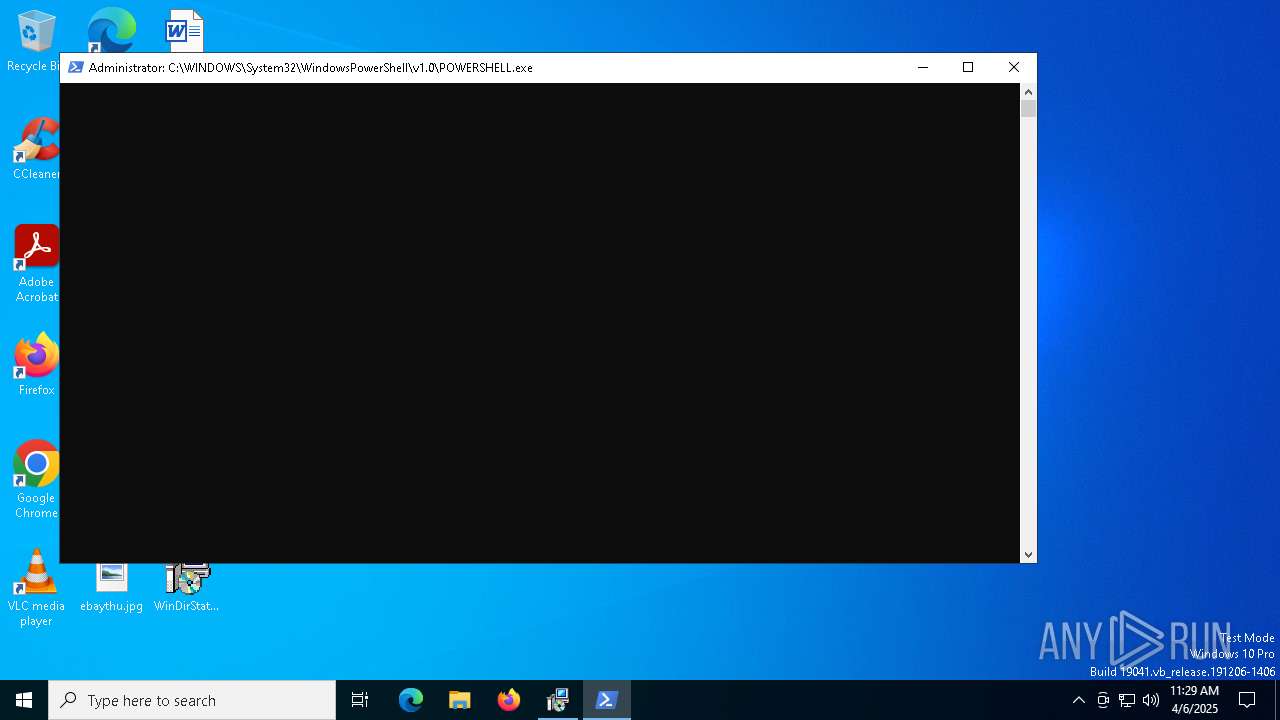
Run PowerShell with an invisible window
- powershell.exe (PID: 5384)
Bypass execution policy to execute commands
- powershell.exe (PID: 5384)
Changes powershell execution policy (Bypass)
- msiexec.exe (PID: 4988)
SUSPICIOUS
Executes as Windows Service
- VSSVC.exe (PID: 5508)
Kill processes via PowerShell
- powershell.exe (PID: 5384)
Hides errors and continues executing the command without stopping
- powershell.exe (PID: 5384)
Manipulates environment variables
- powershell.exe (PID: 5384)
The process hide an interactive prompt from the user
- msiexec.exe (PID: 4988)
The process bypasses the loading of PowerShell profile settings
- msiexec.exe (PID: 4988)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 4988)
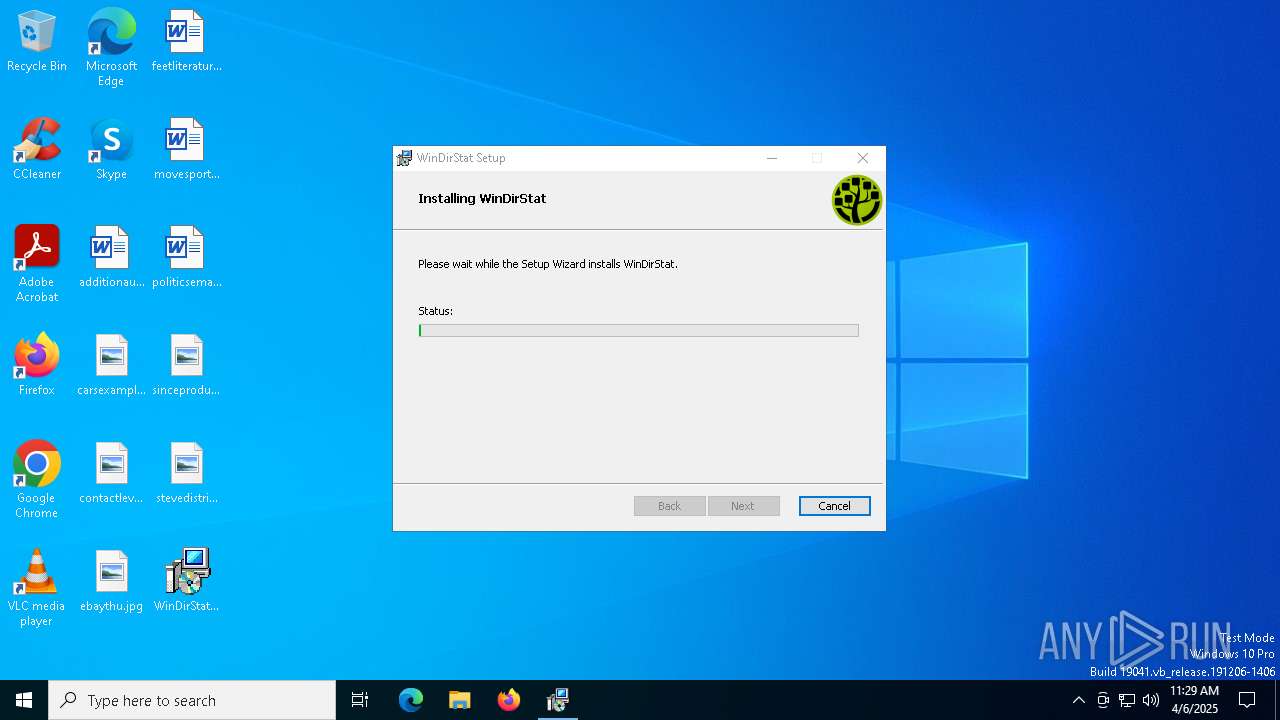
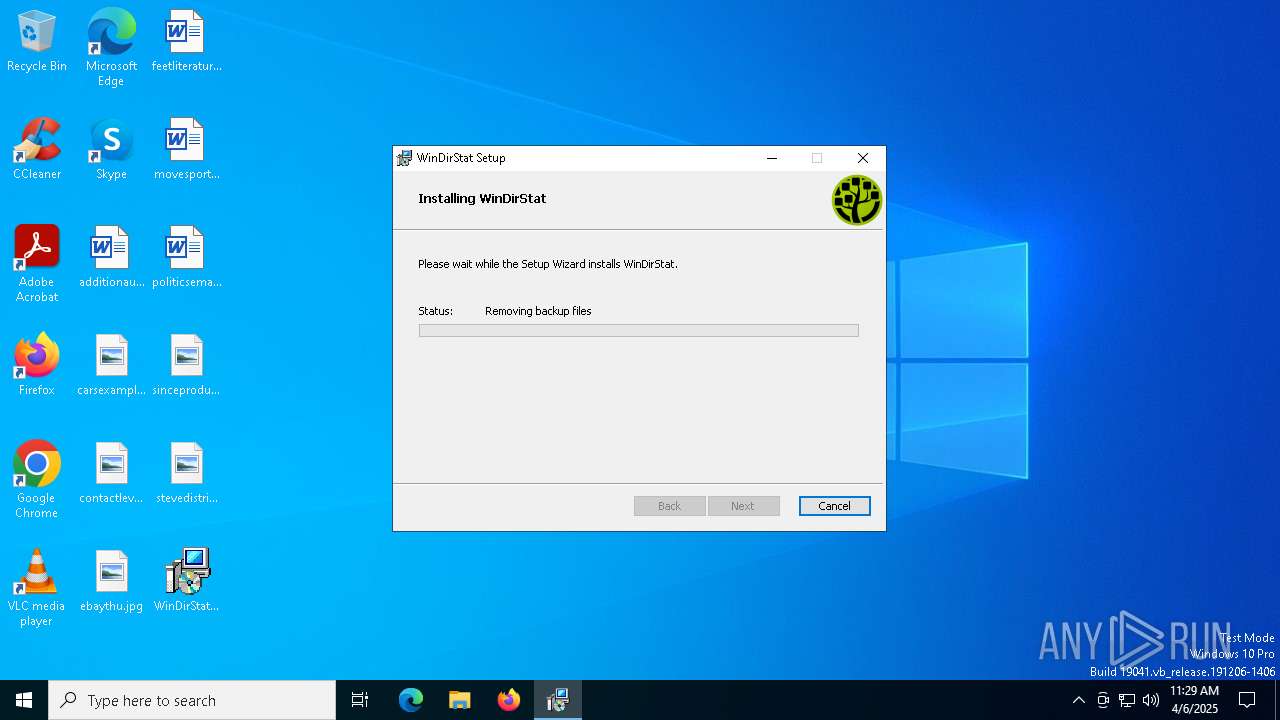
Removes files via Powershell
- powershell.exe (PID: 5384)
Get information on the list of running processes
- msiexec.exe (PID: 4988)
The process hides Powershell's copyright startup banner
- msiexec.exe (PID: 4988)
Returns all items found within a container (POWERSHELL)
- powershell.exe (PID: 5384)
Starts POWERSHELL.EXE for commands execution
- msiexec.exe (PID: 4988)
INFO
Checks proxy server information
- msiexec.exe (PID: 1184)
- slui.exe (PID: 2332)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 1184)
An automatically generated document
- msiexec.exe (PID: 1184)
Creates files or folders in the user directory
- msiexec.exe (PID: 1184)
Checks supported languages
- msiexec.exe (PID: 3888)
- msiexec.exe (PID: 4988)
Executable content was dropped or overwritten
- msiexec.exe (PID: 1184)
- msiexec.exe (PID: 4988)
Reads the software policy settings
- msiexec.exe (PID: 1184)
- msiexec.exe (PID: 4988)
- powershell.exe (PID: 5384)
- slui.exe (PID: 2332)
Reads the computer name
- msiexec.exe (PID: 4988)
- msiexec.exe (PID: 3888)
Manages system restore points
- SrTasks.exe (PID: 3676)
Reads the machine GUID from the registry
- msiexec.exe (PID: 4988)
Returns hidden items found within a container (POWERSHELL)
- conhost.exe (PID: 5260)
- conhost.exe (PID: 6324)
- powershell.exe (PID: 5384)
Returns all items recursively from all subfolders (POWERSHELL)
- powershell.exe (PID: 5384)
Creates a software uninstall entry
- msiexec.exe (PID: 4988)
Create files in a temporary directory
- powershell.exe (PID: 5384)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Windows Installer (98.5) |
|---|---|---|
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| CodePage: | Windows Latin 1 (Western European) |
|---|---|
| Title: | Installation Database |
| Subject: | WinDirStat |
| Author: | WinDirStat Team |
| Keywords: | Installer |
| Comments: | WinDirStat 2.2.2 (x64) |
| Template: | x64;1033 |
| RevisionNumber: | {9EBE4D37-CA39-4030-BC42-D113938DEAE5} |
| CreateDate: | 2025:01:17 23:11:20 |
| ModifyDate: | 2025:01:17 23:11:20 |
| Pages: | 500 |
| Words: | 2 |
| Software: | Windows Installer XML Toolset (3.14.1.8722) |
| Security: | Read-only recommended |
Total processes
139
Monitored processes
9
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
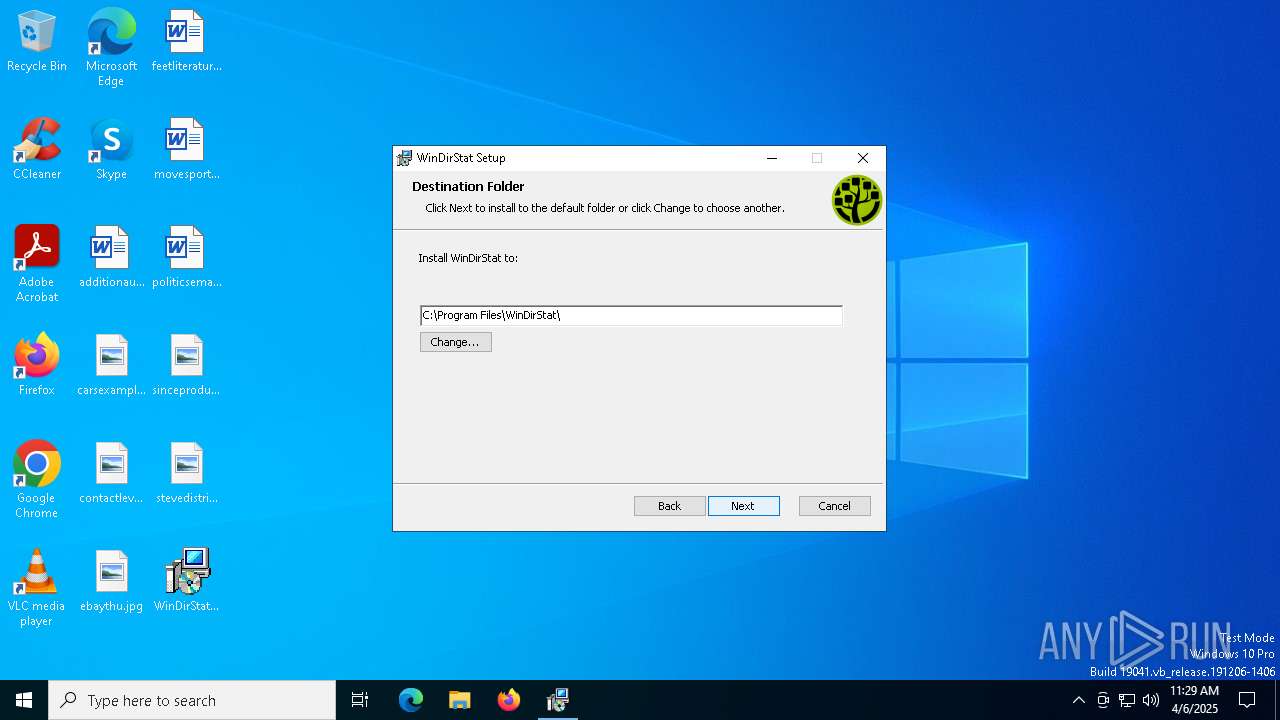
| 1184 | "C:\Windows\System32\msiexec.exe" /i C:\Users\admin\Desktop\WinDirStat-x64.msi | C:\Windows\System32\msiexec.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2332 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3676 | C:\WINDOWS\system32\srtasks.exe ExecuteScopeRestorePoint /WaitForRestorePoint:11 | C:\Windows\System32\SrTasks.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Windows System Protection background tasks. Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3888 | C:\Windows\syswow64\MsiExec.exe -Embedding 5ACAA7A2ECCD3B89E5124A669DD0AC4D C | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4988 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5260 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SrTasks.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5384 | POWERSHELL -NoLogo -NonInteractive -NoProfile -ExecutionPolicy Bypass -WindowStyle Hidden -Command "& { $ErrorActionPreference = 'SilentlyContinue' Get-Process 'WinDirStat*' | Stop-Process -Force $Keys = @() $Keys += Get-ChildItem 'Registry::HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Uninstall\WinDirStat' $Keys += Get-ChildItem 'Registry::HKEY_USERS\*\Software\Microsoft\Windows\CurrentVersion\Uninstall\WinDirStat' ForEach ($Key in $Keys) { $Path = $Key.GetValue('InstallLocation') If (-not (Test-Path ($Path + '\*'))) { Continue } Remove-Item -Path ($Path + '\wdsh*.chm') -Force Remove-Item -Path ($Path + '\wdsr*.dll') -Force Remove-Item -Path ($Path + '\WinDirStat*.*') -Force Remove-Item -Path ($Path + '\Uninstall.exe') -Force If (-not (Test-Path ($Path + '\*'))) { Remove-Item -Path $Path -Force } Remove-Item -Path $Key.PSPath -Force } Remove-Item -Path ($env:SystemDrive + '\Users\*\Desktop\WinDirStat.lnk') -Force Remove-Item -Path ($env:SystemDrive + '\Users\*\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\WinDirStat') -Force -Recurse Remove-Item -Path ($env:ProgramData + '\Microsoft\Windows\Start Menu\Programs\WinDirStat') -Force -Recurse }" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5508 | C:\WINDOWS\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6324 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | powershell.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
17 053
Read events
16 776
Write events
260
Delete events
17
Modification events
| (PID) Process: | (4988) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 4800000000000000DCCCC923E7A6DB017C1300002C050000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4988) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 4800000000000000DCCCC923E7A6DB017C1300002C050000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4988) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Leave) |
Value: 4800000000000000E5891824E7A6DB017C1300002C050000D10700000100000000000000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4988) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 480000000000000044A41F24E7A6DB017C1300002C050000D00700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4988) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 480000000000000092C01324E7A6DB017C1300002C050000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4988) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Enter) |
Value: 480000000000000092C01324E7A6DB017C1300002C050000D10700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4988) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 11 | |||
| (PID) Process: | (4988) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 4800000000000000B7B48F24E7A6DB017C1300002C050000D30700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5508) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 480000000000000001A89B24E7A6DB0184150000040A0000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5508) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 480000000000000001A89B24E7A6DB018415000098170000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
4
Suspicious files
31
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4988 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 1184 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\4E4160FB650E5091C535216313A4ECD3_9C2BA0D68BBB93342E457B5FC2988A9F | binary | |
MD5:AB10FDCF808FED3F5DD6AF2C0ABC0CEA | SHA256:26F8C59BC656FCE030C0B222F59014B82791BFC62DAF800786FA1C285E354FD5 | |||
| 1184 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\856FDBDDFEAC90A3D62D621EBF196637 | binary | |
MD5:E4AF6DEBFB86571BCBFBCEE68DABA556 | SHA256:13943EB10C5A474E425C87DF08683D23444349344F48F66D2AC12768D28C93B4 | |||
| 1184 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\30069012ED3CF5DB92F9F4FC78D55E2D_87238437CEFCADF00F1385E31A888EF4 | binary | |
MD5:D7CF9A39F0880049F654F011293B6678 | SHA256:7CEA04931117346AB926AF8E8EE2E4DA0A42F5D4B714A020C96B0386F36CBFFA | |||
| 1184 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\68FAF71AF355126BCA00CE2E73CC7374_E5F521CA60C5ED8C2B4E2BF399FE2061 | binary | |
MD5:42E58F27383EF27471990CC42A20B802 | SHA256:AE94F59A4ED8A7BE2275181538AB99B44835A5691D2CC9EDE8FEE9CBFCDF2E79 | |||
| 4988 | msiexec.exe | C:\System Volume Information\SPP\snapshot-2 | binary | |
MD5:7A125EA24F8C344FF58492845511A149 | SHA256:239B87B2B78EAE0F8807A59A53465D28BBB74E3B36A5FEDFE7AFEB026A4C6AF8 | |||
| 4988 | msiexec.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{d91821b0-f8cf-4485-9903-4e9729561b22}_OnDiskSnapshotProp | binary | |
MD5:7A125EA24F8C344FF58492845511A149 | SHA256:239B87B2B78EAE0F8807A59A53465D28BBB74E3B36A5FEDFE7AFEB026A4C6AF8 | |||
| 4988 | msiexec.exe | C:\Windows\Installer\inprogressinstallinfo.ipi | binary | |
MD5:5D810D558310C753298D2B943A61F73D | SHA256:964D0DE88AE44EF5E188DF60507408C11E5BFCE97BB66C59697CEEEB9E3D3EAD | |||
| 1184 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSIF52F.tmp | executable | |
MD5:CFBB8568BD3711A97E6124C56FCFA8D9 | SHA256:7F47D98AB25CFEA9B3A2E898C3376CC9BA1CD893B4948B0C27CAA530FD0E34CC | |||
| 4988 | msiexec.exe | C:\Windows\Installer\MSI4CA6.tmp | binary | |
MD5:41D67C689EC9D4BDEEA5FBD135DBAD65 | SHA256:806DEFA25179542E66208D68B732615D00C0EB0F2114EF8CA195CCA8D1ADB23E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
45
TCP/UDP connections
60
DNS requests
18
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1184 | msiexec.exe | GET | 200 | 95.100.110.12:80 | http://subca.ocsp-certum.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTYOkzrrCGQj08njZXbUQQpkoUmuQQUCHbNywf%2FJPbFze27kLzihDdGdfcCEBu1jyUq3yMASSjJrj1%2B7Sc%3D | unknown | — | — | whitelisted |
1184 | msiexec.exe | GET | 200 | 95.100.110.12:80 | http://subca.ocsp-certum.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTYOkzrrCGQj08njZXbUQQpkoUmuQQUCHbNywf%2FJPbFze27kLzihDdGdfcCEBu1jyUq3yMASSjJrj1%2B7Sc%3D | unknown | — | — | whitelisted |
1184 | msiexec.exe | GET | 200 | 95.100.110.11:80 | http://crl.certum.pl/ctnca.crl | unknown | — | — | whitelisted |
1184 | msiexec.exe | GET | 200 | 95.100.110.12:80 | http://subca.ocsp-certum.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRIH1V64SBkA%2BzJQVQ6VFBAcvLB3wQUtqFUOQLDoD%2BOirz61PgcptE6Dv0CEQCZo4AKJlU7ZavcboSms%2Bo5 | unknown | — | — | whitelisted |
1184 | msiexec.exe | GET | 200 | 95.100.110.20:80 | http://ccsca2021.ocsp-certum.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRxypYNH69rICCzQBIRXN0YAFa3AAQU3XRdTADbe5%2BgdMqxbvc8wDLAcM0CEAGRWQdNOfHYTFKn1pQEANY%3D | unknown | — | — | unknown |
— | — | GET | 304 | 20.12.23.50:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | unknown | — | — | unknown |
— | — | GET | 200 | 20.12.23.50:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | unknown | — | — | unknown |
1568 | SIHClient.exe | GET | 200 | 23.216.77.36:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1568 | SIHClient.exe | GET | 200 | 2.16.253.202:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
1568 | SIHClient.exe | GET | 200 | 23.216.77.36:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 20.198.162.76:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | SG | whitelisted |
1184 | msiexec.exe | 95.100.110.12:80 | subca.ocsp-certum.com | Akamai International B.V. | NL | suspicious |
1184 | msiexec.exe | 95.100.110.11:80 | crl.certum.pl | Akamai International B.V. | NL | whitelisted |
1184 | msiexec.exe | 95.100.110.20:80 | subca.ocsp-certum.com | Akamai International B.V. | NL | suspicious |
6544 | svchost.exe | 40.126.32.140:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3216 | svchost.exe | 20.198.162.76:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | SG | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
subca.ocsp-certum.com |
| whitelisted |
crl.certum.pl |
| whitelisted |
ccsca2021.ocsp-certum.com |
| unknown |
login.live.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |