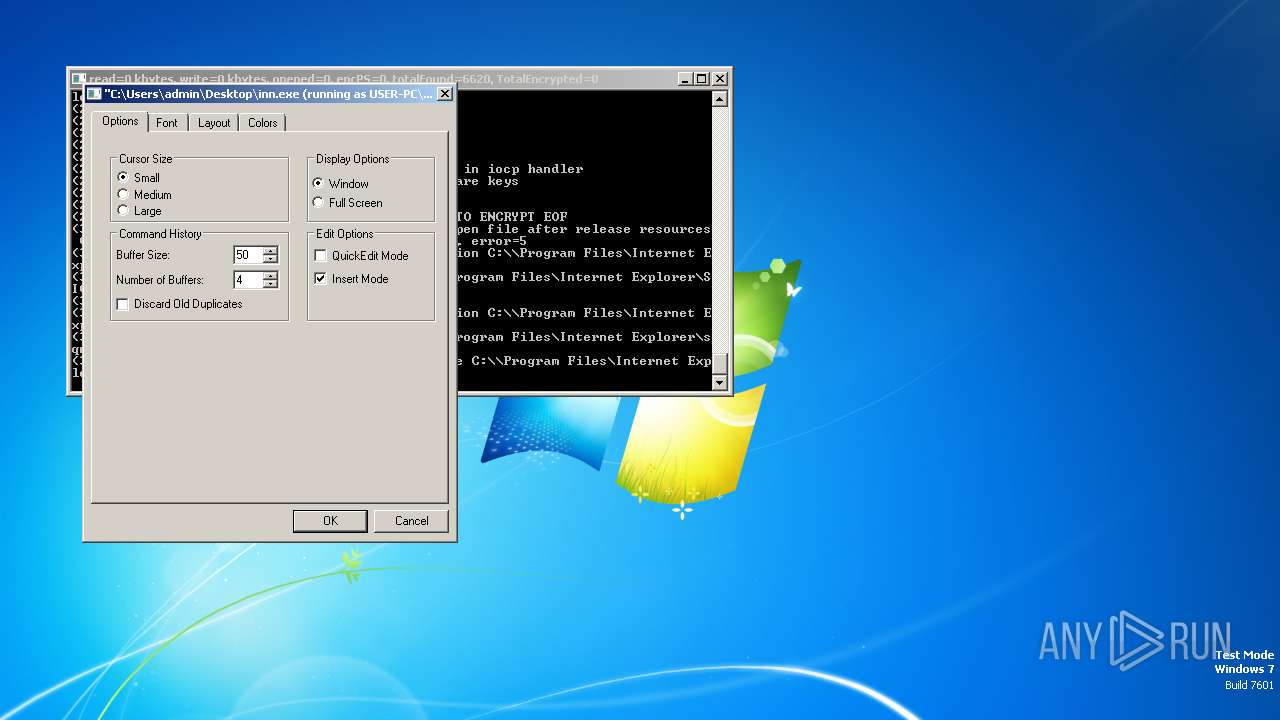
| File name: | inn.exe |
| Full analysis: | https://app.any.run/tasks/0040a823-f318-4638-8474-9b27b240b743 |
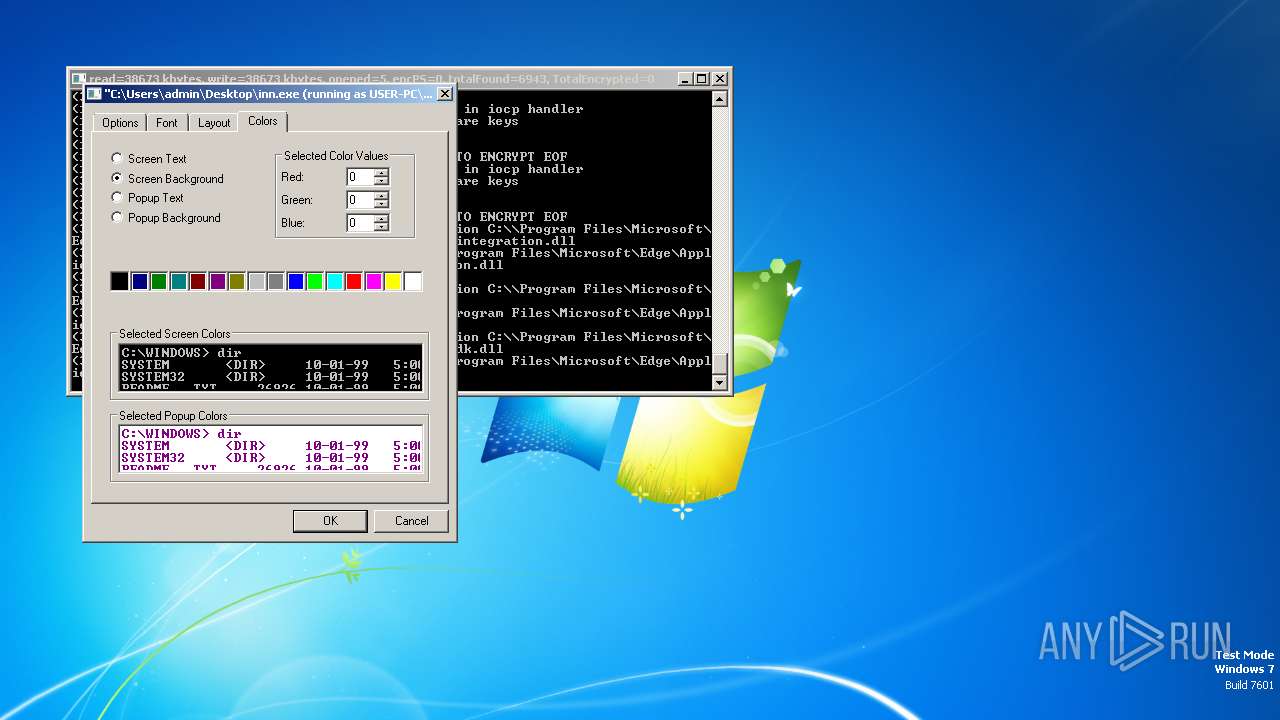
| Verdict: | Malicious activity |
| Analysis date: | December 03, 2023, 19:52:45 |
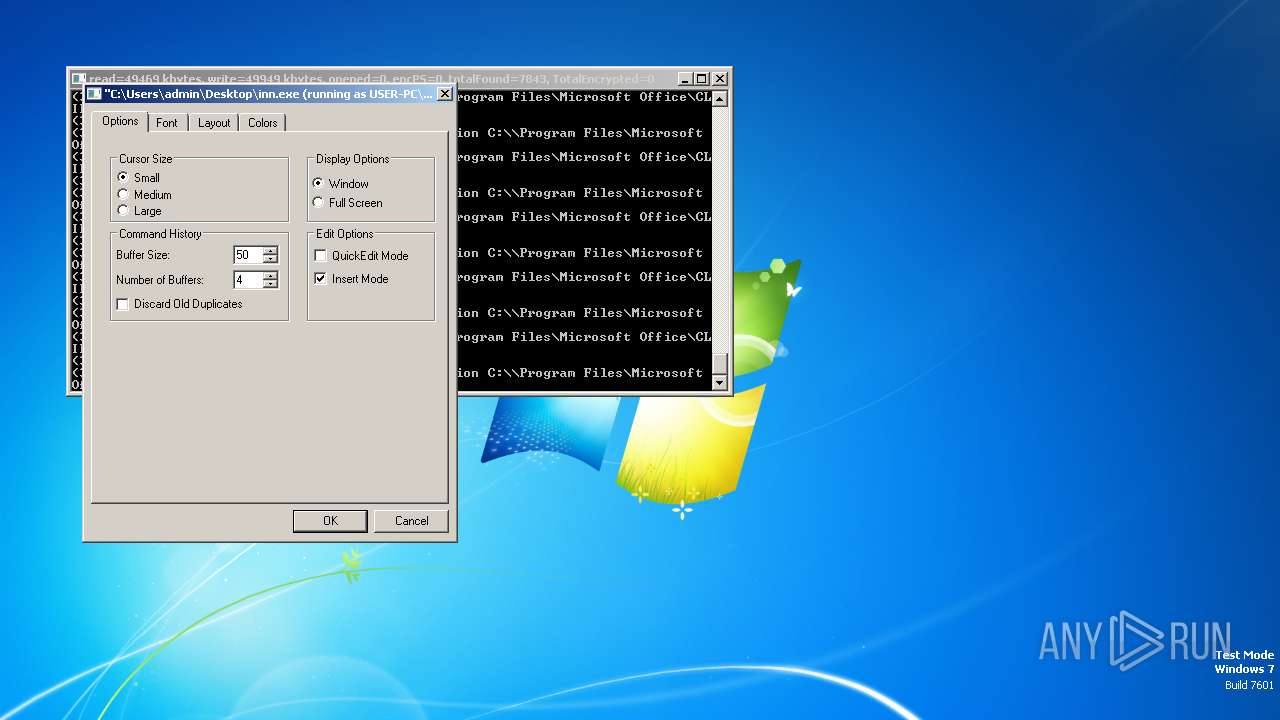
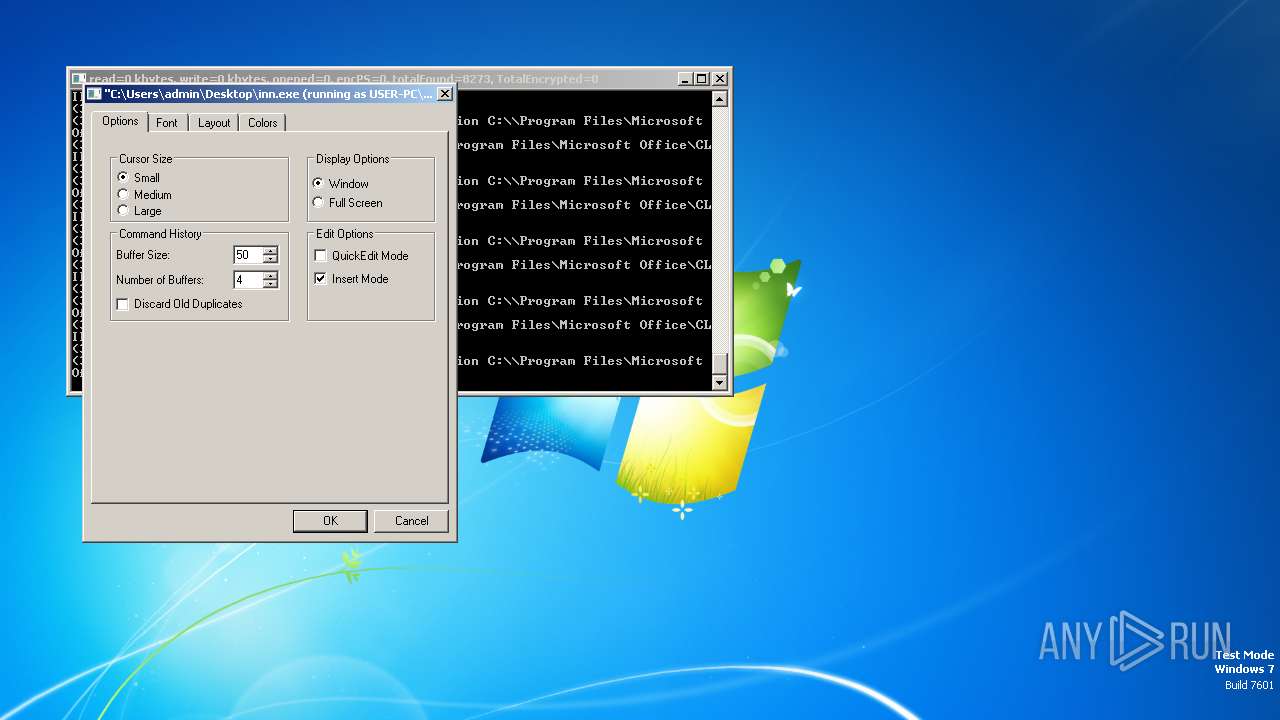
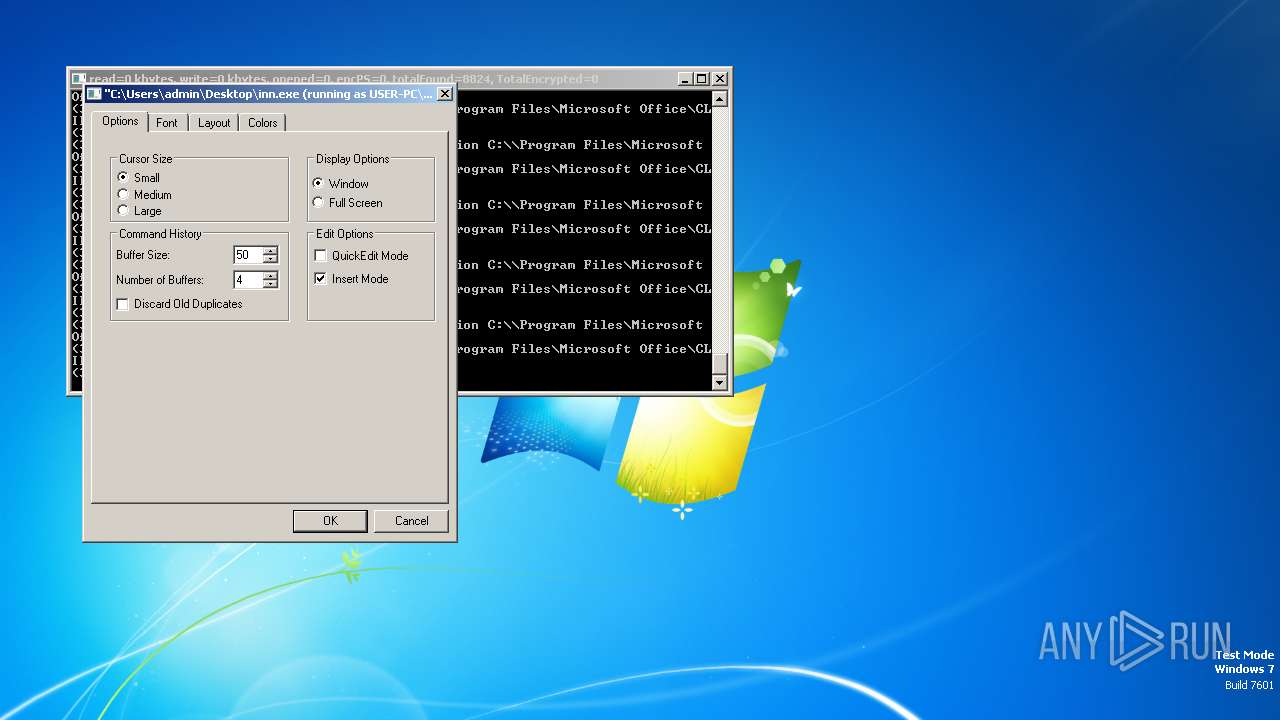
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows |
| MD5: | E455A5DD66D910573D8419D7015BF905 |
| SHA1: | C47629860569BA2F6815CA483EA74332E4E8ADDE |
| SHA256: | 029366E0F395E1FF2230278E31585AC424E2FD711ADF68A2C45B6DE9106084C5 |
| SSDEEP: | 3072:gJxnsDkvtOEjk0borIuH12edrVEcrBqW2ee1yzUCYXyM0n+4UHybOP8pCt+ObhA:AJsDkvpiVFWclqW21yzG/C7XpS+Obh |
MALICIOUS
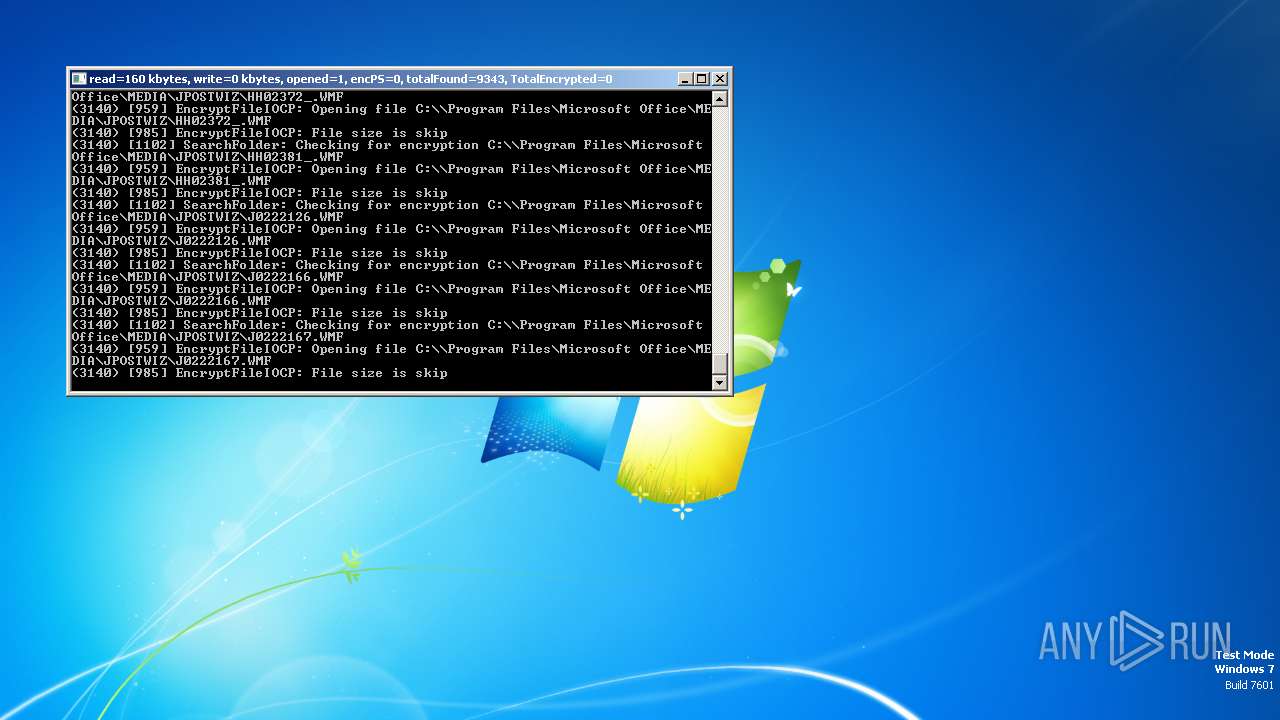
Drops the executable file immediately after the start
- inn.exe (PID: 3064)
Actions looks like stealing of personal data
- inn.exe (PID: 3064)
SUSPICIOUS
Process drops legitimate windows executable
- inn.exe (PID: 3064)
Executes as Windows Service
- VSSVC.exe (PID: 2600)
The process drops C-runtime libraries
- inn.exe (PID: 3064)
INFO
Reads the machine GUID from the registry
- inn.exe (PID: 3064)
Reads the computer name
- inn.exe (PID: 3064)
Checks supported languages
- inn.exe (PID: 3064)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:12:01 21:23:29+01:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 79872 |
| InitializedDataSize: | 128000 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xbfce |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows command line |
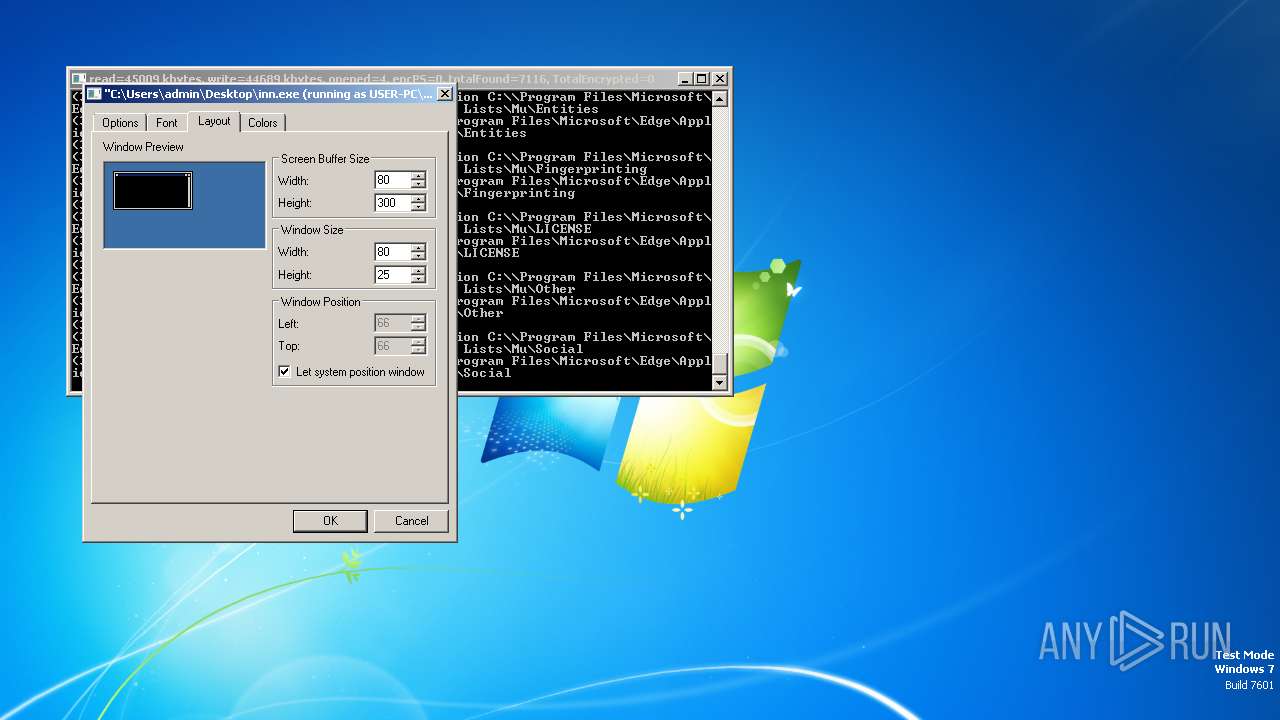
Total processes
46
Monitored processes
3
Malicious processes
2
Suspicious processes
0
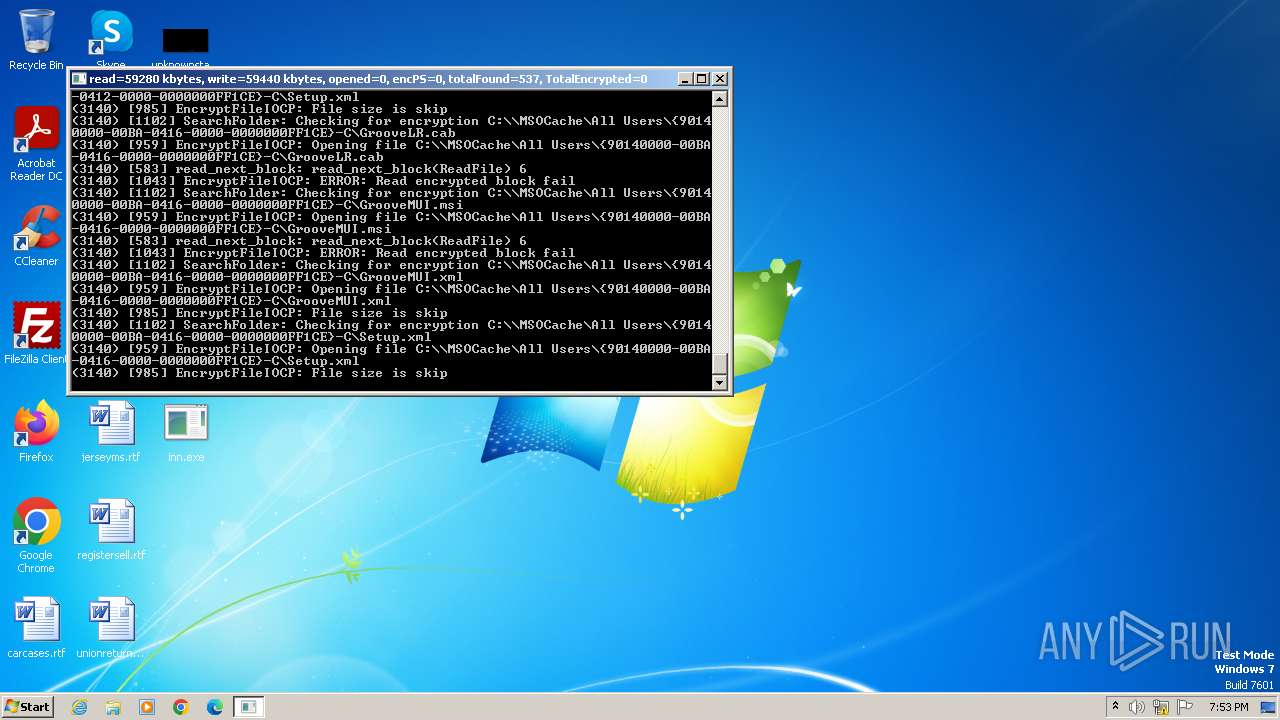
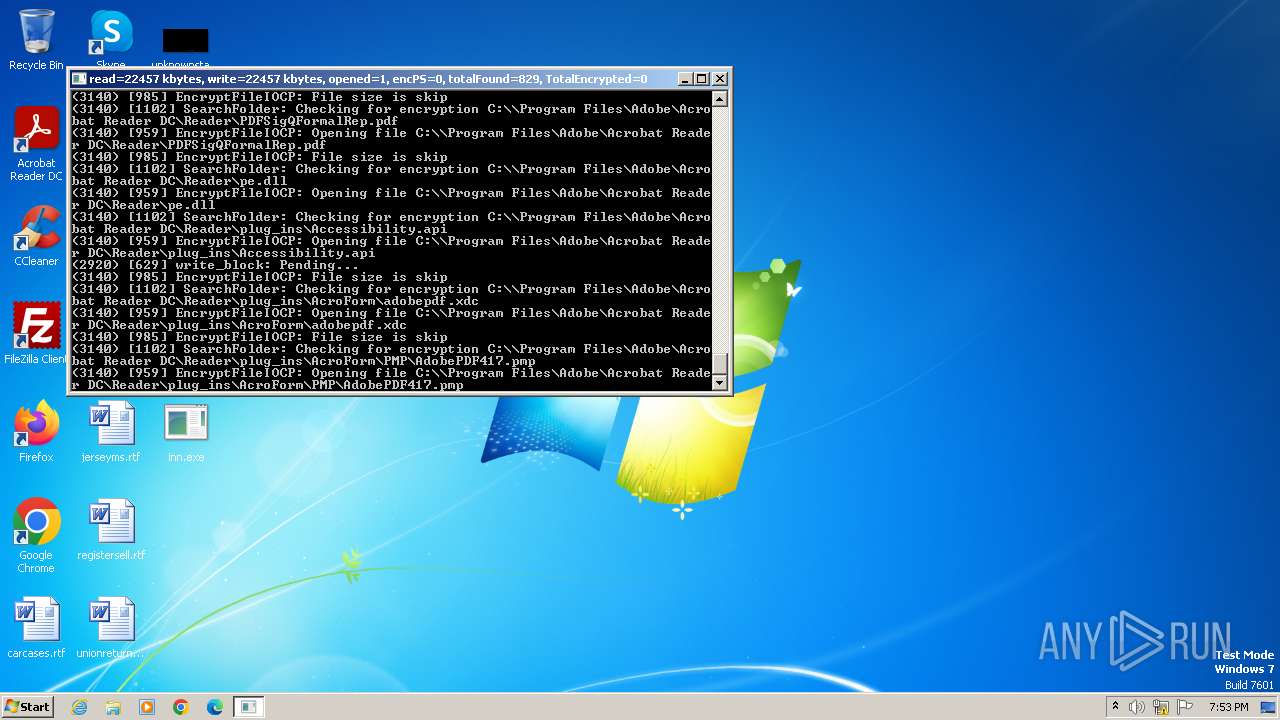
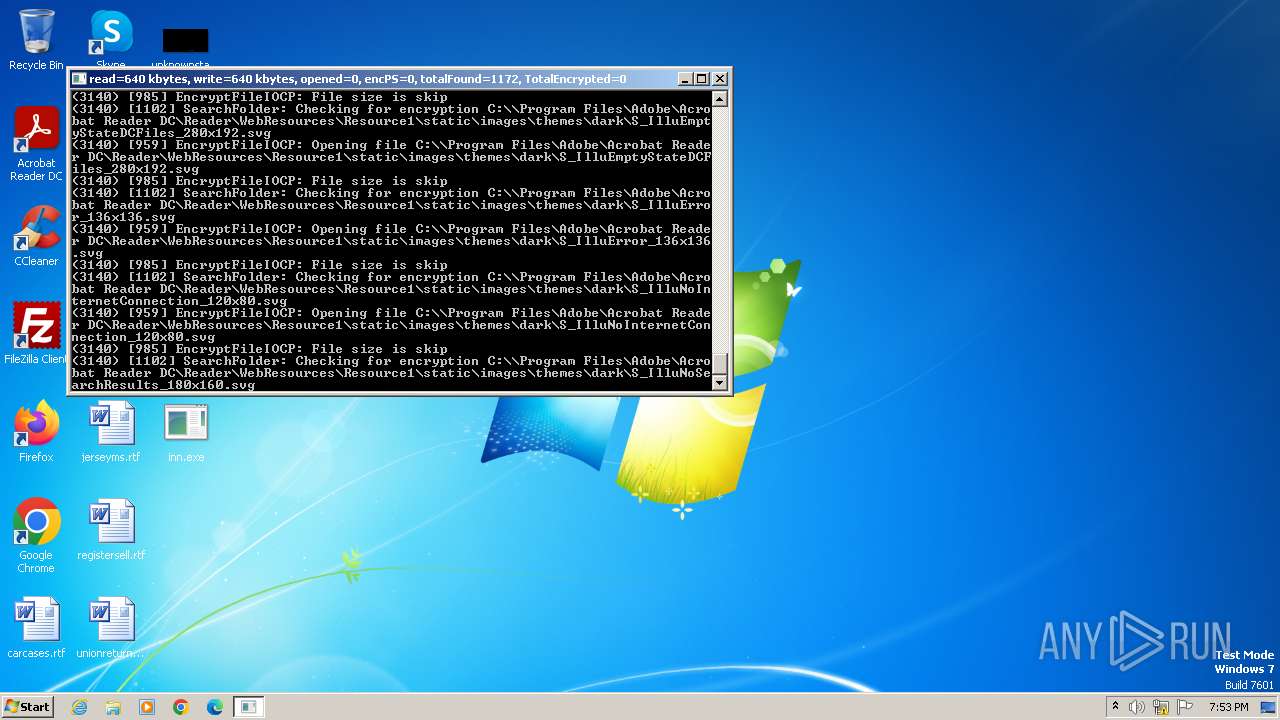
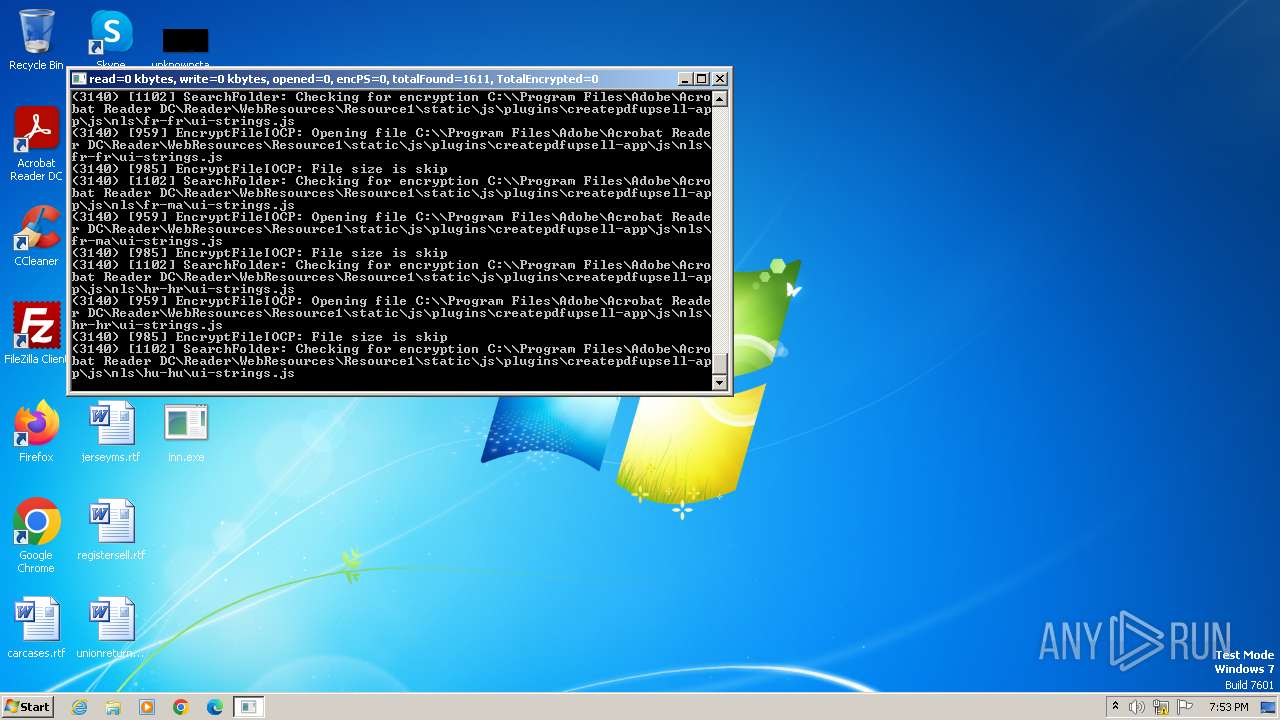
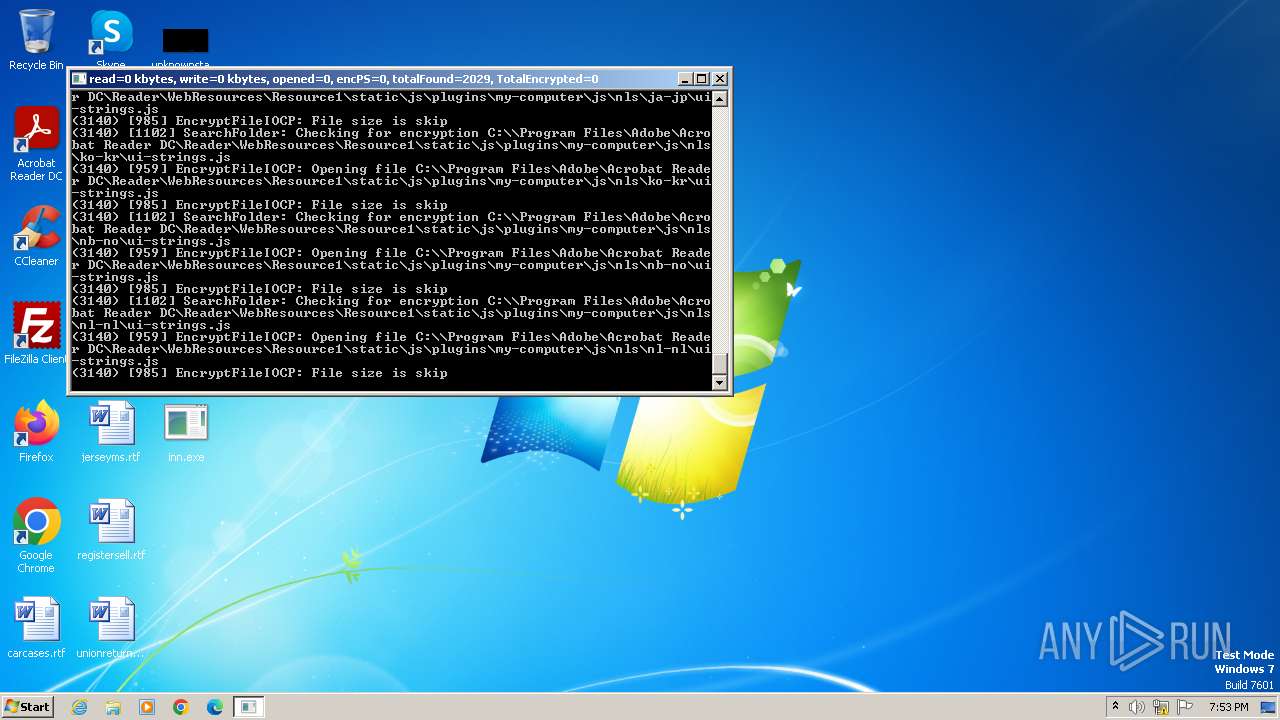
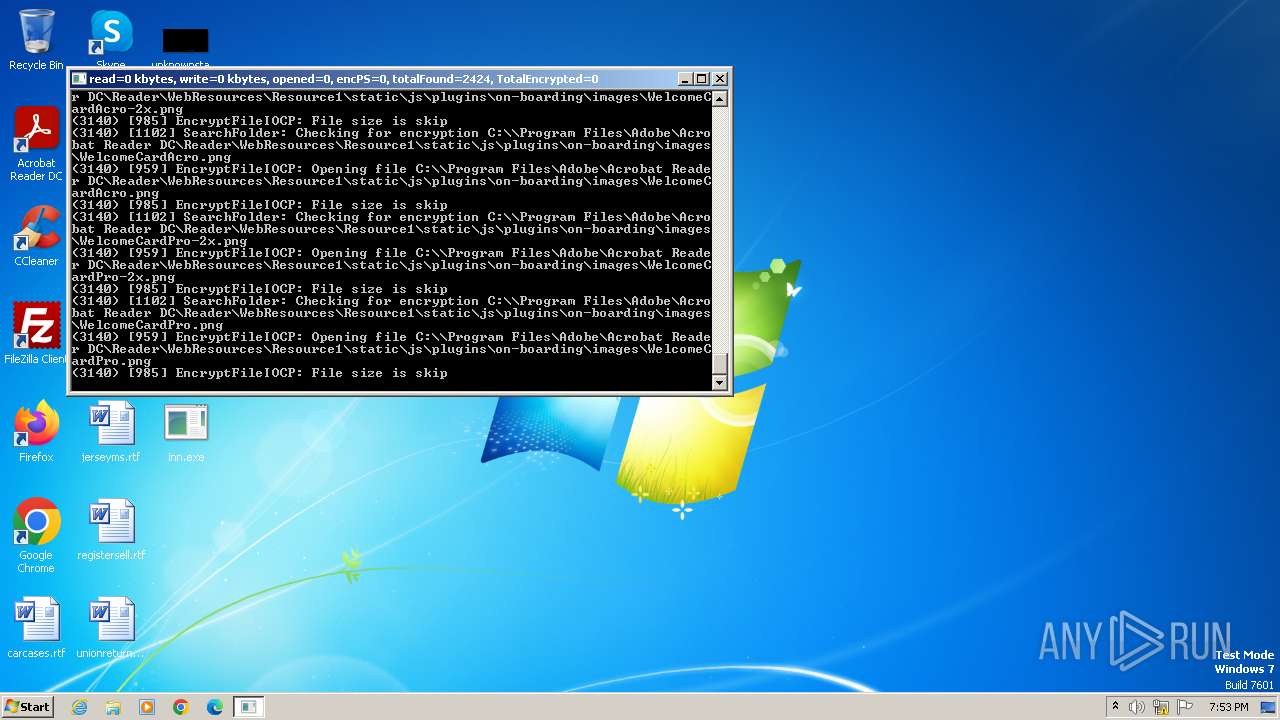
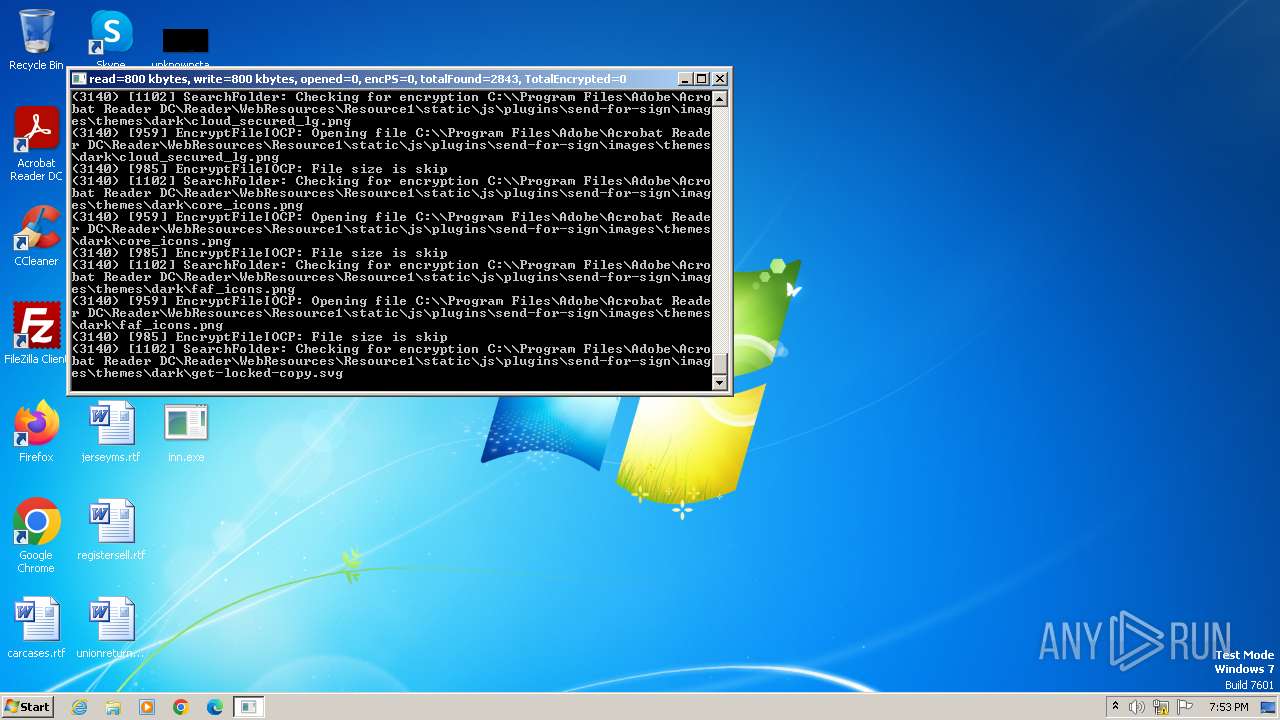
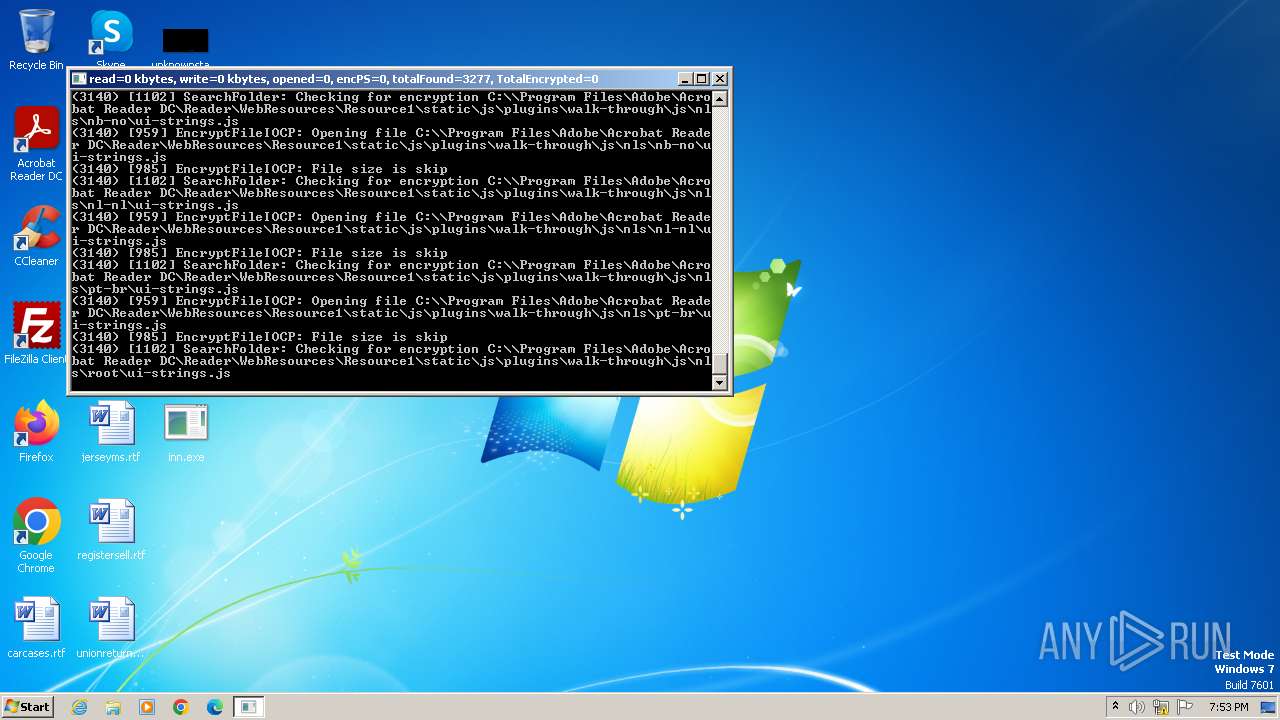
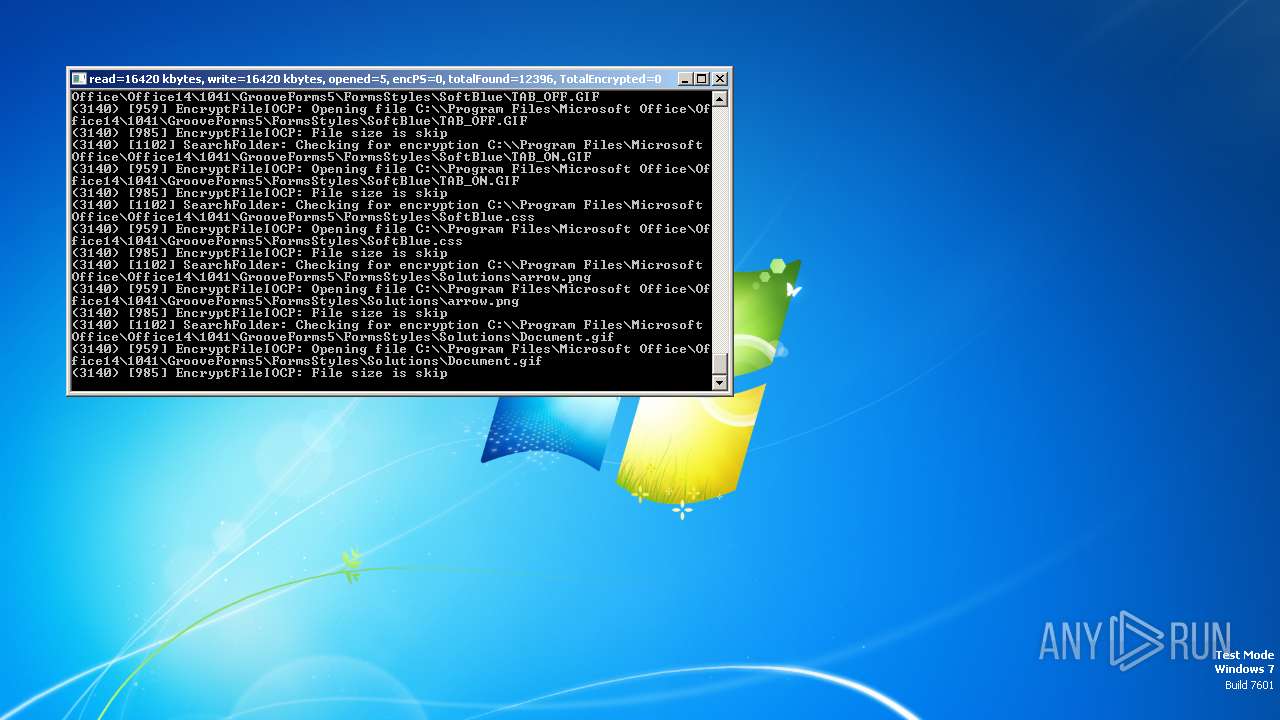
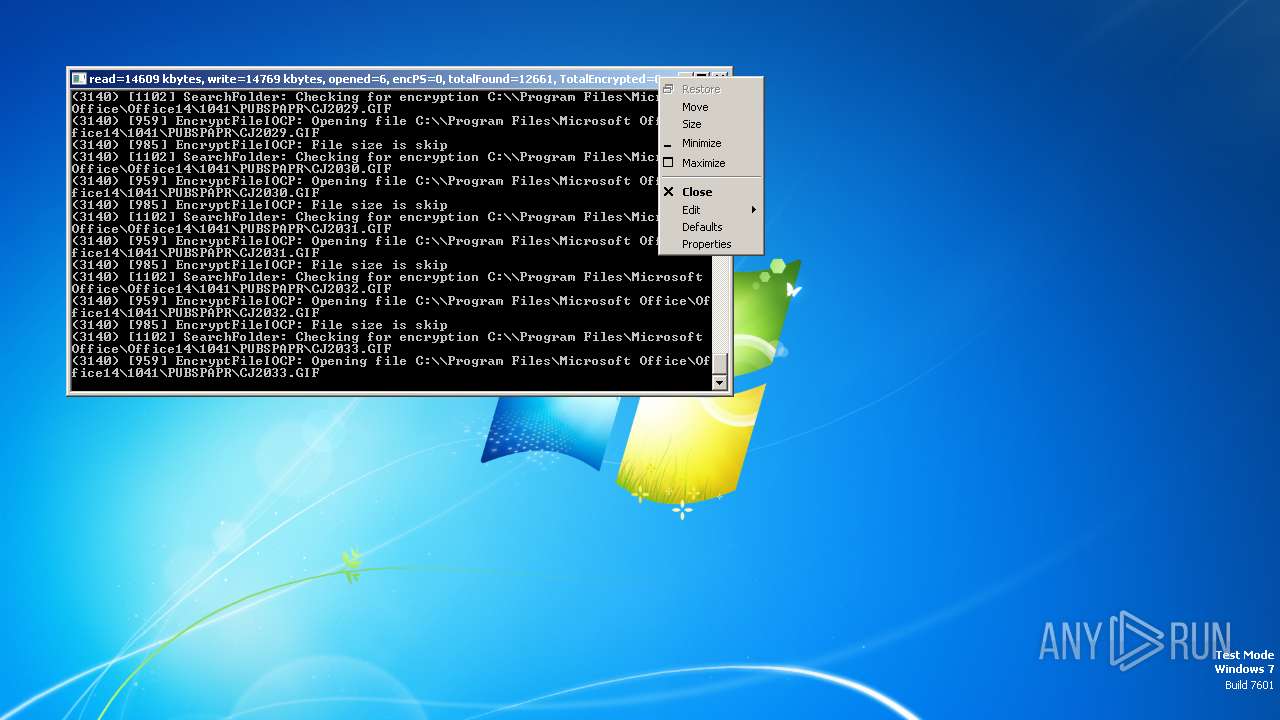
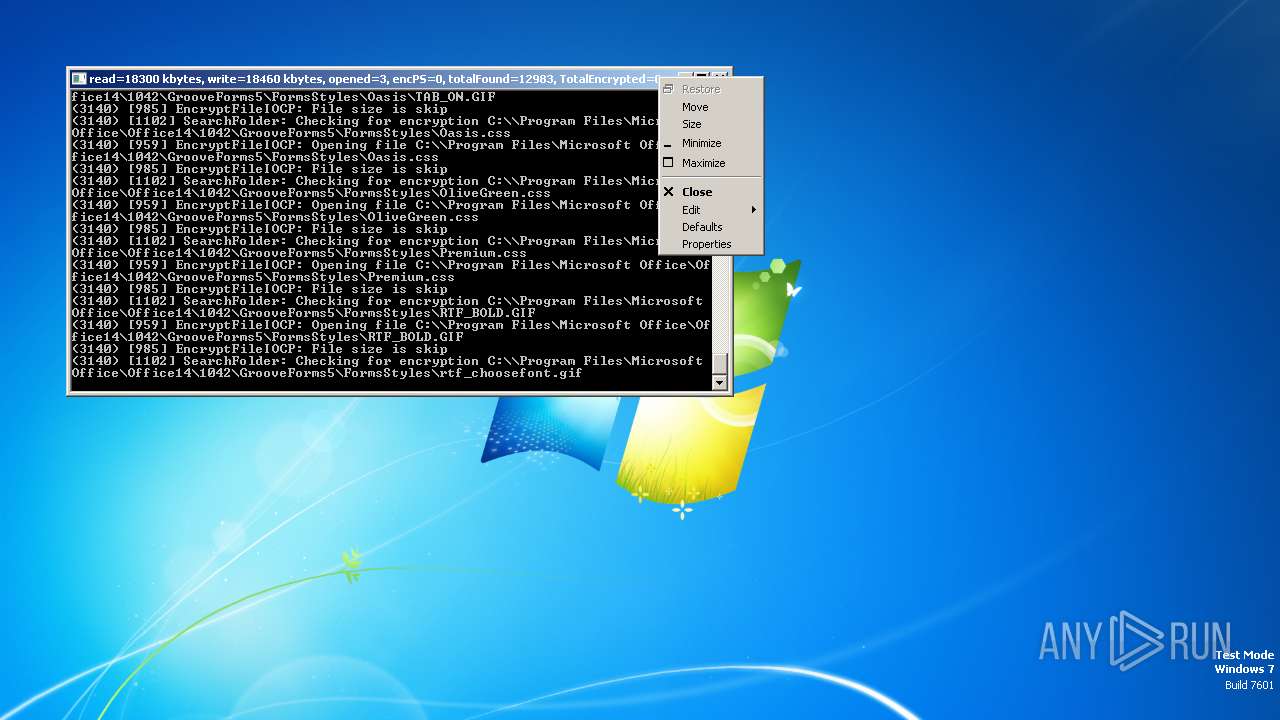
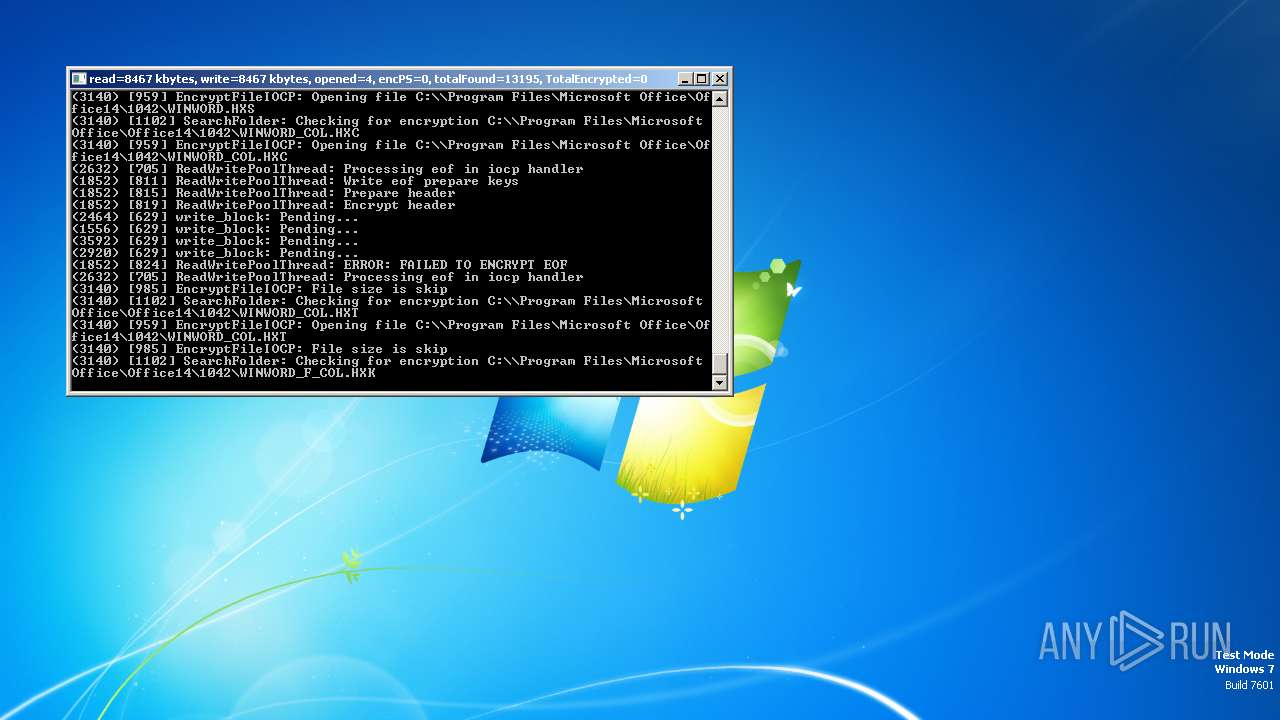
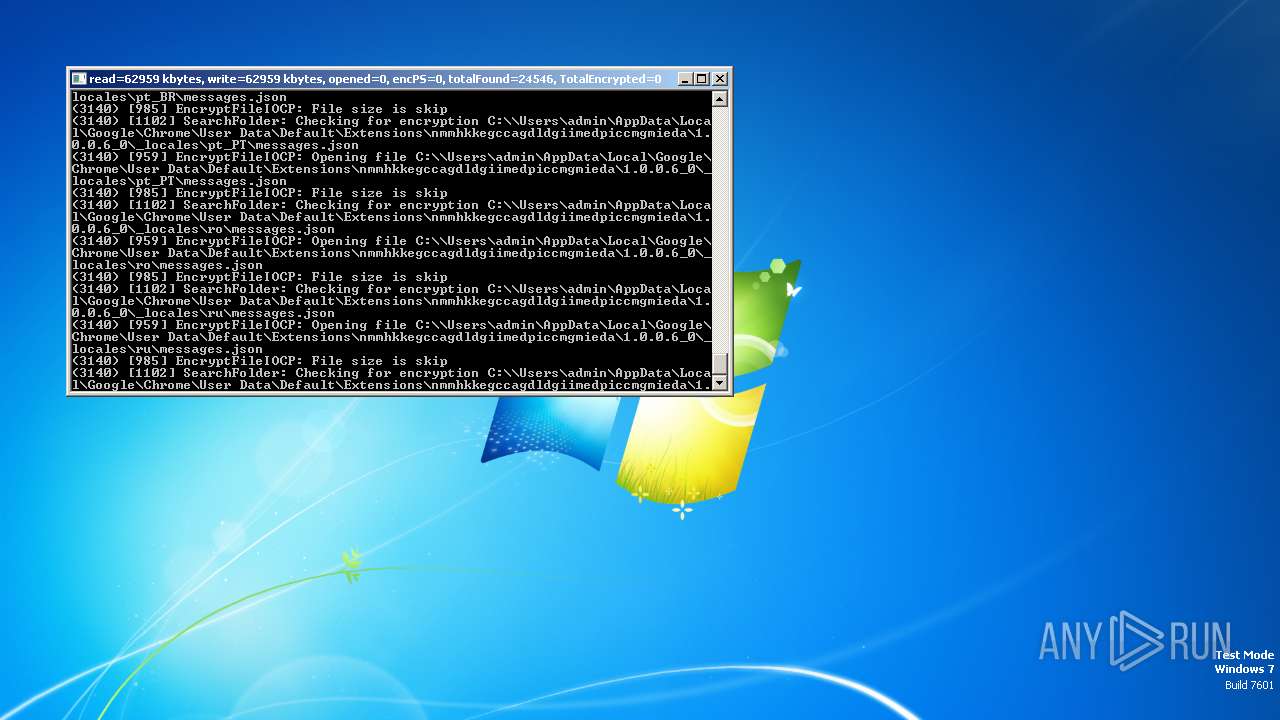
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2600 | C:\Windows\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
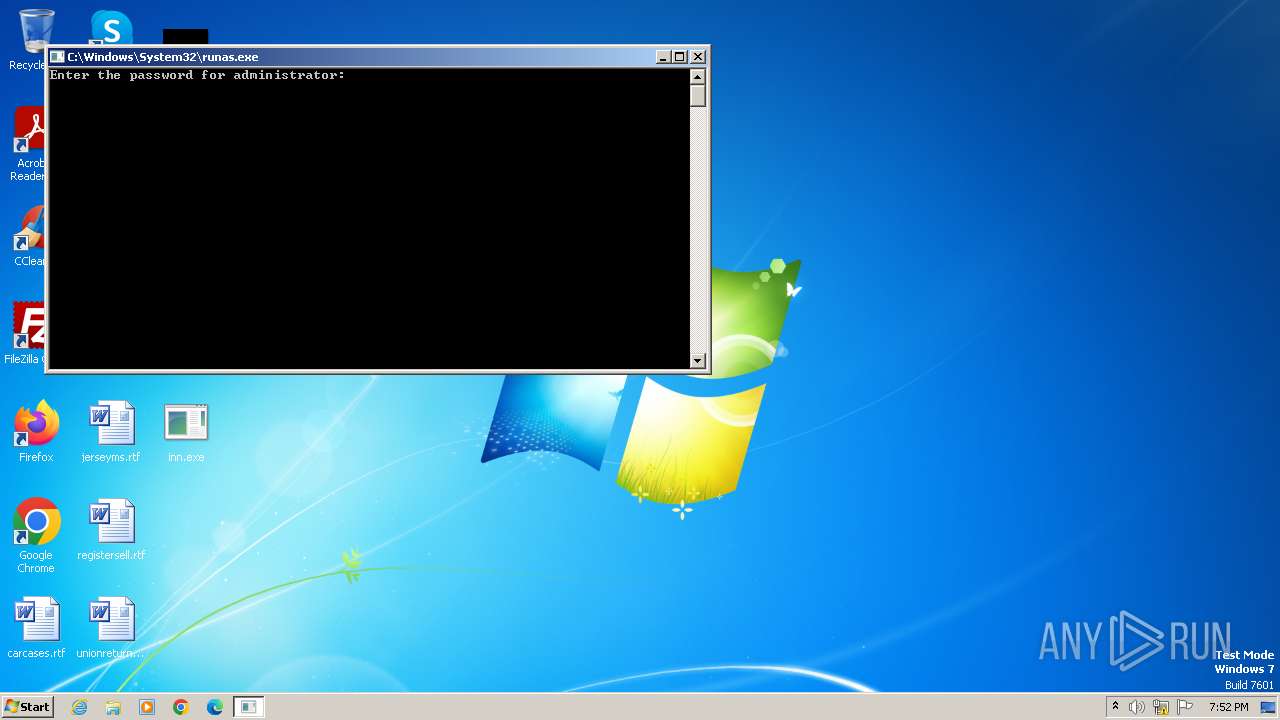
| 2644 | "C:\Windows\System32\runas.exe" /user:administrator C:\Users\admin\Desktop\inn.exe | C:\Windows\System32\runas.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Run As Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
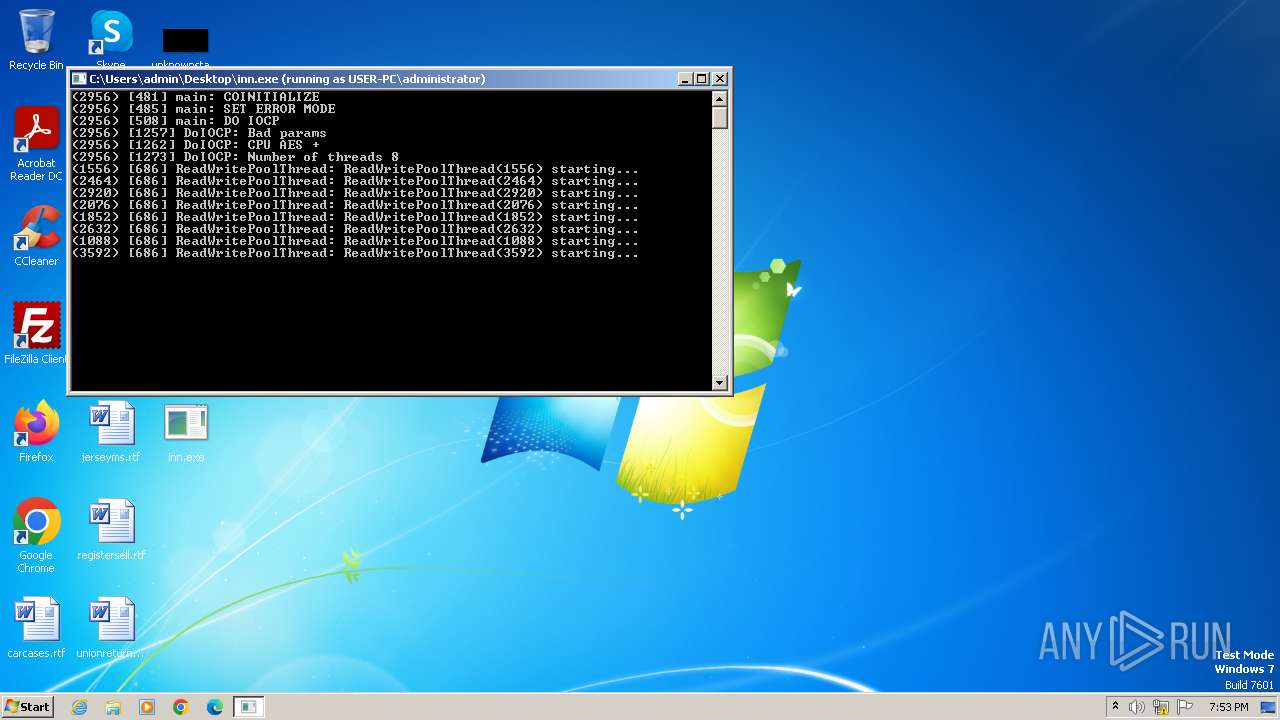
| 3064 | C:\Users\admin\Desktop\inn.exe | C:\Users\admin\Desktop\inn.exe | runas.exe | ||||||||||||
User: Administrator Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
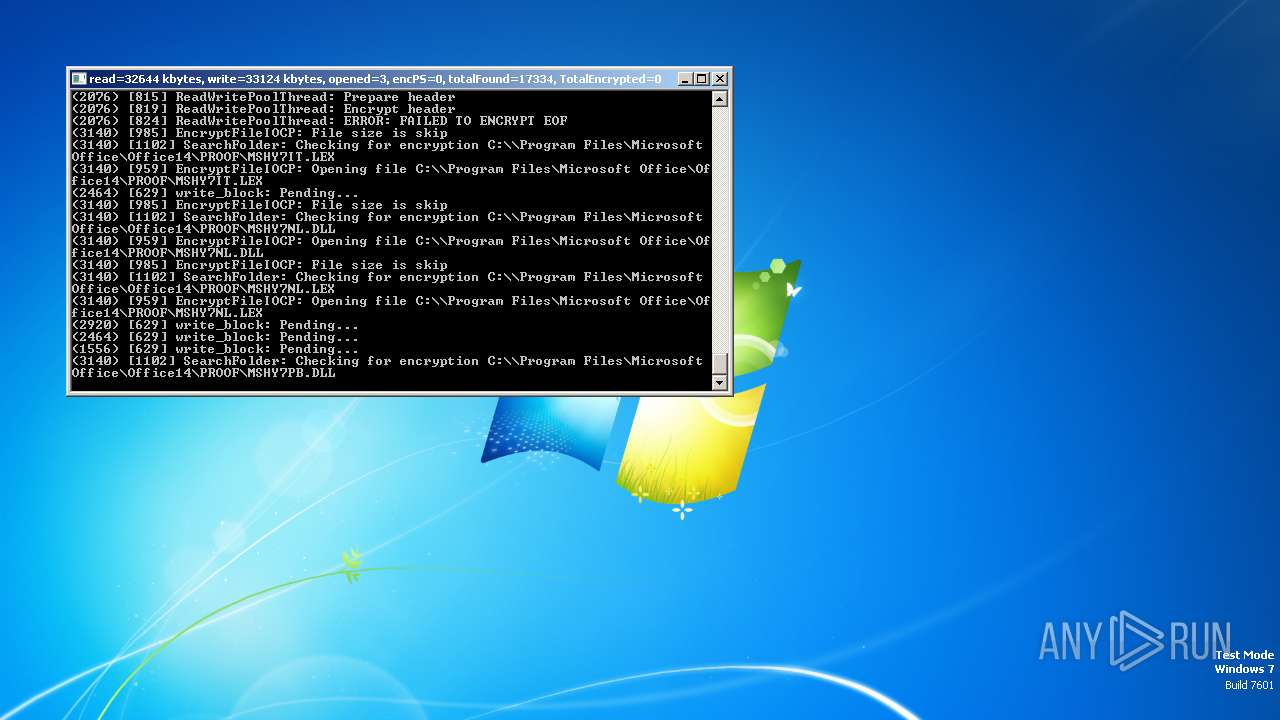
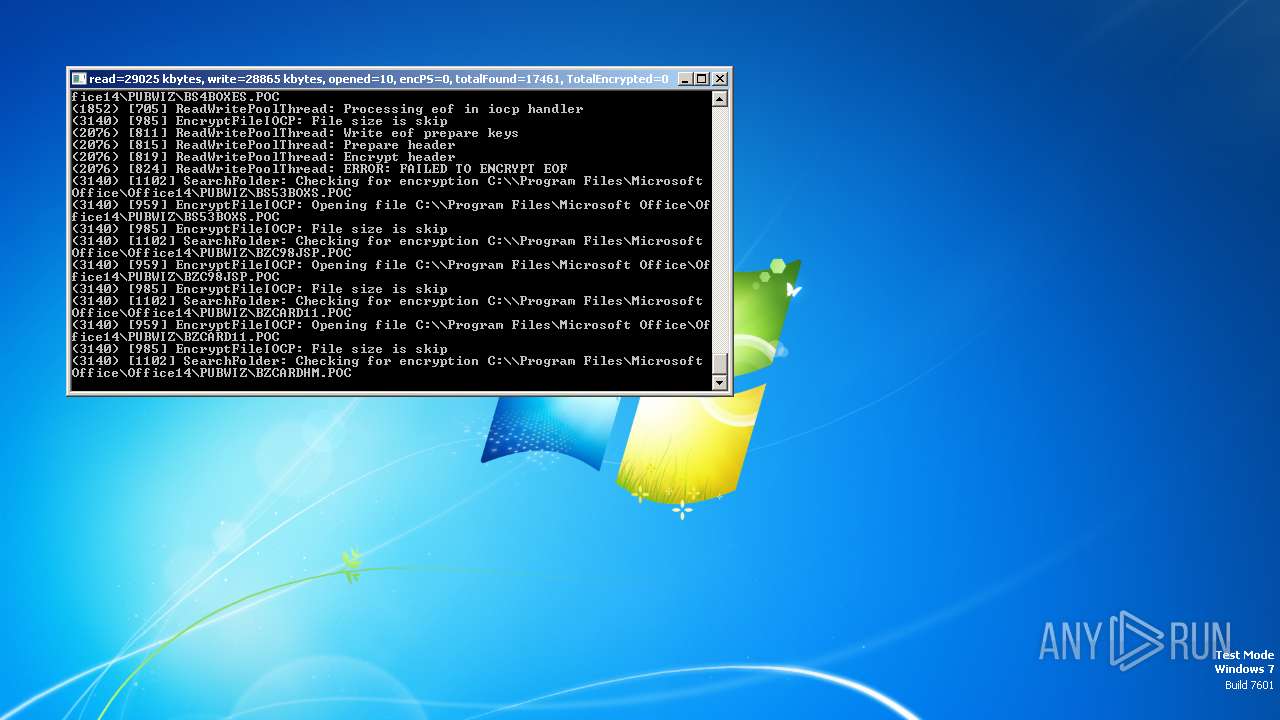
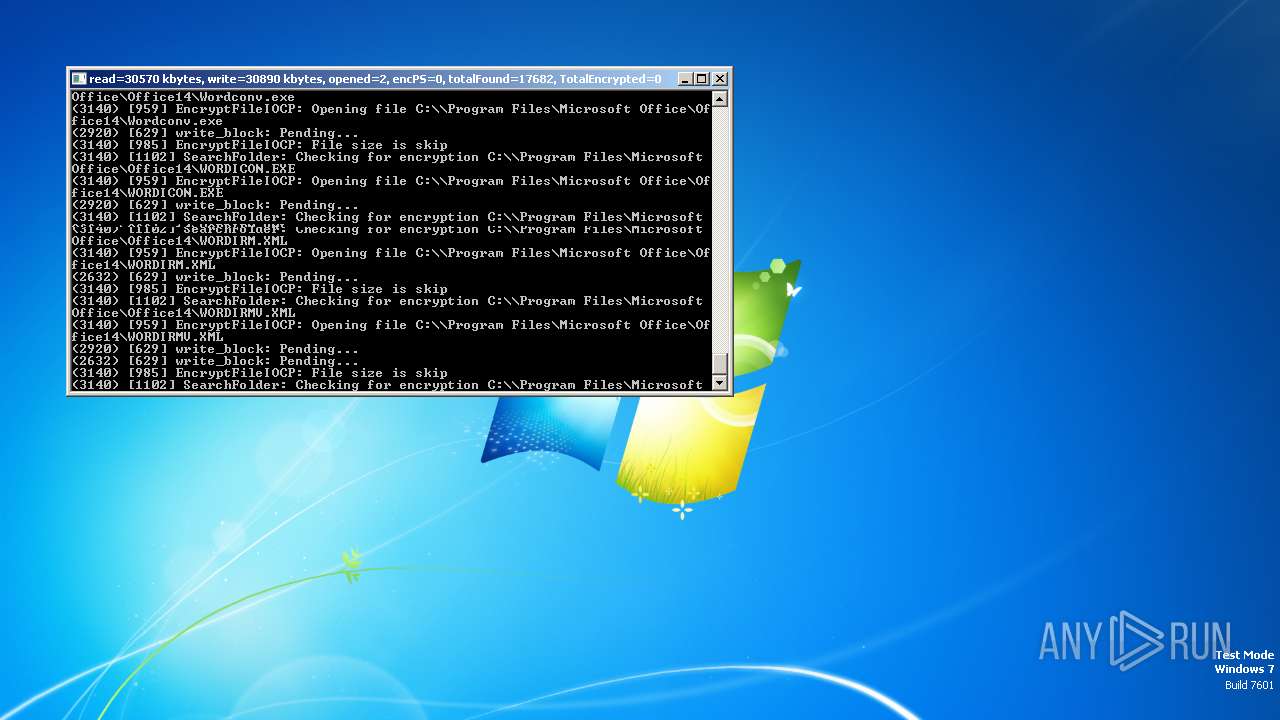
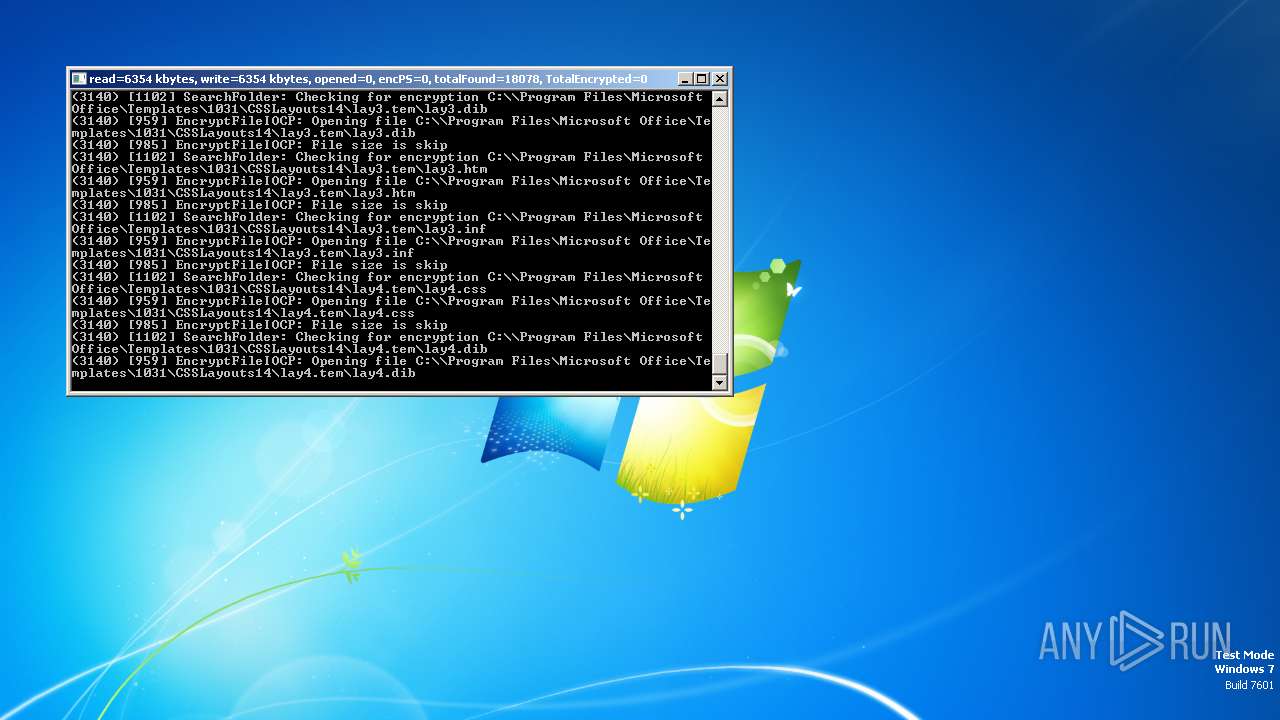
Total events
31 605
Read events
26 395
Write events
8
Delete events
5 202
Modification events
| (PID) Process: | (3064) inn.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | delete value | Name: | RegFilesHash |
Value: 1B7260FBD4AF31C7664D14CDE12BBB8969FDE909430DF866D7BEFBB09A80682B | |||
| (PID) Process: | (3064) inn.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | delete value | Name: | RegFiles0000 |
Value: C:\\hiberfil.sys | |||
| (PID) Process: | (3064) inn.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | delete value | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (3064) inn.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | delete value | Name: | SessionHash |
Value: 4CC7F4BAEC4B623353C05093B27C964B6BAC1B94F26F81614EDAF3486CD514E7 | |||
| (PID) Process: | (3064) inn.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | delete value | Name: | Owner |
Value: F80B00001EBF7E572226DA01 | |||
| (PID) Process: | (3064) inn.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (3064) inn.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | delete value | Name: | RegFilesHash |
Value: 30ED12113B958B4040BEAD12B9DD2CA32C34352A65EB2F2DD41F0979A6953F8F | |||
| (PID) Process: | (3064) inn.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | delete value | Name: | RegFiles0000 |
Value: C:\\Program Files\Adobe\Acrobat Reader DC\Resource\CMap\Identity-H | |||
| (PID) Process: | (3064) inn.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | delete value | Name: | SessionHash |
Value: D6BA757CBAD72E76E6E363829FF6820D99648BA835E4B50DFFCA26BF96BEBB91 | |||
| (PID) Process: | (3064) inn.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | delete value | Name: | RegFilesHash |
Value: 317EA9EE37D5308FC586C652A94FFC913C932EB2942CD620BB63A8E8A649B7F5 | |||
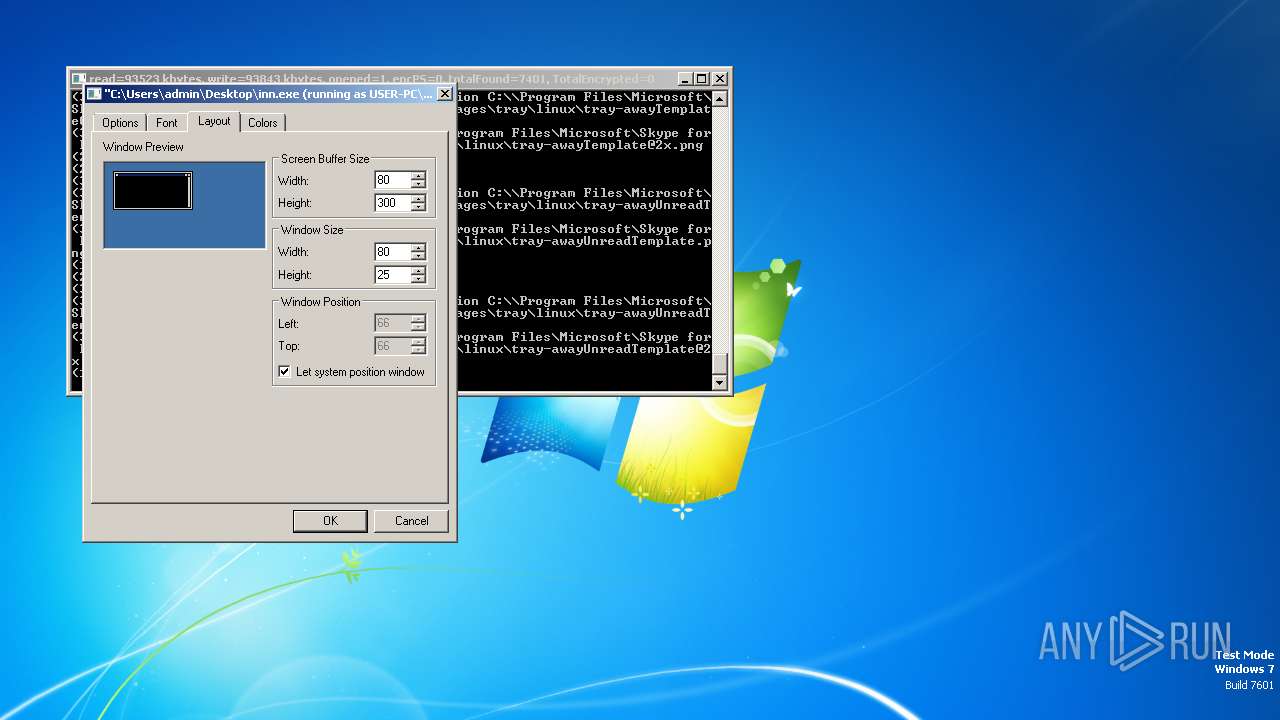
Executable files
191
Suspicious files
165
Text files
3
Unknown types
0
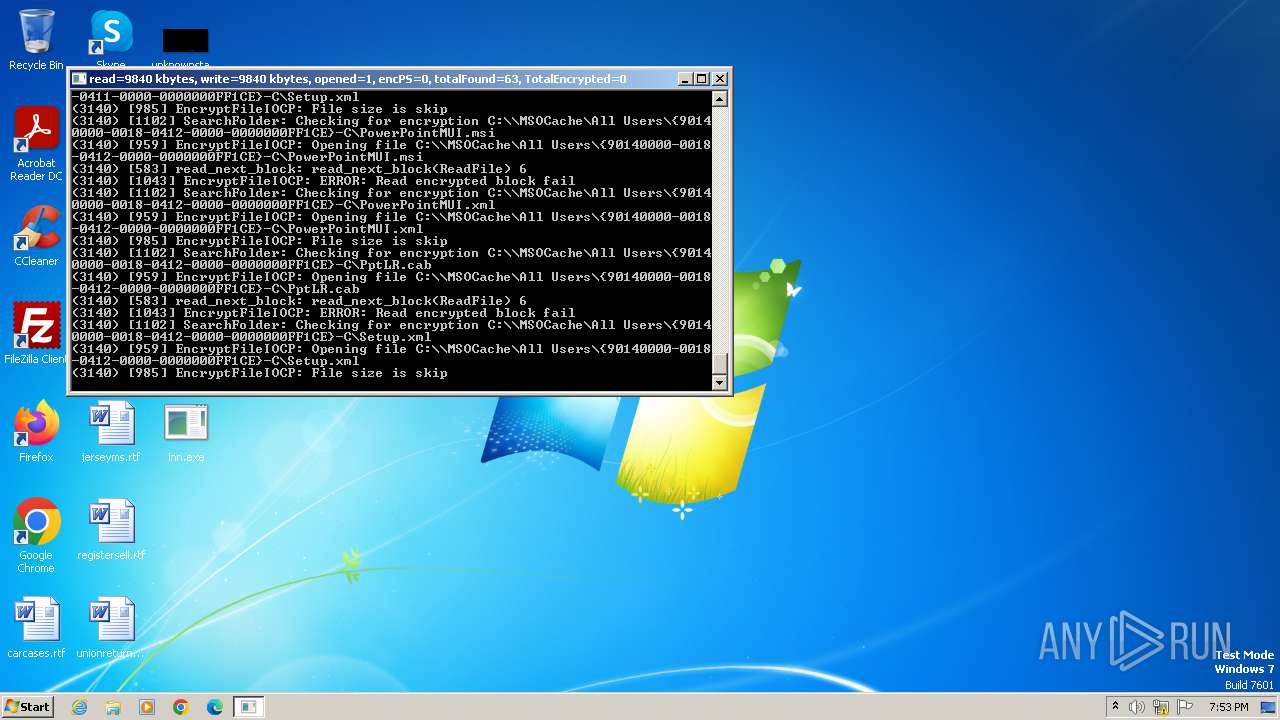
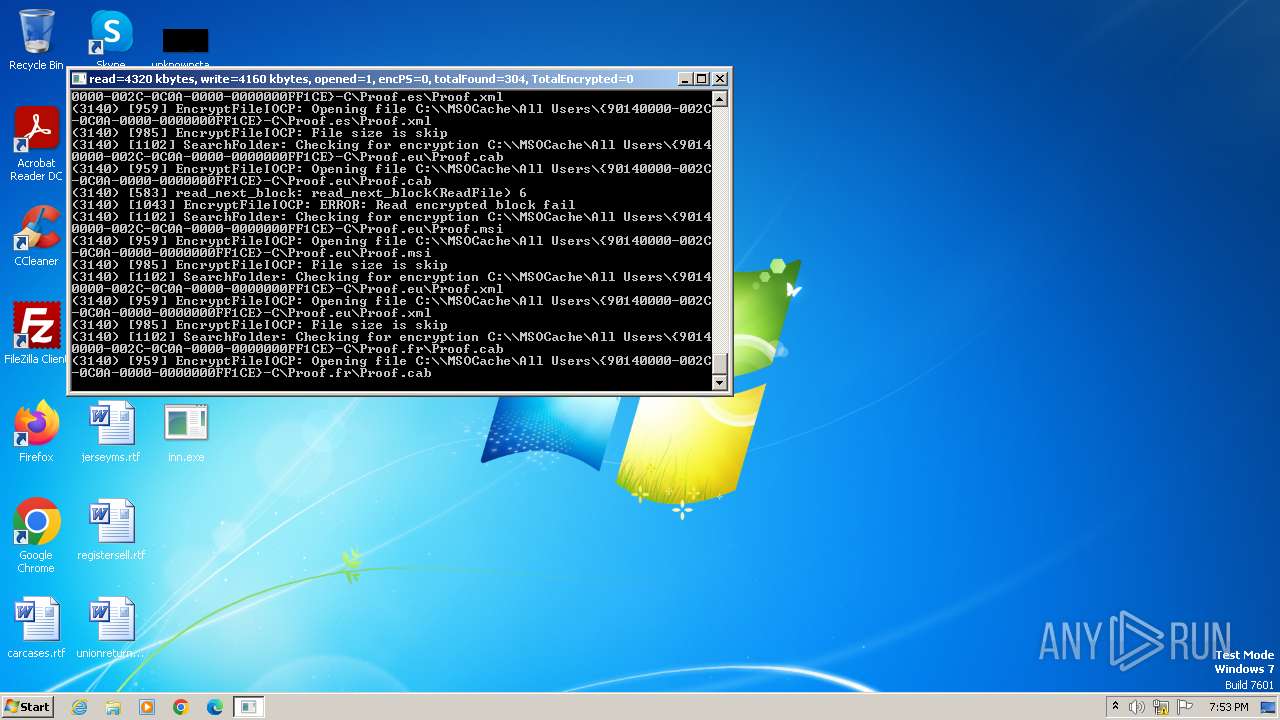
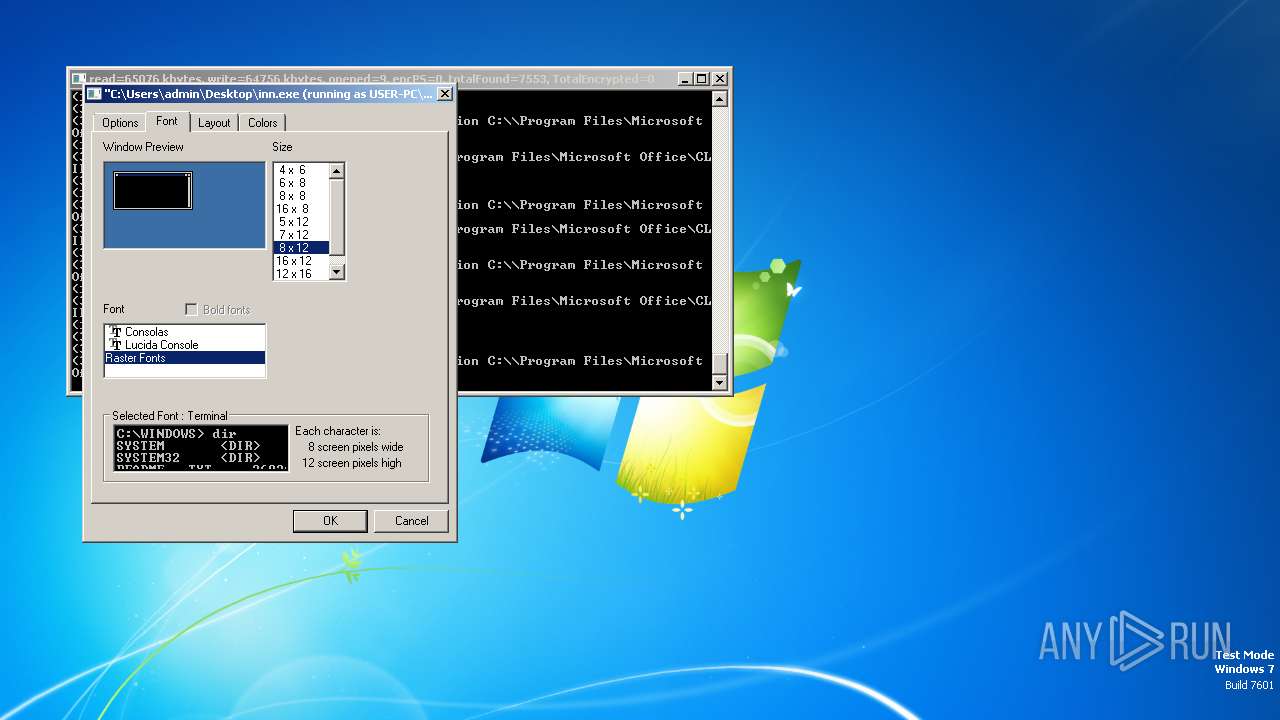
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3064 | inn.exe | C:\MSOCache\All Users\{90140000-0015-040C-0000-0000000FF1CE}-C\AccLR.cab | — | |
MD5:— | SHA256:— | |||
| 3064 | inn.exe | C:\MSOCache\All Users\{90140000-0016-0407-0000-0000000FF1CE}-C\ExcelLR.cab | — | |
MD5:— | SHA256:— | |||
| 3064 | inn.exe | C:\MSOCache\All Users\{90140000-0016-0412-0000-0000000FF1CE}-C\ExcelMUI.msi | — | |
MD5:— | SHA256:— | |||
| 3064 | inn.exe | C:\MSOCache\All Users\{90140000-0017-0419-0000-0000000FF1CE}-C\SPDLR.cab | — | |
MD5:— | SHA256:— | |||
| 3064 | inn.exe | C:\MSOCache\All Users\{90140000-0018-0419-0000-0000000FF1CE}-C\PptLR.cab | — | |
MD5:— | SHA256:— | |||
| 3064 | inn.exe | C:\MSOCache\All Users\{90140000-0019-0407-0000-0000000FF1CE}-C\PublisherMUI.msi | — | |
MD5:— | SHA256:— | |||
| 3064 | inn.exe | C:\MSOCache\All Users\{90140000-001A-0407-0000-0000000FF1CE}-C\OutlookMUI.msi | — | |
MD5:— | SHA256:— | |||
| 3064 | inn.exe | C:\MSOCache\All Users\{90140000-001B-0407-0000-0000000FF1CE}-C\WordMUI.msi | — | |
MD5:— | SHA256:— | |||
| 3064 | inn.exe | C:\MSOCache\All Users\{90140000-002C-0407-0000-0000000FF1CE}-C\Proof.de\Proof.cab | — | |
MD5:— | SHA256:— | |||
| 3064 | inn.exe | C:\MSOCache\All Users\{90140000-002C-040C-0000-0000000FF1CE}-C\Proof.ar\Proof.cab | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |