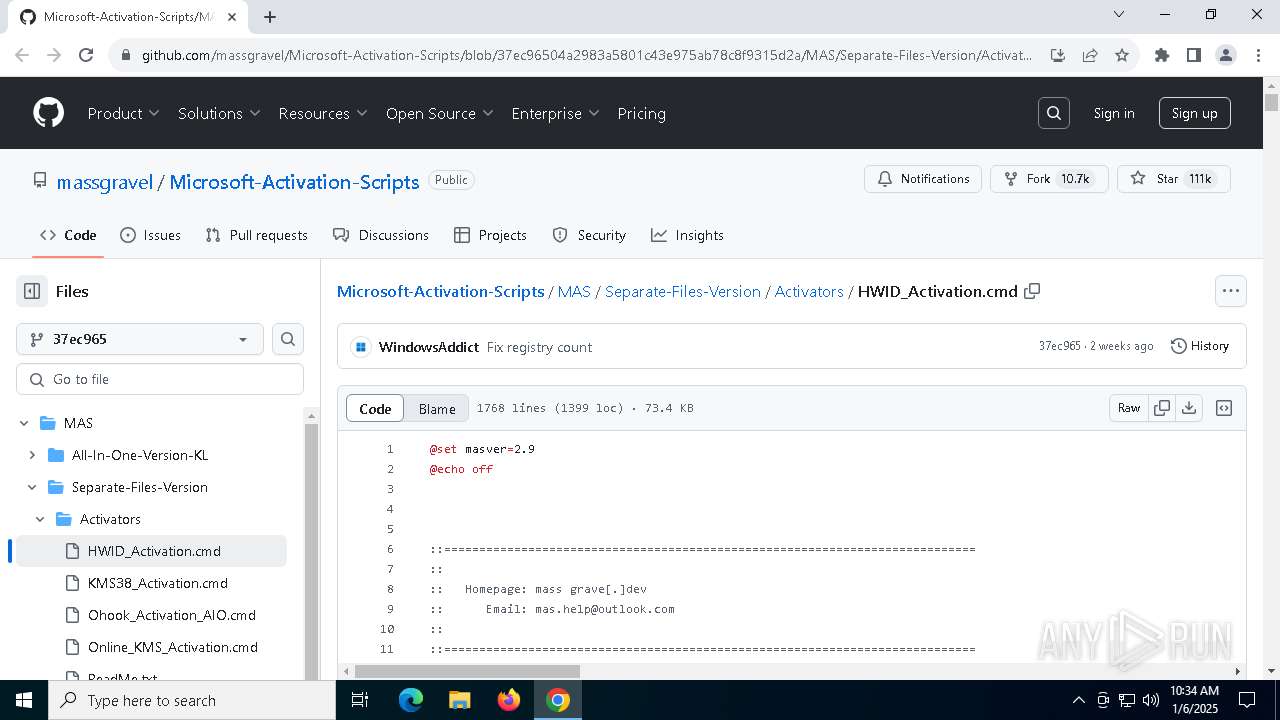
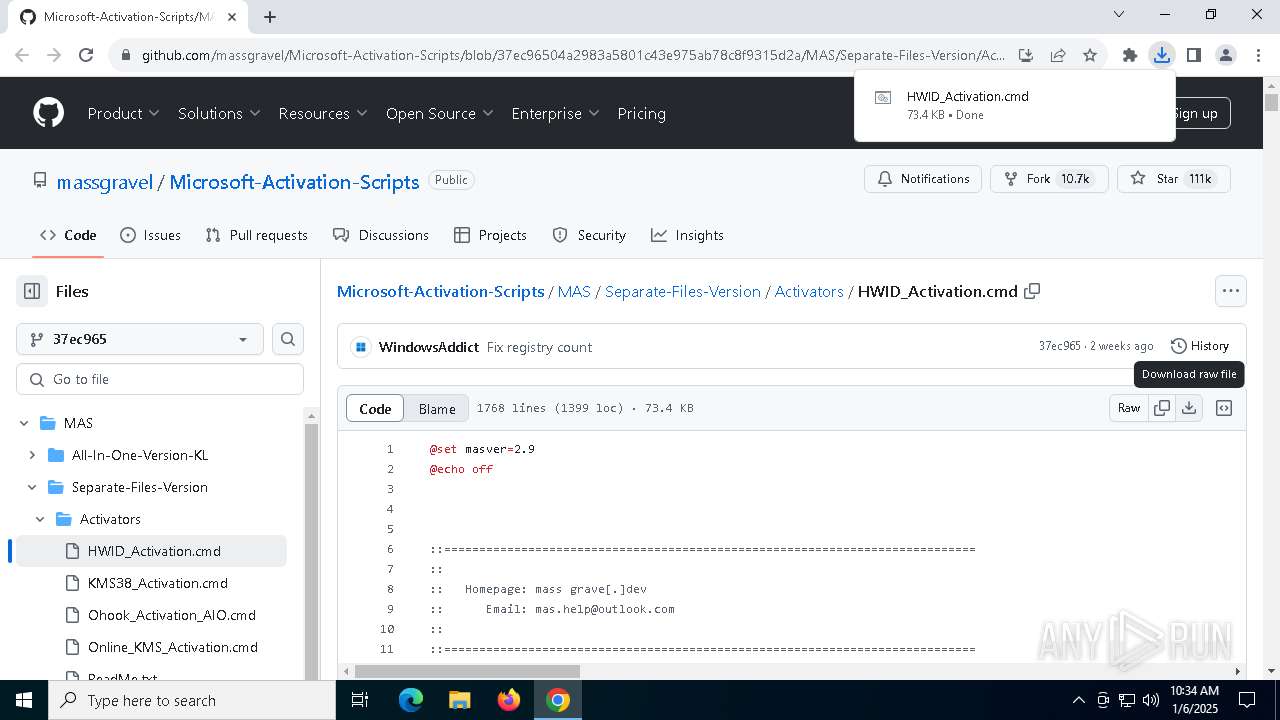
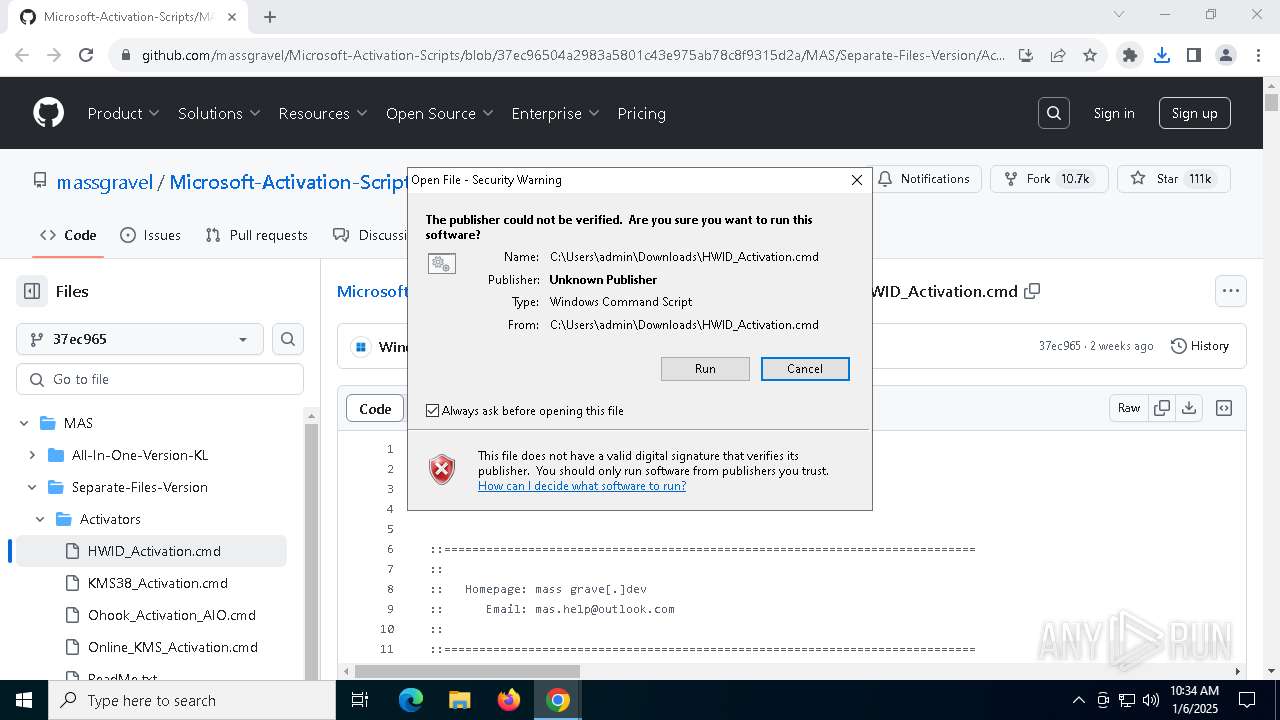
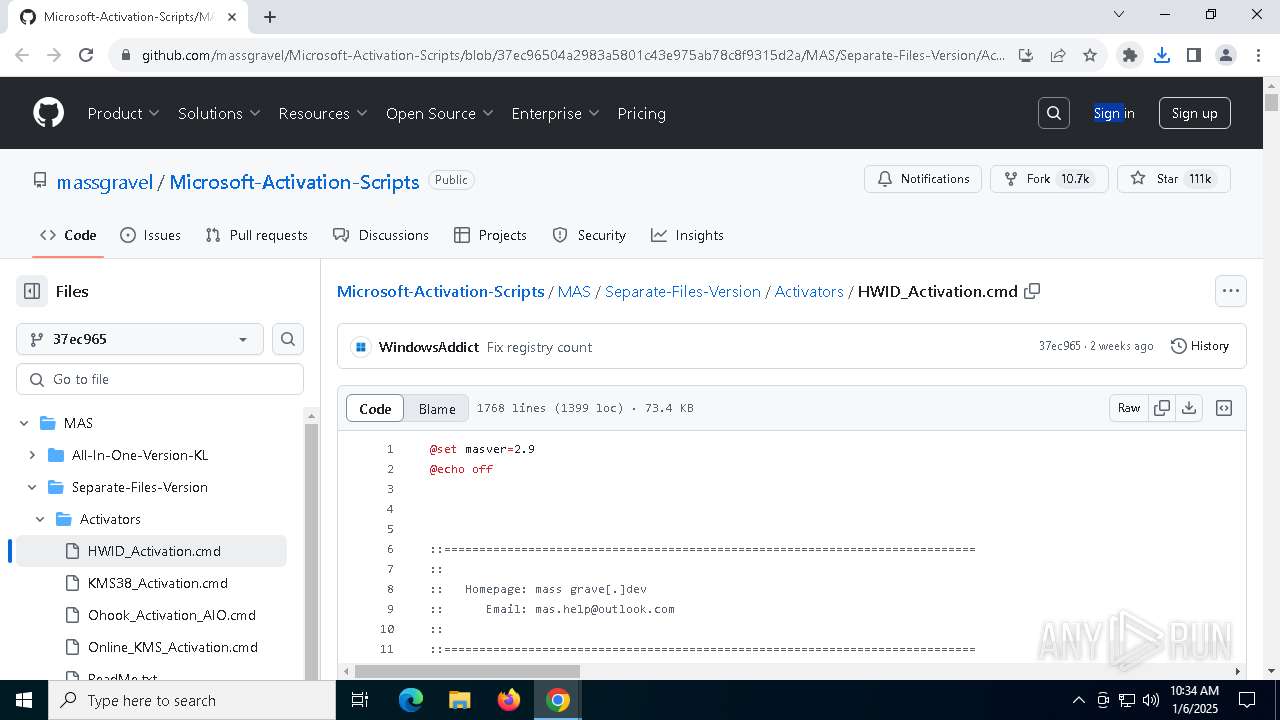
| URL: | https://github.com/massgravel/Microsoft-Activation-Scripts/blob/37ec96504a2983a5801c43e975ab78c8f9315d2a/MAS/Separate-Files-Version/Activators/HWID_Activation.cmd |
| Full analysis: | https://app.any.run/tasks/21221def-afd2-4009-8392-7f16de17cac7 |
| Verdict: | Malicious activity |
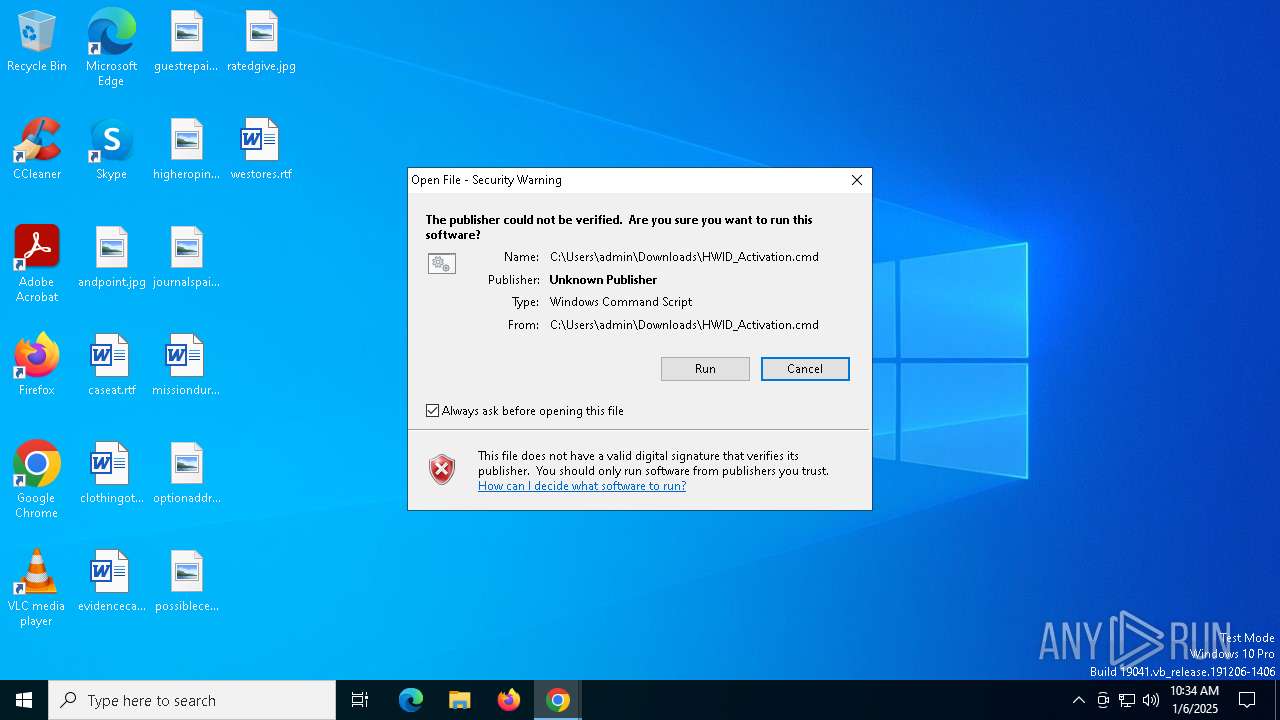
| Analysis date: | January 06, 2025, 10:34:27 |
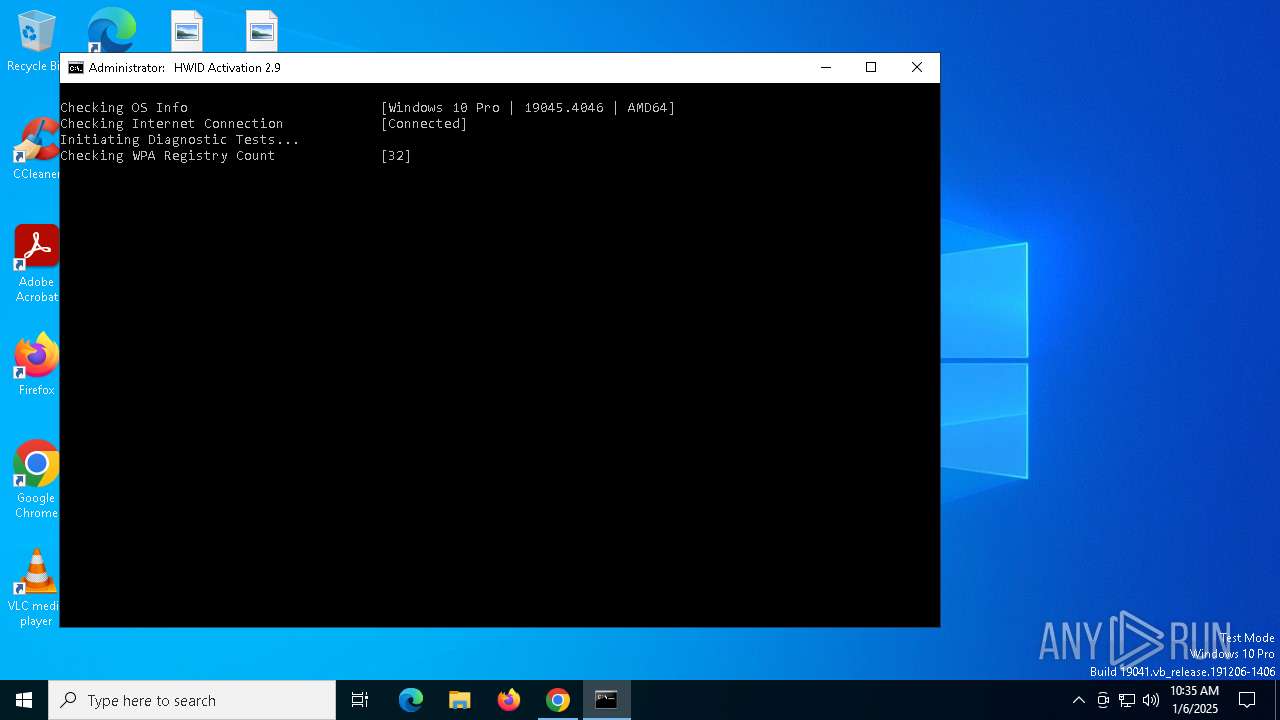
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | DF58D6DB9175F845336FA84C3E2E52F9 |
| SHA1: | D1A837058E88CC3A187A70CCB68D4A15A0585C69 |
| SHA256: | 0290910C9C0FDC08B48A27DD0C33E811828152766D434950CE2F0B1651117239 |
| SSDEEP: | 3:N8tEd4PKoHXuukGR3RLLLGXUxBzPUE35J6PXj4T5OAGCiT4XG8RMsLLbB:2uuPKzukGv/LGXUxBzM4J64T0F4XG8Rr |
MALICIOUS
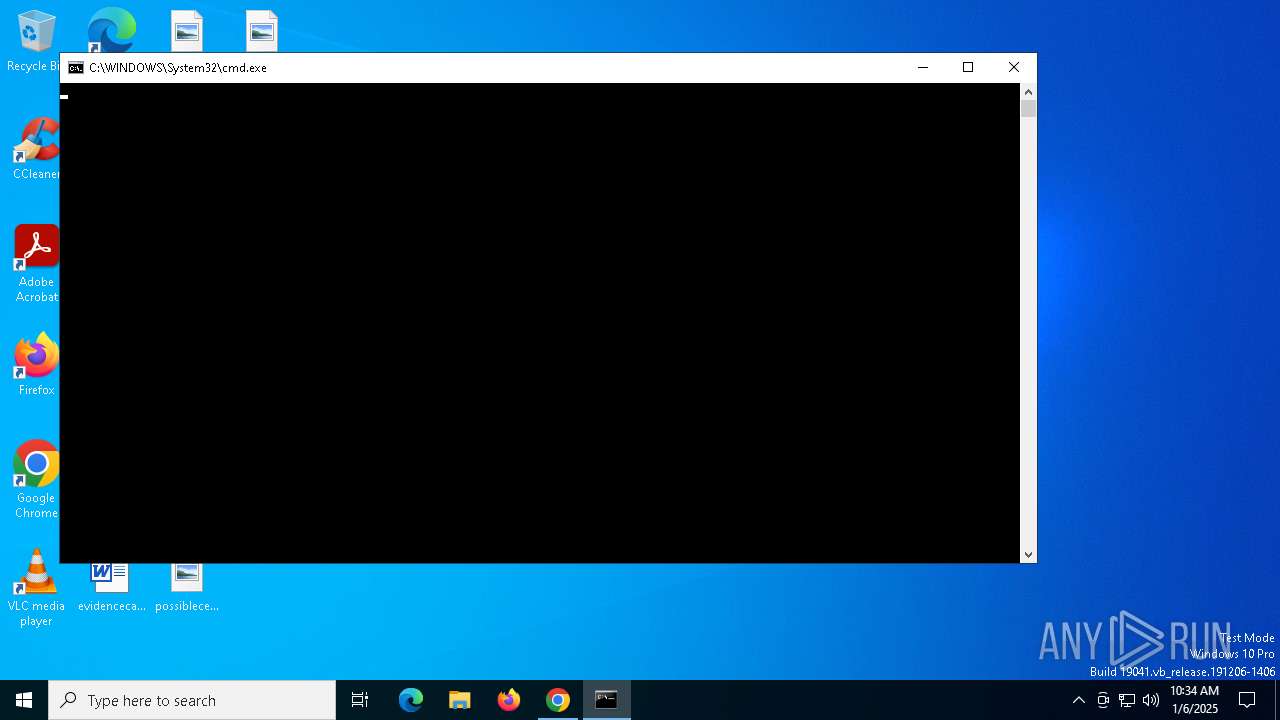
Starts CMD.EXE for commands execution
- chrome.exe (PID: 6316)
SUSPICIOUS
Application launched itself
- cmd.exe (PID: 6604)
- cmd.exe (PID: 4604)
- cmd.exe (PID: 6936)
- cmd.exe (PID: 4648)
- cmd.exe (PID: 4328)
- cmd.exe (PID: 6096)
- powershell.exe (PID: 5252)
- powershell.exe (PID: 6312)
- ClipUp.exe (PID: 5404)
- powershell.exe (PID: 1292)
Starts SC.EXE for service management
- cmd.exe (PID: 6604)
- cmd.exe (PID: 4648)
- cmd.exe (PID: 4328)
Executing commands from ".cmd" file
- chrome.exe (PID: 6316)
- cmd.exe (PID: 6604)
- powershell.exe (PID: 4716)
- cmd.exe (PID: 4648)
- cmd.exe (PID: 4328)
- powershell.exe (PID: 2996)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 6604)
- cmd.exe (PID: 4604)
- powershell.exe (PID: 4716)
- cmd.exe (PID: 4648)
- cmd.exe (PID: 6936)
- cmd.exe (PID: 6096)
- powershell.exe (PID: 2996)
- cmd.exe (PID: 4328)
Windows service management via SC.EXE
- sc.exe (PID: 4132)
- sc.exe (PID: 4468)
- sc.exe (PID: 5588)
- sc.exe (PID: 5788)
- sc.exe (PID: 1804)
- sc.exe (PID: 4984)
- sc.exe (PID: 4972)
- sc.exe (PID: 5404)
- sc.exe (PID: 1344)
- sc.exe (PID: 1864)
- sc.exe (PID: 2676)
- sc.exe (PID: 1080)
- sc.exe (PID: 4392)
- sc.exe (PID: 5308)
- sc.exe (PID: 4624)
- sc.exe (PID: 848)
- sc.exe (PID: 2432)
- sc.exe (PID: 7108)
- sc.exe (PID: 188)
- sc.exe (PID: 7116)
- sc.exe (PID: 6180)
- sc.exe (PID: 2728)
- sc.exe (PID: 3836)
- sc.exe (PID: 5888)
- sc.exe (PID: 1192)
- sc.exe (PID: 1220)
- sc.exe (PID: 5392)
- sc.exe (PID: 6964)
- sc.exe (PID: 4652)
- sc.exe (PID: 7108)
- sc.exe (PID: 1580)
- sc.exe (PID: 4704)
- sc.exe (PID: 2828)
- sc.exe (PID: 1752)
- sc.exe (PID: 7104)
- sc.exe (PID: 1888)
- sc.exe (PID: 204)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 6604)
- cmd.exe (PID: 4648)
- cmd.exe (PID: 4328)
Possibly malicious use of IEX has been detected
- cmd.exe (PID: 4976)
- cmd.exe (PID: 5316)
- cmd.exe (PID: 5340)
- cmd.exe (PID: 4328)
- cmd.exe (PID: 3928)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 4976)
- cmd.exe (PID: 6604)
- cmd.exe (PID: 5316)
- cmd.exe (PID: 5340)
- cmd.exe (PID: 4328)
- cmd.exe (PID: 4648)
- cmd.exe (PID: 188)
- powershell.exe (PID: 5252)
- cmd.exe (PID: 4136)
- cmd.exe (PID: 3928)
- cmd.exe (PID: 4528)
- cmd.exe (PID: 4984)
- powershell.exe (PID: 6312)
- powershell.exe (PID: 1292)
- cmd.exe (PID: 6540)
Probably obfuscated PowerShell command line is found
- cmd.exe (PID: 4976)
- cmd.exe (PID: 5316)
- cmd.exe (PID: 5340)
- cmd.exe (PID: 4328)
- cmd.exe (PID: 3928)
Gets content of a file (POWERSHELL)
- powershell.exe (PID: 5720)
- powershell.exe (PID: 2008)
- powershell.exe (PID: 5916)
- powershell.exe (PID: 5156)
- powershell.exe (PID: 4528)
Uses WMIC.EXE to obtain computer system information
- cmd.exe (PID: 5880)
- cmd.exe (PID: 4328)
Hides command output
- cmd.exe (PID: 3988)
- cmd.exe (PID: 5308)
- cmd.exe (PID: 3928)
- cmd.exe (PID: 3836)
- cmd.exe (PID: 6212)
- cmd.exe (PID: 5936)
- cmd.exe (PID: 1356)
- cmd.exe (PID: 1616)
- cmd.exe (PID: 4528)
- cmd.exe (PID: 4020)
- cmd.exe (PID: 7080)
The process bypasses the loading of PowerShell profile settings
- powershell.exe (PID: 5252)
- powershell.exe (PID: 6312)
- powershell.exe (PID: 1292)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 4328)
- cmd.exe (PID: 3836)
- cmd.exe (PID: 1356)
- cmd.exe (PID: 4020)
The process hides Powershell's copyright startup banner
- powershell.exe (PID: 5252)
- powershell.exe (PID: 6312)
- powershell.exe (PID: 1292)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 4328)
Uses WMIC.EXE to obtain operating system information
- cmd.exe (PID: 5308)
Detects reflection assembly loader (YARA)
- powershell.exe (PID: 2996)
Uses WMIC.EXE to obtain service application data
- cmd.exe (PID: 4328)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 6944)
INFO
The process uses the downloaded file
- chrome.exe (PID: 6316)
- chrome.exe (PID: 5460)
- powershell.exe (PID: 4716)
Checks operating system version
- cmd.exe (PID: 6604)
- cmd.exe (PID: 4648)
- cmd.exe (PID: 4328)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 5720)
- powershell.exe (PID: 2008)
- powershell.exe (PID: 5916)
- powershell.exe (PID: 5156)
- powershell.exe (PID: 4528)
Application launched itself
- chrome.exe (PID: 6316)
Starts MODE.COM to configure console settings
- mode.com (PID: 2728)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 6176)
- WMIC.exe (PID: 5392)
- WMIC.exe (PID: 1888)
- WMIC.exe (PID: 3632)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 1140)
Executable content was dropped or overwritten
- chrome.exe (PID: 836)
The sample compiled with english language support
- chrome.exe (PID: 836)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
426
Monitored processes
288
Malicious processes
6
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 188 | C:\WINDOWS\System32\cmd.exe /c "powershell.exe $AssemblyBuilder = [AppDomain]::CurrentDomain.DefineDynamicAssembly(4, 1); $ModuleBuilder = $AssemblyBuilder.DefineDynamicModule(2, $False); $TypeBuilder = $ModuleBuilder.DefineType(0); [void]$TypeBuilder.DefinePInvokeMethod('SLGetWindowsInformationDWORD', 'slc.dll', 'Public, Static', 1, [int], @([String], [int].MakeByRefType()), 1, 3); $Sku = 0; [void]$TypeBuilder.CreateType()::SLGetWindowsInformationDWORD('Kernel-BrandingInfo', [ref]$Sku); $Sku" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 188 | sc start ClipSVC | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 1056 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 204 | find /i "kaspersky.com" C:\WINDOWS\System32\drivers\etc\hosts | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 204 | sc start Winmgmt | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 1056 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 396 | cmd | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 420 | C:\WINDOWS\System32\cmd.exe /S /D /c" echo "C:\Users\admin\Downloads\HWID_Activation.cmd" " | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 624 | find /i "RUNNING" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (grep) Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 624 | C:\WINDOWS\System32\cmd.exe /c ver | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 624 | reg delete "HKU\S-1-5-20\Software\Microsoft\Windows NT\CurrentVersion\SoftwareProtectionPlatform\PersistedSystemState" /v "SuppressRulesEngine" /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 776 | find /i "kaspersky.com" C:\WINDOWS\System32\drivers\etc\hosts | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
135 870
Read events
135 839
Write events
23
Delete events
8
Modification events
| (PID) Process: | (6316) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6316) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6316) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6316) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6316) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (5460) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {2781761E-28E0-4109-99FE-B9D127C57AFE} {56FFCC30-D398-11D0-B2AE-00A0C908FA49} 0xFFFF |
Value: 0100000000000000910D05982660DB01 | |||
| (PID) Process: | (4980) powershell.exe | Key: | HKEY_CURRENT_USER\Control Panel\International\Geo |
| Operation: | write | Name: | Name |
Value: US | |||
| (PID) Process: | (4980) powershell.exe | Key: | HKEY_CURRENT_USER\Control Panel\International\Geo |
| Operation: | write | Name: | Nation |
Value: 244 | |||
| (PID) Process: | (624) reg.exe | Key: | HKEY_USERS\S-1-5-20\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SoftwareProtectionPlatform\PersistedSystemState |
| Operation: | delete value | Name: | SuppressRulesEngine |
Value: | |||
| (PID) Process: | (4120) powershell.exe | Key: | HKEY_CURRENT_USER\Control Panel\International\Geo |
| Operation: | write | Name: | Name |
Value: US | |||
Executable files
5
Suspicious files
149
Text files
92
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6316 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF135ecd.TMP | — | |
MD5:— | SHA256:— | |||
| 6316 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6316 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF135ecd.TMP | — | |
MD5:— | SHA256:— | |||
| 6316 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6316 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF135edc.TMP | — | |
MD5:— | SHA256:— | |||
| 6316 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6316 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF135edc.TMP | — | |
MD5:— | SHA256:— | |||
| 6316 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF135edc.TMP | — | |
MD5:— | SHA256:— | |||
| 6316 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF135edc.TMP | — | |
MD5:— | SHA256:— | |||
| 6316 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
25
TCP/UDP connections
63
DNS requests
54
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1876 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
6548 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
1876 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
1876 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
2800 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
1876 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
3996 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5064 | SearchApp.exe | 104.126.37.161:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
5064 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6724 | chrome.exe | 64.233.166.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
ocsp.digicert.com |
| unknown |
github.com |
| shared |
accounts.google.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
github.githubassets.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6724 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
6724 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |